| URL: | https://player.jilkatha.com/ |
| Full analysis: | https://app.any.run/tasks/bbbf9b9d-8eb5-4839-b4b8-445082188344 |
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2023, 19:55:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 51DB7197A6A5FB192978C2E6040E5150 |
| SHA1: | CF0C07C27389972FCE1FB3AAF537310E2C190076 |
| SHA256: | 3B95199FF731D839A08B3A32BF6D8ACBB1633F5D7859C996A1D91B198C3D9A6B |
| SSDEEP: | 3:N8N1Y0JrRWyGn:2bYARm |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 116)
The process uses the downloaded file
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://player.jilkatha.com/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2032 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:116 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2780 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\System32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
Total events
26 481
Read events
26 409
Write events
70
Delete events
2
Modification events
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
0
Suspicious files
122
Text files
438
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:22C42A552B32BD5EE8AD65813100E513 | SHA256:AFF8FBC1958929AECFF5CF6A0F676752152B2E8DC3CB2E057C5E77D59B5DB2CC | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:074CE4F8C058883263F09A67A1B80438 | SHA256:A6AF239CA548A4481CC7D3FAEA4DBE17719FA41D62ED75A30E00C66F99CB1A0E | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:B91FC7390E3C5D801BB4294C6190049A | SHA256:8BF10B24636E960D7A4A3B38343D19112C8D73B275CBA0952FA1AC16C00BD445 | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8F8712BCE78D28F9C5E3E950CD93EADA_65D3F18F78AEAA18B0E58242F7706360 | binary | |
MD5:E2A9235A46113C2617BDB71030C79867 | SHA256:419AC3D8D36775335B515548514C0719668A06085074B4C003AF29D2ADAD5282 | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8F8712BCE78D28F9C5E3E950CD93EADA_7A3CFFC47DEA5CADAB91C1F578106443 | binary | |
MD5:435D5A1E5B2B79B408C6B9A98D349401 | SHA256:E617EFB449FC6113DB226D562B43E4D30494DCF72EBF7113DE12592EB6EE2A3E | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\FA0A17BC17FF10008872A7205D0D43E2_608DEF97DFACECDA8E97C6F270153A4F | binary | |
MD5:D2341D2F79F90C22A53A7EA5EAB74F46 | SHA256:F67CD426B04EF2E1D5F98754ACAF12DA5B796A0DF56DADEC1CBECF60048494F6 | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8F8712BCE78D28F9C5E3E950CD93EADA_65D3F18F78AEAA18B0E58242F7706360 | binary | |
MD5:274C286BA0A3E591D9B14CBD499E26CC | SHA256:1FC82CDC26713D7DCE914DB013DBC741CAD91D8B4FE3DFA7865E2446A24C13C0 | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\MTAwMTA2XzE3MDE0MDEyOTAzMjA=[1].jpg | image | |
MD5:AE2B129FC7EF98F3911CEC50F454488E | SHA256:851CF663E680387FCAB3D6B6FE59A0D0305DD7CDA7F78DD58928FDA433F97CA7 | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\MZGBHIVQ.htm | html | |
MD5:36B0E7F84B63EF91A4D9915AAD31A9A4 | SHA256:BB30F5DA69A8CA83C3906431C3DCD672767C3E5A61965DE892814572321A7D71 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
161
TCP/UDP connections
250
DNS requests
53
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2032 | iexplore.exe | GET | 200 | 2.19.198.57:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?53bfb7cf8a6cf97e | unknown | compressed | 4.66 Kb | unknown |
2032 | iexplore.exe | GET | 200 | 2.19.198.57:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?129d20c84d8c4223 | unknown | compressed | 4.66 Kb | unknown |
2032 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
2032 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | binary | 724 b | unknown |
2032 | iexplore.exe | GET | 200 | 163.181.56.215:80 | http://ocsp.dcocsp.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAoEcNCWvIoSyJCm34Ju7Es%3D | unknown | binary | 471 b | unknown |
2032 | iexplore.exe | GET | 200 | 163.181.56.215:80 | http://ocsp.dcocsp.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSmVYFXwi%2FRq9wx3PKhB8lC%2FFYUyAQUkZ9eMRWuEJ%2BtYMH3wcyqSDQvDCYCEARG1gQtWCJqly6jHNwHlBA%3D | unknown | binary | 471 b | unknown |
2032 | iexplore.exe | GET | — | 163.181.56.215:80 | http://ocsp.dcocsp.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSmVYFXwi%2FRq9wx3PKhB8lC%2FFYUyAQUkZ9eMRWuEJ%2BtYMH3wcyqSDQvDCYCEAJ%2BYV%2FN5W2THg4NuR8pUi8%3D | unknown | — | — | unknown |
2032 | iexplore.exe | GET | 200 | 163.181.56.215:80 | http://ocsp.dcocsp.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSmVYFXwi%2FRq9wx3PKhB8lC%2FFYUyAQUkZ9eMRWuEJ%2BtYMH3wcyqSDQvDCYCEAJ%2BYV%2FN5W2THg4NuR8pUi8%3D | unknown | binary | 471 b | unknown |
2032 | iexplore.exe | GET | 200 | 163.181.56.215:80 | http://ocsp.dcocsp.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSmVYFXwi%2FRq9wx3PKhB8lC%2FFYUyAQUkZ9eMRWuEJ%2BtYMH3wcyqSDQvDCYCEAJ%2BYV%2FN5W2THg4NuR8pUi8%3D | unknown | binary | 471 b | unknown |
2032 | iexplore.exe | GET | 200 | 163.181.56.215:80 | http://ocsp.dcocsp.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSmVYFXwi%2FRq9wx3PKhB8lC%2FFYUyAQUkZ9eMRWuEJ%2BtYMH3wcyqSDQvDCYCEAJ%2BYV%2FN5W2THg4NuR8pUi8%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2032 | iexplore.exe | 104.21.52.2:443 | player.jilkatha.com | CLOUDFLARENET | — | unknown |
2032 | iexplore.exe | 2.19.198.57:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2032 | iexplore.exe | 142.250.186.131:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
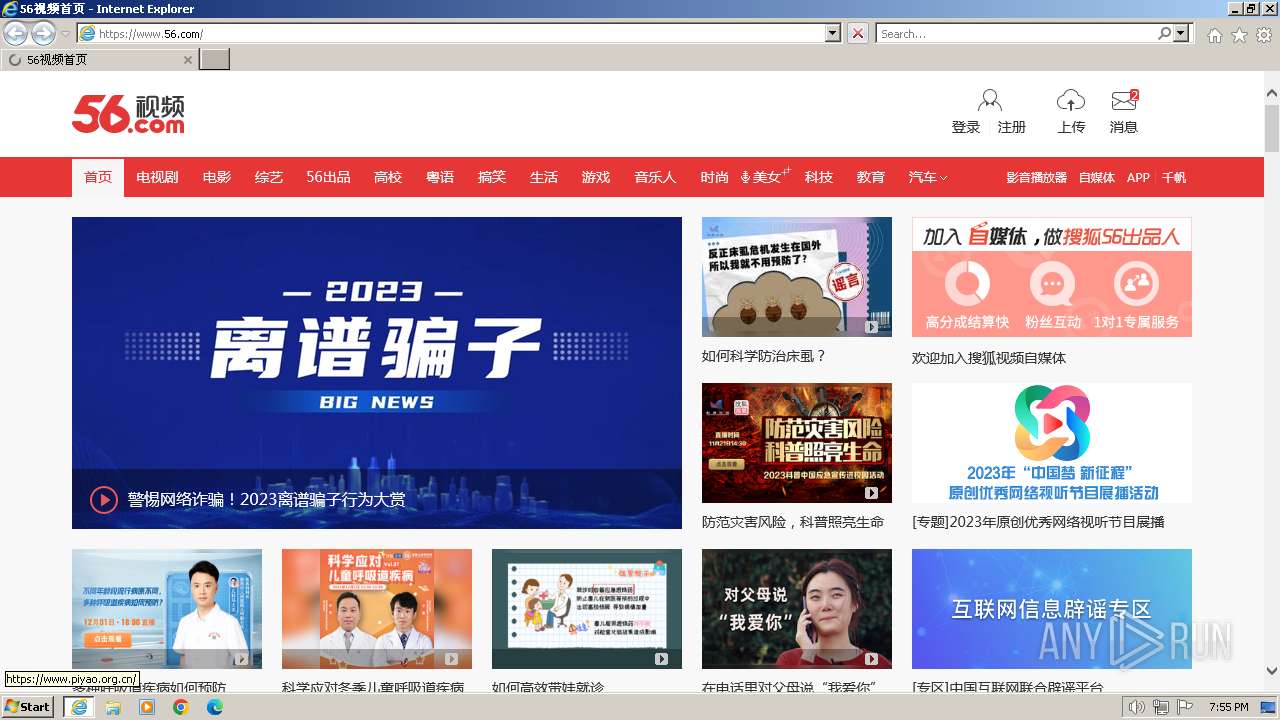
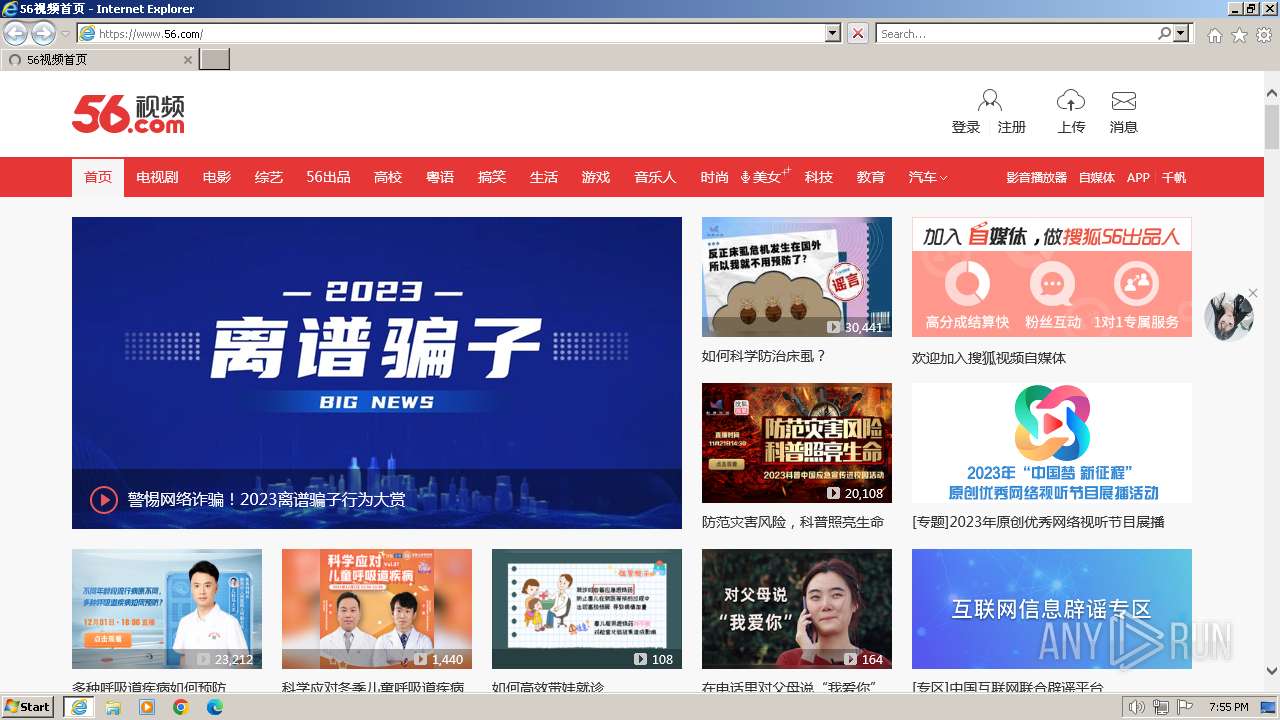
2032 | iexplore.exe | 52.175.9.163:443 | www.56.com | MICROSOFT-CORP-MSN-AS-BLOCK | HK | unknown |
2032 | iexplore.exe | 163.181.56.215:80 | ocsp.dcocsp.cn | Zhejiang Taobao Network Co.,Ltd | DE | unknown |
2032 | iexplore.exe | 138.113.101.21:443 | s2.56img.com | QUANTILNETWORKS | US | unknown |
2032 | iexplore.exe | 138.113.101.19:443 | uface.56img.com | QUANTILNETWORKS | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
player.jilkatha.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.56.com |
| unknown |
ocsp.dcocsp.cn |
| whitelisted |
s2.56img.com |
| whitelisted |
css.tv.itc.cn |
| whitelisted |
js.tv.itc.cn |
| unknown |
s1.56img.com |
| whitelisted |
tv.sohu.com |
| unknown |