| File name: | Install-Script.exe |
| Full analysis: | https://app.any.run/tasks/092f3629-e78c-4cda-923f-ac9cd1be6108 |
| Verdict: | Malicious activity |
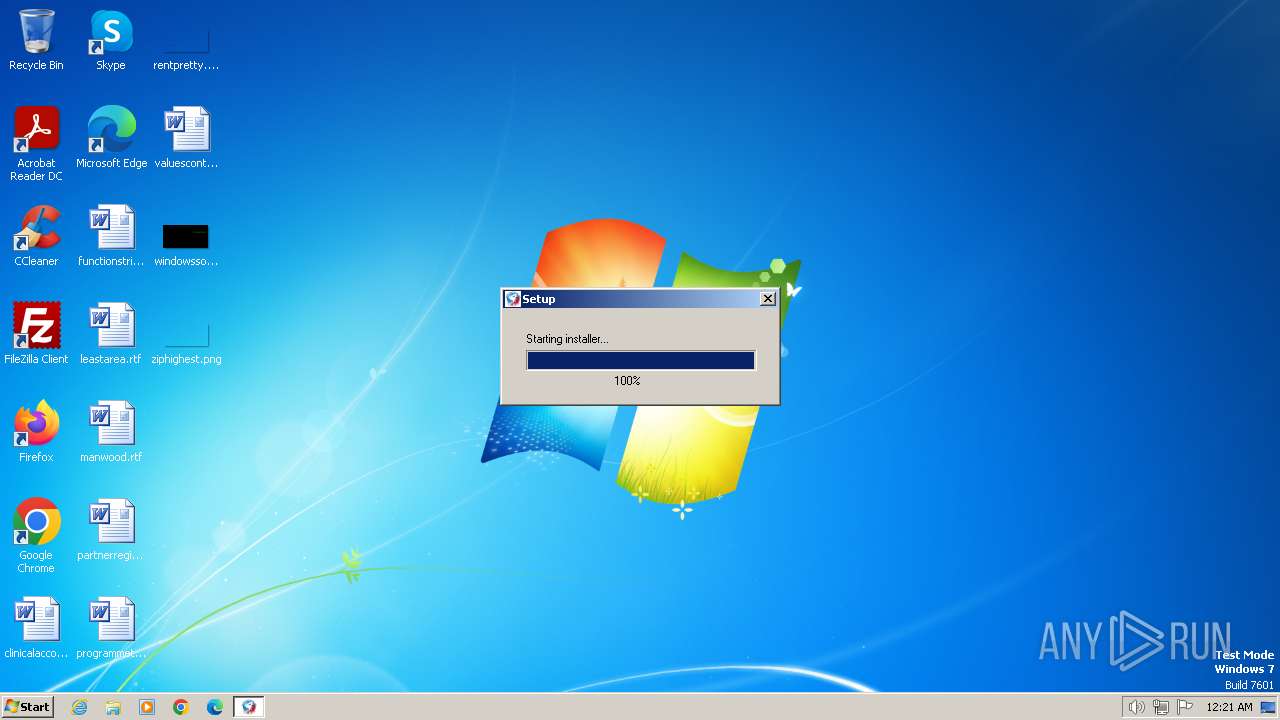
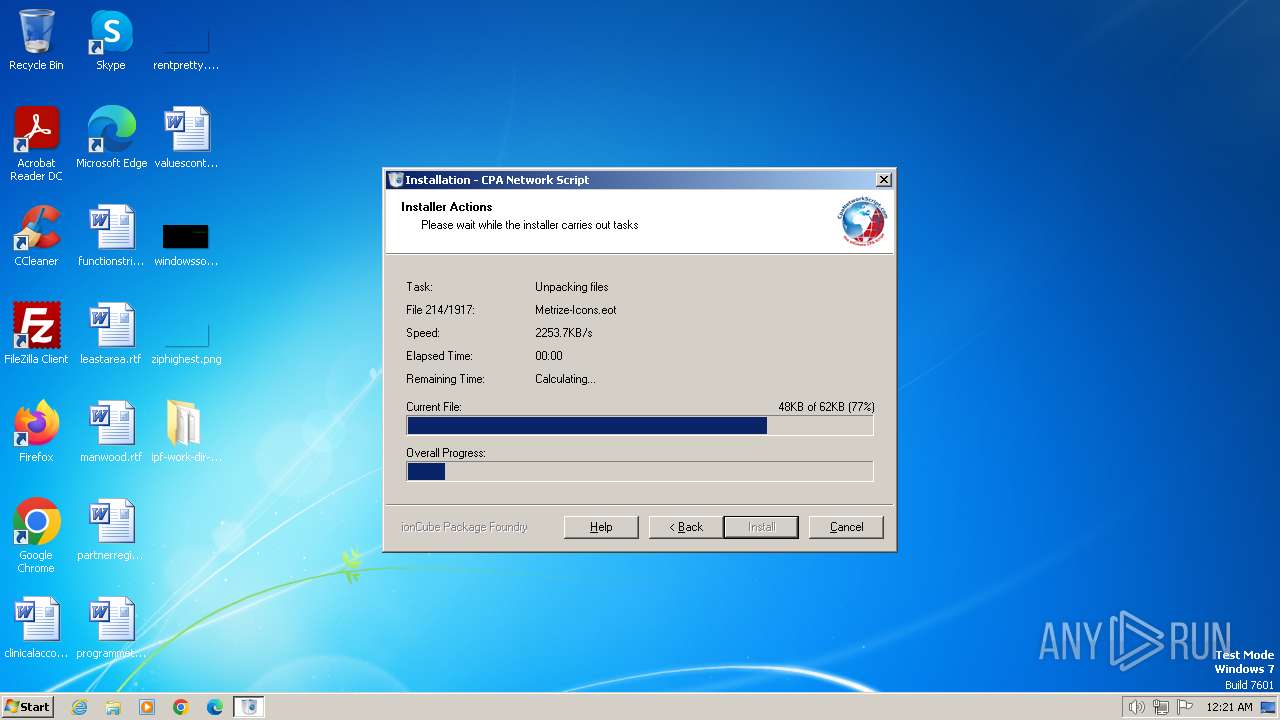
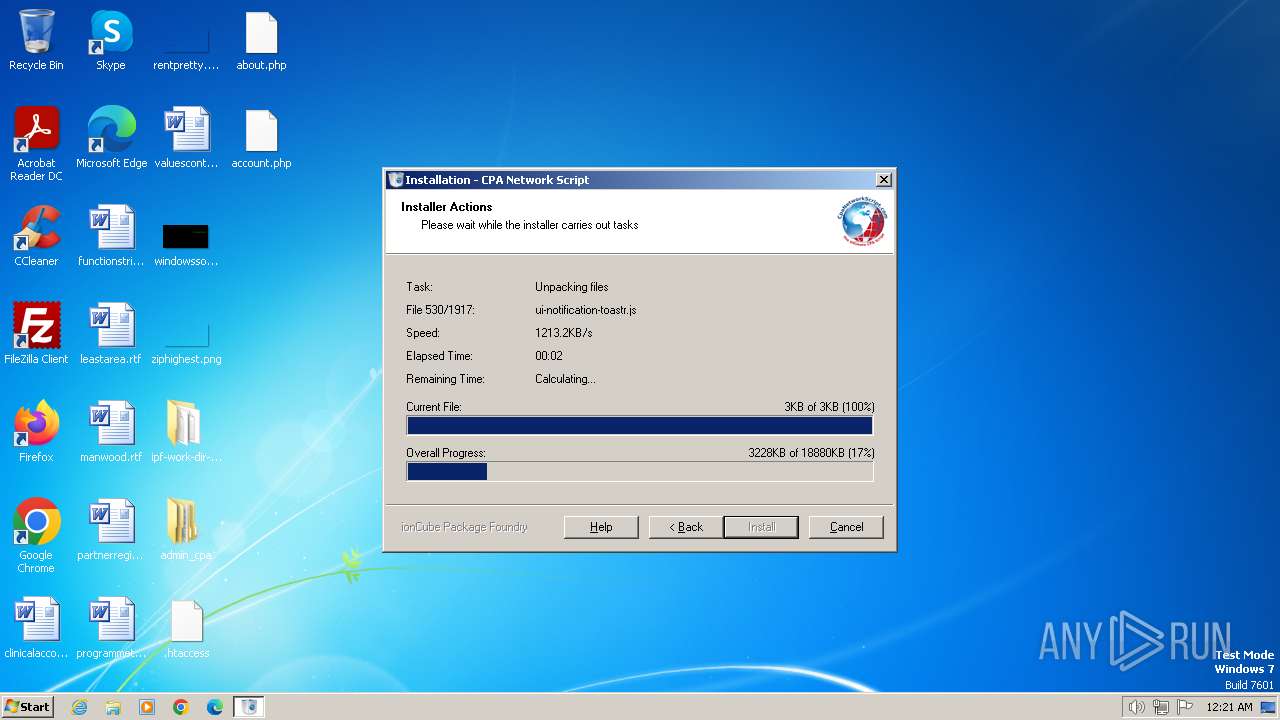
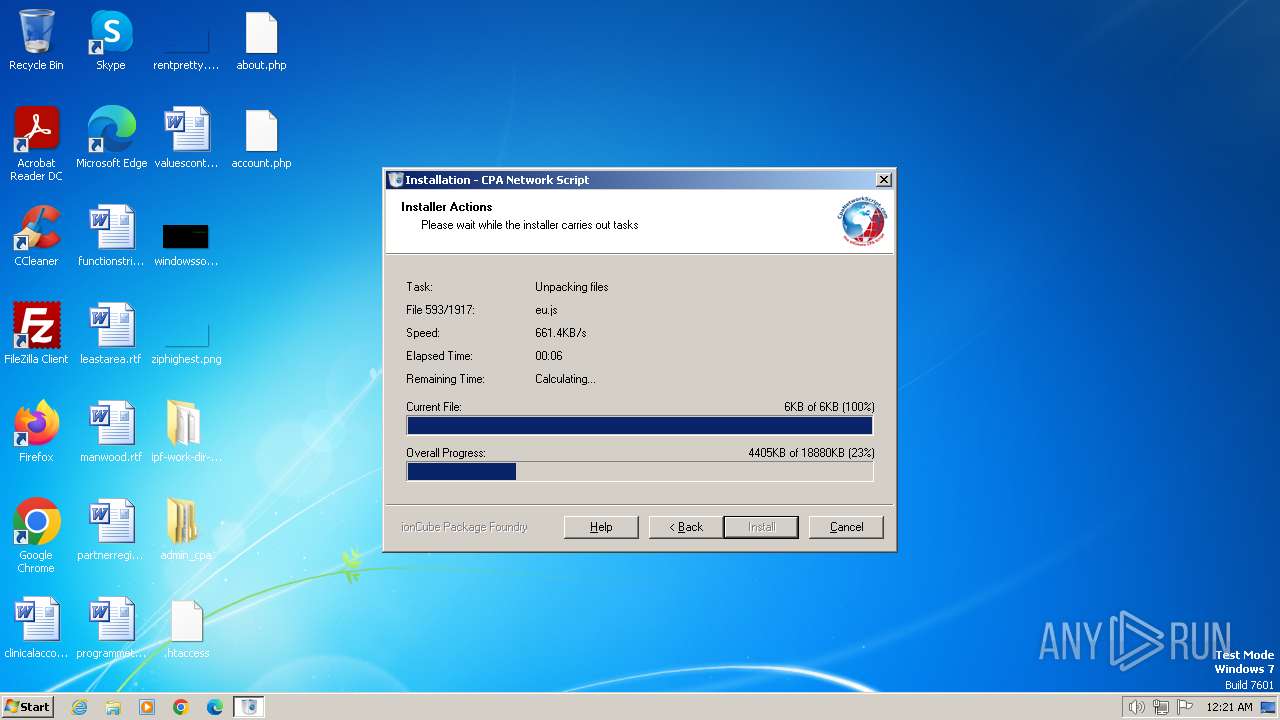
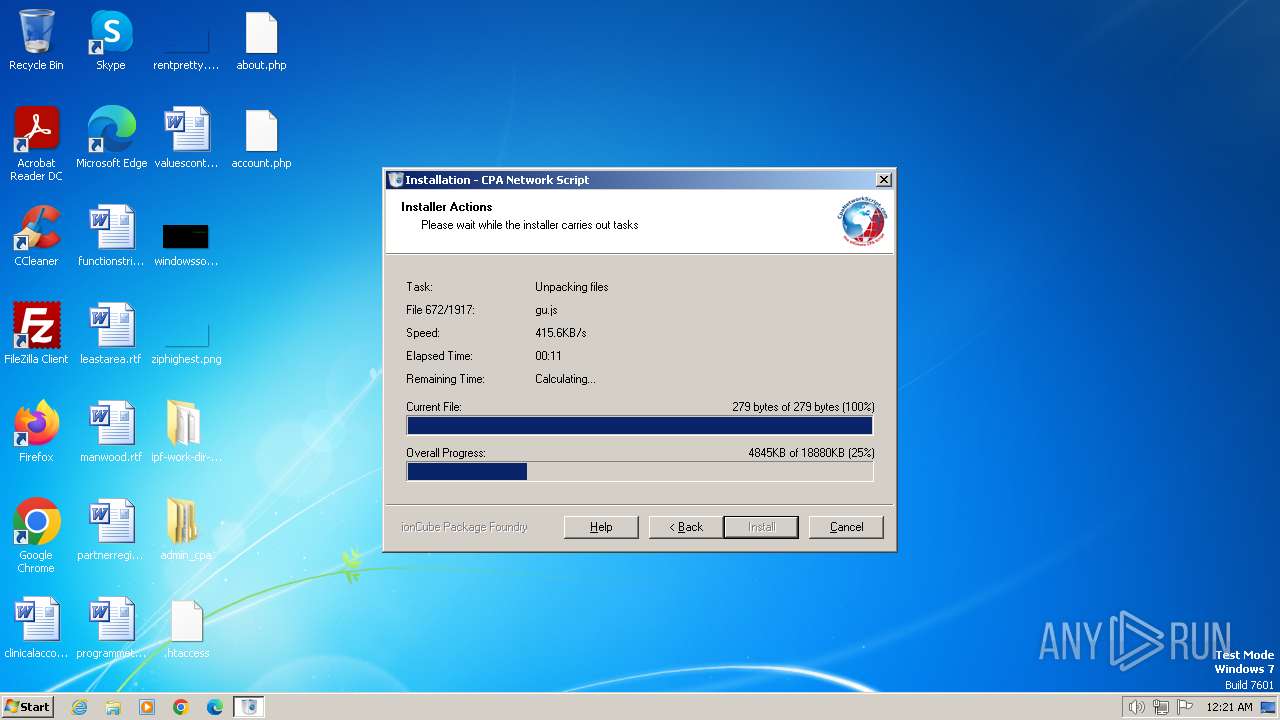
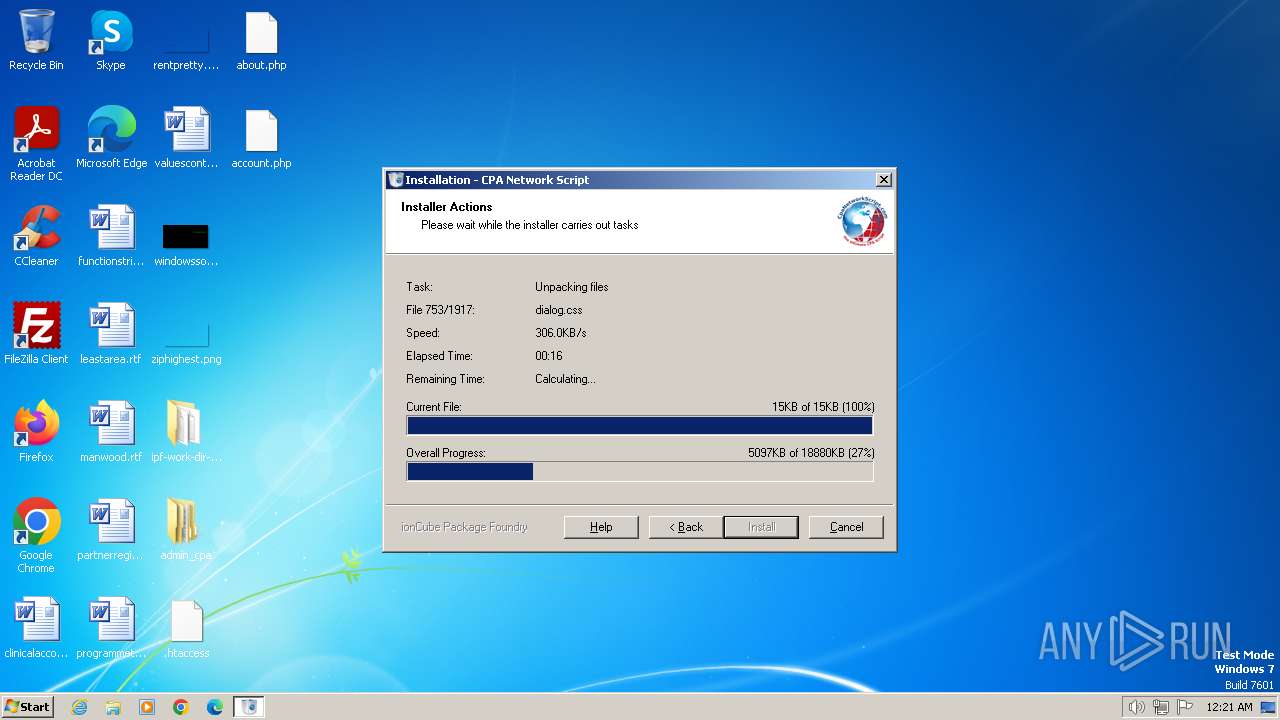
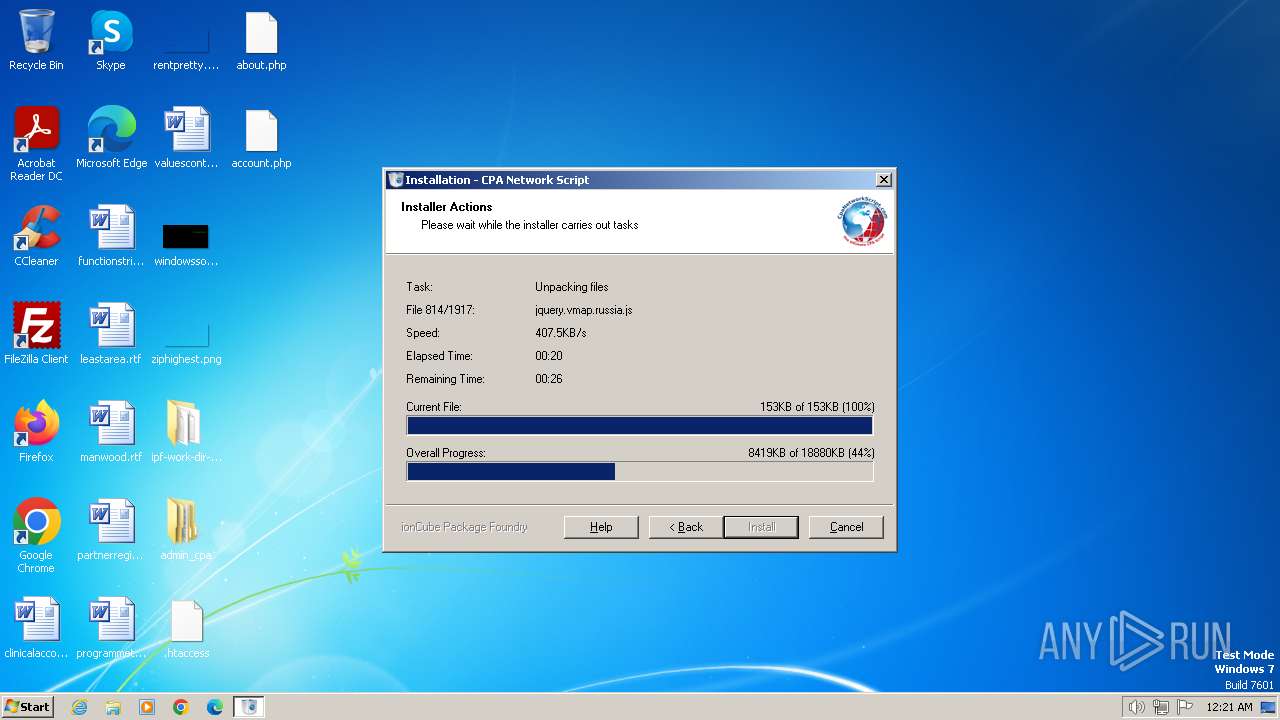
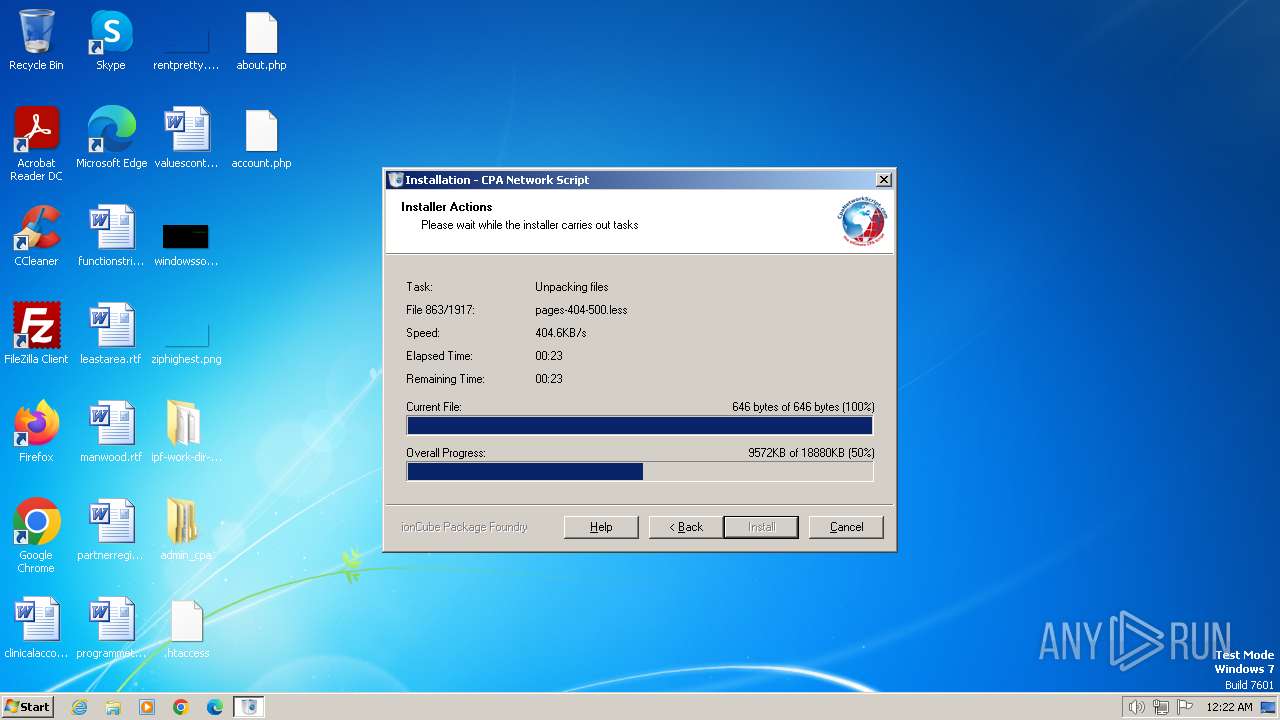
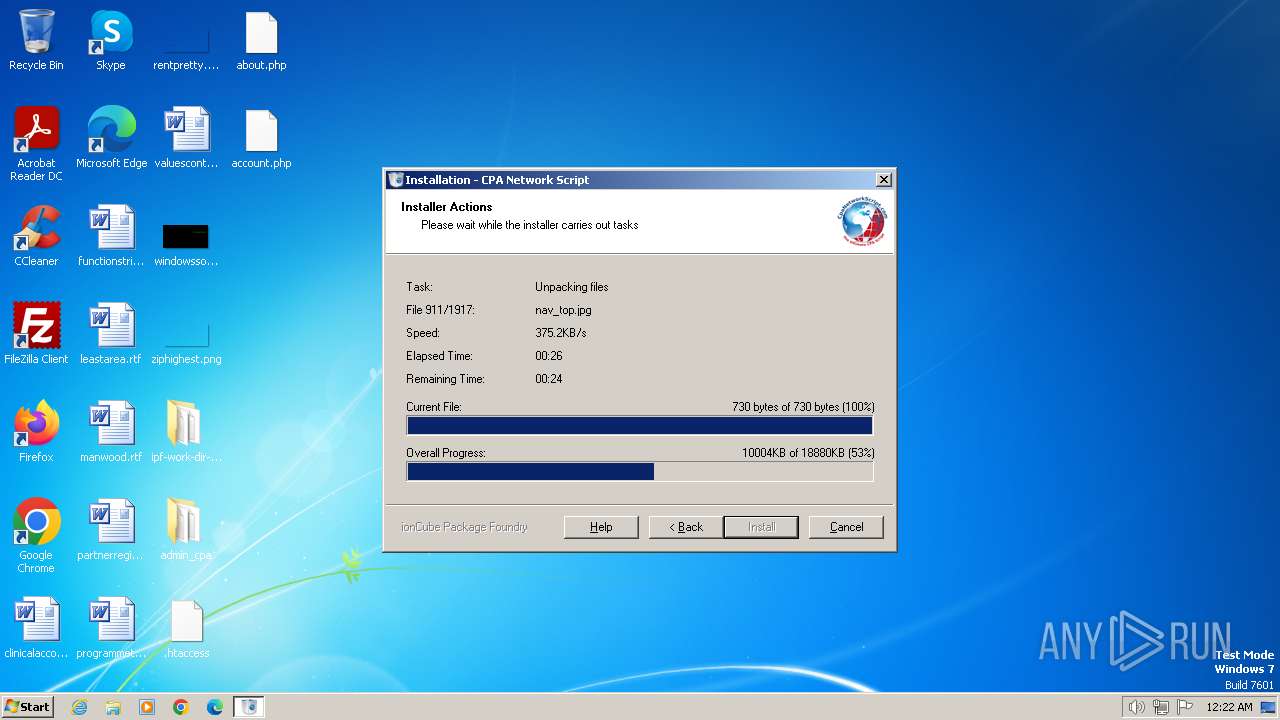
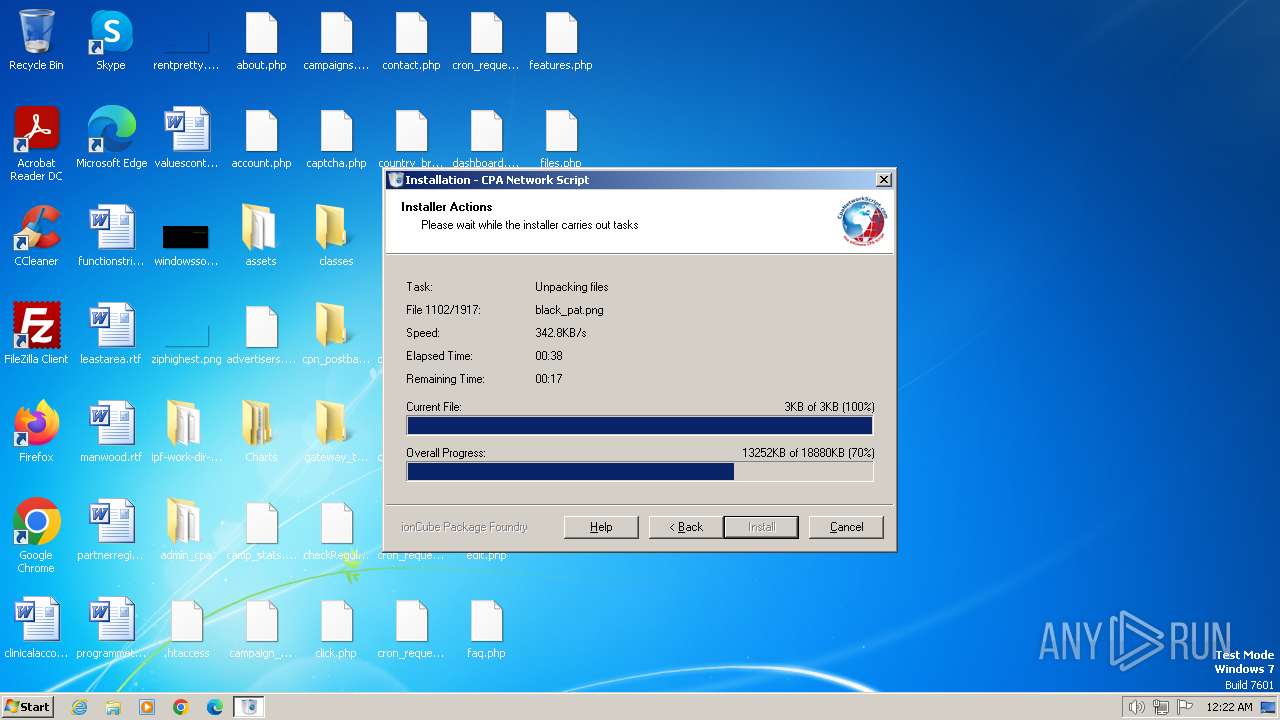
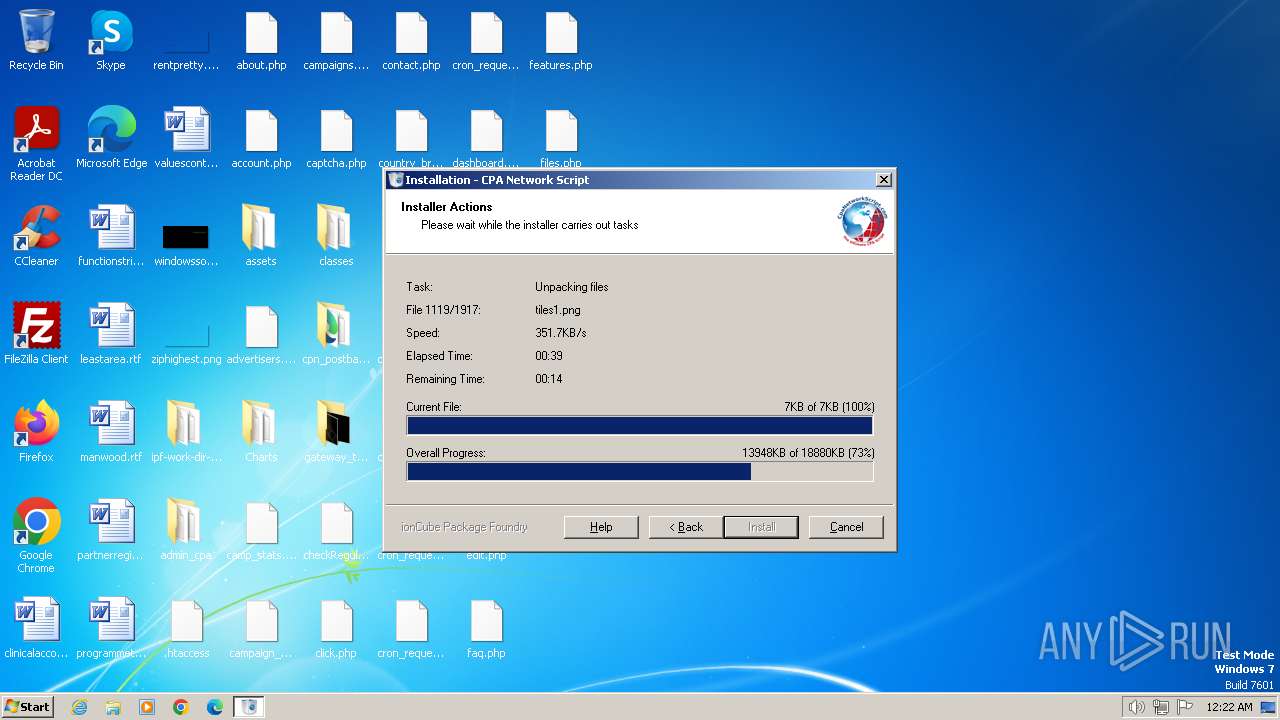
| Analysis date: | January 15, 2024, 00:21:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1270BE833448F35F8AAC2C32F13884A9 |
| SHA1: | 3452AB48BDFA5E4DB480B2BB3D23F3C89F2665D6 |
| SHA256: | 3B8D62FCA3CECFD4C1C4008AF467A7CD4F54B1819425280D5213FE1D7424CD80 |
| SSDEEP: | 98304:ncgx/yPMDn+mdLjzArvW5Os5ksroxIKgBJhiAjNPcnFlpYYY16PYEVorlxVdZteE:24h9Y9IoA02hDf9 |
MALICIOUS
Drops the executable file immediately after the start
- Install-Script.exe (PID: 2024)
- setup.exe (PID: 532)
SUSPICIOUS
Executable content was dropped or overwritten
- setup.exe (PID: 532)
- Install-Script.exe (PID: 2024)
Reads the Internet Settings
- Install-Script.exe (PID: 2024)
INFO
Checks supported languages
- Install-Script.exe (PID: 2024)
- setup.exe (PID: 532)
Create files in a temporary directory
- setup.exe (PID: 532)
- Install-Script.exe (PID: 2024)
Reads the computer name
- Install-Script.exe (PID: 2024)
- setup.exe (PID: 532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2006:10:13 22:04:39+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 16384 |
| InitializedDataSize: | 45056 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x40fa |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.20.0.0 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
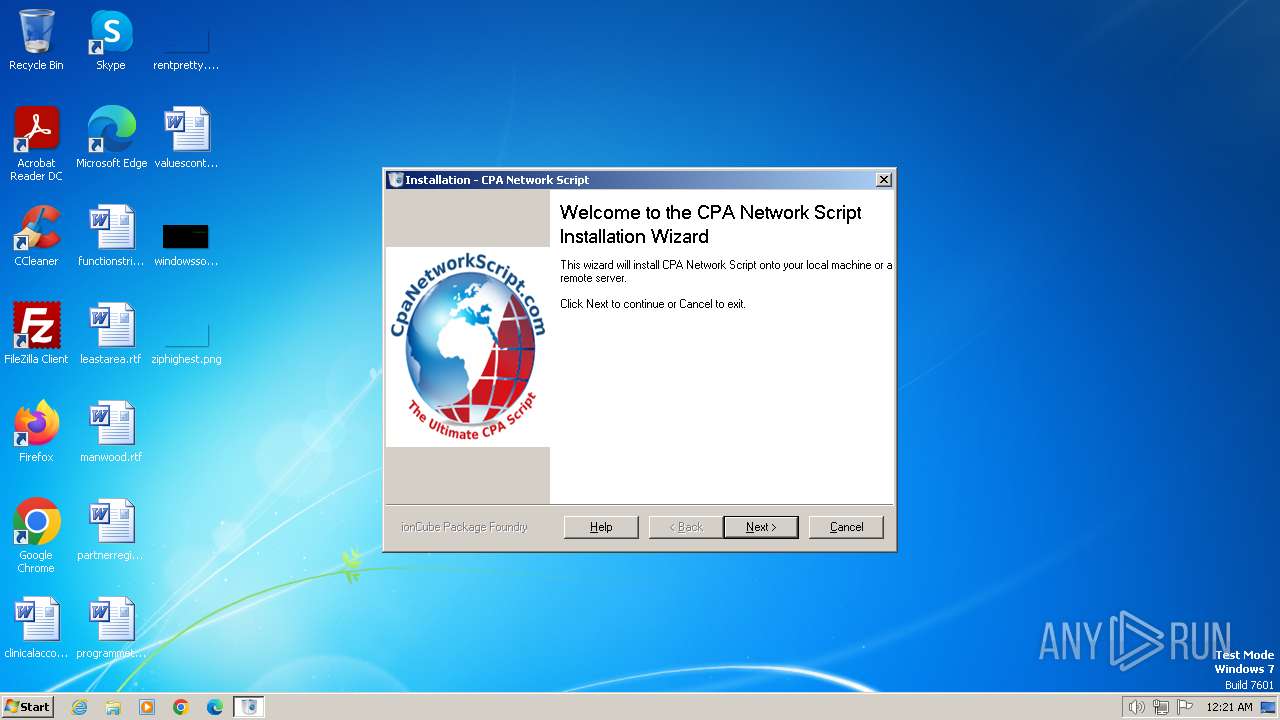
| FileDescription: | Package Foundry created Installer |
| FileVersion: | 1.2 |
| InternalName: | SETUP |
| LegalCopyright: | AMC Inc 2015-2016 |
| LegalTrademarks: | - |
| OriginalFileName: | setup.exe |
| PrivateBuild: | - |
| ProductName: | CpaNetworkScript |
| ProductVersion: | 1.2 |
| SpecialBuild: | - |
Total processes
41
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
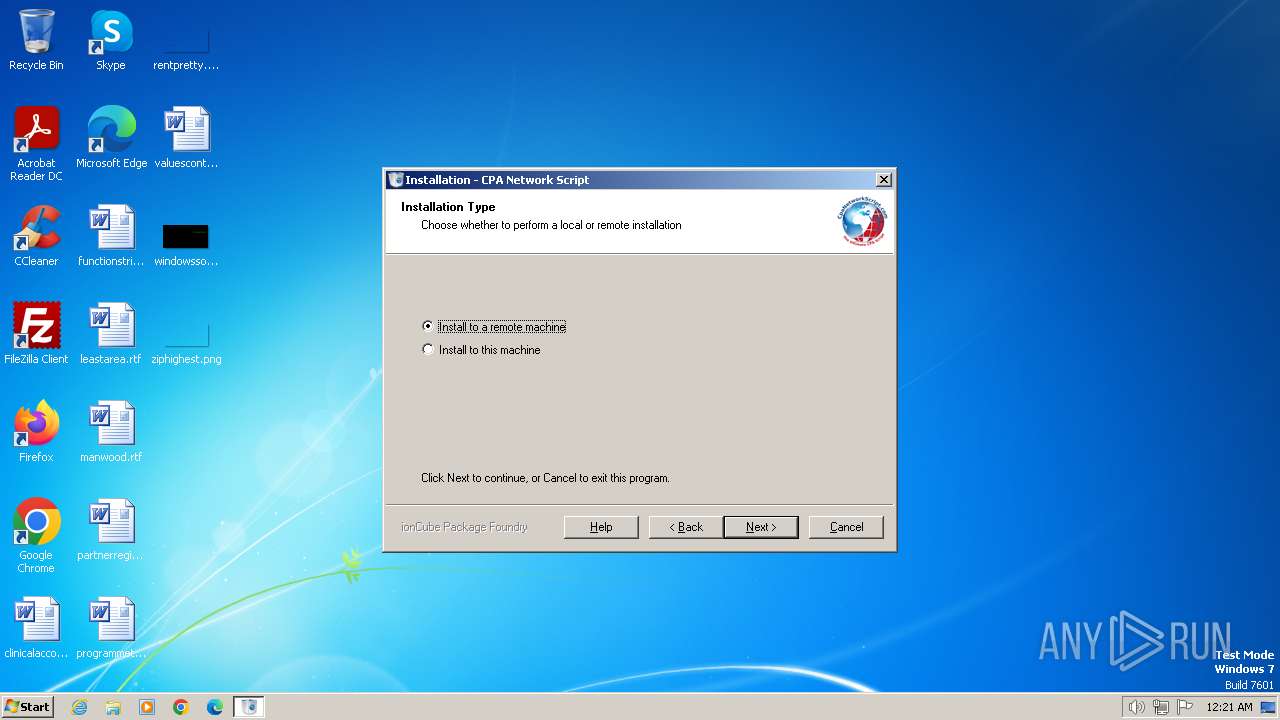
| 532 | "C:\Users\admin\AppData\Local\Temp\ioncube_setup_2024\setup.exe" "C:\Users\admin\AppData\Local\Temp\Install-Script.exe" "3.0" "6" | C:\Users\admin\AppData\Local\Temp\ioncube_setup_2024\setup.exe | Install-Script.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Package Foundry created Installer Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1776 | "C:\Users\admin\AppData\Local\Temp\Install-Script.exe" | C:\Users\admin\AppData\Local\Temp\Install-Script.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2024 | "C:\Users\admin\AppData\Local\Temp\Install-Script.exe" | C:\Users\admin\AppData\Local\Temp\Install-Script.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 747
Read events
1 729
Write events
18
Delete events
0
Modification events
| (PID) Process: | (2024) Install-Script.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2024) Install-Script.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2024) Install-Script.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2024) Install-Script.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (532) setup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
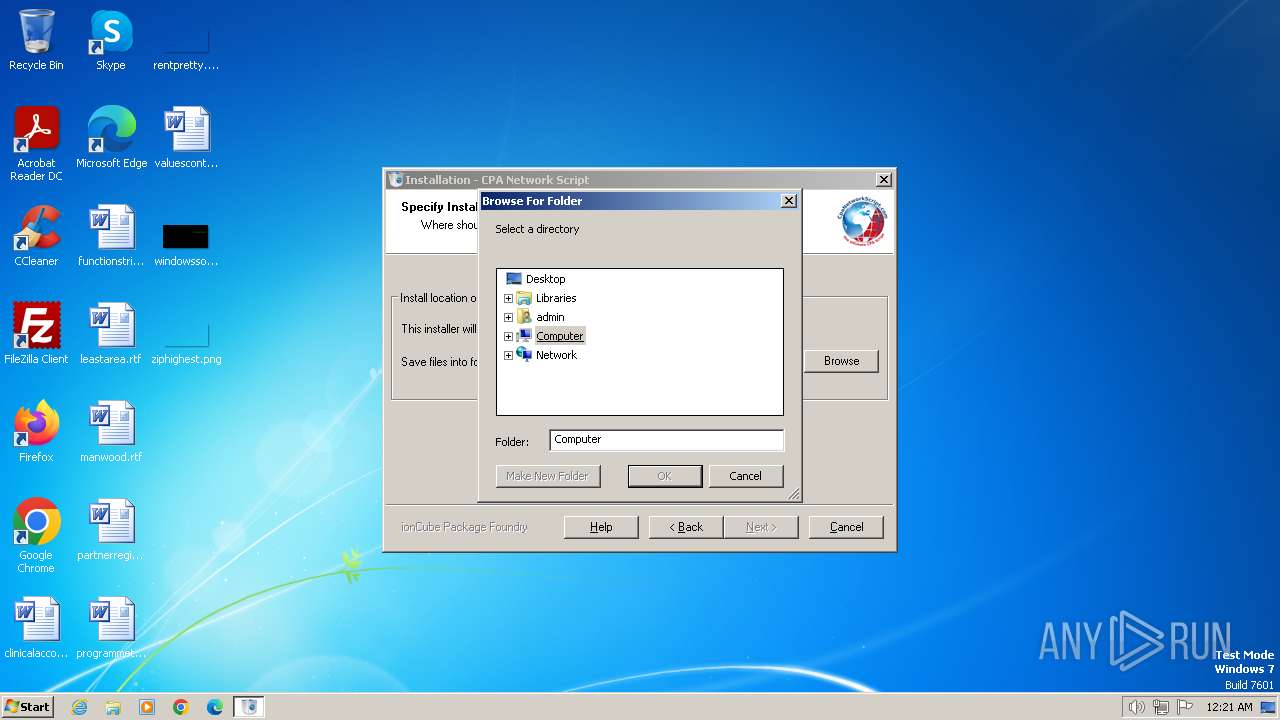
| (PID) Process: | (532) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Width |
Value: 318 | |||
| (PID) Process: | (532) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Height |
Value: 288 | |||
Executable files
3
Suspicious files
42
Text files
1 126
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 532 | setup.exe | C:\Users\admin\Desktop\.htaccess | text | |
MD5:BBD12A0B277068F20CC4E3957DFFEFAF | SHA256:7288D0A04E973D8057B45A5AB5CFD2F58928C1B900723B7DAC9AA40F71B6162E | |||
| 532 | setup.exe | C:\Users\admin\Desktop\about.php | text | |
MD5:F098D4B22BD9D813A798EE263C2E5BEC | SHA256:B66DBA1F788BB41F2A97A98A2735F66033E25503E67A3245A899D88C1640A9FC | |||
| 532 | setup.exe | C:\Users\admin\Desktop\ipf-work-dir-1705278083\ping.php | text | |
MD5:1BA117E13278ACCDE383467A39DEBA64 | SHA256:C8E4D747641460DE35EF36BC83EC322451C5A369DE733D1C5294FB9AB7832065 | |||
| 532 | setup.exe | C:\Users\admin\Desktop\admin_cpa\admins\add.php | text | |
MD5:F7656D25B79417CC012EEC7D289B82DA | SHA256:23D4ADF376C8AC965E566A990A5234C2B9C918F6CAB76611BDDABB3ADE3BA6FE | |||
| 532 | setup.exe | C:\Users\admin\Desktop\admin_cpa\admins\admins.php | text | |
MD5:742B9AB99DBD7B344EB11A98114402E7 | SHA256:D89787571F90ED6C8D8D1F4EFBFC1AF5321048500F66DBD19578668B5C645F09 | |||
| 532 | setup.exe | C:\Users\admin\Desktop\account.php | text | |
MD5:1C94285BD0B6C36BD772896FFE6641A4 | SHA256:1AA1CE36802A5A273329052820F805F0AD604D69640E3269DA8597D2D96C486C | |||
| 532 | setup.exe | C:\Users\admin\Desktop\admin_cpa\assets\css\demo-files\ecommerce-dashboard-1.css | text | |
MD5:946EDB6DE777CAB47A0045AD026A7A17 | SHA256:D35570EC06FAA63C9B110F11AA8E98E238585D211218F1F753131E3A07D4C098 | |||
| 532 | setup.exe | C:\Users\admin\Desktop\admin_cpa\assets\css\demo-files\ecommerce-order-view.css | text | |
MD5:CE8962DE86E0CEFE5E09FD5E04F33218 | SHA256:4BD1A6E25796815182B7986F9F0E5C39F5D664FD89084C08B58B6EECE91F87DA | |||
| 532 | setup.exe | C:\Users\admin\AppData\Local\Temp\ioncube_setup_2024\locale\fr\LC_MESSAGES\driver.mo | binary | |
MD5:7681575C34F1040A31EDBBE3FA0892FB | SHA256:AD8943583FAB96DC0221DE4B816A0D86DEACBE655D174A8689A6AE75323A2E2E | |||
| 532 | setup.exe | C:\Users\admin\Desktop\admin_cpa\assets\css\demo-files\ecommerce-product-edit.css | text | |
MD5:D318AFE8C99D0880E532C173E0789F6E | SHA256:28179DA2B3FD55F513A2BA1743936C104E006CD9B2226F975F772808BD1CD868 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |