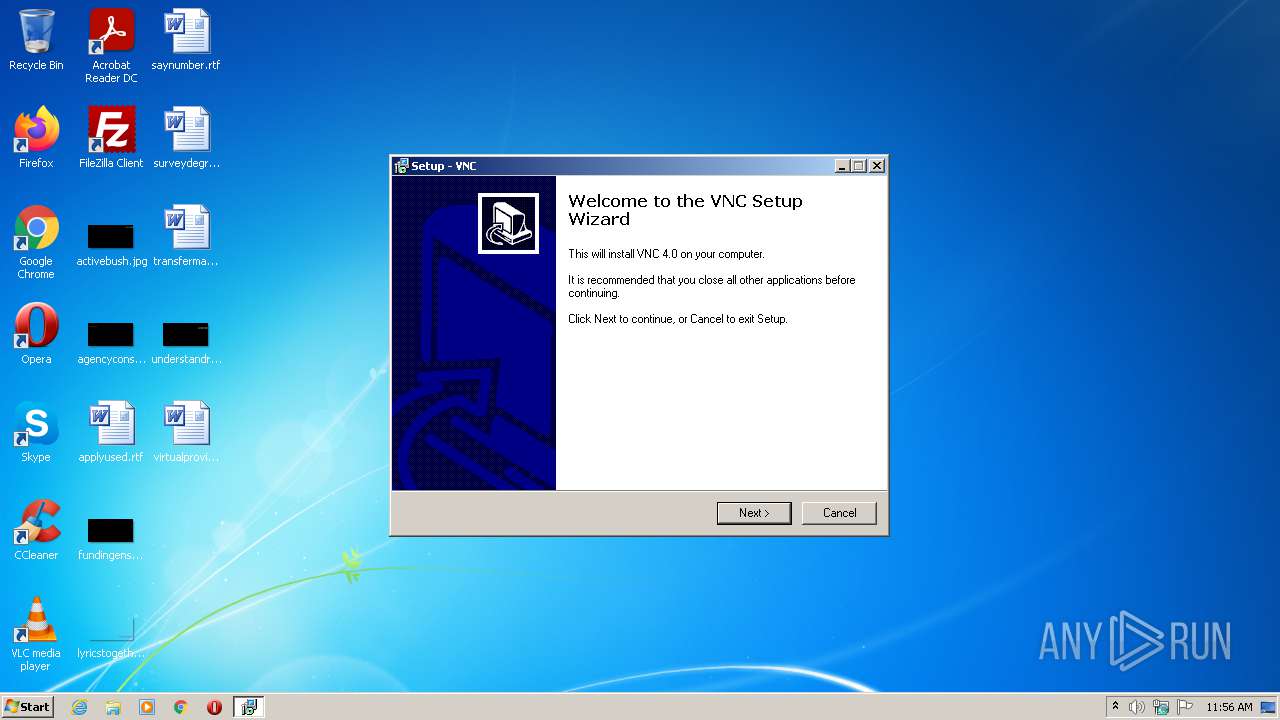
| File name: | vnc-4.0-x86_win32.exe |
| Full analysis: | https://app.any.run/tasks/23213be9-9cff-4e16-afa2-3dac2103dbe2 |
| Verdict: | Malicious activity |
| Analysis date: | July 06, 2021, 10:55:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InnoSetup self-extracting archive |
| MD5: | 98EE2C22C45BBE3F250B73226D357845 |
| SHA1: | 1849E83BD4C85E2B102430B61D4D7368539FB490 |
| SHA256: | 3B8AF9FF8B62B4EE1189280CFAF01D4B6F3529C2E12272BFE7560AABC579B3B6 |
| SSDEEP: | 12288:aXGhddSgXLn30mxaR0g2KnFZKCJMFx38LyiD6uwqp0LAGi3j3TmKt58zhIYYt6st:gUdSg7Nk8CaFxAyiD6FK00jkOZNt |
MALICIOUS
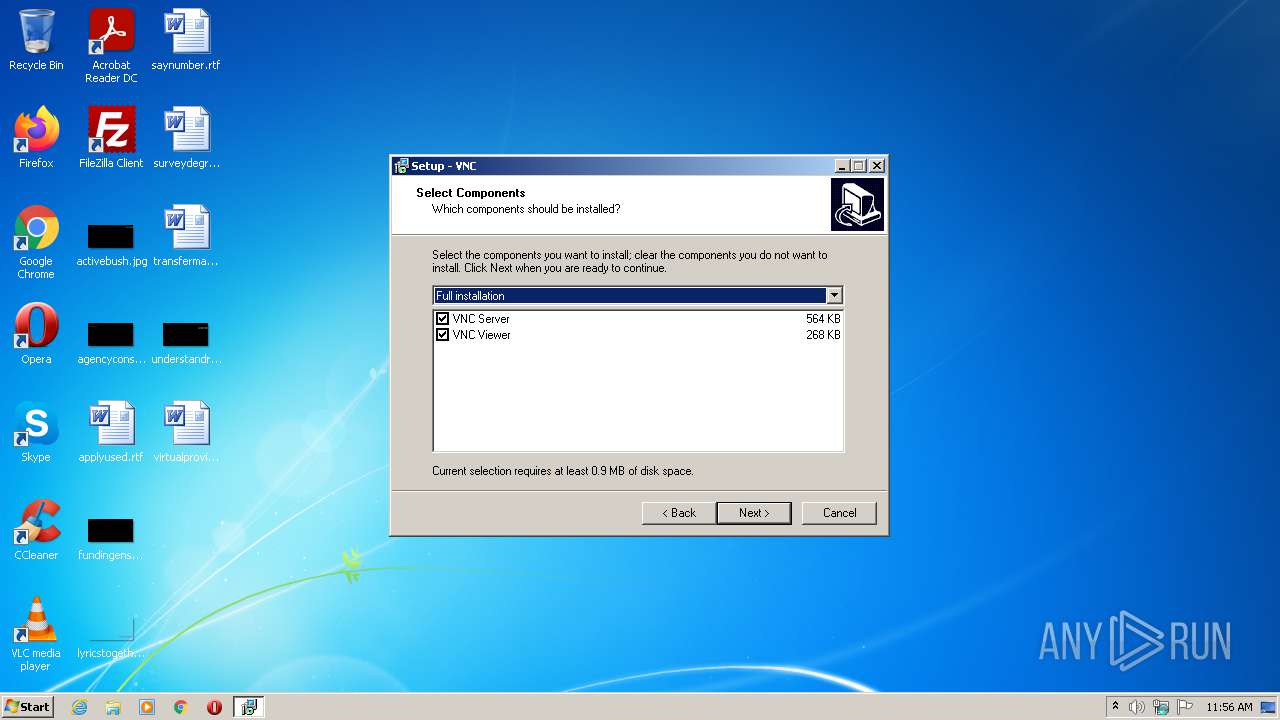
Drops executable file immediately after starts
- vnc-4.0-x86_win32.exe (PID: 1148)
- is-1TAE5.tmp (PID: 696)
Loads dropped or rewritten executable
- WinVNC4.exe (PID: 3696)
- WinVNC4.exe (PID: 2572)
- WinVNC4.exe (PID: 3916)
- WinVNC4.exe (PID: 2944)
- winvnc4.exe (PID: 3604)
Application was dropped or rewritten from another process
- WinVNC4.exe (PID: 3696)
- WinVNC4.exe (PID: 3916)
- WinVNC4.exe (PID: 2572)
- WinVNC4.exe (PID: 2944)
- winvnc4.exe (PID: 3604)
- vncviewer.exe (PID: 1620)
- vncconfig.exe (PID: 1948)
SUSPICIOUS
Checks supported languages
- vnc-4.0-x86_win32.exe (PID: 1148)
- is-1TAE5.tmp (PID: 696)
- WinVNC4.exe (PID: 2572)
- WinVNC4.exe (PID: 3916)
- WinVNC4.exe (PID: 2944)
- WinVNC4.exe (PID: 3696)
- vncviewer.exe (PID: 1620)
- winvnc4.exe (PID: 3604)
- vncconfig.exe (PID: 1948)
Executable content was dropped or overwritten
- vnc-4.0-x86_win32.exe (PID: 1148)
- is-1TAE5.tmp (PID: 696)
Reads the computer name
- is-1TAE5.tmp (PID: 696)
- WinVNC4.exe (PID: 2572)
- WinVNC4.exe (PID: 3916)
- WinVNC4.exe (PID: 3696)
- winvnc4.exe (PID: 3604)
- WinVNC4.exe (PID: 2944)
- vncconfig.exe (PID: 1948)
Reads Windows owner or organization settings
- is-1TAE5.tmp (PID: 696)
Drops a file with too old compile date
- vnc-4.0-x86_win32.exe (PID: 1148)
- is-1TAE5.tmp (PID: 696)
Reads the Windows organization settings
- is-1TAE5.tmp (PID: 696)
Drops a file that was compiled in debug mode
- is-1TAE5.tmp (PID: 696)
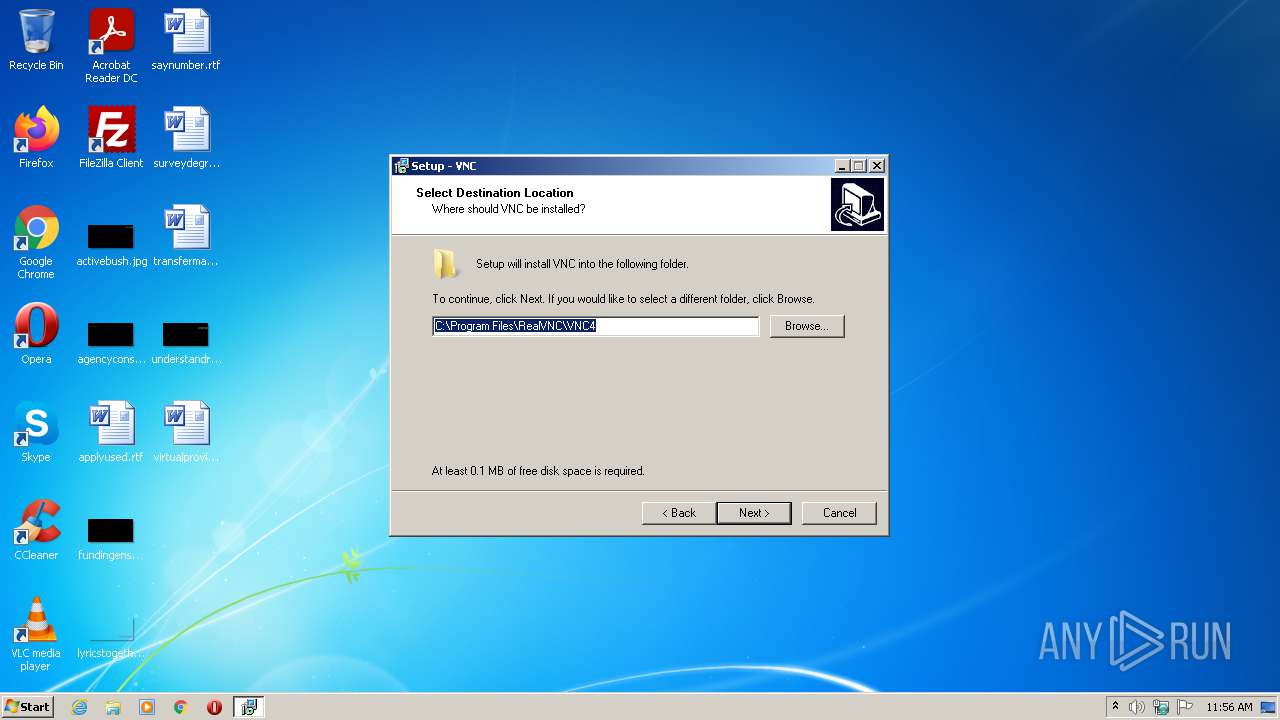
Creates a directory in Program Files
- is-1TAE5.tmp (PID: 696)
Changes default file association
- is-1TAE5.tmp (PID: 696)
Executed as Windows Service
- WinVNC4.exe (PID: 2944)
INFO
Loads dropped or rewritten executable
- is-1TAE5.tmp (PID: 696)
Application was dropped or rewritten from another process
- is-1TAE5.tmp (PID: 696)
Creates files in the program directory
- is-1TAE5.tmp (PID: 696)
Creates a software uninstall entry
- is-1TAE5.tmp (PID: 696)
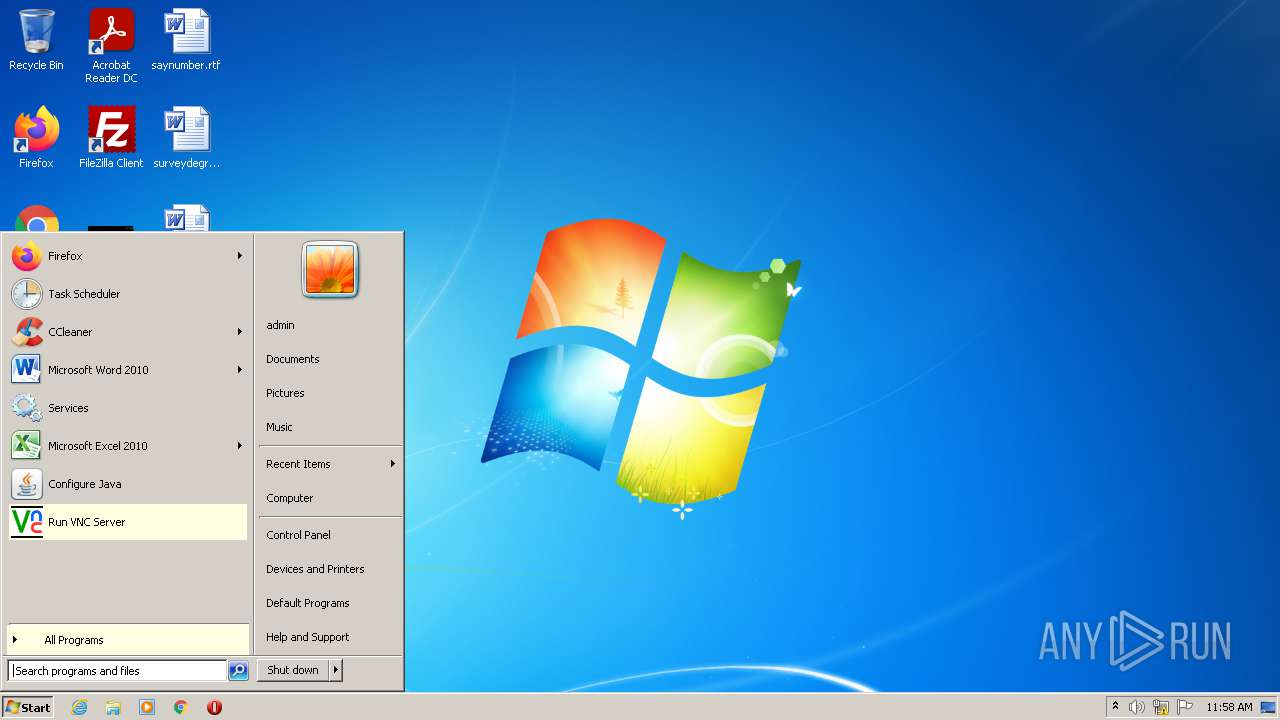
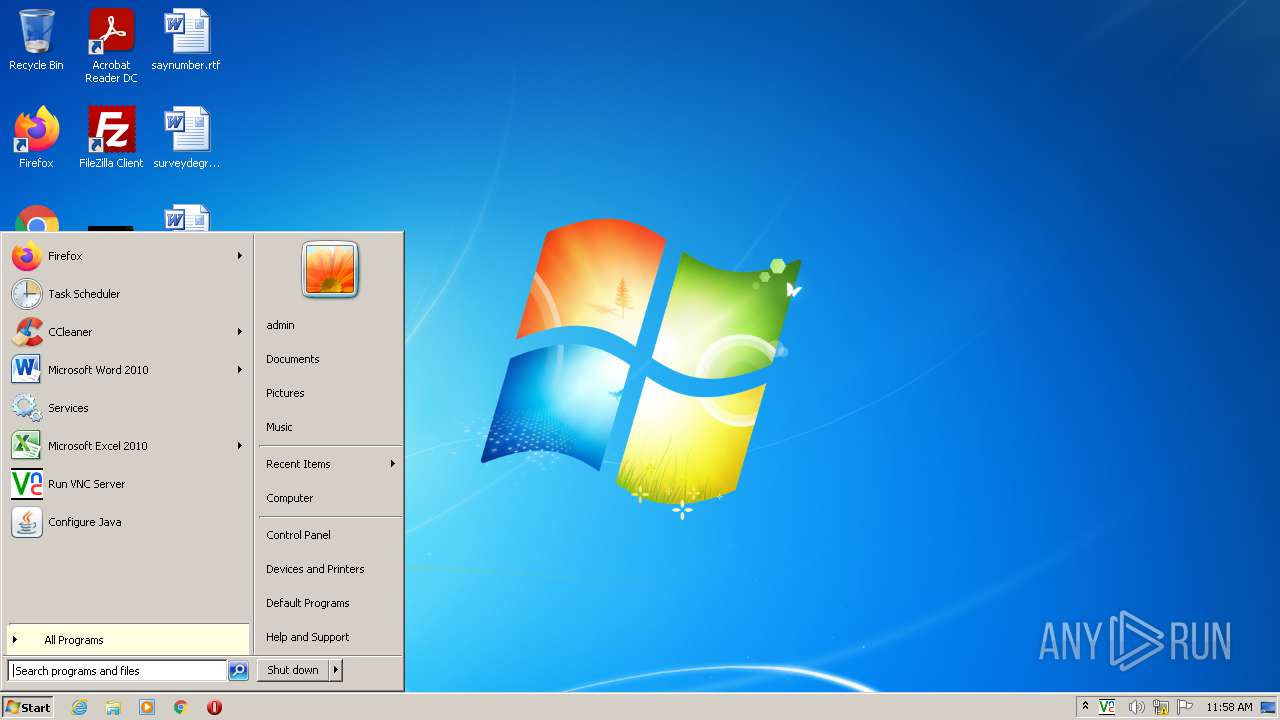
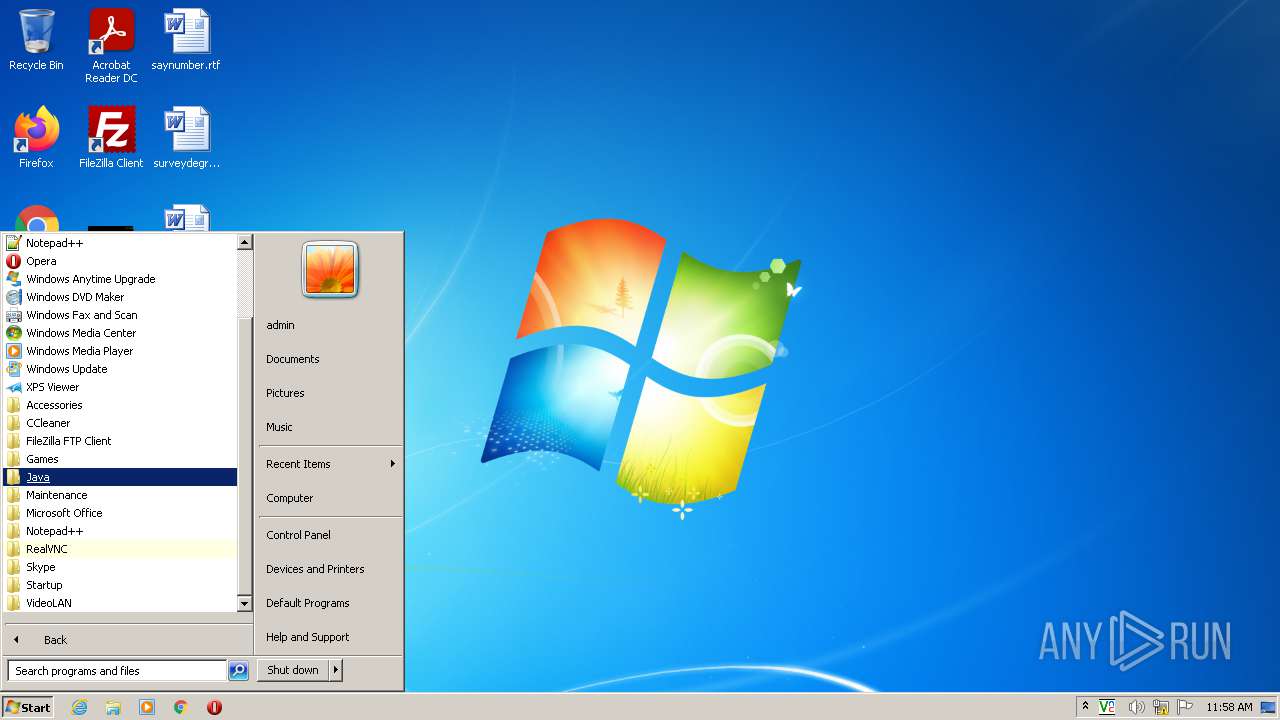
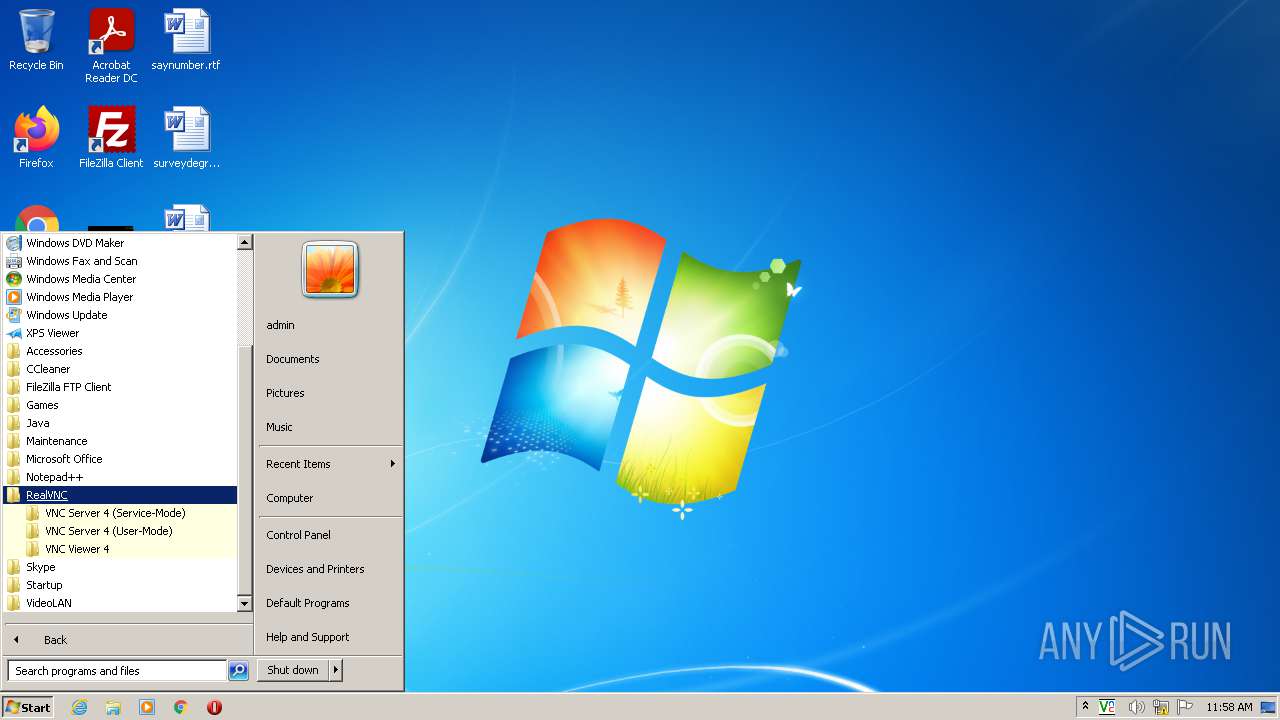
Manual execution by user
- opera.exe (PID: 2664)
- winvnc4.exe (PID: 3604)
- vncviewer.exe (PID: 1620)
Reads the computer name
- opera.exe (PID: 2664)
Checks supported languages
- opera.exe (PID: 2664)
Reads the date of Windows installation
- opera.exe (PID: 2664)
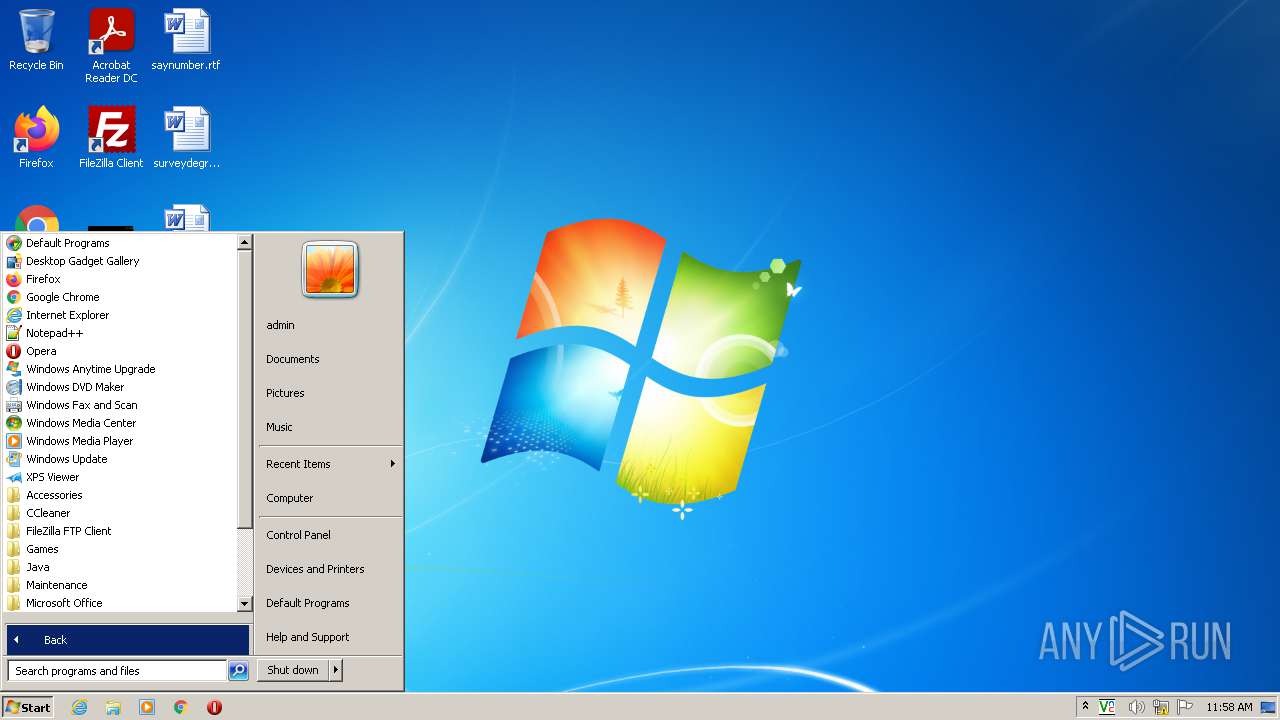
Check for Java to be installed
- opera.exe (PID: 2664)
Creates files in the user directory
- opera.exe (PID: 2664)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 2664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (82.8) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.7) |
| .exe | | | Win32 Executable (generic) (3.4) |
| .exe | | | Generic Win/DOS Executable (1.5) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| ProductVersion: | - |
|---|---|
| ProductName: | - |
| OriginalFileName: | - |
| InternalName: | - |
| FileVersion: | |
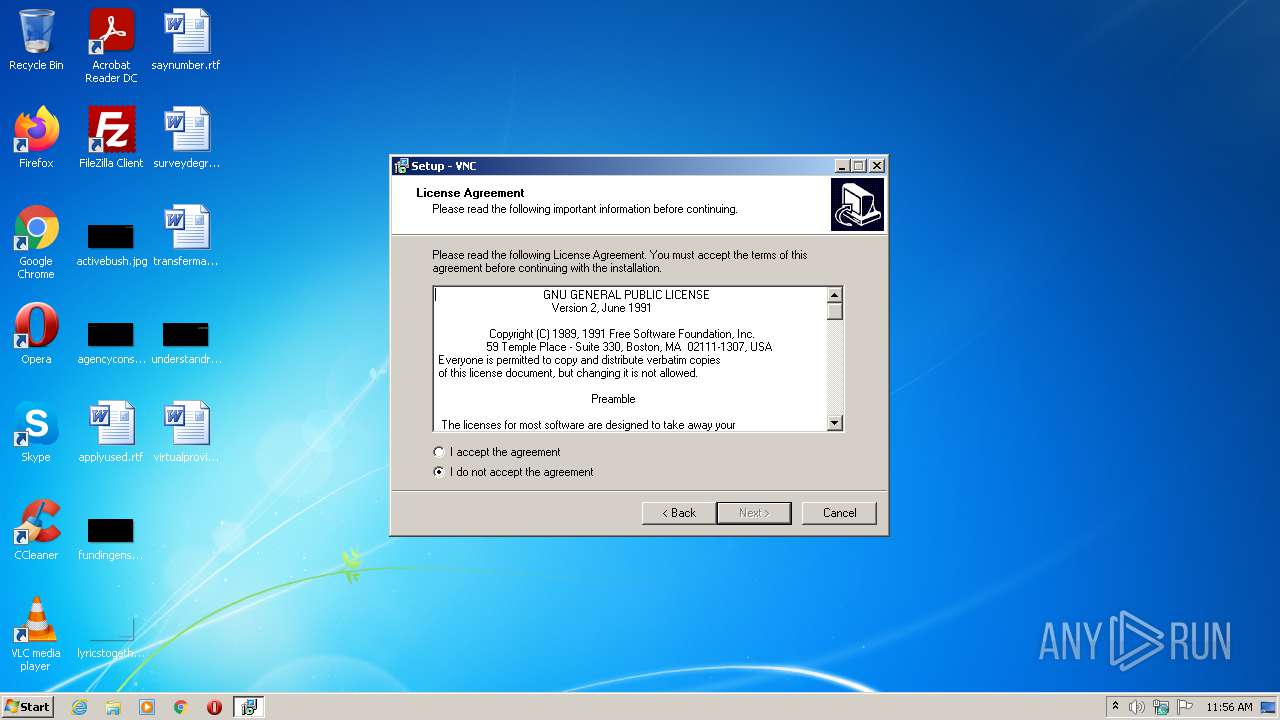
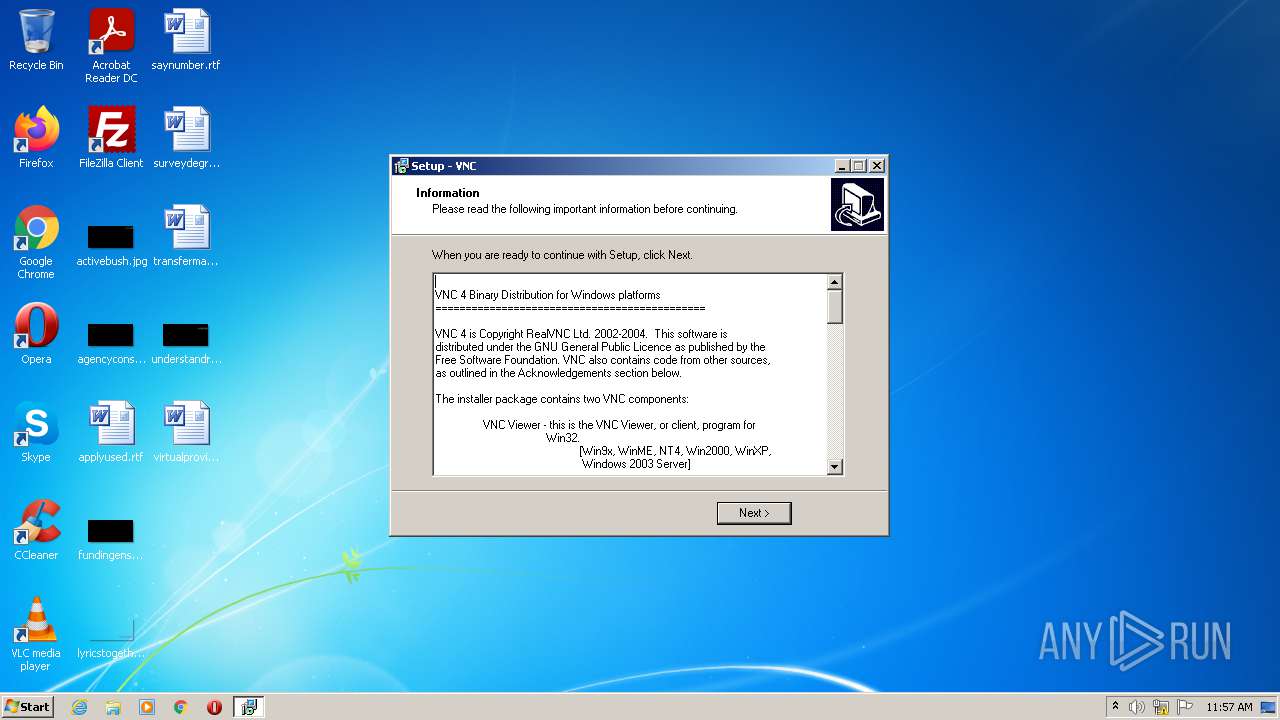
| FileDescription: | VNC Setup |
| CompanyName: | RealVNC Ltd. |
| Comments: | This installation was built with Inno Setup: http://www.innosetup.com |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 0.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 1 |
| EntryPoint: | 0x9220 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 16896 |
| CodeSize: | 35328 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup: http://www.innosetup.com |
| CompanyName: | RealVNC Ltd. |
| FileDescription: | VNC Setup |
| FileVersion: | - |
| InternalName: | - |
| OriginalFilename: | - |
| ProductName: | - |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00008958 | 0x00008A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58183 |
DATA | 0x0000A000 | 0x00000244 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.71786 |
BSS | 0x0000B000 | 0x00000E40 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000C000 | 0x000008A8 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.18925 |
.tls | 0x0000D000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000E000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.199108 |
.reloc | 0x0000F000 | 0x0000084C | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00010000 | 0x00002800 | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.27448 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.86458 | 649 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
51
Monitored processes
11
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 696 | "C:\Users\admin\AppData\Local\Temp\is-K8MRL.tmp\is-1TAE5.tmp" /SL4 $6015A C:\Users\admin\AppData\Local\Temp\vnc-4.0-x86_win32.exe 511279 50688 | C:\Users\admin\AppData\Local\Temp\is-K8MRL.tmp\is-1TAE5.tmp | vnc-4.0-x86_win32.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1148 | "C:\Users\admin\AppData\Local\Temp\vnc-4.0-x86_win32.exe" | C:\Users\admin\AppData\Local\Temp\vnc-4.0-x86_win32.exe | Explorer.EXE | ||||||||||||
User: admin Company: RealVNC Ltd. Integrity Level: HIGH Description: VNC Setup Exit code: 0 Version: Modules
| |||||||||||||||
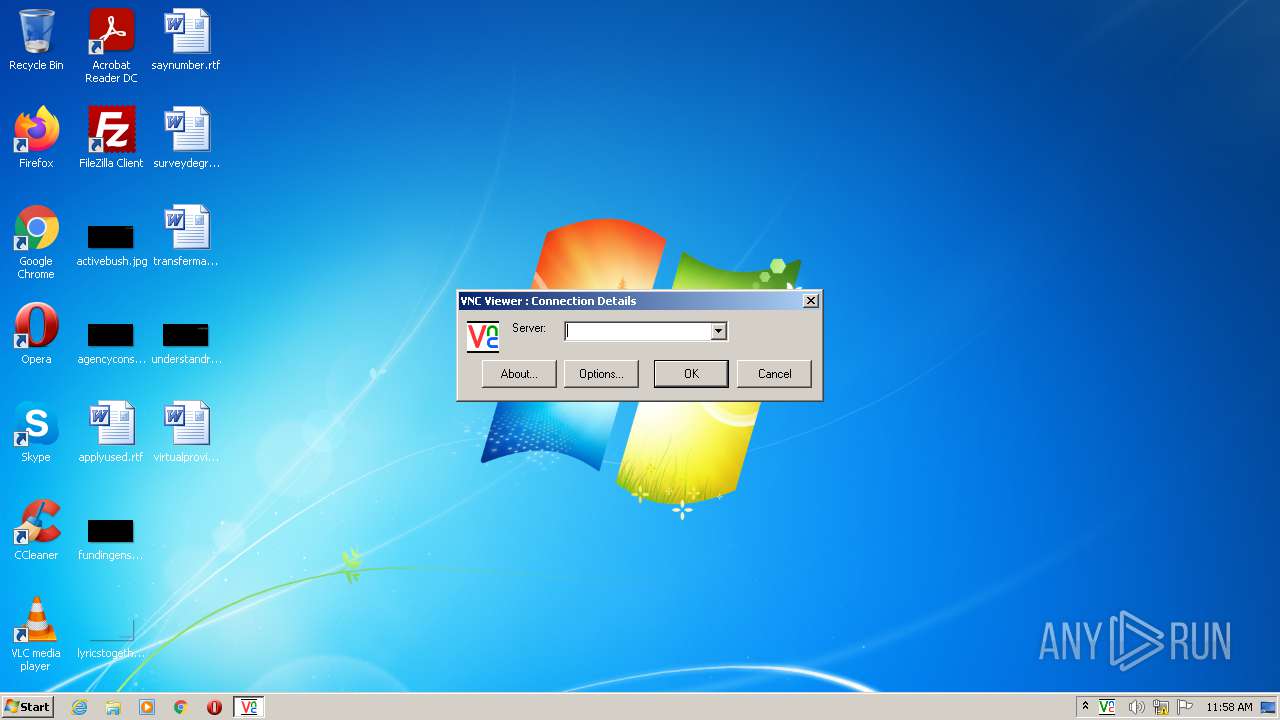
| 1620 | "C:\Program Files\RealVNC\VNC4\vncviewer.exe" | C:\Program Files\RealVNC\VNC4\vncviewer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: RealVNC Ltd. Integrity Level: MEDIUM Description: VNC Viewer for Win32 Exit code: 0 Version: 4.0 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\RealVNC\VNC4\vncconfig.exe" -service | C:\Program Files\RealVNC\VNC4\vncconfig.exe | — | is-1TAE5.tmp | |||||||||||
User: admin Company: RealVNC Ltd. Integrity Level: HIGH Description: VNC Server Configuration Applet for Win32 Exit code: 0 Version: 4.0 Modules
| |||||||||||||||
| 2140 | "C:\Users\admin\AppData\Local\Temp\vnc-4.0-x86_win32.exe" | C:\Users\admin\AppData\Local\Temp\vnc-4.0-x86_win32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: RealVNC Ltd. Integrity Level: MEDIUM Description: VNC Setup Exit code: 3221226540 Version: Modules
| |||||||||||||||
| 2572 | "C:\Program Files\RealVNC\VNC4\WinVNC4.exe" -unregister -register | C:\Program Files\RealVNC\VNC4\WinVNC4.exe | — | is-1TAE5.tmp | |||||||||||
User: admin Company: RealVNC Ltd. Integrity Level: HIGH Description: VNC Server for Win32 Exit code: 0 Version: 4.0 Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | Explorer.EXE | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 2944 | "C:\Program Files\RealVNC\VNC4\WinVNC4.exe" -service | C:\Program Files\RealVNC\VNC4\WinVNC4.exe | — | services.exe | |||||||||||
User: SYSTEM Company: RealVNC Ltd. Integrity Level: SYSTEM Description: VNC Server for Win32 Exit code: 0 Version: 4.0 Modules
| |||||||||||||||
| 3604 | "C:\Program Files\RealVNC\VNC4\winvnc4.exe" -noconsole | C:\Program Files\RealVNC\VNC4\winvnc4.exe | — | Explorer.EXE | |||||||||||
User: admin Company: RealVNC Ltd. Integrity Level: MEDIUM Description: VNC Server for Win32 Exit code: 0 Version: 4.0 Modules
| |||||||||||||||
| 3696 | "C:\Program Files\RealVNC\VNC4\WinVNC4.exe" -stop | C:\Program Files\RealVNC\VNC4\WinVNC4.exe | — | is-1TAE5.tmp | |||||||||||
User: admin Company: RealVNC Ltd. Integrity Level: HIGH Description: VNC Server for Win32 Exit code: 0 Version: 4.0 Modules
| |||||||||||||||
Total events
2 331
Read events
2 243
Write events
88
Delete events
0
Modification events
| (PID) Process: | (696) is-1TAE5.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.vnc |
| Operation: | write | Name: | (default) |
Value: VNC.ConnectionInfo | |||
| (PID) Process: | (696) is-1TAE5.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\VNC.ConnectionInfo |
| Operation: | write | Name: | (default) |
Value: VNC Connection Info | |||
| (PID) Process: | (696) is-1TAE5.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\VNC.ConnectionInfo\DefaultIcon |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\RealVNC\VNC4\vncviewer.exe,0 | |||
| (PID) Process: | (696) is-1TAE5.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\VNC.ConnectionInfo\shell\open\command |
| Operation: | write | Name: | (default) |
Value: "C:\Program Files\RealVNC\VNC4\vncviewer.exe" -config "%1" | |||
| (PID) Process: | (696) is-1TAE5.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RealVNC_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 4.2.2 | |||
| (PID) Process: | (696) is-1TAE5.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RealVNC_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\RealVNC\VNC4 | |||
| (PID) Process: | (696) is-1TAE5.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RealVNC_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: RealVNC | |||
| (PID) Process: | (696) is-1TAE5.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RealVNC_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (696) is-1TAE5.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RealVNC_is1 |
| Operation: | write | Name: | Inno Setup: Setup Type |
Value: full | |||
| (PID) Process: | (696) is-1TAE5.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RealVNC_is1 |
| Operation: | write | Name: | Inno Setup: Selected Components |
Value: winvnc,vncviewer | |||
Executable files
15
Suspicious files
23
Text files
15
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 696 | is-1TAE5.tmp | C:\Users\admin\AppData\Local\Temp\is-2J2V8.tmp\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 696 | is-1TAE5.tmp | C:\Program Files\RealVNC\VNC4\unins000.exe | executable | |
MD5:A73B4C19A233181CD4CF0B9B8B3F7FBF | SHA256:B2C14524F74DE7831B3246313485E4DEBECBD235647791A025653720BEF850B6 | |||
| 1148 | vnc-4.0-x86_win32.exe | C:\Users\admin\AppData\Local\Temp\is-K8MRL.tmp\is-1TAE5.tmp | executable | |
MD5:ADA0596F481E037AB4EB86FCB10E827E | SHA256:CF66BEE55697B7BAB60BDF17898AF35528887EBC916A12C3510189629BF17967 | |||
| 696 | is-1TAE5.tmp | C:\Program Files\RealVNC\VNC4\winvnc4.exe | executable | |
MD5:7043DDF51D7135C1D1B83B4213DFED61 | SHA256:B00D8EA00CB9C6CEF087E574795FE2E309BD8EF61F21BF7E6F6595D3F3707315 | |||
| 696 | is-1TAE5.tmp | C:\Program Files\RealVNC\VNC4\vncconfig.exe | executable | |
MD5:4A84D7C950986D3AE898143451EFAE29 | SHA256:B82FD264F28D6EEB49CDE267866E0E153E364128DA228FF8E8B0BBF22289B626 | |||
| 696 | is-1TAE5.tmp | C:\Program Files\RealVNC\VNC4\is-9UDBS.tmp | executable | |
MD5:7043DDF51D7135C1D1B83B4213DFED61 | SHA256:B00D8EA00CB9C6CEF087E574795FE2E309BD8EF61F21BF7E6F6595D3F3707315 | |||
| 696 | is-1TAE5.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\RealVNC\VNC Server 4 (Service-Mode)\Start VNC Service.lnk | lnk | |
MD5:— | SHA256:— | |||
| 696 | is-1TAE5.tmp | C:\Program Files\RealVNC\VNC4\is-82HUK.tmp | executable | |
MD5:7D042213EC10B666923C72DA24EE4B9E | SHA256:9E1E76C0EBD31BECCE60F214CC1034314FB374B6CB011E919F33F58970DFB816 | |||
| 696 | is-1TAE5.tmp | C:\Program Files\RealVNC\VNC4\is-KKP69.tmp | executable | |
MD5:4A84D7C950986D3AE898143451EFAE29 | SHA256:B82FD264F28D6EEB49CDE267866E0E153E364128DA228FF8E8B0BBF22289B626 | |||
| 696 | is-1TAE5.tmp | C:\Program Files\RealVNC\VNC4\logmessages.dll | executable | |
MD5:A78CD9EECB276ADC9D43074E4362F903 | SHA256:03A0F133151C604C7B73DE1875B1A002BF45B71E0EFDE9C3BF22C197D0263A5F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2664 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2664 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
2664 | opera.exe | 93.184.220.29:80 | crl3.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |