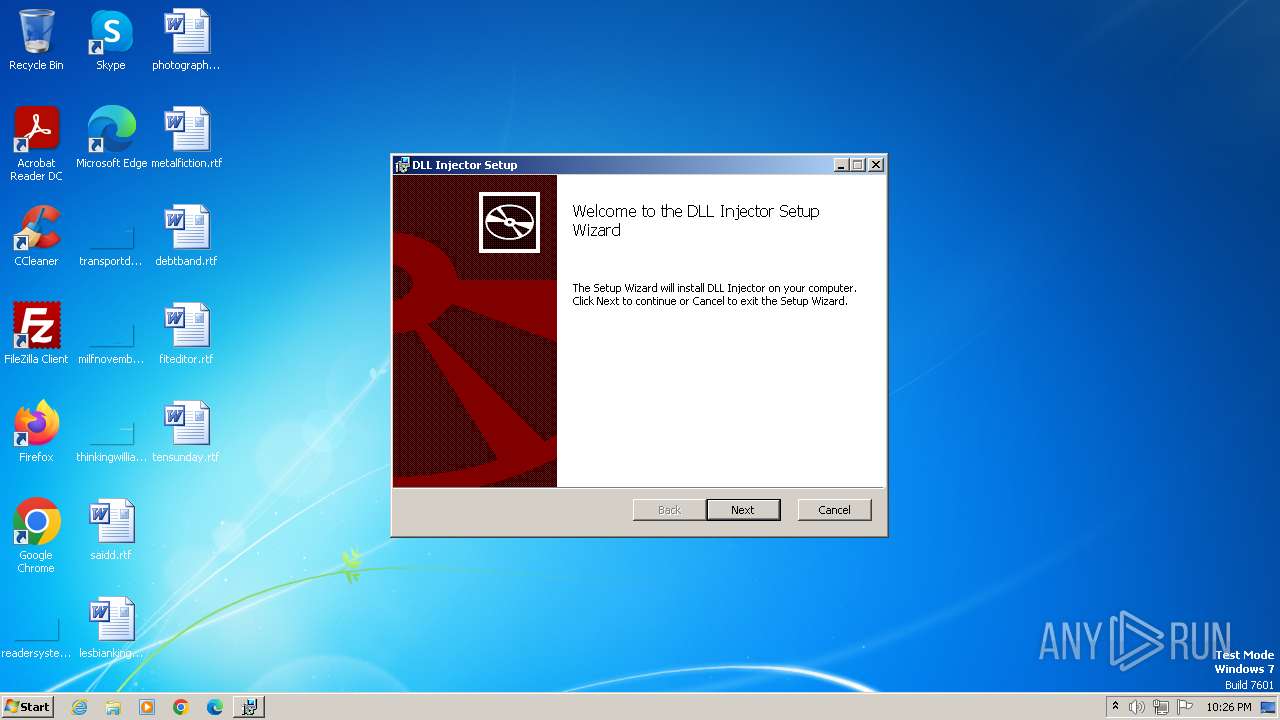
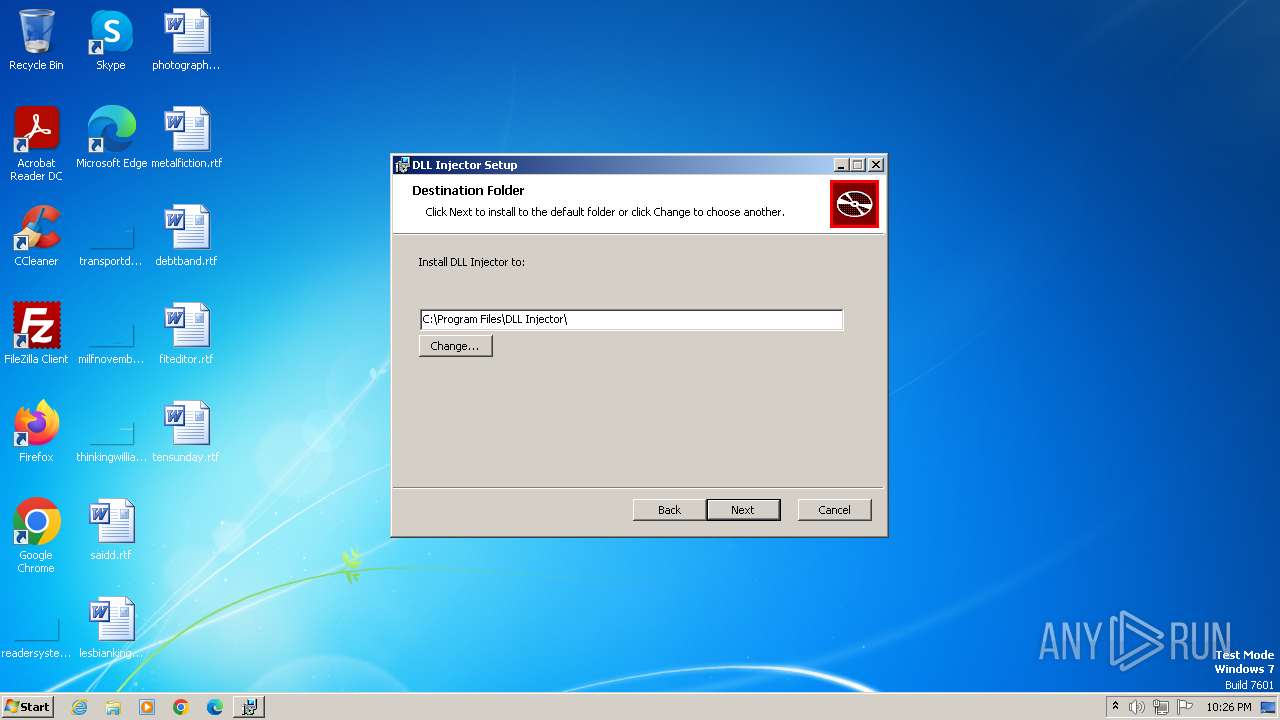
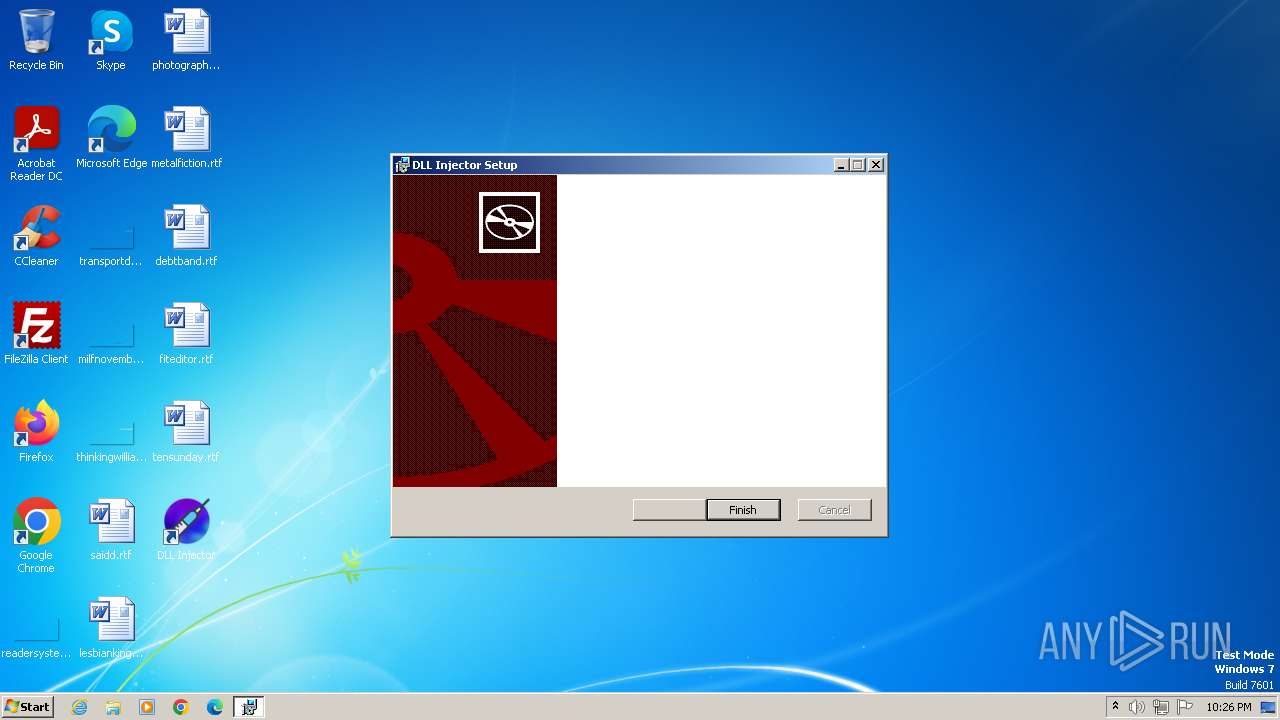
| File name: | DLL Injector_2.1.0_x86_en-US.msi |
| Full analysis: | https://app.any.run/tasks/40e5b77b-ea0f-414d-8458-6aeb269357b1 |
| Verdict: | Malicious activity |
| Analysis date: | October 08, 2023, 21:26:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: DLL Injector, Author: dllinjector, Keywords: Installer, Comments: This installer database contains the logic and data required to install DLL Injector., Template: Intel;0, Revision Number: {E548A4FB-865F-44C0-B2B9-28DA9B180D1F}, Create Time/Date: Tue Mar 14 20:31:28 2023, Last Saved Time/Date: Tue Mar 14 20:31:28 2023, Number of Pages: 450, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.11.2.4516), Security: 2 |
| MD5: | 0592CA25CF22E8D5DAABACD1130D38F6 |
| SHA1: | 0A59FD8723DE4CB9BF6C3272A5DB7771E575EFF9 |
| SHA256: | 3B8991F1EEBFC46988DB25FE0DED11C3C08DF81AE2CA1BAF9103BA8259CAFC99 |
| SSDEEP: | 49152:TXt8FXtmZR9m+/YXz573yI2FvlfC+fM//uuEUNLTVx+pv/Z1BWCMnT5ldQqnUIwJ:T98FXinYXz5ryI2FvvM/mu/NLT41BWdG |
MALICIOUS
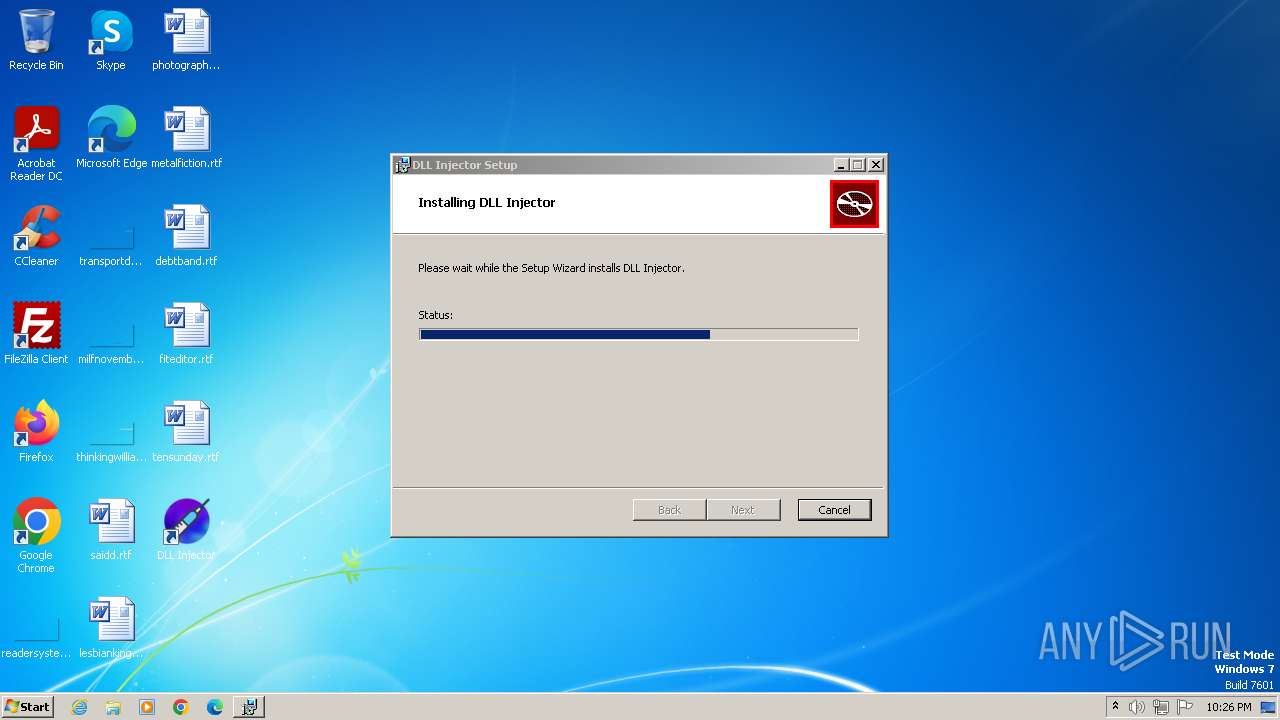
Drops the executable file immediately after the start
- msiexec.exe (PID: 3364)
Run PowerShell with an invisible window
- powershell.exe (PID: 3872)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 3288)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 3364)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 3364)
Powershell scripting: start process
- msiexec.exe (PID: 3364)
Request a resource from the Internet using PowerShell's cmdlet
- msiexec.exe (PID: 3364)
Powershell version downgrade attack
- powershell.exe (PID: 3872)
INFO
Checks supported languages
- msiexec.exe (PID: 4012)
- msiexec.exe (PID: 3364)
Reads the machine GUID from the registry
- msiexec.exe (PID: 3364)
- msiexec.exe (PID: 4012)
Reads the computer name
- msiexec.exe (PID: 3364)
- msiexec.exe (PID: 4012)
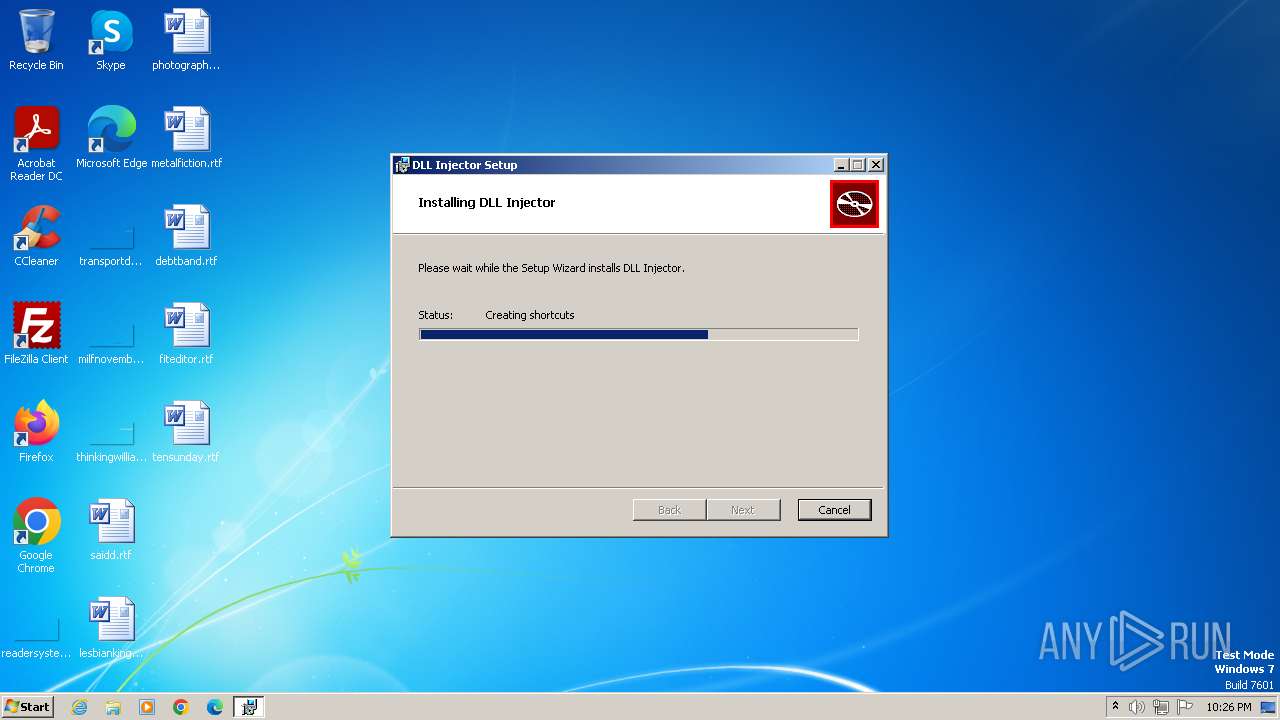
Create files in a temporary directory
- msiexec.exe (PID: 3364)
- msiexec.exe (PID: 3632)
Application launched itself
- msiexec.exe (PID: 3364)
Drops the executable file immediately after the start
- msiexec.exe (PID: 3632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | DLL Injector |
| Author: | dllinjector |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install DLL Injector. |
| Template: | Intel;0 |
| RevisionNumber: | {E548A4FB-865F-44C0-B2B9-28DA9B180D1F} |
| CreateDate: | 2023:03:14 20:31:28 |
| ModifyDate: | 2023:03:14 20:31:28 |
| Pages: | 450 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.11.2.4516) |
| Security: | Read-only recommended |
Total processes
42
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3288 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3364 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3632 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\DLL Injector_2.1.0_x86_en-US.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1603 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3872 | powershell.exe -NoProfile -windowstyle hidden try { [Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12 } catch {}; Invoke-WebRequest -Uri "https://go.microsoft.com/fwlink/p/?LinkId=2124703" -OutFile "$env:TEMP\MicrosoftEdgeWebview2Setup.exe" ; Start-Process -FilePath "$env:TEMP\MicrosoftEdgeWebview2Setup.exe" -ArgumentList ('/silent', '/install') -Wait | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4012 | C:\Windows\system32\MsiExec.exe -Embedding CF2E8E6EAD51D9AD0FC029DC24E900DE C | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 692
Read events
4 524
Write events
70
Delete events
98
Modification events
| (PID) Process: | (3364) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000F2B487BA16B0D901C80700002C0A0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3364) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000F2B487BA16B0D901C80700002C0A0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3364) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 72 | |||
| (PID) Process: | (3364) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000008C62D6BA16B0D901C80700002C0A0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3364) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Leave) |
Value: 400000000000000064514ABC16B0D901C80700002C0A0000D3070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3364) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppAddInterestingComponents (Enter) |
Value: 400000000000000064514ABC16B0D901C80700002C0A0000D4070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3364) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppAddInterestingComponents (Leave) |
Value: 400000000000000034645DBC16B0D901C80700002C0A0000D4070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3364) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Leave) |
Value: 4000000000000000781D5ABD16B0D901C80700002C0A0000D0070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3364) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Leave) |
Value: 4000000000000000781D5ABD16B0D901C80700002C0A0000D5070000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3364) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SystemRestore |
| Operation: | write | Name: | FirstRun |
Value: 0 | |||
Executable files
5
Suspicious files
19
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3364 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3364 | msiexec.exe | C:\Windows\Installer\154a41.msi | executable | |
MD5:0592CA25CF22E8D5DAABACD1130D38F6 | SHA256:3B8991F1EEBFC46988DB25FE0DED11C3C08DF81AE2CA1BAF9103BA8259CAFC99 | |||
| 3364 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:5F21A877FF1962FA06A1FF38DB132371 | SHA256:23BBAC05F66D915AB424D8D1017C04493BAC4D981FB0751E24C381F1D361C619 | |||
| 3364 | msiexec.exe | C:\Program Files\DLL Injector\resources\db.json | binary | |
MD5:A40C7716154F37886DDD4C622F6C77BC | SHA256:5AD42E7977EF8EC640B037A9D22C992CBA1D96C9FF4F81DA057574CC6E82049D | |||
| 3364 | msiexec.exe | C:\Program Files\DLL Injector\DLL Injector.exe | executable | |
MD5:C6EAEAE3CAB85586271AA8E94A1D3DE8 | SHA256:C91C71046F15CC7F5DC4BB4E1E14B5A7A3329EA95954A245C47E181C808A70D2 | |||
| 3364 | msiexec.exe | C:\Windows\Installer\154a42.ipi | binary | |
MD5:F398F75DD9CF475B03190A781C32F51C | SHA256:3B1BC8EBC74A86684E852BBEA8A12A9D616A3CB9E94FE978558C94709EEABD69 | |||
| 3364 | msiexec.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\DLL Injector\DLL Injector.lnk | binary | |
MD5:4F56DDF921D5A242059728E79499C165 | SHA256:7ED67B8EC001BC2BBADCDAC5C125A822DF3F220BF85AAF08B67985359ADC4708 | |||
| 3364 | msiexec.exe | C:\Users\Public\Desktop\DLL Injector.lnk | binary | |
MD5:0D6317E79854417CAC69BDCA3EF86EC7 | SHA256:B5AC9A0AD471C54034B31D811B53F496C95584F96EB87F1236F0B8790226F0D8 | |||
| 3364 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF2009765F07859E2F.TMP | binary | |
MD5:1665706C758457B4D3B339E608890CCE | SHA256:0D243C6ED69AEF2D840BB2FC359517BB571A4C19D60FD34F86790A620D1EA364 | |||
| 3364 | msiexec.exe | C:\Program Files\DLL Injector\resources\x64_DLL_Injector.exe | executable | |
MD5:E69DFA19D697E916F6AFAB3089E109D4 | SHA256:02DFCC045FC842D1086DE42EDC1F0536A8F942920A20EF9F5D72E68004469605 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |