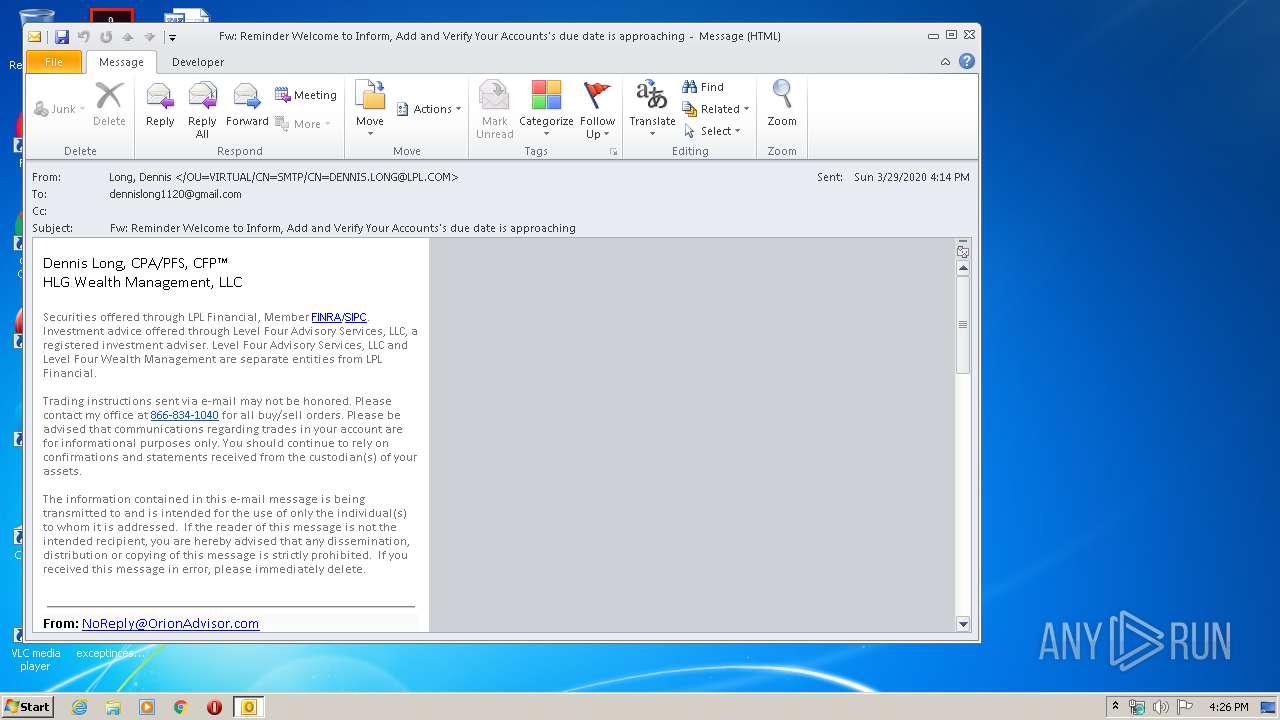
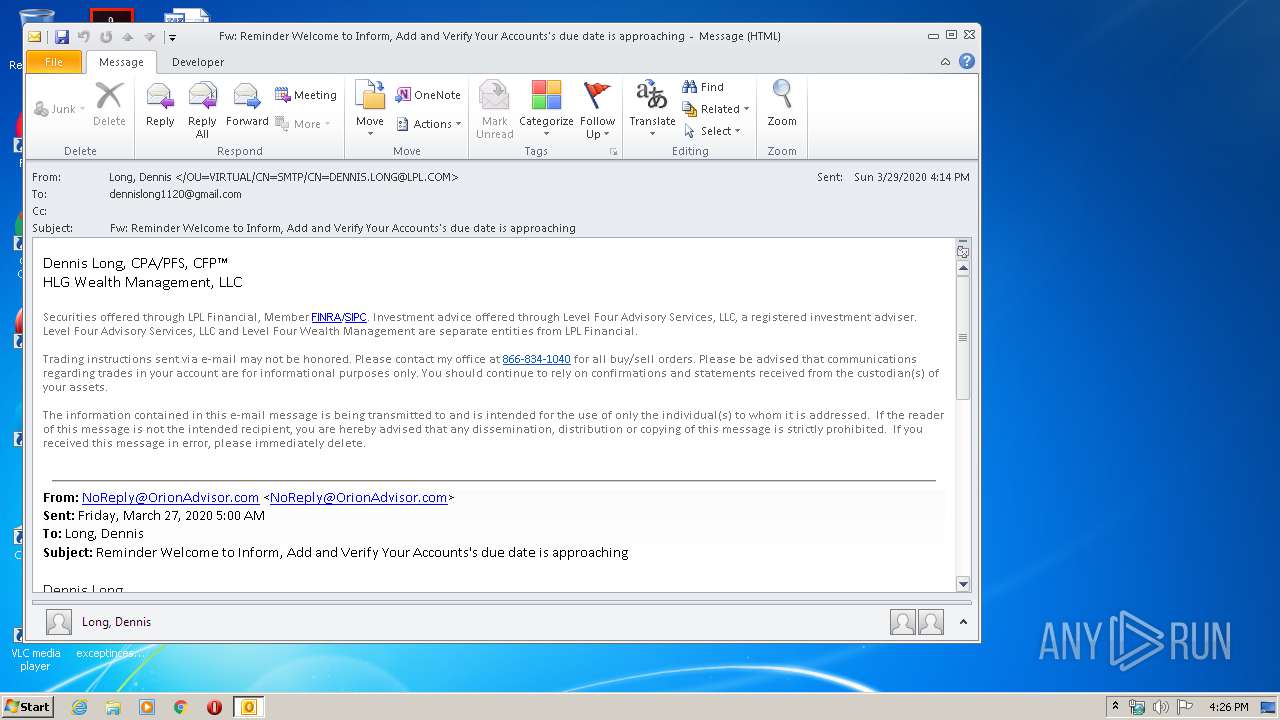
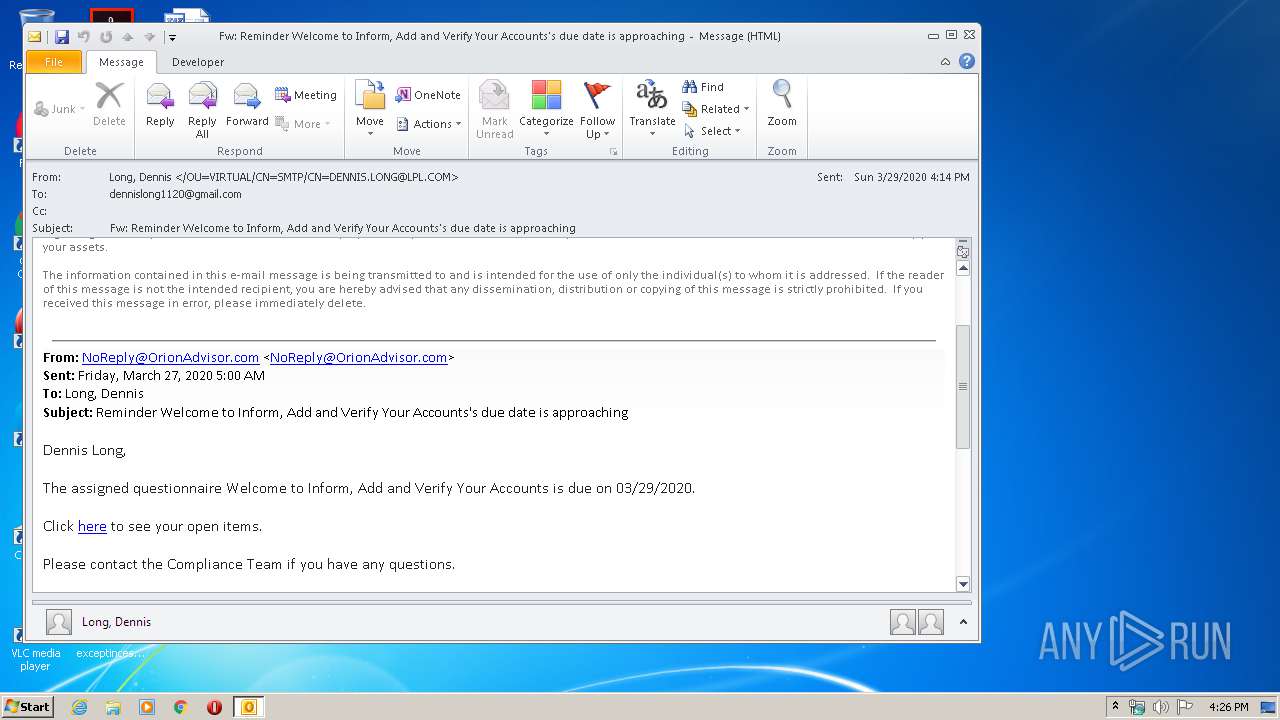
| File name: | 20200329_Fw Reminder Welcome to Inform, Add and Verify Your Accounts's due date is approaching (1).msg |
| Full analysis: | https://app.any.run/tasks/01440b2f-5480-43f2-ab03-c30031be22e3 |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 15:26:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 6DD3F4E37D75B59235C4421388315081 |
| SHA1: | A777A212CC1E625FAFF87D8071563C6B782F8C3B |
| SHA256: | 3B7D3D3181C7AF0119948E4C9F554210DD2301D126BA0ACA92EBD5383837440B |
| SSDEEP: | 192:MGtmn/4uJxFzpwREpwRiRbtD6yc46AFq7H4Acp8NlDrIp/6uxpNTLo7bASPgVdf9:6ZWAWiRbh6THL4AcpYgp7pxLofHkB26 |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3368)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 3368)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3368)
INFO
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3368)
- iexplore.exe (PID: 4056)
- iexplore.exe (PID: 3740)
Changes internet zones settings
- iexplore.exe (PID: 3740)
Creates files in the user directory
- iexplore.exe (PID: 3740)
- iexplore.exe (PID: 4056)
Reads internet explorer settings
- iexplore.exe (PID: 4056)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3368)
Reads settings of System Certificates
- iexplore.exe (PID: 4056)
- iexplore.exe (PID: 3740)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3740)
Changes settings of System certificates
- iexplore.exe (PID: 3740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
41
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
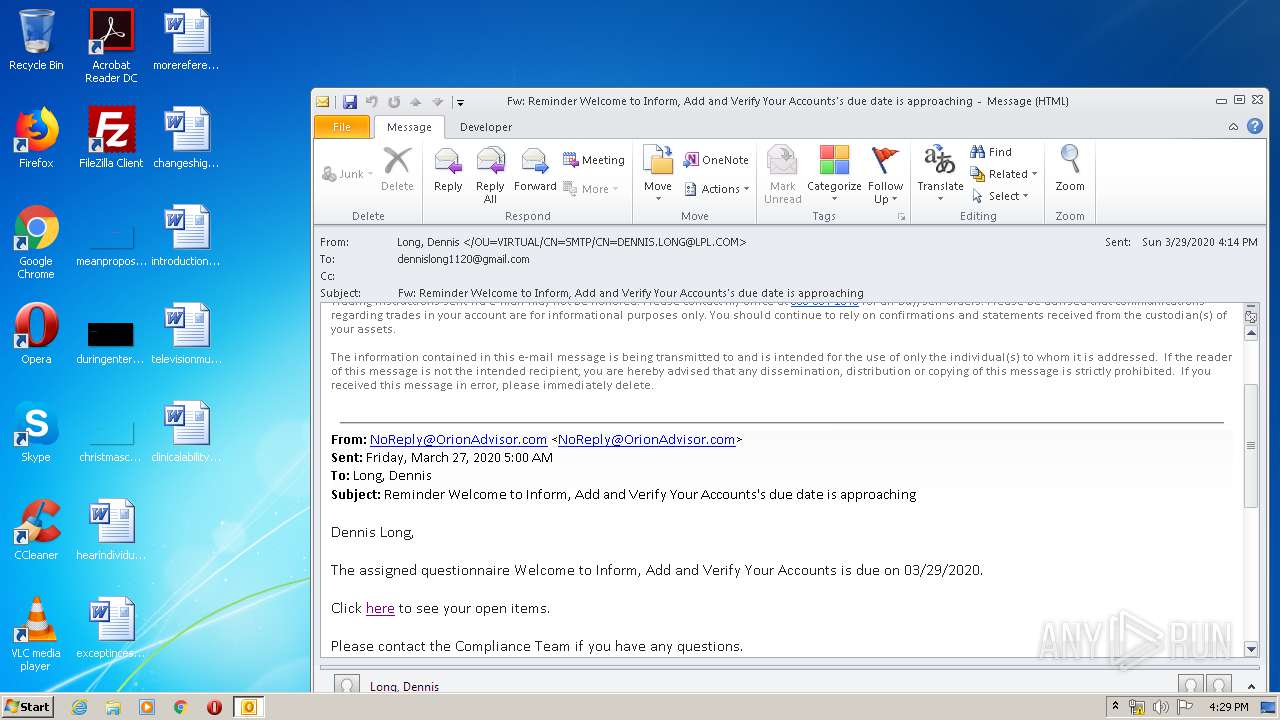
| 3368 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\20200329_Fw Reminder Welcome to Inform, Add and Verify Your Accounts's due date is approaching (1).msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
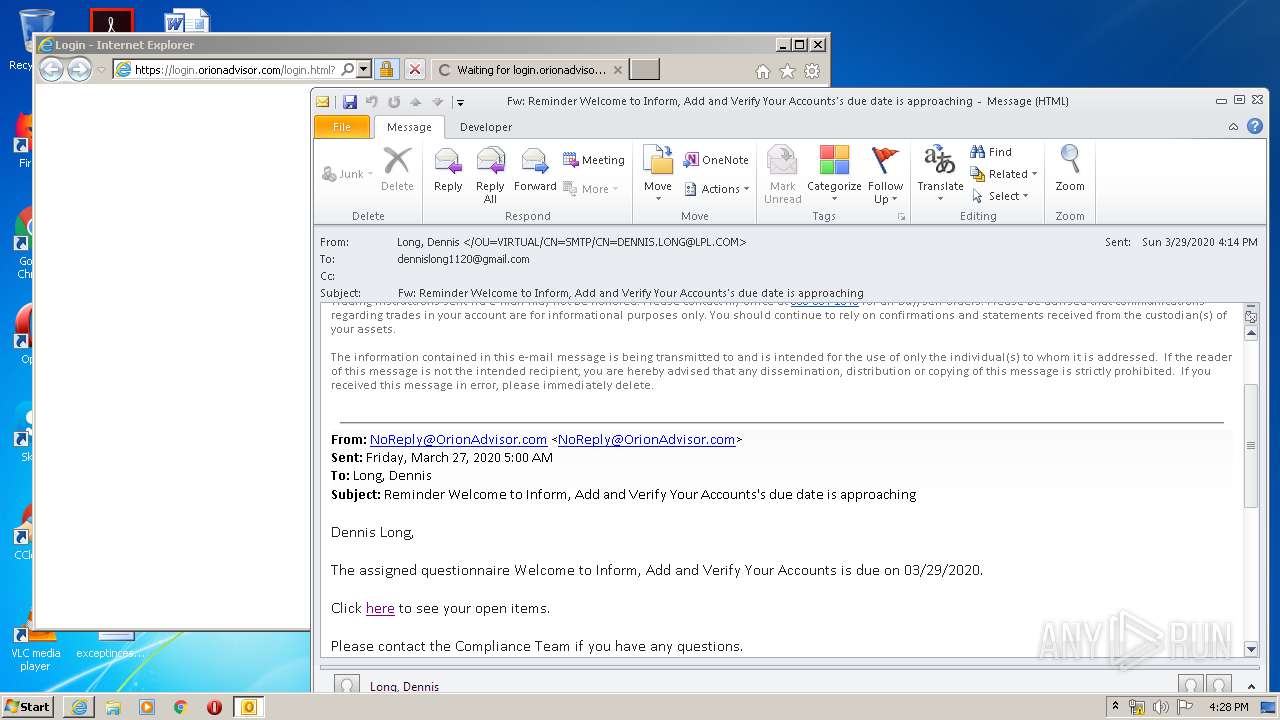
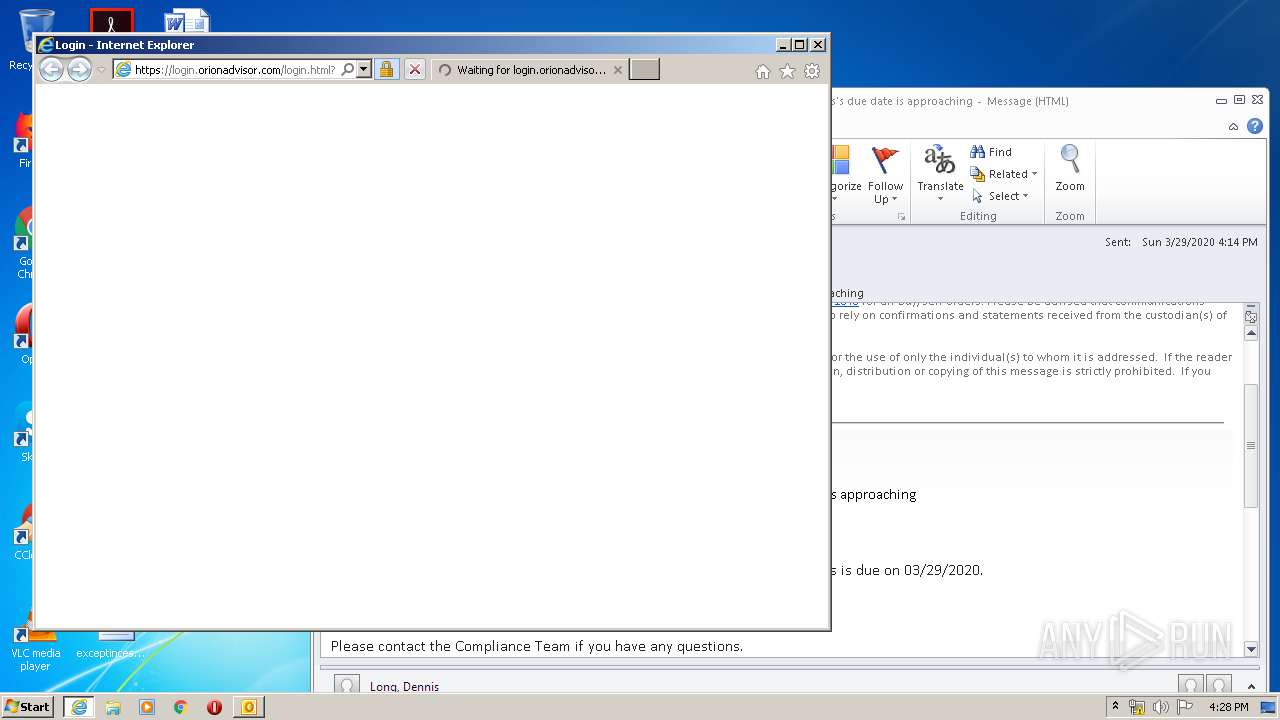
| 3740 | "C:\Program Files\Internet Explorer\iexplore.exe" https://urldefense.proofpoint.com/v2/url?u=https-3A__login.orionadvisor.com_login.html-3Fs-3DorionConnect-26p-3D_tools_inform_dashboard&d=DwMFAg&c=2jpuOek3j4P5cpE4ozX__g&r=2nI_r4QHLE5HlP_8EEX8keA-hIDZyfEqVrq5zI80WbE&m=qxrA9_aExsHfP4ryvawPtNrXZN7rf4jMjelaaYi3dH4&s=YQz5knHvryekXMha-ePGb-rVl-tCi8_bi-NJxDQcoJQ&e= | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4056 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3740 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
7 574
Read events
1 808
Write events
4 025
Delete events
1 741
Modification events
| (PID) Process: | (3368) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3368) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3368) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3368) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3368) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3368) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3368) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3368) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3368) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (3368) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
69
Text files
57
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3368 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR6B74.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4056 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabBB59.tmp | — | |
MD5:— | SHA256:— | |||
| 4056 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarBB5A.tmp | — | |
MD5:— | SHA256:— | |||
| 3740 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3368 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 4056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9915FBCE5ECE56452A09FB65EDE2FAD2_45296097FCB4A9277617A3FC36F918D0 | der | |
MD5:— | SHA256:— | |||
| 4056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_D93C575AD9E9AF9B95268A3CB953B5A1 | der | |
MD5:— | SHA256:— | |||
| 4056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_AD319D6DA1A11BC83AC8B4E4D3638231 | binary | |
MD5:— | SHA256:— | |||
| 4056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9915FBCE5ECE56452A09FB65EDE2FAD2_45296097FCB4A9277617A3FC36F918D0 | binary | |
MD5:— | SHA256:— | |||
| 3368 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
53
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4056 | iexplore.exe | GET | 200 | 192.124.249.24:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
4056 | iexplore.exe | GET | 200 | 192.124.249.24:80 | http://ocsp.godaddy.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCQC5vRqbS5h40w%3D%3D | US | der | 1.74 Kb | whitelisted |
4056 | iexplore.exe | GET | 200 | 172.217.21.227:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
4056 | iexplore.exe | GET | 200 | 172.217.21.227:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
4056 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJaiu8Zb34NbCEEshrmcCs%3D | US | der | 471 b | whitelisted |
4056 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://status.thawte.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSFvn094QJ%2BcWGTwWWEy%2BBXPZkW8AQUo8heZVTlMHjBBeoHCmpZzLn%2B3loCEAQViTVKQs0cDuXr0z1ijHs%3D | US | der | 471 b | whitelisted |
4056 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://status.thawte.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSFvn094QJ%2BcWGTwWWEy%2BBXPZkW8AQUo8heZVTlMHjBBeoHCmpZzLn%2B3loCEAQViTVKQs0cDuXr0z1ijHs%3D | US | der | 471 b | whitelisted |
4056 | iexplore.exe | GET | 200 | 172.217.21.227:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDy4NKedukSQwgAAAAAMgpY | US | der | 472 b | whitelisted |
4056 | iexplore.exe | GET | 200 | 172.217.21.227:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDy4NKedukSQwgAAAAAMgpY | US | der | 472 b | whitelisted |
4056 | iexplore.exe | GET | 200 | 172.217.21.227:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDy4NKedukSQwgAAAAAMgpY | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4056 | iexplore.exe | 67.231.146.66:443 | urldefense.proofpoint.com | Proofpoint, Inc. | US | suspicious |
3368 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
4056 | iexplore.exe | 98.142.89.45:443 | login.orionadvisor.com | COSENTRY.NET, LLC | US | unknown |
4056 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4056 | iexplore.exe | 72.21.91.29:80 | status.thawte.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4056 | iexplore.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
3740 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4056 | iexplore.exe | 151.139.128.14:80 | ocsp.trust-provider.com | Highwinds Network Group, Inc. | US | suspicious |
4056 | iexplore.exe | 192.124.249.24:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
4056 | iexplore.exe | 172.217.23.106:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
urldefense.proofpoint.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
status.thawte.com |
| whitelisted |
login.orionadvisor.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
www.google.com |
| malicious |
ajax.googleapis.com |
| whitelisted |