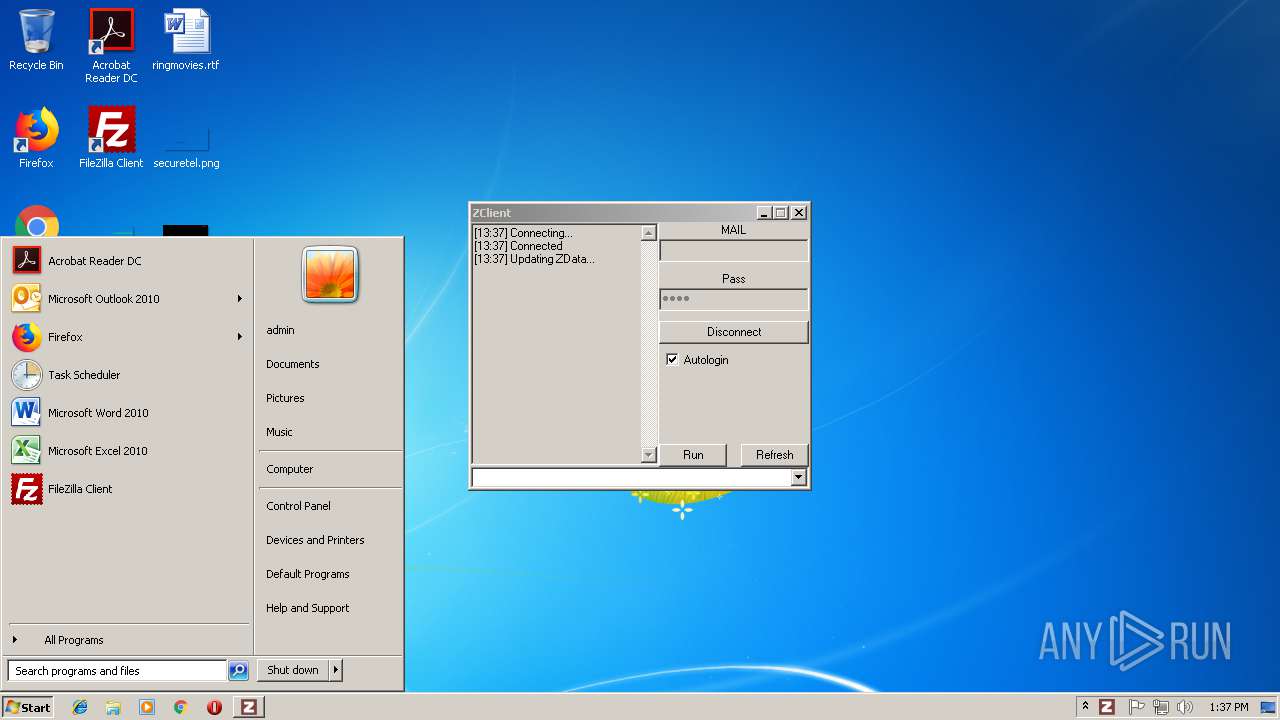
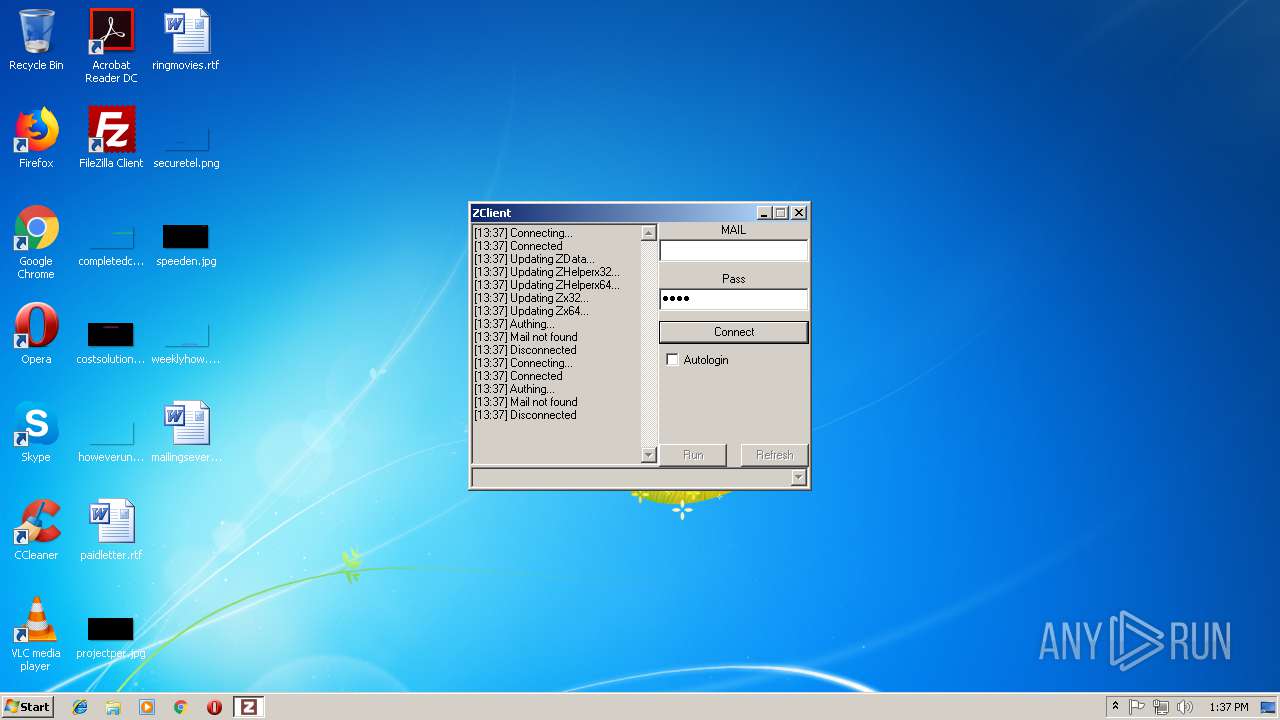
| download: | ZClient.exe |
| Full analysis: | https://app.any.run/tasks/2223db85-3a38-449d-b81d-f3c7a9e64f14 |
| Verdict: | No threats detected |
| Analysis date: | November 06, 2018, 13:36:43 |
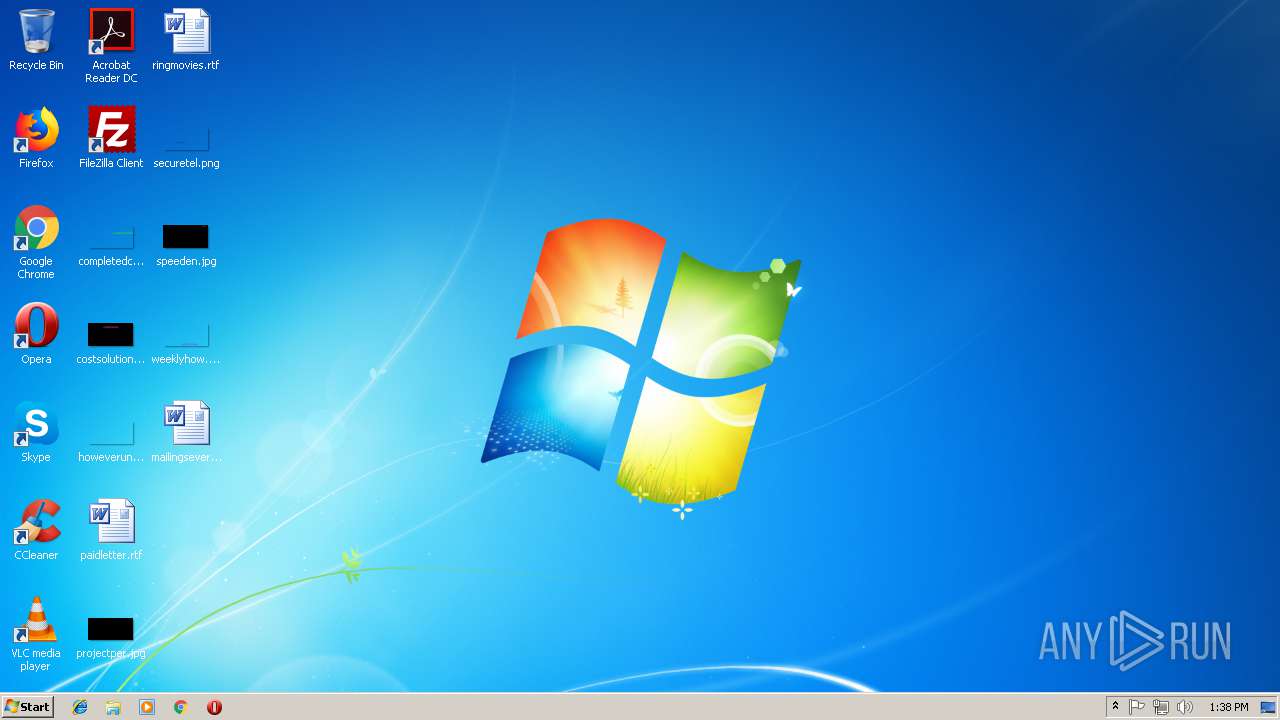
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | FC919143C5F19EBF1DE0A1C011421842 |
| SHA1: | 61AF62E7E71A3703E2E7A4C53721E66A3CE42C9E |
| SHA256: | 3B7463F805B08737DFC6017D14F22614269AB7B2EE684DA5AA5ED08449F1A895 |
| SSDEEP: | 49152:6dtfE2l6na2vKUU2lyvXiy1y4dwtQ1l5myDblmKfjIYK:6dtqNvDvy/i0vdGAKydm25K |
MALICIOUS
No malicious indicators.SUSPICIOUS
Connects to unusual port
- ZClient.exe (PID: 360)
Executable content was dropped or overwritten
- ZClient.exe (PID: 360)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE Yoda's Crypter (63.7) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.7) |
| .exe | | | Win32 Executable (generic) (10.8) |
| .exe | | | Generic Win/DOS Executable (4.8) |
| .exe | | | DOS Executable Generic (4.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| PEType: | PE32 |
| LinkerVersion: | 6.66 |
| CodeSize: | 1912832 |
| InitializedDataSize: | 36864 |
| UninitializedDataSize: | 5132288 |
| EntryPoint: | 0x6b85c0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
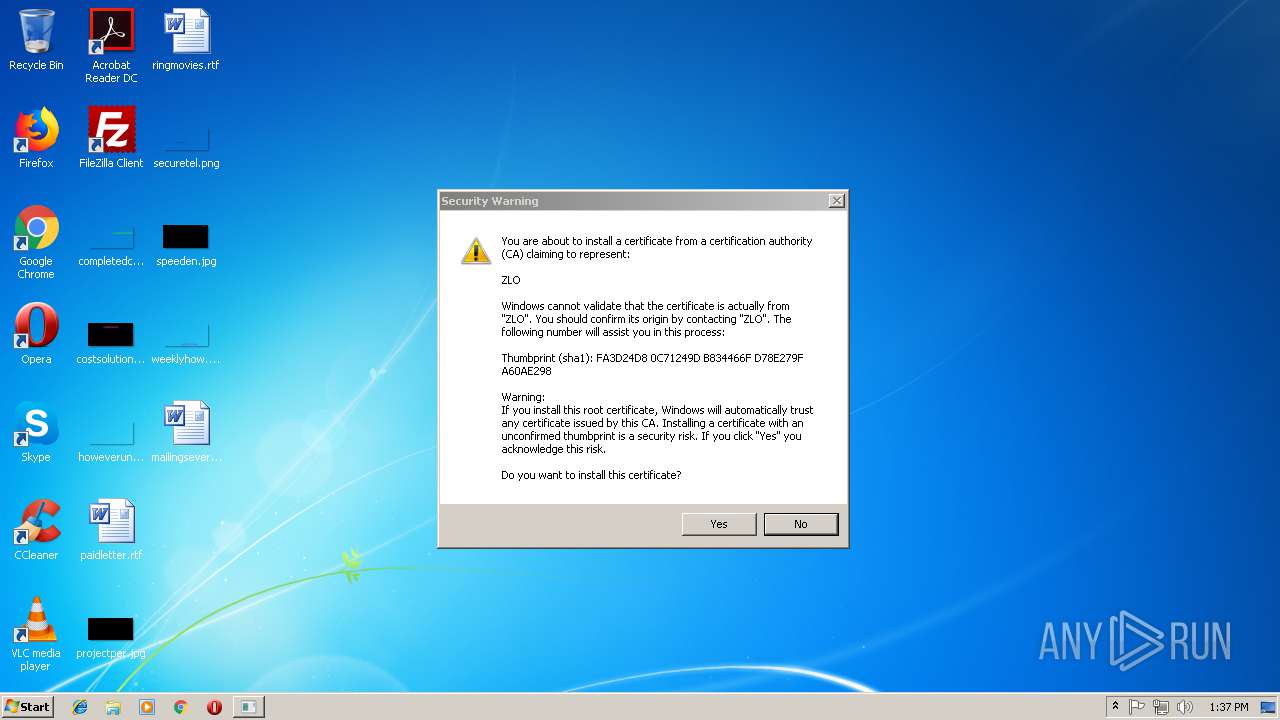
| CompanyName: | ZLOFENIX |
| LegalCopyright: | ZLOFENIX |
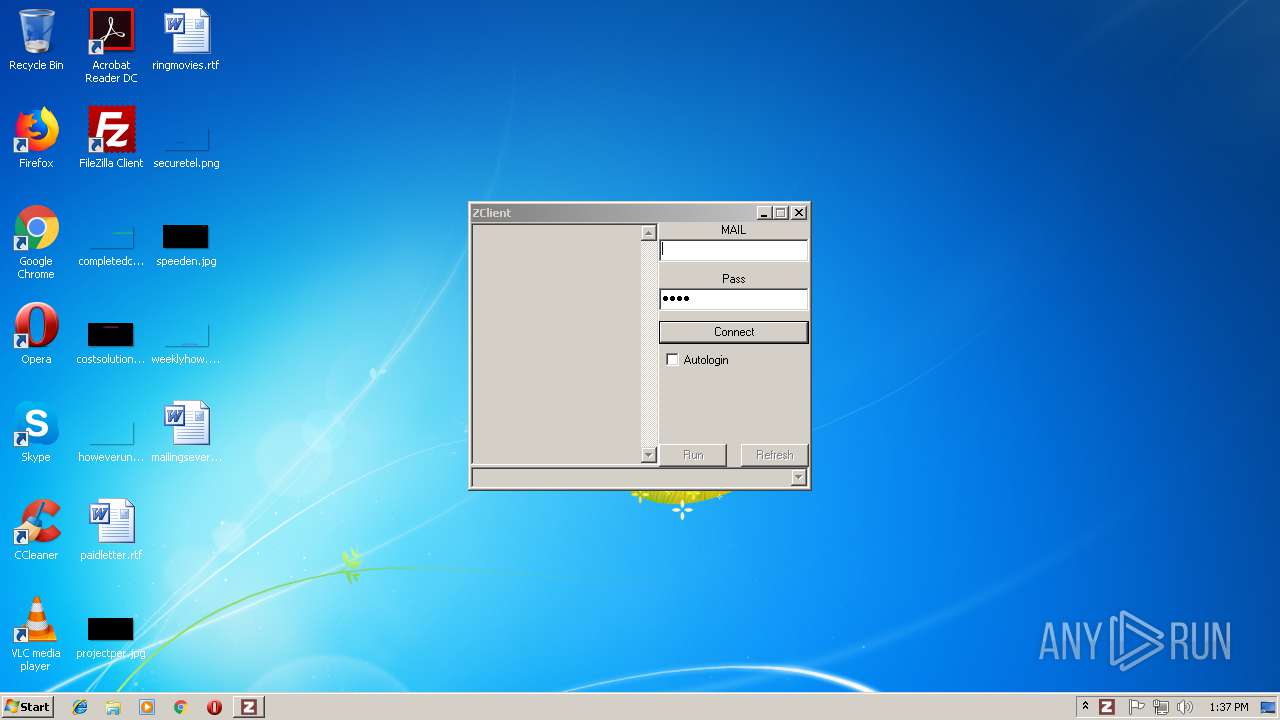
| FileDescription: | ZLOFENIX ZClient |
| FileVersion: | - |
| InternalName: | ZClient |
| OriginalFileName: | ZClient.exe |
| ProductName: | ZLOFENIX ZClient |
| ProductVersion: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Jan-1970 00:00:00 |
| Detected languages: |
|
| TLS Callbacks: | 1 callback(s) detected. |
| CompanyName: | ZLOFENIX |
| LegalCopyright: | ZLOFENIX |
| FileDescription: | ZLOFENIX ZClient |
| FileVersion: | - |
| InternalName: | ZClient |
| OriginalFilename: | ZClient.exe |
| ProductName: | ZLOFENIX ZClient |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-Jan-1970 00:00:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
FDS | 0x00001000 | 0x004E5000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
FGS | 0x004E6000 | 0x001D3000 | 0x001D2800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.90717 |
.rsrc | 0x006B9000 | 0x00009000 | 0x00008800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.37466 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.04305 | 645 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.04305 | 645 | UNKNOWN | English - United States | RT_MANIFEST |
3 | 2.85906 | 5672 | UNKNOWN | English - United States | RT_ICON |
4 | 4.15487 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 4.71686 | 1384 | UNKNOWN | English - United States | RT_ICON |
100 | 7.22221 | 414 | UNKNOWN | UNKNOWN | RT_DIALOG |
200 | 2.58916 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
298 | 7.76419 | 2417 | UNKNOWN | UNKNOWN | UNKNOWN |
299 | 7.89339 | 23284 | UNKNOWN | UNKNOWN | UNKNOWN |
300 | 7.88652 | 12013 | UNKNOWN | UNKNOWN | UNKNOWN |
Imports
ADVAPI32.dll |
CRYPT32.dll |
KERNEL32.DLL |
RPCRT4.dll |
USER32.dll |
WS2_32.dll |
msvcrt.dll |
Total processes
38
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | "C:\Users\admin\AppData\Local\Temp\ZClient.exe" | C:\Users\admin\AppData\Local\Temp\ZClient.exe | explorer.exe | ||||||||||||
User: admin Company: ZLOFENIX Integrity Level: HIGH Description: ZLOFENIX ZClient Exit code: 0 Modules
| |||||||||||||||
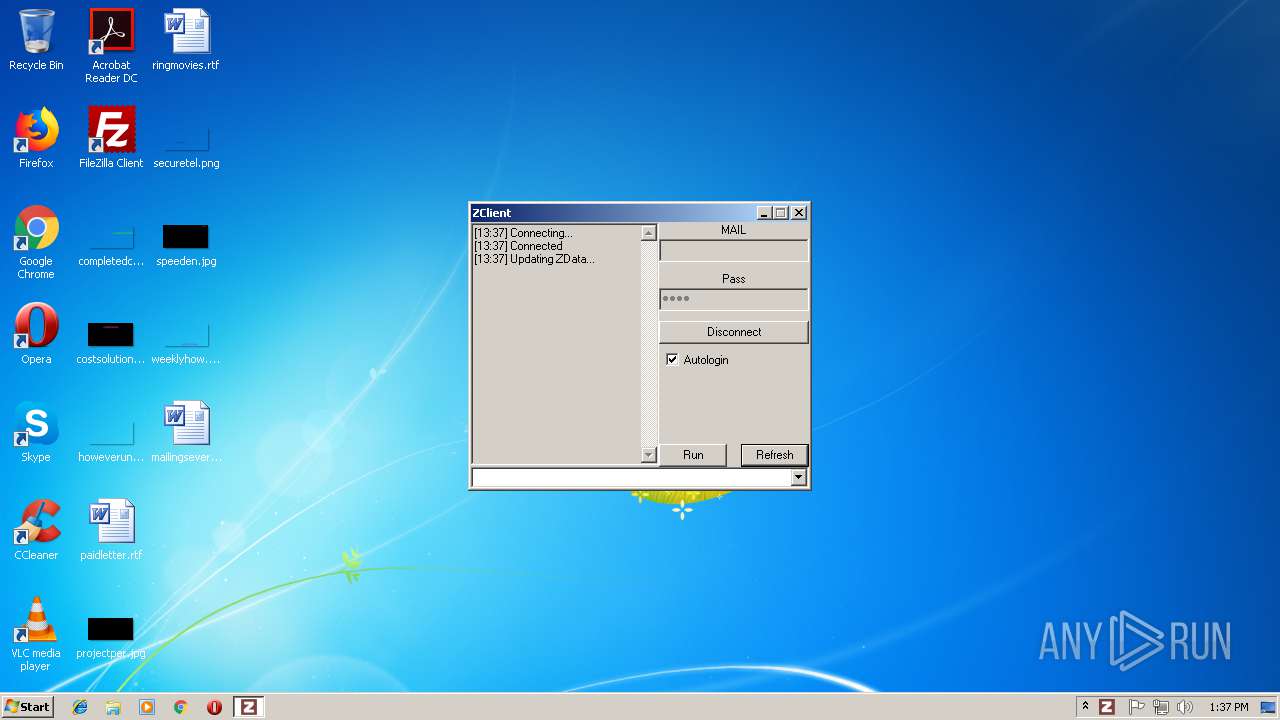
| 1020 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3728 | "C:\Users\admin\AppData\Local\Temp\ZClient.exe" | C:\Users\admin\AppData\Local\Temp\ZClient.exe | — | explorer.exe | |||||||||||
User: admin Company: ZLOFENIX Integrity Level: MEDIUM Description: ZLOFENIX ZClient Exit code: 3221226540 Modules
| |||||||||||||||
Total events
33
Read events
33
Write events
0
Delete events
0
Modification events
Executable files
72
Suspicious files
21
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
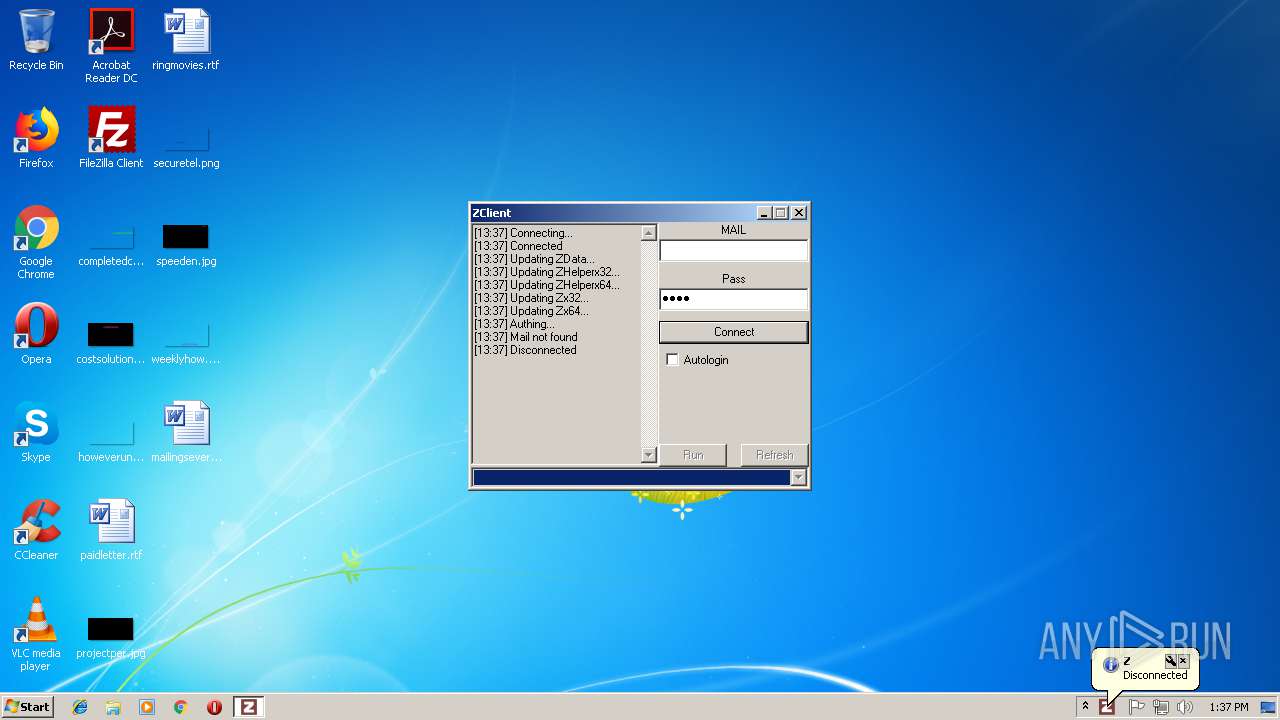
| 360 | ZClient.exe | C:\Users\admin\AppData\Local\Temp\ZData_Settings.zlo | text | |
MD5:41DE1182525153AE47549D2A5768F393 | SHA256:07B3B643AB999B308702F12202EB83C7BE7459060A80A88D170272B407B0ABB9 | |||
| 360 | ZClient.exe | C:\Users\admin\AppData\Local\Temp\ZHelperx64.exe.tmp | executable | |
MD5:622474777922B44980ADF8D34988D22E | SHA256:954C33BFAF32D340D684198F90643054D8EEDAE00C08C7ED414313D7146C6077 | |||
| 360 | ZClient.exe | C:\Users\admin\AppData\Local\Temp\ZData.zlo.tmp | binary | |
MD5:F7BD6B305993EBB4BAAD10749329D22E | SHA256:64B844D60F1C7B5A66D9341DC77A6D7ACD3BC37DD2EA75D08C9AC060435E3E60 | |||
| 360 | ZClient.exe | C:\Users\admin\AppData\Local\Temp\Zx32.dll.tmp | executable | |
MD5:5CF93F45AC5BC3A347D3B8C681D59A97 | SHA256:89FCD839DEE094A3951C2E8743CCAF350334F70F7FB6E83BADBFE4E1A266318D | |||
| 360 | ZClient.exe | C:\Users\admin\AppData\Local\Temp\ZHelperx32.exe.tmp | executable | |
MD5:1E9279E3207D2622E1652D0CBA50A825 | SHA256:72087121D8ECA7BC0350F9A1544CBAE0E657FF3E60A08FA6605CB61CCB363FDF | |||
| 360 | ZClient.exe | C:\Users\admin\AppData\Local\Temp\ZData.zlo | binary | |
MD5:1A51828E91271E32F7DB1C1AB858A554 | SHA256:A0C4B7453E50C4F3FCB049BE9780A93E10C6D4765018695906A7EDC24BED0E19 | |||
| 360 | ZClient.exe | C:\Users\admin\AppData\Local\Temp\ZHelperx32.exe | executable | |
MD5:8CB215268D97C505A8AB72E555B6484D | SHA256:0CFDF8B57D97C9BE7432C160DF445BEEAB738C10A25B3490CB3F224C33A9980D | |||
| 360 | ZClient.exe | C:\Users\admin\AppData\Local\Temp\ZHelperx64.exe | executable | |
MD5:47FDB0988A0B8A2E2CD03A369ECD31B9 | SHA256:93FC8F92B58CE1E86A3733C6D759D3E3FE460C1B84DB3C36D1B1266A96BFB7FF | |||
| 360 | ZClient.exe | C:\Users\admin\AppData\Local\Temp\Zx64.dll | executable | |
MD5:C156C82CED4DB90188AC4F589B869B1A | SHA256:9D89BEACA0CDADE8A32C6294DCADB49776A898BBBF57E8FF8F33AE42488C361E | |||
| 360 | ZClient.exe | C:\Users\admin\AppData\Local\Temp\Zx64.dll.tmp | executable | |
MD5:8F1B549A8DB91F144300FE2F24D7C76A | SHA256:EEFDF69EA7C9FD1200706A9A22E4FA66E45B95A78E4033C72DC7C11666A82354 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
360 | ZClient.exe | 149.202.87.147:48377 | zm.zloemu.net | OVH SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
zm.zloemu.net |
| unknown |