| File name: | 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe |
| Full analysis: | https://app.any.run/tasks/e25221f5-1264-44d0-bfb1-8e8556e45a25 |
| Verdict: | Malicious activity |
| Analysis date: | April 22, 2024, 14:00:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 0444B3D690823924667302CFAE1F0655 |
| SHA1: | 737D0D001E60CE20C8F35A2BBAC0F4D525B96174 |
| SHA256: | 3B685F4A59211225997256A5CD900F44953BBA276B6EB92545966B35B6EF89B5 |
| SSDEEP: | 6144:JYj1IZU72k7rleEncWiaQ4+JqCdzNH0tQ14X67L7:JYj1IZU72kXleCcWR+YUz54tIL7 |
MALICIOUS
Drops the executable file immediately after the start
- 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe (PID: 3768)
Deletes shadow copies
- cmd.exe (PID: 3360)
- cmd.exe (PID: 3620)
Using BCDEDIT.EXE to modify recovery options
- cmd.exe (PID: 3780)
- cmd.exe (PID: 2480)
Actions looks like stealing of personal data
- 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe (PID: 3768)
Starts CMD.EXE for self-deleting
- 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe (PID: 3768)
SUSPICIOUS
Found strings related to reading or modifying Windows Defender settings
- 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe (PID: 3768)
Reads the Internet Settings
- 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe (PID: 3768)
- cmd.exe (PID: 2880)
Starts CMD.EXE for commands execution
- 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe (PID: 3768)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2360)
- cmd.exe (PID: 4032)
- cmd.exe (PID: 1344)
- cmd.exe (PID: 2880)
- cmd.exe (PID: 2492)
- cmd.exe (PID: 4092)
- cmd.exe (PID: 1632)
- cmd.exe (PID: 3404)
- cmd.exe (PID: 3432)
- cmd.exe (PID: 1112)
- cmd.exe (PID: 3612)
- cmd.exe (PID: 3216)
- cmd.exe (PID: 4000)
- cmd.exe (PID: 2052)
- cmd.exe (PID: 3652)
- cmd.exe (PID: 3300)
- cmd.exe (PID: 2132)
- cmd.exe (PID: 2784)
- cmd.exe (PID: 896)
- cmd.exe (PID: 3020)
- cmd.exe (PID: 1428)
- cmd.exe (PID: 3984)
- cmd.exe (PID: 3440)
- cmd.exe (PID: 2476)
- cmd.exe (PID: 4092)
- cmd.exe (PID: 3988)
- cmd.exe (PID: 1644)
- cmd.exe (PID: 4020)
Reads security settings of Internet Explorer
- 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe (PID: 3768)
Uses WEVTUTIL.EXE to cleanup log
- cmd.exe (PID: 3720)
- cmd.exe (PID: 3940)
- cmd.exe (PID: 2060)
- cmd.exe (PID: 1876)
- cmd.exe (PID: 2376)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2524)
Creates file in the systems drive root
- 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe (PID: 3768)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 3568)
Hides command output
- cmd.exe (PID: 3568)
INFO
Checks supported languages
- 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe (PID: 3768)
Reads the machine GUID from the registry
- 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe (PID: 3768)
Reads the computer name
- 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe (PID: 3768)
Creates files in the program directory
- 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe (PID: 3768)
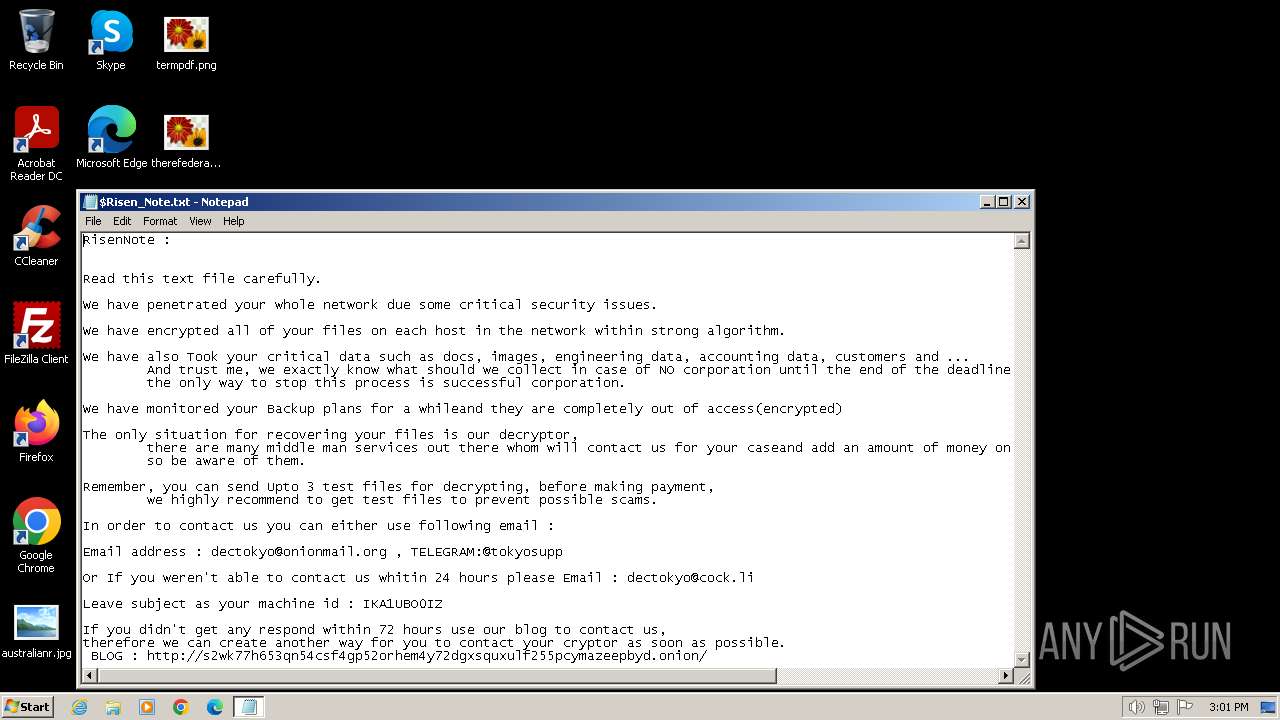
Dropped object may contain TOR URL's
- 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe (PID: 3768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.6) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:03:18 10:11:16+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 151552 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 290816 |
| EntryPoint: | 0x6bd40 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
Total processes
176
Monitored processes
93
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 796 | bcdedit /set {default} bootstatuspolicy IgnoreAllFailures | C:\Windows\System32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Boot Configuration Data Editor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 844 | reg add "HKEY_LOCAL_MACHINE\Software\Policies\Microsoft\Windows\WinRE" /v "DisableSetup" /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 864 | reg add "HKEY_LOCAL_MACHINE\Software\Policies\Microsoft\Windows Defender\Spynet" /v "SubmitSamplesConsent" /t REG_DWORD /d 2 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 876 | reg add "HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer" /v "NoRun" /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 896 | "C:\Windows\System32\cmd.exe" /c reg add "HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer" /v "NoClose" /t REG_DWORD /d 1 /f | C:\Windows\System32\cmd.exe | — | 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 896 | ping 127.0.0.1 -n 5 | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1112 | "C:\Windows\System32\cmd.exe" /c reg add "HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System" /v "DisableChangePassword" /t REG_DWORD /d 1 /f | C:\Windows\System32\cmd.exe | — | 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1264 | wevtutil.exe cl Security | C:\Windows\System32\wevtutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Eventing Command Line Utility Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1344 | "C:\Windows\System32\cmd.exe" /c reg add "HKEY_LOCAL_MACHINE\Software\Policies\Microsoft\Windows Defender\Real-Time Protection" /v "DisableRealtimeMonitoring" /t REG_DWORD /d 1 /f | C:\Windows\System32\cmd.exe | — | 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1368 | reg add "HKEY_LOCAL_MACHINE\Software\Policies\Microsoft\Windows NT\SystemRestore" /v "DisableSR" /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
8 250
Read events
7 874
Write events
376
Delete events
0
Modification events
| (PID) Process: | (3768) 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3768) 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3768) 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3768) 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2880) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2880) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2880) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2880) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
43
Text files
103
Unknown types
77
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3768 | 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe | C:\MSOCache\$Risen_Note.txt | — | |
MD5:— | SHA256:— | |||
| 3768 | 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe | C:\ProgramData\$Risen_Guide.hta | — | |
MD5:— | SHA256:— | |||
| 3768 | 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe | C:\ProgramData\Oracle\$Risen[IKA1UBO0IZ].Private | binary | |
MD5:B7AB8DCD508F98C6E185AA54F7B754DB | SHA256:23D0ED6A409108157FF69B00331ABDF6EB77DD21F1EABEABB4EB8B057672284E | |||
| 3768 | 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe | C:\ProgramData\Adobe\$Risen_Note.txt | text | |
MD5:CF277C4EA3FD42A88D3A8E188B4CB9E9 | SHA256:4DA9ECB64DFEE3715AE7E87B38392B90EF90DD79FA9DE97B55058049013040A0 | |||
| 3768 | 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe | C:\ProgramData\$Risen[IKA1UBO0IZ].Private | binary | |
MD5:B7AB8DCD508F98C6E185AA54F7B754DB | SHA256:23D0ED6A409108157FF69B00331ABDF6EB77DD21F1EABEABB4EB8B057672284E | |||
| 3768 | 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe | C:\ProgramData\$Risen_Note.txt | text | |
MD5:CF277C4EA3FD42A88D3A8E188B4CB9E9 | SHA256:4DA9ECB64DFEE3715AE7E87B38392B90EF90DD79FA9DE97B55058049013040A0 | |||
| 3768 | 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe | C:\MSOCache\$Risen_Guide.hta | html | |
MD5:47E628990C04161C5DD07169ABBD0486 | SHA256:51B3F2EDF7A8284D6BBF9EE8D6F1944E44BAE5AD83F214106A3114C9F69AED12 | |||
| 3768 | 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe | C:\ProgramData\Adobe\$Risen_Guide.hta | html | |
MD5:47E628990C04161C5DD07169ABBD0486 | SHA256:51B3F2EDF7A8284D6BBF9EE8D6F1944E44BAE5AD83F214106A3114C9F69AED12 | |||
| 3768 | 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe | C:\ProgramData\Adobe\$Risen[IKA1UBO0IZ].Private | binary | |
MD5:B7AB8DCD508F98C6E185AA54F7B754DB | SHA256:23D0ED6A409108157FF69B00331ABDF6EB77DD21F1EABEABB4EB8B057672284E | |||
| 3768 | 3b685f4a59211225997256a5cd900f44953bba276b6eb92545966b35b6ef89b5.exe | C:\ProgramData\Oracle\$Risen_Note.txt | text | |
MD5:CF277C4EA3FD42A88D3A8E188B4CB9E9 | SHA256:4DA9ECB64DFEE3715AE7E87B38392B90EF90DD79FA9DE97B55058049013040A0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |