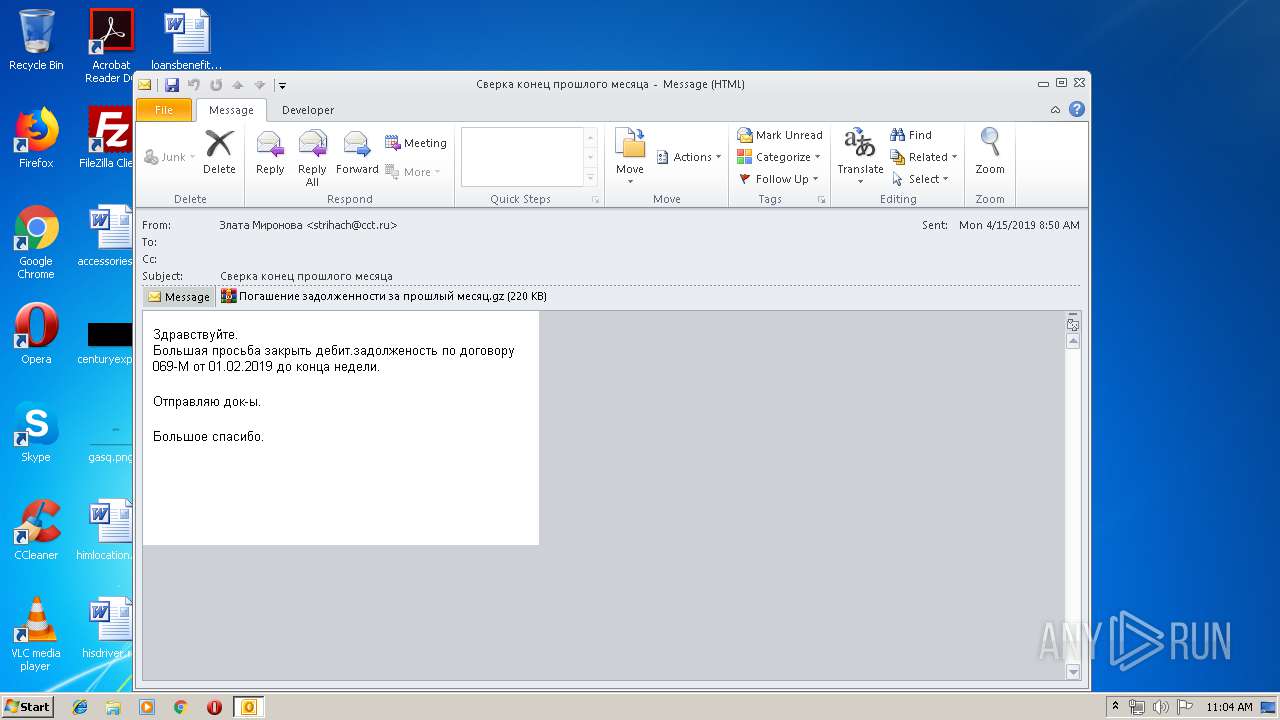
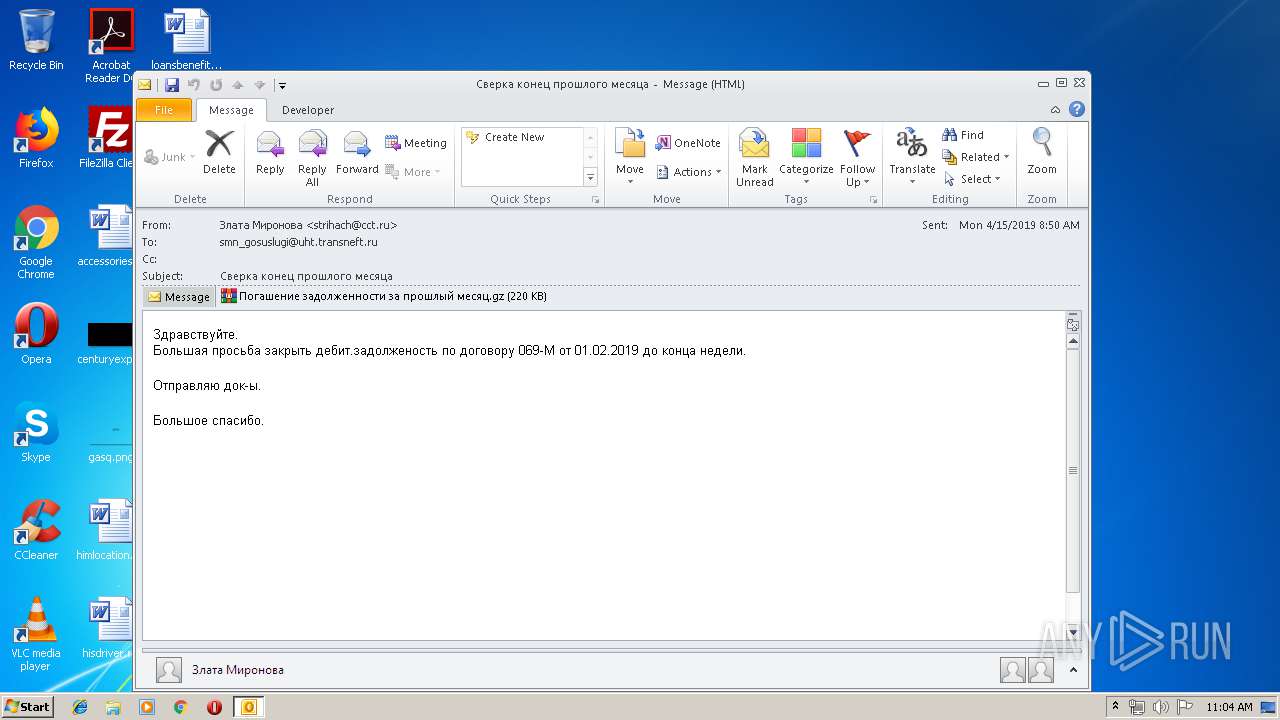
| File name: | Сверка конец прошлого месяца.eml |
| Full analysis: | https://app.any.run/tasks/8f7955ae-e33f-476a-9f80-9187ecde231f |
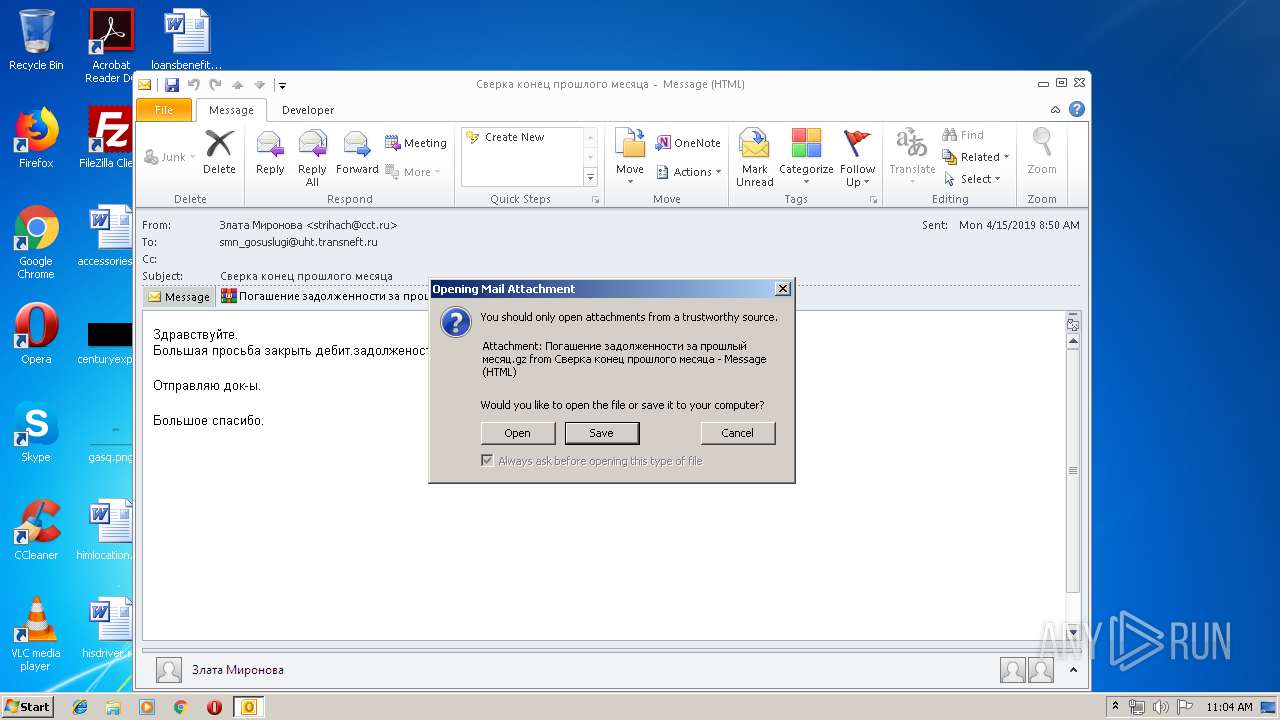
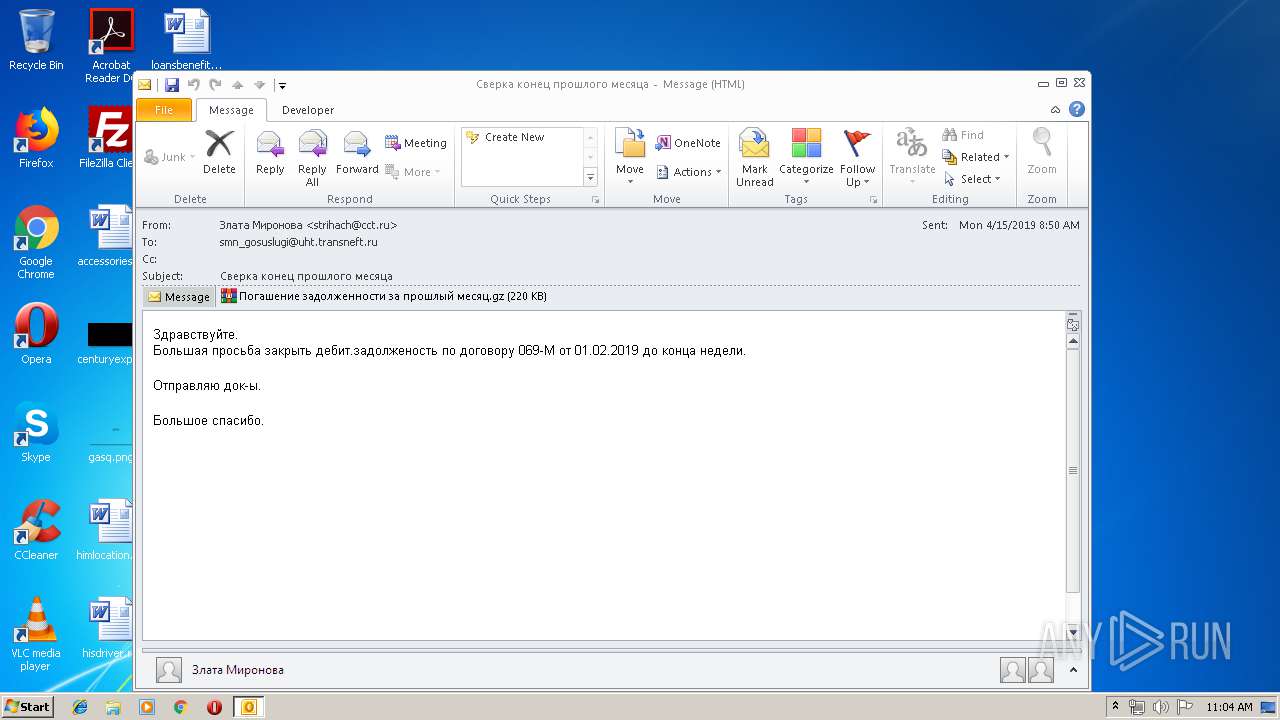
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2019, 10:04:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | C49E646438BD81E0C9BA1F00E23F89EB |
| SHA1: | C5ABA27BEADD0D8374F61E4ECF0865E060D376B7 |
| SHA256: | 3B66A0C4A4E15FEA84E746B15605ECF06BE32A02A843AA27F5F1E5A226EF2D49 |
| SSDEEP: | 6144:LGHiy9oykaT7RM4w8fittxNMh0IKFnJPdCL/kagcfTv9YSX:sZ+ykk7RMb8fstYqZJ1CucffX |
MALICIOUS
Changes the autorun value in the registry
- Погашение задолженности за прошлый месяц.exe (PID: 2204)
Application was dropped or rewritten from another process
- Погашение задолженности за прошлый месяц.exe (PID: 2204)
Loads dropped or rewritten executable
- rundll32.exe (PID: 3324)
- rundll32.exe (PID: 3424)
Loads the Task Scheduler COM API
- rundll32.exe (PID: 3324)
Changes settings of System certificates
- rundll32.exe (PID: 3424)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2504)
Executable content was dropped or overwritten
- Погашение задолженности за прошлый месяц.exe (PID: 2204)
- WinRAR.exe (PID: 2200)
- rundll32.exe (PID: 3324)
Uses RUNDLL32.EXE to load library
- Погашение задолженности за прошлый месяц.exe (PID: 2204)
Creates files in the program directory
- rundll32.exe (PID: 3324)
Adds / modifies Windows certificates
- rundll32.exe (PID: 3424)
Connects to server without host name
- rundll32.exe (PID: 3424)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
38
Monitored processes
5
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
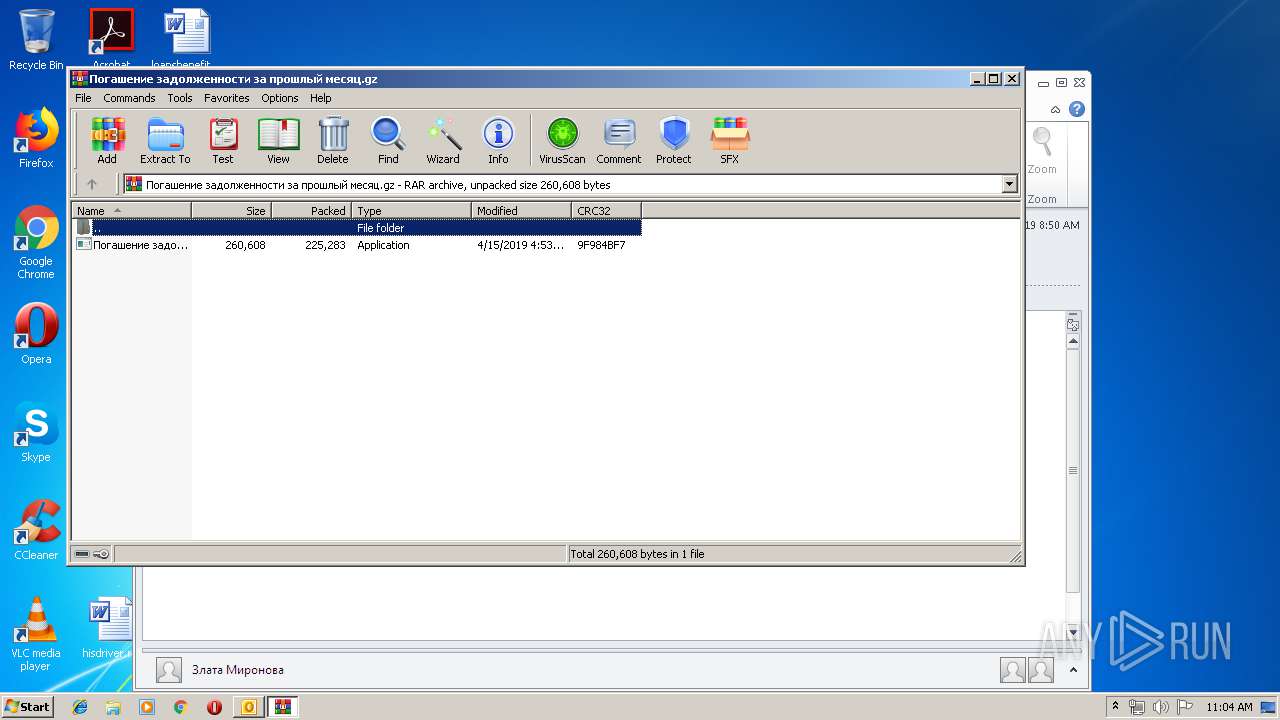
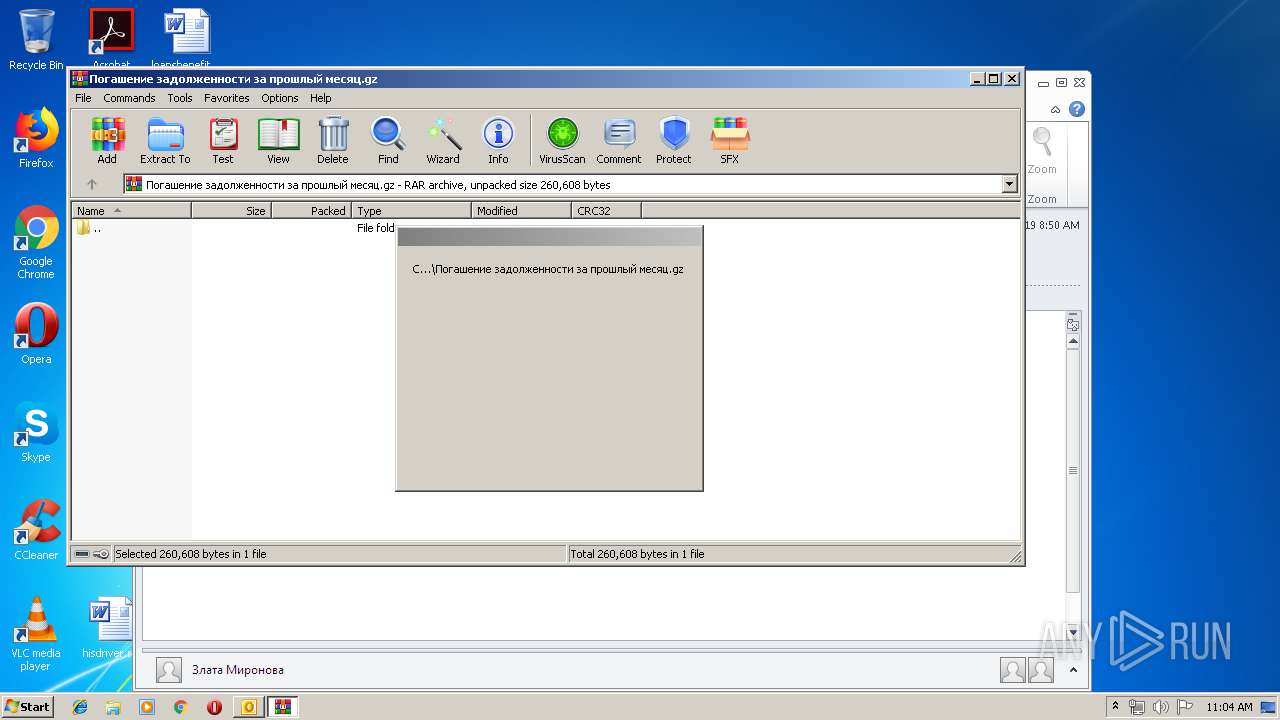
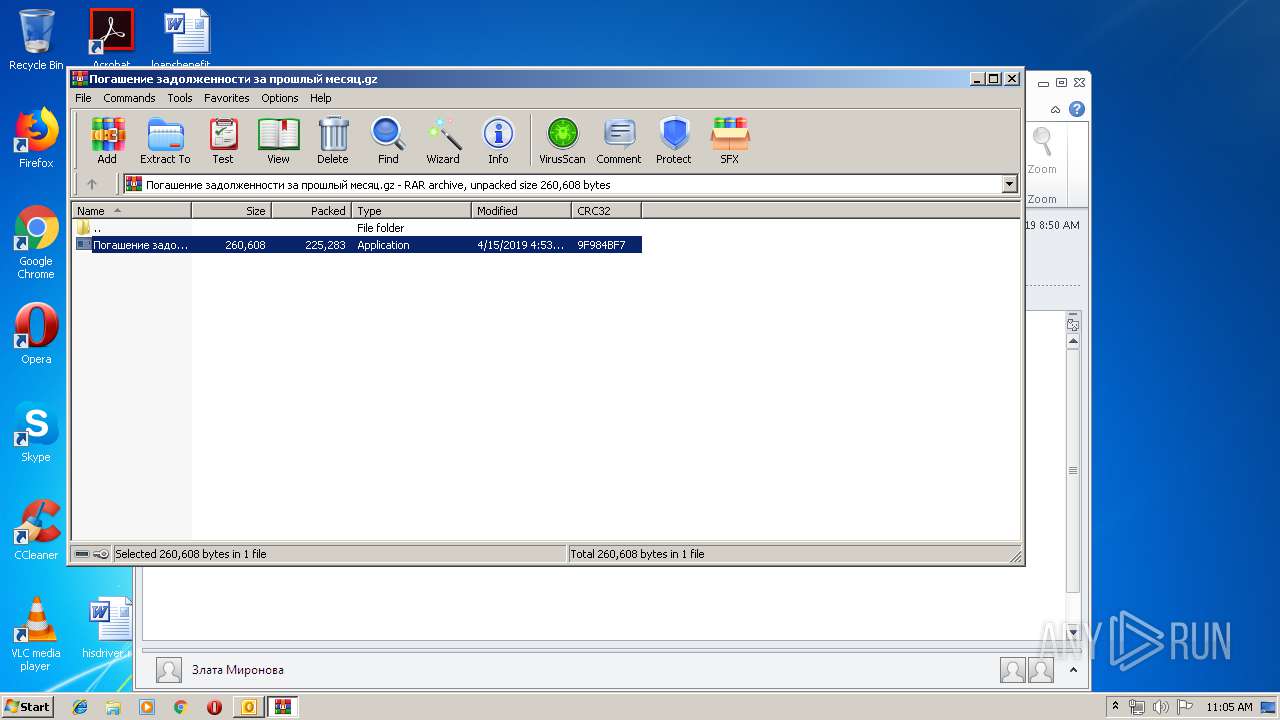
| 2200 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\4ZQEKVF4\Погашение задолженности за прошлый месяц.gz" | C:\Program Files\WinRAR\WinRAR.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2204 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2200.20059\Погашение задолженности за прошлый месяц.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2200.20059\Погашение задолженности за прошлый месяц.exe | WinRAR.exe | ||||||||||||
User: admin Company: Корпорация Майкрософт Integrity Level: MEDIUM Description: Самоизвлечение CAB-файлов Win32 Exit code: 0 Version: 6.00.2900.5512 (xpsp.080413-2105) Modules
| |||||||||||||||
| 2504 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Сверка конец прошлого месяца.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3324 | rundll32.exe 467.dll,DllGetClassObject root 000000000000 Post Install program: <None> | C:\Windows\system32\rundll32.exe | Погашение задолженности за прошлый месяц.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3424 | rundll32.exe "C:\ProgramData\2401bf603c90\2702bc633f93.dat",DllGetClassObject root | C:\Windows\system32\rundll32.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 028
Read events
1 580
Write events
426
Delete events
22
Modification events
| (PID) Process: | (2504) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2504) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2504) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | =+; |
Value: 3D2B3B00C8090000010000000000000000000000 | |||
| (PID) Process: | (2504) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: C8090000866CD59B72F3D40100000000 | |||
| (PID) Process: | (2504) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2504) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219996000 | |||
| (PID) Process: | (2504) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2504) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2504) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2504) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1317994517 | |||
Executable files
3
Suspicious files
2
Text files
24
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2504 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR63AD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2504 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp6600.tmp | — | |
MD5:— | SHA256:— | |||
| 2504 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\4ZQEKVF4\Погашение задолженности за прошлый месяц (2).gz\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2504 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\4ZQEKVF4\Погашение задолженности за прошлый месяц (2).gz | compressed | |
MD5:— | SHA256:— | |||
| 2200 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2200.20059\Погашение задолженности за прошлый месяц.exe | executable | |
MD5:— | SHA256:— | |||
| 3324 | rundll32.exe | C:\ProgramData\2401bf603c90\2702bc633f93.dat | executable | |
MD5:— | SHA256:— | |||
| 2204 | Погашение задолженности за прошлый месяц.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\467.dll | executable | |
MD5:— | SHA256:— | |||
| 2504 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:48DD6CAE43CE26B992C35799FCD76898 | SHA256:7BFE1F3691E2B4FB4D61FBF5E9F7782FBE49DA1342DBD32201C2CC8E540DBD1A | |||
| 2504 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2504 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\4ZQEKVF4\Погашение задолженности за прошлый месяц.gz | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3424 | rundll32.exe | POST | — | 185.203.119.104:80 | http://185.203.119.104/index.php | BG | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2504 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3424 | rundll32.exe | 52.36.204.116:443 | namecoin.cyphrs.com | Amazon.com, Inc. | US | unknown |
3424 | rundll32.exe | 185.203.119.104:80 | — | BelCloud Hosting Corporation | BG | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
dns.msftncsi.com |
| shared |
namecoin.cyphrs.com |
| unknown |