| File name: | 3b63f74430f0f907111835cef9b893790d92d73f01b31ffc7658e0727fa787b4.exe |
| Full analysis: | https://app.any.run/tasks/911d5ee2-52f9-46cd-96ac-e6a4fd252622 |
| Verdict: | Malicious activity |
| Analysis date: | May 25, 2024, 18:26:10 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InstallShield self-extracting archive |
| MD5: | 4F1A8CFDA914EC7F81B306BC5FFC5457 |
| SHA1: | B43485DAC6DD758E332F2C58774F57DB884CD570 |
| SHA256: | 3B63F74430F0F907111835CEF9B893790D92D73F01B31FFC7658E0727FA787B4 |
| SSDEEP: | 98304:DkA8y/YfSbASdjbp9uCfDCUDr1gt/4YPMQDLf90XDdHsZ0VjhhK:j |
MALICIOUS
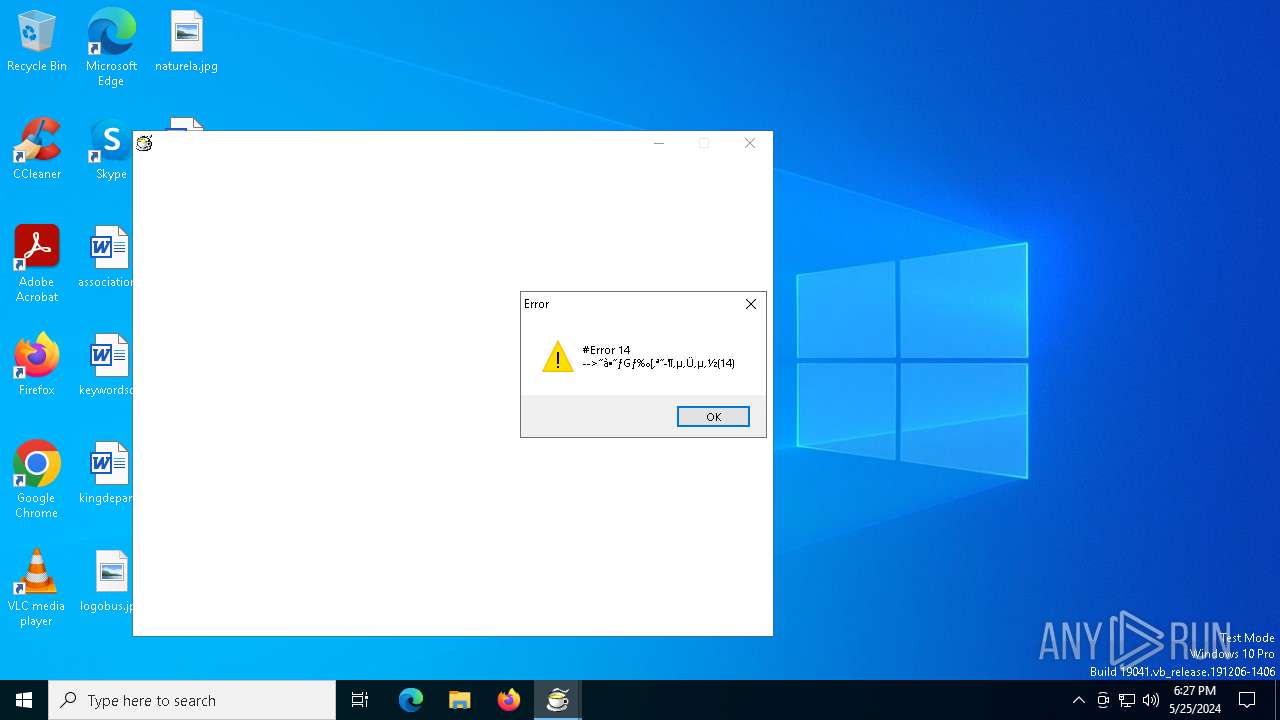
Drops the executable file immediately after the start
- 3b63f74430f0f907111835cef9b893790d92d73f01b31ffc7658e0727fa787b4.exe (PID: 472)
SUSPICIOUS
Executable content was dropped or overwritten
- 3b63f74430f0f907111835cef9b893790d92d73f01b31ffc7658e0727fa787b4.exe (PID: 472)
Reads security settings of Internet Explorer
- boot.exe (PID: 704)
Process requests binary or script from the Internet
- boot.exe (PID: 704)
Checks Windows Trust Settings
- boot.exe (PID: 704)
INFO
Reads the computer name
- 3b63f74430f0f907111835cef9b893790d92d73f01b31ffc7658e0727fa787b4.exe (PID: 472)
- boot.exe (PID: 704)
Checks proxy server information
- boot.exe (PID: 704)
Checks supported languages
- boot.exe (PID: 704)
- 3b63f74430f0f907111835cef9b893790d92d73f01b31ffc7658e0727fa787b4.exe (PID: 472)
Reads the software policy settings
- boot.exe (PID: 704)
Reads the machine GUID from the registry
- boot.exe (PID: 704)
Creates files or folders in the user directory
- boot.exe (PID: 704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2000:12:18 04:52:02+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 5.2 |
| CodeSize: | 24064 |
| InitializedDataSize: | 11264 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1a90 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.10.0.0 |
| ProductVersionNumber: | 1.10.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Japanese |
| CharacterSet: | Unicode |
| FileDescription: | Cabinet Self-Extractor |
| FileVersion: | 1.1 |
| InternalName: | CABSFX |
| LegalCopyright: | Copyright (C) 1999-2000 Y.Shirakawa |
| OriginalFileName: | CABSFX |
| ProductName: | CABSFX |
| ProductVersion: | 1.1 |
Total processes
127
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | "C:\Users\admin\AppData\Local\Temp\3b63f74430f0f907111835cef9b893790d92d73f01b31ffc7658e0727fa787b4.exe" | C:\Users\admin\AppData\Local\Temp\3b63f74430f0f907111835cef9b893790d92d73f01b31ffc7658e0727fa787b4.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Cabinet Self-Extractor Exit code: 0 Version: 1.10 Modules
| |||||||||||||||
| 704 | C:\kasoft\j\boot.exe | C:\kasoft\j\boot.exe | 3b63f74430f0f907111835cef9b893790d92d73f01b31ffc7658e0727fa787b4.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
Total events
1 476
Read events
1 464
Write events
12
Delete events
0
Modification events
| (PID) Process: | (704) boot.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: boot.exe | |||
| (PID) Process: | (704) boot.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (704) boot.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (704) boot.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (704) boot.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (704) boot.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (704) boot.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (704) boot.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
4
Suspicious files
6
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 704 | boot.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:9C4CFAEC98BB4BD38E0F445C17594194 | SHA256:8BF9650EFE5508943CD0D0B1CED2A28D99C256323692BCCC45B032C888B7AA7A | |||
| 704 | boot.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:B54EE3141B59659AF5E3F171445C5ECE | SHA256:F1B98092B580635F43D37E747B963BD80F39EFBBE414633290C1BE160C5ACE1F | |||
| 704 | boot.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_E0B3E71C82BFD33CB0604785B69090B6 | binary | |
MD5:6ED1DC0A7B9745190C89D23650858C62 | SHA256:429353CDB29CDDA5FE7C7FF85E4BB3AB89099A29BF680660D394646191A3C243 | |||
| 472 | 3b63f74430f0f907111835cef9b893790d92d73f01b31ffc7658e0727fa787b4.exe | C:\kasoft\j\boot.exe | executable | |
MD5:3ACAEC1CF8D5BA711444379F95402D46 | SHA256:E410B726164605EEF5666F1A3D906C965068A2FCE2A0813E64C2BDBE23620574 | |||
| 472 | 3b63f74430f0f907111835cef9b893790d92d73f01b31ffc7658e0727fa787b4.exe | C:\kasoft\j\hspinet.dll | executable | |
MD5:7573BF4D3F906E7FD6210BCF0C66F665 | SHA256:949C2E20E8DB4D4F11806EA8A8E3ACAE08F2358F48492D3A8A2D43F0BE71EAA0 | |||
| 472 | 3b63f74430f0f907111835cef9b893790d92d73f01b31ffc7658e0727fa787b4.exe | C:\kasoft\j\hspext.dll | executable | |
MD5:A296A95B90DE1D07B4BD7F171C39D97B | SHA256:152BB1383A27AAE38E4A71B6394C84B8CB376DD440DE436E99C3BBC30F303AF0 | |||
| 472 | 3b63f74430f0f907111835cef9b893790d92d73f01b31ffc7658e0727fa787b4.exe | C:\kasoft\j\hspda.dll | executable | |
MD5:BAD75330D0D91AC87708A6AFFC682EE7 | SHA256:1033E6512C779ED2527927E9443339BC88CE38F76DE5F83FCFBBC5DB724D8F09 | |||
| 704 | boot.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_E0B3E71C82BFD33CB0604785B69090B6 | binary | |
MD5:0D48B4118986DFE849CAFC142E78F5F7 | SHA256:A3515DF1B106DD5180CC9B1791783AFCD2D02C145A74A9CA49AC15565E65A520 | |||
| 704 | boot.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\91EC98F1FF35B4FCD5C243F52C98A93F_A2FFEA91D55FC1B148765BF3DAB43FA9 | binary | |
MD5:1ED80EF0A63A807D2A8C950DBCF28903 | SHA256:5AB30C9127E0415655100C3D70486091030FBCDA984DA82290E022213A5F09EC | |||
| 704 | boot.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\91EC98F1FF35B4FCD5C243F52C98A93F_A2FFEA91D55FC1B148765BF3DAB43FA9 | binary | |
MD5:3A24B410519B9BDAE27859FAC1D0C5D0 | SHA256:6222781BFC44245D34E4AA24A287FA15CE1E30B4407D384285222AB533B88FF5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
55
DNS requests
21
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
704 | boot.exe | GET | 302 | 49.212.69.13:80 | http://okaka.sakura.ne.jp/j/m.exe | unknown | — | — | unknown |
2392 | svchost.exe | GET | 200 | 23.220.251.153:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
2392 | svchost.exe | GET | 200 | 23.61.29.203:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1788 | SIHClient.exe | GET | 200 | 23.61.29.203:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
1608 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
704 | boot.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSXjZmGWpL1ehpiPZo26onoT2OcqQQUEuZqJYZx7cyOaQxZGcAHvByorUsCEQDhy6r31AOBVYstBGSu3zH2 | unknown | — | — | unknown |
704 | boot.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | — | — | unknown |
1788 | SIHClient.exe | GET | 200 | 23.61.29.203:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
704 | boot.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEHQ978p4sJJelNtO%2F%2BmH4Jk%3D | unknown | — | — | unknown |
2084 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | unknown |
4364 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
4540 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5140 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
704 | boot.exe | 49.212.69.13:80 | okaka.sakura.ne.jp | SAKURA Internet Inc. | JP | unknown |
2392 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2392 | svchost.exe | 23.220.251.153:80 | crl.microsoft.com | Akamai International B.V. | US | unknown |
2392 | svchost.exe | 23.61.29.203:80 | www.microsoft.com | NTT DOCOMO, INC. | JP | unknown |
704 | boot.exe | 49.212.69.13:443 | okaka.sakura.ne.jp | SAKURA Internet Inc. | JP | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
okaka.sakura.ne.jp |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
r.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | ET MALWARE Single char EXE direct download likely trojan (multiple families) |
— | — | Potentially Bad Traffic | ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile |
— | — | A Network Trojan was detected | ET MALWARE Potential Dridex.Maldoc Minimal Executable Request |