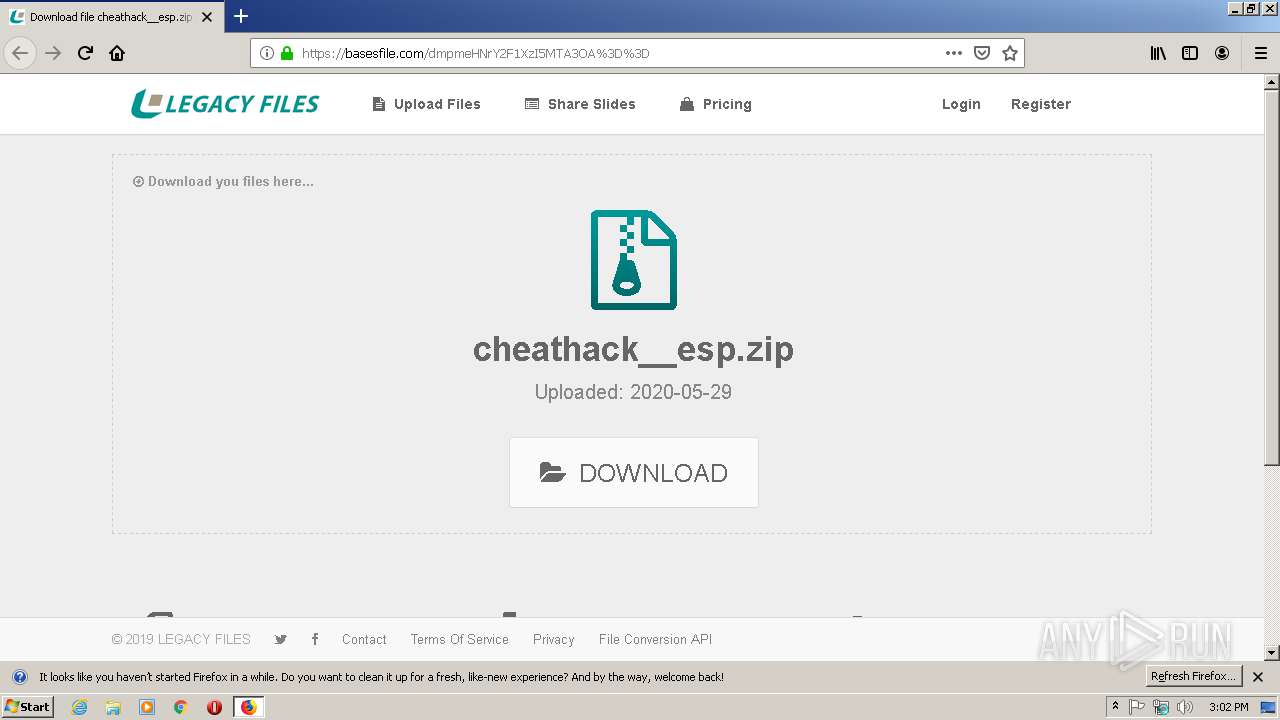
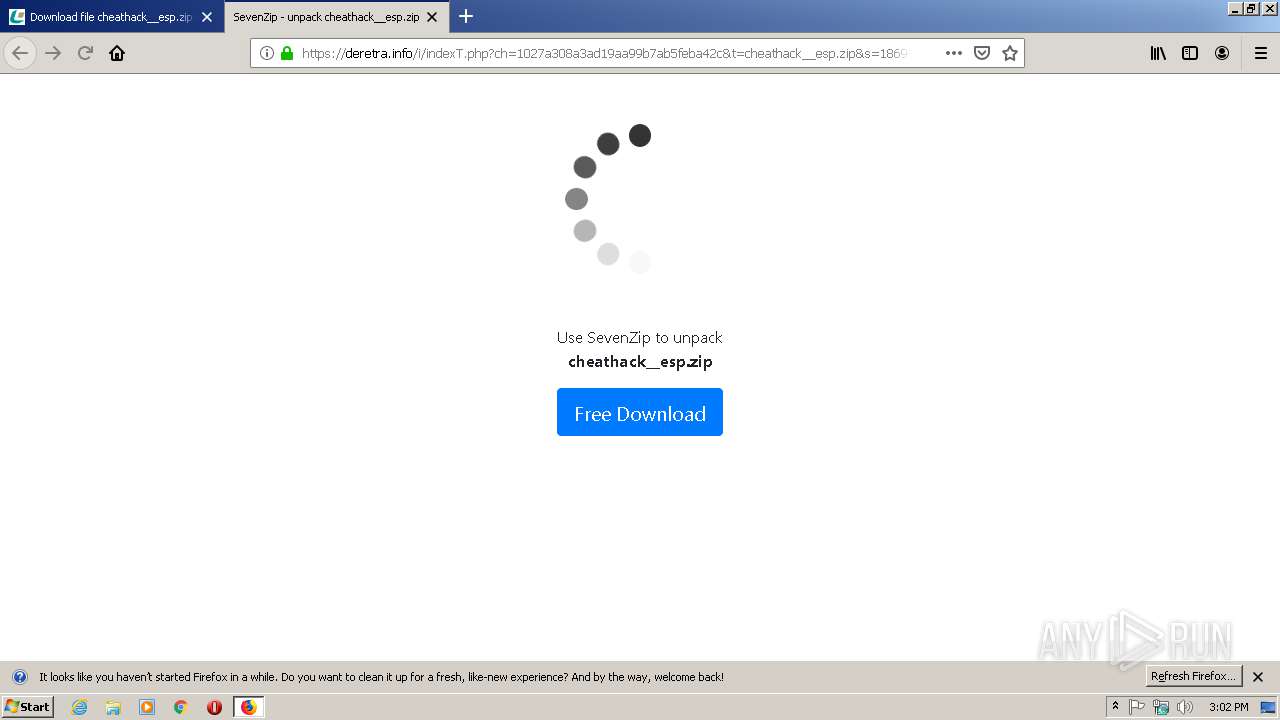
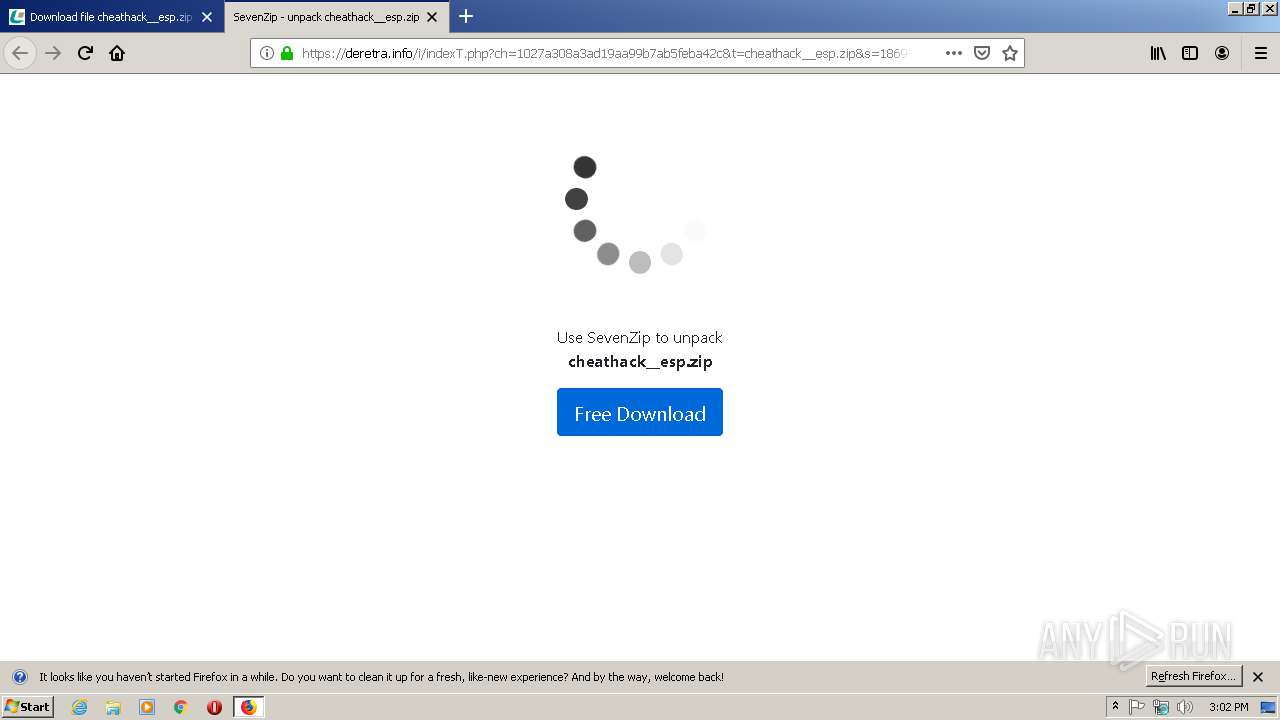
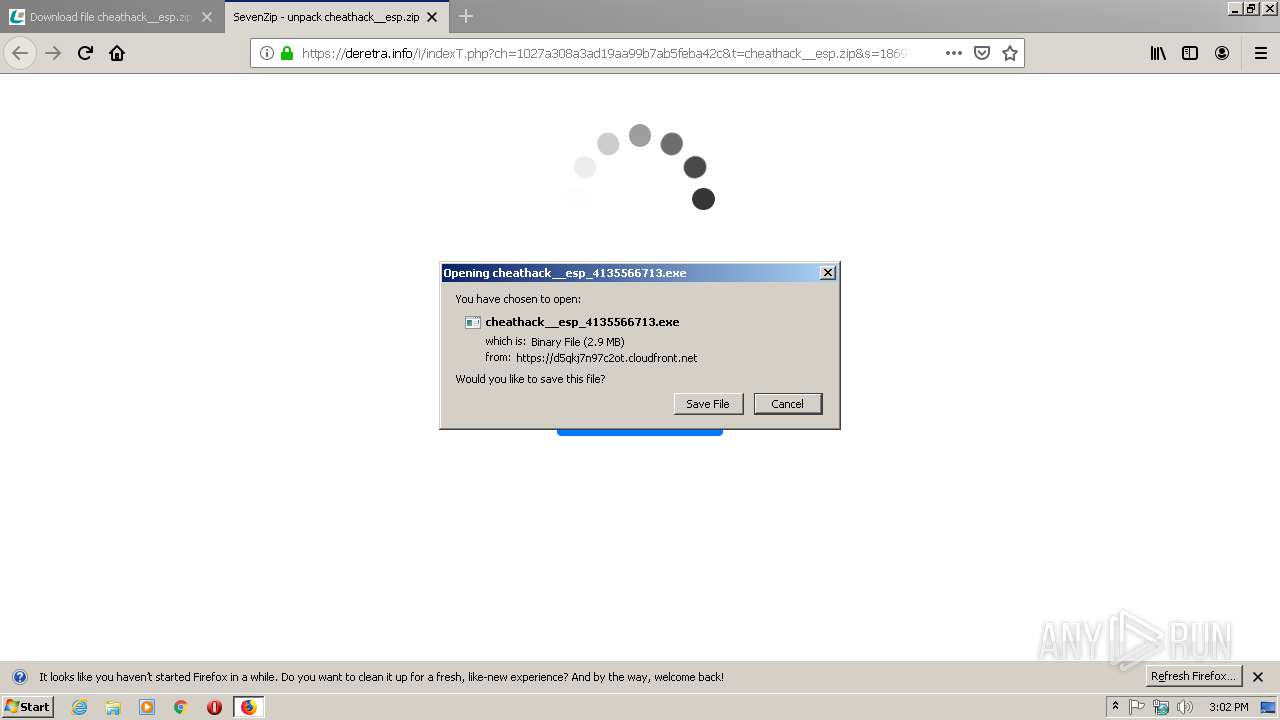
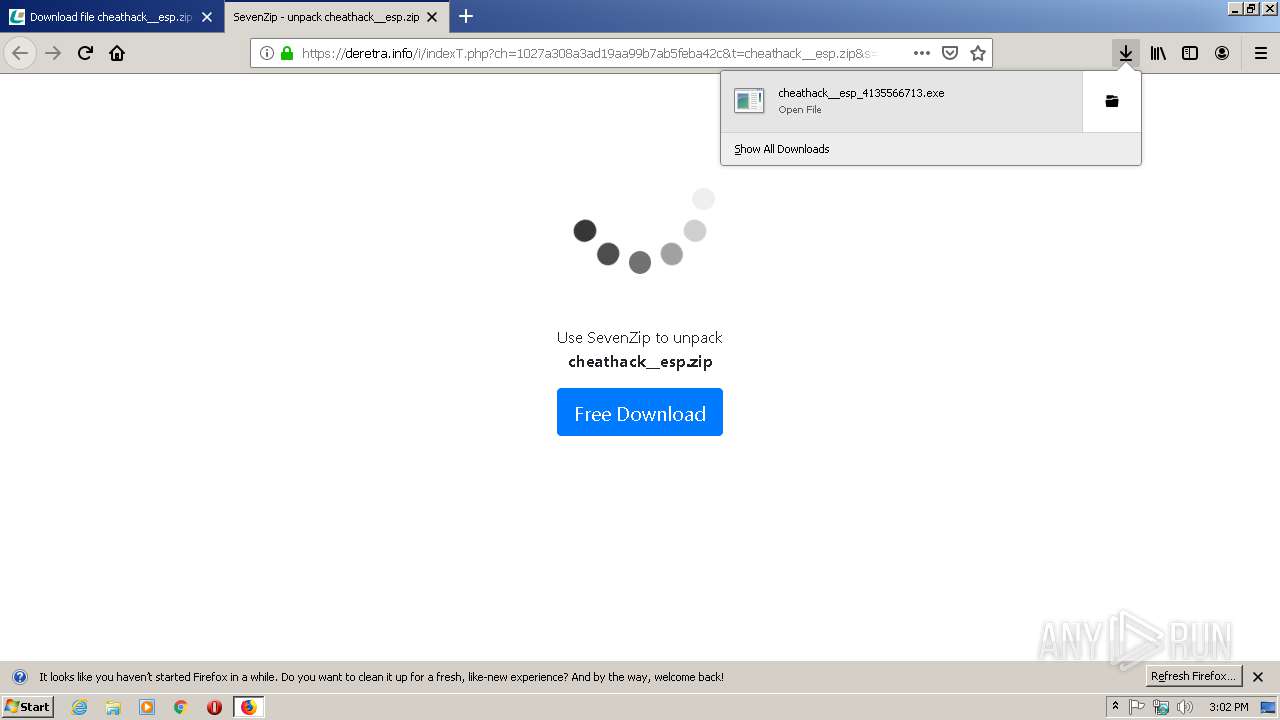
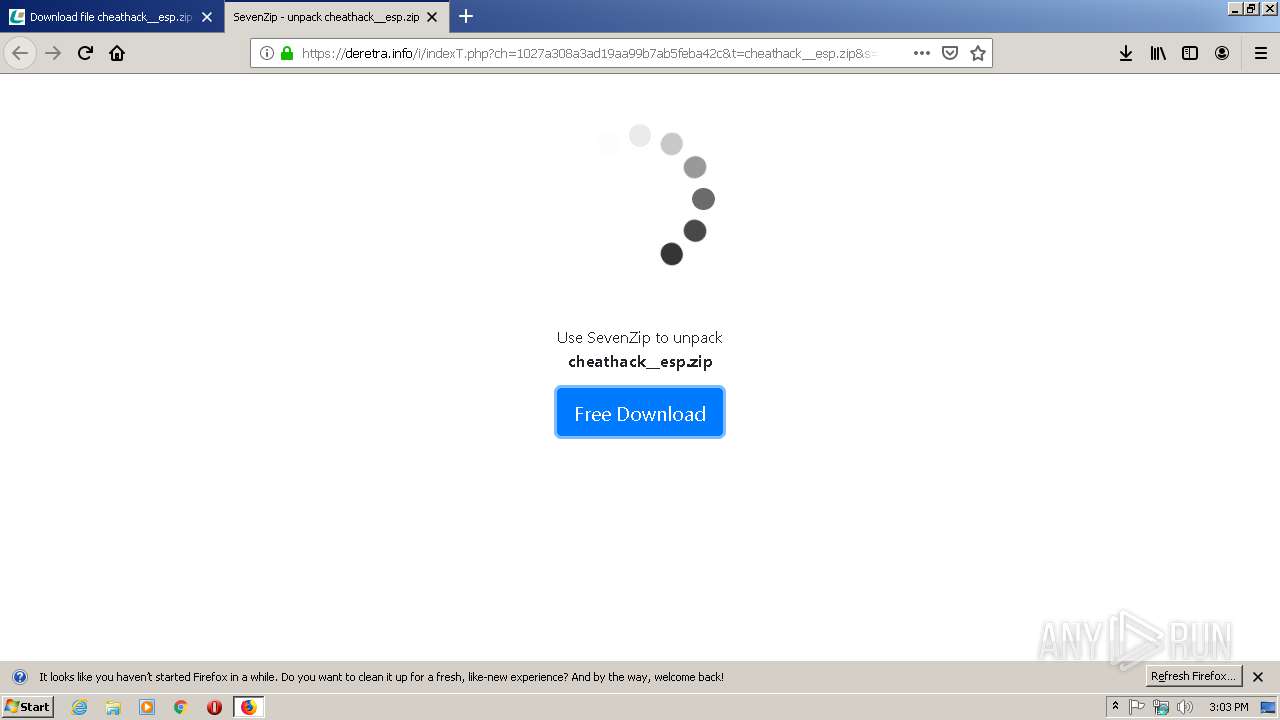
| URL: | https://clink.fun/ESP_Cheat |
| Full analysis: | https://app.any.run/tasks/612dcbdd-a0f1-490b-b213-452a3ad8ca4b |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 14:02:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8CCCE8119DE94F9B9538F9652EF82F1F |
| SHA1: | 63C00D91576984C5C1AD70AA9B4B3FCDA960041A |
| SHA256: | 3B5F4DFF49825FE8B8D50C315CB7B9B864471D25ADB98D343D21BDB0B566E48E |
| SSDEEP: | 3:N8UV3Vz1NS4:2URo4 |
MALICIOUS
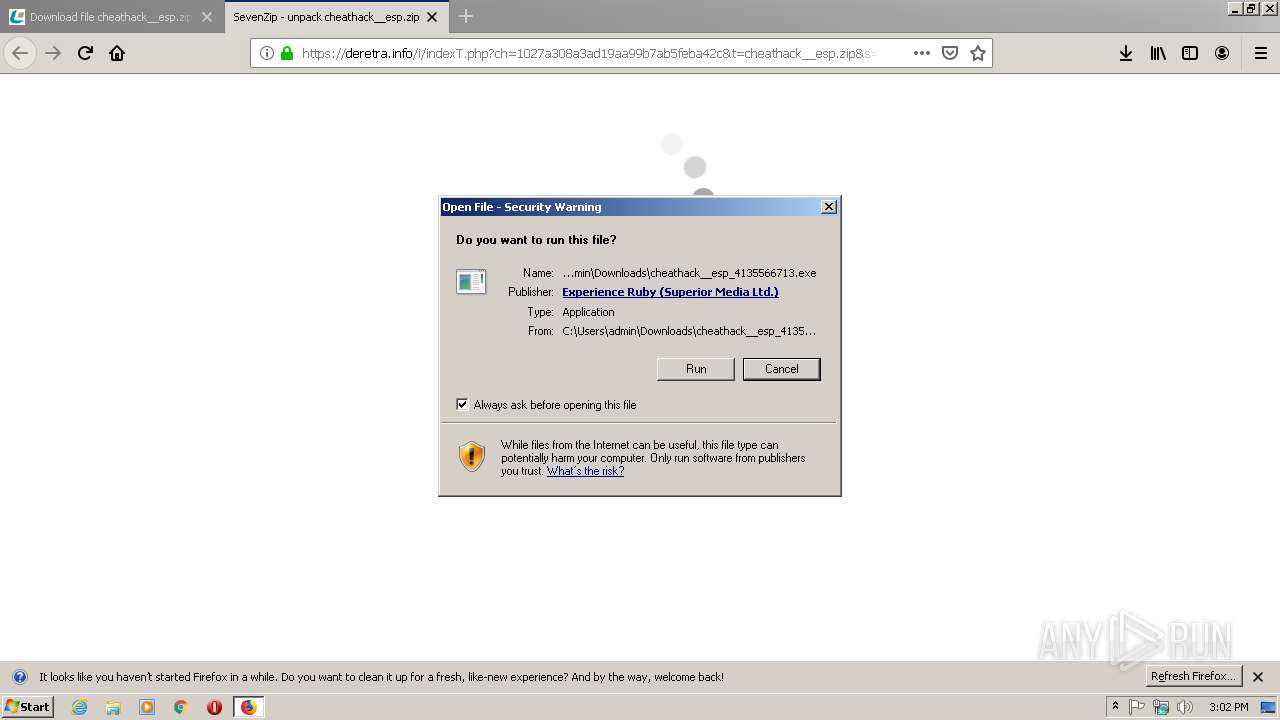
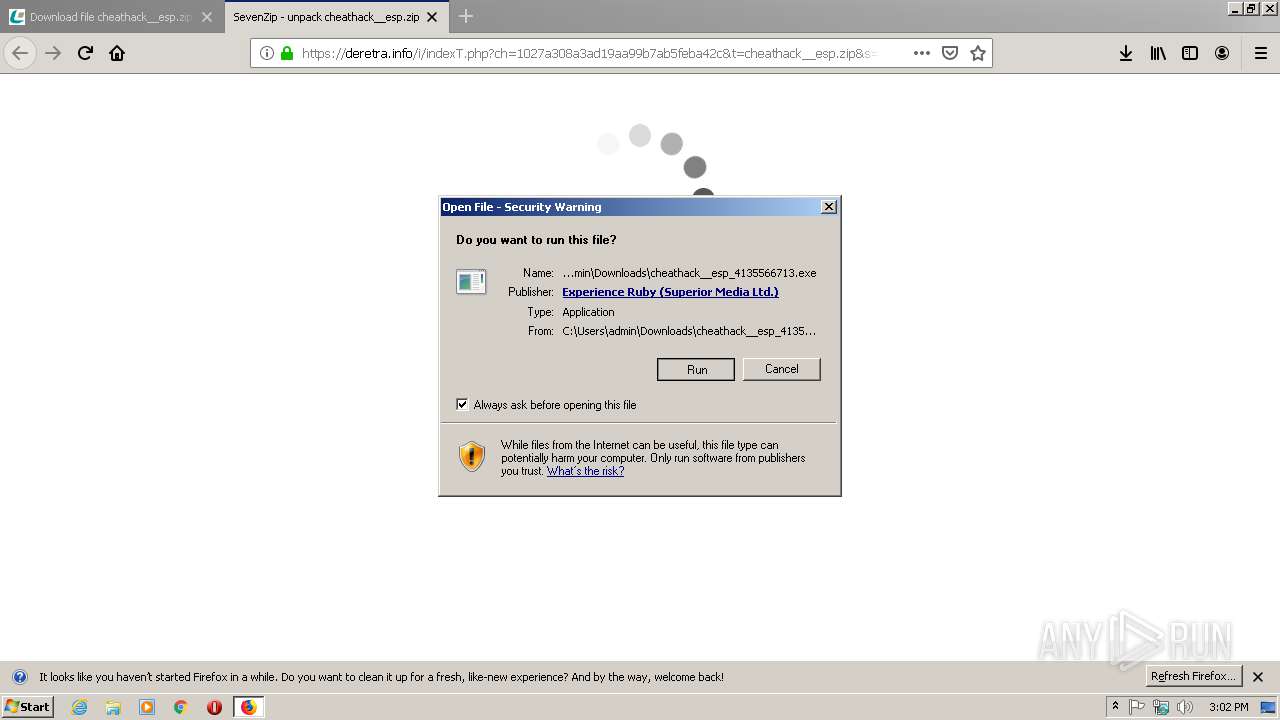
Application was dropped or rewritten from another process
- cheathack__esp_4135566713.exe (PID: 2556)
- cheathack__esp_4135566713.exe (PID: 4048)
Loads dropped or rewritten executable
- cheathack__esp_4135566713.exe (PID: 4048)
Actions looks like stealing of personal data
- cheathack__esp_4135566713.exe (PID: 4048)
Changes the autorun value in the registry
- reg.exe (PID: 3672)
SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 2680)
Application launched itself
- cheathack__esp_4135566713.exe (PID: 2556)
- Skype.exe (PID: 1688)
- Skype.exe (PID: 2696)
Executable content was dropped or overwritten
- cheathack__esp_4135566713.exe (PID: 4048)
- firefox.exe (PID: 2680)
Reads internet explorer settings
- cheathack__esp_4135566713.exe (PID: 4048)
Cleans NTFS data-stream (Zone Identifier)
- cheathack__esp_4135566713.exe (PID: 2556)
Reads Environment values
- cheathack__esp_4135566713.exe (PID: 4048)
Creates files in the user directory
- Skype.exe (PID: 1688)
Reads CPU info
- Skype.exe (PID: 1688)
Uses REG.EXE to modify Windows registry
- Skype.exe (PID: 1688)
Modifies the open verb of a shell class
- Skype.exe (PID: 1688)
INFO
Application launched itself
- firefox.exe (PID: 620)
- firefox.exe (PID: 2680)
Creates files in the user directory
- firefox.exe (PID: 2680)
Reads Internet Cache Settings
- firefox.exe (PID: 2680)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 2680)
Reads settings of System Certificates
- firefox.exe (PID: 2680)
Reads CPU info
- firefox.exe (PID: 2680)
Manual execution by user
- Skype.exe (PID: 1688)
Reads the hosts file
- Skype.exe (PID: 1688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
14
Malicious processes
4
Suspicious processes
1
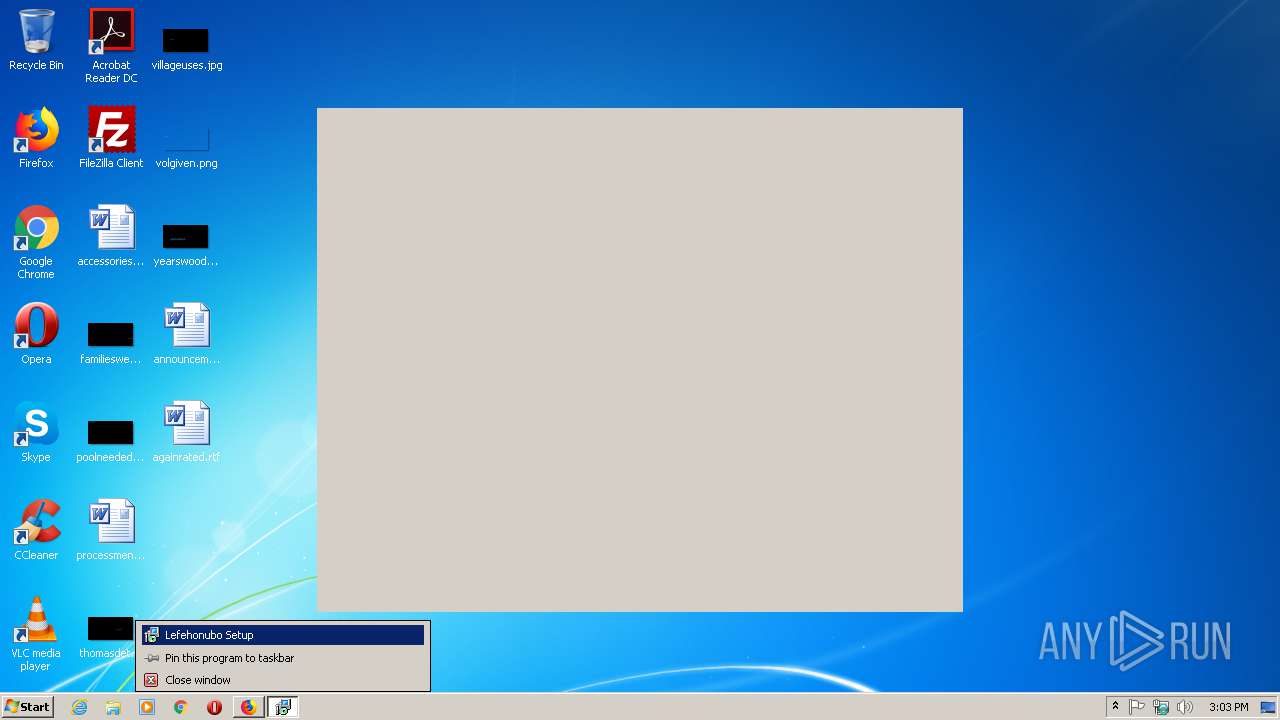
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 620 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://clink.fun/ESP_Cheat" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1624 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2680.0.855471711\1024947542" -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2680 "\\.\pipe\gecko-crash-server-pipe.2680" 1180 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | explorer.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2680.20.1998521164\423762057" -childID 3 -isForBrowser -prefsHandle 3700 -prefMapHandle 3704 -prefsLen 6719 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2680 "\\.\pipe\gecko-crash-server-pipe.2680" 3724 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2400 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | Skype.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
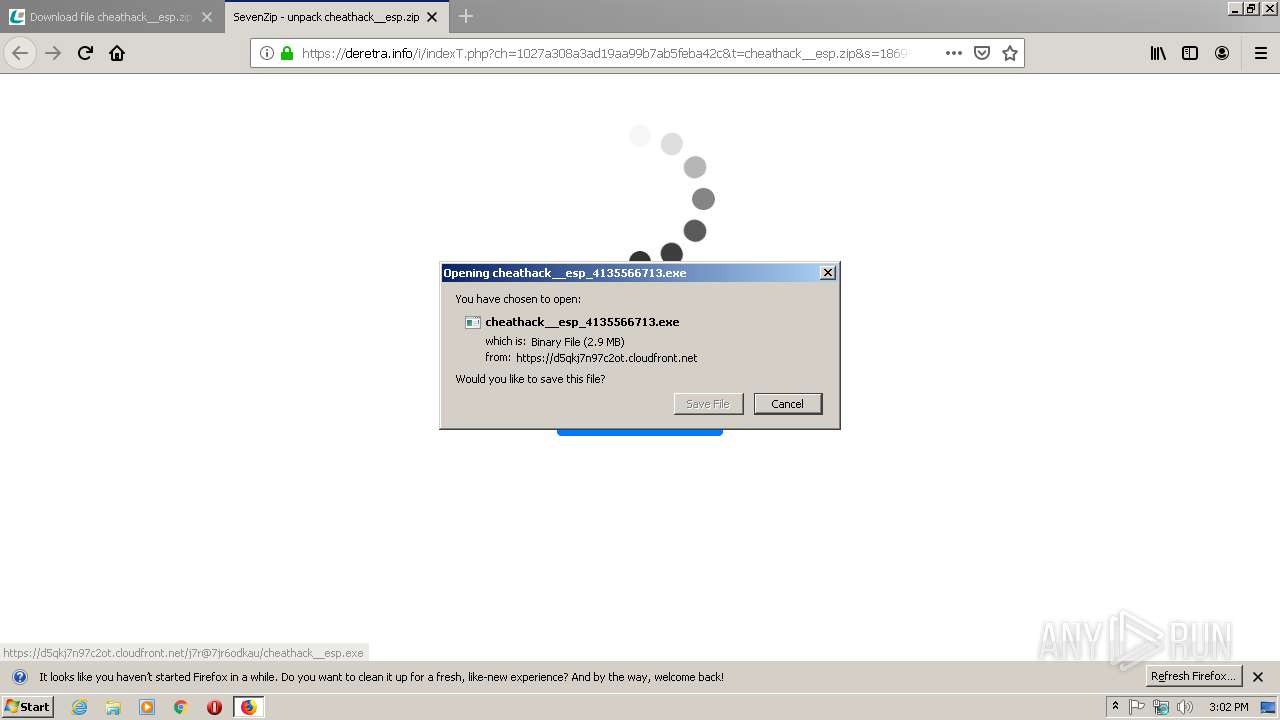
| 2556 | "C:\Users\admin\Downloads\cheathack__esp_4135566713.exe" | C:\Users\admin\Downloads\cheathack__esp_4135566713.exe | — | firefox.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Lefehonubo Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2680.13.572613367\1175084076" -childID 2 -isForBrowser -prefsHandle 2776 -prefMapHandle 2844 -prefsLen 5997 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2680 "\\.\pipe\gecko-crash-server-pipe.2680" 2848 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2680 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://clink.fun/ESP_Cheat | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2696 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --type=renderer --ms-disable-indexeddb-transaction-timeout --no-sandbox --service-pipe-token=16F29DEFE6AD81F545FB71D951126CAE --lang=en-US --app-user-model-id=Microsoft.Skype.SkypeDesktop --app-path="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar" --node-integration=false --webview-tag=true --no-sandbox --preload="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar\Preload.js" --context-id=2 --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=16F29DEFE6AD81F545FB71D951126CAE --renderer-client-id=3 --mojo-platform-channel-handle=1576 /prefetch:1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | — | Skype.exe | |||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
| 3004 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2680.3.72641863\422267731" -childID 1 -isForBrowser -prefsHandle 1736 -prefMapHandle 1732 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2680 "\\.\pipe\gecko-crash-server-pipe.2680" 1756 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
Total events
1 950
Read events
1 895
Write events
55
Delete events
0
Modification events
| (PID) Process: | (2680) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 415B7D0000000000 | |||
| (PID) Process: | (620) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 405B7D0000000000 | |||
| (PID) Process: | (2680) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (2680) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2680) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2680) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2680) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (2680) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
| (PID) Process: | (2680) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dnsapi.dll,-103 |
Value: Domain Name System (DNS) Server Trust | |||
| (PID) Process: | (2680) firefox.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-843 |
Value: BitLocker Drive Encryption | |||
Executable files
5
Suspicious files
97
Text files
99
Unknown types
57
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2680 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2680 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2680 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2680 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2680 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2680 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 2680 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 2680 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 2680 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 2680 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\FD6F44C81A06EA91EF69FA6D9C542F2D90E54400 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
42
DNS requests
106
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
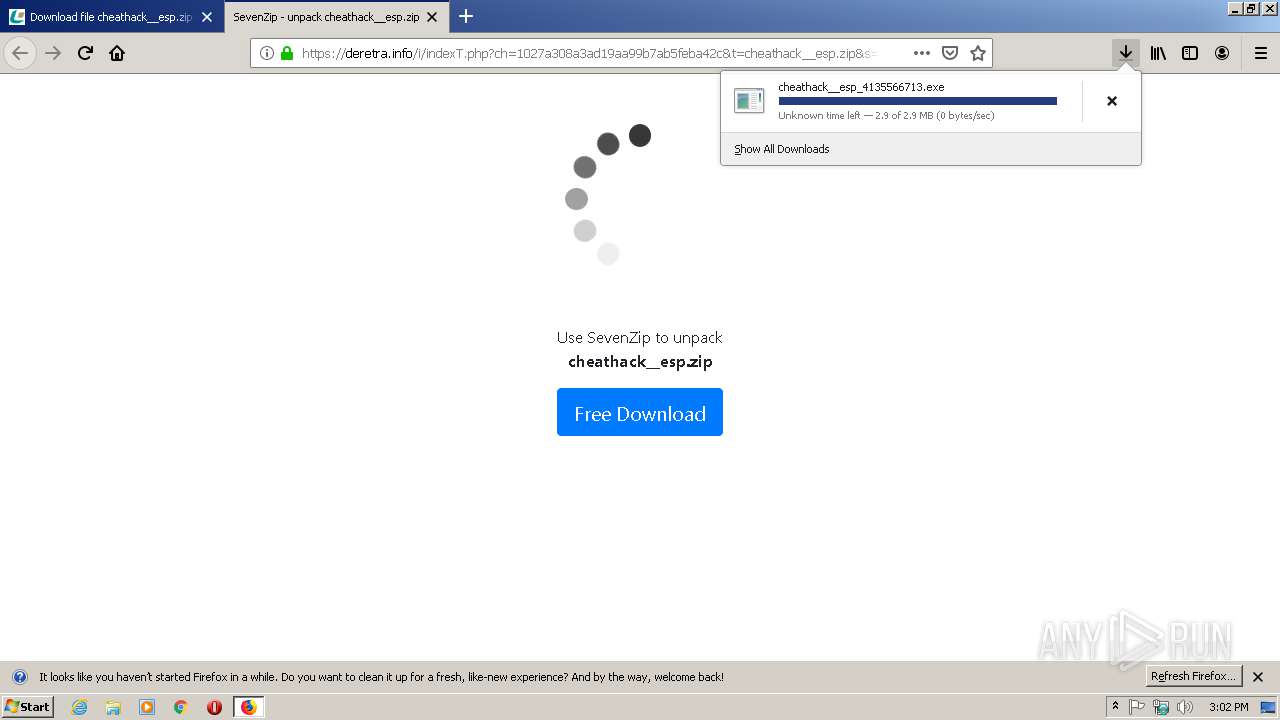
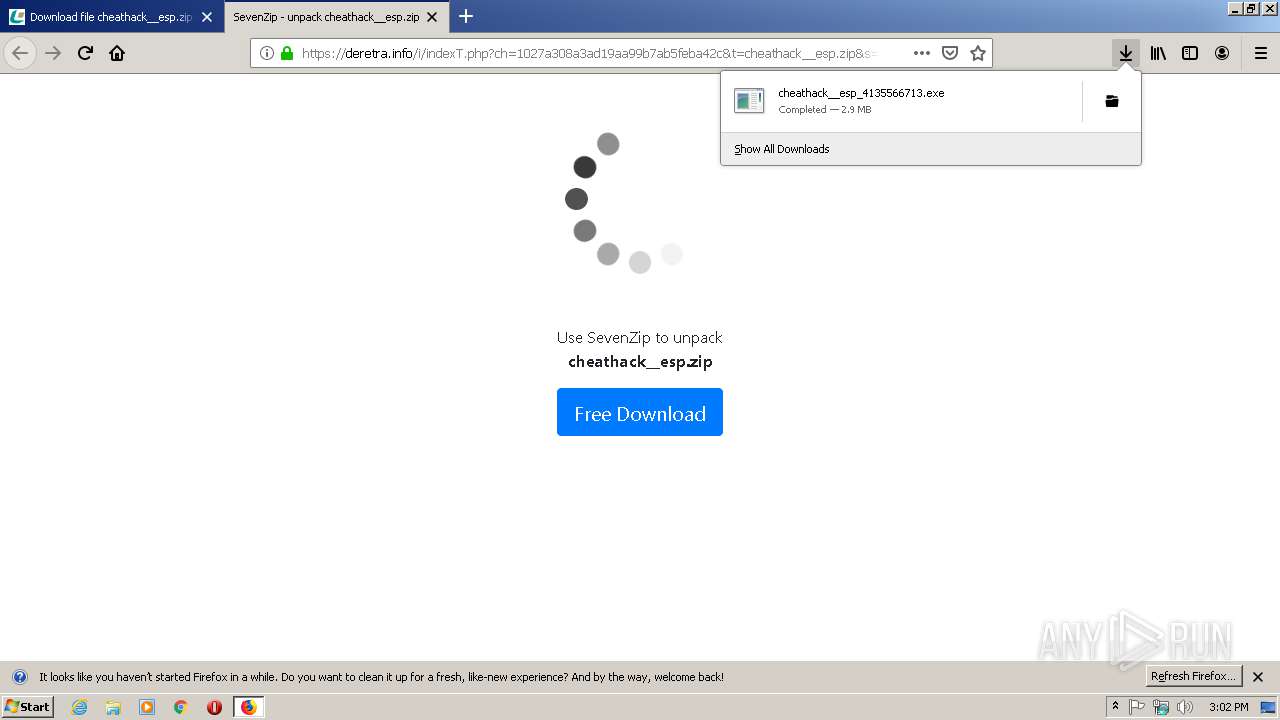
4048 | cheathack__esp_4135566713.exe | POST | 200 | 13.35.254.111:80 | http://mysql.bekottff-sos.com/ | US | text | 1.23 Kb | whitelisted |
2680 | firefox.exe | POST | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsrsadvsslca2018 | US | der | 1.49 Kb | whitelisted |
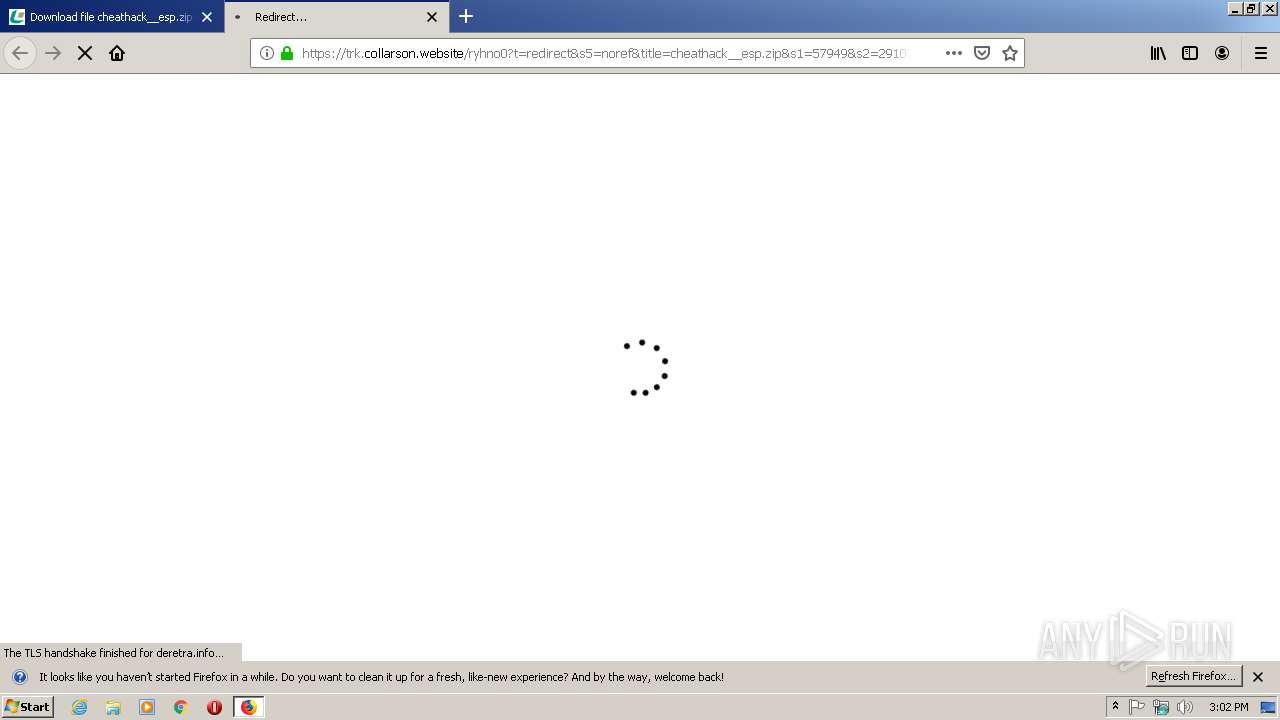
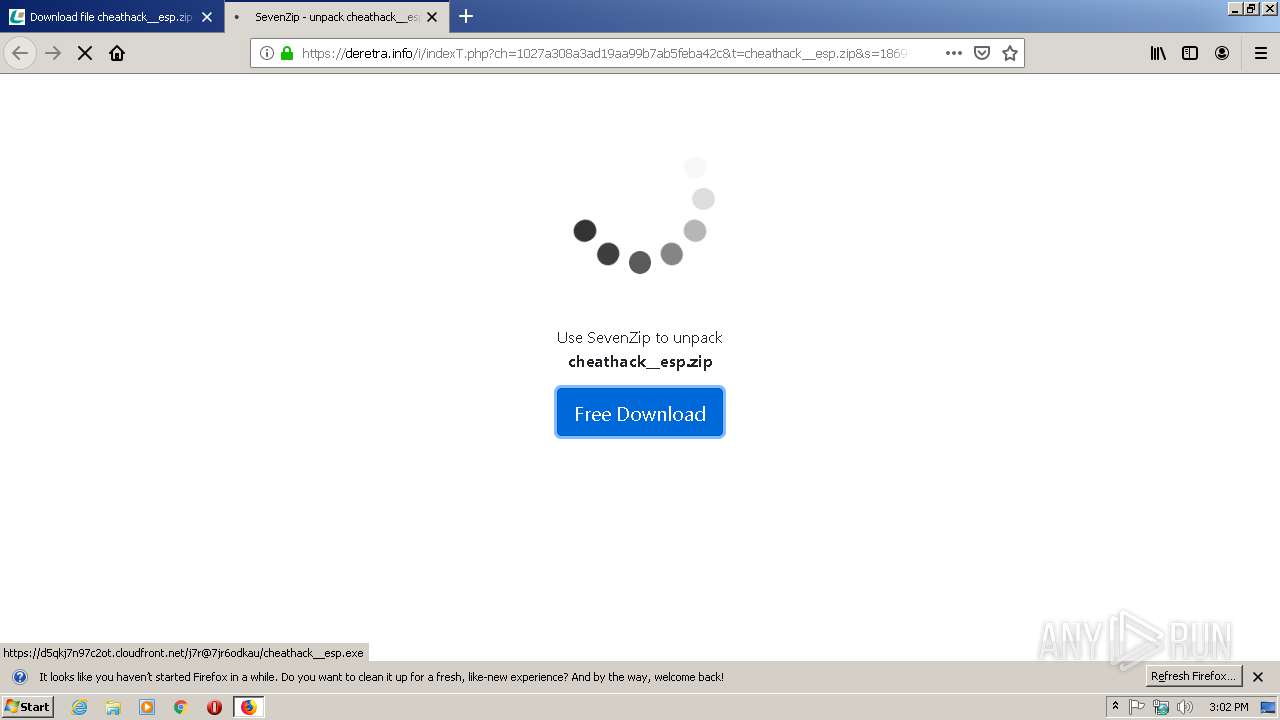
2680 | firefox.exe | GET | 302 | 18.202.12.61:80 | http://trk.sparkrainstorm.host/aff_r?offer_id=195&aff_id=1869&url=https%3A%2F%2Fderetra.info%2Fi%2FindexT.php%3Fch%3D1027a308a3ad19aa99b7ab5feba42c%26t%3Dcheathack__esp.zip%26s%3D1869-57949&urlauth=750253950417604457728410299276 | US | html | 293 b | shared |
2680 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
4048 | cheathack__esp_4135566713.exe | POST | 200 | 13.35.254.76:80 | http://www1.bekottff-sos.com/ | US | — | — | whitelisted |
2680 | firefox.exe | POST | 200 | 143.204.208.173:80 | http://ocsp.sca1b.amazontrust.com/ | US | der | 471 b | whitelisted |
2680 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://ocsp.pki.goog/gts1o1 | US | der | 471 b | whitelisted |
4048 | cheathack__esp_4135566713.exe | POST | 200 | 13.35.254.45:80 | http://www1.bekottff-sos.com/ | US | — | — | whitelisted |
4048 | cheathack__esp_4135566713.exe | POST | 200 | 143.204.201.118:80 | http://media.bekottff-sos.com/ | US | binary | 892 Kb | whitelisted |
2680 | firefox.exe | GET | 302 | 18.202.12.61:80 | http://trk.sparkrainstorm.host/aff_c?source=1869-57949&offer_id=195&aff_click_id=&aff_id=1869&aff_sub=57949&aff_sub2=291078&aff_sub3=Windows_7|Firefox&aff_sub4=basesfile.com&aff_sub5=noref&aff_unique1=&aff_unique2=&aff_unique3=&name=cheathack__esp.zip&url=&url_id=12 | US | html | 394 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2680 | firefox.exe | 2.16.107.58:80 | detectportal.firefox.com | Akamai International B.V. | — | suspicious |
2680 | firefox.exe | 52.41.191.52:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2680 | firefox.exe | 37.140.192.184:443 | clink.fun | Domain names registrar REG.RU, Ltd | RU | unknown |
2680 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2680 | firefox.exe | 172.67.153.211:443 | orssmante.space | — | US | malicious |
2680 | firefox.exe | 172.67.177.186:443 | trk.collarson.website | — | US | unknown |
2680 | firefox.exe | 18.202.12.61:80 | trk.sparkrainstorm.host | — | US | shared |
2680 | firefox.exe | 104.31.82.45:443 | deretra.info | Cloudflare Inc | US | shared |
2680 | firefox.exe | 209.197.3.15:443 | maxcdn.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
2680 | firefox.exe | 209.197.3.24:443 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
clink.fun |
| suspicious |
ocsp.digicert.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
Process | Message |
|---|---|
Skype.exe | [4000:4044:0530/150325.982:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1]
|
Skype.exe | [4000:4044:0530/150325.982:VERBOSE1:crash_service.cc(145)] window handle is 00020136
|
Skype.exe | [4000:2228:0530/150325.998:VERBOSE1:crash_service.cc(333)] client start. pid = 1688
|
Skype.exe | [4000:4044:0530/150325.998:VERBOSE1:crash_service.cc(300)] pipe name is \\.\pipe\skype-preview Crash Service
dumps at C:\Users\admin\AppData\Local\Temp\skype-preview Crashes
|
Skype.exe | [4000:4044:0530/150325.998:VERBOSE1:crash_service_main.cc(94)] Ready to process crash requests
|
Skype.exe | [4000:4044:0530/150325.998:VERBOSE1:crash_service.cc(304)] checkpoint is C:\Users\admin\AppData\Local\Temp\skype-preview Crashes\crash_checkpoint.txt
server is https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload
maximum 128 reports/day
reporter is electron-crash-service
|
Skype.exe | [4000:2228:0530/150328.542:VERBOSE1:crash_service.cc(333)] client start. pid = 2696
|
Skype.exe | [2400:1284:0530/150328.819:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1]
|
Skype.exe | [2400:1284:0530/150328.820:VERBOSE1:crash_service.cc(300)] pipe name is \\.\pipe\skype-preview Crash Service
dumps at C:\Users\admin\AppData\Local\Temp\skype-preview Crashes
|
Skype.exe | [2400:1284:0530/150328.820:VERBOSE1:crash_service.cc(145)] window handle is 000101AA
|