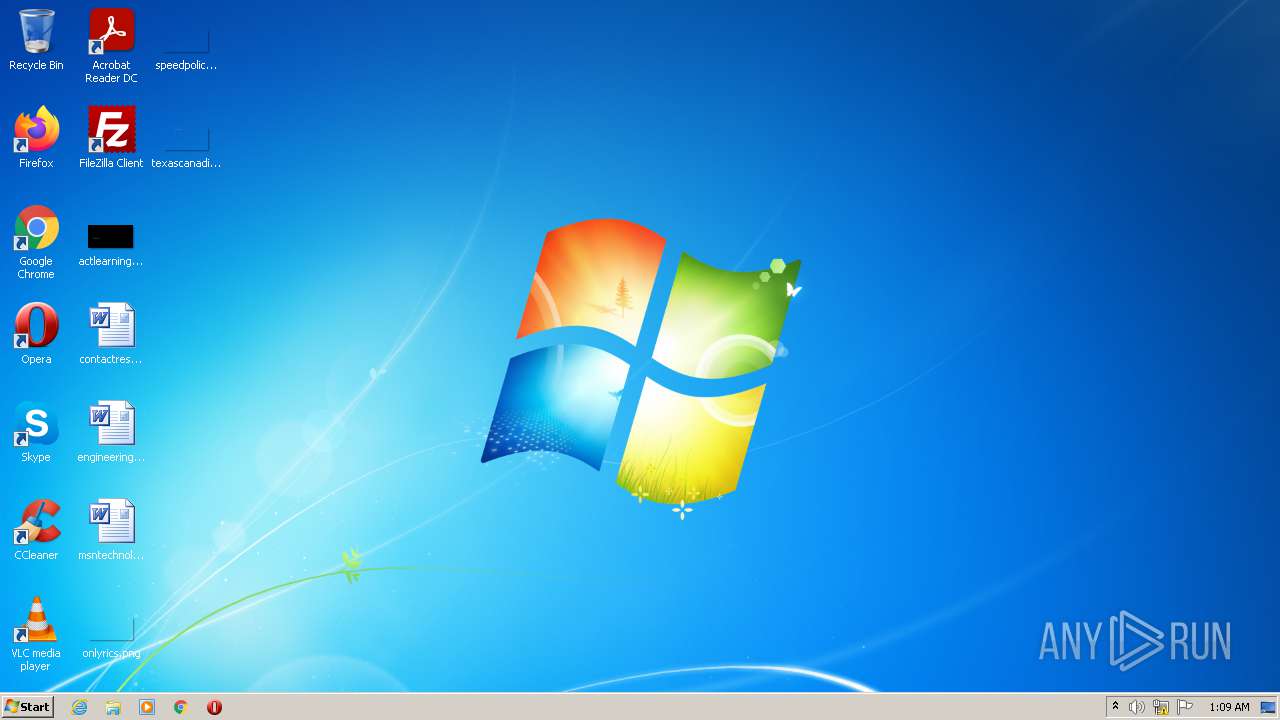
| File name: | winlogon.exe |
| Full analysis: | https://app.any.run/tasks/d761e088-9de4-4a68-9d9f-0e2b6925b021 |
| Verdict: | Malicious activity |
| Analysis date: | October 26, 2021, 00:09:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 0D9607205A552FFE78CC6C30B234F776 |
| SHA1: | 6CA00928C9C057D73384BDF3FCD07470998A3874 |
| SHA256: | 3B55F30BFA5A319D7A32282982B41CFD08A731AE4AAC179B07C5D218C023F1D9 |
| SSDEEP: | 12288:N+cM8MQoaCtkzmKCNa2EdmrlTT6zncVUJ7vn:kcJoRtWmK92pTT6DN |
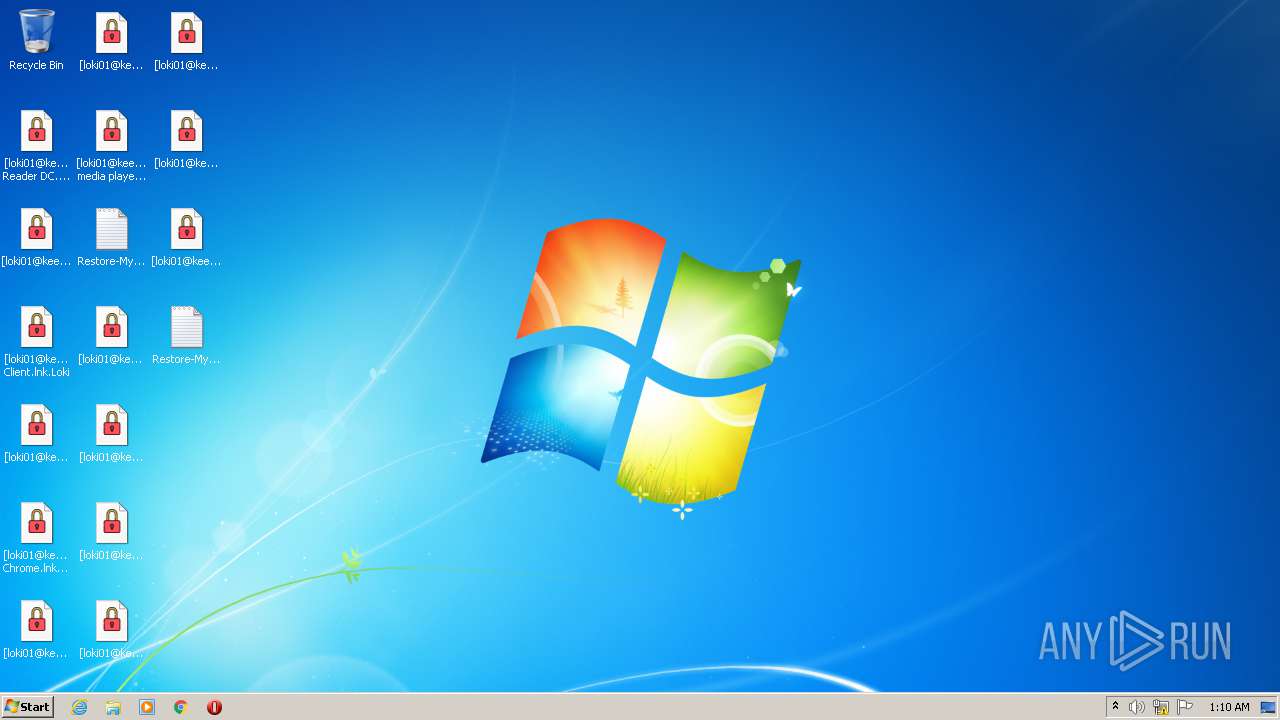
MALICIOUS
Changes the autorun value in the registry
- winlogon.exe (PID: 3556)
- winlogon.exe (PID: 2548)
Starts Visual C# compiler
- winlogon.exe (PID: 3556)
- winlogon.exe (PID: 2548)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 2900)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2976)
- wbengine.exe (PID: 2456)
Writes to a start menu file
- winlogon.exe (PID: 3556)
- winlogon.exe (PID: 2548)
Drops executable file immediately after starts
- csc.exe (PID: 2068)
- winlogon.exe (PID: 2548)
- csc.exe (PID: 2076)
Deletes shadow copies
- cmd.exe (PID: 2876)
- cmd.exe (PID: 2720)
- cmd.exe (PID: 1940)
Turns off the firewall via NETSH.EXE
- cmd.exe (PID: 3088)
Starts BCDEDIT.EXE to disable recovery
- cmd.exe (PID: 1108)
Runs injected code in another process
- wbadmin.exe (PID: 2172)
Application was injected by another process
- SearchIndexer.exe (PID: 2276)
- svchost.exe (PID: 876)
- svchost.exe (PID: 1096)
Disables Windows Defender
- winlogon.exe (PID: 2548)
SUSPICIOUS
Checks supported languages
- winlogon.exe (PID: 3556)
- cmd.exe (PID: 2900)
- cvtres.exe (PID: 1876)
- winlogon.exe (PID: 2548)
- csc.exe (PID: 2076)
- cvtres.exe (PID: 3420)
- csc.exe (PID: 2068)
- cmd.exe (PID: 2768)
- cmd.exe (PID: 1940)
- cmd.exe (PID: 2876)
- cmd.exe (PID: 2720)
- WMIC.exe (PID: 2272)
- cmd.exe (PID: 3088)
- cmd.exe (PID: 1108)
- cmd.exe (PID: 2216)
- cmd.exe (PID: 456)
Drops a file with too old compile date
- winlogon.exe (PID: 3556)
- winlogon.exe (PID: 2548)
Creates files in the user directory
- winlogon.exe (PID: 3556)
Reads the computer name
- winlogon.exe (PID: 3556)
- winlogon.exe (PID: 2548)
- WMIC.exe (PID: 2272)
Creates files in the Windows directory
- svchost.exe (PID: 876)
- winlogon.exe (PID: 2548)
- wbadmin.exe (PID: 2172)
Creates files in the program directory
- csc.exe (PID: 2068)
- winlogon.exe (PID: 3556)
- winlogon.exe (PID: 2548)
- csc.exe (PID: 2076)
- SearchIndexer.exe (PID: 2276)
Executable content was dropped or overwritten
- winlogon.exe (PID: 3556)
- csc.exe (PID: 2068)
- winlogon.exe (PID: 2548)
- csc.exe (PID: 2076)
Drops a file with a compile date too recent
- csc.exe (PID: 2068)
- csc.exe (PID: 2076)
- winlogon.exe (PID: 2548)
Application launched itself
- winlogon.exe (PID: 3556)
Starts CMD.EXE for commands execution
- winlogon.exe (PID: 3556)
- winlogon.exe (PID: 2548)
Changes default file association
- winlogon.exe (PID: 2548)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 3088)
- cmd.exe (PID: 456)
Executed as Windows Service
- vssvc.exe (PID: 1248)
- wbengine.exe (PID: 2456)
- vds.exe (PID: 3920)
Reads Environment values
- netsh.exe (PID: 820)
- netsh.exe (PID: 1356)
Executed via COM
- DllHost.exe (PID: 3760)
- vdsldr.exe (PID: 1872)
Writes to a desktop.ini file (may be used to cloak folders)
- winlogon.exe (PID: 2548)
INFO
Reads the computer name
- schtasks.exe (PID: 2976)
- vssadmin.exe (PID: 1844)
- wbadmin.exe (PID: 1408)
- vssvc.exe (PID: 1248)
- netsh.exe (PID: 820)
- netsh.exe (PID: 1356)
- wbengine.exe (PID: 2456)
- vdsldr.exe (PID: 1872)
- vds.exe (PID: 3920)
- wbadmin.exe (PID: 2172)
- DllHost.exe (PID: 3760)
Checks supported languages
- schtasks.exe (PID: 2976)
- svchost.exe (PID: 876)
- vssadmin.exe (PID: 1844)
- wbadmin.exe (PID: 2172)
- bcdedit.exe (PID: 3524)
- netsh.exe (PID: 820)
- wbadmin.exe (PID: 1408)
- bcdedit.exe (PID: 656)
- netsh.exe (PID: 1356)
- vssvc.exe (PID: 1248)
- DllHost.exe (PID: 3760)
- wbengine.exe (PID: 2456)
- vdsldr.exe (PID: 1872)
- vds.exe (PID: 3920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (64.5) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (13.6) |
| .exe | | | Win32 Executable (generic) (9.3) |
| .exe | | | Win16/32 Executable Delphi generic (4.2) |
| .exe | | | Generic Win/DOS Executable (4.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2041:02:25 03:01:34+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 321024 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8608a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Microsoft |
| FileDescription: | svchost |
| FileVersion: | 1.0.0.0 |
| InternalName: | svchost.exe |
| LegalCopyright: | Copyright © 2021 |
| LegalTrademarks: | - |
| OriginalFileName: | svchost.exe |
| ProductName: | svchost |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.2.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jan-1905 19:33:18 |
| Comments: | - |
| CompanyName: | Microsoft |
| FileDescription: | svchost |
| FileVersion: | 1.0.0.0 |
| InternalName: | svchost.exe |
| LegalCopyright: | Copyright © 2021 |
| LegalTrademarks: | - |
| OriginalFilename: | svchost.exe |
| ProductName: | svchost |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.2.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 19-Jan-1905 19:33:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
*\x13?\x0d?\x17?\x02$f\x01 | 0x00002000 | 0x00016624 | 0x00016800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.51749 |
T&d\x1b{/.\x05$f\x01 | 0x0001A000 | 0x00016624 | 0x00016800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99761 |
.text | 0x00032000 | 0x0004E300 | 0x0004E400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.26152 |
.rsrc | 0x00082000 | 0x000005A8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.07478 |
.reloc | 0x00084000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
.RVA | 0x00086000 | 0x000000DB | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0.769849 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
82
Monitored processes
32
Malicious processes
6
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Windows\System32\cmd.exe" /C netsh firewall set opmode mode=disable | C:\Windows\System32\cmd.exe | — | winlogon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 656 | bcdedit /set {default} recoveryenabled no | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 820 | netsh advfirewall set currentprofile state off | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 876 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\system32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1096 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\system32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1108 | "C:\Windows\System32\cmd.exe" /C bcdedit /set {default} recoveryenabled no | C:\Windows\System32\cmd.exe | — | winlogon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1248 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft� Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1356 | netsh firewall set opmode mode=disable | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1408 | wbadmin delete catalog -quiet | C:\Windows\system32\wbadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft� BLB Backup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1844 | vssadmin delete shadows /all /quiet | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft� Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 260
Read events
5 036
Write events
224
Delete events
0
Modification events
| (PID) Process: | (3556) winlogon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3556) winlogon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3556) winlogon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3556) winlogon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3556) winlogon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3556) winlogon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3556) winlogon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3556) winlogon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3556) winlogon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3556) winlogon.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
Executable files
7
Suspicious files
1 013
Text files
238
Unknown types
35
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3556 | winlogon.exe | C:\Users\admin\AppData\Local\Temp\ryh4guri.cmdline | text | |
MD5:— | SHA256:— | |||
| 876 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 2068 | csc.exe | C:\ProgramData\n3uegcx4.exe | executable | |
MD5:— | SHA256:— | |||
| 876 | svchost.exe | C:\Windows\System32\Tasks\Loki | xml | |
MD5:— | SHA256:— | |||
| 2068 | csc.exe | C:\ProgramData\CSCD8CE1FF589EA4271B1D657AD4D95540.TMP | res | |
MD5:— | SHA256:— | |||
| 1876 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RESD441.tmp | o | |
MD5:— | SHA256:— | |||
| 2068 | csc.exe | C:\Users\admin\AppData\Local\Temp\ryh4guri.out | text | |
MD5:— | SHA256:— | |||
| 2076 | csc.exe | C:\ProgramData\CSCF18F00115E9A40079CA1305020A1A58D.TMP | res | |
MD5:— | SHA256:— | |||
| 2548 | winlogon.exe | C:\Users\admin\AppData\Local\Temp\hrsqve15.cmdline | text | |
MD5:— | SHA256:— | |||
| 3556 | winlogon.exe | C:\Users\admin\AppData\Local\Temp\zqpn1wjz.ico | image | |
MD5:DBC49B5F7714255217080C2E81F05A99 | SHA256:6D2F1F6164CBD331B9DC43B37948372E21B2EE45407AA99E199693835CDED09C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
13
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3556 | winlogon.exe | POST | 200 | 91.223.82.6:80 | http://loki-locker.one/index.php | NL | text | 600 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.1:445 | — | — | — | unknown |
— | — | 192.168.100.2:139 | — | — | — | whitelisted |
3556 | winlogon.exe | 91.223.82.6:80 | loki-locker.one | Iws Networks LLC | NL | malicious |
— | — | 192.168.100.1:139 | — | — | — | unknown |
— | — | 192.168.100.2:445 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
loki-locker.one |
| malicious |