| File name: | Deluxe RDP Cracker.rar |
| Full analysis: | https://app.any.run/tasks/9484a5d7-330d-4858-a968-4fe43a5f3bc9 |
| Verdict: | Malicious activity |
| Analysis date: | March 11, 2019, 15:12:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
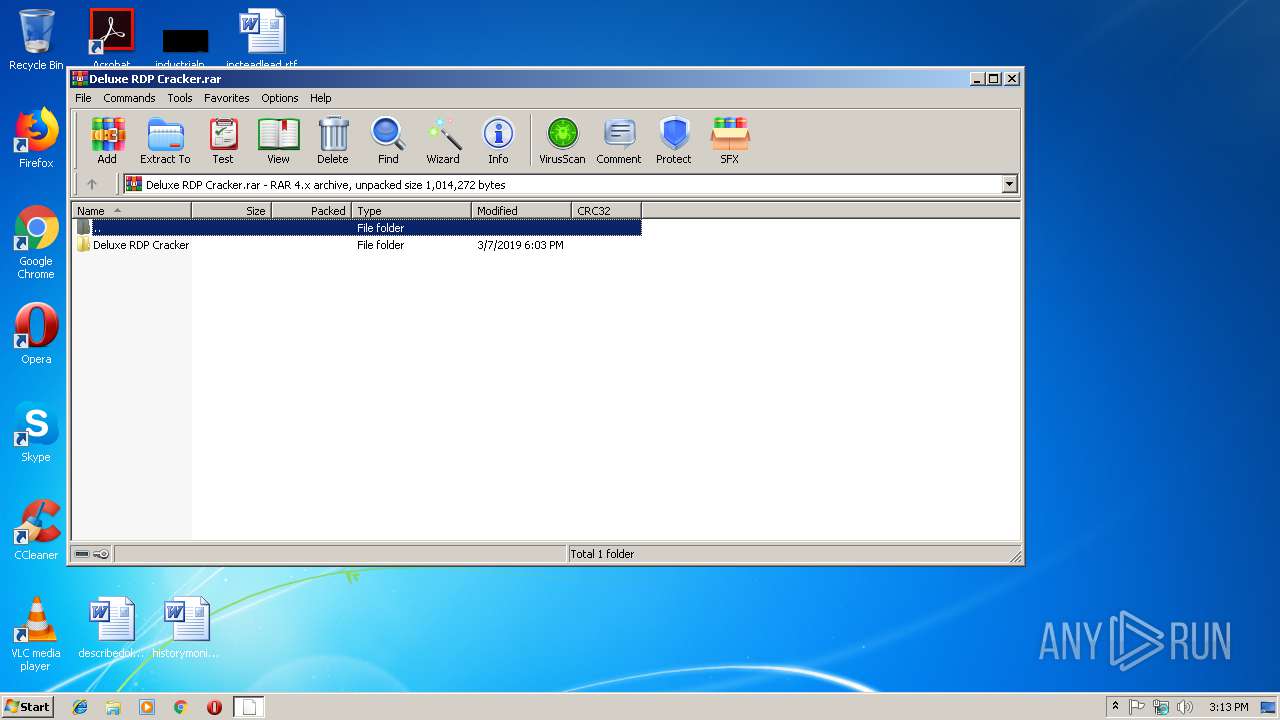
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 6BB500C58C2A8EEAECCE6354DAFE5103 |
| SHA1: | E2FC1DF51834CEC803B231434D9900411370E5FF |
| SHA256: | 3B49093F7DD4DD67C719652EDEF7157F92749E0803D865DA36476E0DF66DF8E0 |
| SSDEEP: | 6144:1tR4ubdD6QRcMWrfcZwrPhqysZ0HJDxiwhM80age6C4bToZv+hIKR3+i2RY2MvXl:ZbXRcTcmsCHpxisM80age6fAnKRuttm |
MALICIOUS
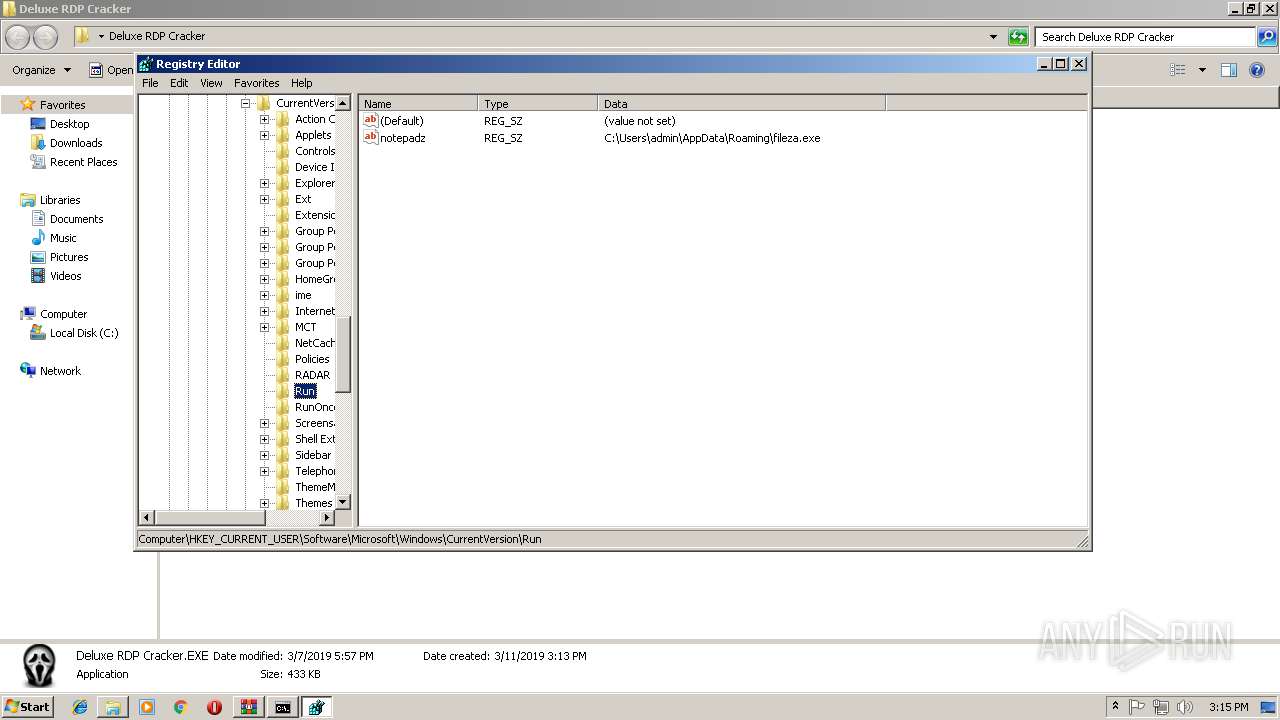
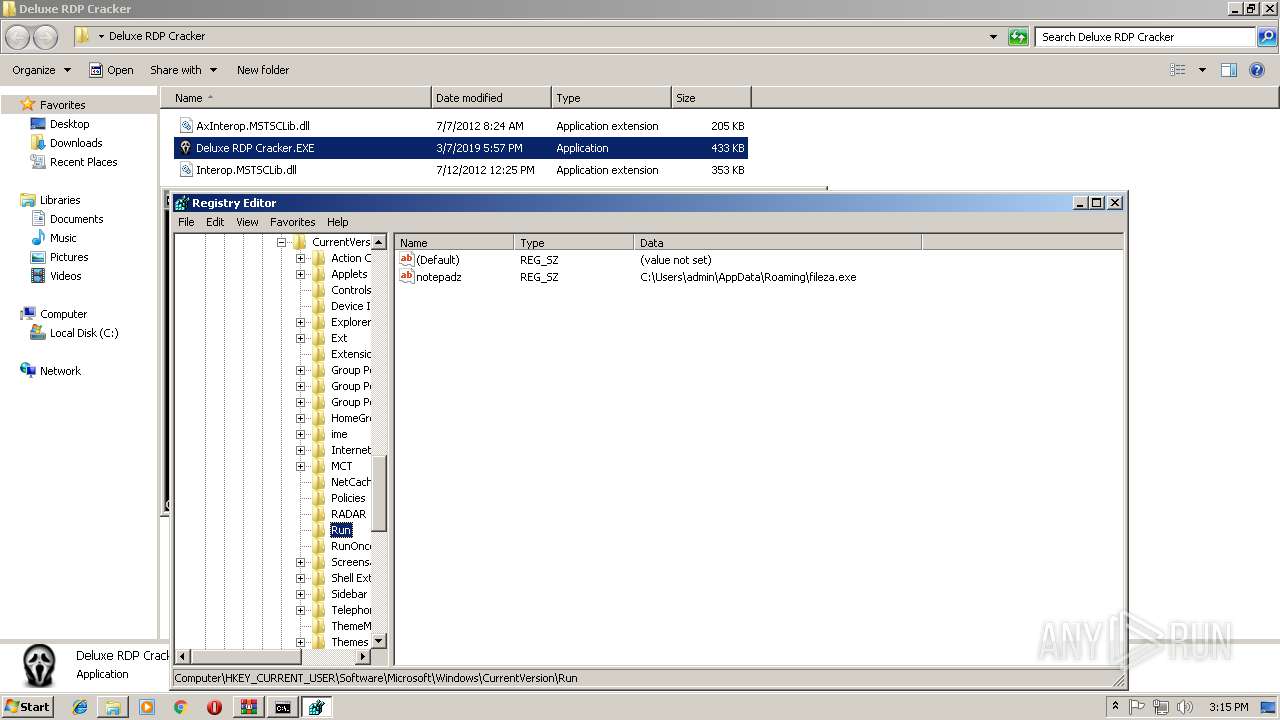
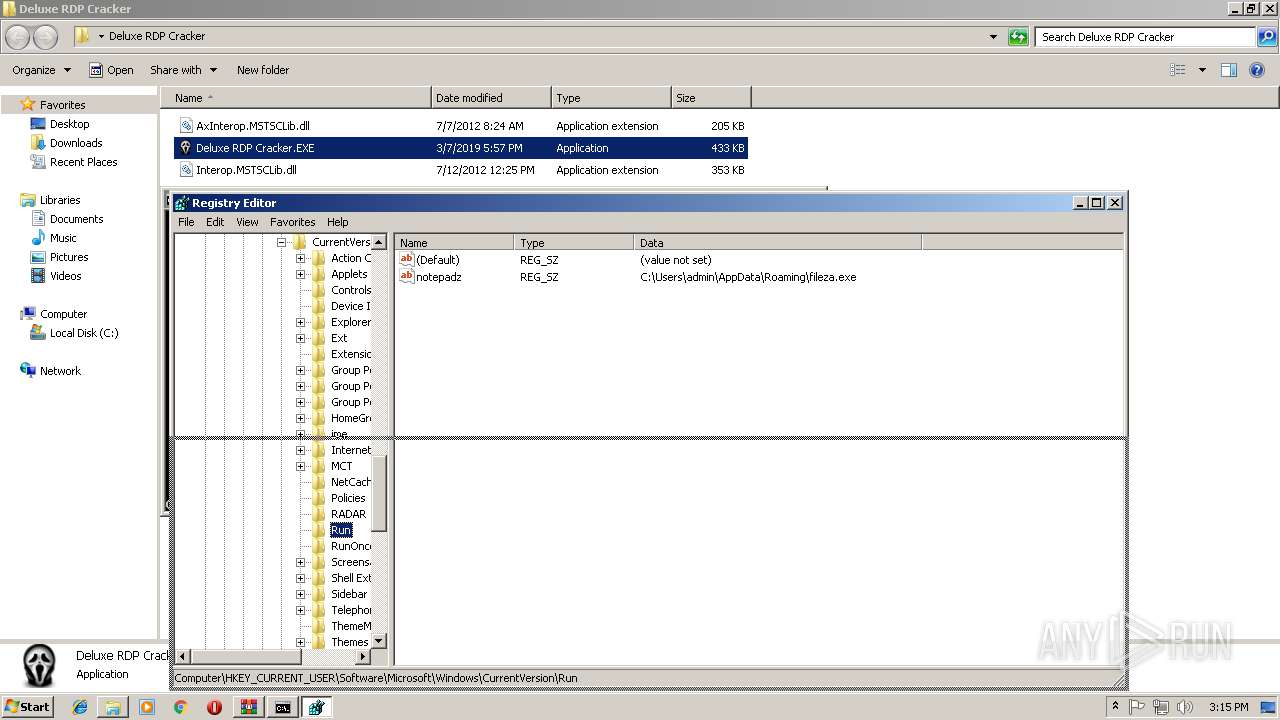
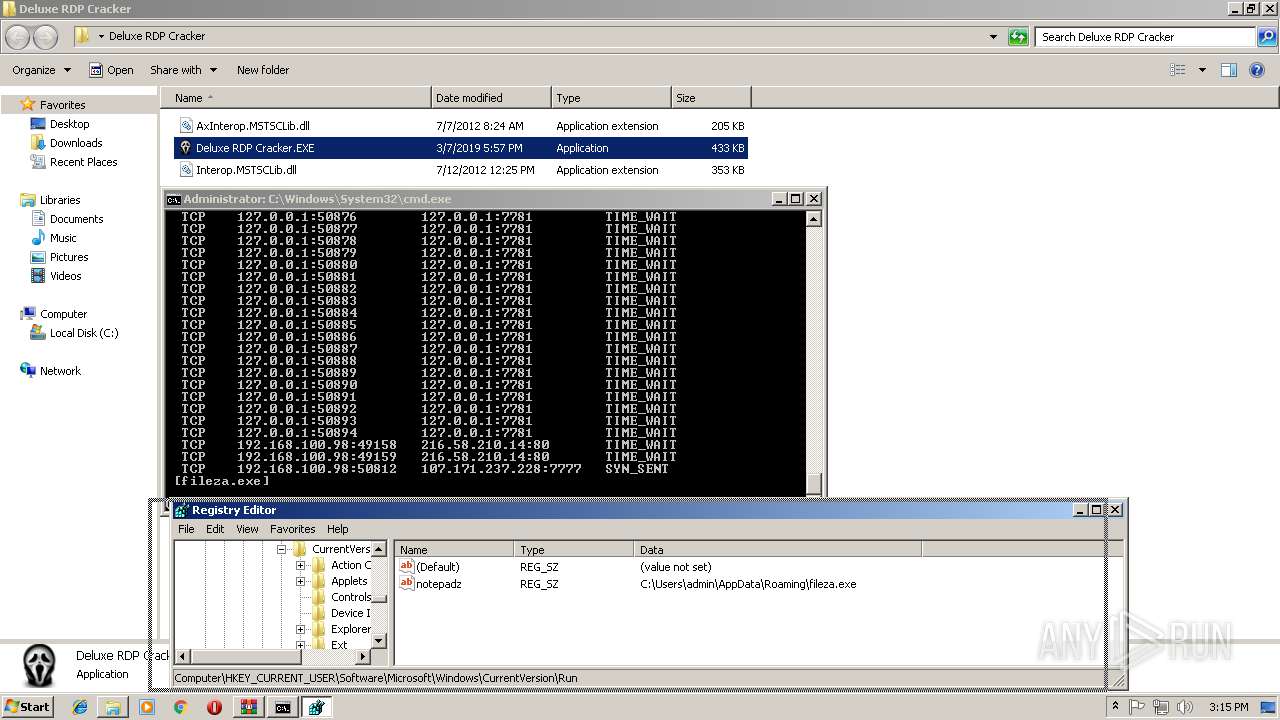
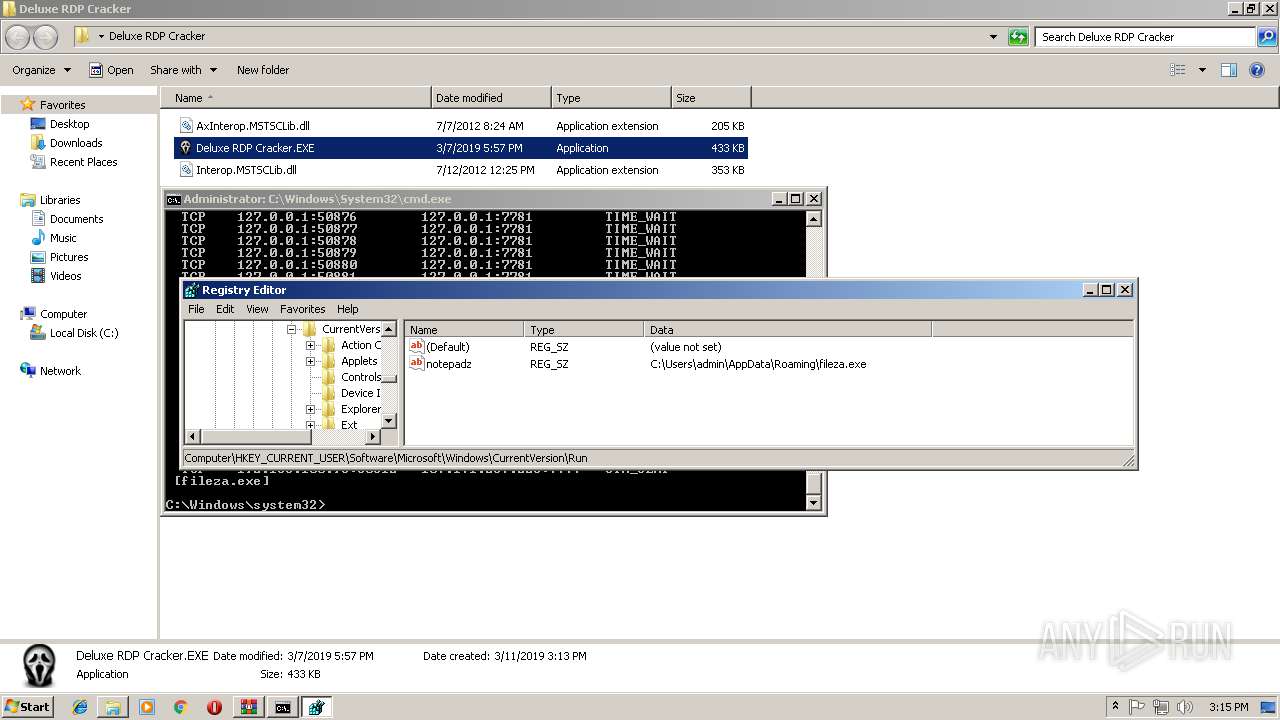
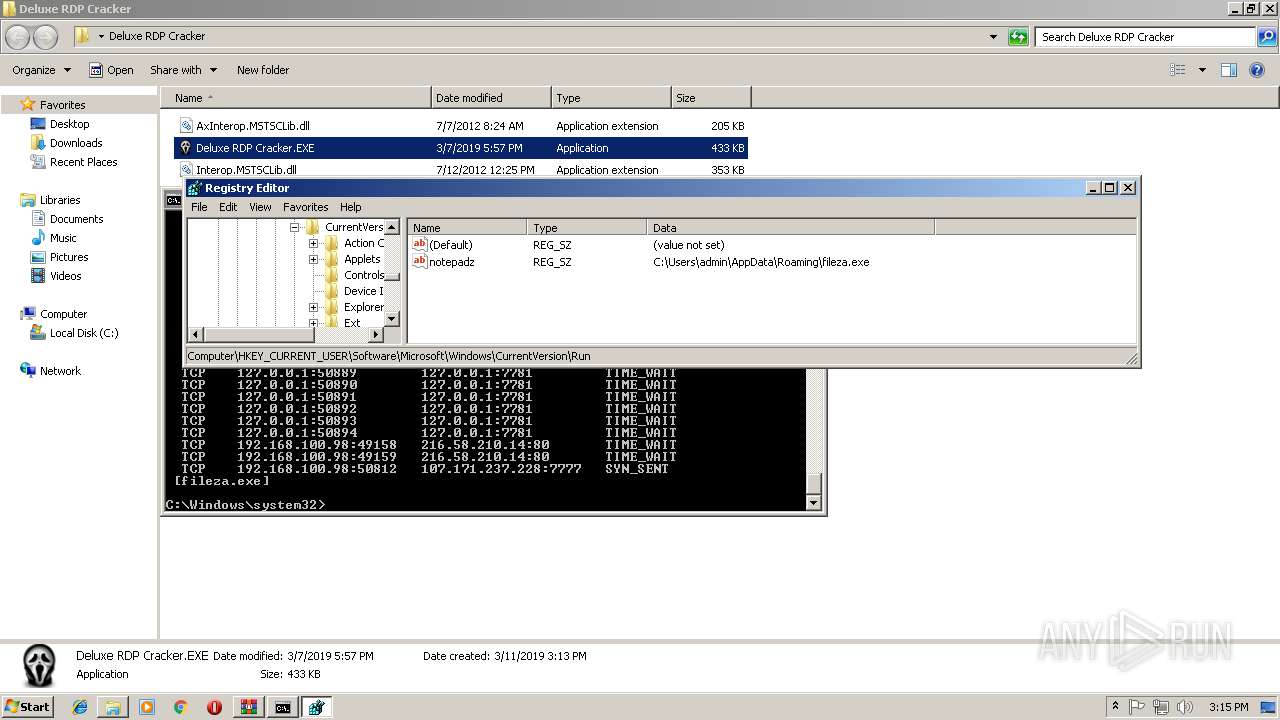
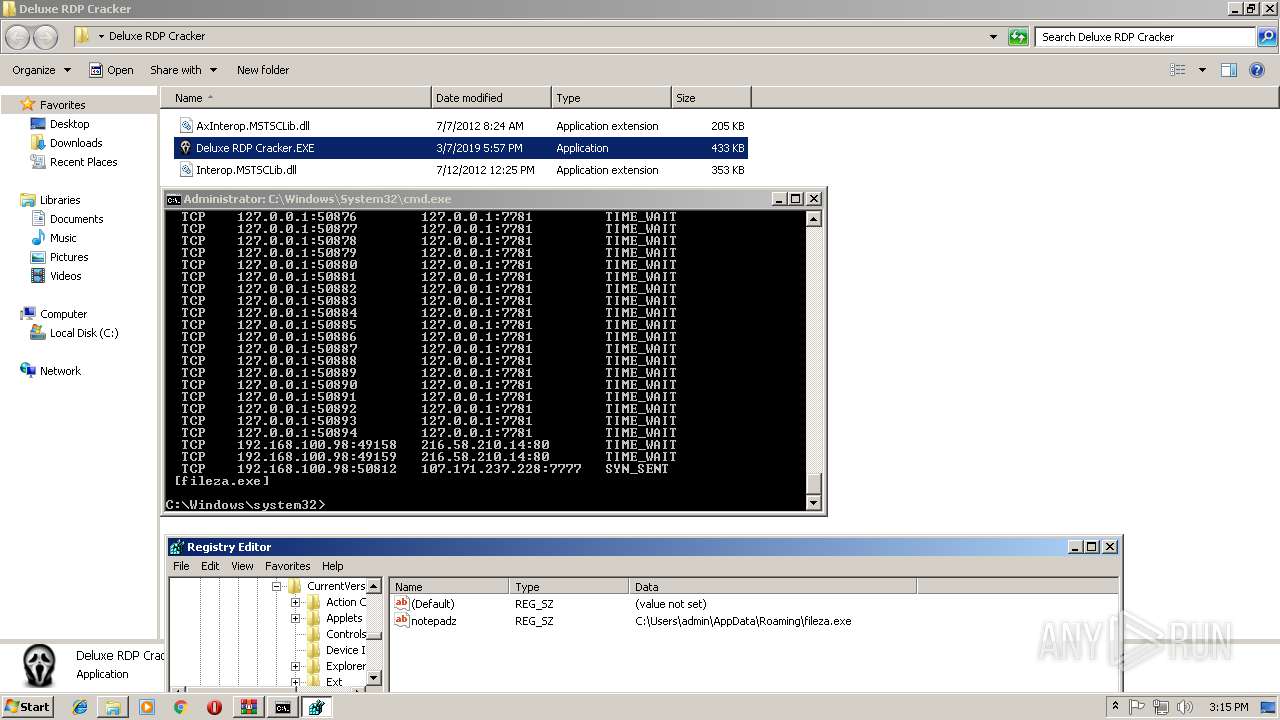
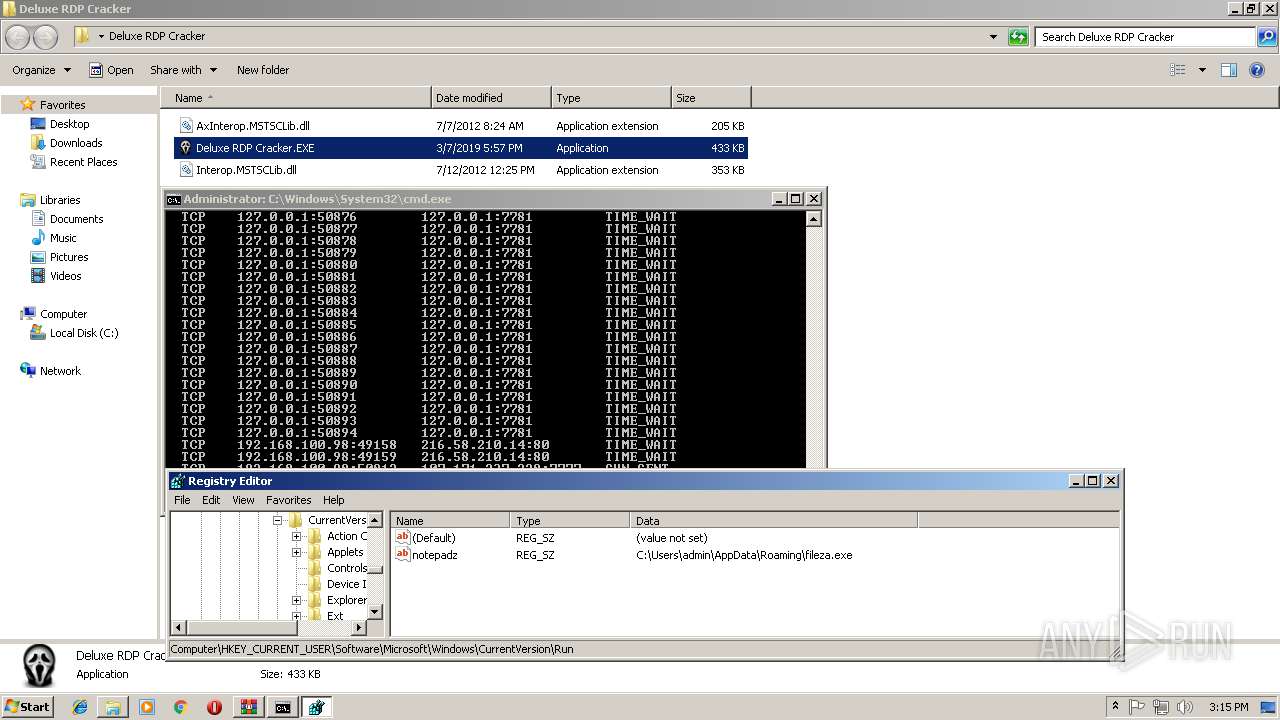
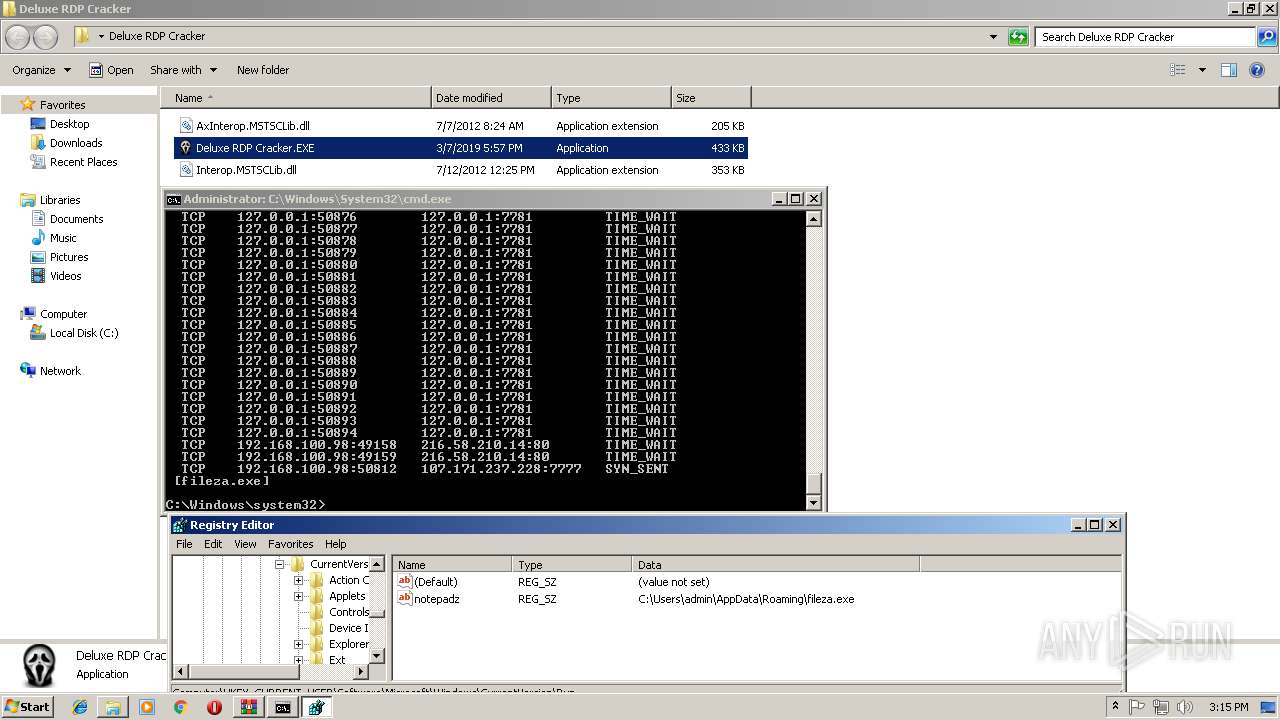
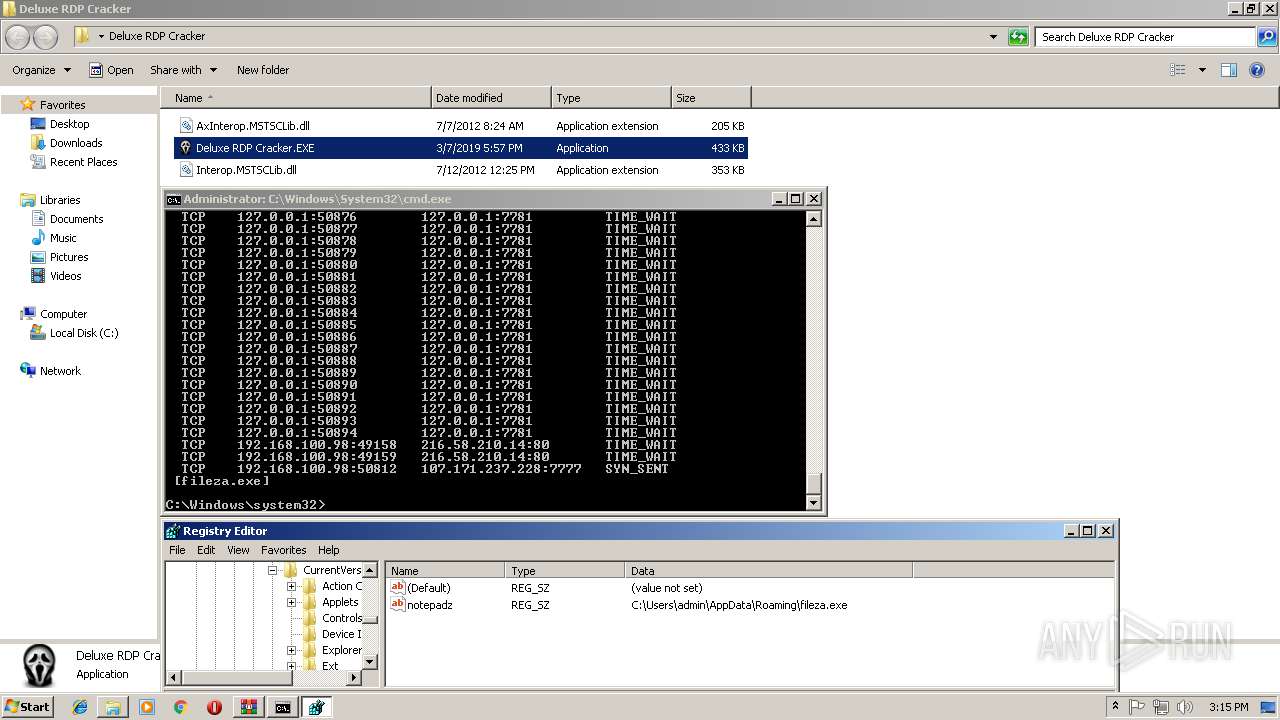
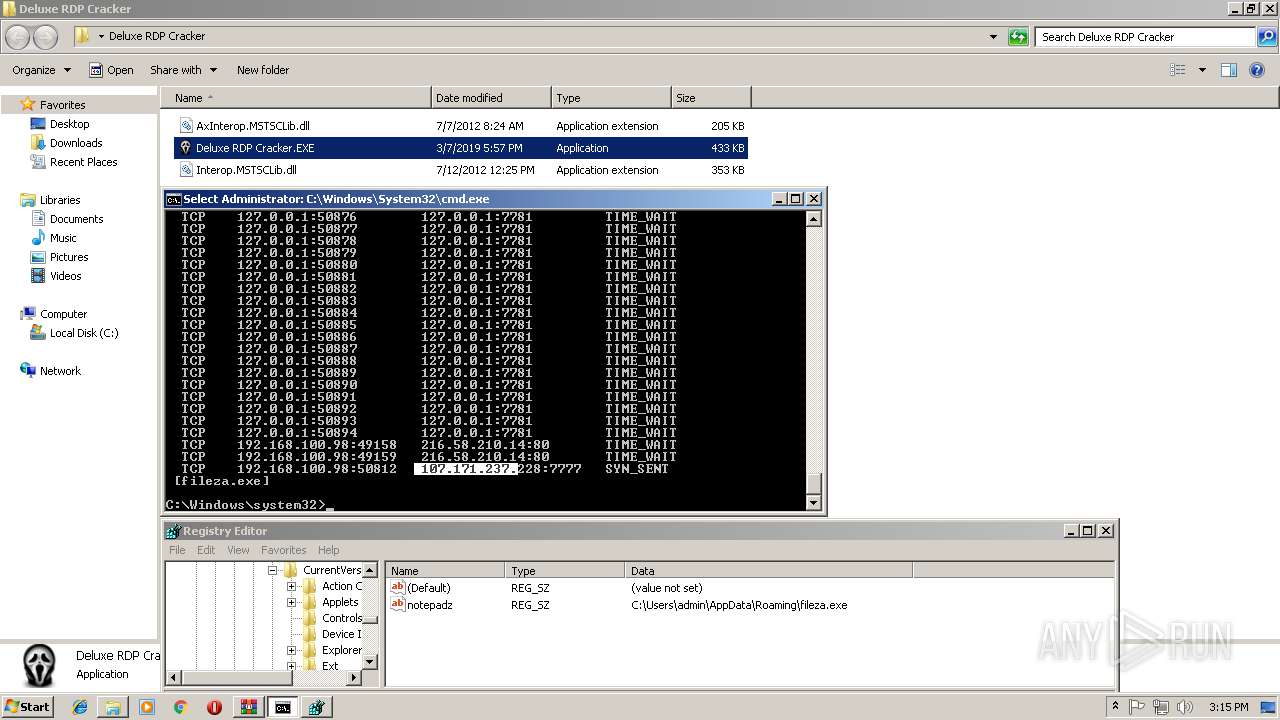
Changes the autorun value in the registry
- Deluxe RDP Cracker.EXE (PID: 2676)
- fileza.exe (PID: 864)
Writes to a start menu file
- fileza.exe (PID: 864)
Application was dropped or rewritten from another process
- fileza.exe (PID: 864)
- Deluxe RDP Cracker.EXE (PID: 2676)
- taskhost.exe (PID: 3376)
- DELUXE~1.EXE (PID: 3988)
- Deluxe RDP Cracker.EXE (PID: 3040)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 920)
SUSPICIOUS
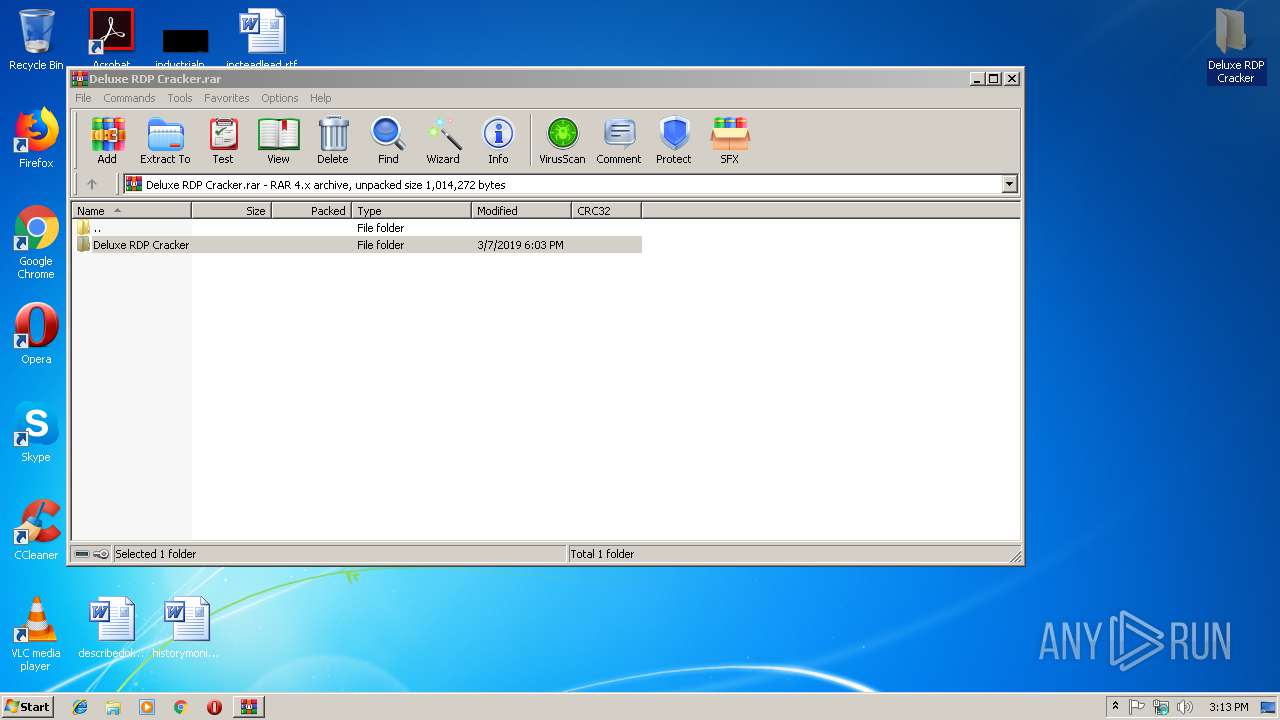
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2856)
- taskhost.exe (PID: 3376)
- fileza.exe (PID: 864)
- Deluxe RDP Cracker.EXE (PID: 2676)
Connects to unusual port
- taskhost.exe (PID: 3376)
- fileza.exe (PID: 864)
Starts itself from another location
- taskhost.exe (PID: 3376)
Creates files in the user directory
- fileza.exe (PID: 864)
- taskhost.exe (PID: 3376)
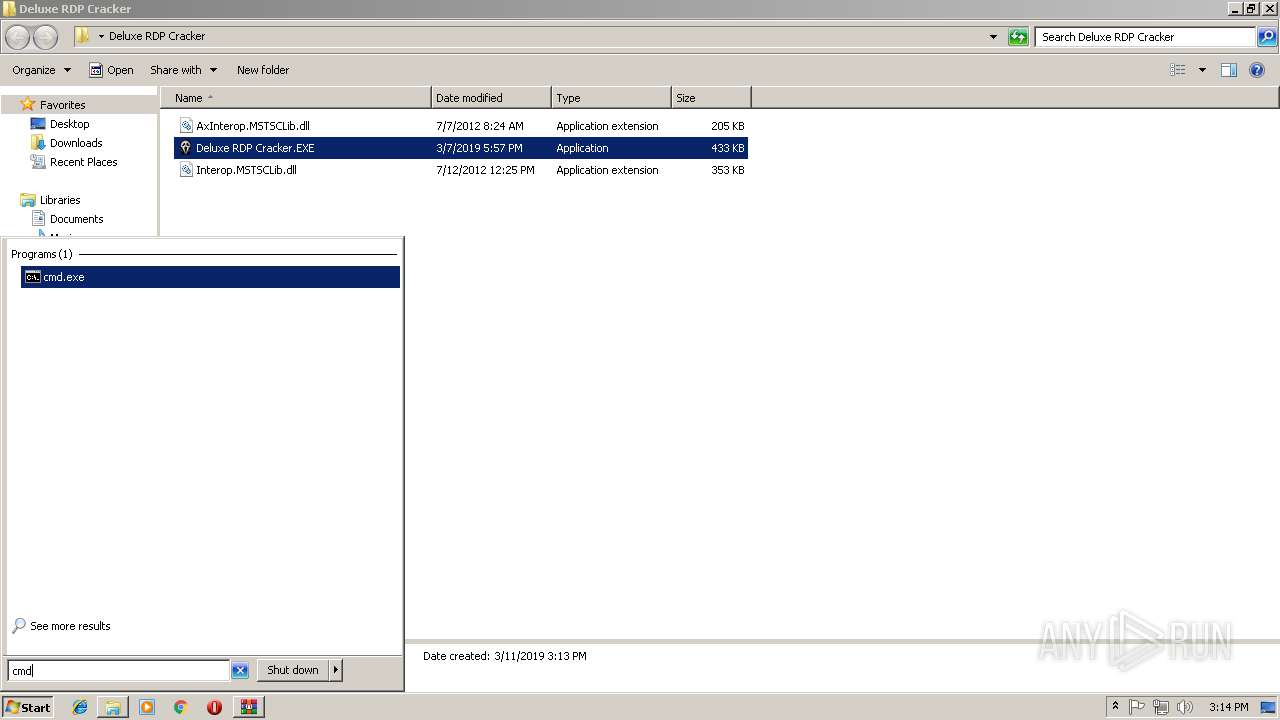
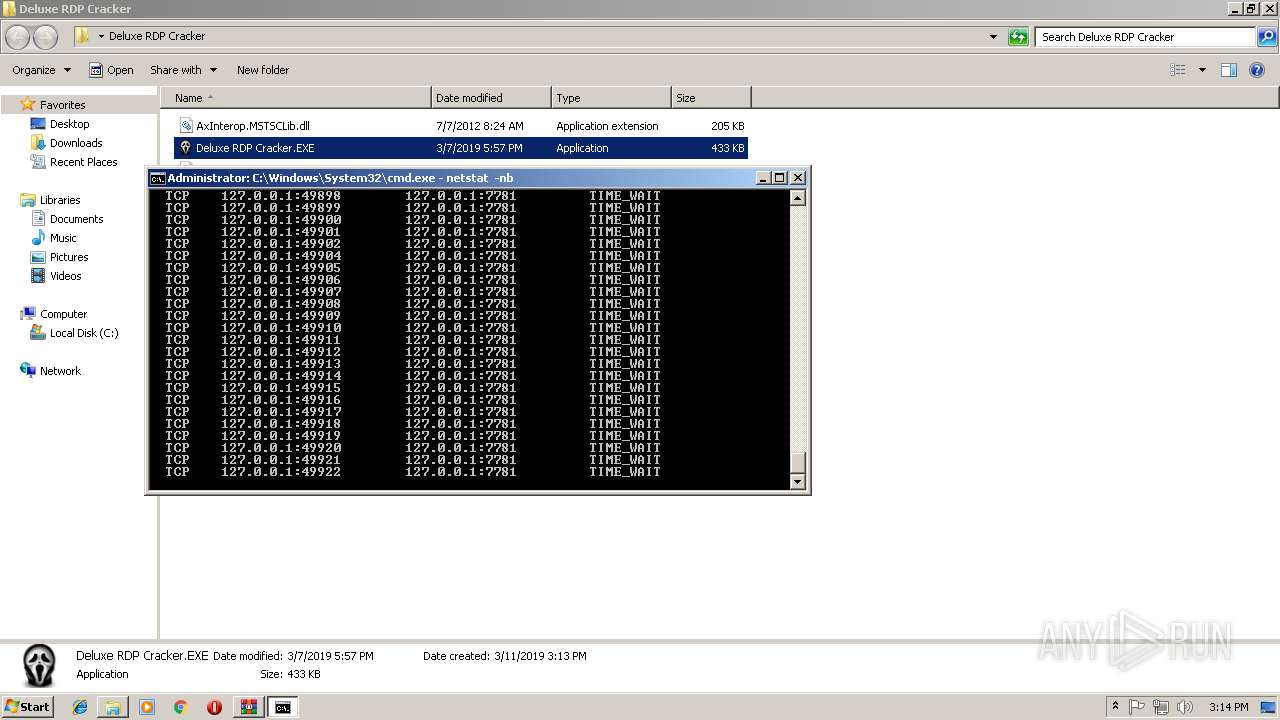
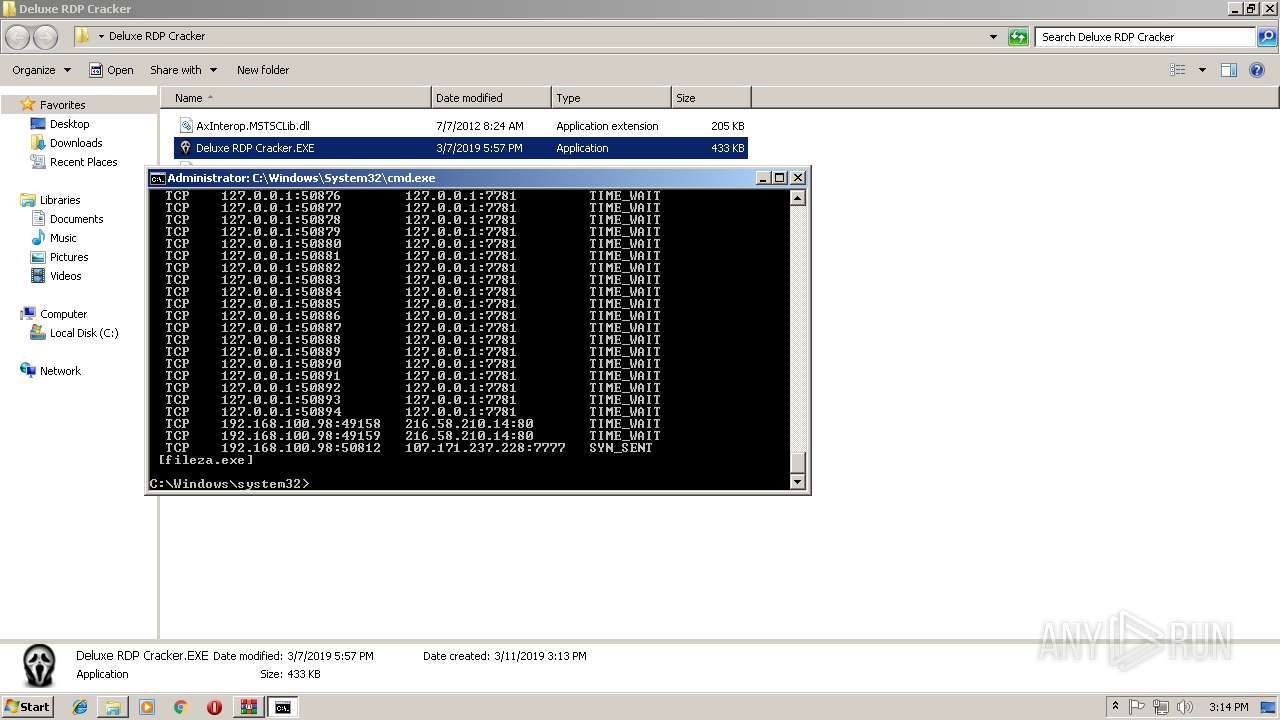
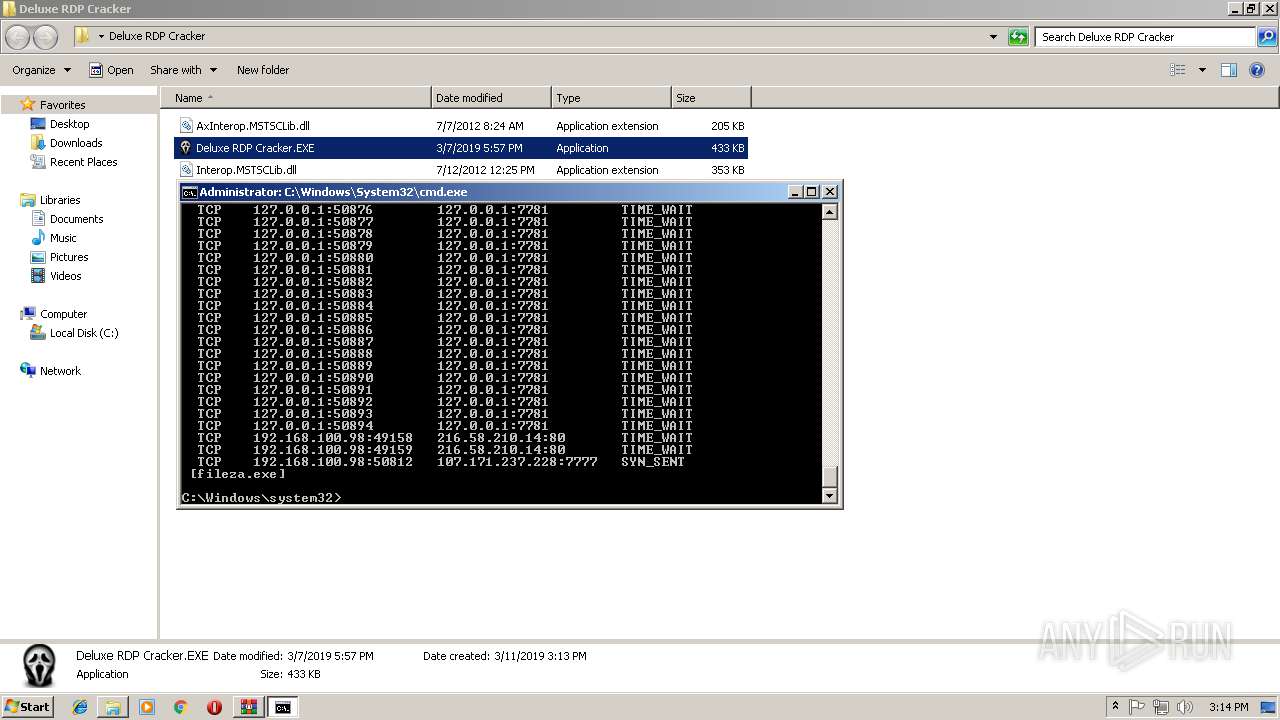
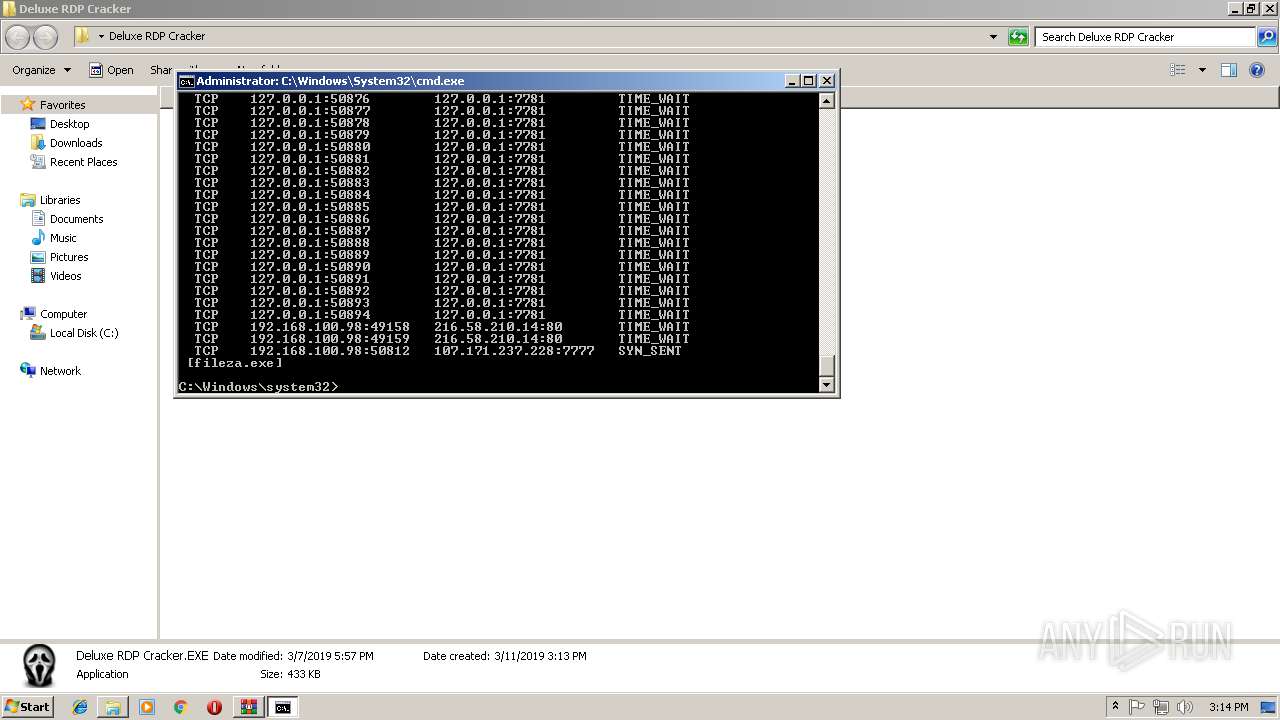
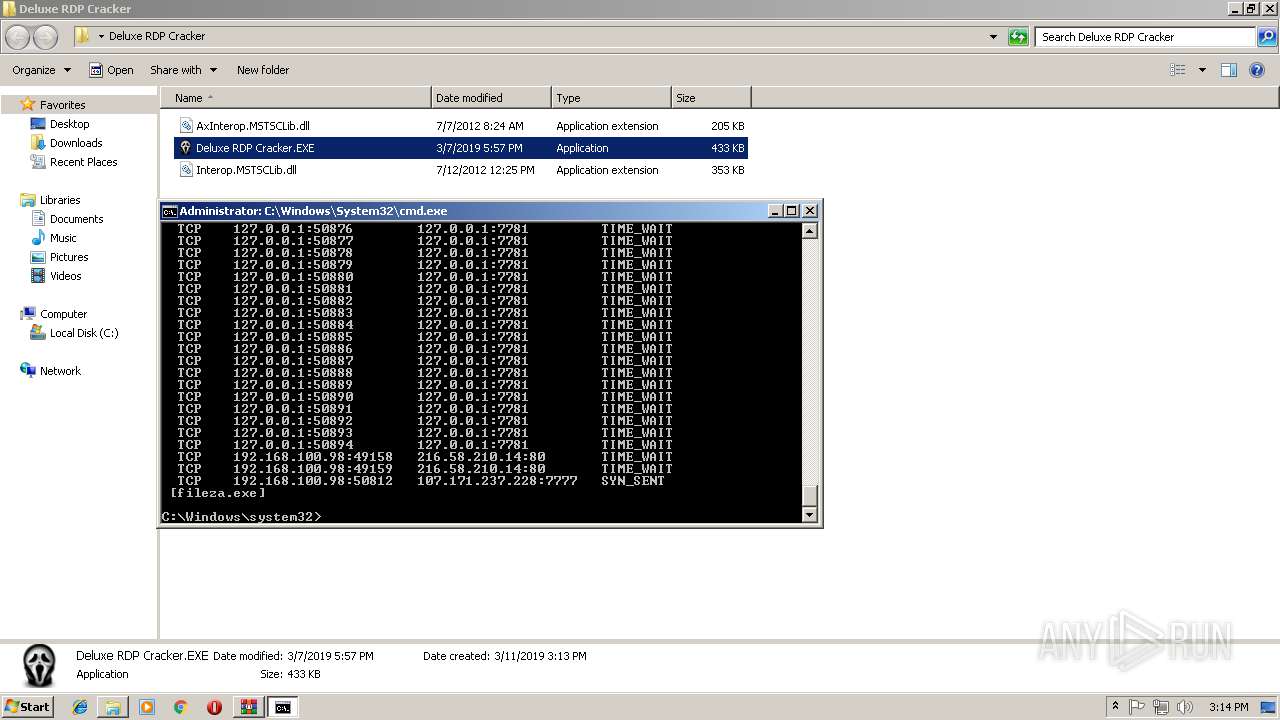
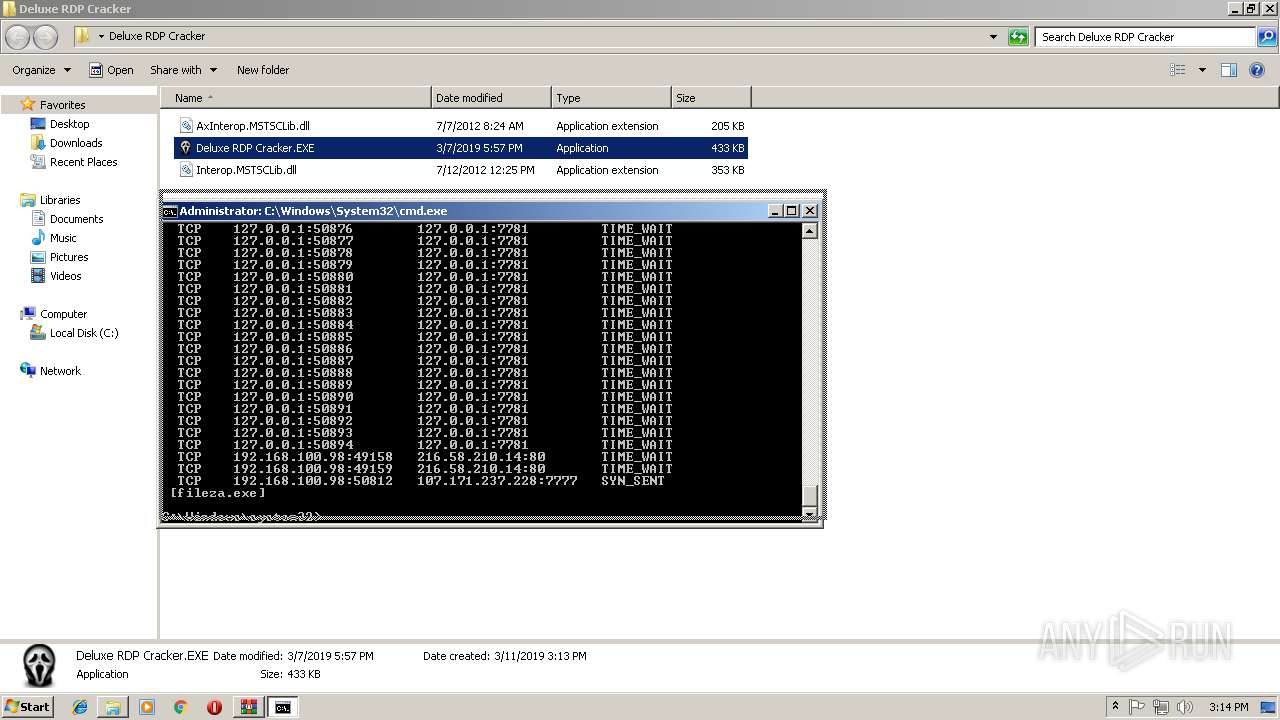
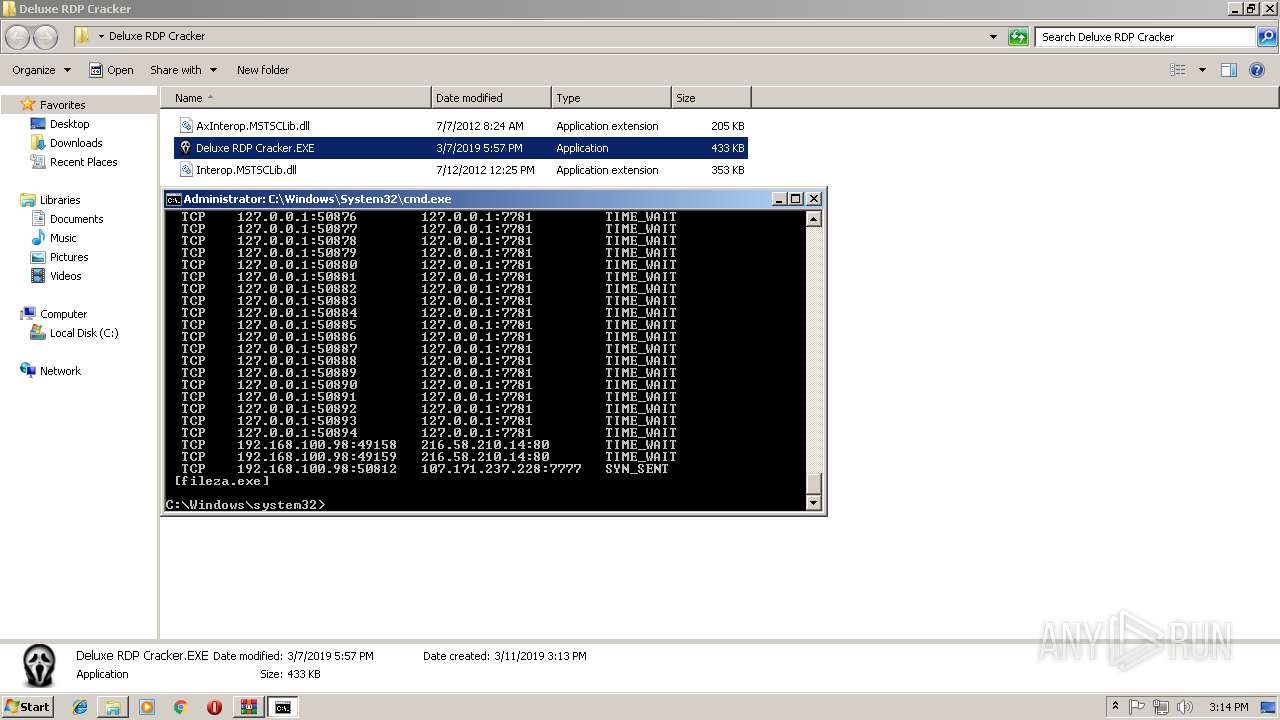
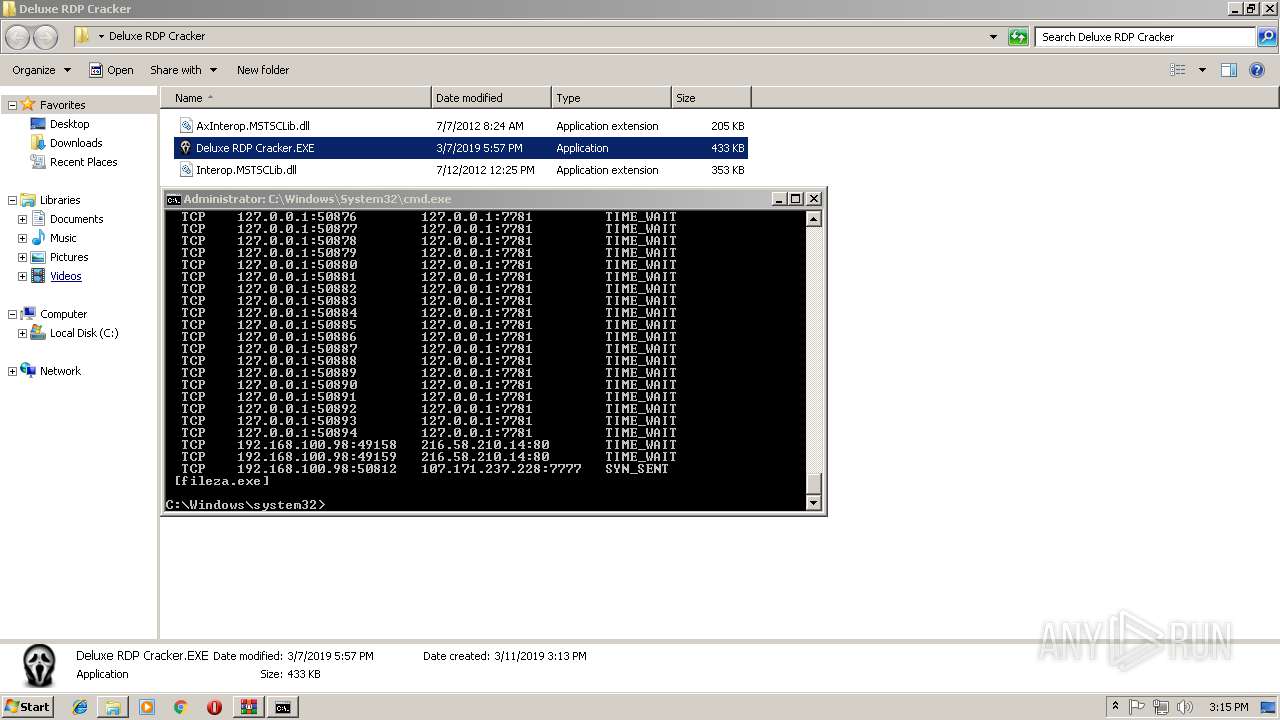
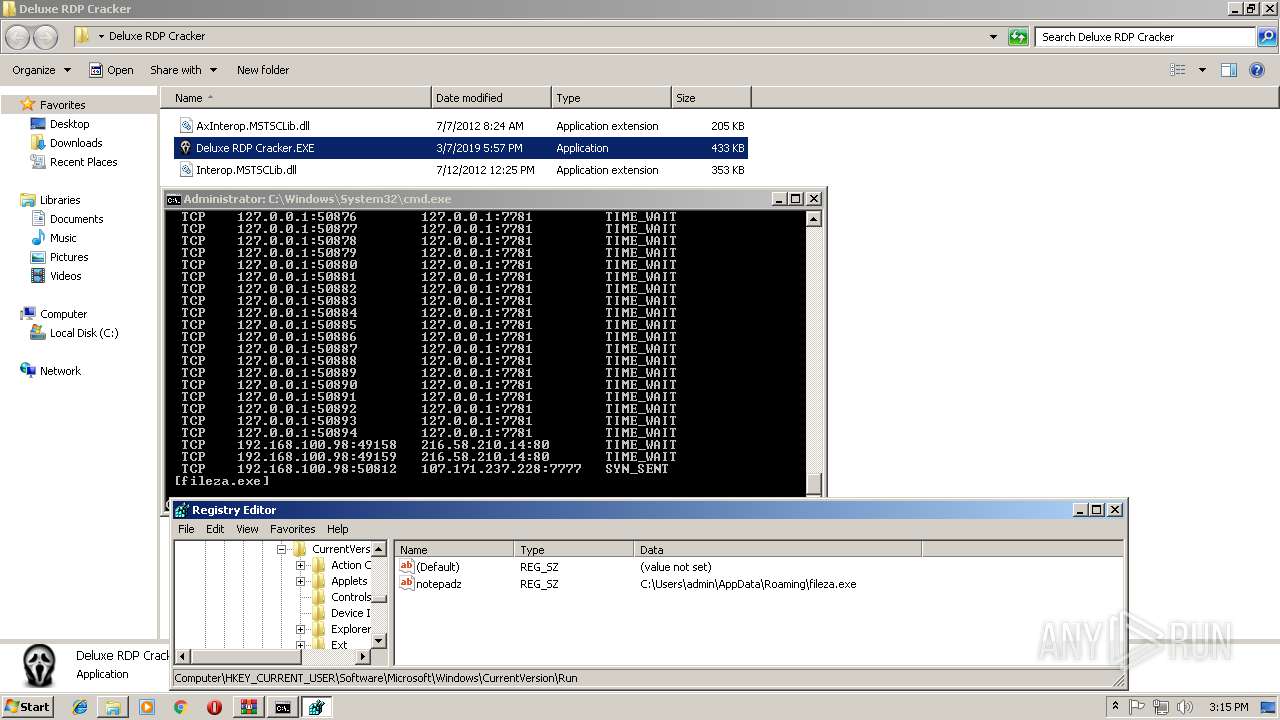
Uses NETSTAT.EXE to discover network connections
- cmd.exe (PID: 3280)
Reads the machine GUID from the registry
- DELUXE~1.EXE (PID: 3988)
INFO
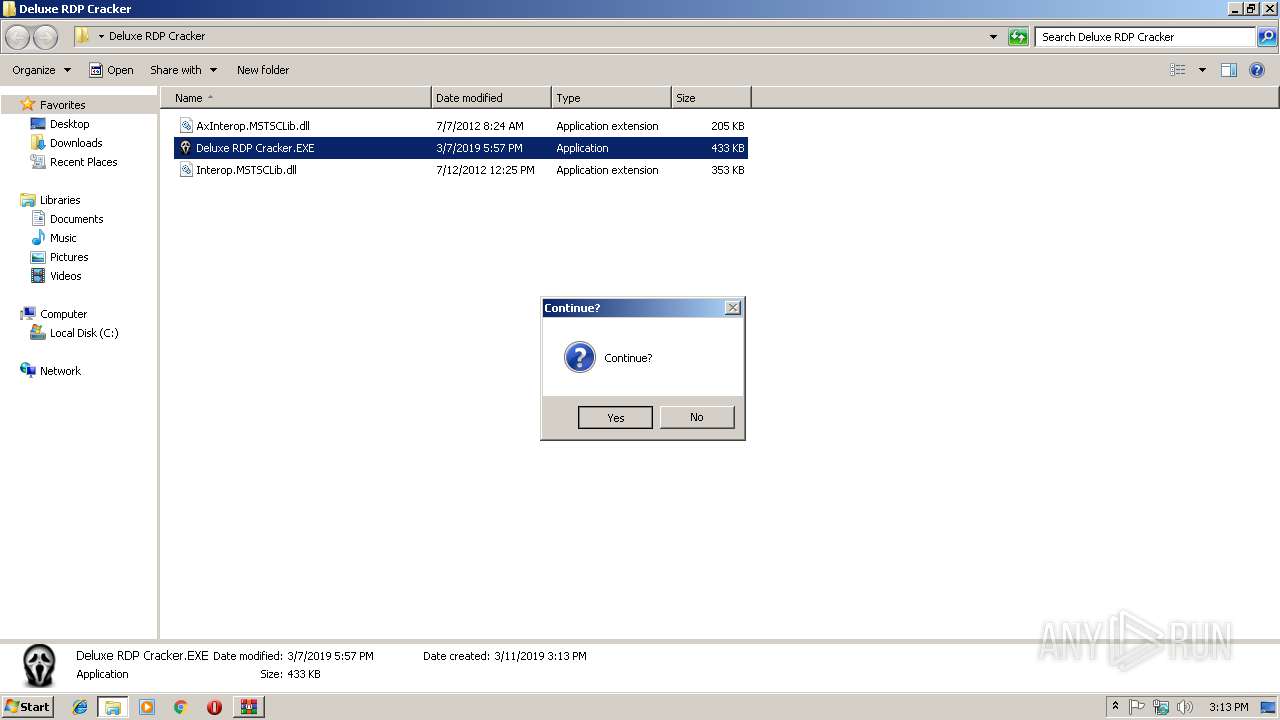
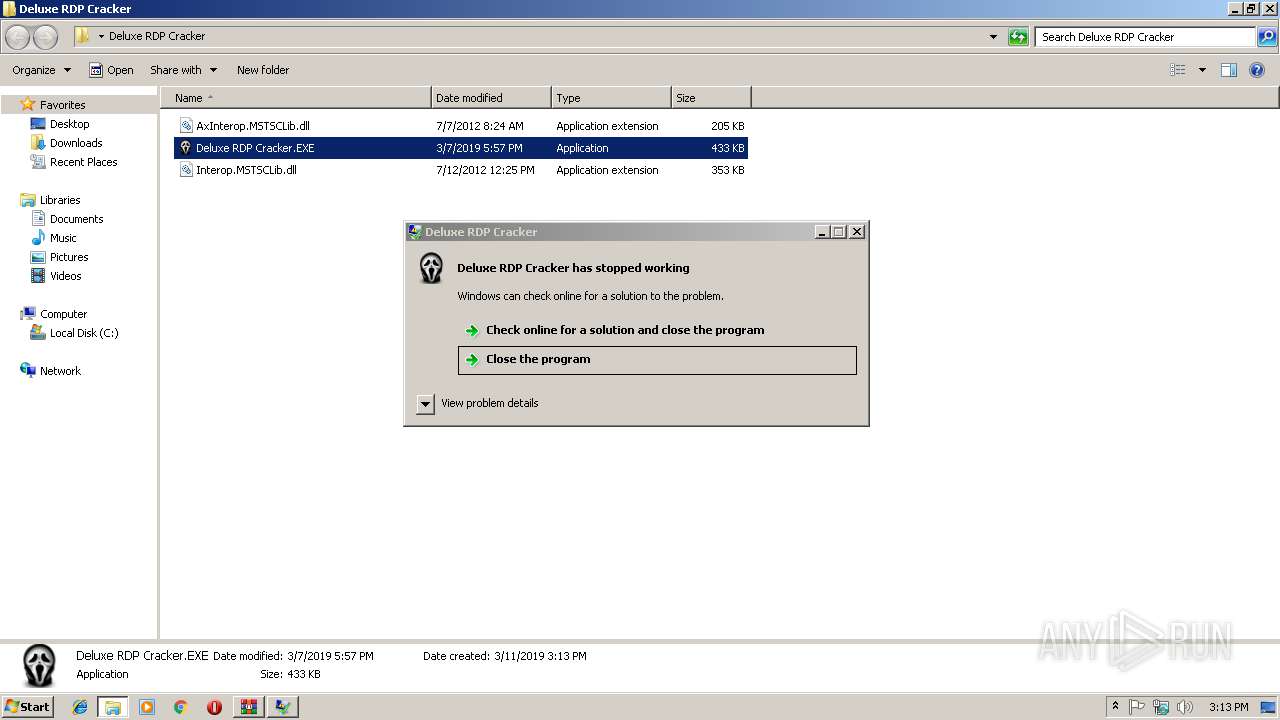
Application was crashed
- DELUXE~1.EXE (PID: 3988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 31047 |
|---|---|
| UncompressedSize: | 209920 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2012:07:07 08:24:07 |
| PackingMethod: | Normal |
| ArchivedFileName: | Deluxe RDP Cracker\AxInterop.MSTSCLib.dll |
Total processes
56
Monitored processes
11
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | "C:\Users\admin\AppData\Roaming\fileza.exe" | C:\Users\admin\AppData\Roaming\fileza.exe | taskhost.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: taskhost Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 920 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2136 | netstat -nb | C:\Windows\system32\NETSTAT.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Netstat Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
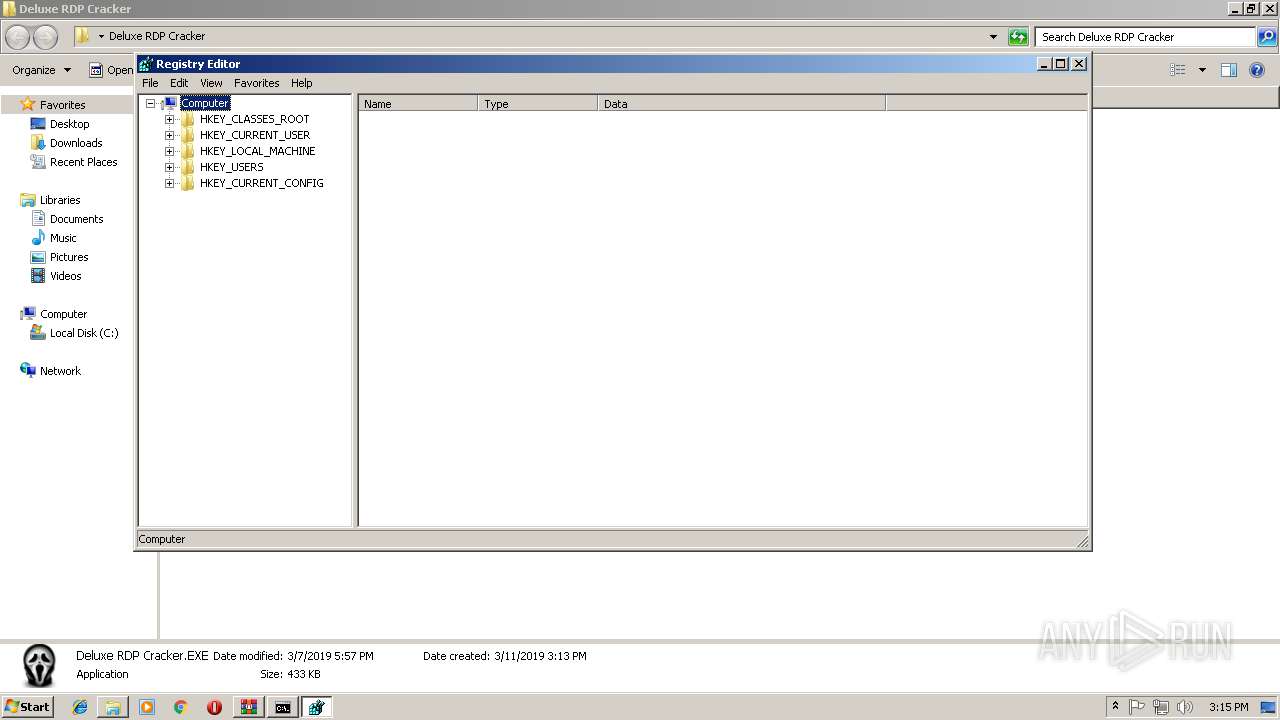
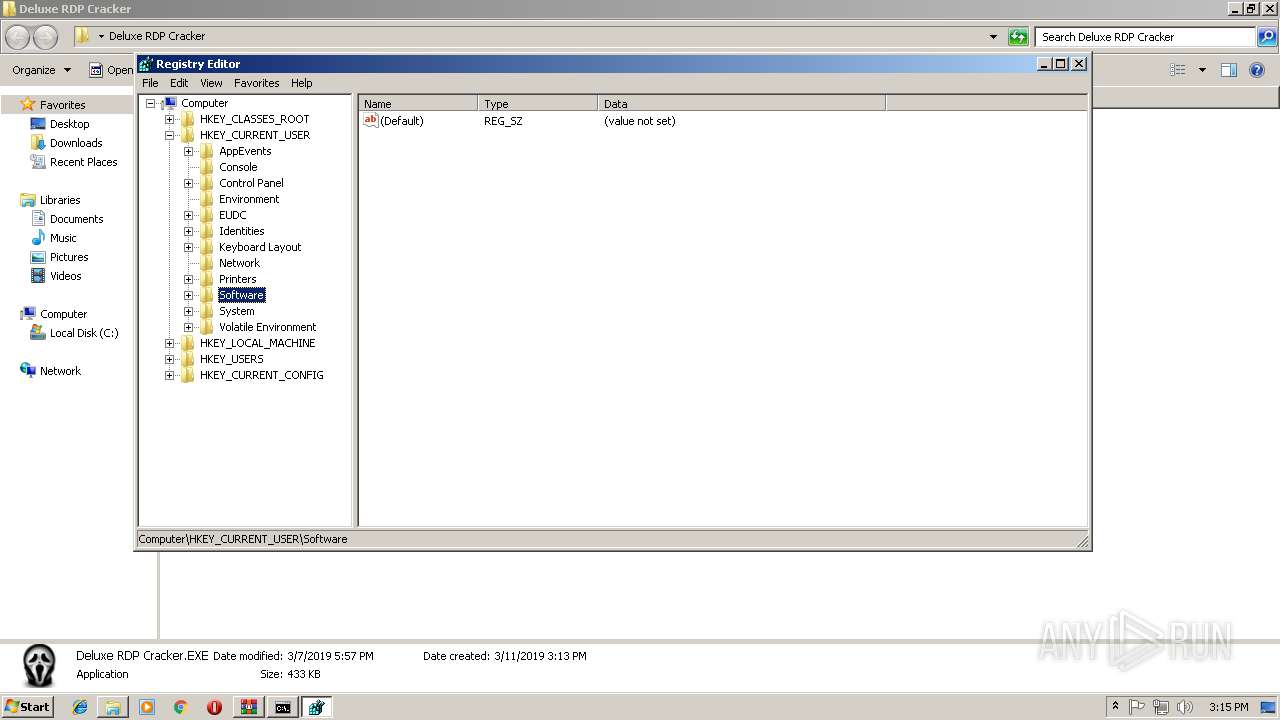
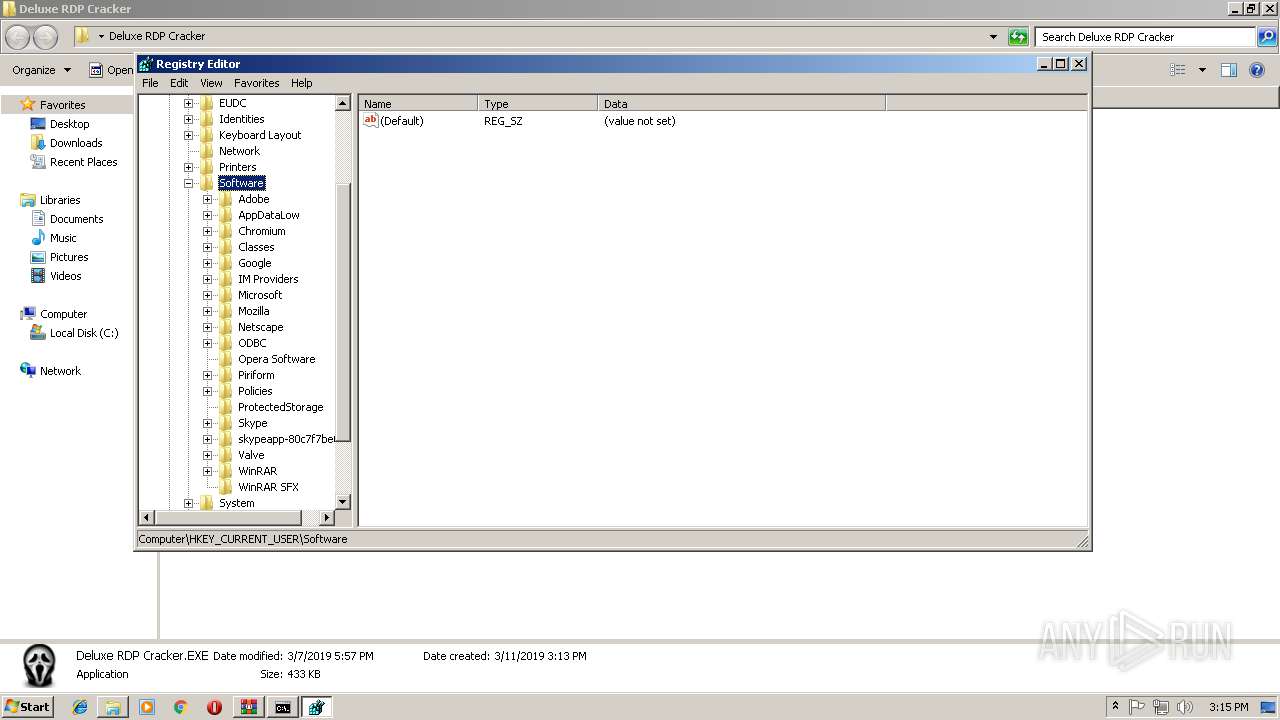
| 2380 | "C:\Windows\regedit.exe" | C:\Windows\regedit.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
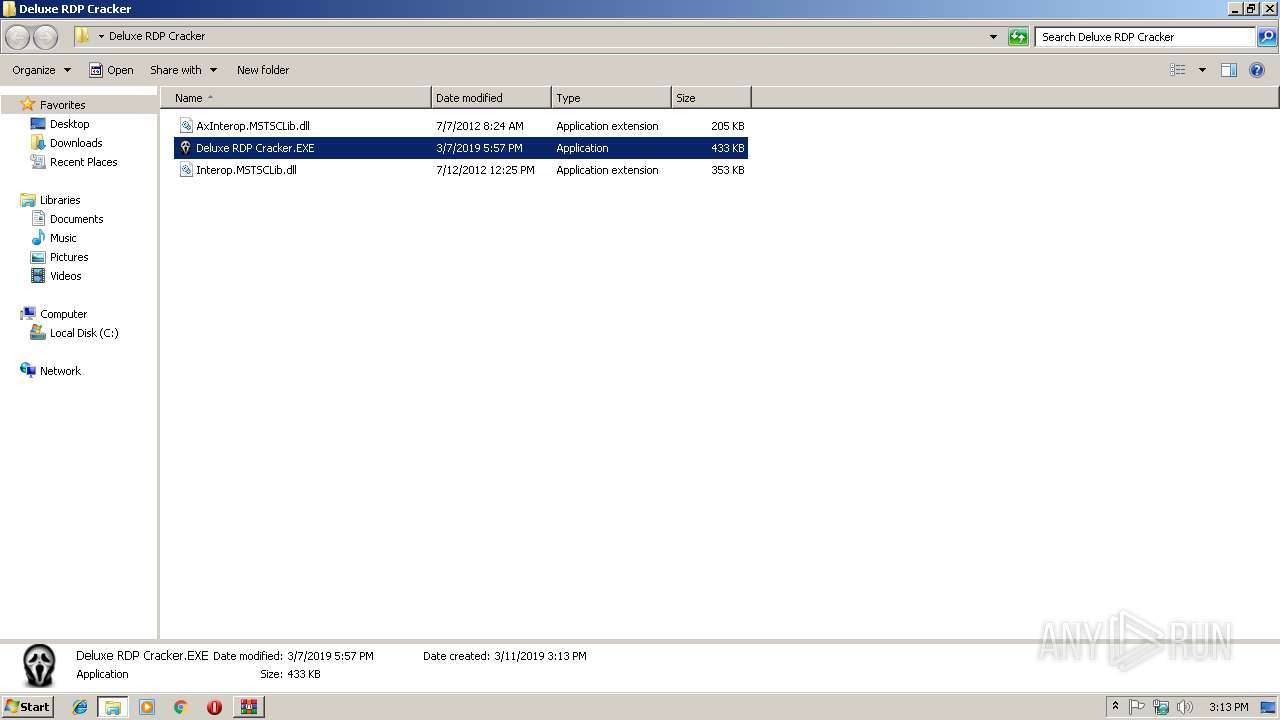
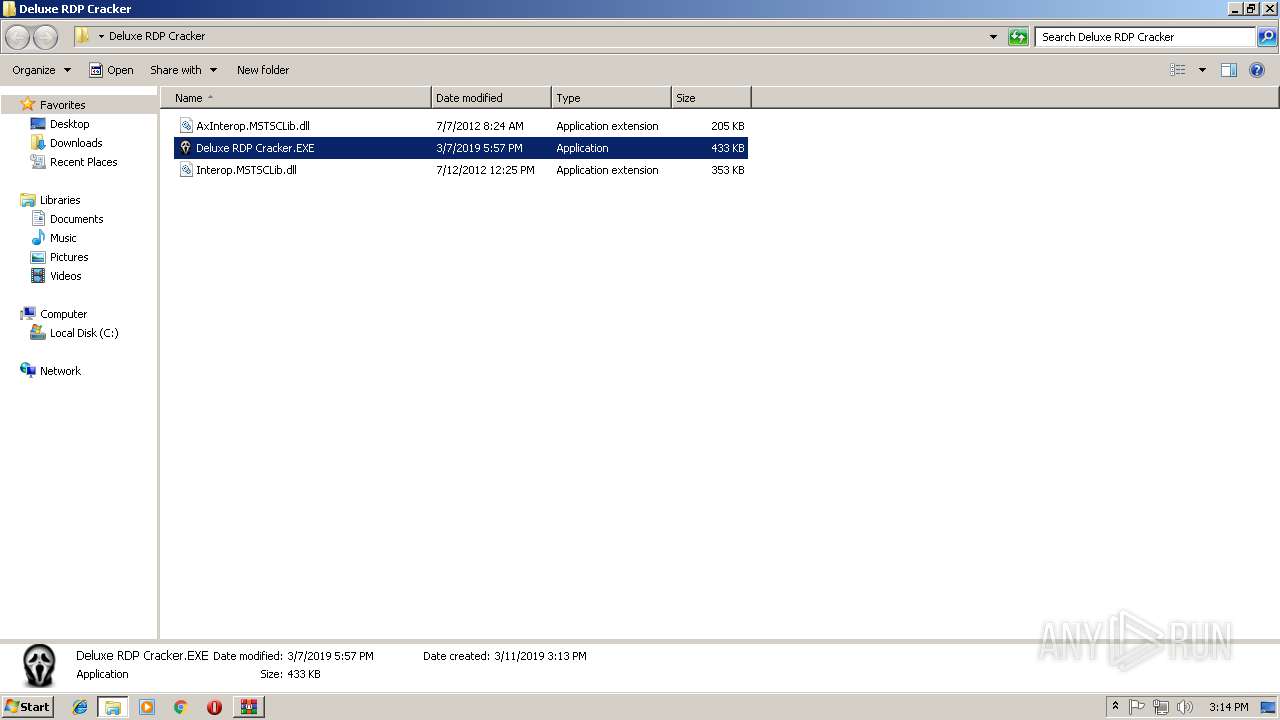
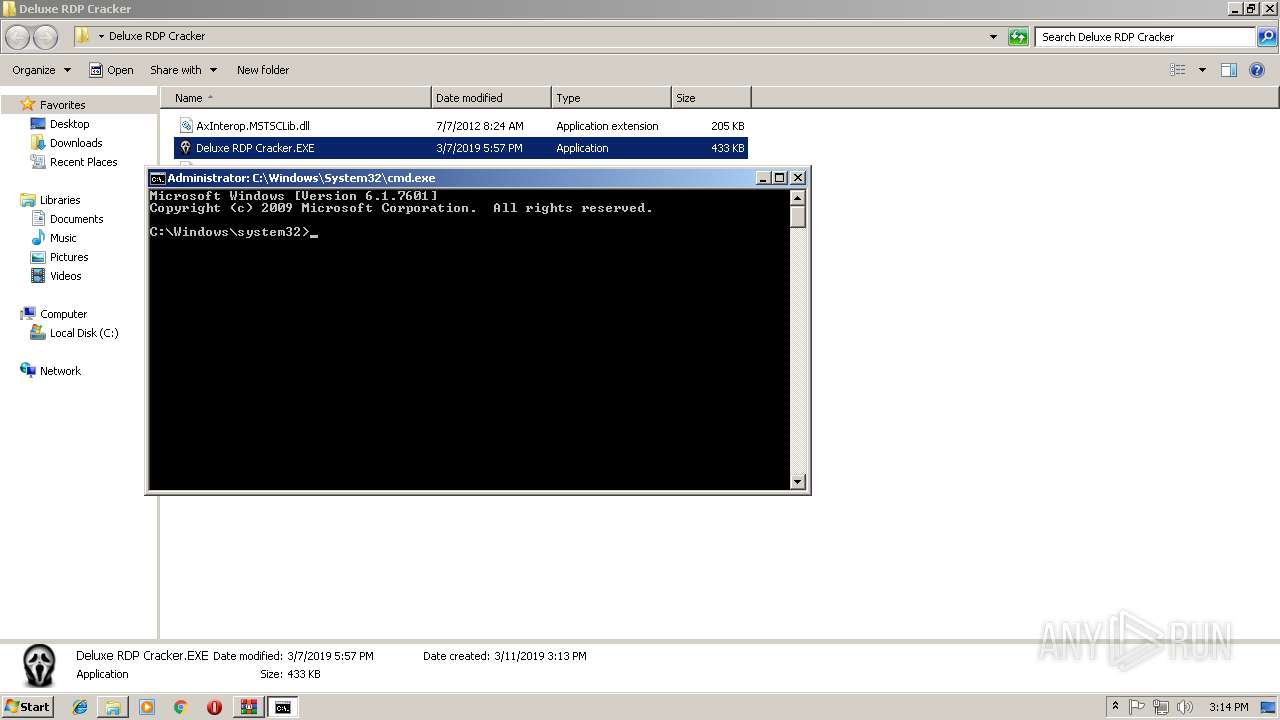
| 2676 | "C:\Users\admin\Desktop\Deluxe RDP Cracker\Deluxe RDP Cracker.EXE" | C:\Users\admin\Desktop\Deluxe RDP Cracker\Deluxe RDP Cracker.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2856 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Deluxe RDP Cracker.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3040 | "C:\Users\admin\Desktop\Deluxe RDP Cracker\Deluxe RDP Cracker.EXE" | C:\Users\admin\Desktop\Deluxe RDP Cracker\Deluxe RDP Cracker.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Win32 Cabinet Self-Extractor Exit code: 2147943623 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3280 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3376 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\taskhost.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\taskhost.exe | Deluxe RDP Cracker.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: taskhost Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3988 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\DELUXE~1.EXE | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\DELUXE~1.EXE | Deluxe RDP Cracker.EXE | ||||||||||||
User: admin Company: VirtuaSOFT Integrity Level: HIGH Description: Deluxe RDP Cracker Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 172
Read events
1 156
Write events
15
Delete events
1
Modification events
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Deluxe RDP Cracker.rar | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2856) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
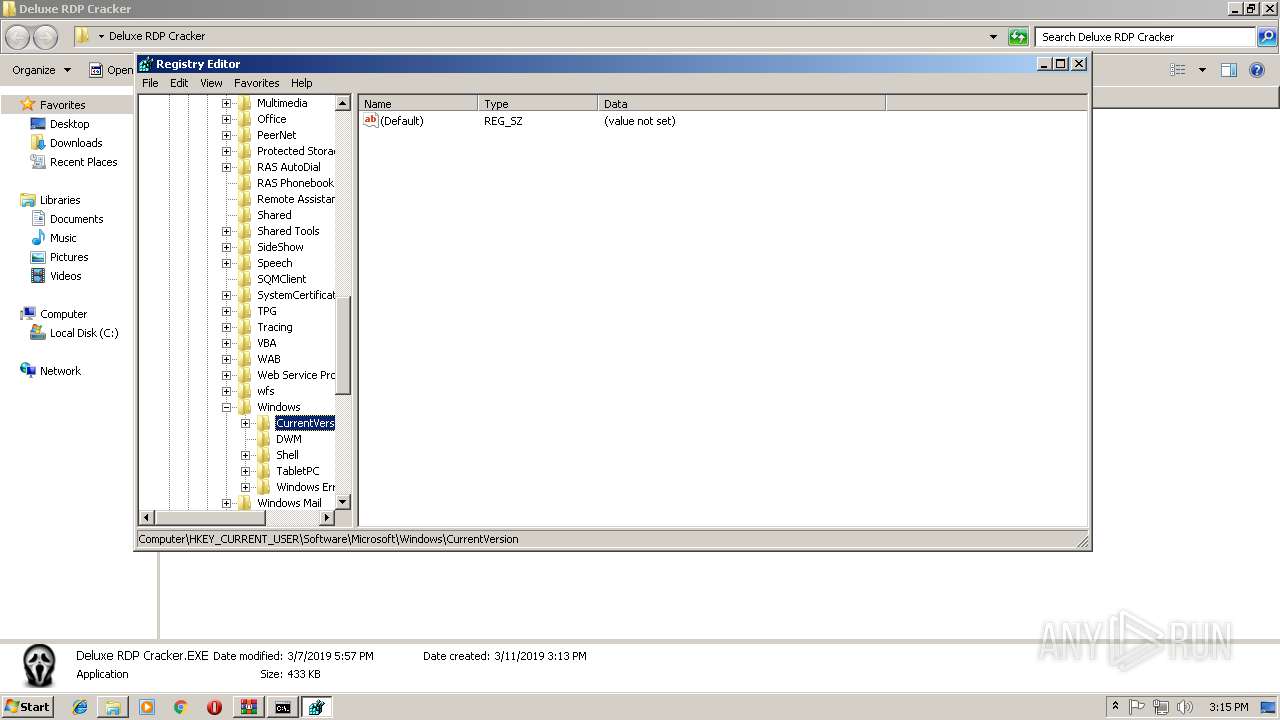
| (PID) Process: | (2676) Deluxe RDP Cracker.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wextract_cleanup0 |
Value: rundll32.exe C:\Windows\system32\advpack.dll,DelNodeRunDLL32 "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\" | |||
| (PID) Process: | (3376) taskhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
9
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3376 | taskhost.exe | C:\Users\admin\AppData\Roaming\fileza.exe | executable | |
MD5:— | SHA256:— | |||
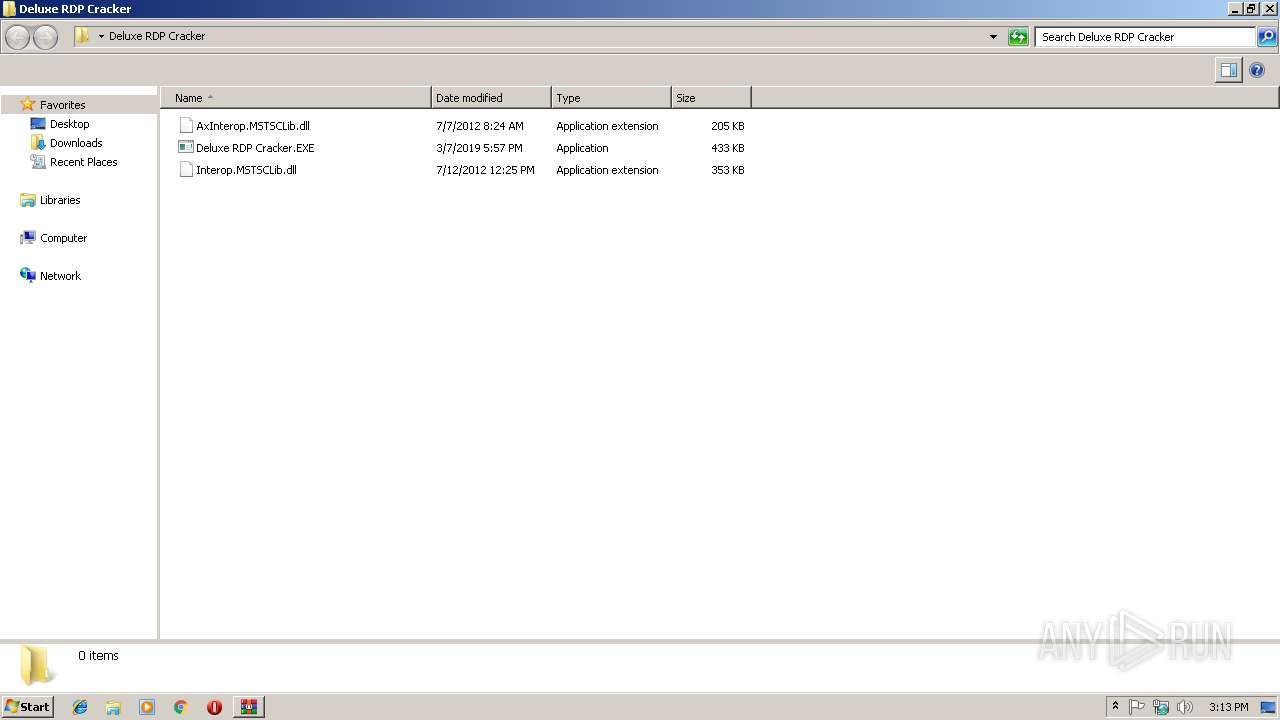
| 2856 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2856.18835\Deluxe RDP Cracker\Deluxe RDP Cracker.EXE | executable | |
MD5:— | SHA256:— | |||
| 2676 | Deluxe RDP Cracker.EXE | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\taskhost.exe | executable | |
MD5:— | SHA256:— | |||
| 864 | fileza.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\taskhost.exe | executable | |
MD5:— | SHA256:— | |||
| 2676 | Deluxe RDP Cracker.EXE | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\INTERO~1.DLL | executable | |
MD5:4966D55E49FE28B7E006A2B762C0D026 | SHA256:6519B3F797B2B93C123F11E53F0E0AE438ABBAF7F01DB879EA3046D26D1D0432 | |||
| 2676 | Deluxe RDP Cracker.EXE | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\AXINTE~1.DLL | executable | |
MD5:75E00166775611138F411351403E2A2D | SHA256:68A817826846142A5FEAEAF514632921654409051BE57D6C87AA871983CB52C1 | |||
| 2856 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2856.18835\Deluxe RDP Cracker\Interop.MSTSCLib.dll | executable | |
MD5:4966D55E49FE28B7E006A2B762C0D026 | SHA256:6519B3F797B2B93C123F11E53F0E0AE438ABBAF7F01DB879EA3046D26D1D0432 | |||
| 2676 | Deluxe RDP Cracker.EXE | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\DELUXE~1.EXE | executable | |
MD5:CB5DD718C56545BCF47E97B296C48922 | SHA256:34B1604D749E3588ED90544E00D1769D04DD3F252A7604DC227C7E450C224E29 | |||
| 2856 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2856.18835\Deluxe RDP Cracker\AxInterop.MSTSCLib.dll | executable | |
MD5:75E00166775611138F411351403E2A2D | SHA256:68A817826846142A5FEAEAF514632921654409051BE57D6C87AA871983CB52C1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
13
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
864 | fileza.exe | 107.171.237.228:7777 | — | Videotron Telecom Ltee | CA | unknown |
3376 | taskhost.exe | 107.171.237.228:7777 | — | Videotron Telecom Ltee | CA | unknown |