analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
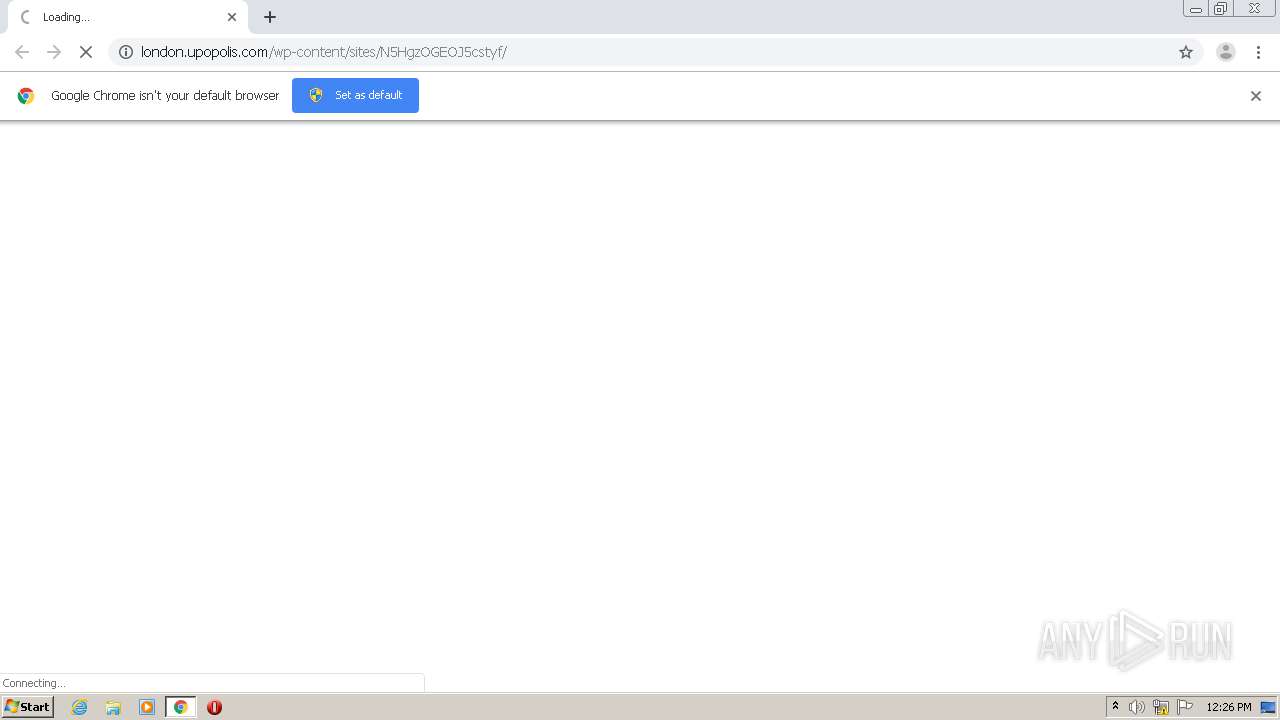
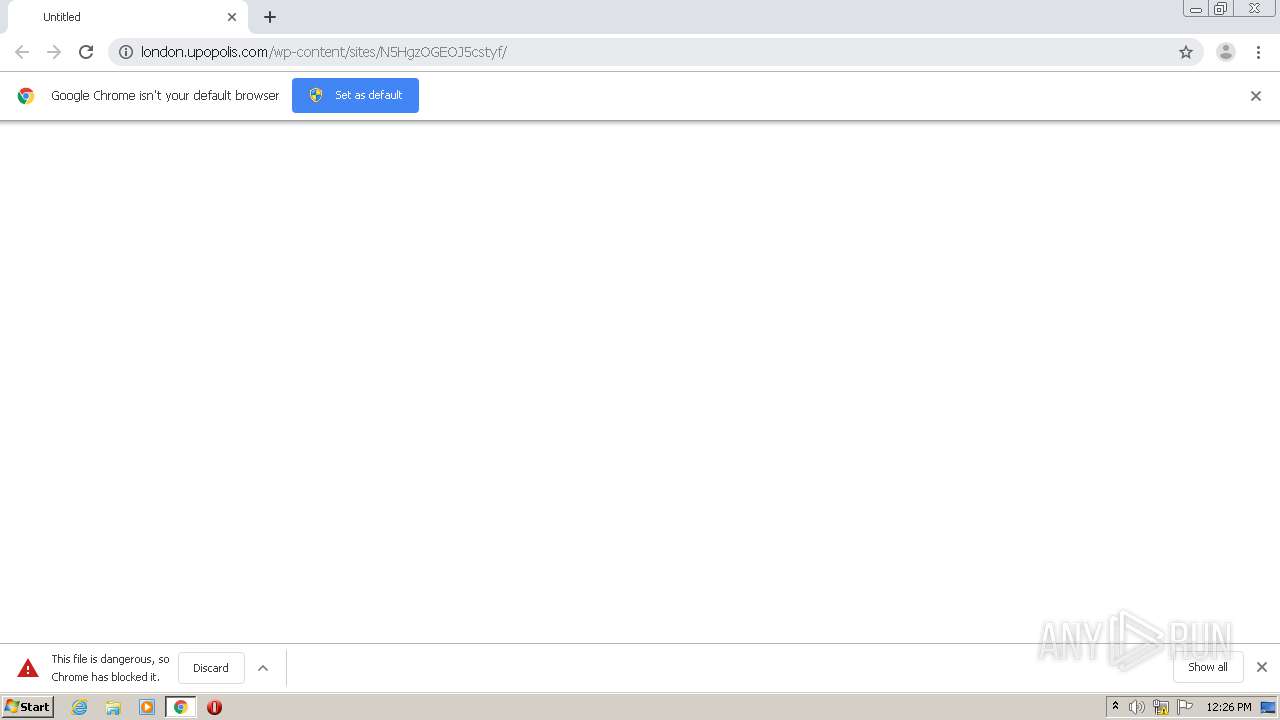
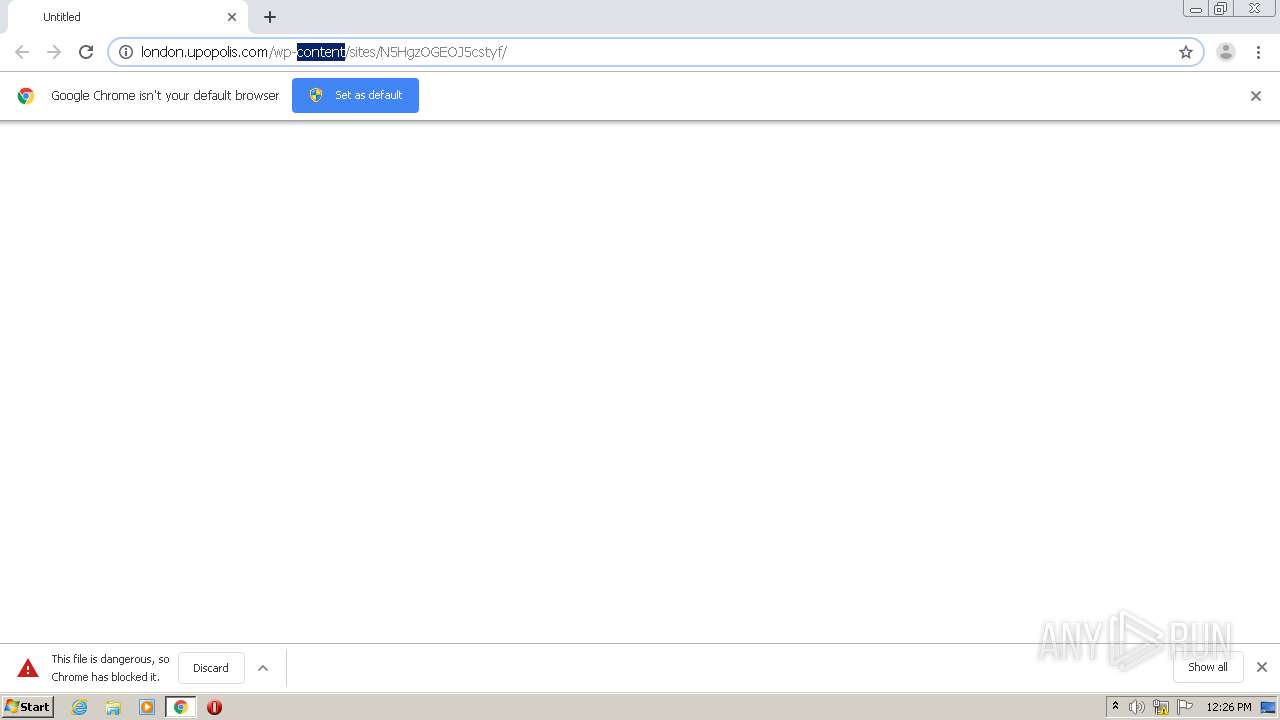
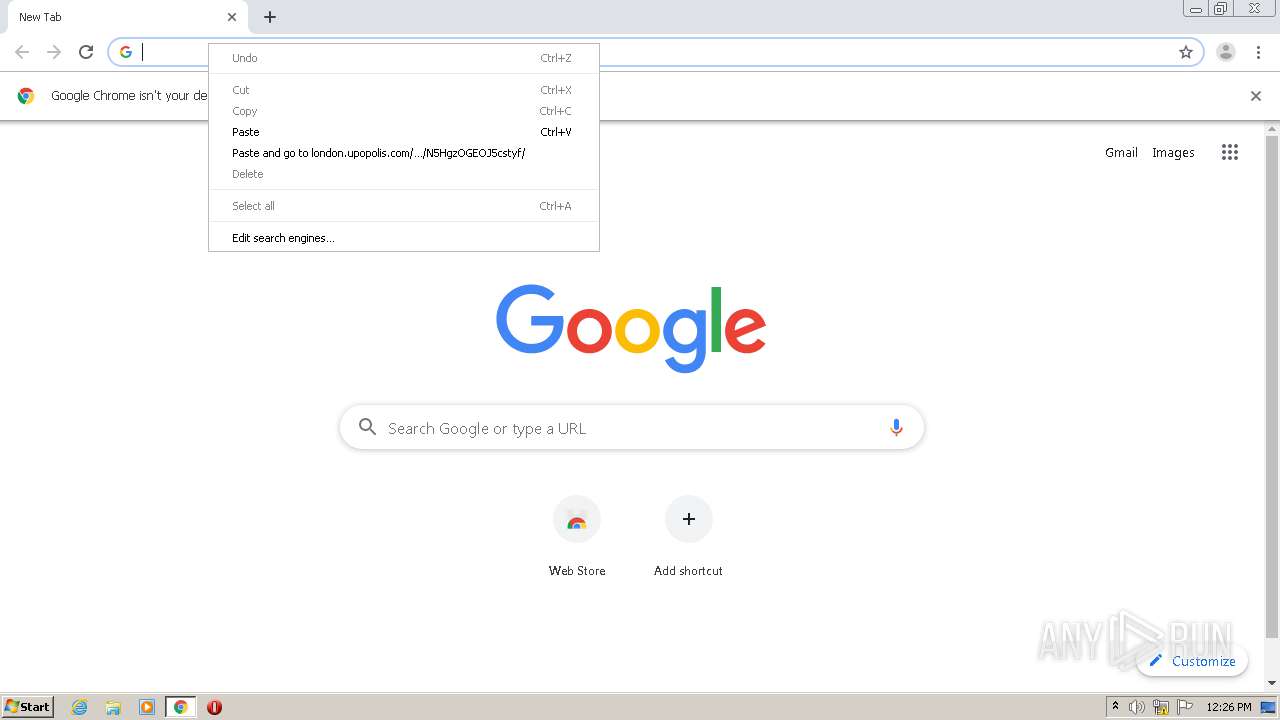
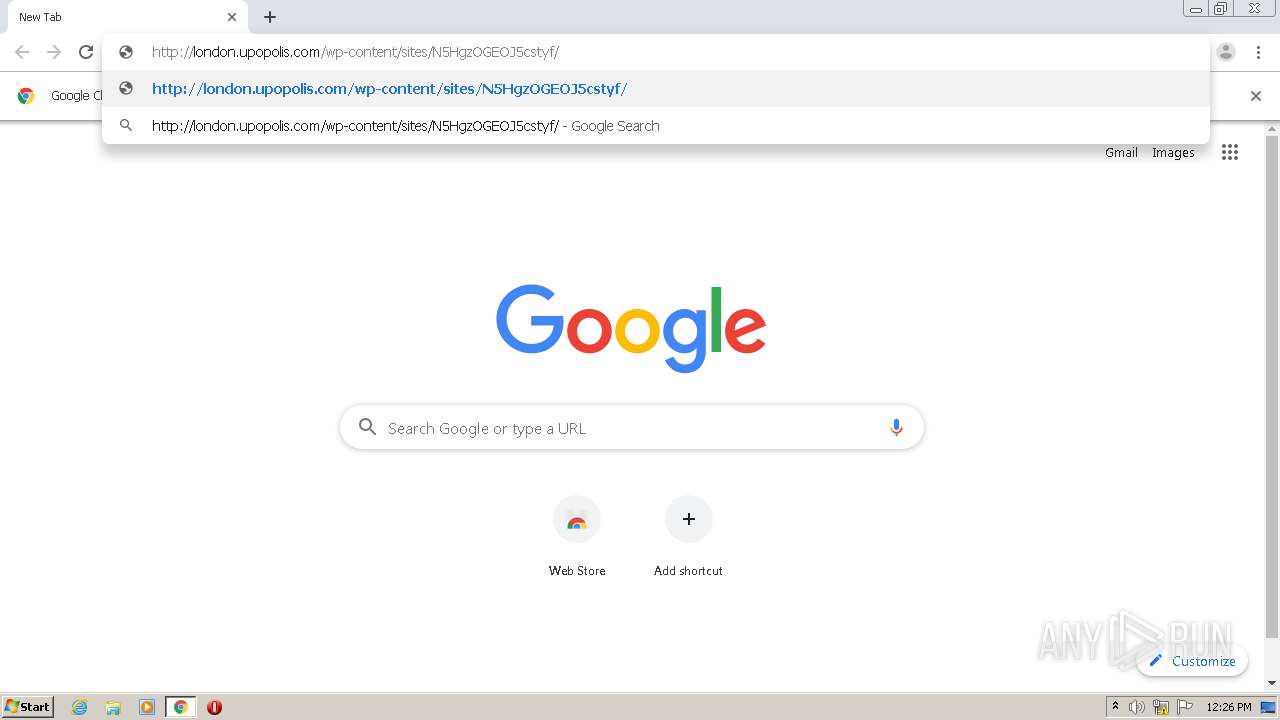
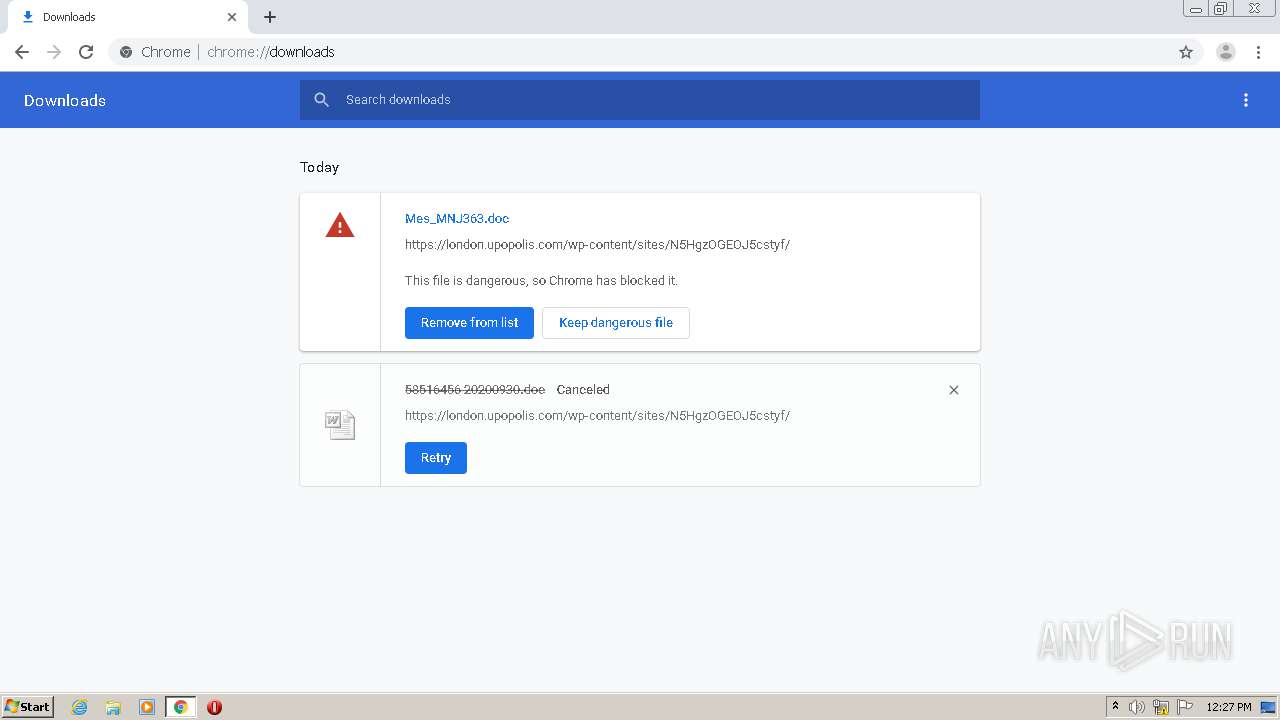
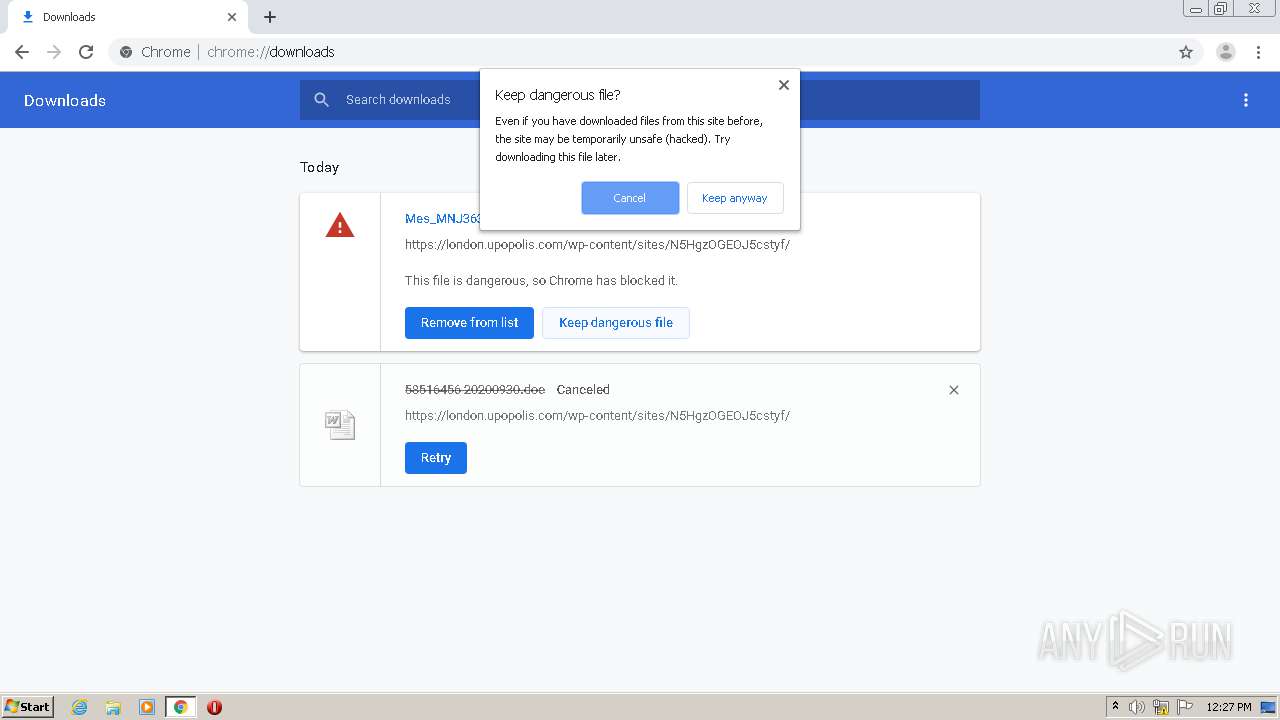
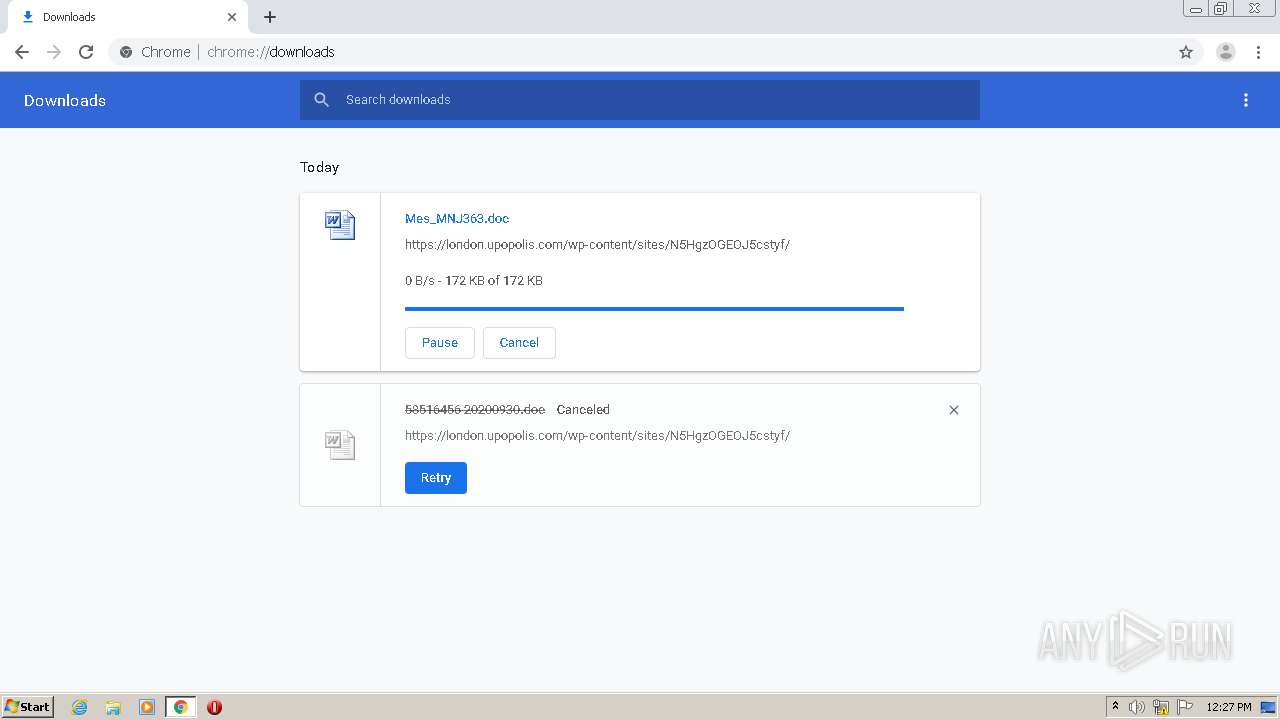
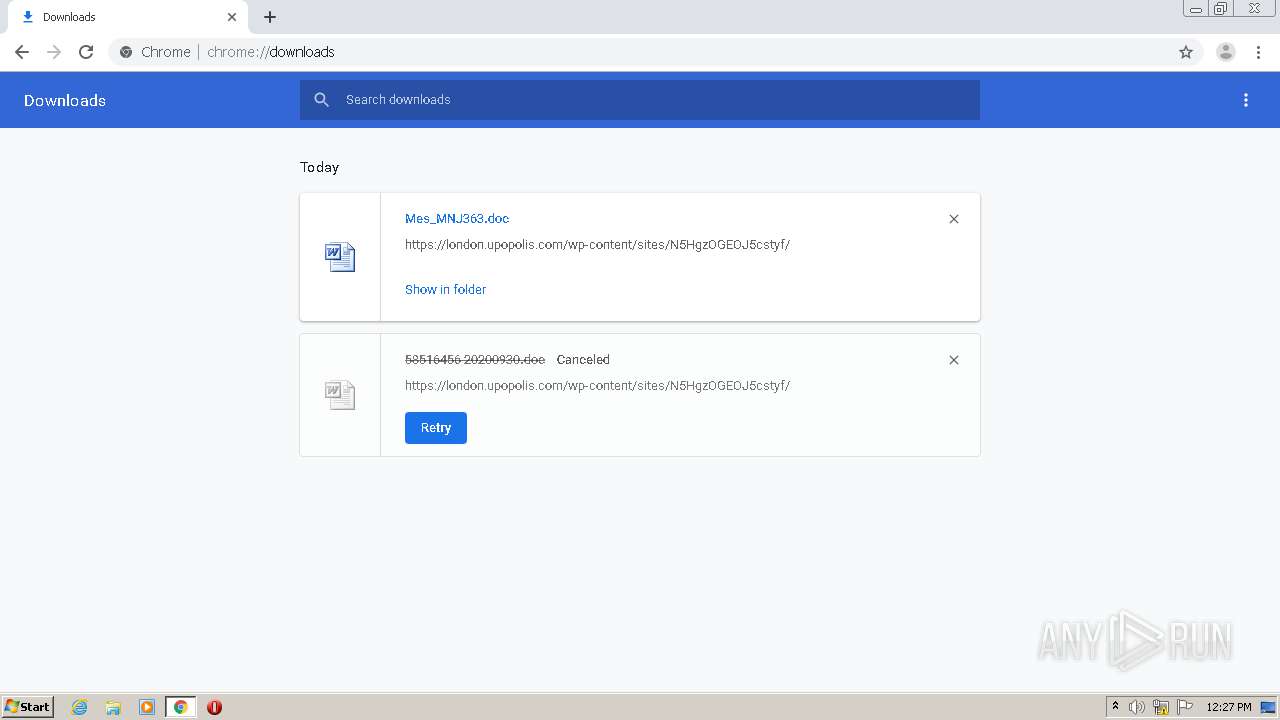
| URL: | http://london.upopolis.com/wp-content/sites/N5HgzOGEOJ5cstyf/ |
| Full analysis: | https://app.any.run/tasks/d5a76389-0bd3-4286-8ec1-246e53a2f403 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 11:25:58 |
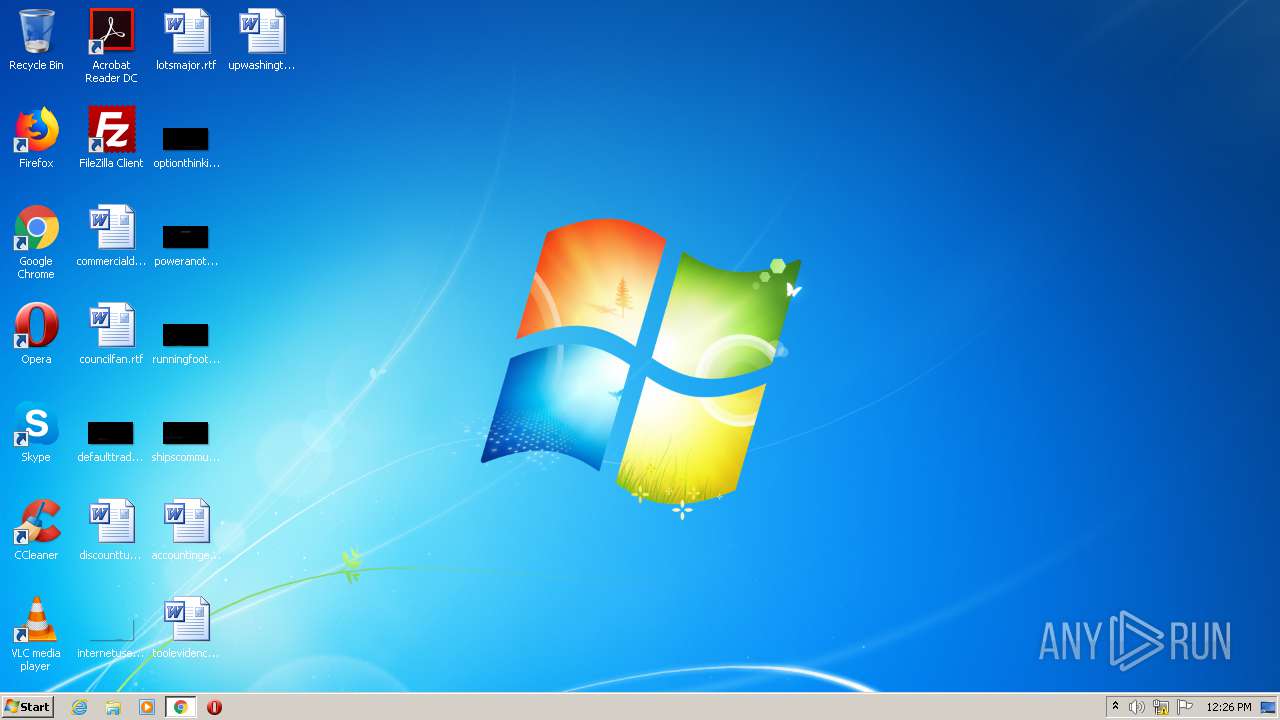
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 341979580D427520A69CB88A1D1FB267 |
| SHA1: | D061E69D923E095E29725CAD3D18B2366EE4EB29 |
| SHA256: | 3B446E1A8FE9AD5C497A1F0A1C37AC8417153585C07185601FED75F8DD87E2AC |
| SSDEEP: | 3:N1KSKLacOKJMM0VOlAQLRmCqIcDK:CSHclJMM0VOlAQcmyK |
MALICIOUS
Application was dropped or rewritten from another process
- Mvgvqd34.exe (PID: 3268)
- ubpm.exe (PID: 760)
Changes the autorun value in the registry
- ubpm.exe (PID: 760)
Connects to CnC server
- ubpm.exe (PID: 760)
EMOTET was detected
- ubpm.exe (PID: 760)
SUSPICIOUS
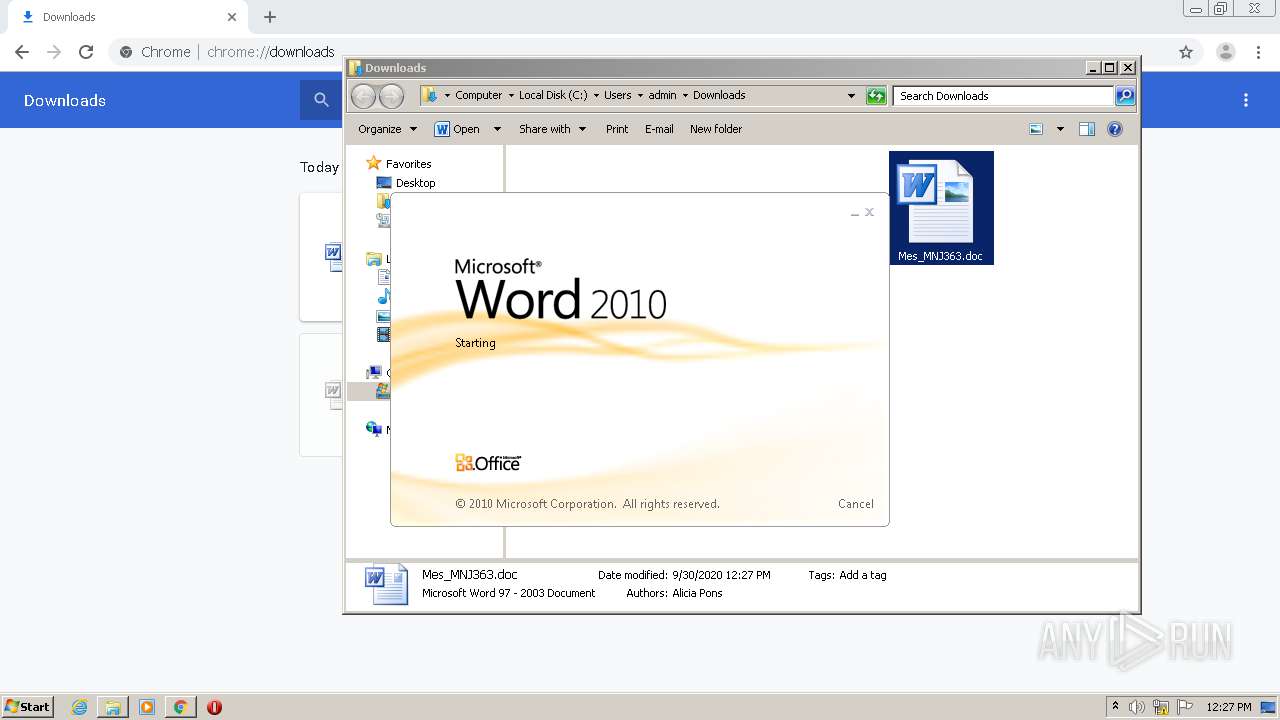
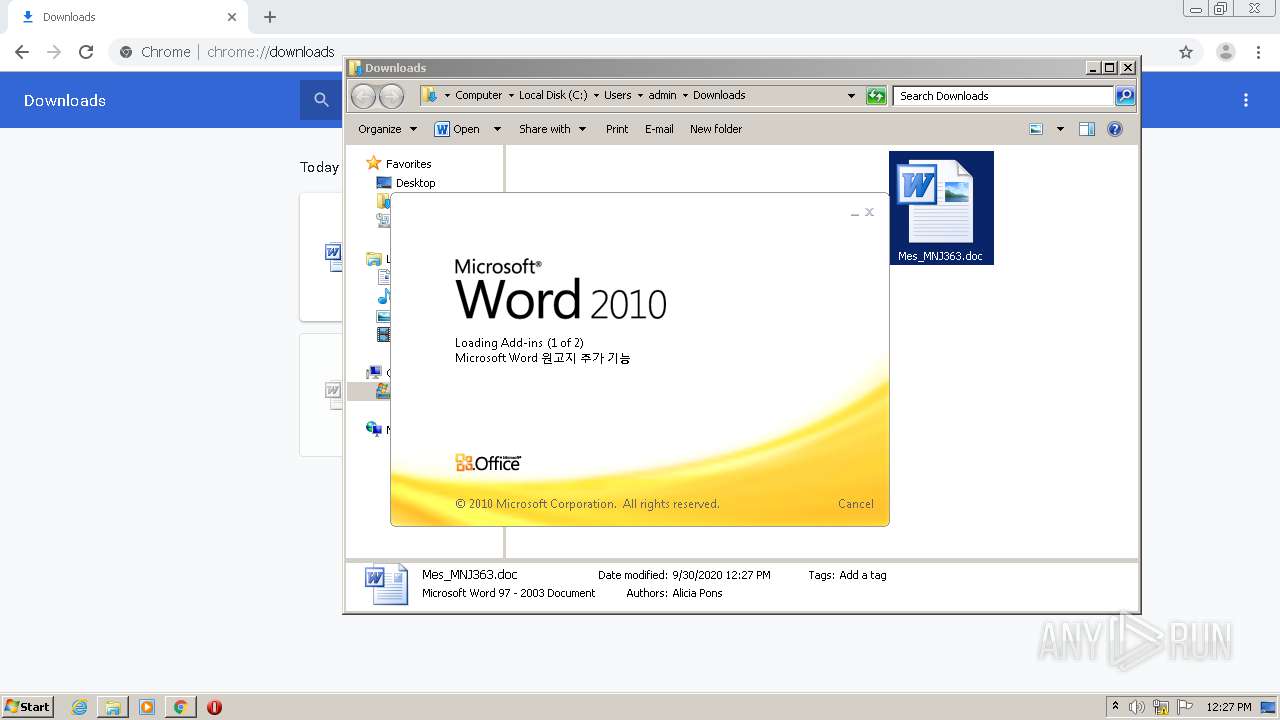
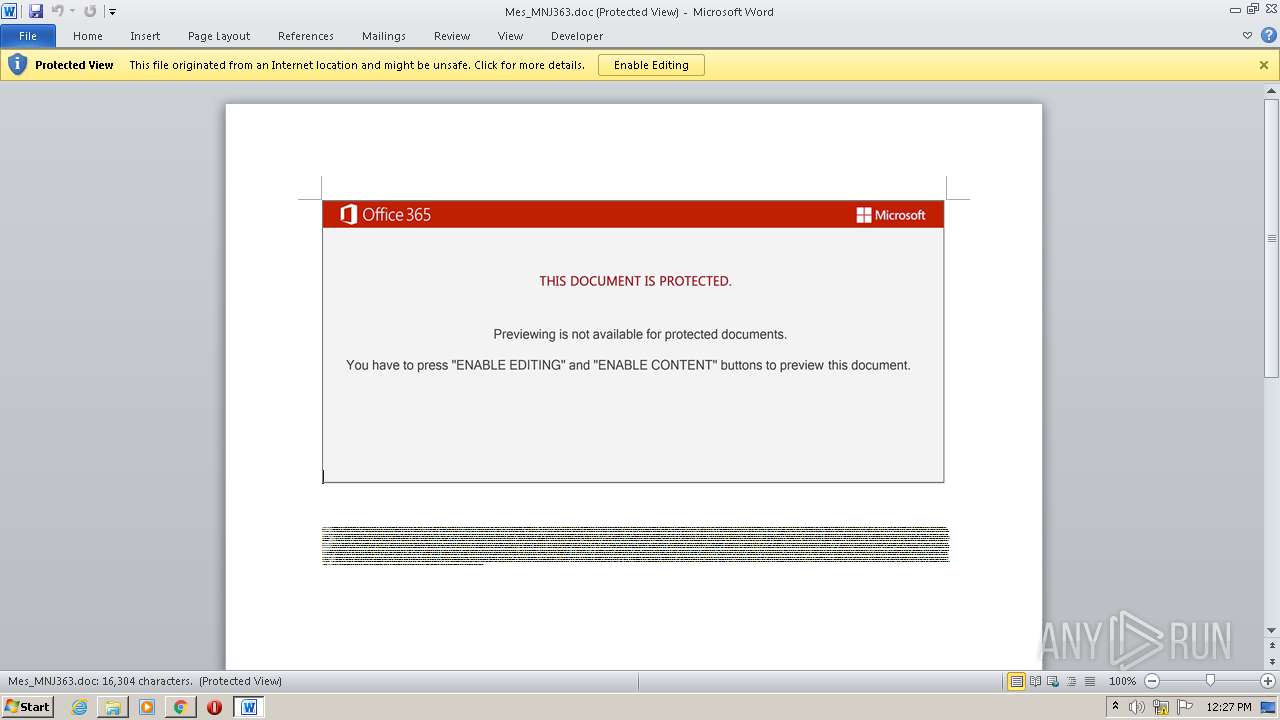
Starts Microsoft Office Application
- WINWORD.EXE (PID: 4008)
Application launched itself
- WINWORD.EXE (PID: 4008)
Starts itself from another location
- Mvgvqd34.exe (PID: 3268)
Creates files in the user directory
- POwersheLL.exe (PID: 1516)
Executed via WMI
- POwersheLL.exe (PID: 1516)
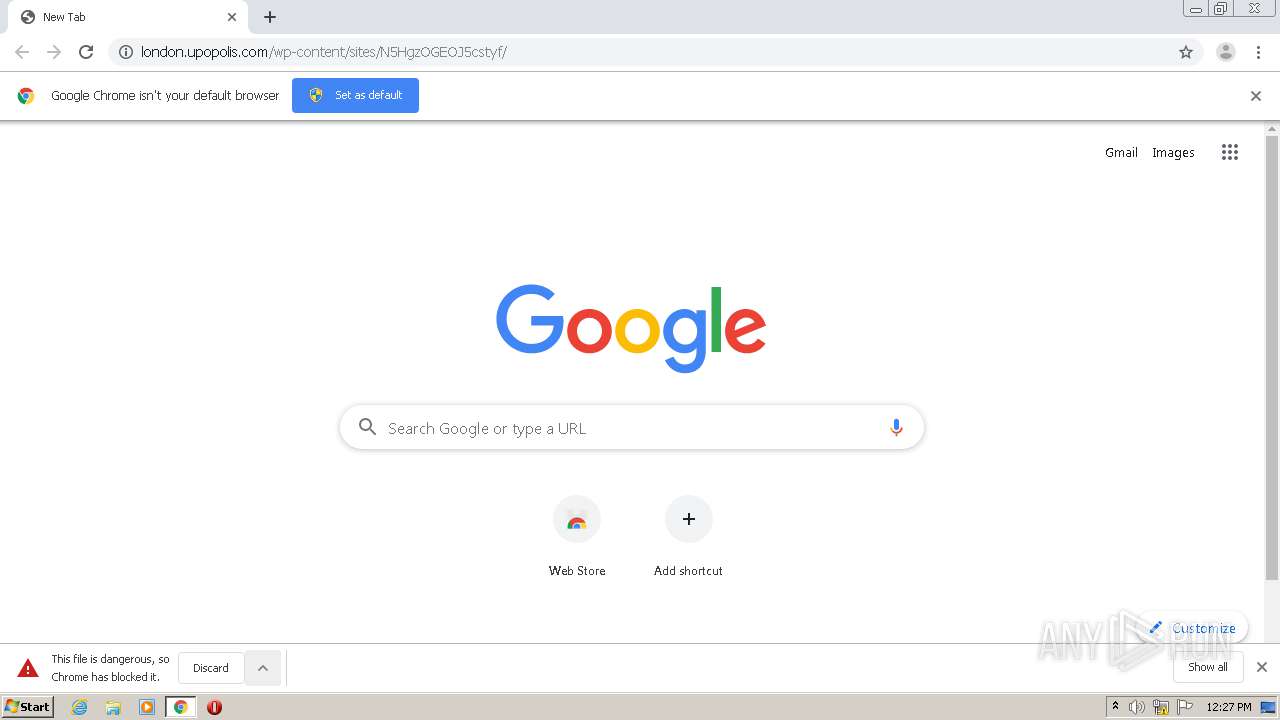
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 1516)
- Mvgvqd34.exe (PID: 3268)
PowerShell script executed
- POwersheLL.exe (PID: 1516)
Reads Internet Cache Settings
- ubpm.exe (PID: 760)
INFO
Reads the hosts file
- chrome.exe (PID: 3180)
- chrome.exe (PID: 3908)
- chrome.exe (PID: 3448)
- chrome.exe (PID: 2336)
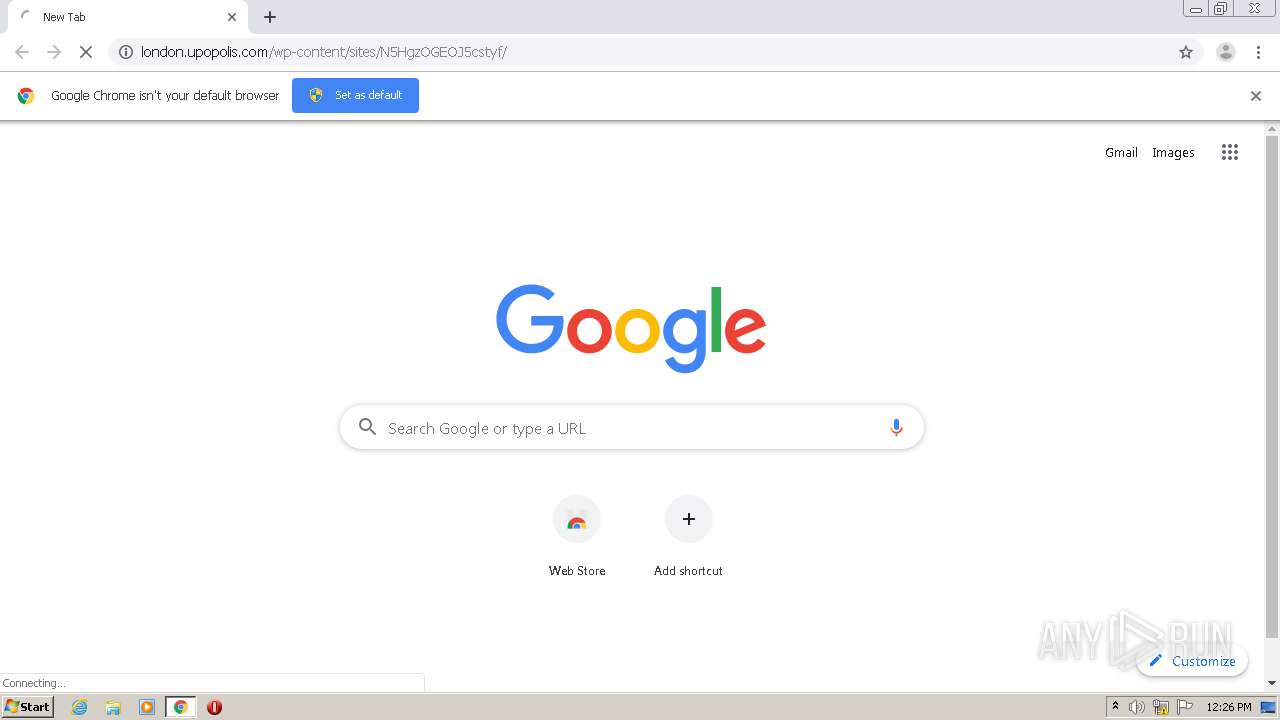
Manual execution by user
- chrome.exe (PID: 3448)
- WINWORD.EXE (PID: 4008)
Application launched itself
- chrome.exe (PID: 3180)
- chrome.exe (PID: 3448)
Reads Internet Cache Settings
- chrome.exe (PID: 3448)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 4008)
- WINWORD.EXE (PID: 3128)
Creates files in the user directory
- WINWORD.EXE (PID: 4008)
Reads settings of System Certificates
- POwersheLL.exe (PID: 1516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
79
Monitored processes
37
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 3180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://london.upopolis.com/wp-content/sites/N5HgzOGEOJ5cstyf/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 | ||||
| 3956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f15a9d0,0x6f15a9e0,0x6f15a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 3532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=828 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 3036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,513536830573471123,15266908378006956909,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2084616574929082953 --mojo-platform-channel-handle=1032 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 3908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,513536830573471123,15266908378006956909,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=17533830396870603931 --mojo-platform-channel-handle=1612 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 3192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,513536830573471123,15266908378006956909,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12515607949646066377 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1692 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 2536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,513536830573471123,15266908378006956909,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=321865719304909040 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2124 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 1932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,513536830573471123,15266908378006956909,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13230553868839534225 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,513536830573471123,15266908378006956909,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8630752113935510725 --mojo-platform-channel-handle=3468 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 3012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,513536830573471123,15266908378006956909,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=8931938537629832991 --mojo-platform-channel-handle=3168 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
Total events
4 436
Read events
3 350
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
49
Text files
161
Unknown types
11
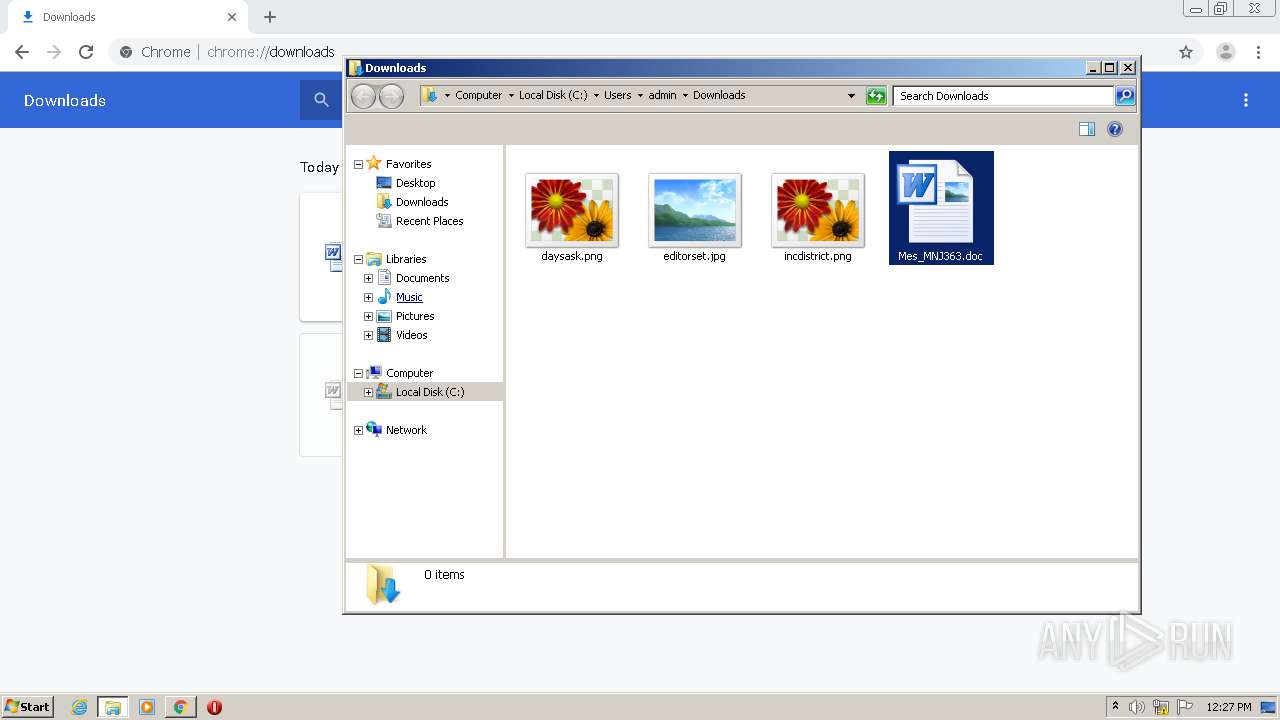
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F746B56-C6C.pma | — | |
MD5:— | SHA256:— | |||
| 3180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\13073448-2e2b-4215-9b02-27b8b9328a5e.tmp | — | |
MD5:— | SHA256:— | |||
| 3180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF3bc14d.TMP | text | |
MD5:4AFC066387D33D5264F8E796393B223B | SHA256:BB3E0F925E883318FB09FC498CACEA57F0F71548C9D42FF07634DC30D87F2D86 | |||
| 3180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:D55489ED6031D8B188E37B0B59F5CED3 | SHA256:365B01D1B3333E366EEA50106551AAC8721156CB2572C173E2F501D8255093F4 | |||
| 3180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:4AFC066387D33D5264F8E796393B223B | SHA256:BB3E0F925E883318FB09FC498CACEA57F0F71548C9D42FF07634DC30D87F2D86 | |||
| 3180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF3bc13d.TMP | text | |
MD5:D55489ED6031D8B188E37B0B59F5CED3 | SHA256:365B01D1B3333E366EEA50106551AAC8721156CB2572C173E2F501D8255093F4 | |||
| 3180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:D33038DC70A58F2AC0EA1823980691AE | SHA256:6EE5DB5588EB879D13CE5A0DB3CA1744079C1BE3F73959A3B900684C56061D97 | |||
| 3180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF3bc218.TMP | text | |
MD5:3401B14F6B2624E5E44EB20FB8735443 | SHA256:E32F20AE6528B8952EE2FF112DACEE4E9005868B7DAF85D3533B6F0135403875 | |||
| 3180 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF3bc1ca.TMP | text | |
MD5:C5C3F347BDC11EA7A5BF62BCEA89896F | SHA256:EAE604A1C662FF82AD4B2D1056179FD77587159FDD7F1674404C0465E0610BC1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
45
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3908 | chrome.exe | GET | 301 | 206.162.161.204:80 | http://london.upopolis.com/wp-content/sites/N5HgzOGEOJ5cstyf/ | CA | html | 270 b | unknown |
760 | ubpm.exe | POST | 200 | 202.22.141.45:80 | http://202.22.141.45/PQhHE12ZxL2NPZh1/4oz4efJ59WrLn/A0nN3ST2uyE5s3H/VoRHmGaiKo3f6/tKKedPLAKJF6lQhXMMr/ | NC | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3908 | chrome.exe | 142.250.74.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3908 | chrome.exe | 206.162.161.204:80 | london.upopolis.com | TELUS Communications Inc. | CA | unknown |
3908 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
3908 | chrome.exe | 206.162.161.204:443 | london.upopolis.com | TELUS Communications Inc. | CA | unknown |
3908 | chrome.exe | 216.58.212.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3908 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3908 | chrome.exe | 216.58.207.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2336 | chrome.exe | 172.217.16.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2336 | chrome.exe | 206.162.161.204:80 | london.upopolis.com | TELUS Communications Inc. | CA | unknown |
2336 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
london.upopolis.com |
| unknown |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
760 | ubpm.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |