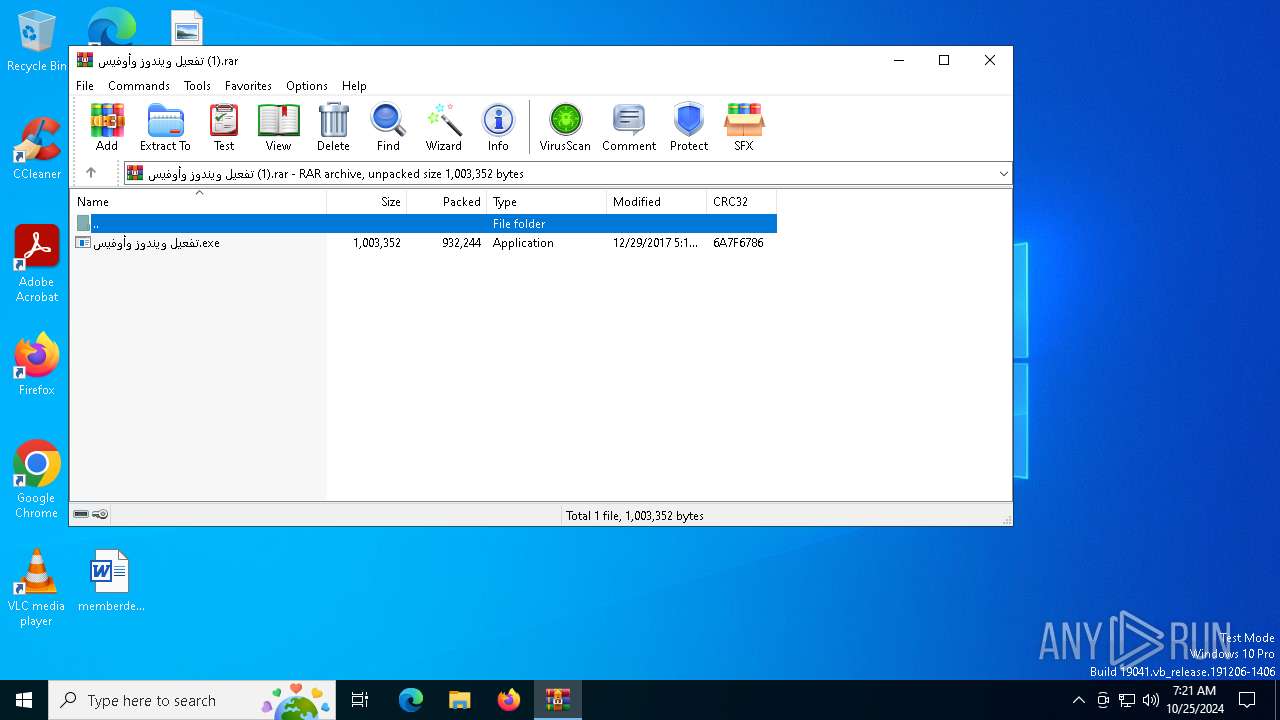
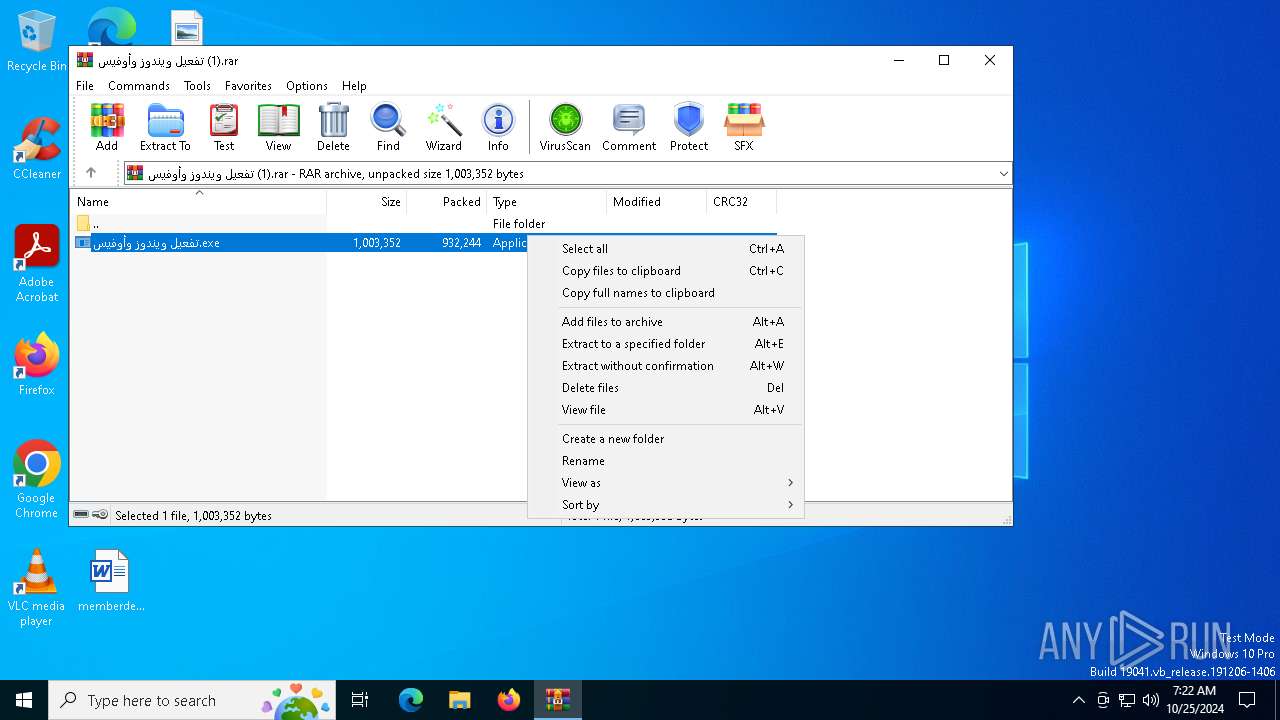
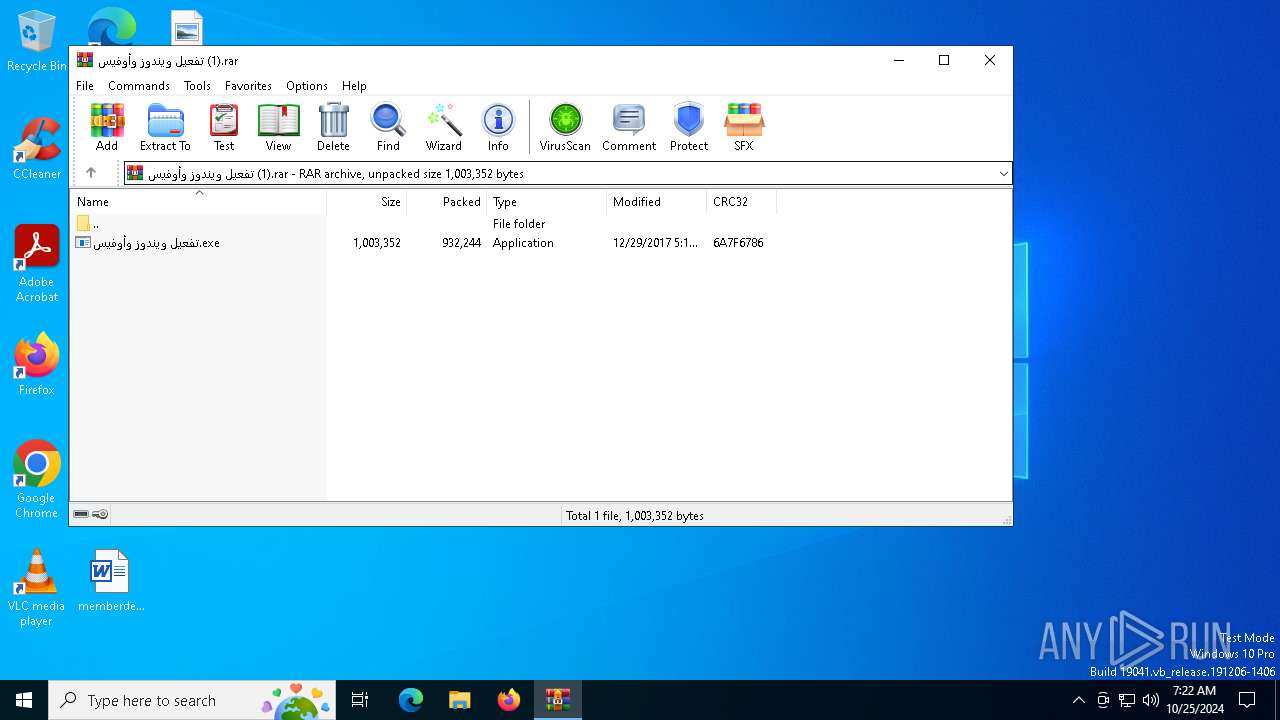
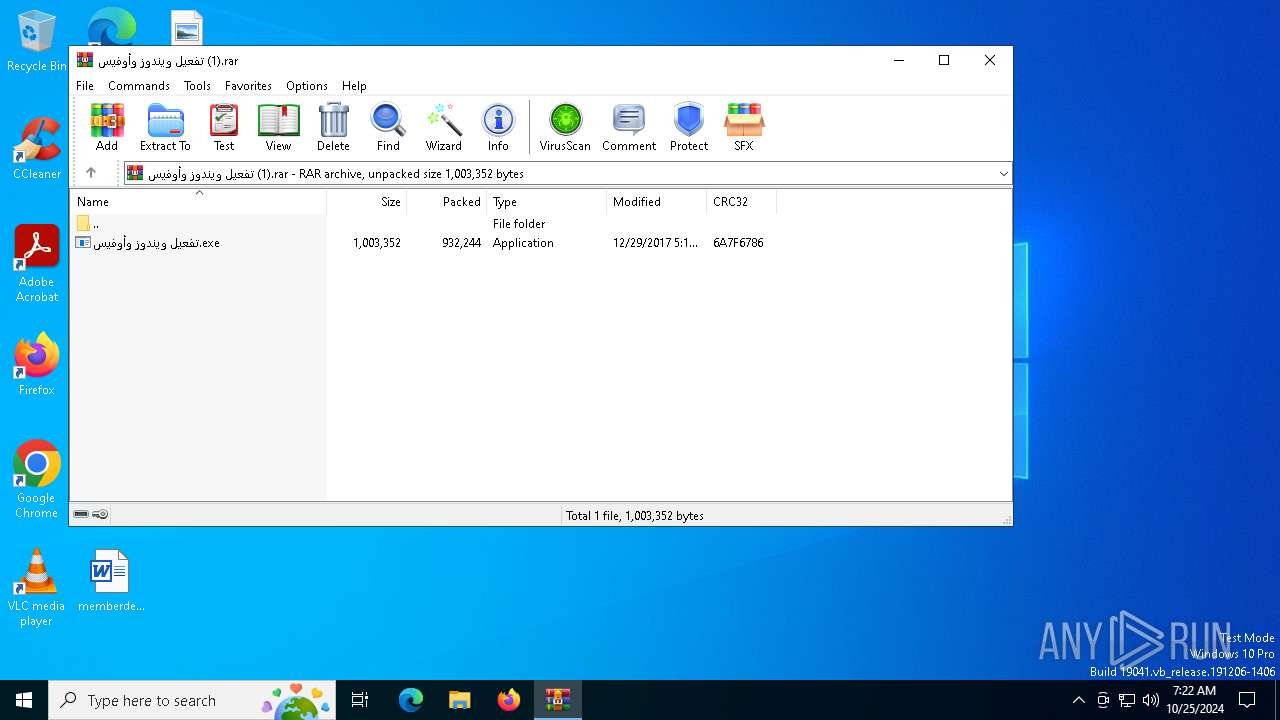
| File name: | تفعيل ويندوز وأوفيس (1).rar |
| Full analysis: | https://app.any.run/tasks/41edcff4-ab83-48bb-a432-d99d1c4dd73a |
| Verdict: | Malicious activity |
| Analysis date: | October 25, 2024, 07:21:46 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 0A743D9895BBE13977D9B8C0D3ACD54B |
| SHA1: | 80D51AE0E33BE35702E28EB1B3FF86892BDC90EC |
| SHA256: | 3B1FA2F68ED51FE5738CDD02EA423BB470B4573AE1000566E5A2B62660A628C2 |
| SSDEEP: | 49152:7ZoXebMPi8Jd8QeaTlpE5W5o2AB8sTDoAr0xeqGCd5ZgtyMasaqjMhHPxvPFjgN3:7ZGebSi8Afa7E5W5o2ABLLrKeqFd5iaM |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6316)
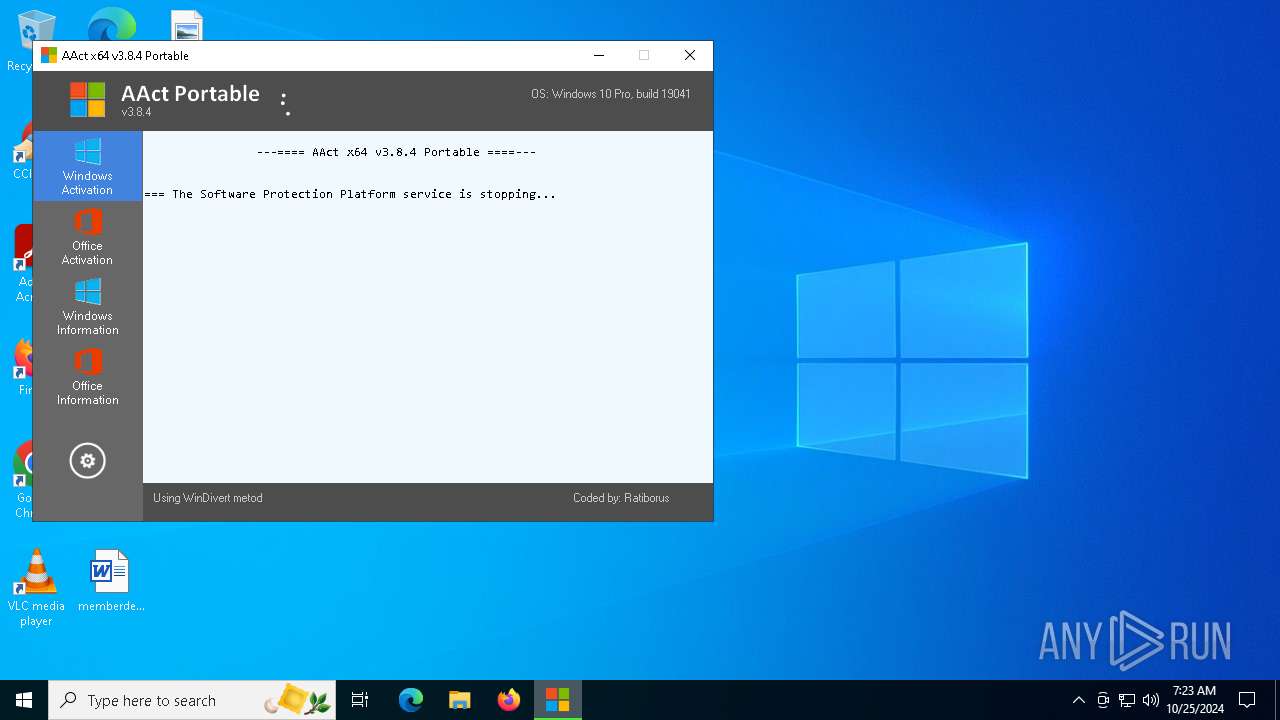
Starts NET.EXE for service management
- cmd.exe (PID: 6180)
- net.exe (PID: 4076)
- cmd.exe (PID: 4408)
- net.exe (PID: 5236)
SUSPICIOUS
Starts SC.EXE for service management
- cmd.exe (PID: 4508)
- cmd.exe (PID: 4568)
- cmd.exe (PID: 1880)
- cmd.exe (PID: 4812)
- cmd.exe (PID: 848)
- cmd.exe (PID: 3788)
- cmd.exe (PID: 6292)
- cmd.exe (PID: 6132)
- cmd.exe (PID: 3772)
- cmd.exe (PID: 6556)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6164)
- cmd.exe (PID: 6416)
- cmd.exe (PID: 5048)
- cmd.exe (PID: 2708)
- cmd.exe (PID: 3508)
- cmd.exe (PID: 2132)
- cmd.exe (PID: 6736)
- cmd.exe (PID: 2124)
- cmd.exe (PID: 6972)
- cmd.exe (PID: 2444)
- cmd.exe (PID: 6176)
- cmd.exe (PID: 6328)
- cmd.exe (PID: 2724)
Uses ROUTE.EXE to obtain the routing table information
- cmd.exe (PID: 5372)
- cmd.exe (PID: 4072)
- cmd.exe (PID: 300)
- cmd.exe (PID: 3396)
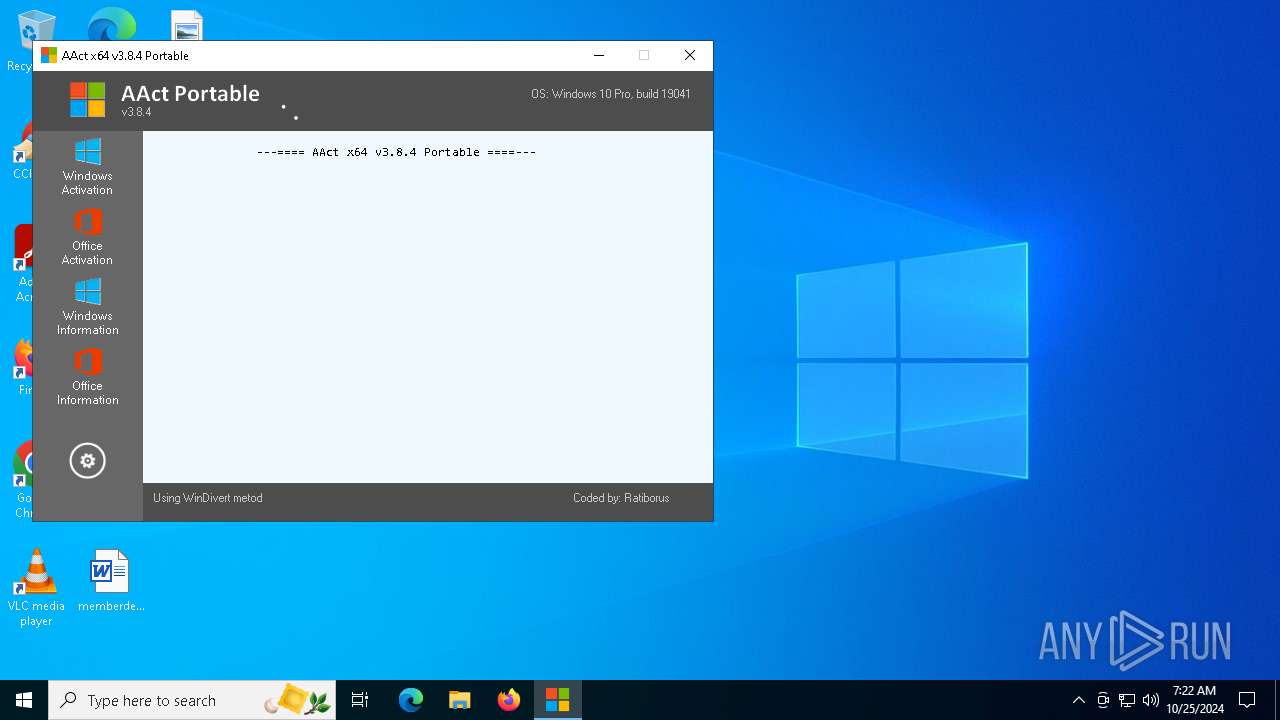
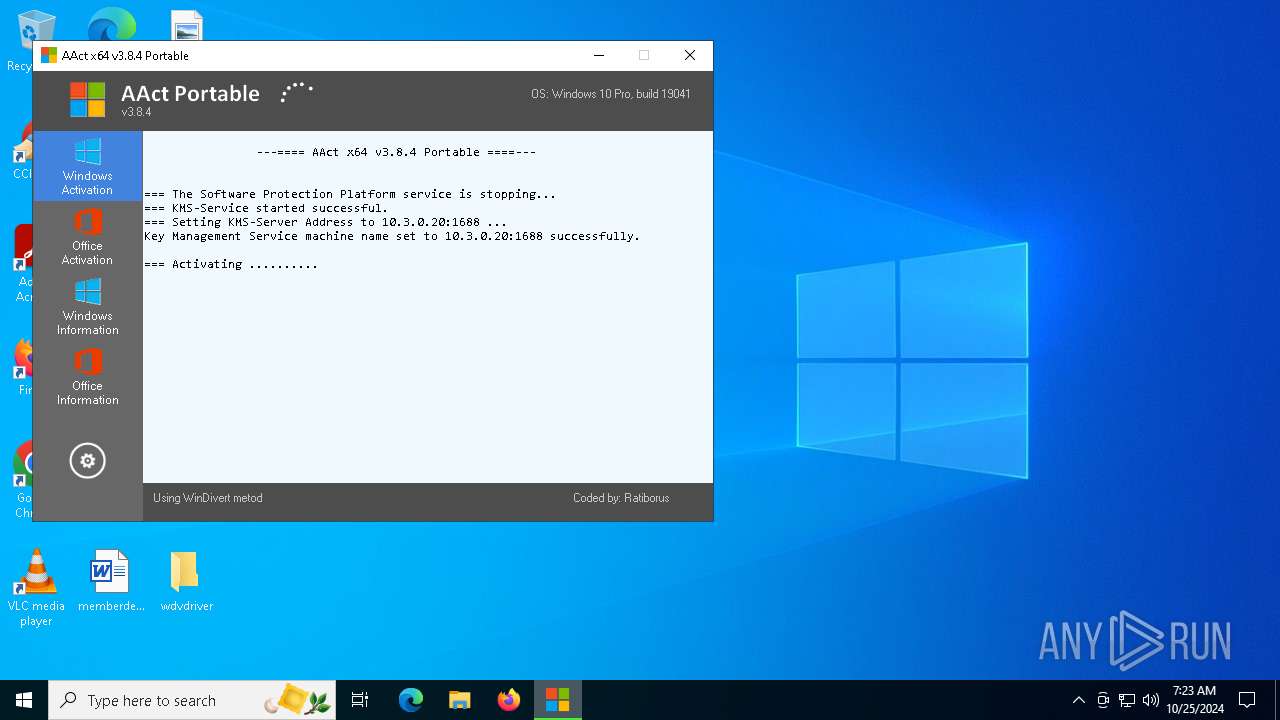
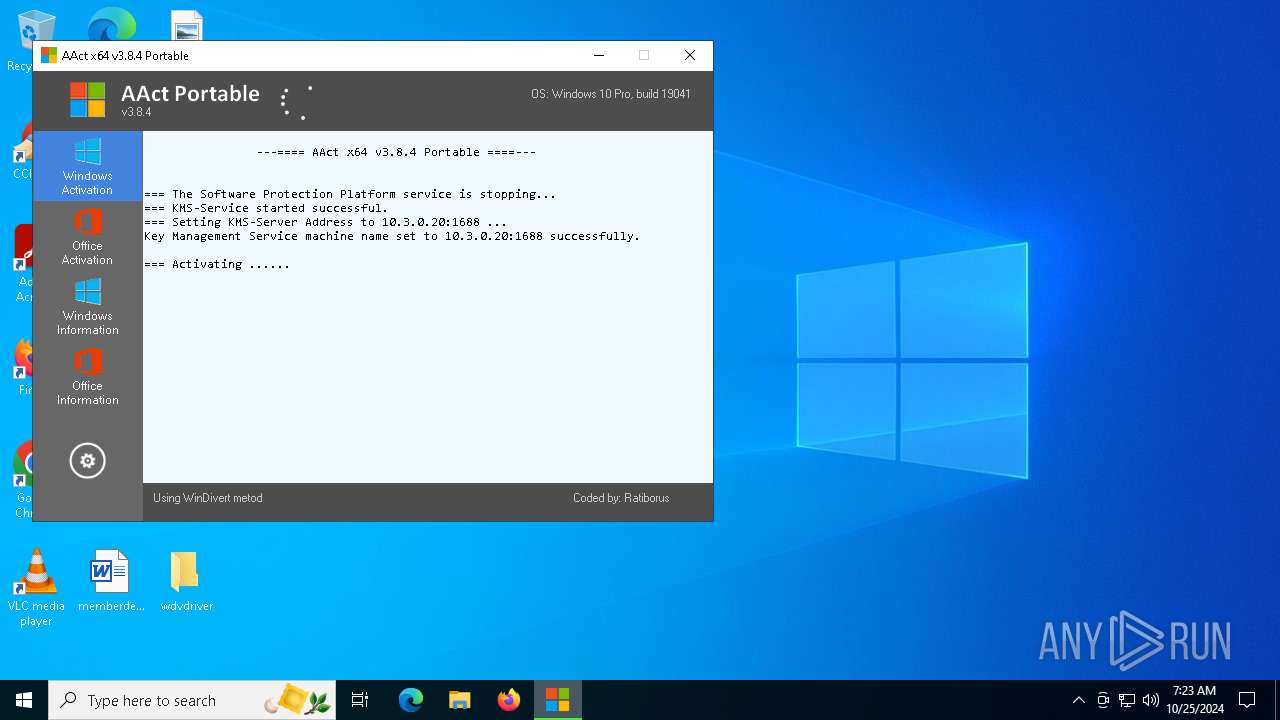
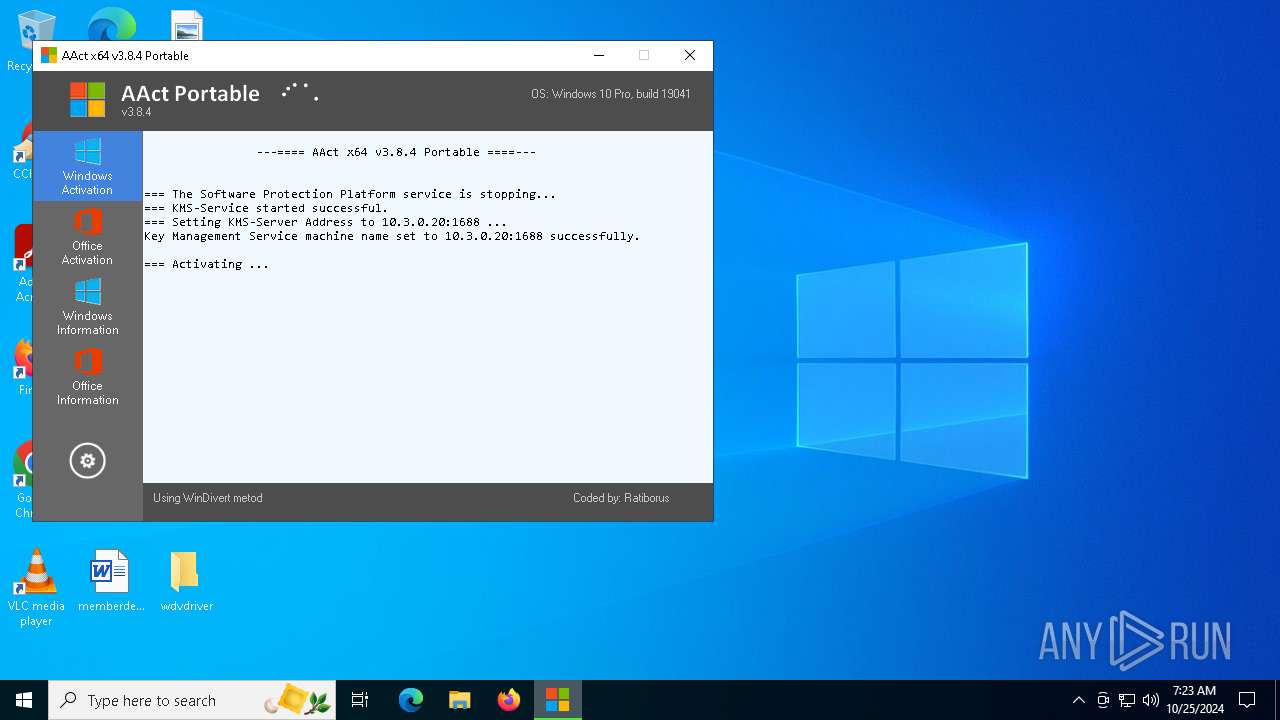
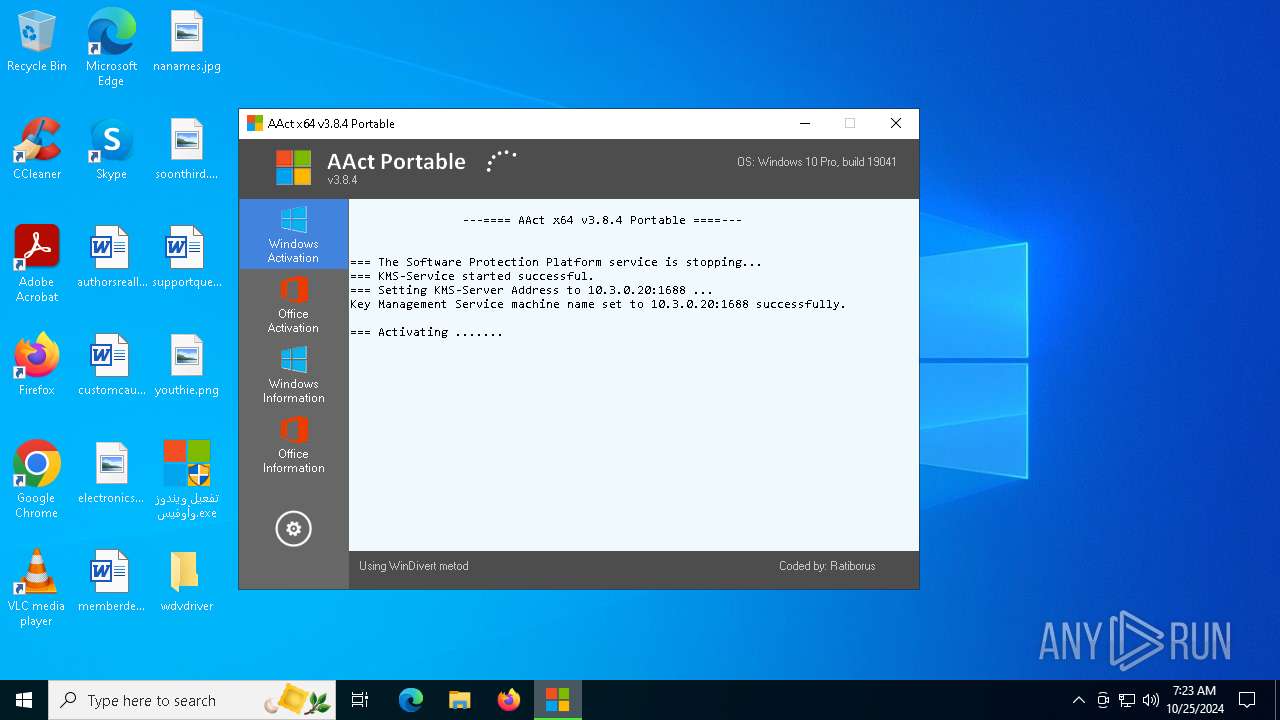
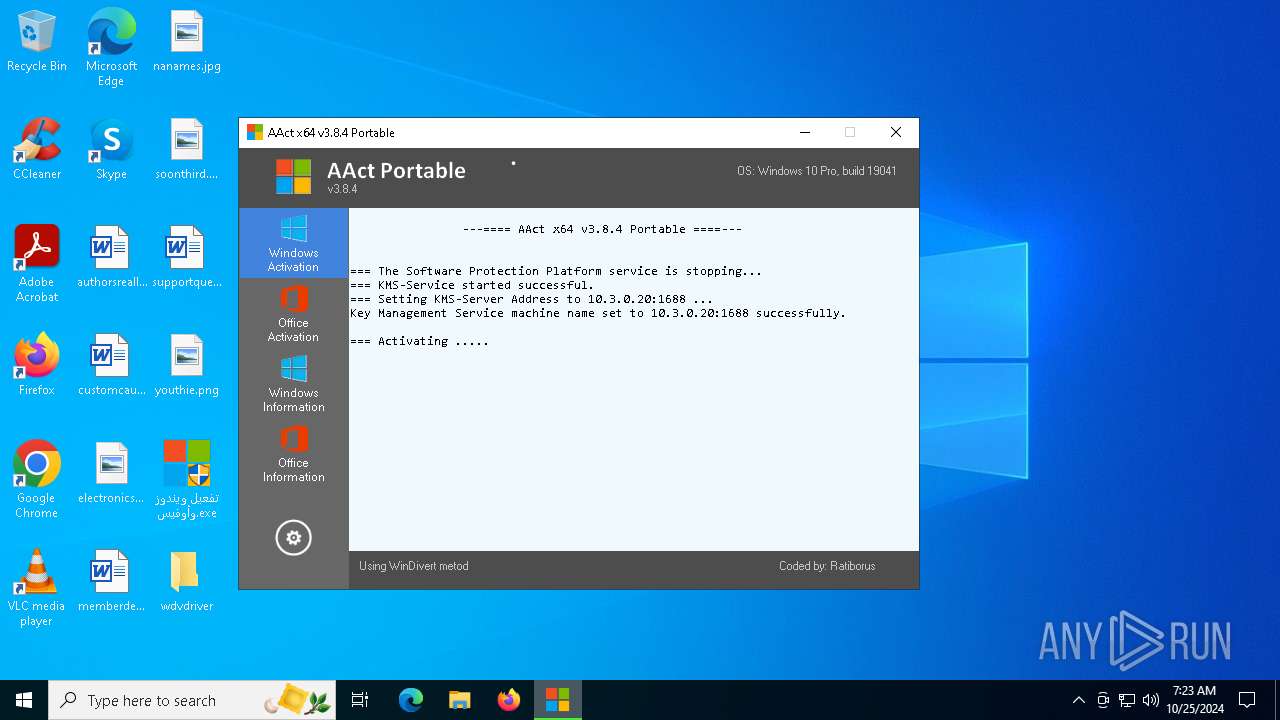
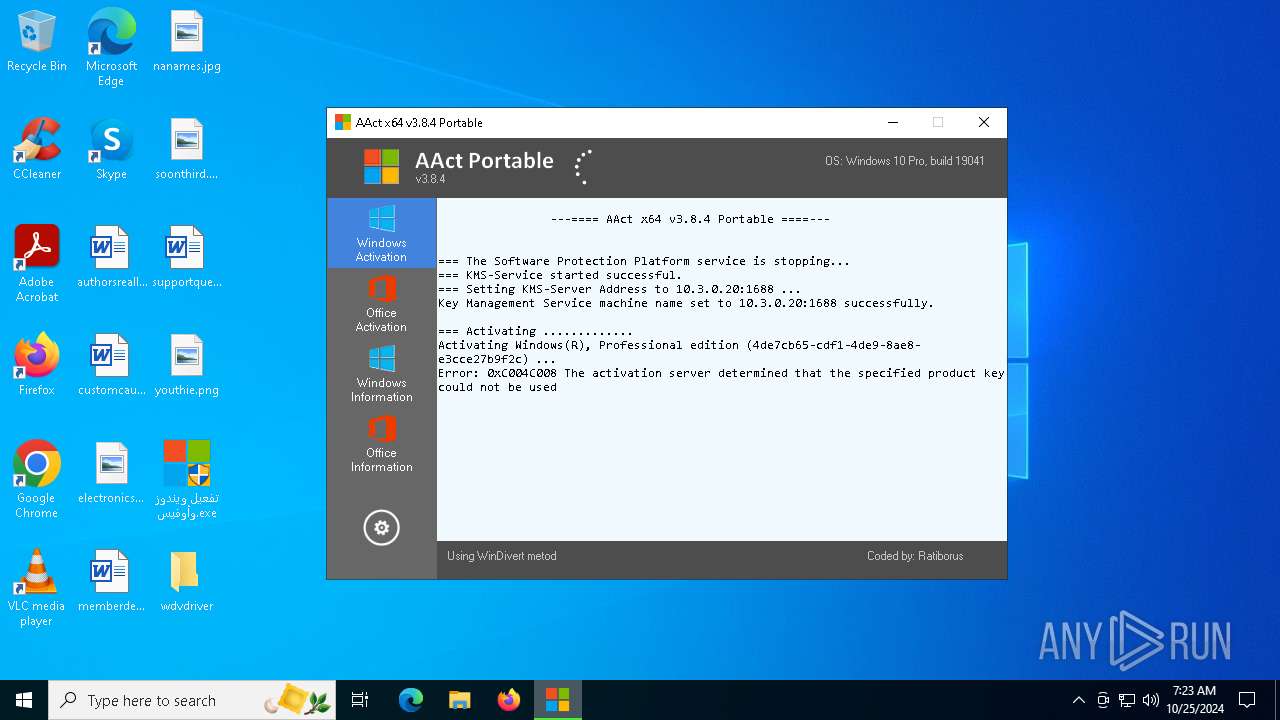
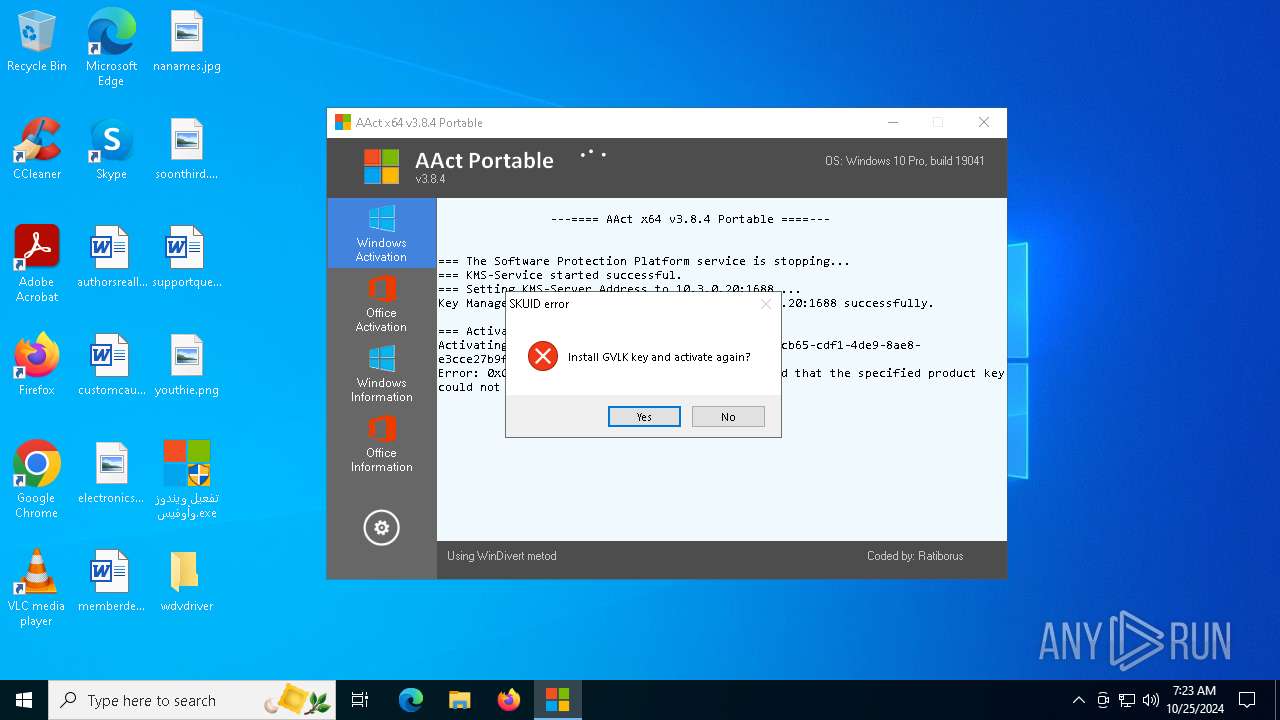
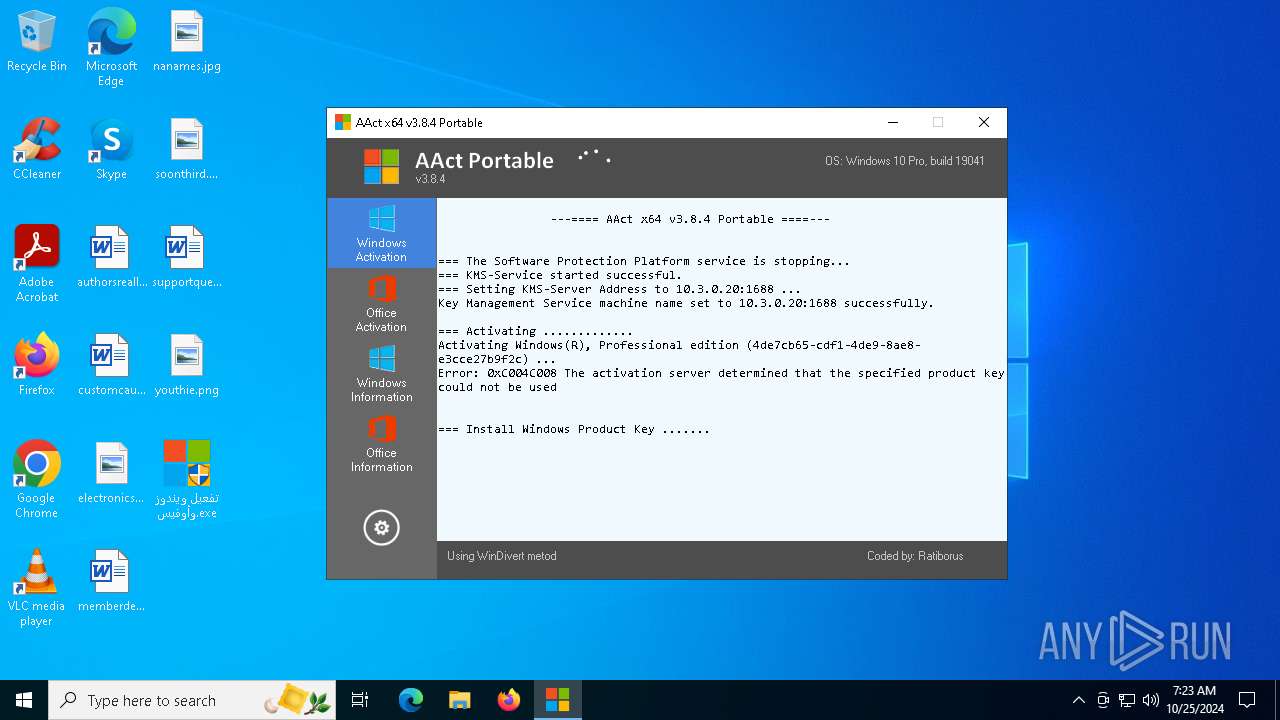
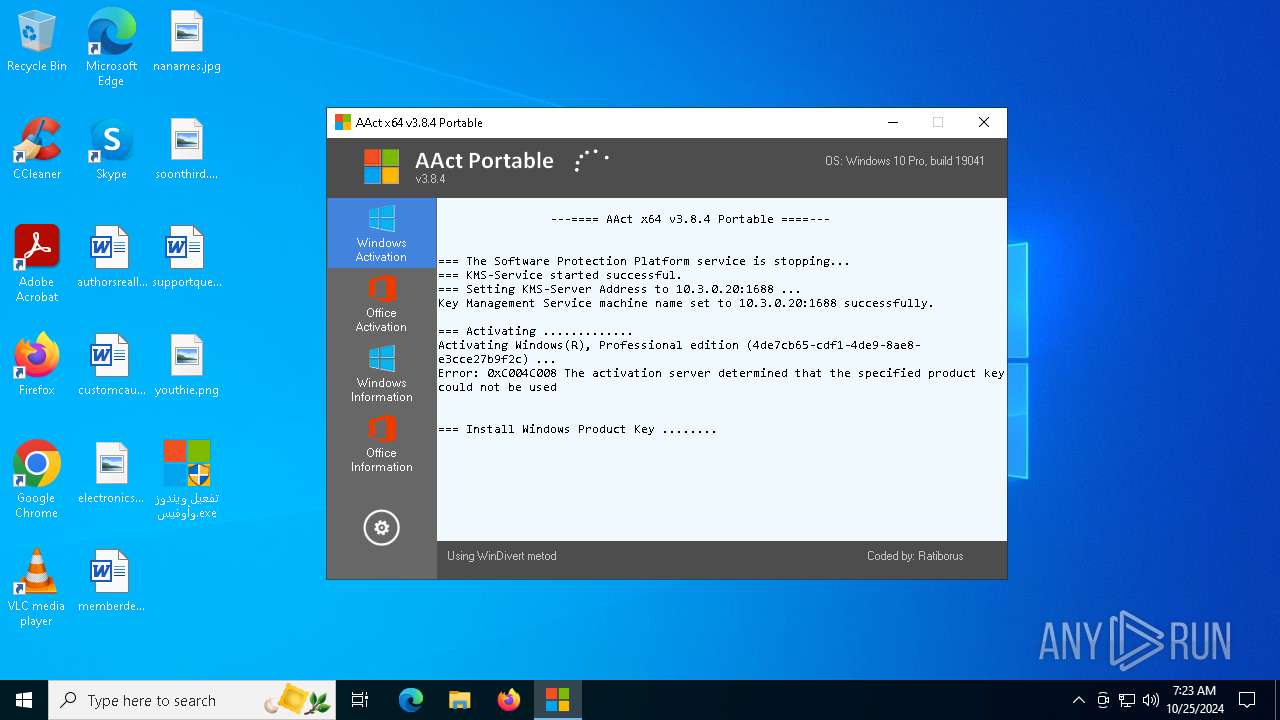
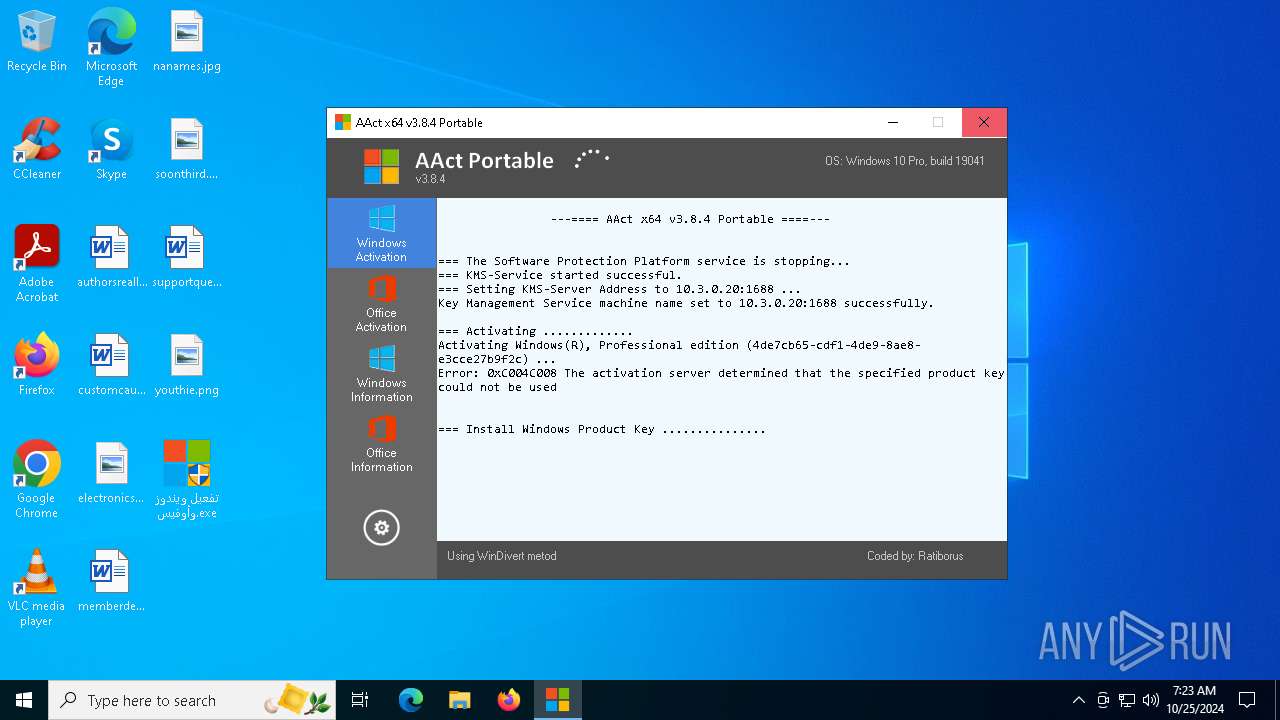
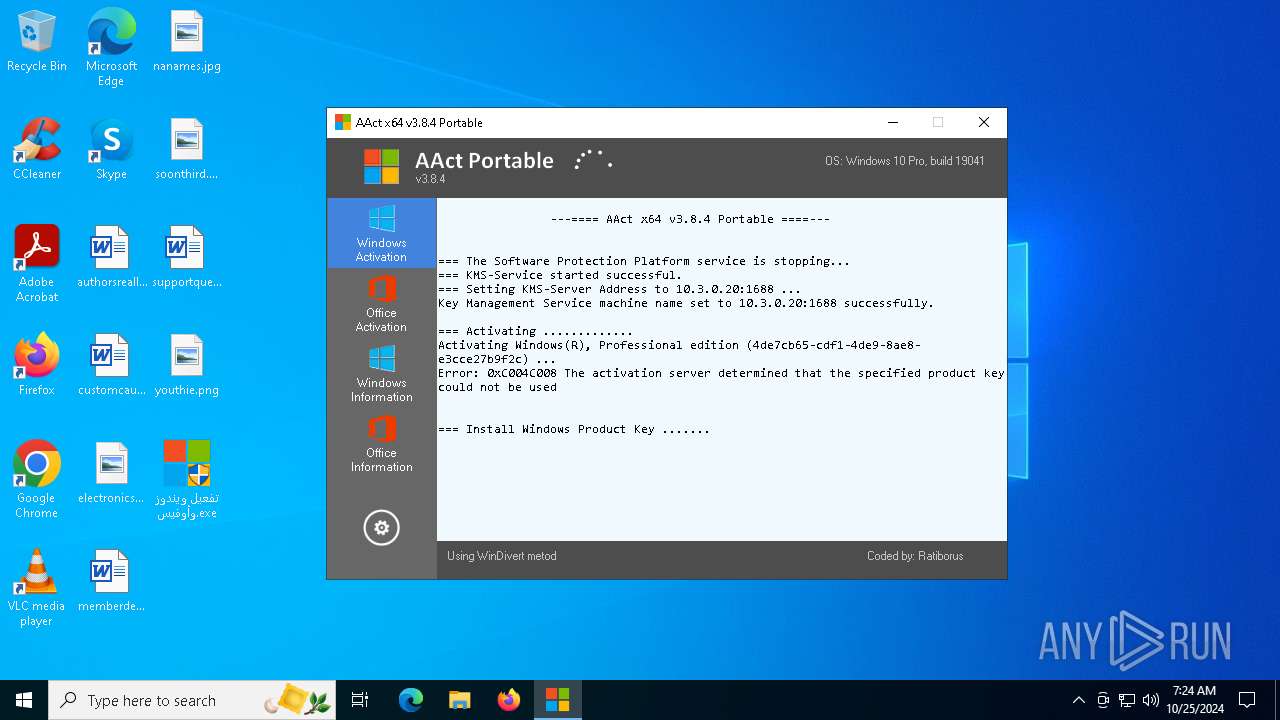
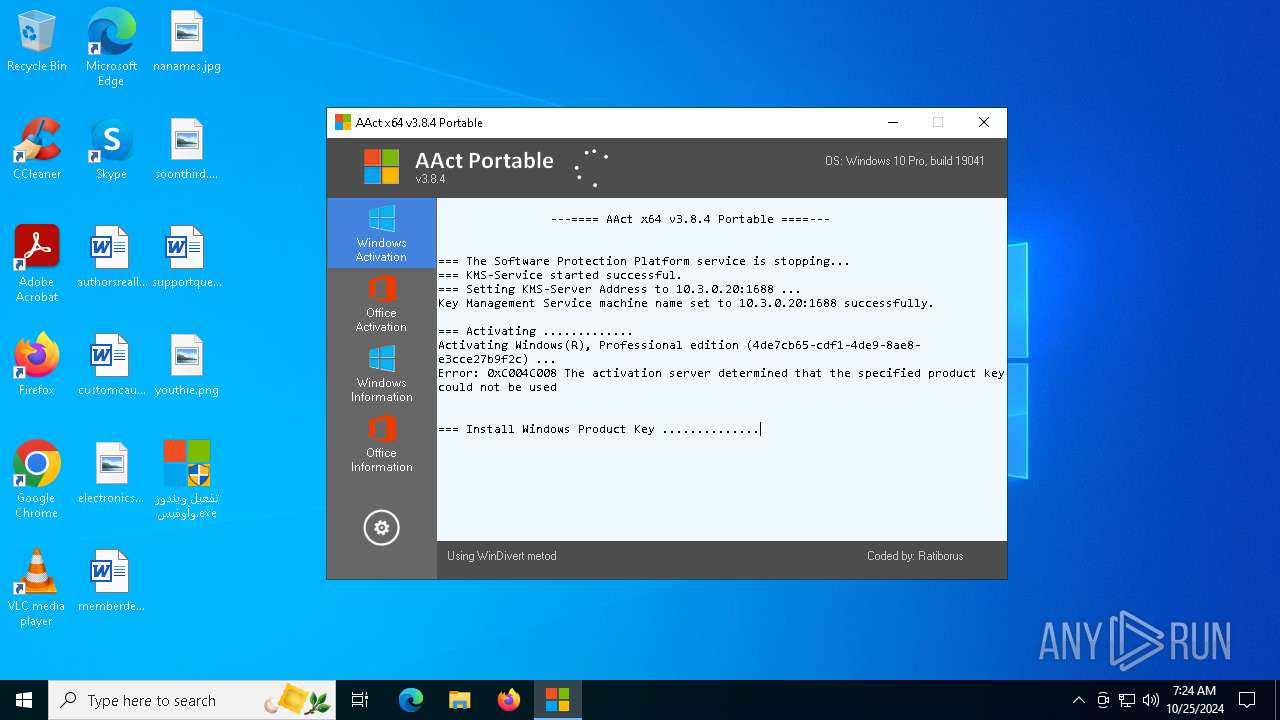
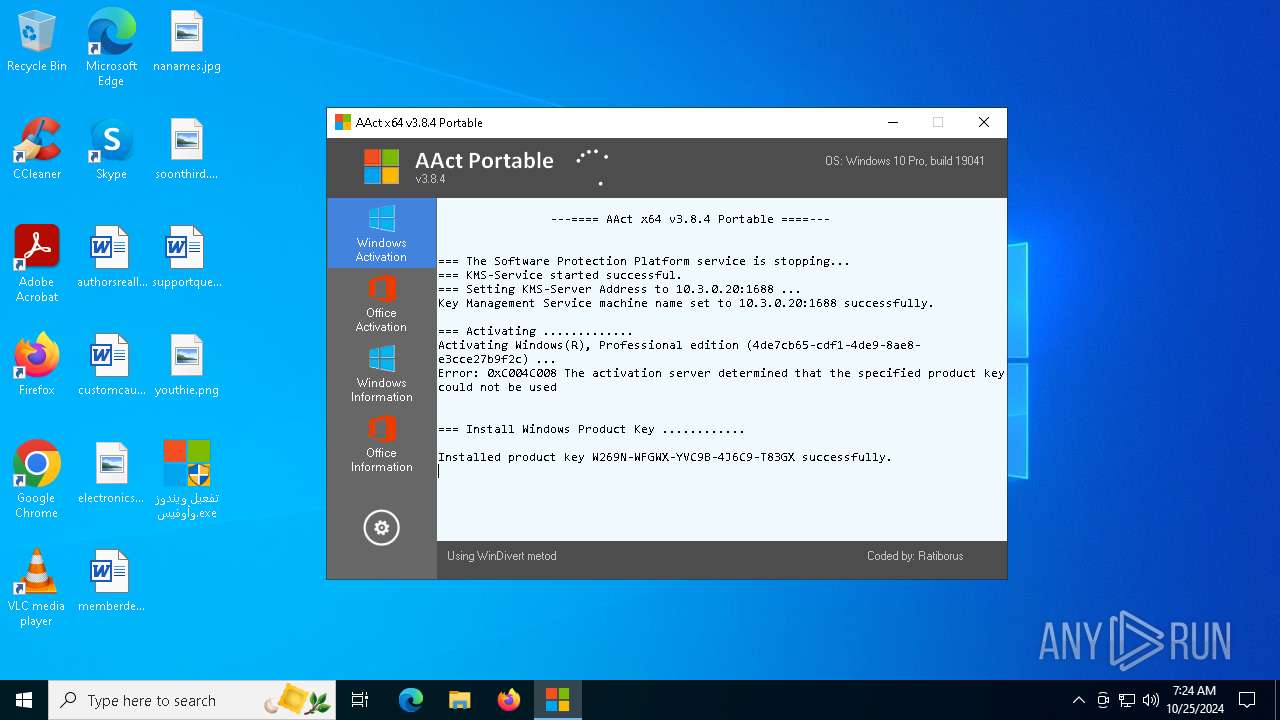
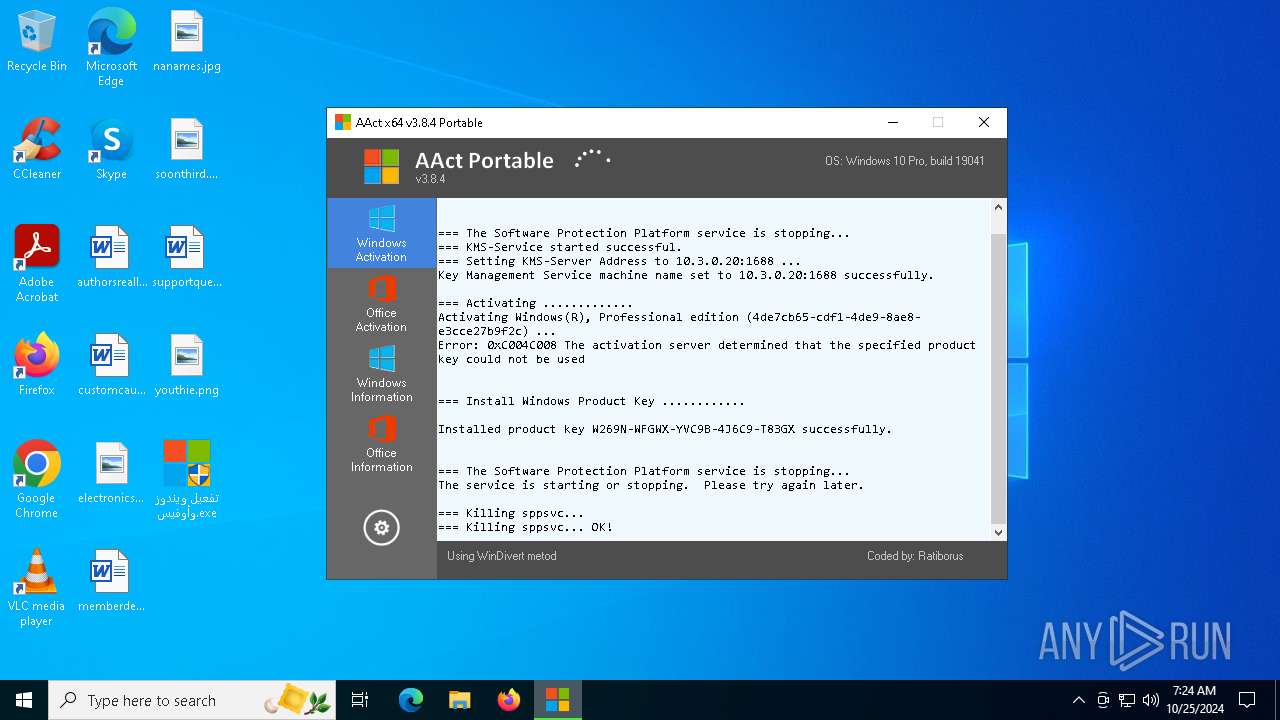
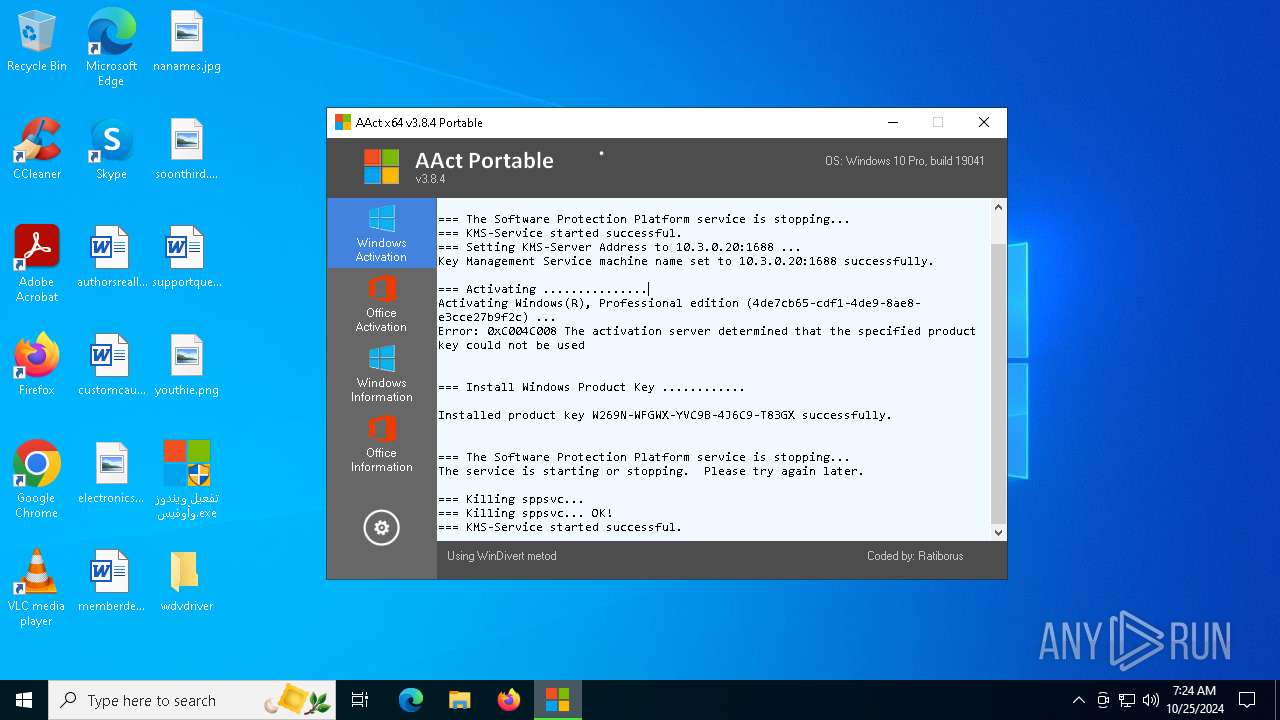
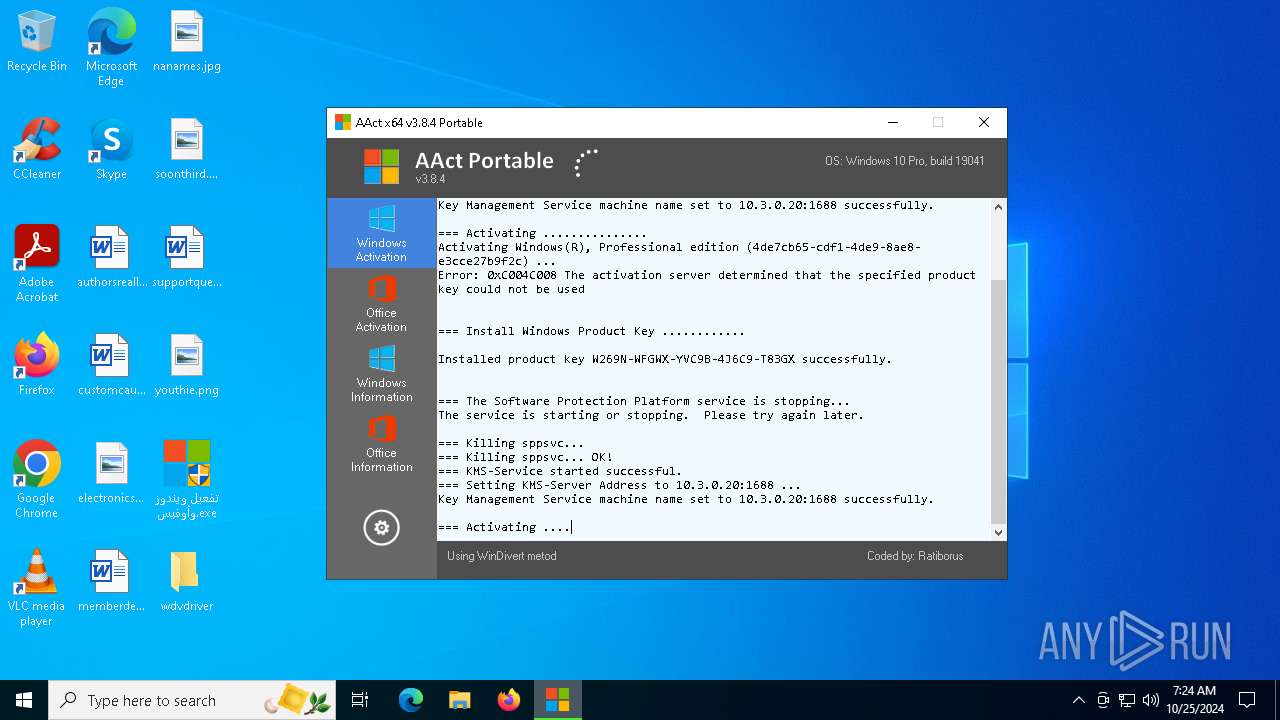
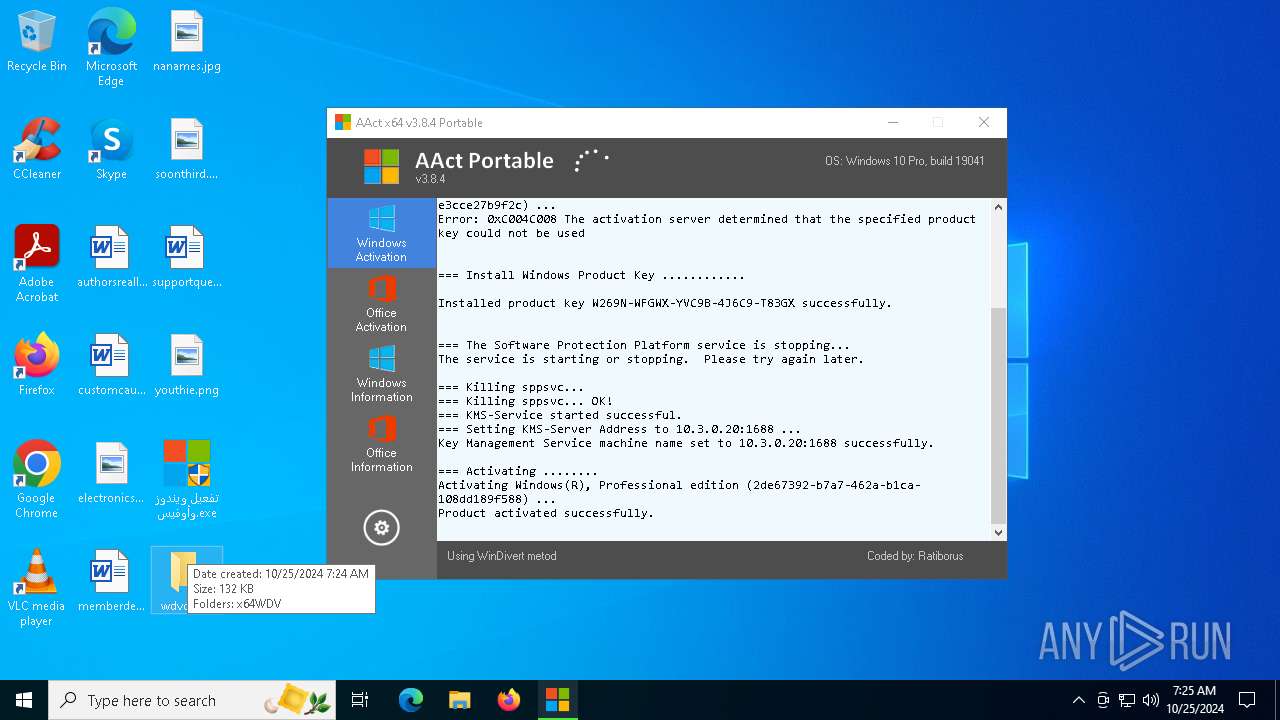
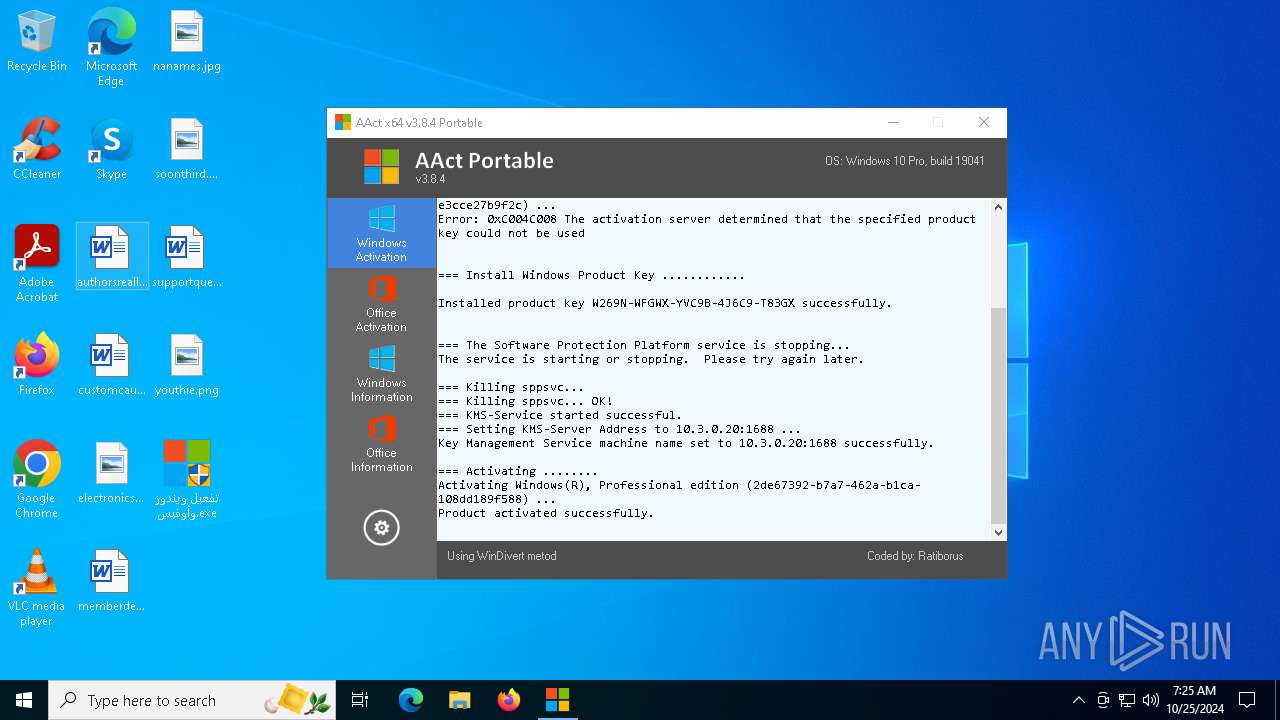
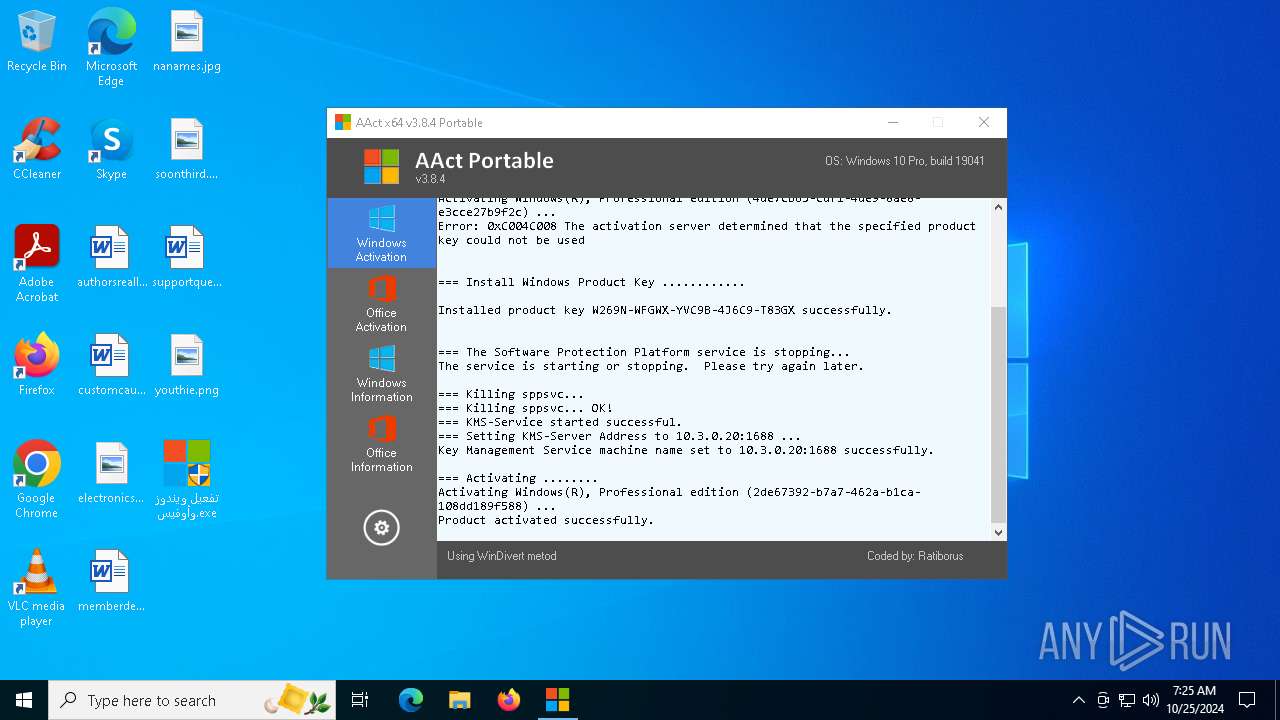
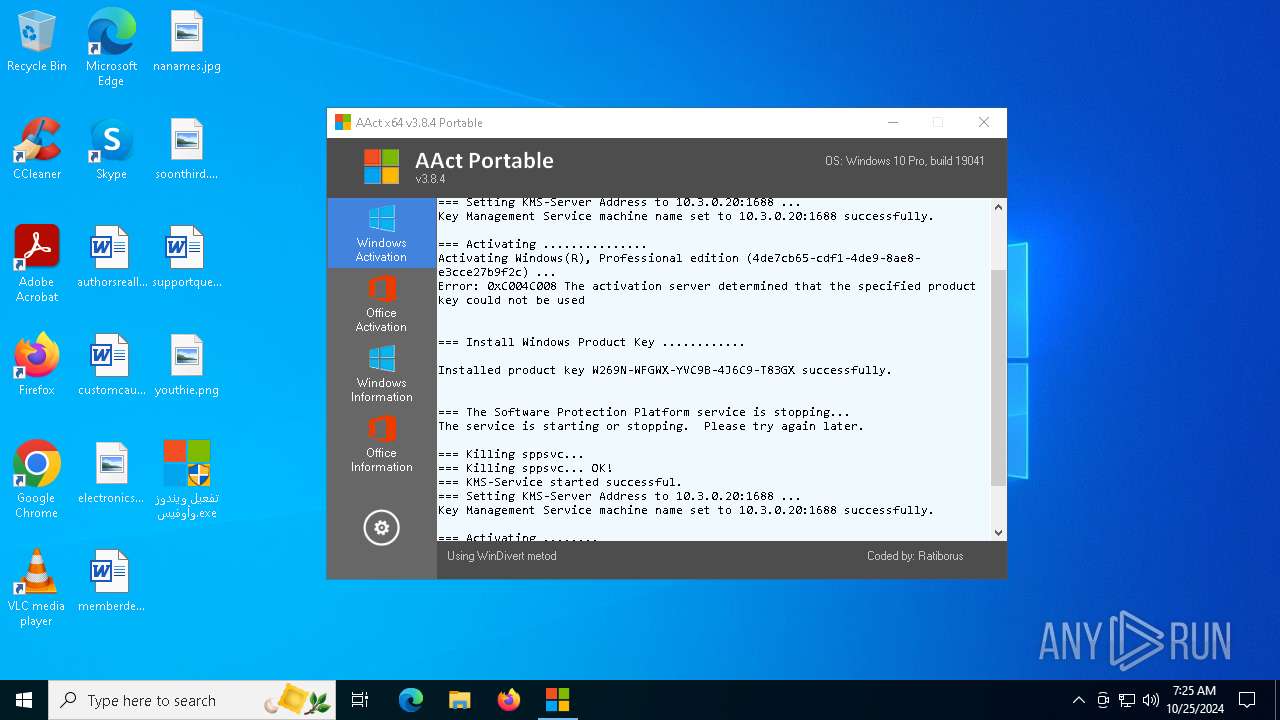
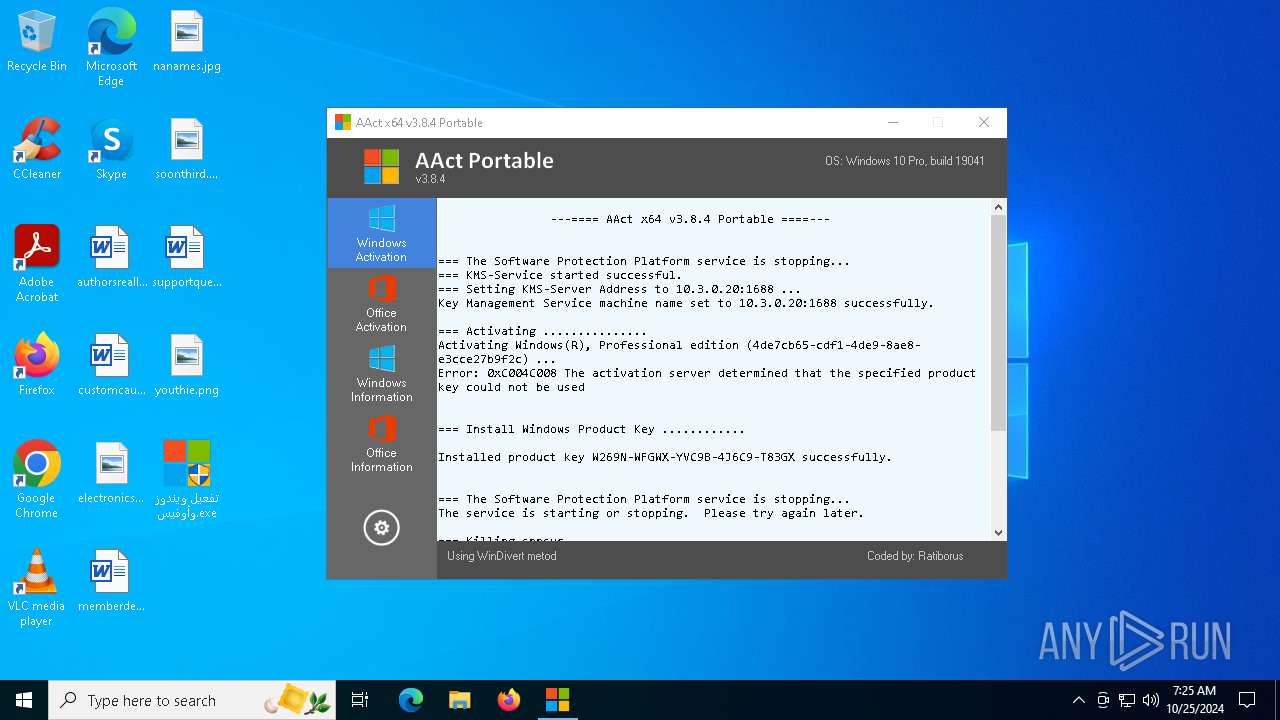
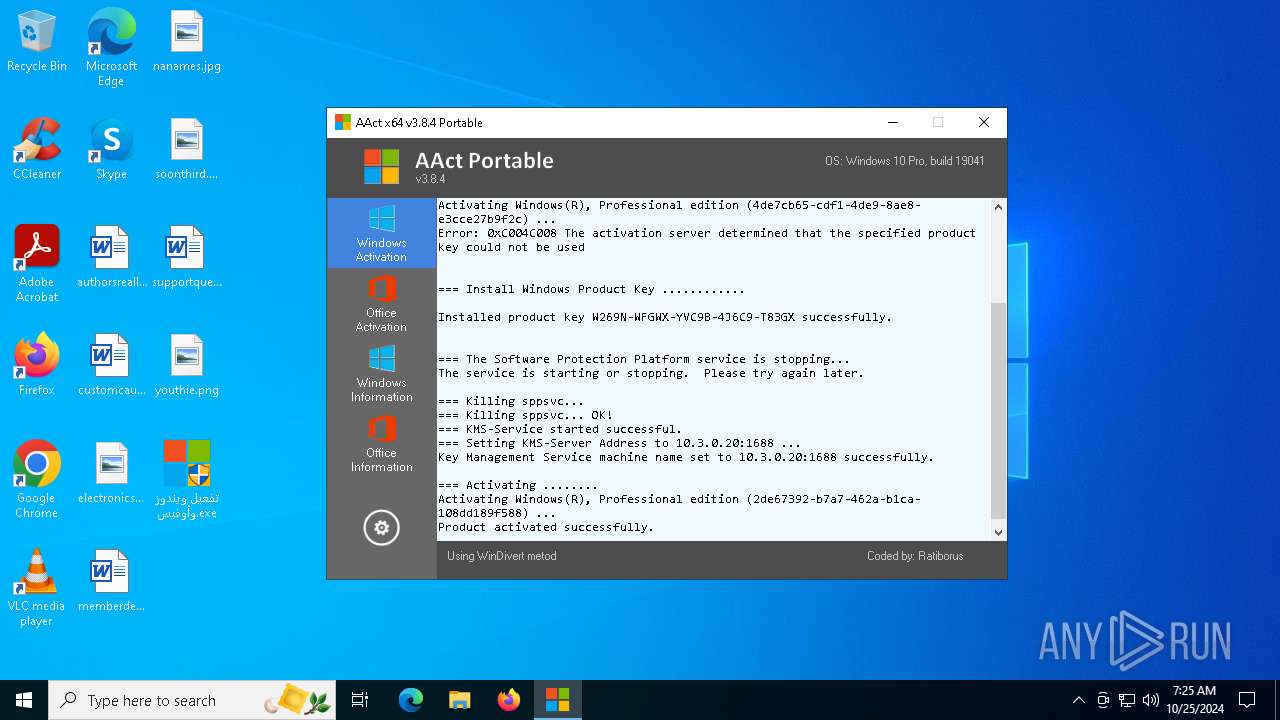
KMS tool has been detected
- تفعيل ويندوز وأوفيس.exe (PID: 3848)
- cmd.exe (PID: 6456)
- cmd.exe (PID: 3508)
- cmd.exe (PID: 920)
- cmd.exe (PID: 2620)
- cmd.exe (PID: 5400)
- cmd.exe (PID: 6136)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 6456)
- cmd.exe (PID: 920)
- cmd.exe (PID: 5400)
- cmd.exe (PID: 6136)
Hides command output
- cmd.exe (PID: 1880)
- cmd.exe (PID: 6292)
Process drops legitimate windows executable
- تفعيل ويندوز وأوفيس.exe (PID: 3848)
The process executes VB scripts
- cmd.exe (PID: 5048)
- cmd.exe (PID: 6996)
- cmd.exe (PID: 6540)
- cmd.exe (PID: 7072)
- cmd.exe (PID: 6820)
- cmd.exe (PID: 4164)
- cmd.exe (PID: 5616)
- cmd.exe (PID: 6496)
- cmd.exe (PID: 6784)
- cmd.exe (PID: 4060)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 5236)
- cmd.exe (PID: 6720)
- cmd.exe (PID: 5464)
- cmd.exe (PID: 6280)
- cmd.exe (PID: 5508)
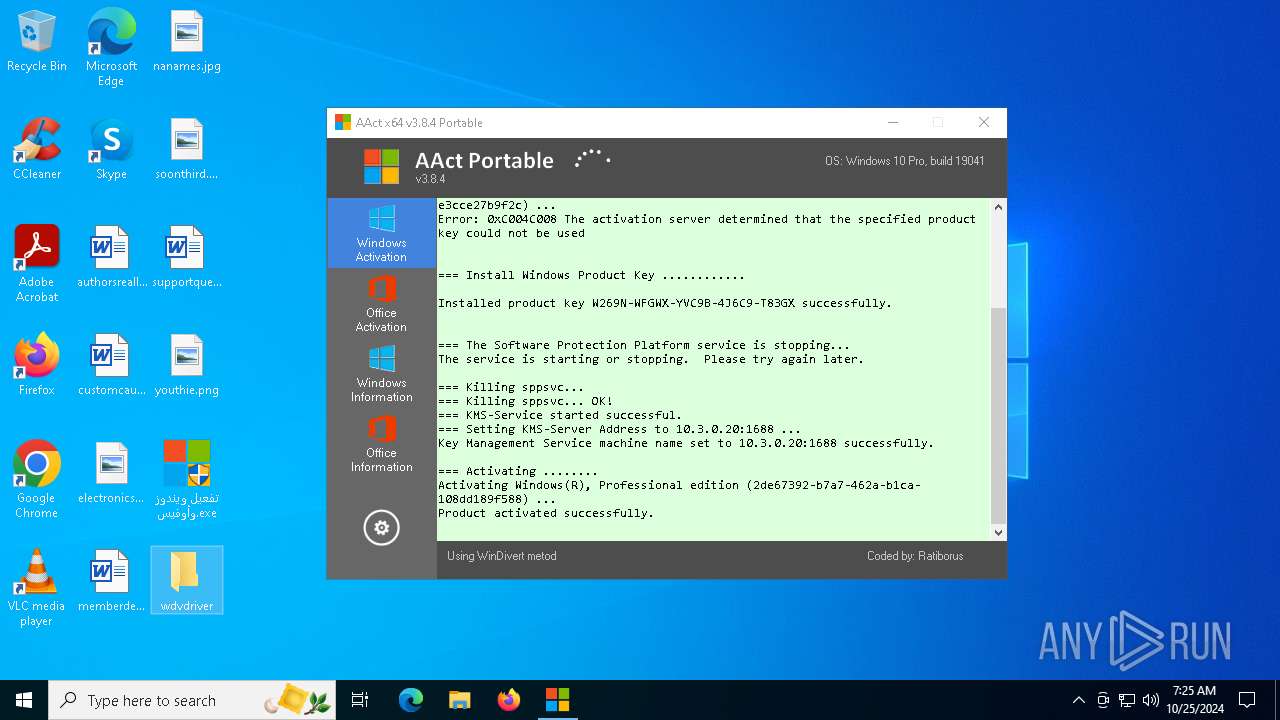
Drops a system driver (possible attempt to evade defenses)
- تفعيل ويندوز وأوفيس.exe (PID: 3848)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 3508)
- cmd.exe (PID: 2620)
Uses REG/REGEDIT.EXE to modify registry
- تفعيل ويندوز وأوفيس.exe (PID: 3848)
Uses ROUTE.EXE to modify routing table
- cmd.exe (PID: 6548)
- cmd.exe (PID: 4232)
Starts application with an unusual extension
- تفعيل ويندوز وأوفيس.exe (PID: 3848)
The process downloads a VBScript from the remote host
- cmd.exe (PID: 5616)
- cmd.exe (PID: 6280)
Starts CMD.EXE for commands execution
- تفعيل ويندوز وأوفيس.exe (PID: 3848)
Executable content was dropped or overwritten
- تفعيل ويندوز وأوفيس.exe (PID: 3848)
INFO
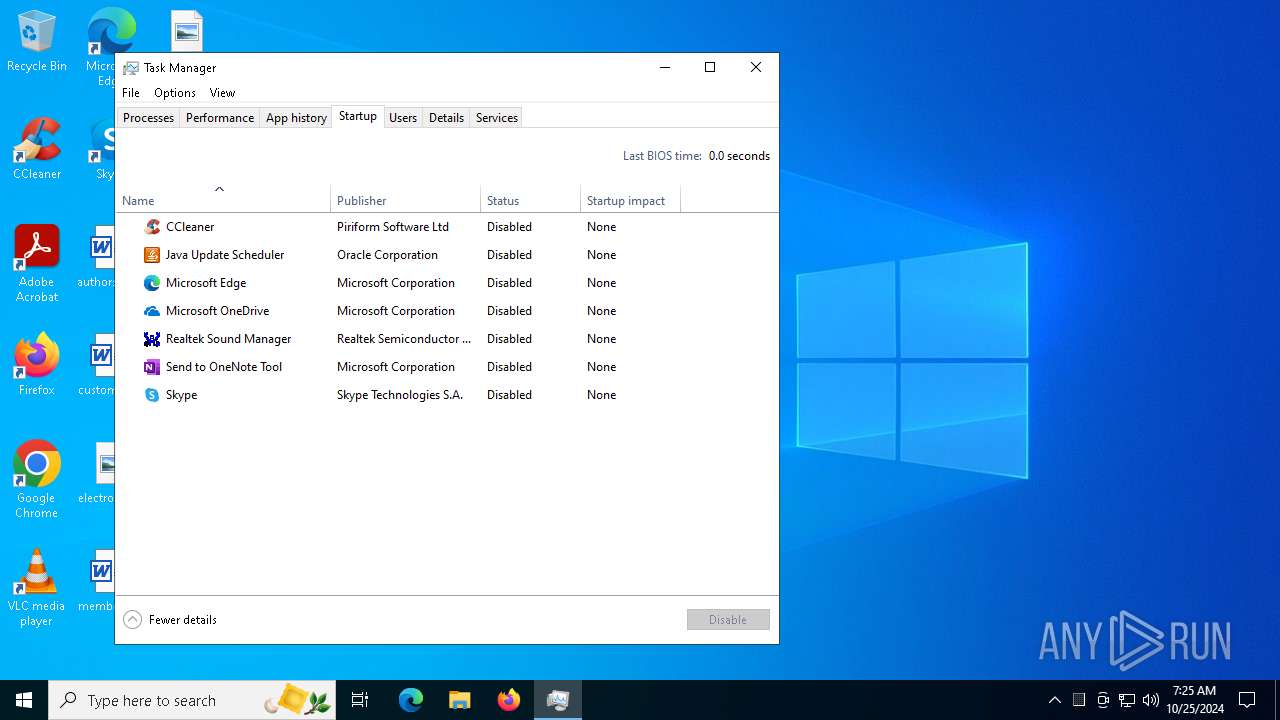
Manual execution by a user
- تفعيل ويندوز وأوفيس.exe (PID: 2652)
- تفعيل ويندوز وأوفيس.exe (PID: 3848)
- Taskmgr.exe (PID: 4408)
- Taskmgr.exe (PID: 6692)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6316)
Deletes a route via ROUTE.EXE
- ROUTE.EXE (PID: 2416)
- ROUTE.EXE (PID: 2088)
- ROUTE.EXE (PID: 6360)
- ROUTE.EXE (PID: 3936)
Adds a route via ROUTE.EXE
- ROUTE.EXE (PID: 3852)
- ROUTE.EXE (PID: 6232)
UPX packer has been detected
- FakeClient.exe (PID: 6584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 932244 |
| UncompressedSize: | 1003352 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | تفعيل ويندوز وأوفيس.exe |
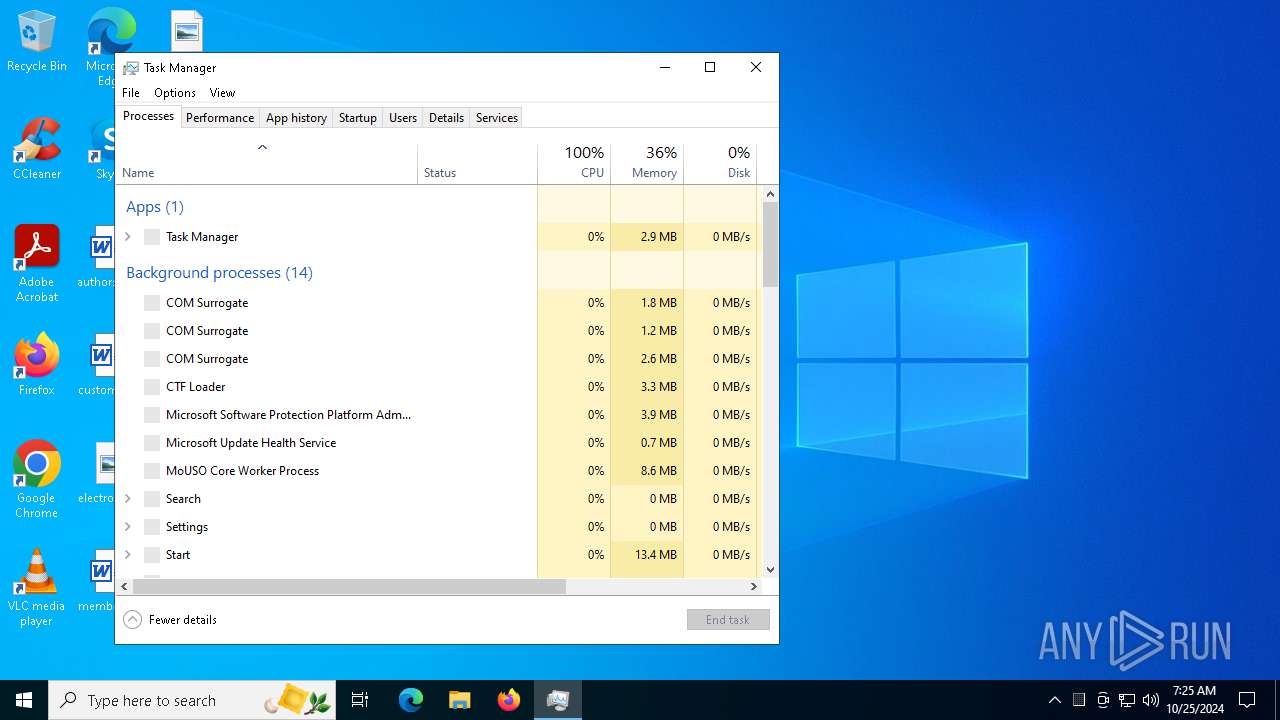
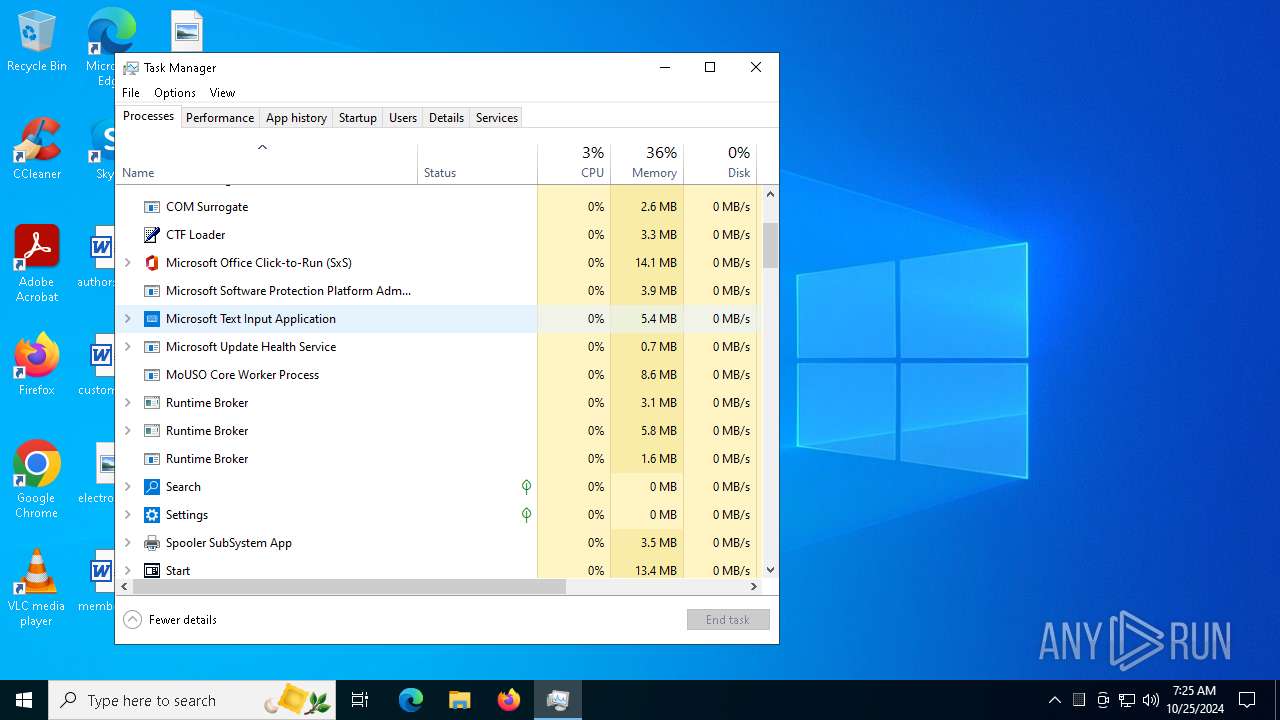
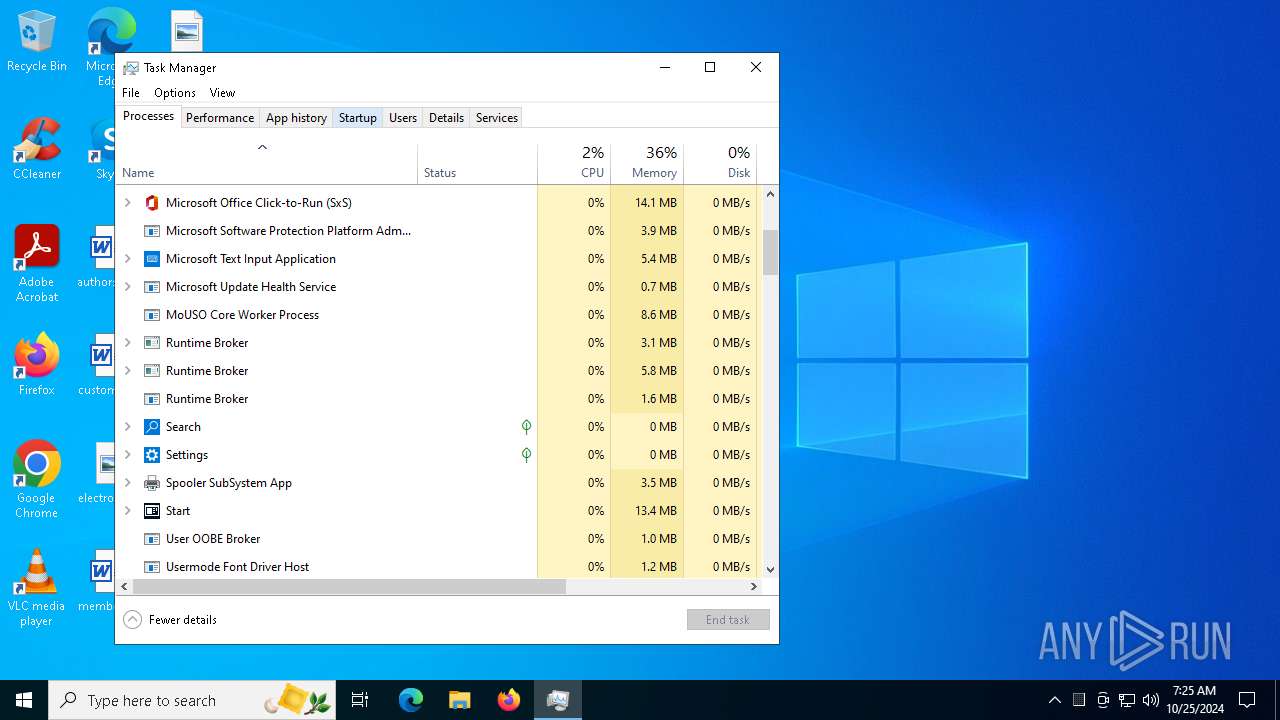
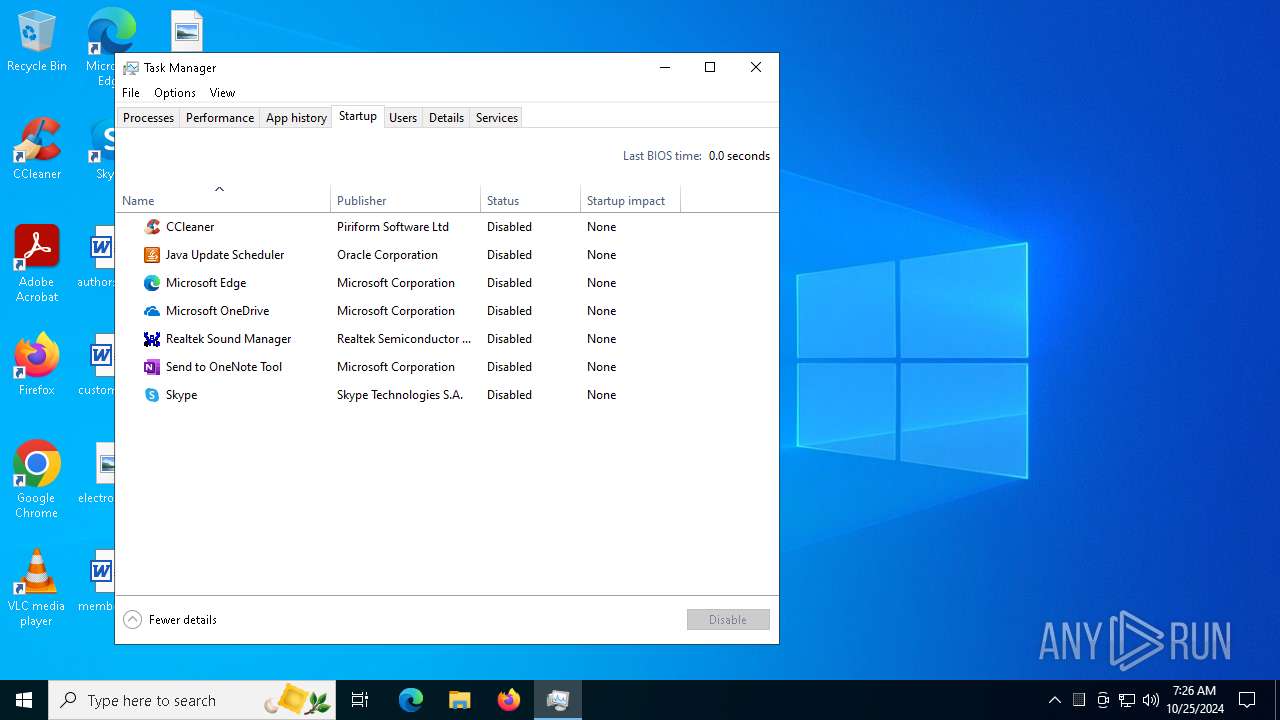
Total processes
331
Monitored processes
190
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 204 | Netsh.exe Advfirewall Firewall delete rule name=0pen_Port_KMS protocol=TCP | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | "C:\WINDOWS\System32\cmd.exe" /c route delete 10.3.0.20 0.0.0.0 | C:\Windows\System32\cmd.exe | — | تفعيل ويندوز وأوفيس.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 624 | sc.exe stop sppsvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 700 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 784 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 848 | "C:\WINDOWS\System32\cmd.exe" /c sc.exe stop WinDivert1.1 | C:\Windows\System32\cmd.exe | — | تفعيل ويندوز وأوفيس.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | "C:\WINDOWS\System32\cmd.exe" /c Netsh.exe Advfirewall Firewall delete rule name=0pen_Port_KMS protocol=TCP | C:\Windows\System32\cmd.exe | — | تفعيل ويندوز وأوفيس.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | Netsh.exe Advfirewall Firewall delete rule name=0pen_Port_KMS protocol=TCP | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1028 | "C:\WINDOWS\System32\reg.exe" DELETE "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\55c92734-d682-4d71-983e-d6ec3f16059f" /f /reg:64 | C:\Windows\System32\reg.exe | — | تفعيل ويندوز وأوفيس.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1084 | cscript.exe C:\WINDOWS\System32\slmgr.vbs //NoLogo /ato | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
Total events
16 314
Read events
16 266
Write events
32
Delete events
16
Modification events
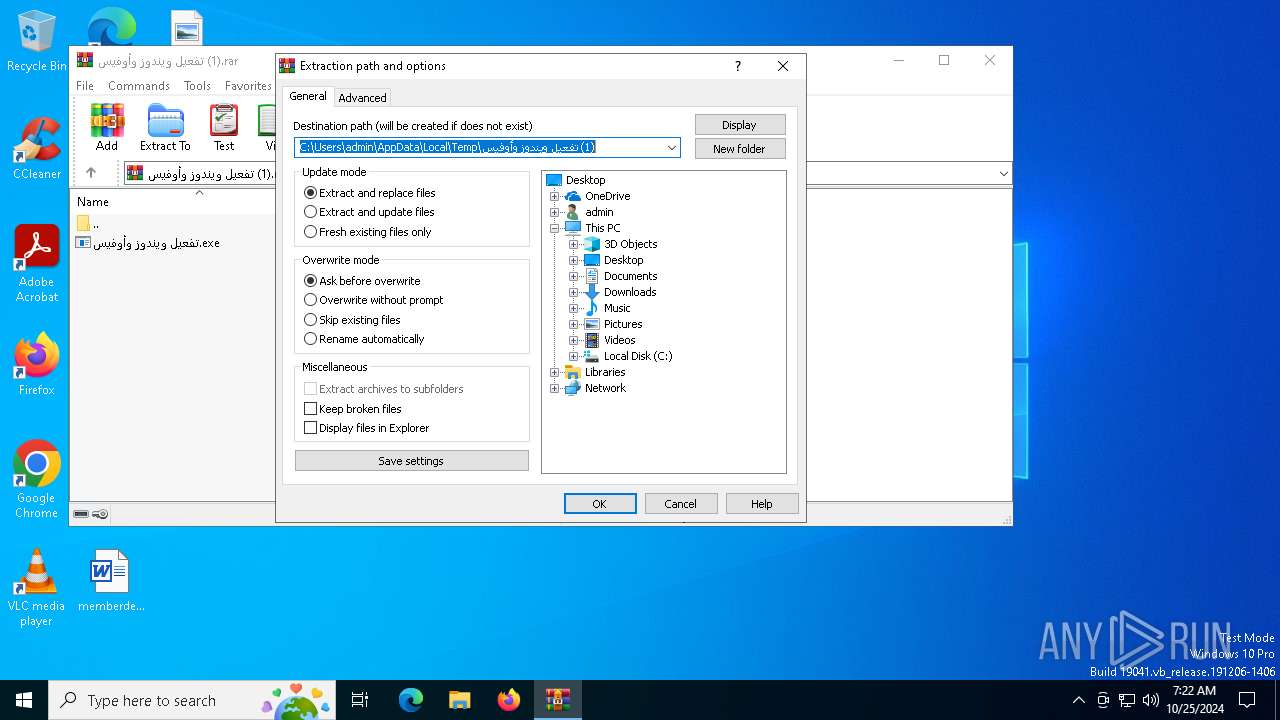
| (PID) Process: | (6316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\تفعيل ويندوز وأوفيس (1).rar | |||
| (PID) Process: | (6316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (6316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
| (PID) Process: | (6316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 13 |
Value: | |||
| (PID) Process: | (6316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 12 |
Value: | |||
Executable files
7
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6316 | WinRAR.exe | C:\Users\admin\Desktop\تفعيل ويندوز وأوفيس.exe | executable | |
MD5:41C52736ACCAACB7136036F7015E60E4 | SHA256:A096CD7BC8124FC41CF1C2E8DCF7338245DF14DD3F4A7D83289F9FFB21E852C1 | |||
| 3848 | تفعيل ويندوز وأوفيس.exe | C:\Users\admin\Desktop\wdvdriver\x64WDV\WinDivert.sys | executable | |
MD5:A0D15D8727D0780C51628DF46B7268B3 | SHA256:5E23F3ED1D6620C39A644F9879404A22DED86B3B076EC4A898B4B6BE244AFD64 | |||
| 3848 | تفعيل ويندوز وأوفيس.exe | C:\Users\admin\Desktop\wdvdriver\x64WDV\FakeClient.exe | executable | |
MD5:6C3306178A8D224E84D2C6022F4C43F8 | SHA256:E38F5DEB8B642C0A234ED2CA79C866B0678CB9AB49992C347CFE8870C68A7989 | |||
| 3848 | تفعيل ويندوز وأوفيس.exe | C:\Users\admin\Desktop\wdvdriver\x64WDV\WinDivert.inf | text | |
MD5:A94D989905A248AFCA52BC3CBFCB248B | SHA256:6C9F7DEA4F9A47788D5D2BA110B08457FD00DBABE4812EBCA6F022300843A75D | |||
| 3848 | تفعيل ويندوز وأوفيس.exe | C:\Users\admin\Desktop\wdvdriver\AAct.dll | executable | |
MD5:27949092E204D67E932218F70C64E978 | SHA256:7DD8CAA816EBD0498B8E7BAF144409C294BA64F400C2FF9DB5BE7DEB29F4A27B | |||
| 3848 | تفعيل ويندوز وأوفيس.exe | C:\Users\admin\Desktop\wdvdriver\x64WDV\WdfCoInstaller01009.dll | executable | |
MD5:BE566E174EAF5B93B0474593CD8F2715 | SHA256:CEE8496BFA1080FD84FC48BA4375625238900FE93EA739B2DC0300206FDE8330 | |||
| 3848 | تفعيل ويندوز وأوفيس.exe | C:\Users\admin\Desktop\wdvdriver\x64WDV\WinDivert.dll | executable | |
MD5:3F0C03E5076C7E6B404F894FF4DC5BB1 | SHA256:4E7EBED8410C83B73A23185AA94680143DA2933305CD6DEEFE8EC0B51B7EE6F3 | |||
| 6584 | FakeClient.exe | C:\Windows\setupact.log | text | |
MD5:1F6C3533285F224D97CE0D5A6A71D408 | SHA256:66A26AB8BC4700B3F295DCB43371A5613067AAA0B962EA3B3EAEA3E11412FB93 | |||
| 6692 | Taskmgr.exe | C:\Users\admin\AppData\Local\D3DSCache\3534848bb9f4cb71\F4EB2D6C-ED2B-4BDD-AD9D-F913287E6768.lock | text | |
MD5:F49655F856ACB8884CC0ACE29216F511 | SHA256:7852FCE59C67DDF1D6B8B997EAA1ADFAC004A9F3A91C37295DE9223674011FBA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
49
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4700 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 314 b | whitelisted |
6944 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
6944 | svchost.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
6164 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
6164 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
3604 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2464 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6944 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4360 | SearchApp.exe | 2.16.110.168:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
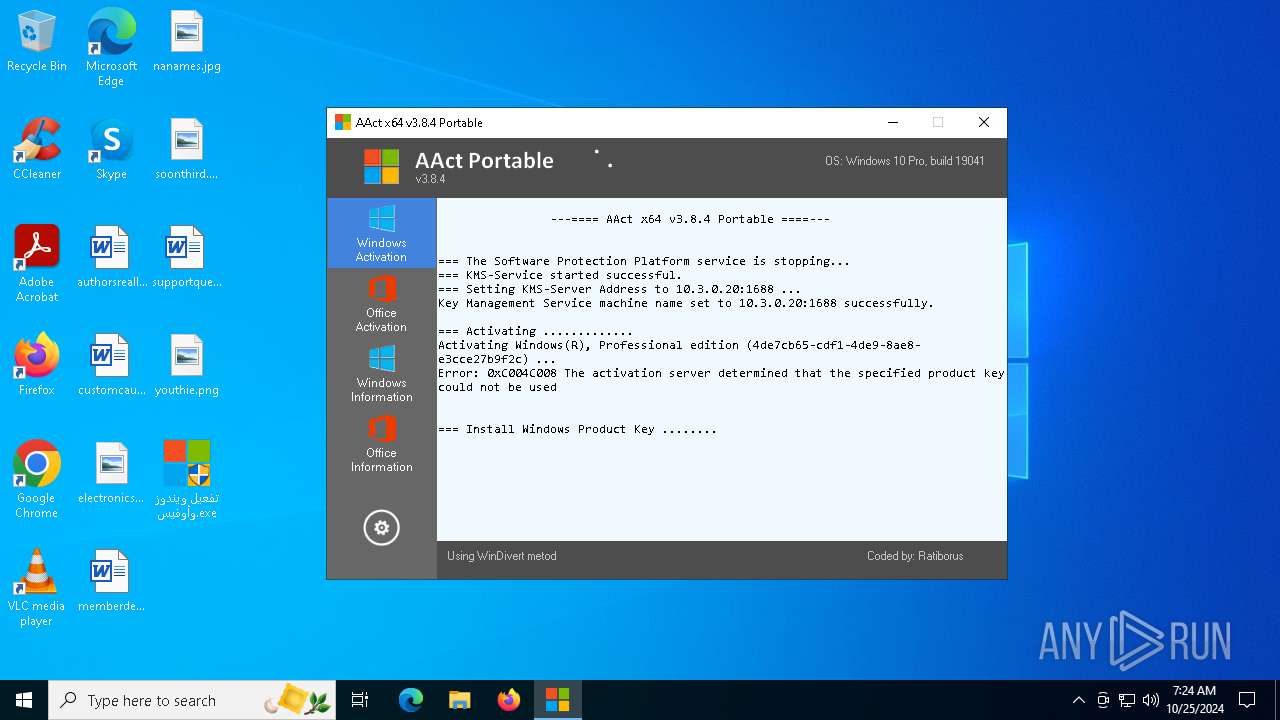
FakeClient.exe | WdfCoInstaller: [10/25/2024 07:23.01.363] ReadComponents: WdfSection for Driver Service windivert using KMDF lib version Major 0x1, minor 0x9
|
FakeClient.exe | WdfCoInstaller: [10/25/2024 07:23.02.194] BootApplication: could not open service windivert, error error(1060) The specified service does not exist as an installed service.
|
FakeClient.exe | WdfCoInstaller: [10/25/2024 07:23.02.348] BootApplication: GetStartType error error(87) The parameter is incorrect.
Driver Service name windivert
|
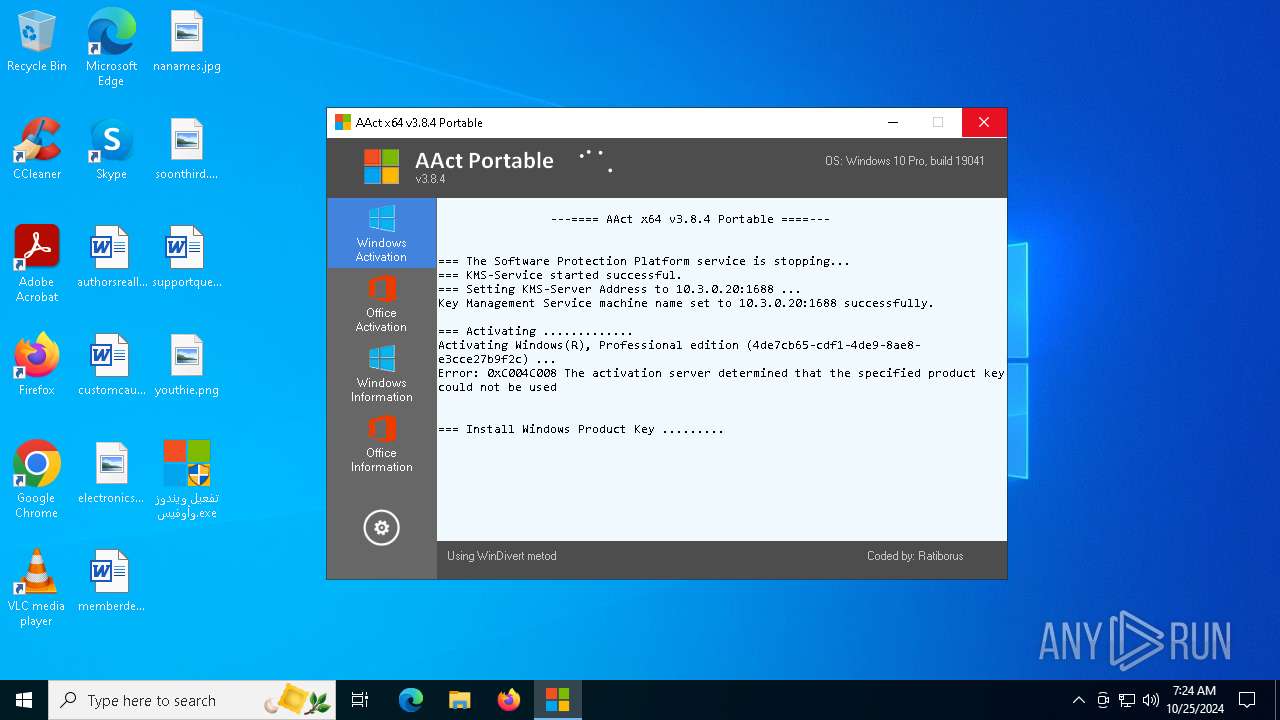
FakeClient.exe | WdfCoInstaller: [10/25/2024 07:24.42.990] ReadComponents: WdfSection for Driver Service windivert using KMDF lib version Major 0x1, minor 0x9
|
FakeClient.exe | WdfCoInstaller: [10/25/2024 07:24.42.997] BootApplication: could not open service windivert, error error(1060) The specified service does not exist as an installed service.
|
FakeClient.exe | WdfCoInstaller: [10/25/2024 07:24.42.999] BootApplication: GetStartType error error(87) The parameter is incorrect.
Driver Service name windivert
|