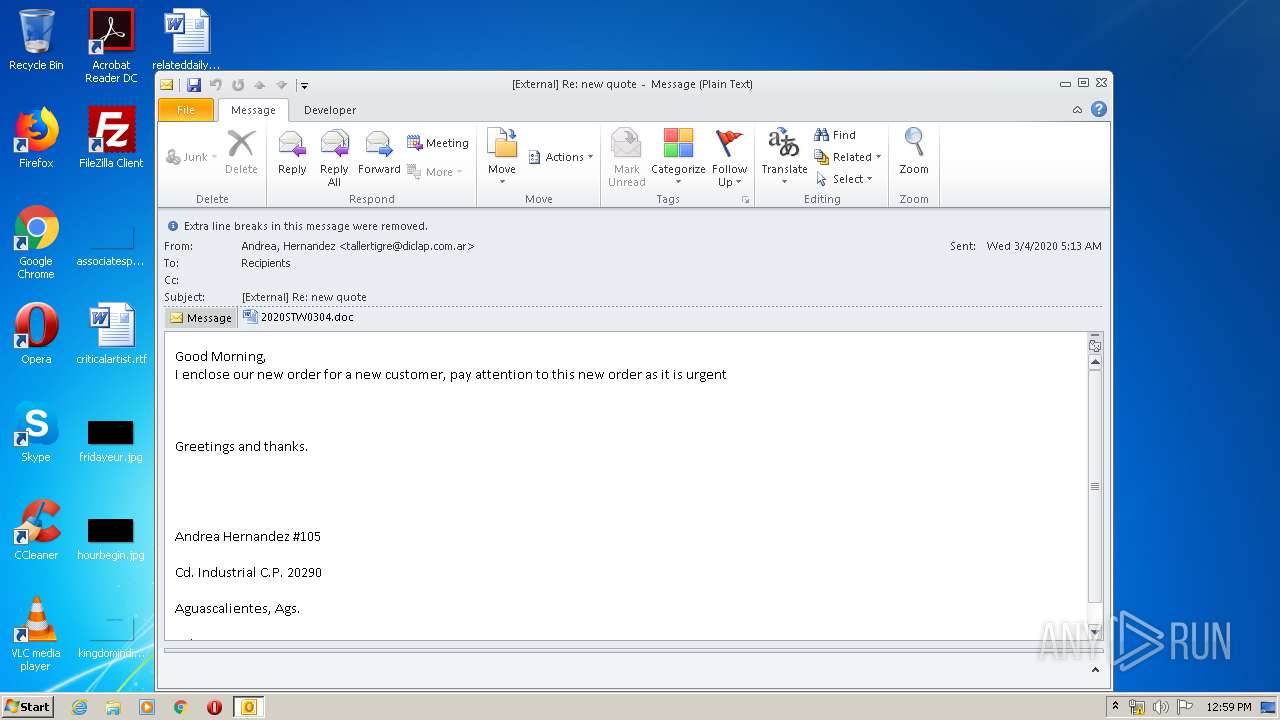
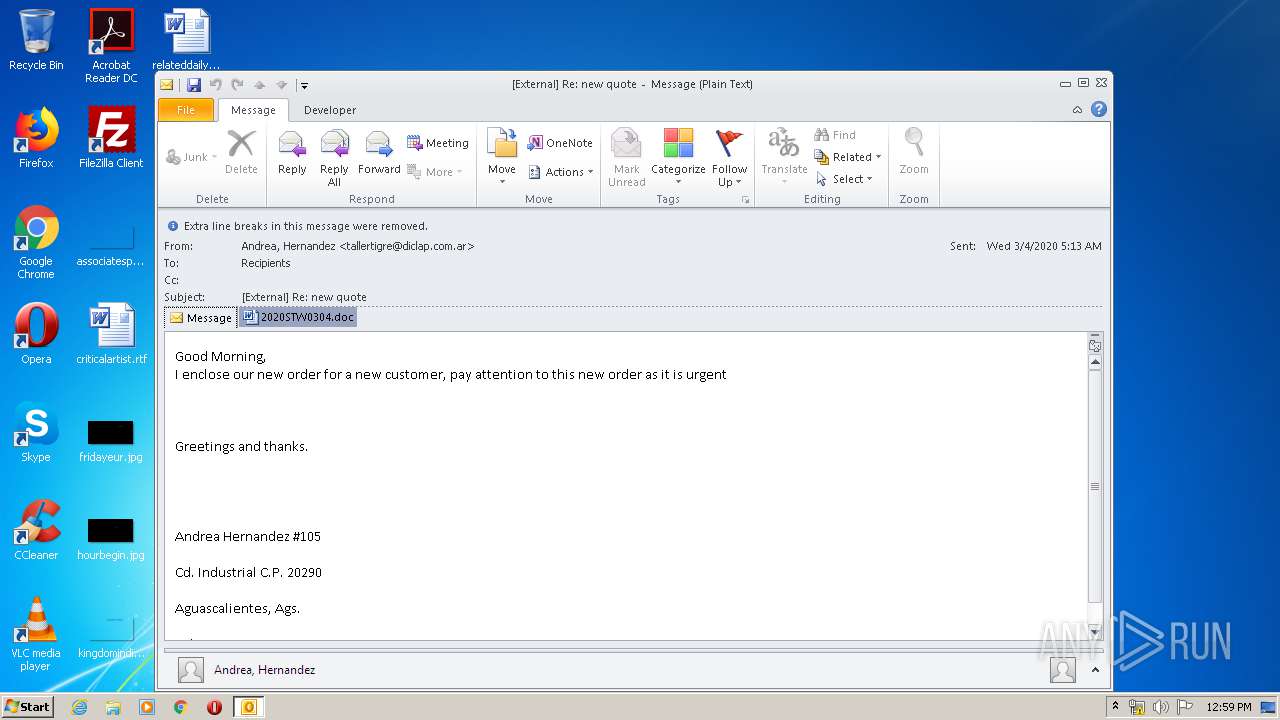
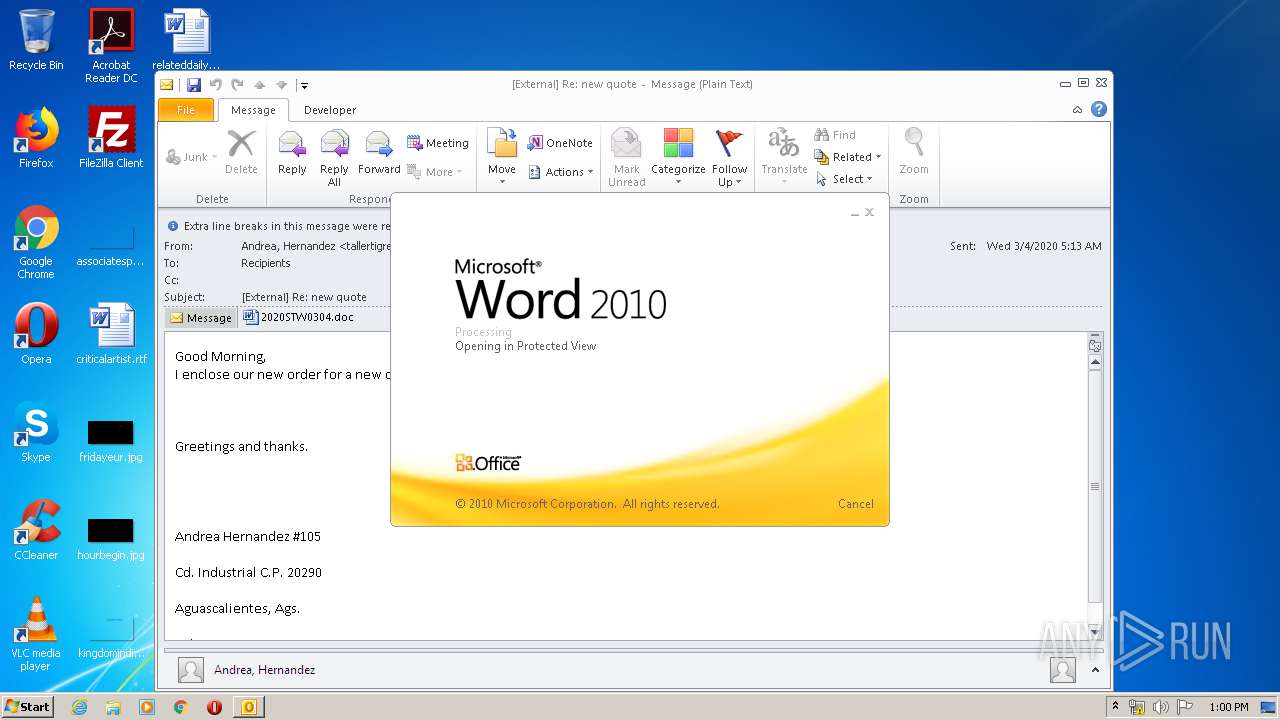
| File name: | External Re new quote.msg |
| Full analysis: | https://app.any.run/tasks/0dfe5b2d-c748-408c-8680-55d56e58fd09 |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2020, 11:59:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 0D9FAF8B026E8B9E38C3B8B0480E4E24 |
| SHA1: | DEC09D5C57C60BF9B9645B8445D5FE96726030C7 |
| SHA256: | 3B1A489C3A62B56A1D198219063A548E707863BDB20D2B3816DE6341577132F3 |
| SSDEEP: | 24576:gbbGpRxpRxpRxpRxpRxpRxpRxpRxpRxpRxpRxpRxpRxpRxpRxpRxpRxpRxpRxpR6:Jtttttttttttttttttttttttt |
MALICIOUS
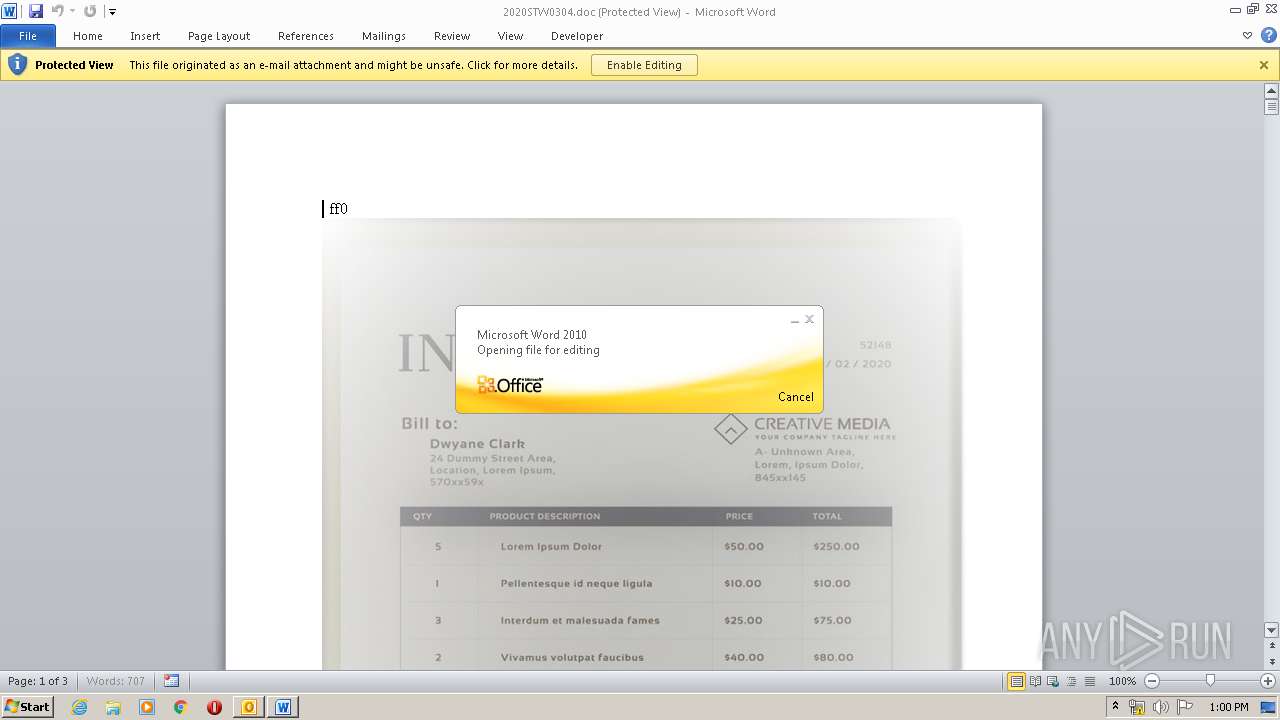
Actions looks like stealing of personal data
- WINWORD.EXE (PID: 2232)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2104)
- EQNEDT32.EXE (PID: 2112)
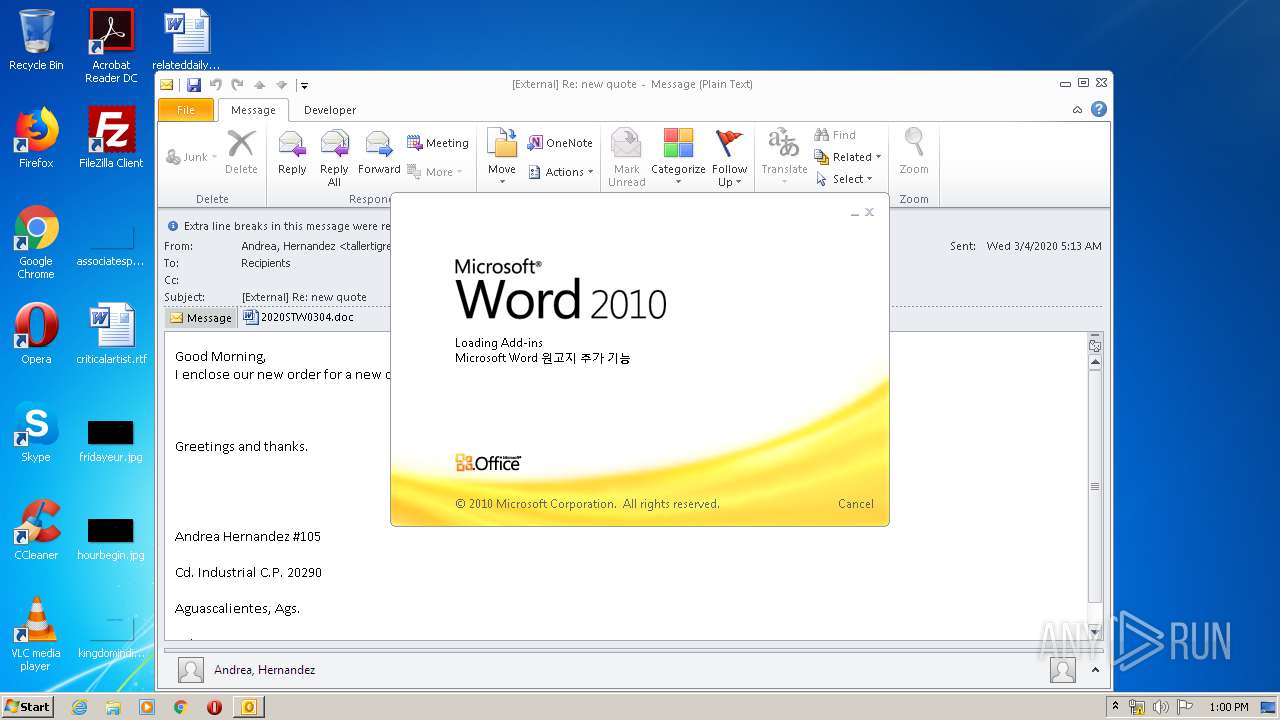
Executed via COM
- EQNEDT32.EXE (PID: 2112)
Reads Internet Cache Settings
- EQNEDT32.EXE (PID: 2112)
Application launched itself
- WINWORD.EXE (PID: 2232)
Starts Microsoft Office Application
- WINWORD.EXE (PID: 2232)
- OUTLOOK.EXE (PID: 2104)
INFO
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2104)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1520)
- OUTLOOK.EXE (PID: 2104)
- WINWORD.EXE (PID: 2232)
Creates files in the user directory
- WINWORD.EXE (PID: 2232)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
44
Monitored processes
4
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1520 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\External Re new quote.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
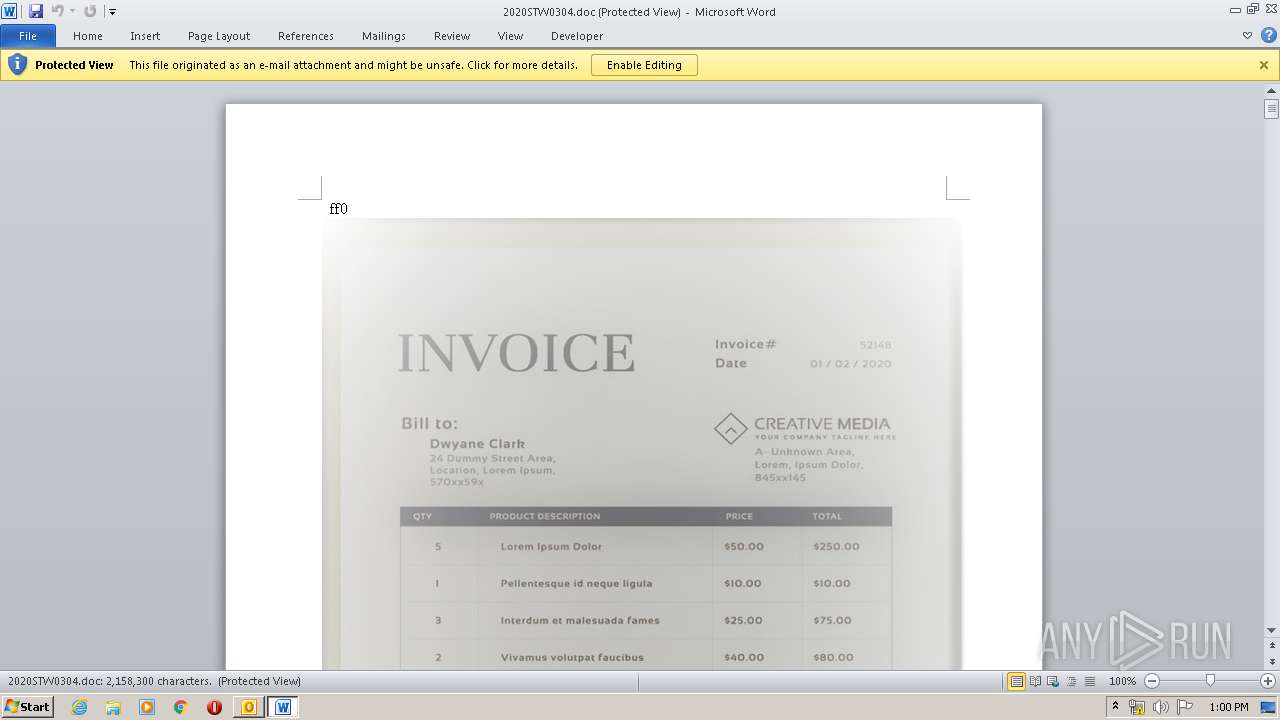
| 2232 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\J4JSH1RN\2020STW0304.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
4 560
Read events
2 866
Write events
1 515
Delete events
179
Modification events
| (PID) Process: | (2104) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2104) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2104) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2104) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2104) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2104) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2104) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2104) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2104) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2104) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
1
Text files
32
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2104 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR9E65.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2104 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\J4JSH1RN\2020STW0304 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2232 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRC759.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2232 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_94B02C56-4DCD-497D-9639-AF553061D2C2.0\7588E82.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 1520 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_94B02C56-4DCD-497D-9639-AF553061D2C2.0\~WRS{00DD8878-ACA9-4608-8520-EC4E80CBDB11}.tmp | — | |
MD5:— | SHA256:— | |||
| 1520 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_94B02C56-4DCD-497D-9639-AF553061D2C2.0\~WRF{E77EA2DB-86F8-4F3A-AD0D-EE384AADCD6A}.tmp | — | |
MD5:— | SHA256:— | |||
| 2104 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2232 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2112 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\2uUUBE2[1].htm | html | |
MD5:— | SHA256:— | |||
| 2104 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\J4JSH1RN\2020STW0304 (2).doc | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2112 | EQNEDT32.EXE | GET | — | 192.185.119.99:80 | http://www.melonco.com/images/stwha.jpg | US | — | — | malicious |
2112 | EQNEDT32.EXE | GET | 301 | 67.199.248.10:80 | http://bit.ly/2uUUBE2 | US | html | 126 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2112 | EQNEDT32.EXE | 67.199.248.10:80 | bit.ly | Bitly Inc | US | shared |
2112 | EQNEDT32.EXE | 192.185.119.99:80 | www.melonco.com | CyrusOne LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
bit.ly |
| shared |
www.melonco.com |
| malicious |