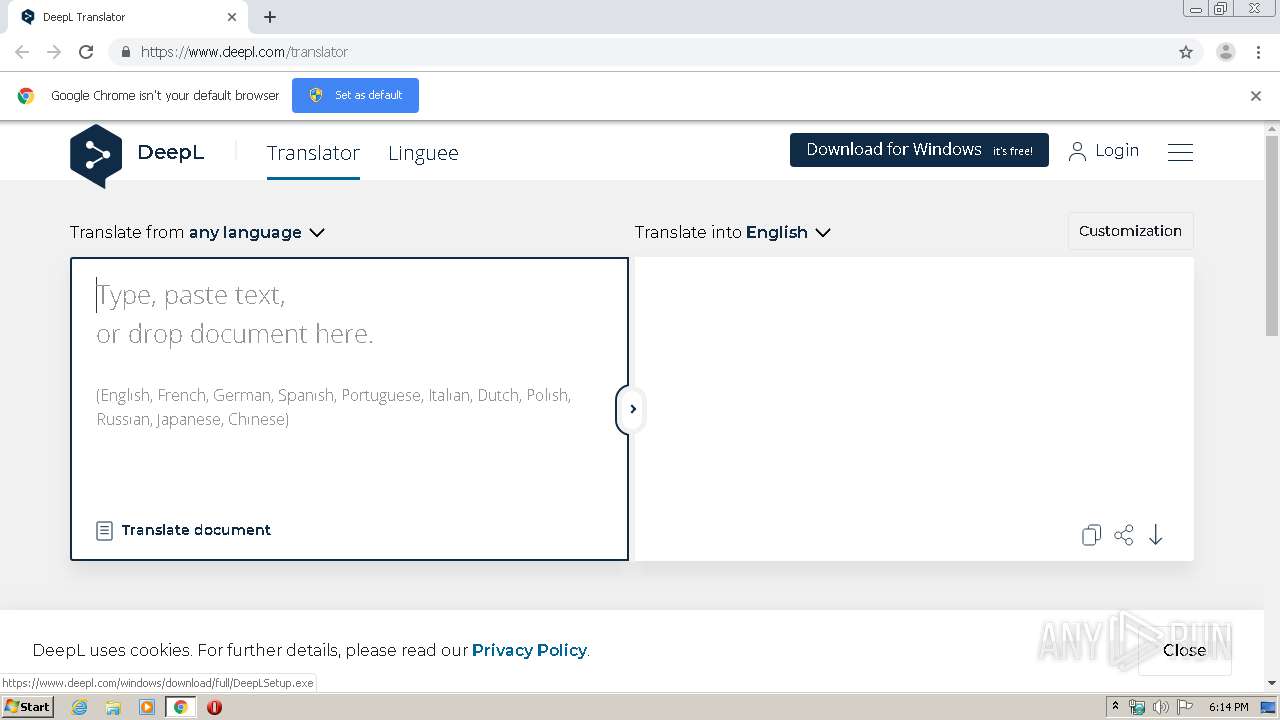
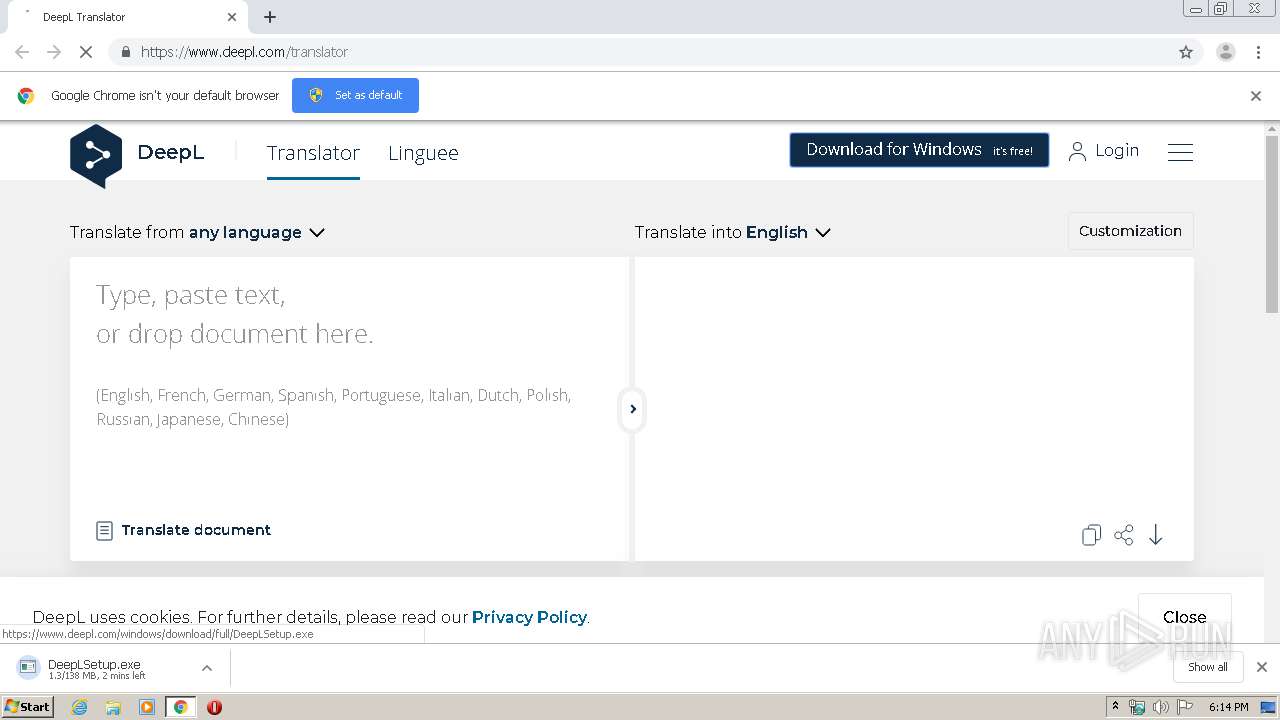
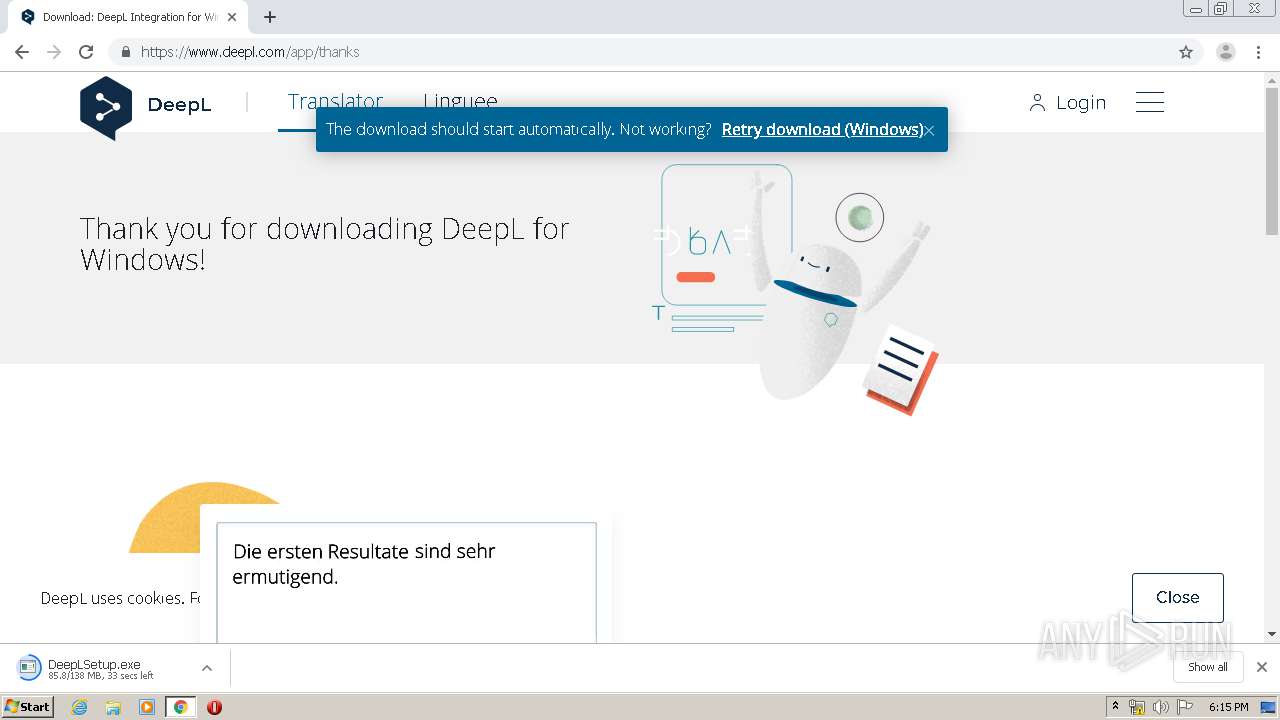
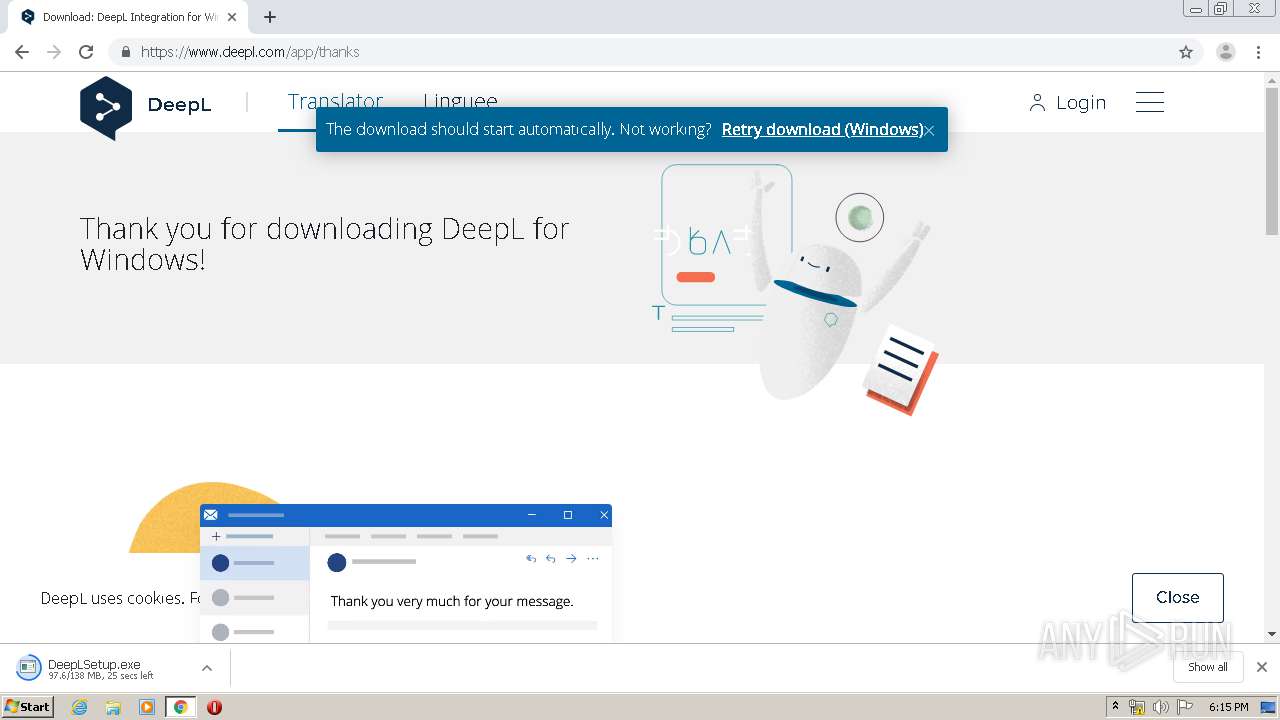
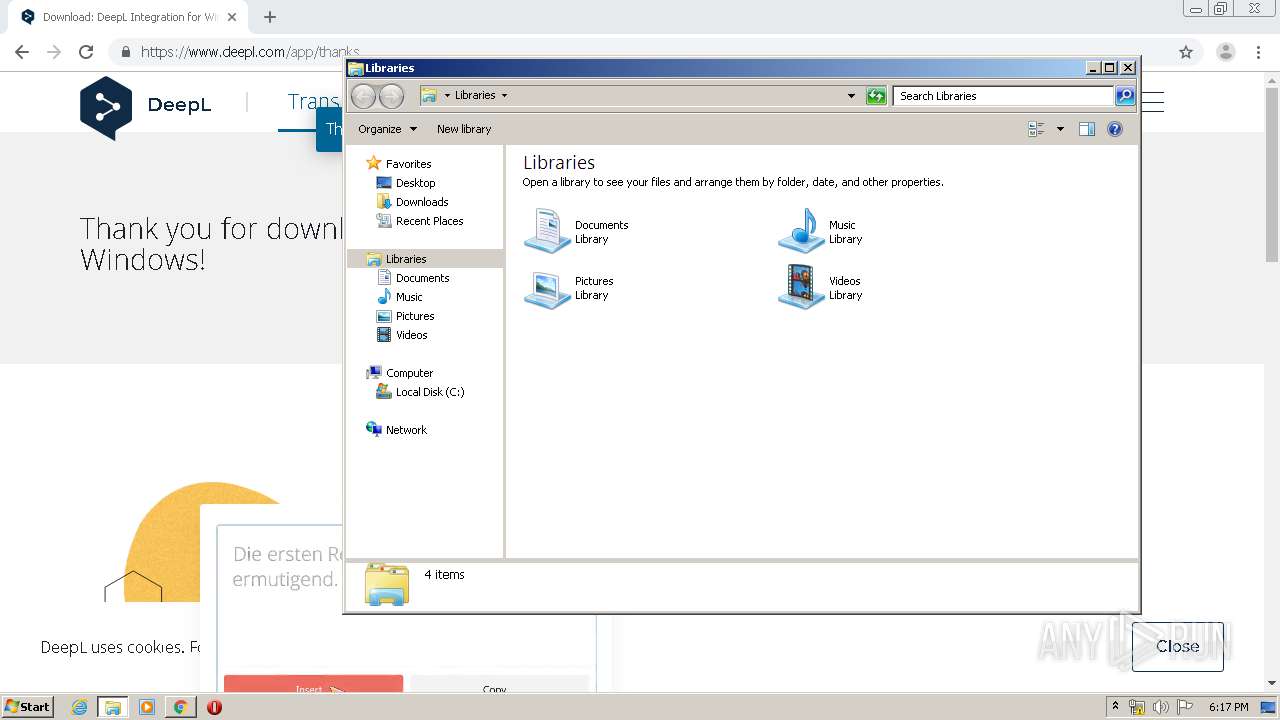
| URL: | https://www.deepl.com |
| Full analysis: | https://app.any.run/tasks/7a26bb4d-b9cc-4b12-b39c-73d43938bff5 |
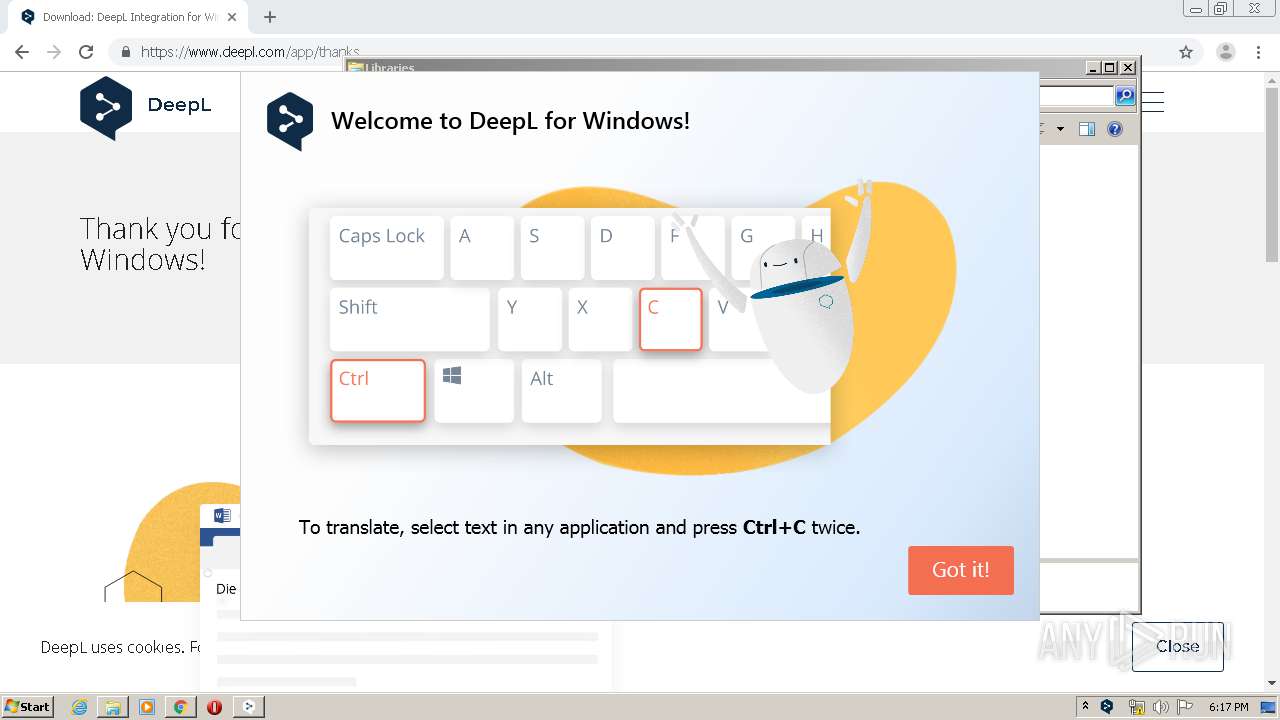
| Verdict: | Malicious activity |
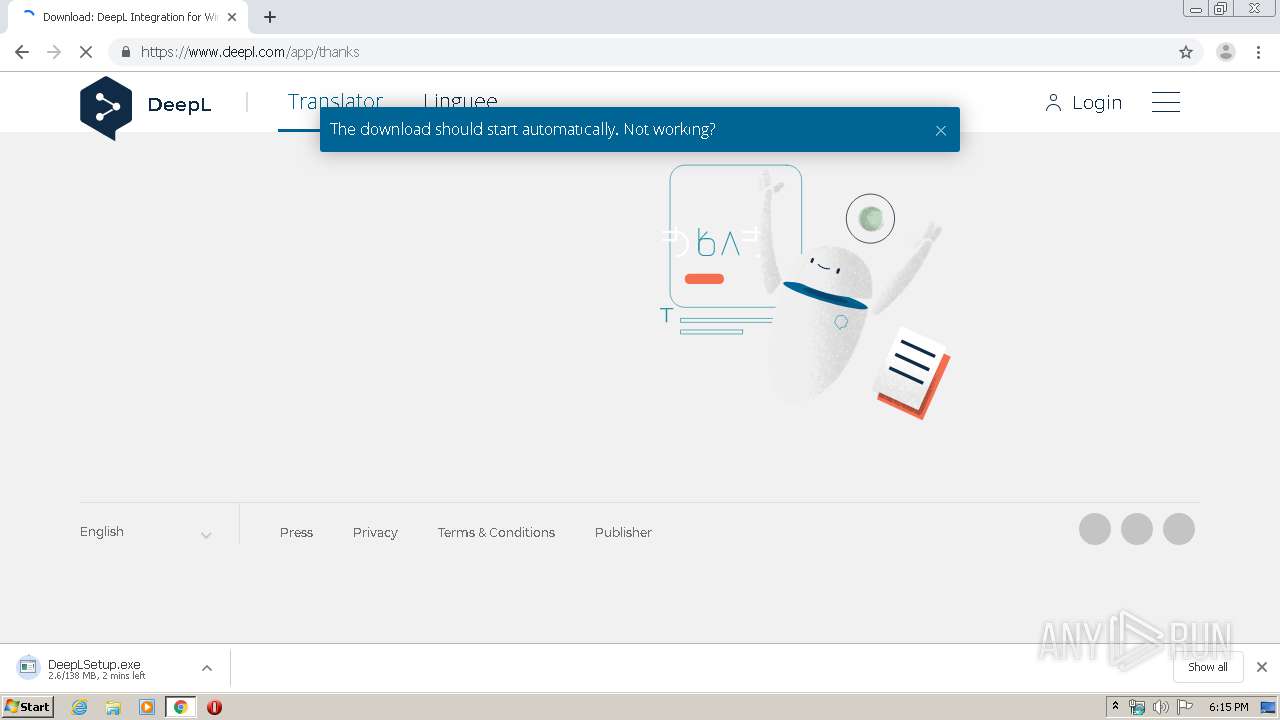
| Analysis date: | May 13, 2020, 17:14:33 |
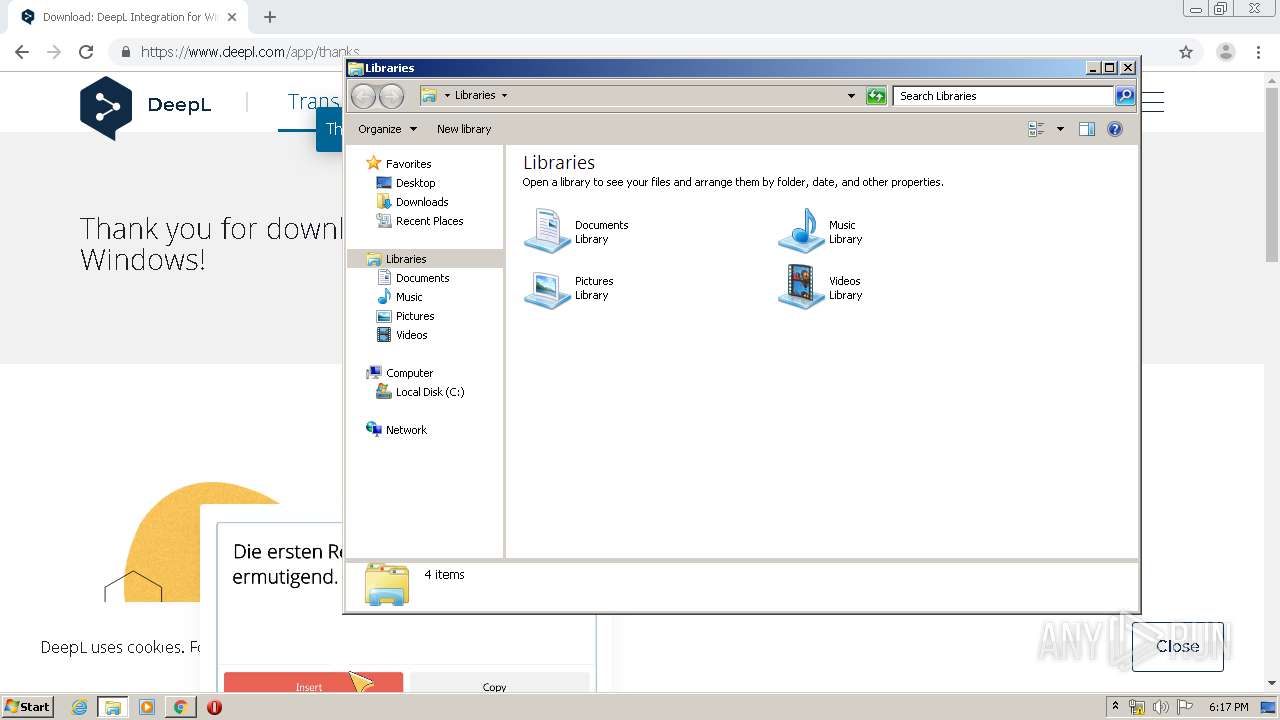
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4A7EB143061548C2ACDC7381D987094A |
| SHA1: | BEE6486A4911B047146DDFD32F46E8A8EED85064 |
| SHA256: | 3AFB6CACCF0C6925343DA4B901E17C078AC1CB7198C5384C03E7E0F51A8720FC |
| SSDEEP: | 3:N8DSLVJZI:2OLjZI |
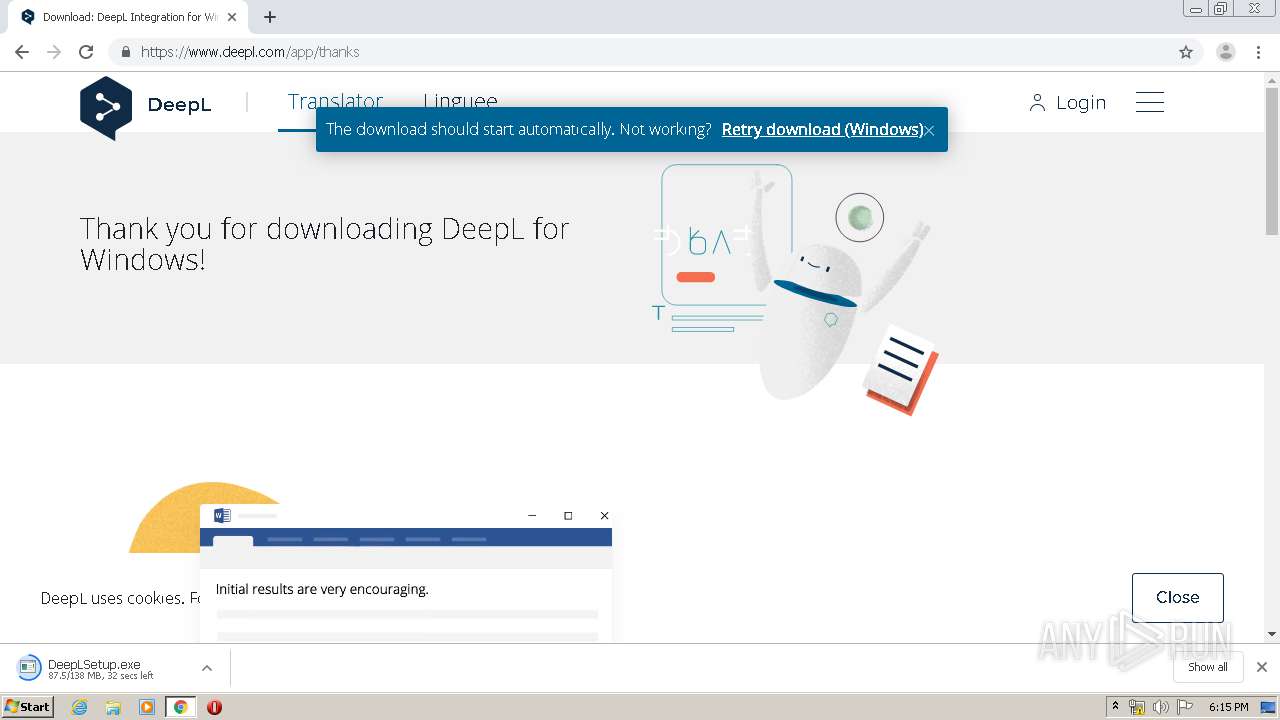
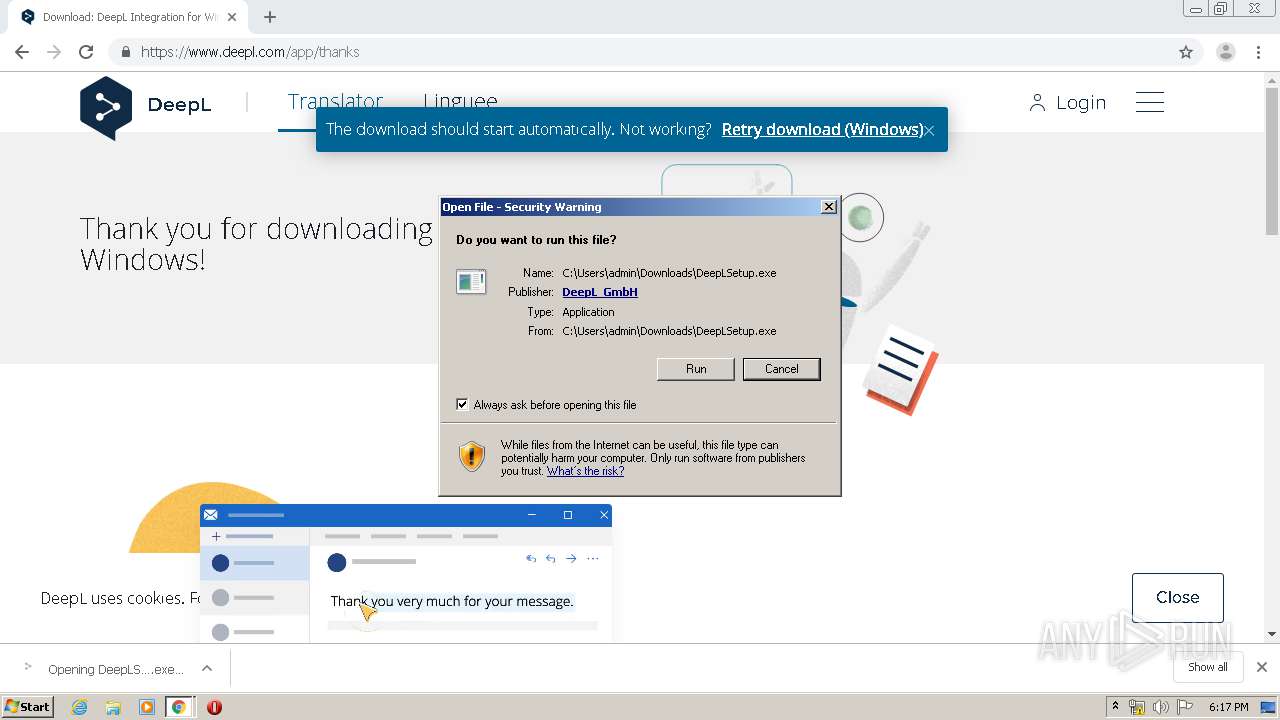
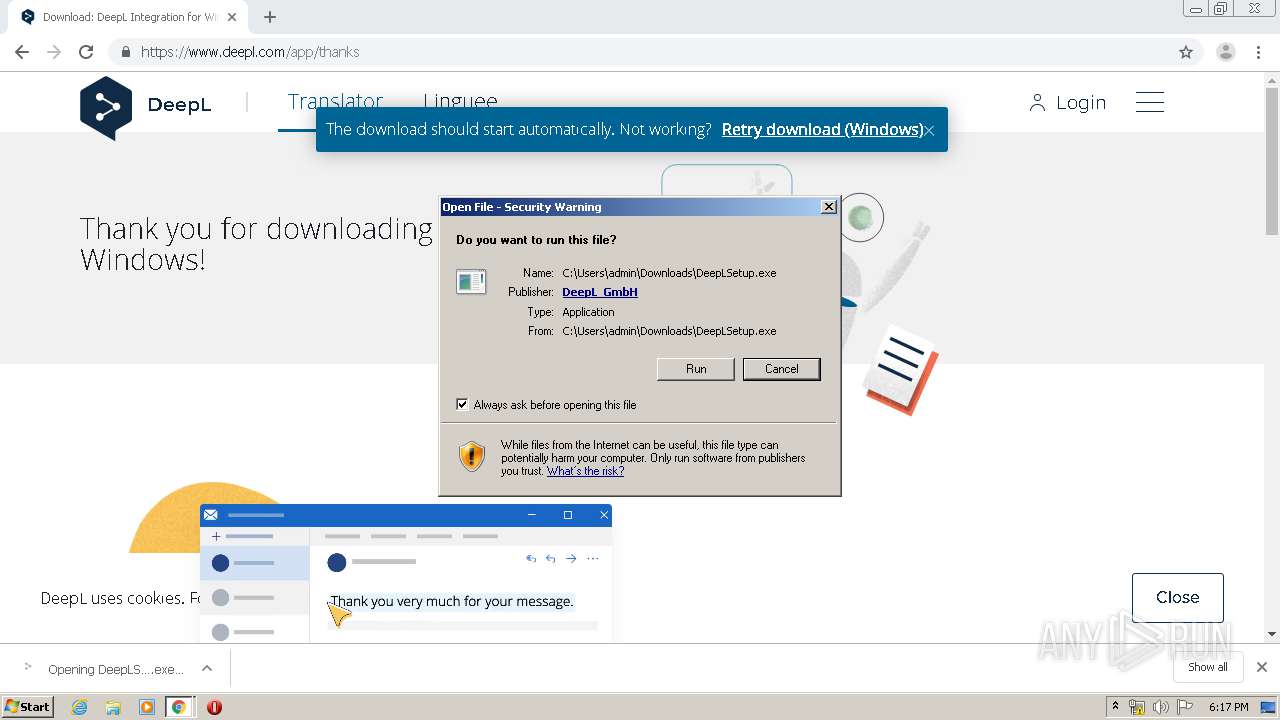
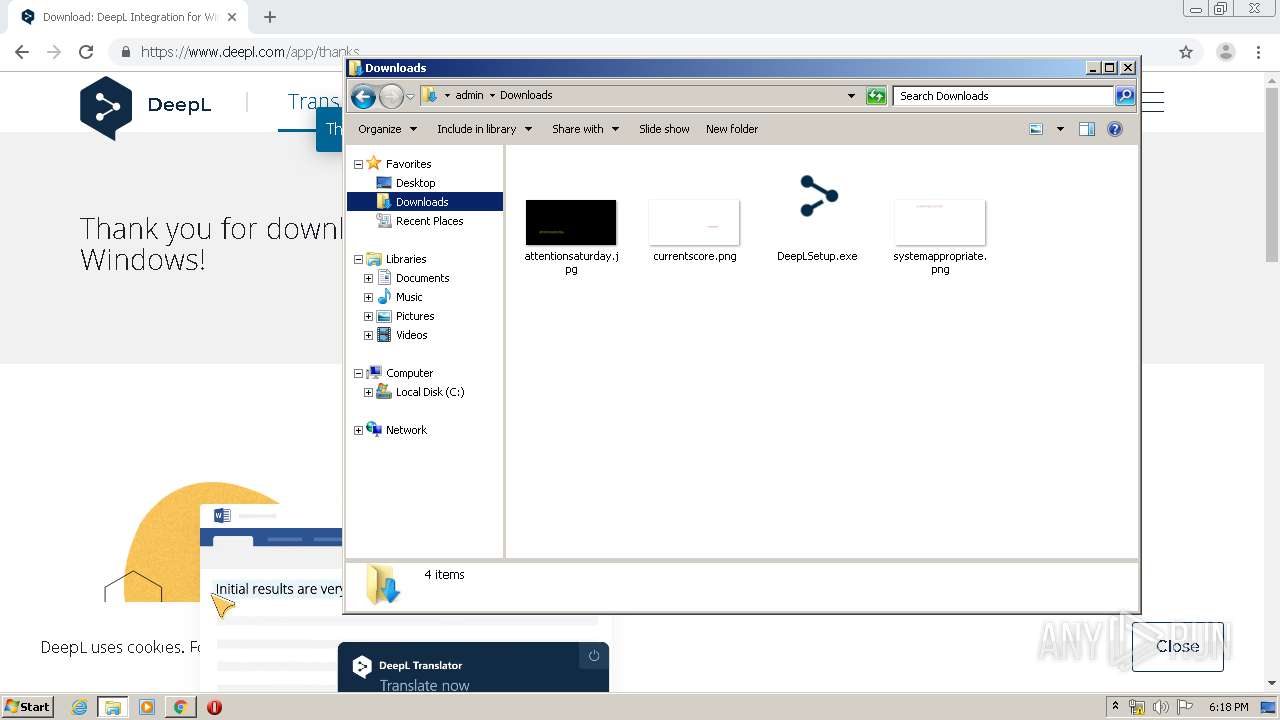
MALICIOUS
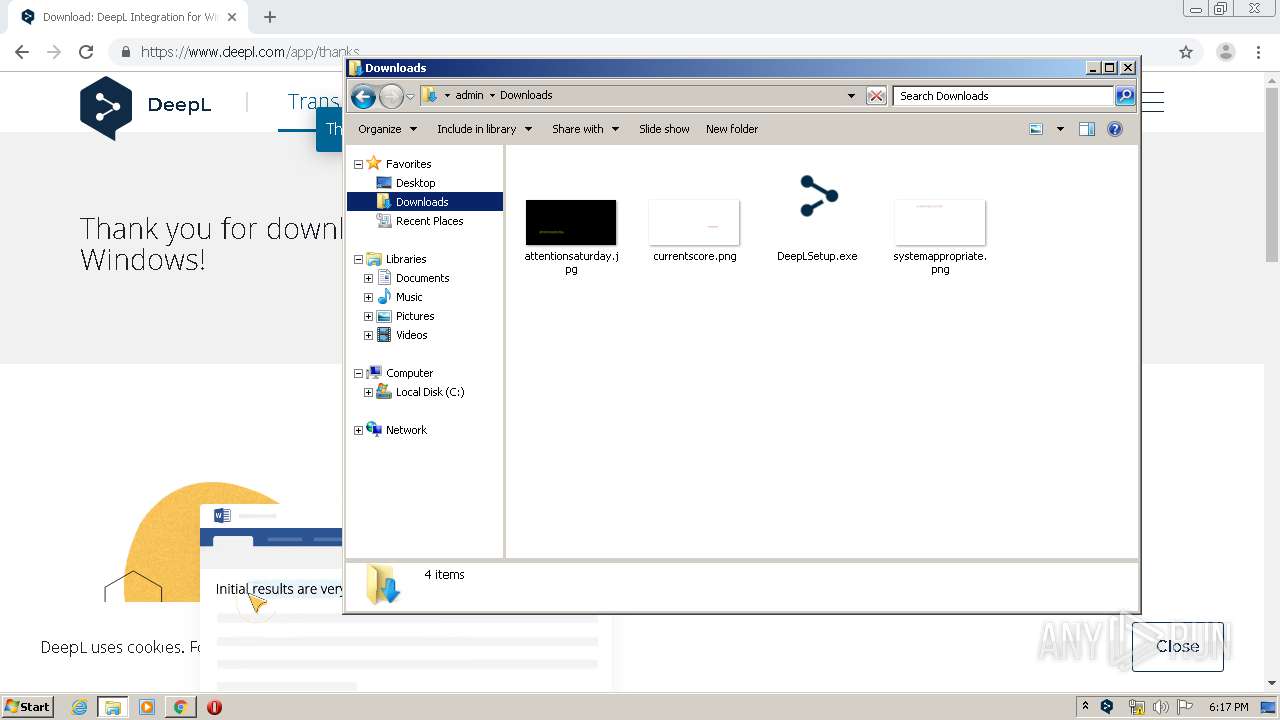
Application was dropped or rewritten from another process
- DeepLSetup.exe (PID: 3084)
- Update.exe (PID: 3156)
- DeepL.exe (PID: 3920)
- DeepL.exe (PID: 3132)
- CefSharp.BrowserSubprocess.exe (PID: 3688)
- CefSharp.BrowserSubprocess.exe (PID: 2168)
- CefSharp.BrowserSubprocess.exe (PID: 3692)
- CefSharp.BrowserSubprocess.exe (PID: 3644)
Loads dropped or rewritten executable
- DeepL.exe (PID: 3920)
- CefSharp.BrowserSubprocess.exe (PID: 3688)
- DeepL.exe (PID: 3132)
- CefSharp.BrowserSubprocess.exe (PID: 2168)
- CefSharp.BrowserSubprocess.exe (PID: 3692)
- CefSharp.BrowserSubprocess.exe (PID: 3644)
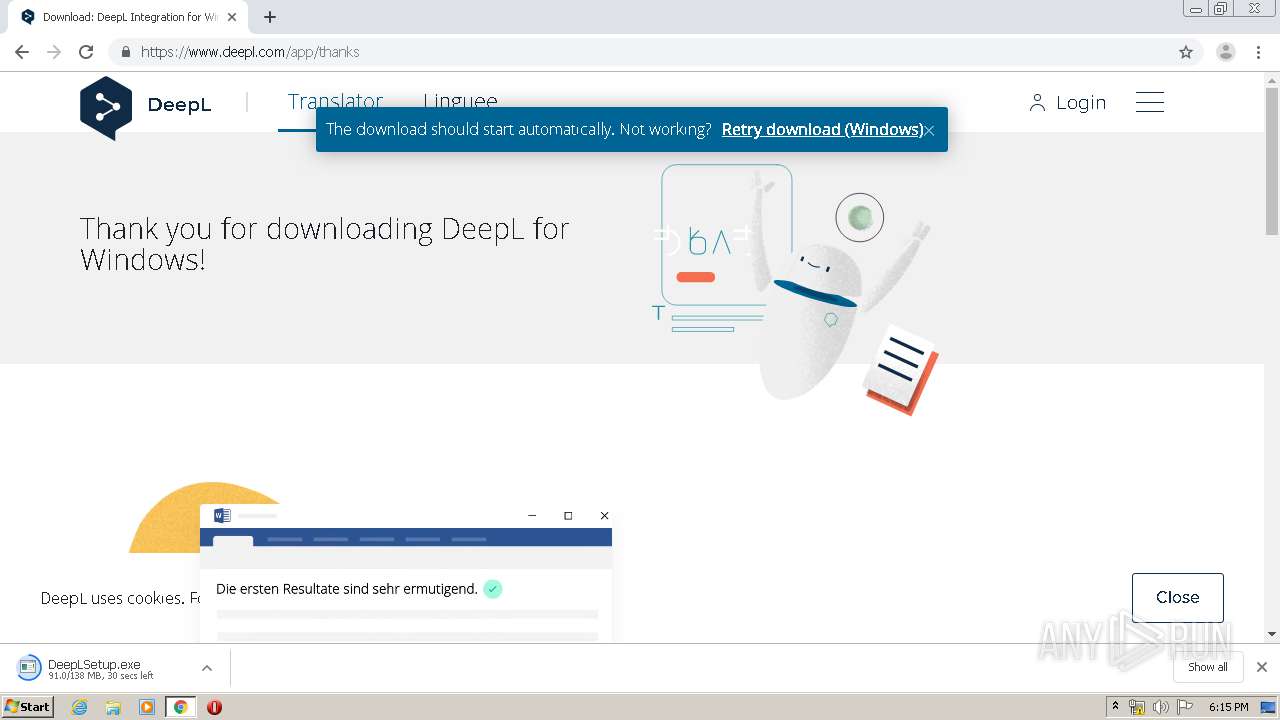
Changes the autorun value in the registry
- DeepL.exe (PID: 3920)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2296)
- DeepLSetup.exe (PID: 3084)
- Update.exe (PID: 3156)
Reads Environment values
- DeepL.exe (PID: 3920)
- DeepL.exe (PID: 3132)
Creates files in the user directory
- DeepL.exe (PID: 3920)
Creates a software uninstall entry
- DeepL.exe (PID: 3920)
- Update.exe (PID: 3156)
Creates files in the program directory
- DeepL.exe (PID: 3920)
Searches for installed software
- Update.exe (PID: 3156)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2296)
INFO
Reads the hosts file
- chrome.exe (PID: 2296)
- chrome.exe (PID: 3128)
- DeepL.exe (PID: 3132)
- CefSharp.BrowserSubprocess.exe (PID: 2168)
Application launched itself
- chrome.exe (PID: 2296)
Reads settings of System Certificates
- chrome.exe (PID: 2296)
Reads Internet Cache Settings
- chrome.exe (PID: 2296)
Dropped object may contain Bitcoin addresses
- Update.exe (PID: 3156)
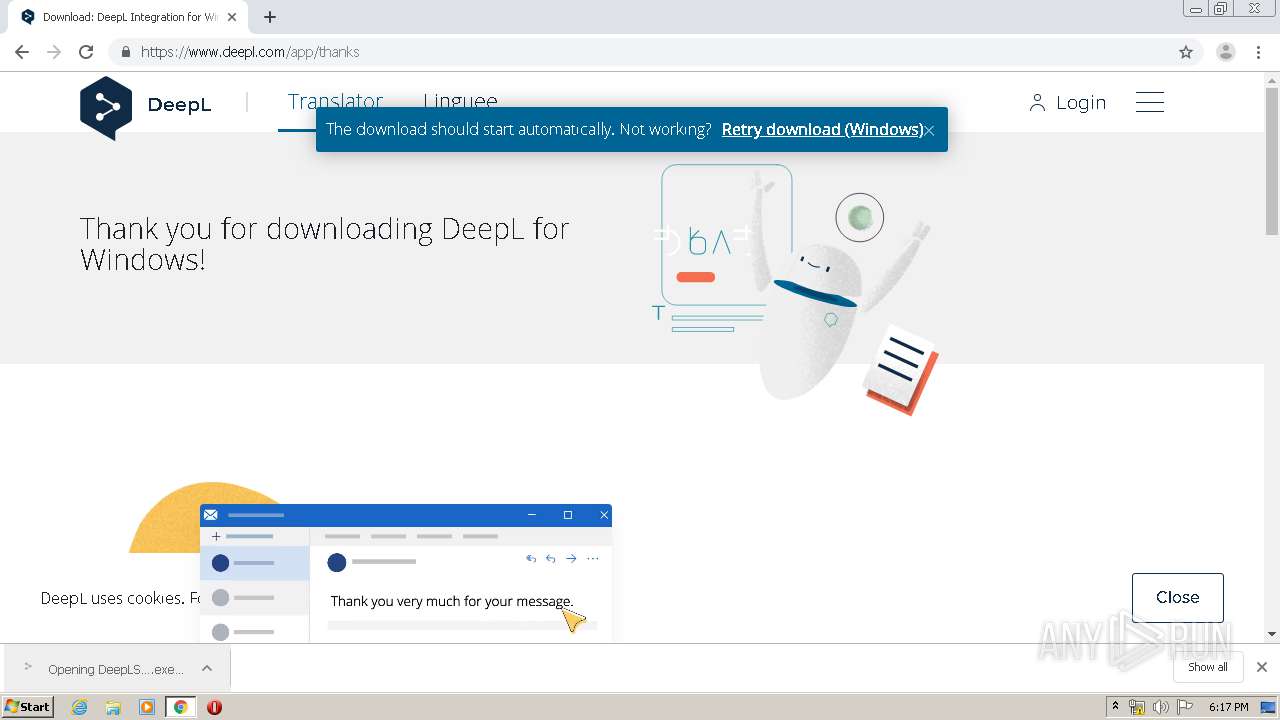
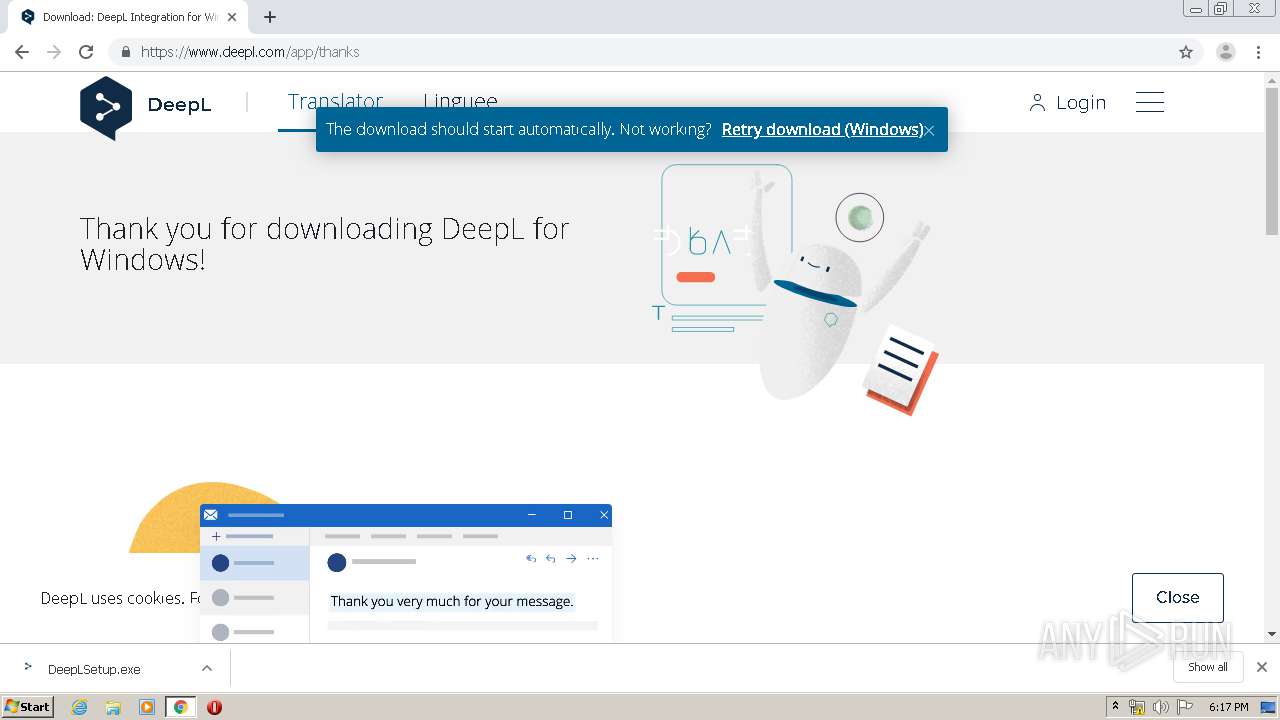
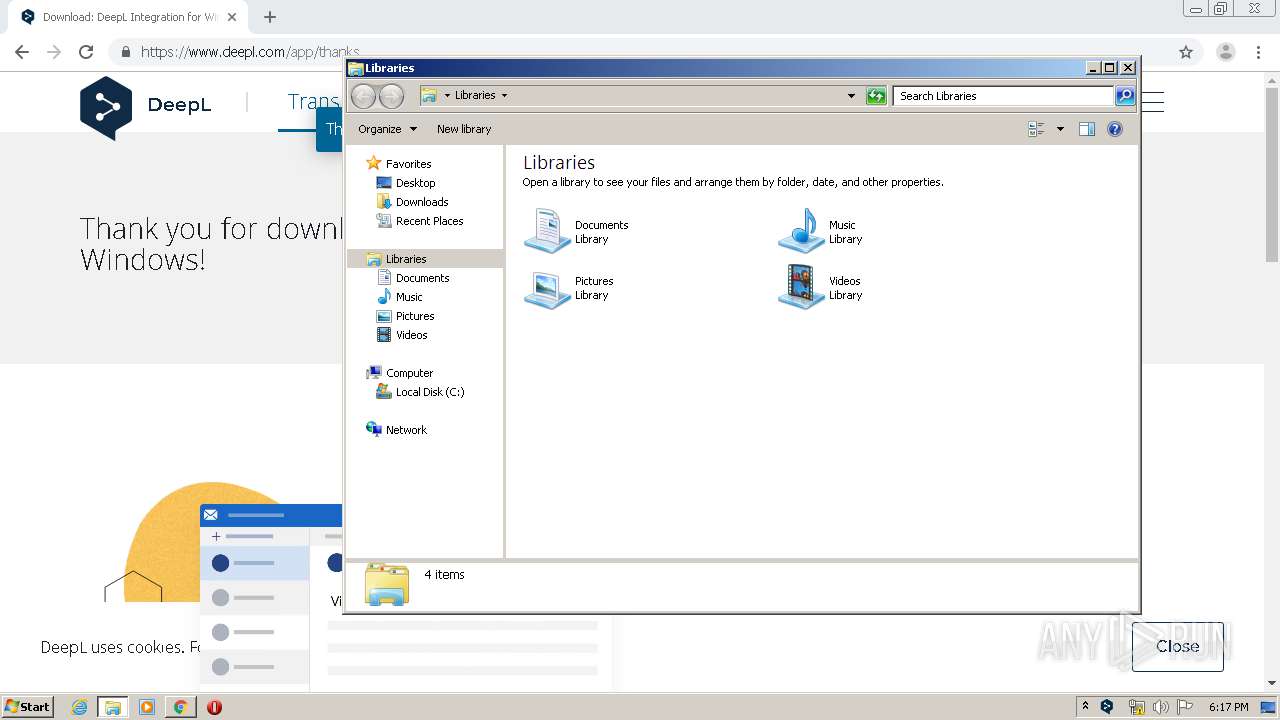
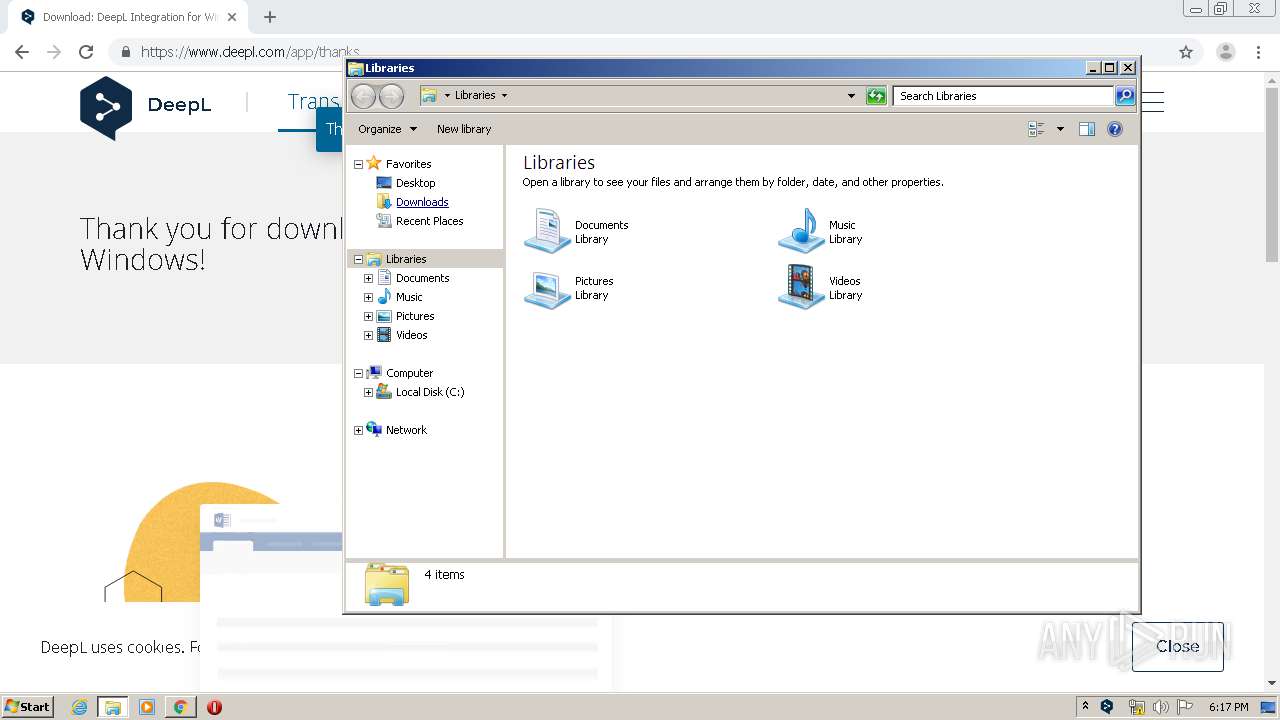
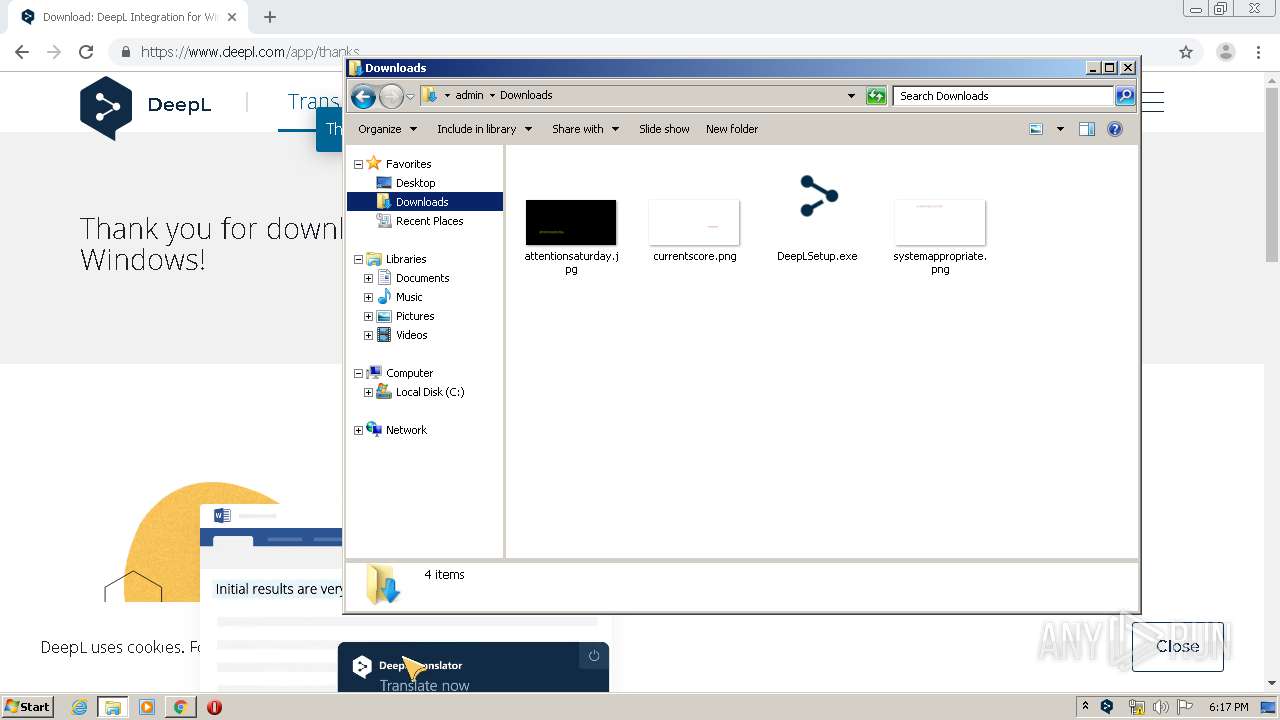
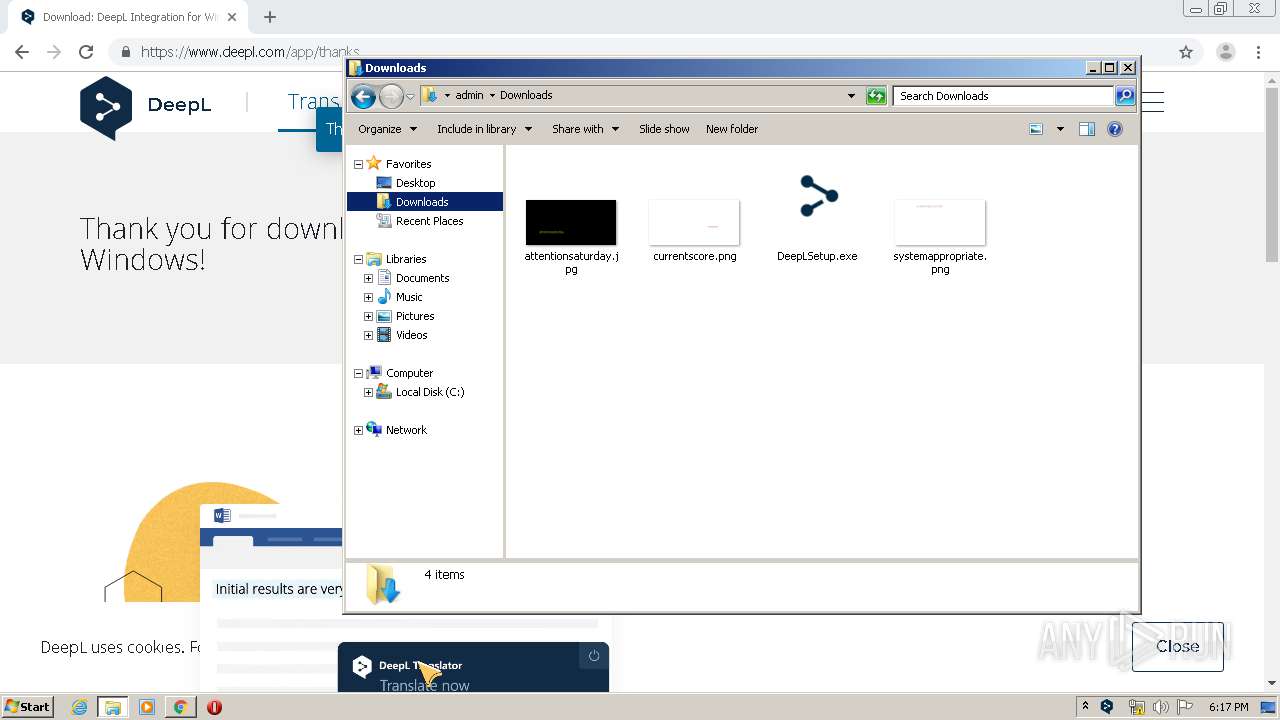
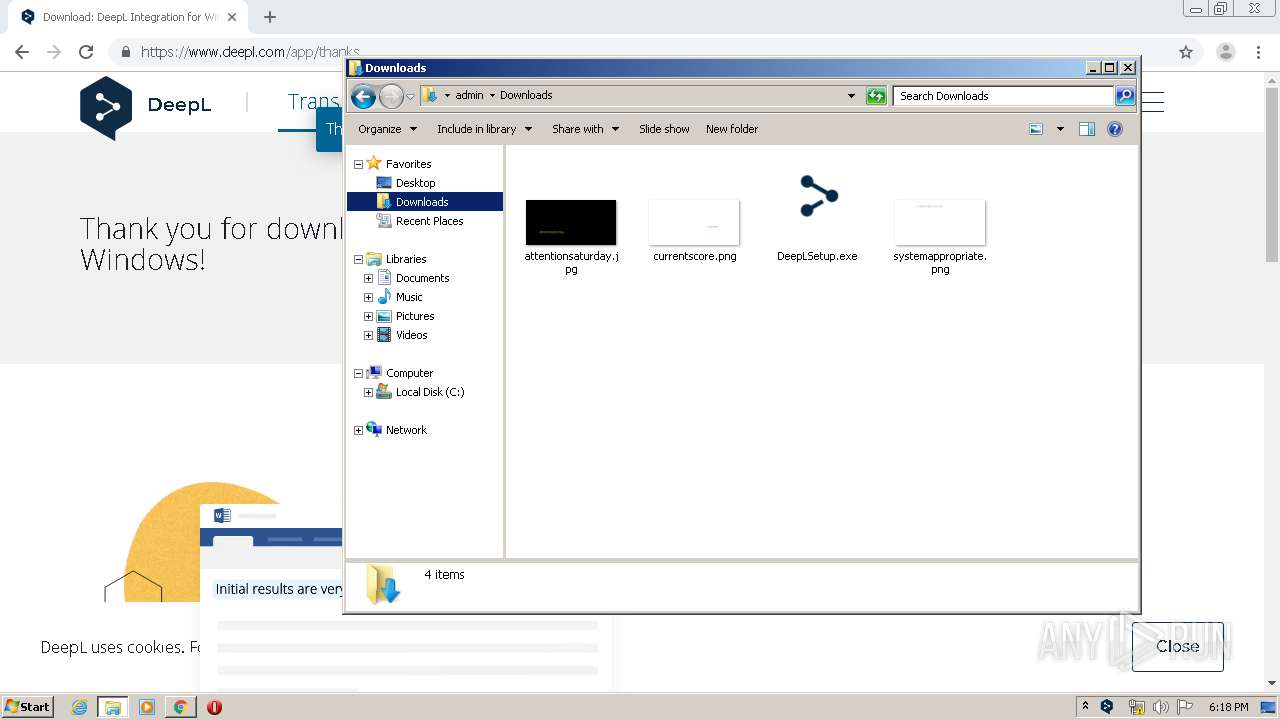
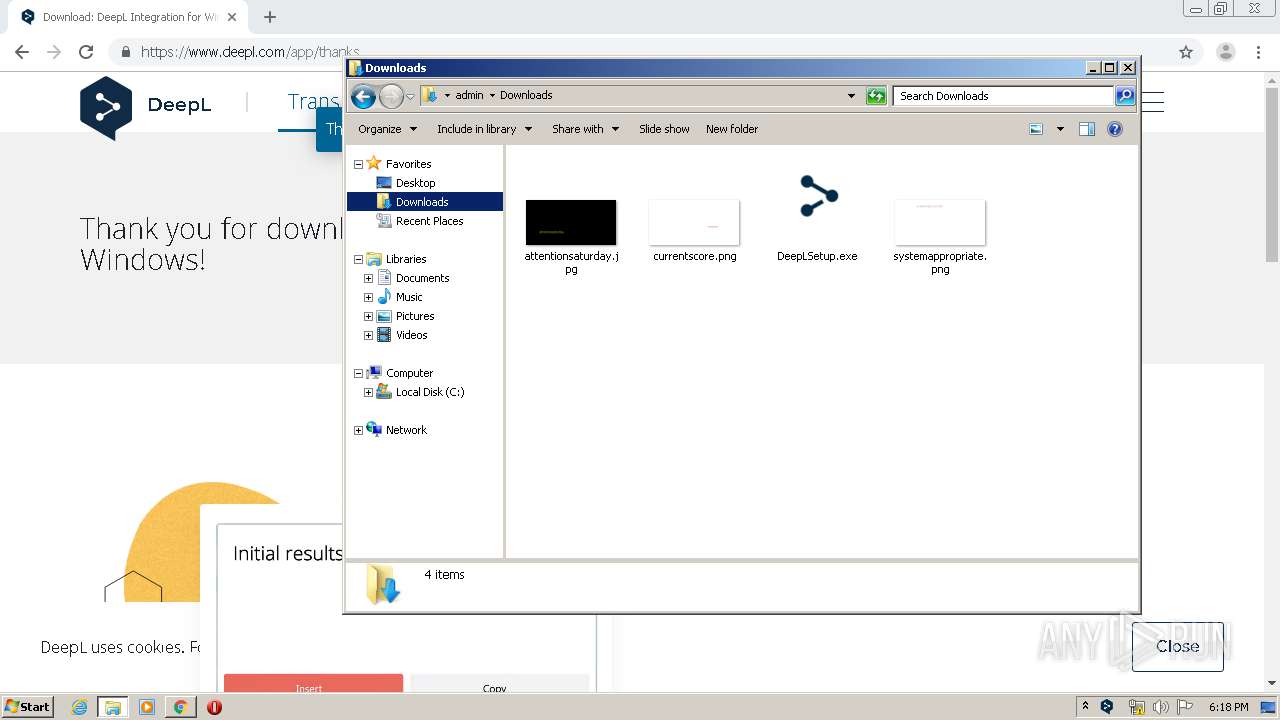
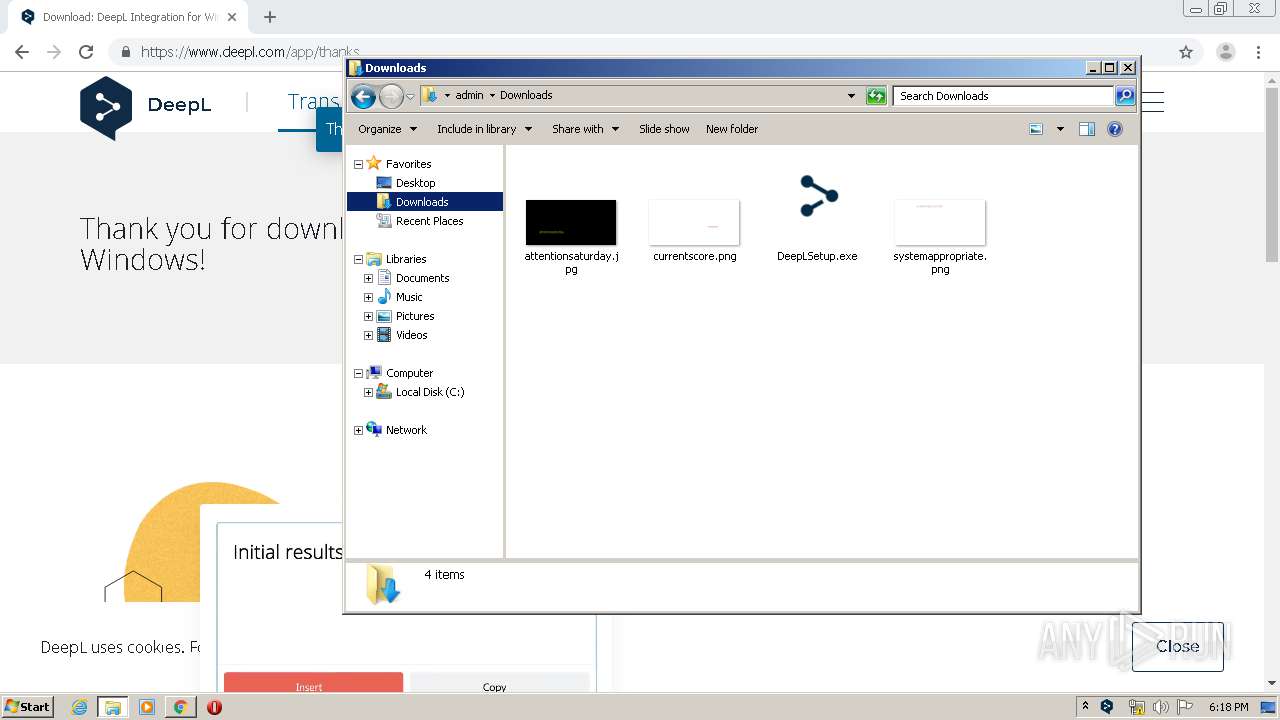
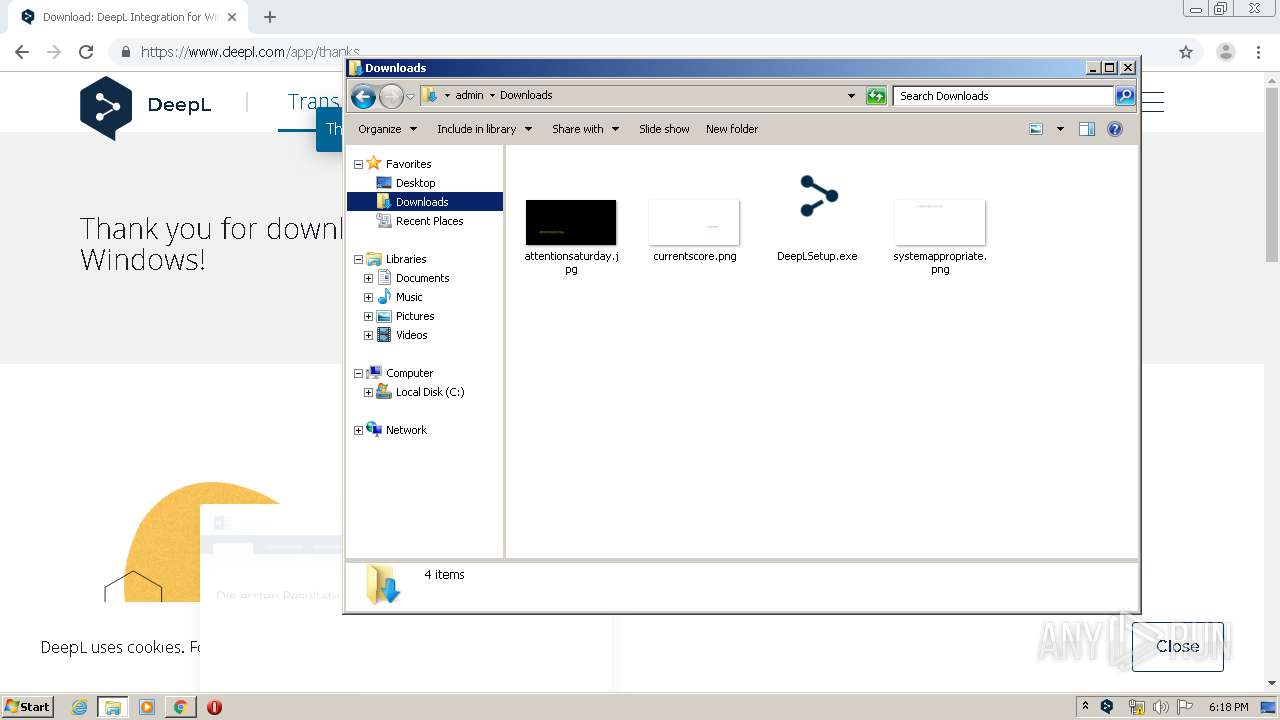
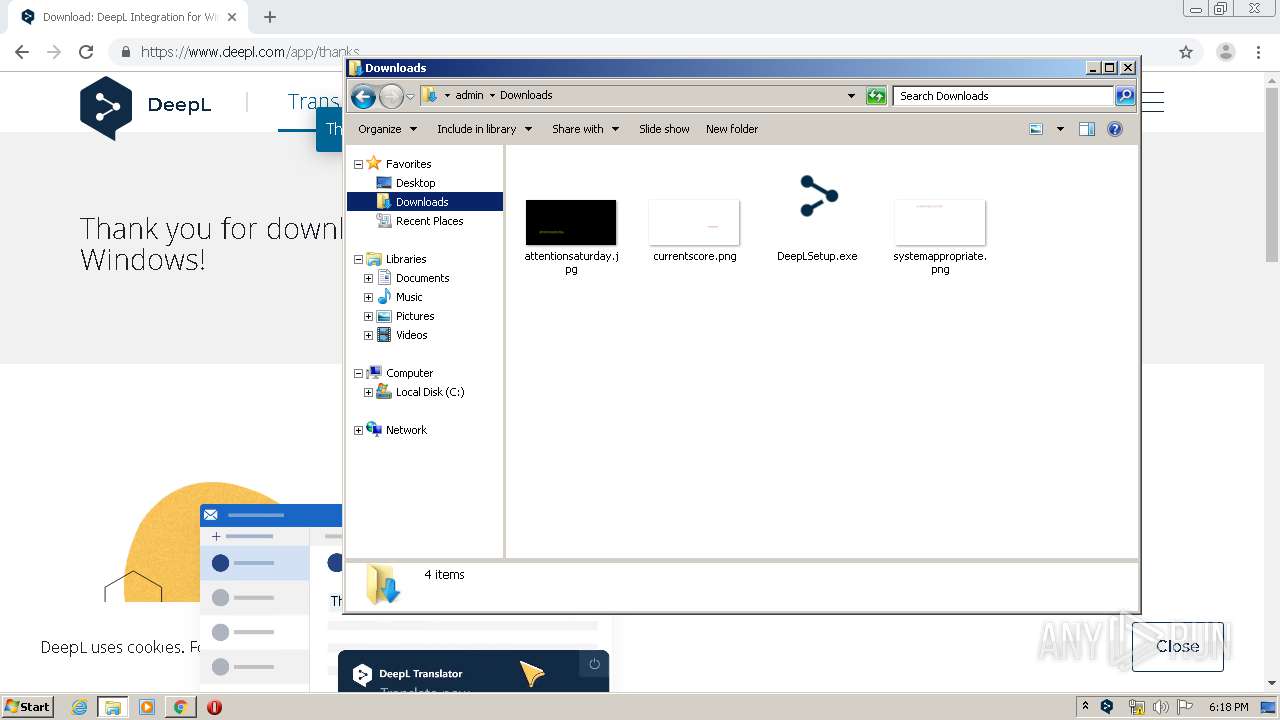
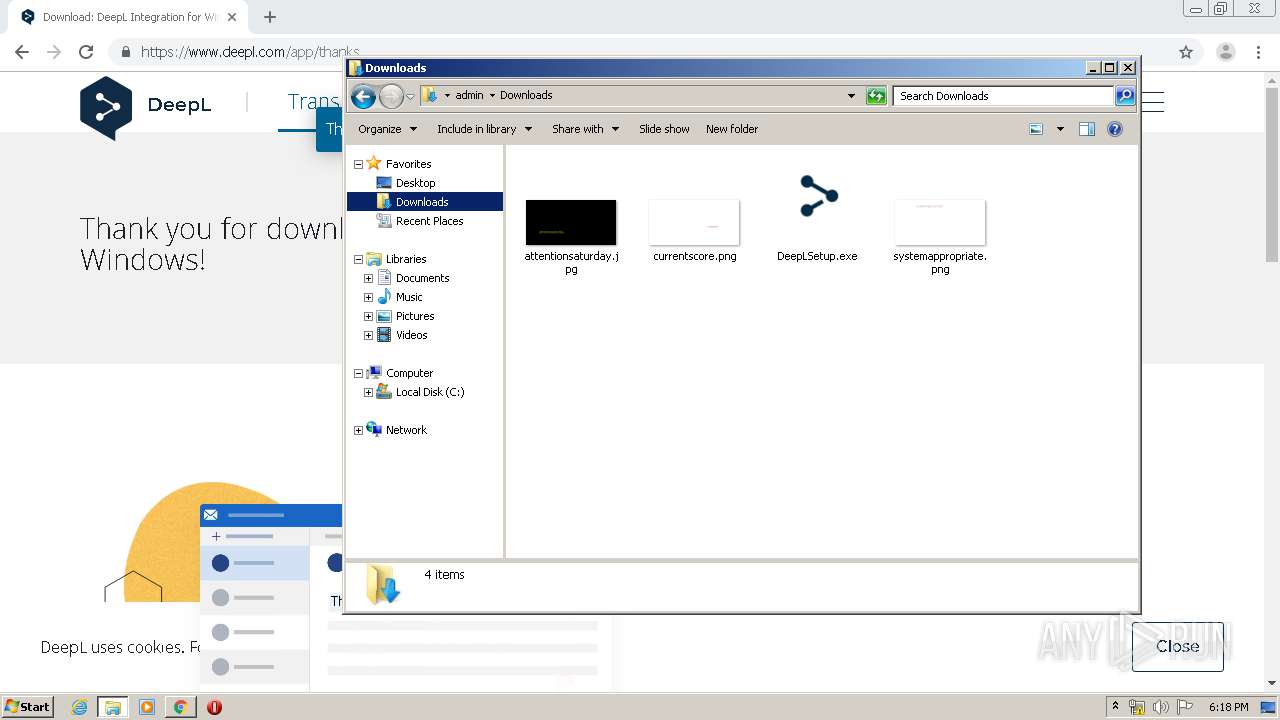
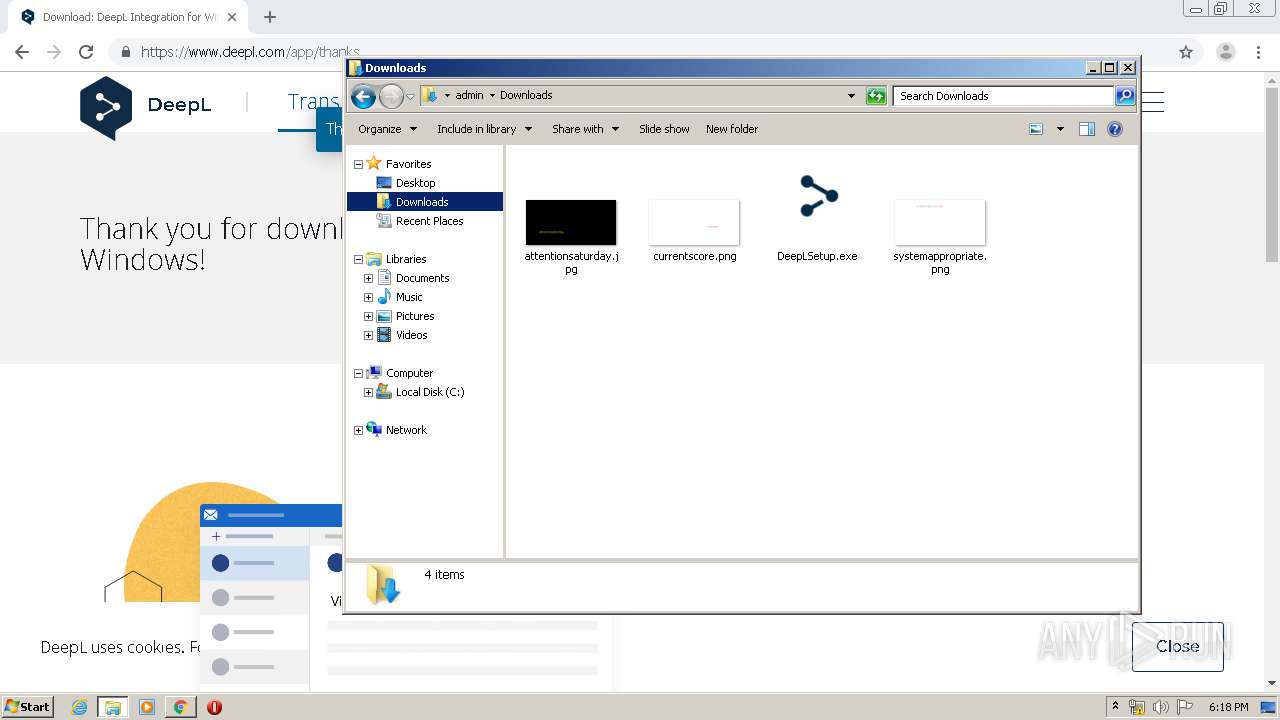
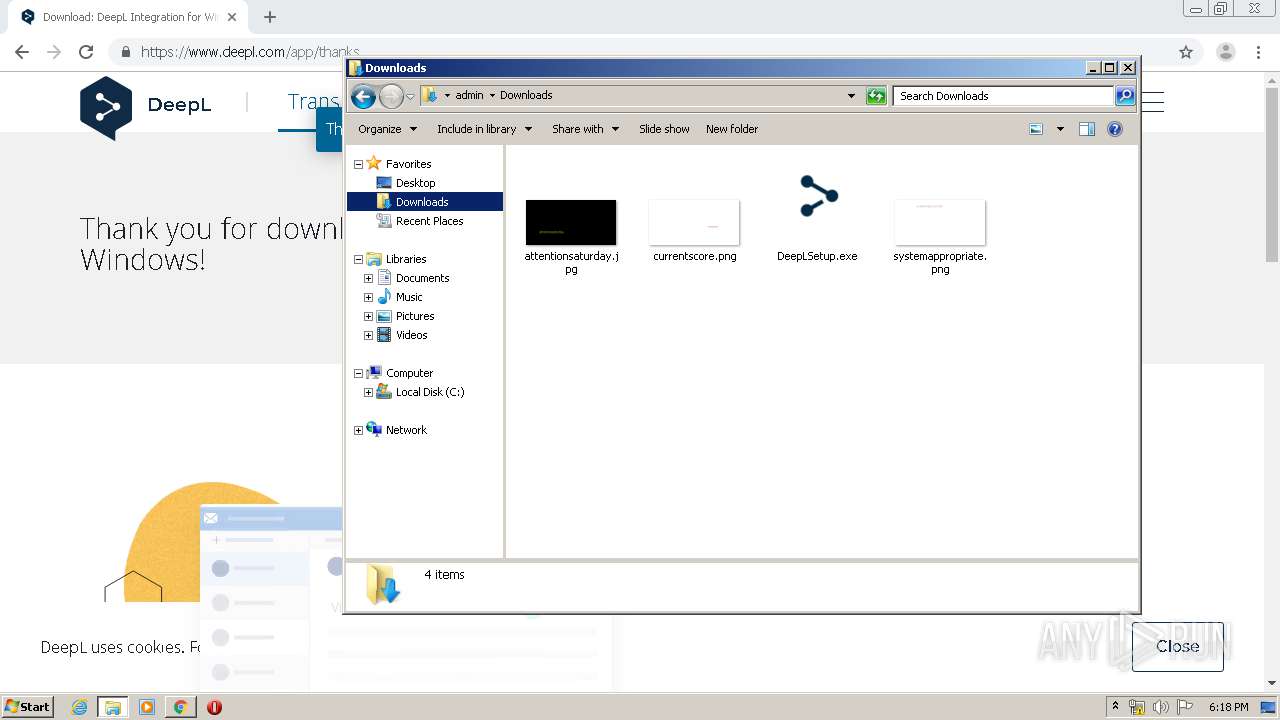
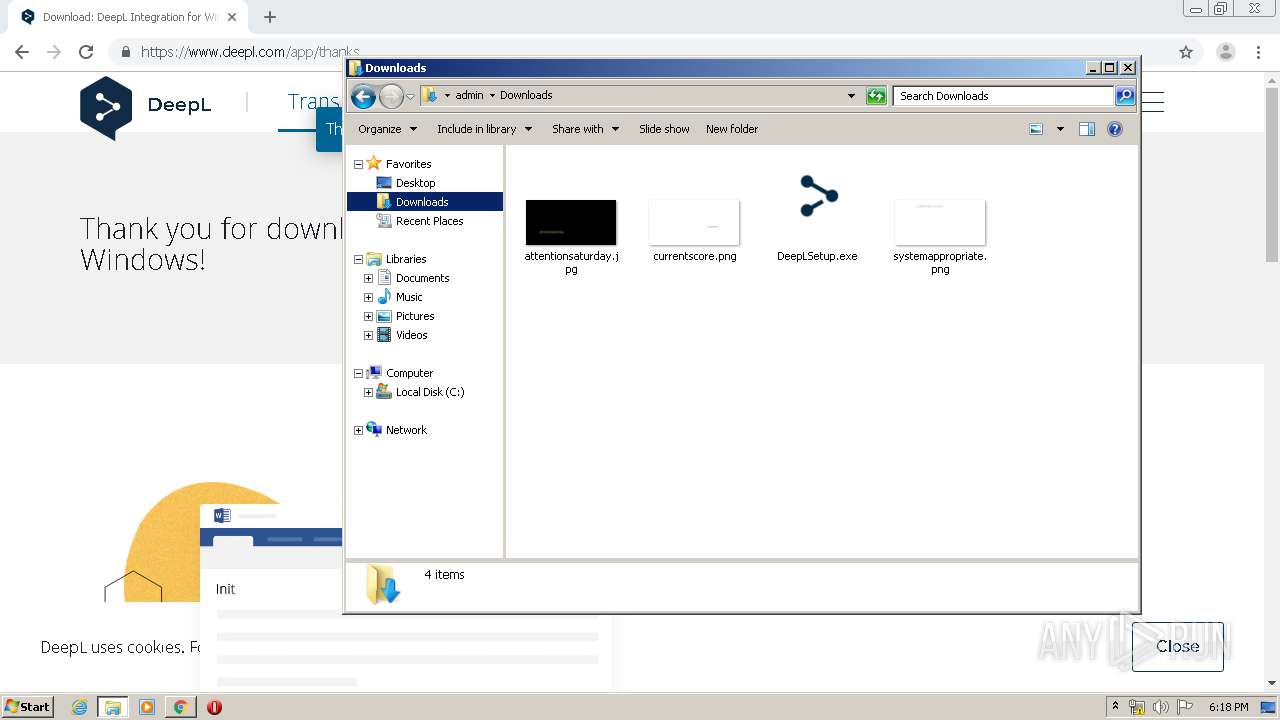
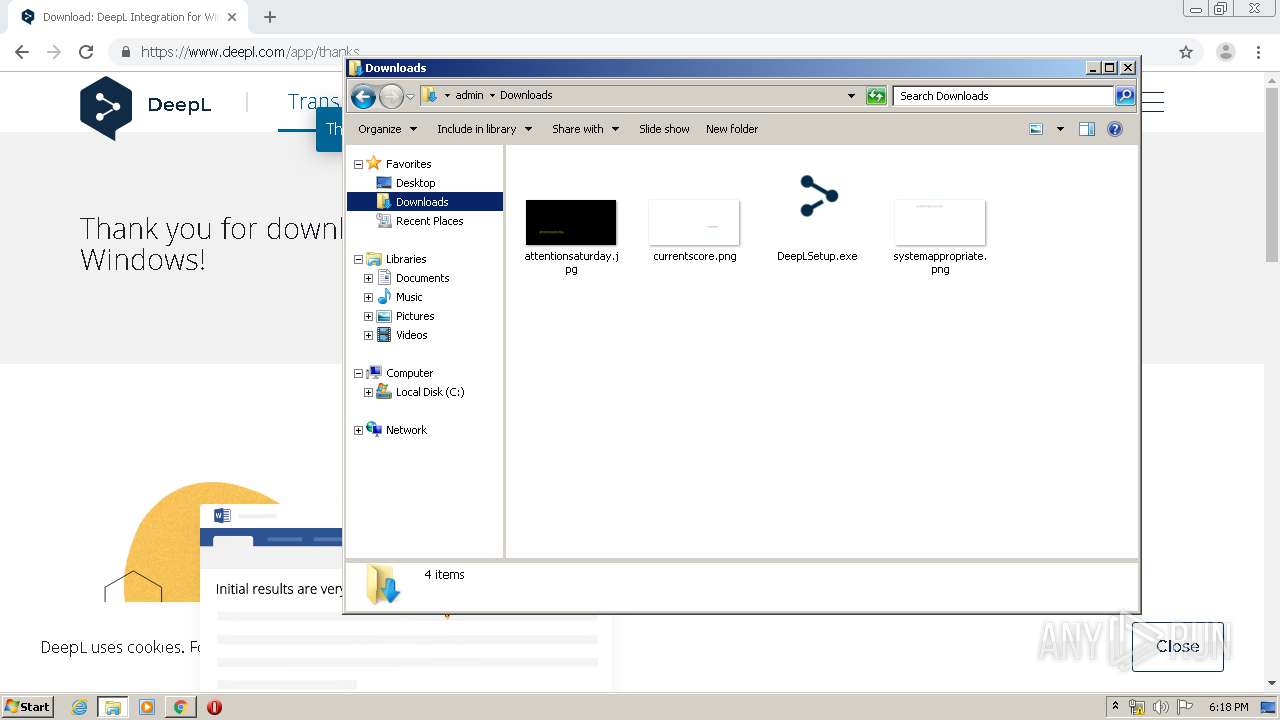
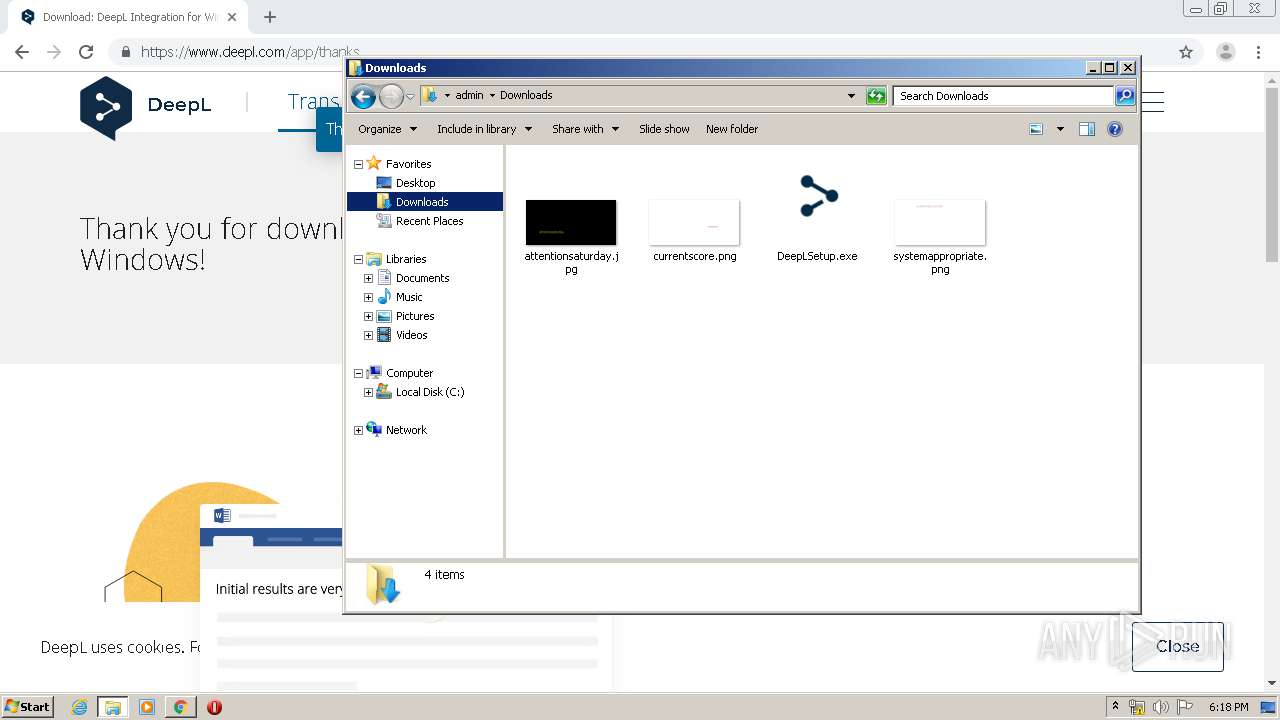
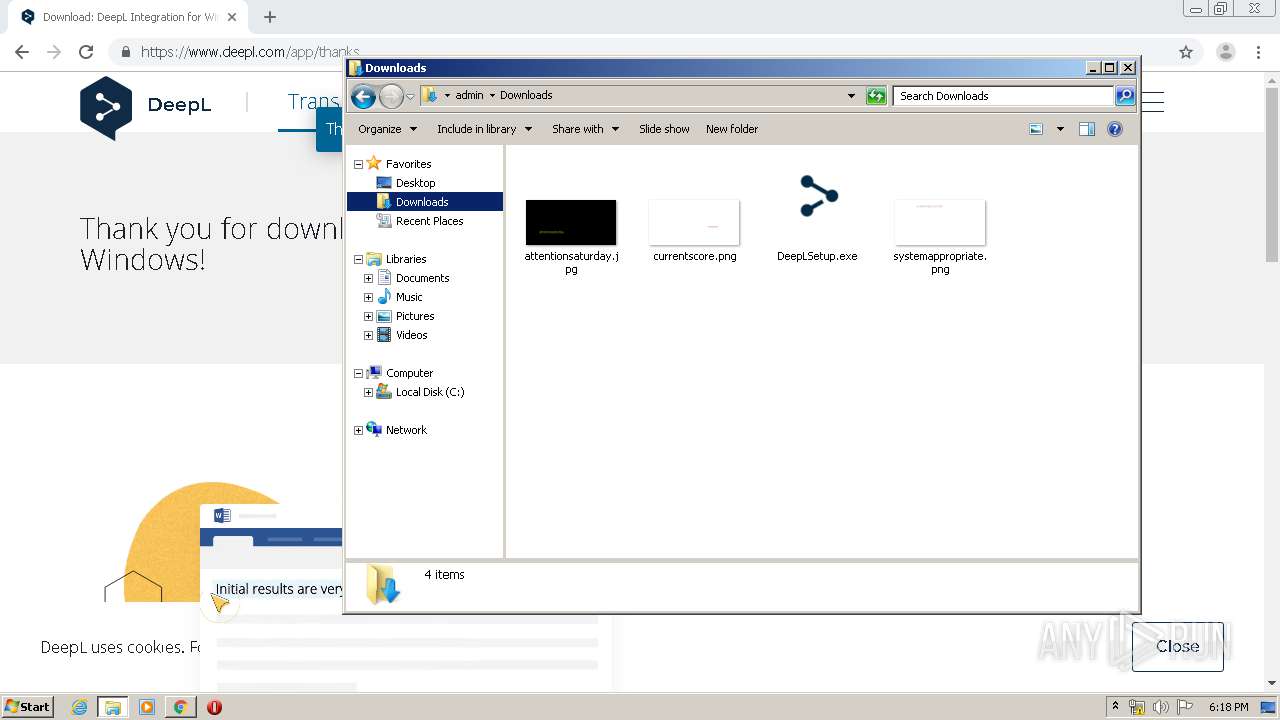
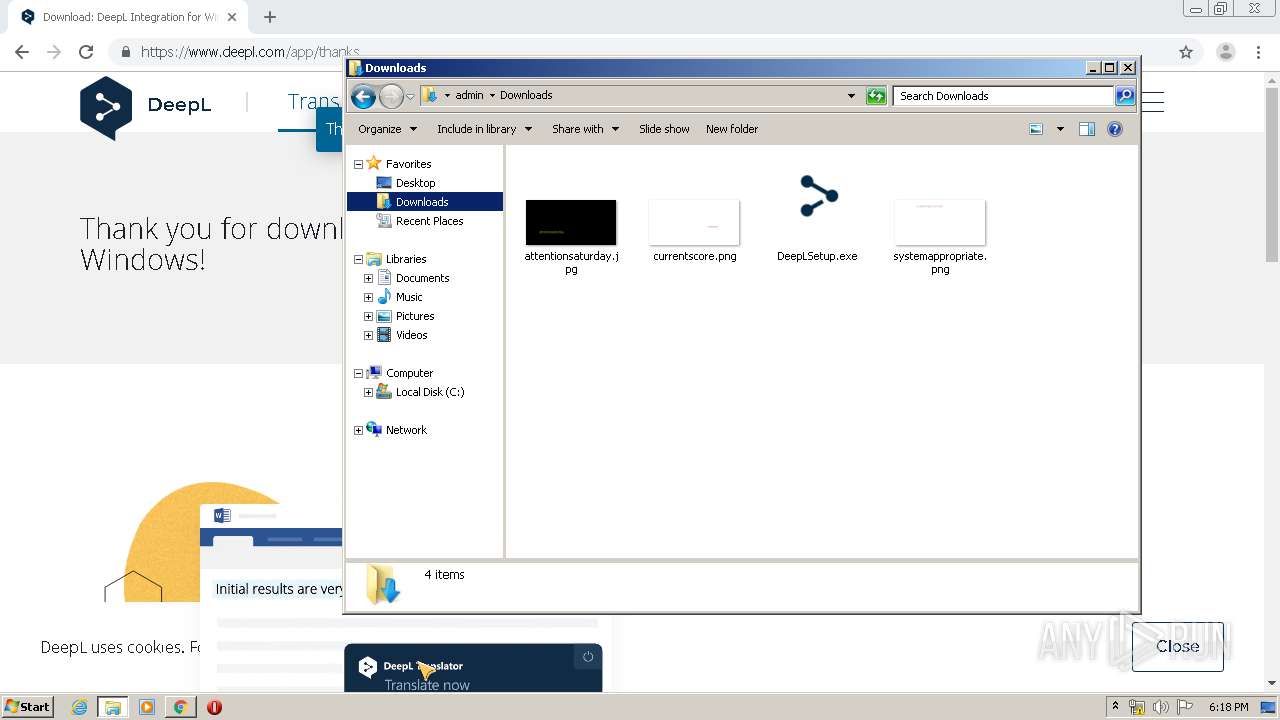
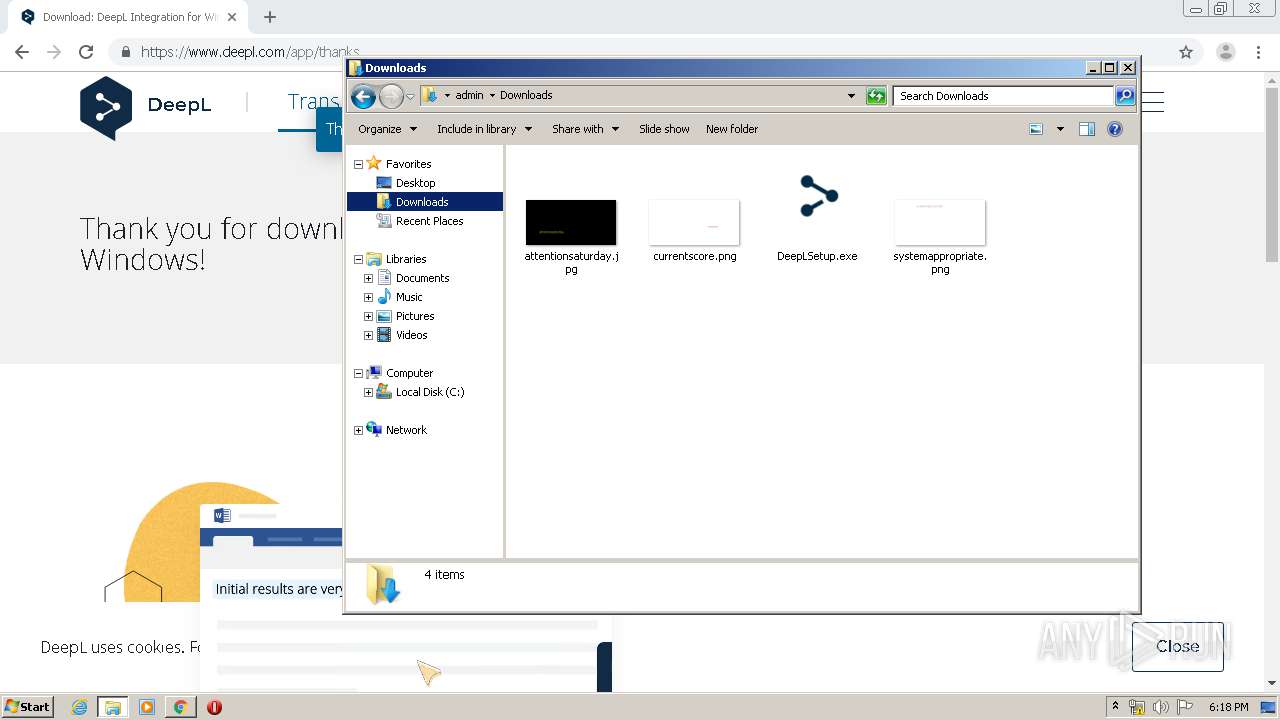
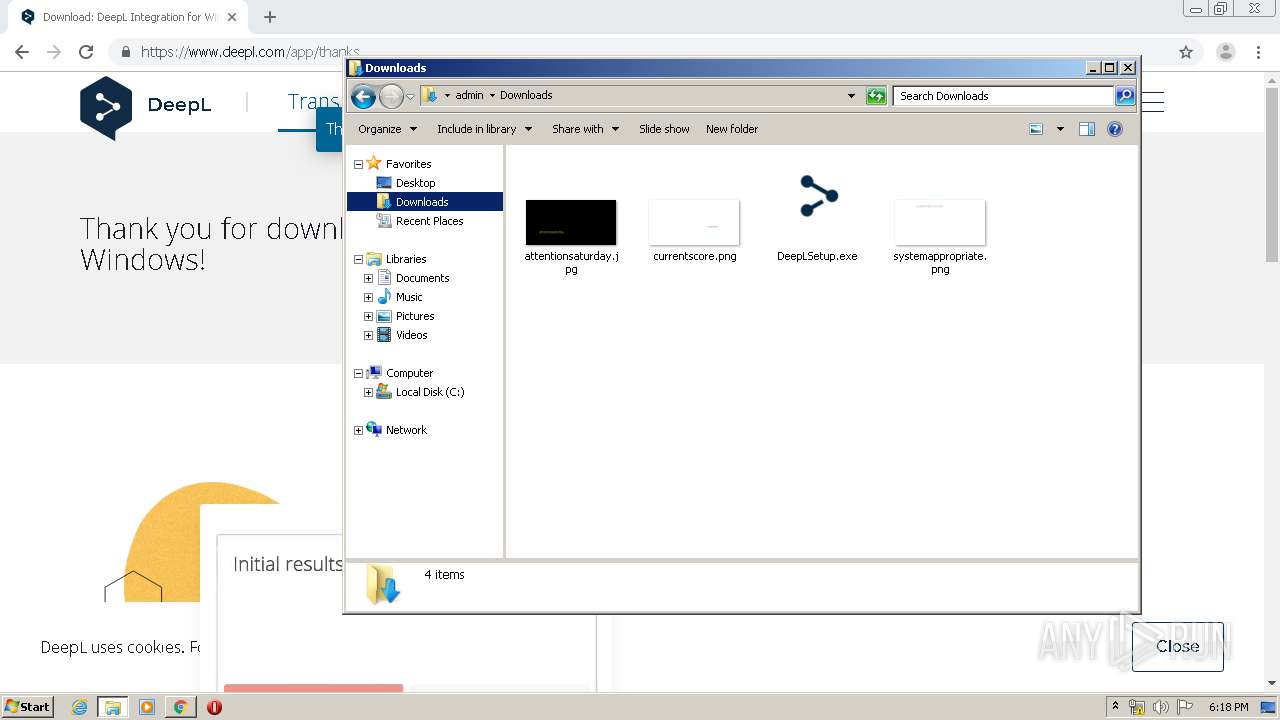
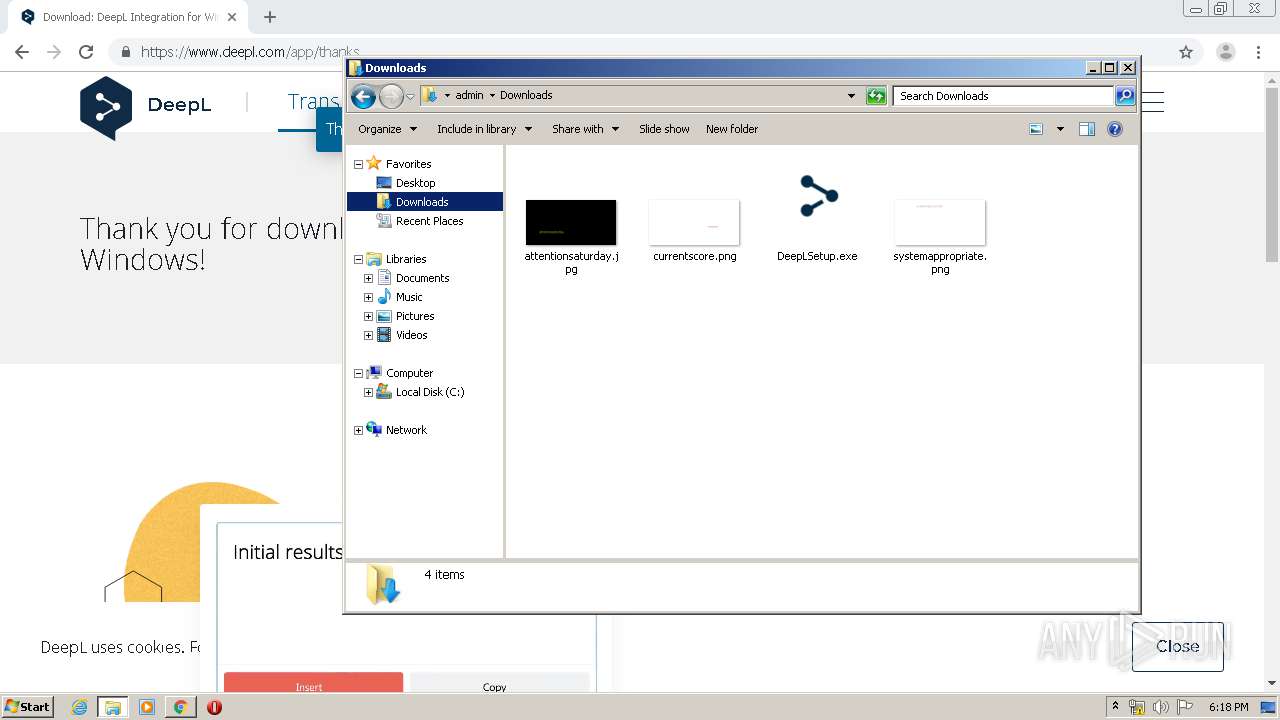
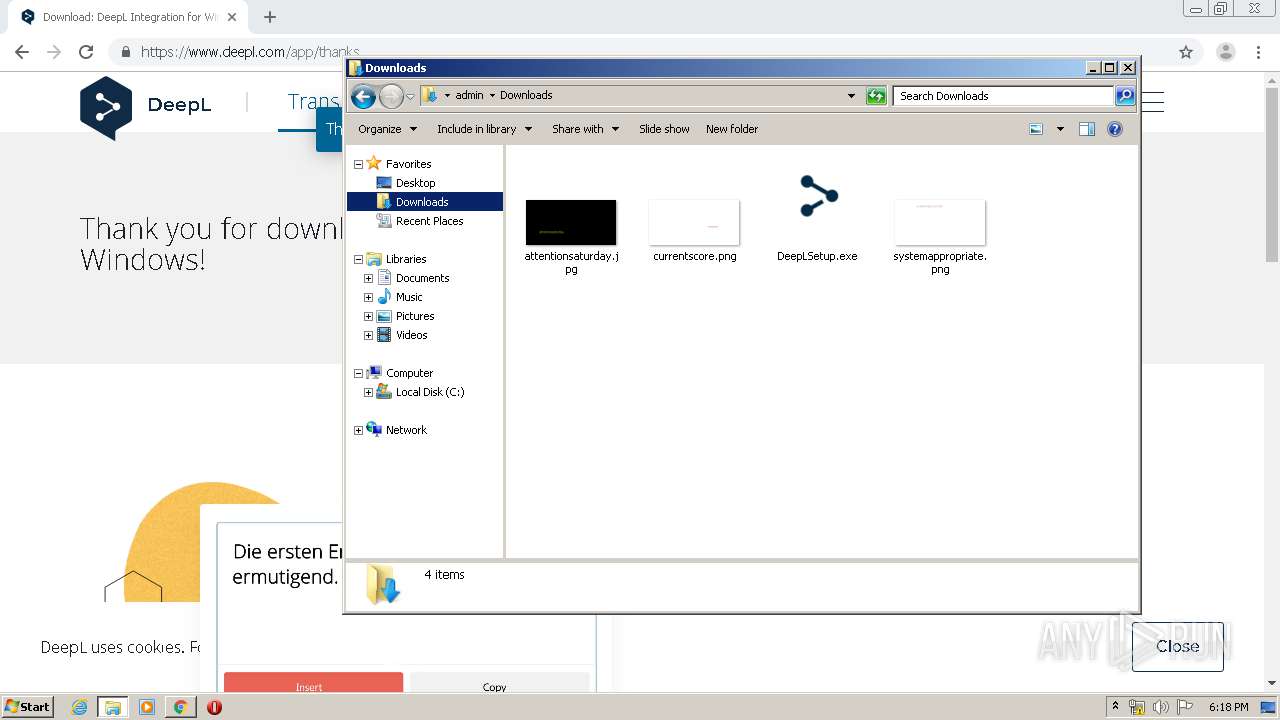
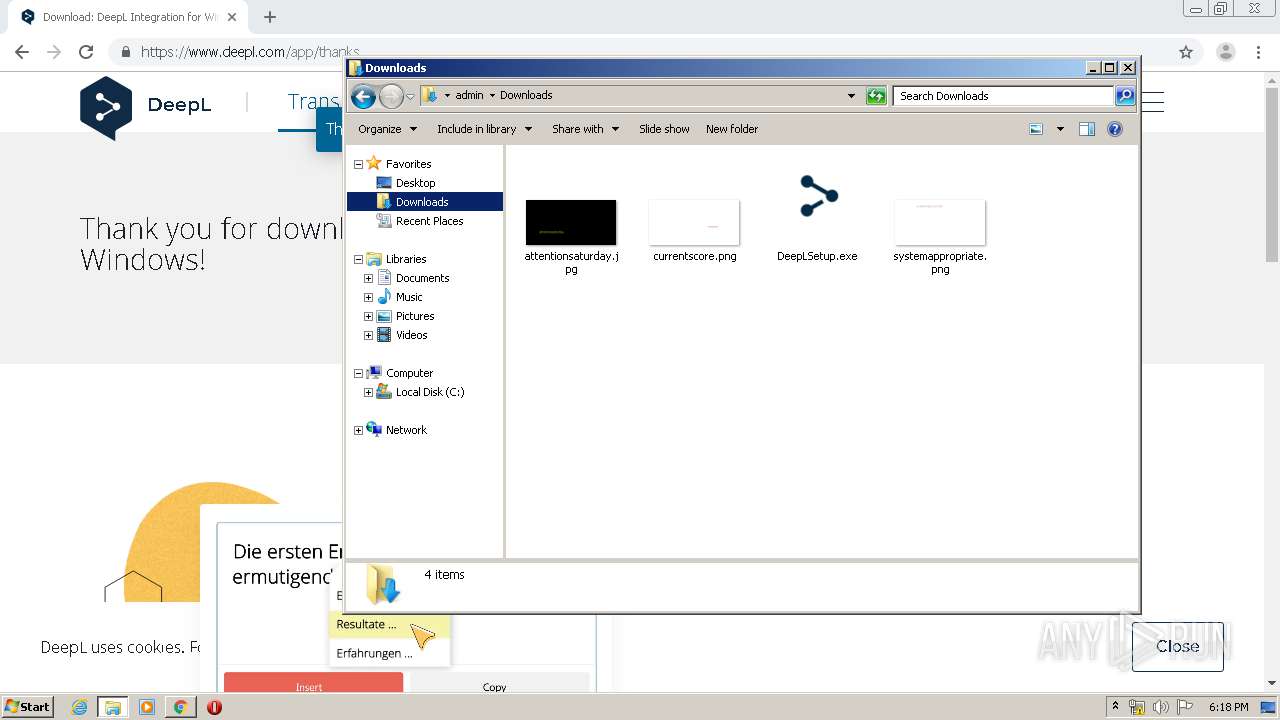
Manual execution by user
- explorer.exe (PID: 2800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
77
Monitored processes
35
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,4699929076933261588,8658156528357005958,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13218102936385222972 --mojo-platform-channel-handle=3360 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,4699929076933261588,8658156528357005958,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5843748844567014204 --mojo-platform-channel-handle=4240 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,4699929076933261588,8658156528357005958,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3323609352438804342 --mojo-platform-channel-handle=4264 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,4699929076933261588,8658156528357005958,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13535577796383934856 --mojo-platform-channel-handle=4188 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,4699929076933261588,8658156528357005958,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8639032947836984318 --mojo-platform-channel-handle=4324 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,4699929076933261588,8658156528357005958,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6409592320109192222 --mojo-platform-channel-handle=3792 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,4699929076933261588,8658156528357005958,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15534092550597028800 --mojo-platform-channel-handle=4264 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,4699929076933261588,8658156528357005958,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1431622277128733786 --mojo-platform-channel-handle=4644 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,4699929076933261588,8658156528357005958,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2751734952819248769 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1984 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,4699929076933261588,8658156528357005958,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4103156898944818168 --mojo-platform-channel-handle=3980 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 998
Read events
1 811
Write events
182
Delete events
5
Modification events
| (PID) Process: | (2296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2860) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2296-13233863691060000 |
Value: 259 | |||
| (PID) Process: | (2296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2296) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2296) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
277
Suspicious files
69
Text files
287
Unknown types
140
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EBC2B0B-8F8.pma | — | |
MD5:— | SHA256:— | |||
| 2296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7f62e539-d0c6-43e2-82c8-6f3e45451bf1.tmp | — | |
MD5:— | SHA256:— | |||
| 2296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RFa87638.TMP | — | |
MD5:— | SHA256:— | |||
| 2296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa8751f.TMP | text | |
MD5:— | SHA256:— | |||
| 2296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 2296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa876f4.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
35
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3128 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
3128 | chrome.exe | GET | 200 | 173.194.183.200:80 | http://r3---sn-aigl6nl7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=185.92.25.167&mm=28&mn=sn-aigl6nl7&ms=nvh&mt=1589389992&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 816 Kb | whitelisted |
3128 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 524 b | whitelisted |
3128 | chrome.exe | GET | 200 | 173.194.183.168:80 | http://r3---sn-aigl6ney.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.92.25.167&mm=28&mn=sn-aigl6ney&ms=nvh&mt=1589389992&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3128 | chrome.exe | 172.65.253.13:443 | www.deepl.com | Cloudflare Inc | US | suspicious |
3128 | chrome.exe | 216.58.212.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3128 | chrome.exe | 172.217.22.78:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3128 | chrome.exe | 172.217.23.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
3128 | chrome.exe | 172.65.226.29:443 | s.deepl.com | Cloudflare Inc | US | suspicious |
3128 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
3128 | chrome.exe | 85.93.93.95:443 | appdownload.deepl.com | Host Europe GmbH | DE | unknown |
3128 | chrome.exe | 172.217.23.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3128 | chrome.exe | 173.194.183.168:80 | r3---sn-aigl6ney.gvt1.com | Google Inc. | US | whitelisted |
3128 | chrome.exe | 216.58.208.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.deepl.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
clients1.google.com |
| whitelisted |
s.deepl.com |
| suspicious |
www.google.com |
| malicious |
appdownload.deepl.com |
| suspicious |
Threats
Process | Message |
|---|---|
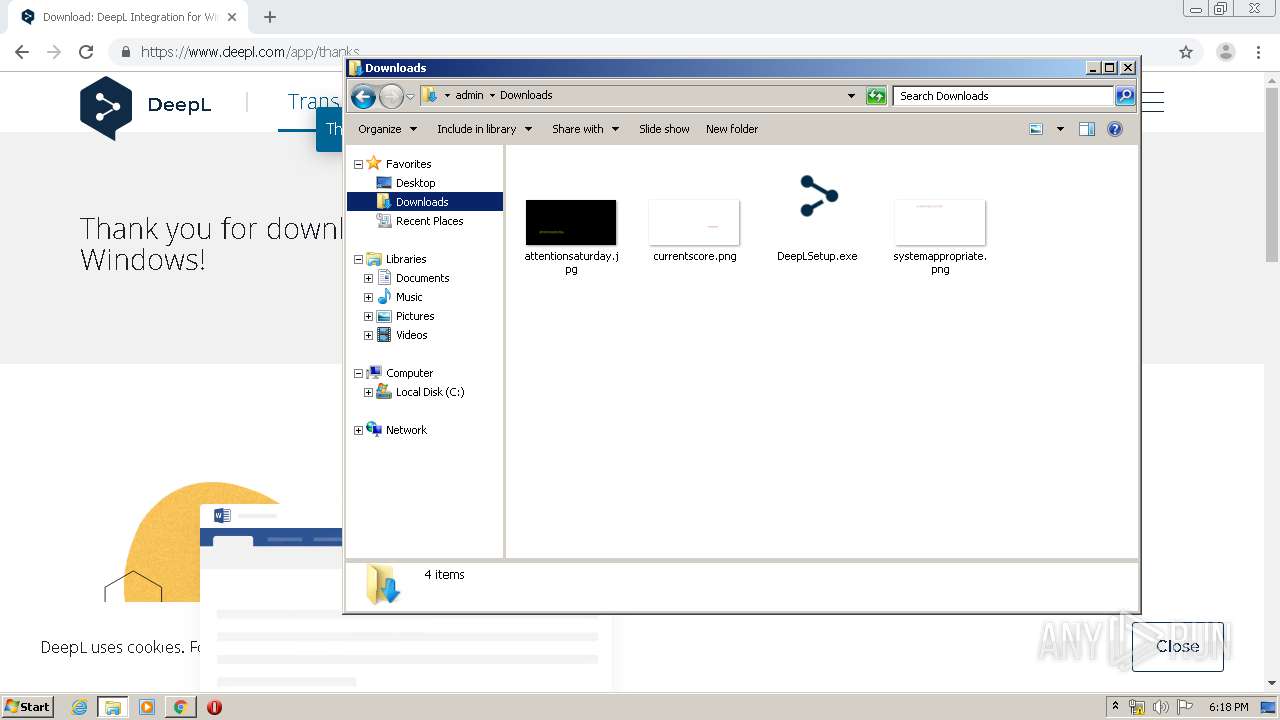
DeepL.exe | Native library pre-loader is trying to load native SQLite library "C:\Users\admin\AppData\Local\DeepL\app-1.11.0\x86\SQLite.Interop.dll"...
|
DeepL.exe | [0513/181738.107:INFO:CONSOLE(18)] "DeepL Translator", source: https://www.deepl.com/js/translator_glossary_late.min.js?v=1157298140 (18)
|
DeepL.exe | [0513/181738.136:INFO:CONSOLE(18)] "isApp", source: https://www.deepl.com/js/translator_glossary_late.min.js?v=1157298140 (18)
|
DeepL.exe | [0513/181738.144:INFO:CONSOLE(3)] "webTranslator.publicInterface.getLangInfo()", source: https://www.deepl.com/js/translator_glossary_late.min.js?v=1157298140 (3)
|
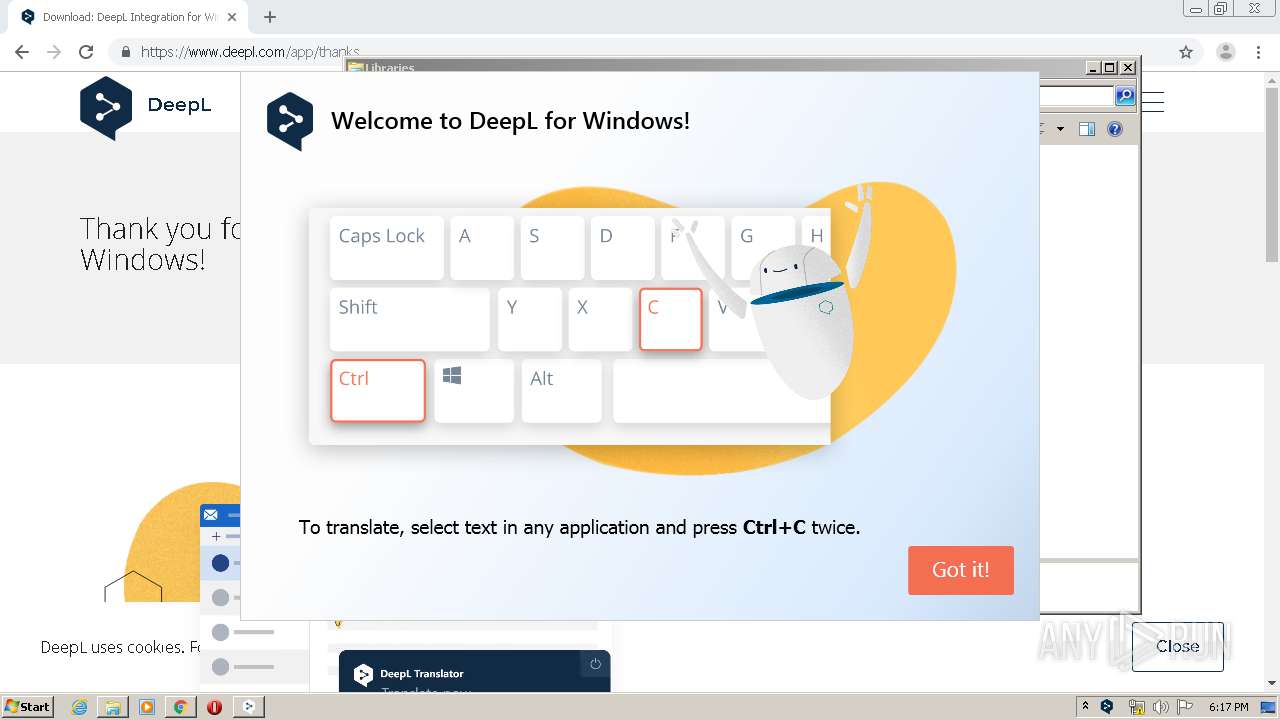
DeepL.exe | [0513/181738.220:INFO:CONSOLE(1)] "Welcome to DeepL.com!", source: https://www.deepl.com/js/translator_glossary_late.min.js?v=1157298140 (1)
|
DeepL.exe | [0513/181738.362:INFO:CONSOLE(3)] "App initialized", source: about:blank (3)
|