| File name: | mrsmajor.exe |
| Full analysis: | https://app.any.run/tasks/bbea9b57-a52f-4e71-a7c5-cb2709da75e5 |
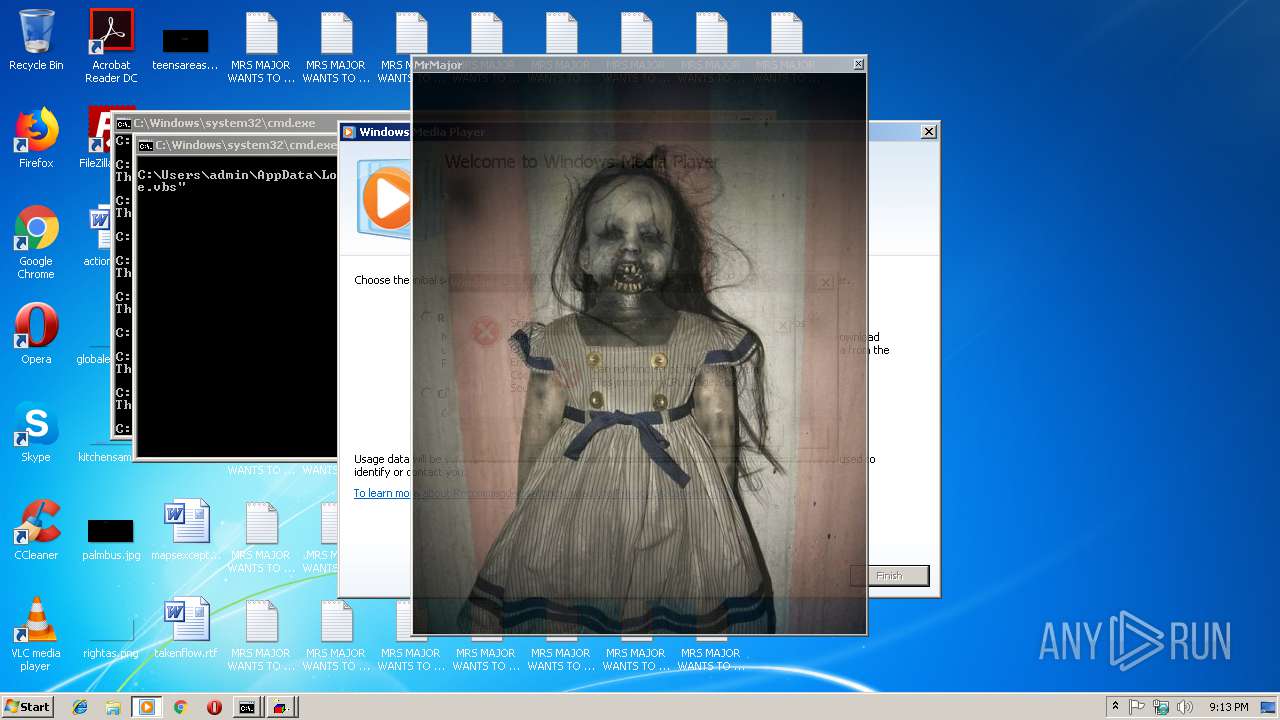
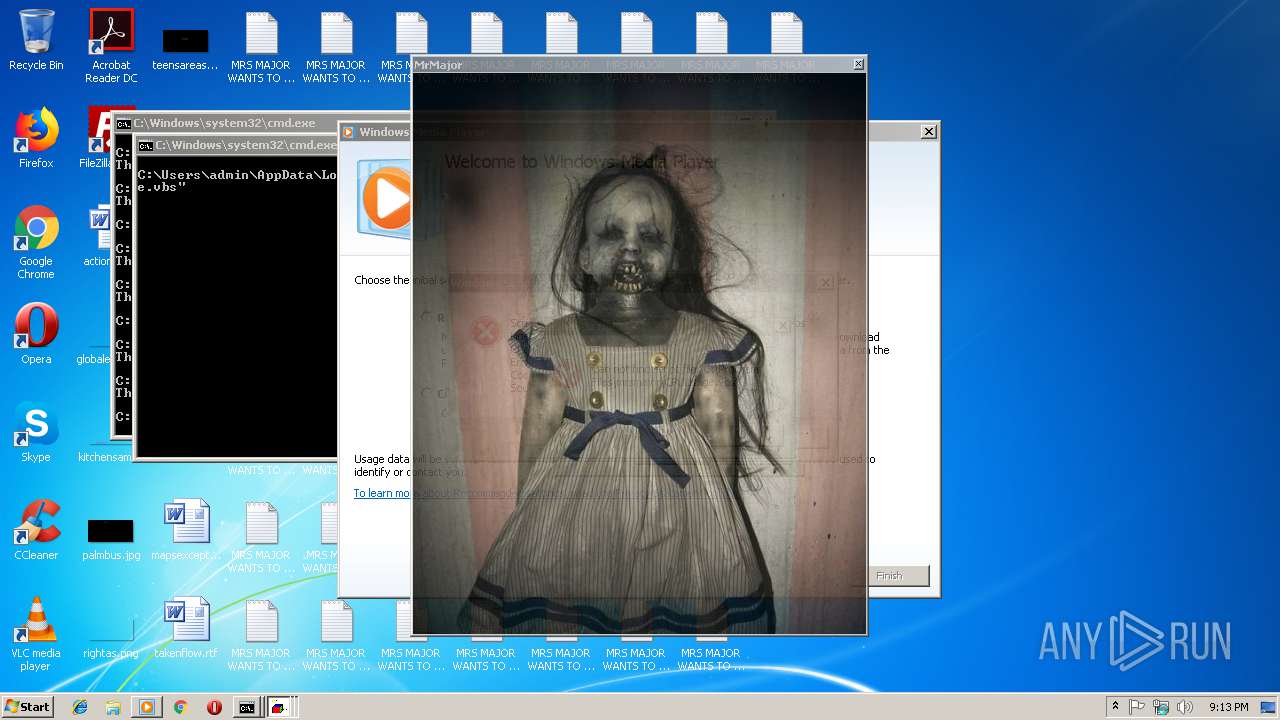
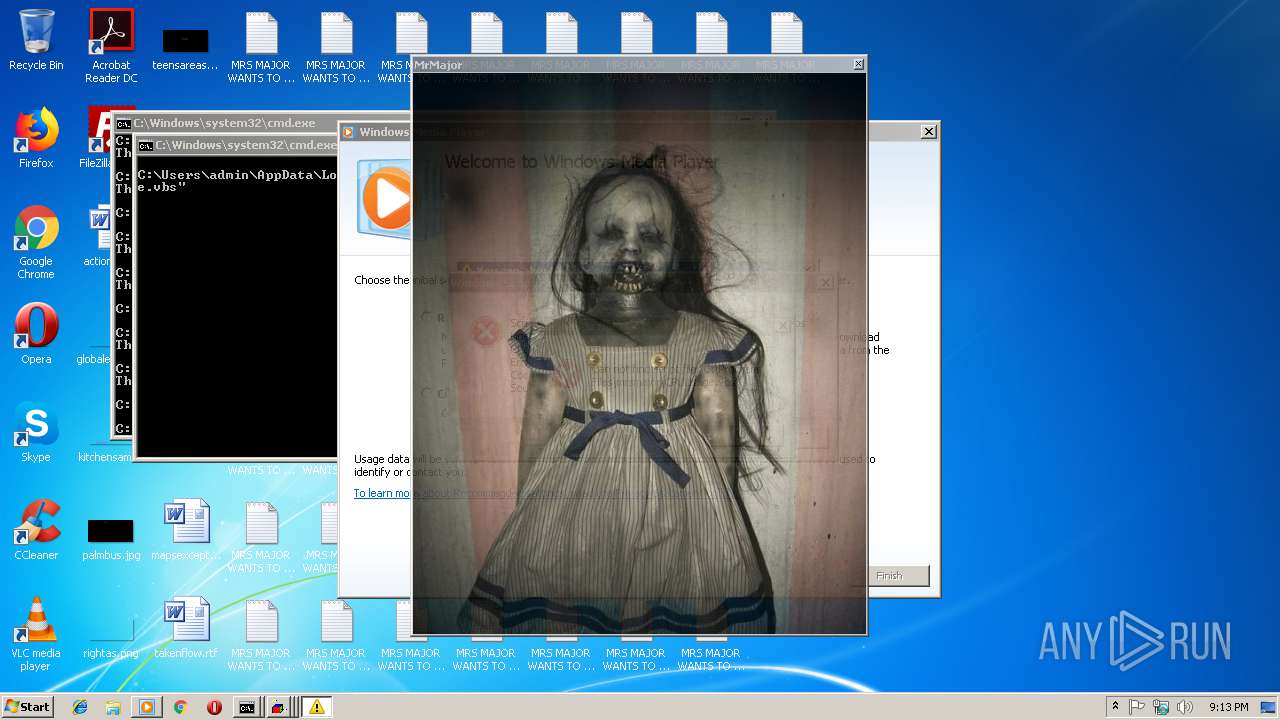
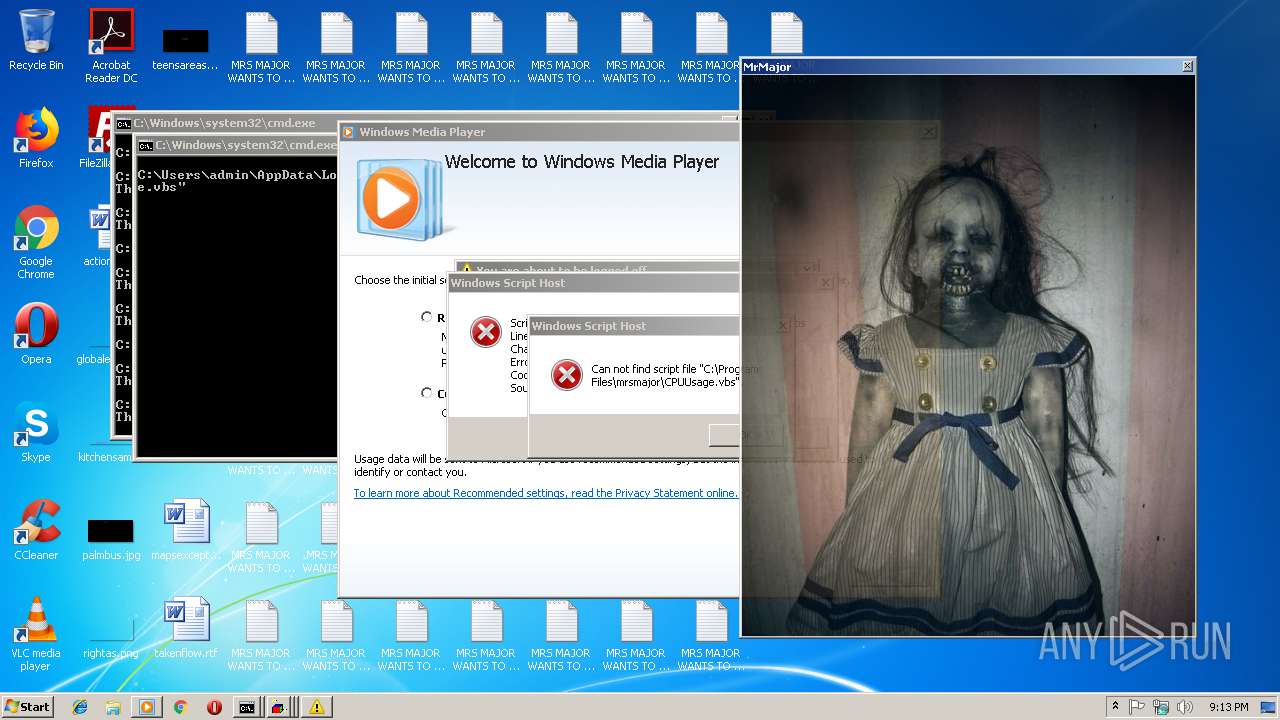
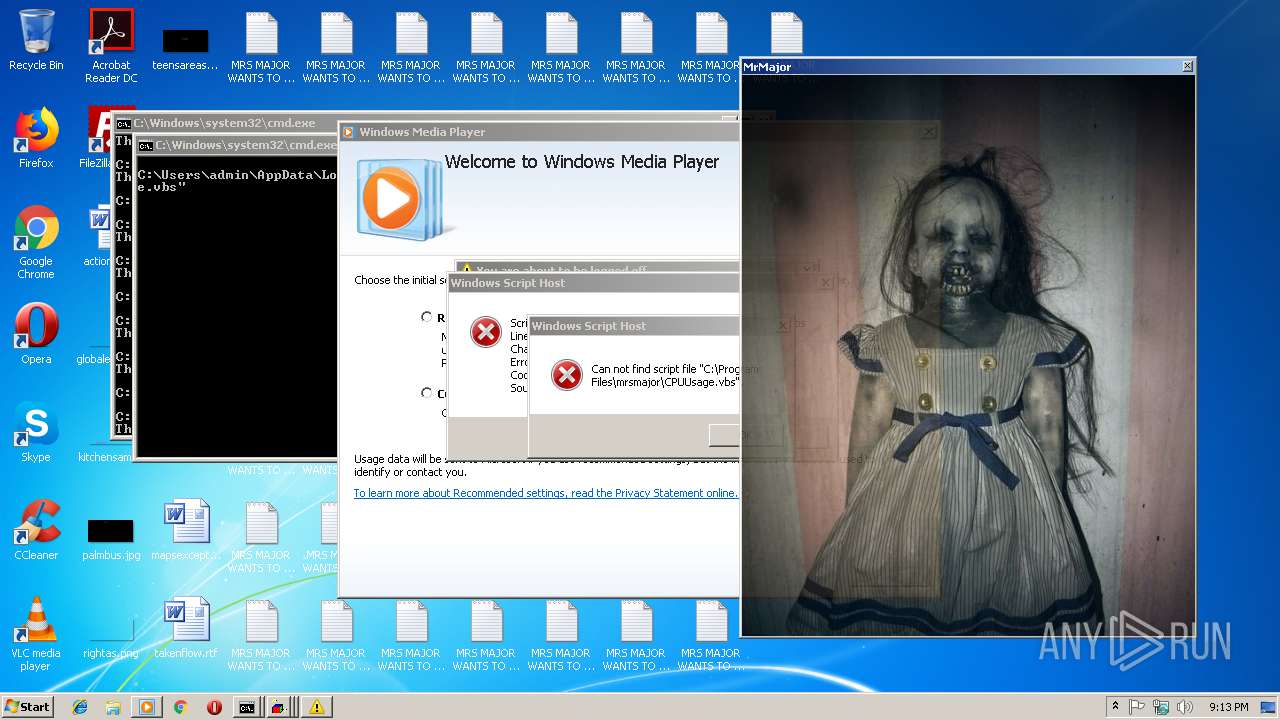
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2019, 21:13:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 83C5204BACB49B83AFECEA31BEAF1F63 |
| SHA1: | B284A3C19EA6586BE416EABDC3E9F6254A45B01C |
| SHA256: | 3AED3315E667EDDD7FEDB3AA2C65AF9C56F9B360D4BC1F5381ED2B0FEC28AD7B |
| SSDEEP: | 6144:S/fAhvV6B8ErzPZp5wdz753RSvX+tgAUHATUDAvjX7QInd:SfAv6B8azBwdeX+tg3HATYAvb7/nd |
MALICIOUS
Changes the login/logoff helper path in the registry
- WScript.exe (PID: 2344)
Application was dropped or rewritten from another process
- MrsMjrGui.exe (PID: 2816)
SUSPICIOUS
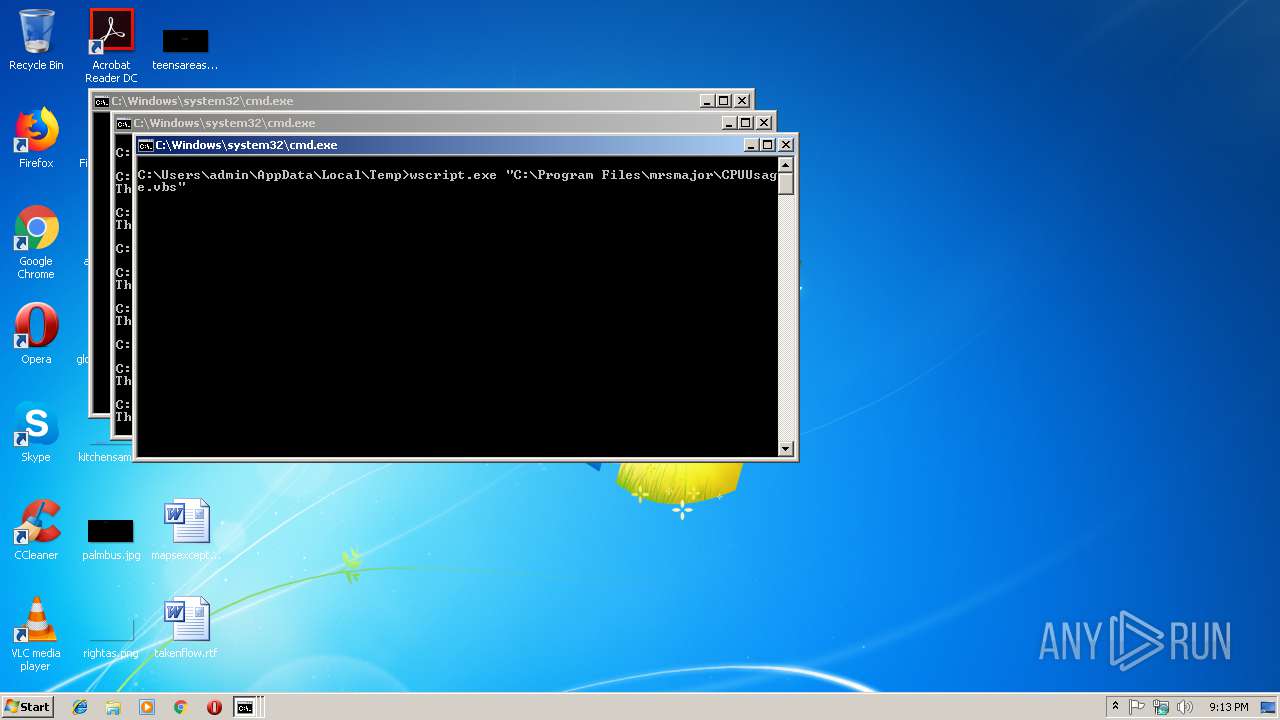
Executes scripts
- mrsmajor.exe (PID: 3088)
- cmd.exe (PID: 3392)
Executable content was dropped or overwritten
- mrsmajor.exe (PID: 3088)
Starts CMD.EXE for commands execution
- mrsmajor.exe (PID: 3088)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 3388)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3388)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:30 20:01:44+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 190976 |
| InitializedDataSize: | 239616 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d549 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Sep-2018 18:01:44 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 30-Sep-2018 18:01:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002E924 | 0x0002EA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69845 |
.rdata | 0x00030000 | 0x00009A8C | 0x00009C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13014 |
.data | 0x0003A000 | 0x000203A0 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.23545 |
.gfids | 0x0005B000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.09308 |
.rsrc | 0x0005C000 | 0x0000E4E3 | 0x0000E600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.5802 |
.reloc | 0x0006B000 | 0x00001FDC | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.67876 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.10026 | 2216 | UNKNOWN | English - United States | RT_ICON |
3 | 5.25868 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 5.02609 | 1128 | UNKNOWN | English - United States | RT_ICON |
5 | 5.18109 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.04307 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.23498 | 564 | UNKNOWN | German - Germany | RT_STRING |
8 | 3.21532 | 616 | UNKNOWN | German - Germany | RT_STRING |
9 | 3.20126 | 604 | UNKNOWN | German - Germany | RT_STRING |
10 | 3.20175 | 416 | UNKNOWN | German - Germany | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
63
Monitored processes
24
Malicious processes
2
Suspicious processes
1
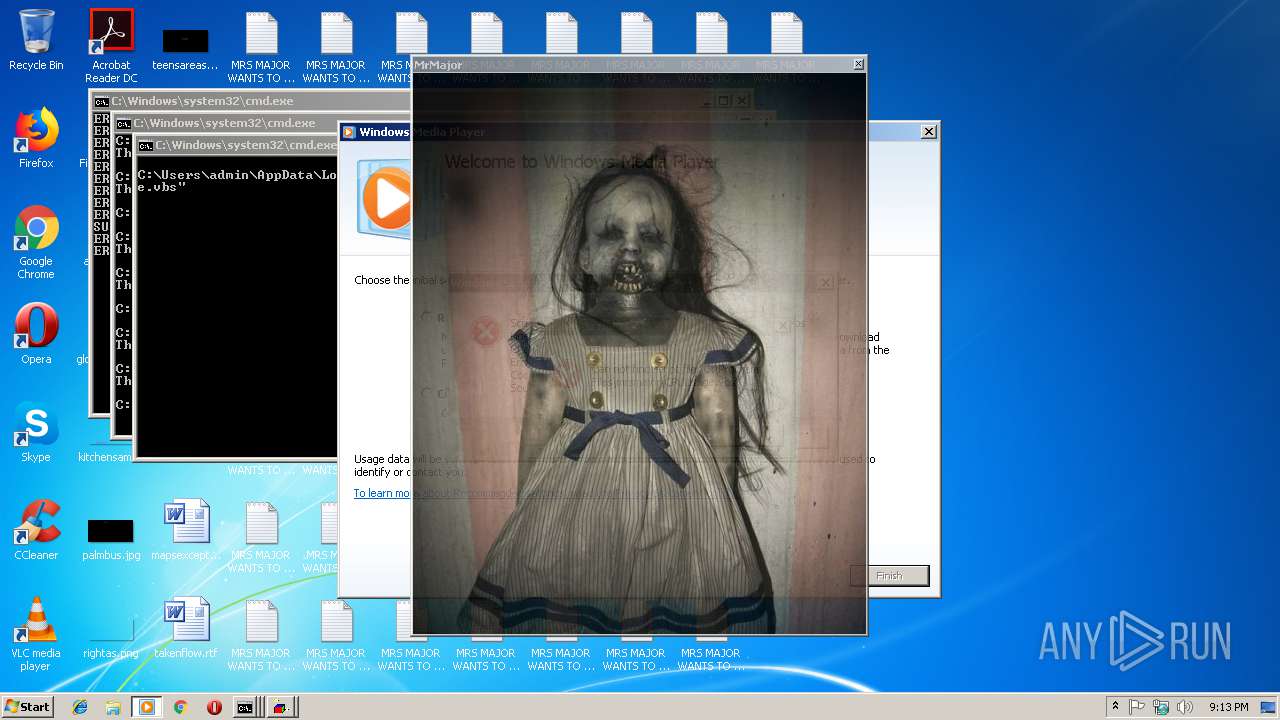
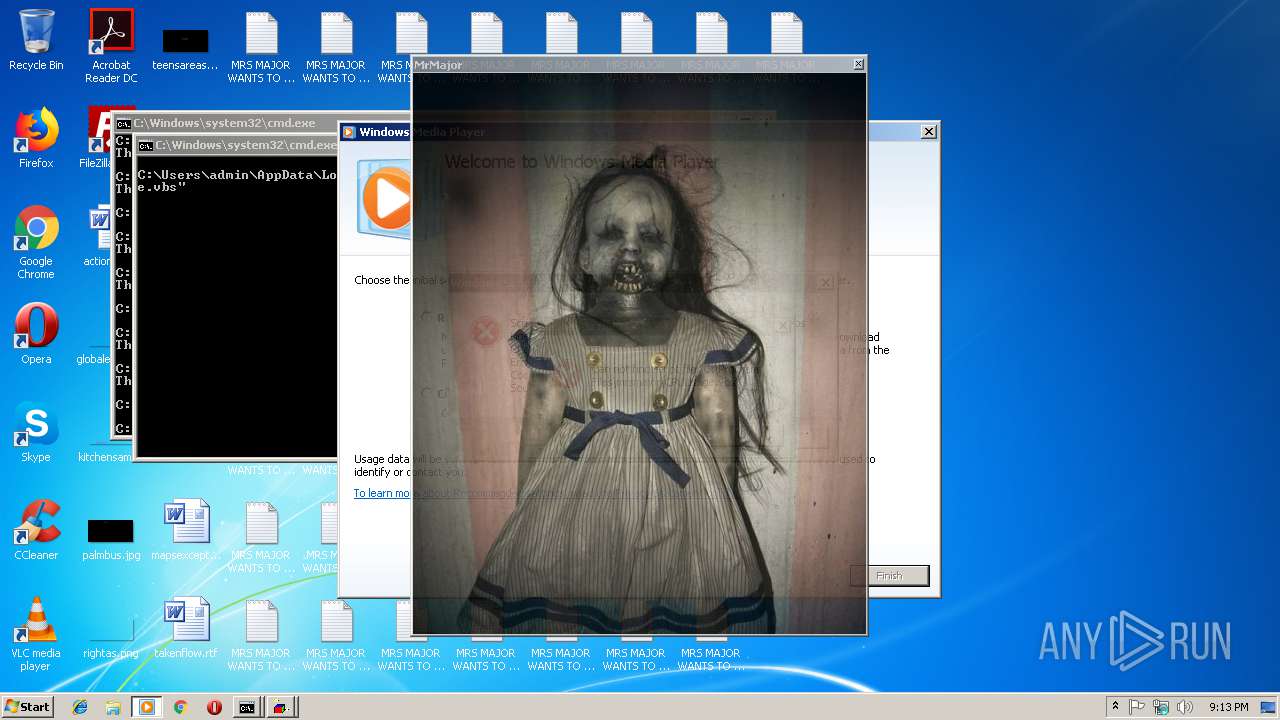
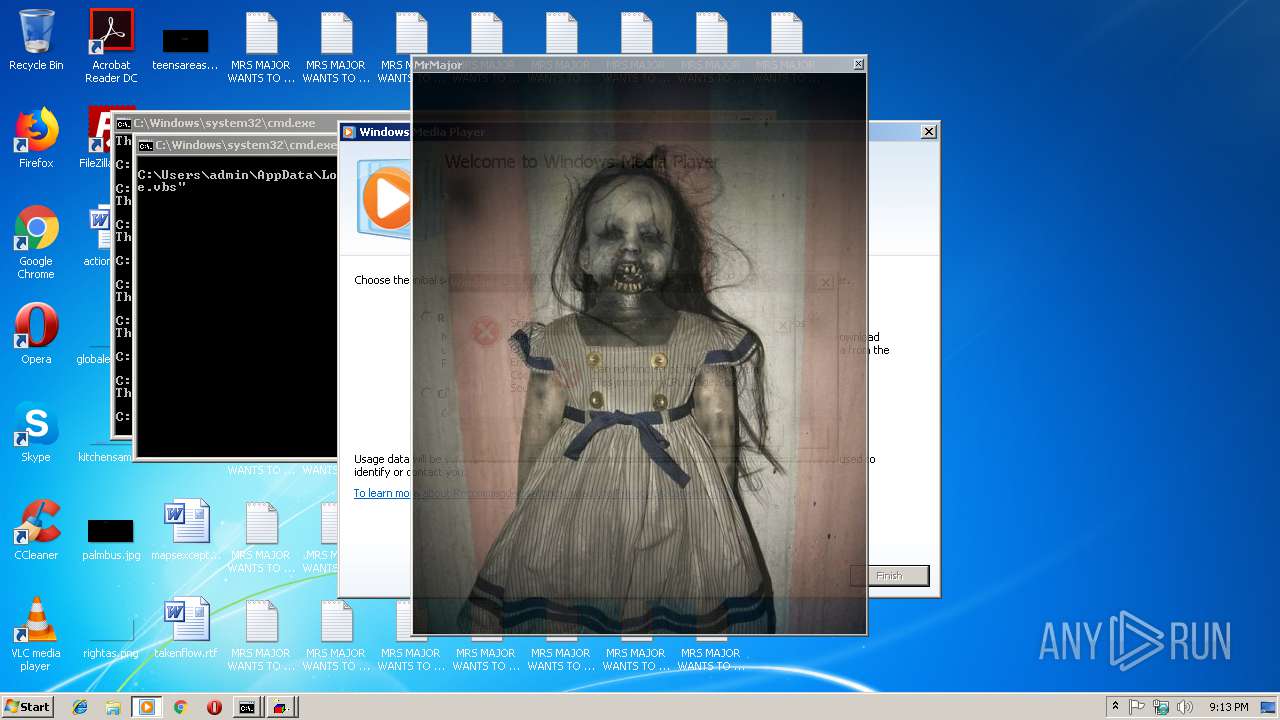
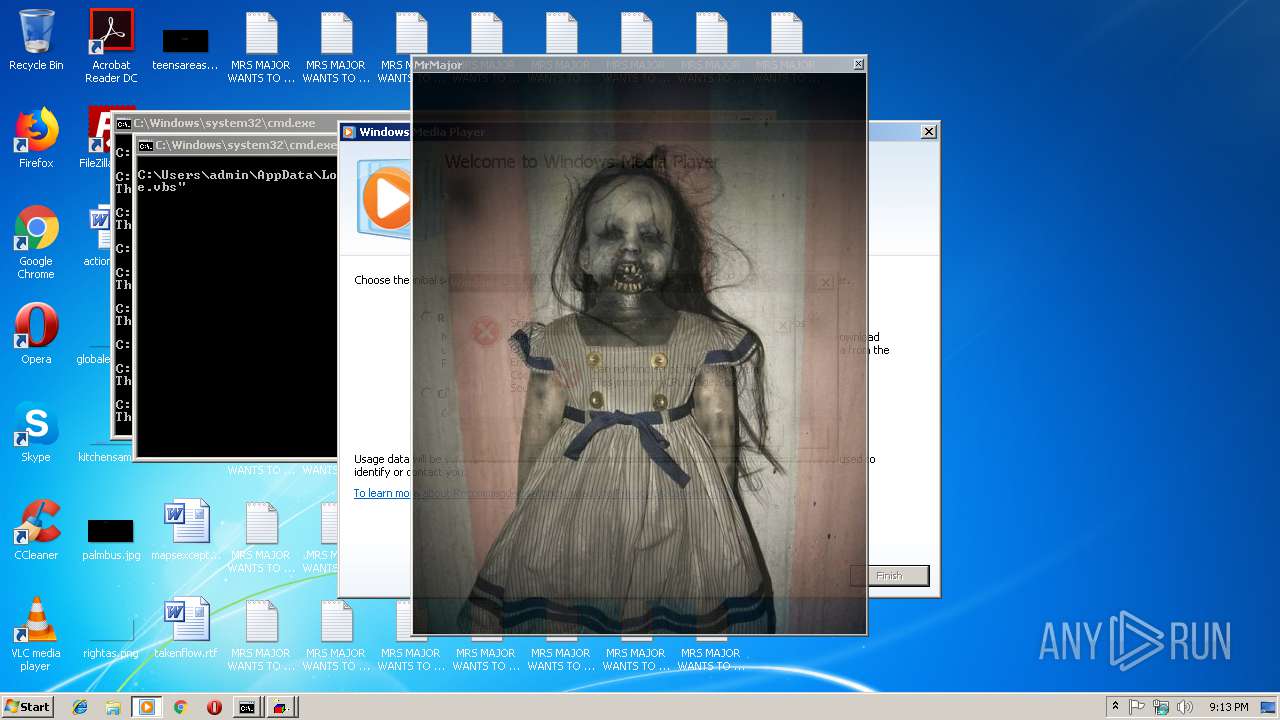
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
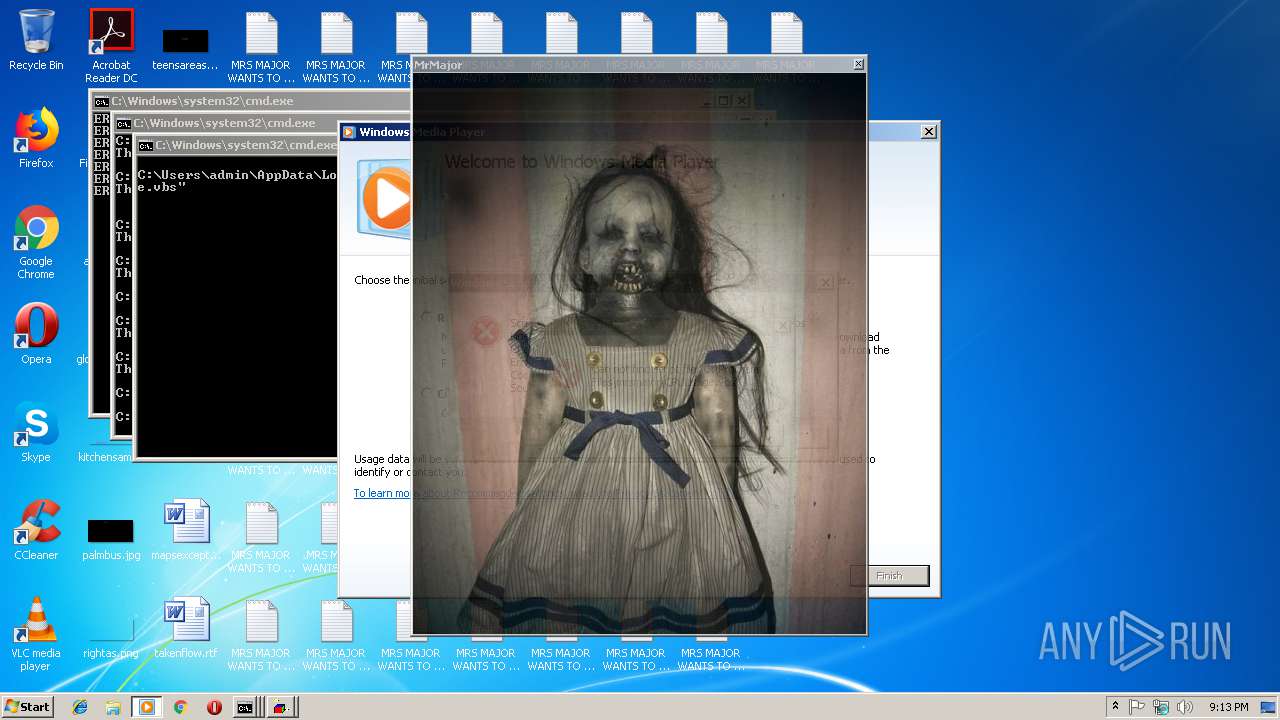
| 272 | taskkill /f /im opera.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2344 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\mrsmajorlauncher.vbs" | C:\Windows\System32\WScript.exe | mrsmajor.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1073807364 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2352 | "C:\Windows\System32\shutdown.exe" -r -t 03 | C:\Windows\System32\shutdown.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2632 | cmd /c ""C:\Users\admin\AppData\Local\Temp\MrsMjrGuiLauncher.bat" " | C:\Windows\system32\cmd.exe | — | mrsmajor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1073807364 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
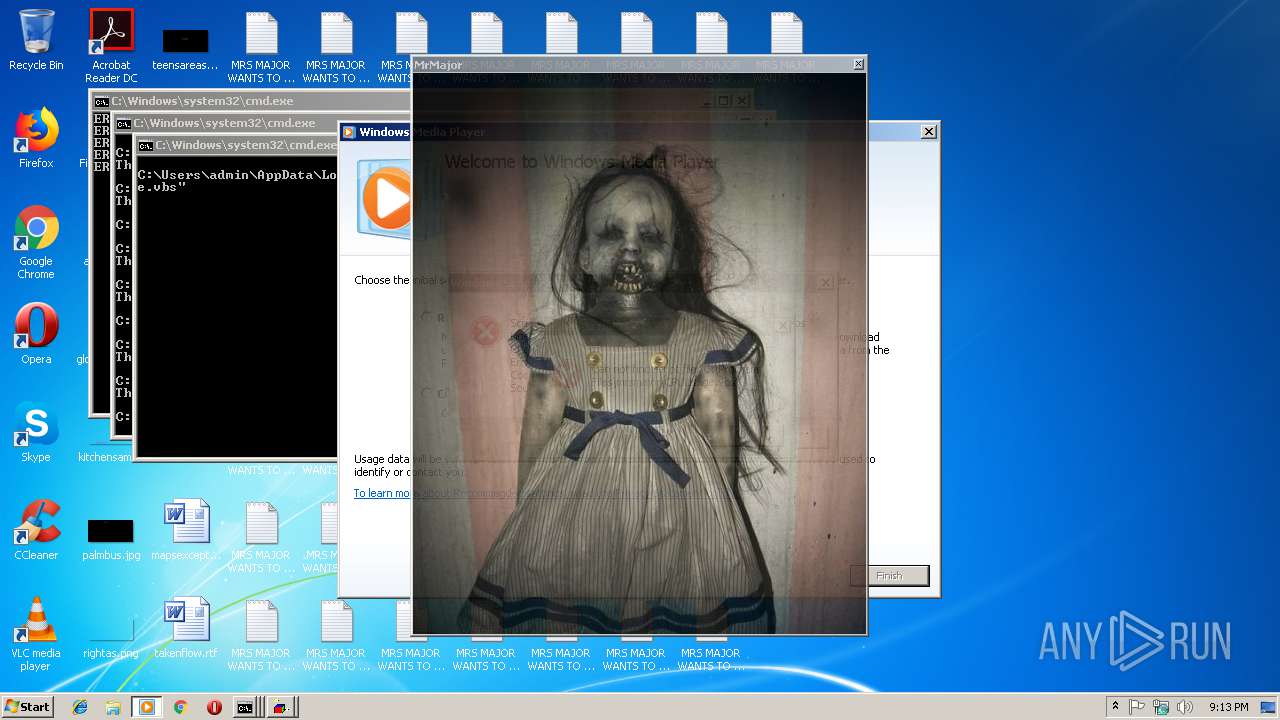
| 2752 | "C:\Program Files\Windows Media Player\wmplayer.exe" "C:\Program Files\mrsmajor\def_resource\f11.mp4" | C:\Program Files\Windows Media Player\wmplayer.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
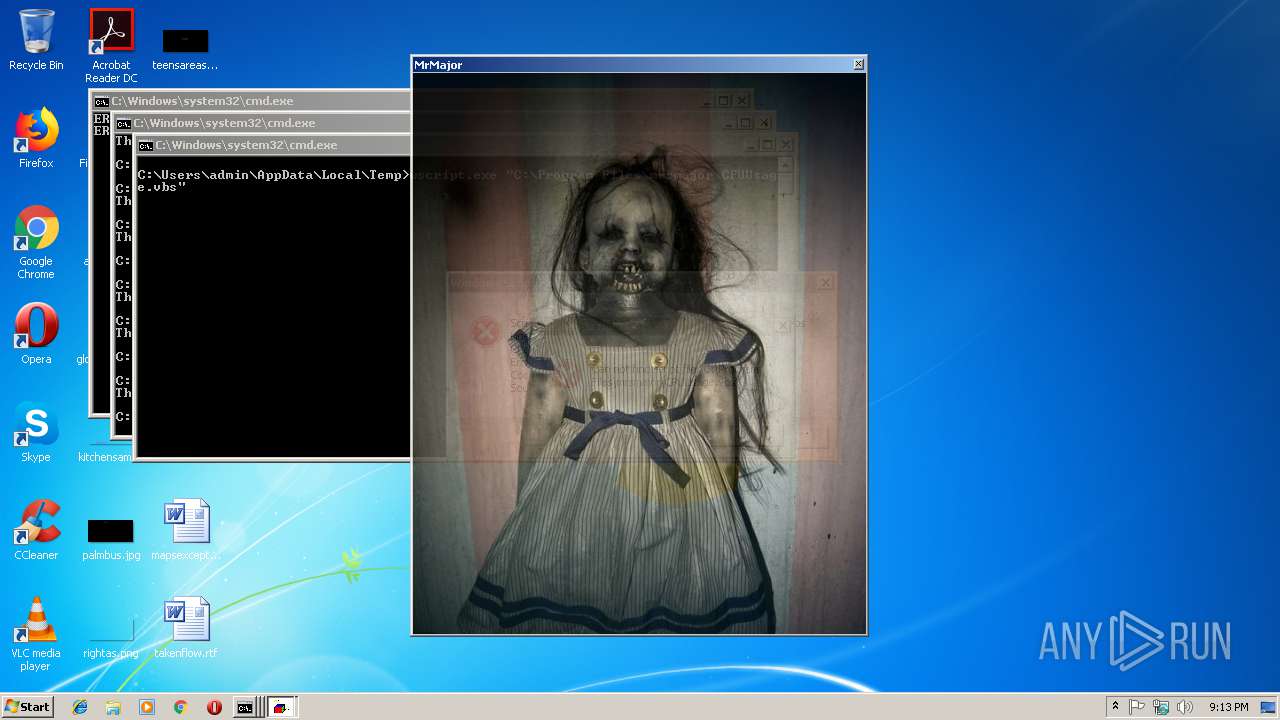
| 2816 | "C:\Users\admin\AppData\Local\Temp\MrsMjrGui.exe" | C:\Users\admin\AppData\Local\Temp\MrsMjrGui.exe | — | mrsmajor.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1073807364 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3048 | taskkill /f /im bing.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3060 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\CPUUsage.vbs" | C:\Windows\System32\WScript.exe | — | mrsmajor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1073807364 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3088 | "C:\Users\admin\AppData\Local\Temp\mrsmajor.exe" | C:\Users\admin\AppData\Local\Temp\mrsmajor.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3120 | taskkill /f /im iexplore.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
765
Read events
741
Write events
24
Delete events
0
Modification events
| (PID) Process: | (3088) mrsmajor.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3088) mrsmajor.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2344) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | ConsentPromptBehaviorAdmin |
Value: 0 | |||
| (PID) Process: | (2344) WScript.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | Arrow |
Value: C:\Program Files\mrsmajor\def_resource\skullcur.cur | |||
| (PID) Process: | (2344) WScript.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | AppStarting |
Value: C:\Program Files\mrsmajor\def_resource\skullcur.cur | |||
| (PID) Process: | (2344) WScript.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | Hand |
Value: C:\Program Files\mrsmajor\def_resource\skullcur.cur | |||
| (PID) Process: | (2344) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\txtfile\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Program Files\mrsmajor\Icon_resource\SkullIco.ico | |||
| (PID) Process: | (2344) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\exefile\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Program Files\mrsmajor\Icon_resource\SkullIco.ico | |||
| (PID) Process: | (2344) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\inifile\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Program Files\mrsmajor\Icon_resource\SkullIco.ico | |||
| (PID) Process: | (2344) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
59
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3088 | mrsmajor.exe | C:\Users\admin\AppData\Local\Temp\DreS_X.bat | text | |
MD5:BA81D7FA0662E8EE3780C5BECC355A14 | SHA256:2590879A8CD745DBBE7AD66A548F31375CCFB0F8090D56B5E4BD5909573AC816 | |||
| 3088 | mrsmajor.exe | C:\Users\admin\AppData\Local\Temp\mrsmajorlauncher.vbs | text | |
MD5:E3FDF285B14FB588F674EBFC2134200C | SHA256:4D3AA3ECD16A6BA46A9D6C0BDACDCD9DCE70D93585941A94E544696E3E6F7D92 | |||
| 3088 | mrsmajor.exe | C:\Users\admin\AppData\Local\Temp\MrsMjrGui.exe | executable | |
MD5:450F49426B4519ECAAC8CD04814C03A4 | SHA256:087FCA40E079746B9C1DFAF777D3994C0321EA8F69D08238CDFC02FB109ADD1D | |||
| 3088 | mrsmajor.exe | C:\Users\admin\AppData\Local\Temp\Launcher.vbs | text | |
MD5:B5A1C9AE4C2AE863AC3F6A019F556A22 | SHA256:6F0BB8CC239AF15C9215867D6225C8FF344052AAA0DEEB3452DBF463B8C46529 | |||
| 2344 | WScript.exe | C:\Users\admin\Desktop\MRS MAJOR WANTS TO MEET YOU 2.txt | text | |
MD5:E20F623B1D5A781F86B51347260D68A5 | SHA256:AFEEBE824FC4A955A673D3D8569A0B49DFBC43C6CC1D4E3D66D9855C28A7A179 | |||
| 2344 | WScript.exe | C:\Users\admin\Desktop\MRS MAJOR WANTS TO MEET YOU 7.txt | text | |
MD5:E20F623B1D5A781F86B51347260D68A5 | SHA256:AFEEBE824FC4A955A673D3D8569A0B49DFBC43C6CC1D4E3D66D9855C28A7A179 | |||
| 2344 | WScript.exe | C:\Users\admin\Desktop\MRS MAJOR WANTS TO MEET YOU 3.txt | text | |
MD5:E20F623B1D5A781F86B51347260D68A5 | SHA256:AFEEBE824FC4A955A673D3D8569A0B49DFBC43C6CC1D4E3D66D9855C28A7A179 | |||
| 3088 | mrsmajor.exe | C:\Users\admin\AppData\Local\Temp\reStart.vbs | text | |
MD5:0851E8D791F618DAA5B72D40E0C8E32B | SHA256:2CBD8BC239C5CFC3EF02F8472D867DFF61E5AED9FDE8A3823CDA28CC37D77722 | |||
| 3088 | mrsmajor.exe | C:\Users\admin\AppData\Local\Temp\WinLogon.bat | text | |
MD5:870BCE376C1B71365390A9E9AEFB9A33 | SHA256:2798DAD008F62AACE1841EDFB43146147A9CADE388C419C96DA788FCAA2F76BC | |||
| 2344 | WScript.exe | C:\Users\admin\Desktop\MRS MAJOR WANTS TO MEET YOU 4.txt | text | |
MD5:E20F623B1D5A781F86B51347260D68A5 | SHA256:AFEEBE824FC4A955A673D3D8569A0B49DFBC43C6CC1D4E3D66D9855C28A7A179 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report