| File name: | mrsmajor.exe |
| Full analysis: | https://app.any.run/tasks/4864746d-fb96-4ba7-be8b-f12f9a6f2e70 |
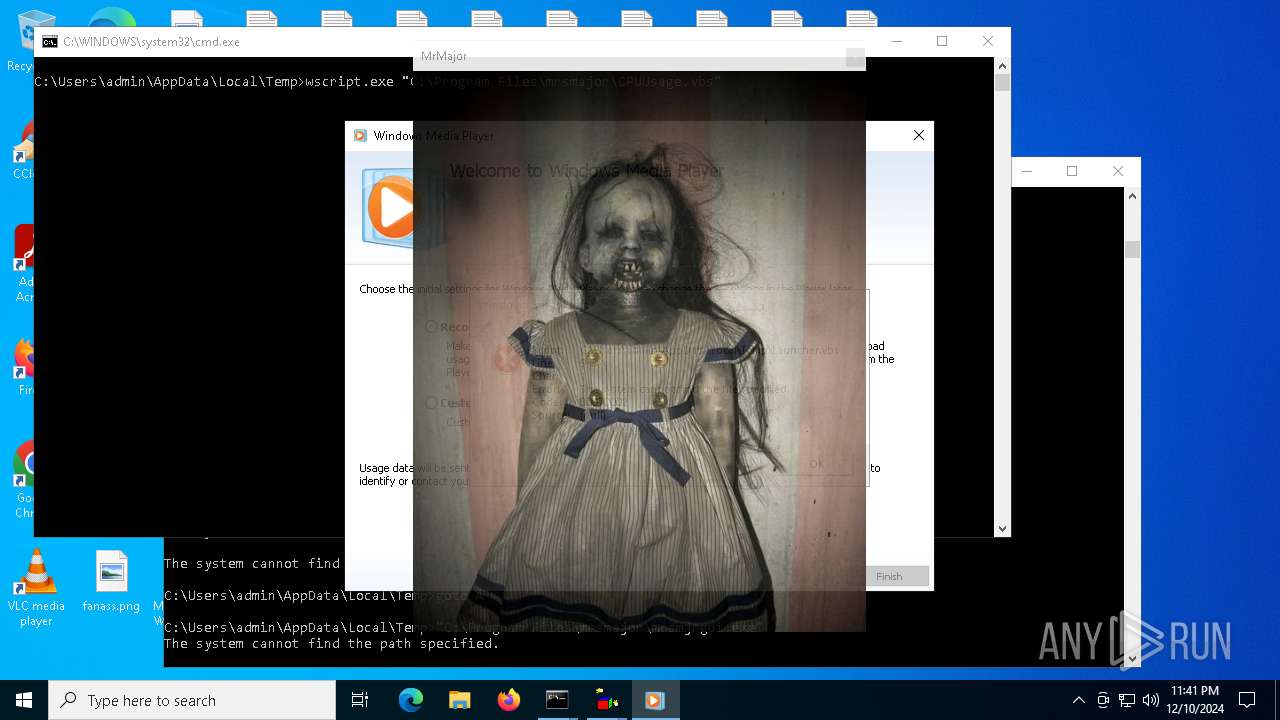
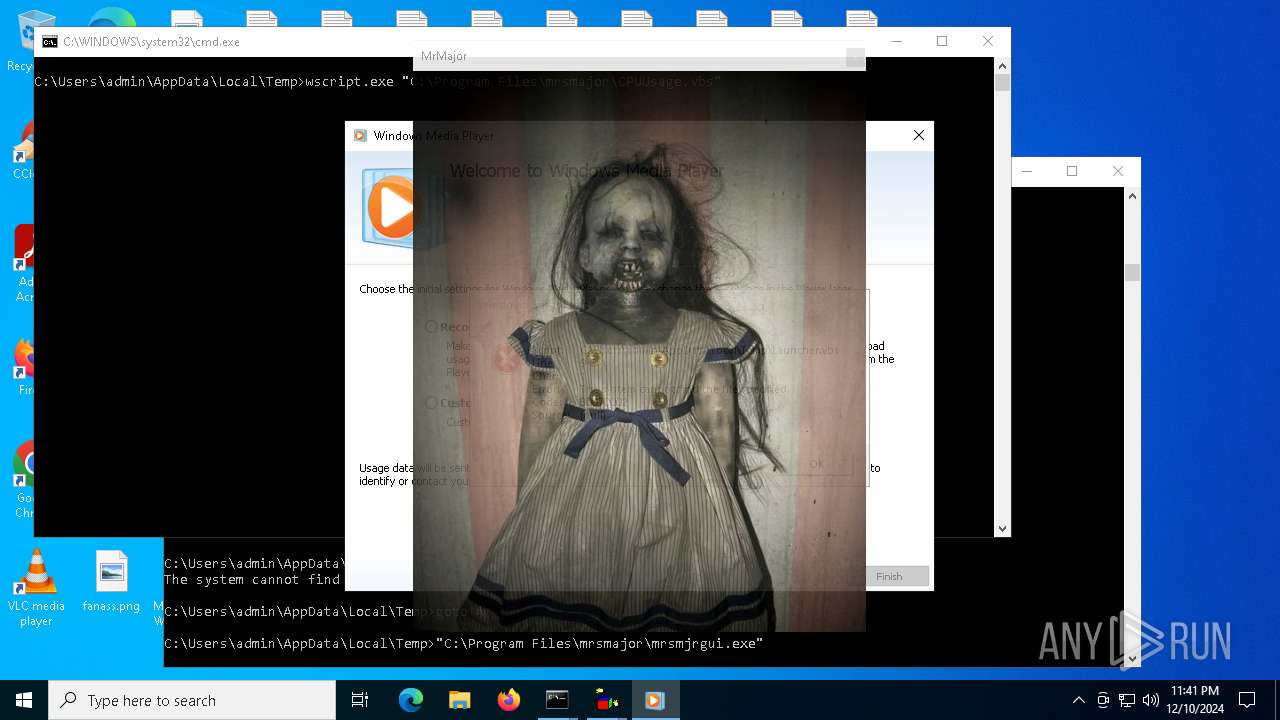
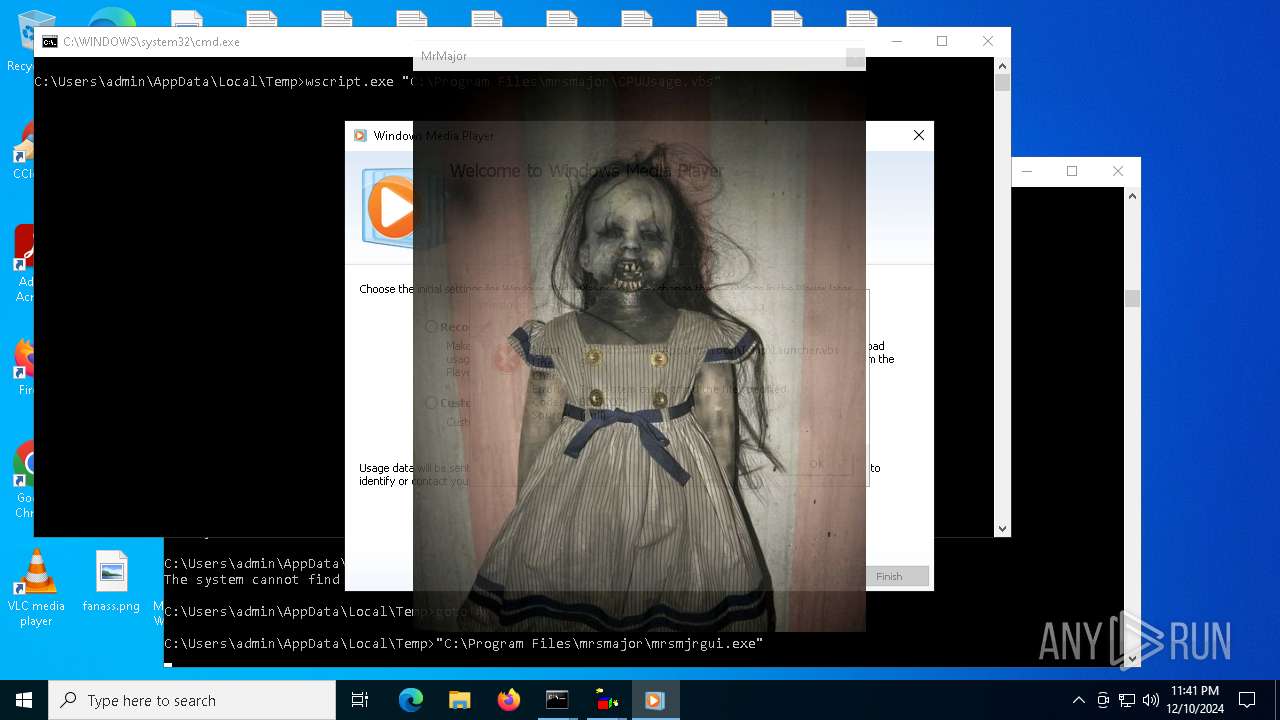
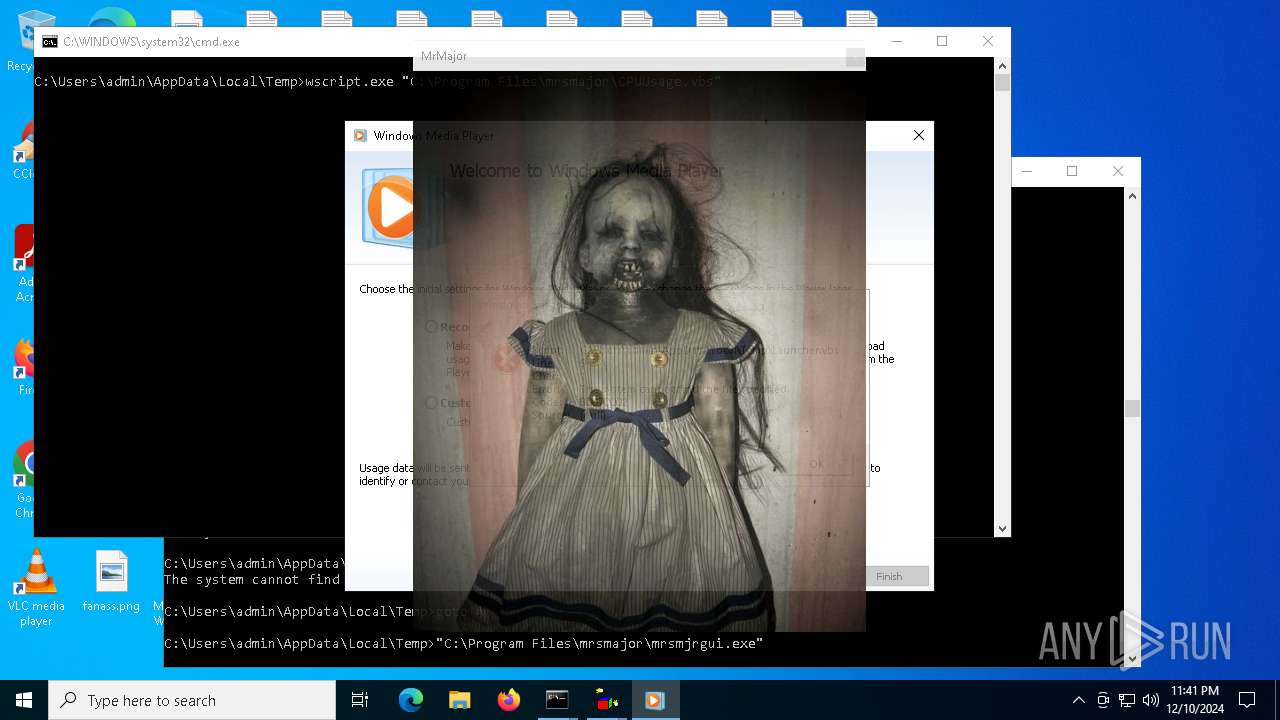
| Verdict: | Malicious activity |
| Analysis date: | December 10, 2024, 23:41:41 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 83C5204BACB49B83AFECEA31BEAF1F63 |
| SHA1: | B284A3C19EA6586BE416EABDC3E9F6254A45B01C |
| SHA256: | 3AED3315E667EDDD7FEDB3AA2C65AF9C56F9B360D4BC1F5381ED2B0FEC28AD7B |
| SSDEEP: | 6144:S/fAhvV6B8ErzPZp5wdz753RSvX+tgAUHATUDAvjX7QInd:SfAv6B8azBwdeX+tg3HATYAvb7/nd |
MALICIOUS
Gets path to any of the special folders (SCRIPT)
- wscript.exe (PID: 6460)
- wscript.exe (PID: 6412)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 6412)
- wscript.exe (PID: 6460)
Gets TEMP folder path (SCRIPT)
- wscript.exe (PID: 6412)
- wscript.exe (PID: 6460)
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 6460)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- wscript.exe (PID: 6460)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 6376)
- wscript.exe (PID: 6460)
SUSPICIOUS
Reads security settings of Internet Explorer
- mrsmajor.exe (PID: 4504)
- setup_wm.exe (PID: 6932)
- wmplayer.exe (PID: 6832)
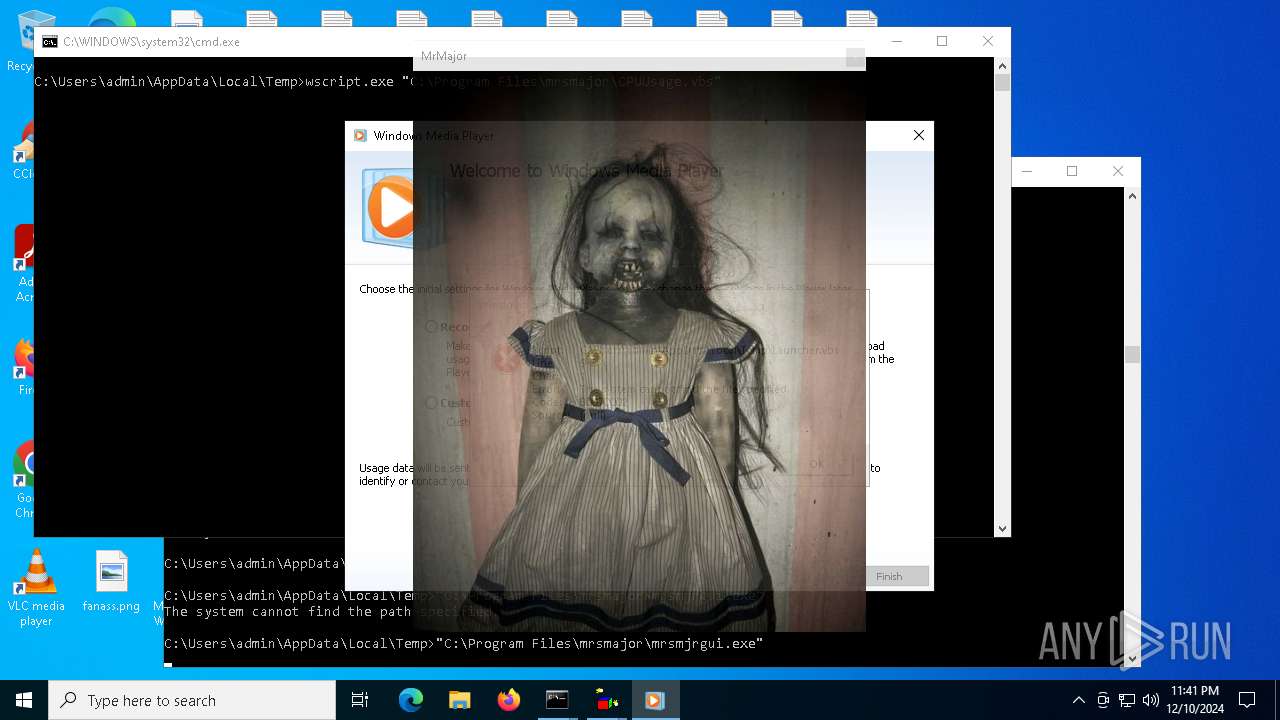
Executable content was dropped or overwritten
- mrsmajor.exe (PID: 4504)
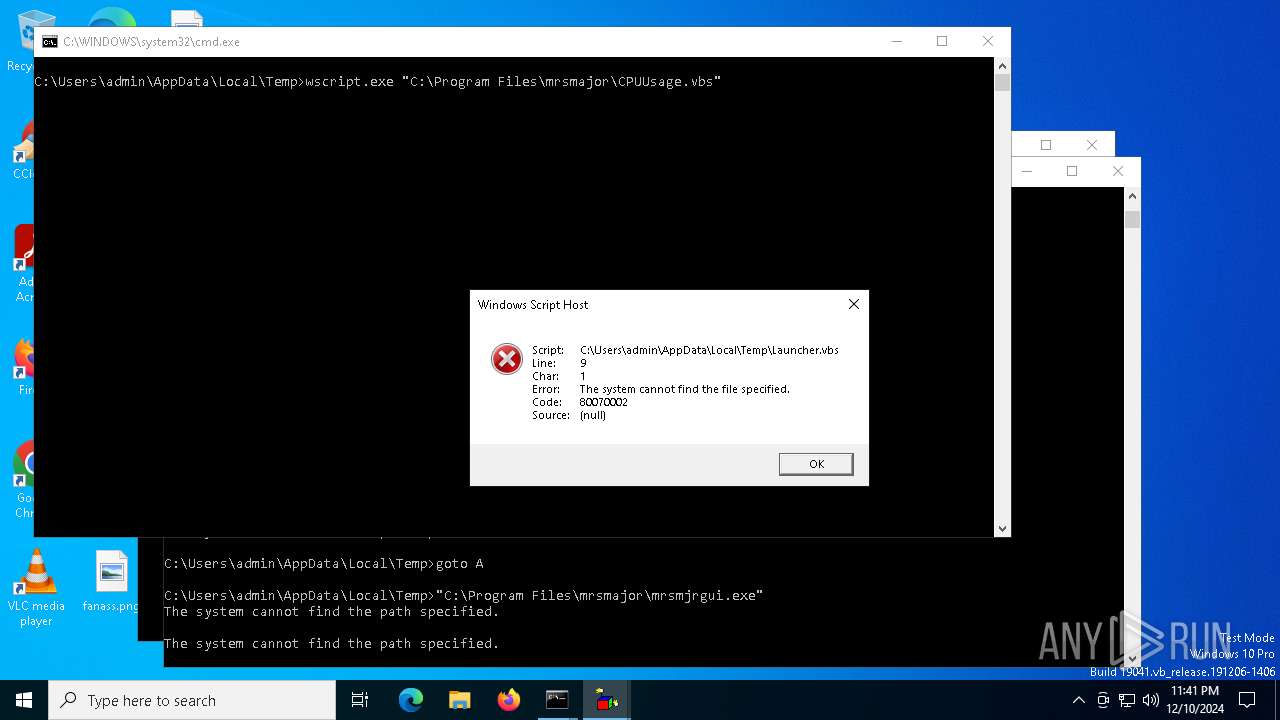
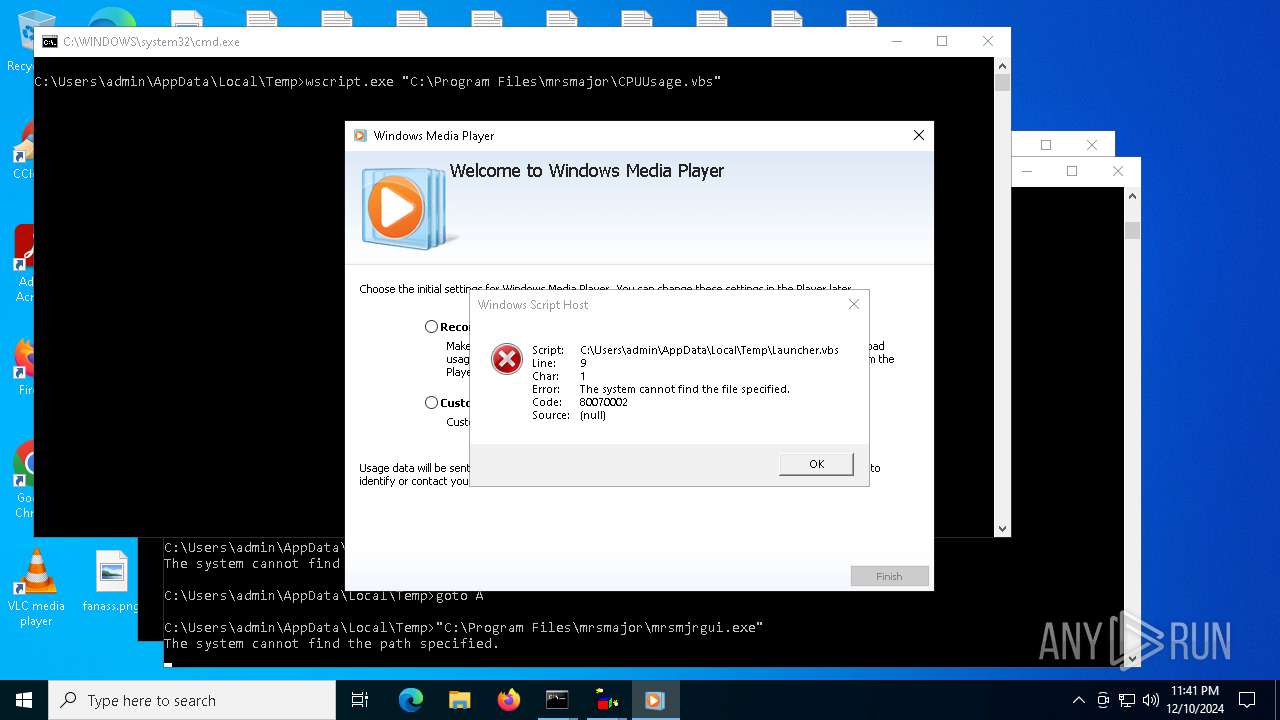
Executing commands from a ".bat" file
- mrsmajor.exe (PID: 4504)
The process executes VB scripts
- mrsmajor.exe (PID: 4504)
- cmd.exe (PID: 6548)
Starts CMD.EXE for commands execution
- mrsmajor.exe (PID: 4504)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 6412)
- wscript.exe (PID: 6460)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 6460)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 6460)
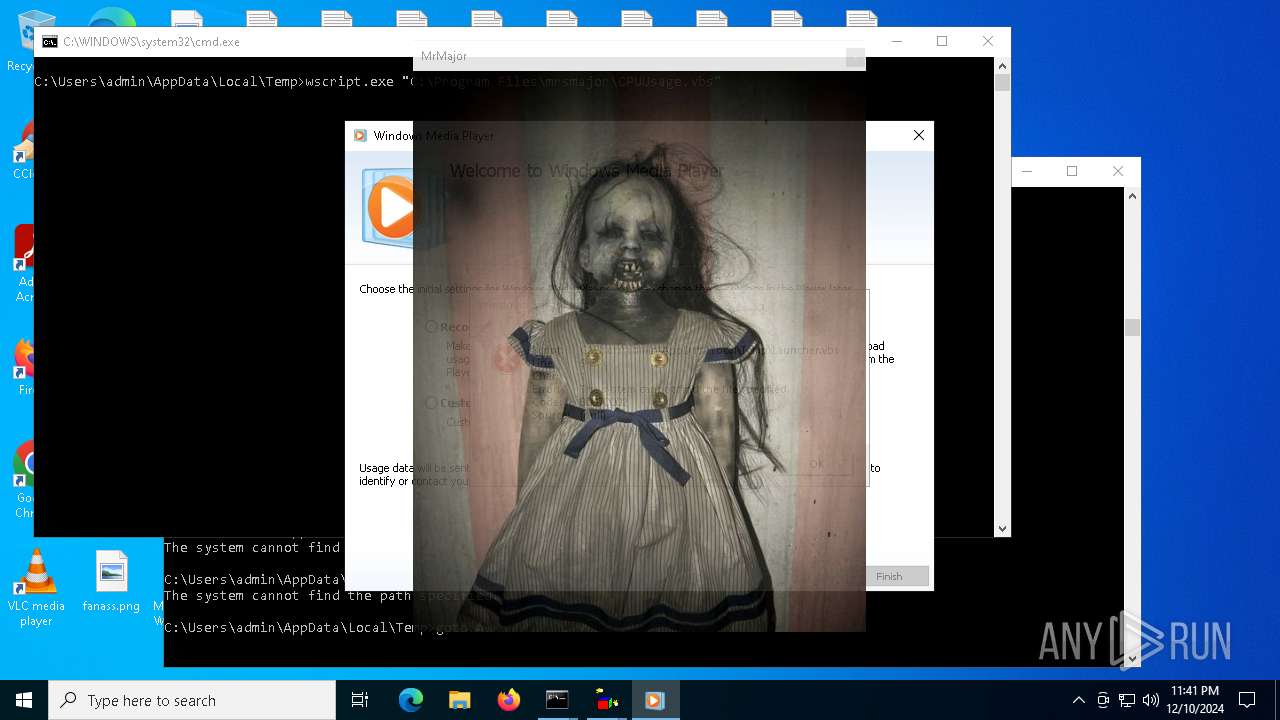
Runs shell command (SCRIPT)
- wscript.exe (PID: 6412)
- wscript.exe (PID: 6460)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6396)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 6396)
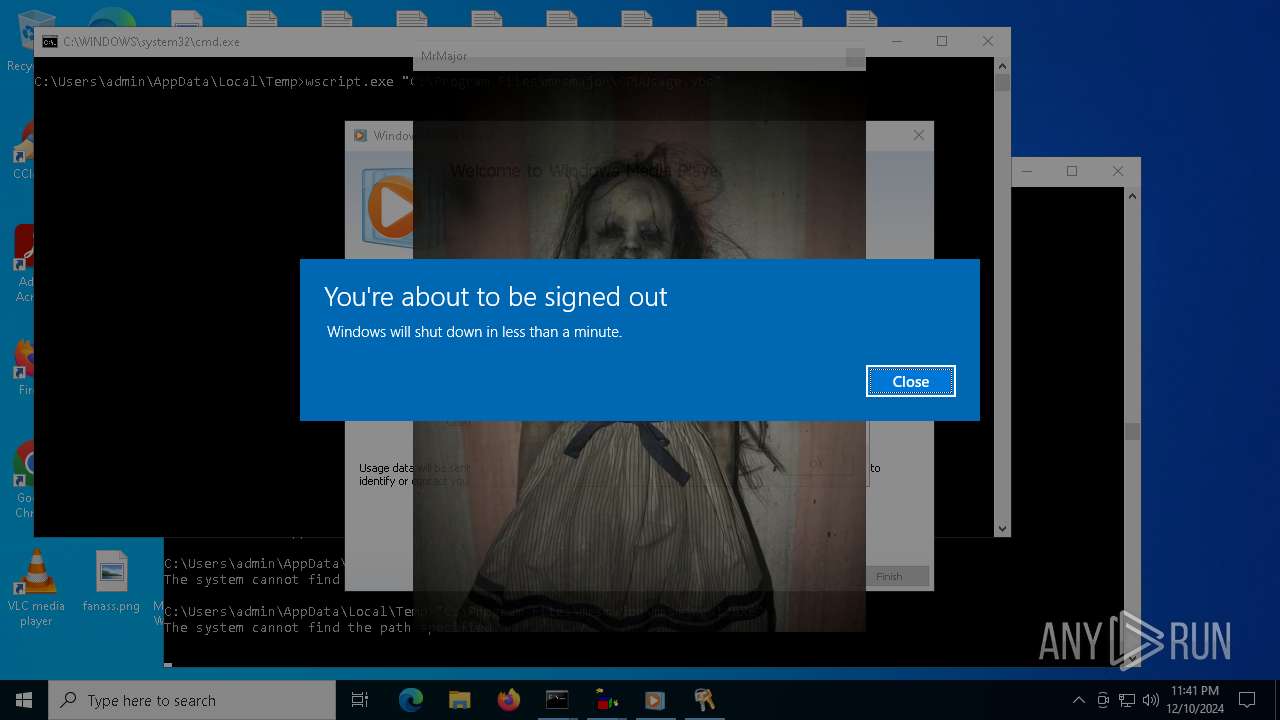
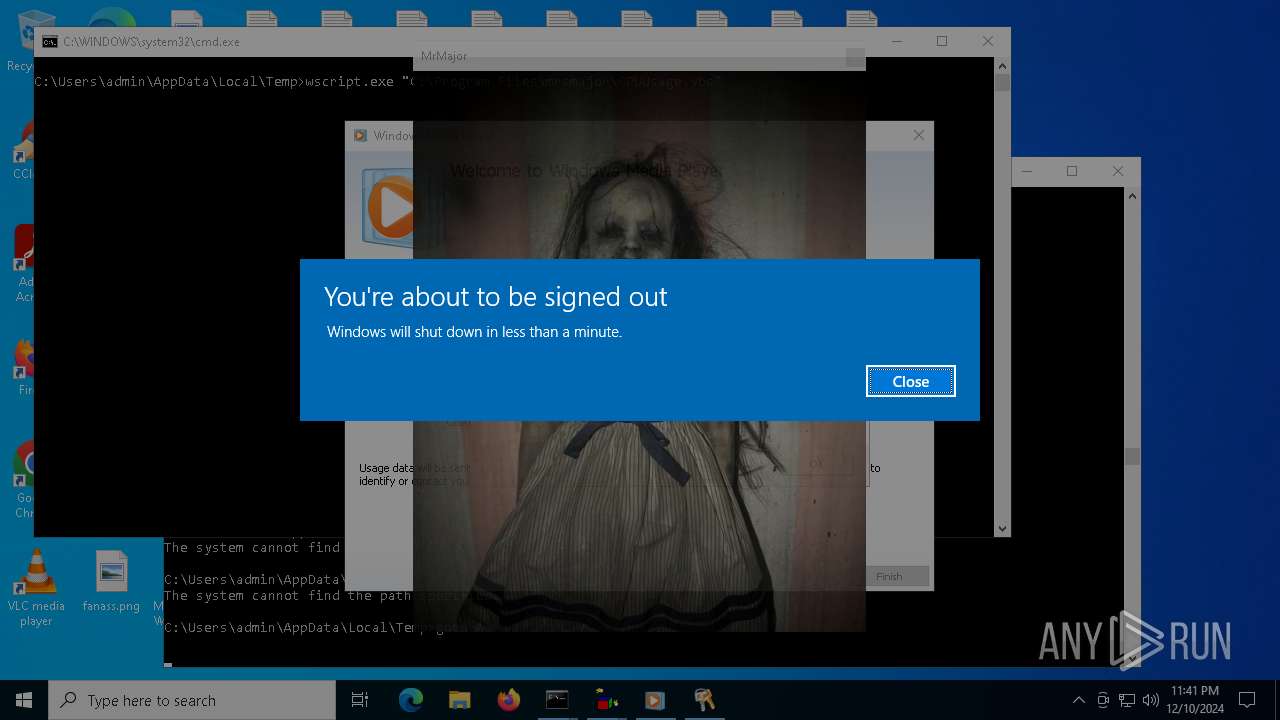
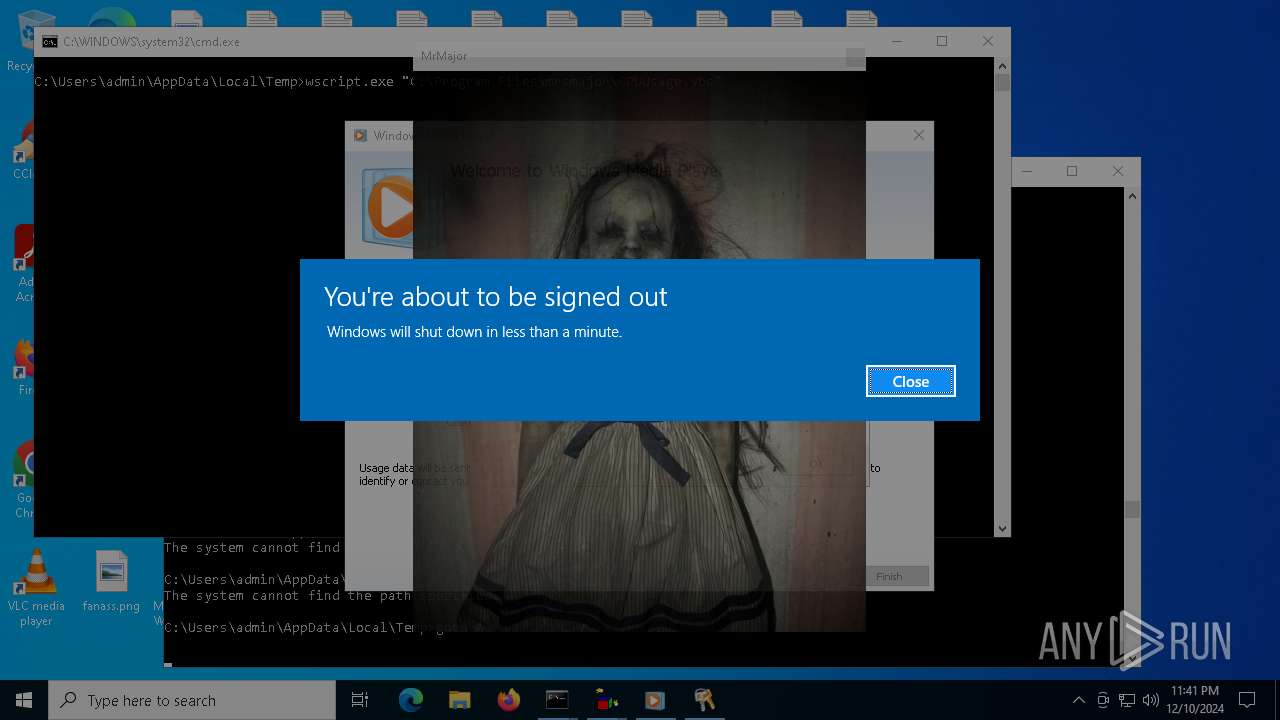
The system shut down or reboot
- wscript.exe (PID: 6460)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 3108)
INFO
Create files in a temporary directory
- mrsmajor.exe (PID: 4504)
- unregmp2.exe (PID: 6952)
Reads the computer name
- mrsmajor.exe (PID: 4504)
- MrsMjrGui.exe (PID: 6484)
- wmplayer.exe (PID: 6832)
- setup_wm.exe (PID: 6932)
- PLUGScheduler.exe (PID: 3108)
Checks supported languages
- mrsmajor.exe (PID: 4504)
- MrsMjrGui.exe (PID: 6484)
- wmplayer.exe (PID: 6832)
- setup_wm.exe (PID: 6932)
- PLUGScheduler.exe (PID: 3108)
Process checks computer location settings
- mrsmajor.exe (PID: 4504)
- wmplayer.exe (PID: 6832)
- setup_wm.exe (PID: 6932)
The process uses the downloaded file
- mrsmajor.exe (PID: 4504)
- wmplayer.exe (PID: 6832)
- unregmp2.exe (PID: 6952)
- wscript.exe (PID: 6460)
Checks proxy server information
- setup_wm.exe (PID: 6932)
Creates files or folders in the user directory
- unregmp2.exe (PID: 7060)
Reads the machine GUID from the registry
- MrsMjrGui.exe (PID: 6484)
Creates files in the program directory
- PLUGScheduler.exe (PID: 3108)
Reads security settings of Internet Explorer
- unregmp2.exe (PID: 6952)
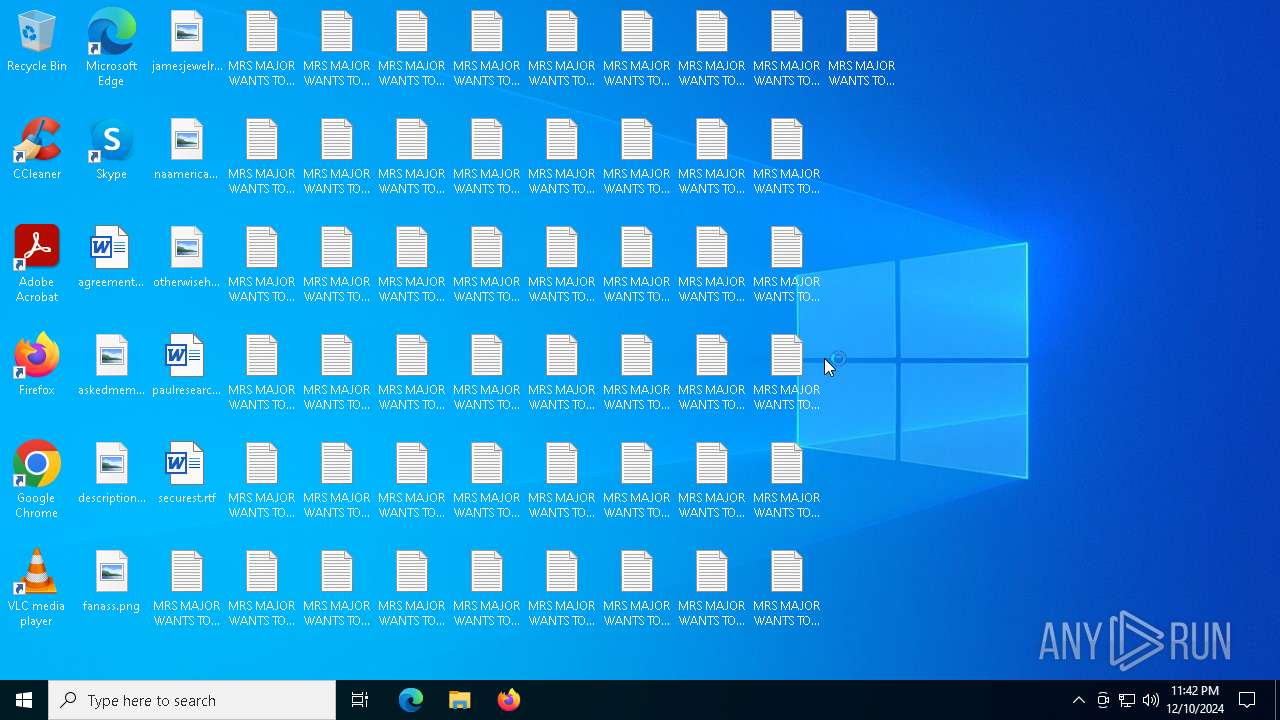
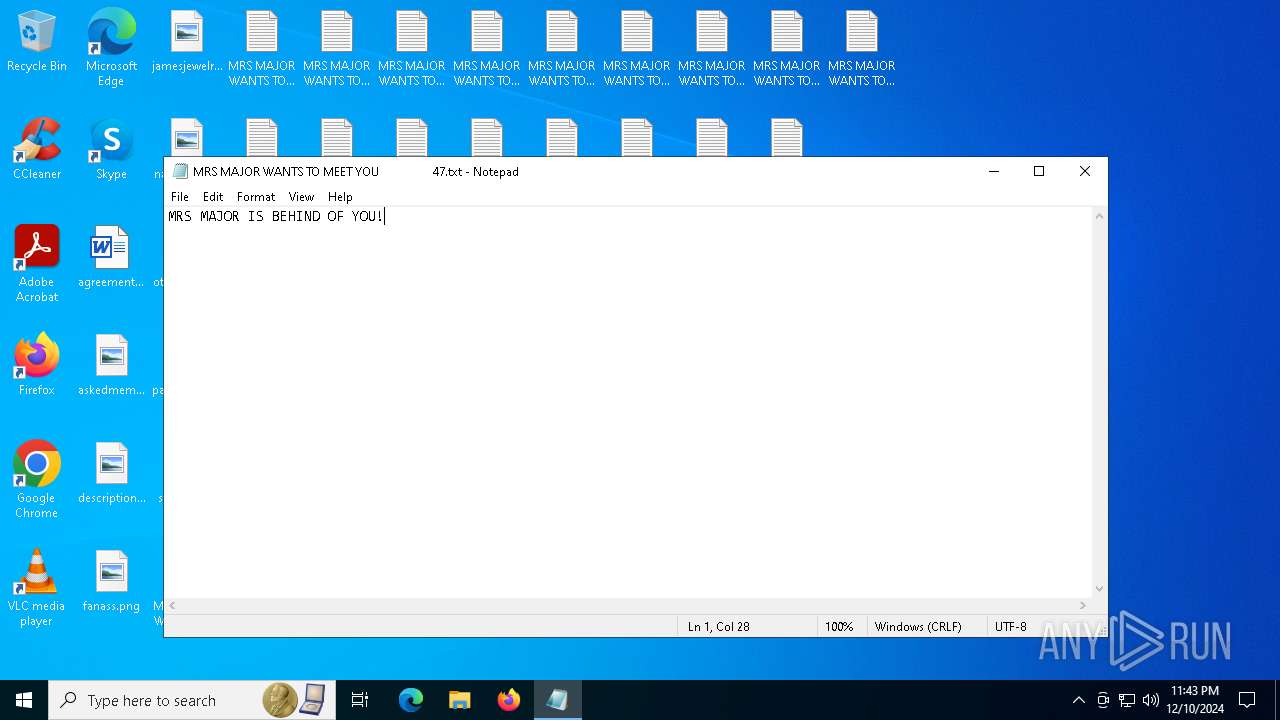
Manual execution by a user
- notepad.exe (PID: 924)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:30 18:01:44+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 190976 |
| InitializedDataSize: | 239616 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d549 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
282
Monitored processes
33
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 924 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\MRS MAJOR WANTS TO MEET YOU 47.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3108 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3144 | taskkill /f /im mspaint.exe | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4504 | "C:\Users\admin\AppData\Local\Temp\mrsmajor.exe" | C:\Users\admin\AppData\Local\Temp\mrsmajor.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4708 | "C:\Windows\System32\shutdown.exe" -r -t 03 | C:\Windows\SysWOW64\shutdown.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5404 | wscript.exe "C:\Program Files\mrsmajor\reStart.vbs" | C:\Windows\SysWOW64\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 3221226091 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 5432 | taskkill /f /im microsoftedge.exe | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6184 | taskkill /f /im msedge.exe | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6316 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | shutdown.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6376 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\CPUUsage.vbs" | C:\Windows\SysWOW64\wscript.exe | — | mrsmajor.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1073807364 Version: 5.812.10240.16384 Modules
| |||||||||||||||
Total events
6 364
Read events
6 266
Write events
92
Delete events
6
Modification events
| (PID) Process: | (4504) mrsmajor.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
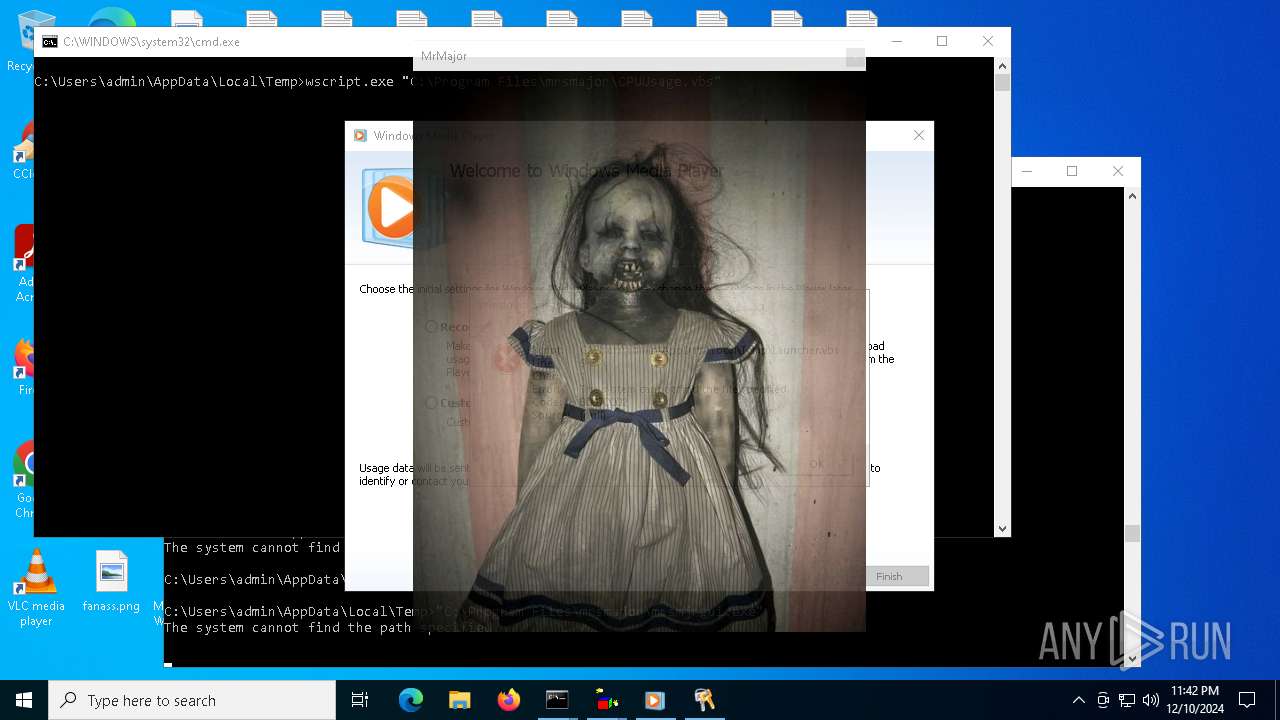
| (PID) Process: | (6460) wscript.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | Arrow |
Value: C:\Program Files\mrsmajor\def_resource\skullcur.cur | |||
| (PID) Process: | (6460) wscript.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | AppStarting |
Value: C:\Program Files\mrsmajor\def_resource\skullcur.cur | |||
| (PID) Process: | (6460) wscript.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | Hand |
Value: C:\Program Files\mrsmajor\def_resource\skullcur.cur | |||
| (PID) Process: | (6932) setup_wm.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6932) setup_wm.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6932) setup_wm.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6932) setup_wm.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\MediaPlayer\Preferences |
| Operation: | delete value | Name: | UsageTracking |
Value: | |||
| (PID) Process: | (6932) setup_wm.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\MediaPlayer\Preferences |
| Operation: | delete value | Name: | ForceUsageTracking |
Value: | |||
| (PID) Process: | (6932) setup_wm.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\MediaPlayer\Preferences |
| Operation: | delete value | Name: | SQMLaunchIndex |
Value: | |||
Executable files
1
Suspicious files
41
Text files
64
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4504 | mrsmajor.exe | C:\Users\admin\AppData\Local\Temp\DreS_X.bat | text | |
MD5:BA81D7FA0662E8EE3780C5BECC355A14 | SHA256:2590879A8CD745DBBE7AD66A548F31375CCFB0F8090D56B5E4BD5909573AC816 | |||
| 4504 | mrsmajor.exe | C:\Users\admin\AppData\Local\Temp\mrsmajorlauncher.vbs | text | |
MD5:E3FDF285B14FB588F674EBFC2134200C | SHA256:4D3AA3ECD16A6BA46A9D6C0BDACDCD9DCE70D93585941A94E544696E3E6F7D92 | |||
| 4504 | mrsmajor.exe | C:\Users\admin\AppData\Local\Temp\MrsMjrGuiLauncher.bat | text | |
MD5:C7146F88F4184C6EE5DCF7A62846AA23 | SHA256:47E6C9F62FFC41FBC555F8644AD099A96573C8C023797127F78B1A952CA1B963 | |||
| 4504 | mrsmajor.exe | C:\Users\admin\AppData\Local\Temp\CPUUsage.vbs | text | |
MD5:0E4C01BF30B13C953F8F76DB4A7E857D | SHA256:28E69E90466034CE392E84DB2BDE3AD43AD556D12609E3860F92016641B2A738 | |||
| 4504 | mrsmajor.exe | C:\Users\admin\AppData\Local\Temp\Launcher.vbs | text | |
MD5:B5A1C9AE4C2AE863AC3F6A019F556A22 | SHA256:6F0BB8CC239AF15C9215867D6225C8FF344052AAA0DEEB3452DBF463B8C46529 | |||
| 4504 | mrsmajor.exe | C:\Users\admin\AppData\Local\Temp\default.txt | text | |
MD5:30CFD8BB946A7E889090FB148EA6F501 | SHA256:E1EBBD3ABFCADDF7D6960708F3CCD8EDA64C944723F0905FF76551C692B94210 | |||
| 4504 | mrsmajor.exe | C:\Users\admin\AppData\Local\Temp\WinLogon.bat | text | |
MD5:870BCE376C1B71365390A9E9AEFB9A33 | SHA256:2798DAD008F62AACE1841EDFB43146147A9CADE388C419C96DA788FCAA2F76BC | |||
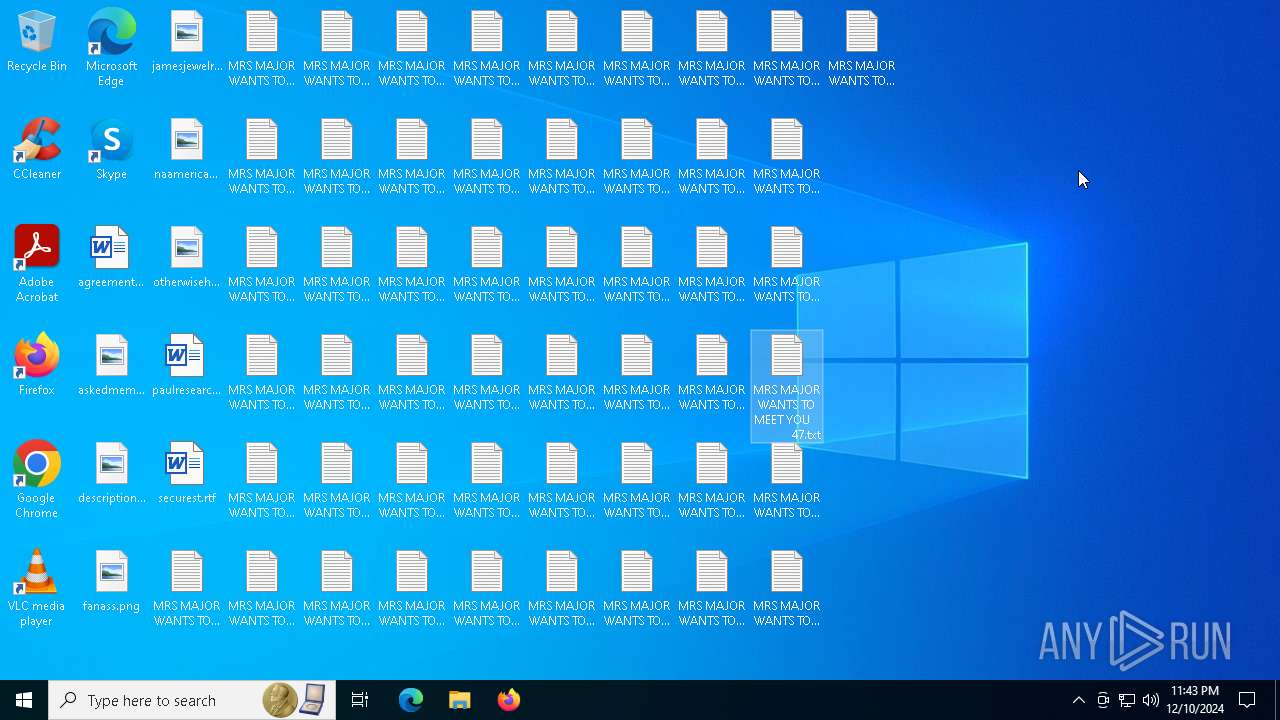
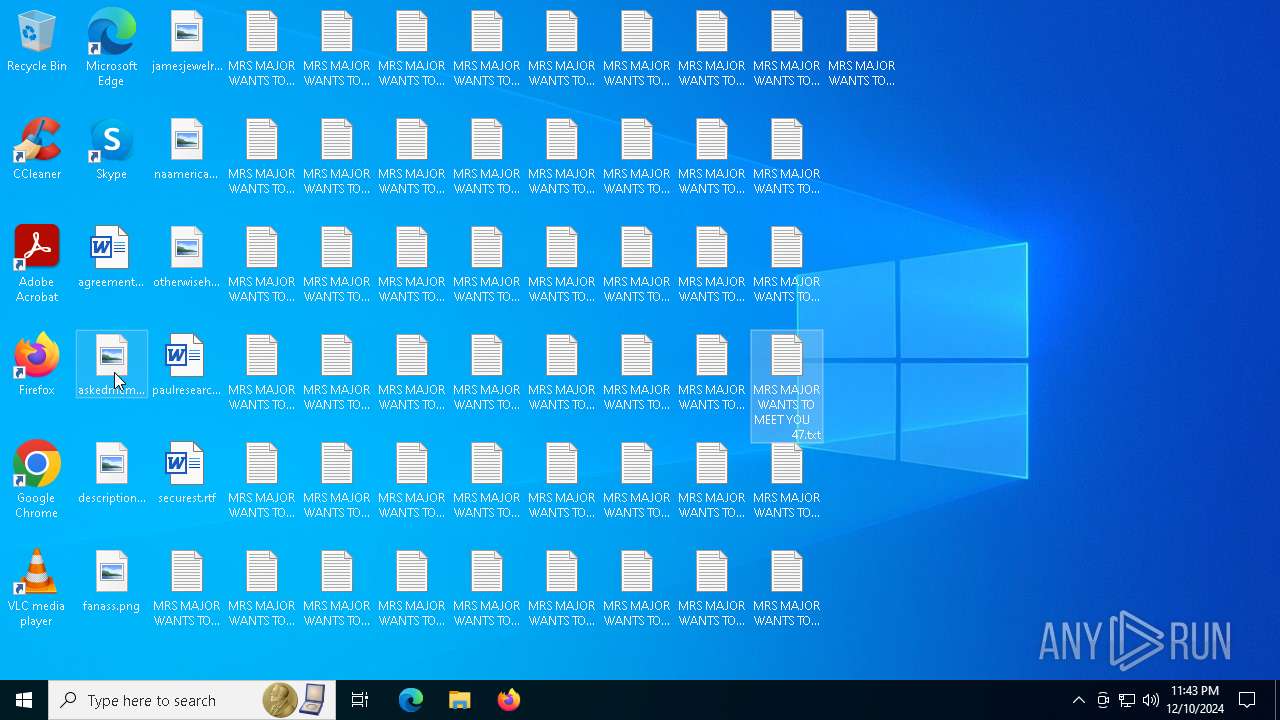
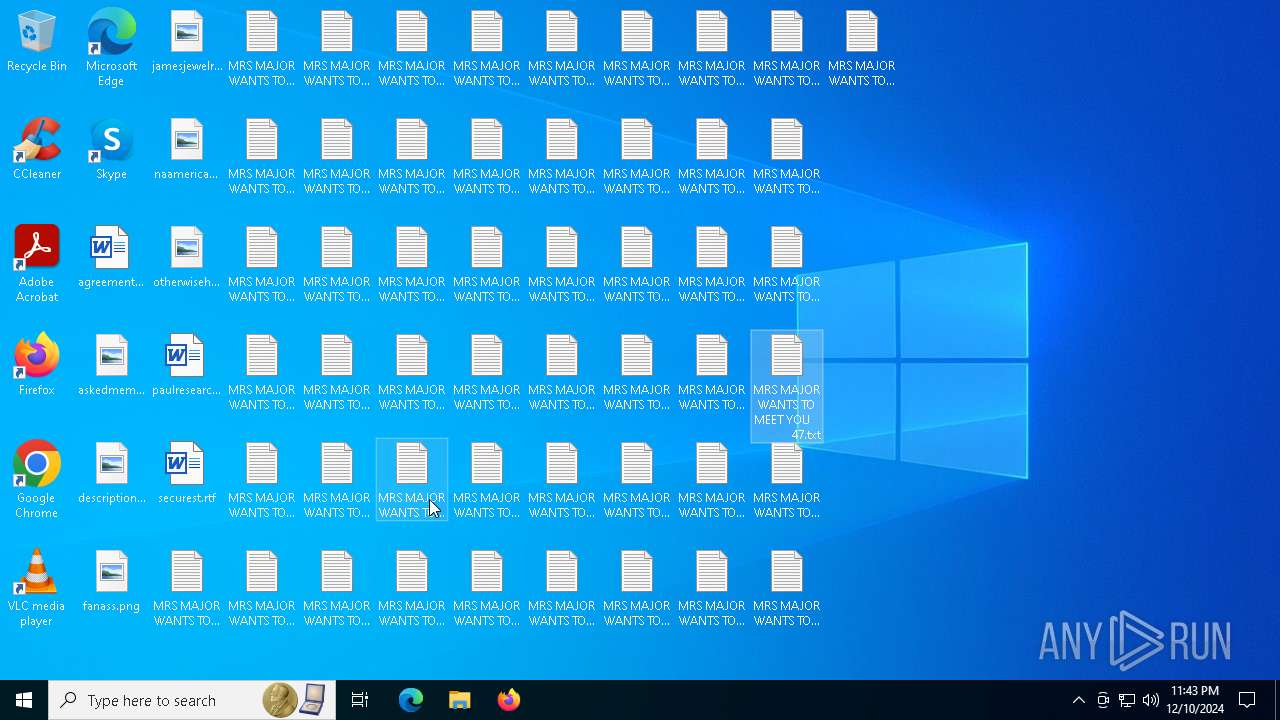
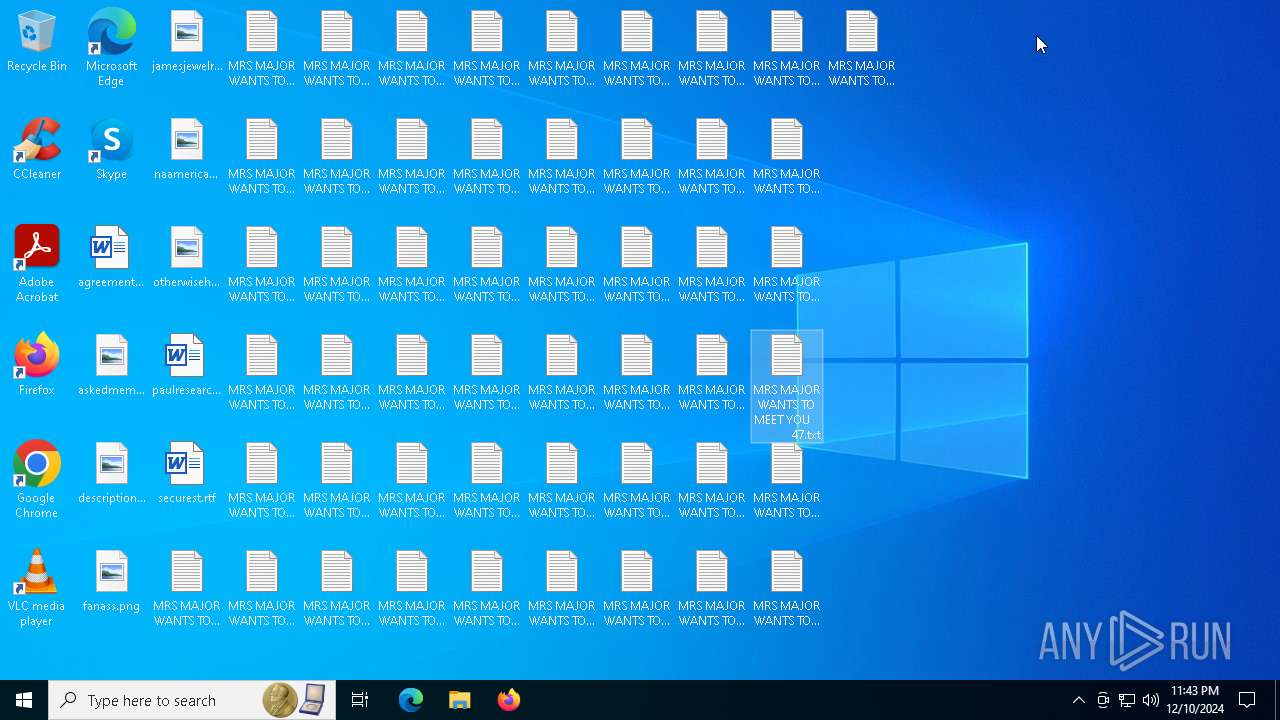
| 6460 | wscript.exe | C:\Users\admin\Desktop\MRS MAJOR WANTS TO MEET YOU 3.txt | text | |
MD5:E20F623B1D5A781F86B51347260D68A5 | SHA256:AFEEBE824FC4A955A673D3D8569A0B49DFBC43C6CC1D4E3D66D9855C28A7A179 | |||
| 6460 | wscript.exe | C:\Users\admin\Desktop\MRS MAJOR WANTS TO MEET YOU 4.txt | text | |
MD5:E20F623B1D5A781F86B51347260D68A5 | SHA256:AFEEBE824FC4A955A673D3D8569A0B49DFBC43C6CC1D4E3D66D9855C28A7A179 | |||
| 6460 | wscript.exe | C:\Users\admin\Desktop\MRS MAJOR WANTS TO MEET YOU 5.txt | text | |
MD5:E20F623B1D5A781F86B51347260D68A5 | SHA256:AFEEBE824FC4A955A673D3D8569A0B49DFBC43C6CC1D4E3D66D9855C28A7A179 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
50
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4896 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
— | — | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
— | — | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
— | — | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 314 b | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
5468 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 418 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.16.204.151:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1076 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
wmploc.dll |
| unknown |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |