| File name: | ransomware jigsaw.exe |
| Full analysis: | https://app.any.run/tasks/b9c5c5fb-136e-44c5-b388-529b727c6982 |
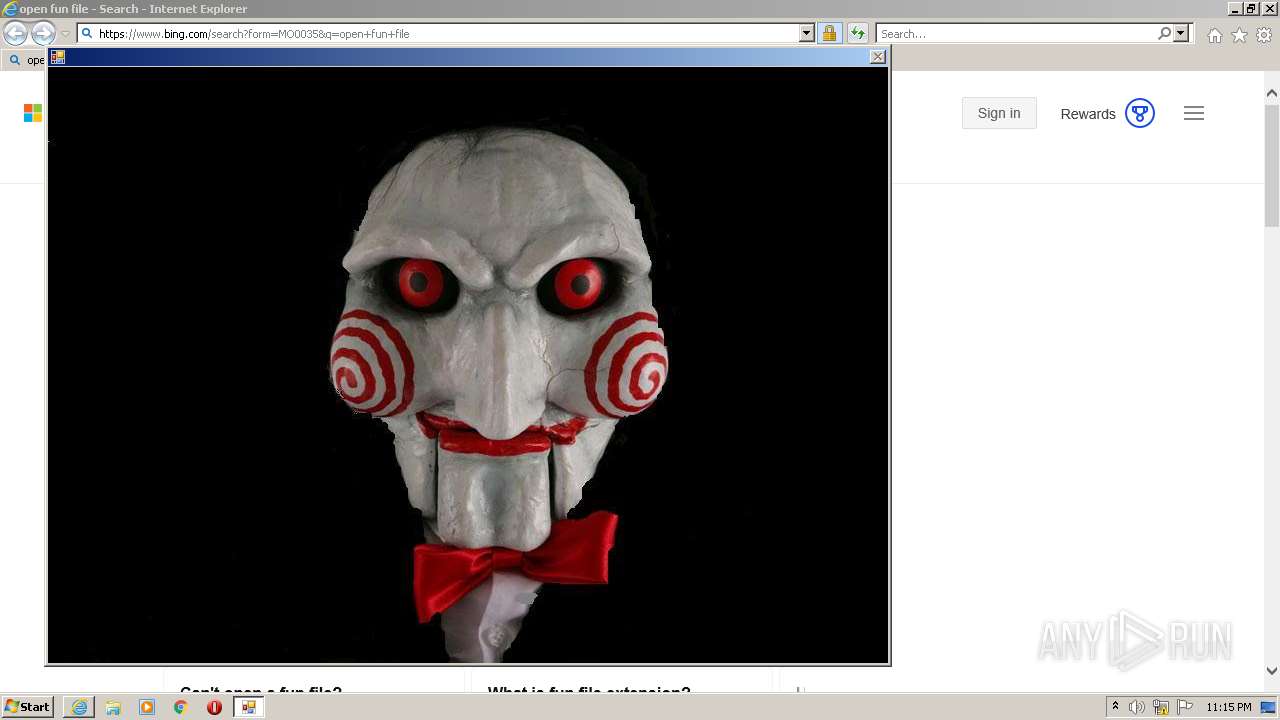
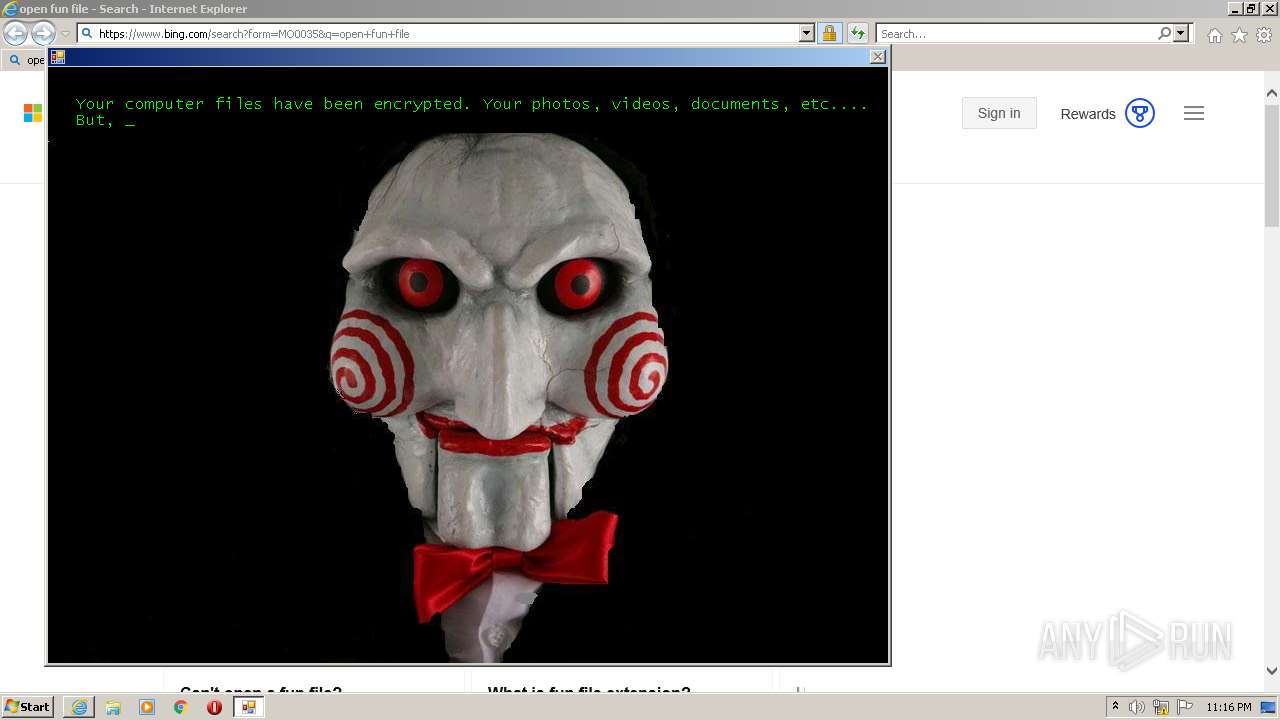
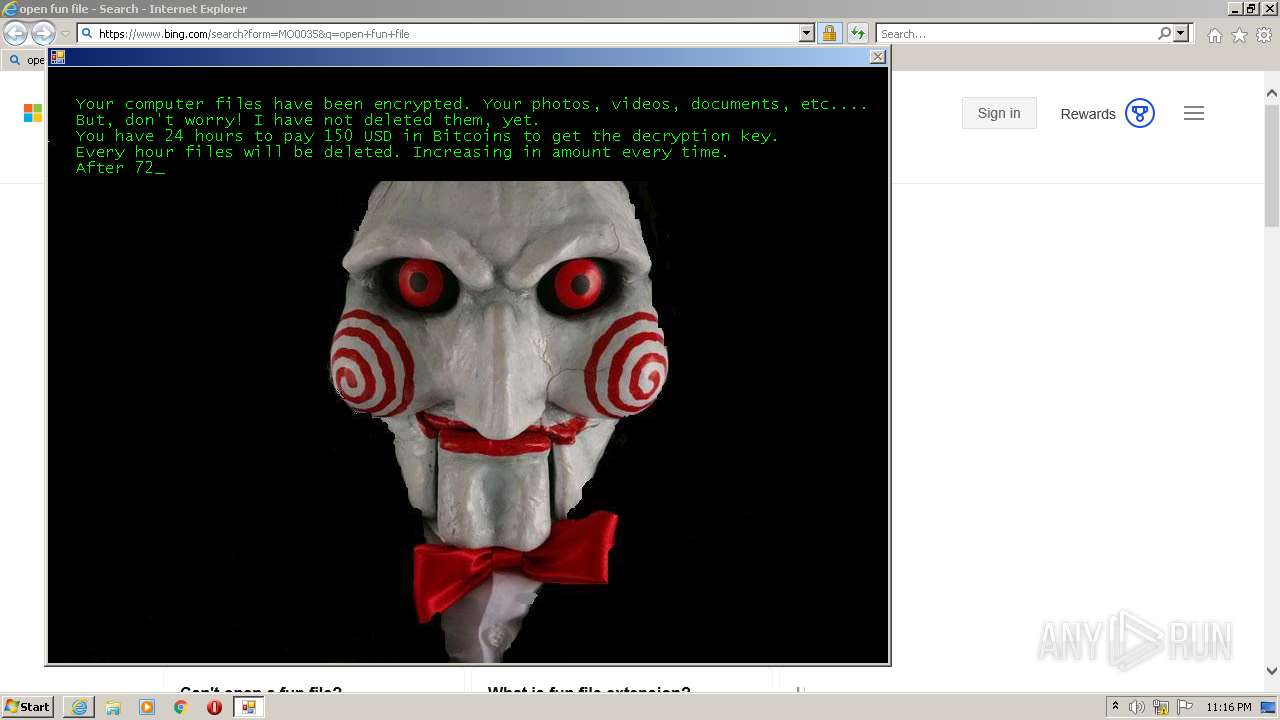
| Verdict: | Malicious activity |
| Analysis date: | March 27, 2023, 22:14:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 2773E3DC59472296CB0024BA7715A64E |
| SHA1: | 27D99FBCA067F478BB91CDBCB92F13A828B00859 |
| SHA256: | 3AE96F73D805E1D3995253DB4D910300D8442EA603737A1428B613061E7F61E7 |
| SSDEEP: | 6144:7fukPLPvucHiQQQ4uuy9ApZbZWxcZt+kTfMLJTOAZiYSXjjeqXus:7fu5cCT7yYlWi8kTfMLJTOAZiYSXjyqX |
MALICIOUS
Steals credentials from Web Browsers
- drpbx.exe (PID: 876)
Actions looks like stealing of personal data
- drpbx.exe (PID: 876)
SUSPICIOUS
Executable content was dropped or overwritten
- ransomware jigsaw.exe (PID: 2368)
Starts itself from another location
- ransomware jigsaw.exe (PID: 2368)
Reads the Internet Settings
- ransomware jigsaw.exe (PID: 2368)
- rundll32.exe (PID: 3480)
INFO
Checks supported languages
- ransomware jigsaw.exe (PID: 2368)
- drpbx.exe (PID: 876)
The process checks LSA protection
- ransomware jigsaw.exe (PID: 2368)
- drpbx.exe (PID: 876)
- explorer.exe (PID: 3812)
Reads the machine GUID from the registry
- ransomware jigsaw.exe (PID: 2368)
- drpbx.exe (PID: 876)
Reads the computer name
- ransomware jigsaw.exe (PID: 2368)
Creates files or folders in the user directory
- ransomware jigsaw.exe (PID: 2368)
- drpbx.exe (PID: 876)
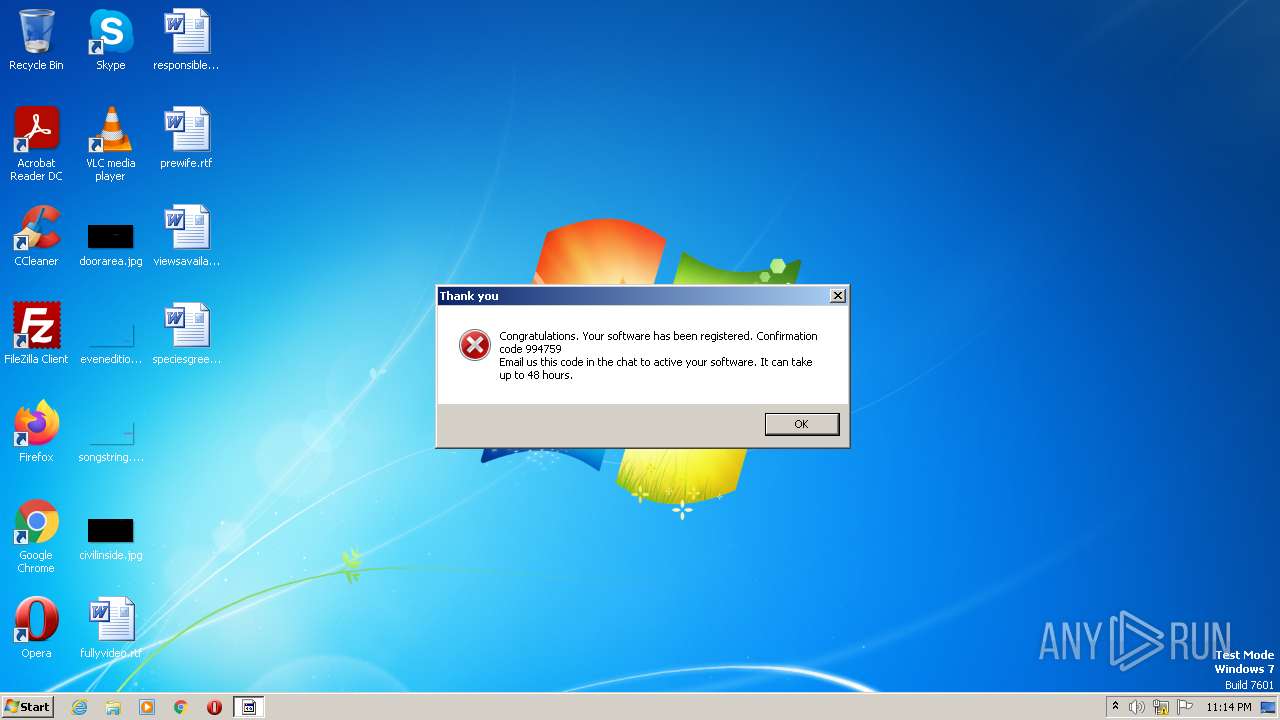
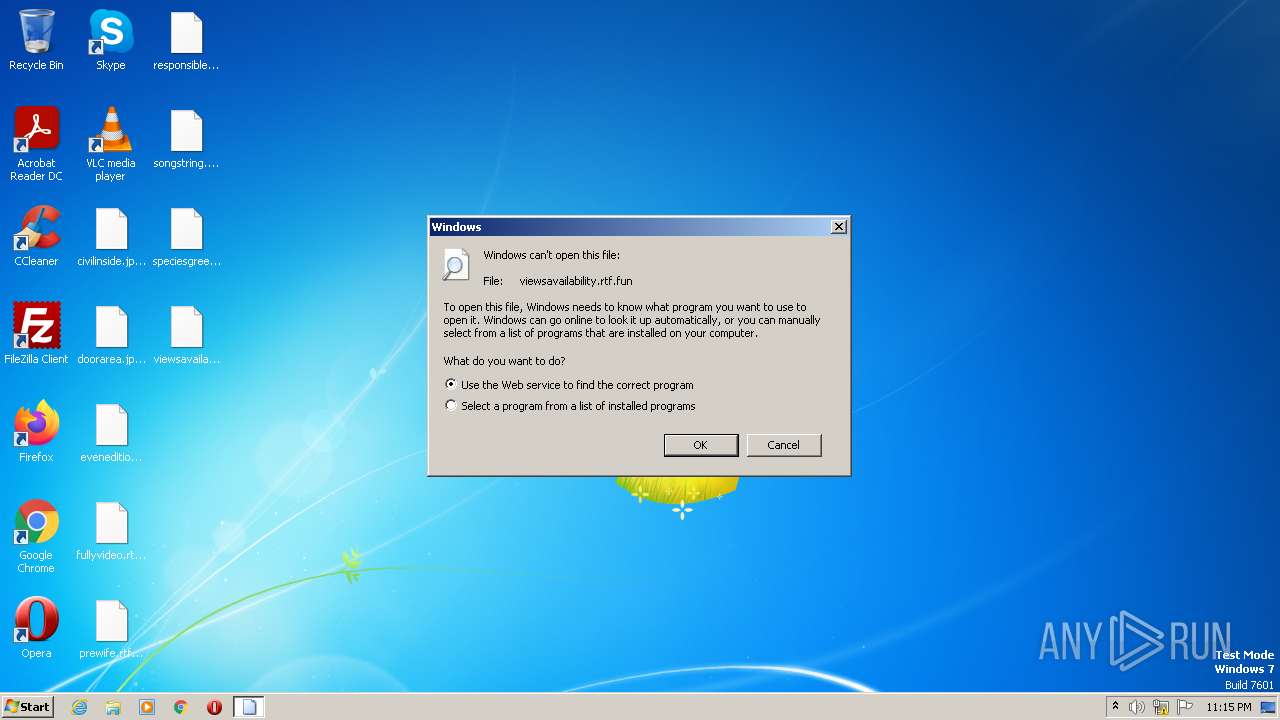
Manual execution by a user
- explorer.exe (PID: 3812)
- rundll32.exe (PID: 3480)
Application launched itself
- iexplore.exe (PID: 3876)
Creates files in the program directory
- drpbx.exe (PID: 876)
Create files in a temporary directory
- drpbx.exe (PID: 876)
- iexplore.exe (PID: 3876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| AssemblyVersion: | 37.0.2.5583 |
|---|---|
| ProductVersion: | 37.0.2.5583 |
| ProductName: | Firefox |
| OriginalFileName: | BitcoinBlackmailer.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright 1999-2012 Firefox and Mozzilla developers. All rights reserved. |
| InternalName: | BitcoinBlackmailer.exe |
| FileVersion: | 37.0.2.5583 |
| FileDescription: | Firefox |
| CompanyName: | - |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 37.0.2.5583 |
| FileVersionNumber: | 37.0.2.5583 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x4e00a |
| UninitializedDataSize: | - |
| InitializedDataSize: | 216576 |
| CodeSize: | 72704 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2016:03:31 06:28:14+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Mar-2016 06:28:14 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Firefox |
| FileVersion: | 37.0.2.5583 |
| InternalName: | BitcoinBlackmailer.exe |
| LegalCopyright: | Copyright 1999-2012 Firefox and Mozzilla developers. All rights reserved. |
| LegalTrademarks: | - |
| OriginalFilename: | BitcoinBlackmailer.exe |
| ProductName: | Firefox |
| ProductVersion: | 37.0.2.5583 |
| Assembly Version: | 37.0.2.5583 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 31-Mar-2016 06:28:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
\x01\x1e!mmUPp`B\x03 | 0x00002000 | 0x00034260 | 0x00034400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99912 |
.text | 0x00038000 | 0x00011878 | 0x00011A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.39056 |
.rsrc | 0x0004A000 | 0x00000650 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.58099 |
.reloc | 0x0004C000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0980042 |
0x0004E000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0.13873 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
44
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 876 | "C:\Users\admin\AppData\Local\Drpbx\drpbx.exe" C:\Users\admin\AppData\Local\Temp\ransomware?jigsaw.exe | C:\Users\admin\AppData\Local\Drpbx\drpbx.exe | ransomware jigsaw.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 37.0.2.5583 Modules
| |||||||||||||||
| 1620 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3876 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | |||||||||||||||
| 2368 | "C:\Users\admin\AppData\Local\Temp\ransomware jigsaw.exe" | C:\Users\admin\AppData\Local\Temp\ransomware jigsaw.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 37.0.2.5583 Modules
| |||||||||||||||
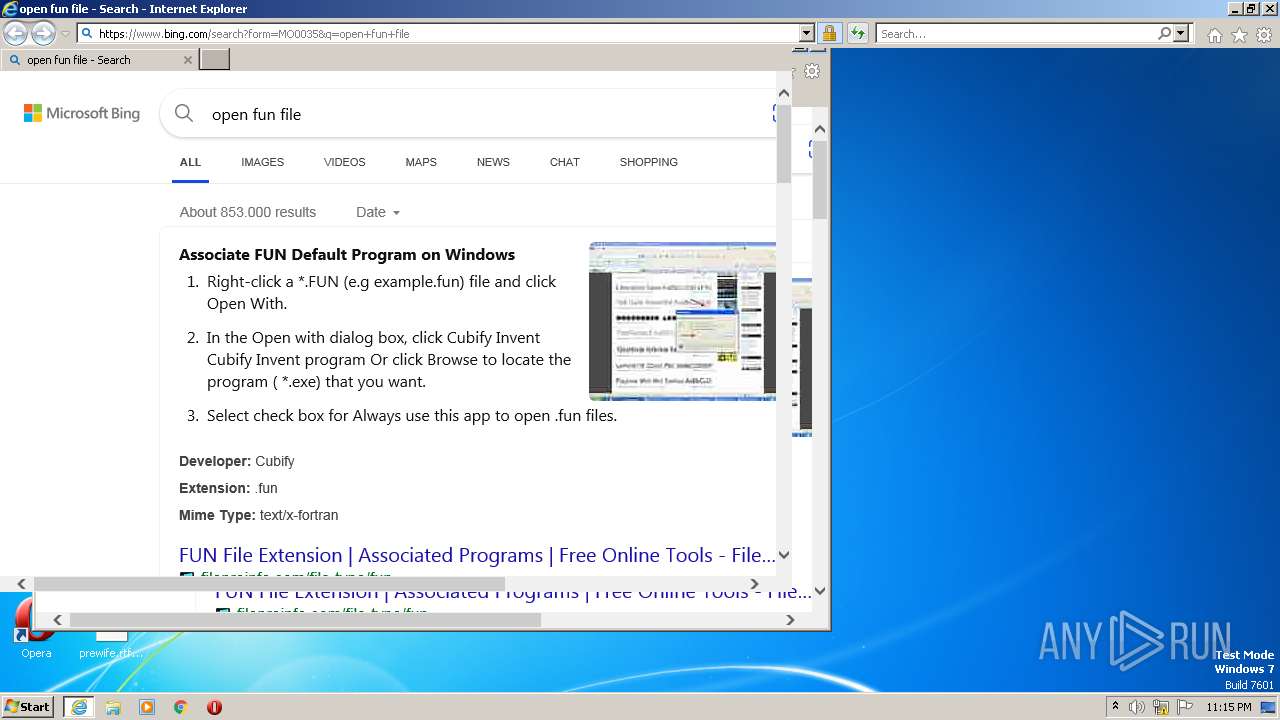
| 3480 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\viewsavailability.rtf.fun | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 3812 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3876 | "C:\Program Files\Internet Explorer\iexplore.exe" http://go.microsoft.com/fwlink/?LinkId=57426&Ext=fun | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | |||||||||||||||
Total events
76 920
Read events
76 904
Write events
16
Delete events
0
Modification events
| (PID) Process: | (2368) ransomware jigsaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2368) ransomware jigsaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2368) ransomware jigsaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2368) ransomware jigsaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
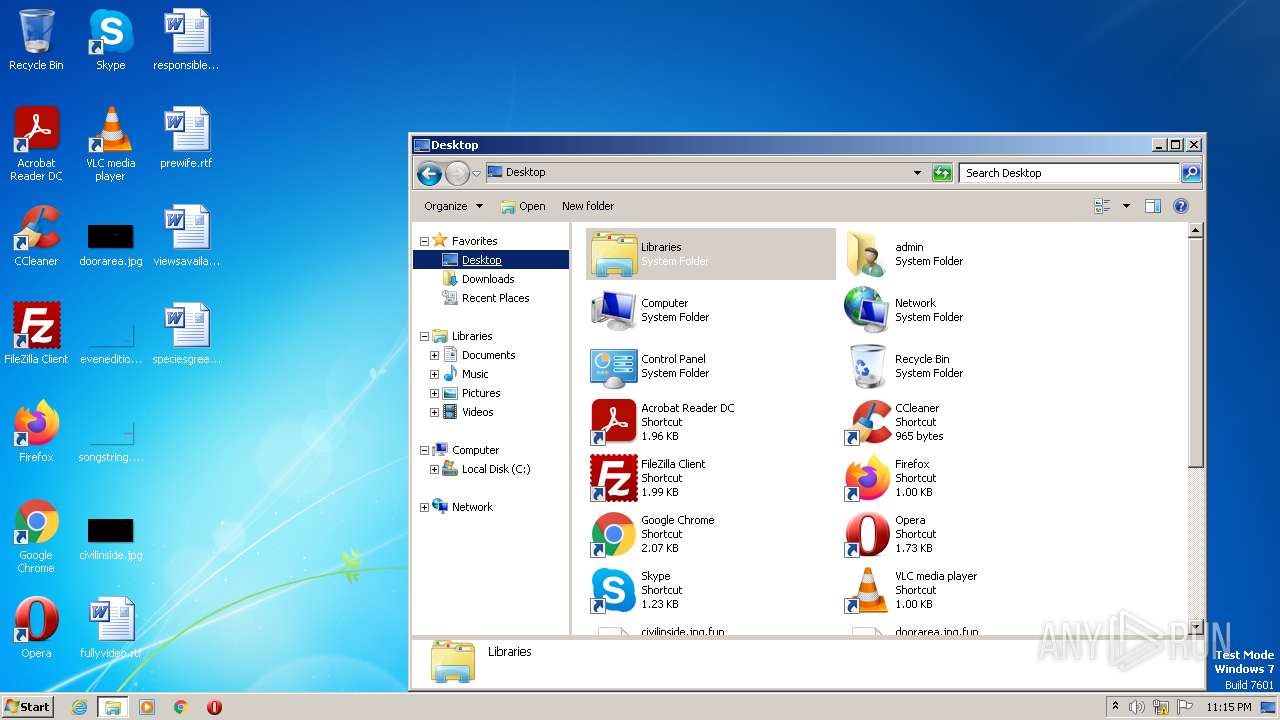
Executable files
4
Suspicious files
1 924
Text files
340
Unknown types
20
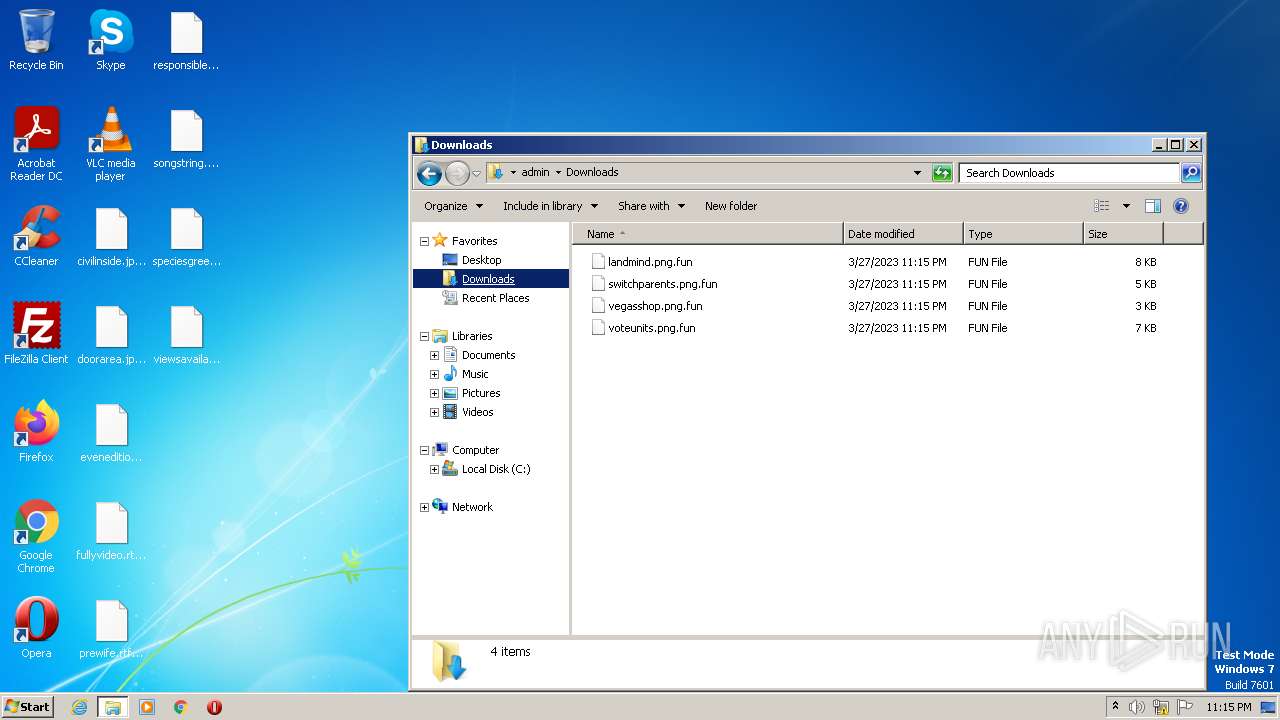
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 876 | drpbx.exe | C:\MSOCache\All Users\{90140000-0015-0410-0000-0000000FF1CE}-C\branding.xml.fun | binary | |
MD5:FD2ABF1B947745C51FC989779BC0A002 | SHA256:21CF977AA01CC53D7C5C54A2C448755455F033AA35953A8CB969E19F221FF4CE | |||
| 876 | drpbx.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccessMUI.xml.fun | binary | |
MD5:B8E36A31142237D9E5C6A18056D448C1 | SHA256:9E30A1A8685998EC8227FAA33A0FD0B2485FF430C4A3D4FC41CDAC6C33F33BE7 | |||
| 876 | drpbx.exe | C:\MSOCache\All Users\{90140000-0015-0412-0000-0000000FF1CE}-C\branding.xml.fun | binary | |
MD5:7B192D60D97933EB76C4BCEB21C8189C | SHA256:0A0193004AC8E5882C3797AC06378540FC0A31DE45E5828316CFA52C70FF6EC6 | |||
| 876 | drpbx.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\Setup.xml.fun | binary | |
MD5:9D19D98D71BBB006AED9379F74906F6B | SHA256:E32F5C1558986B99421C3F197F1FEFDF2CB485693FF4AD4963904CBBBEBB9574 | |||
| 2368 | ransomware jigsaw.exe | C:\Users\admin\AppData\Roaming\Frfx\firefox.exe | executable | |
MD5:2773E3DC59472296CB0024BA7715A64E | SHA256:3AE96F73D805E1D3995253DB4D910300D8442EA603737A1428B613061E7F61E7 | |||
| 876 | drpbx.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\Setup.xml.fun | binary | |
MD5:26F9CD4F0D02DAD6930E5236953A470D | SHA256:53D145BB1F639490715965053E247D07633EC8C3A7EBCA2FBED934427968D25A | |||
| 876 | drpbx.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\AccessMUI.xml.fun | binary | |
MD5:C004E8491FF15DE08F1FA4E4C998A799 | SHA256:11F36C2CDDB7ACFBE430A304D826F2D3921826B33B08A9A82624AD6ADB3D3C74 | |||
| 876 | drpbx.exe | C:\MSOCache\All Users\{90140000-0015-040C-0000-0000000FF1CE}-C\branding.xml.fun | binary | |
MD5:D2112D5C5B9E497E6E4209DE70F2574C | SHA256:F43E43A77A95CB8C9159A1CEC6D038EF9A956EC3327BCFC95B998EC036B2D29C | |||
| 876 | drpbx.exe | C:\MSOCache\All Users\{90140000-0015-0410-0000-0000000FF1CE}-C\AccessMUI.xml.fun | binary | |
MD5:E69B0F16096387BAF64C01C5469DFB69 | SHA256:261AF3987D4EACA7EBE7EB049FACEAEDF0CA95675D0FD7500EE050F9CAABC43F | |||
| 876 | drpbx.exe | C:\MSOCache\All Users\{90140000-0015-0410-0000-0000000FF1CE}-C\Setup.xml.fun | binary | |
MD5:F5E7F47DD11D3B203003805B6E709333 | SHA256:B865AB1E62E3579C6ADA2E4BD3A0F0AA13064F61A2AC61429FA0DFF7B8EAB4D7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
22
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1620 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
1620 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
1620 | iexplore.exe | GET | 301 | 2.21.20.141:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=fun | DE | — | — | whitelisted |
1620 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
1620 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
1620 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?230e2f6622aa1e49 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1620 | iexplore.exe | 95.100.53.90:443 | go.microsoft.com | AKAMAI-AS | CH | suspicious |
1620 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1620 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1620 | iexplore.exe | 2.21.20.141:80 | shell.windows.com | Akamai International B.V. | DE | suspicious |
1620 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3876 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1620 | iexplore.exe | 23.36.163.98:443 | r.bing.com | Akamai International B.V. | DE | suspicious |
1620 | iexplore.exe | 40.126.32.76:443 | login.microsoftonline.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
shell.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
r.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |