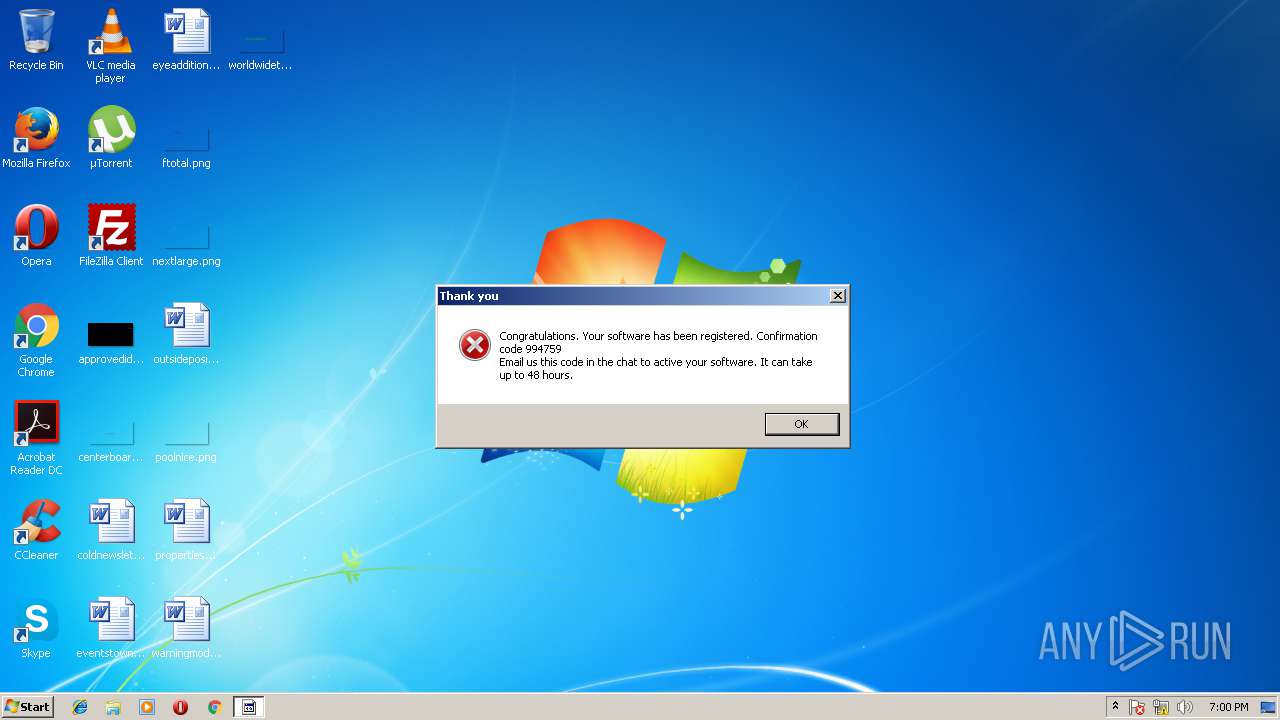
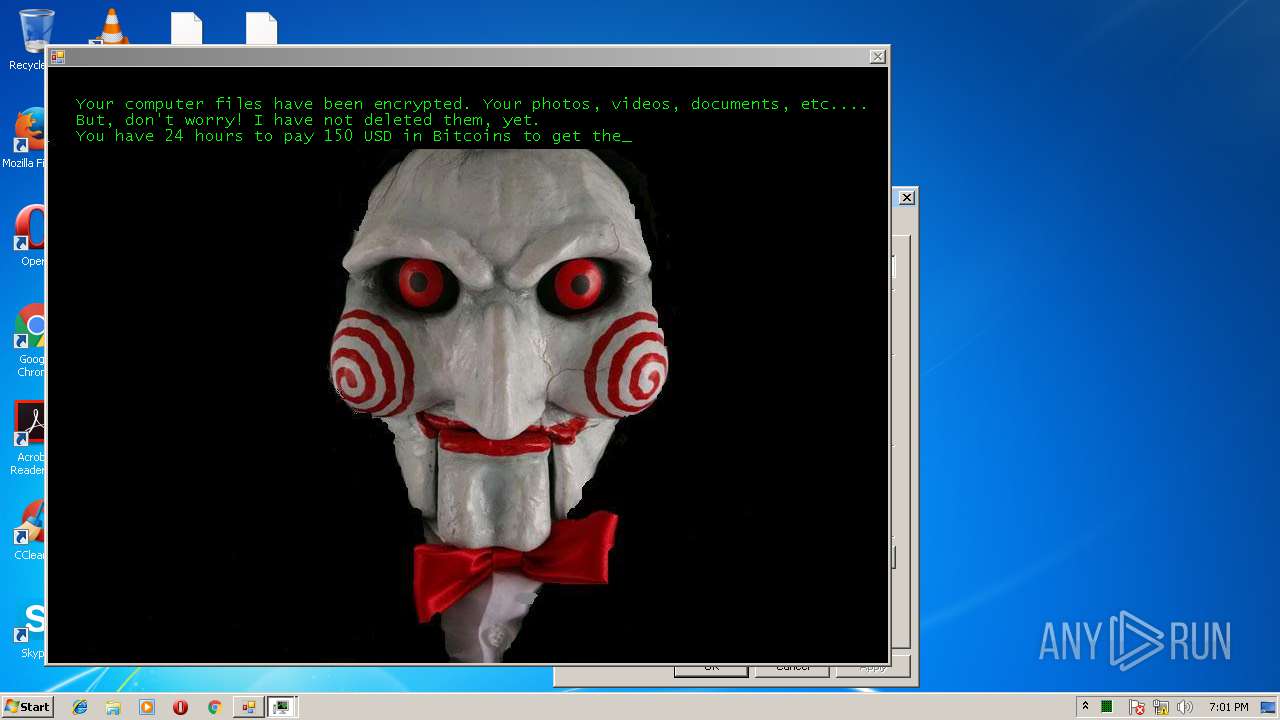
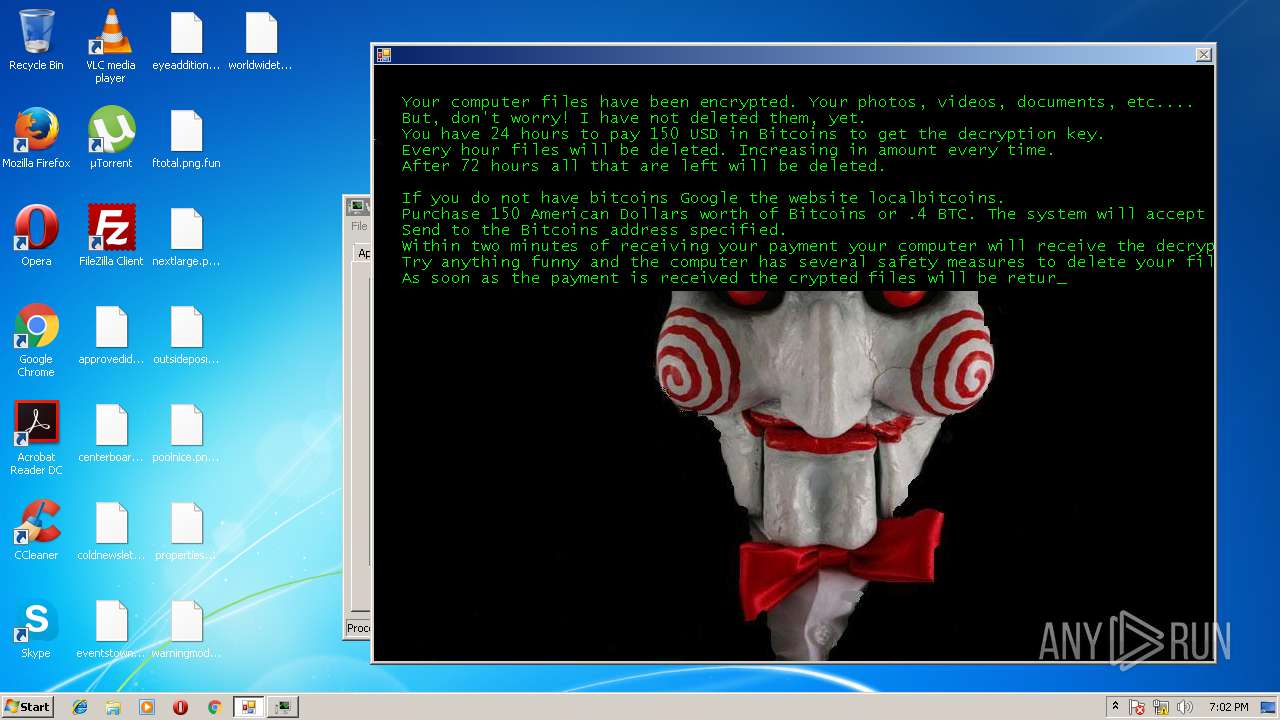
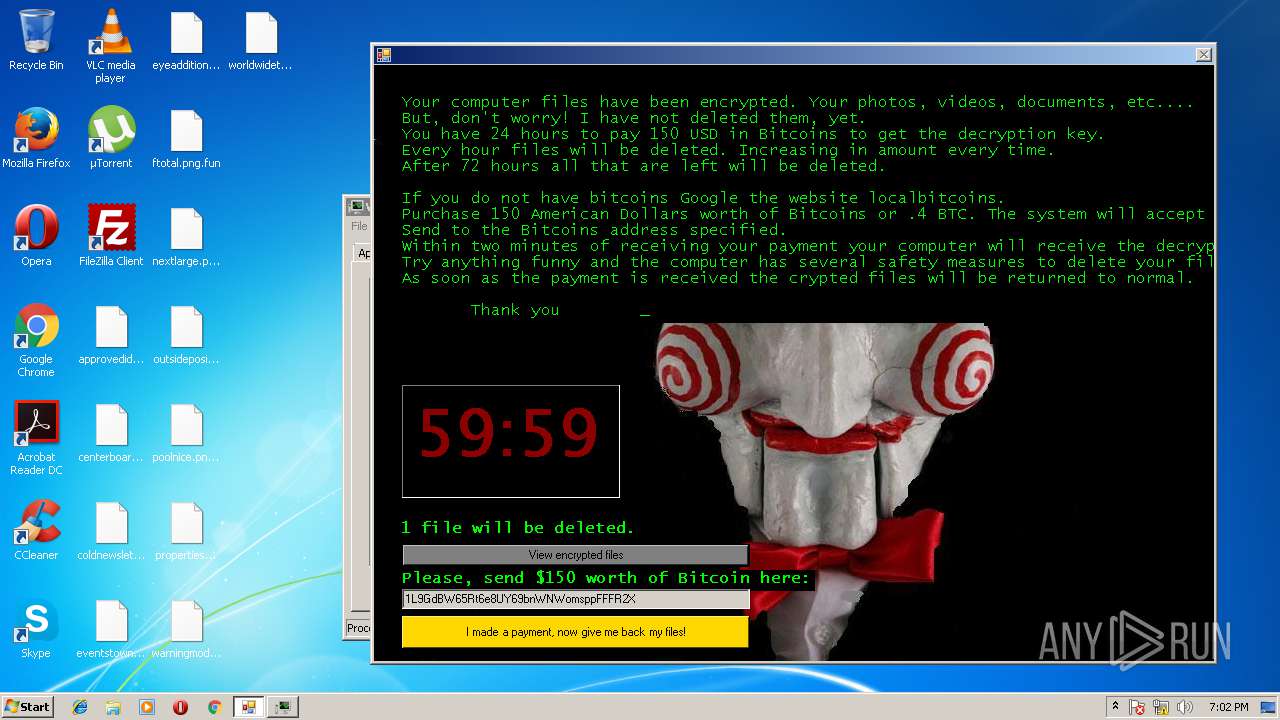
| File name: | jigsaw |
| Full analysis: | https://app.any.run/tasks/463cb971-a7dd-44f6-b6e1-d1526fcfa536 |
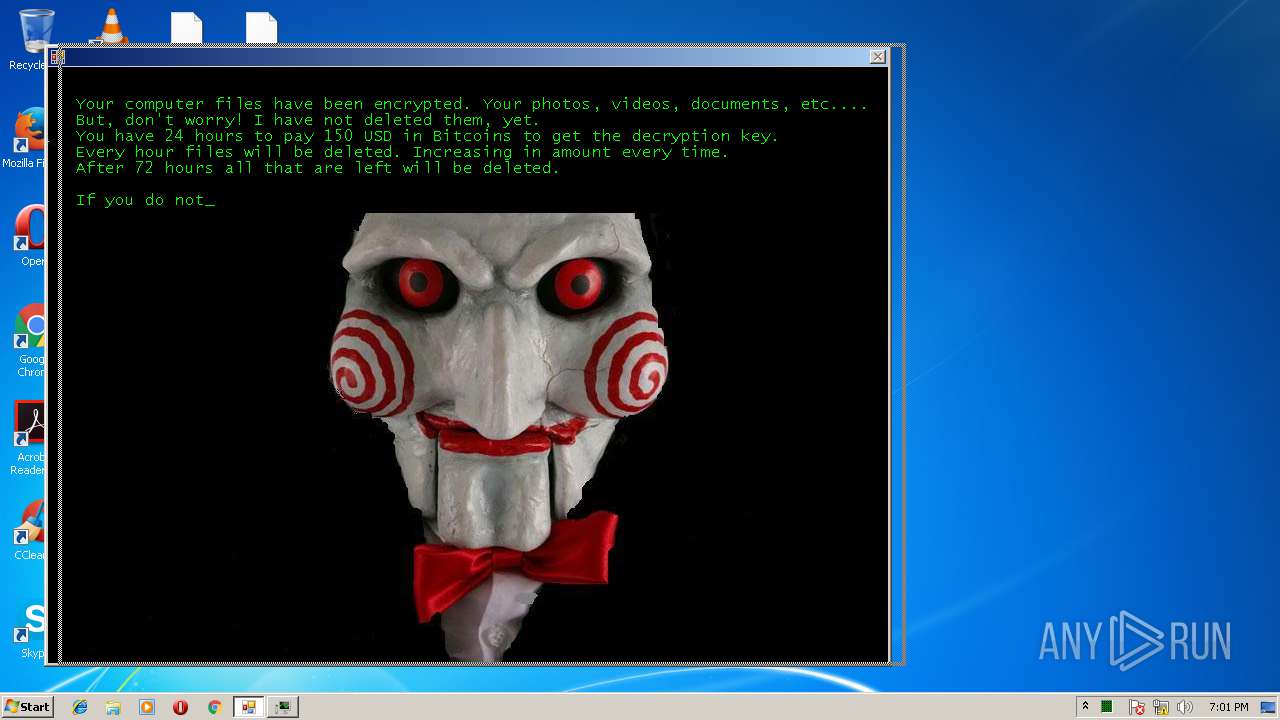
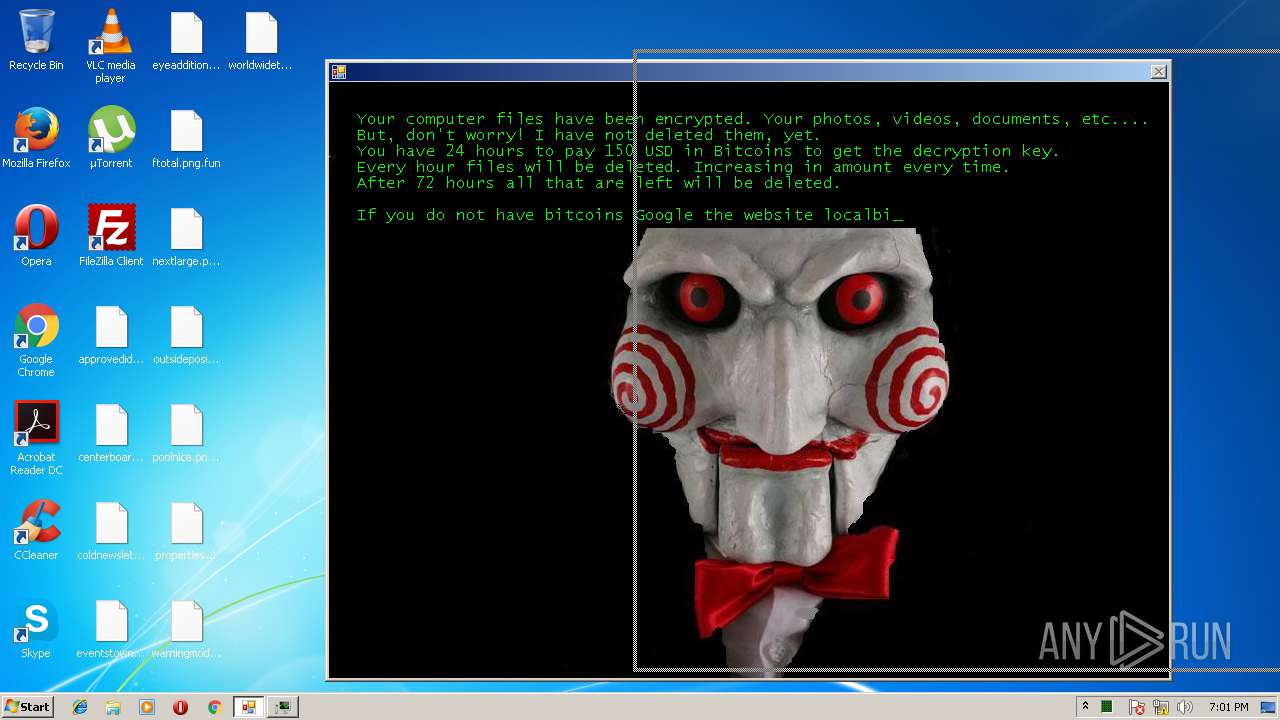
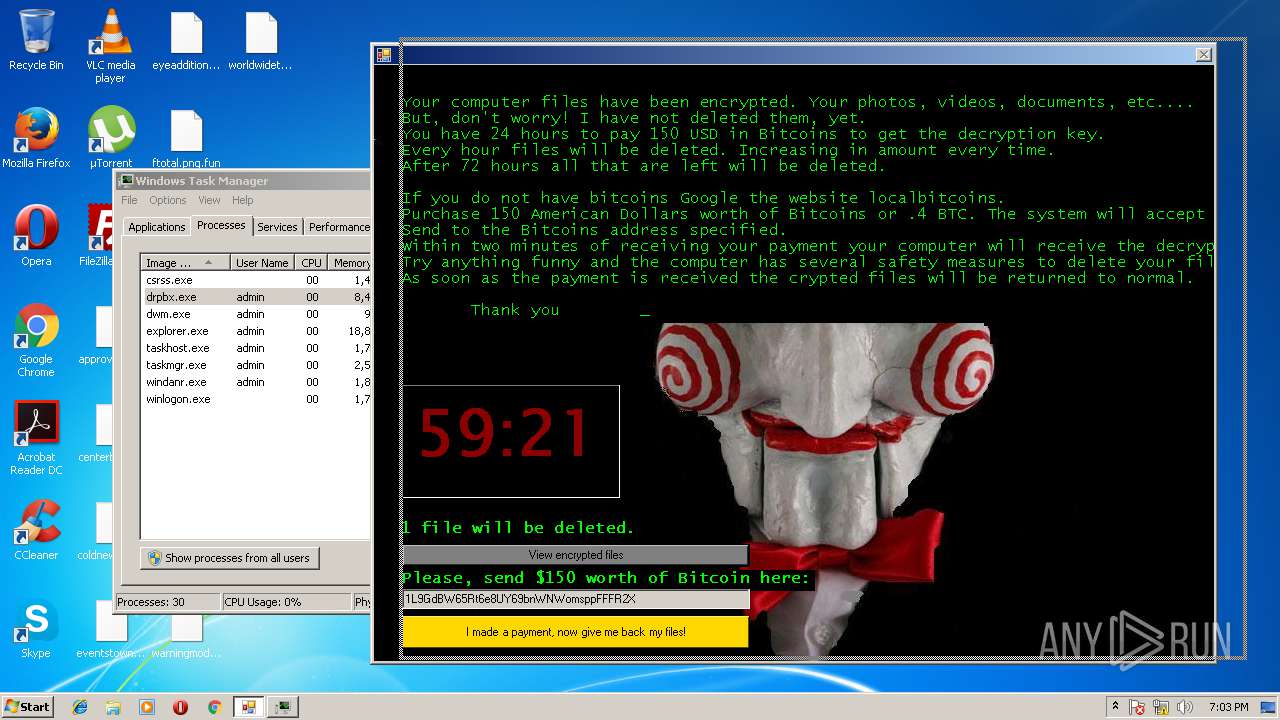
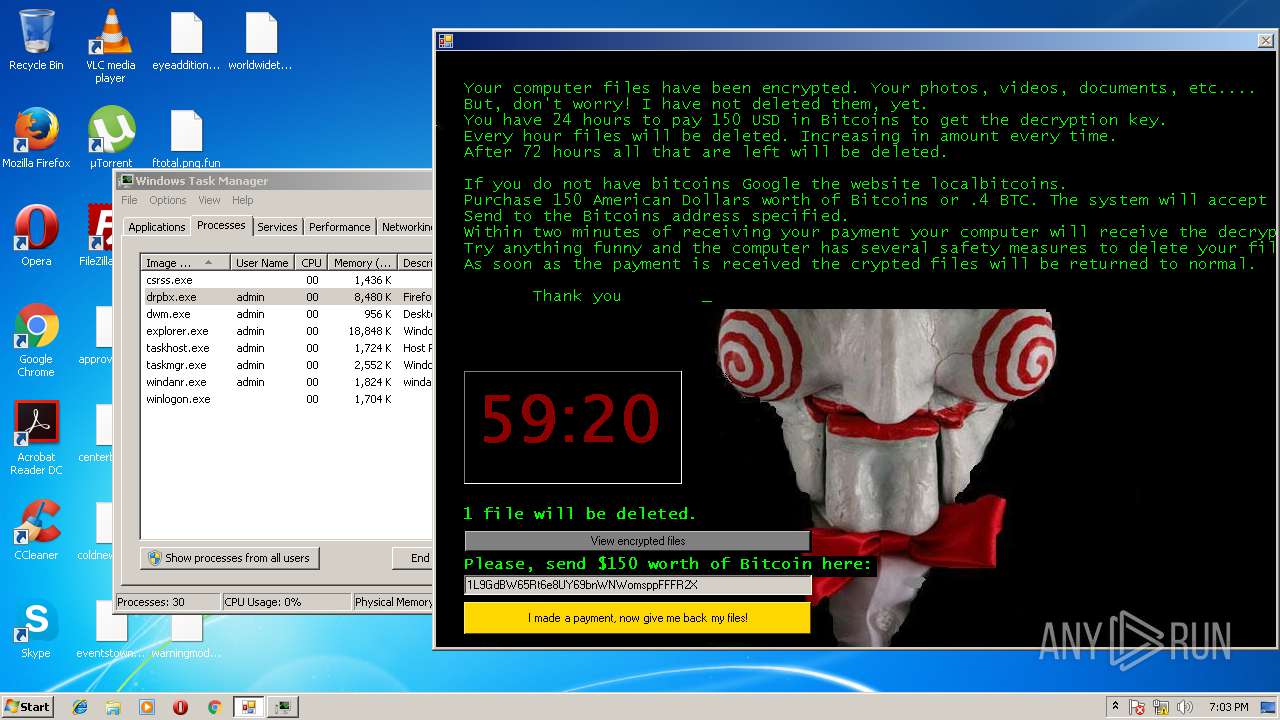
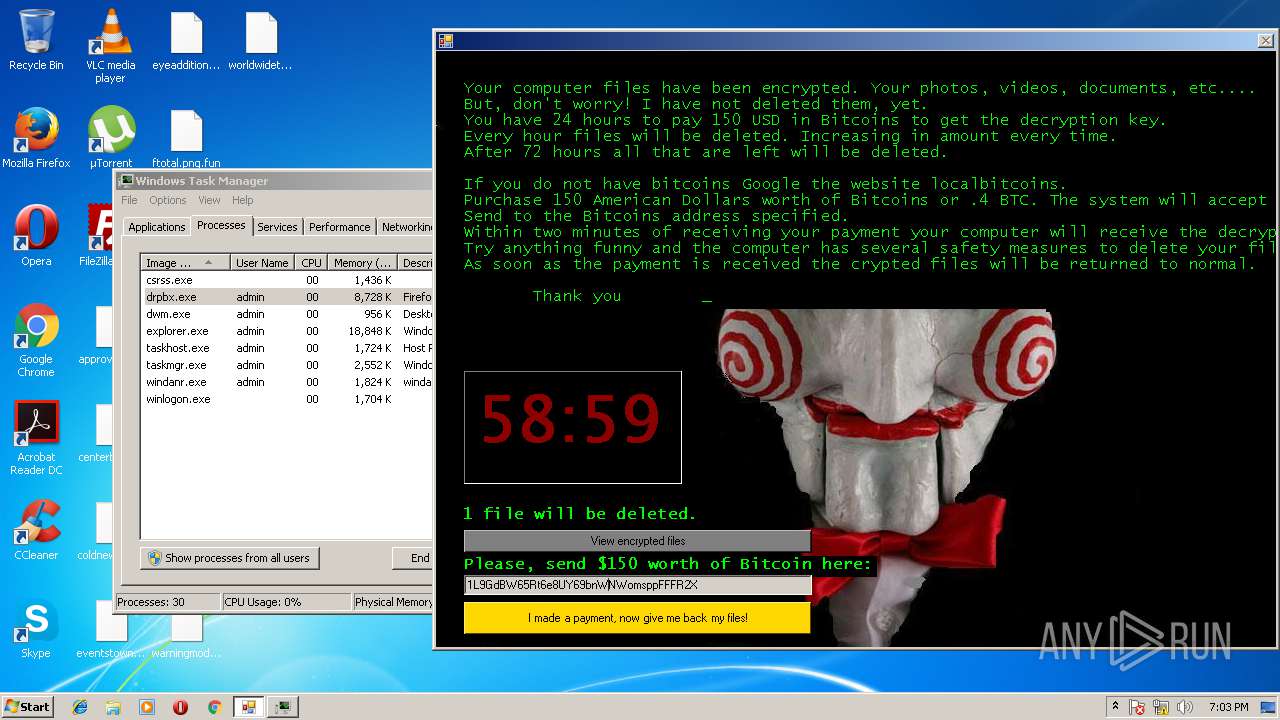
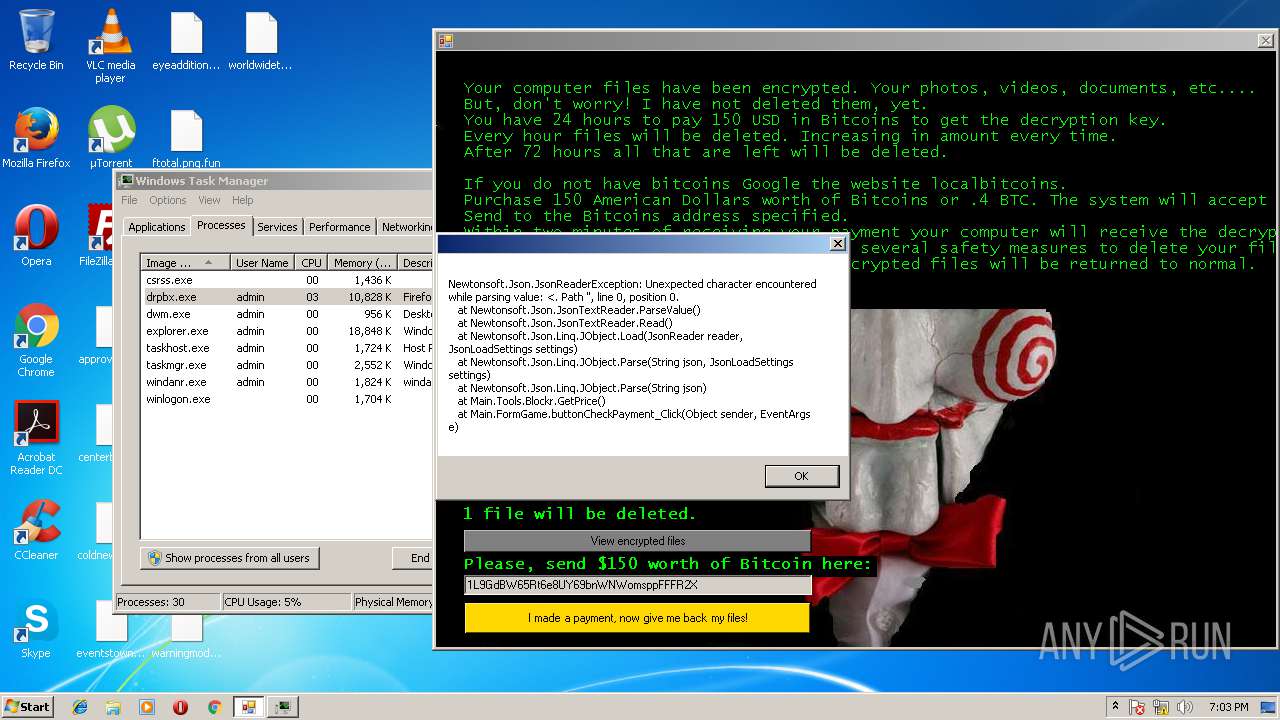
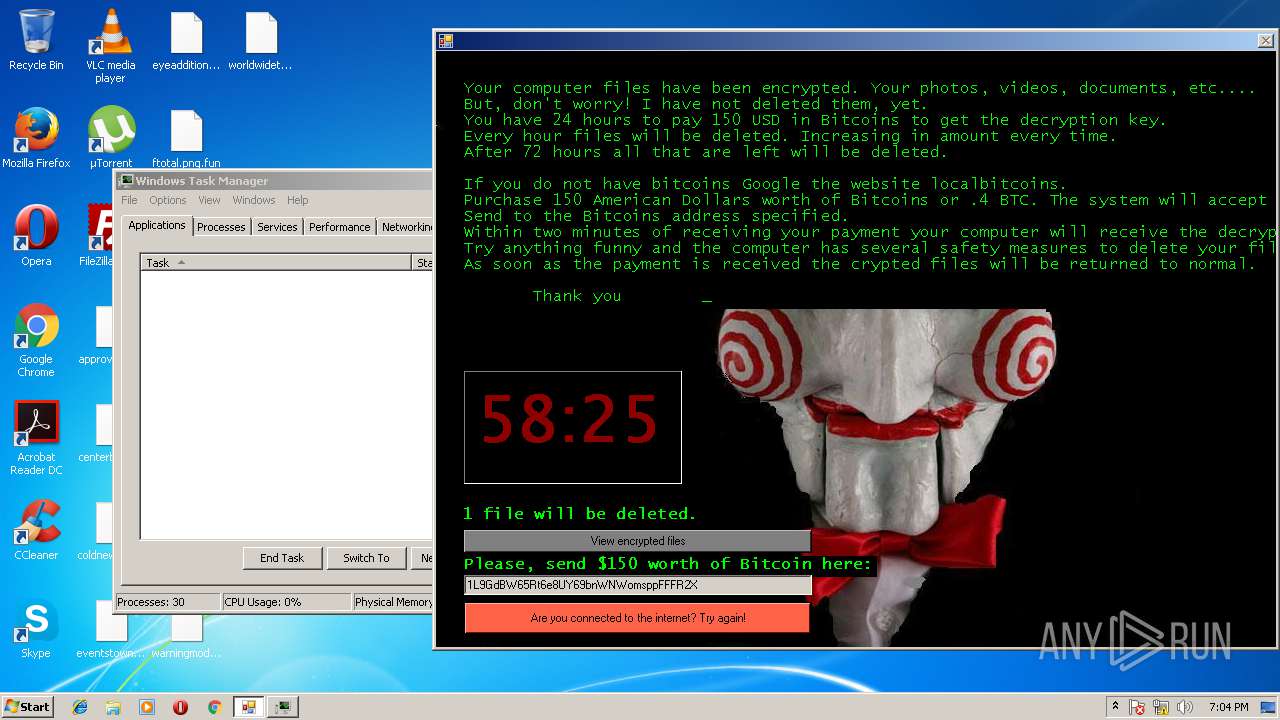
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2018, 18:00:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 2773E3DC59472296CB0024BA7715A64E |
| SHA1: | 27D99FBCA067F478BB91CDBCB92F13A828B00859 |
| SHA256: | 3AE96F73D805E1D3995253DB4D910300D8442EA603737A1428B613061E7F61E7 |
| SSDEEP: | 6144:7fukPLPvucHiQQQ4uuy9ApZbZWxcZt+kTfMLJTOAZiYSXjjeqXus:7fu5cCT7yYlWi8kTfMLJTOAZiYSXjyqX |
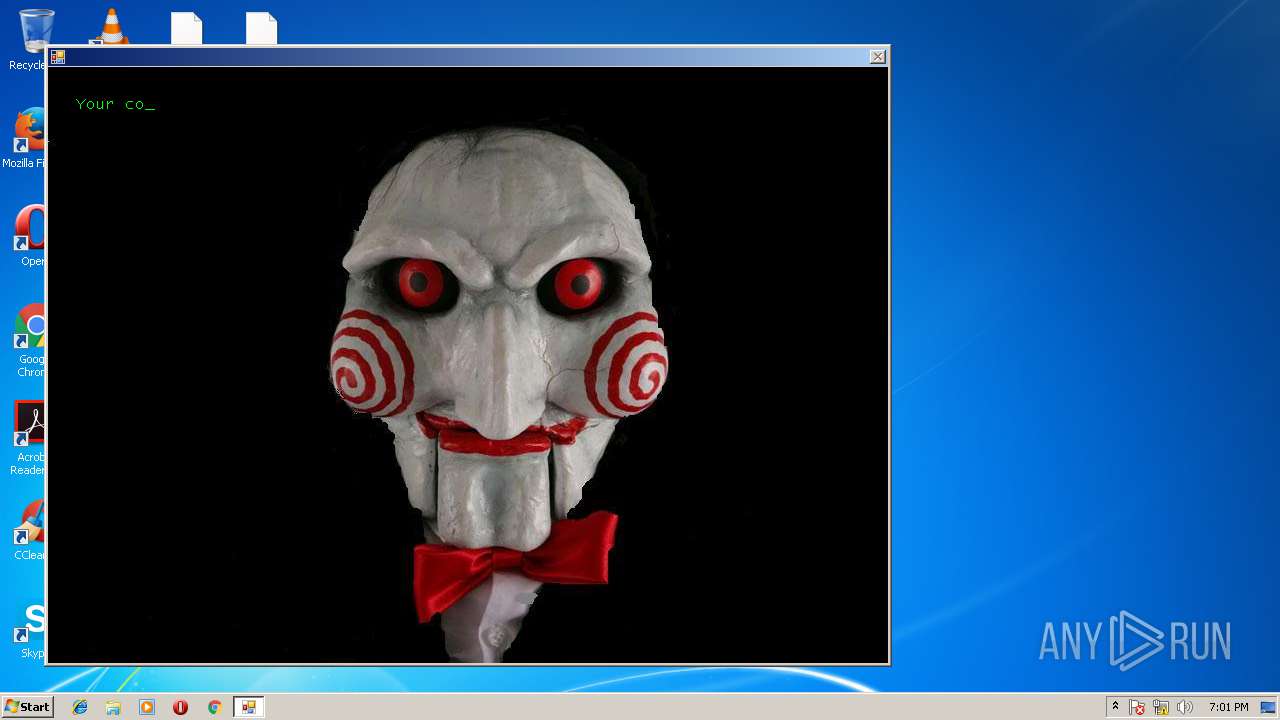
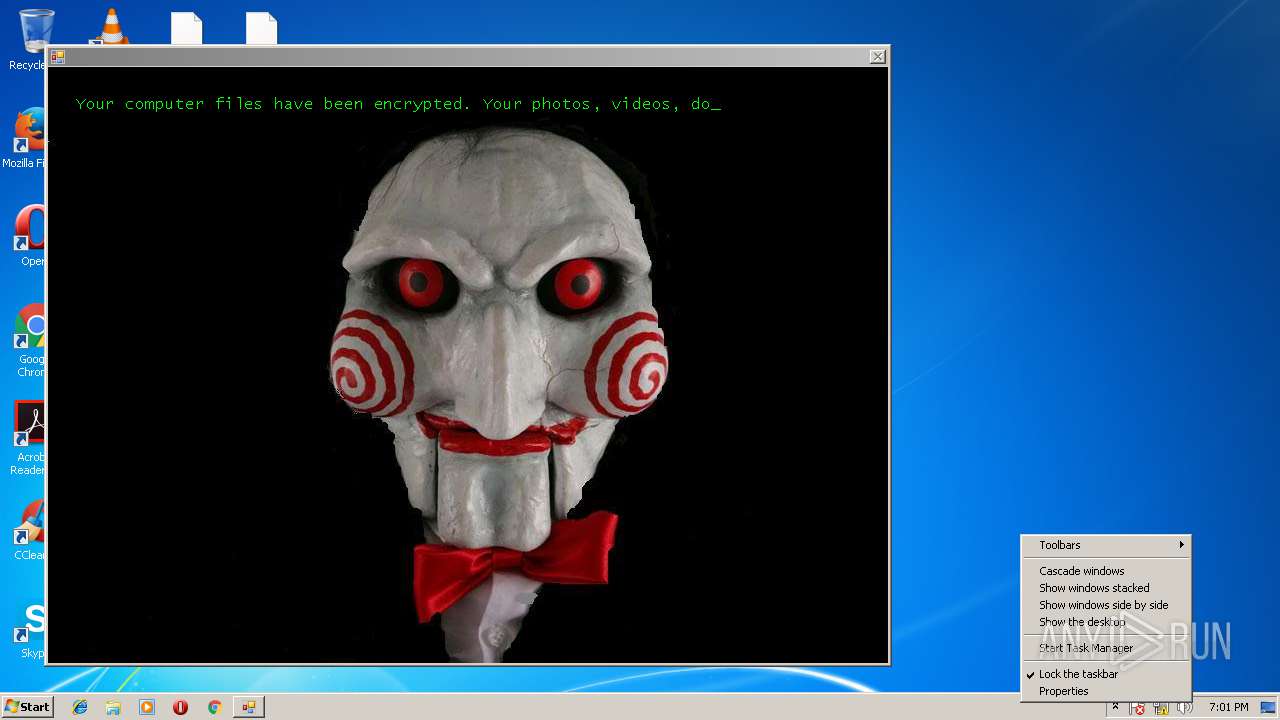
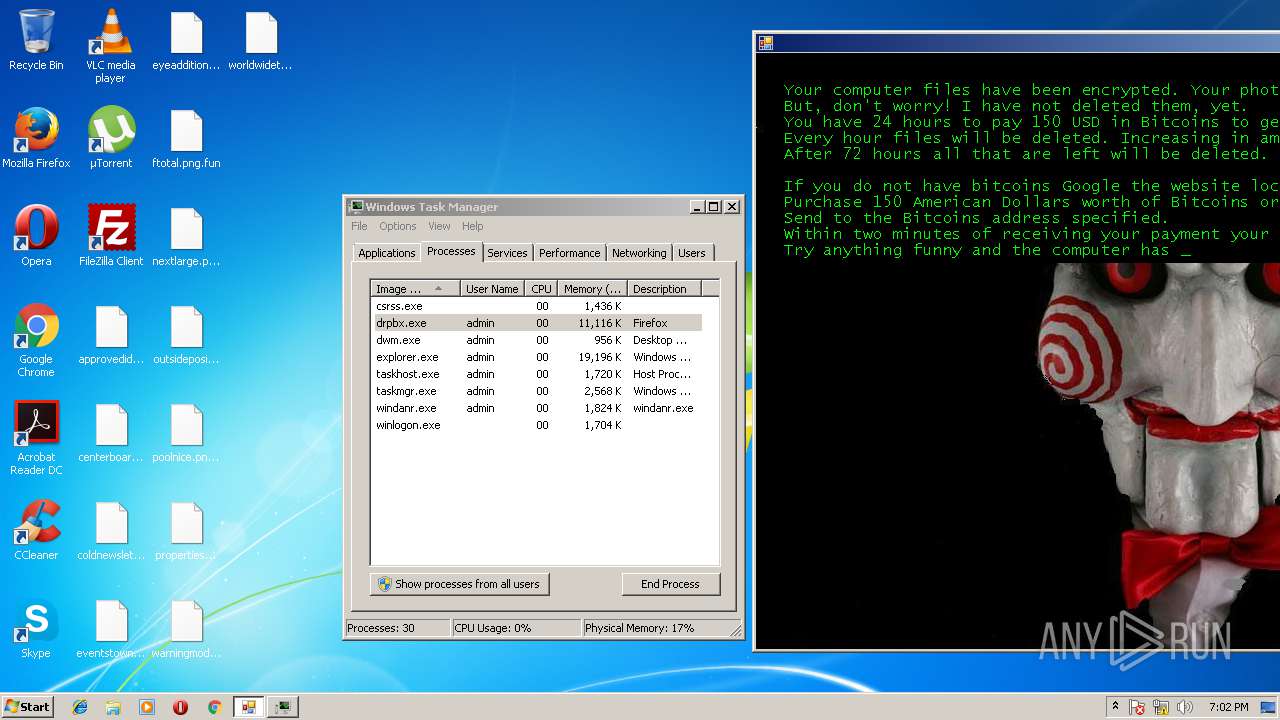
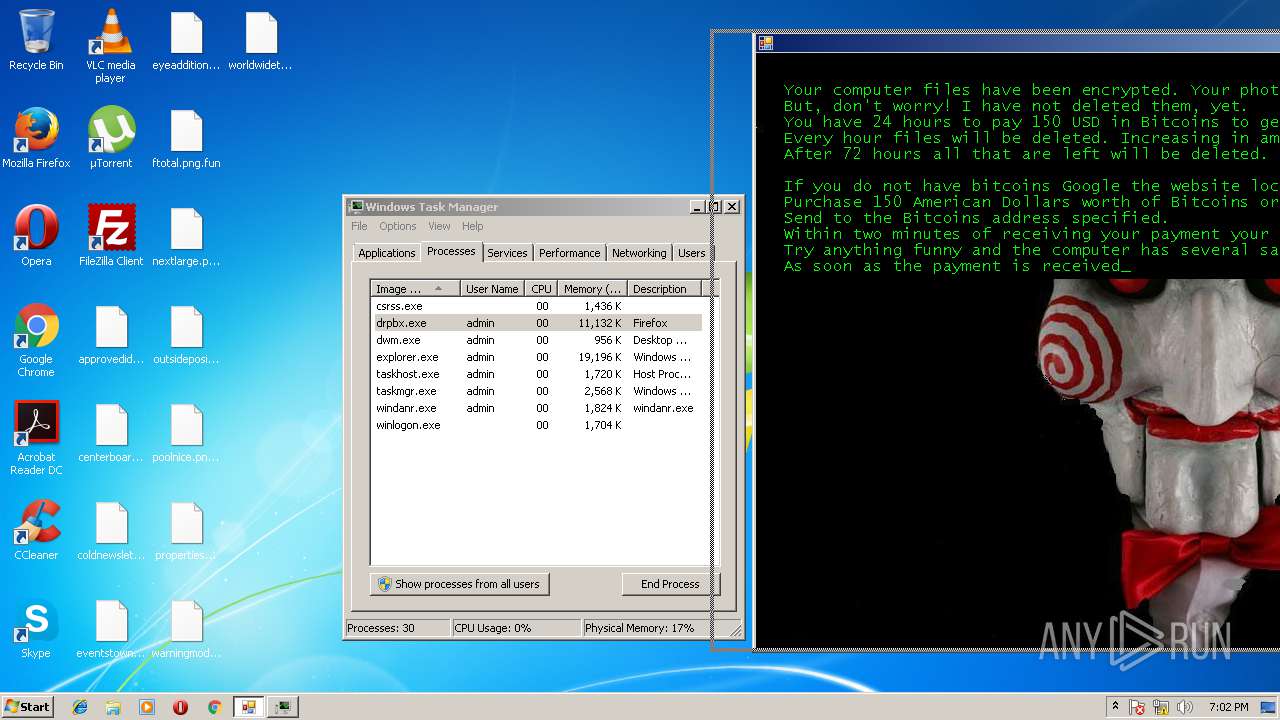
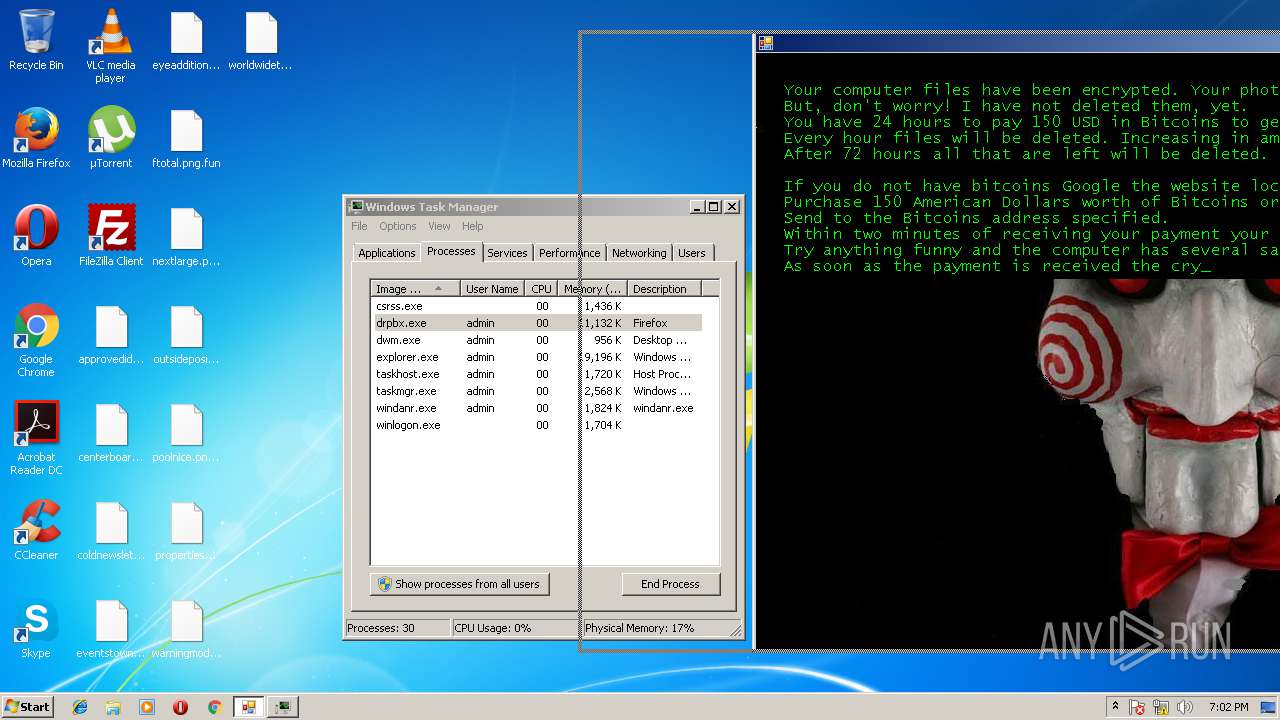
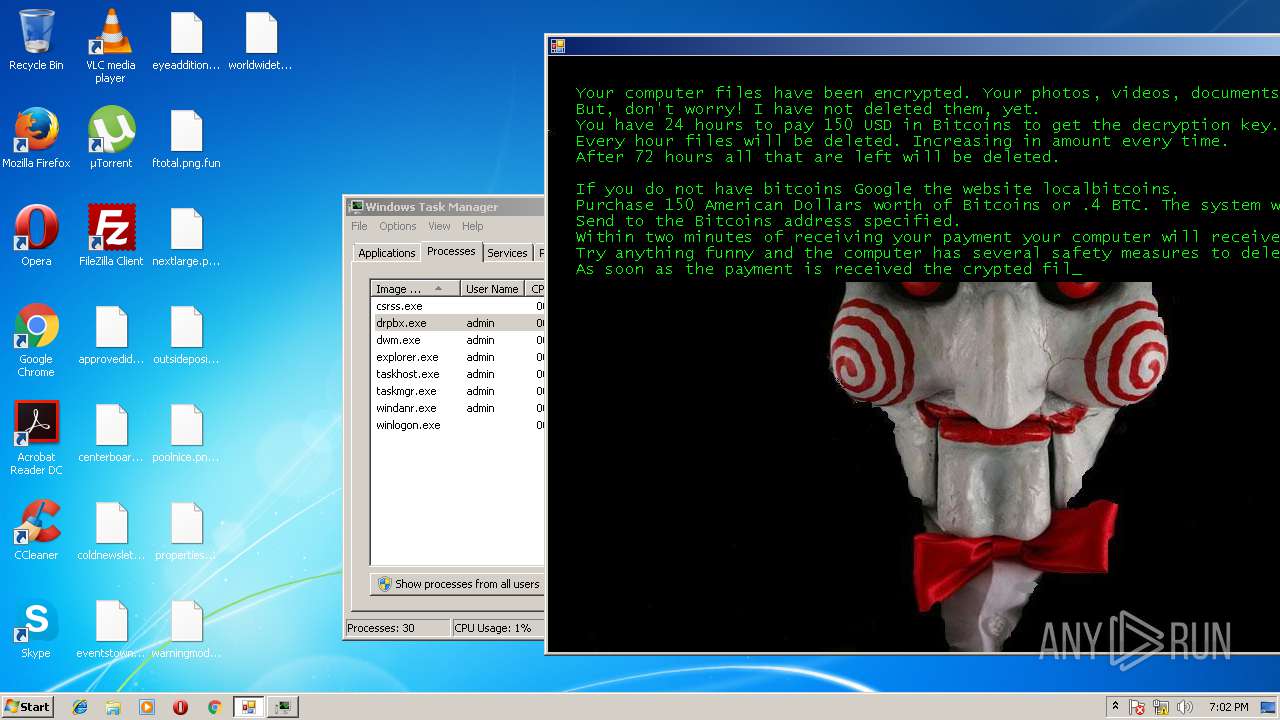
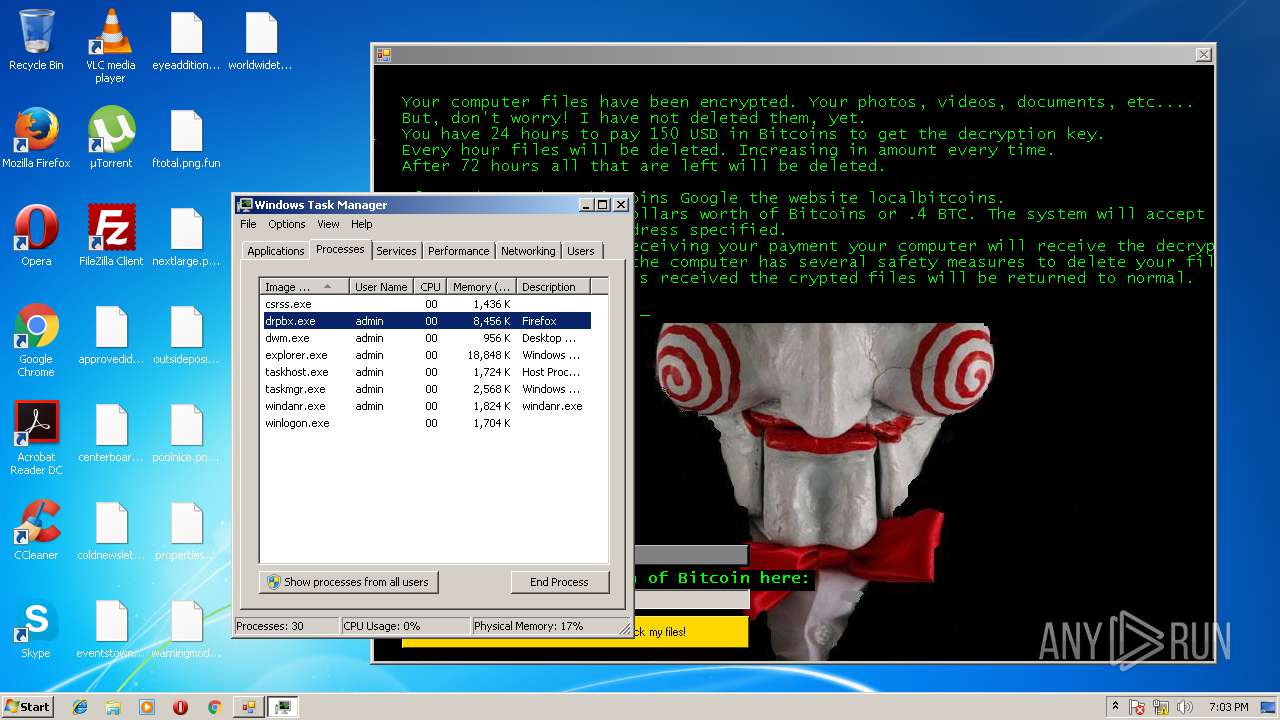
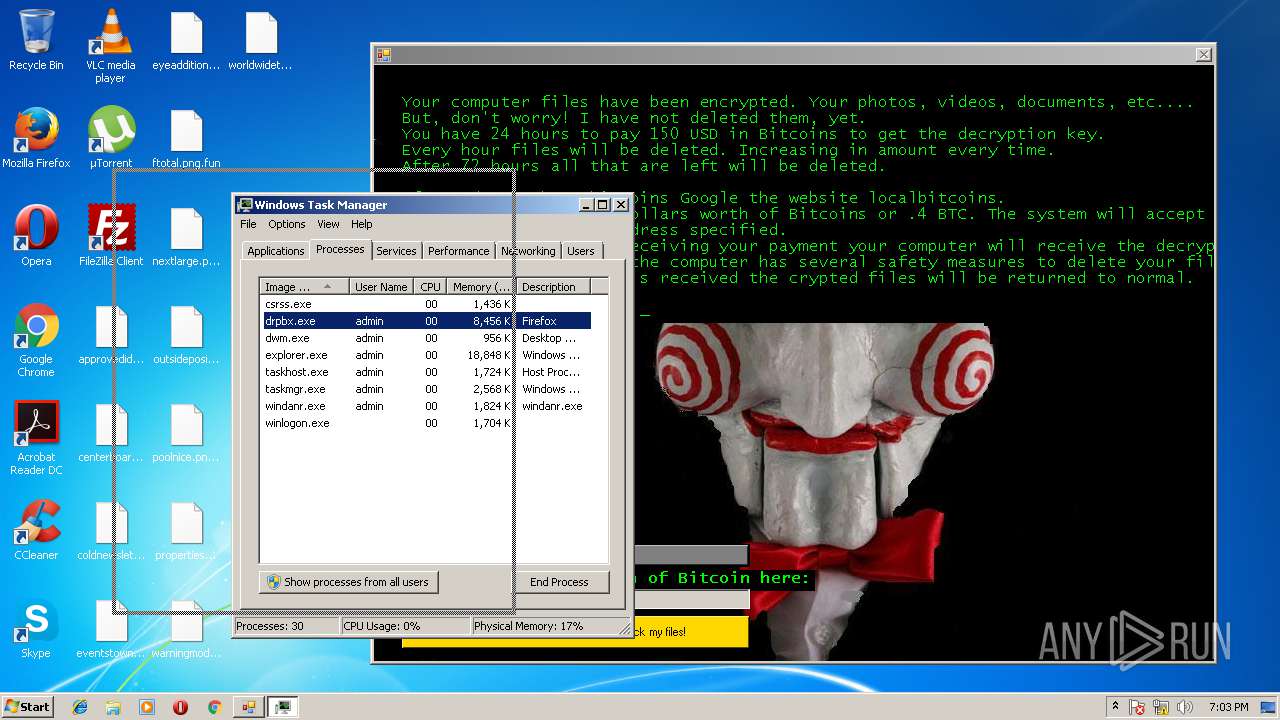
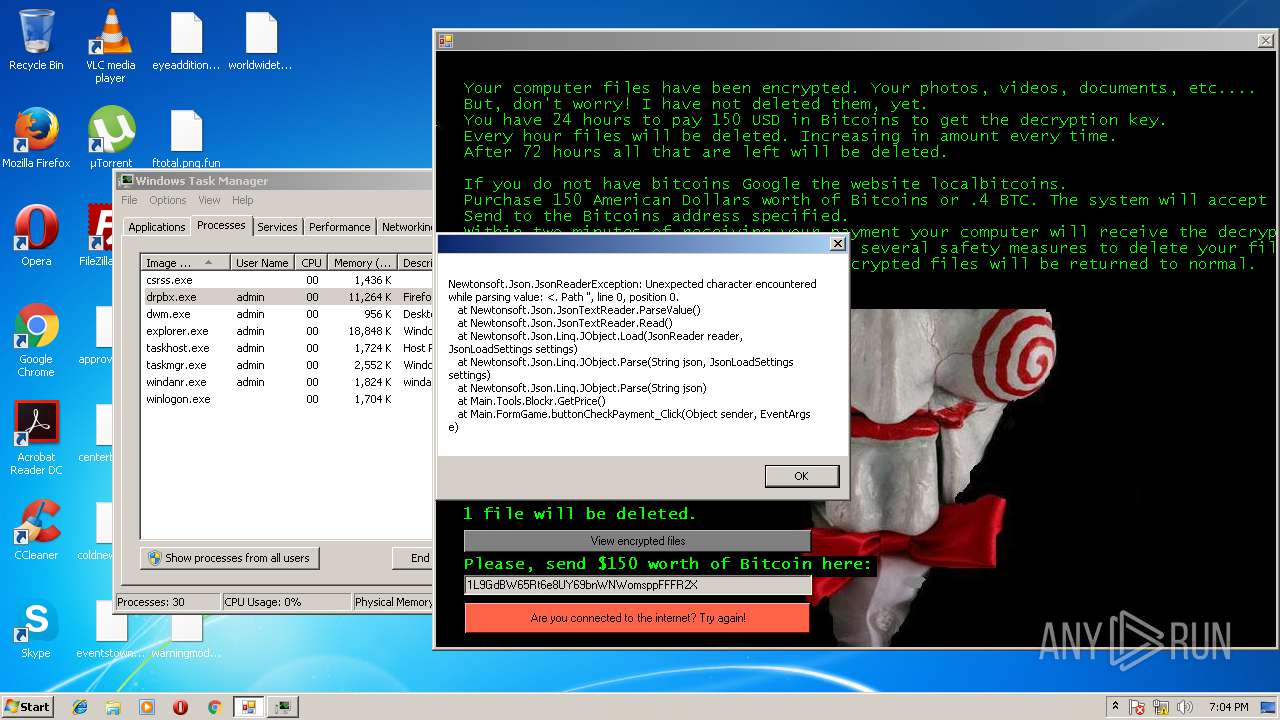
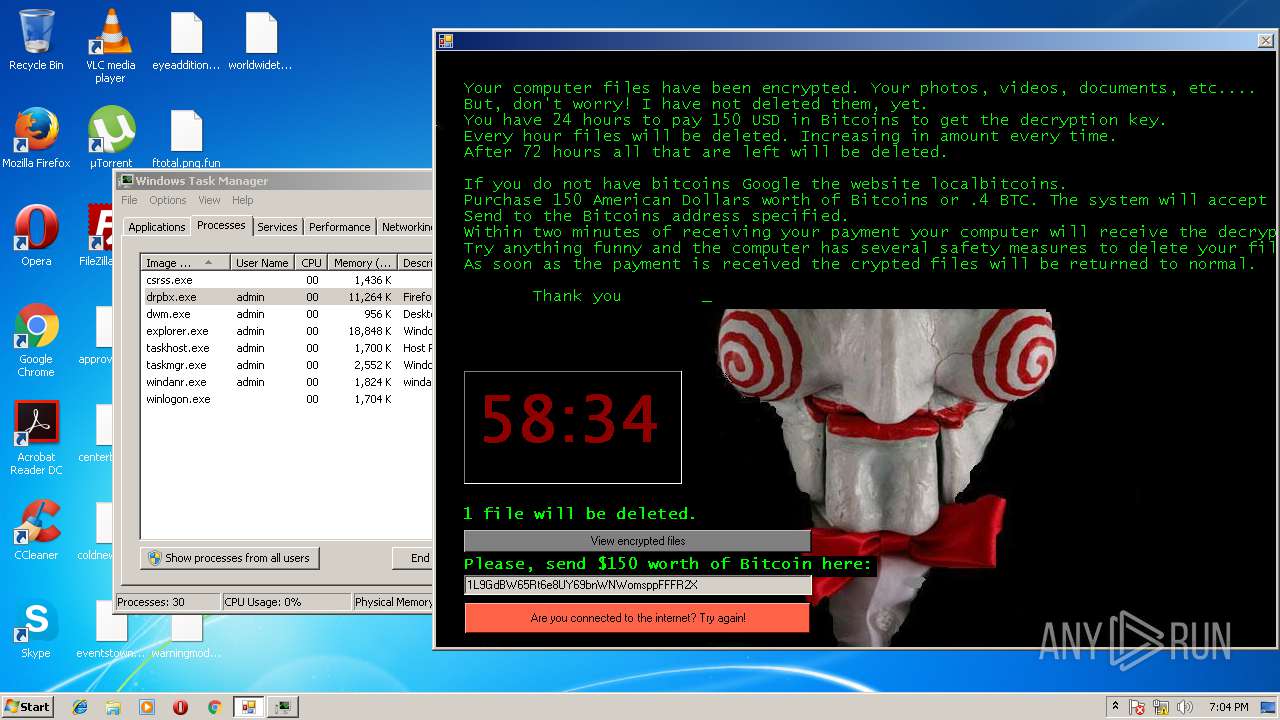
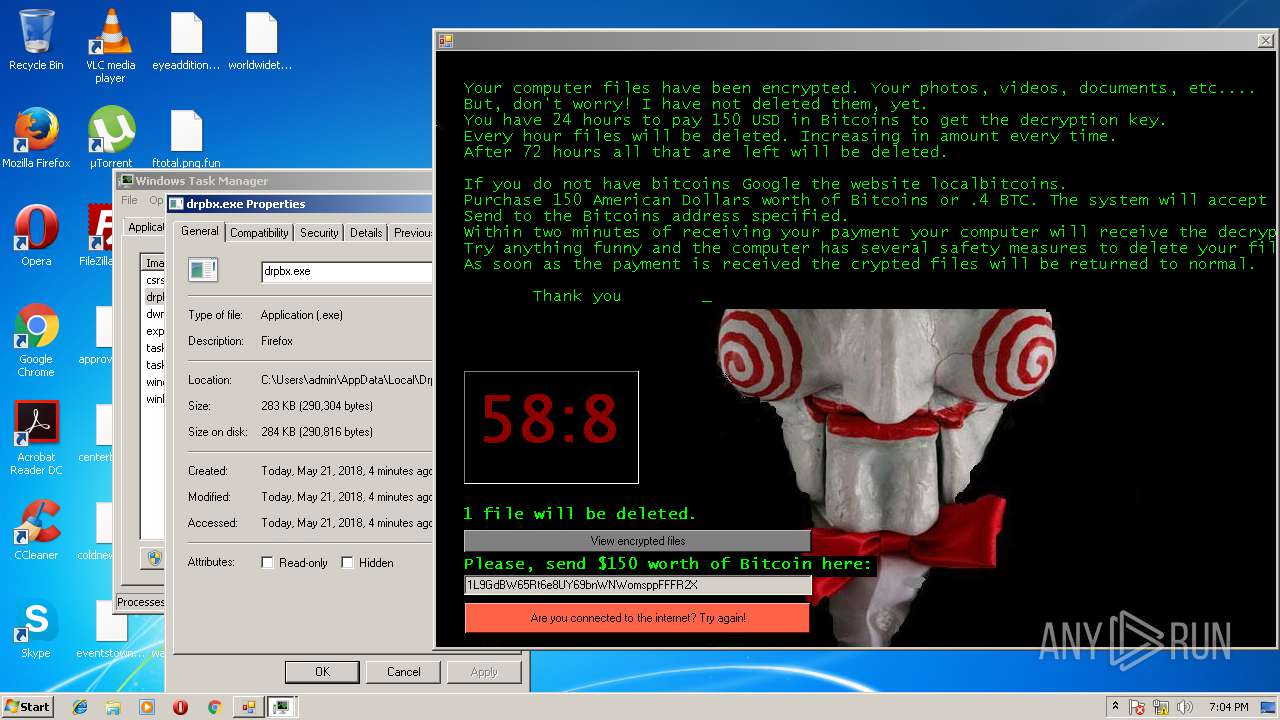
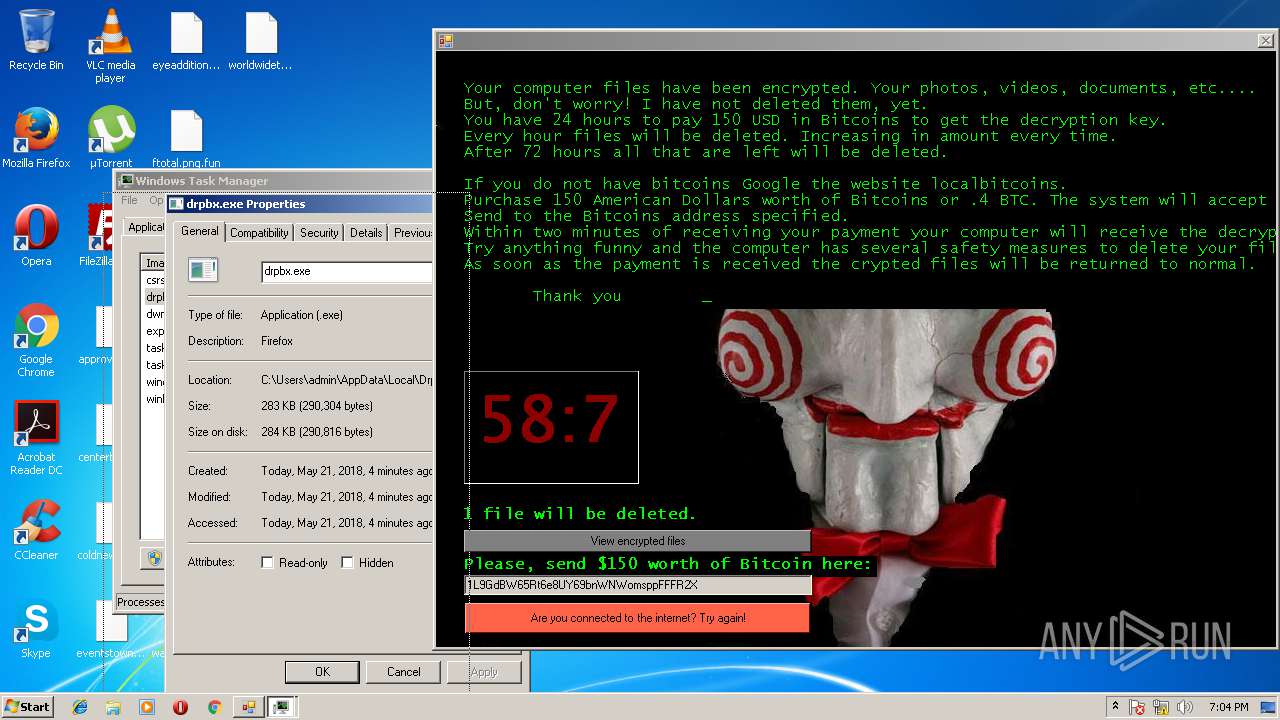
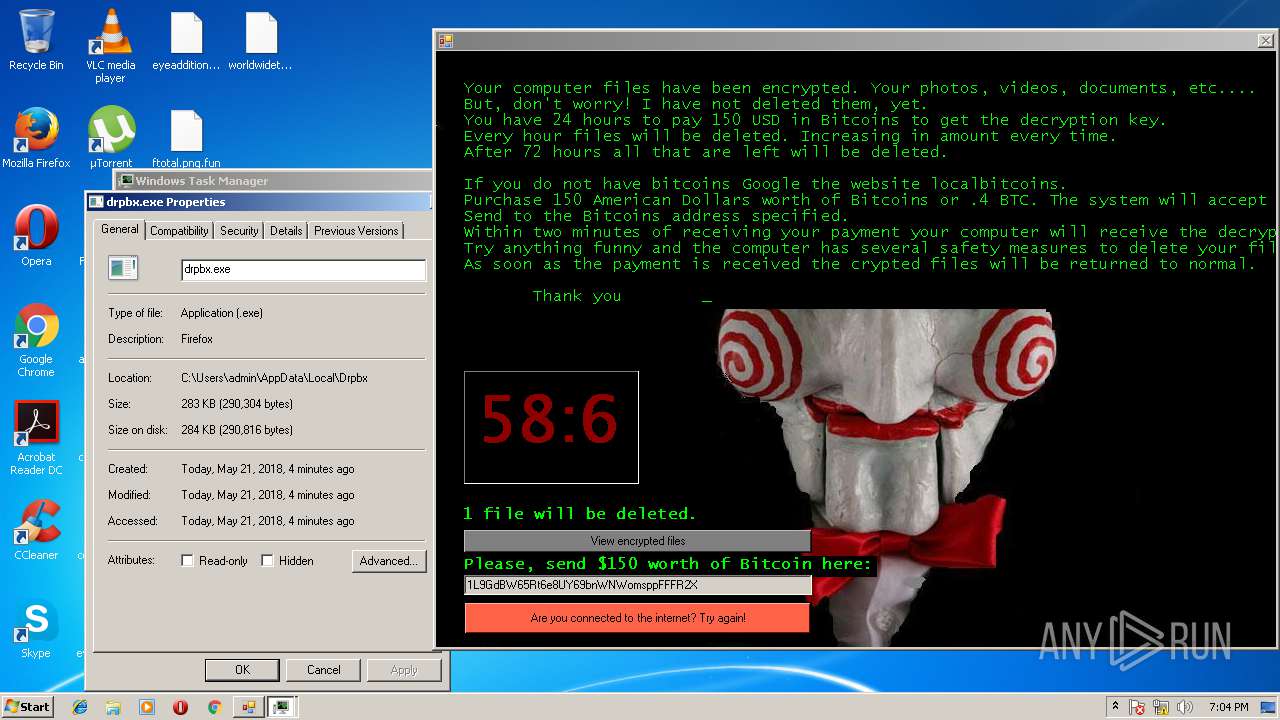
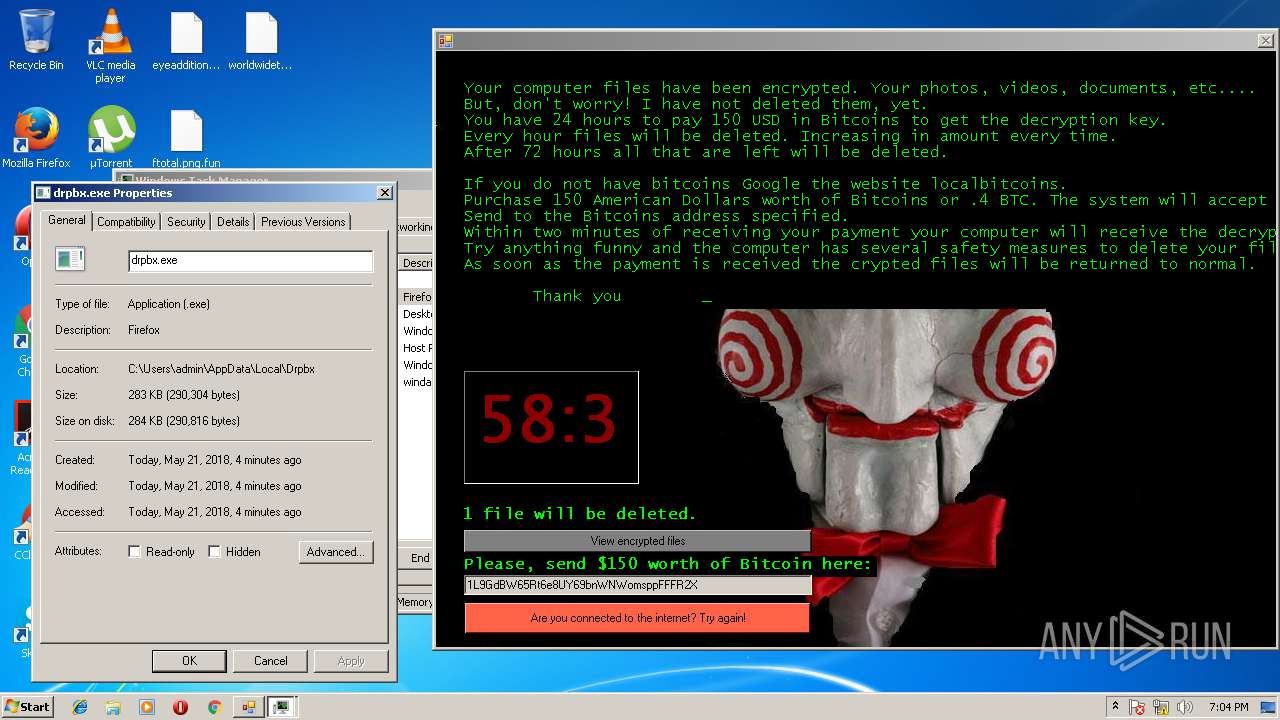
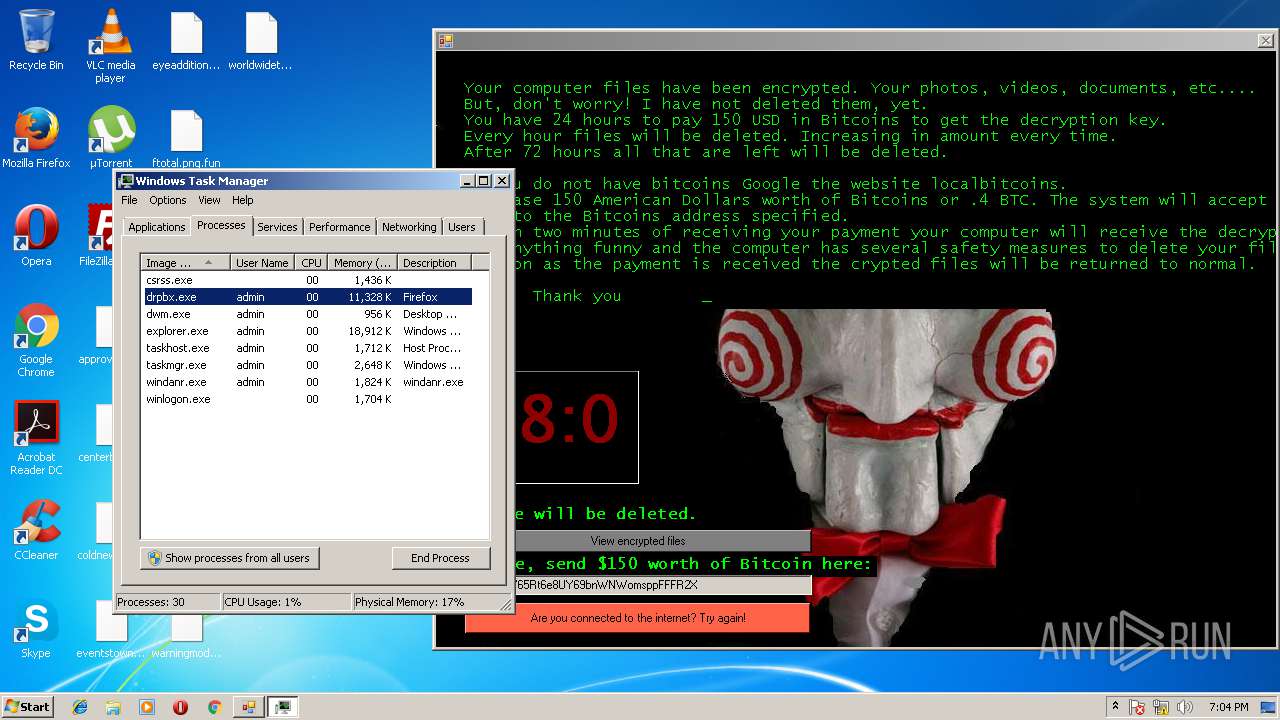
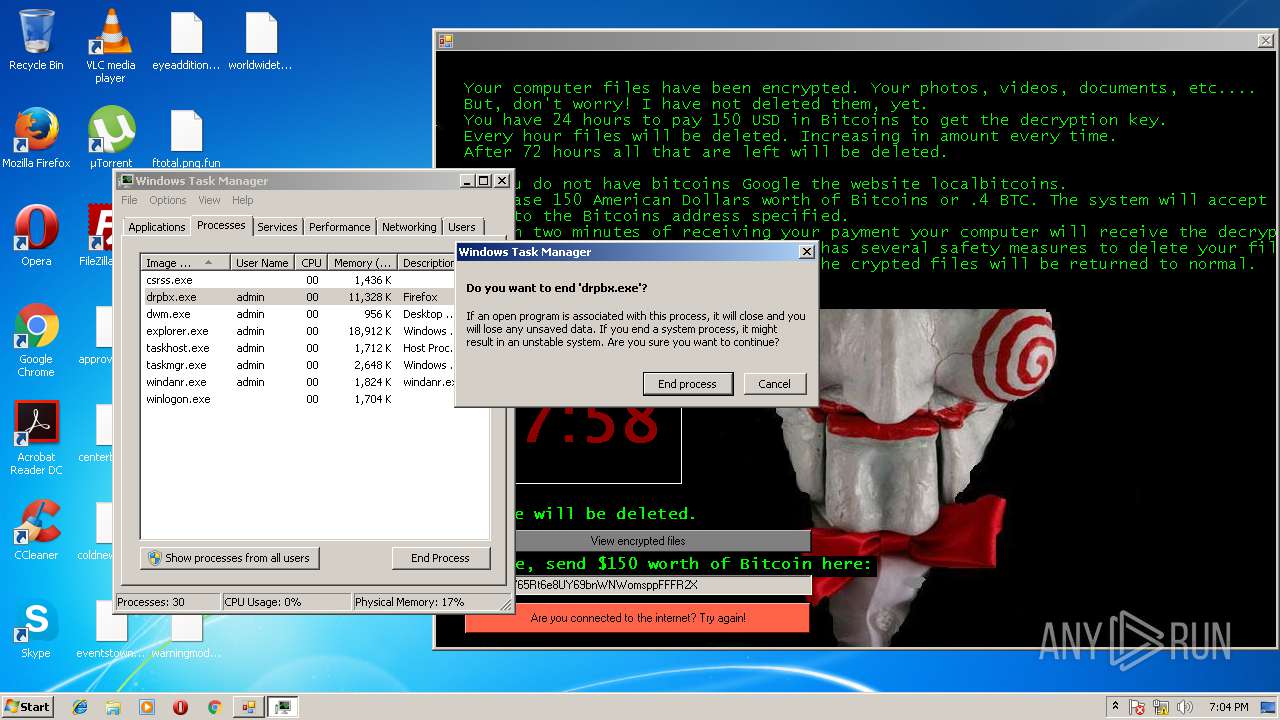
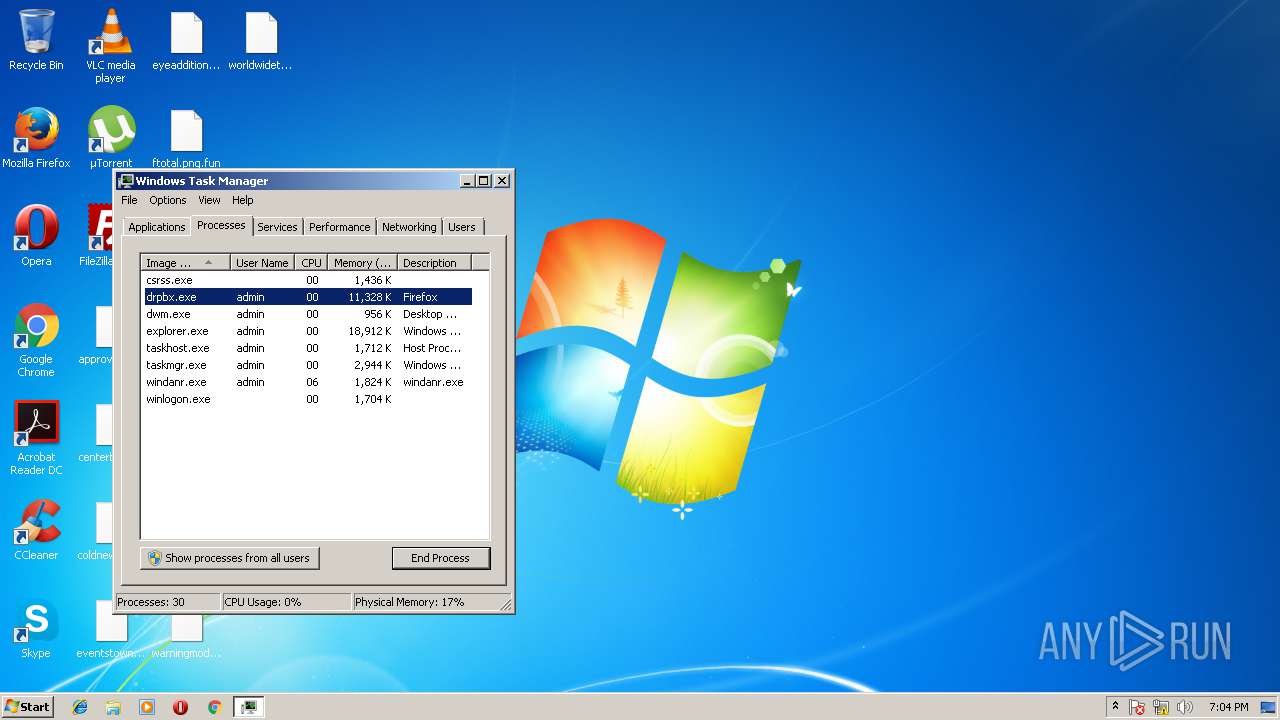
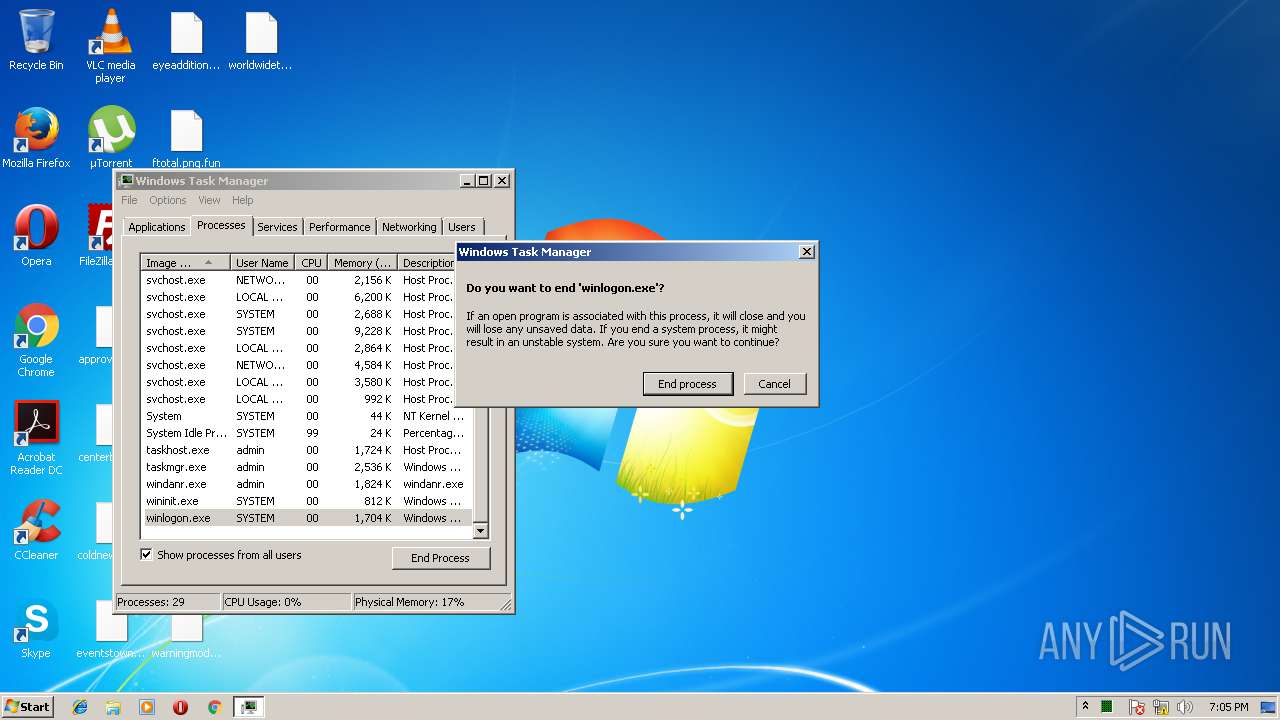
MALICIOUS
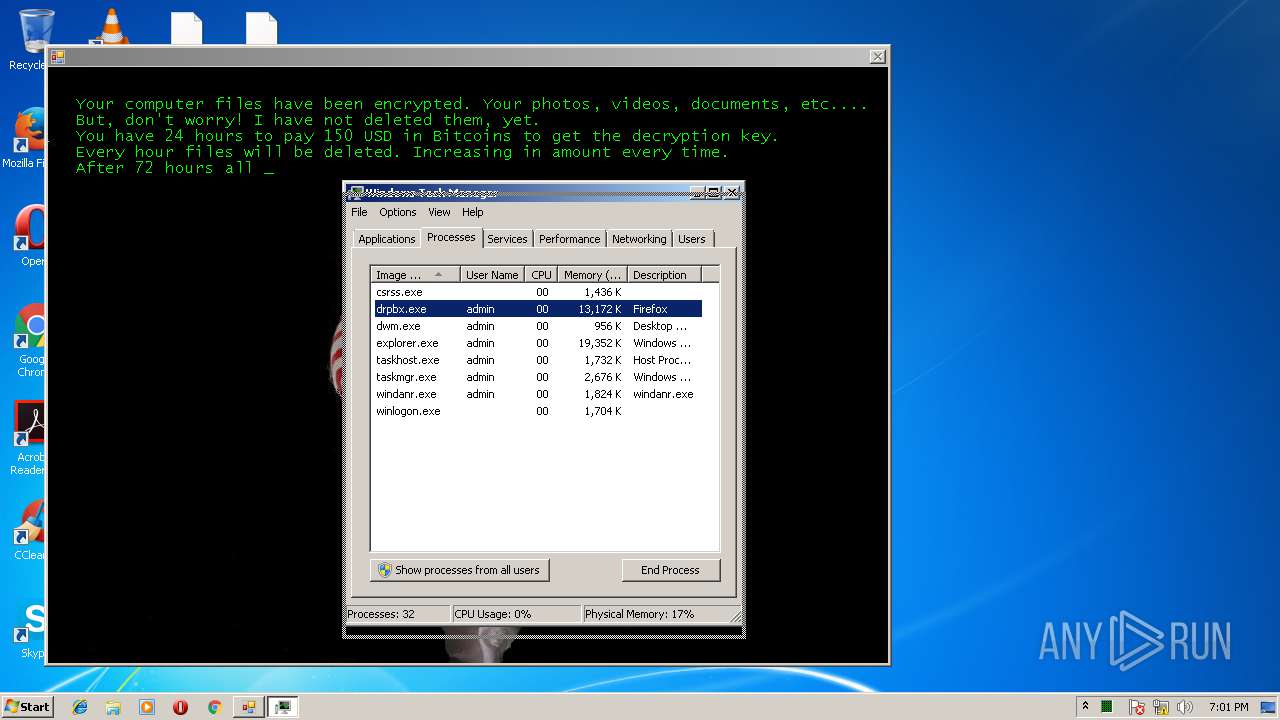
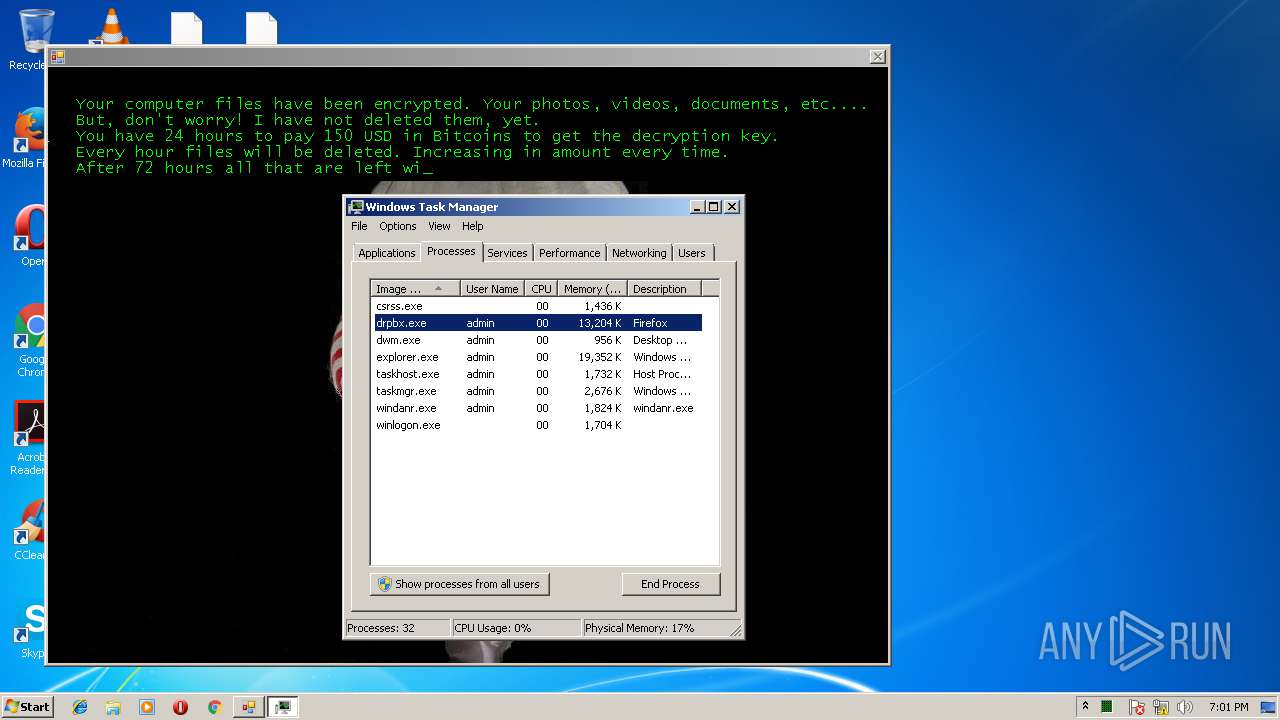
Changes the autorun value in the registry
- jigsaw.exe (PID: 3260)
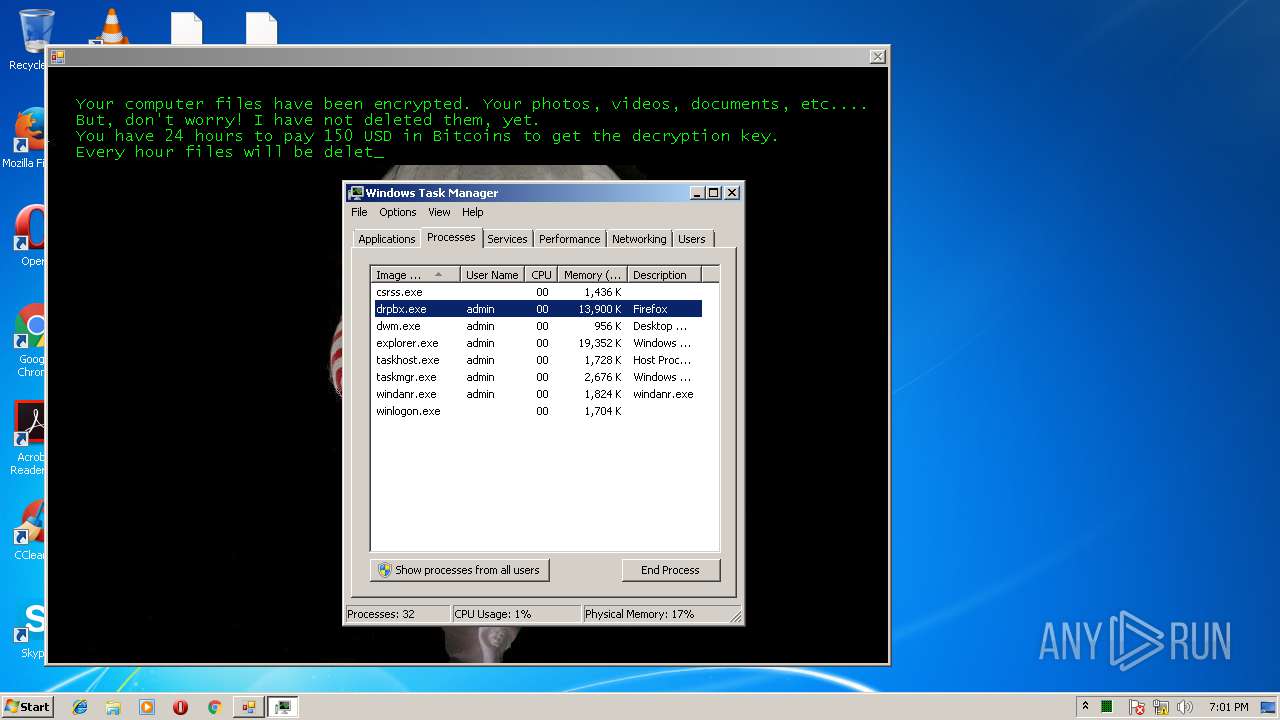
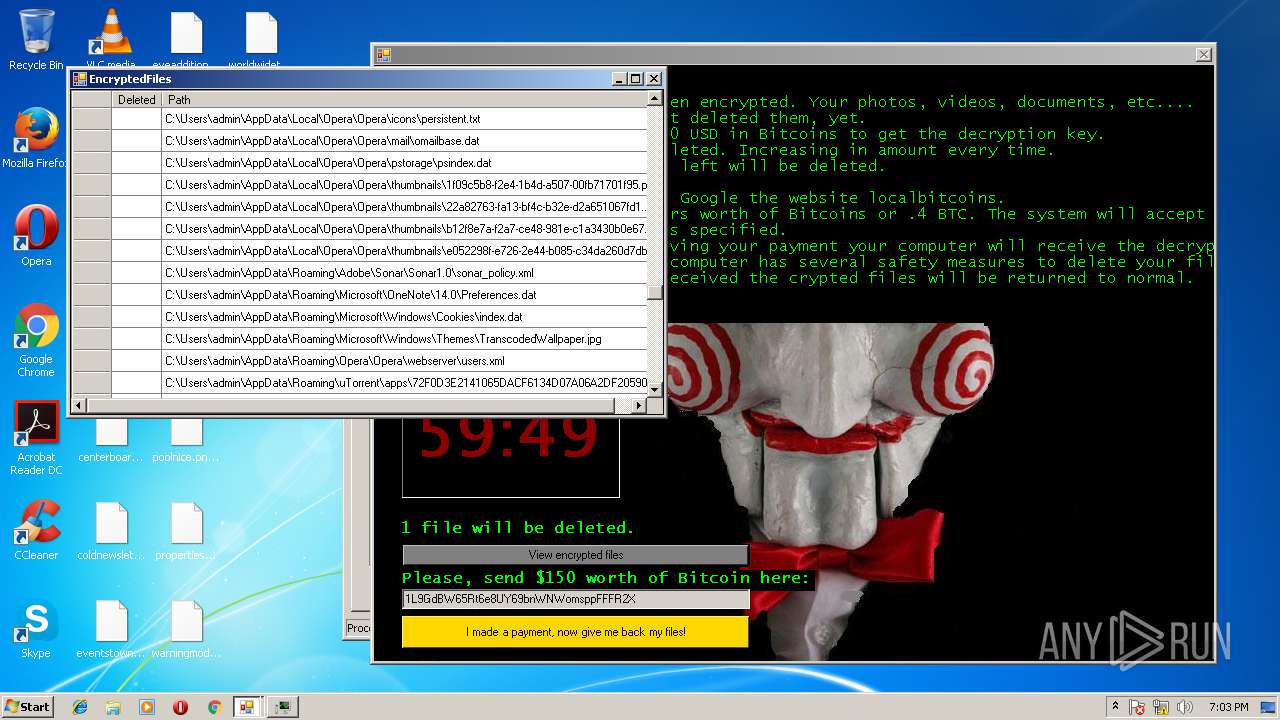
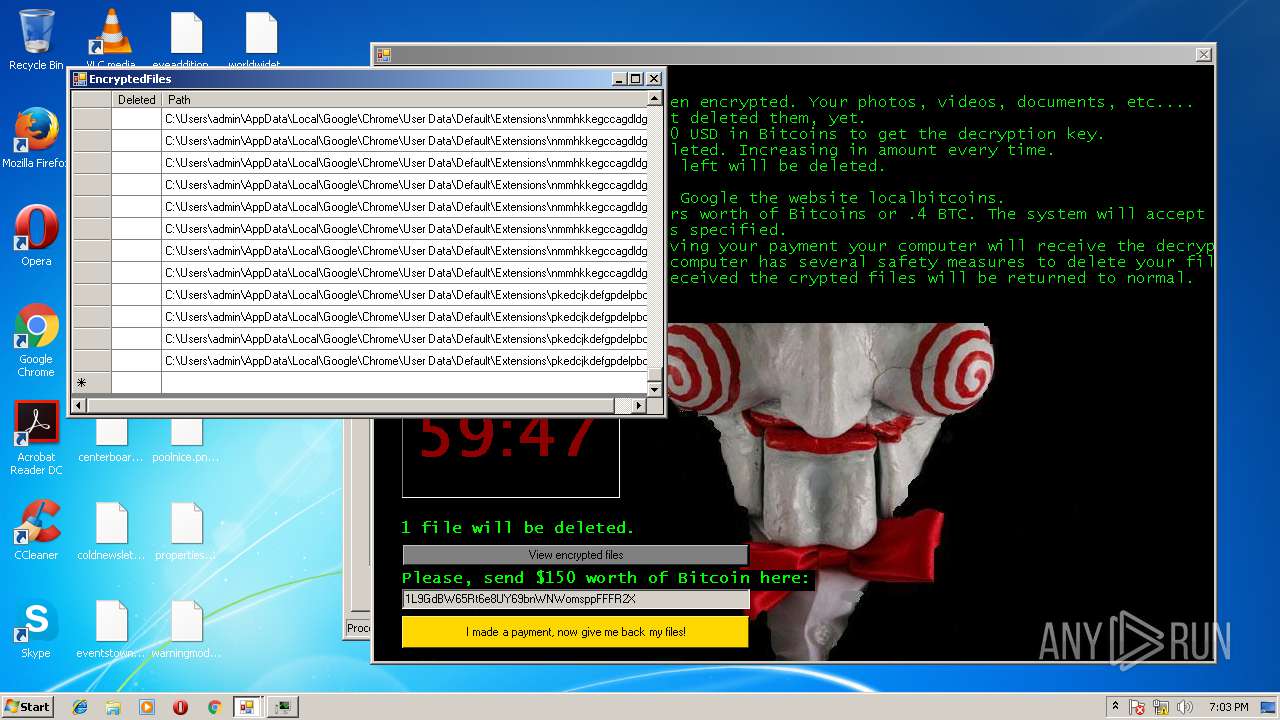
Modifies files in Chrome extension folder
- drpbx.exe (PID: 3116)
Loads the Task Scheduler COM API
- taskhost.exe (PID: 2396)
Actions looks like stealing of personal data
- drpbx.exe (PID: 3116)
SUSPICIOUS
Creates files in the user directory
- jigsaw.exe (PID: 3260)
- drpbx.exe (PID: 3116)
Executable content was dropped or overwritten
- jigsaw.exe (PID: 3260)
Creates files in the program directory
- drpbx.exe (PID: 3116)
- chrmstp.exe (PID: 3968)
Starts itself from another location
- jigsaw.exe (PID: 3260)
Application launched itself
- taskmgr.exe (PID: 2628)
Creates files in the Windows directory
- chrmstp.exe (PID: 1912)
INFO
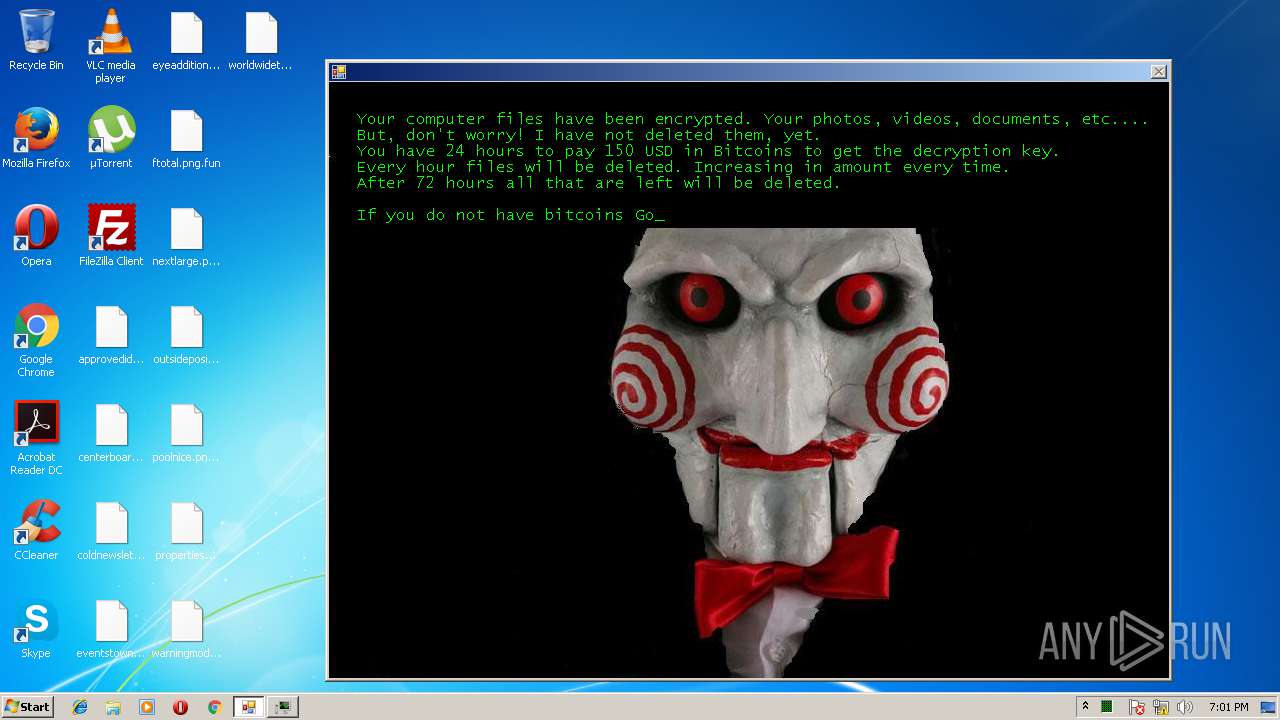
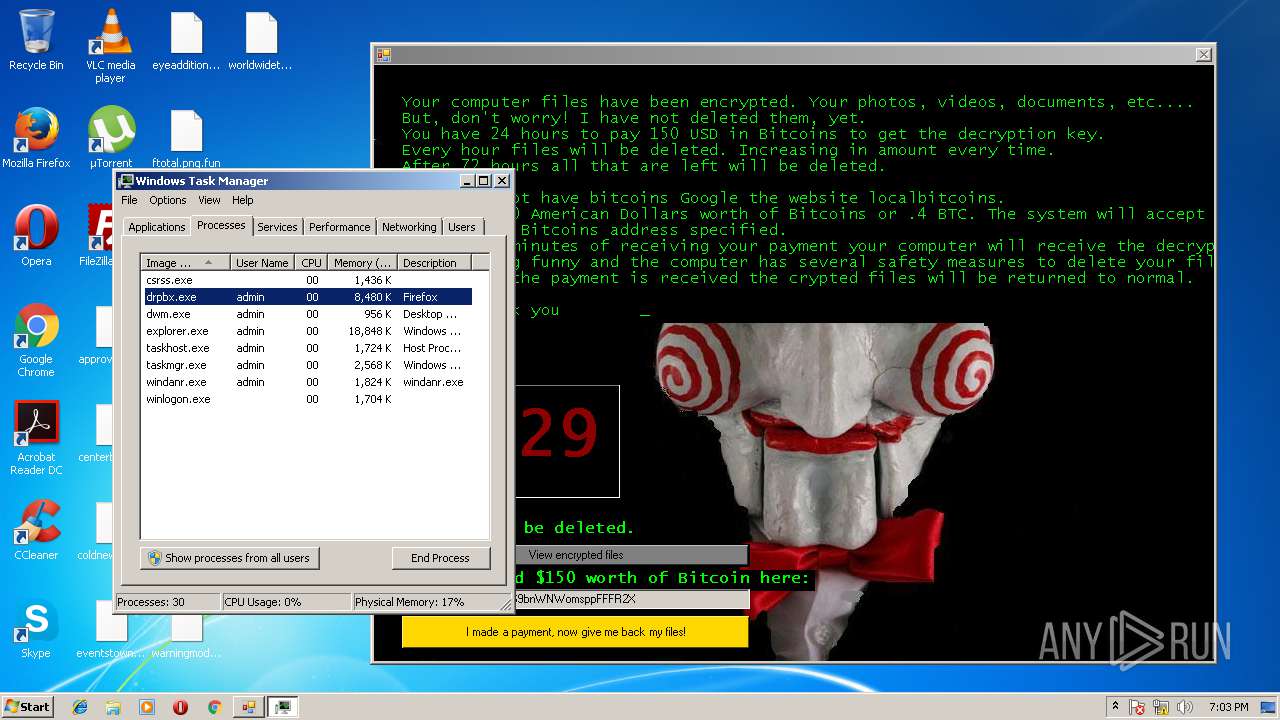
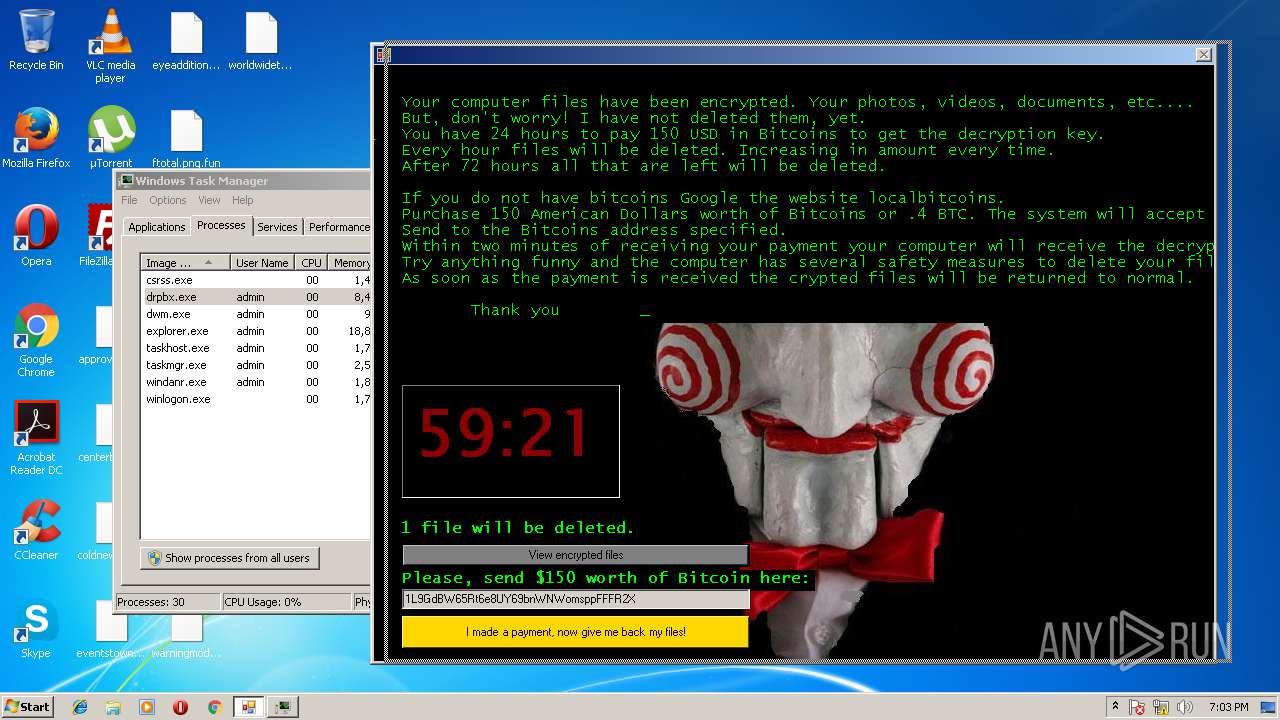
Dropped object may contain Bitcoin addresses
- drpbx.exe (PID: 3116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:03:31 08:28:14+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 72704 |
| InitializedDataSize: | 216576 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4e00a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 37.0.2.5583 |
| ProductVersionNumber: | 37.0.2.5583 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Firefox |
| FileVersion: | 37.0.2.5583 |
| InternalName: | BitcoinBlackmailer.exe |
| LegalCopyright: | Copyright 1999-2012 Firefox and Mozzilla developers. All rights reserved. |
| LegalTrademarks: | - |
| OriginalFileName: | BitcoinBlackmailer.exe |
| ProductName: | Firefox |
| ProductVersion: | 37.0.2.5583 |
| AssemblyVersion: | 37.0.2.5583 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Mar-2016 06:28:14 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Firefox |
| FileVersion: | 37.0.2.5583 |
| InternalName: | BitcoinBlackmailer.exe |
| LegalCopyright: | Copyright 1999-2012 Firefox and Mozzilla developers. All rights reserved. |
| LegalTrademarks: | - |
| OriginalFilename: | BitcoinBlackmailer.exe |
| ProductName: | Firefox |
| ProductVersion: | 37.0.2.5583 |
| Assembly Version: | 37.0.2.5583 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 31-Mar-2016 06:28:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
\x01\x1e!mmUPp`B\x03 | 0x00002000 | 0x00034260 | 0x00034400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99912 |
.text | 0x00038000 | 0x00011878 | 0x00011A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.39056 |
.rsrc | 0x0004A000 | 0x00000650 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.58099 |
.reloc | 0x0004C000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0980042 |
0x0004E000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0.13873 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
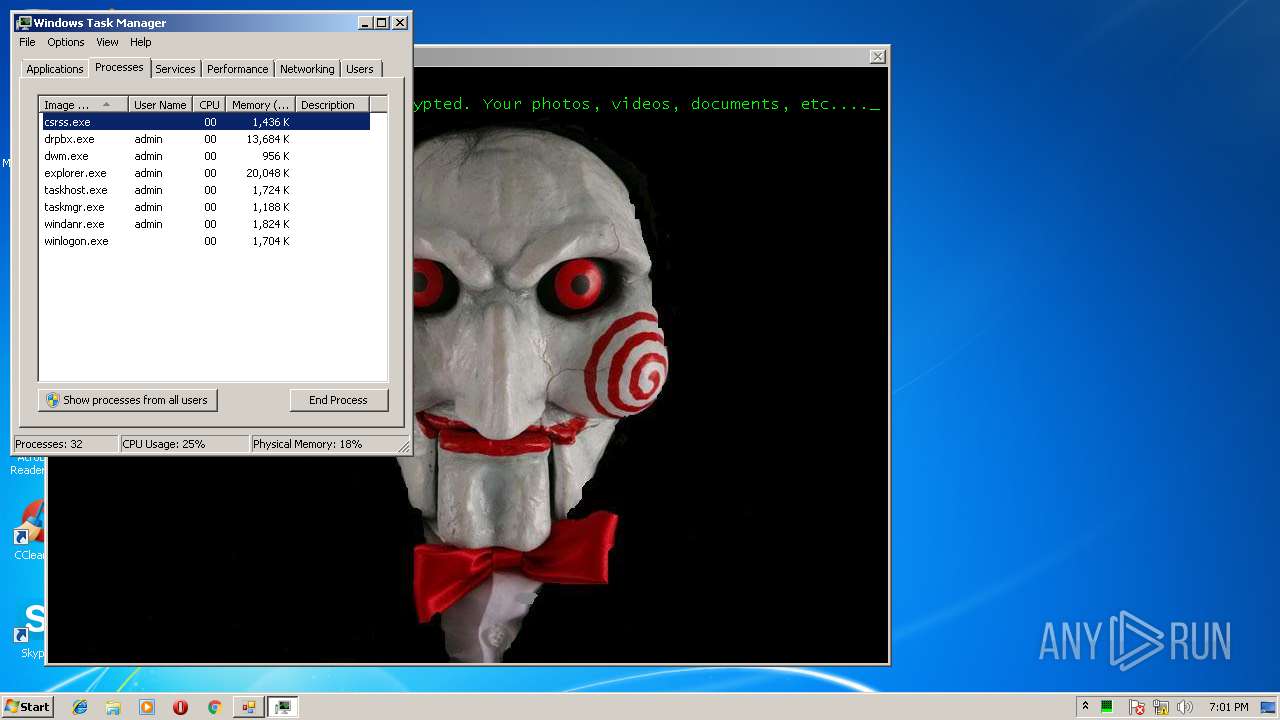
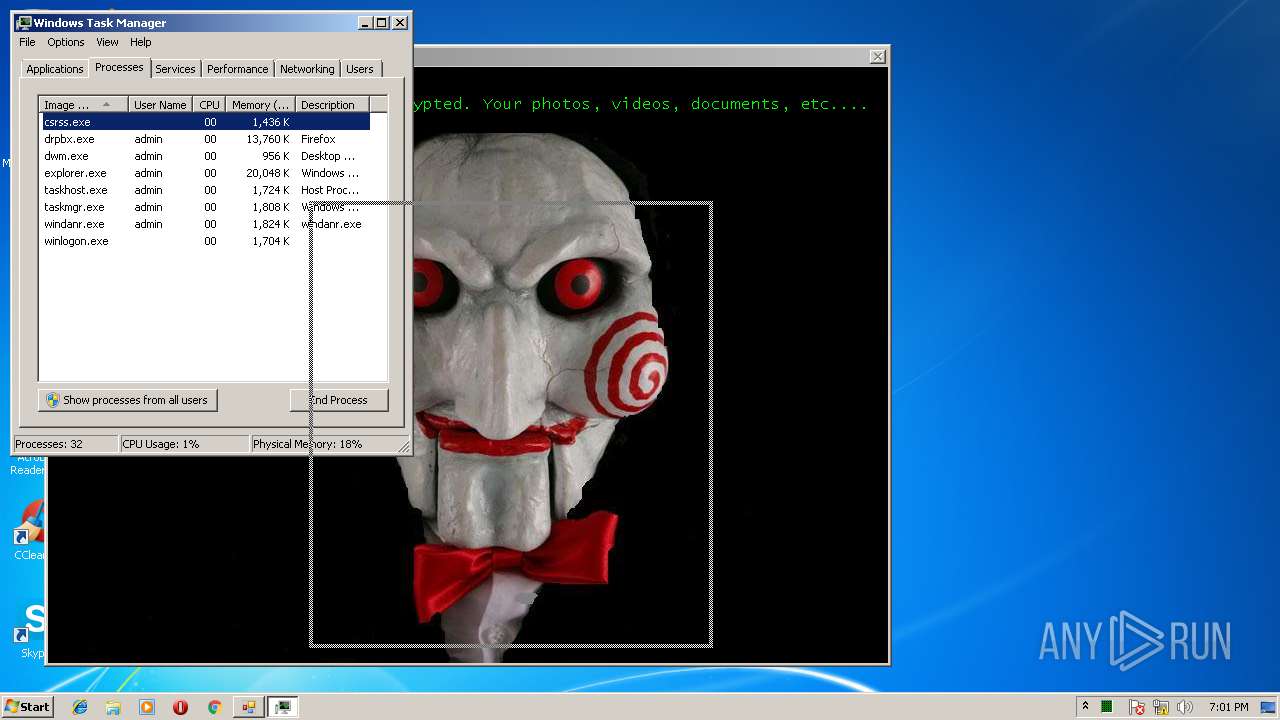
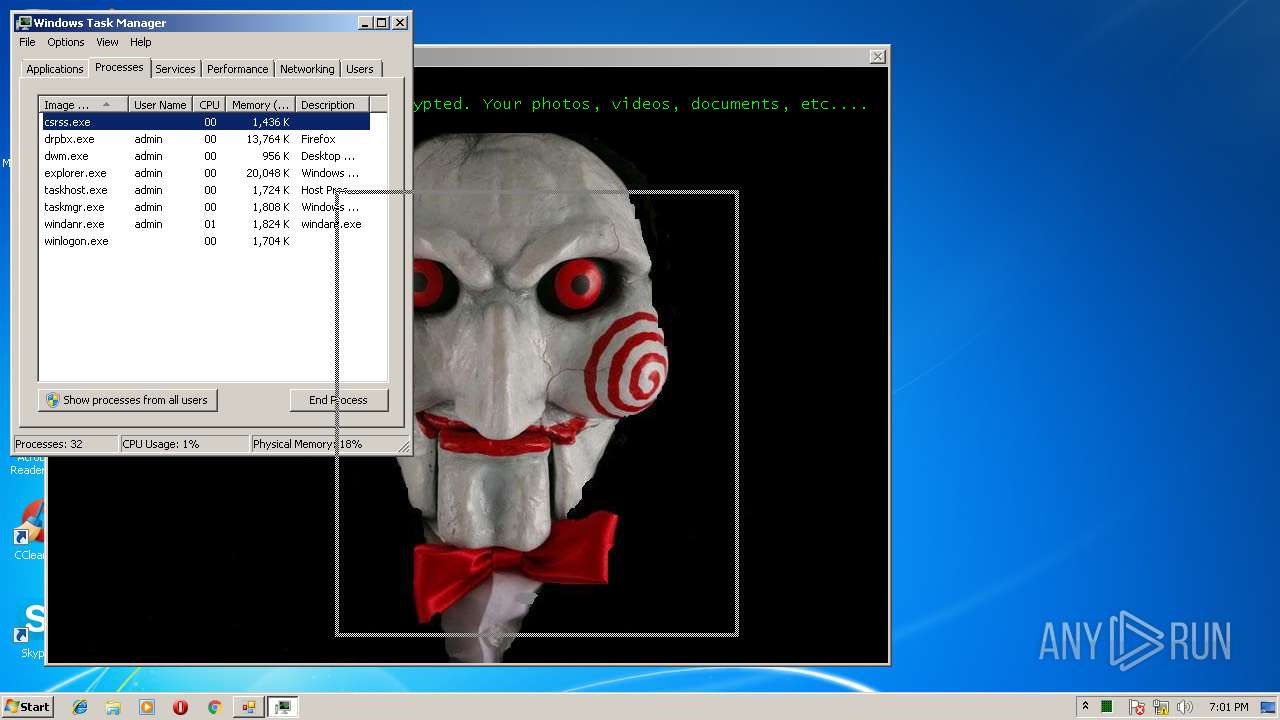
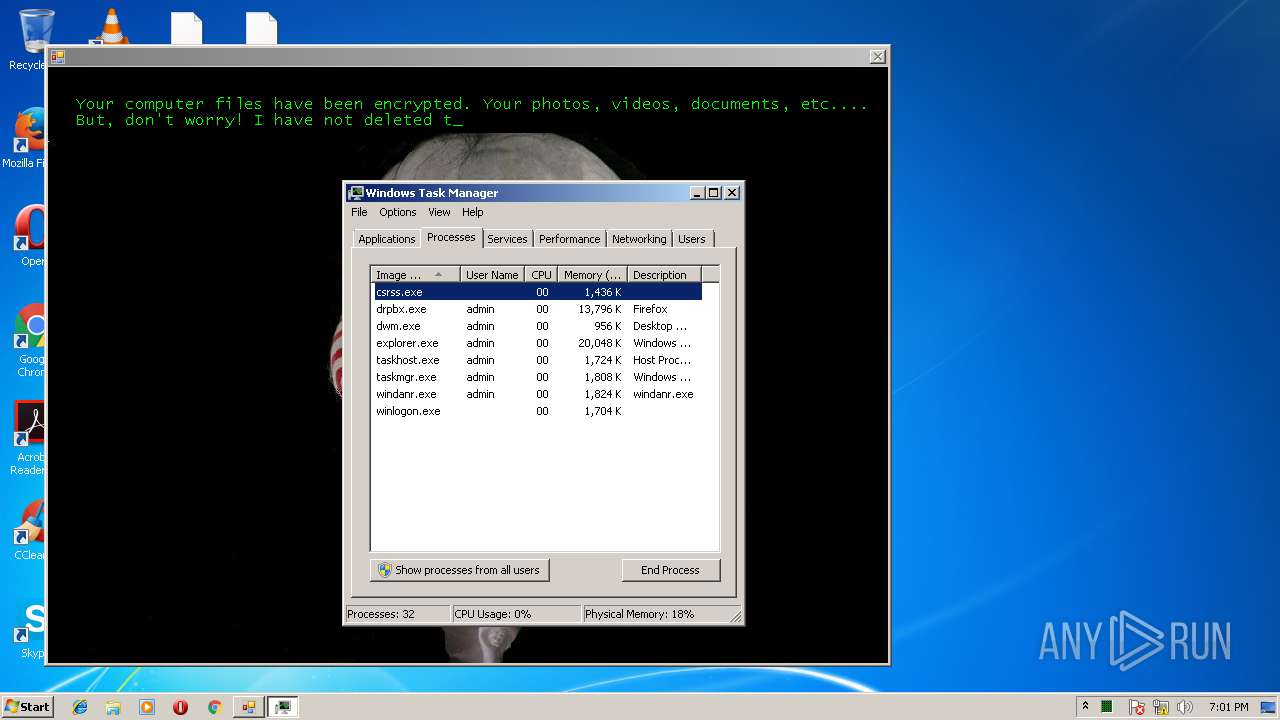
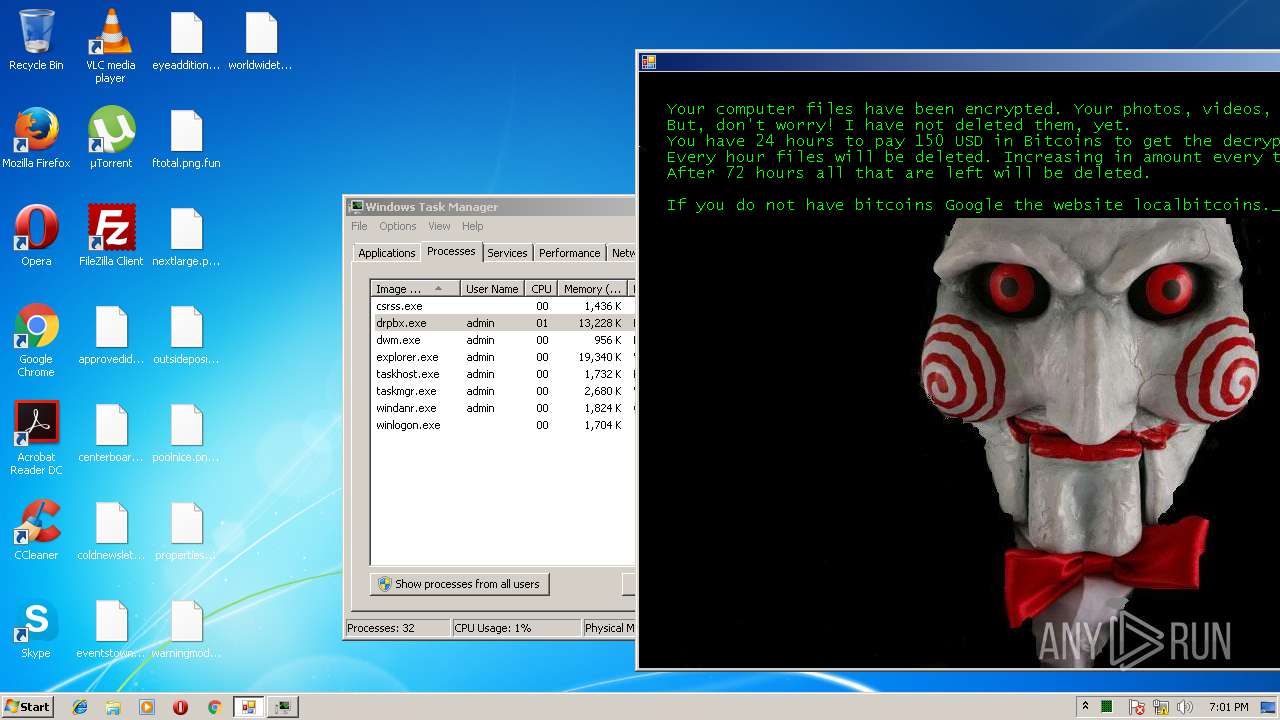
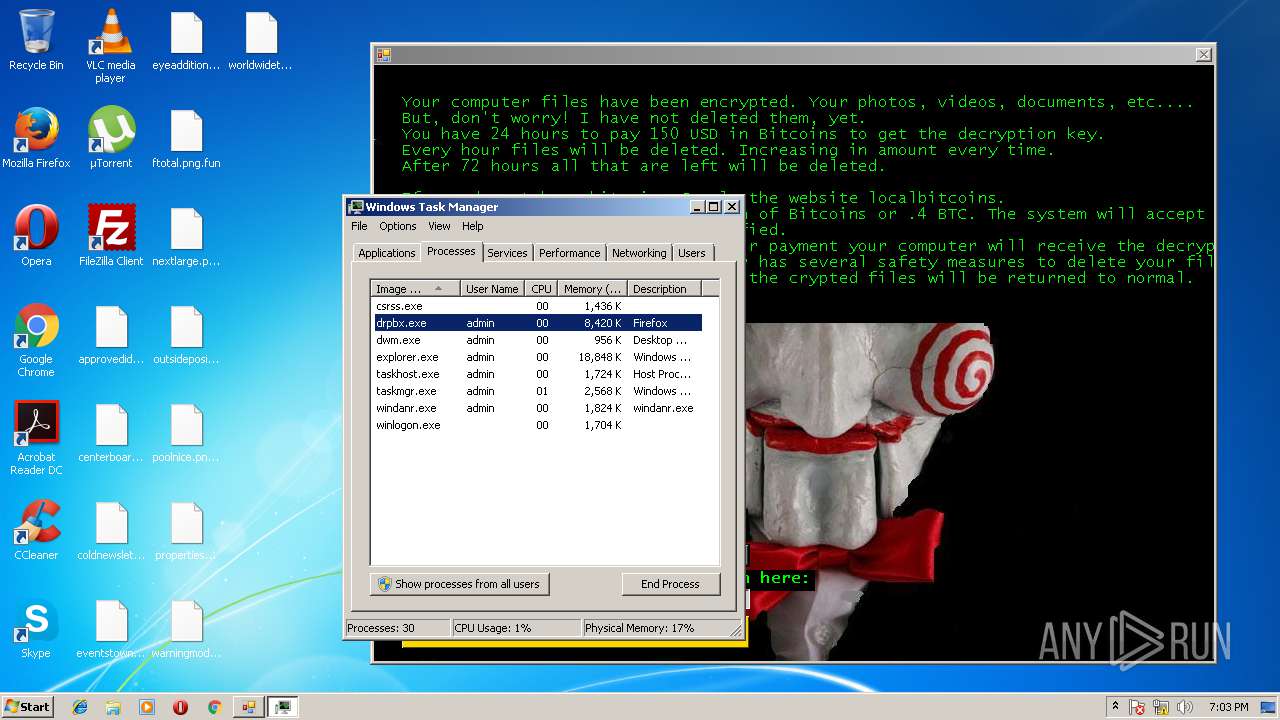
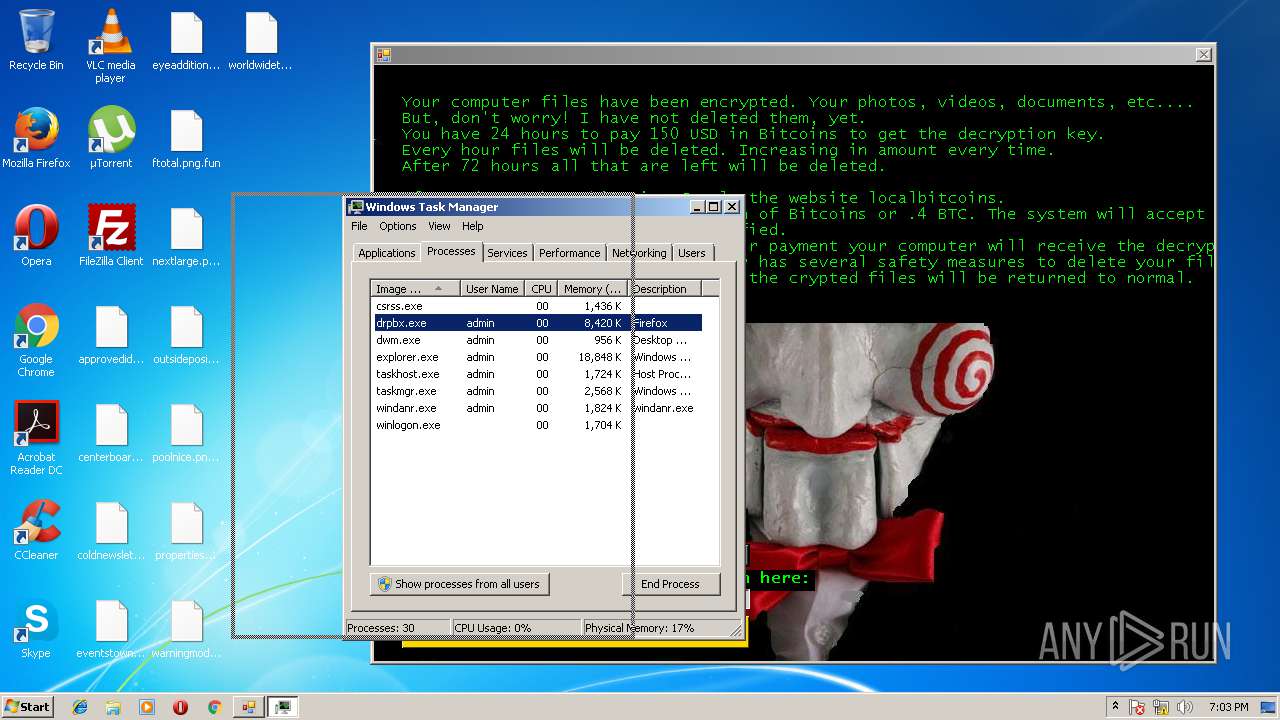
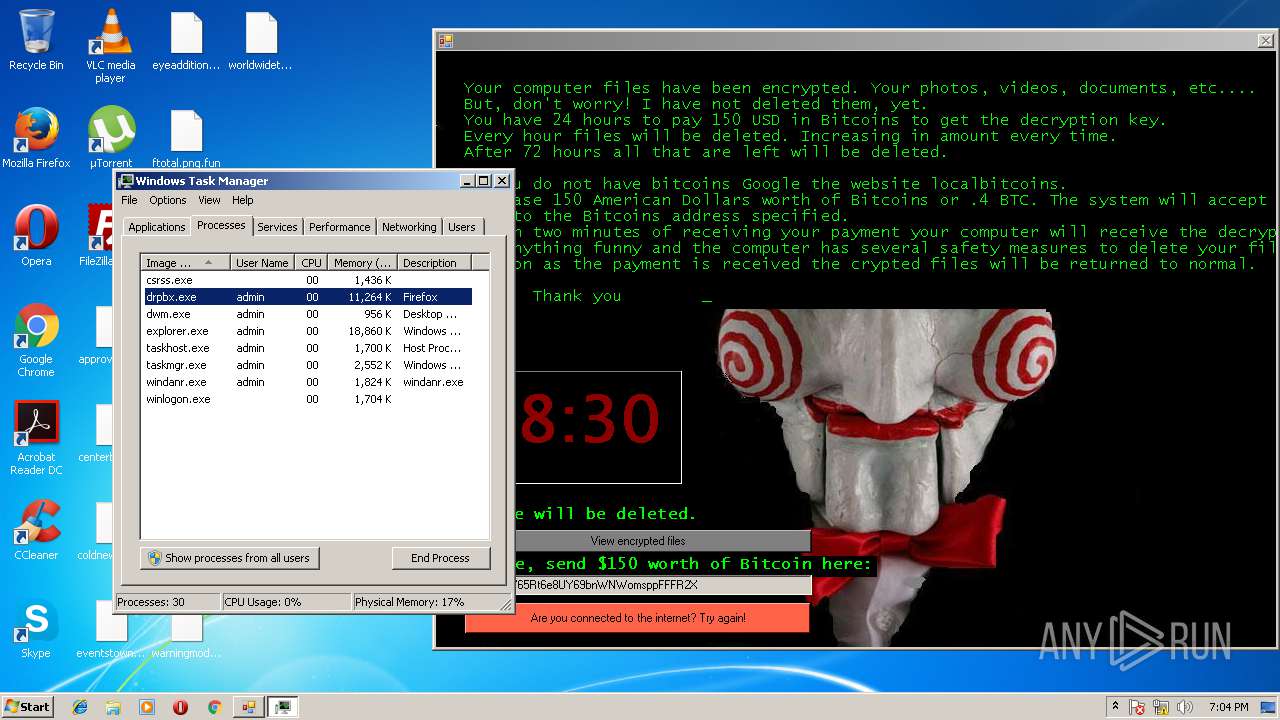
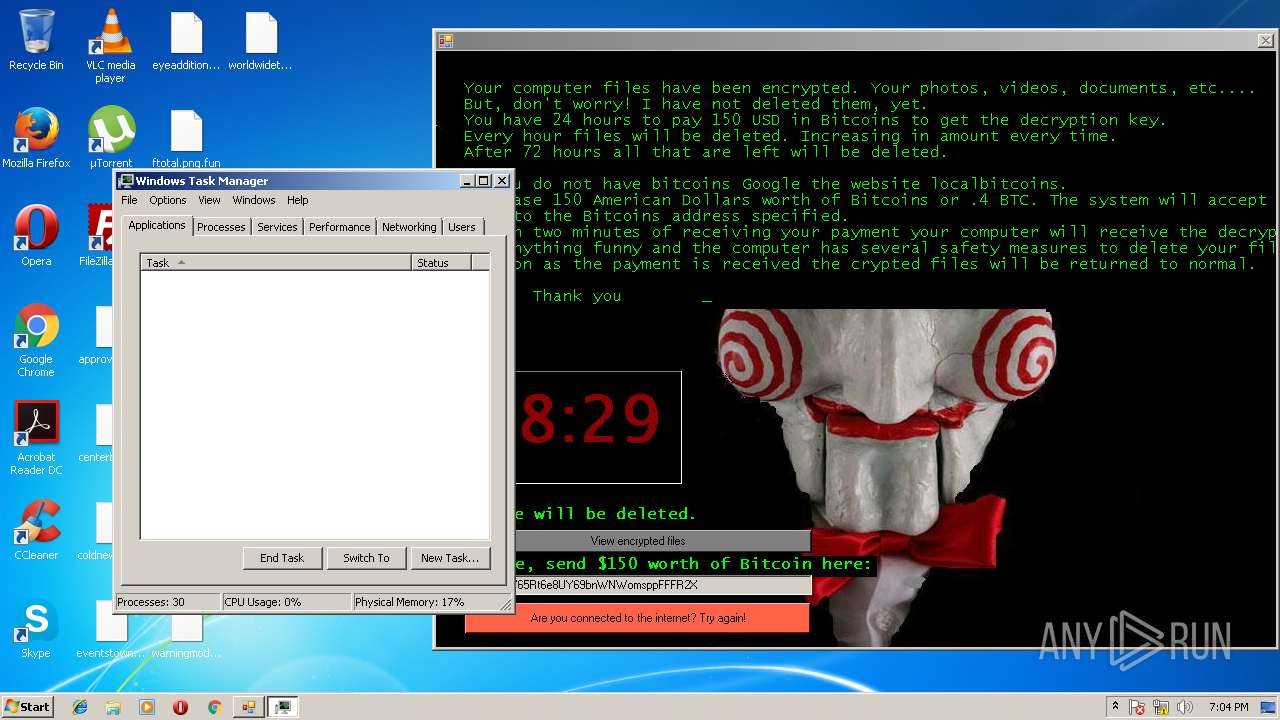
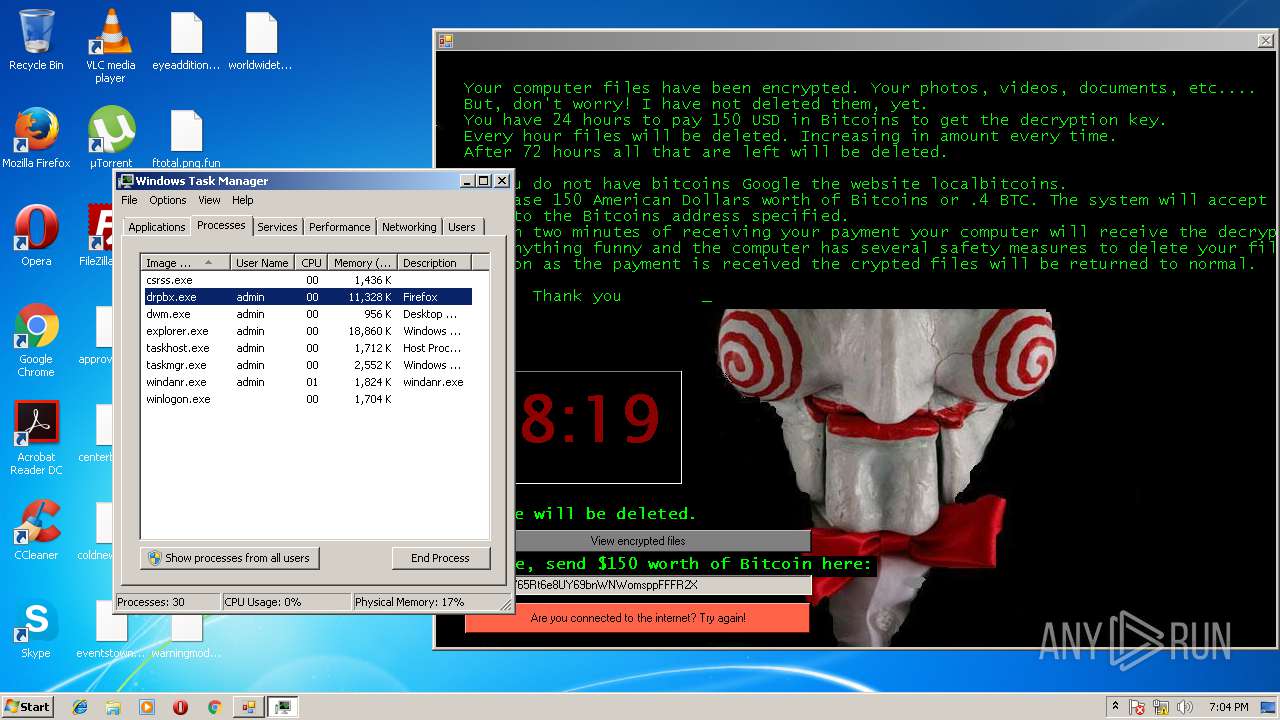
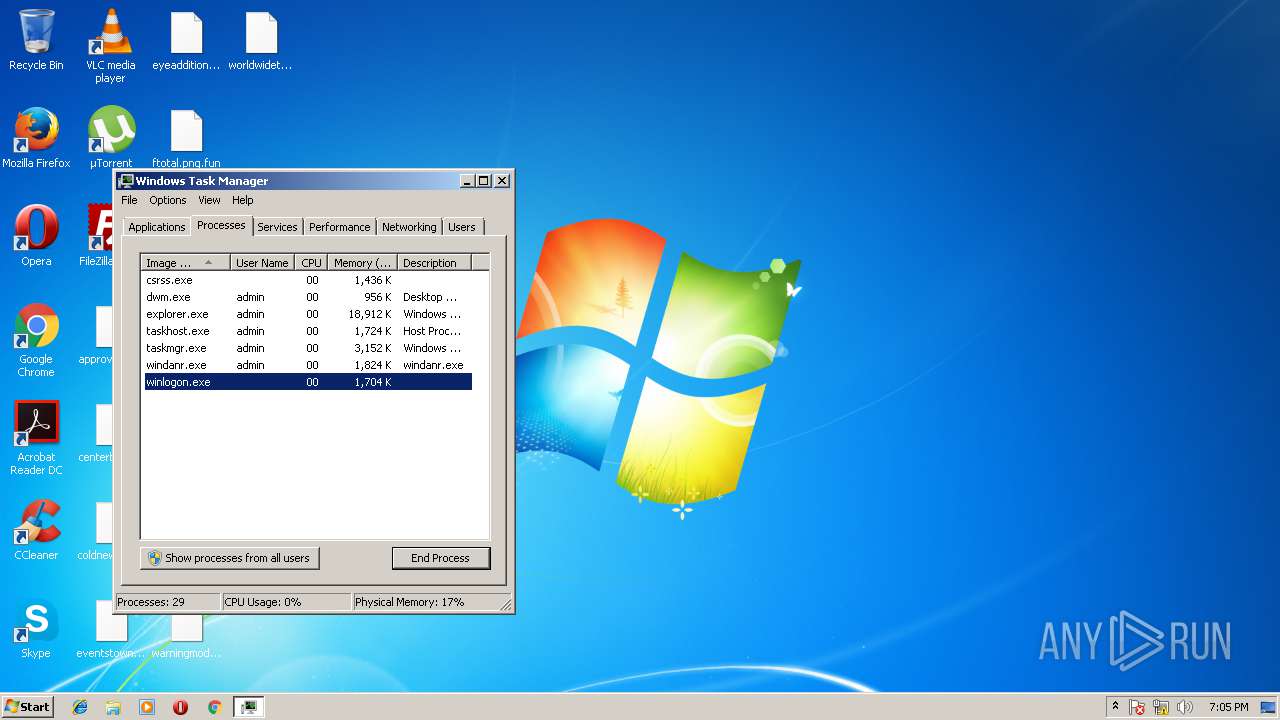
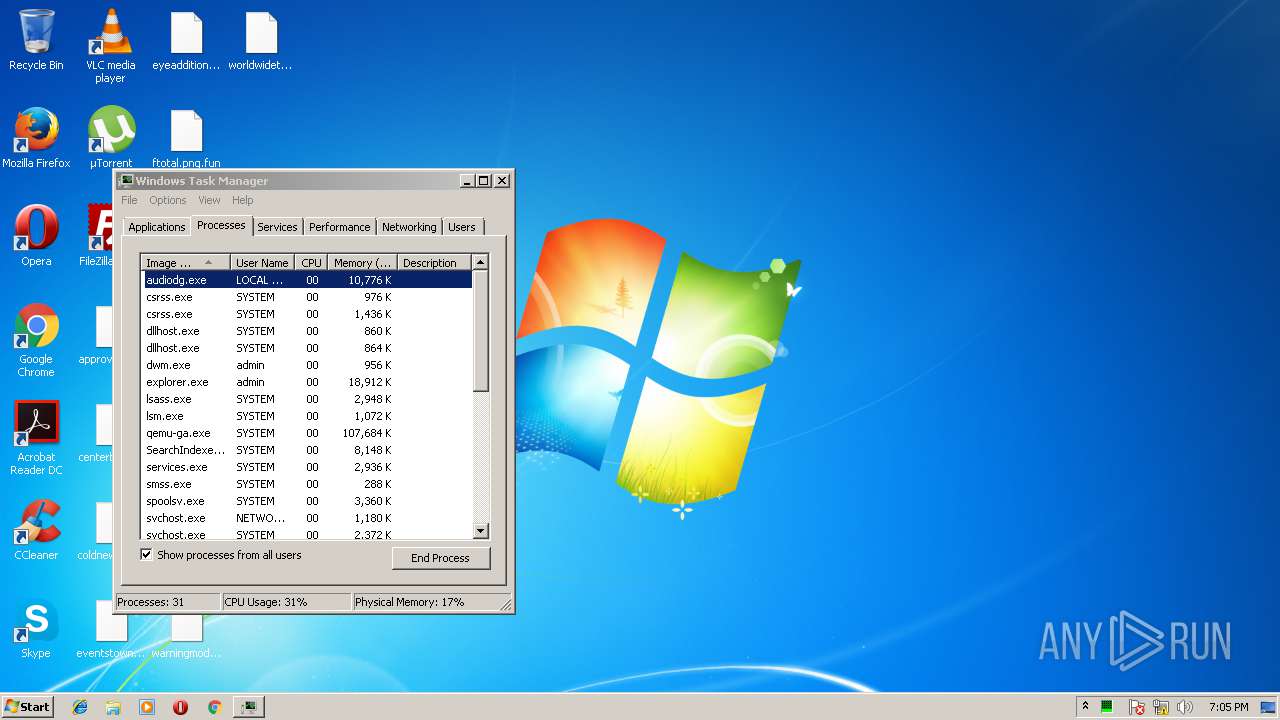
Total processes
59
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
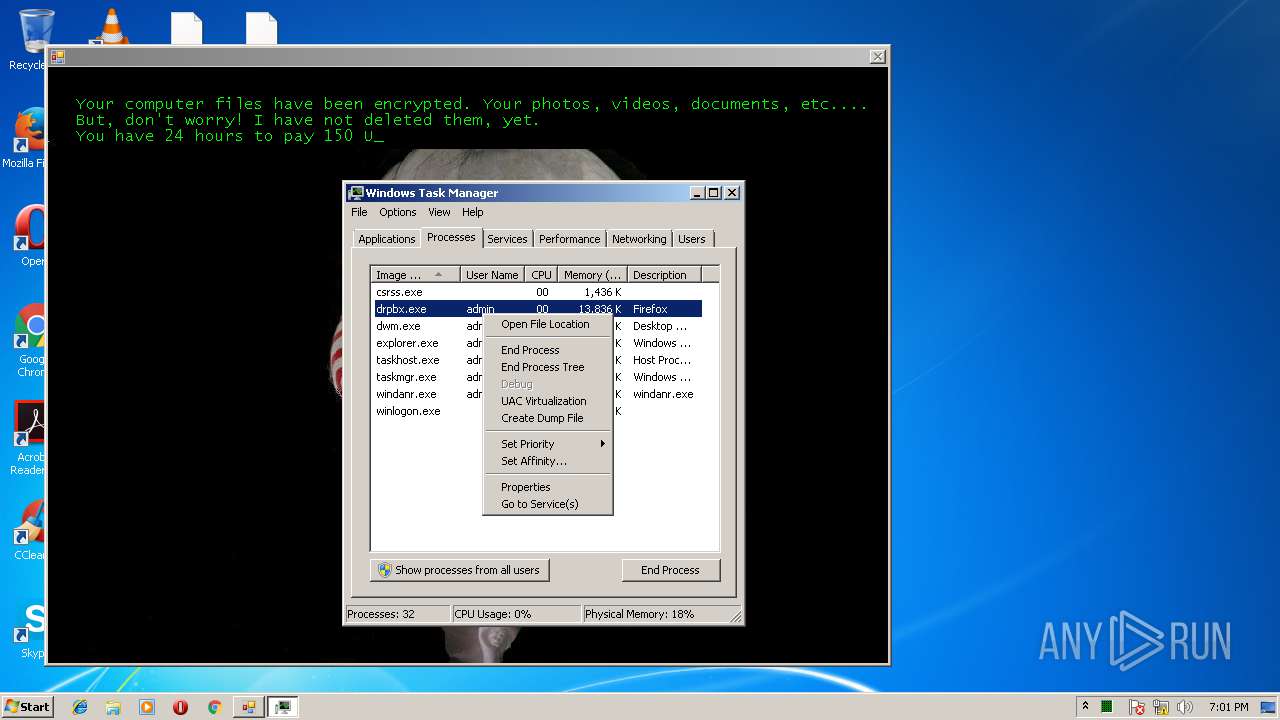
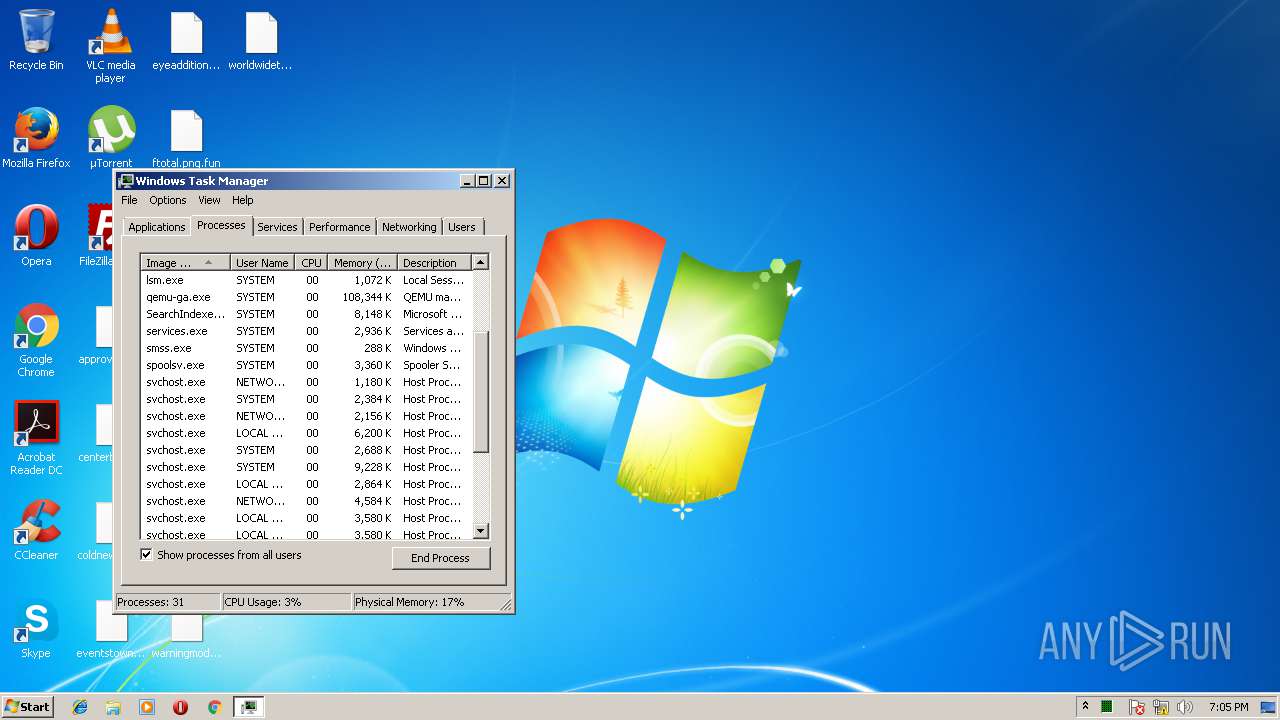
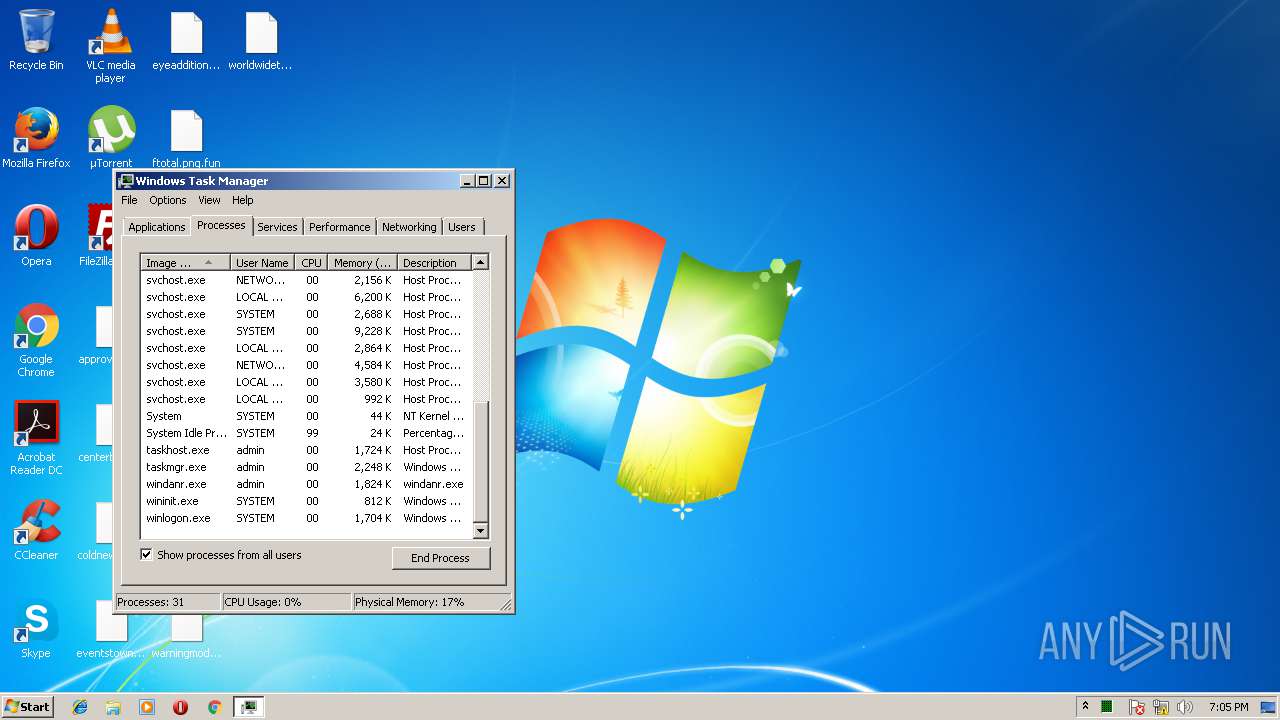
Process information
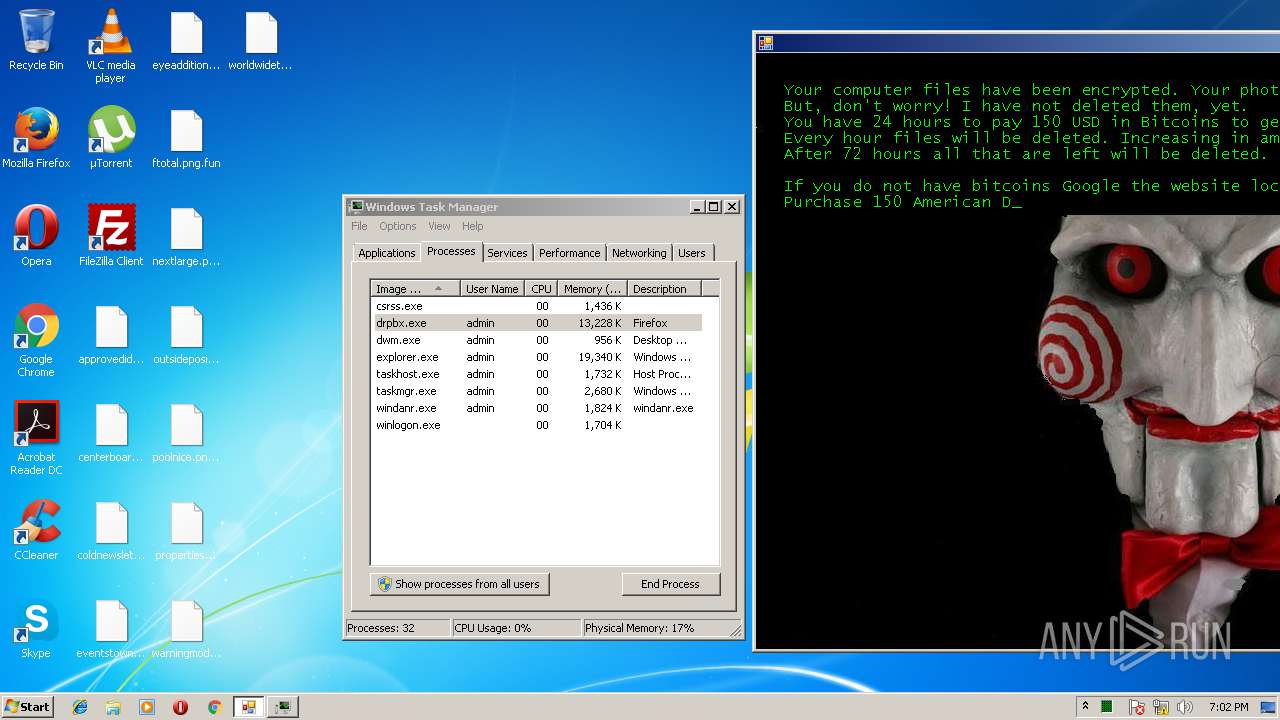
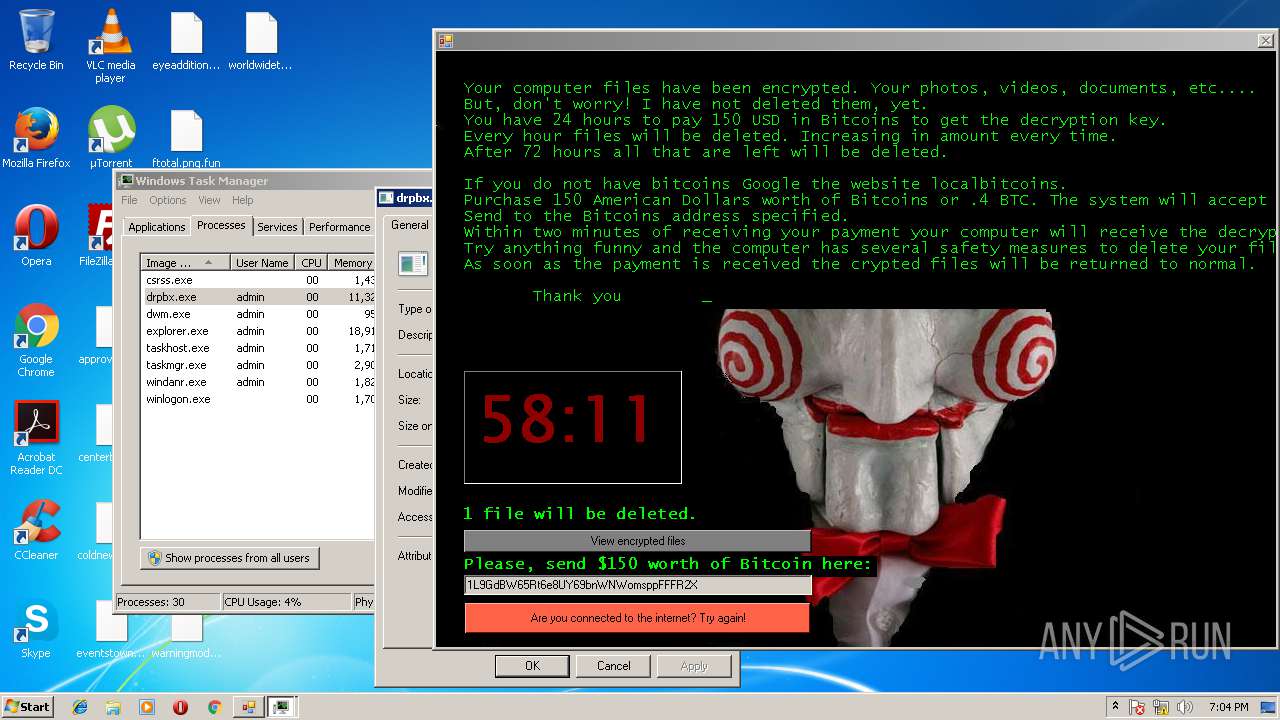
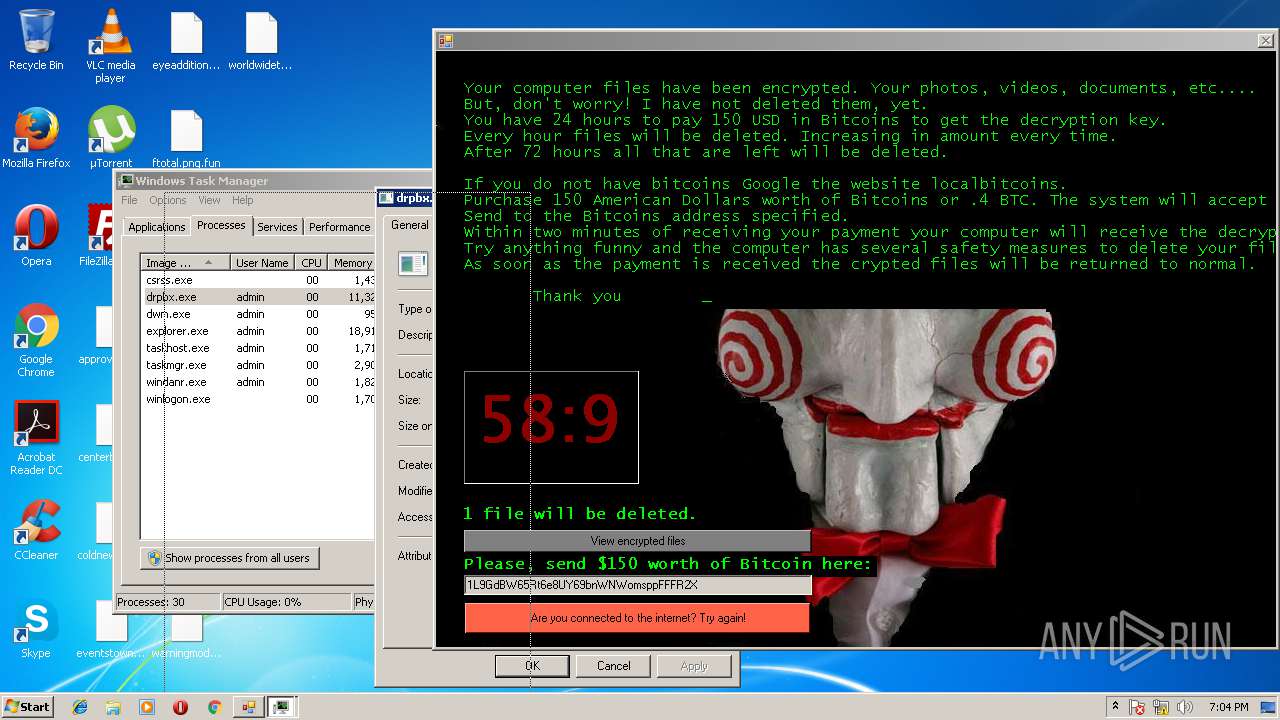
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1912 | "C:\Program Files\Google\Chrome\Application\61.0.3163.100\Installer\chrmstp.exe" --type=crashpad-handler /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Windows\TEMP\Crashpad --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=61.0.3163.100 --initial-client-data=0xc0,0xc4,0xc8,0xb8,0xcc,0xedfde8,0xedfdd8,0xedfdc0 | C:\Program Files\Google\Chrome\Application\61.0.3163.100\Installer\chrmstp.exe | — | chrmstp.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Chrome Installer Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
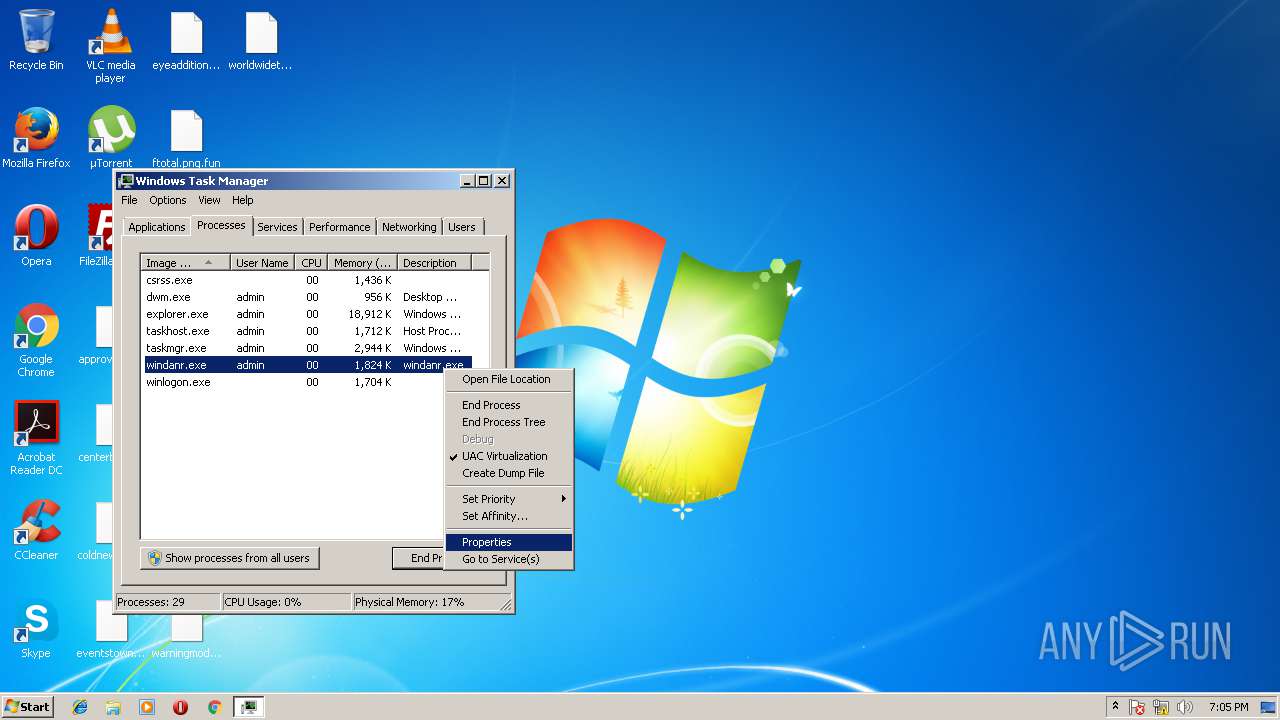
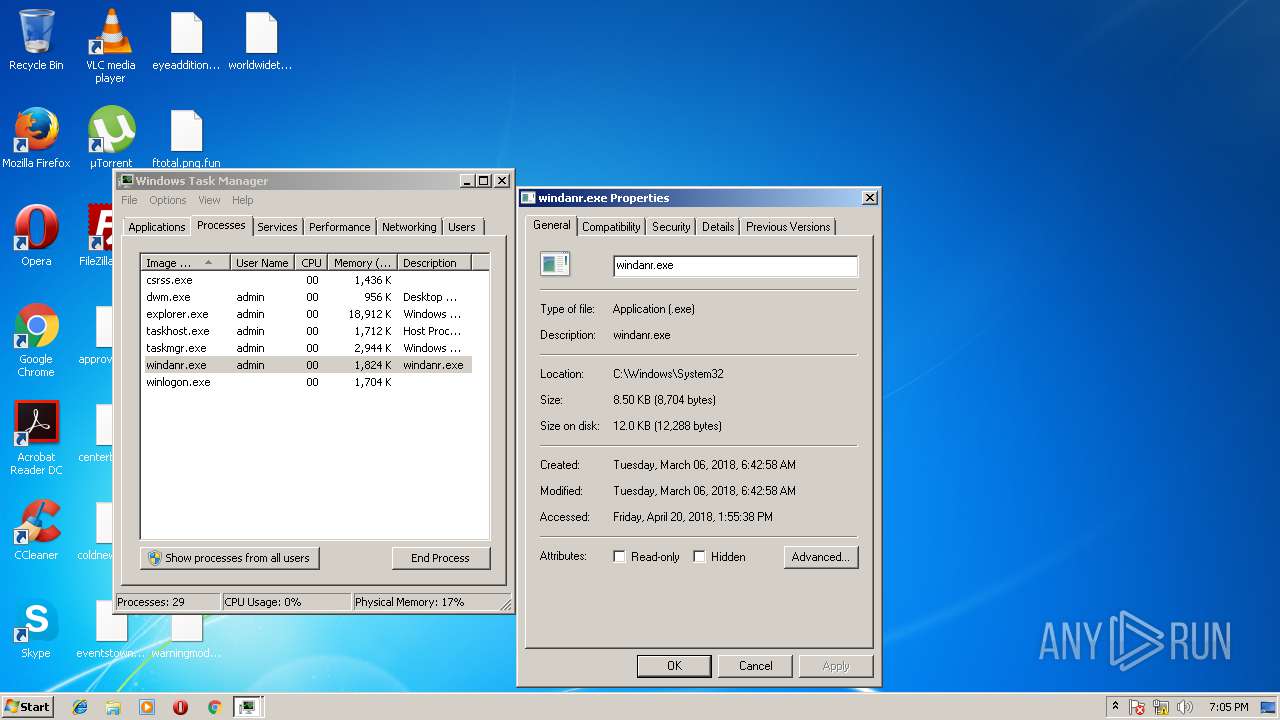
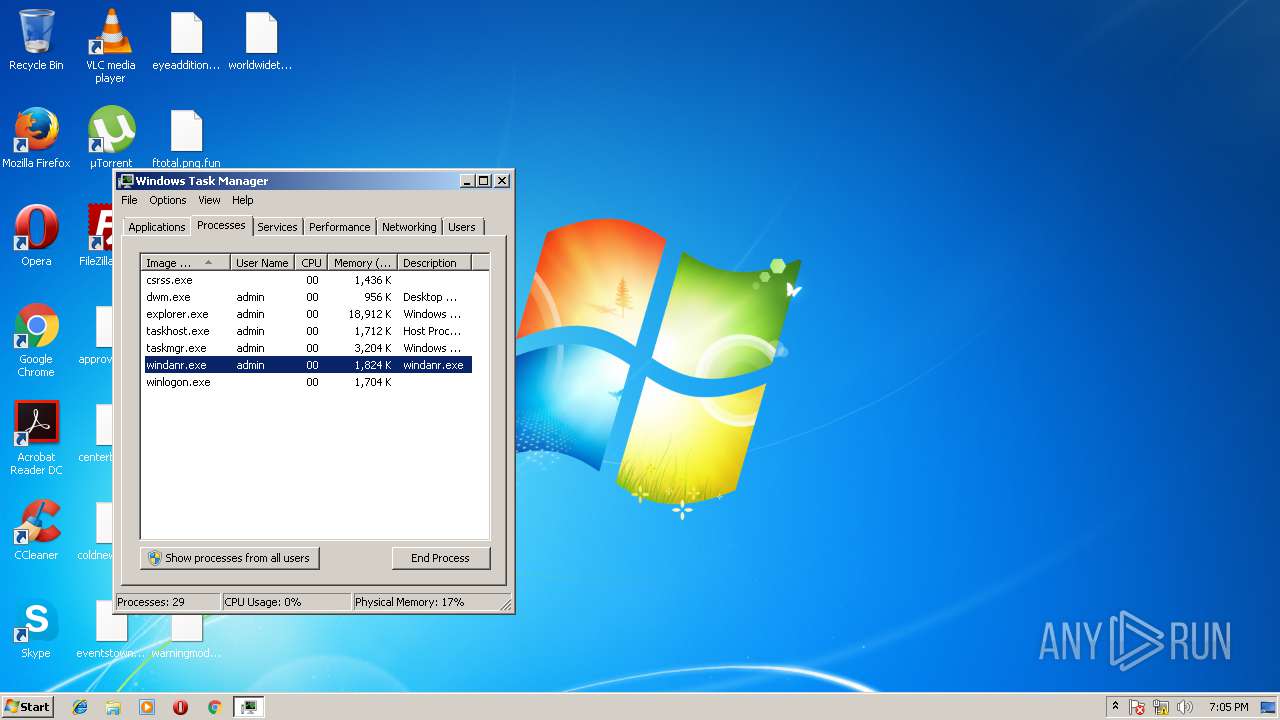
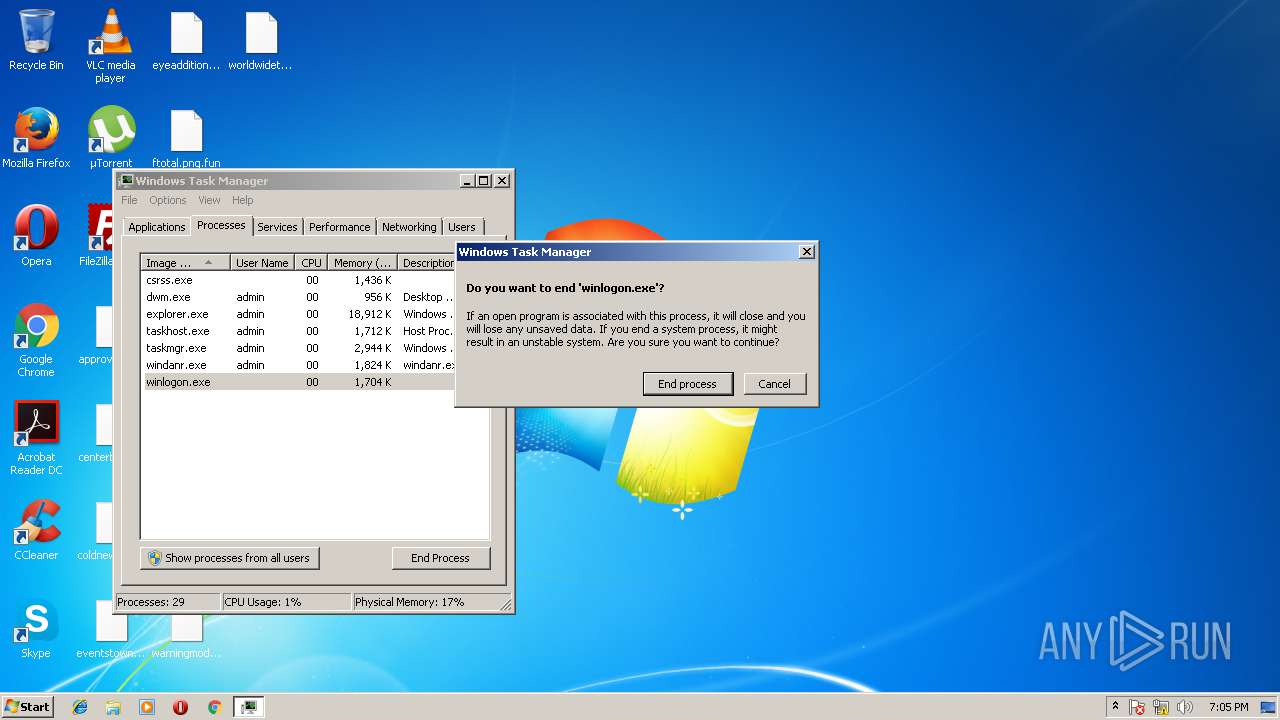
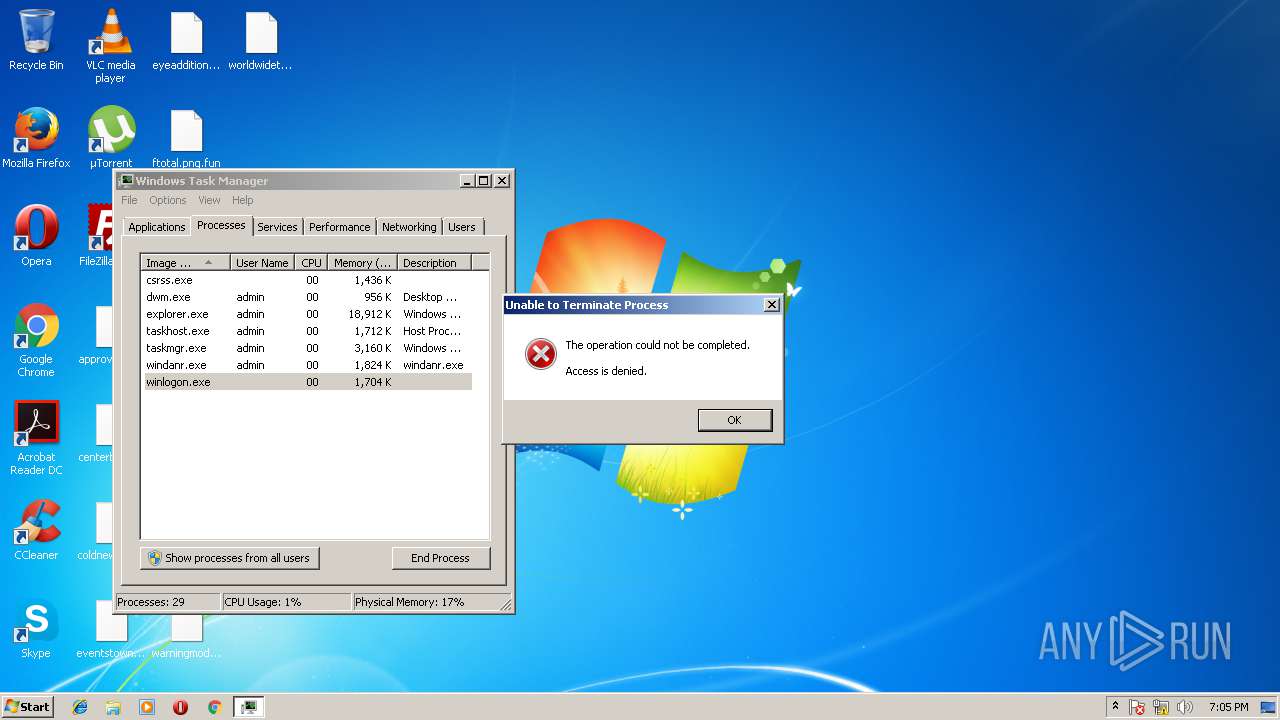
| 2144 | "C:\Windows\system32\taskmgr.exe" /1 | C:\Windows\system32\taskmgr.exe | taskmgr.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2396 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2628 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3116 | "C:\Users\admin\AppData\Local\Drpbx\drpbx.exe" C:\Users\admin\AppData\Local\Temp\jigsaw.exe | C:\Users\admin\AppData\Local\Drpbx\drpbx.exe | jigsaw.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 37.0.2.5583 Modules
| |||||||||||||||
| 3260 | "C:\Users\admin\AppData\Local\Temp\jigsaw.exe" | C:\Users\admin\AppData\Local\Temp\jigsaw.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 37.0.2.5583 Modules
| |||||||||||||||
| 3264 | "C:\Windows\System32\rundll32.exe" "C:\Program Files\Adobe\Acrobat Reader DC\Esl\AiodLite.dll",CreateReaderUserSettings | C:\Windows\System32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3520 | "taskhost.exe" | C:\Windows\system32\taskhost.exe | — | services.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3968 | "C:\Program Files\Google\Chrome\Application\61.0.3163.100\Installer\chrmstp.exe" --configure-user-settings --verbose-logging --system-level | C:\Program Files\Google\Chrome\Application\61.0.3163.100\Installer\chrmstp.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Chrome Installer Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
Total events
1 041
Read events
981
Write events
59
Delete events
1
Modification events
| (PID) Process: | (3260) jigsaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | firefox.exe |
Value: C:\Users\admin\AppData\Roaming\Frfx\firefox.exe | |||
| (PID) Process: | (3260) jigsaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3260) jigsaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3116) drpbx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\drpbx_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3116) drpbx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\drpbx_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3116) drpbx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\drpbx_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3116) drpbx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\drpbx_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3116) drpbx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\drpbx_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3116) drpbx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\drpbx_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3116) drpbx.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\drpbx_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
2
Suspicious files
243
Text files
10
Unknown types
3
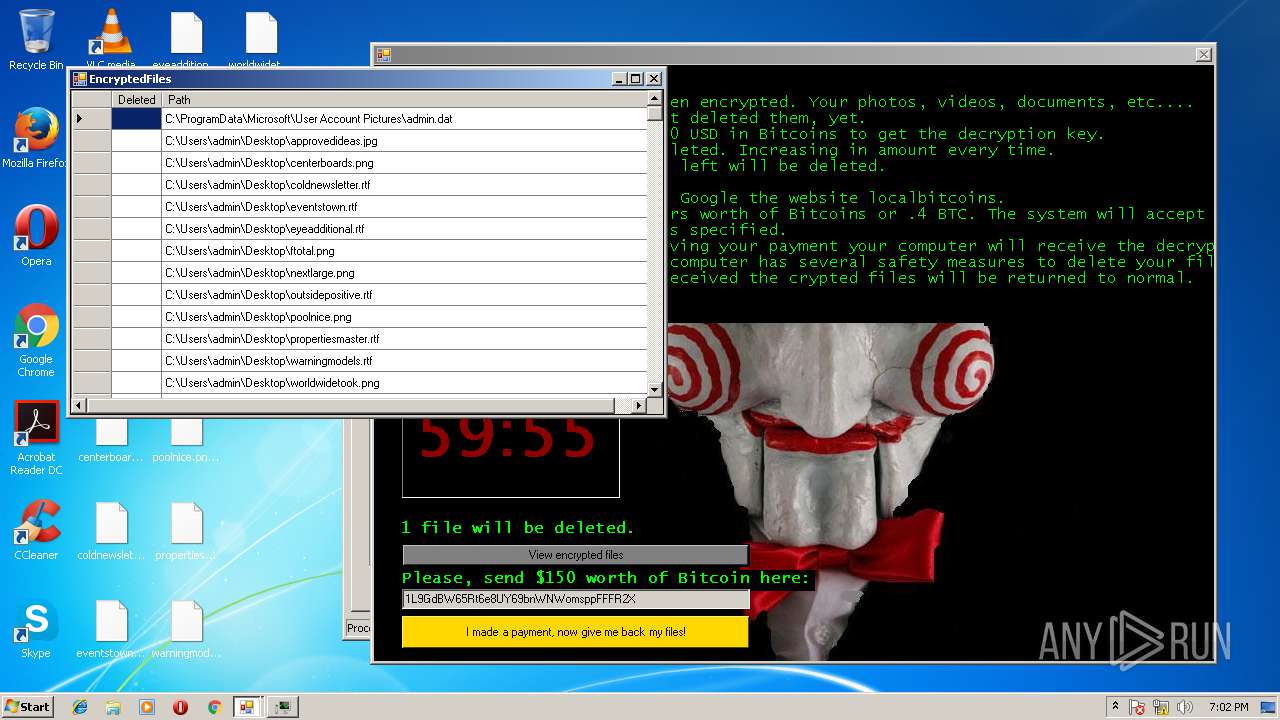
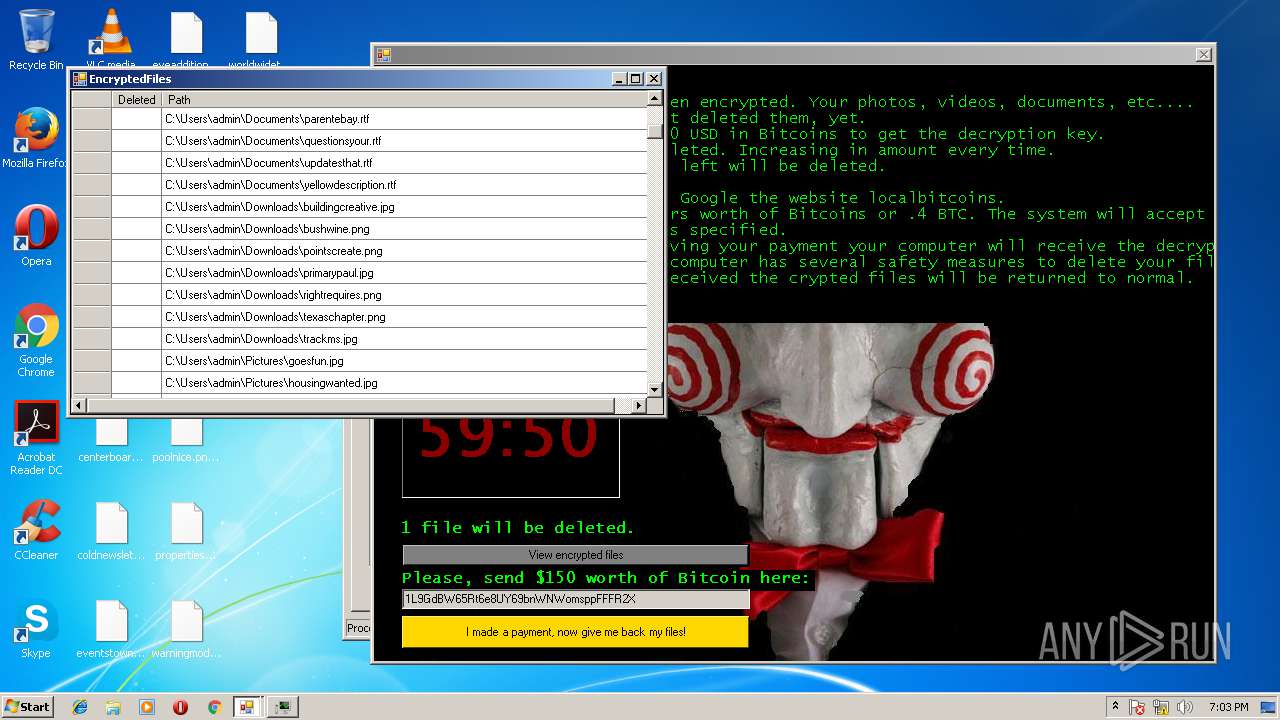
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3116 | drpbx.exe | C:\Users\admin\Desktop\ftotal.png.fun | binary | |
MD5:— | SHA256:— | |||
| 3116 | drpbx.exe | C:\Users\admin\Desktop\centerboards.png.fun | binary | |
MD5:— | SHA256:— | |||
| 3116 | drpbx.exe | C:\Users\admin\Desktop\warningmodels.rtf.fun | binary | |
MD5:— | SHA256:— | |||
| 3116 | drpbx.exe | C:\Users\admin\Desktop\eventstown.rtf.fun | binary | |
MD5:— | SHA256:— | |||
| 3116 | drpbx.exe | C:\Users\admin\Desktop\poolnice.png.fun | binary | |
MD5:— | SHA256:— | |||
| 3116 | drpbx.exe | C:\Users\admin\Desktop\propertiesmaster.rtf.fun | binary | |
MD5:— | SHA256:— | |||
| 3116 | drpbx.exe | C:\Users\admin\Desktop\outsidepositive.rtf.fun | binary | |
MD5:— | SHA256:— | |||
| 3260 | jigsaw.exe | C:\Users\admin\AppData\Local\Drpbx\drpbx.exe | executable | |
MD5:2773E3DC59472296CB0024BA7715A64E | SHA256:3AE96F73D805E1D3995253DB4D910300D8442EA603737A1428B613061E7F61E7 | |||
| 3116 | drpbx.exe | C:\Users\admin\Desktop\worldwidetook.png.fun | binary | |
MD5:— | SHA256:— | |||
| 3116 | drpbx.exe | C:\Users\admin\Documents\frameitself.rtf.fun | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
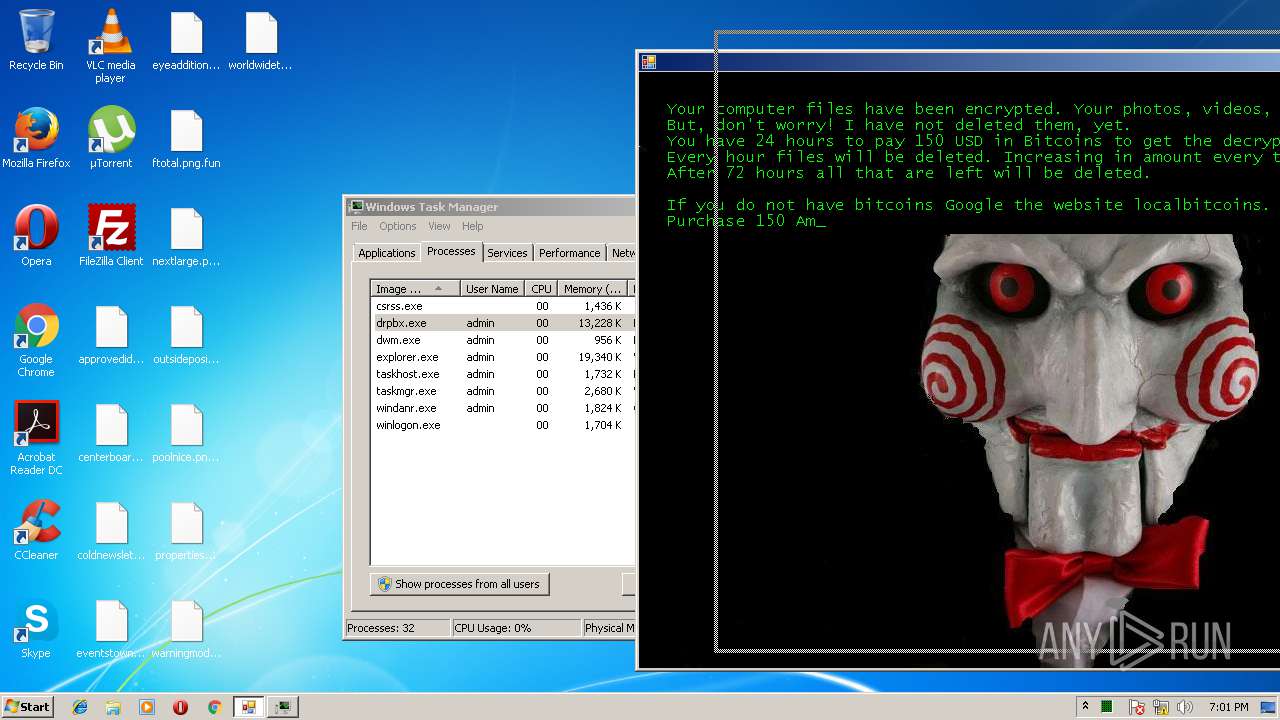
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3116 | drpbx.exe | GET | 301 | 104.16.150.172:80 | http://btc.blockr.io/api/v1/coin/info/ | US | — | — | shared |
3116 | drpbx.exe | GET | 301 | 104.16.150.172:80 | http://btc.blockr.io/api/v1/coin/info/ | US | — | — | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3116 | drpbx.exe | 104.16.150.172:80 | btc.blockr.io | Cloudflare Inc | US | shared |
3116 | drpbx.exe | 104.16.8.251:443 | www.coinbase.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
btc.blockr.io |
| unknown |
www.coinbase.com |
| suspicious |