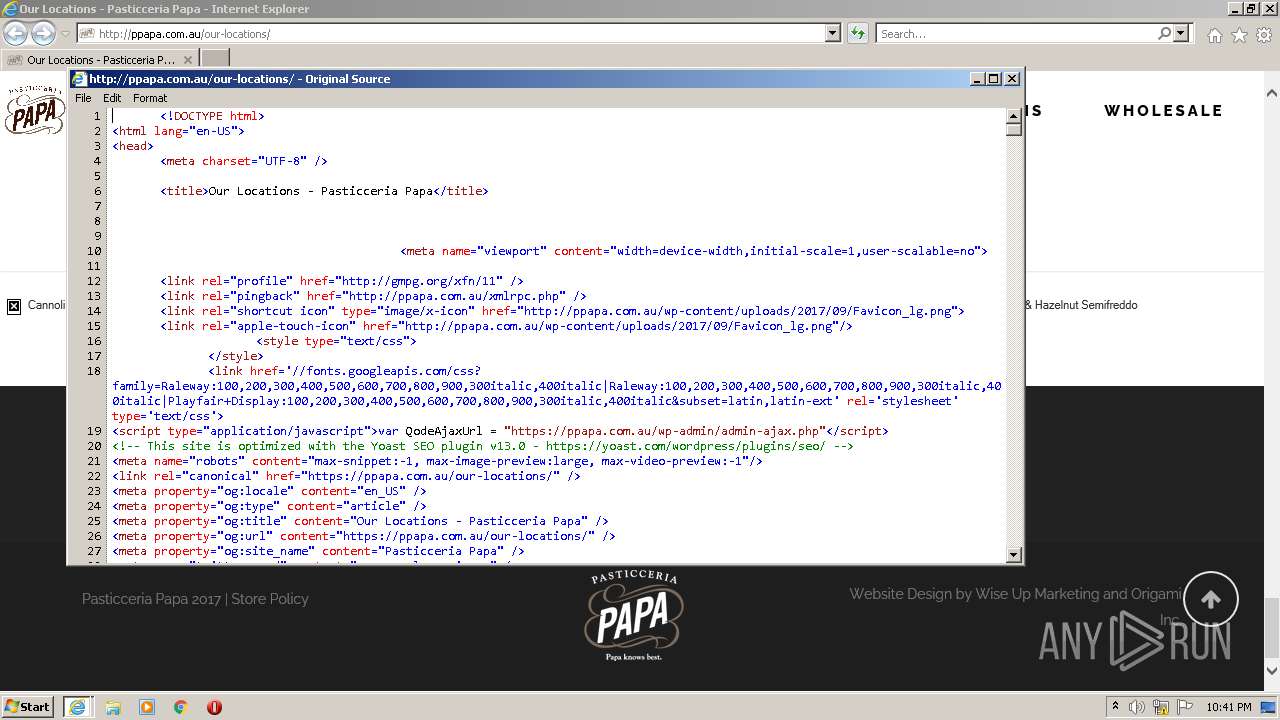
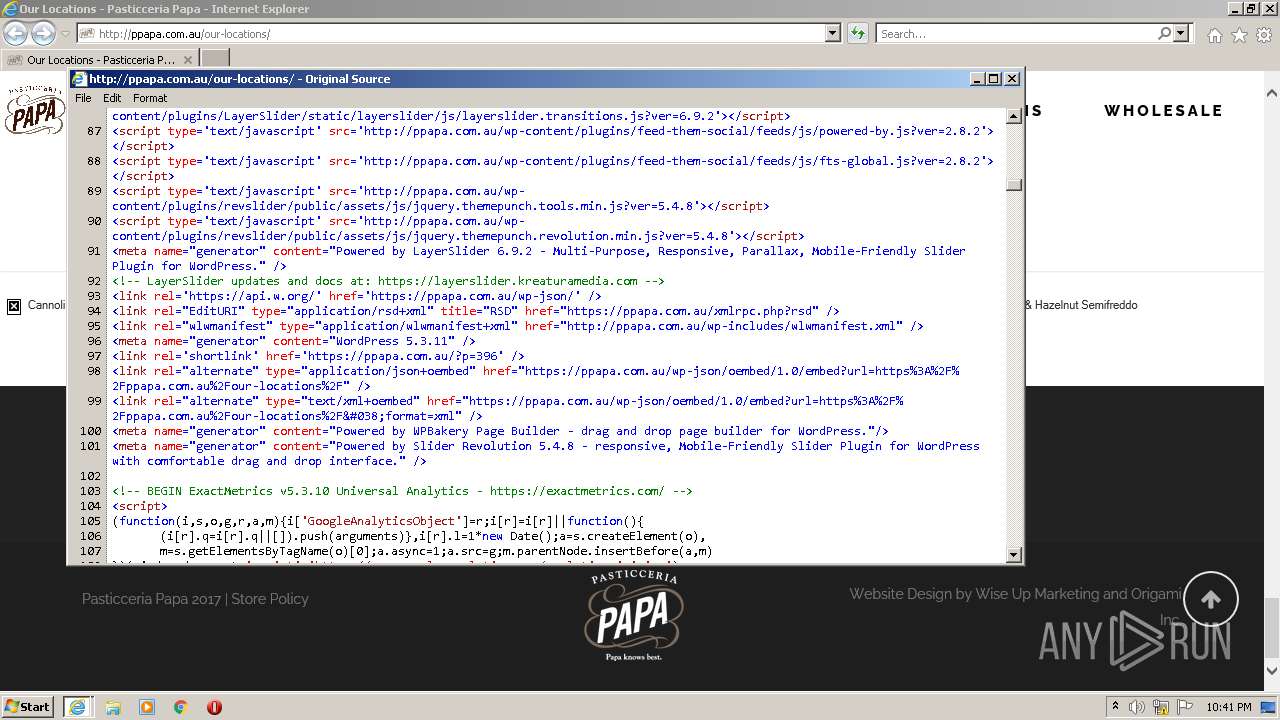
| URL: | http://ppapa.com.au/our-locations/ |
| Full analysis: | https://app.any.run/tasks/2d29be9a-165e-4e8e-a399-6f3d361db862 |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 22:40:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7644447E51CBDE718CBD6BE9AAAC74C0 |
| SHA1: | 3F3FDA4CDA2A31B630BFBF02F2AF2969D5B22279 |
| SHA256: | 3AE50CD00B7CA986FE1709A67C6C67941A82546692C8F7AADAA304415F3DDECF |
| SSDEEP: | 3:N1KOVVLGKIl2Y1K:COVQ8Y1K |
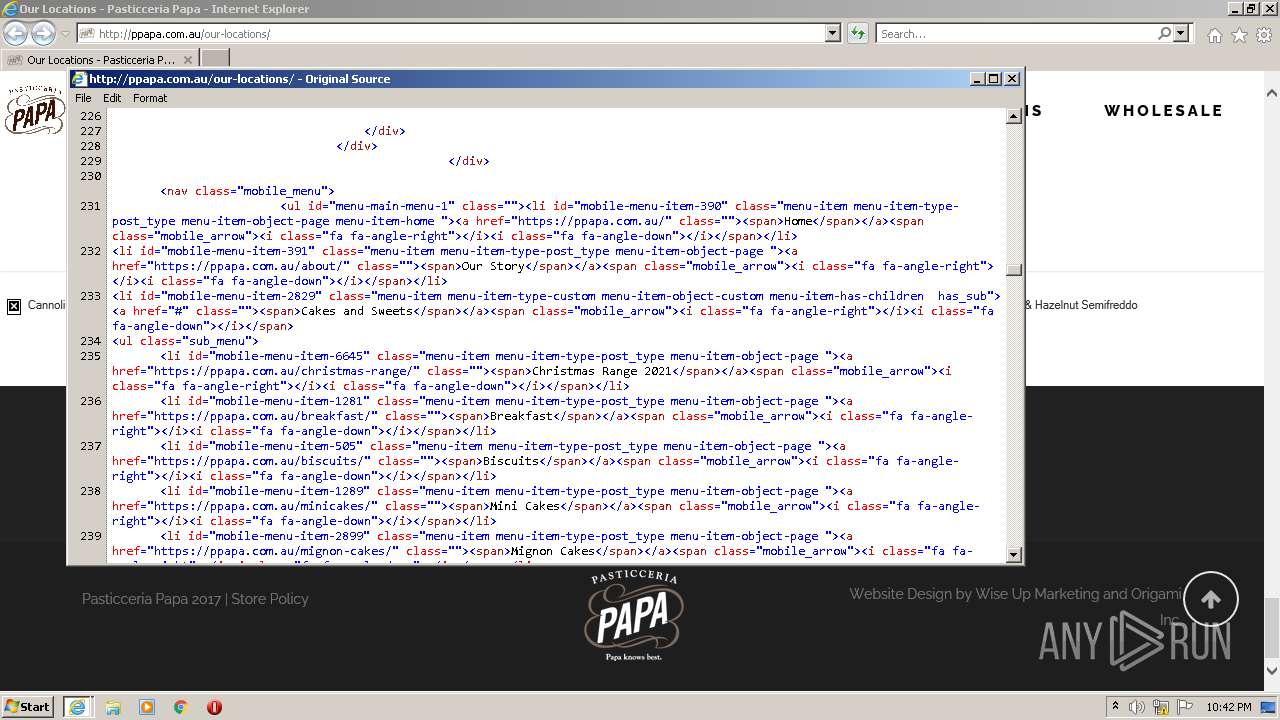
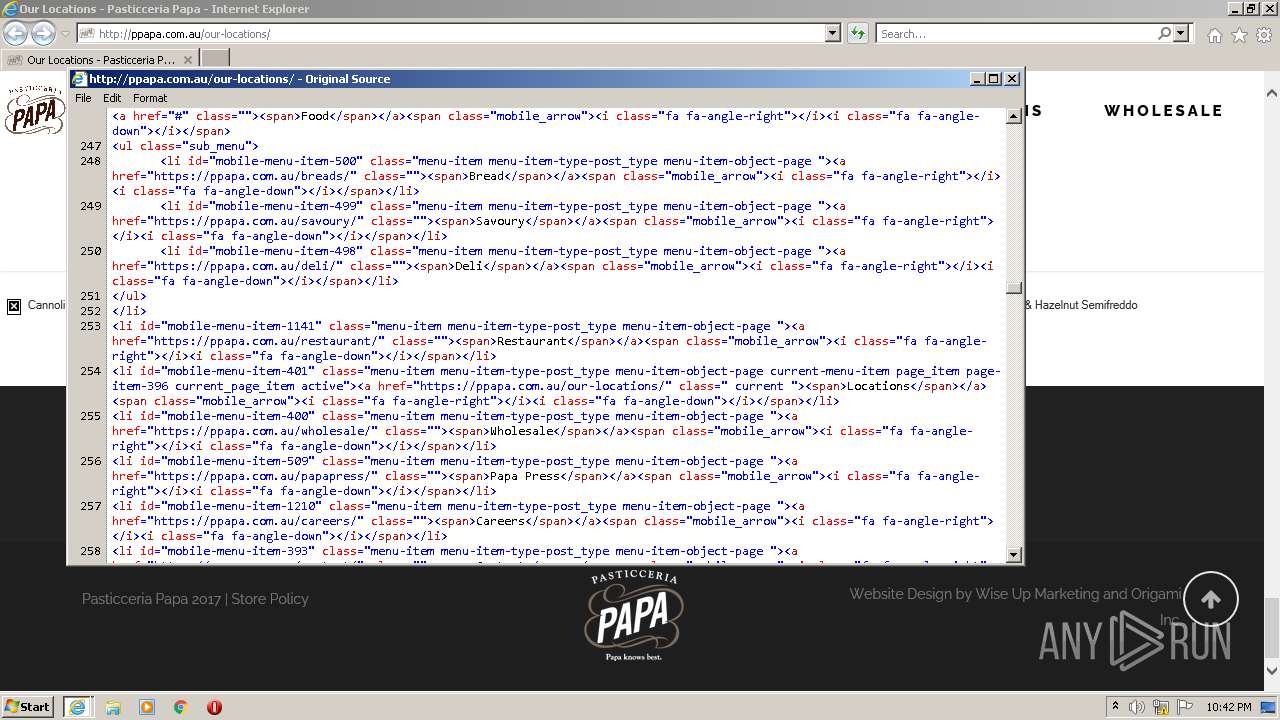
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 572)
INFO
Checks supported languages
- iexplore.exe (PID: 1704)
- iexplore.exe (PID: 572)
Reads the computer name
- iexplore.exe (PID: 1704)
- iexplore.exe (PID: 572)
Application launched itself
- iexplore.exe (PID: 1704)
Changes internet zones settings
- iexplore.exe (PID: 1704)
Checks Windows Trust Settings
- iexplore.exe (PID: 1704)
- iexplore.exe (PID: 572)
Reads settings of System Certificates
- iexplore.exe (PID: 1704)
- iexplore.exe (PID: 572)
Reads internet explorer settings
- iexplore.exe (PID: 572)
Creates files in the user directory
- iexplore.exe (PID: 572)
- iexplore.exe (PID: 1704)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1704)
Changes settings of System certificates
- iexplore.exe (PID: 1704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1704 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://ppapa.com.au/our-locations/" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
15 753
Read events
15 614
Write events
137
Delete events
2
Modification events
| (PID) Process: | (1704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30937459 | |||
| (PID) Process: | (1704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30937459 | |||
| (PID) Process: | (1704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
19
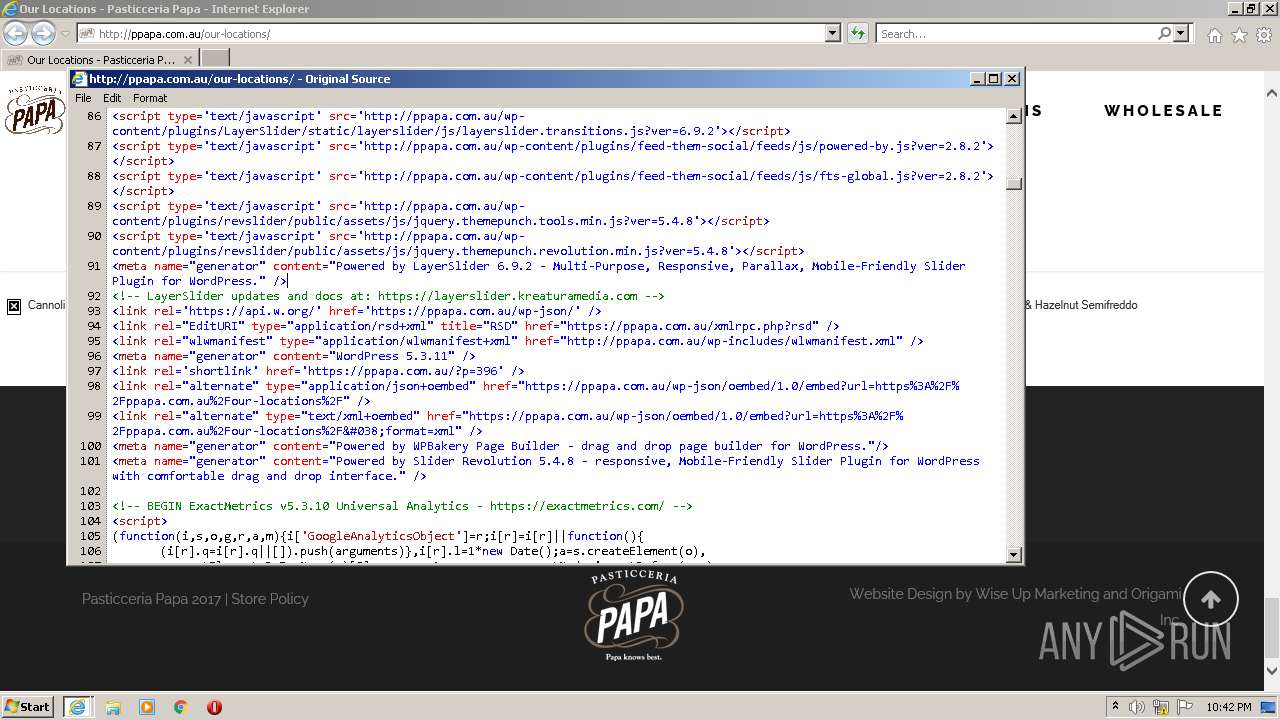
Text files
122
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\css[1].css | text | |
MD5:— | SHA256:— | |||
| 572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\our-locations[1].htm | html | |
MD5:— | SHA256:— | |||
| 572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\css[1].css | text | |
MD5:— | SHA256:— | |||
| 572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\settings[1].css | text | |
MD5:3562402588E3BD6410012CF058D1948C | SHA256:23A57AED407545BD964231BCB511674996BDD28A4F2A57CA66BCA72DE0BF3D2D | |||
| 572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\style.min[1].css | text | |
MD5:612B7AB9F699E968F5B3206CA16EE834 | SHA256:DFD6D929422D1F69A727FB6B525F610562EAB183A333576516BEC0B0503CB049 | |||
| 572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\font-awesome.min[1].css | text | |
MD5:269550530CC127B6AA5A35925A7DE6CE | SHA256:799AEB25CC0373FDEE0E1B1DB7AD6C2F6A0E058DFADAA3379689F583213190BD | |||
| 572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\style_dynamic[1].css | text | |
MD5:— | SHA256:— | |||
| 572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\style[1].css | text | |
MD5:18513056C4A412491127BC1CEE55D372 | SHA256:B5CAD6A450F4007B75FF83016582537871825A08C94CE709EFB80947DB45D40C | |||
| 572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\wp-emoji-release.min[1].js | text | |
MD5:D6AEFFD9E0126160FF89D369C05A5FBE | SHA256:95309410230B1D3148E52211DCEE018BFA011A2D69E9D7D6F81164035E8518A0 | |||
| 572 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\custom_css[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
133
TCP/UDP connections
122
DNS requests
27
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
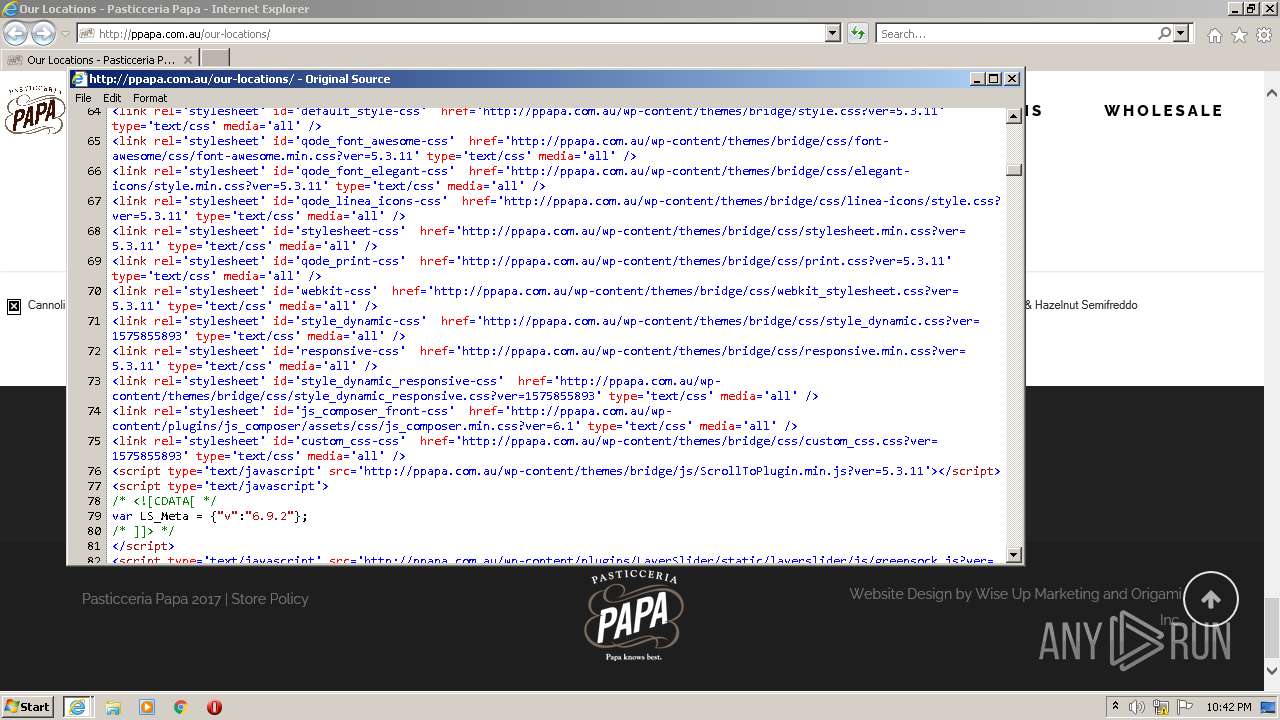
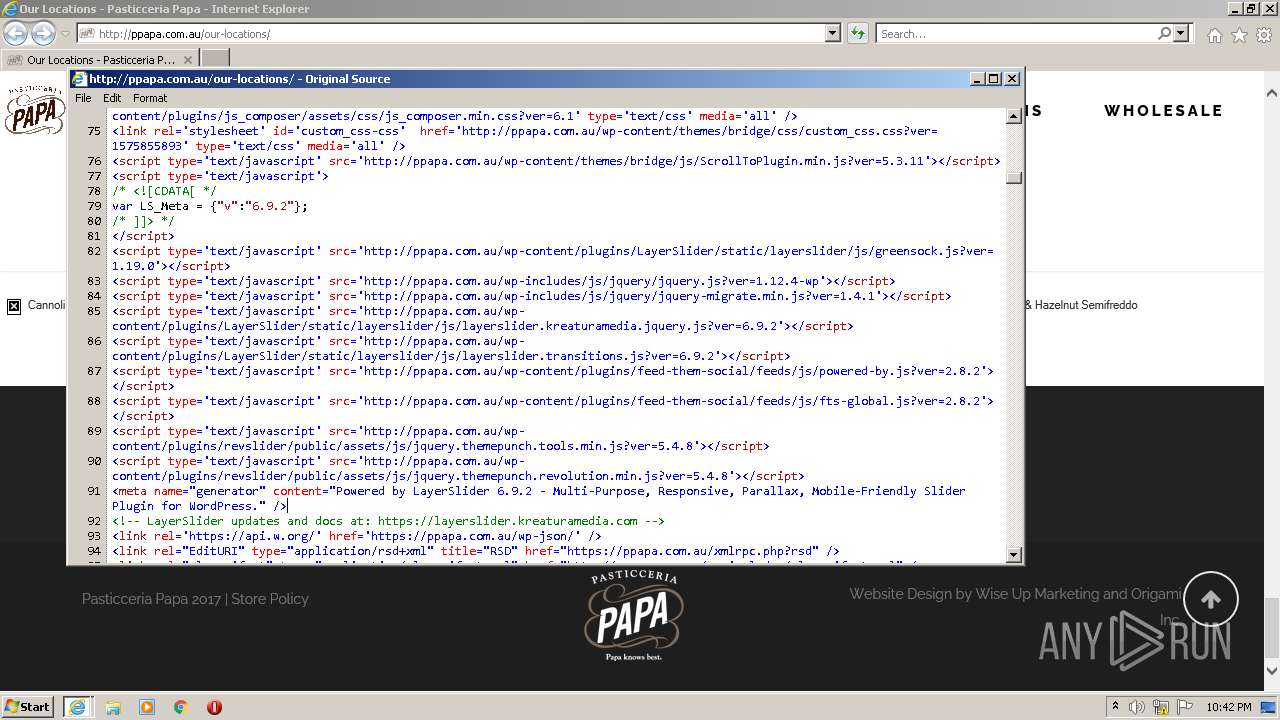
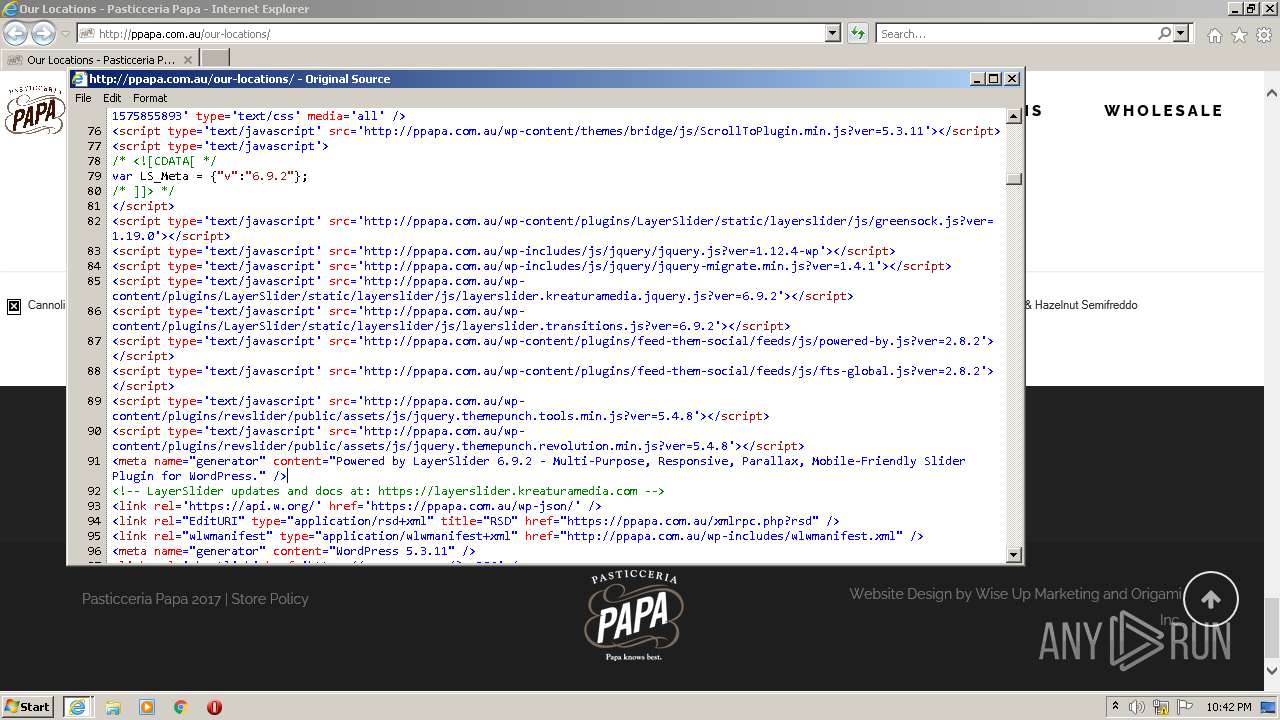
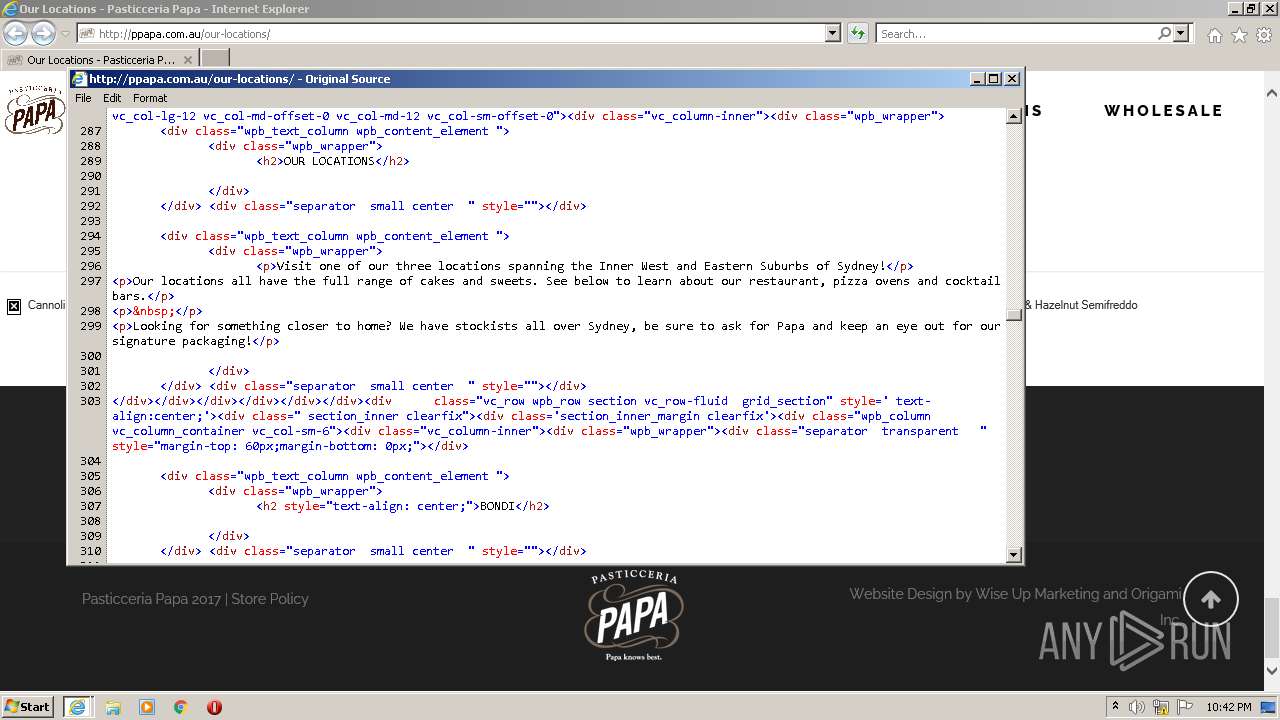
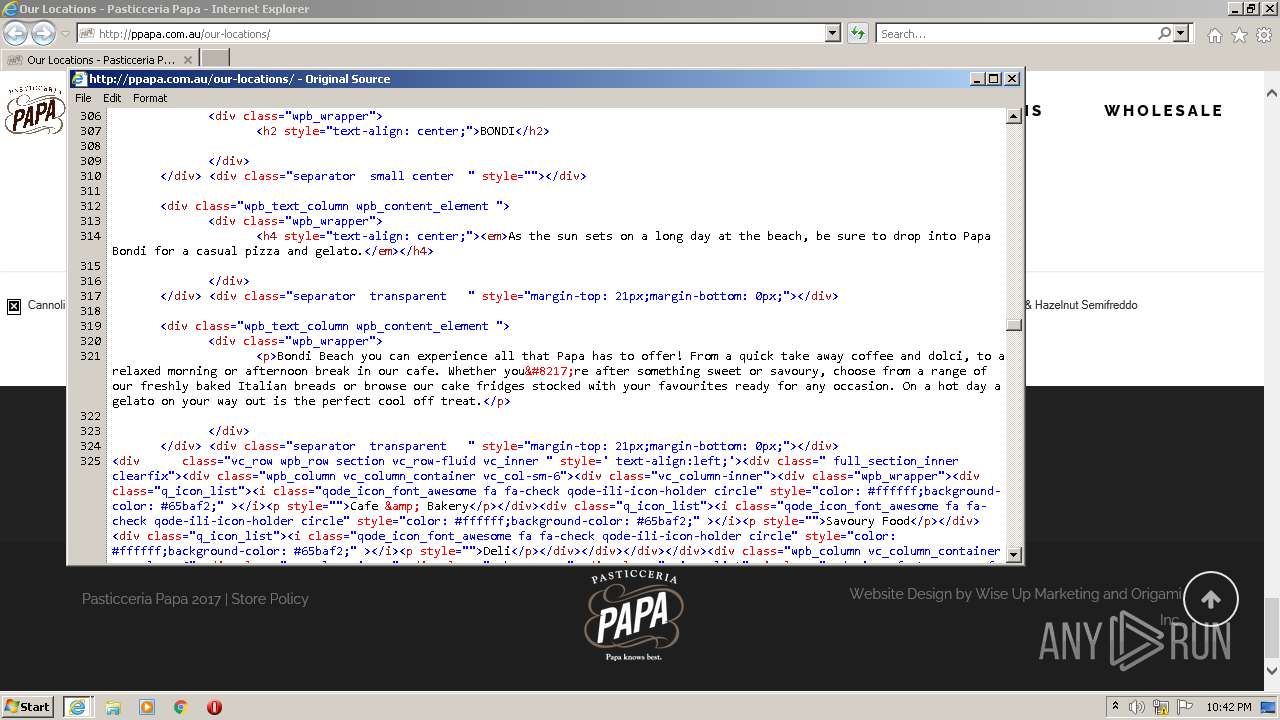
572 | iexplore.exe | GET | 200 | 139.99.186.24:80 | http://ppapa.com.au/our-locations/ | AU | compressed | 13.9 Kb | suspicious |
572 | iexplore.exe | GET | 200 | 139.99.186.24:80 | http://ppapa.com.au/wp-content/plugins/revslider/public/assets/css/settings.css?ver=5.4.8 | AU | compressed | 11.1 Kb | suspicious |
572 | iexplore.exe | GET | 200 | 139.99.186.24:80 | http://ppapa.com.au/wp-content/plugins/LayerSlider/static/layerslider/css/layerslider.css?ver=6.9.2 | AU | compressed | 5.09 Kb | suspicious |
572 | iexplore.exe | GET | 200 | 139.99.186.24:80 | http://ppapa.com.au/wp-content/plugins/feed-them-social/feeds/css/styles.css?ver=2.8.2 | AU | compressed | 23.5 Kb | suspicious |
572 | iexplore.exe | GET | 200 | 139.99.186.24:80 | http://ppapa.com.au/wp-content/themes/bridge/style.css?ver=5.3.11 | AU | compressed | 358 b | suspicious |
572 | iexplore.exe | GET | 200 | 139.99.186.24:80 | http://ppapa.com.au/wp-content/themes/bridge/css/elegant-icons/style.min.css?ver=5.3.11 | AU | compressed | 4.68 Kb | suspicious |
572 | iexplore.exe | GET | 200 | 139.99.186.24:80 | http://ppapa.com.au/wp-includes/js/wp-emoji-release.min.js?ver=5.3.11 | AU | compressed | 5.11 Kb | suspicious |
572 | iexplore.exe | GET | 200 | 139.99.186.24:80 | http://ppapa.com.au/wp-content/themes/bridge/css/linea-icons/style.css?ver=5.3.11 | AU | compressed | 9.44 Kb | suspicious |
572 | iexplore.exe | GET | 200 | 139.99.186.24:80 | http://ppapa.com.au/wp-content/themes/bridge/css/stylesheet.min.css?ver=5.3.11 | AU | compressed | 106 Kb | suspicious |
572 | iexplore.exe | GET | 200 | 139.99.186.24:80 | http://ppapa.com.au/wp-content/themes/bridge/css/print.css?ver=5.3.11 | AU | compressed | 285 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
572 | iexplore.exe | 142.251.5.155:443 | stats.g.doubleclick.net | Google Inc. | US | unknown |
572 | iexplore.exe | 142.250.184.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
572 | iexplore.exe | 139.99.186.24:443 | ppapa.com.au | OVH SAS | AU | suspicious |
572 | iexplore.exe | 139.99.186.24:80 | ppapa.com.au | OVH SAS | AU | suspicious |
572 | iexplore.exe | 142.250.186.106:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1704 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
572 | iexplore.exe | 20.191.246.109:443 | widget.dimmi.com.au | Microsoft Corporation | US | unknown |
— | — | 95.140.236.128:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | GB | malicious |
572 | iexplore.exe | 95.140.236.128:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | GB | malicious |
572 | iexplore.exe | 192.124.249.23:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ppapa.com.au |
| suspicious |
fonts.googleapis.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
widget.dimmi.com.au |
| unknown |
www.dimmi.com.au |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
widget.thefork.com.au |
| unknown |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
572 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
572 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
572 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
572 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
572 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
572 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |