| File name: | FIFA-22_73988.exe |
| Full analysis: | https://app.any.run/tasks/7b1c5ef2-4172-46d2-acbd-76925a28bccc |
| Verdict: | Malicious activity |
| Analysis date: | April 10, 2022, 19:23:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 891860064F823C696324CB157CDC88D6 |
| SHA1: | 2B06E040F94533625DC9393E80C325E9B1E100D4 |
| SHA256: | 3AD57C5D41A71945E5C66C31CDBE70D592B6DA8A8ADD70C618653DB73EDE2614 |
| SSDEEP: | 24576:cXwOrRsH52hdHAE1L0kkGL/n6Mq2p+sghs7Iyr9++nBPDYrrK6fimBZmTvcSxI:cgwRyGdHnRxRghs7Iyr8+nBVFmBwTESO |
MALICIOUS
Drops executable file immediately after starts
- FIFA-22_73988.exe (PID: 1580)
Application was dropped or rewritten from another process
- BrightTRAMPUtil.exe (PID: 1412)
- BrightTRAMPUtil.exe (PID: 1464)
- BrightyUtil.exe (PID: 3944)
Loads dropped or rewritten executable
- BrightTRAMPUtil.exe (PID: 1464)
- chrome.exe (PID: 4036)
- chrome.exe (PID: 2076)
- svchost.exe (PID: 868)
SUSPICIOUS
Reads the computer name
- FIFA-22_73988.exe (PID: 1580)
- BrightTRAMPUtil.exe (PID: 1412)
- BrightTRAMPUtil.exe (PID: 1464)
- BrightyUtil.exe (PID: 3944)
Checks supported languages
- FIFA-22_73988.exe (PID: 1580)
- BrightTRAMPUtil.exe (PID: 1412)
- BrightTRAMPUtil.exe (PID: 1464)
- BrightyUtil.exe (PID: 3944)
Application launched itself
- BrightTRAMPUtil.exe (PID: 1412)
Drops a file with a compile date too recent
- FIFA-22_73988.exe (PID: 1580)
Executable content was dropped or overwritten
- BrightTRAMPUtil.exe (PID: 1464)
- FIFA-22_73988.exe (PID: 1580)
- BrightyUtil.exe (PID: 3944)
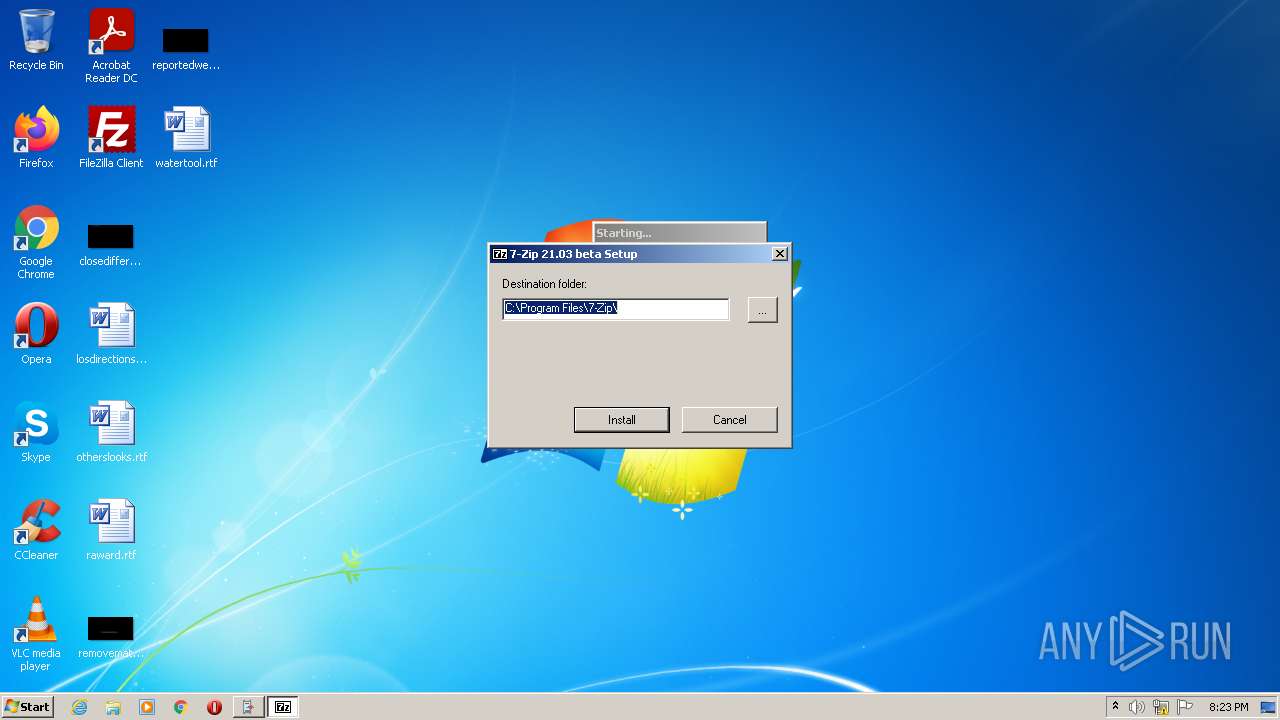
Creates files in the program directory
- BrightTRAMPUtil.exe (PID: 1464)
- BrightyUtil.exe (PID: 3944)
Creates a directory in Program Files
- BrightTRAMPUtil.exe (PID: 1464)
- BrightyUtil.exe (PID: 3944)
Creates/Modifies COM task schedule object
- BrightyUtil.exe (PID: 3944)
Creates a software uninstall entry
- BrightyUtil.exe (PID: 3944)
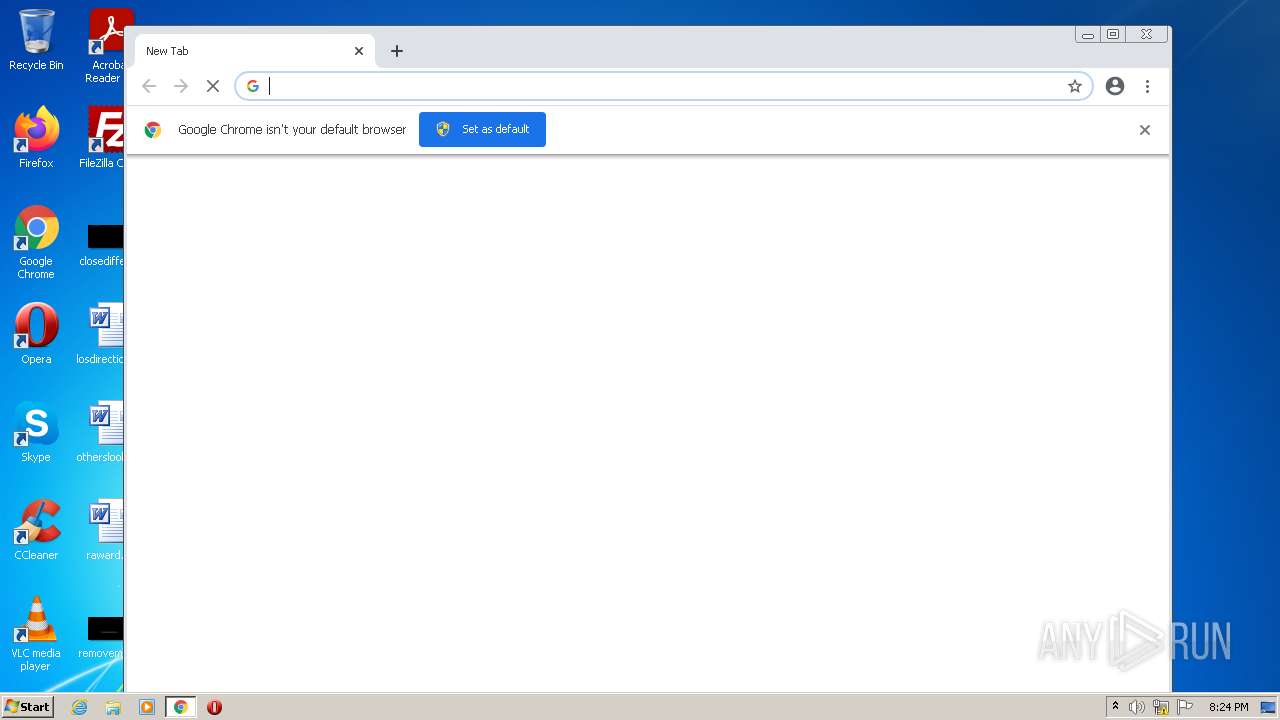
Modifies files in Chrome extension folder
- chrome.exe (PID: 1648)
INFO
Checks supported languages
- chrome.exe (PID: 1648)
- chrome.exe (PID: 1280)
- chrome.exe (PID: 3484)
- chrome.exe (PID: 3540)
- chrome.exe (PID: 2976)
- chrome.exe (PID: 2360)
- chrome.exe (PID: 2956)
- chrome.exe (PID: 1956)
- chrome.exe (PID: 3928)
- chrome.exe (PID: 1388)
- chrome.exe (PID: 1988)
- chrome.exe (PID: 756)
- chrome.exe (PID: 3928)
- chrome.exe (PID: 2076)
- chrome.exe (PID: 1068)
- chrome.exe (PID: 4036)
Manual execution by user
- chrome.exe (PID: 1648)
Reads the hosts file
- chrome.exe (PID: 3540)
- chrome.exe (PID: 1648)
Reads the computer name
- chrome.exe (PID: 1648)
- chrome.exe (PID: 3540)
- chrome.exe (PID: 3484)
- chrome.exe (PID: 1956)
- chrome.exe (PID: 4036)
- chrome.exe (PID: 2076)
- chrome.exe (PID: 1388)
Application launched itself
- chrome.exe (PID: 1648)
Reads settings of System Certificates
- chrome.exe (PID: 3540)
Reads the date of Windows installation
- chrome.exe (PID: 2076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:31 01:38:51+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 101888 |
| InitializedDataSize: | 89088 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1942f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.55.0.4 |
| ProductVersionNumber: | 1.55.0.4 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
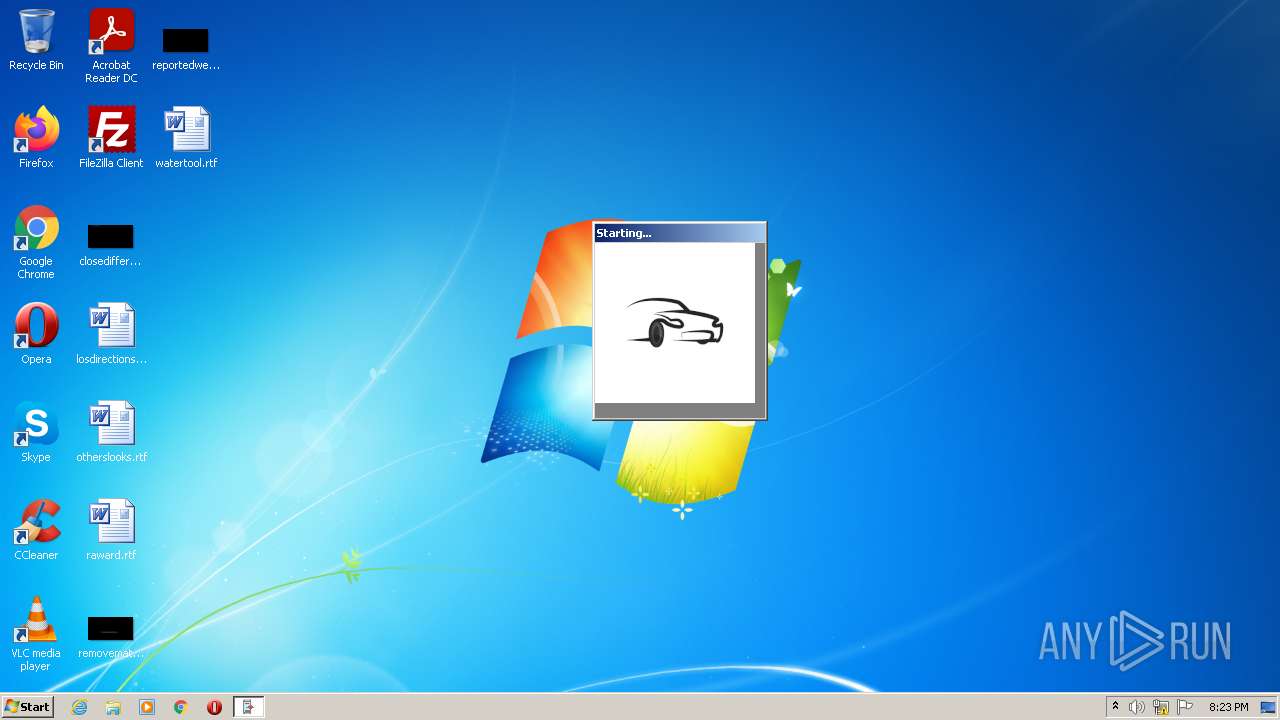
| CompanyName: | Bright TRAMP |
| FileDescription: | Bright TRAMP Util |
| FileVersion: | 1.55.0.4 |
| InternalName: | BrightTRAMPUtil.exe |
| LegalCopyright: | Bright TRAMP (c). All rights reserved |
| OriginalFileName: | BrightTRAMPUtil.exe |
| ProductName: | Bright TRAMP Util |
| ProductVersion: | 1.55.0.4 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Dec-2012 00:38:51 |
| Detected languages: |
|
| CompanyName: | Bright TRAMP |
| FileDescription: | Bright TRAMP Util |
| FileVersion: | 1.55.0.4 |
| InternalName: | BrightTRAMPUtil.exe |
| LegalCopyright: | Bright TRAMP (c). All rights reserved |
| OriginalFilename: | BrightTRAMPUtil.exe |
| ProductName: | Bright TRAMP Util |
| ProductVersion: | 1.55.0.4 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0060 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000060 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 31-Dec-2012 00:38:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00018DDE | 0x00018E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67402 |
.rdata | 0x0001A000 | 0x00003BCA | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.71339 |
.data | 0x0001E000 | 0x00004DEC | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.45098 |
.rsrc | 0x00023000 | 0x00011544 | 0x00011600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.7626 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.01659 | 1656 | Latin 1 / Western European | English - United States | RT_MANIFEST |
5 | 1.43775 | 52 | UNKNOWN | English - United States | RT_STRING |
500 | 3.09294 | 184 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
56
Monitored processes
21
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,14218924068067844885,16228842343901337153,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3196 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 868 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\system32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,14218924068067844885,16228842343901337153,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2944 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6ea7d988,0x6ea7d998,0x6ea7d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,14218924068067844885,16228842343901337153,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1860 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1412 | "C:\Users\admin\AppData\Local\BrightTRAMP\BrightTRAMPUtil.exe" "C:\Users\admin\AppData\Local\Temp\FIFA-22_73988.exe" | C:\Users\admin\AppData\Local\BrightTRAMP\BrightTRAMPUtil.exe | — | FIFA-22_73988.exe | |||||||||||
User: admin Company: Bright TRAMP Integrity Level: MEDIUM Description: Bright TRAMP Util Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 1464 | "C:\Users\admin\AppData\Local\BrightTRAMP\BrightTRAMPUtil.exe" "C:\Users\admin\AppData\Local\Temp\FIFA-22_73988.exe" By5DuycGPk45/TWlgH0/hKX+QXQJTfykQjozLbwv1NQbeo6xIsneba+E4DV6X1+scRMA0gAP4bJTiOyAUwid4iU667w5rpgzKPLbZRAZ7uU= /uuv | C:\Users\admin\AppData\Local\BrightTRAMP\BrightTRAMPUtil.exe | BrightTRAMPUtil.exe | ||||||||||||
User: admin Company: Bright TRAMP Integrity Level: HIGH Description: Bright TRAMP Util Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 1580 | "C:\Users\admin\AppData\Local\Temp\FIFA-22_73988.exe" | C:\Users\admin\AppData\Local\Temp\FIFA-22_73988.exe | Explorer.EXE | ||||||||||||
User: admin Company: Bright TRAMP Integrity Level: MEDIUM Description: Bright TRAMP Util Exit code: 0 Version: 1.55.0.4 Modules
| |||||||||||||||
| 1648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,14218924068067844885,16228842343901337153,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2844 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
13 851
Read events
13 704
Write events
145
Delete events
2
Modification events
| (PID) Process: | (1580) FIFA-22_73988.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1580) FIFA-22_73988.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1580) FIFA-22_73988.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1580) FIFA-22_73988.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1412) BrightTRAMPUtil.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1412) BrightTRAMPUtil.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1412) BrightTRAMPUtil.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1412) BrightTRAMPUtil.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (868) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 2 | |||
| (PID) Process: | (868) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 1 | |||
Executable files
11
Suspicious files
113
Text files
180
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 868 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 1580 | FIFA-22_73988.exe | C:\Users\admin\AppData\Local\BrightTRAMP\BrightTRAMPUtil.exe | executable | |
MD5:— | SHA256:— | |||
| 3944 | BrightyUtil.exe | C:\Program Files\7-Zip\Lang\af.txt | text | |
MD5:FBBE51ACB879B525CC6B19D386697924 | SHA256:3793FB69EE9FD958CF15A272B1ED54E4B3D75592836EBCD085DC0E7B1400D1CB | |||
| 3944 | BrightyUtil.exe | C:\Program Files\7-Zip\descript.ion | text | |
MD5:EB7E322BDC62614E49DED60E0FB23845 | SHA256:1DA513F5A4E8018B9AE143884EB3EAF72454B606FD51F2401B7CFD9BE4DBBF4F | |||
| 1464 | BrightTRAMPUtil.exe | C:\Program Files\BrightTRAMPpevUtil\BrightyUtil.exe | executable | |
MD5:7358BF3886A22150B2661340B94D5497 | SHA256:447916156F9F8A4D0BF9371745250EC4A59C6172993E428141BD2F28D68A0FB9 | |||
| 3944 | BrightyUtil.exe | C:\Program Files\7-Zip\History.txt | text | |
MD5:9EBDE31BD2CD85CD81DCD76977318B8A | SHA256:C588599CAA710A918E330D41A41A5BA876BE7BB5CBCE1A43D7793586410CD6A2 | |||
| 3944 | BrightyUtil.exe | C:\Program Files\7-Zip\Lang\an.txt | text | |
MD5:BF8564B2DAD5D2506887F87AEE169A0A | SHA256:0E8DD119DFA6C6C1B3ACA993715092CDF1560947871092876D309DBC1940A14A | |||
| 3944 | BrightyUtil.exe | C:\Program Files\7-Zip\Lang\ar.txt | text | |
MD5:1C45E6A6ECB3B71A7316C466B6A77C1C | SHA256:972261B53289DE2BD8A65E787A6E7CD6DEFC2B5F7E344128F2FE0492ED30CCF1 | |||
| 3944 | BrightyUtil.exe | C:\Program Files\7-Zip\Lang\ast.txt | text | |
MD5:1F86AE235BC747A279C9E9EC72675CE4 | SHA256:8FCD1B8CE6FED05F406C4B81AEA821132800BC494D3FD6F42A4258A81F8998EC | |||
| 1464 | BrightTRAMPUtil.exe | C:\Users\admin\AppData\Local\Temp\curl.dll | executable | |
MD5:8C578E63F4CFBC672B4DFF2344B9DD26 | SHA256:7886823E8F5BDE504BF09C61041A16AFBFFEEFDA64F3AEAFB1CCF0B508CC12CD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
19
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3540 | chrome.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 557 b | whitelisted |
3540 | chrome.exe | GET | 200 | 173.194.137.73:80 | http://r4---sn-aigzrn76.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=e_&mip=185.198.243.203&mm=28&mn=sn-aigzrn76&ms=nvh&mt=1649618419&mv=m&mvi=4&pl=24&shardbypass=sd&smhost=r2---sn-aigzrne7.gvt1.com | US | crx | 242 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1464 | BrightTRAMPUtil.exe | 172.67.73.41:443 | webmanagefile.com | — | US | unknown |
3540 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
3540 | chrome.exe | 142.250.185.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
3540 | chrome.exe | 142.250.186.173:443 | accounts.google.com | Google Inc. | US | suspicious |
3540 | chrome.exe | 142.250.184.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3540 | chrome.exe | 142.250.185.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3540 | chrome.exe | 173.194.137.73:80 | r4---sn-aigzrn76.gvt1.com | Google Inc. | US | whitelisted |
3540 | chrome.exe | 172.217.18.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3540 | chrome.exe | 142.250.184.206:443 | apis.google.com | Google Inc. | US | whitelisted |
3540 | chrome.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
webmanagefile.com |
| unknown |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |