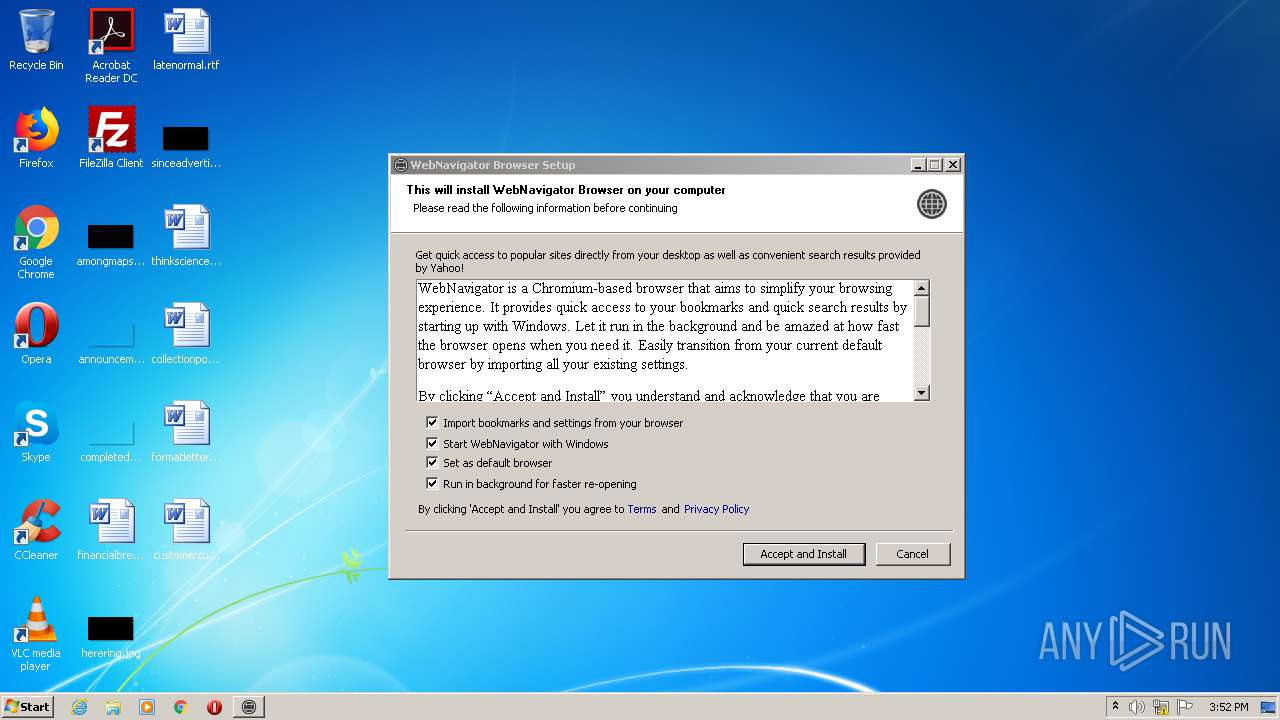
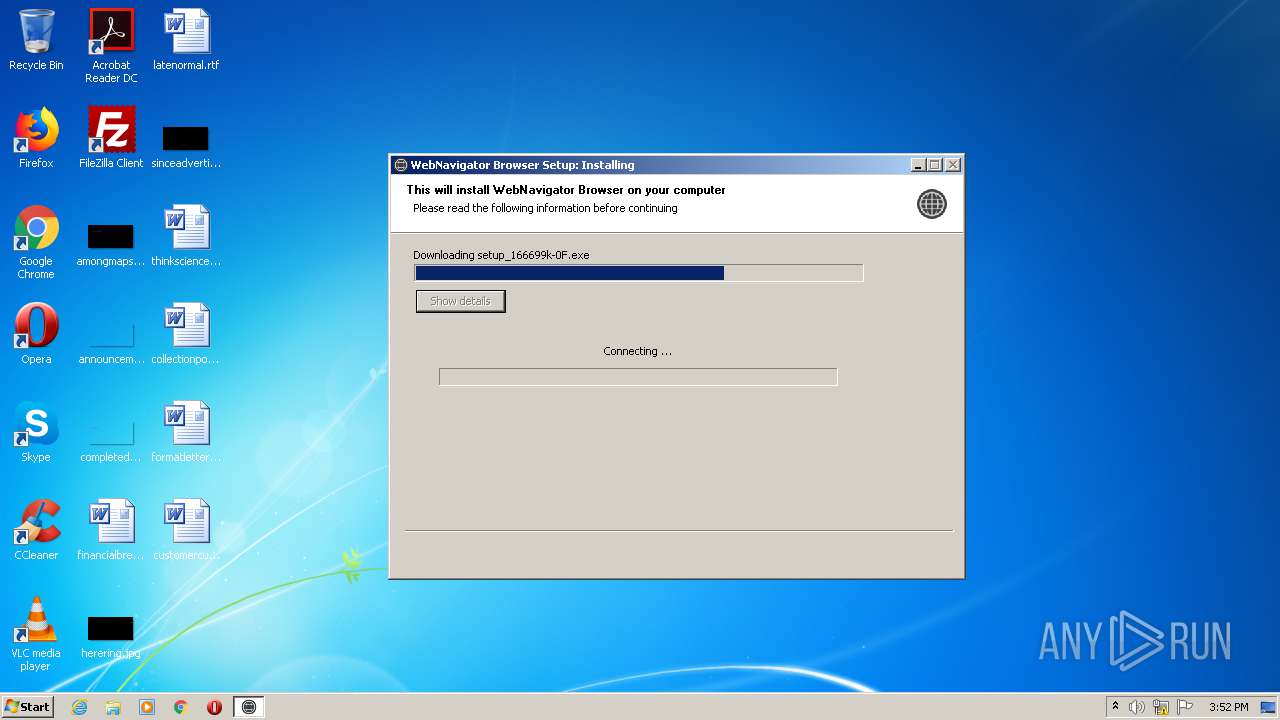
| File name: | Click HERE to start the WebNavigator Browser Installer_166699k_.exe |
| Full analysis: | https://app.any.run/tasks/acd2df85-3240-4dc6-94cb-52b2ed10f0a1 |
| Verdict: | Malicious activity |
| Analysis date: | September 04, 2020, 14:51:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 2FB8F187D5C181FAD90FEE57267C4A58 |
| SHA1: | F0710A45F05D0E65A46861561891351246D1F47E |
| SHA256: | 3ACE4CC2E440B30E39307EFC6980F713DB7FFC99E37AA648A293CFE40C72734D |
| SSDEEP: | 3072:PHyUVnSxLlPMcN9RISgyfAAsXdvtjYdNwbl6e5OgyE0Hnr:Pwrp//sMNCy/nr |
MALICIOUS
Loads dropped or rewritten executable
- Click HERE to start the WebNavigator Browser Installer_166699k_.exe (PID: 2668)
SUSPICIOUS
Reads Internet Cache Settings
- Click HERE to start the WebNavigator Browser Installer_166699k_.exe (PID: 2668)
Executable content was dropped or overwritten
- Click HERE to start the WebNavigator Browser Installer_166699k_.exe (PID: 2668)
INFO
Reads settings of System Certificates
- Click HERE to start the WebNavigator Browser Installer_166699k_.exe (PID: 2668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 23:24:22+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24576 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x31d6 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.0.6 |
| ProductVersionNumber: | 2.2.0.6 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Better Cloud Solutions Ltd |
| FileDescription: | Installer of WebNavigator Browser |
| FileVersion: | 2.2.0.6 |
| LegalCopyright: | Copyright 2020 Better Cloud Solutions Ltd. All rights reserved. |
| OriginalFileName: | BrowserInstaller |
| ProductName: | WebNavigator Browser Setup |
| ProductVersion: | 2.2.0.6 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:24:22 |
| Detected languages: |
|
| CompanyName: | Better Cloud Solutions Ltd |
| FileDescription: | Installer of WebNavigator Browser |
| FileVersion: | 2.2.0.6 |
| LegalCopyright: | Copyright 2020 Better Cloud Solutions Ltd. All rights reserved. |
| OriginalFilename: | BrowserInstaller |
| ProductName: | WebNavigator Browser Setup |
| ProductVersion: | 2.2.0.6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:24:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005F0D | 0x00006000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45039 |
.rdata | 0x00007000 | 0x00001250 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00109 |
.data | 0x00009000 | 0x0001A818 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.12959 |
.ndata | 0x00024000 | 0x00016000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003A000 | 0x000059A0 | 0x00005A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.19341 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29611 | 1059 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 0 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 0 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 0 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 3.05969 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.89384 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
36
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2668 | "C:\Users\admin\AppData\Local\Temp\Click HERE to start the WebNavigator Browser Installer_166699k_.exe" | C:\Users\admin\AppData\Local\Temp\Click HERE to start the WebNavigator Browser Installer_166699k_.exe | explorer.exe | ||||||||||||
User: admin Company: Better Cloud Solutions Ltd Integrity Level: MEDIUM Description: Installer of WebNavigator Browser Exit code: 0 Version: 2.2.0.6 Modules
| |||||||||||||||
Total events
423
Read events
399
Write events
24
Delete events
0
Modification events
| (PID) Process: | (2668) Click HERE to start the WebNavigator Browser Installer_166699k_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2668) Click HERE to start the WebNavigator Browser Installer_166699k_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2668) Click HERE to start the WebNavigator Browser Installer_166699k_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2668) Click HERE to start the WebNavigator Browser Installer_166699k_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2668) Click HERE to start the WebNavigator Browser Installer_166699k_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2668) Click HERE to start the WebNavigator Browser Installer_166699k_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2668) Click HERE to start the WebNavigator Browser Installer_166699k_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2668) Click HERE to start the WebNavigator Browser Installer_166699k_.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2668) Click HERE to start the WebNavigator Browser Installer_166699k_.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (2668) Click HERE to start the WebNavigator Browser Installer_166699k_.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
Executable files
5
Suspicious files
8
Text files
1
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2668 | Click HERE to start the WebNavigator Browser Installer_166699k_.exe | C:\Users\admin\AppData\Local\Temp\CabDC95.tmp | — | |
MD5:— | SHA256:— | |||
| 2668 | Click HERE to start the WebNavigator Browser Installer_166699k_.exe | C:\Users\admin\AppData\Local\Temp\TarDC96.tmp | — | |
MD5:— | SHA256:— | |||
| 2668 | Click HERE to start the WebNavigator Browser Installer_166699k_.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:— | SHA256:— | |||
| 2668 | Click HERE to start the WebNavigator Browser Installer_166699k_.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | binary | |
MD5:— | SHA256:— | |||
| 2668 | Click HERE to start the WebNavigator Browser Installer_166699k_.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | binary | |
MD5:— | SHA256:— | |||
| 2668 | Click HERE to start the WebNavigator Browser Installer_166699k_.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\FC5A820A001B41D68902E051F36A5282_BD3589638B587B731676265DC43933CA | binary | |
MD5:— | SHA256:— | |||
| 2668 | Click HERE to start the WebNavigator Browser Installer_166699k_.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_93E4B2BA79A897B3100CCB27F2D3BF4F | der | |
MD5:— | SHA256:— | |||
| 2668 | Click HERE to start the WebNavigator Browser Installer_166699k_.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\75CA58072B9926F763A91F0CC2798706_93E4B2BA79A897B3100CCB27F2D3BF4F | binary | |
MD5:— | SHA256:— | |||
| 2668 | Click HERE to start the WebNavigator Browser Installer_166699k_.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\FC5A820A001B41D68902E051F36A5282_BD3589638B587B731676265DC43933CA | der | |
MD5:— | SHA256:— | |||
| 2668 | Click HERE to start the WebNavigator Browser Installer_166699k_.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
6
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2668 | Click HERE to start the WebNavigator Browser Installer_166699k_.exe | GET | 200 | 13.35.253.198:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
2668 | Click HERE to start the WebNavigator Browser Installer_166699k_.exe | GET | 200 | 13.35.253.198:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
2668 | Click HERE to start the WebNavigator Browser Installer_166699k_.exe | GET | 200 | 143.204.208.79:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
2668 | Click HERE to start the WebNavigator Browser Installer_166699k_.exe | GET | 200 | 143.204.208.79:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEASEMKM1GT%2BI%2BAQQadgL9bQ%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2668 | Click HERE to start the WebNavigator Browser Installer_166699k_.exe | 3.20.70.173:443 | download.webnavigator.co | — | US | suspicious |
2668 | Click HERE to start the WebNavigator Browser Installer_166699k_.exe | 52.14.221.236:443 | download.webnavigator.co | Amazon.com, Inc. | US | suspicious |
2668 | Click HERE to start the WebNavigator Browser Installer_166699k_.exe | 143.204.208.79:80 | o.ss2.us | — | US | whitelisted |
2668 | Click HERE to start the WebNavigator Browser Installer_166699k_.exe | 13.35.253.198:80 | ocsp.rootg2.amazontrust.com | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.webnavigator.co |
| suspicious |
dns.msftncsi.com |
| shared |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.sca1b.amazontrust.com |
| whitelisted |