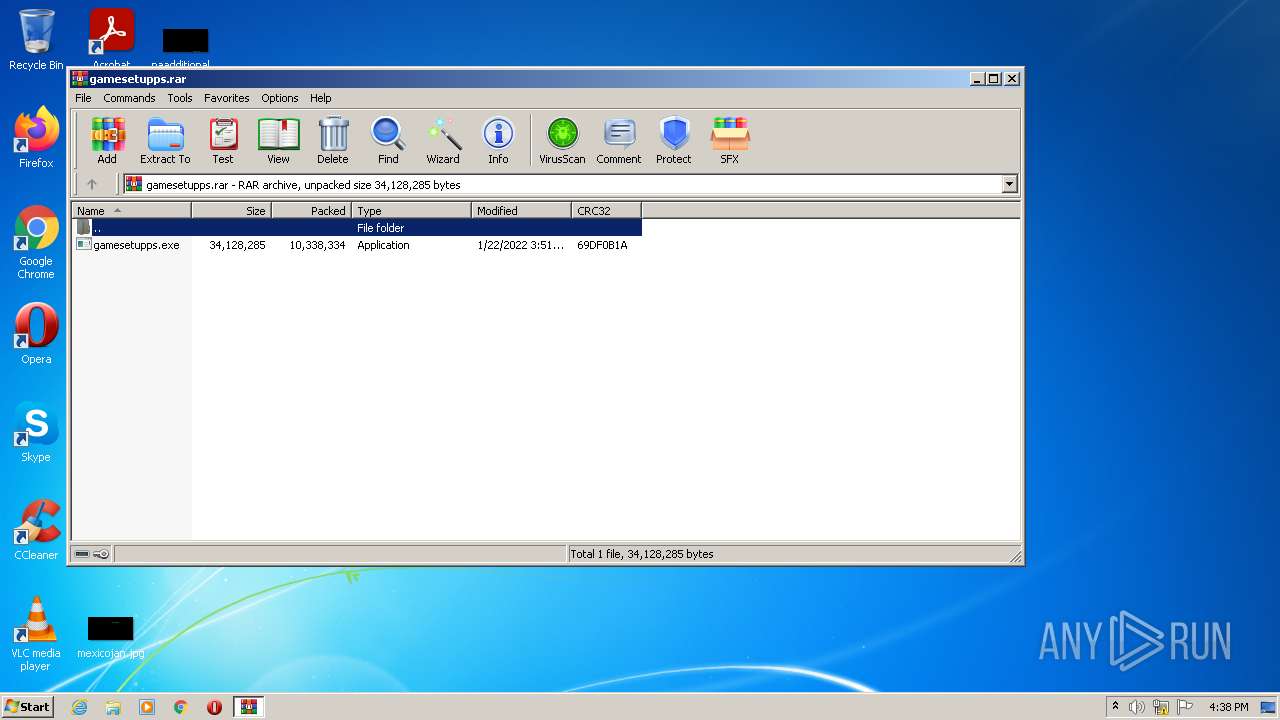
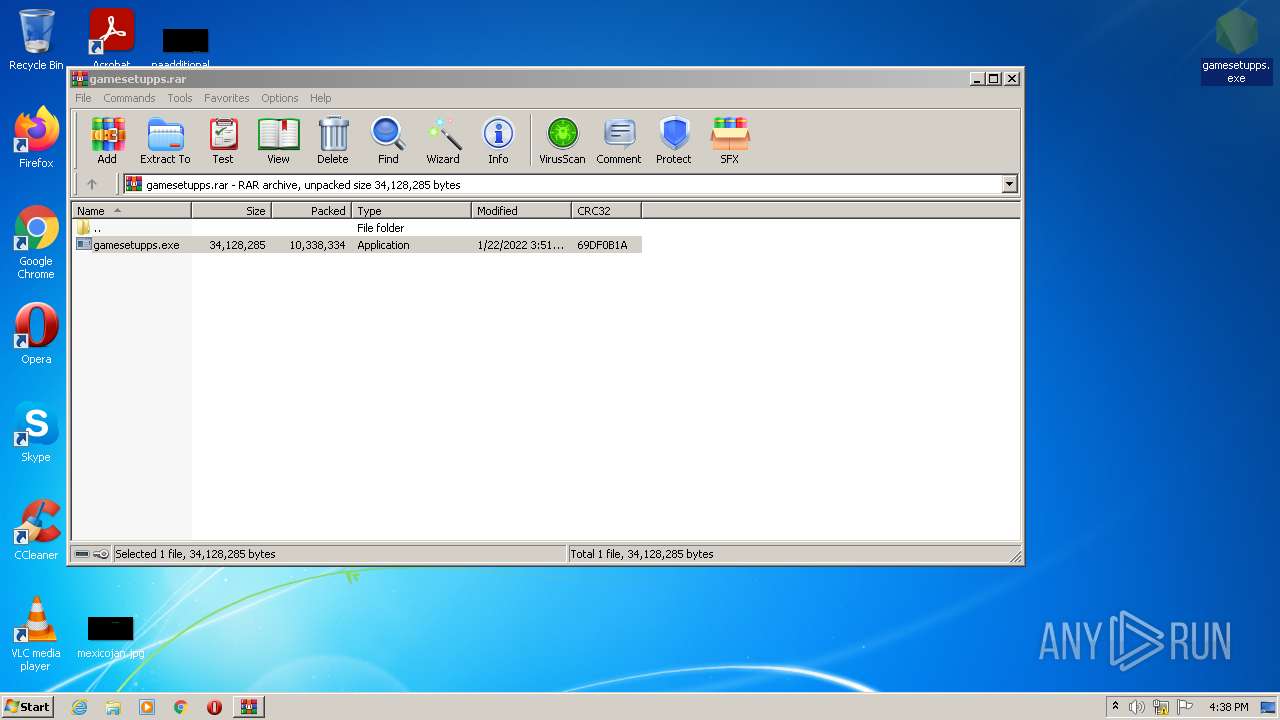
| File name: | gamesetupps.rar |
| Full analysis: | https://app.any.run/tasks/7031542b-64a0-4759-9a66-6e5c49f035b7 |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 16:38:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 9796F1836287C645CD519E9871A01734 |
| SHA1: | 8E9BCF631794503B929D9D47795D7F173CCE61DF |
| SHA256: | 3ACA9B920C88B17EE54CBE48A7BD9D41C8DF1F070190EEEC48B05EF037FD79C2 |
| SSDEEP: | 196608:QJnCLRu0DxSr9YodxM0kOL8C/mKXwJsdLbGj/O0/v0p58mSJVTYg5Ro:QJ6RsrqkdHnPXwaF+/r05BZYRo |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 3520)
Checks supported languages
- WinRAR.exe (PID: 3520)
- notepad++.exe (PID: 480)
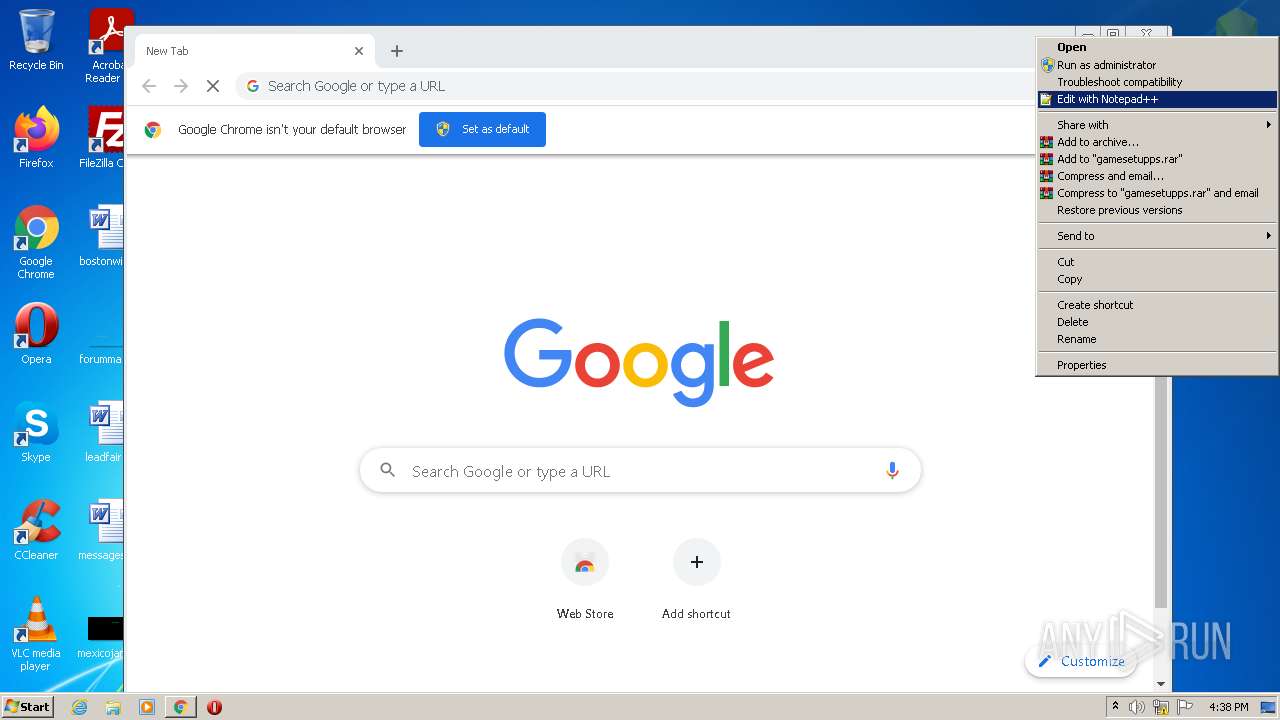
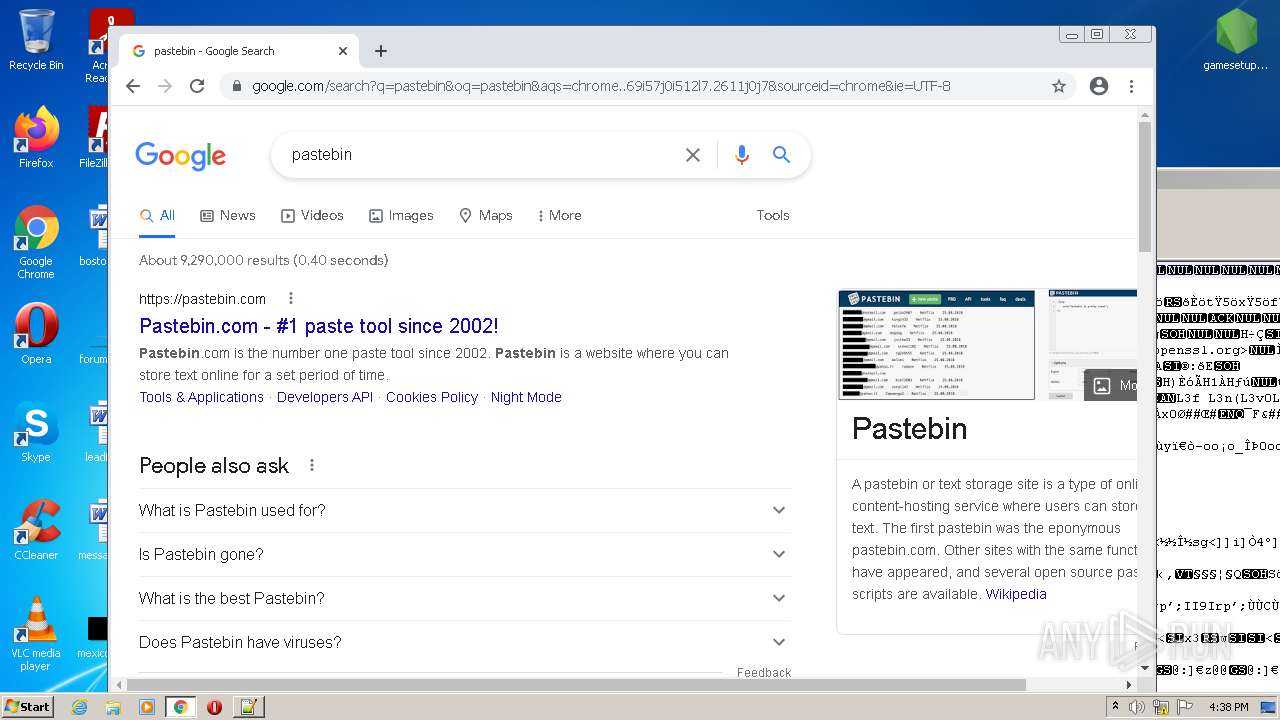
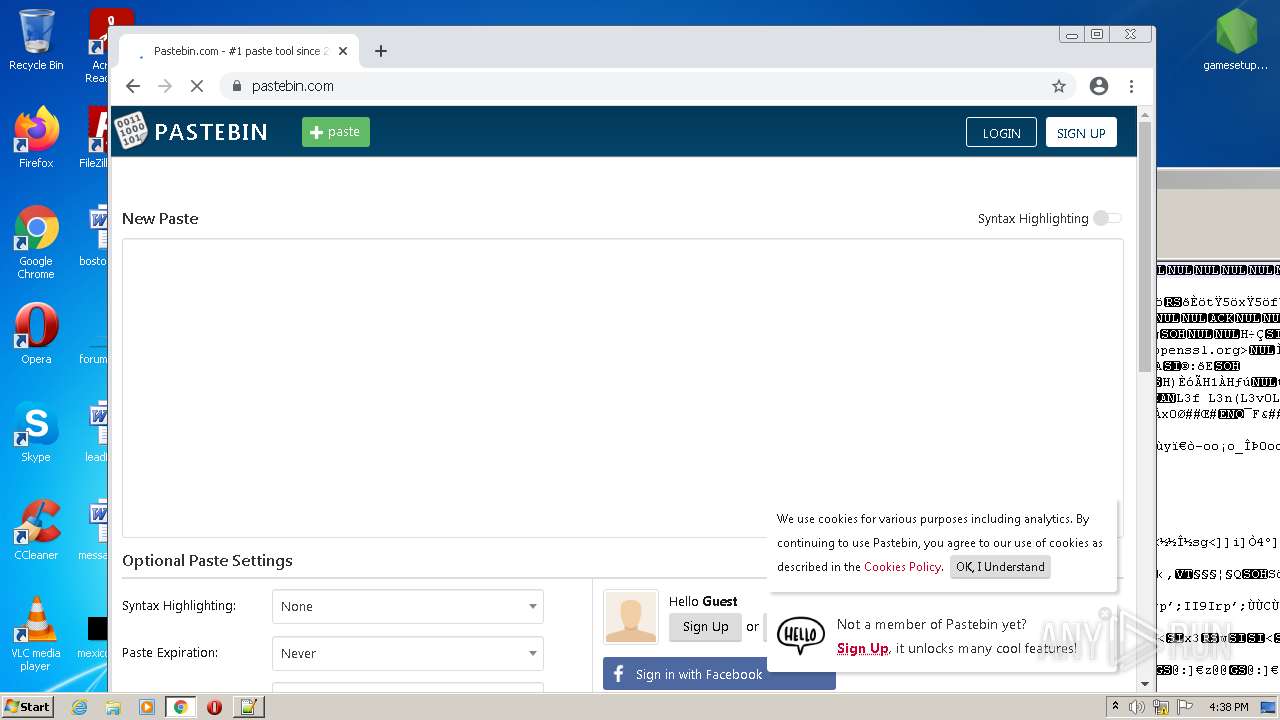
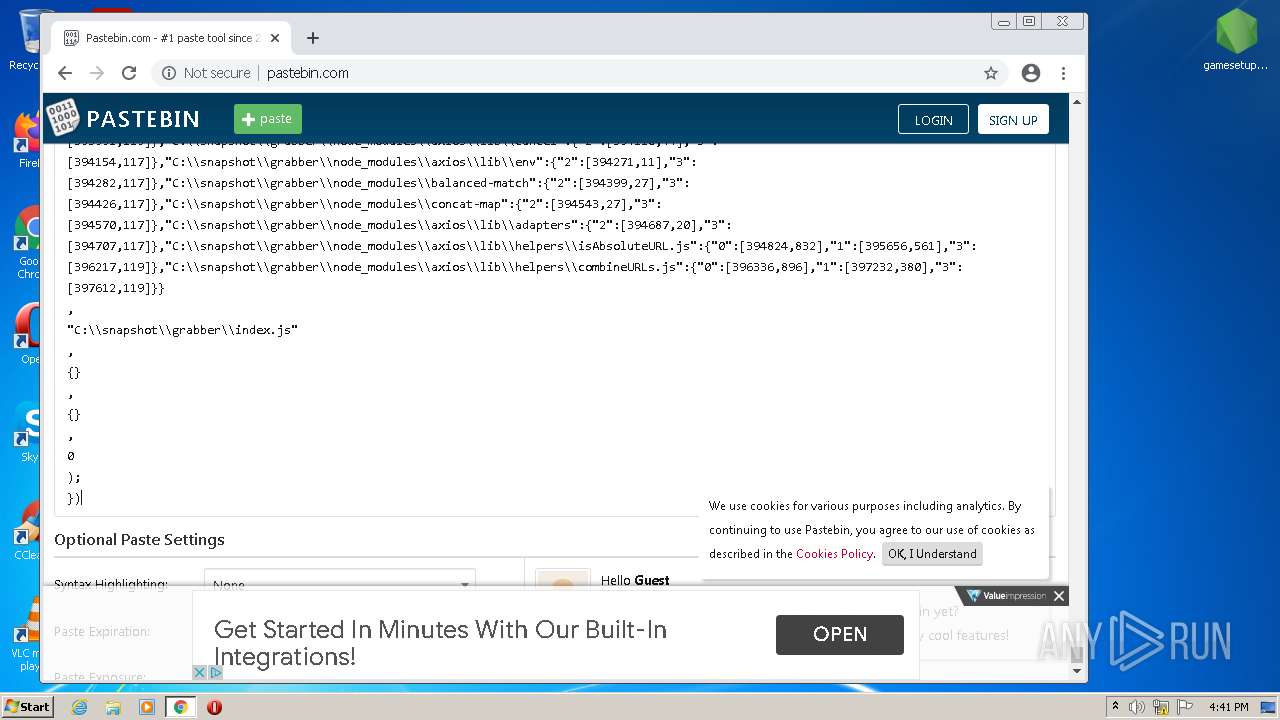
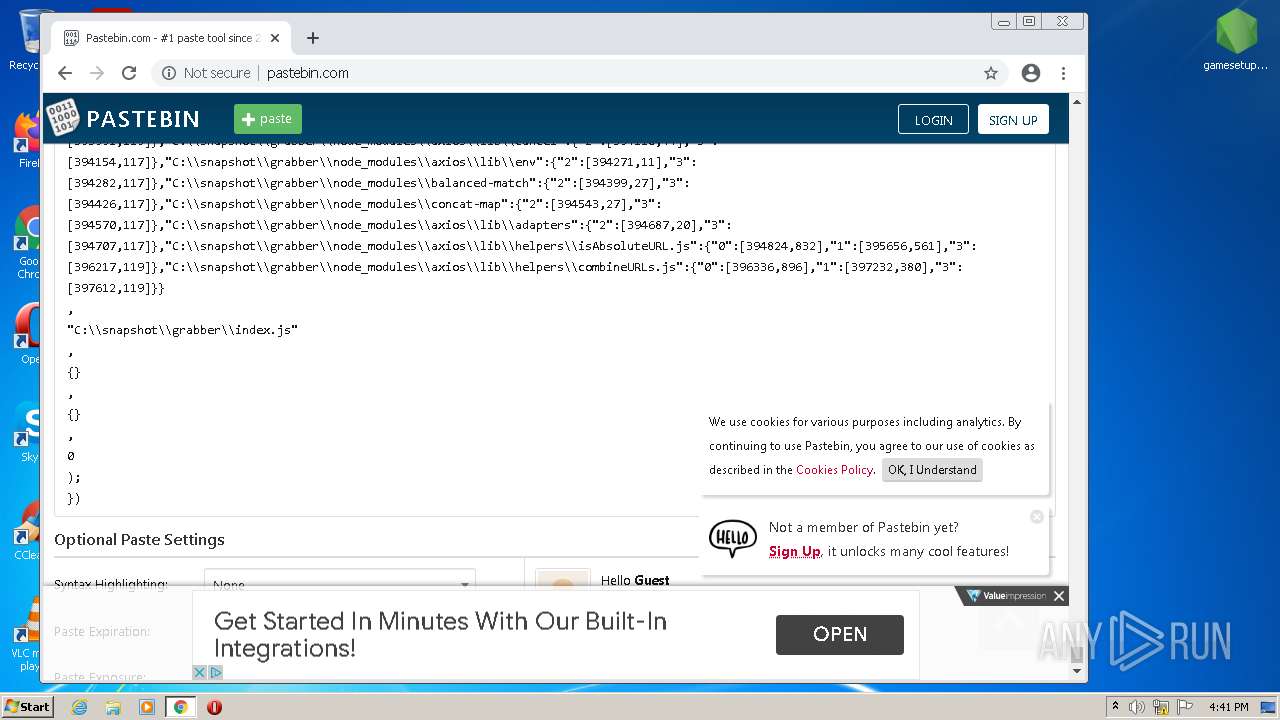
Modifies files in Chrome extension folder
- chrome.exe (PID: 1888)
Creates files in the user directory
- notepad++.exe (PID: 480)
INFO
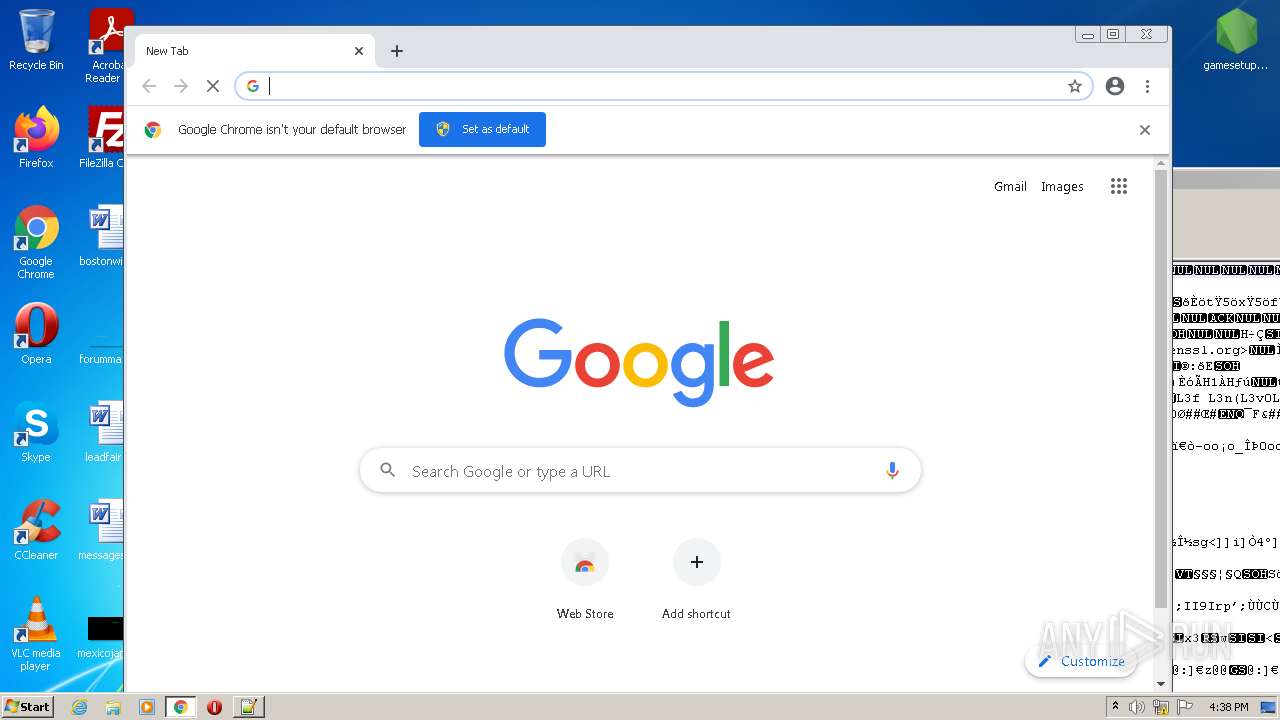
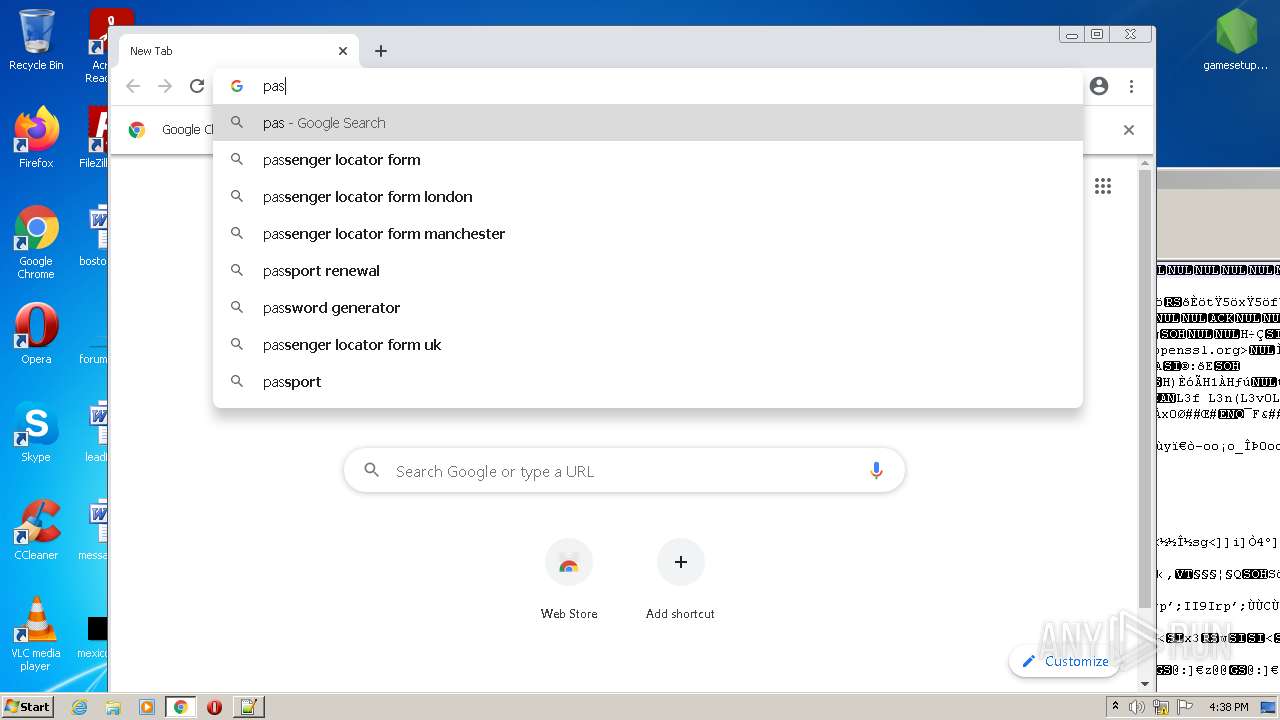
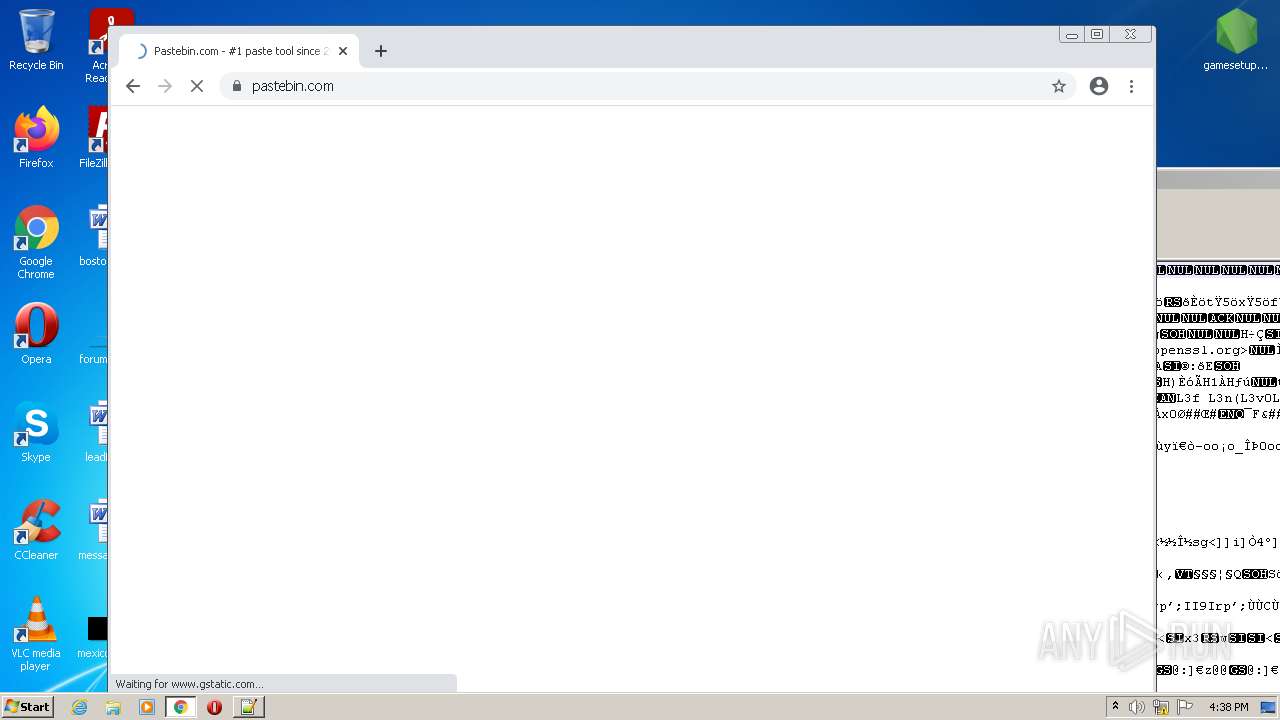
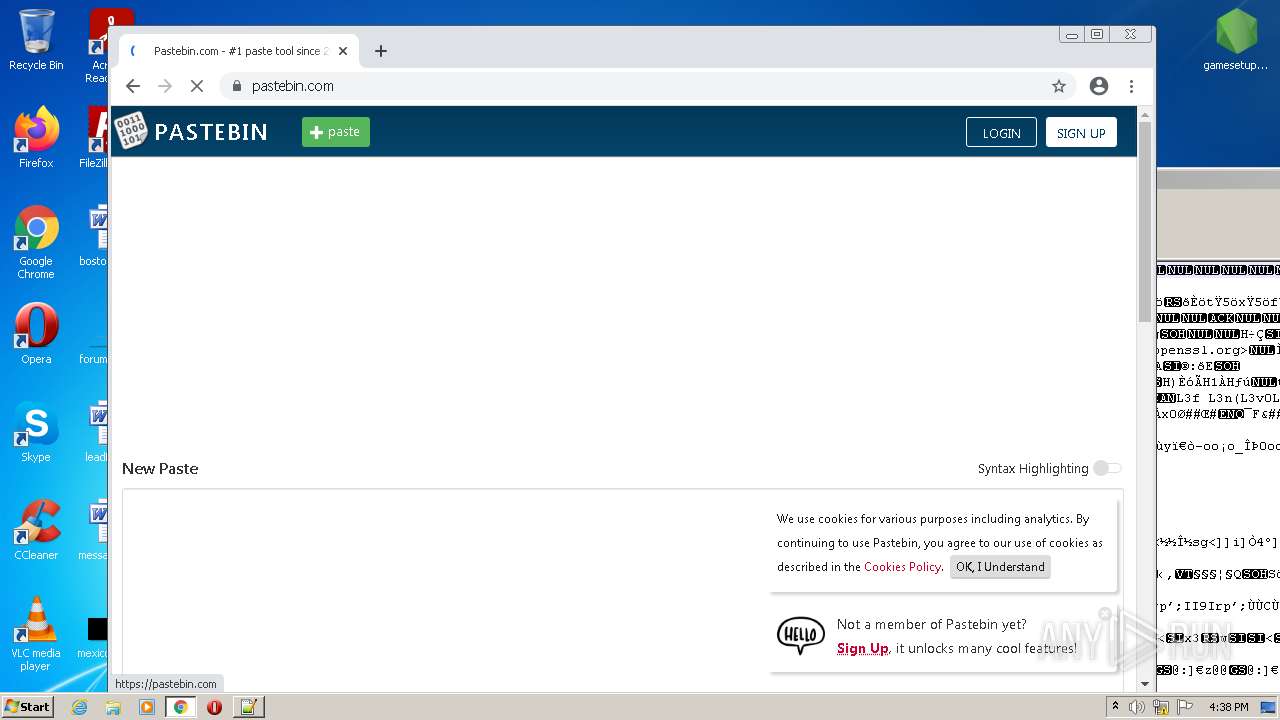
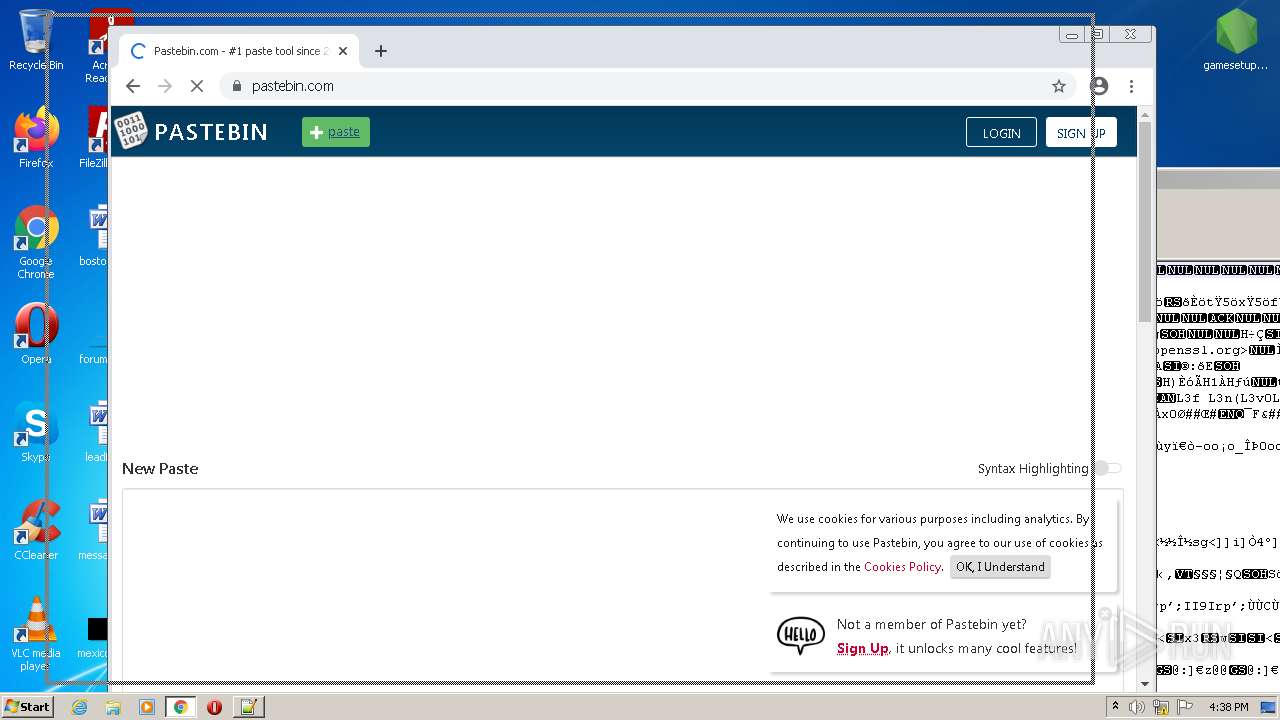
Manual execution by user
- chrome.exe (PID: 1888)
- notepad++.exe (PID: 480)
Checks supported languages
- chrome.exe (PID: 1888)
- chrome.exe (PID: 3516)
- chrome.exe (PID: 1408)
- chrome.exe (PID: 992)
- chrome.exe (PID: 2924)
- chrome.exe (PID: 3360)
- chrome.exe (PID: 3112)
- chrome.exe (PID: 1312)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 2320)
- chrome.exe (PID: 1072)
- chrome.exe (PID: 1968)
- chrome.exe (PID: 2604)
- chrome.exe (PID: 2848)
- chrome.exe (PID: 2628)
- chrome.exe (PID: 3960)
- chrome.exe (PID: 3668)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 2688)
- chrome.exe (PID: 3716)
- chrome.exe (PID: 3192)
- chrome.exe (PID: 1128)
- chrome.exe (PID: 3116)
- chrome.exe (PID: 3504)
- chrome.exe (PID: 1420)
- chrome.exe (PID: 1056)
- chrome.exe (PID: 2836)
- chrome.exe (PID: 2620)
- chrome.exe (PID: 1716)
- chrome.exe (PID: 1896)
- chrome.exe (PID: 2960)
- chrome.exe (PID: 3096)
- chrome.exe (PID: 1256)
- chrome.exe (PID: 3116)
- chrome.exe (PID: 412)
- chrome.exe (PID: 2744)
- chrome.exe (PID: 2316)
- chrome.exe (PID: 3488)
- chrome.exe (PID: 2544)
- chrome.exe (PID: 4076)
- chrome.exe (PID: 3908)
- chrome.exe (PID: 3448)
- chrome.exe (PID: 516)
- chrome.exe (PID: 3812)
- chrome.exe (PID: 2992)
- chrome.exe (PID: 3472)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 3676)
- chrome.exe (PID: 2848)
- chrome.exe (PID: 2452)
- chrome.exe (PID: 3468)
- chrome.exe (PID: 1896)
- chrome.exe (PID: 2176)
- chrome.exe (PID: 3172)
- chrome.exe (PID: 3244)
- chrome.exe (PID: 3616)
- chrome.exe (PID: 268)
- chrome.exe (PID: 3388)
- chrome.exe (PID: 3076)
Reads the computer name
- chrome.exe (PID: 1888)
- chrome.exe (PID: 3516)
- chrome.exe (PID: 3360)
- chrome.exe (PID: 3112)
- chrome.exe (PID: 2688)
- chrome.exe (PID: 2620)
- chrome.exe (PID: 1056)
- chrome.exe (PID: 1716)
- chrome.exe (PID: 3908)
Reads the hosts file
- chrome.exe (PID: 1888)
- chrome.exe (PID: 3360)
Application launched itself
- chrome.exe (PID: 1888)
Reads settings of System Certificates
- chrome.exe (PID: 3360)
Reads the date of Windows installation
- chrome.exe (PID: 1056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
97
Monitored processes
61
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,5086708993159759356,15241780462763305851,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=55 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4412 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,5086708993159759356,15241780462763305851,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2368 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
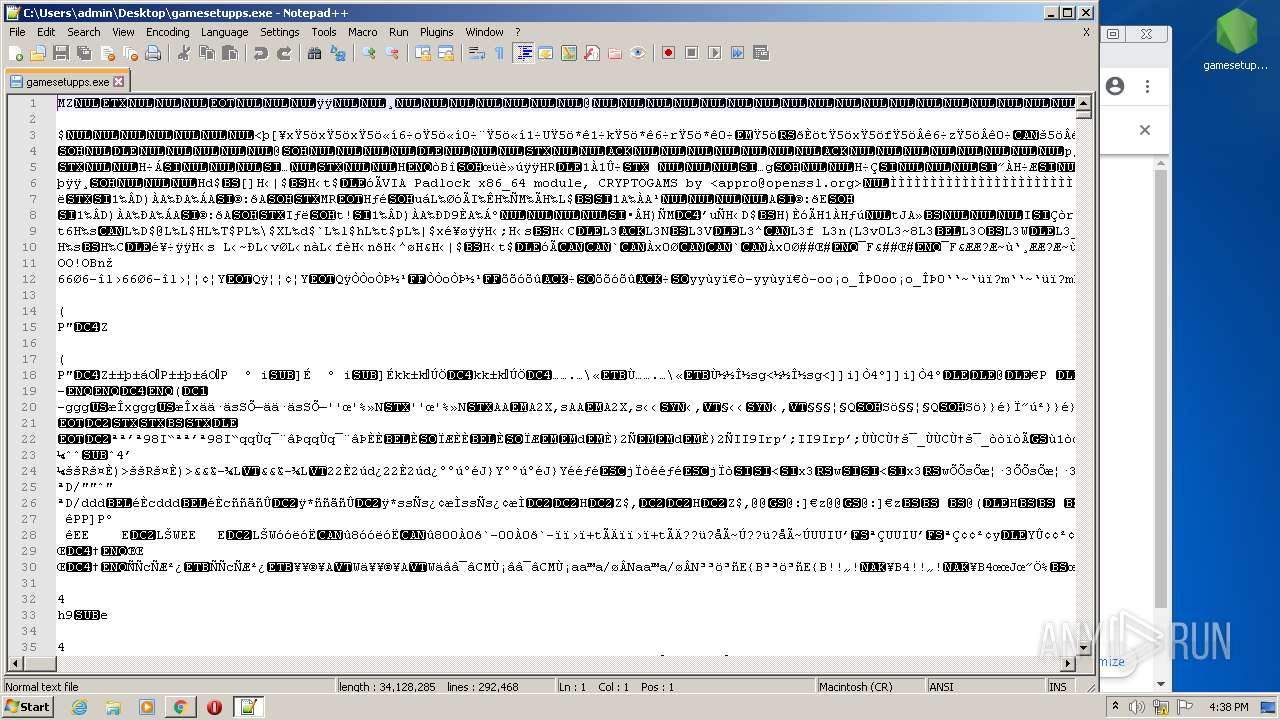
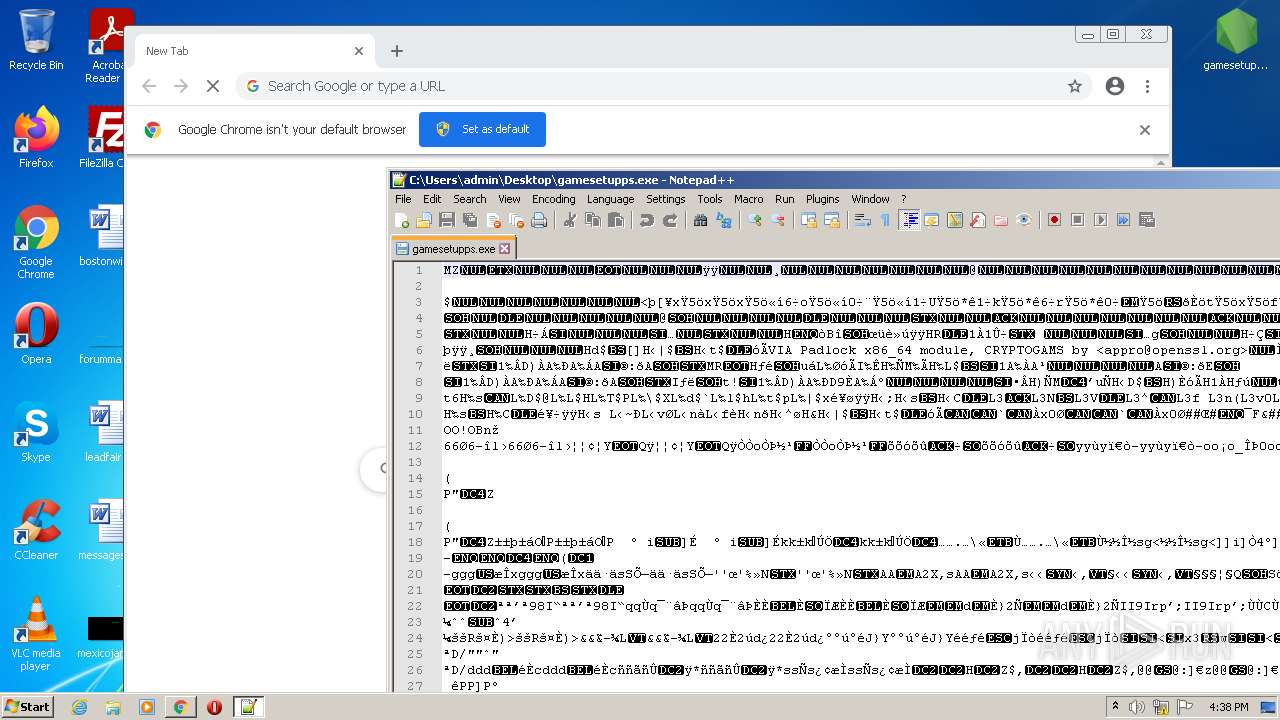
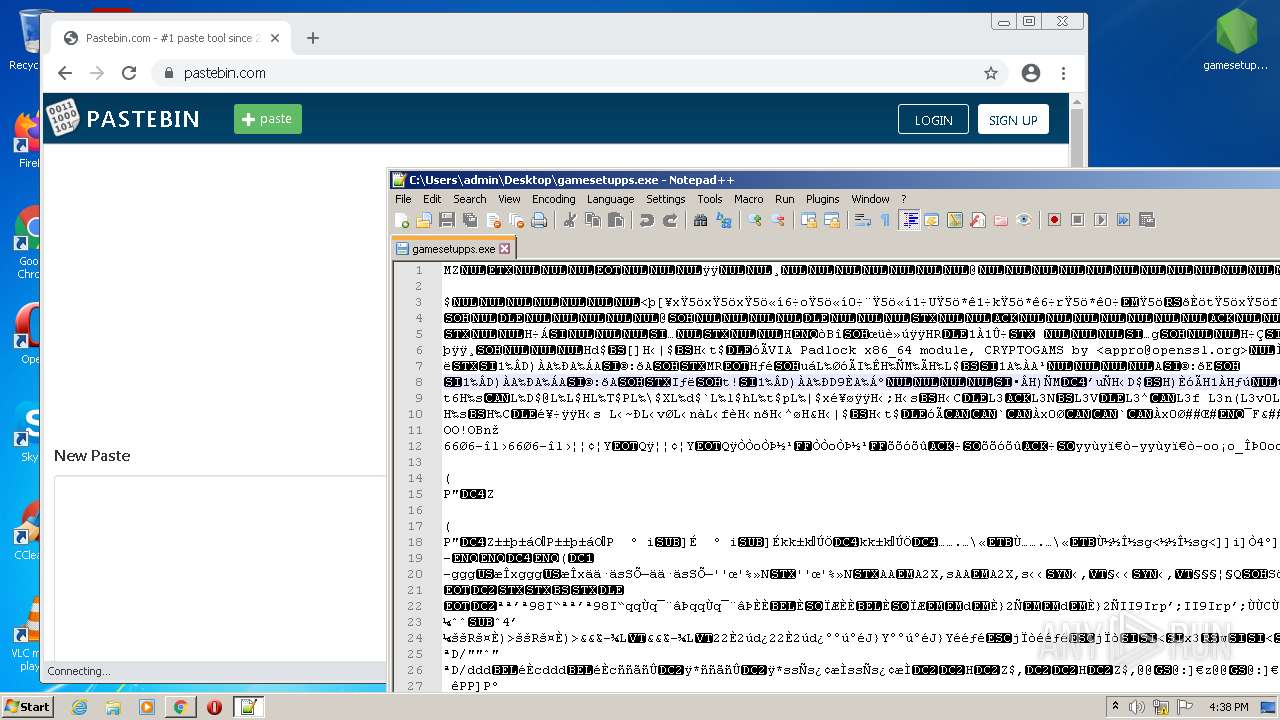
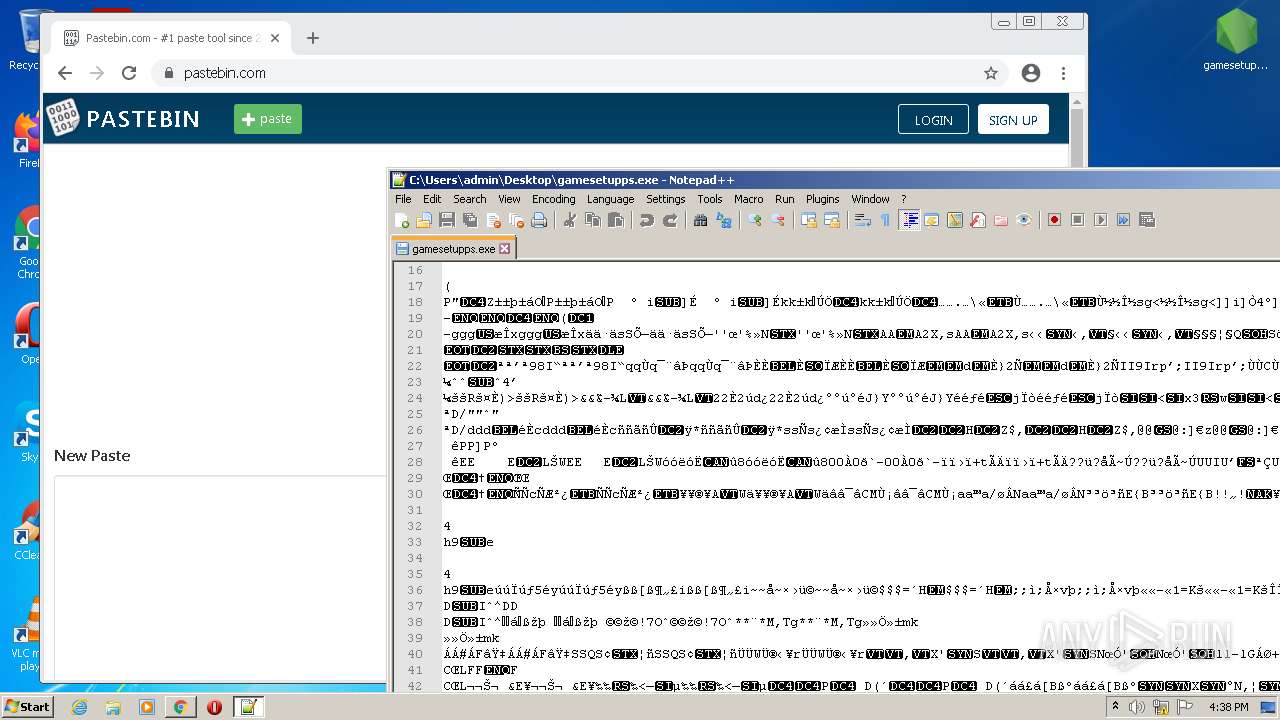
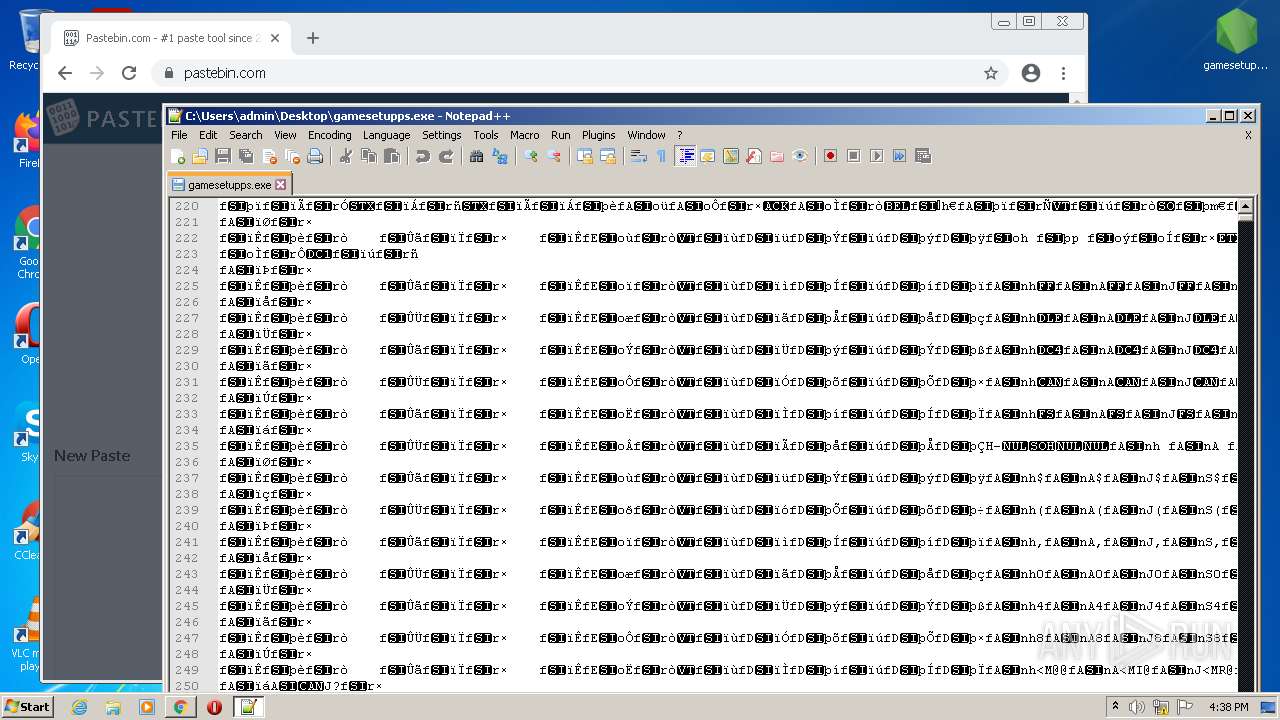
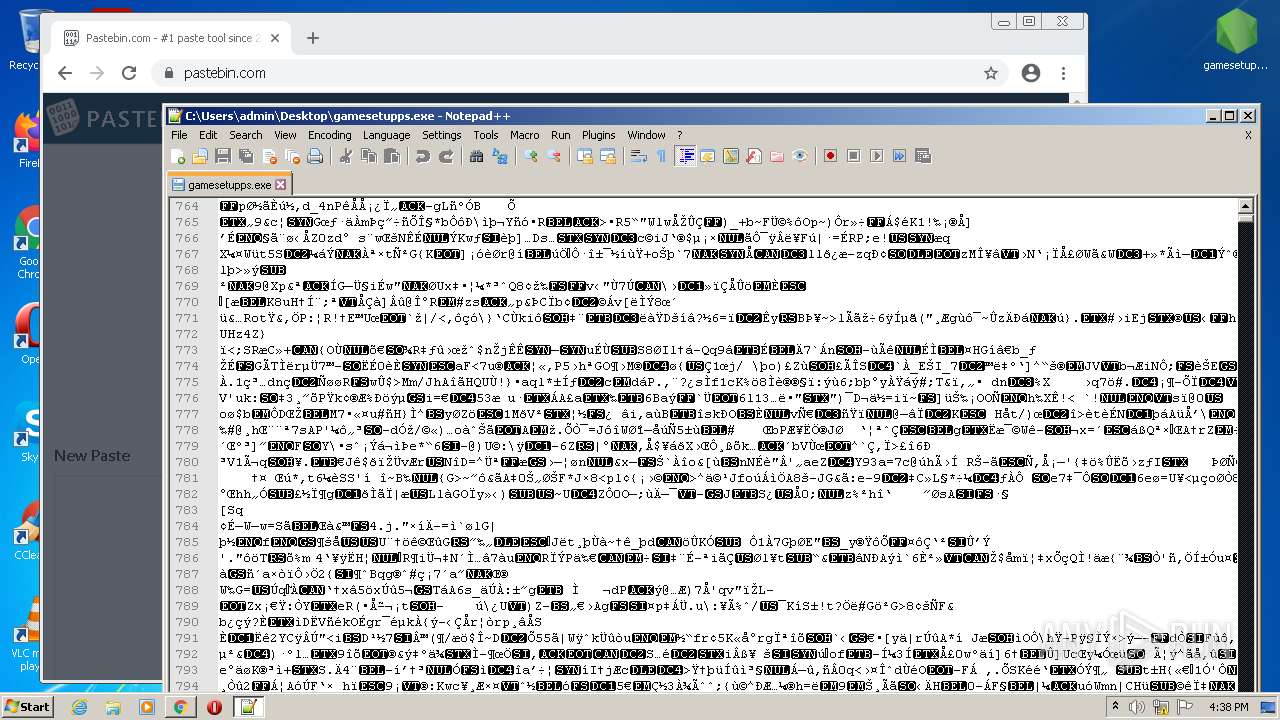
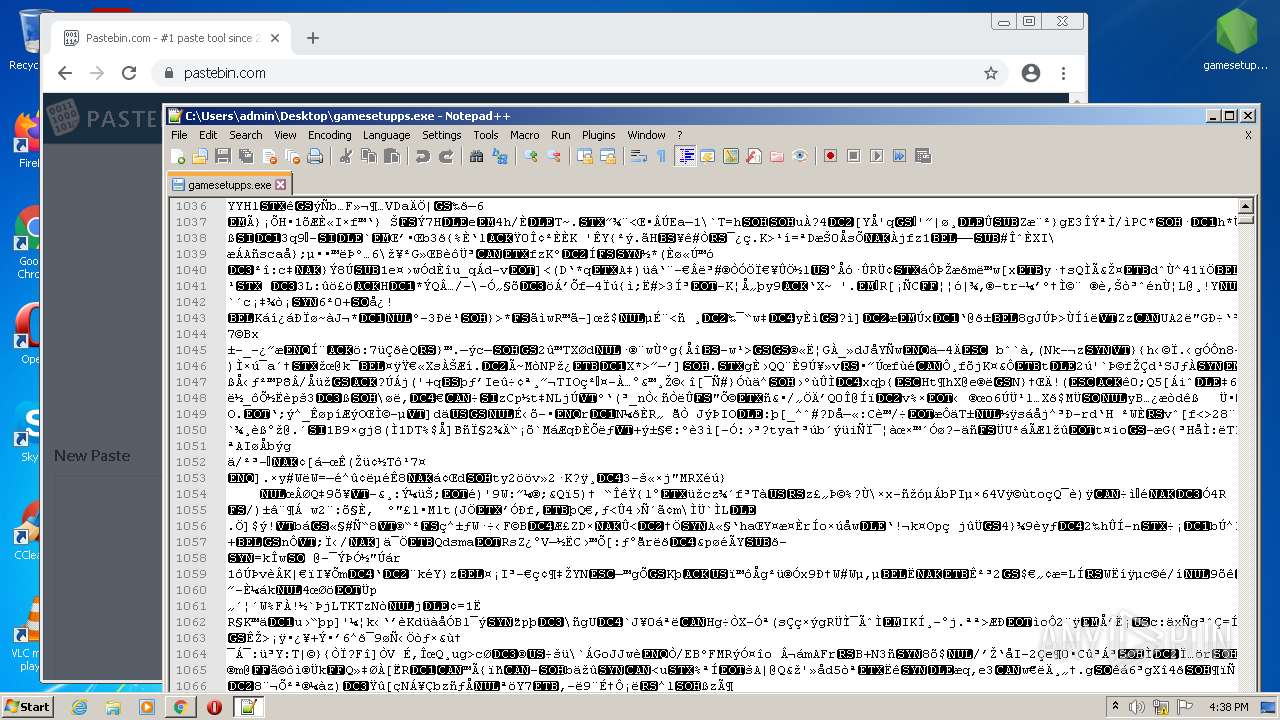
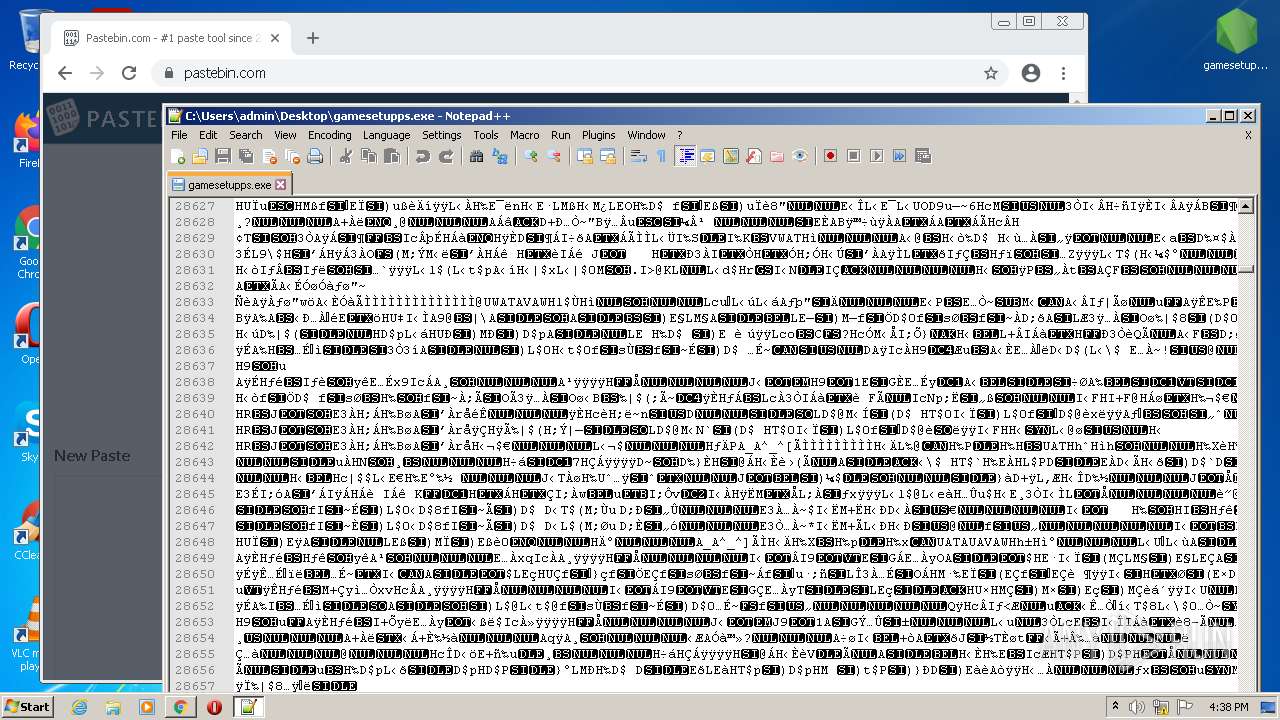
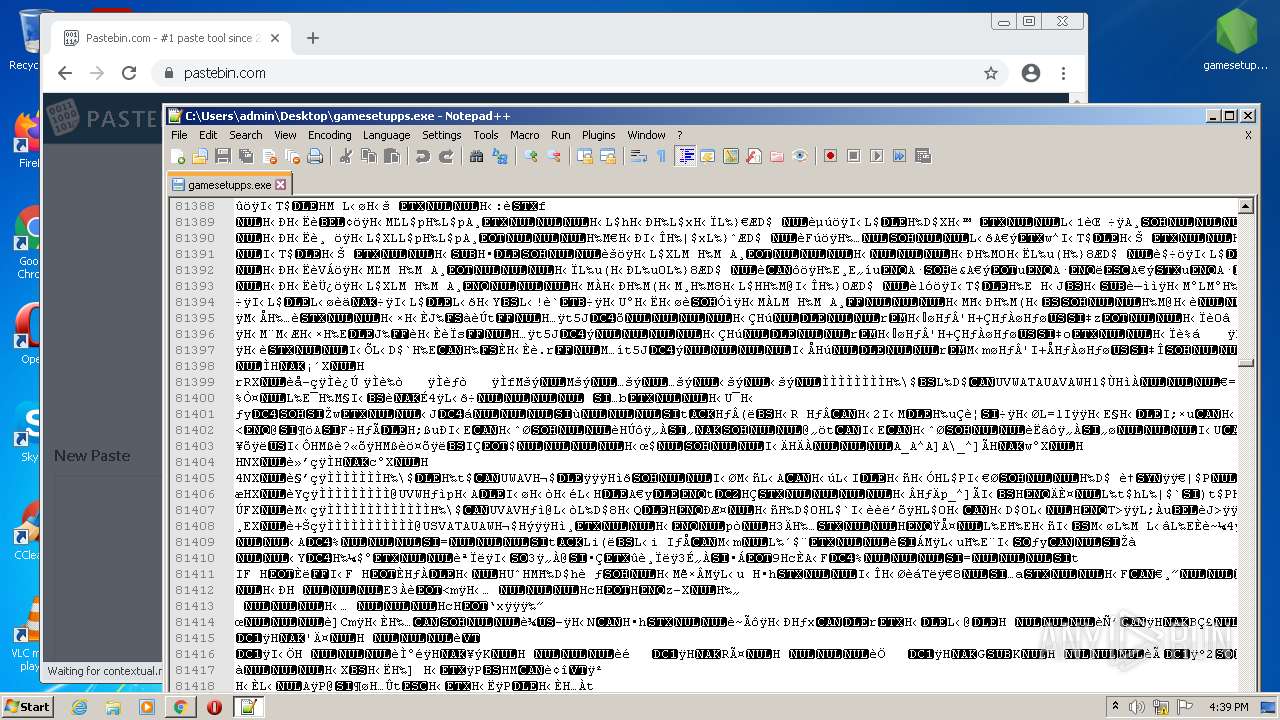
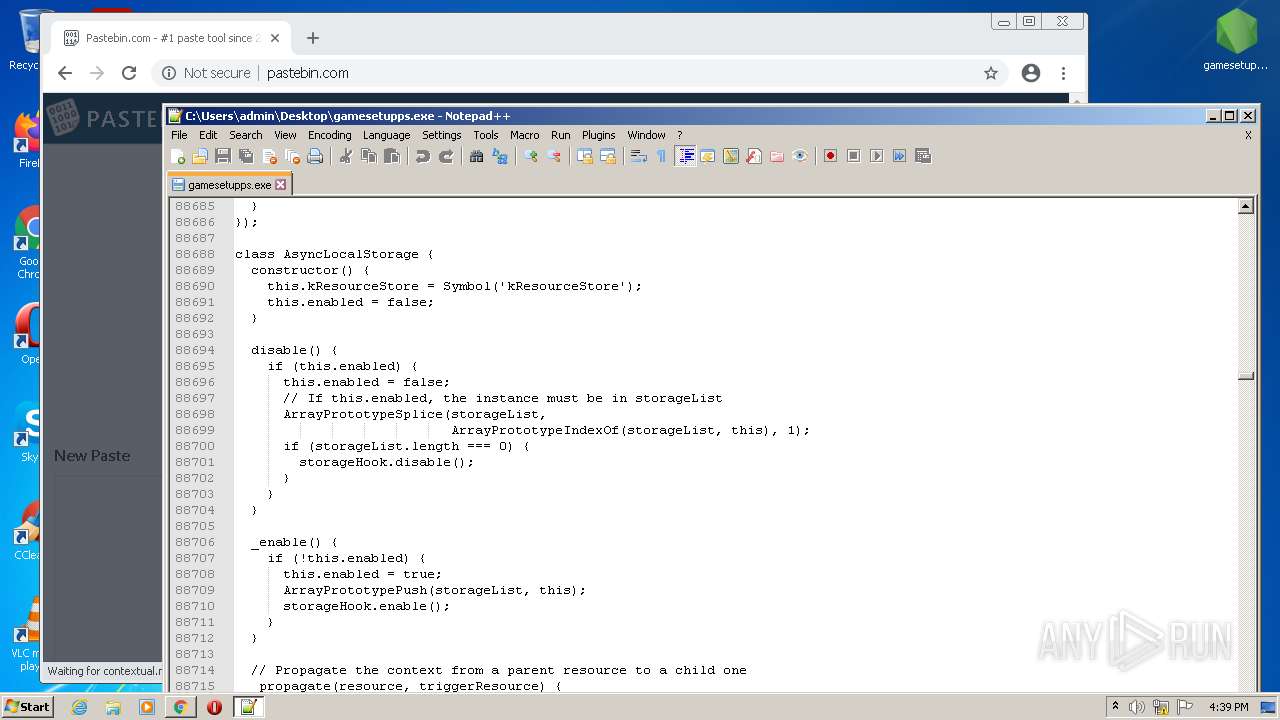
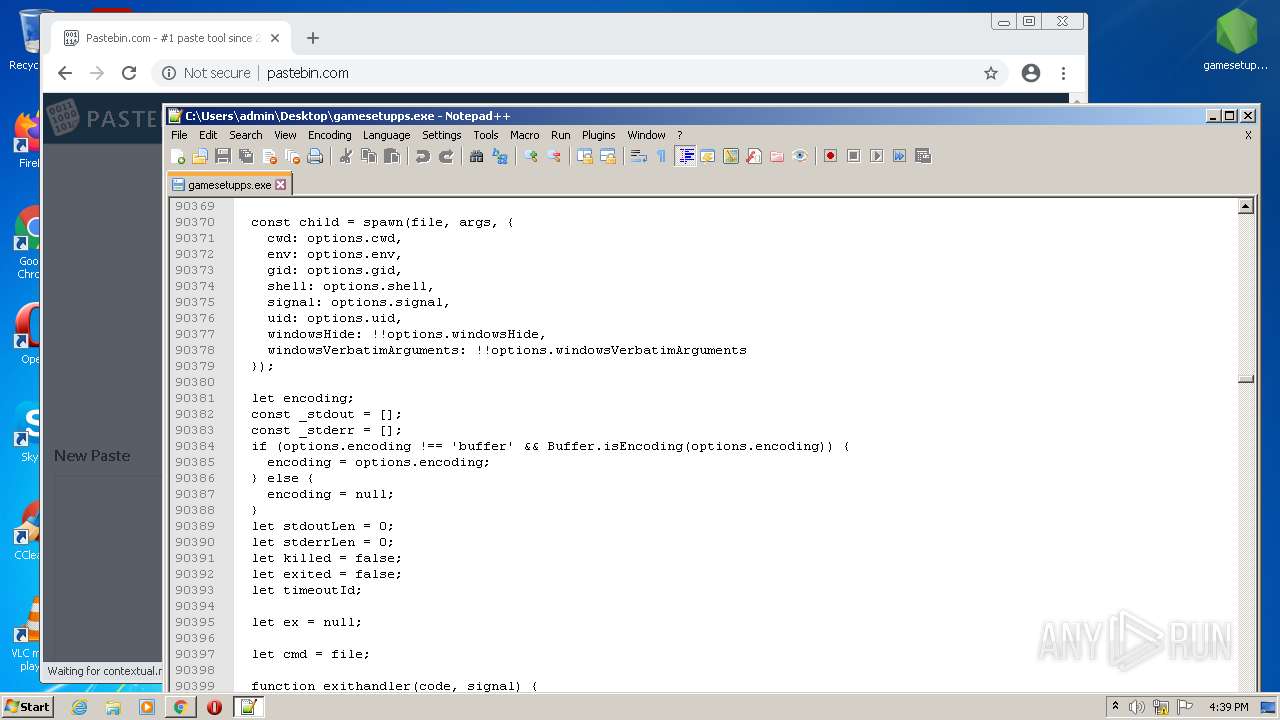
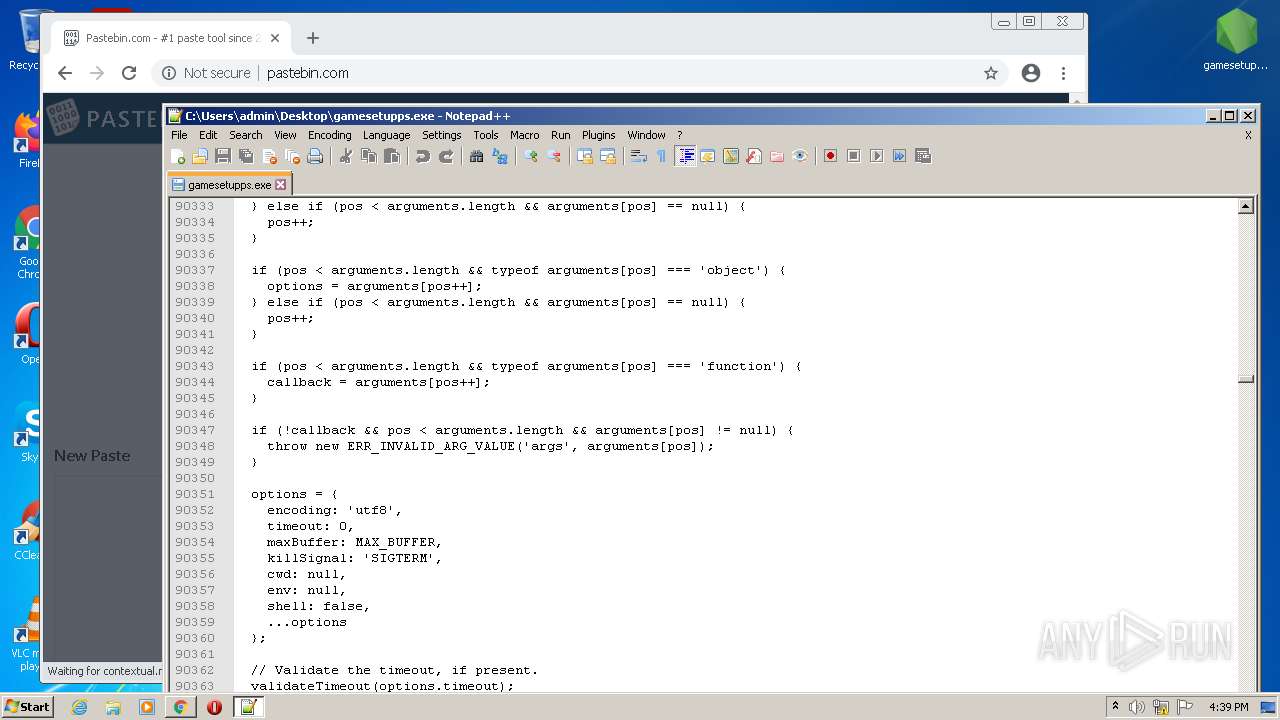
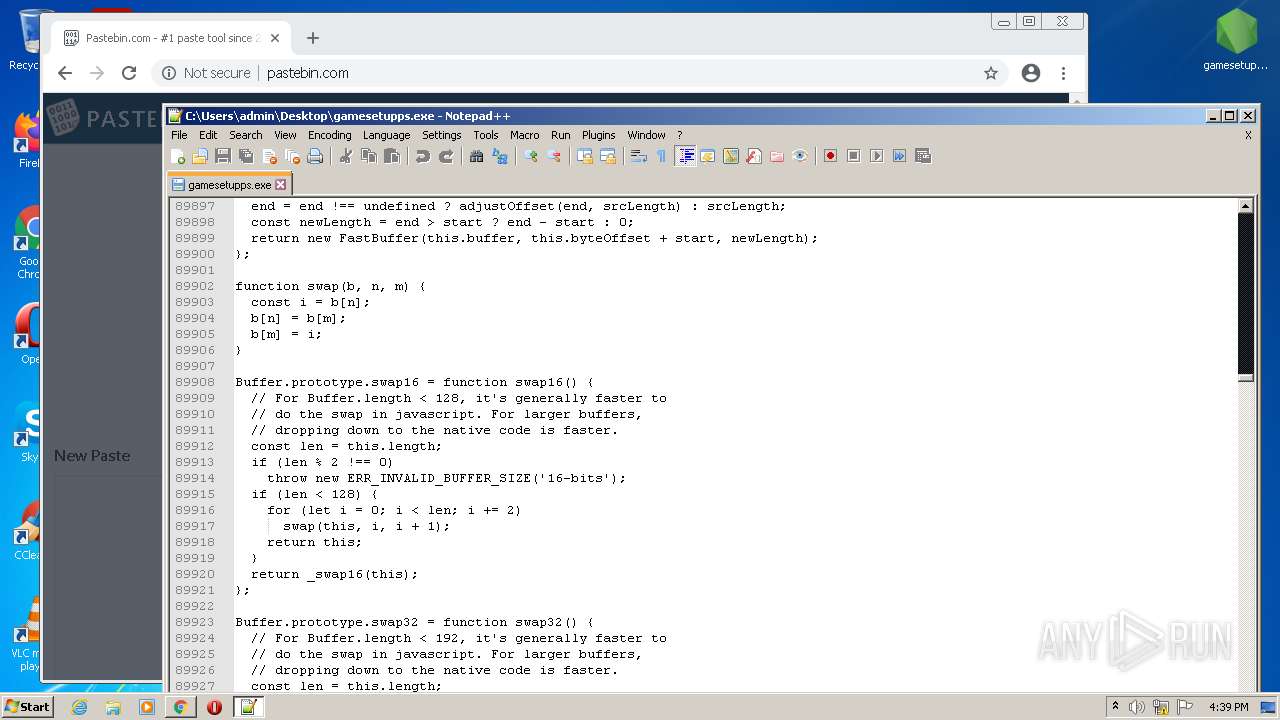
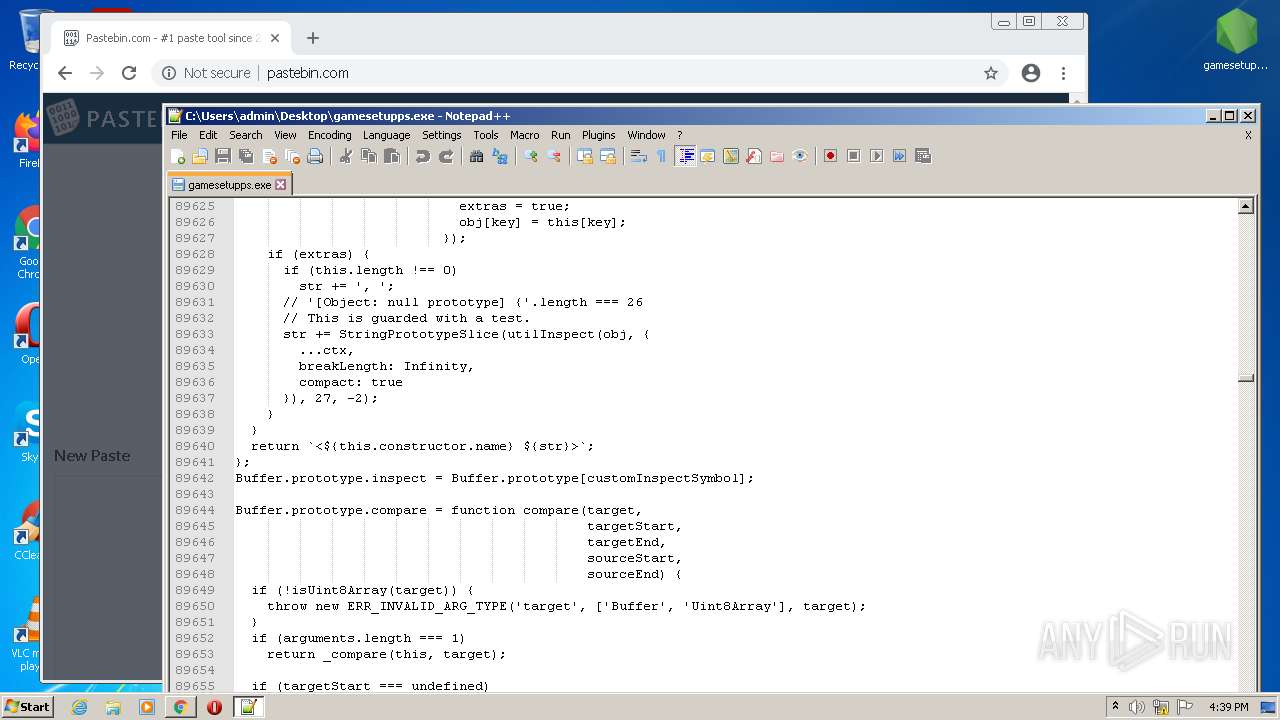
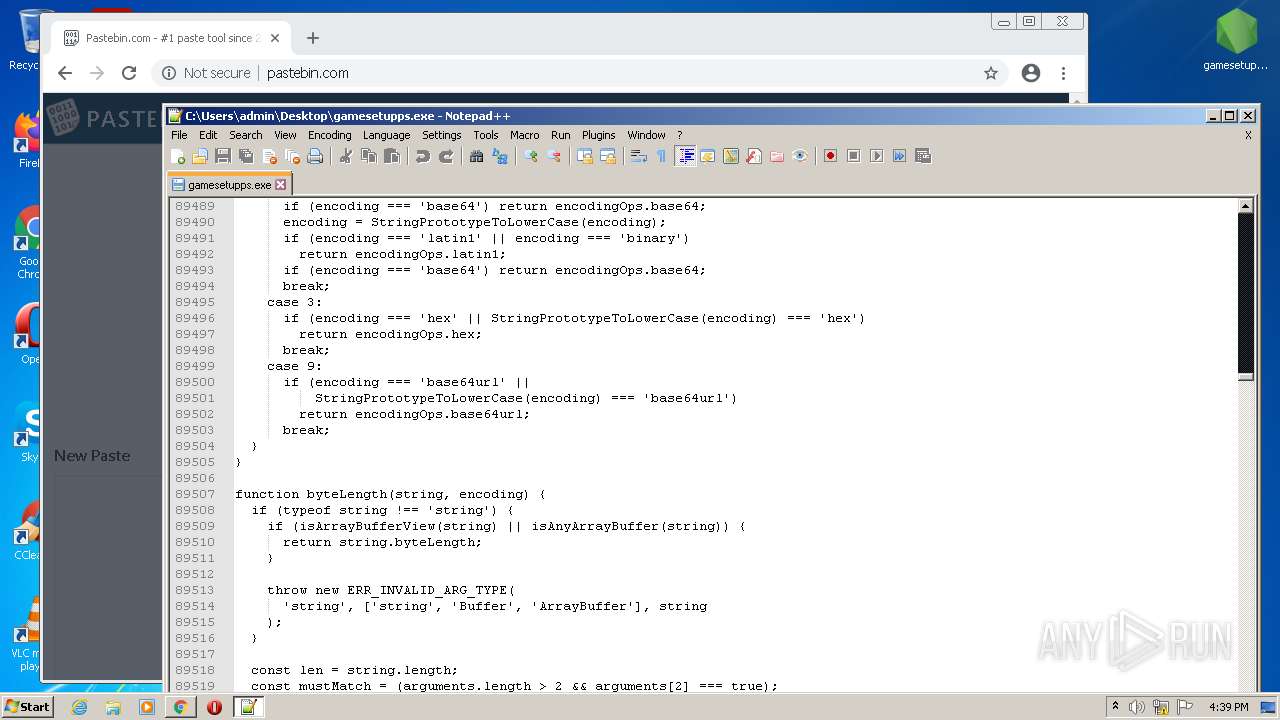
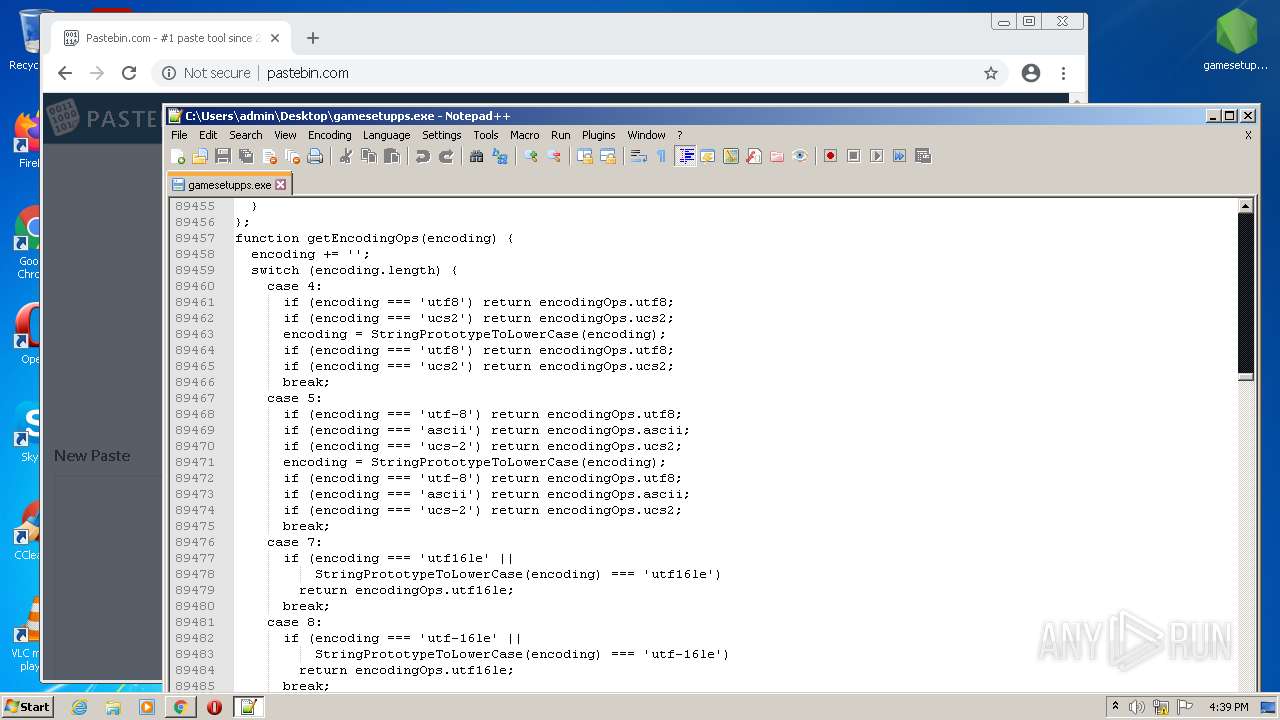
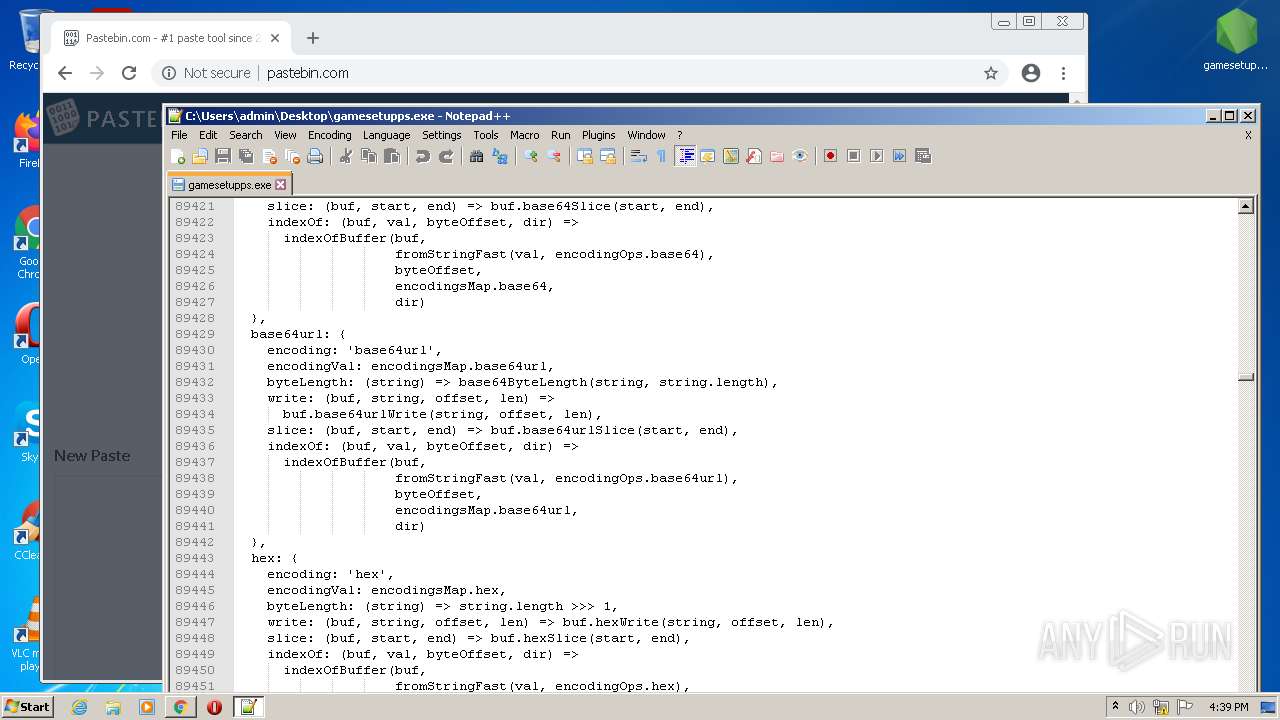
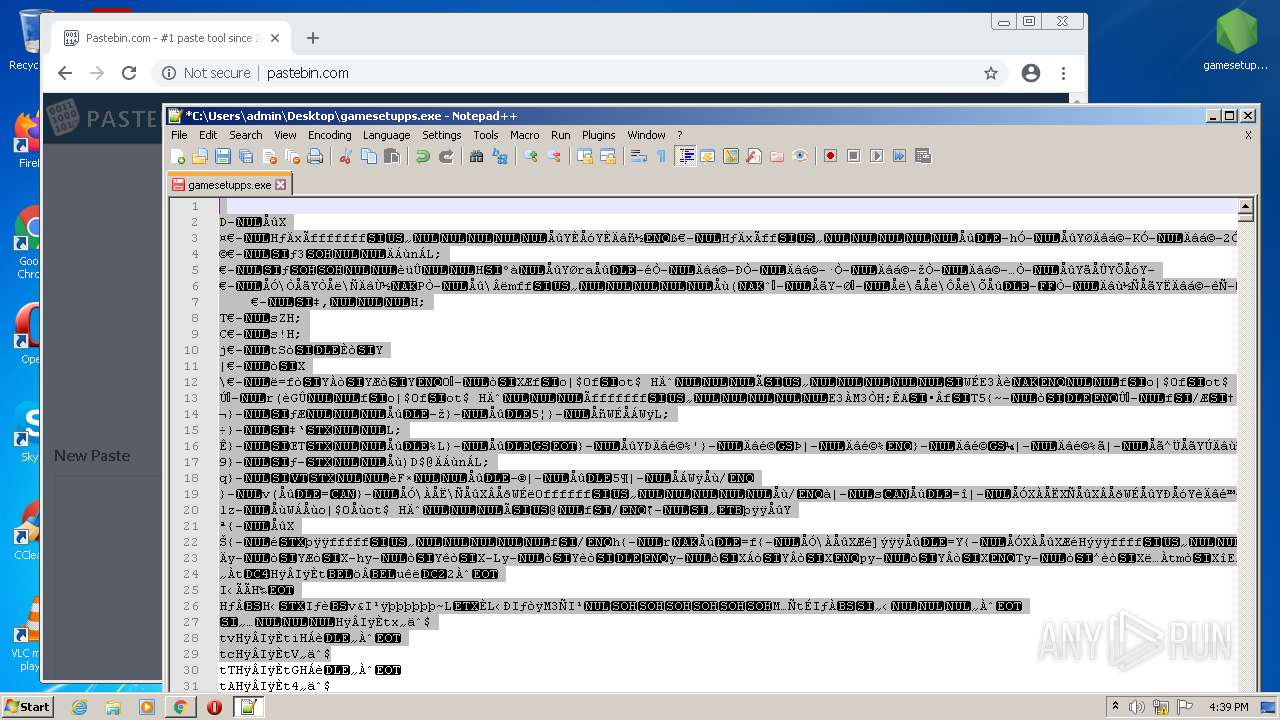
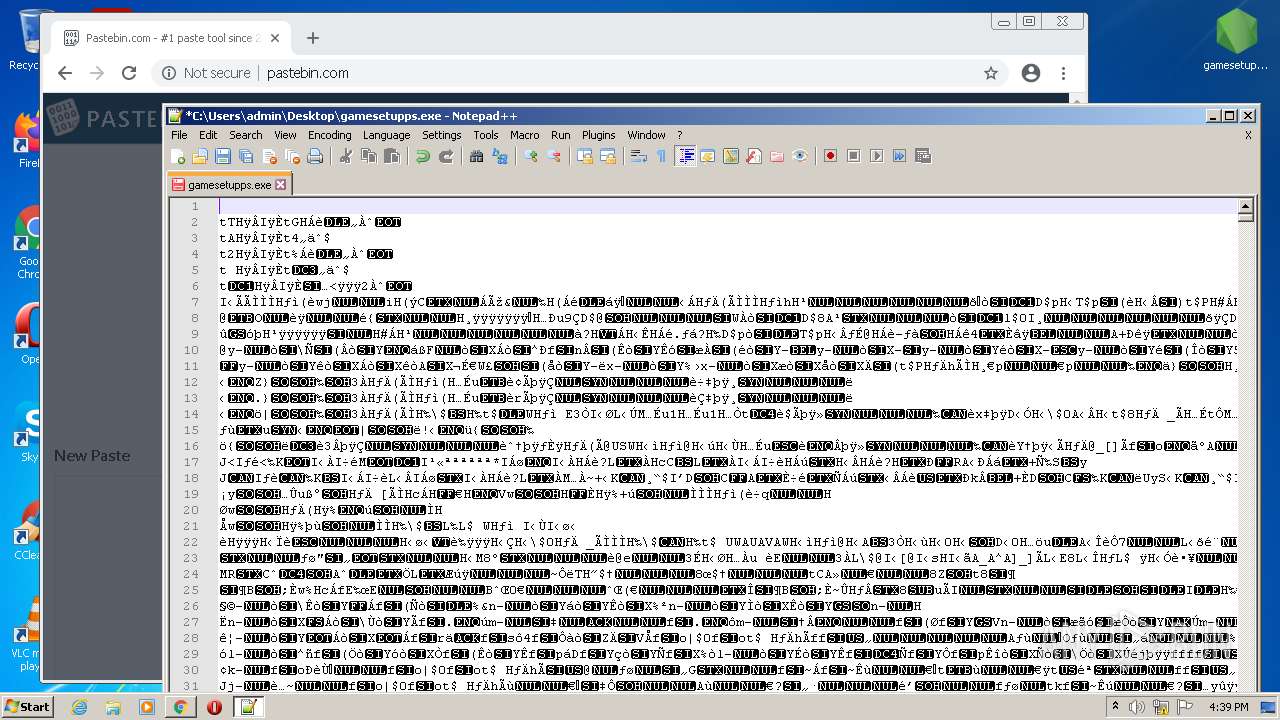
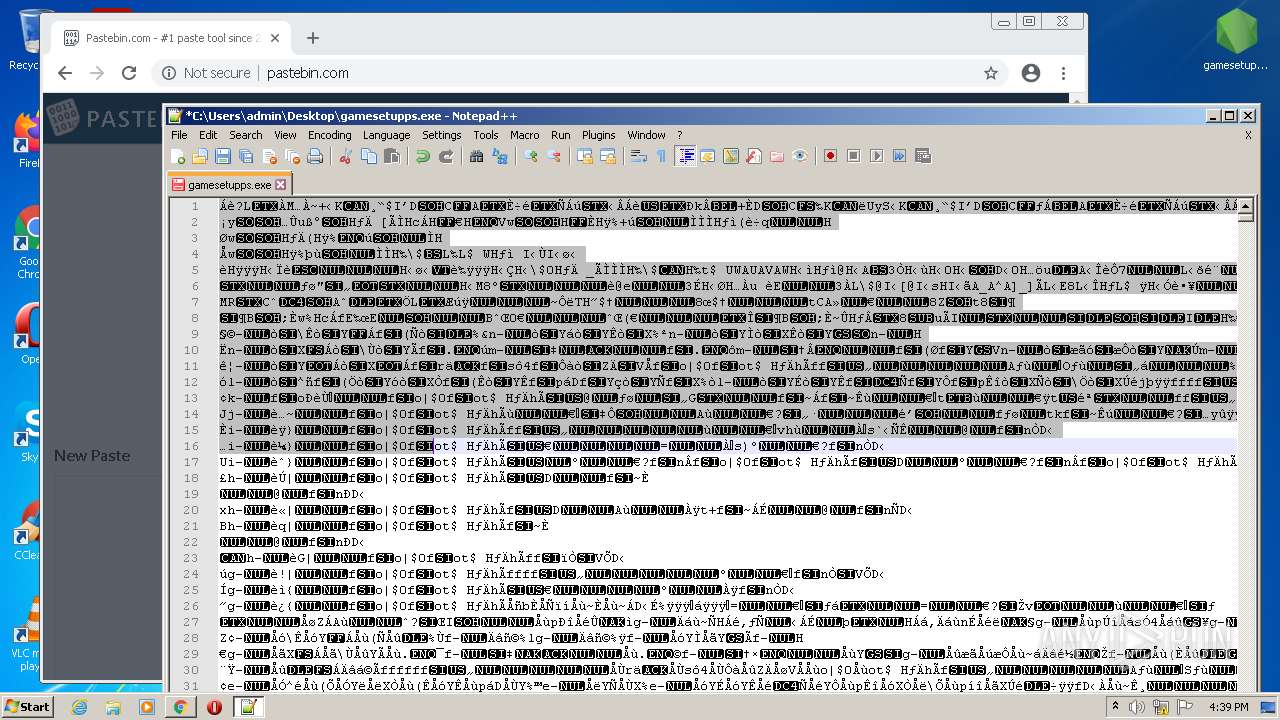
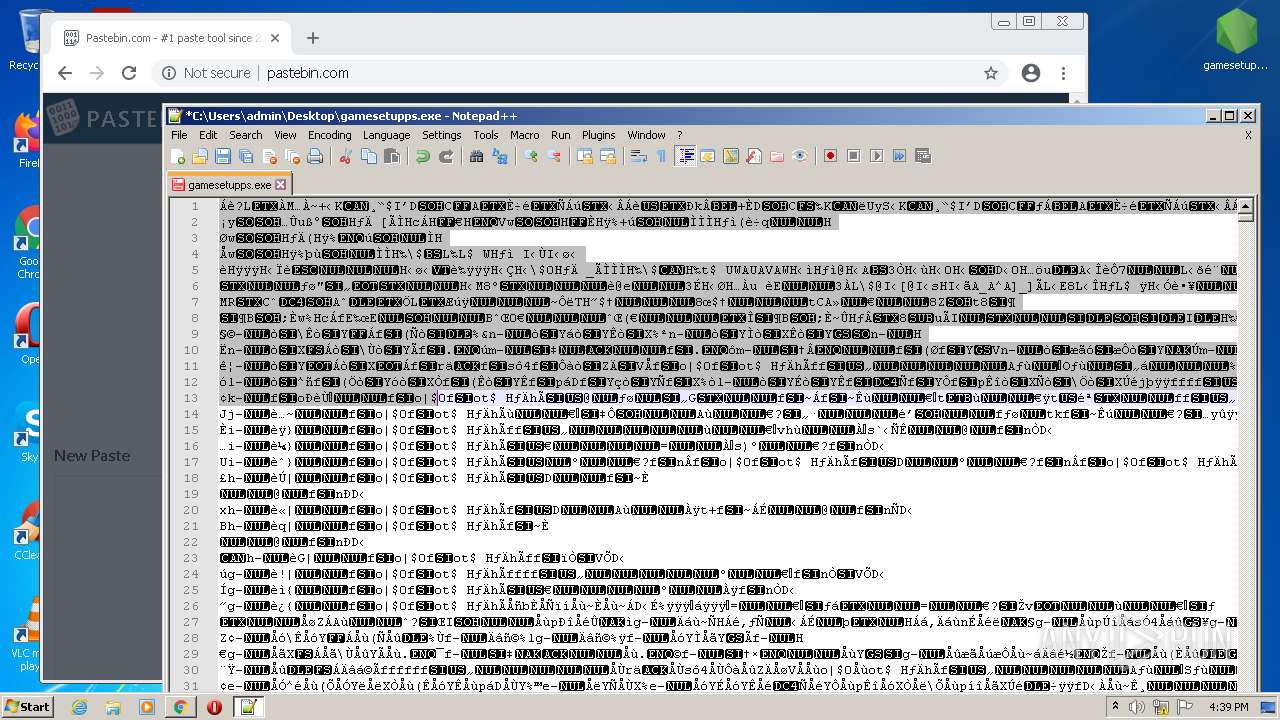
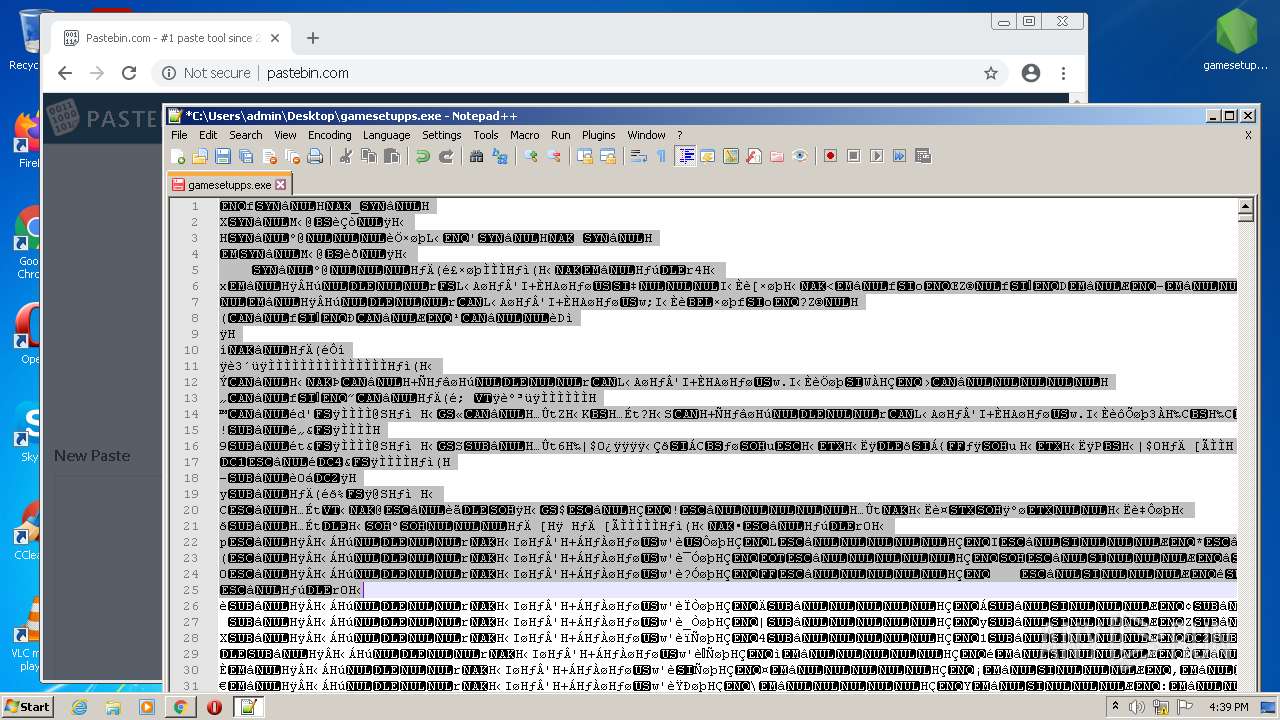
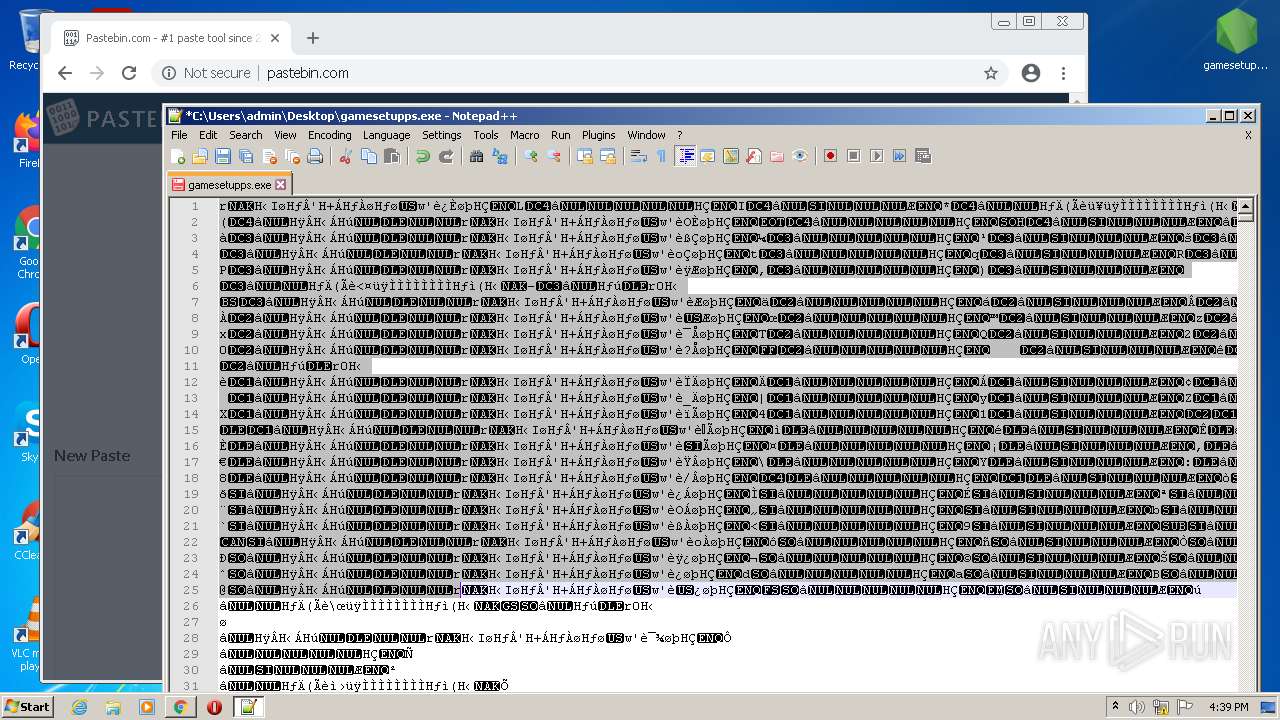
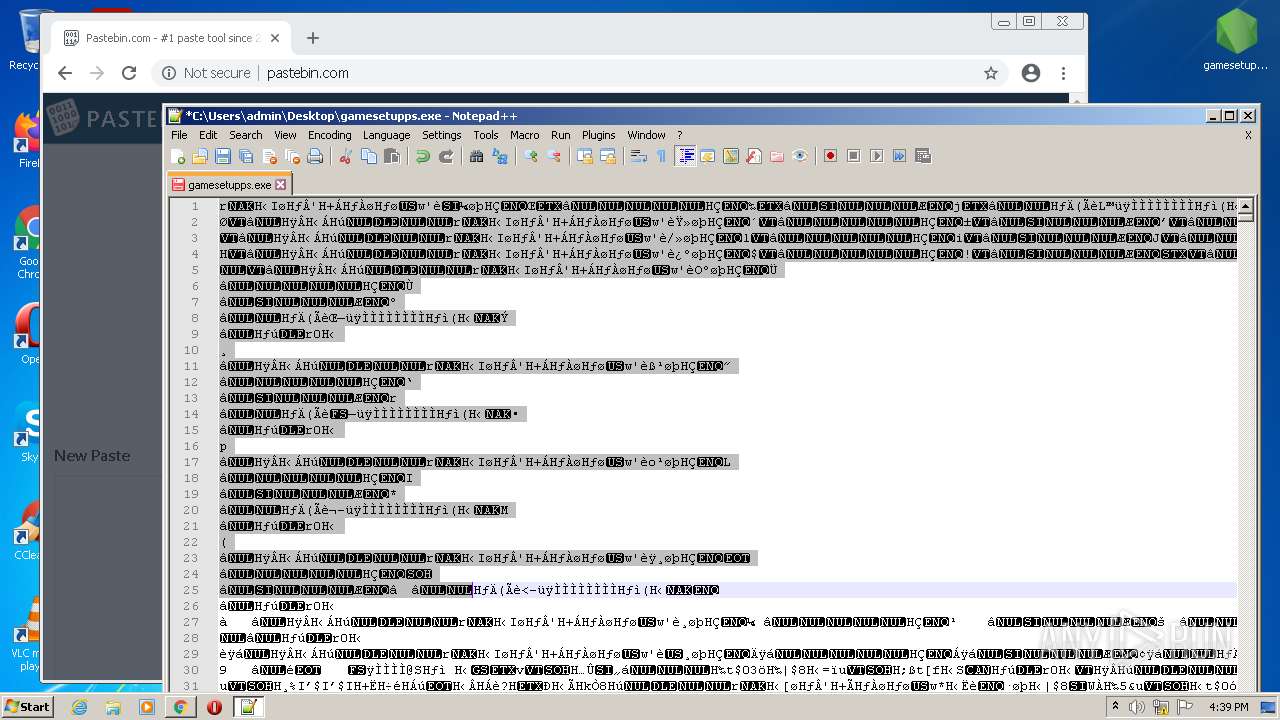
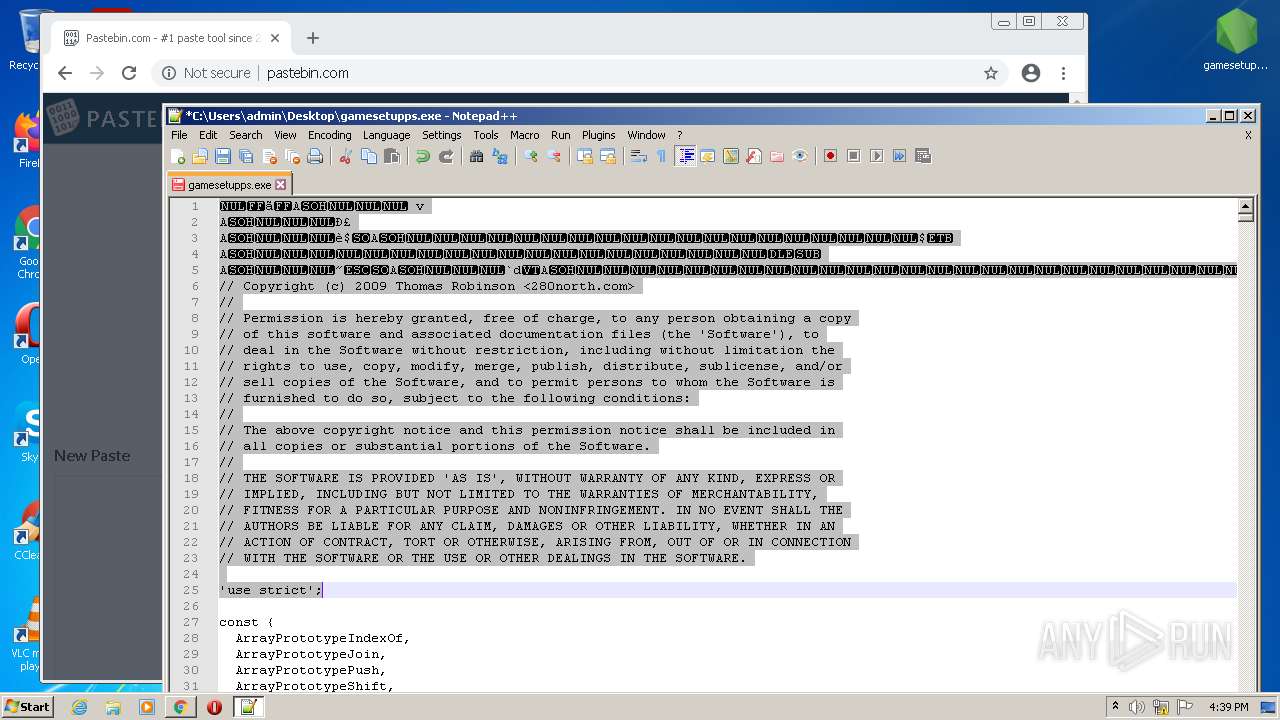
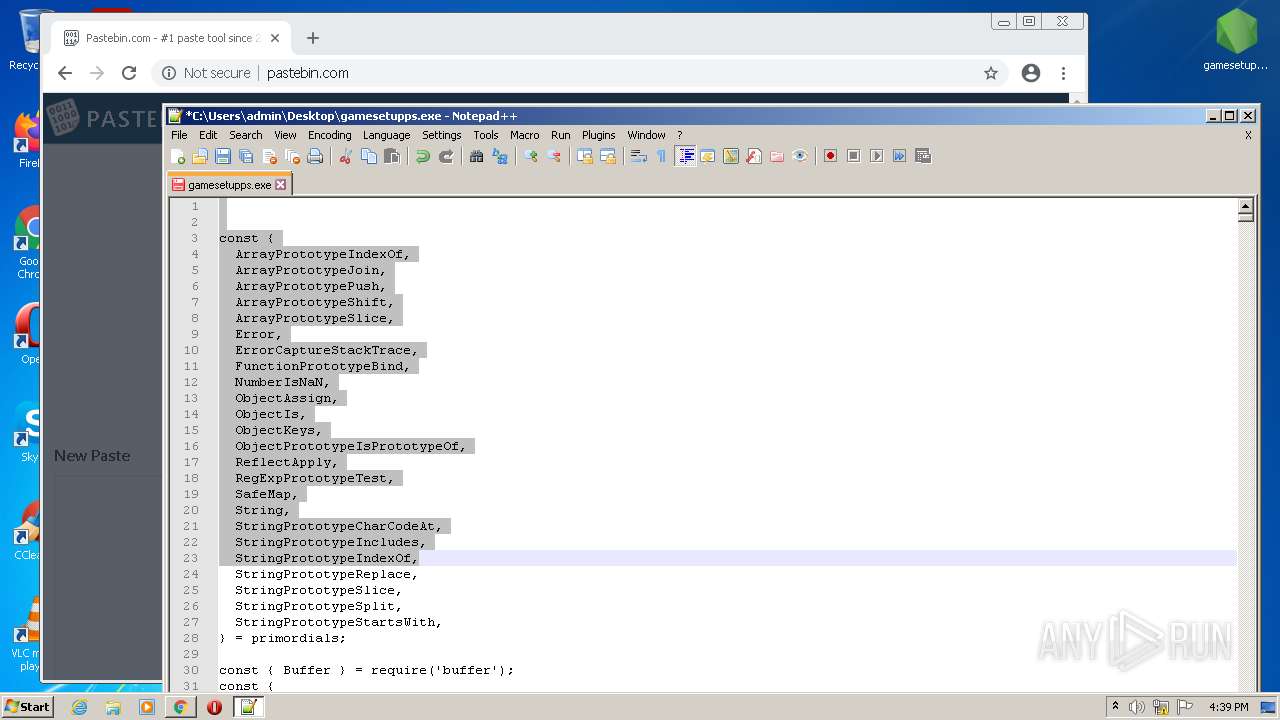
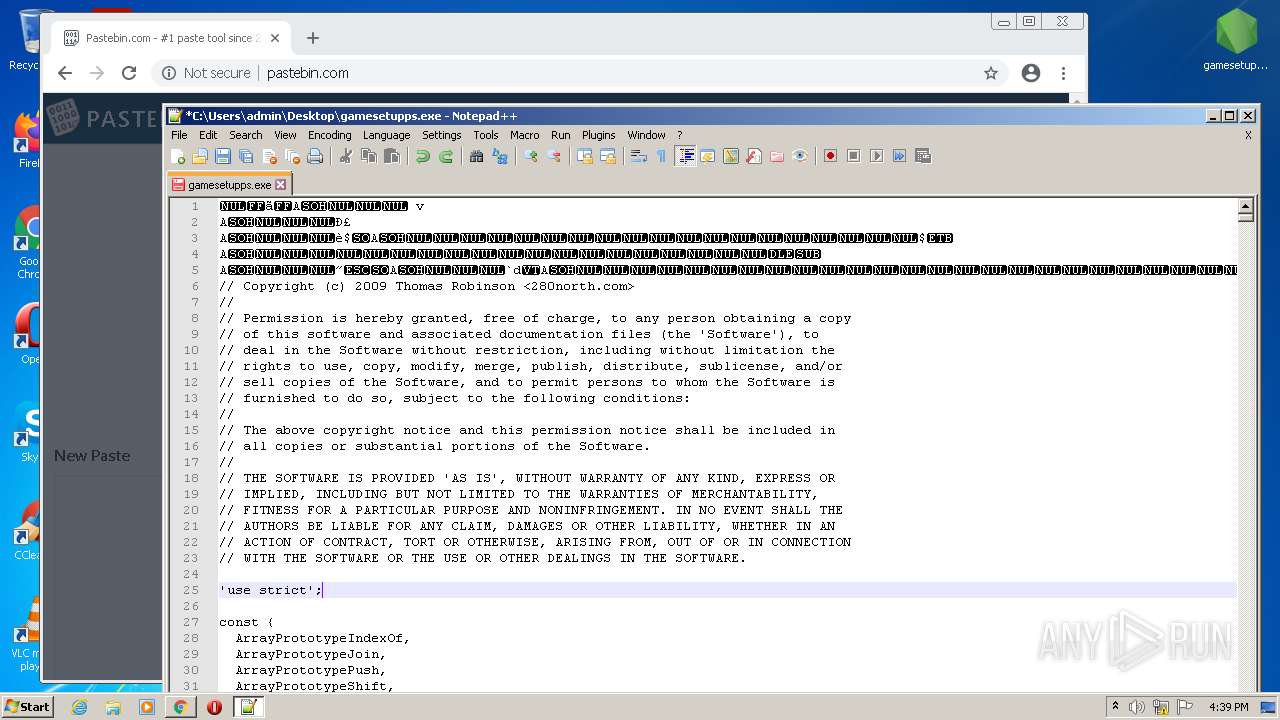
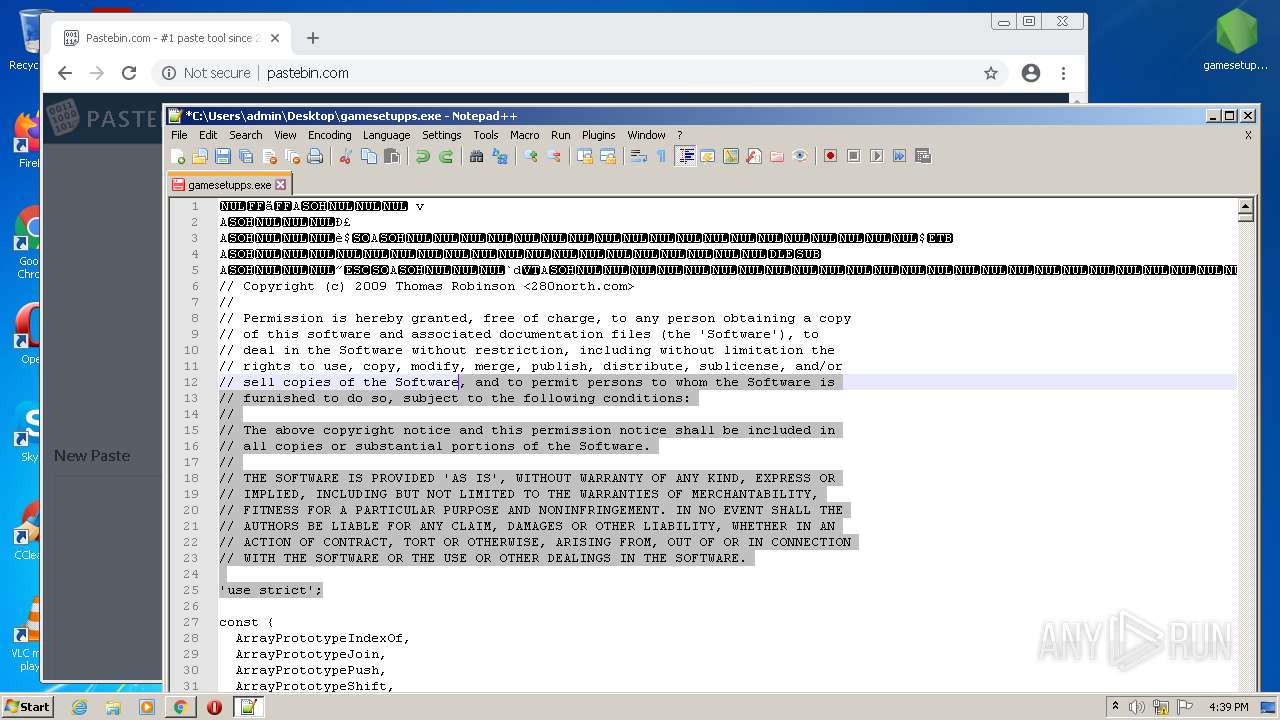
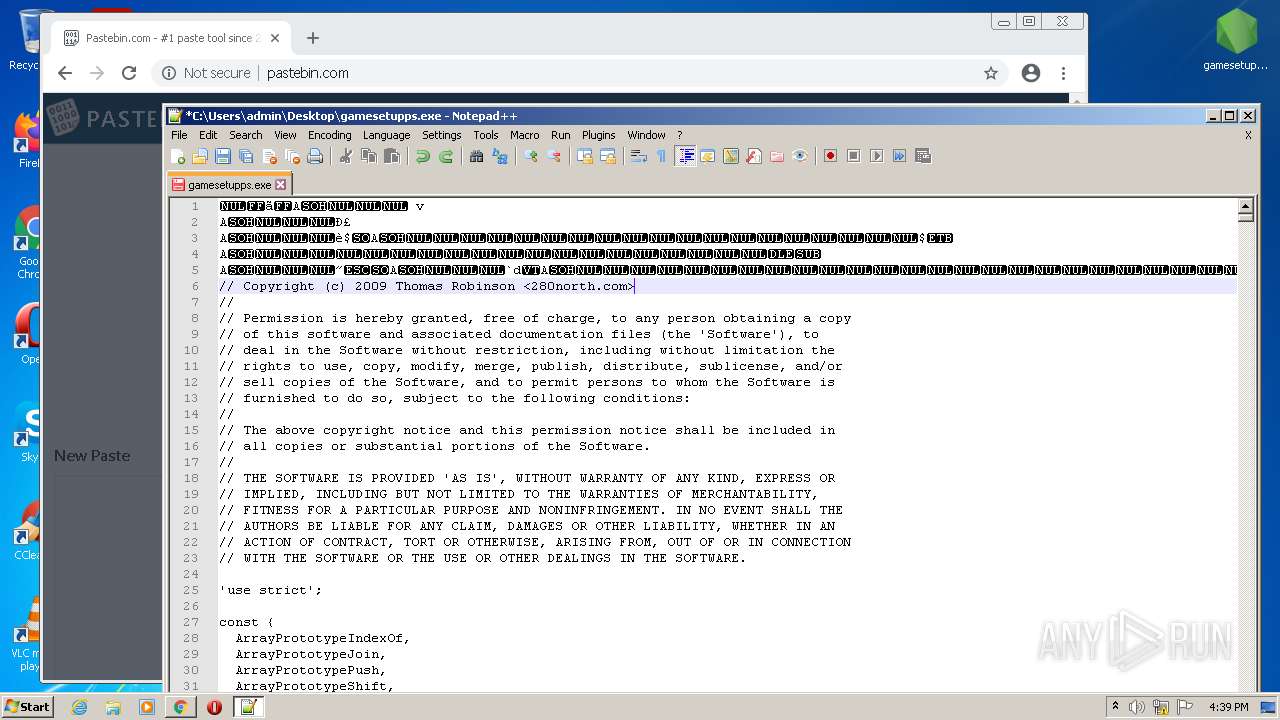
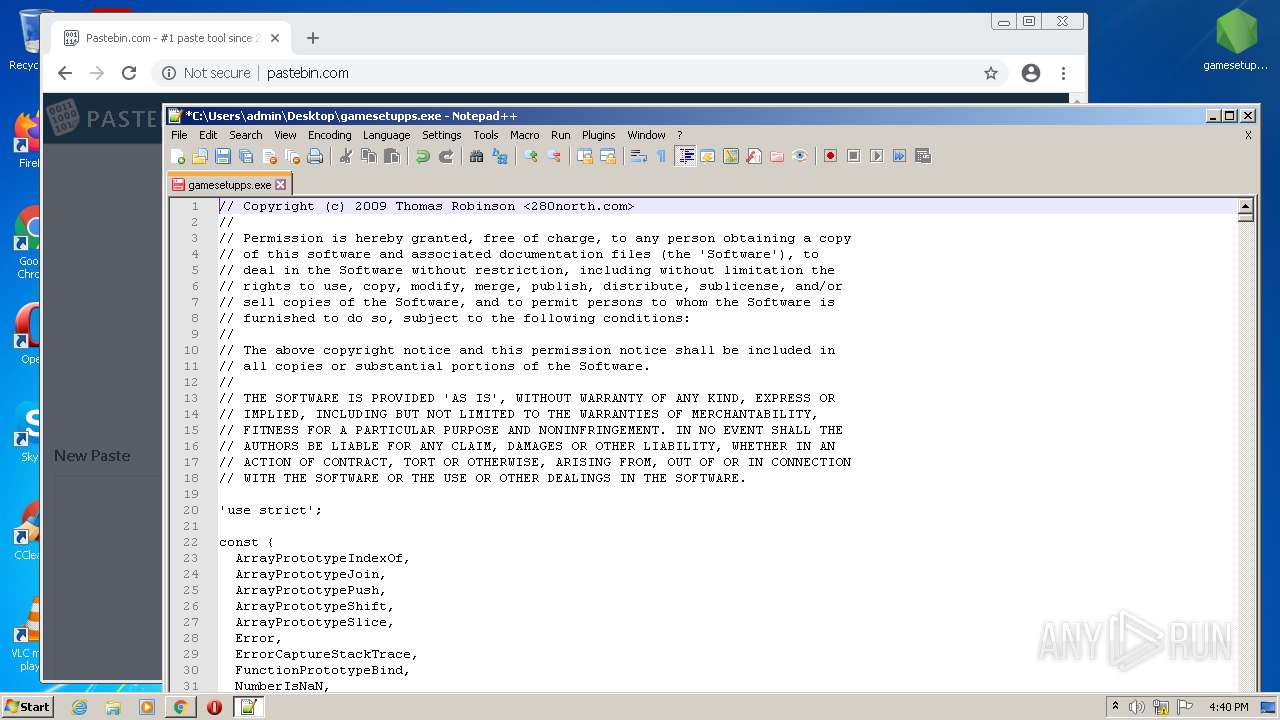
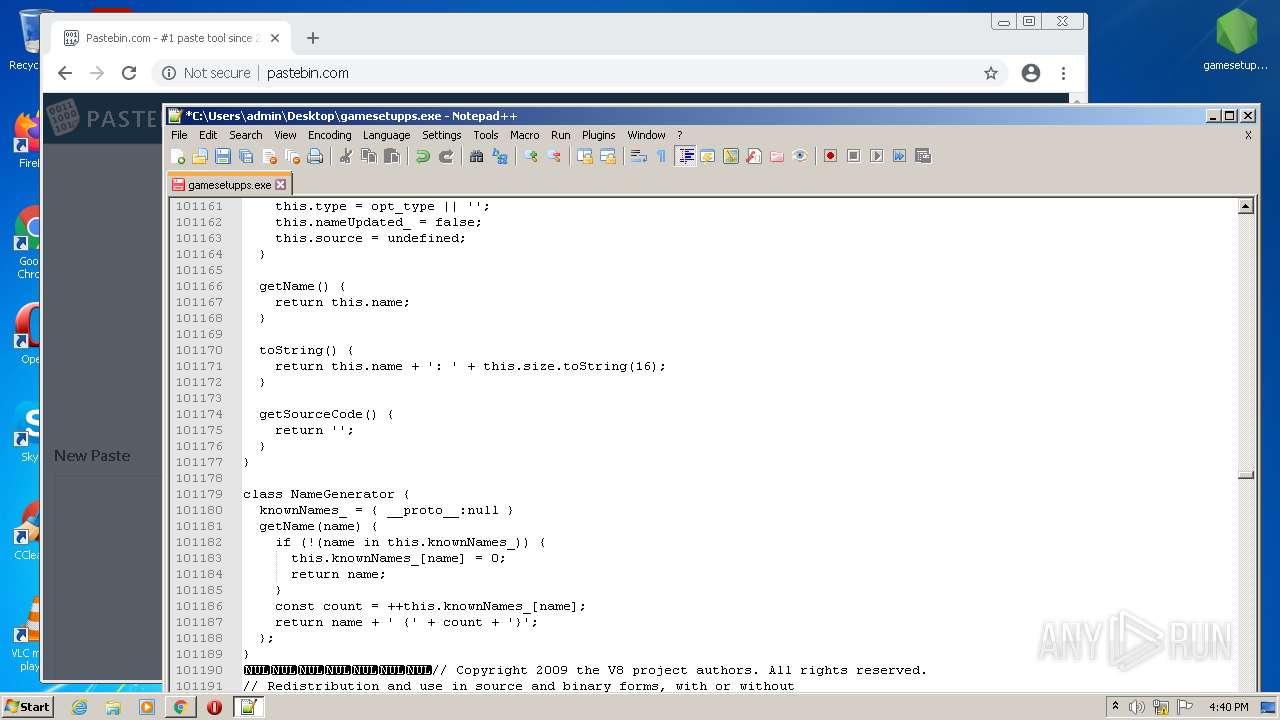
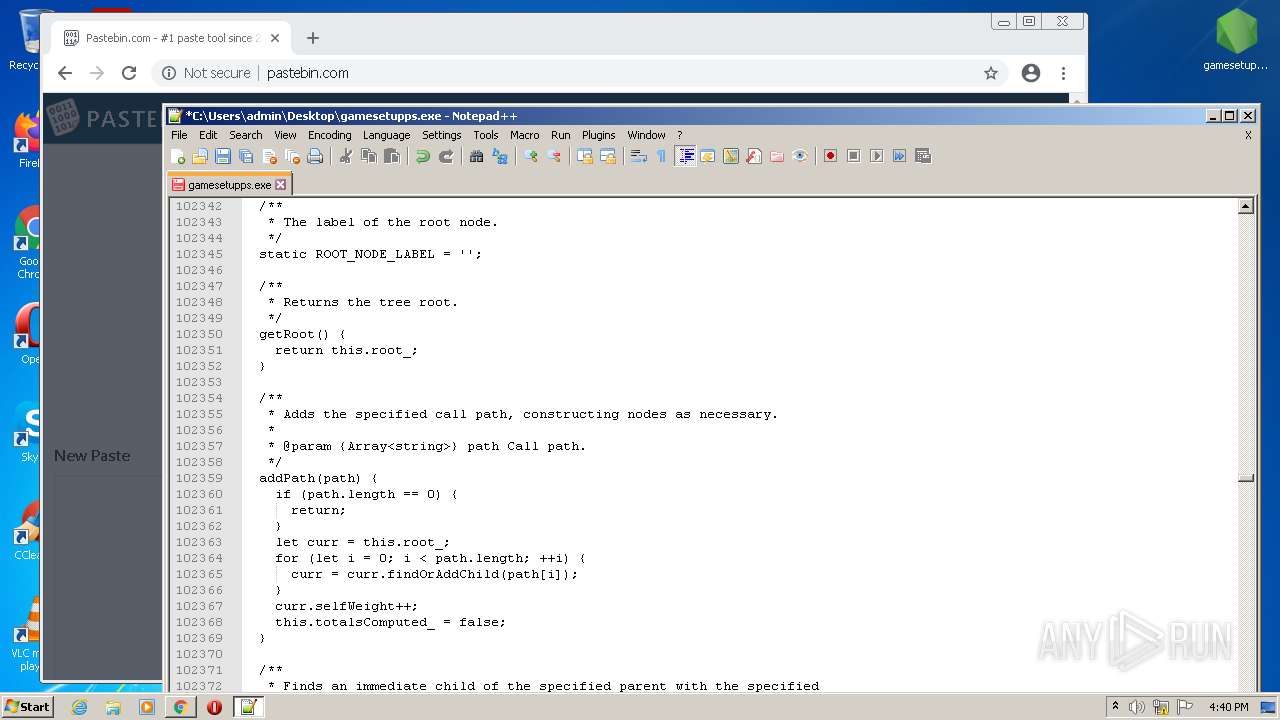
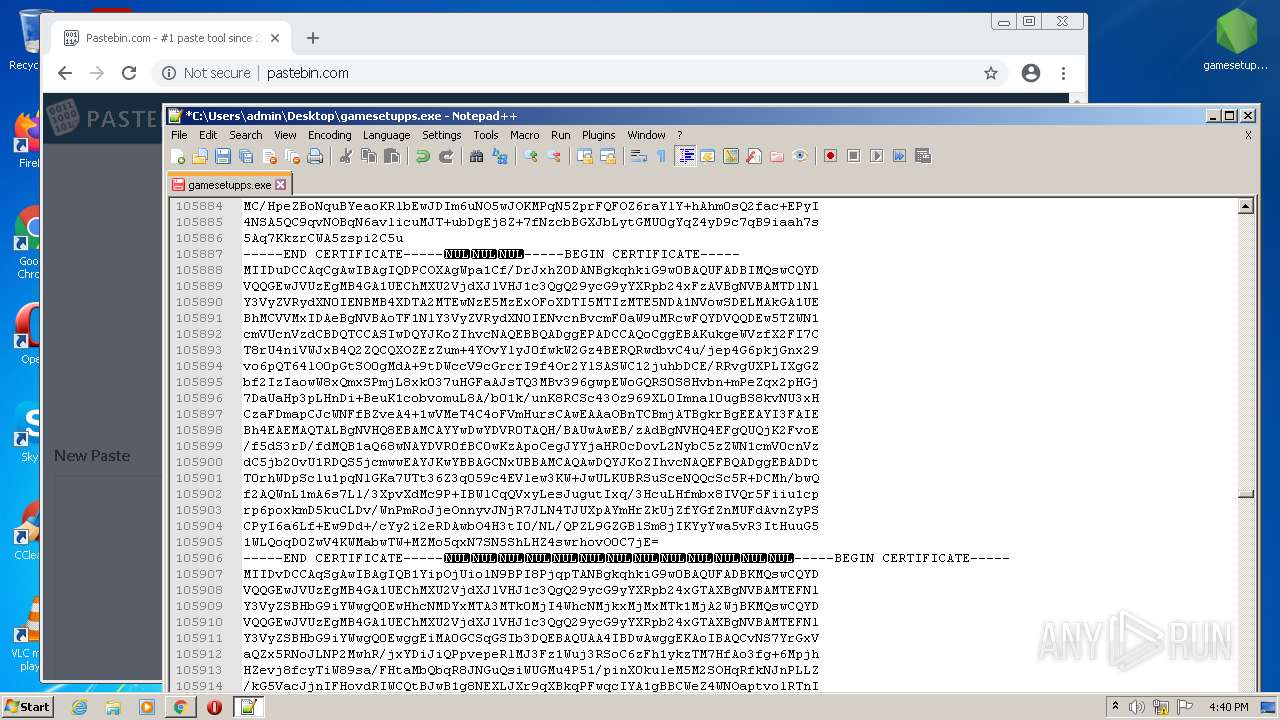
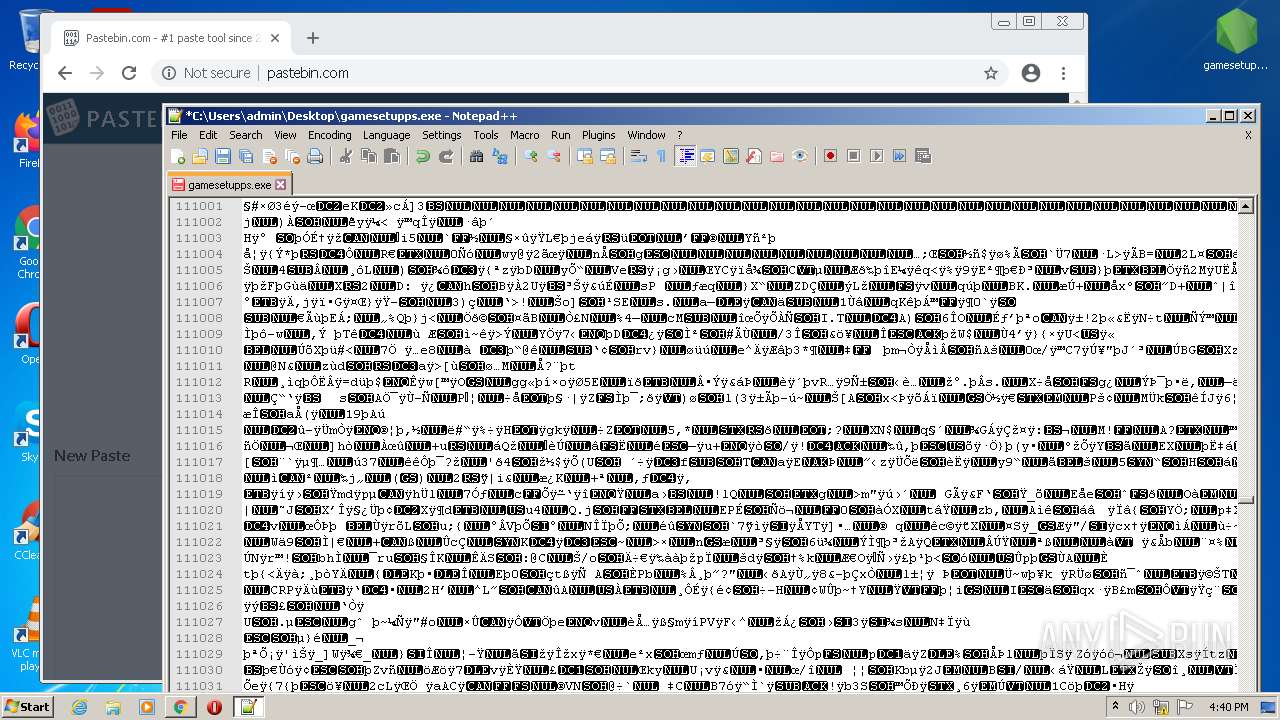
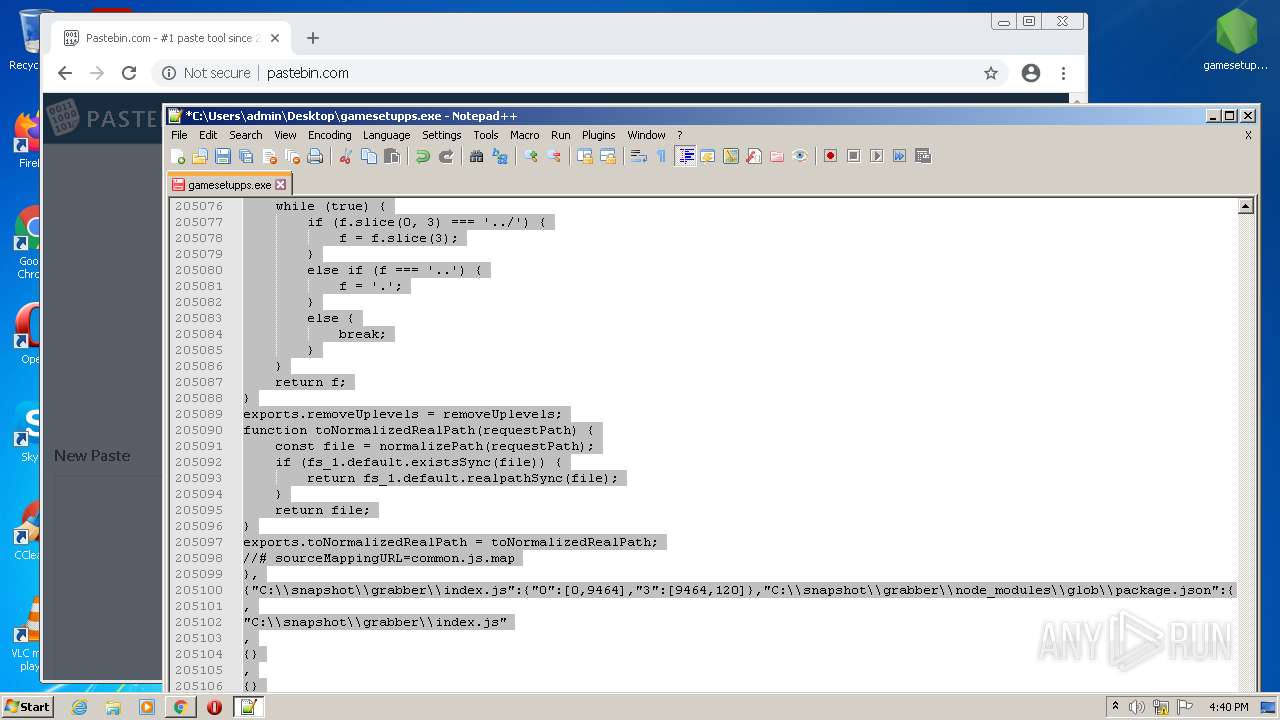
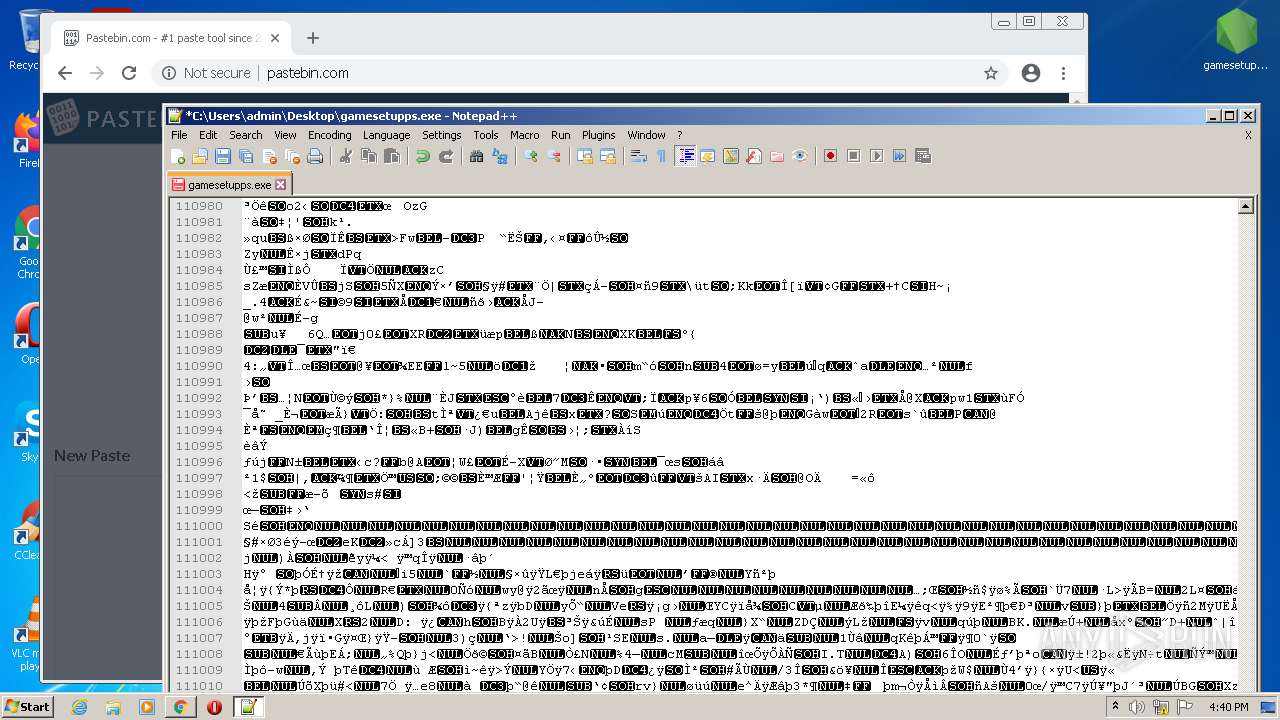
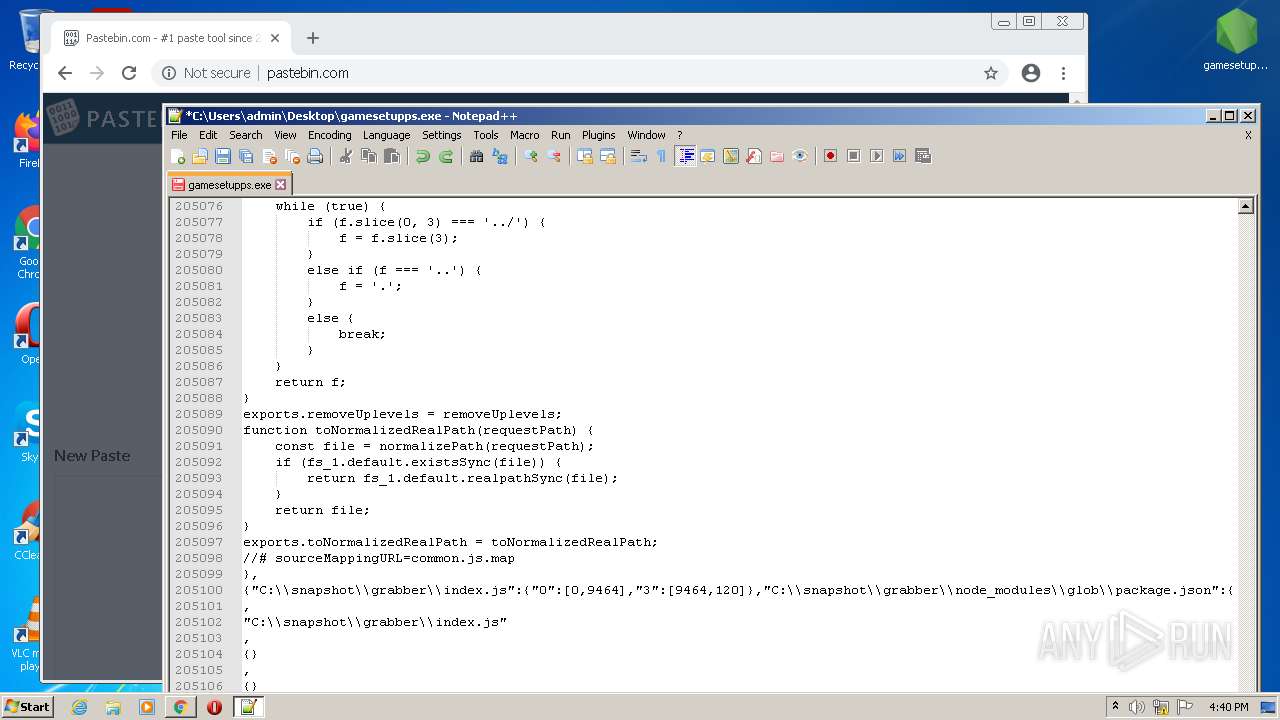
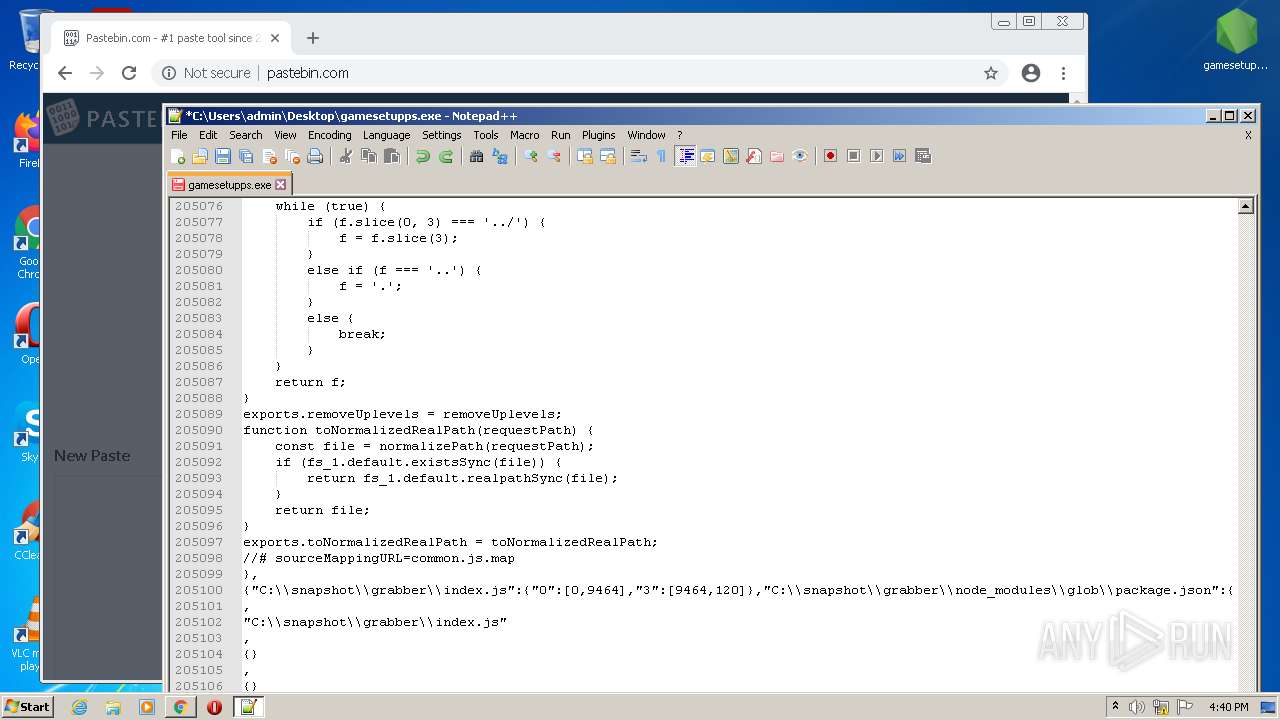
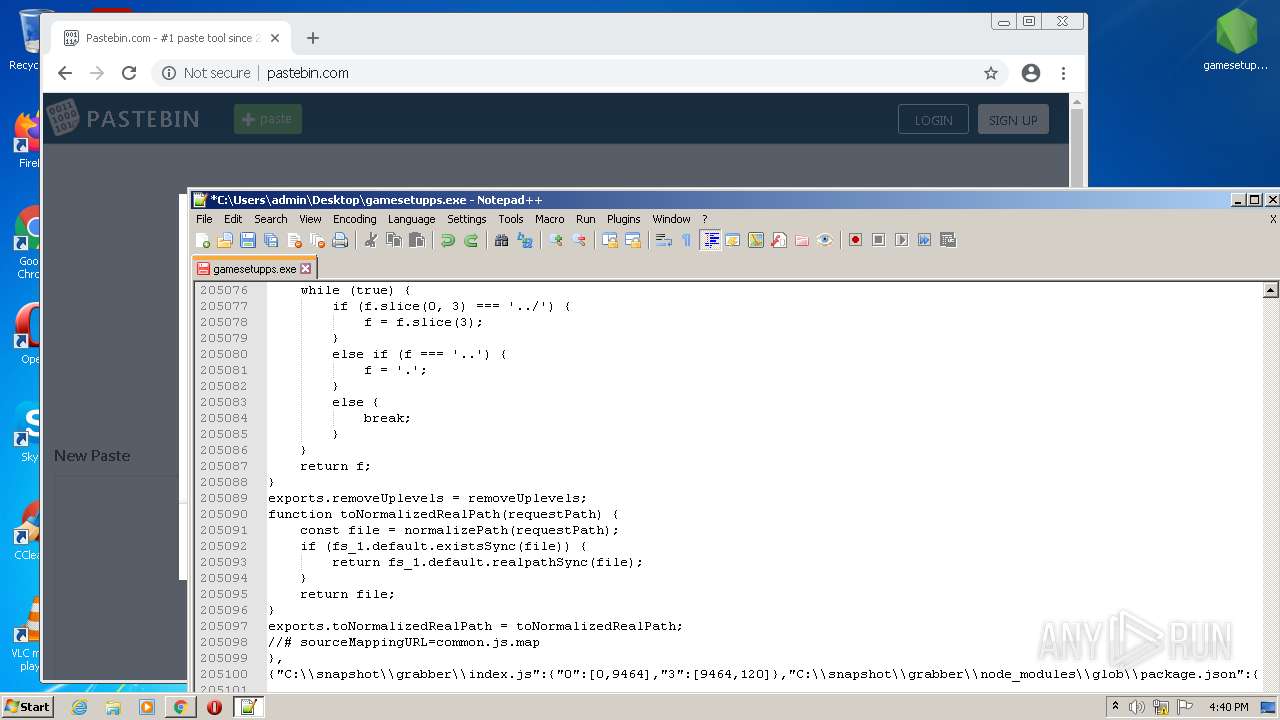
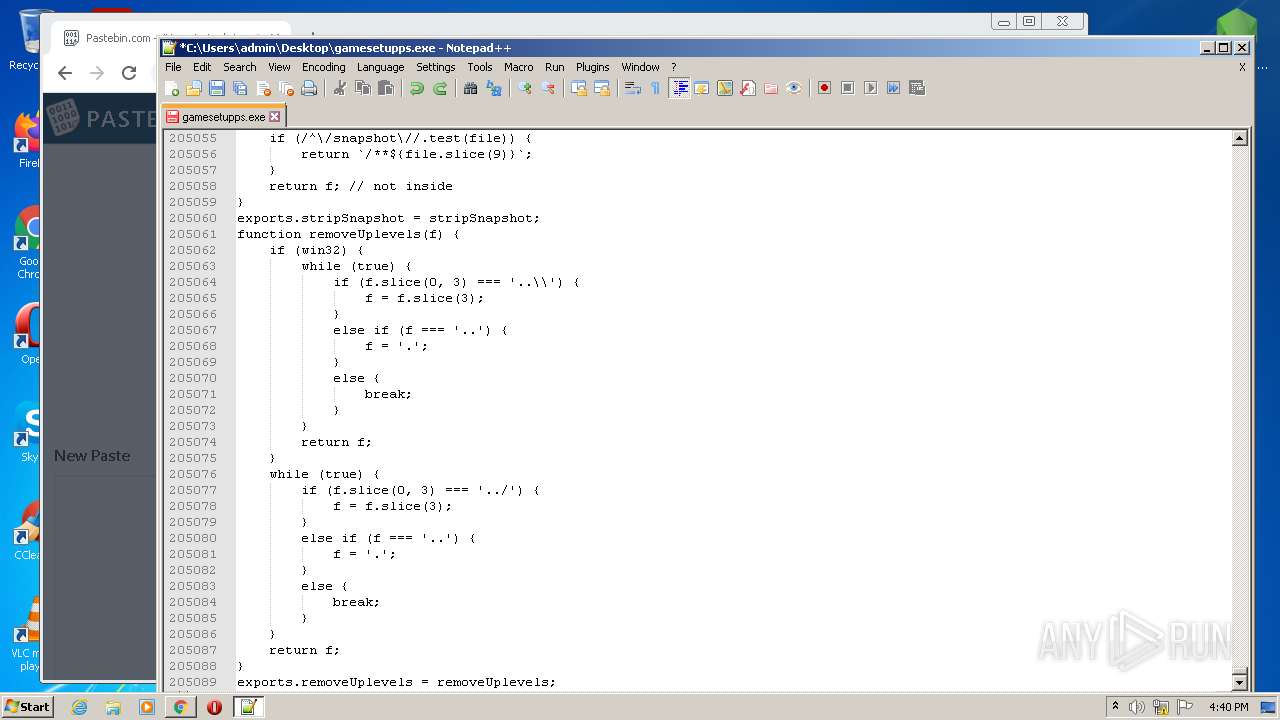
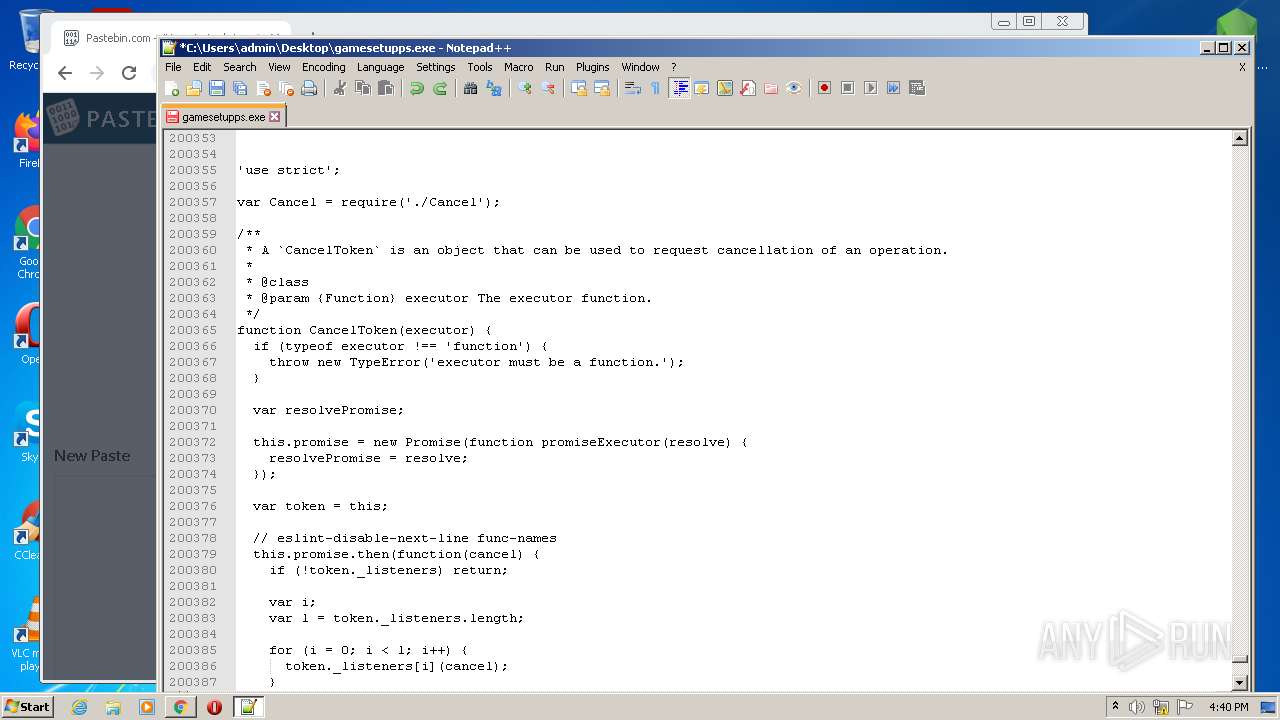
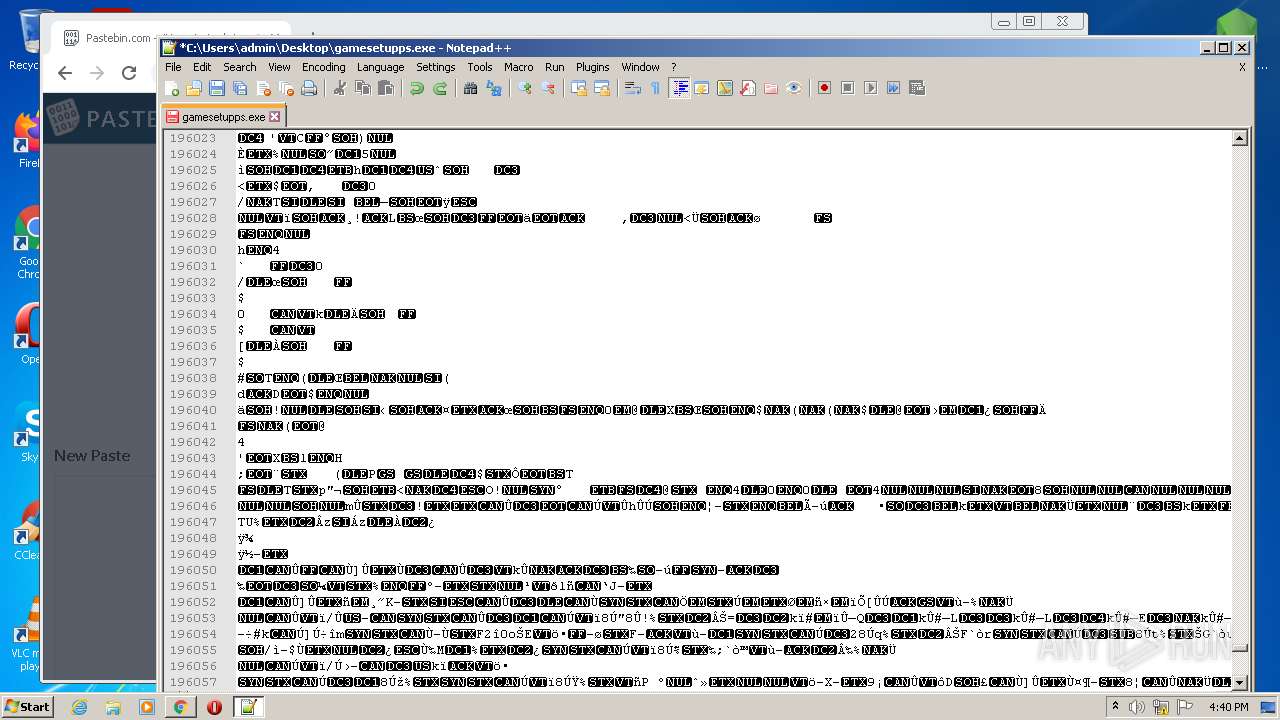
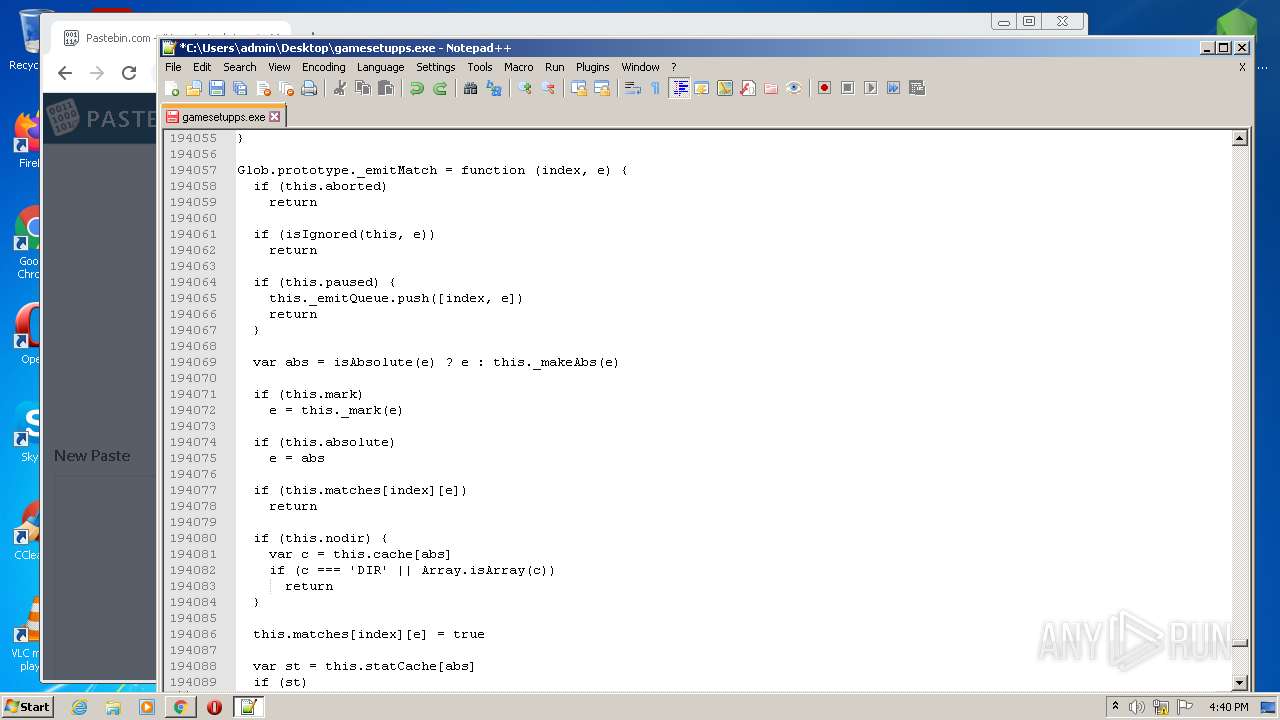
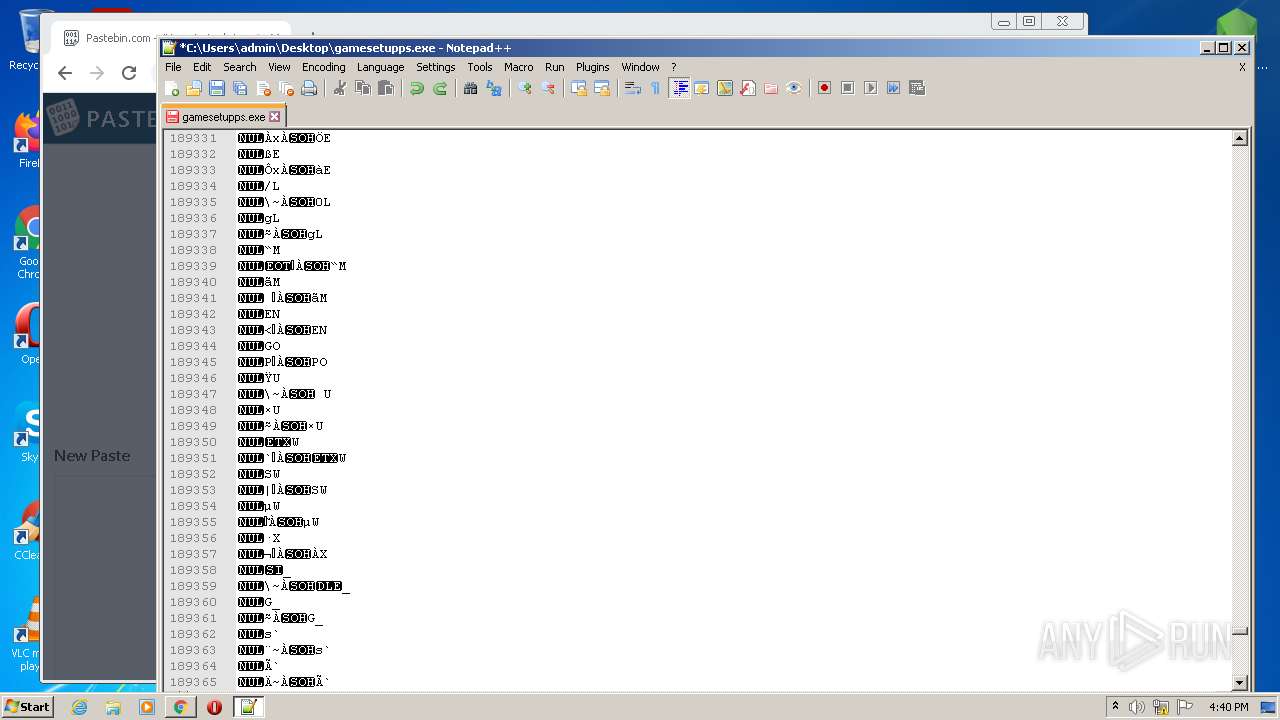
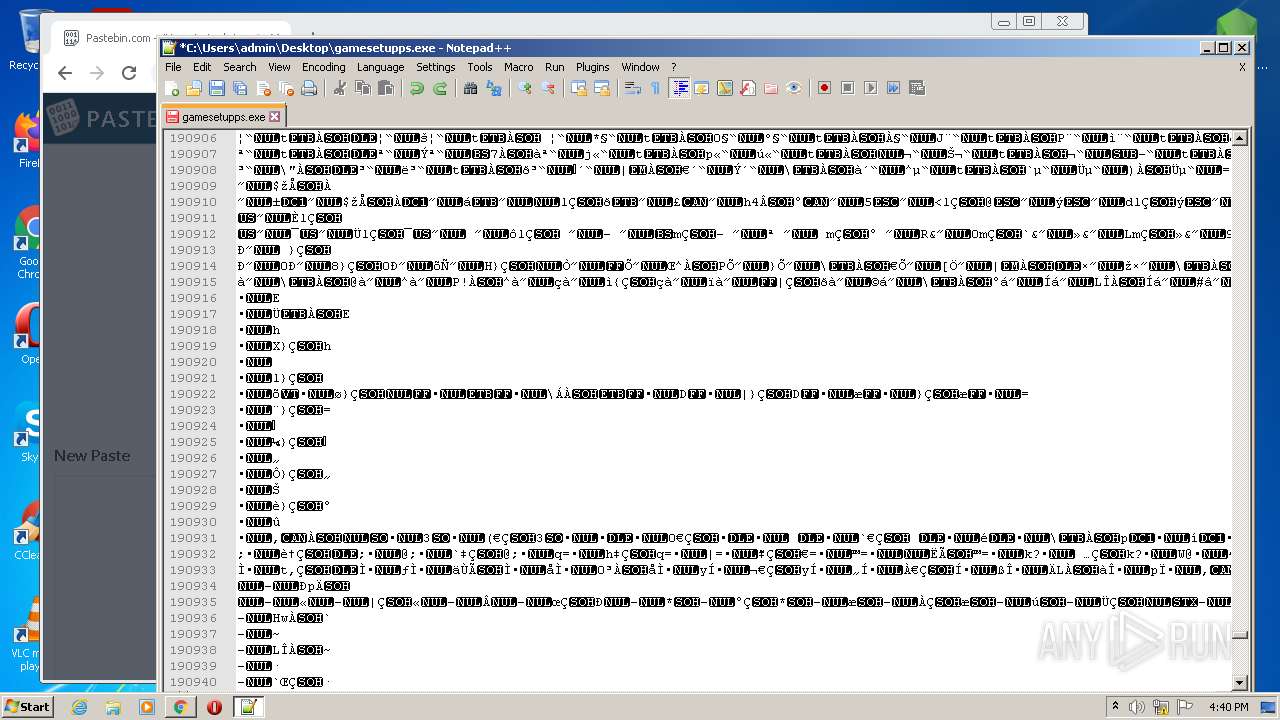
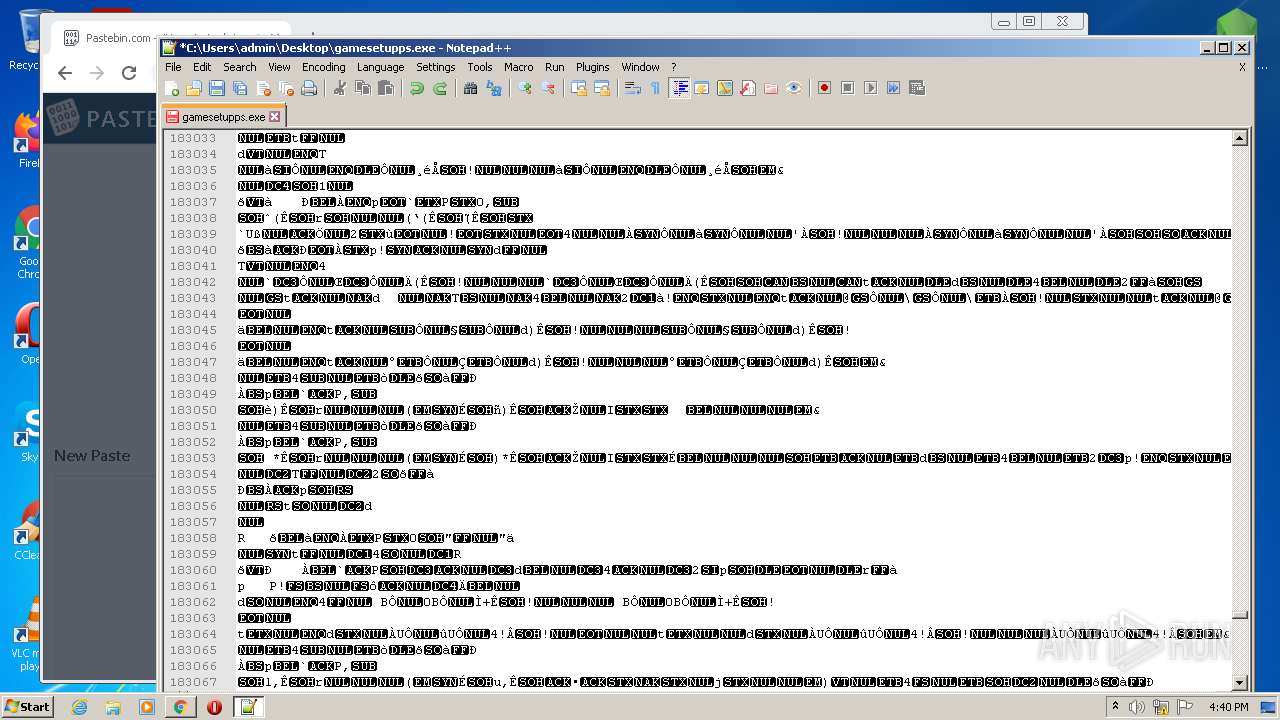
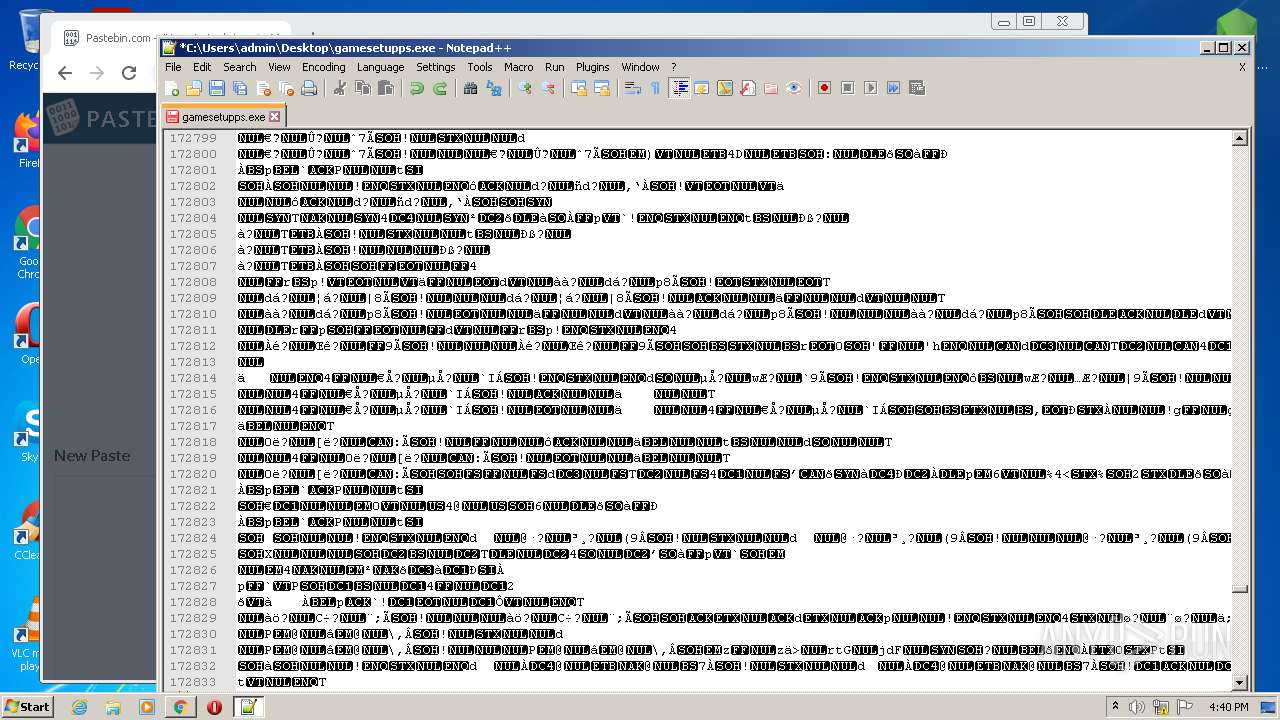
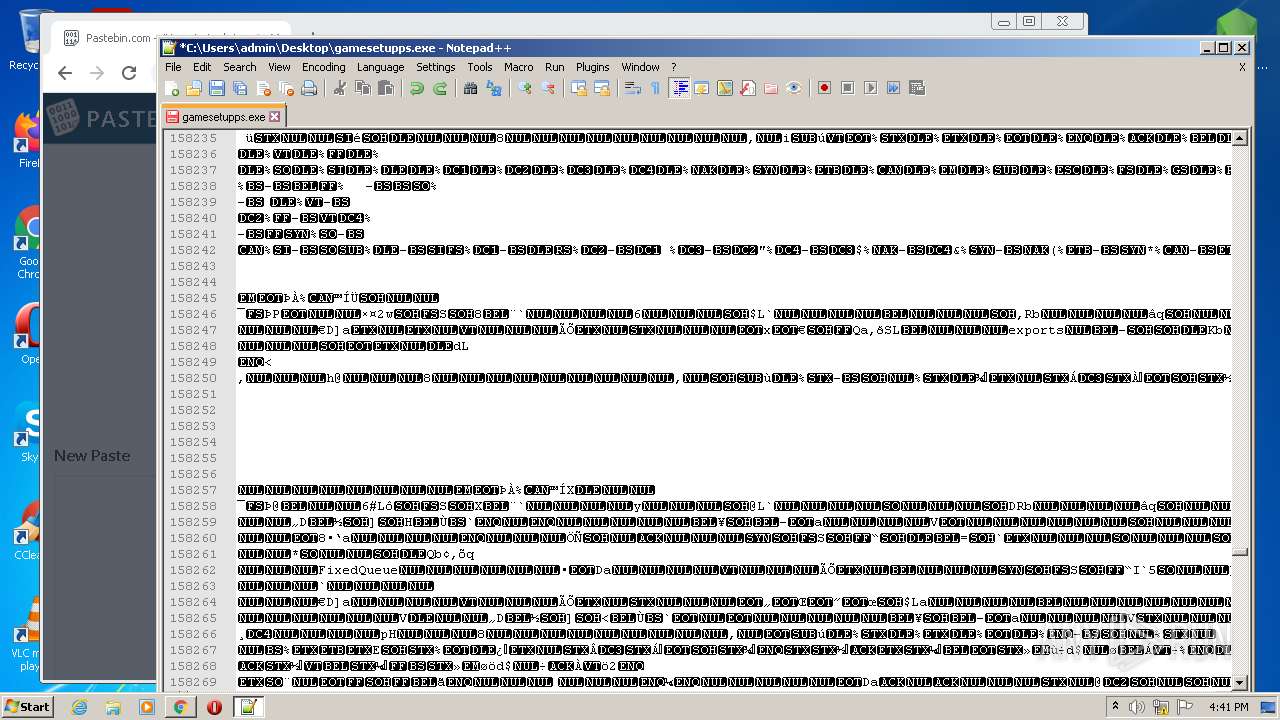
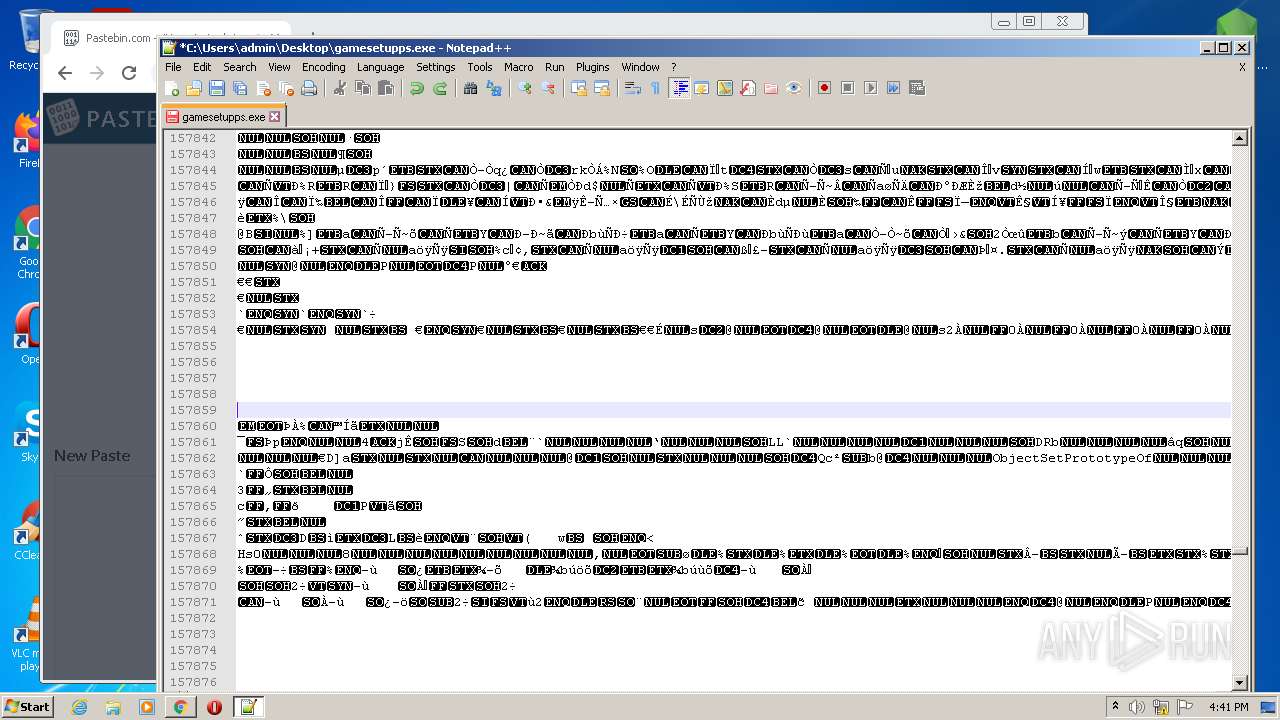
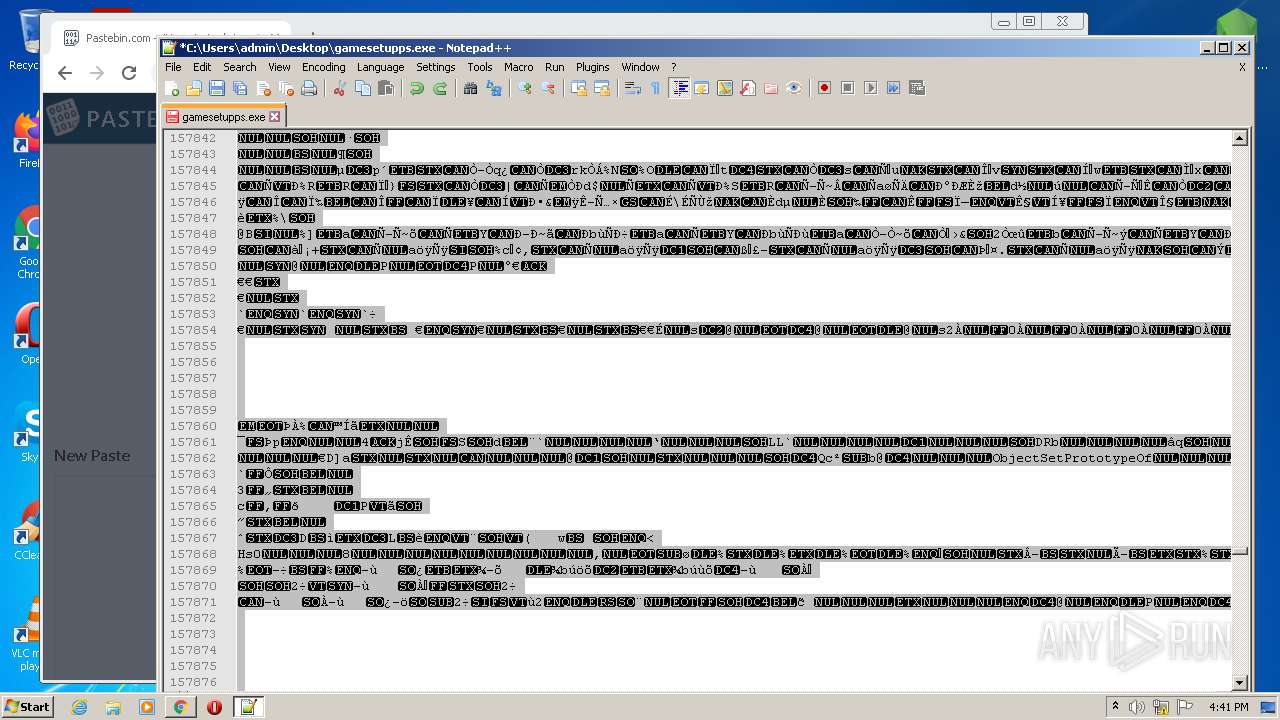
| 480 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\gamesetupps.exe" | C:\Program Files\Notepad++\notepad++.exe | Explorer.EXE | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1032,5086708993159759356,15241780462763305851,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3948 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,5086708993159759356,15241780462763305851,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1032,5086708993159759356,15241780462763305851,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3152 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1032,5086708993159759356,15241780462763305851,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3604 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,5086708993159759356,15241780462763305851,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3348 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1032,5086708993159759356,15241780462763305851,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1992 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,5086708993159759356,15241780462763305851,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1292 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
21 669
Read events
21 482
Write events
185
Delete events
2
Modification events
| (PID) Process: | (3520) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3520) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3520) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3520) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3520) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3520) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\gamesetupps.rar | |||
| (PID) Process: | (3520) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3520) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3520) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3520) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
0
Suspicious files
241
Text files
209
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3520 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3520.45429\gamesetupps.exe | — | |
MD5:— | SHA256:— | |||
| 1888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61EED601-760.pma | — | |
MD5:— | SHA256:— | |||
| 1888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\935994f5-3dc1-43ac-8f22-ee9ee3212380.tmp | text | |
MD5:— | SHA256:— | |||
| 3360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 1888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 1888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 1888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RF1176d3.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
| 1888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 1888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e2d4eefe-4972-4f74-bd88-e73a7e11c25e.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 1888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
301
DNS requests
143
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3360 | chrome.exe | GET | 302 | 13.248.245.213:80 | http://eb2.3lift.com/xuid?mid=7666&xuid=ec508f3d-6ff1-4bb2-8293-5fc0076e813a&dongle=8f7 | US | — | — | shared |
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/mhzu72vkczhlmfqomqnf35nvau_2765/jflookgnkcckhobaglndicnbbgbonegd_2765_all_jdd5fasdwpeesmnmtivieegk2a.crx3 | US | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/mhzu72vkczhlmfqomqnf35nvau_2765/jflookgnkcckhobaglndicnbbgbonegd_2765_all_jdd5fasdwpeesmnmtivieegk2a.crx3 | US | binary | 9.75 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/mhzu72vkczhlmfqomqnf35nvau_2765/jflookgnkcckhobaglndicnbbgbonegd_2765_all_jdd5fasdwpeesmnmtivieegk2a.crx3 | US | binary | 5.67 Kb | whitelisted |
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 64 b | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 720 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/mhzu72vkczhlmfqomqnf35nvau_2765/jflookgnkcckhobaglndicnbbgbonegd_2765_all_jdd5fasdwpeesmnmtivieegk2a.crx3 | US | binary | 9.74 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 44.1 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 38.7 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/mhzu72vkczhlmfqomqnf35nvau_2765/jflookgnkcckhobaglndicnbbgbonegd_2765_all_jdd5fasdwpeesmnmtivieegk2a.crx3 | US | binary | 64 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3360 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
3360 | chrome.exe | 142.250.186.100:443 | www.google.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 142.250.186.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 142.250.186.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 142.250.184.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 142.250.181.238:443 | apis.google.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 142.250.186.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 142.250.181.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 142.250.185.67:443 | update.googleapis.com | Google Inc. | US | whitelisted |
3360 | chrome.exe | 142.250.184.200:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3360 | chrome.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
Process | Message |
|---|---|
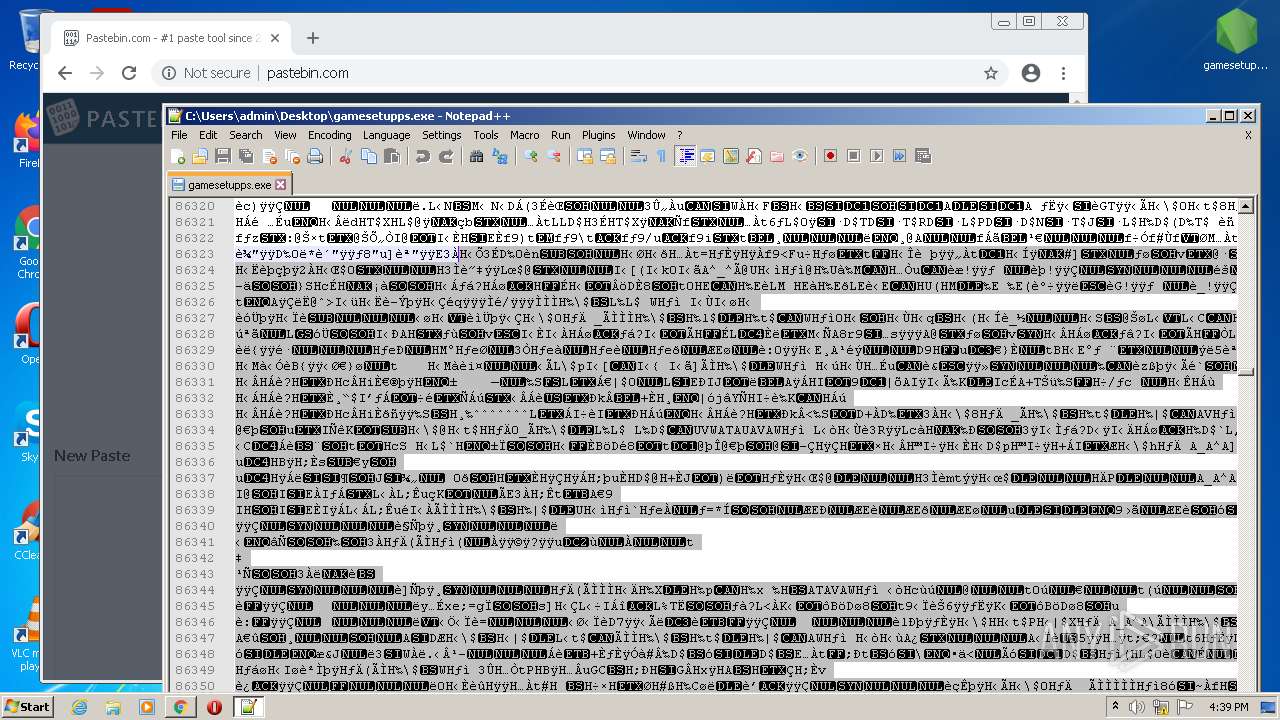
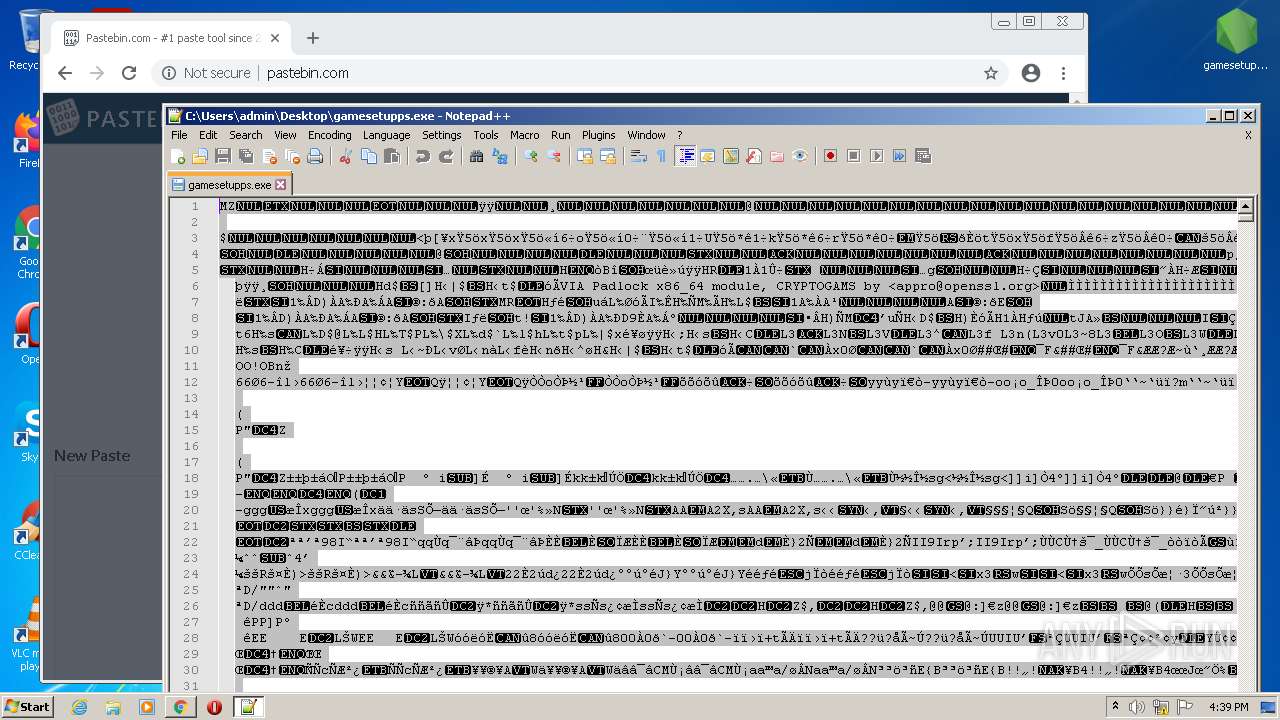
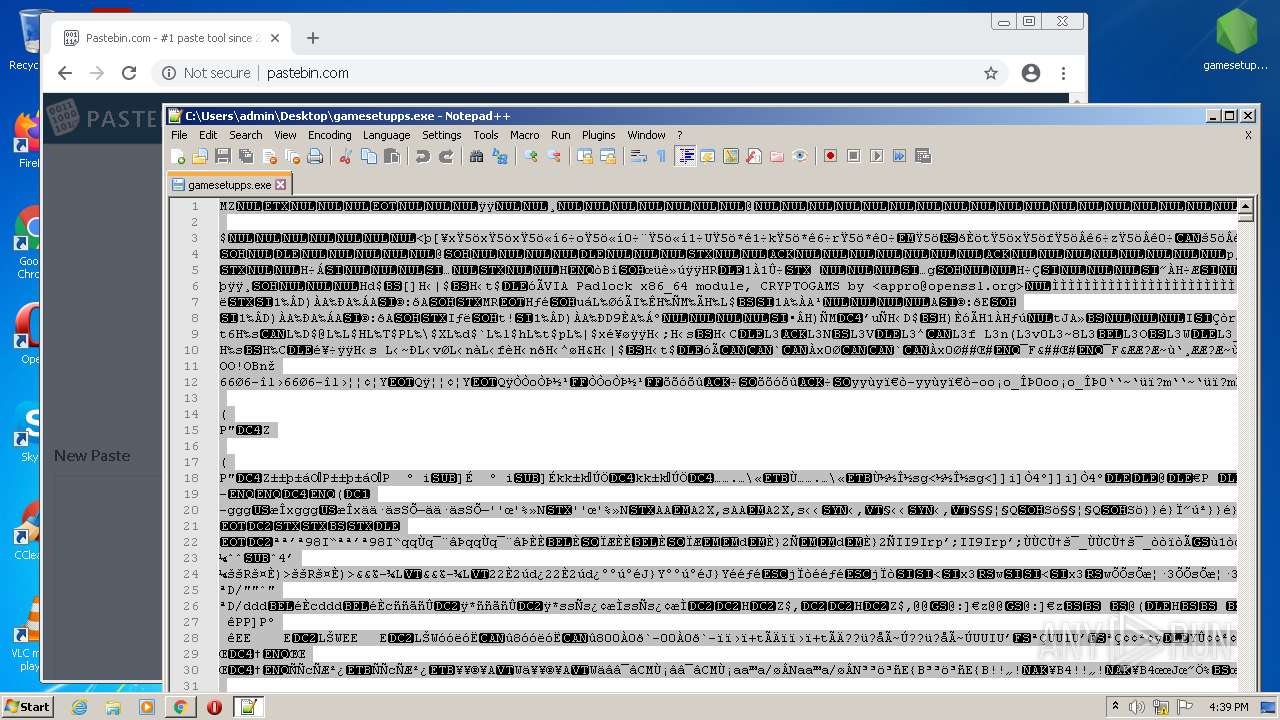
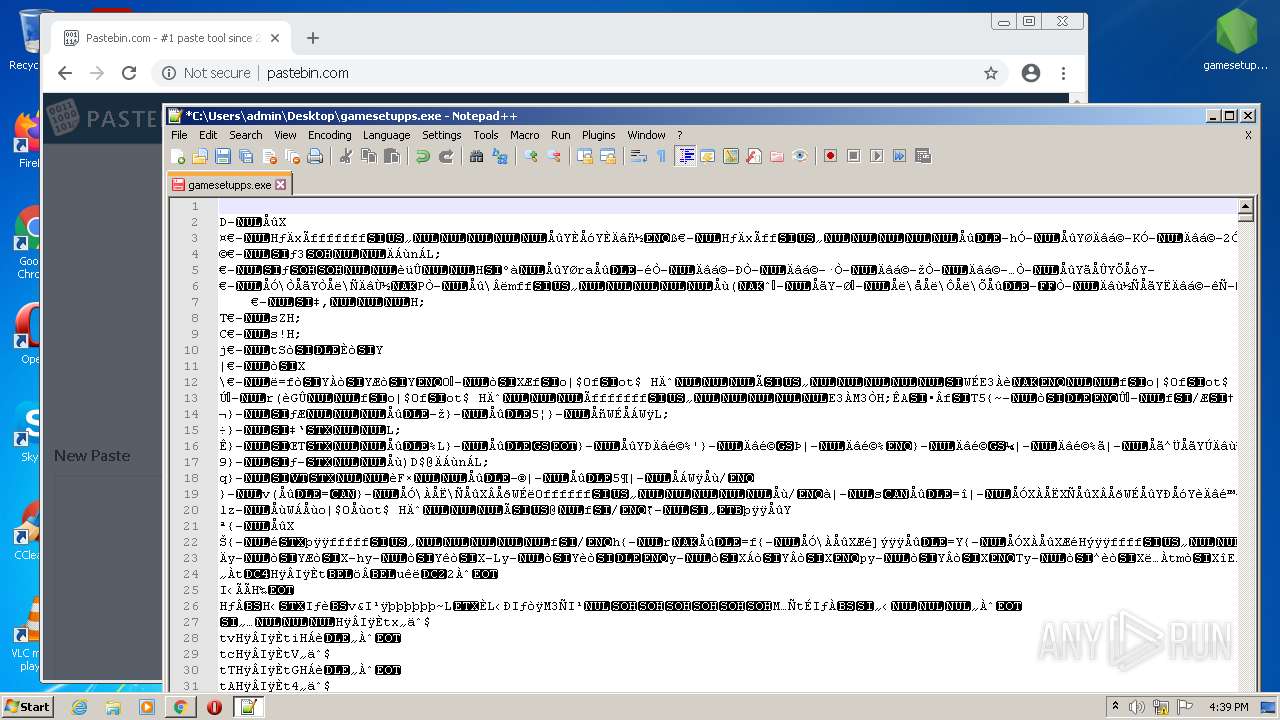
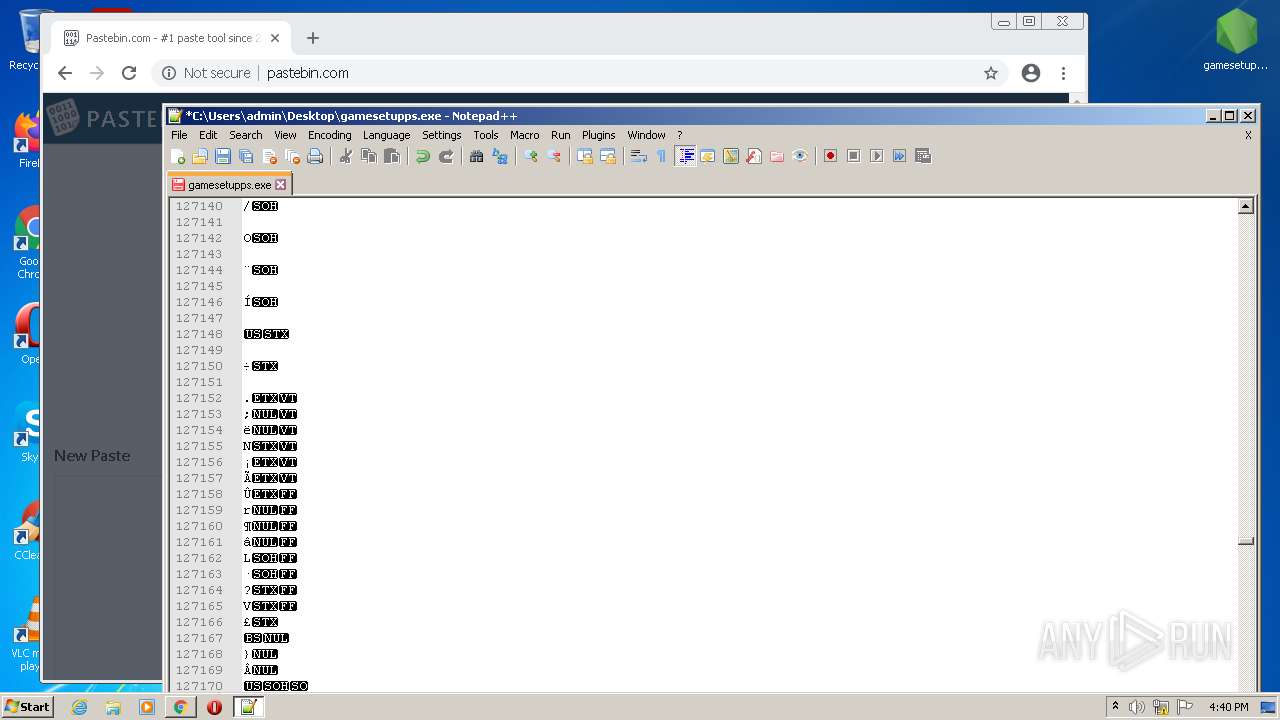
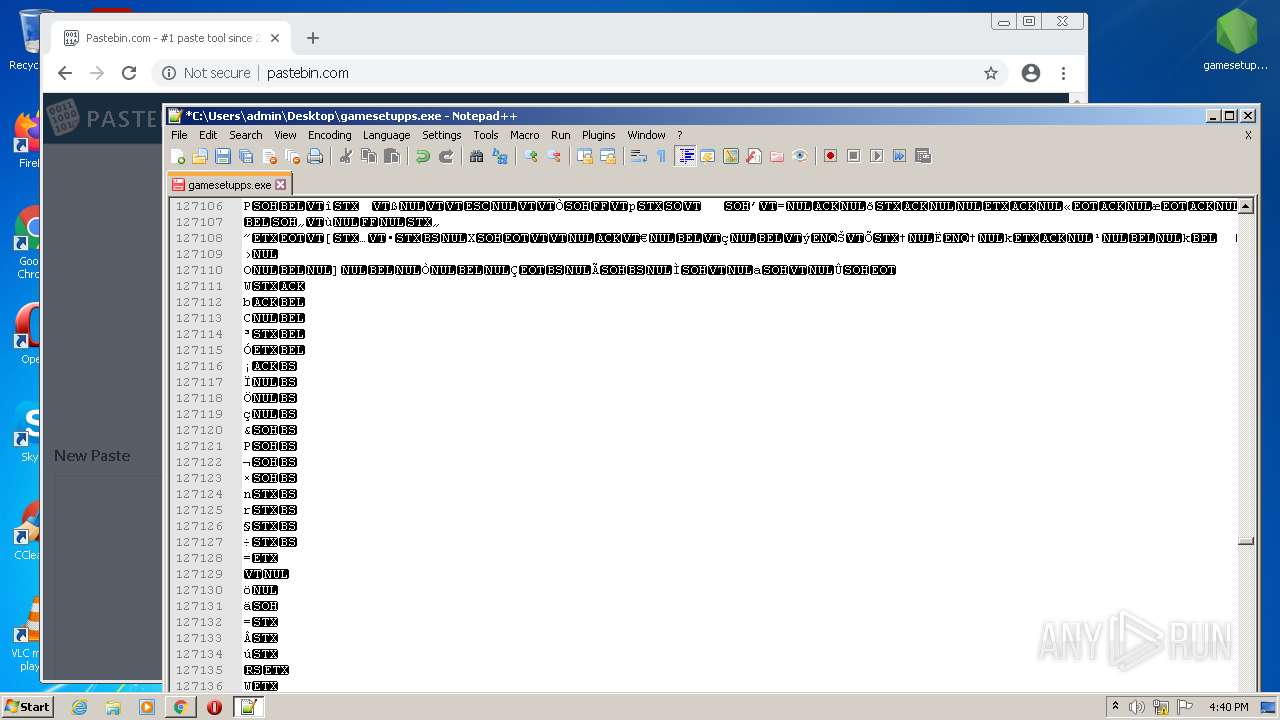
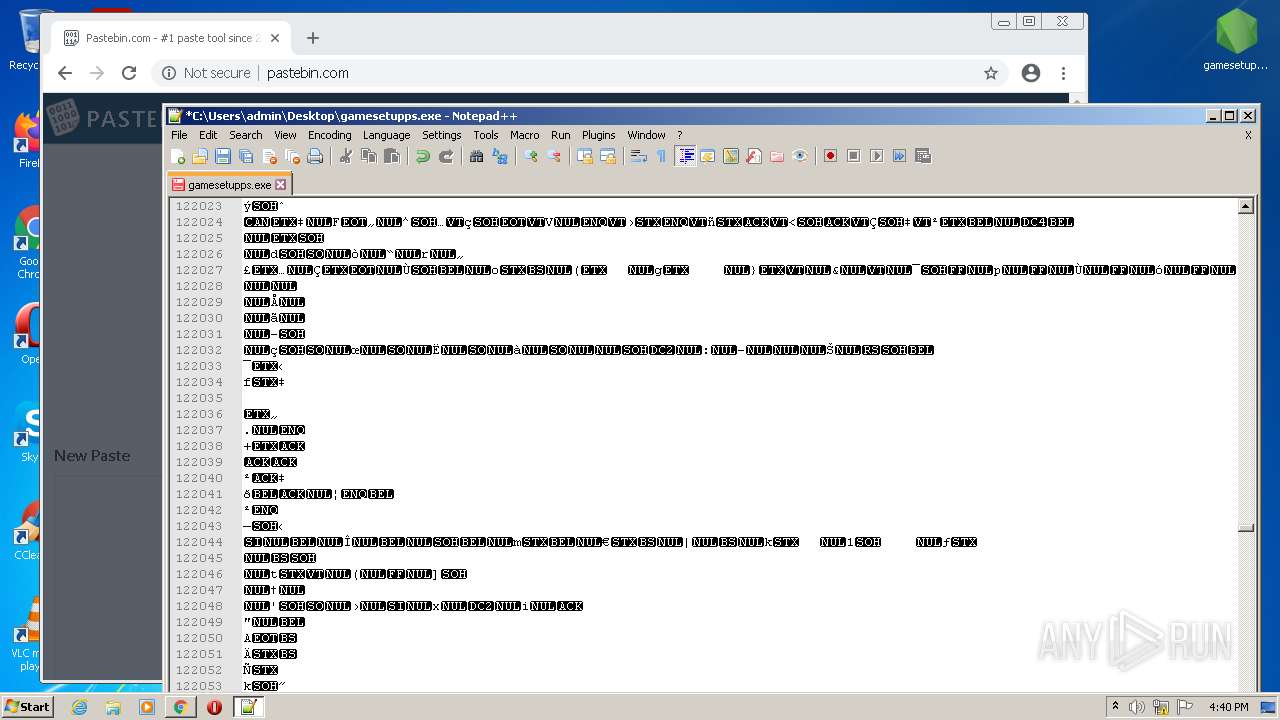
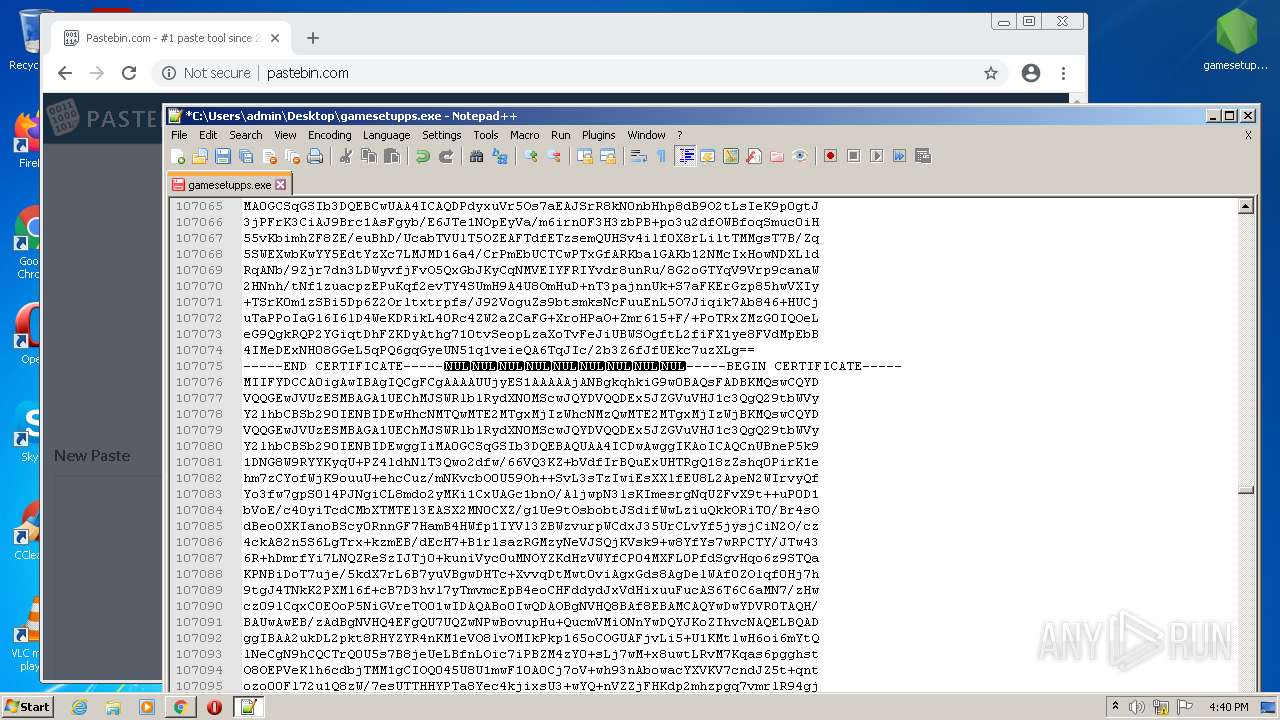
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|