analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
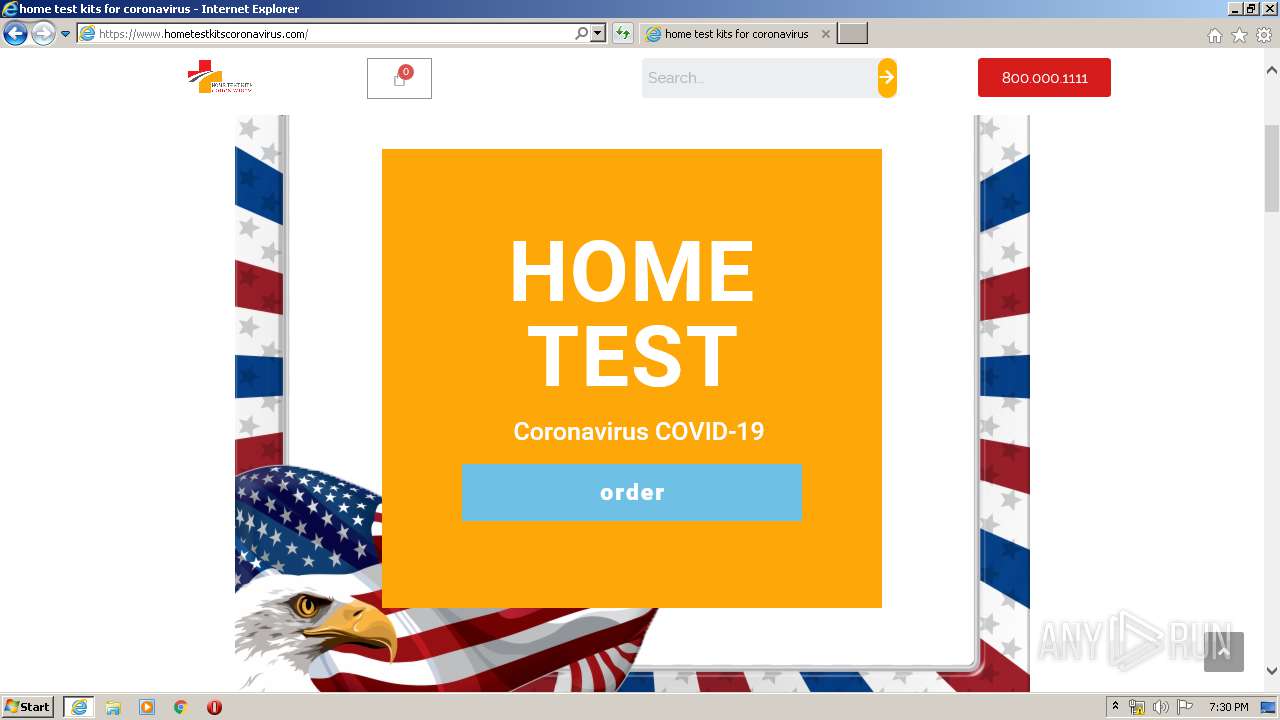
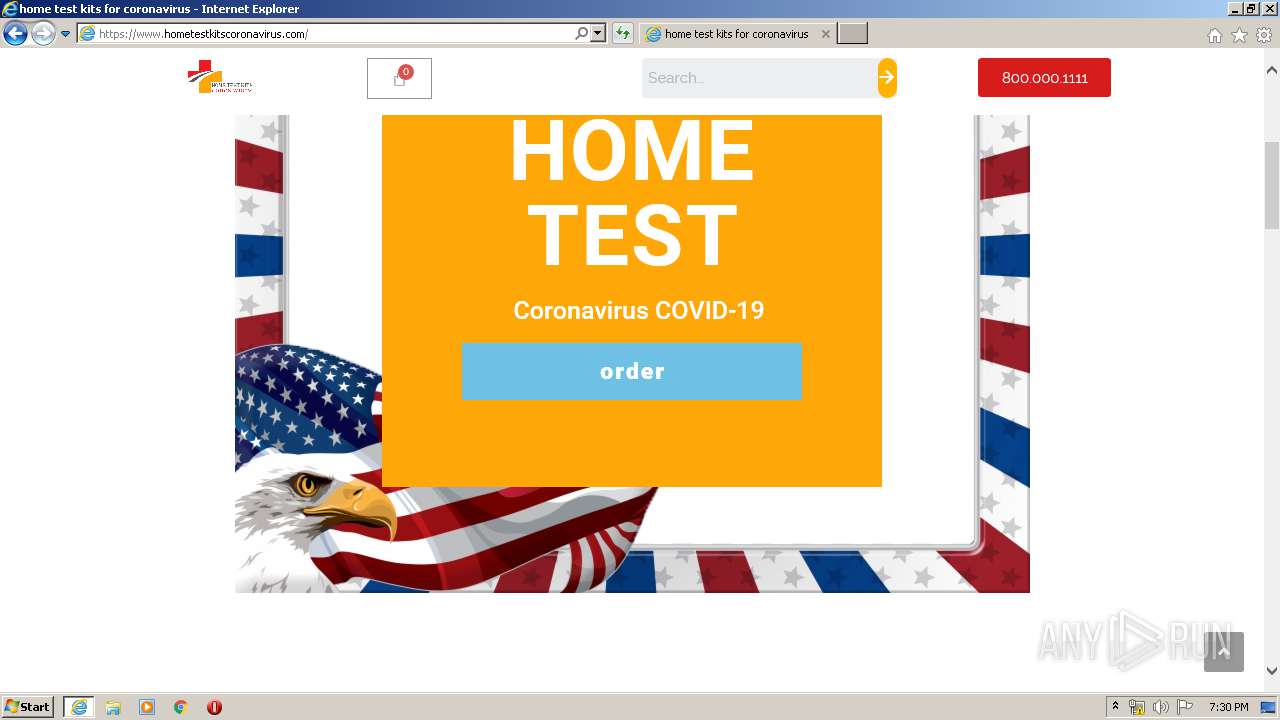
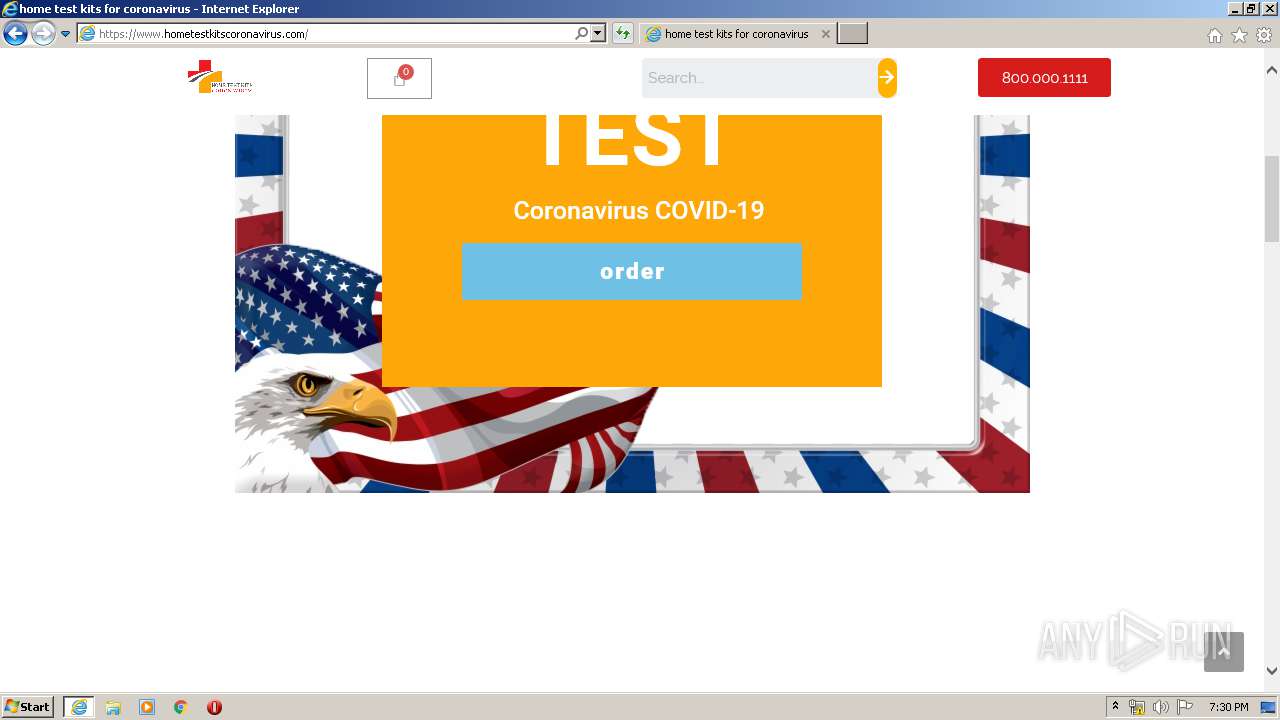
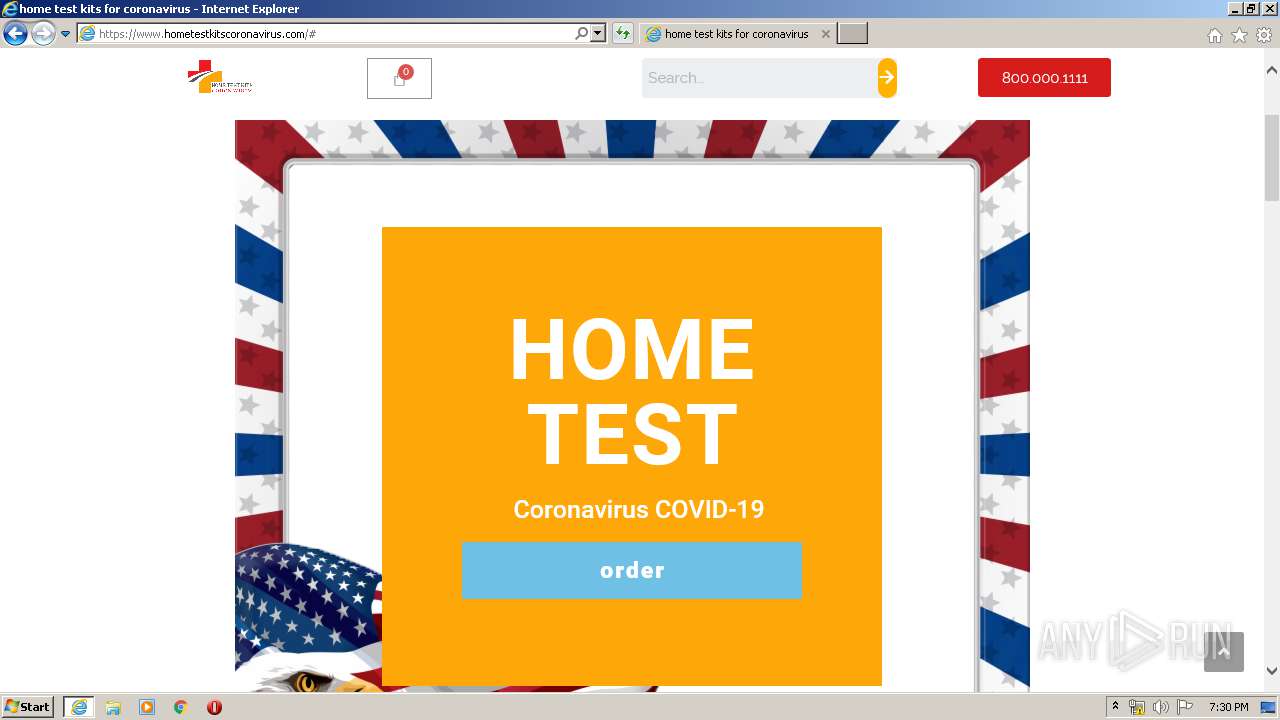
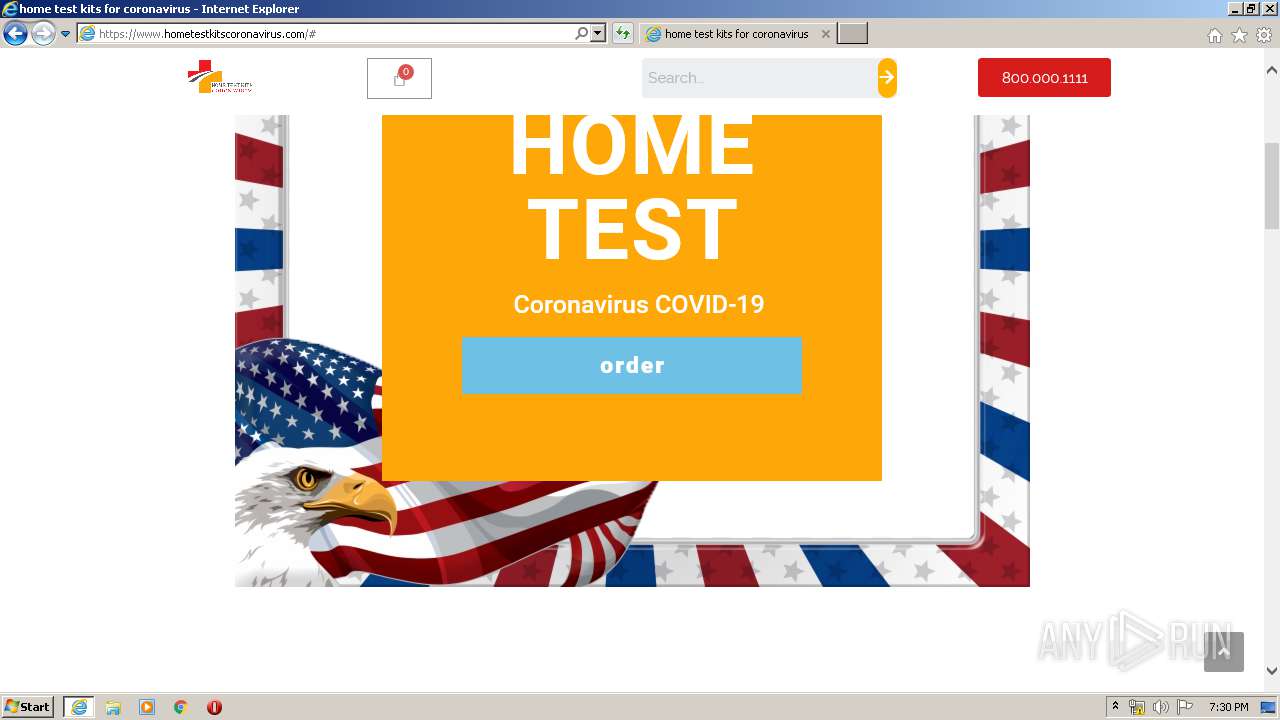
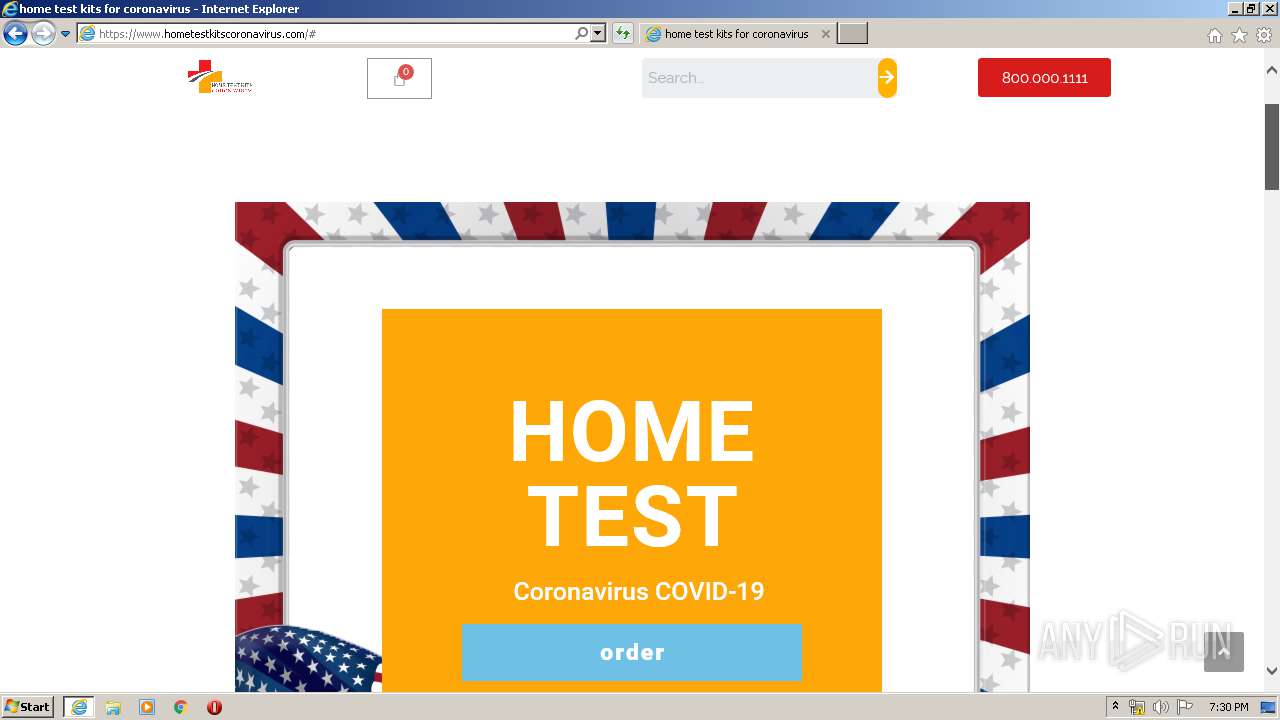
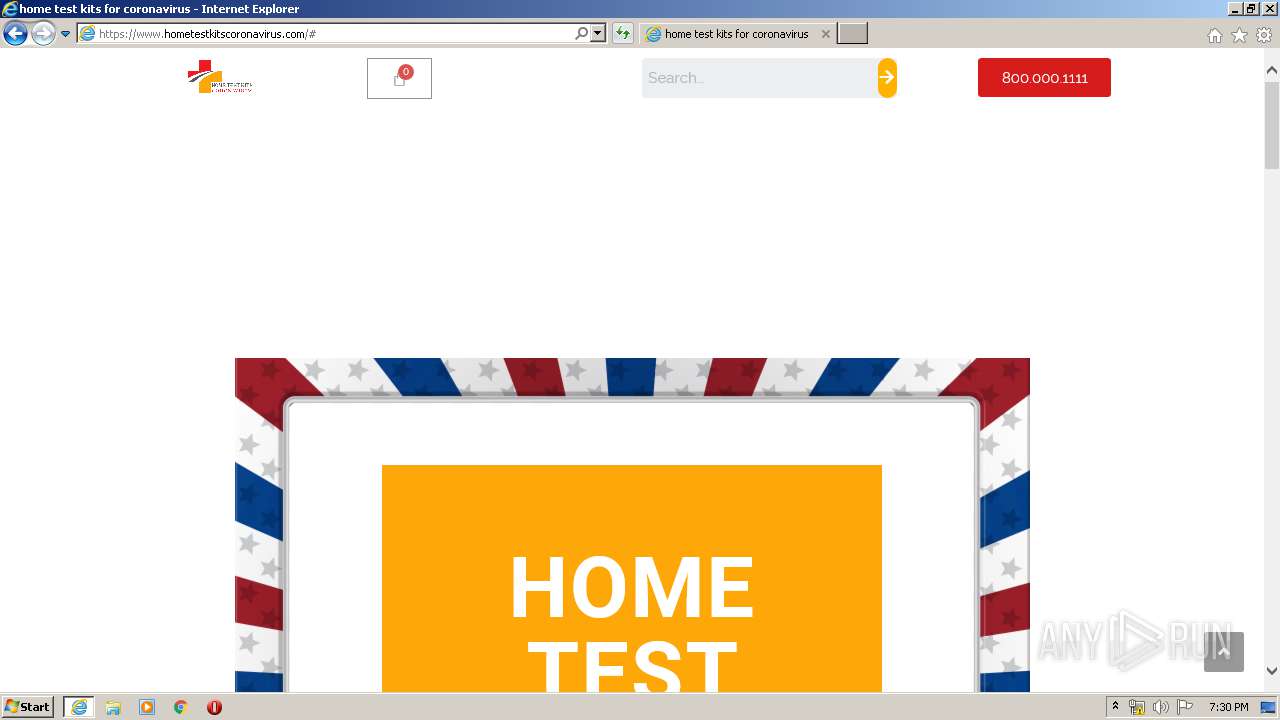
| URL: | http://www.hometestkitscoronavirus.com |
| Full analysis: | https://app.any.run/tasks/30d973ff-dcc9-4ee8-962d-8e9ac37695c9 |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 18:27:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 56A7DFEB5C3BDDB76A387D19C6723232 |
| SHA1: | B027025DE9F953299EE088AEC7FB38B7CD3CEF7C |
| SHA256: | 3AC046D7BA56FA0826FCF9E8B506AF4DD491F717B97FB0171B576435F203F811 |
| SSDEEP: | 3:N1KJS4lsPMQ6jn:Cc4lSMQ6jn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3620)
- iexplore.exe (PID: 1196)
Reads internet explorer settings
- iexplore.exe (PID: 1196)
Changes internet zones settings
- iexplore.exe (PID: 3620)
Application launched itself
- iexplore.exe (PID: 3620)
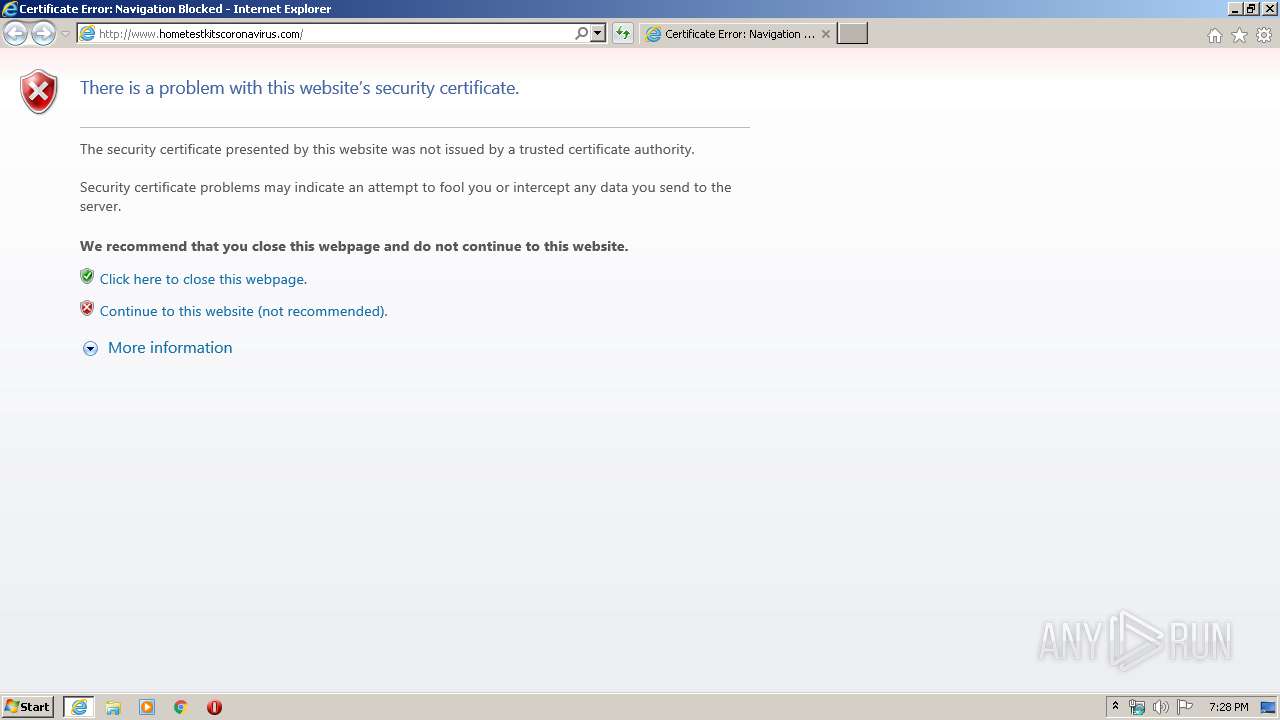
Reads settings of System Certificates
- iexplore.exe (PID: 1196)
- iexplore.exe (PID: 3620)
Drops Coronavirus (possible) decoy
- iexplore.exe (PID: 1196)
Creates files in the user directory
- iexplore.exe (PID: 3620)
Changes settings of System certificates
- iexplore.exe (PID: 3620)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 3620 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://www.hometestkitscoronavirus.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | ||||
| 1196 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3620 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | ||||
Total events
9 103
Read events
887
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
54
Text files
95
Unknown types
79
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3620 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3620 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabB3A4.tmp | — | |
MD5:— | SHA256:— | |||
| 3620 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarB3A5.tmp | — | |
MD5:— | SHA256:— | |||
| 3620 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\TKP7DMNH.txt | — | |
MD5:— | SHA256:— | |||
| 3620 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\4V3RLV70.txt | — | |
MD5:— | SHA256:— | |||
| 3620 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\verB701.tmp | — | |
MD5:— | SHA256:— | |||
| 1196 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\invalidcert[2] | text | |
MD5:8CE0833CCA8957BDA3AD7E4FE051E1DC | SHA256:F18E9671426708C65F999CA0FD11492E699CB13EDC84A7D863FA9F83EB2178C3 | |||
| 1196 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\errorPageStrings[1] | text | |
MD5:E3E4A98353F119B80B323302F26B78FA | SHA256:9466D620DC57835A2475F8F71E304F54AEE7160E134BA160BAAE0F19E5E71E66 | |||
| 1196 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\invalidcert[1] | html | |
MD5:A5D6BA8403D720F2085365C16CEBEBEF | SHA256:59E53005E12D5C200AD84AEB73B4745875973877BD7A2F5F80512FE507DE02B7 | |||
| 3620 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_D9817BD5013875AD517DA73475345203 | der | |
MD5:B211134DC2B559A0A8FDD5600FCA0662 | SHA256:471E7C400B878CF174F3D1E67CFBFF5B099378A6EAA8E4E5E346E7D6B681981E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
56
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3620 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1196 | iexplore.exe | GET | 301 | 148.66.138.141:80 | http://www.hometestkitscoronavirus.com/ | SG | — | — | suspicious |
3620 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3620 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1196 | iexplore.exe | GET | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1196 | iexplore.exe | GET | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1196 | iexplore.exe | GET | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3620 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3620 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3620 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1196 | iexplore.exe | 148.66.138.141:443 | www.hometestkitscoronavirus.com | GoDaddy.com, LLC | SG | suspicious |
3620 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3620 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3620 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3620 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1196 | iexplore.exe | 148.66.138.141:80 | www.hometestkitscoronavirus.com | GoDaddy.com, LLC | SG | suspicious |
1196 | iexplore.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1196 | iexplore.exe | 216.58.210.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1196 | iexplore.exe | 172.217.22.3:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3620 | iexplore.exe | 148.66.138.141:443 | www.hometestkitscoronavirus.com | GoDaddy.com, LLC | SG | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.hometestkitscoronavirus.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Suspicious Domain Request for Possible COVID-19 Domain M2 |
1196 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 Domain M2 |
1196 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious TLS SNI Request for Possible COVID-19 Domain M2 |
1196 | iexplore.exe | Potentially Bad Traffic | ET INFO Possible COVID-19 Domain in SSL Certificate M1 |
1196 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious TLS SNI Request for Possible COVID-19 Domain M2 |
1196 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious TLS SNI Request for Possible COVID-19 Domain M2 |
1196 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious TLS SNI Request for Possible COVID-19 Domain M2 |
1196 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious TLS SNI Request for Possible COVID-19 Domain M2 |
1196 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious TLS SNI Request for Possible COVID-19 Domain M2 |
1196 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious TLS SNI Request for Possible COVID-19 Domain M2 |