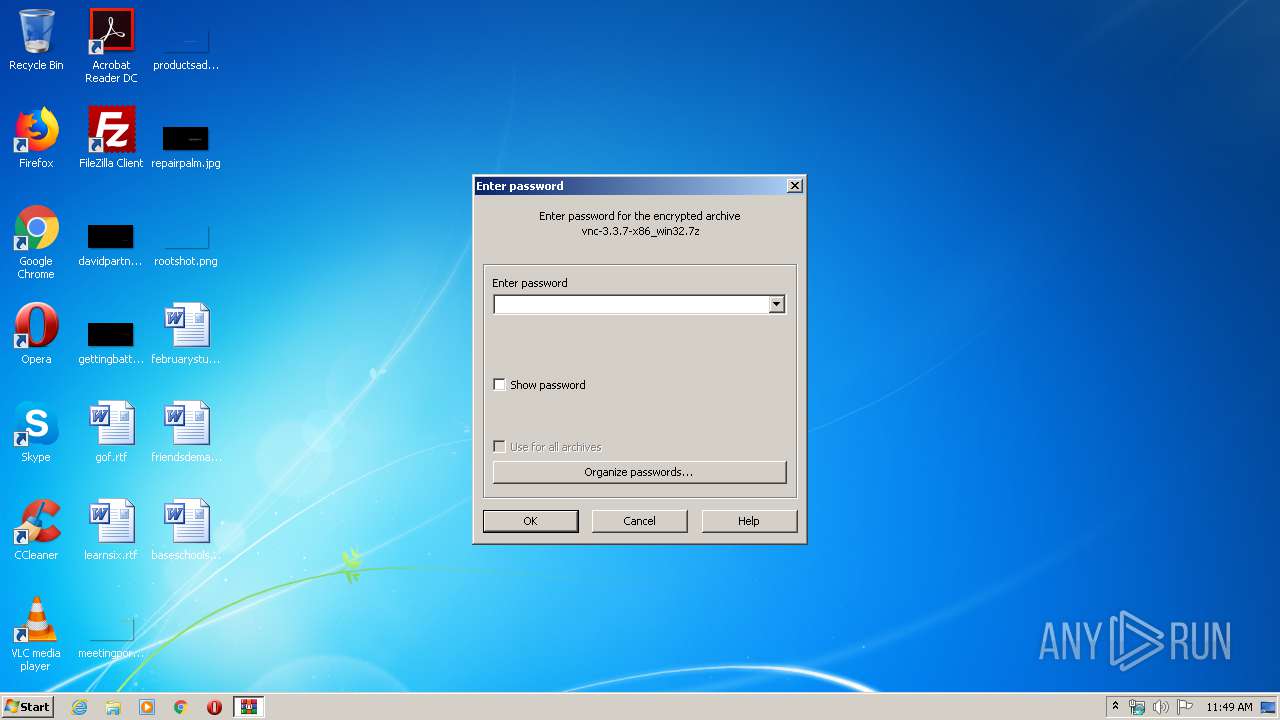
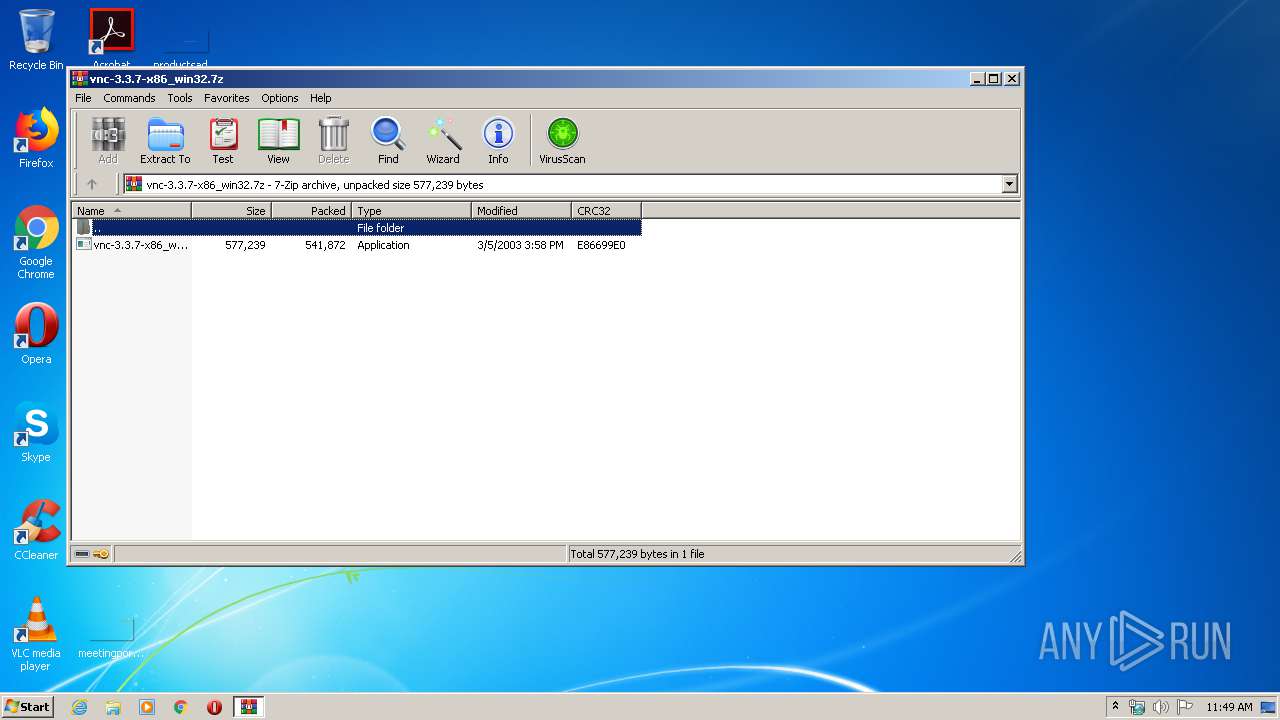
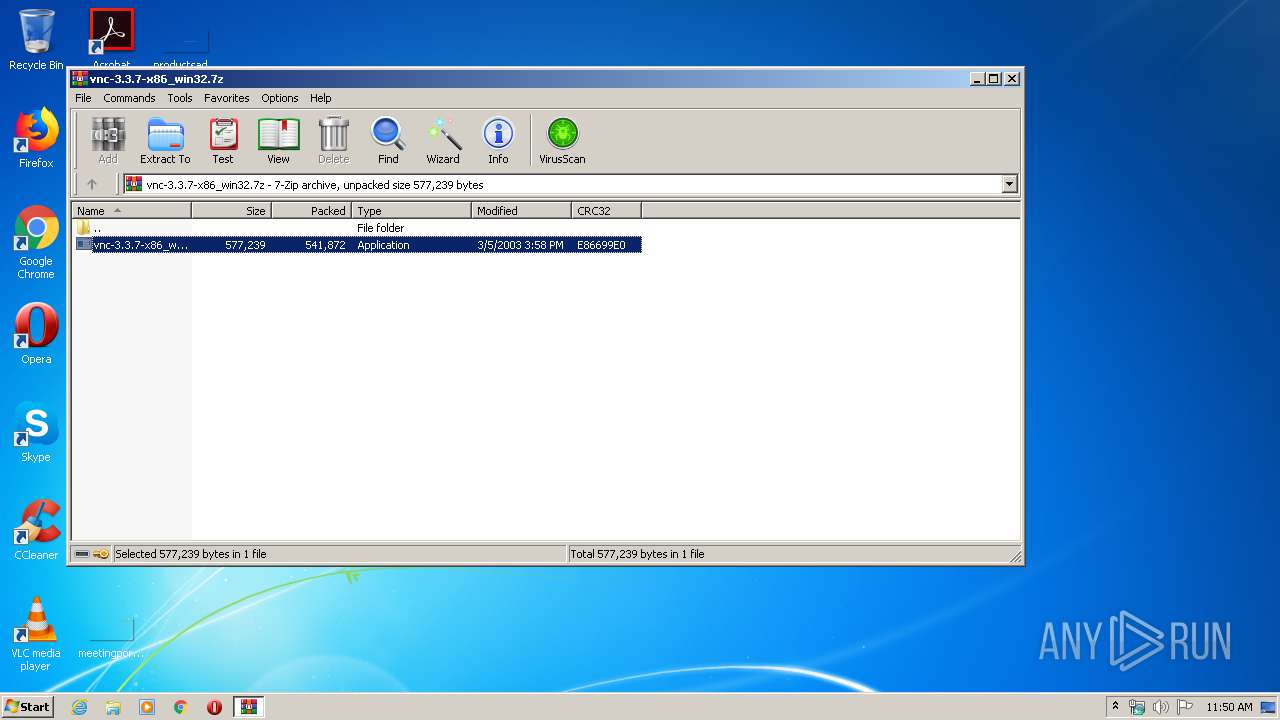
| File name: | vnc-3.3.7-x86_win32.7z |
| Full analysis: | https://app.any.run/tasks/891566a9-9ea9-462e-85d3-7333f55f42a3 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 10:49:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 2320DF1E59FBFA33A0771105A3A5CFD9 |
| SHA1: | 230F5380449871687F3DBCD688FB38906AFC6096 |
| SHA256: | 3AAB7DC7D017643132F4927DC9A555E7CA8846259252584CFBE7826FBD5D7B19 |
| SSDEEP: | 12288:HM5k26Y+bR5N03HR2aAi6iZB+Q5wiAPgyLHVOgk73A:HZ2YbR4Hofu5wiAPzzVOgV |
MALICIOUS
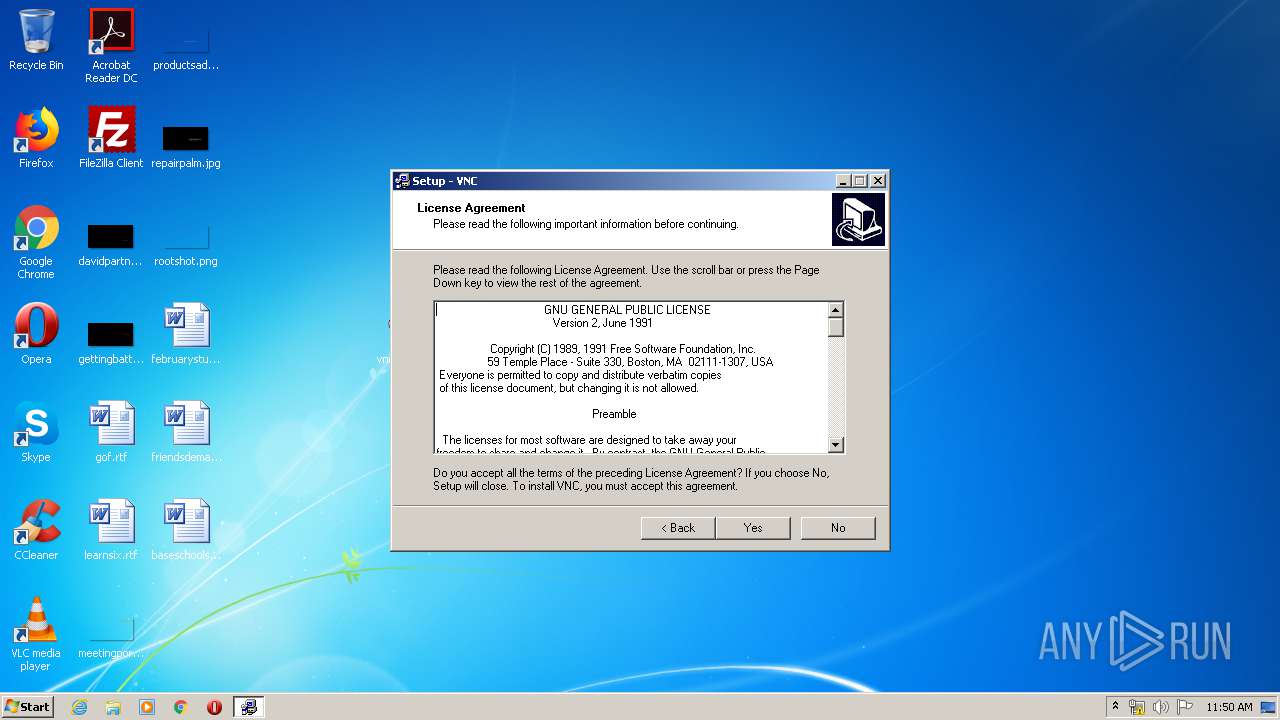
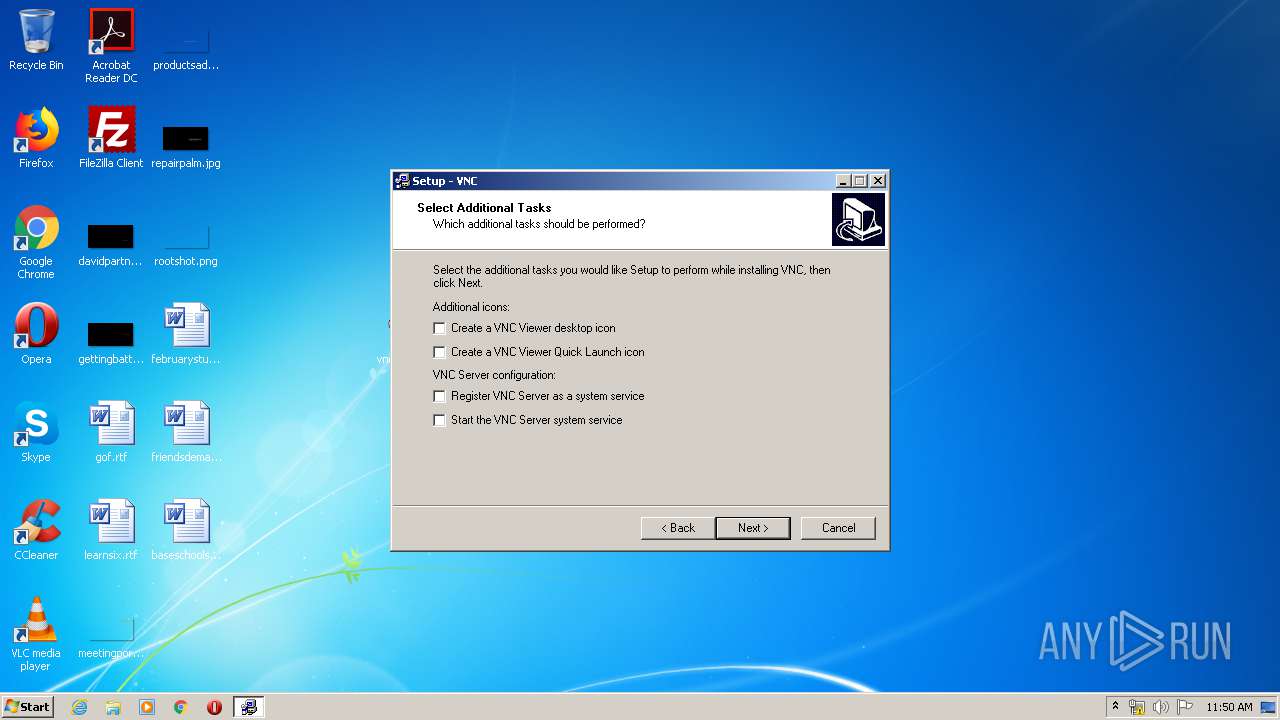
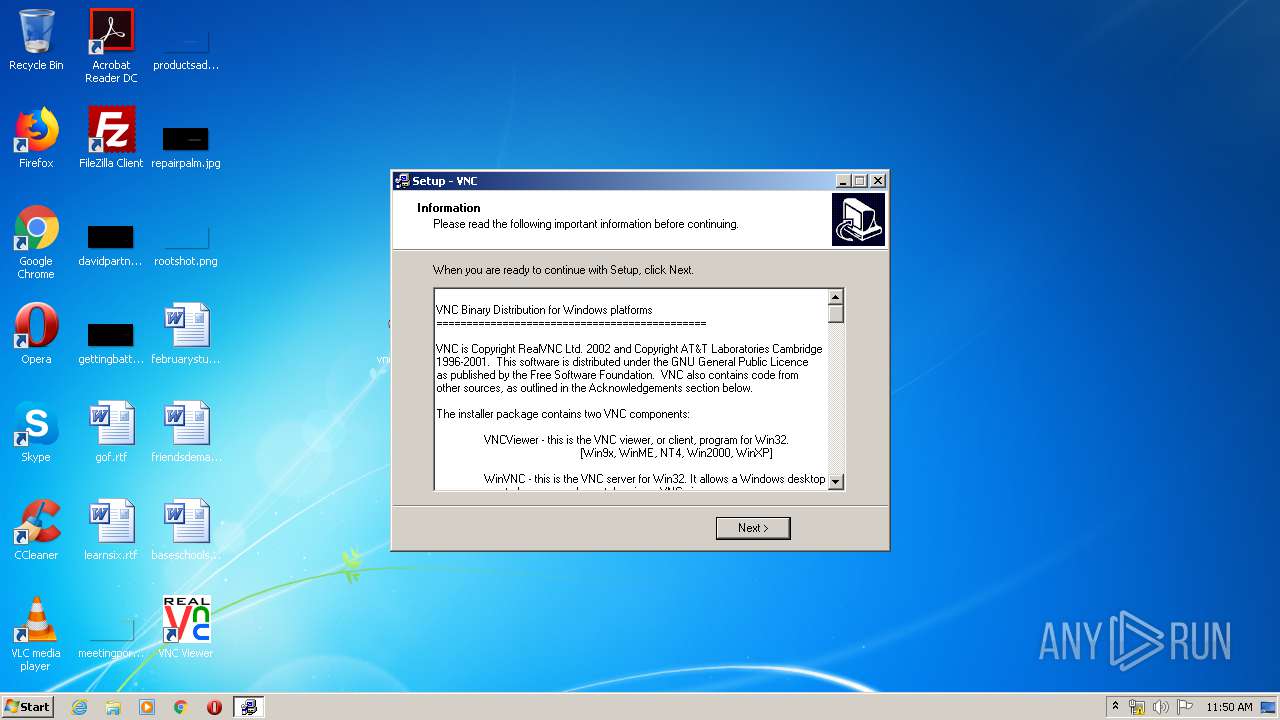
Application was dropped or rewritten from another process
- vnc-3.3.7-x86_win32.exe (PID: 1536)
- vnc-3.3.7-x86_win32.exe (PID: 3168)
- INS36F2.tmp (PID: 3884)
Loads dropped or rewritten executable
- INS36F2.tmp (PID: 3884)
SUSPICIOUS
Executable content was dropped or overwritten
- INS36F2.tmp (PID: 3884)
- WinRAR.exe (PID: 2896)
- vnc-3.3.7-x86_win32.exe (PID: 1536)
Starts application with an unusual extension
- vnc-3.3.7-x86_win32.exe (PID: 1536)
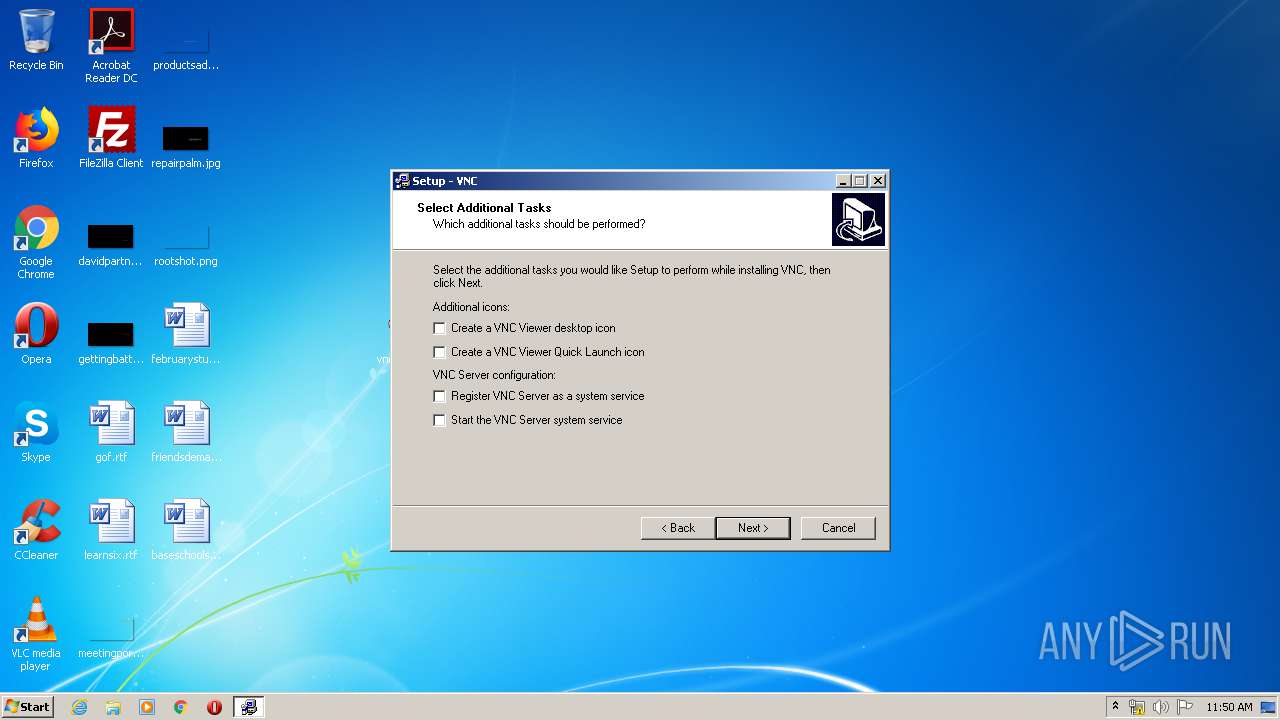
Creates files in the program directory
- INS36F2.tmp (PID: 3884)
Creates a software uninstall entry
- INS36F2.tmp (PID: 3884)
INFO
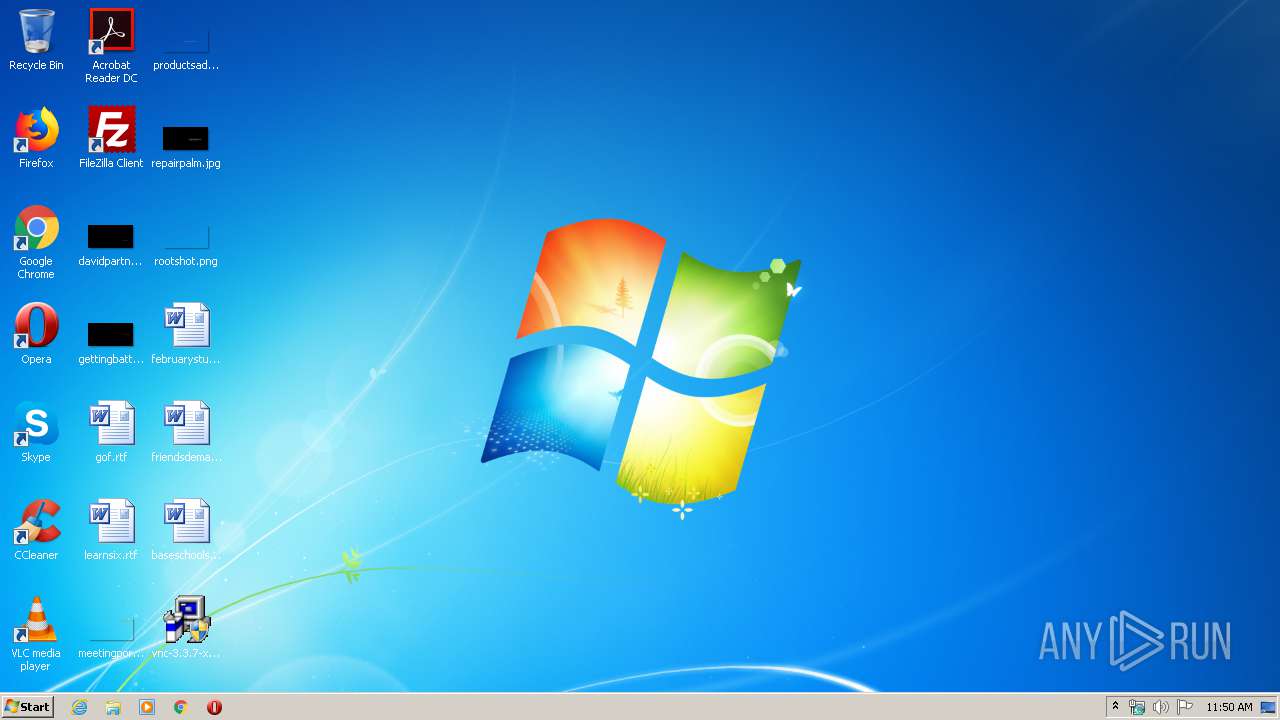
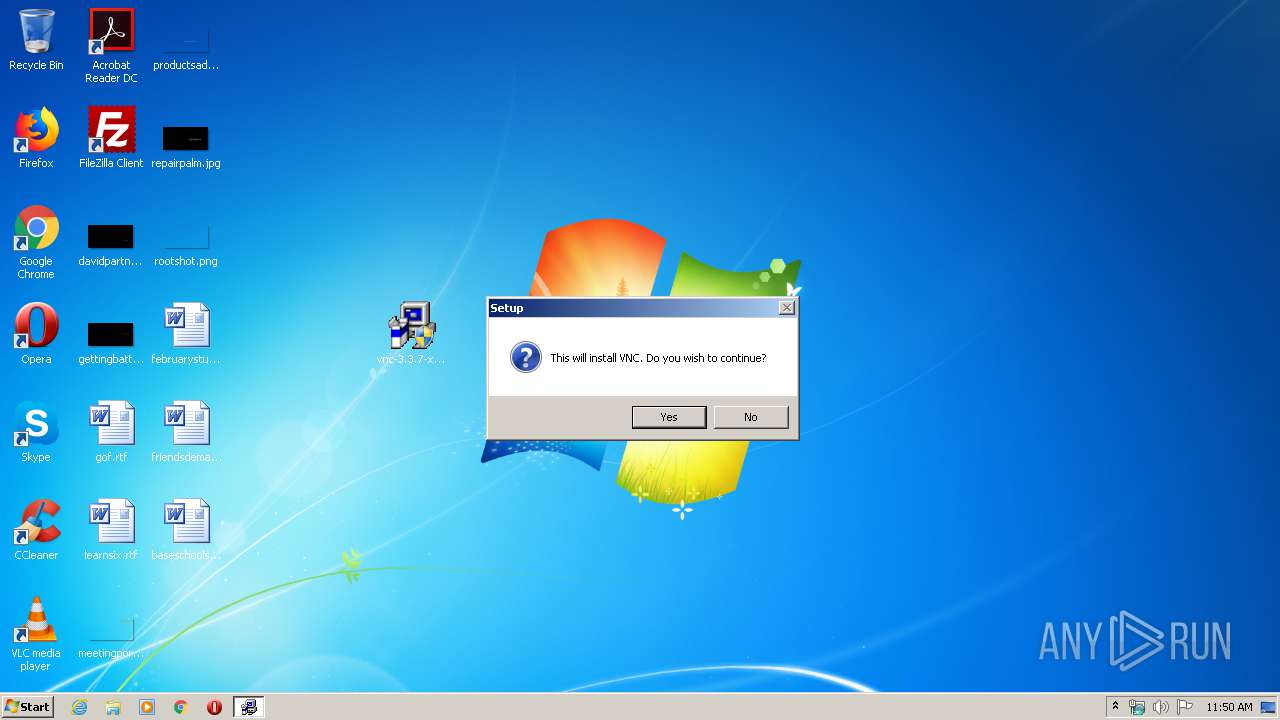
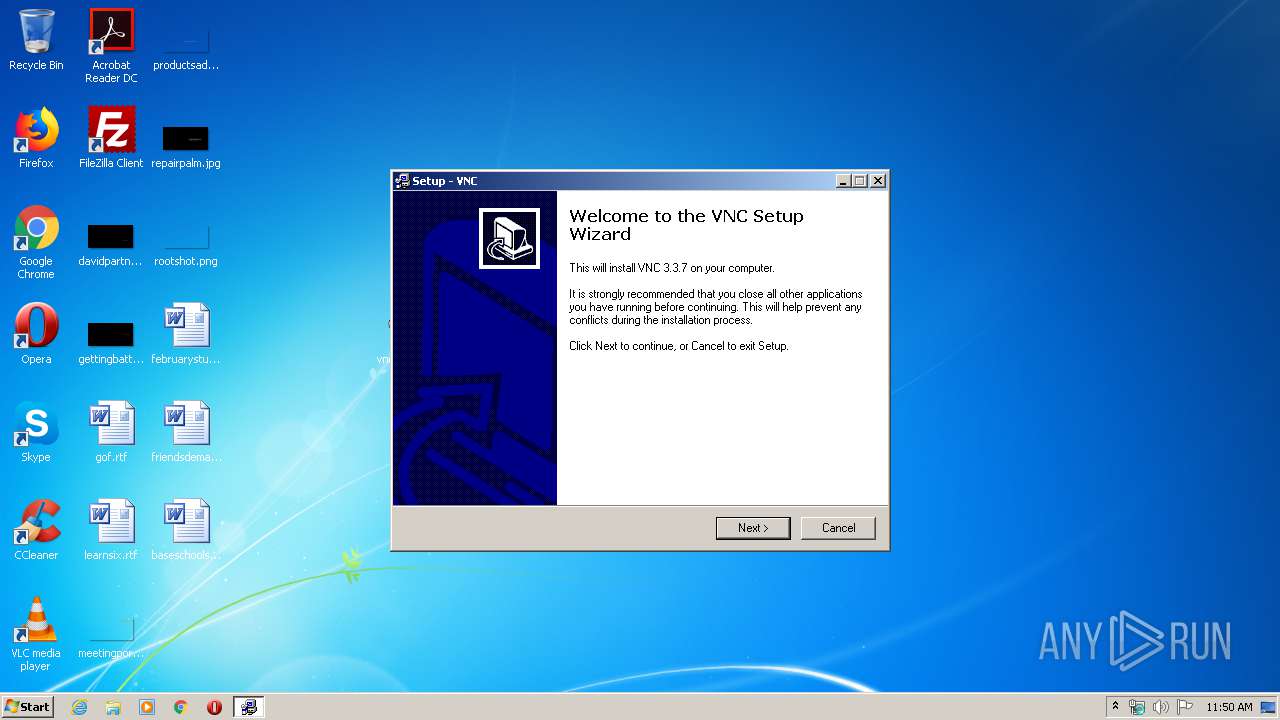
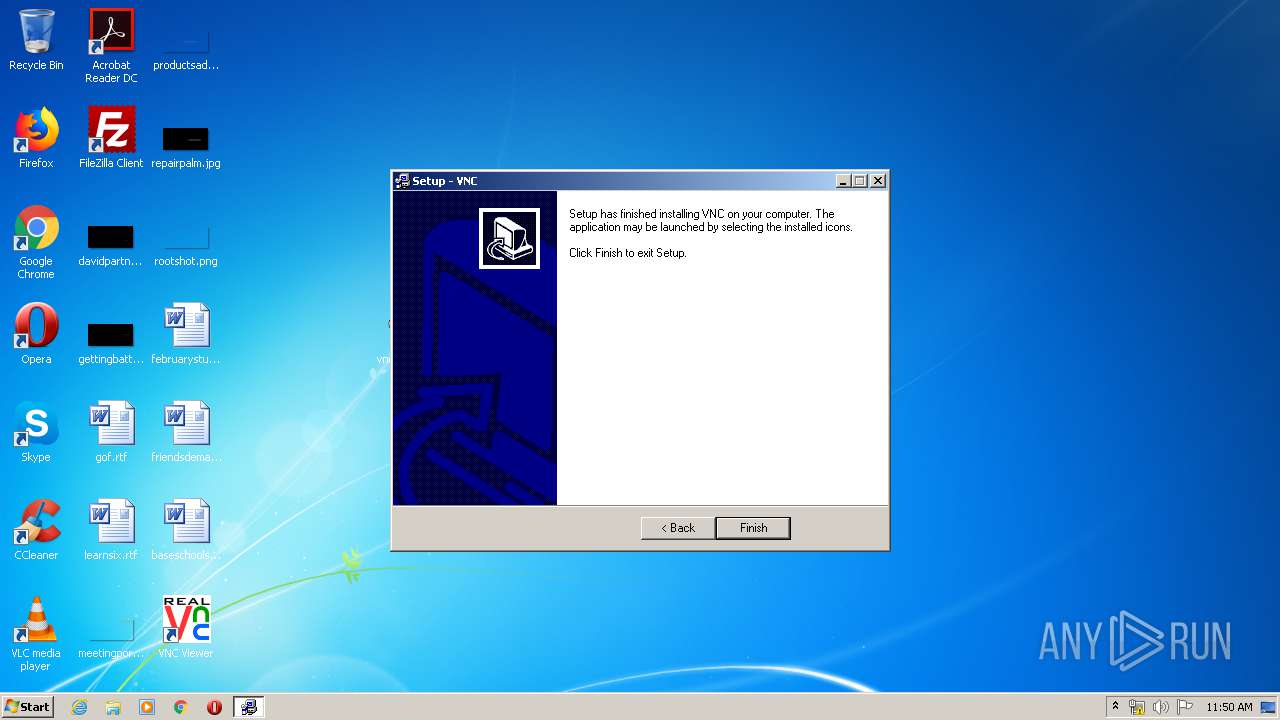
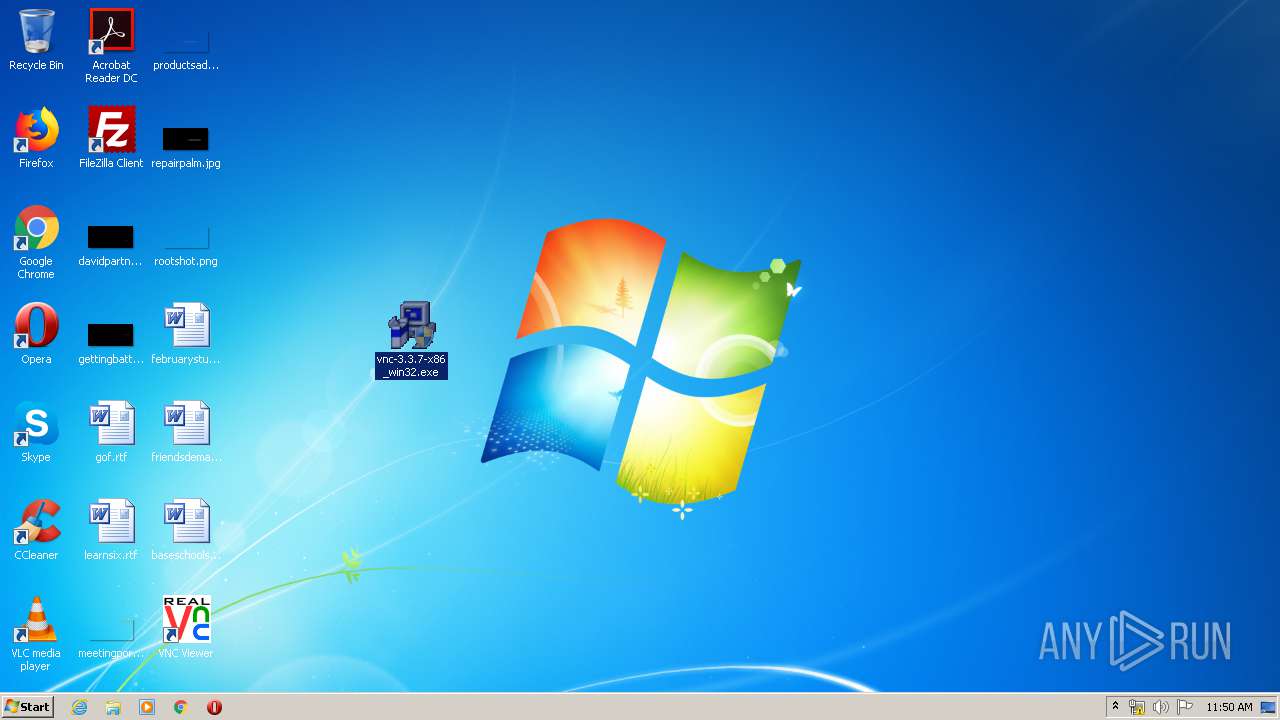
Manual execution by user
- vnc-3.3.7-x86_win32.exe (PID: 3168)
- vnc-3.3.7-x86_win32.exe (PID: 1536)
Dropped object may contain Bitcoin addresses
- INS36F2.tmp (PID: 3884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
43
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
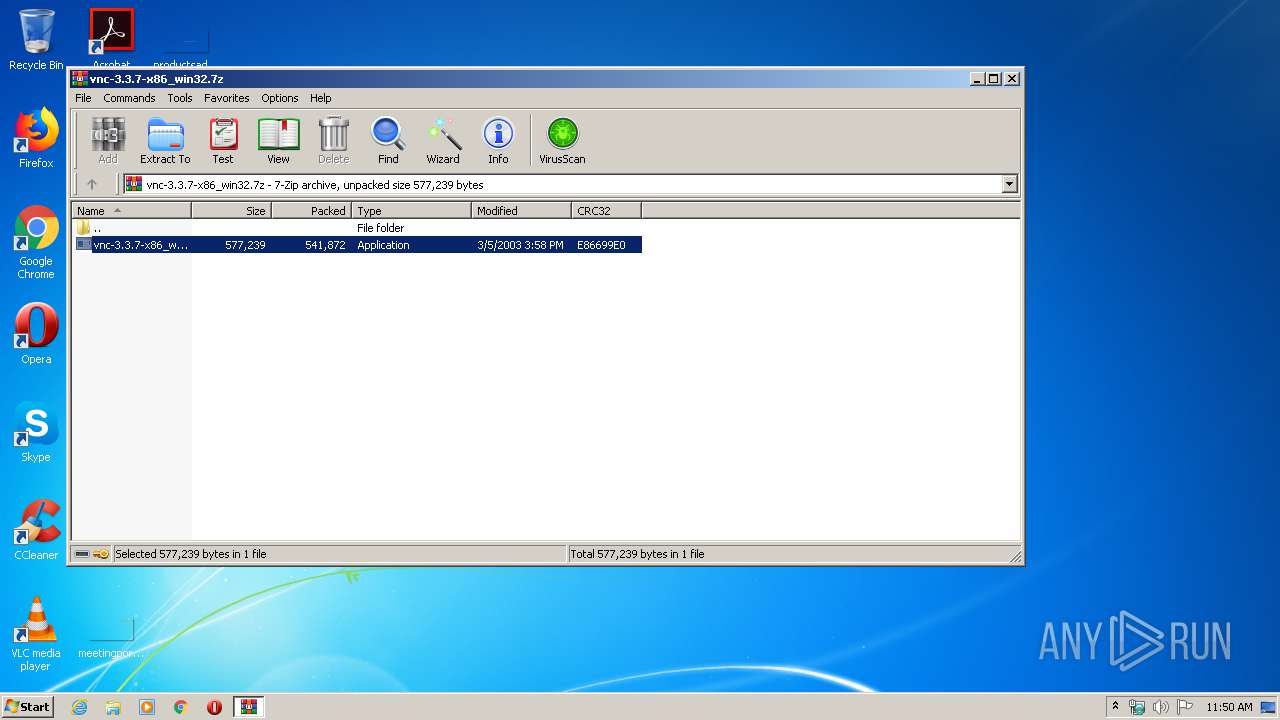
| 1536 | "C:\Users\admin\Desktop\vnc-3.3.7-x86_win32.exe" | C:\Users\admin\Desktop\vnc-3.3.7-x86_win32.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
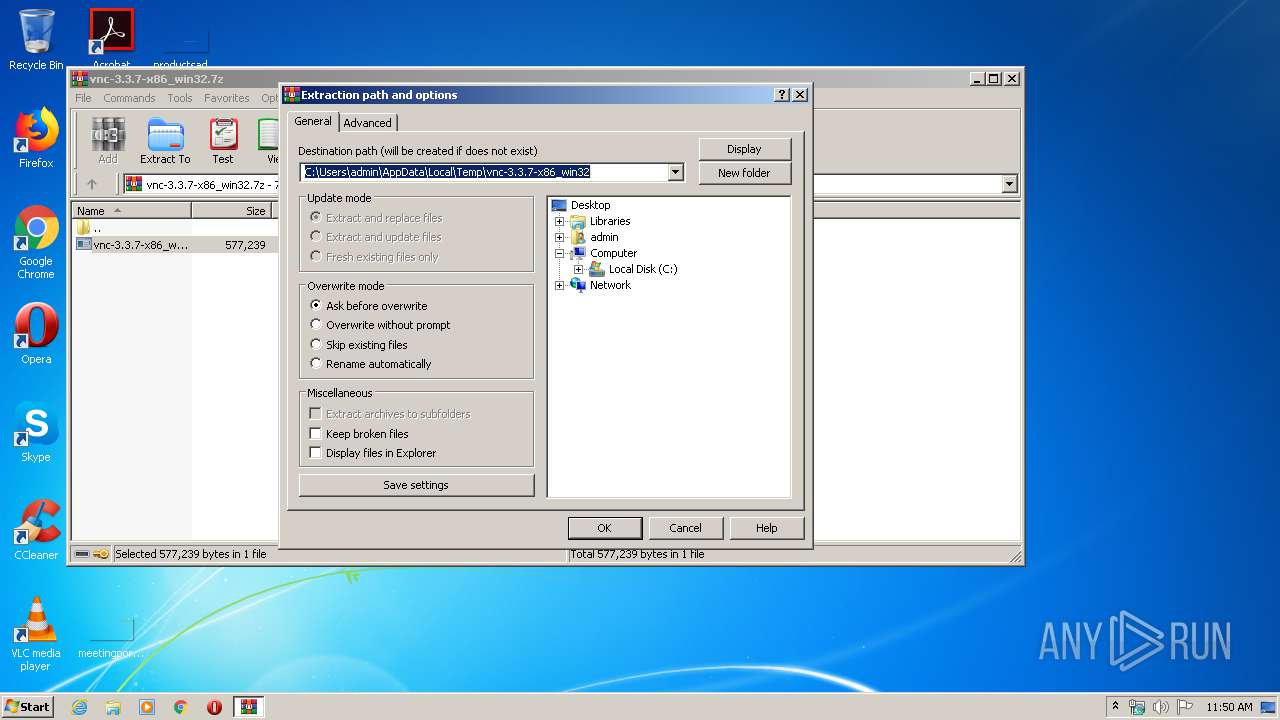
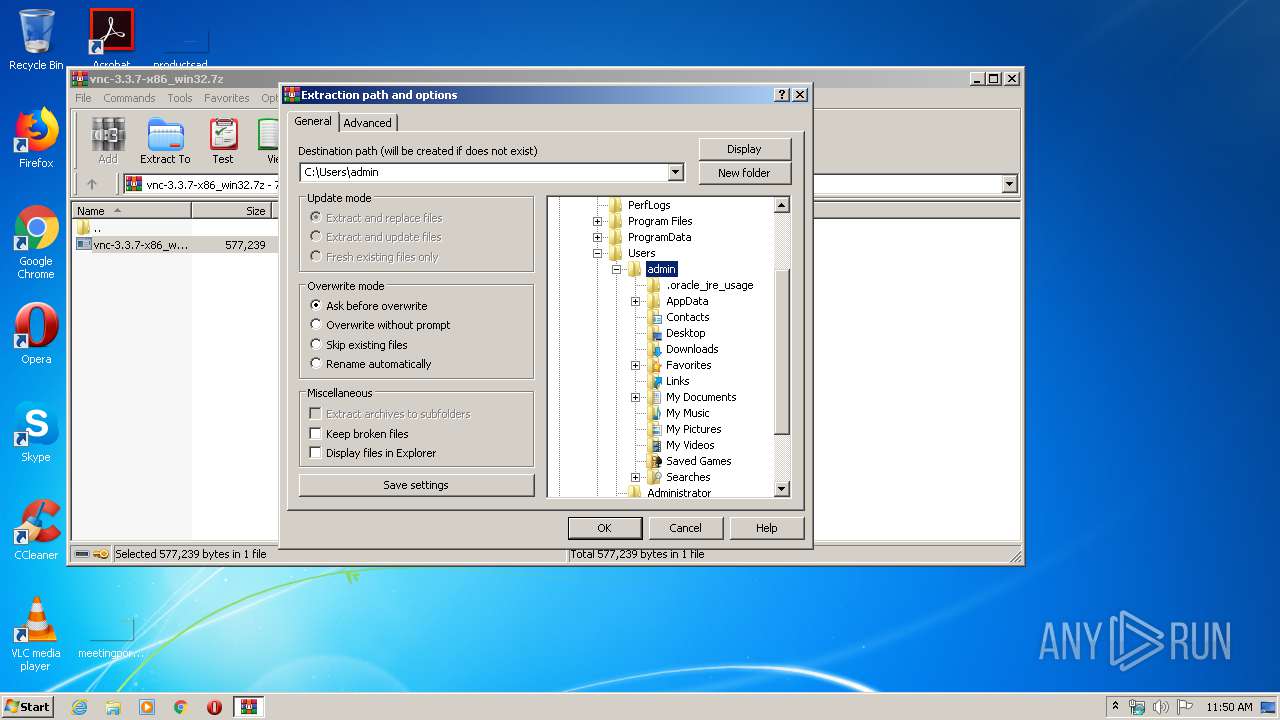
| 2896 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\vnc-3.3.7-x86_win32.7z" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3168 | "C:\Users\admin\Desktop\vnc-3.3.7-x86_win32.exe" | C:\Users\admin\Desktop\vnc-3.3.7-x86_win32.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
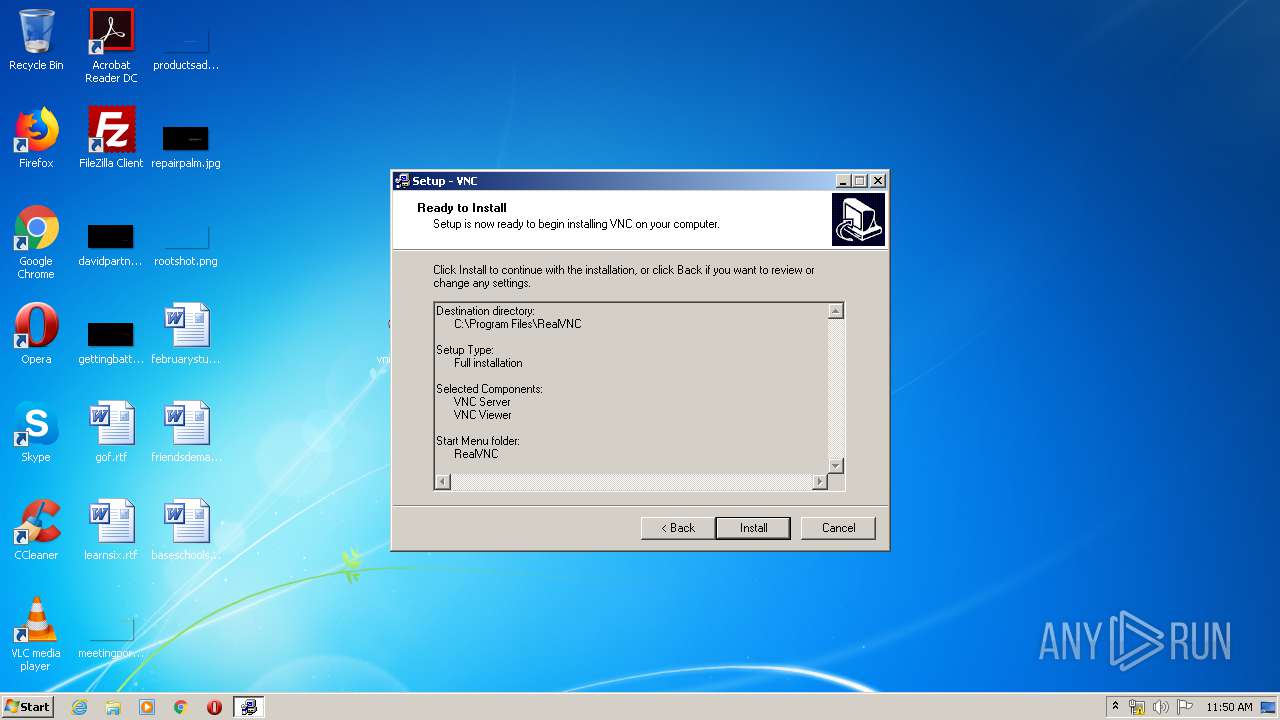
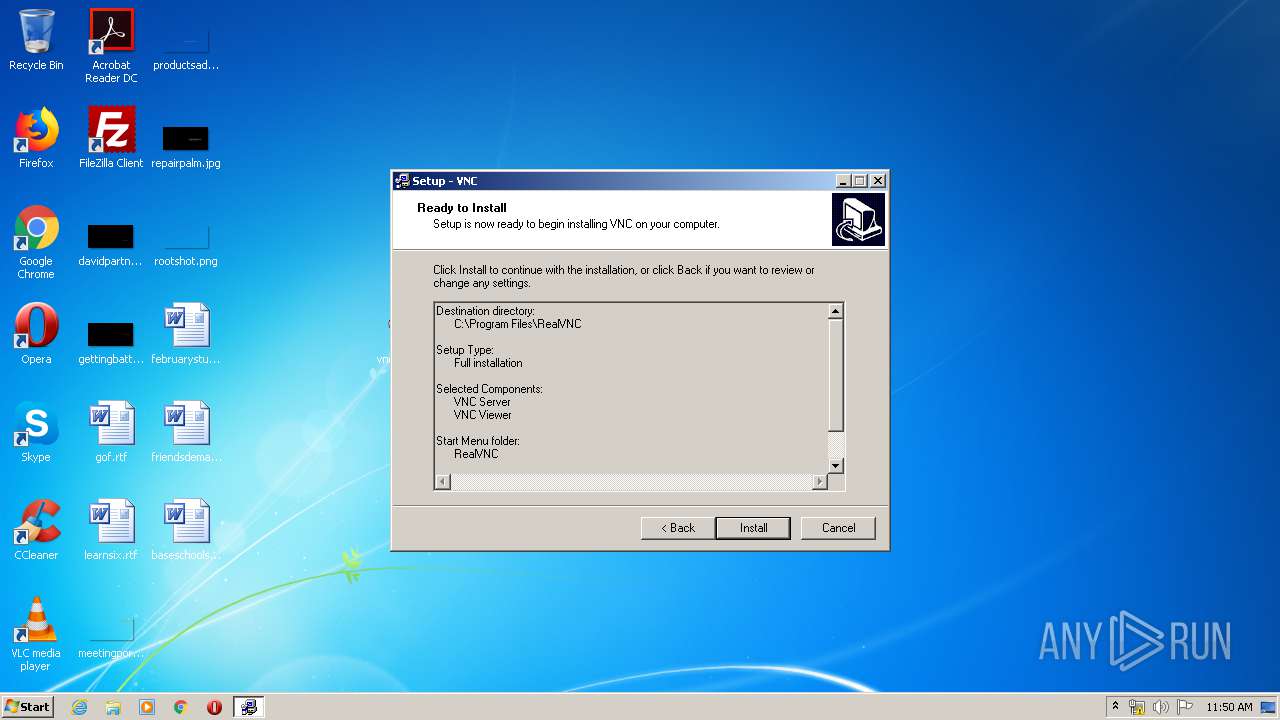
| 3884 | C:\Users\admin\AppData\Local\Temp\INS36F2.tmp /SL3 $C024E C:\Users\admin\Desktop\vnc-3.3.7-x86_win32.exe 560733 564093 61440 | C:\Users\admin\AppData\Local\Temp\INS36F2.tmp | vnc-3.3.7-x86_win32.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
701
Read events
658
Write events
43
Delete events
0
Modification events
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\vnc-3.3.7-x86_win32.7z | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2896) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
Executable files
9
Suspicious files
0
Text files
0
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
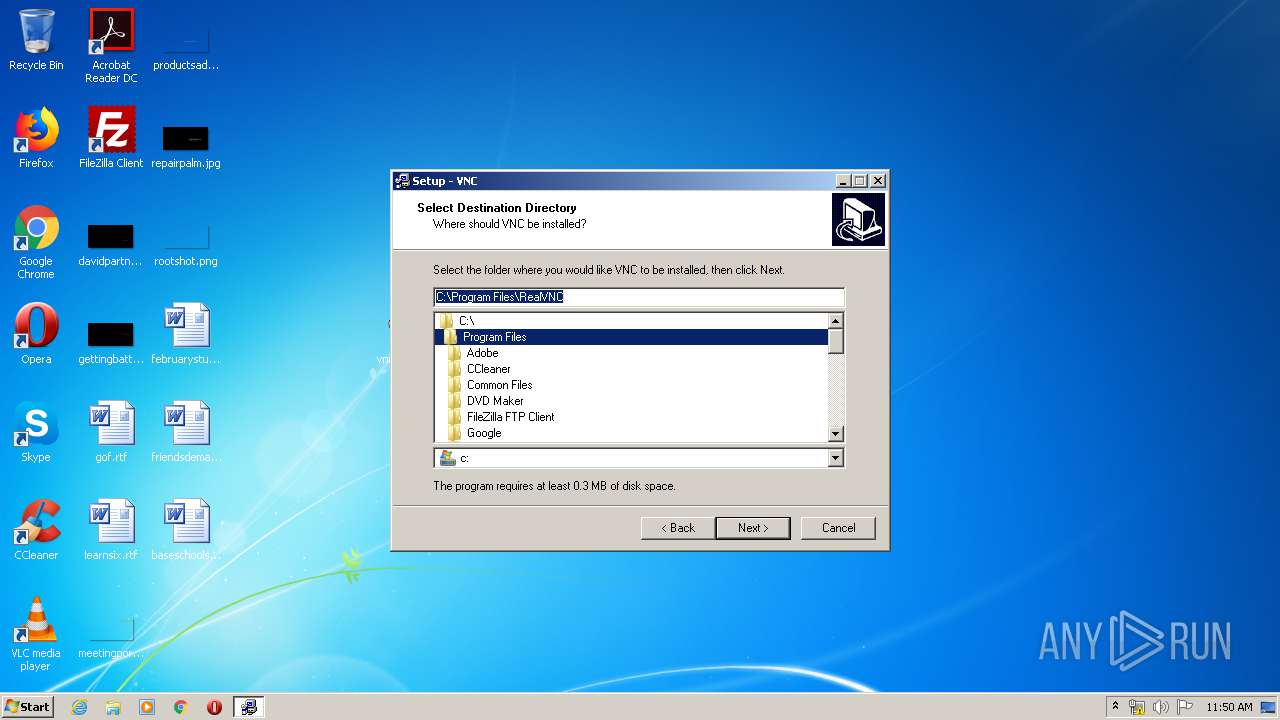
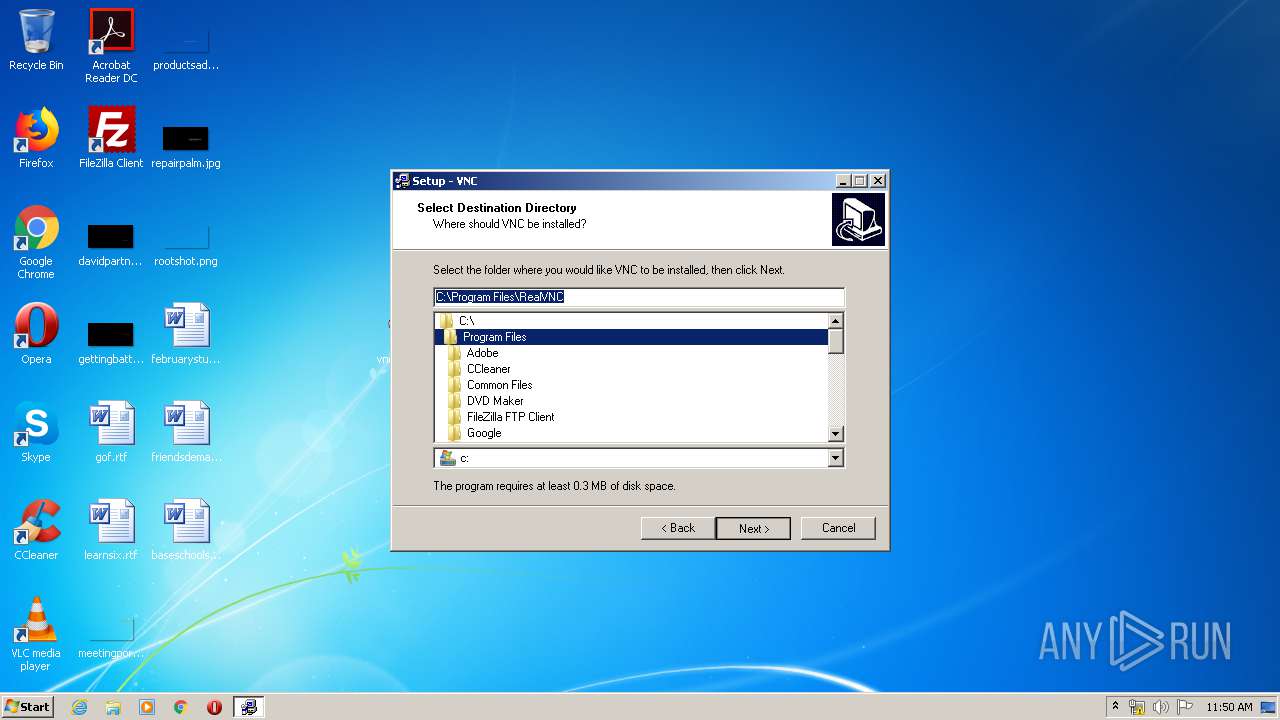
| 3884 | INS36F2.tmp | C:\Program Files\RealVNC\is-NVK6E.tmp | — | |
MD5:— | SHA256:— | |||
| 3884 | INS36F2.tmp | C:\Program Files\RealVNC\WinVNC\is-I4SEA.tmp | — | |
MD5:— | SHA256:— | |||
| 3884 | INS36F2.tmp | C:\Program Files\RealVNC\WinVNC\is-8GFN2.tmp | — | |
MD5:— | SHA256:— | |||
| 3884 | INS36F2.tmp | C:\Program Files\RealVNC\WinVNC\is-PAA92.tmp | — | |
MD5:— | SHA256:— | |||
| 3884 | INS36F2.tmp | C:\Program Files\RealVNC\is-MOQ29.tmp | — | |
MD5:— | SHA256:— | |||
| 3884 | INS36F2.tmp | C:\Users\admin\AppData\Local\Temp\is-M5AUG.tmp\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
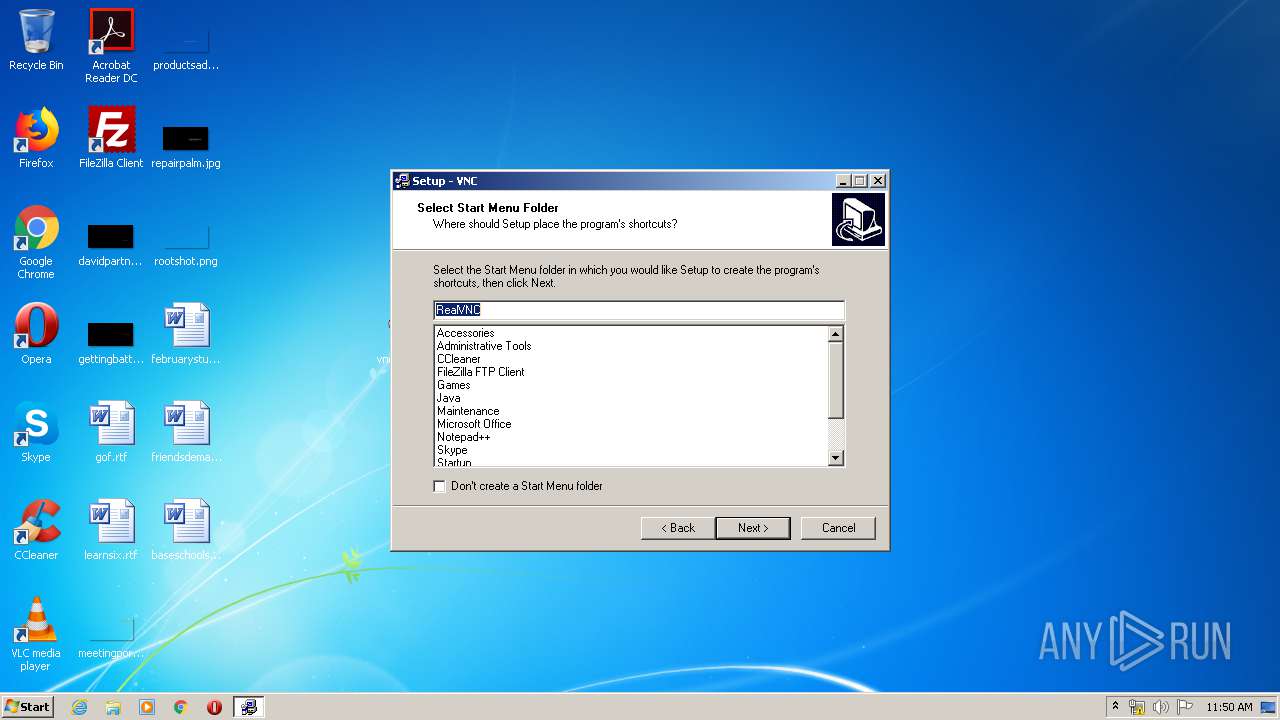
| 3884 | INS36F2.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\RealVNC\VNC Server\Run Service Helper.lnk | lnk | |
MD5:B35810E8F61A089F4BECA16095883486 | SHA256:3F91E30DBF9D33F62272574AFE351264F6F7B3EA01576B6595977315D5665F54 | |||
| 3884 | INS36F2.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\RealVNC\VNC Server\Show Default Properties.lnk | lnk | |
MD5:75EBAFFE0777D69BBC0ED8D2949DB727 | SHA256:DAFFD5194E6086CFC86228F795C44D6B53B16030DFBA683A8DCA56AEF87811B6 | |||
| 3884 | INS36F2.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\RealVNC\VNC Server\Show About Box.lnk | lnk | |
MD5:69B0BABDACB6CE21A1ACA3DC4364BCF3 | SHA256:51DB75229B43612F39AAF8BB741DB9CD8969955776493E3A0596088A33A61E86 | |||
| 3884 | INS36F2.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\RealVNC\Run VNC Server.lnk | lnk | |
MD5:08E23A1EAD94CBD6E9DA9C256ABBE663 | SHA256:94461EC03E1120A4474EFF458B35755A35DA6F1BF33E615CC8860685C0DAEB59 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report