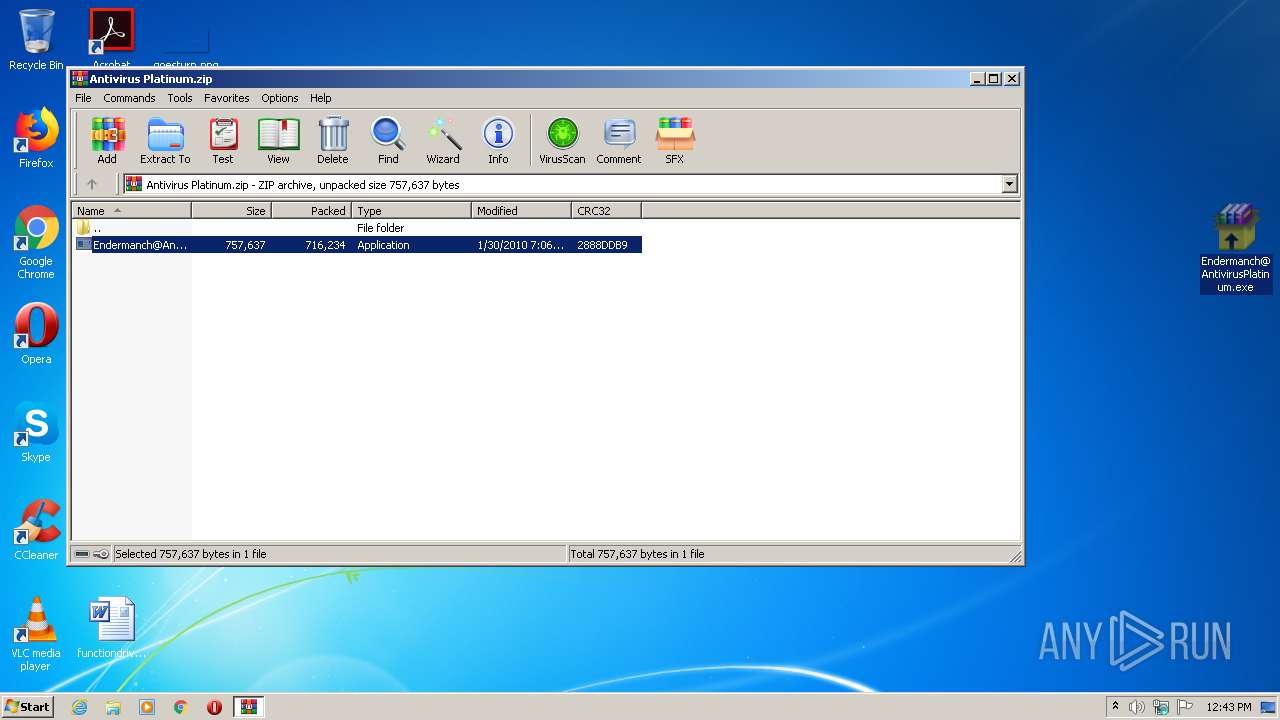
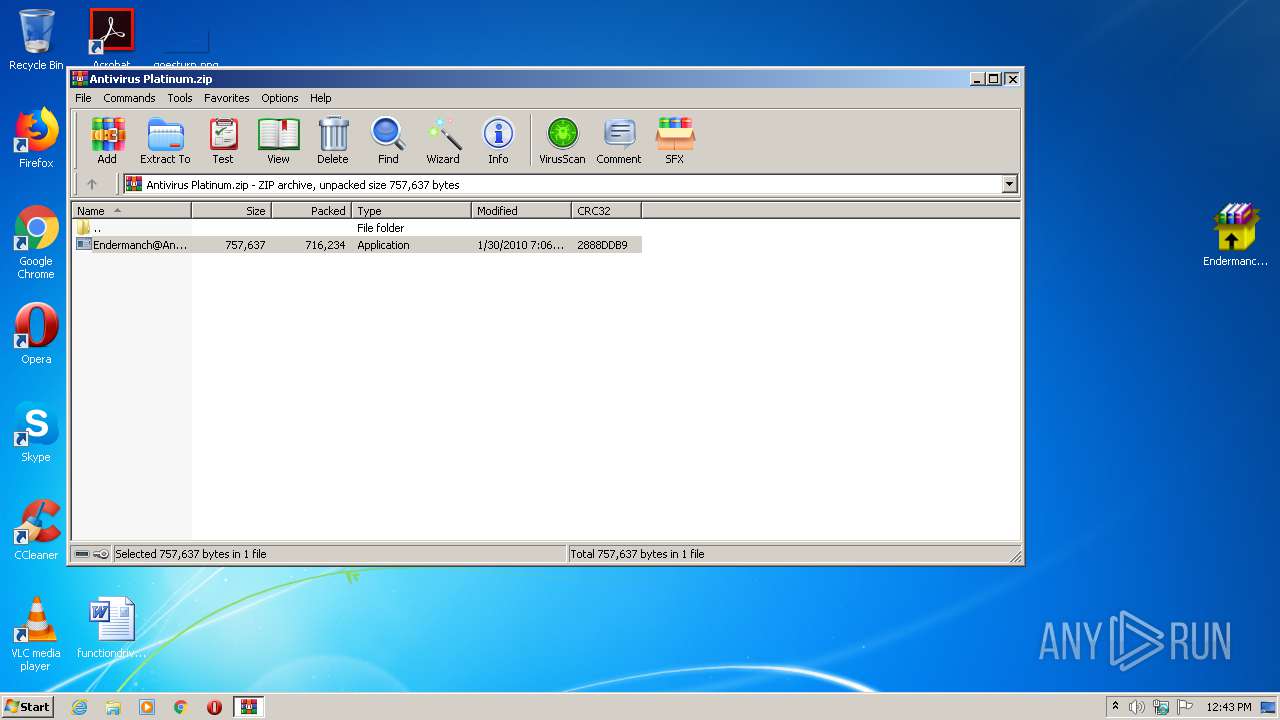
| File name: | Antivirus Platinum.zip |
| Full analysis: | https://app.any.run/tasks/d93ba477-8d03-4756-938b-8d4d8969562b |
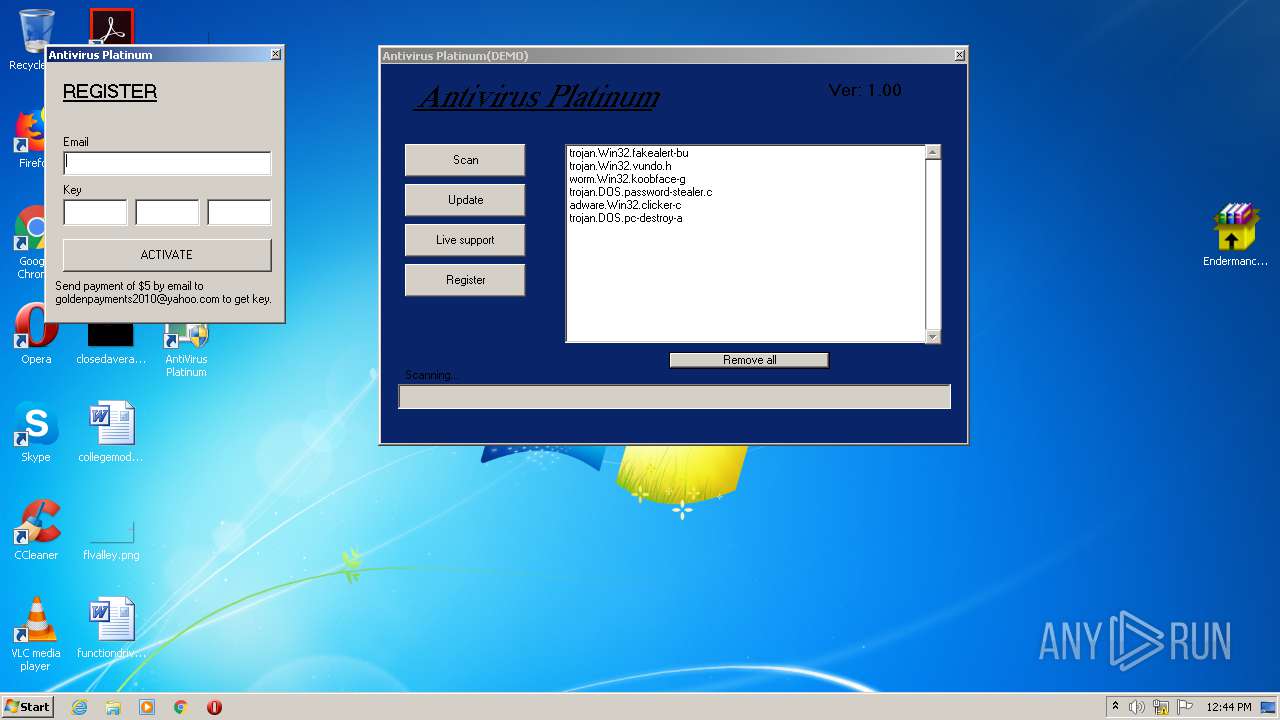
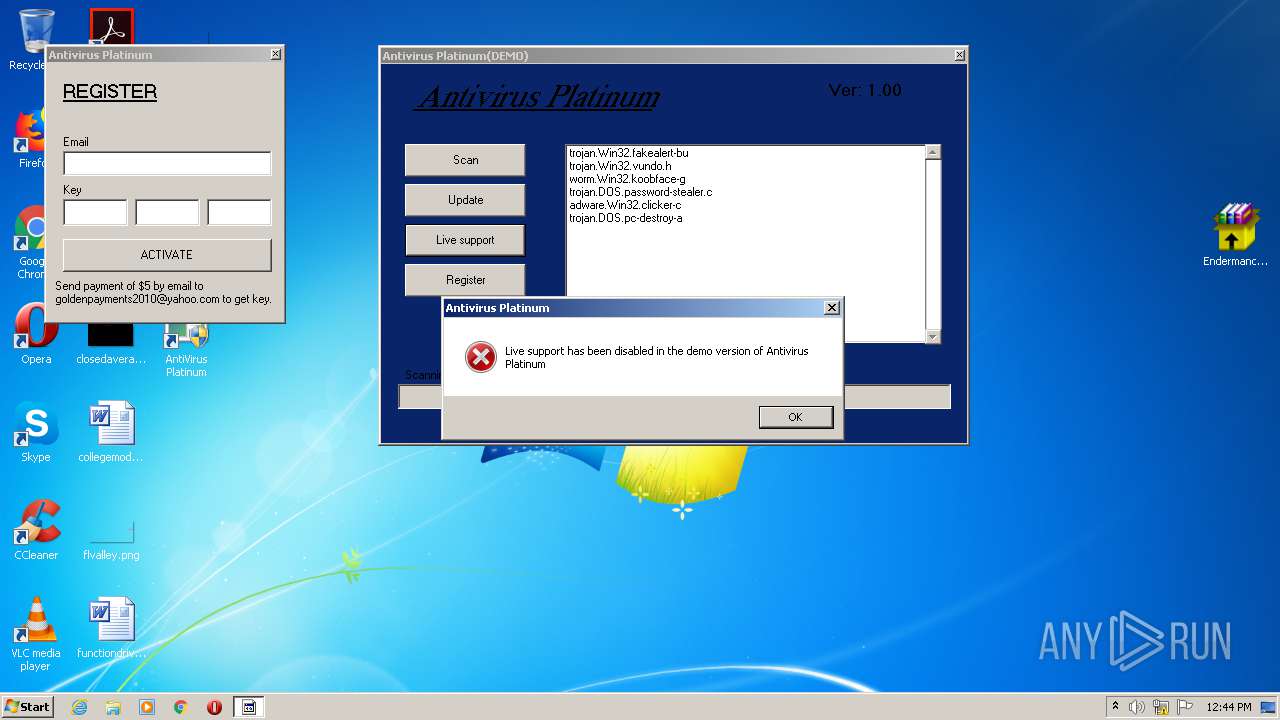
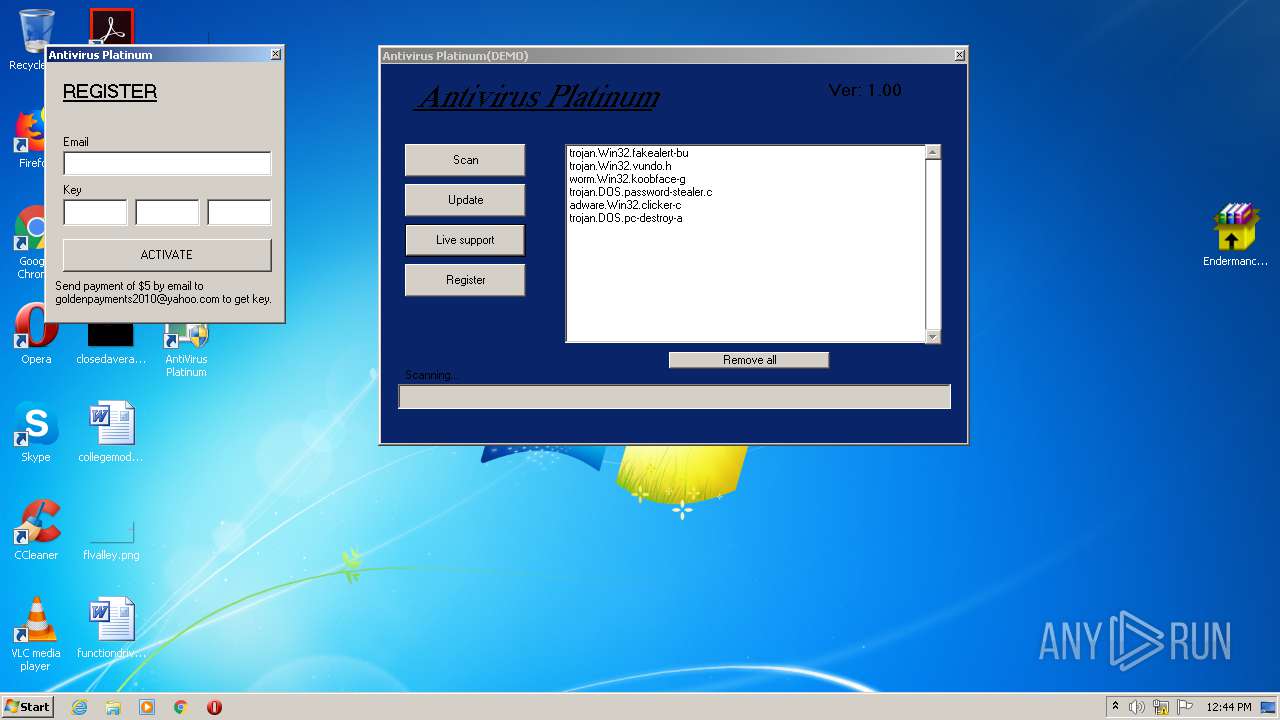
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2020, 11:42:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | FF84853A0F564152BD0B98D3FA63E695 |
| SHA1: | 47D628D279DE8A0D47534F93FA5B046BB7F4C991 |
| SHA256: | 3AAA9E8EA7C213575FD3AC4EC004629B4EDE0DE06E243F6AAD3CF2403E65D3F2 |
| SSDEEP: | 12288:pKAT6gPoHT7CzZy7fmzVyaF3zA0mKz8doC3m/LuXCC32H+REYWzTdjhoMlX1Q4QM:2gPoHT7CtEfwyaFDAjKz8Bm/LYC+3uYi |
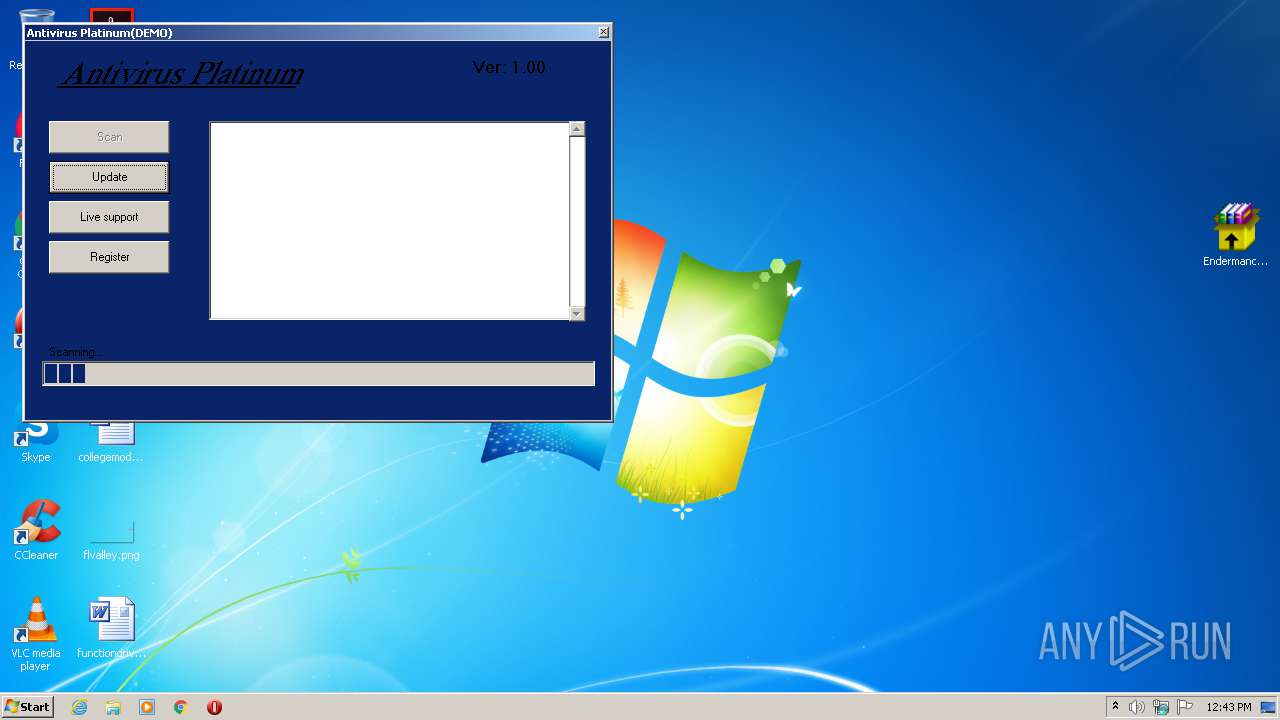
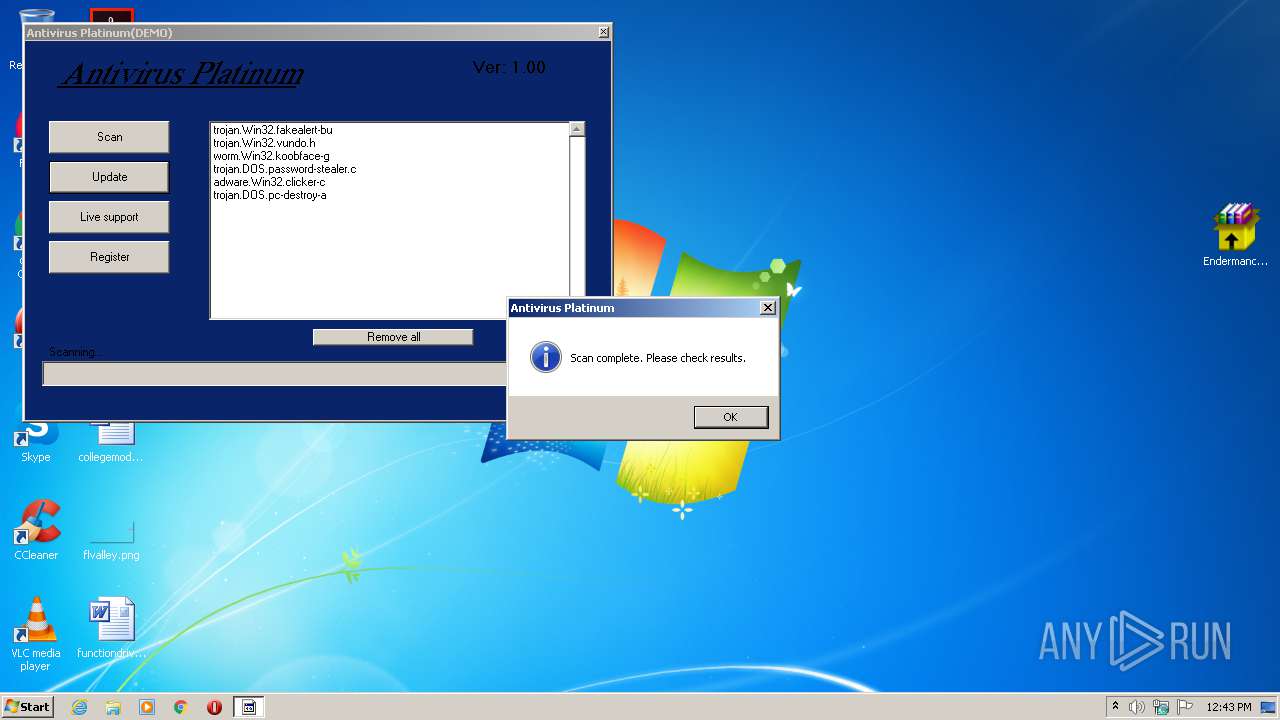
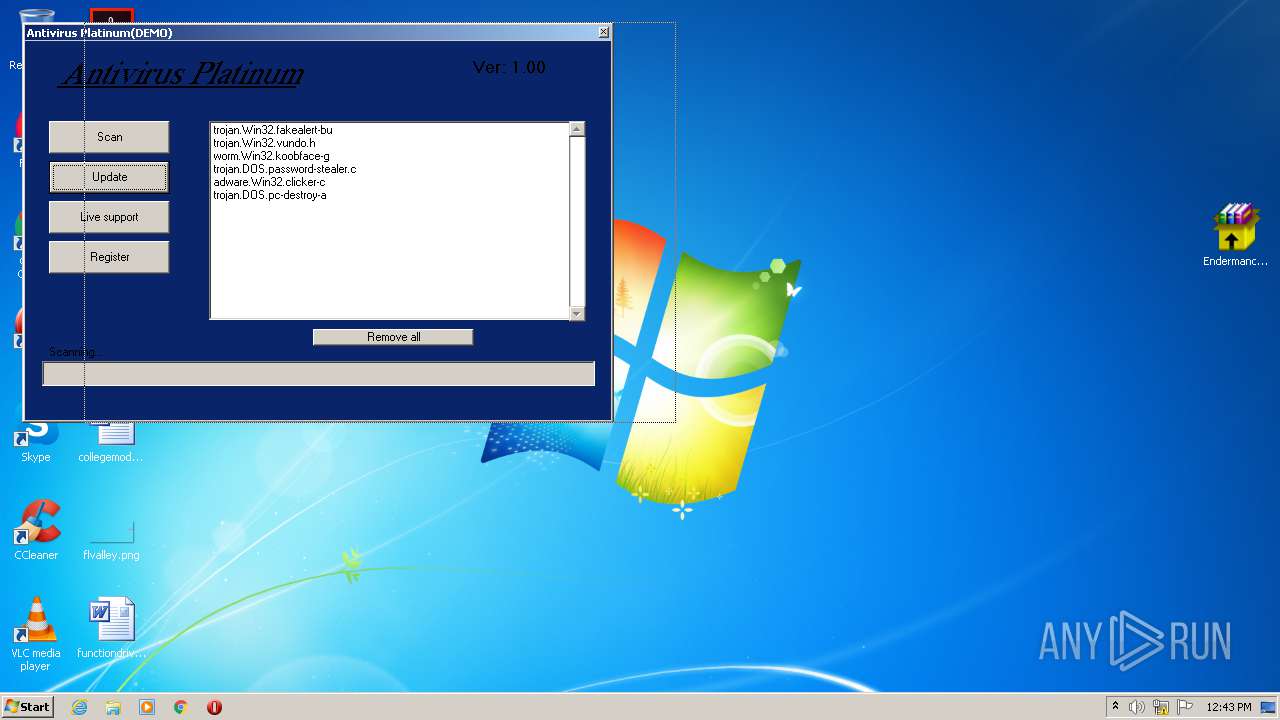
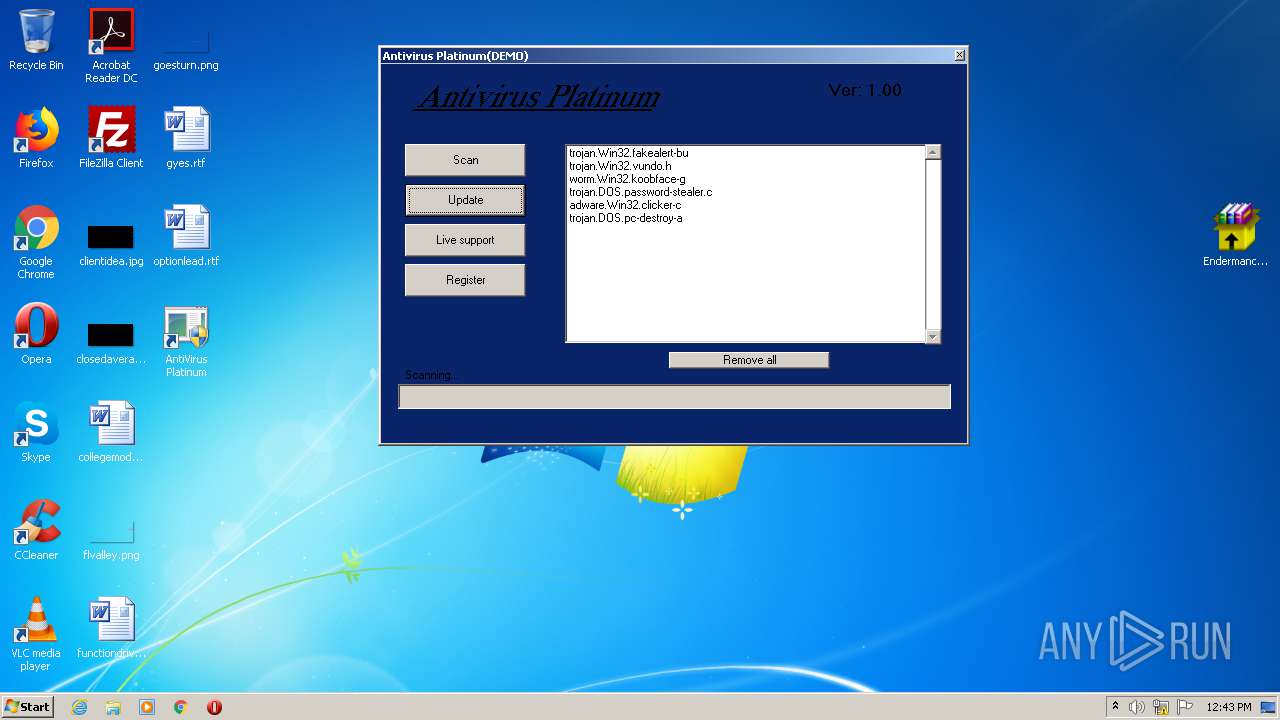
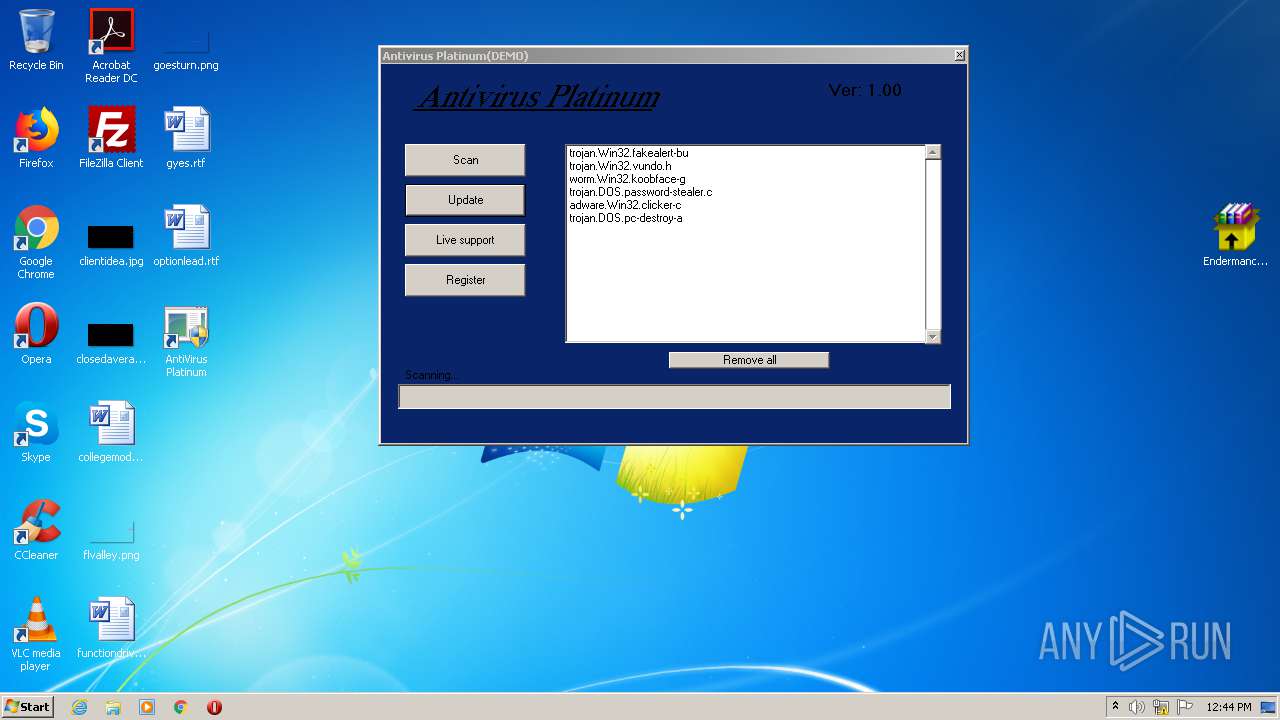
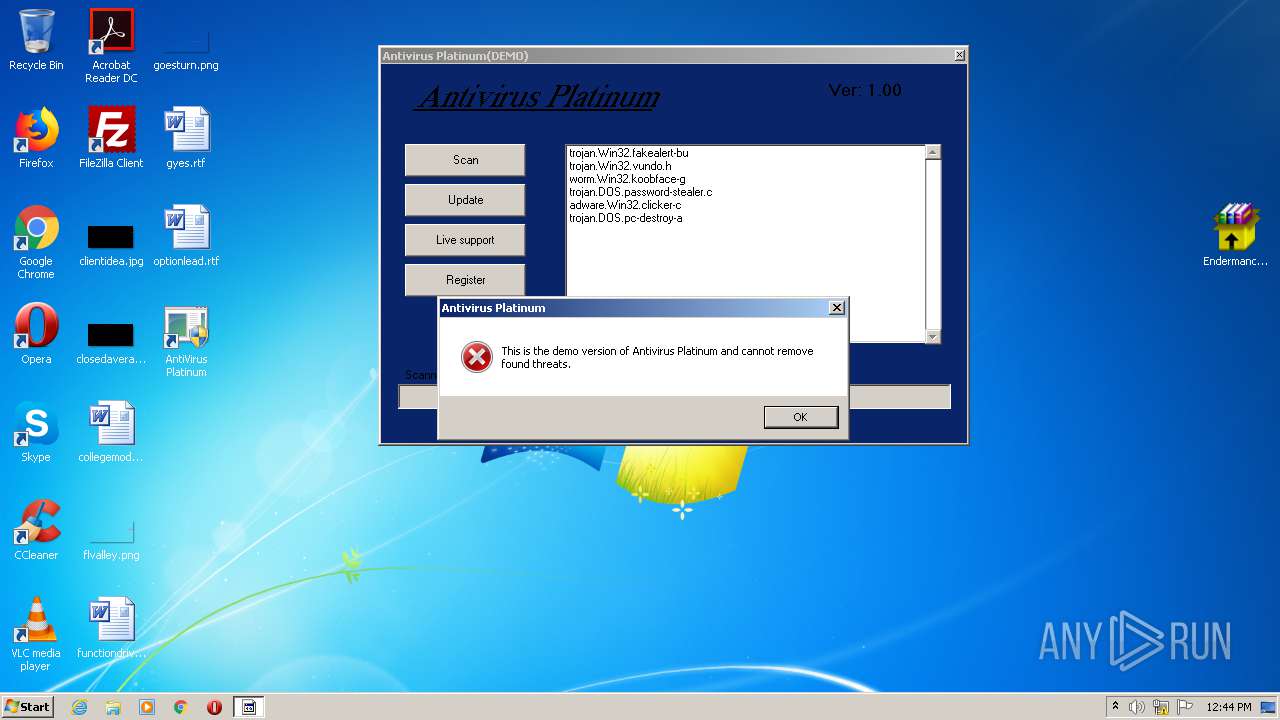
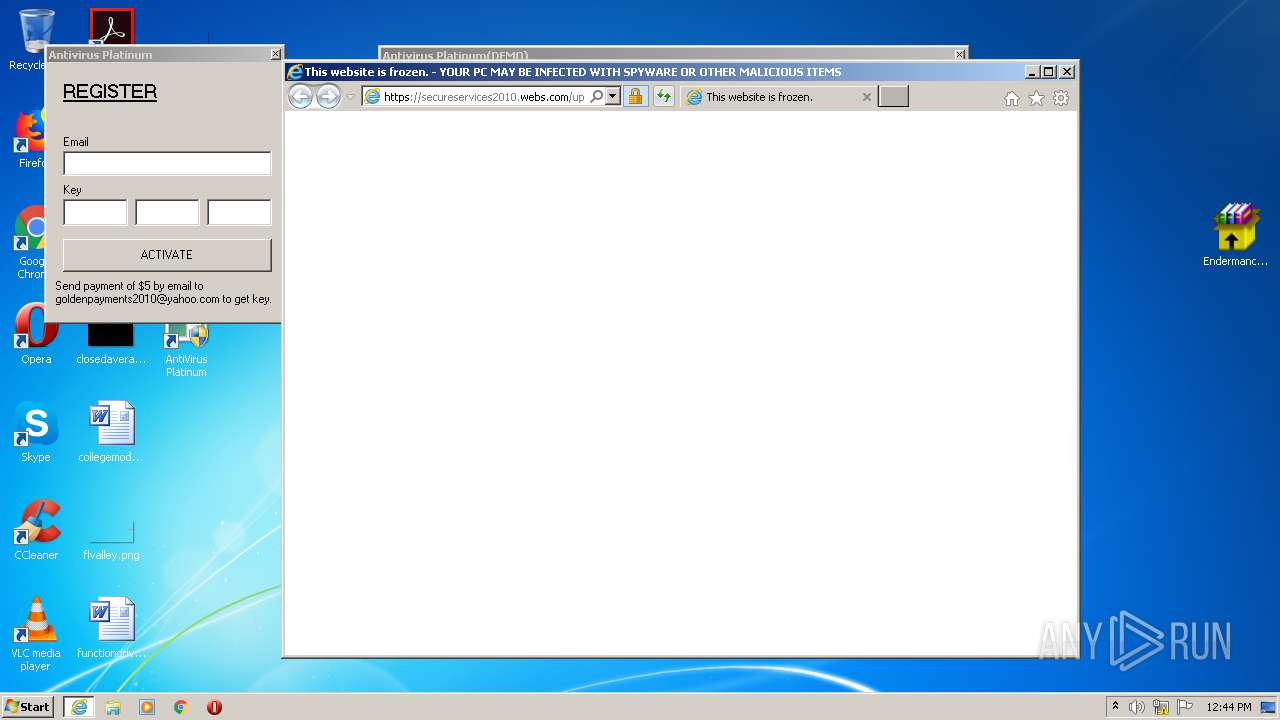
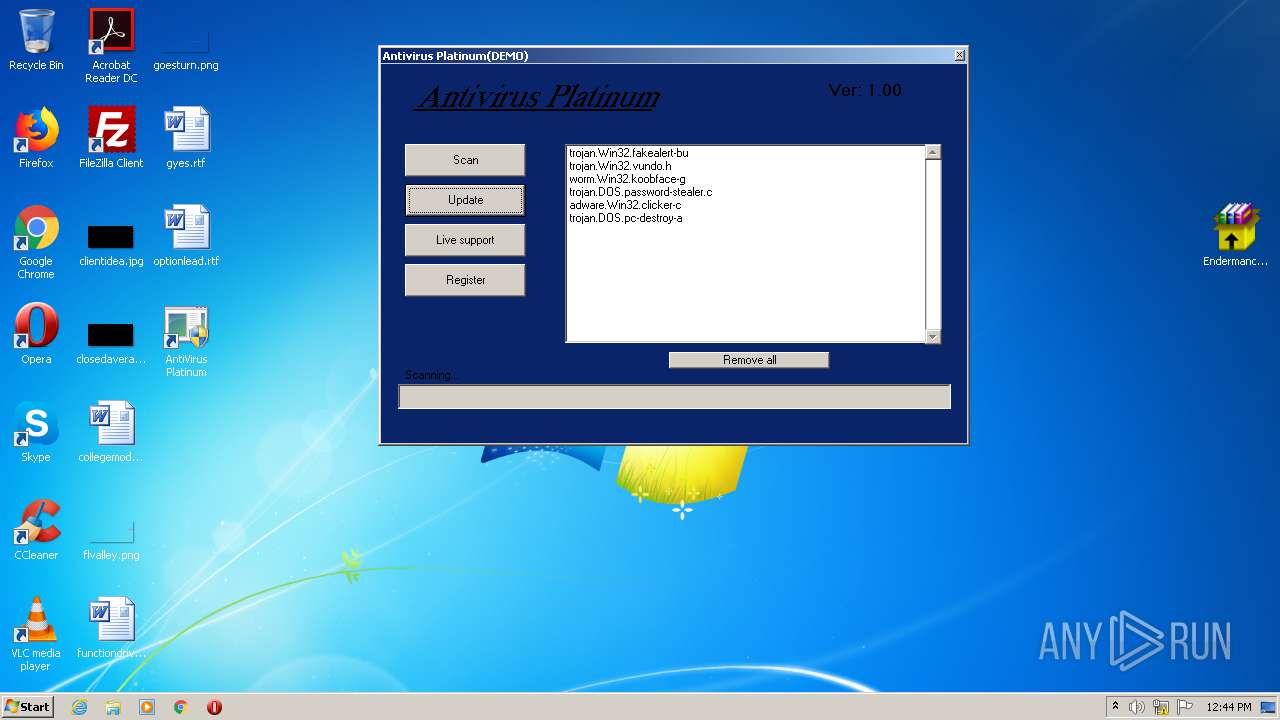
MALICIOUS
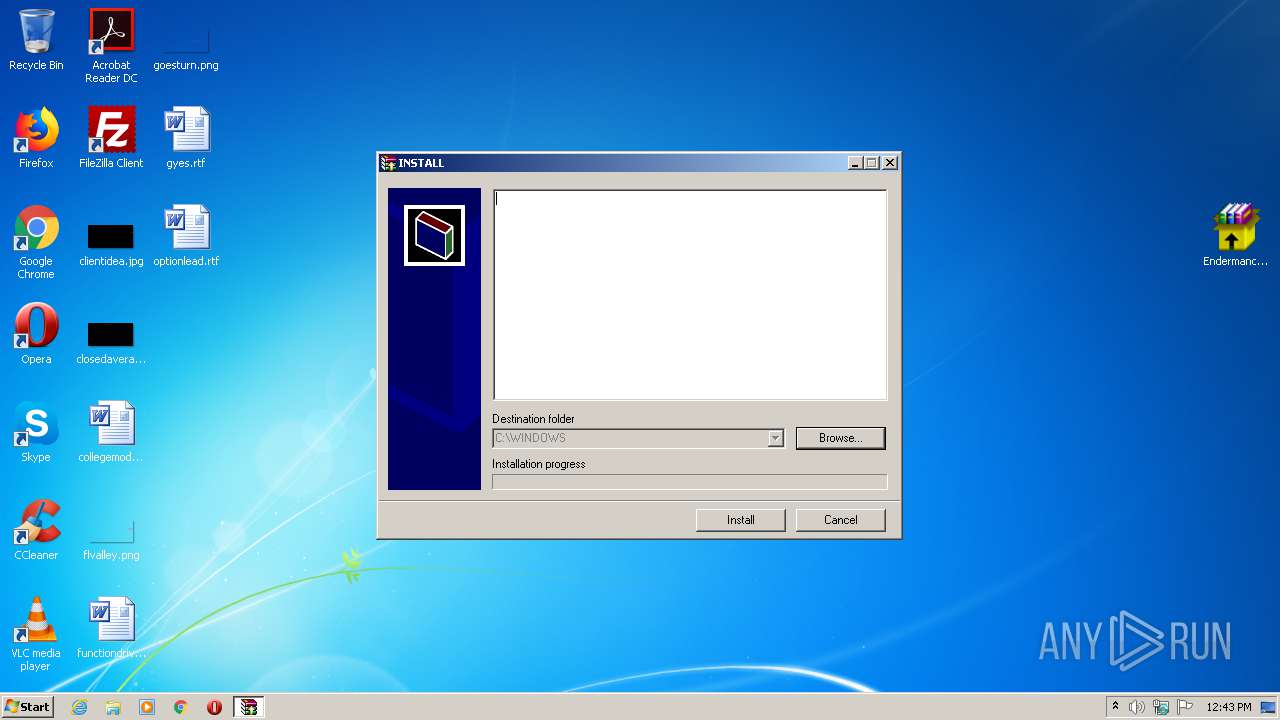
Application was dropped or rewritten from another process
- Endermanch@AntivirusPlatinum.exe (PID: 3360)
- Endermanch@AntivirusPlatinum.exe (PID: 2876)
- 302746537.exe (PID: 1748)
- antivirus-platinum.exe (PID: 956)
Registers / Runs the DLL via REGSVR32.EXE
- cmd.exe (PID: 680)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 2176)
- regsvr32.exe (PID: 3788)
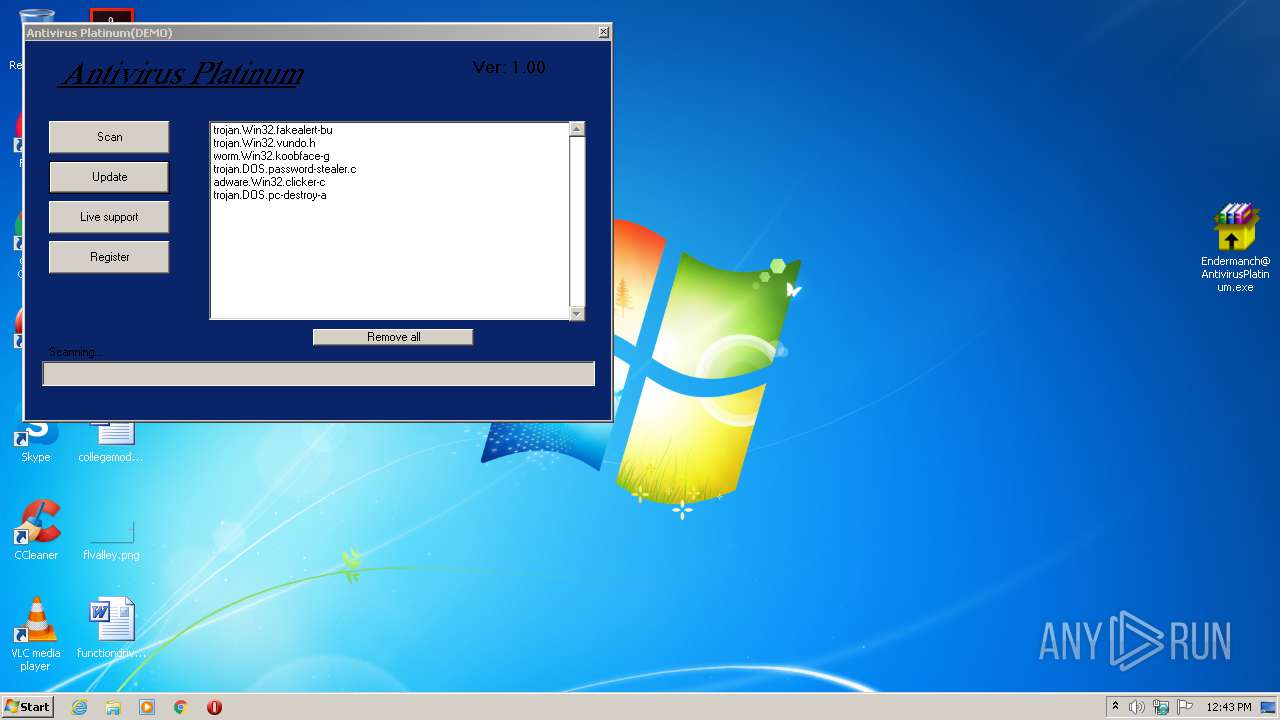
Task Manager has been disabled (taskmgr)
- antivirus-platinum.exe (PID: 956)
Changes Security Center notification settings
- antivirus-platinum.exe (PID: 956)
Disables the LogOff in Start menu
- antivirus-platinum.exe (PID: 956)
Disables registry editing tools (regedit)
- antivirus-platinum.exe (PID: 956)
Disables Windows System Restore
- antivirus-platinum.exe (PID: 956)
Disables the Shutdown in Start menu
- antivirus-platinum.exe (PID: 956)
SUSPICIOUS
Application launched itself
- Endermanch@AntivirusPlatinum.exe (PID: 3360)
Creates files in the Windows directory
- Endermanch@AntivirusPlatinum.exe (PID: 2876)
Executable content was dropped or overwritten
- Endermanch@AntivirusPlatinum.exe (PID: 2876)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 680)
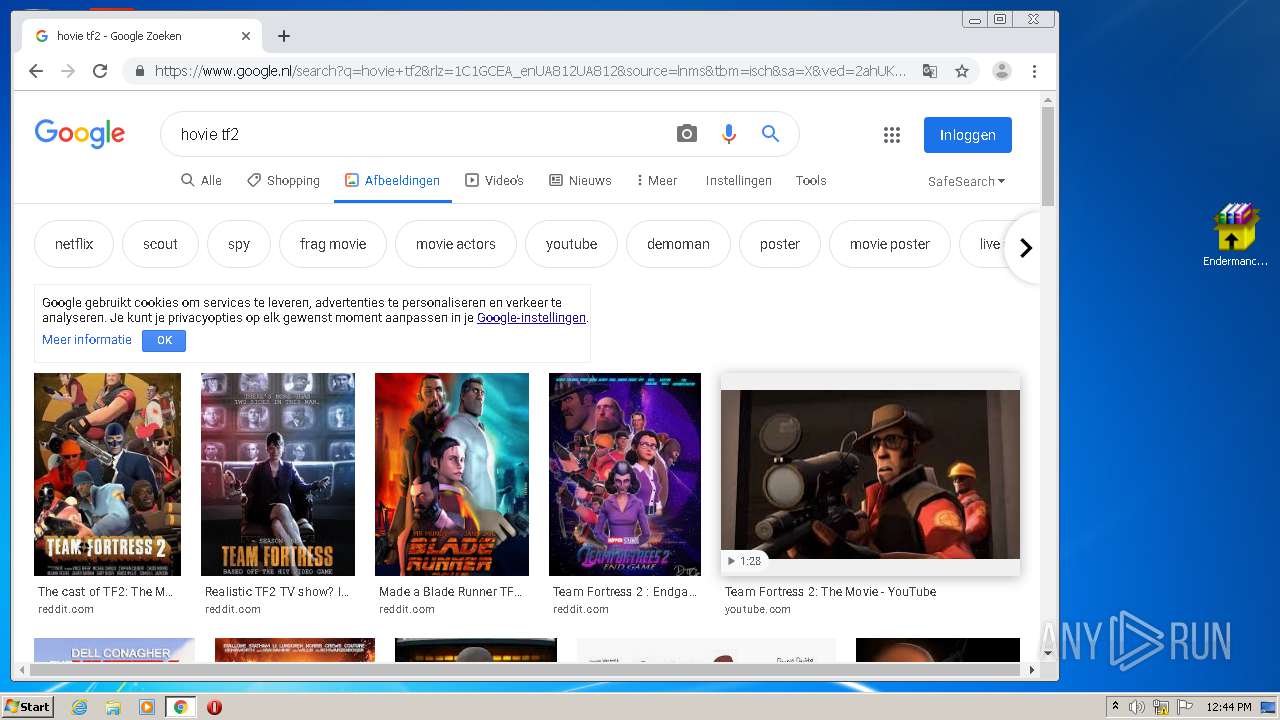
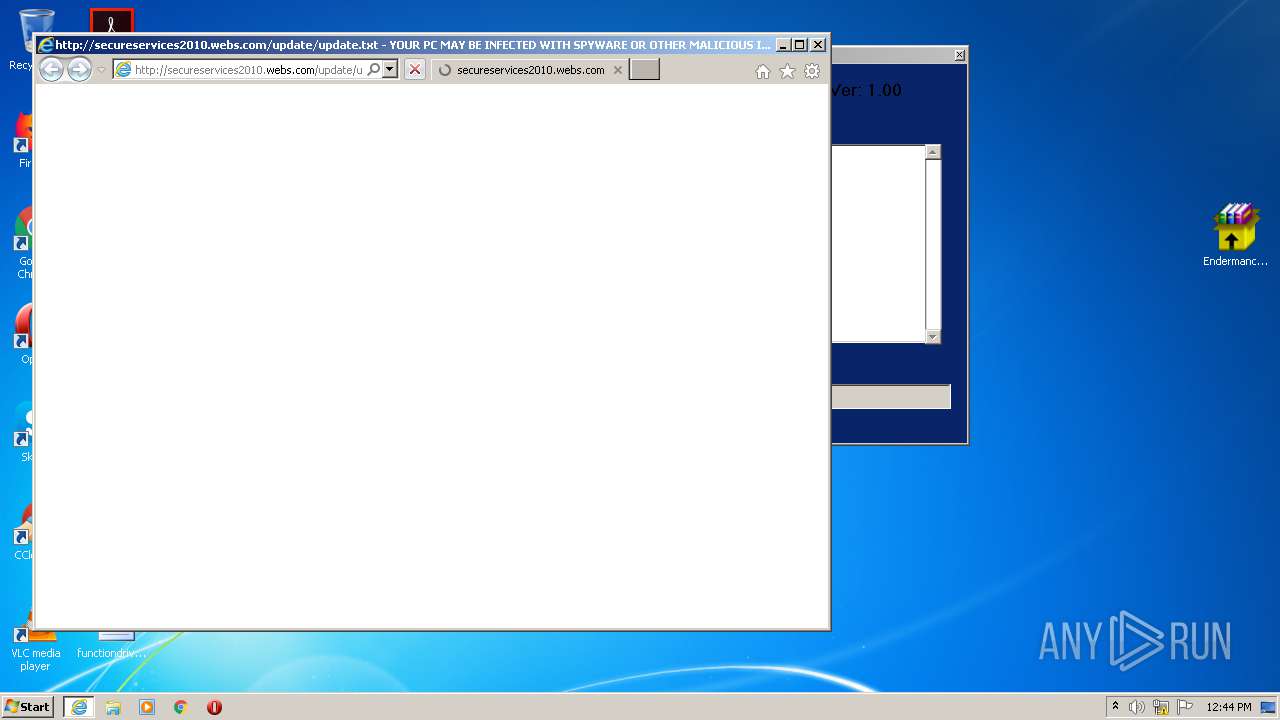
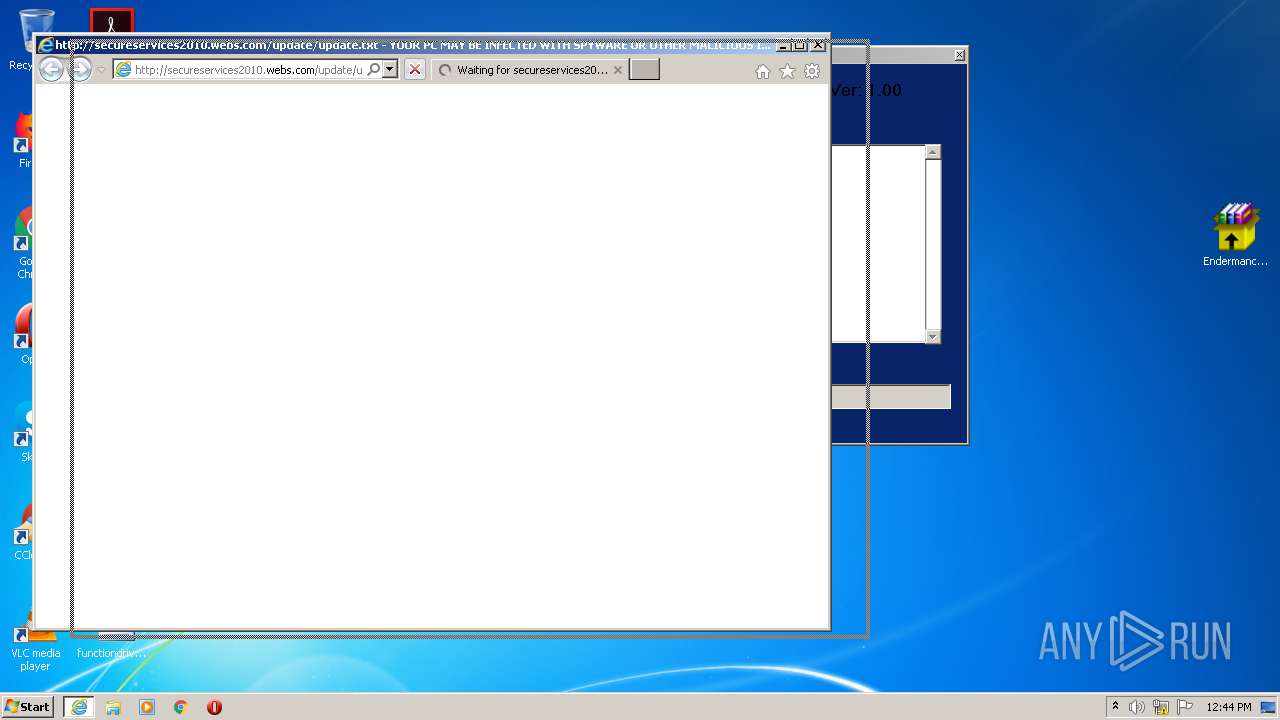
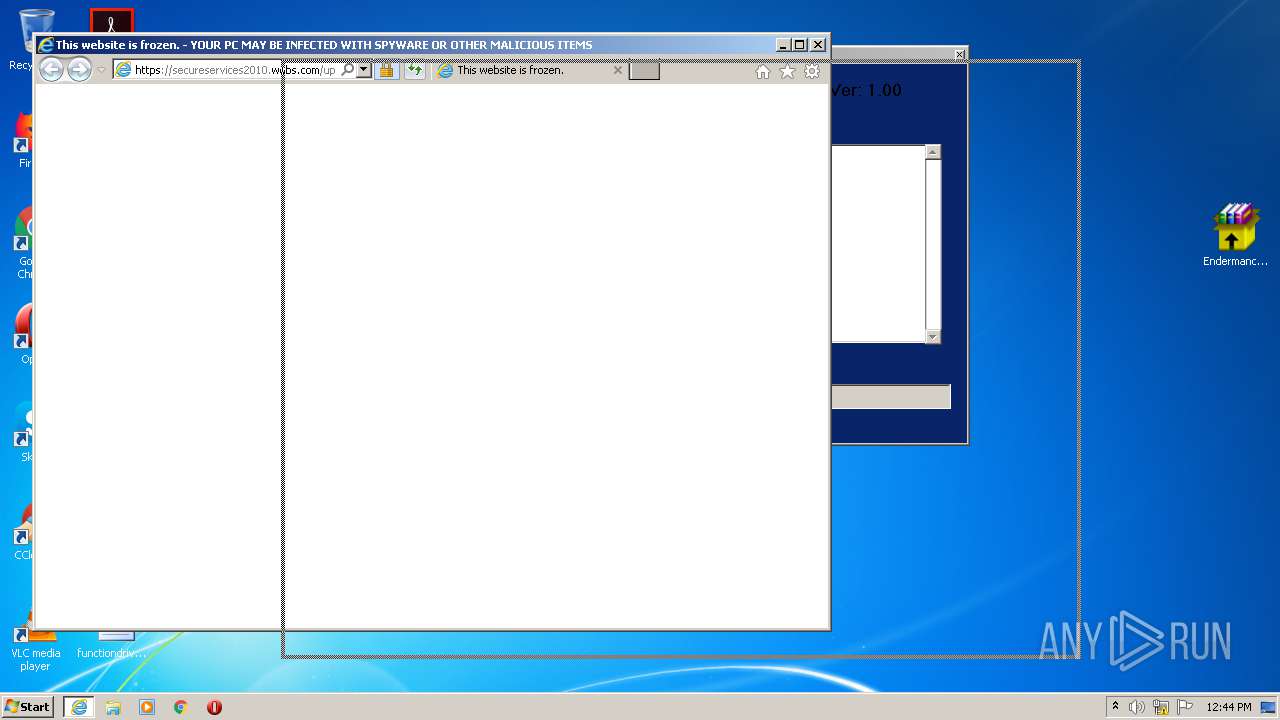
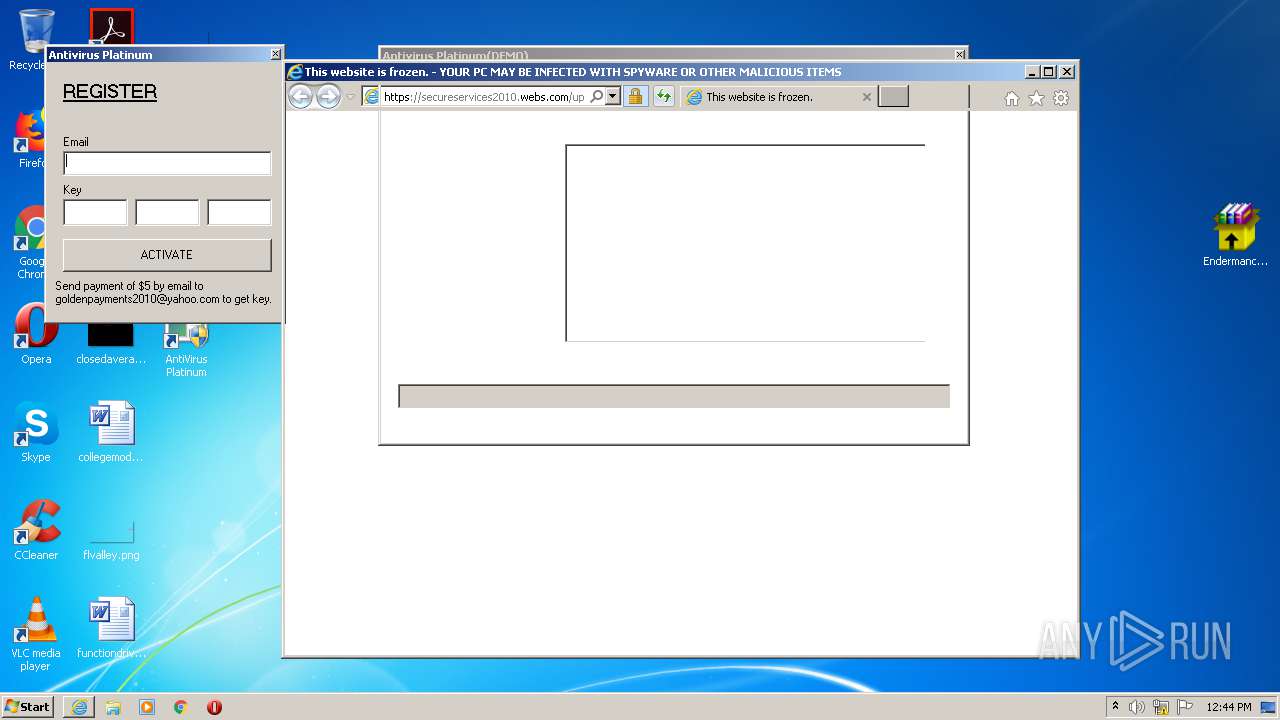
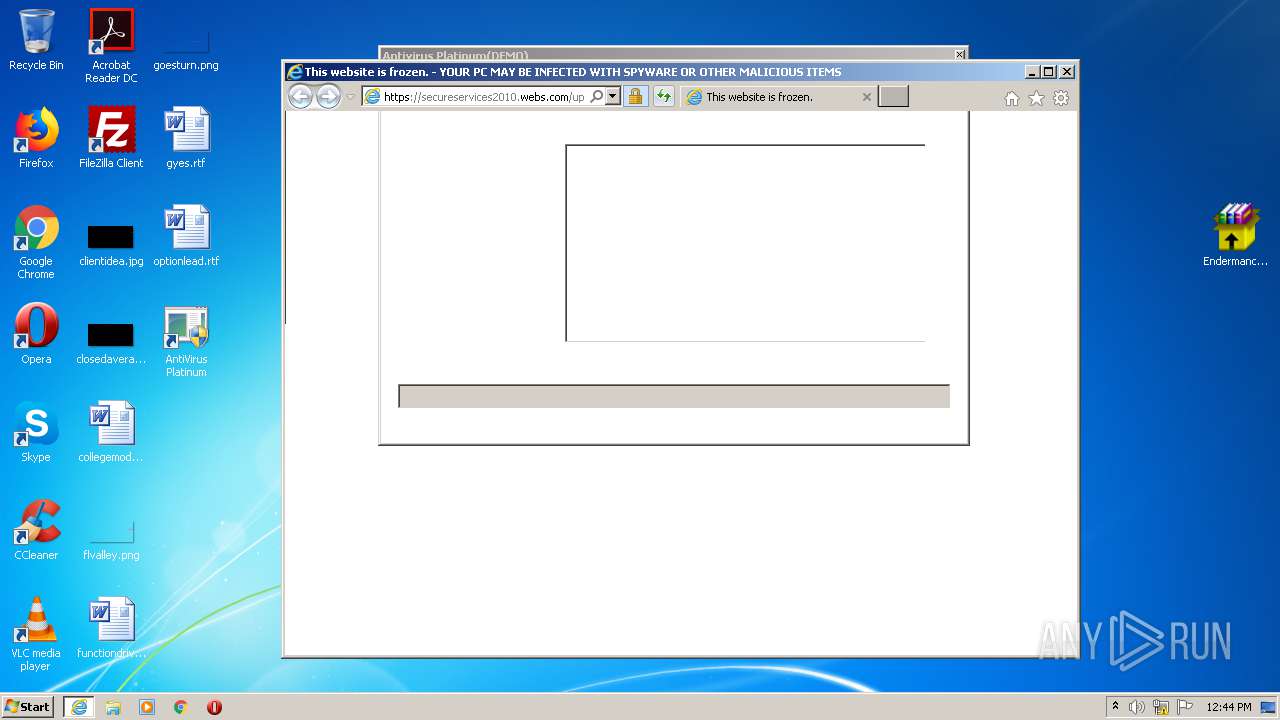
Changes the started page of IE
- antivirus-platinum.exe (PID: 956)
Starts CMD.EXE for commands execution
- 302746537.exe (PID: 1748)
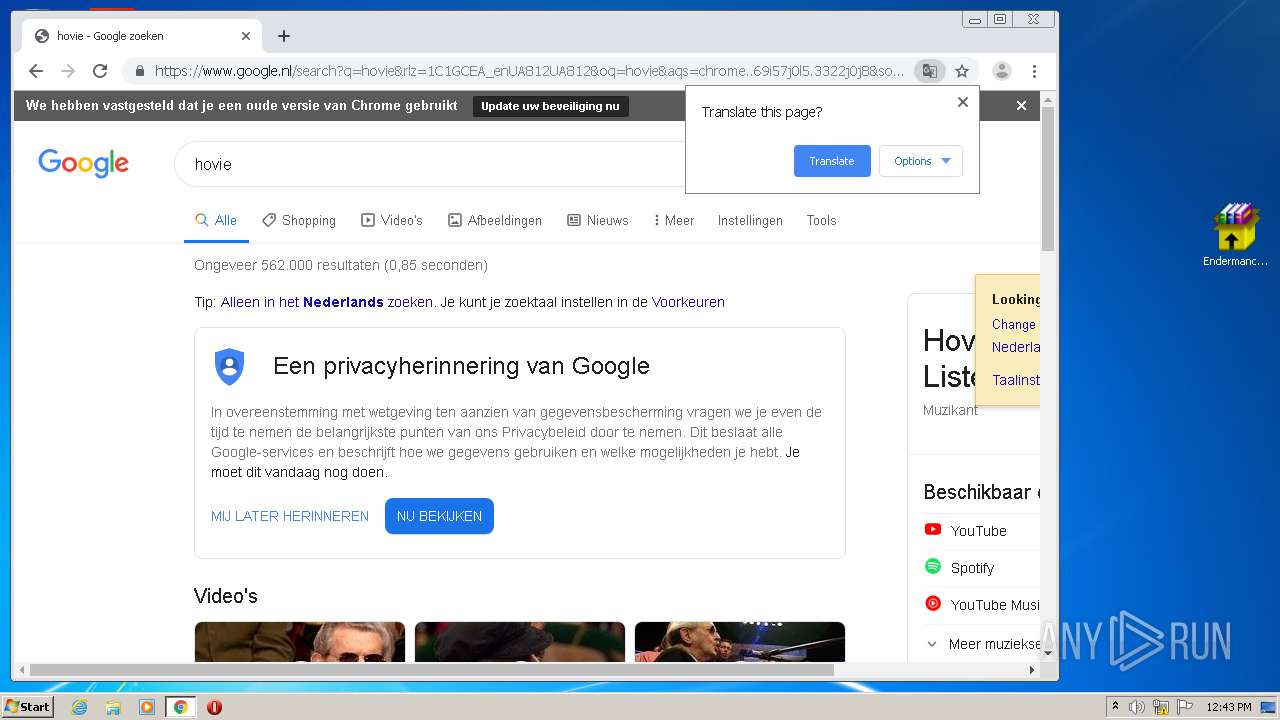
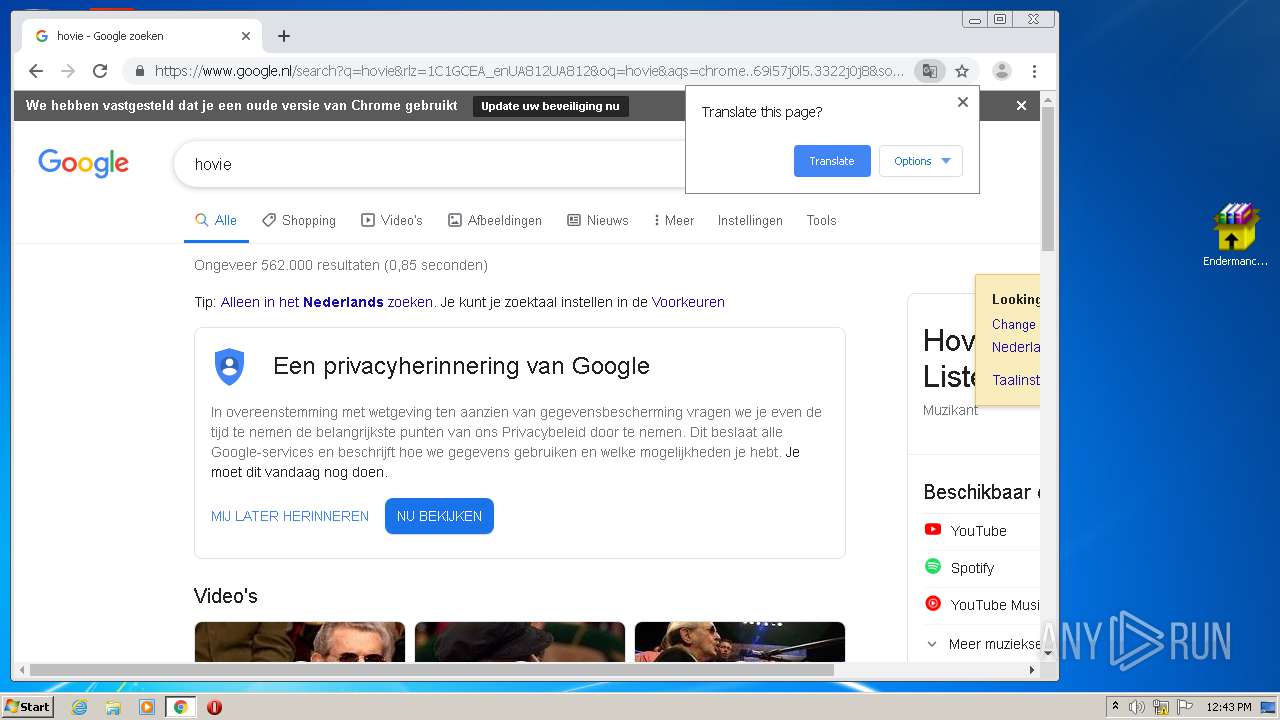
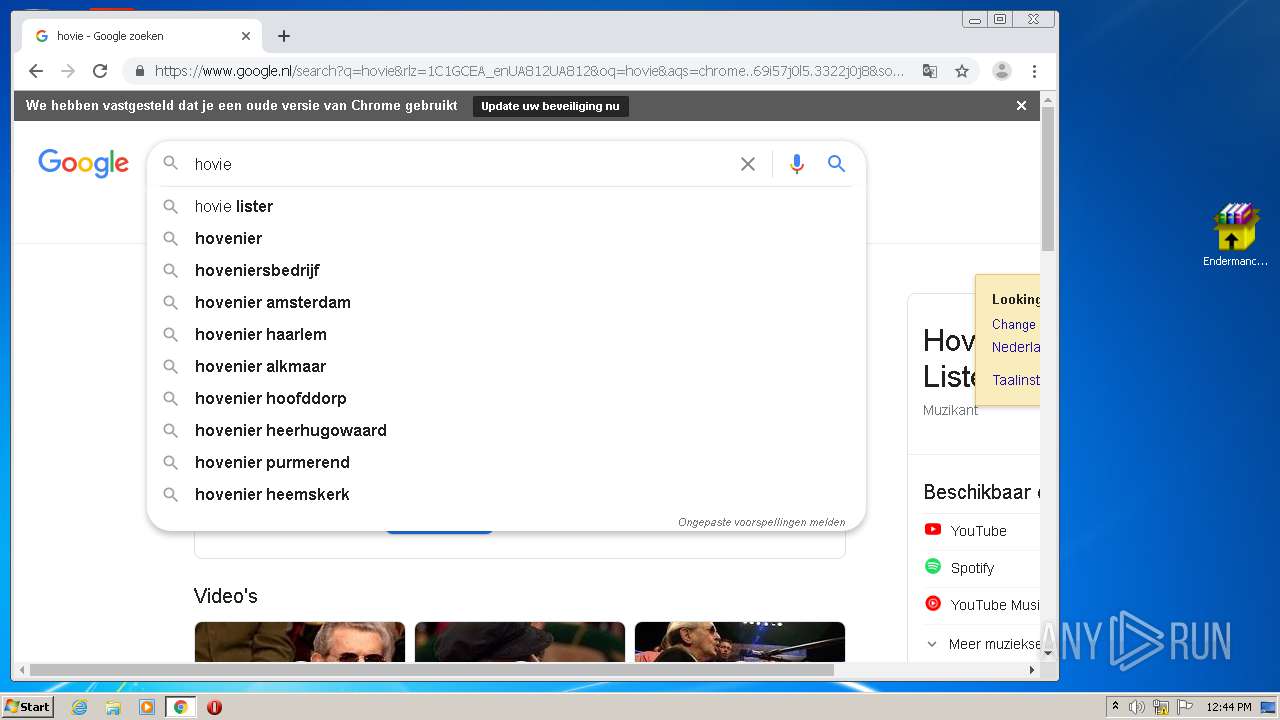
Modifies files in Chrome extension folder
- chrome.exe (PID: 1004)
Starts Internet Explorer
- antivirus-platinum.exe (PID: 956)
INFO
Manual execution by user
- Endermanch@AntivirusPlatinum.exe (PID: 3360)
- chrome.exe (PID: 1004)
Application launched itself
- chrome.exe (PID: 1004)
Reads the hosts file
- chrome.exe (PID: 1004)
- chrome.exe (PID: 2248)
Reads Internet Cache Settings
- iexplore.exe (PID: 3836)
- iexplore.exe (PID: 2876)
Changes internet zones settings
- iexplore.exe (PID: 3836)
Reads settings of System Certificates
- iexplore.exe (PID: 2876)
- chrome.exe (PID: 2248)
Reads internet explorer settings
- iexplore.exe (PID: 2876)
Creates files in the user directory
- iexplore.exe (PID: 2876)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2876)
Changes settings of System certificates
- iexplore.exe (PID: 2876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
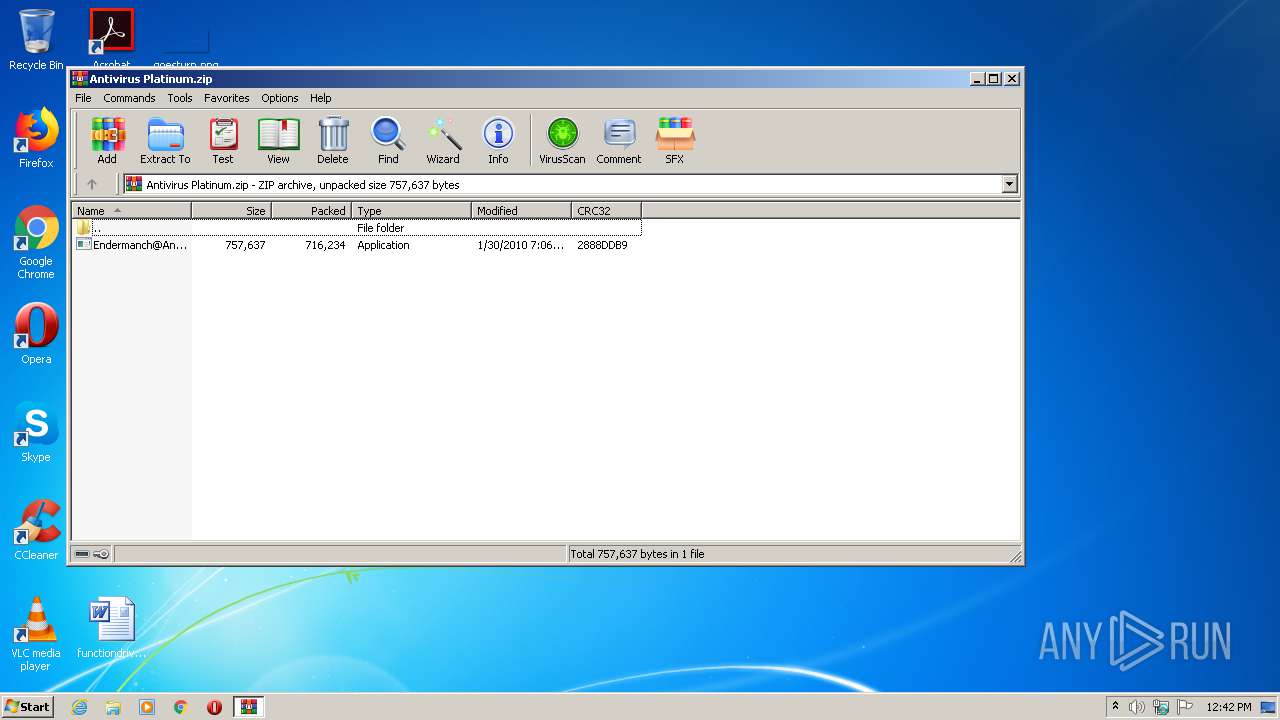
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2010:01:30 10:06:03 |
| ZipCRC: | 0x2888ddb9 |
| ZipCompressedSize: | 716234 |
| ZipUncompressedSize: | 757637 |
| ZipFileName: | Endermanch@AntivirusPlatinum.exe |
Total processes
81
Monitored processes
41
Malicious processes
5
Suspicious processes
0
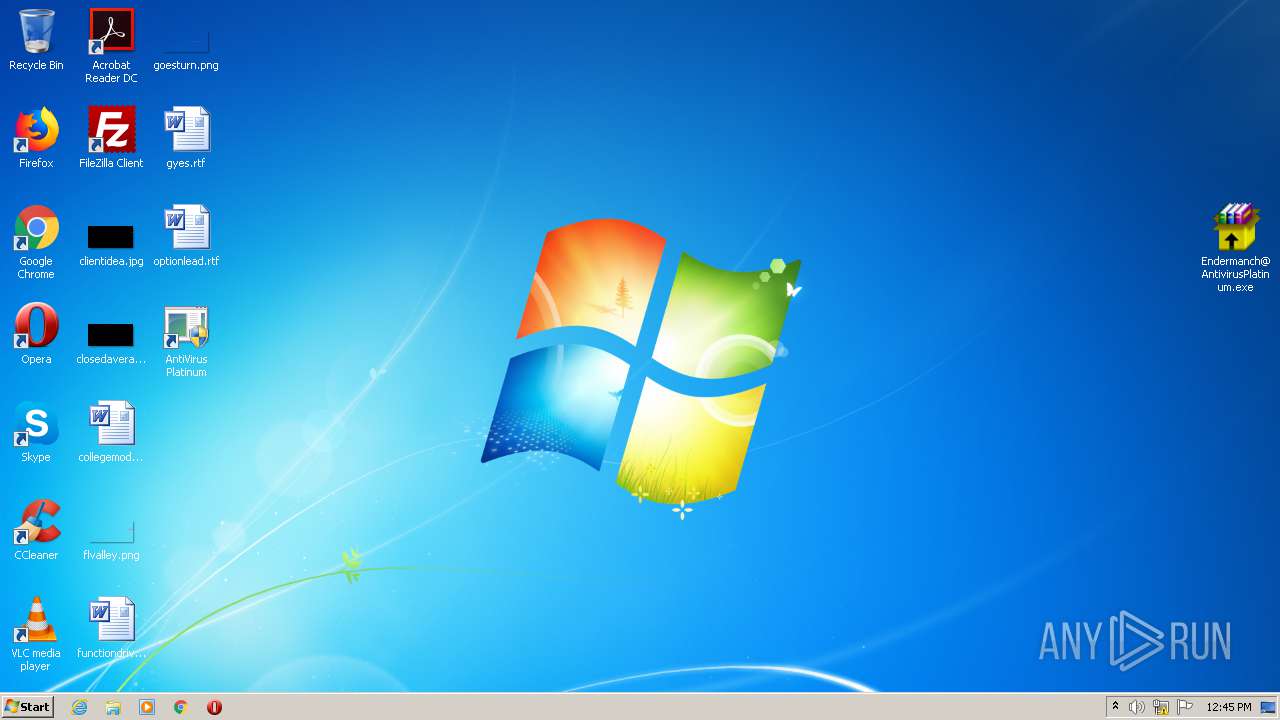
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,16262673138534000304,17583349842208699960,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11404682307309919414 --mojo-platform-channel-handle=4288 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,16262673138534000304,17583349842208699960,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2573471527709795650 --mojo-platform-channel-handle=4364 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,16262673138534000304,17583349842208699960,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8781690900467745997 --mojo-platform-channel-handle=4340 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,16262673138534000304,17583349842208699960,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6077166182729289435 --mojo-platform-channel-handle=3420 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 680 | cmd /c ""C:\Users\admin\AppData\Local\Temp\7EC.tmp\302746537.bat" " | C:\Windows\system32\cmd.exe | — | 302746537.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 956 | c:\windows\antivirus-platinum.exe | c:\windows\antivirus-platinum.exe | — | cmd.exe | |||||||||||
User: admin Company: BKHN Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,16262673138534000304,17583349842208699960,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2032198002434117859 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3648 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1748 | "C:\WINDOWS\302746537.exe" | C:\WINDOWS\302746537.exe | — | Endermanch@AntivirusPlatinum.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
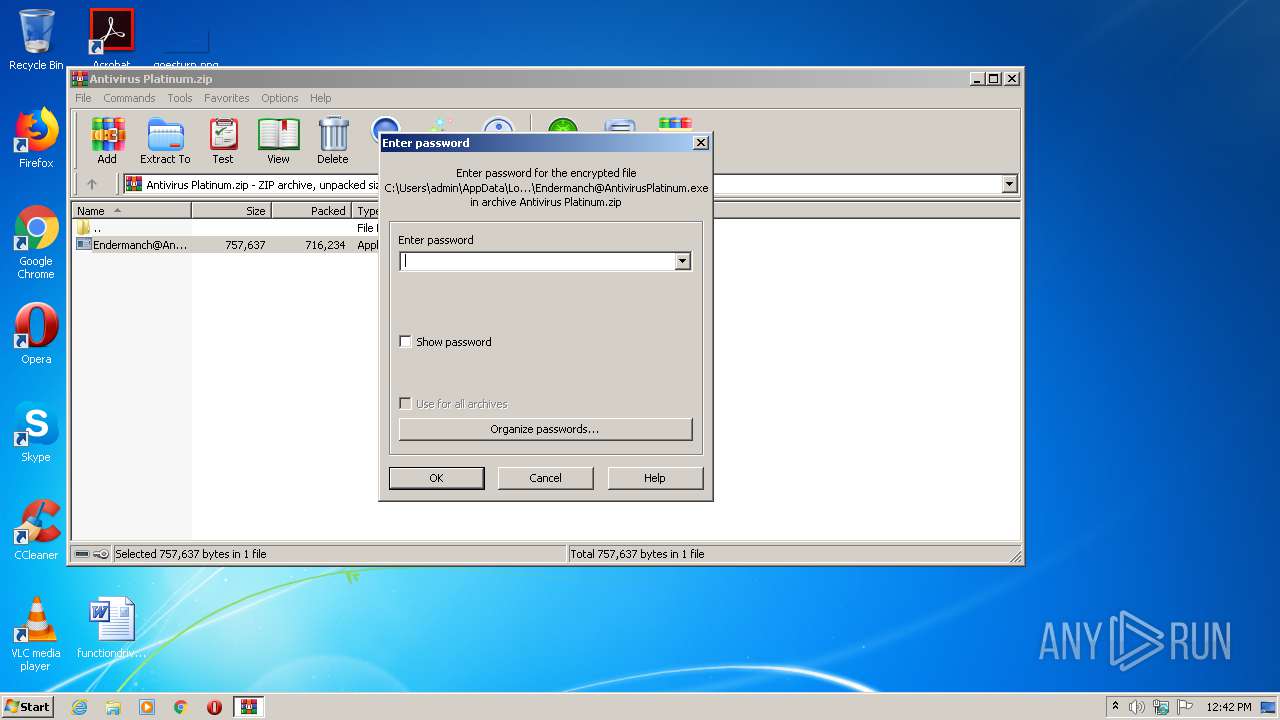
| 1852 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Antivirus Platinum.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
4 343
Read events
2 269
Write events
2 009
Delete events
65
Modification events
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Antivirus Platinum.zip | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
Executable files
4
Suspicious files
112
Text files
281
Unknown types
35
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1852 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1852.49919\Endermanch@AntivirusPlatinum.exe | — | |
MD5:— | SHA256:— | |||
| 1004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F0AF771-3EC.pma | — | |
MD5:— | SHA256:— | |||
| 1004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\95143aa7-1fd5-44b0-b020-188e03cd1be7.tmp | — | |
MD5:— | SHA256:— | |||
| 2876 | Endermanch@AntivirusPlatinum.exe | C:\Users\admin\Desktop\AntiVirus Platinum.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF116ed4.TMP | text | |
MD5:— | SHA256:— | |||
| 1004 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF116ed4.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
60
DNS requests
41
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
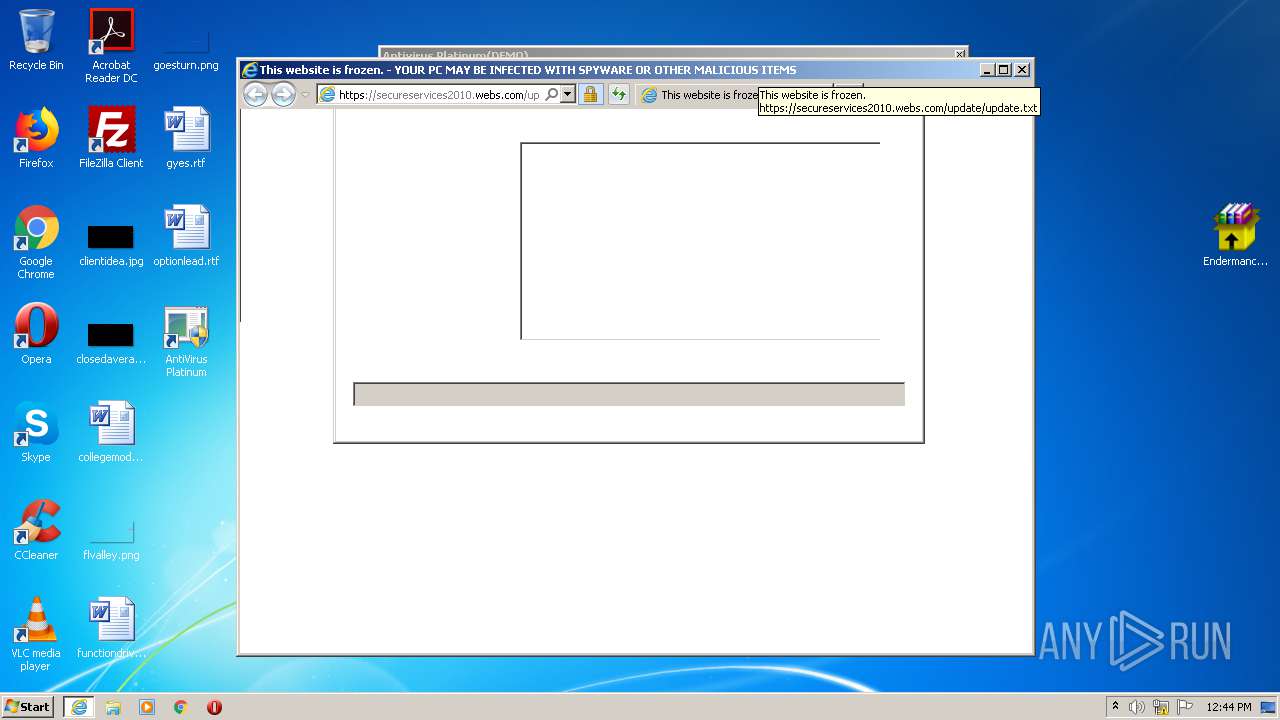
2876 | iexplore.exe | GET | 301 | 104.17.119.40:80 | http://secureservices2010.webs.com/update/update.txt | US | — | — | malicious |
2248 | chrome.exe | GET | 302 | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 523 b | whitelisted |
2876 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrBBNpPfHTPX6Jy6BVzyBPnBWMnQQUPnQtH89FdQR%2BP8Cihz5MQ4NRE8YCEAXoVMFsORfvvHup8VBgwtU%3D | US | der | 278 b | whitelisted |
2876 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
2876 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 471 b | whitelisted |
2876 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2248 | chrome.exe | GET | 200 | 172.217.132.8:80 | http://r3---sn-5hne6nsd.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=45.86.201.12&mm=28&mn=sn-5hne6nsd&ms=nvh&mt=1594553536&mv=u&mvi=3&pl=27&shardbypass=yes | US | crx | 823 Kb | whitelisted |
2876 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2876 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrBBNpPfHTPX6Jy6BVzyBPnBWMnQQUPnQtH89FdQR%2BP8Cihz5MQ4NRE8YCEA4Gpe7b9YPekM6FHtCr%2BMk%3D | US | der | 278 b | whitelisted |
2876 | iexplore.exe | GET | 200 | 172.217.18.163:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2248 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2248 | chrome.exe | 172.217.18.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2248 | chrome.exe | 172.217.22.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2248 | chrome.exe | 216.58.212.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2248 | chrome.exe | 216.58.207.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2248 | chrome.exe | 172.217.23.142:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
2248 | chrome.exe | 172.217.23.110:443 | apis.google.com | Google Inc. | US | whitelisted |
2248 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
2248 | chrome.exe | 172.217.21.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2248 | chrome.exe | 172.217.22.3:443 | www.google.nl | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
www.google.nl |
| whitelisted |