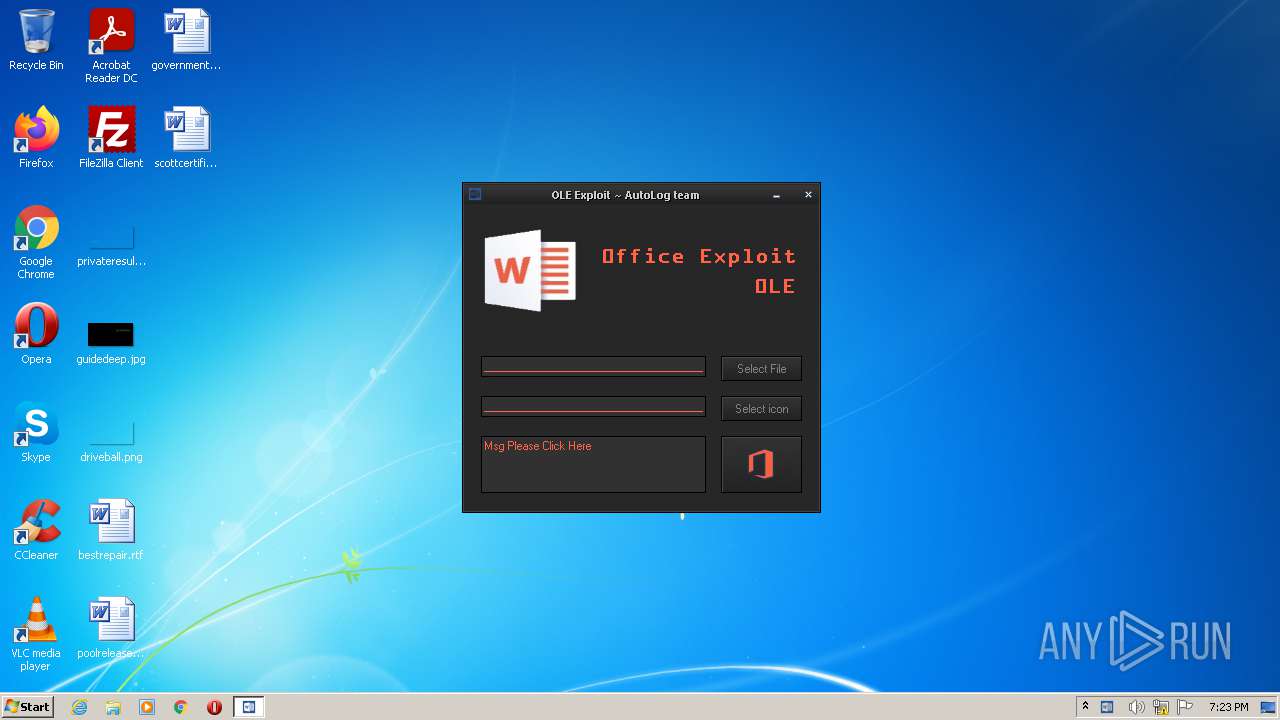
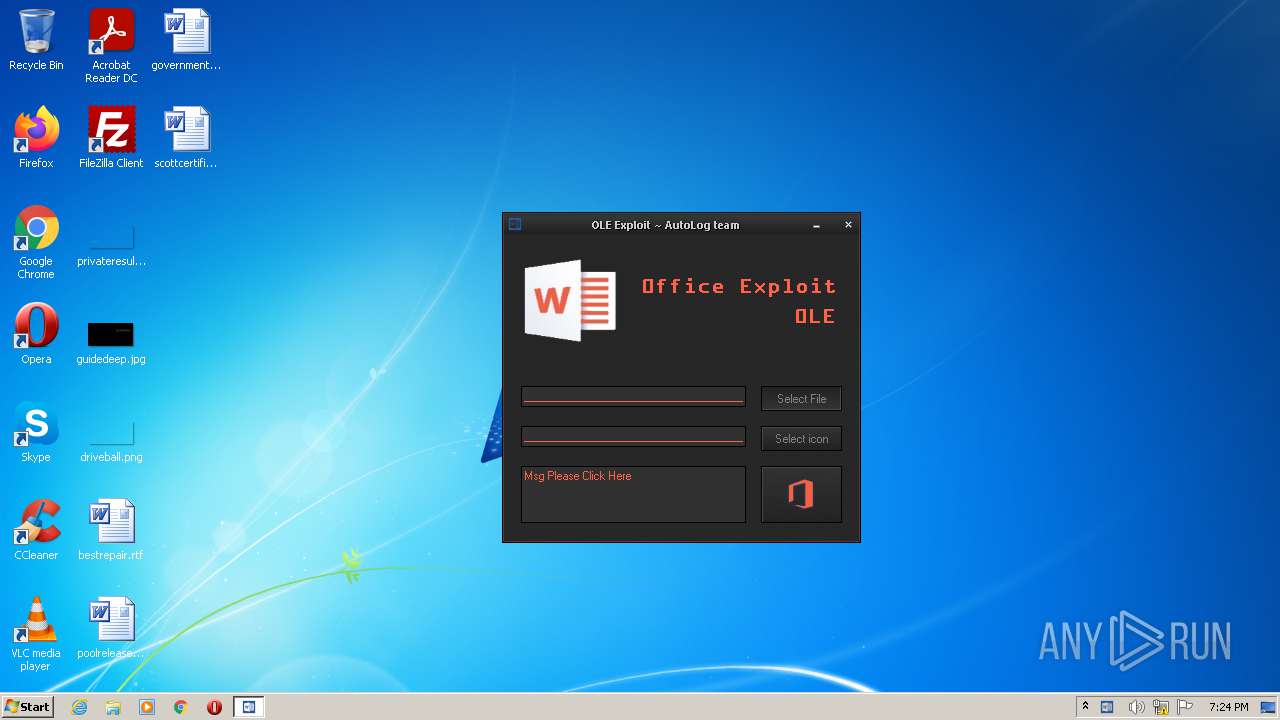
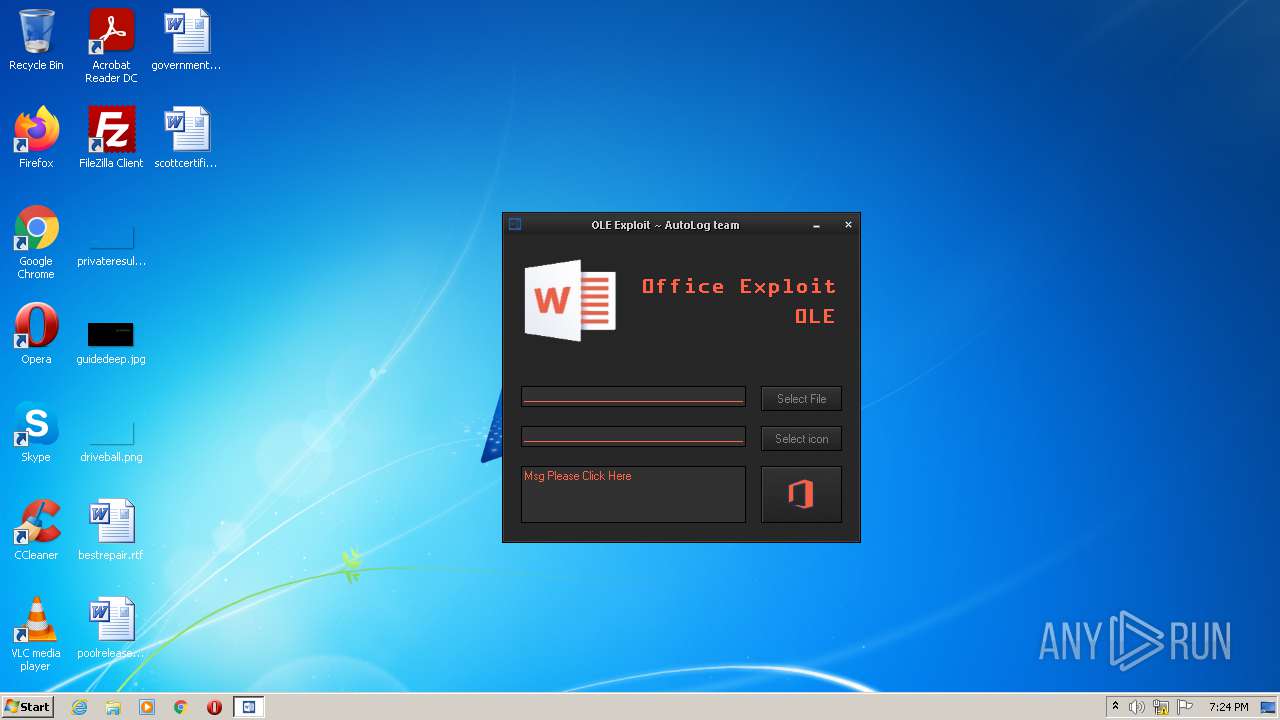
| File name: | DOC Exploit.exe |
| Full analysis: | https://app.any.run/tasks/7de5faf7-ea7e-46f1-af81-39438ba2d4af |
| Verdict: | Malicious activity |
| Analysis date: | October 30, 2021, 18:23:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BC8ACFC2141FB98925F55201959881F2 |
| SHA1: | CC4D8F3476ECCD2E89790FC9B1964C587621AEAF |
| SHA256: | 3AA395F65A4C7D67D4821D478328808409FA8BF0DB5448787663C296FC85652E |
| SSDEEP: | 24576:xCdxte/80jYLT3U1jfsWaGWBuMUCQmP/i+EH3/QhpfkJzQ:ww80cTsjkWaG8uMUClP/XEH3Yh5b |
MALICIOUS
Drops executable file immediately after starts
- DOC Exploit.exe (PID: 3580)
Loads dropped or rewritten executable
- DOC Exploit.exe (PID: 3580)
SUSPICIOUS
Checks supported languages
- DOC Exploit.exe (PID: 3580)
Reads mouse settings
- DOC Exploit.exe (PID: 3580)
Executable content was dropped or overwritten
- DOC Exploit.exe (PID: 3580)
Drops a file with too old compile date
- DOC Exploit.exe (PID: 3580)
Reads the computer name
- DOC Exploit.exe (PID: 3580)
Reads default file associations for system extensions
- DOC Exploit.exe (PID: 3580)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:11:24 21:23:04+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 581120 |
| InitializedDataSize: | 1058816 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x27f4a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Nov-2017 20:23:04 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 24-Nov-2017 20:23:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008DD2E | 0x0008DE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67588 |
.rdata | 0x0008F000 | 0x0002E10E | 0x0002E200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.76073 |
.data | 0x000BE000 | 0x00008F74 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.19881 |
.rsrc | 0x000C7000 | 0x000C8043 | 0x000C8200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.13719 |
.reloc | 0x00190000 | 0x00007130 | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.78238 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.40026 | 1007 | Latin 1 / Western European | English - United Kingdom | RT_MANIFEST |
2 | 2.05883 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 2.25499 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 1.99197 | 270376 | UNKNOWN | English - United Kingdom | RT_ICON |
5 | 4.1668 | 1128 | UNKNOWN | English - United Kingdom | RT_ICON |
6 | 2.814 | 9640 | UNKNOWN | English - United Kingdom | RT_ICON |
7 | 3.34702 | 1428 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 3.2817 | 1674 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 3.28849 | 1168 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 3.28373 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
35
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3580 | "C:\Users\admin\AppData\Local\Temp\DOC Exploit.exe" | C:\Users\admin\AppData\Local\Temp\DOC Exploit.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
5 443
Read events
5 315
Write events
127
Delete events
1
Modification events
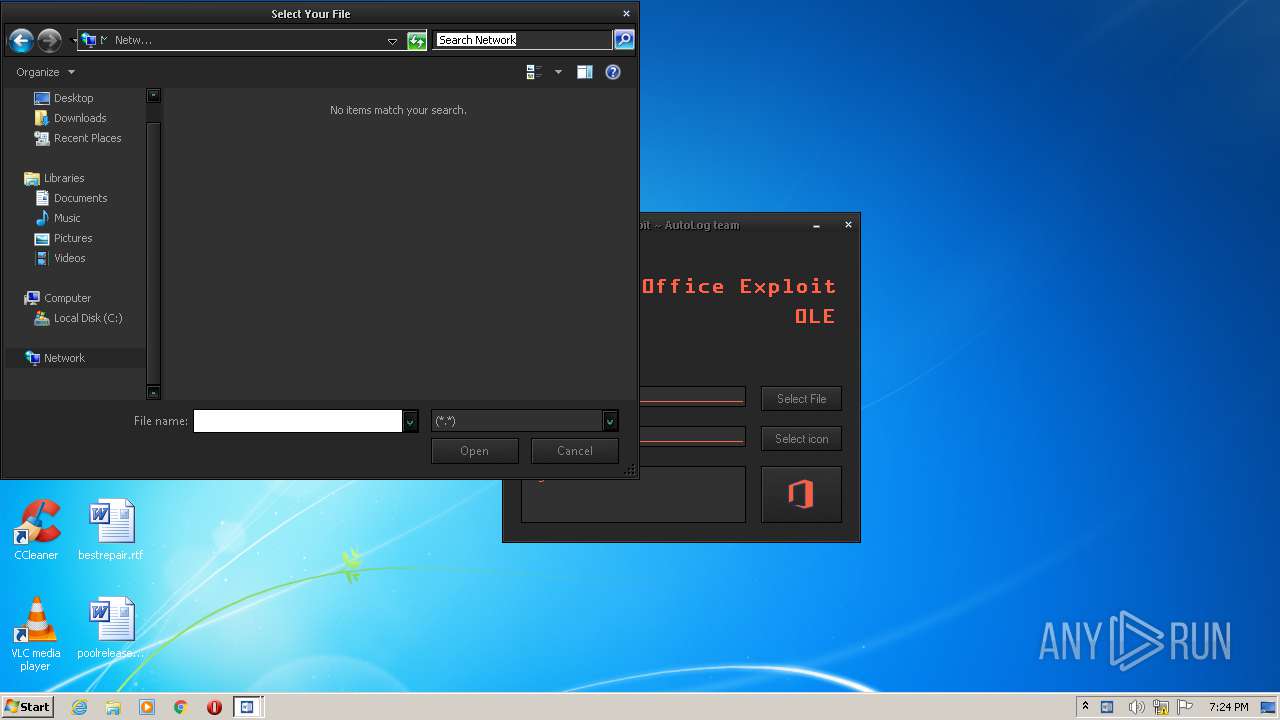
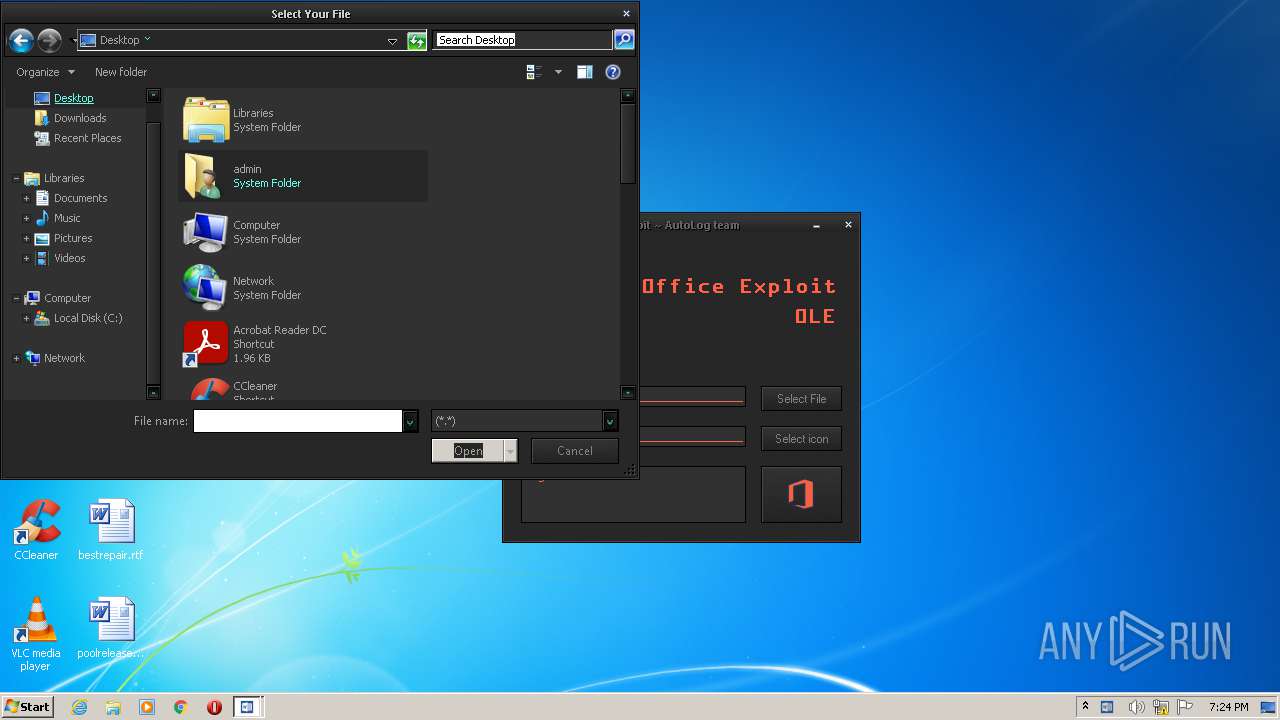
| (PID) Process: | (3580) DOC Exploit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | 0 |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0044004F00430020004500780070006C006F00690074002E00650078006500000043003A005C00550073006500720073005C00610064006D0069006E005C004400650073006B0074006F0070000000 | |||
| (PID) Process: | (3580) DOC Exploit.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\FirstFolder |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (3580) DOC Exploit.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3580) DOC Exploit.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0D00000001000000020000000C000000000000000B00000007000000060000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3580) DOC Exploit.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3580) DOC Exploit.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\82\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | Mode |
Value: 6 | |||
| (PID) Process: | (3580) DOC Exploit.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\82\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | LogicalViewMode |
Value: 2 | |||
| (PID) Process: | (3580) DOC Exploit.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\82\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | FFlags |
Value: | |||
| (PID) Process: | (3580) DOC Exploit.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\82\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | IconSize |
Value: 48 | |||
| (PID) Process: | (3580) DOC Exploit.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\82\ComDlg\{5C4F28B5-F869-4E84-8E60-F11DB97C5CC7} |
| Operation: | write | Name: | ColInfo |
Value: 00000000000000000000000000000000FDDFDFFD100000000000000000000000040000001800000030F125B7EF471A10A5F102608C9EEBAC0A000000A000000030F125B7EF471A10A5F102608C9EEBAC0C00000050000000A66A63283D95D211B5D600C04FD918D00B0000007800000030F125B7EF471A10A5F102608C9EEBAC0E00000078000000 | |||
Executable files
3
Suspicious files
3
Text files
4
Unknown types
2
Dropped files
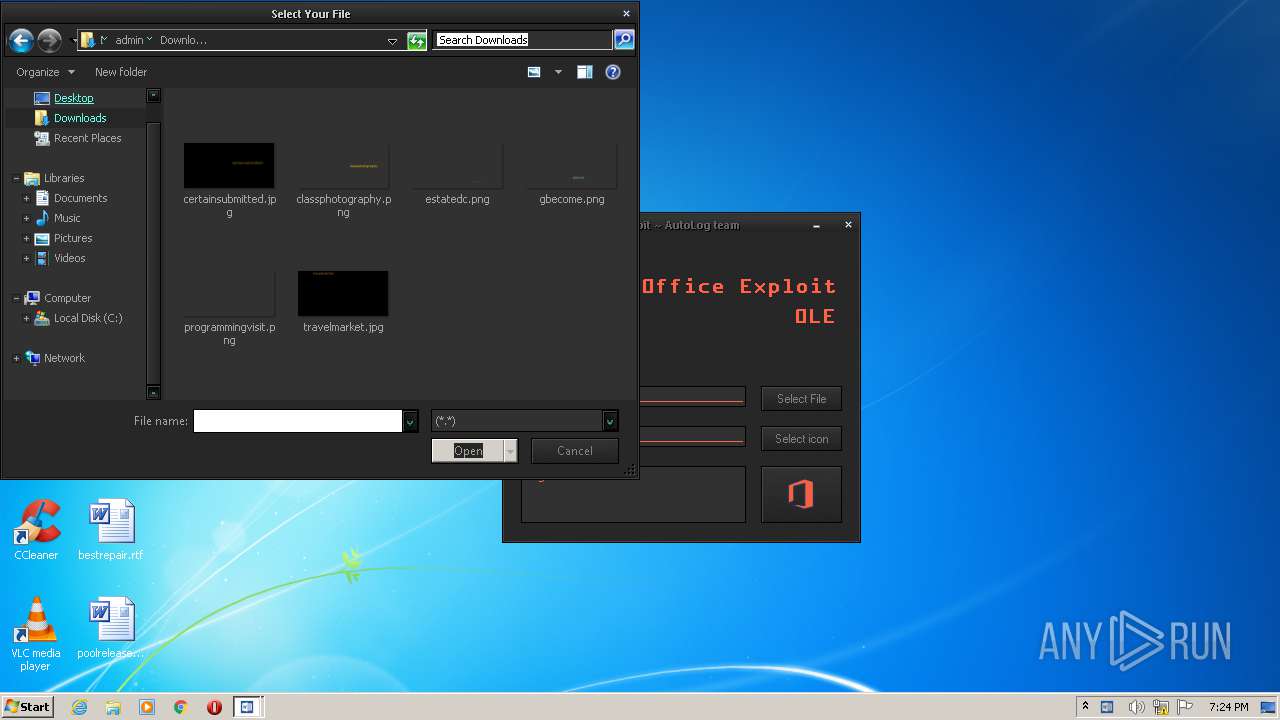
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3580 | DOC Exploit.exe | C:\Users\admin\AppData\Local\Temp\autA887.tmp | mp3 | |
MD5:5D576E372446A31B0B487E53A971089D | SHA256:4B4AB8243ED3BE25A58EB4BEF6CD27992640AE106734B8489472D22C73988AB6 | |||
| 3580 | DOC Exploit.exe | C:\Users\admin\AppData\Local\Temp\olex.jpg | image | |
MD5:E7285121ADF3FF4CA875EAD987BCAE79 | SHA256:A228C3FAA1AF24F858C9491F1D823FDCFEE8ADEF0DFA9808F66D6273A1A5D532 | |||
| 3580 | DOC Exploit.exe | C:\Users\admin\AppData\Local\Temp\autA888.tmp | binary | |
MD5:5AD9FB1382CC4B104FC4FB5DCEFBC4A9 | SHA256:7017BADEC30312A2D6D60A6EB09283D99B55A852B49A8BA7F3BB915FCFEA1218 | |||
| 3580 | DOC Exploit.exe | C:\Users\admin\AppData\Local\Temp\abzjeua | text | |
MD5:F4260729DB4446D4536EFA8C919443E4 | SHA256:6BFB221419332168B74FC5278ED762066244A796F4854AD9C45BBE7F20BB7C88 | |||
| 3580 | DOC Exploit.exe | C:\Users\admin\AppData\Local\Temp\autA817.tmp | binary | |
MD5:01A0C1BD8DEFC2DF7796D1E9542A2EBB | SHA256:2FD19F4D0636BE9A381C399792073BD49E67E8715254239EFC3ED729FE824865 | |||
| 3580 | DOC Exploit.exe | C:\Users\admin\AppData\Local\Temp\skin.dll | executable | |
MD5:29E1D5770184BF45139084BCED50D306 | SHA256:794987C4069286F797631F936C73B925C663C42D552AECA821106DFC7C7BA307 | |||
| 3580 | DOC Exploit.exe | C:\Users\admin\AppData\Local\Temp\skinclas.msstyles | executable | |
MD5:719C51F5637D922E8416E23D0978B8CB | SHA256:6CF0BF46C9EE98FDE7EB4DBC0B147E33BABEABF9B1F50A4722E29DD57E95EF09 | |||
| 3580 | DOC Exploit.exe | C:\Users\admin\AppData\Local\Temp\xc1.ico | image | |
MD5:034C268FFC3A63DB99EF0FE66C14A4E4 | SHA256:17A46EB6076EEE70791D378EF29C1C2DA61725B51C63242626CC5D93F2219178 | |||
| 3580 | DOC Exploit.exe | C:\Users\admin\AppData\Local\Temp\autA856.tmp | executable | |
MD5:29E1D5770184BF45139084BCED50D306 | SHA256:794987C4069286F797631F936C73B925C663C42D552AECA821106DFC7C7BA307 | |||
| 3580 | DOC Exploit.exe | C:\Users\admin\AppData\Local\Temp\autA7F6.tmp | binary | |
MD5:A7984E49D25A9FB3D2CDC2885DC7ACD8 | SHA256:4BE16BAB3B82A736BD47DDDE8FCDD09A76A6F1B4032AB883DFBF2325E7E36E9F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report