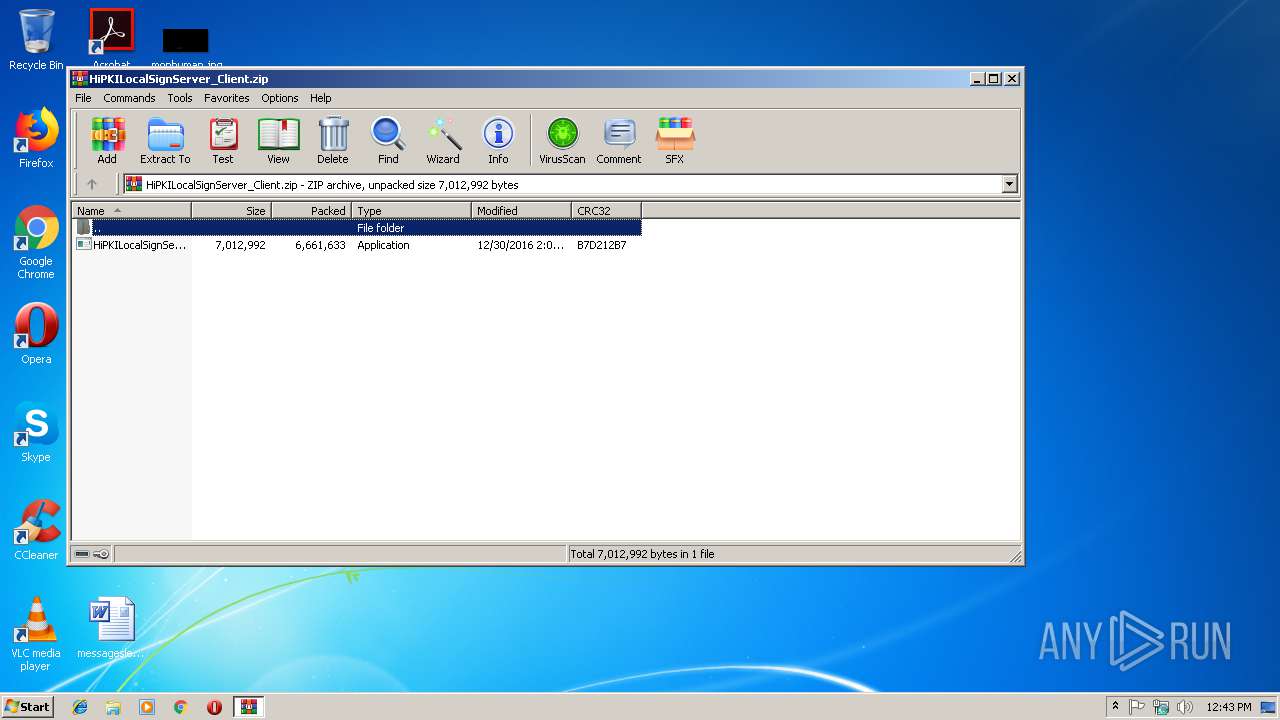
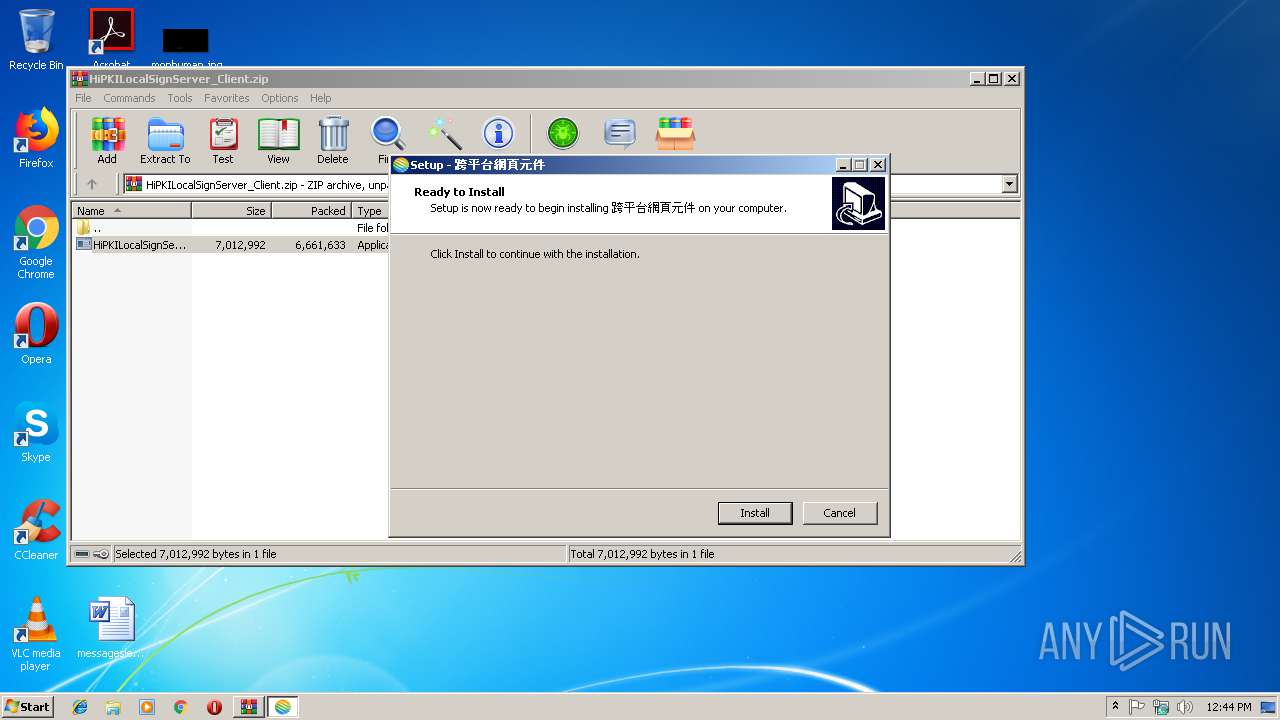
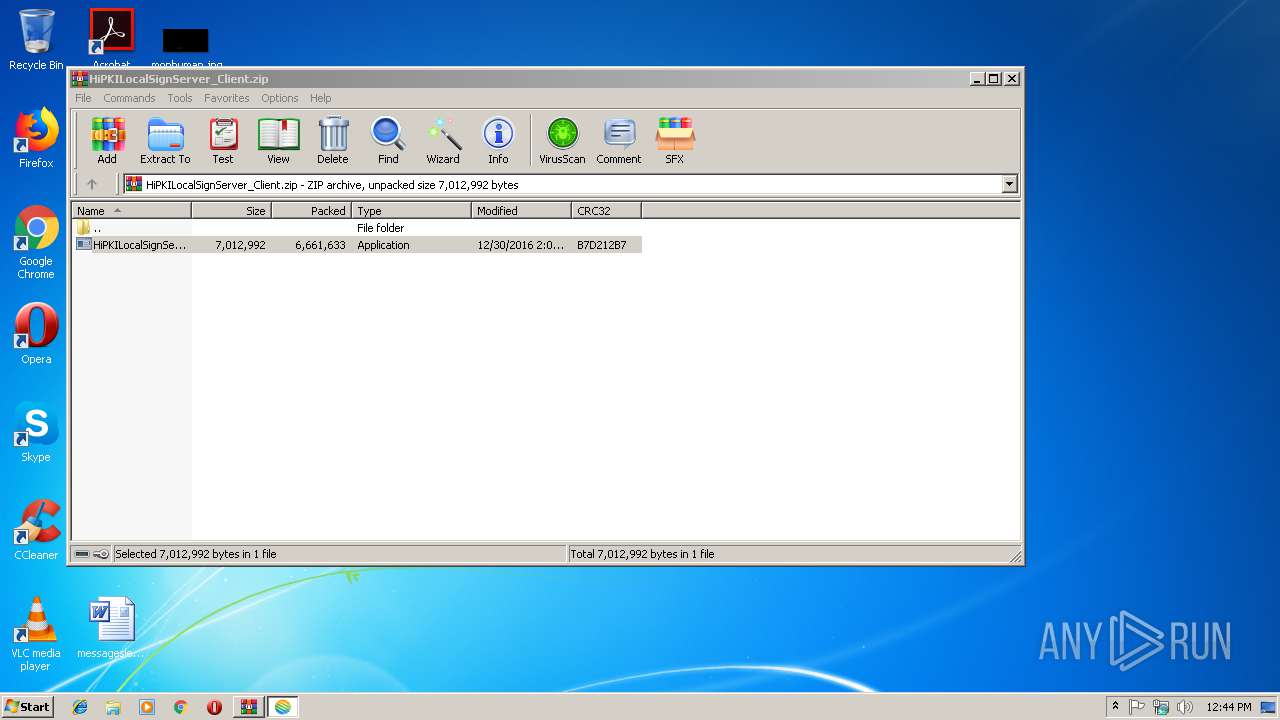
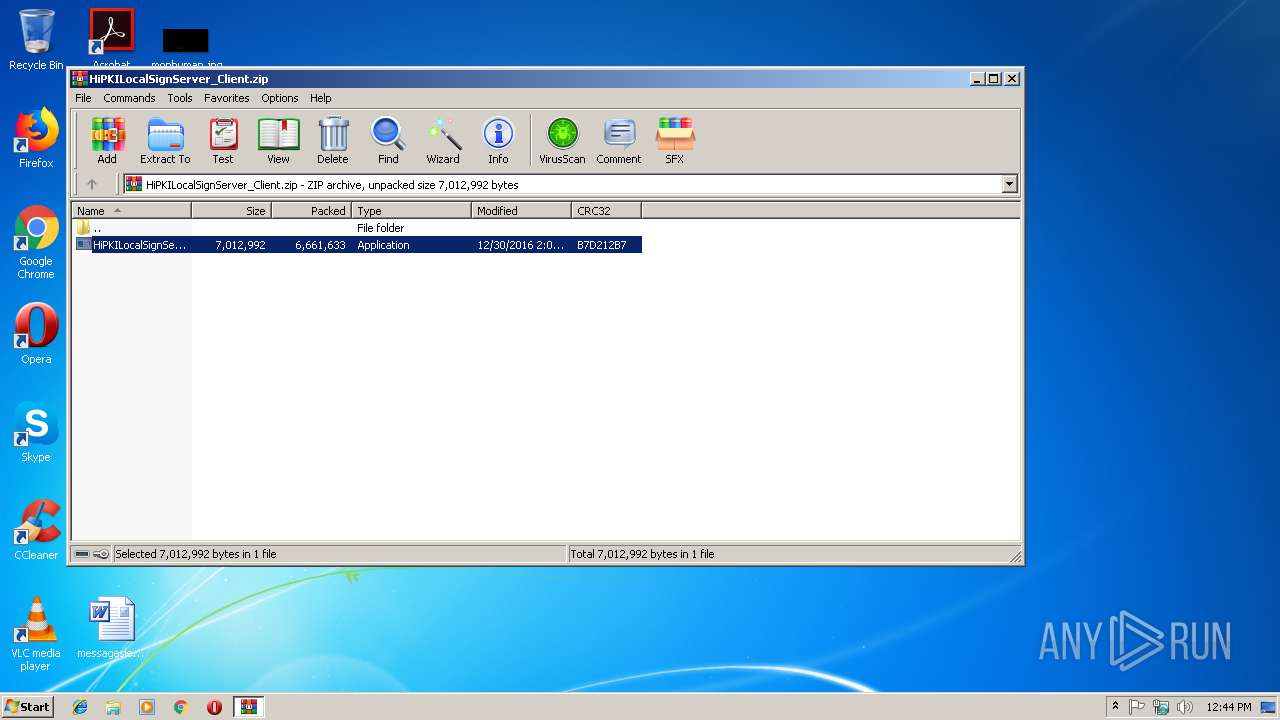
| download: | HiPKILocalSignServer_Client.zip |
| Full analysis: | https://app.any.run/tasks/7120e84b-f3b2-4628-ae40-3363425d3166 |
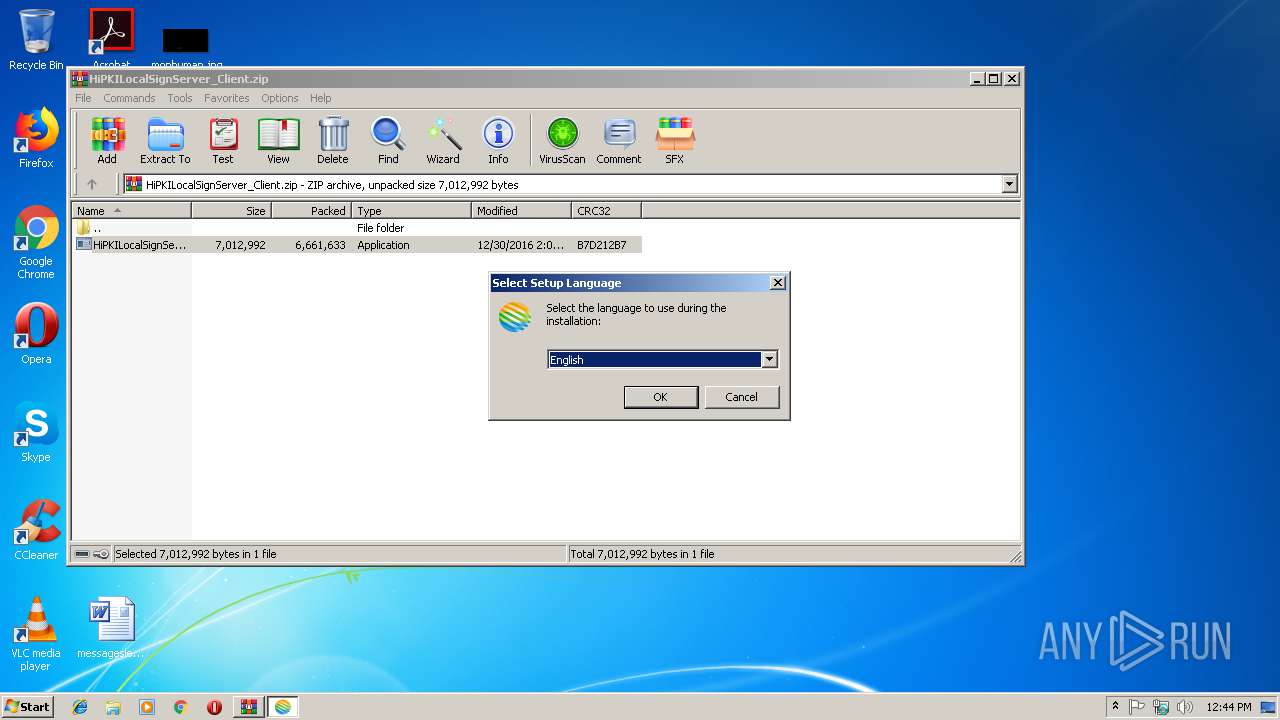
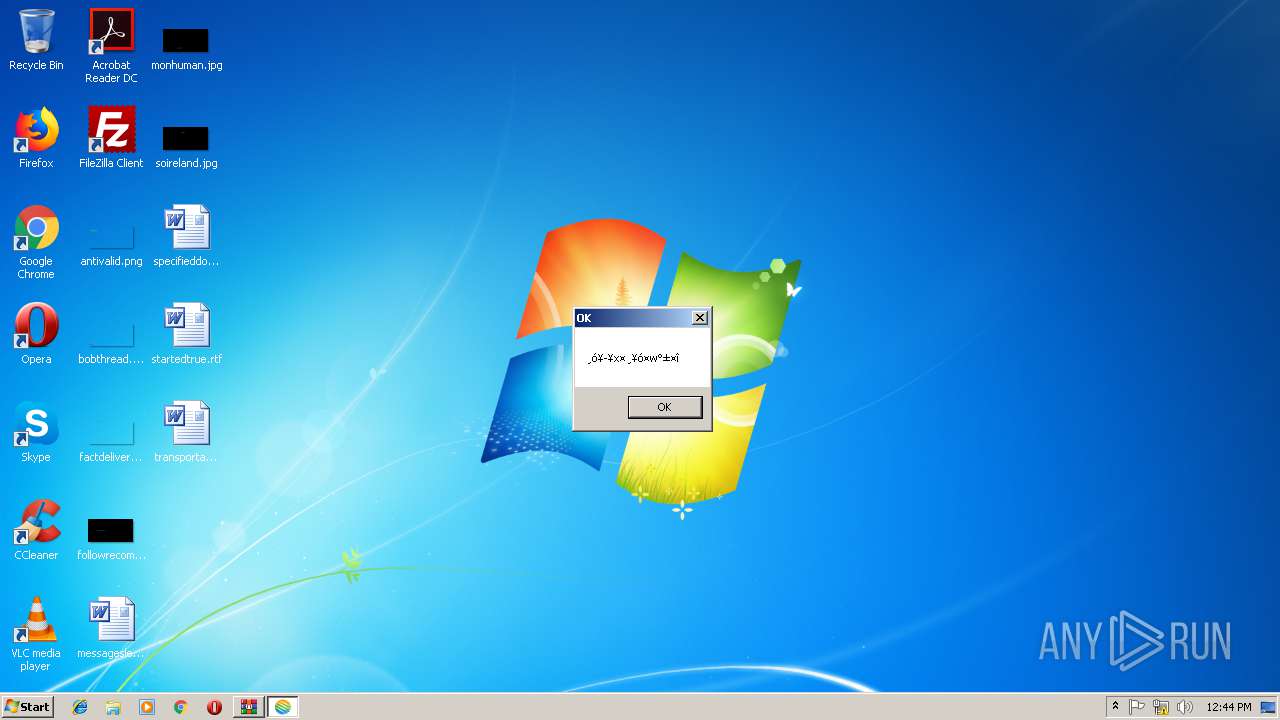
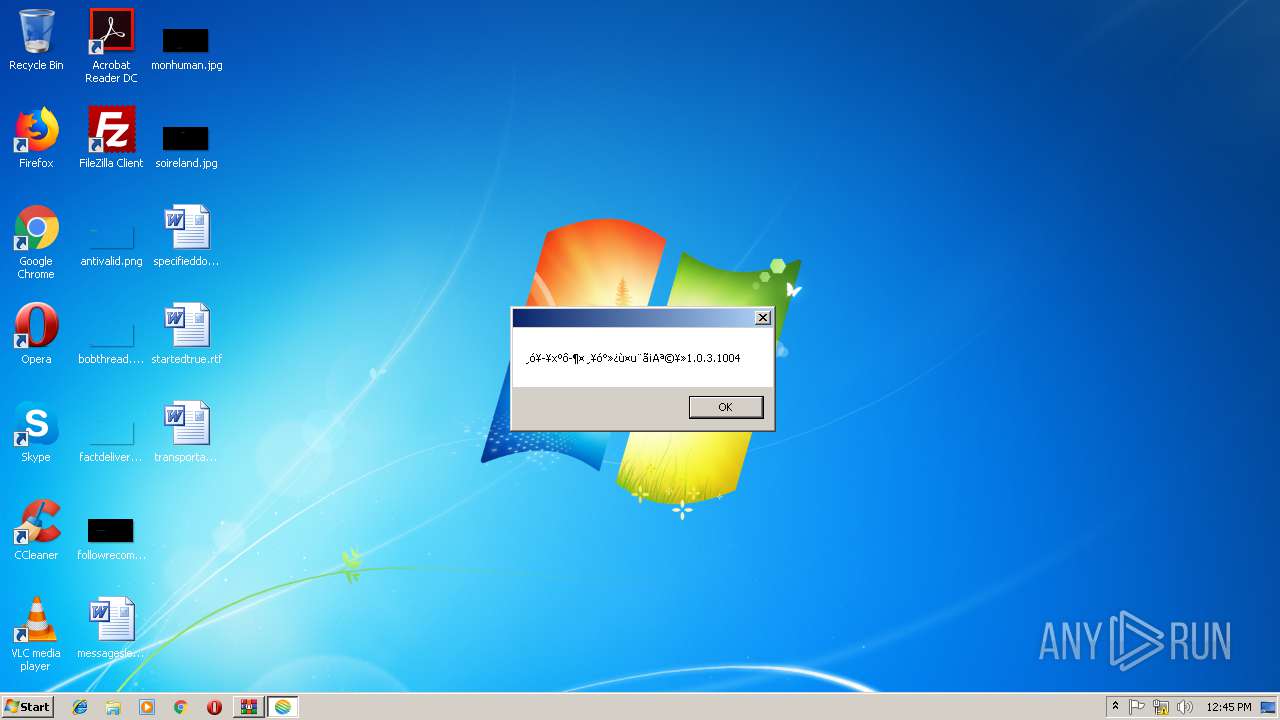
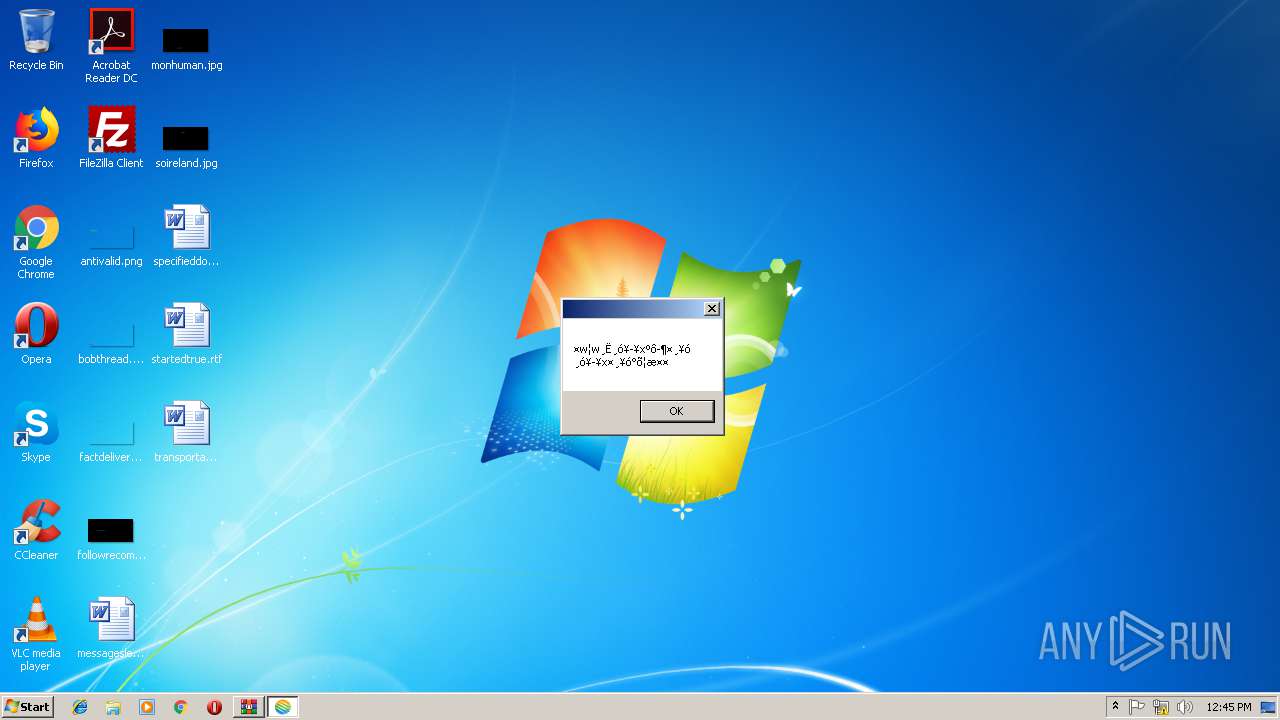
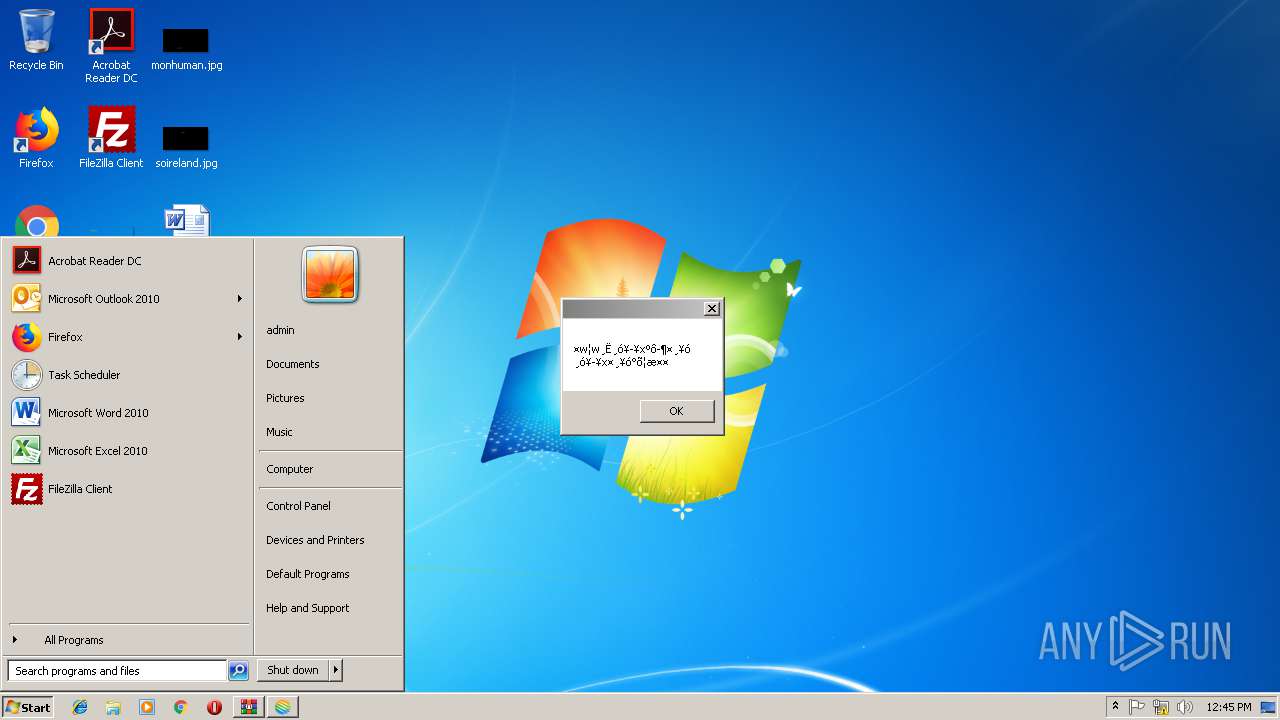
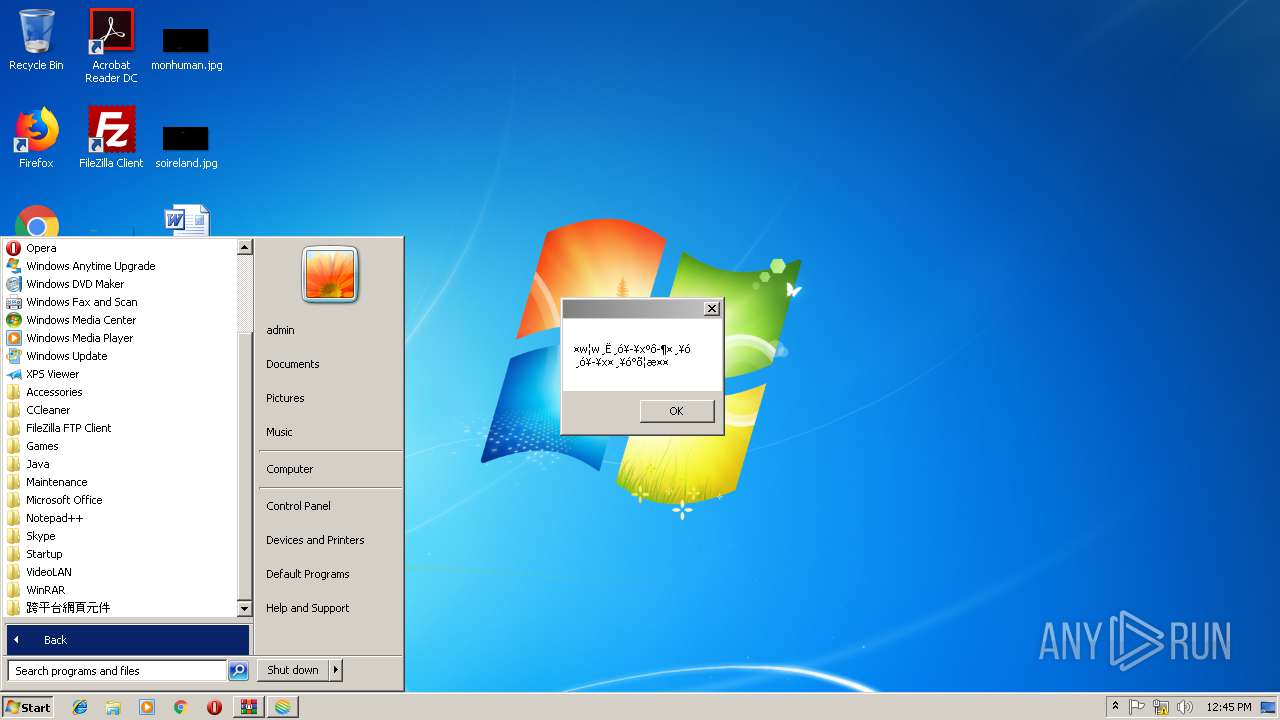
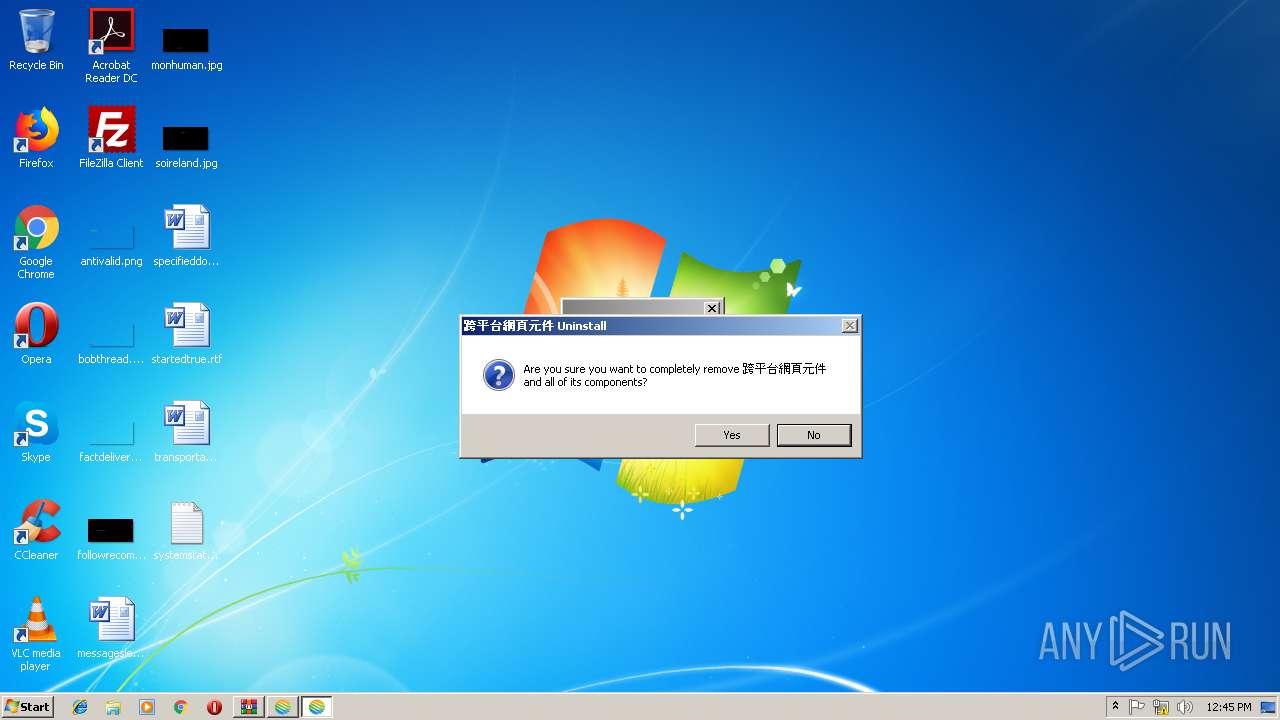
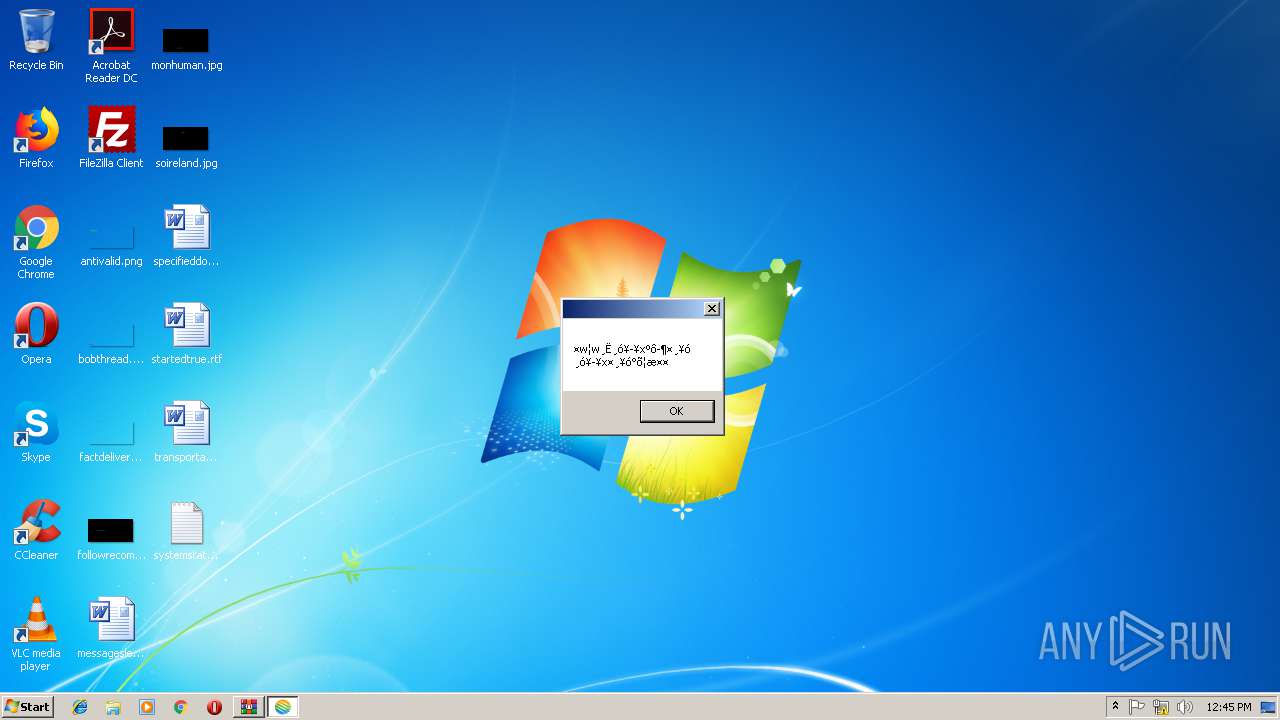
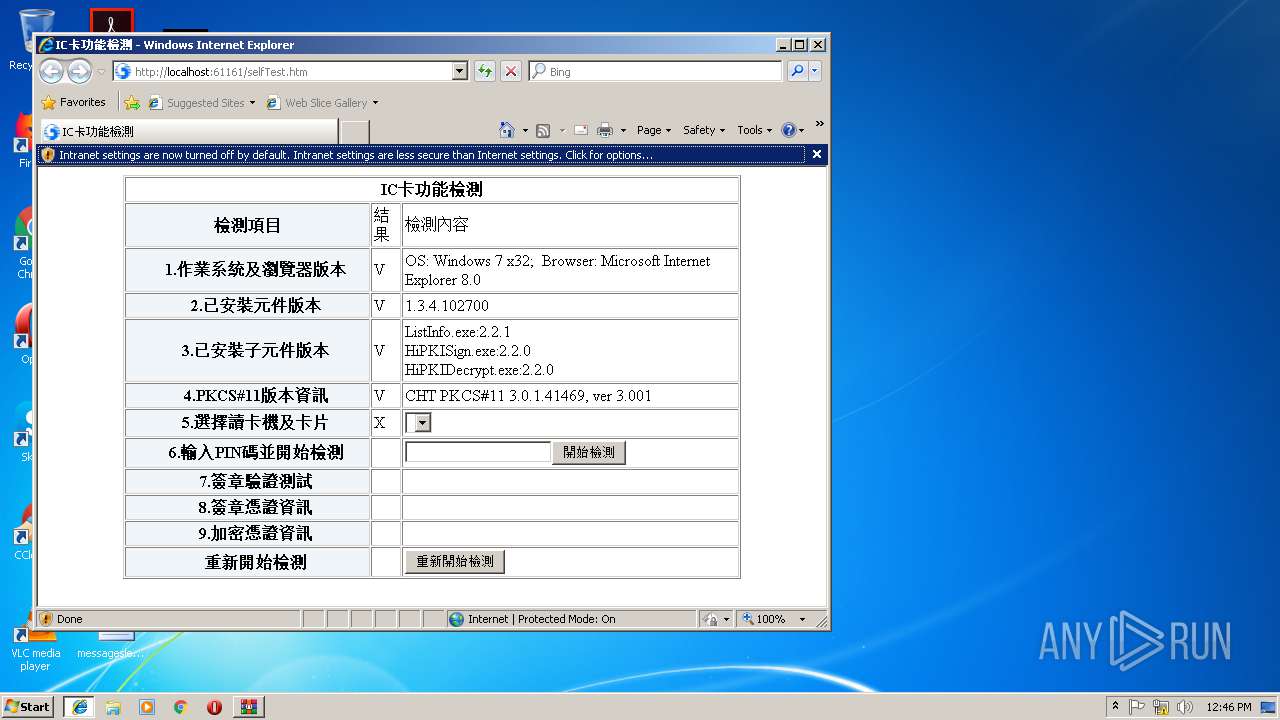
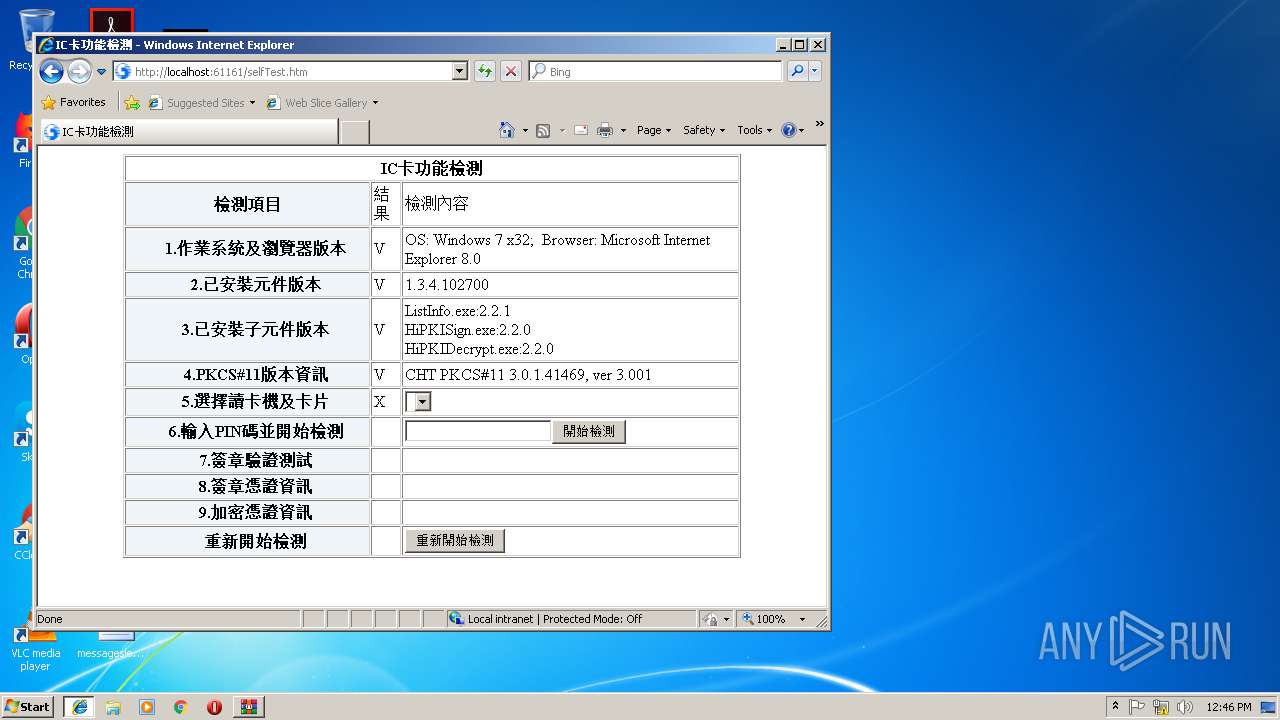
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2018, 12:43:24 |
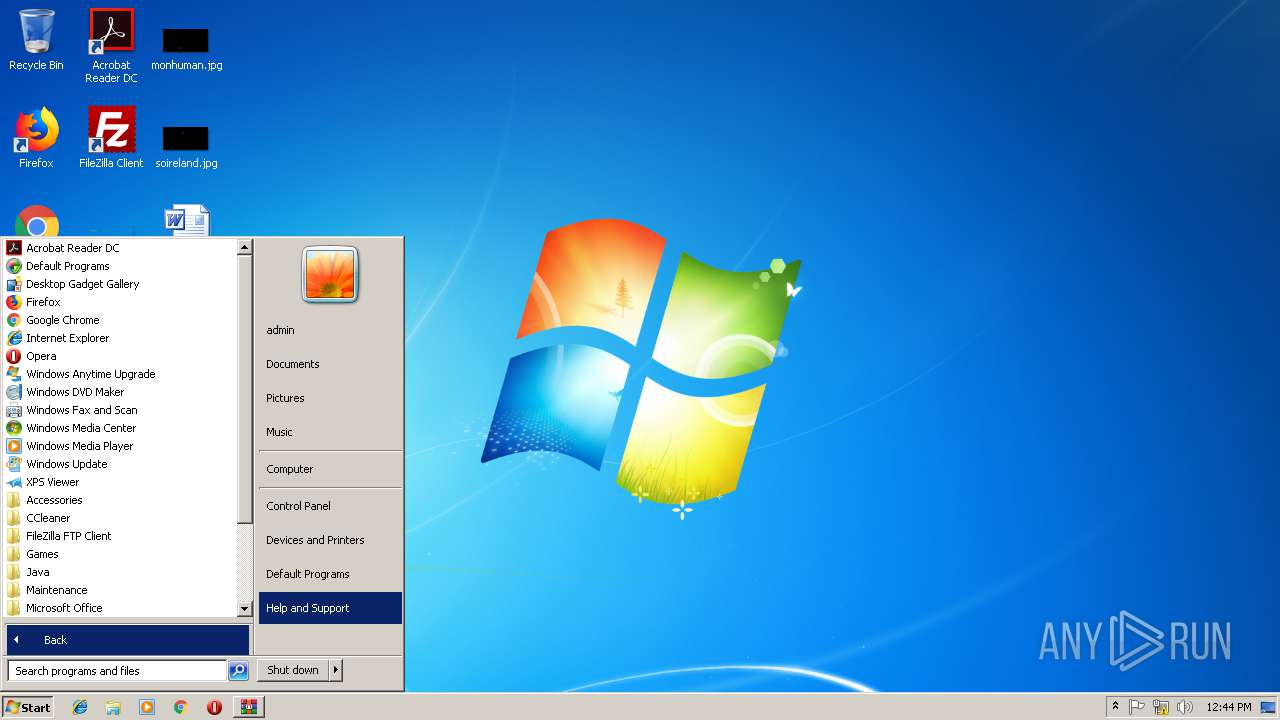
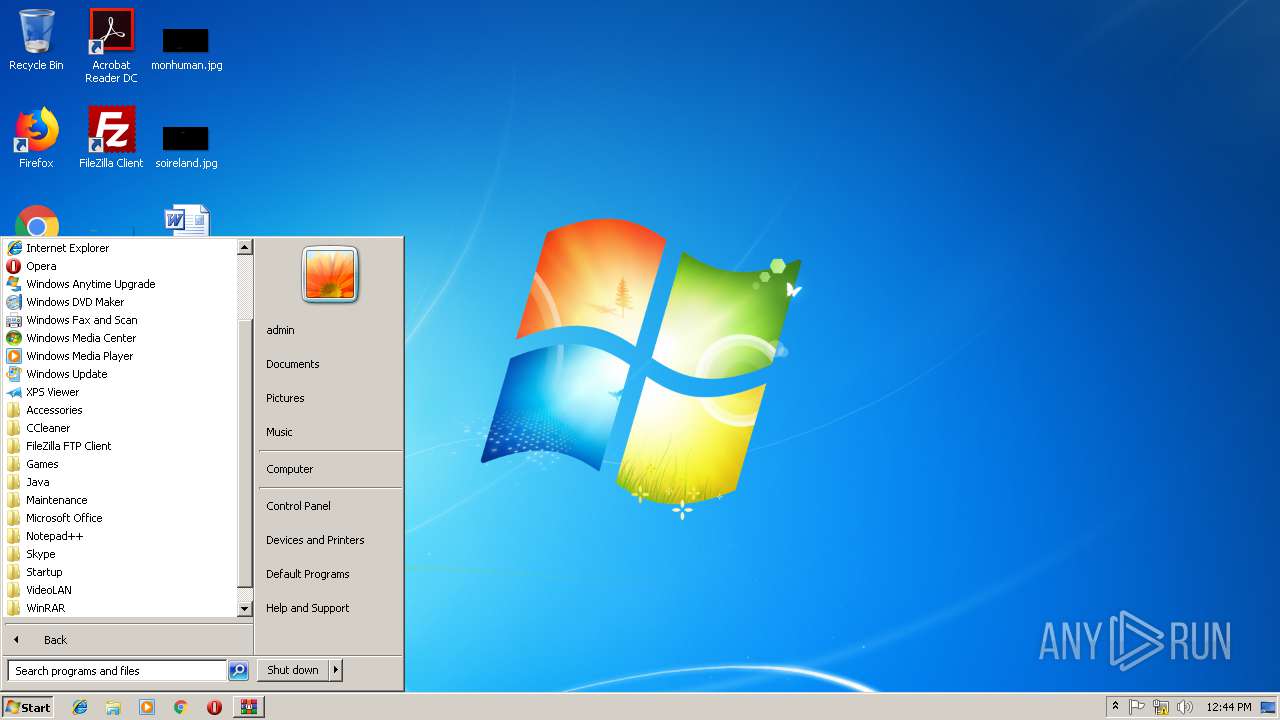
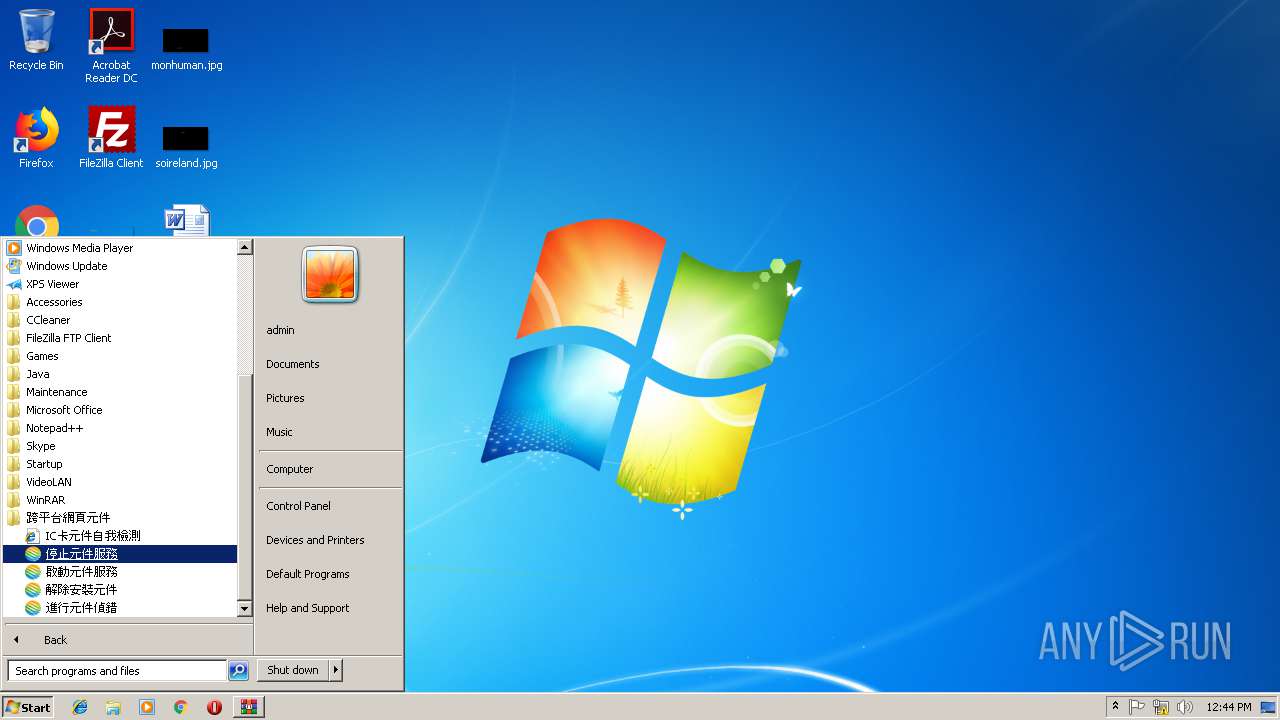
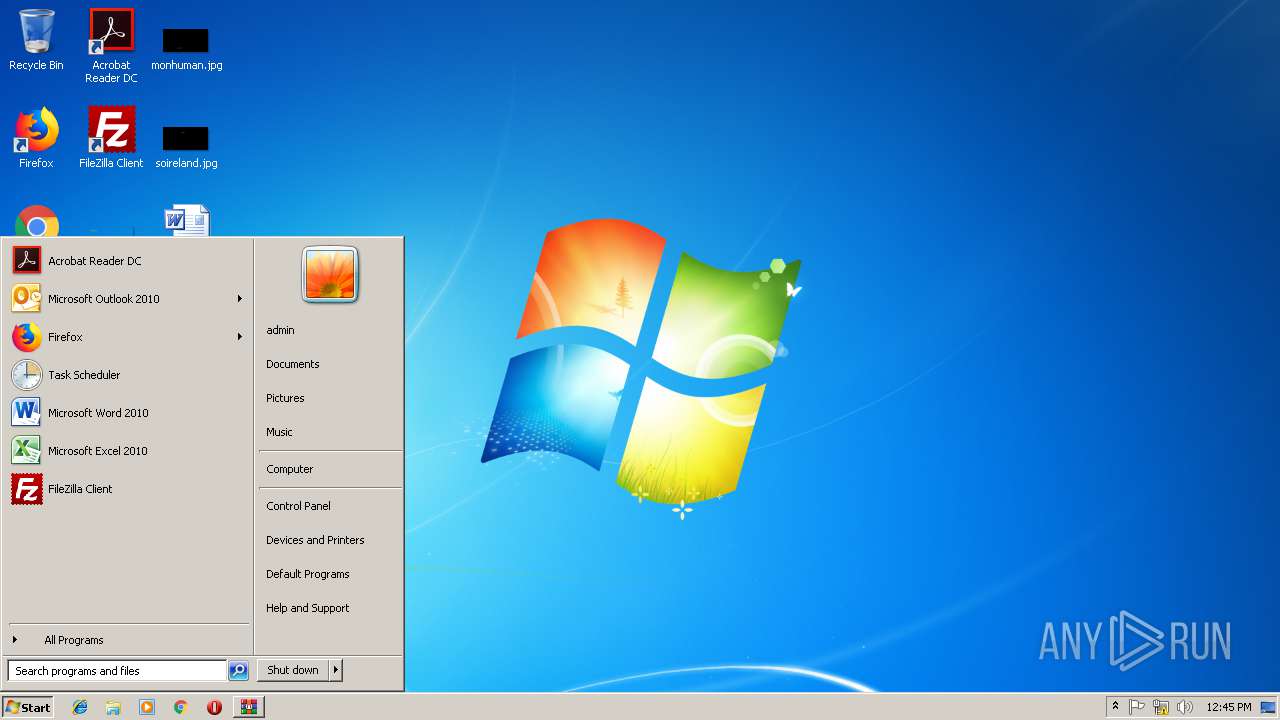
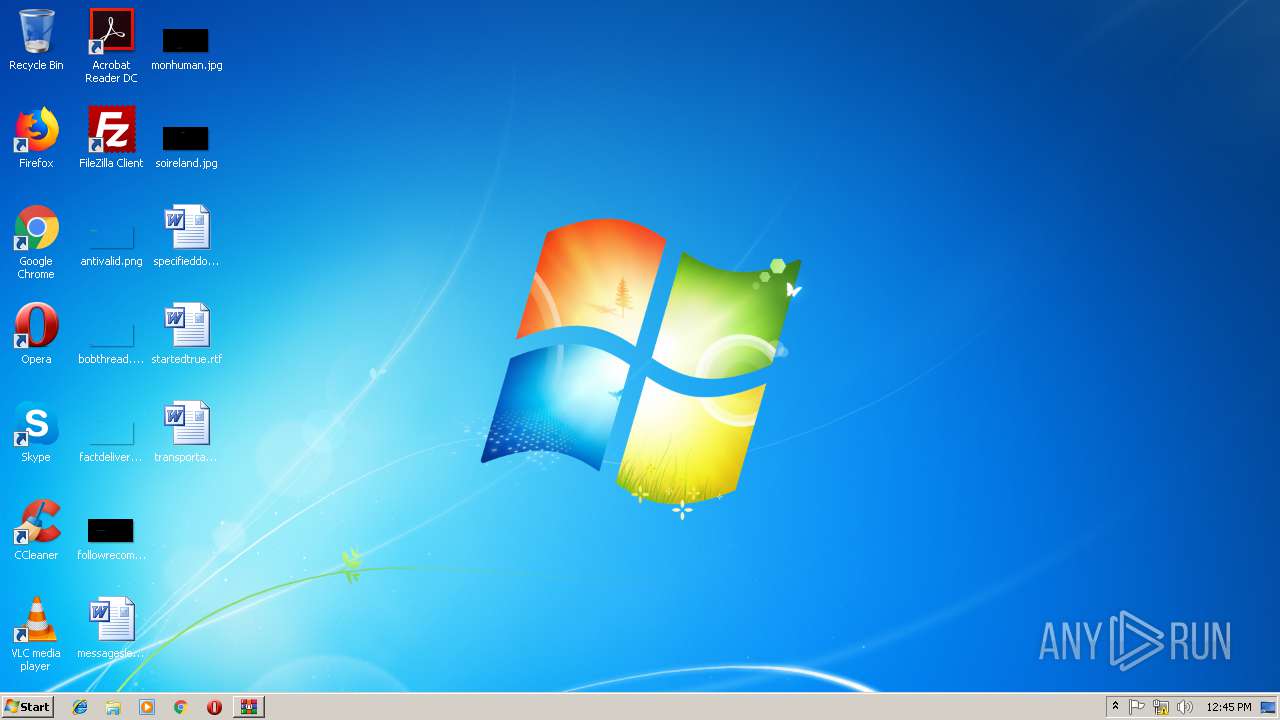
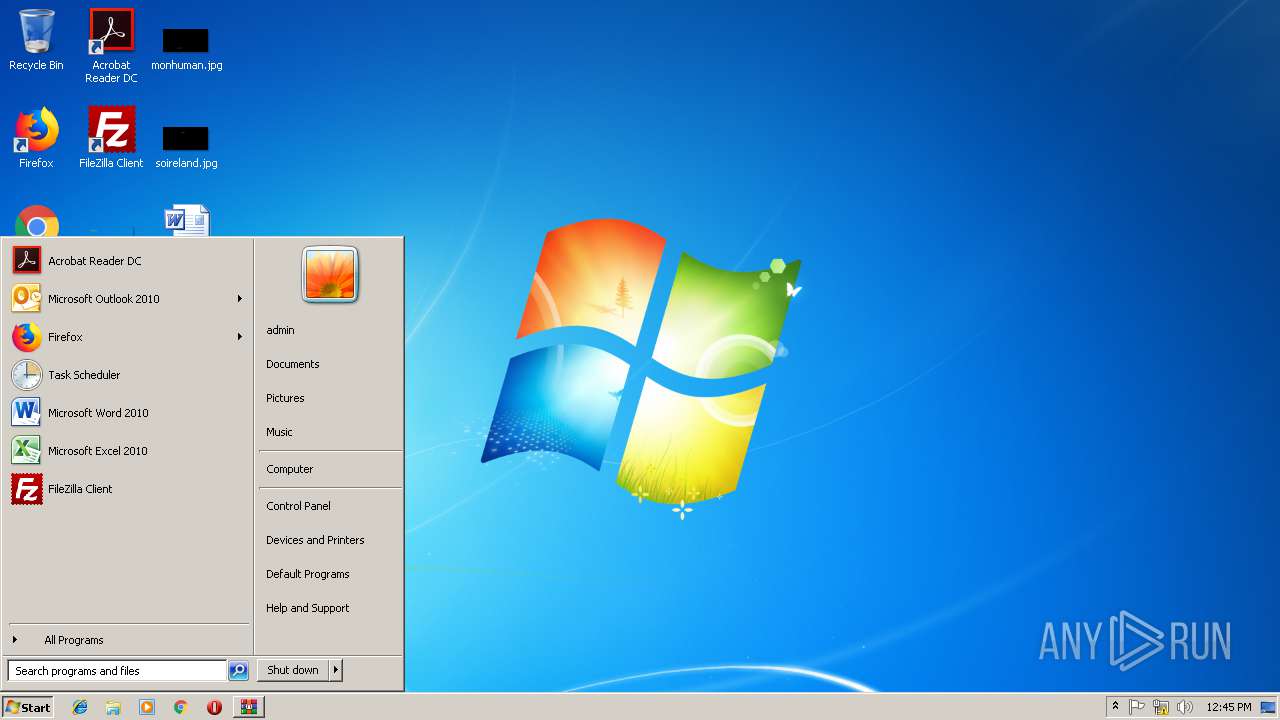
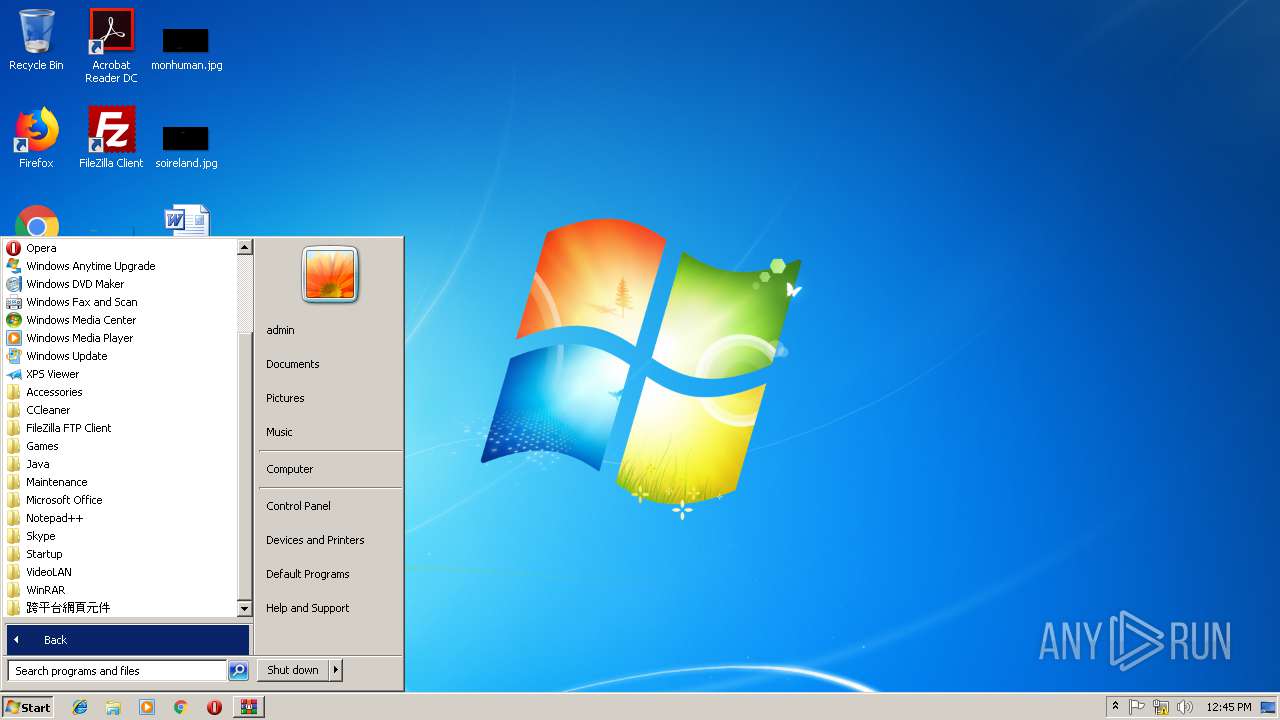
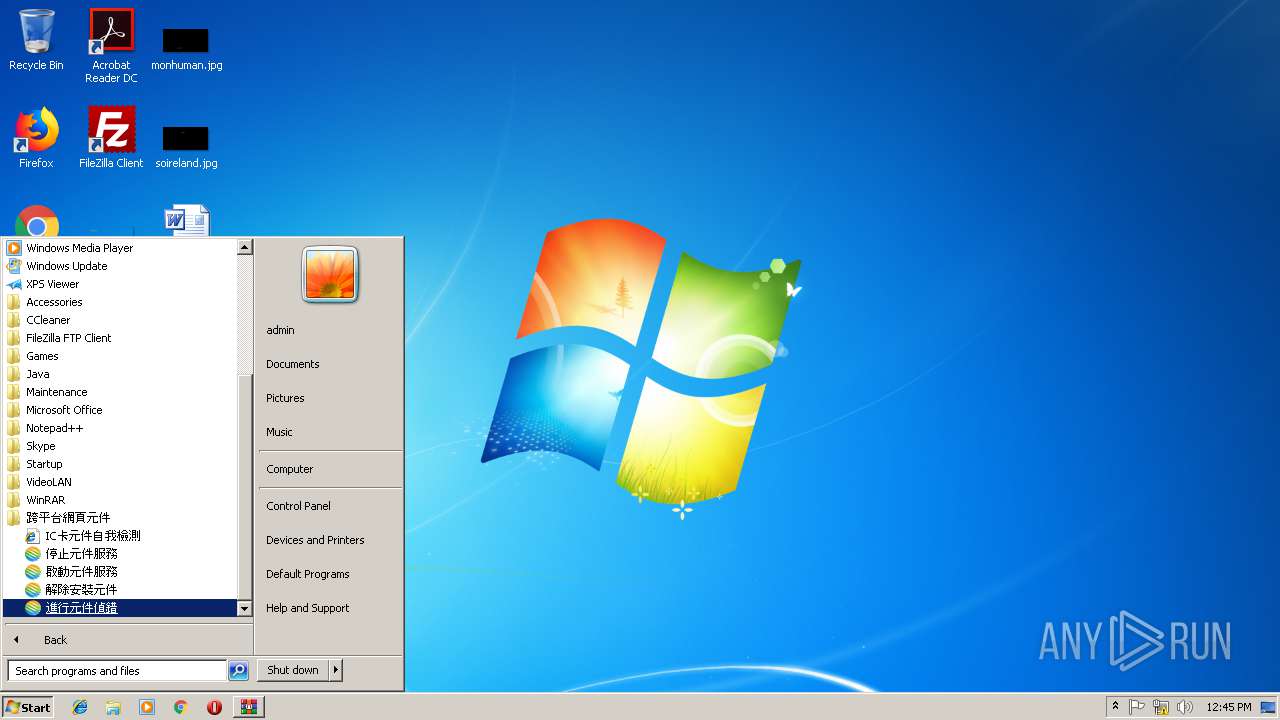
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | AC10470A9F1A5D003152AC69D064E56E |
| SHA1: | F975598958A16C3F2A9B6A366925459BBD794F76 |
| SHA256: | 3A974144E2FC7F71464CBA506088A5C09027CCDB9F2A8AE011F229F2055703F2 |
| SSDEEP: | 98304:w64EXsMN8XlHJ8/UB3UD0lAMkPuHBfLBhcGFp5fsQO/edpL07qCuRLy/1J:VsMNQlH+UUpMkPKBQSfVtLQ |
MALICIOUS
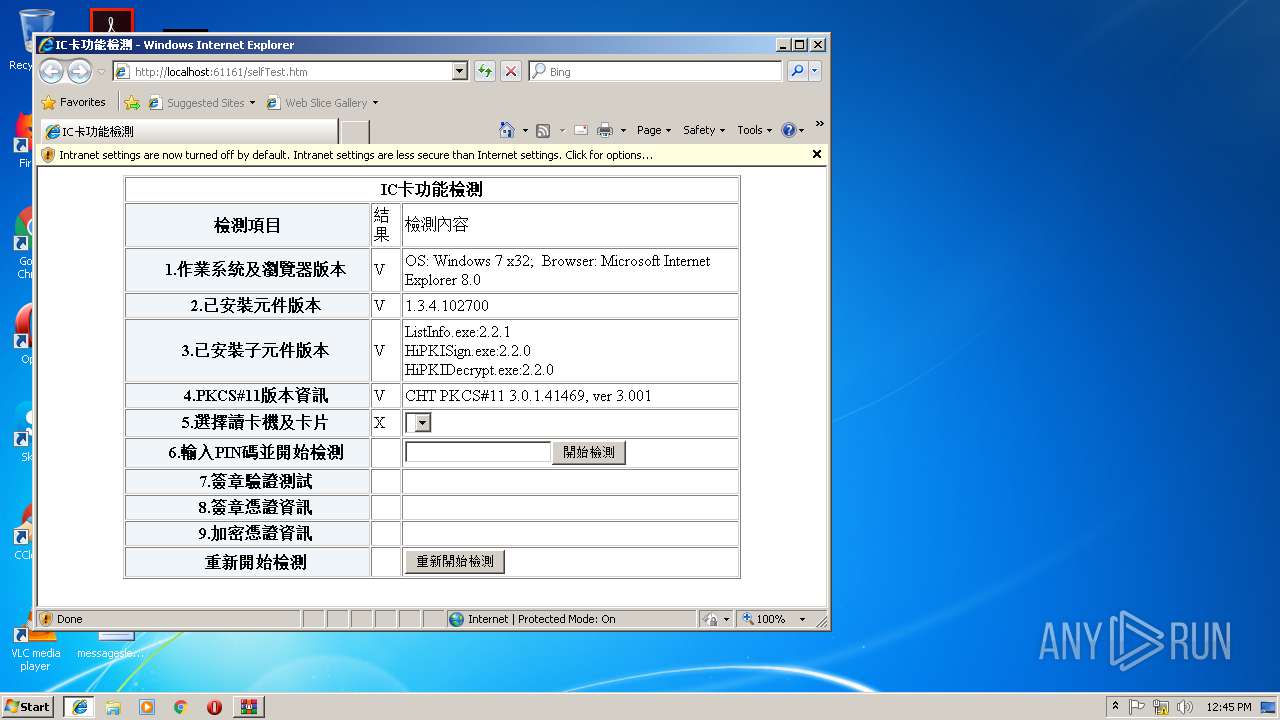
Application was dropped or rewritten from another process
- HiPKILocalSignServer_1.3.4_102700.exe (PID: 3672)
- CheckServer.exe (PID: 3552)
- chtnode.exe (PID: 1520)
- chtnode.exe (PID: 2576)
- CheckServer.exe (PID: 3044)
- CheckServer.exe (PID: 2040)
- CheckServer.exe (PID: 3068)
- unins000.exe (PID: 2312)
- ListInfo.exe (PID: 2664)
- HiPKISign.exe (PID: 996)
- _iu14D2N.tmp (PID: 3092)
- ListInfo.exe (PID: 3732)
- HiPKIDecrypt.exe (PID: 3424)
- HiPKIDecrypt.exe (PID: 2388)
- HiPKISign.exe (PID: 2608)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 3164)
- _iu14D2N.tmp (PID: 3092)
- ListInfo.exe (PID: 2664)
Registers / Runs the DLL via REGSVR32.EXE
- HiPKILocalSignServer_1.3.4_102700.tmp (PID: 2236)
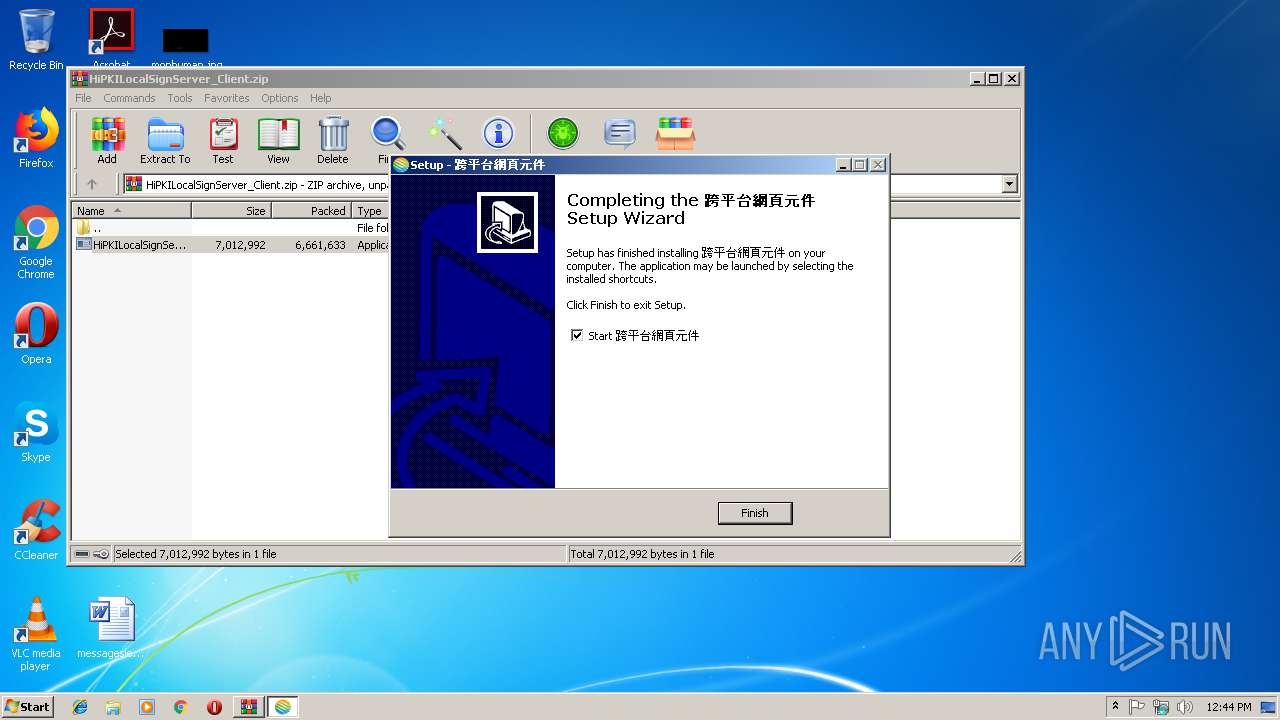
Changes the autorun value in the registry
- HiPKILocalSignServer_1.3.4_102700.tmp (PID: 2236)
SUSPICIOUS
Reads the Windows organization settings
- HiPKILocalSignServer_1.3.4_102700.tmp (PID: 2236)
- _iu14D2N.tmp (PID: 3092)
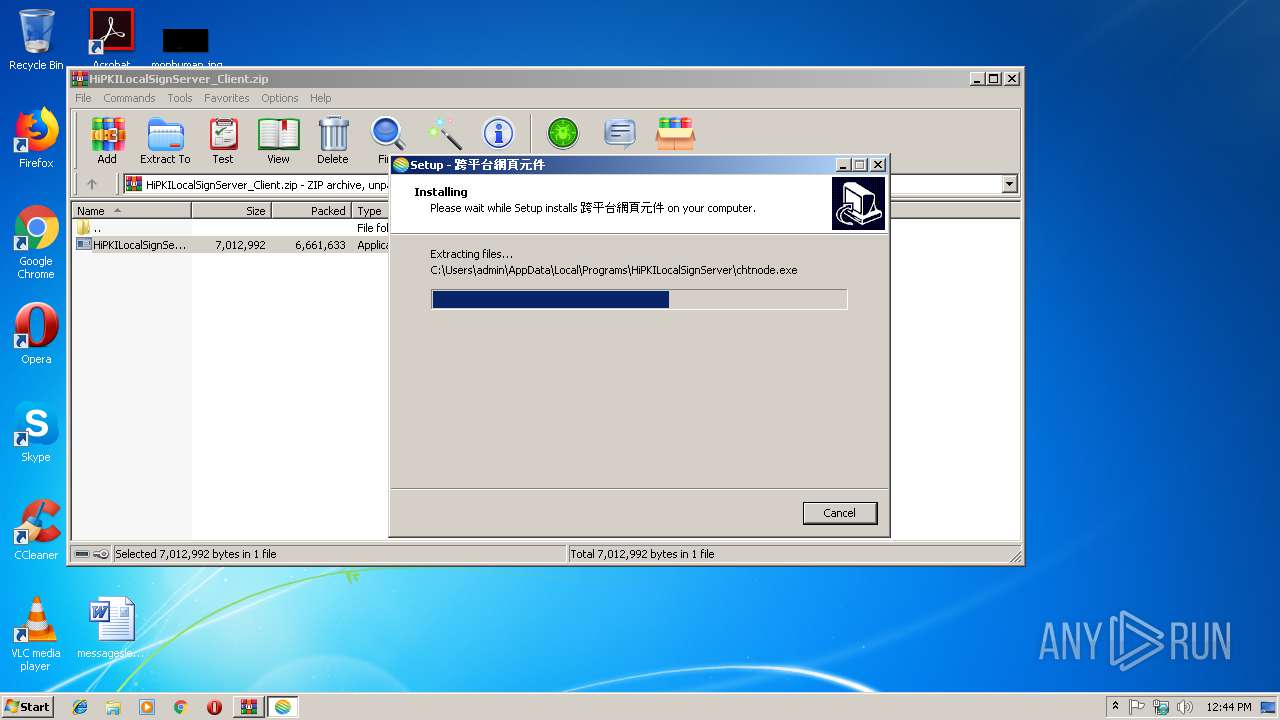
Executable content was dropped or overwritten
- HiPKILocalSignServer_1.3.4_102700.tmp (PID: 2236)
- WinRAR.exe (PID: 4072)
- unins000.exe (PID: 2312)
- _iu14D2N.tmp (PID: 3092)
- HiPKILocalSignServer_1.3.4_102700.exe (PID: 3672)
Creates files in the user directory
- HiPKILocalSignServer_1.3.4_102700.tmp (PID: 2236)
Creates COM task schedule object
- regsvr32.exe (PID: 3164)
Starts application with an unusual extension
- unins000.exe (PID: 2312)
Reads Windows owner or organization settings
- _iu14D2N.tmp (PID: 3092)
- HiPKILocalSignServer_1.3.4_102700.tmp (PID: 2236)
INFO
Loads dropped or rewritten executable
- HiPKILocalSignServer_1.3.4_102700.tmp (PID: 2236)
Creates a software uninstall entry
- HiPKILocalSignServer_1.3.4_102700.tmp (PID: 2236)
Reads internet explorer settings
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 3140)
Reads Internet Cache Settings
- iexplore.exe (PID: 2956)
Creates files in the user directory
- iexplore.exe (PID: 3196)
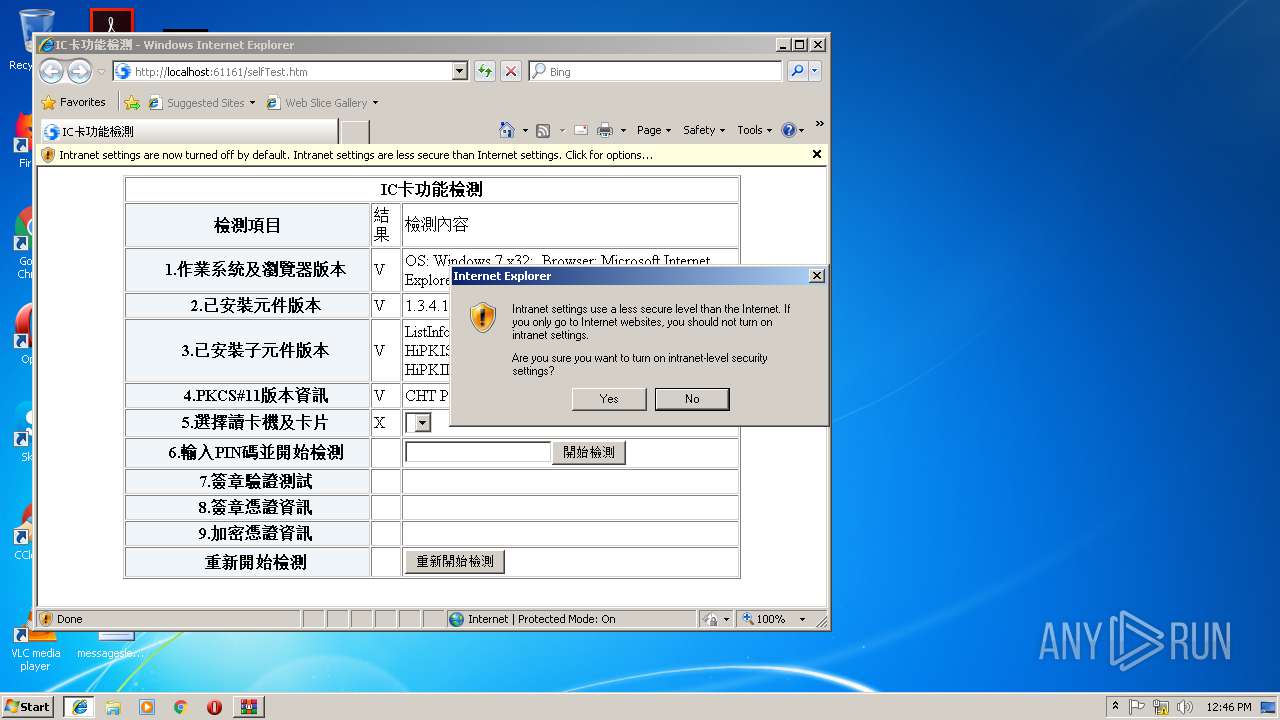
Changes internet zones settings
- iexplore.exe (PID: 3196)
Application launched itself
- iexplore.exe (PID: 3196)
Application was dropped or rewritten from another process
- HiPKILocalSignServer_1.3.4_102700.tmp (PID: 2236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2016:12:30 10:07:03 |
| ZipCRC: | 0xb7d212b7 |
| ZipCompressedSize: | 6661633 |
| ZipUncompressedSize: | 7012992 |
| ZipFileName: | HiPKILocalSignServer_1.3.4_102700.exe |
Total processes
58
Monitored processes
21
Malicious processes
6
Suspicious processes
3
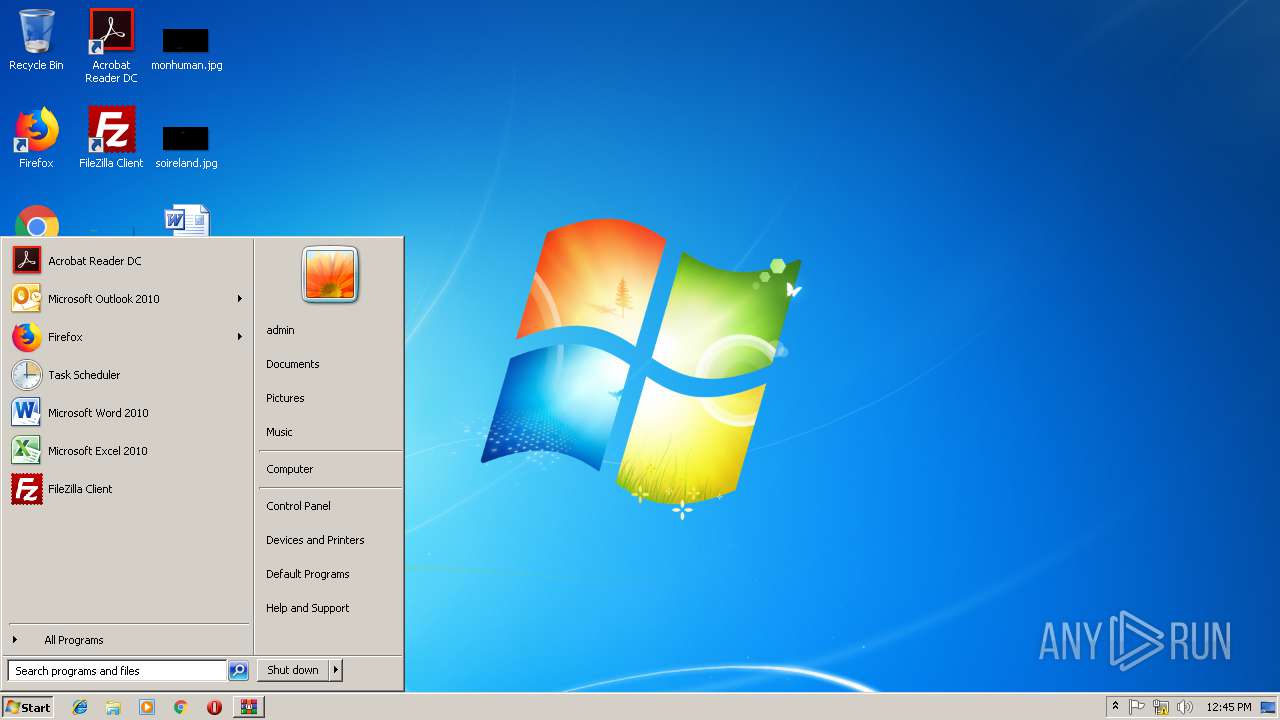
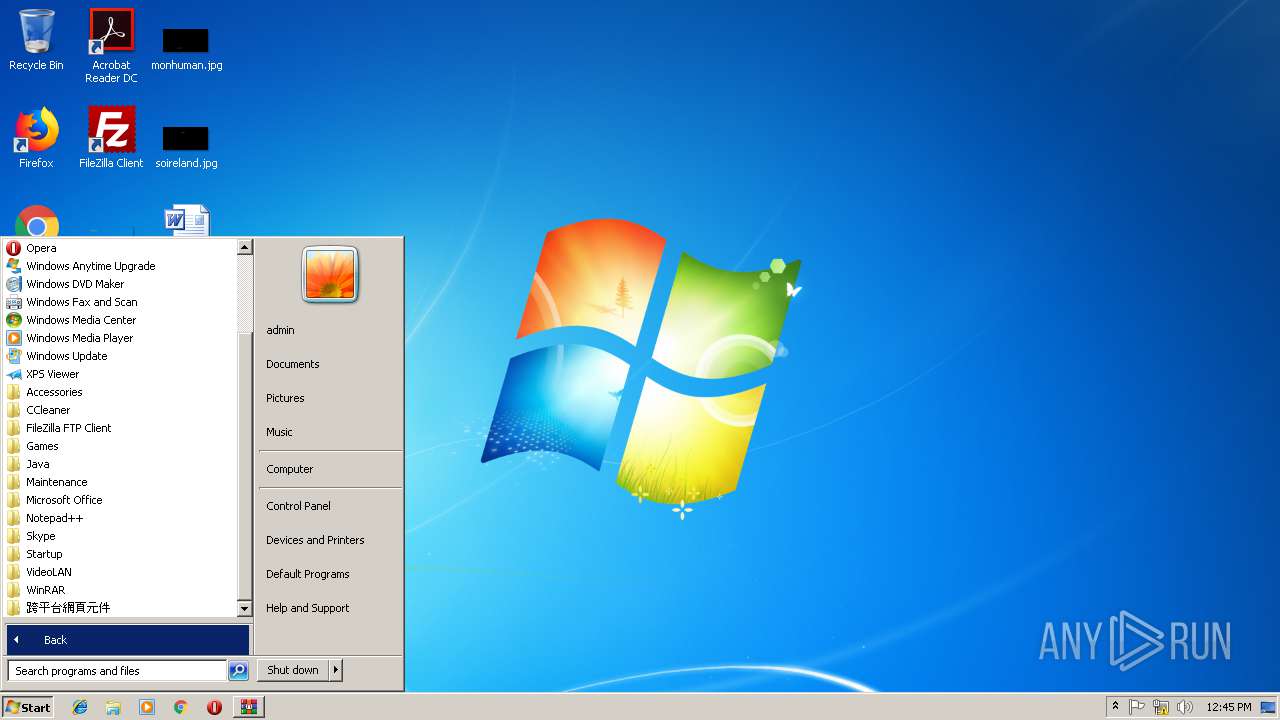
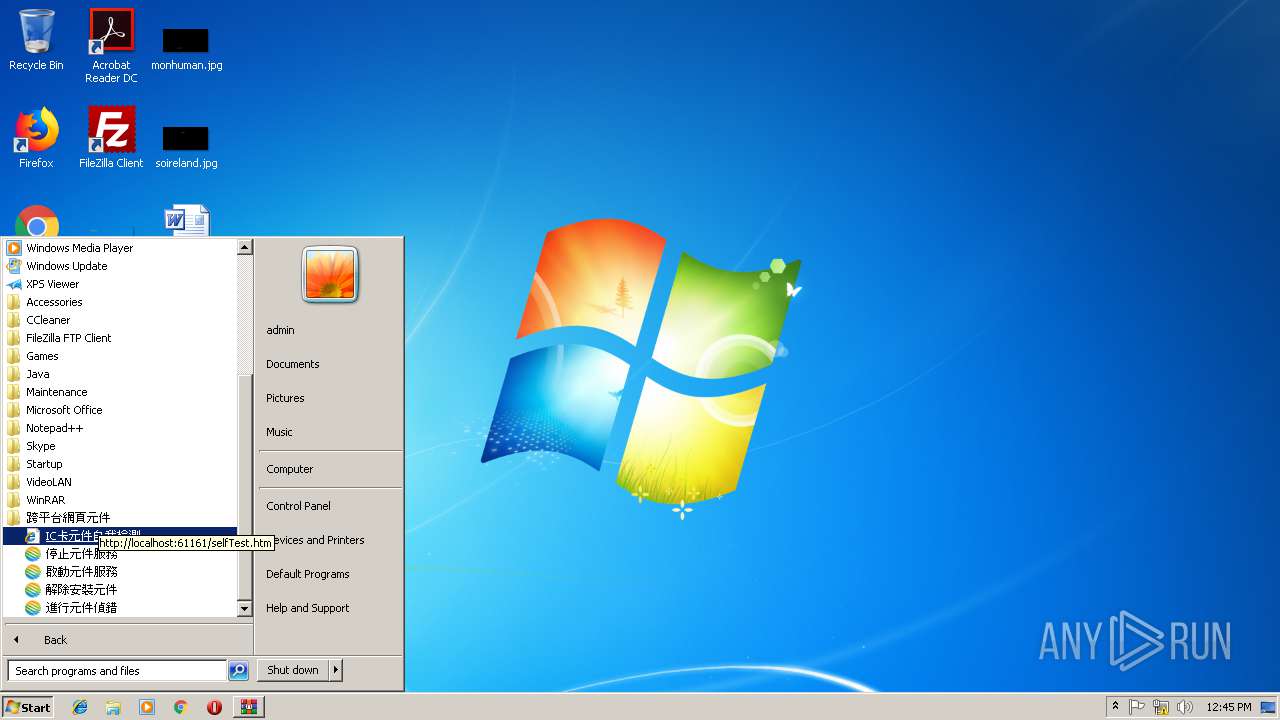
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 996 | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer/HiPKISign.exe "{\"pin\":1234,\"tbs\":\"MTIz\"}" | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\HiPKISign.exe | — | chtnode.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1520 | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\chtnode.exe hipkiLocalServer.js | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\chtnode.exe | — | CheckServer.exe | |||||||||||
User: admin Company: Node.js Integrity Level: MEDIUM Description: Node.js: Server-side JavaScript Exit code: 0 Version: 4.2.1 Modules
| |||||||||||||||
| 2040 | "C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\CheckServer.exe" /start | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\CheckServer.exe | — | HiPKILocalSignServer_1.3.4_102700.tmp | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2236 | "C:\Users\admin\AppData\Local\Temp\is-HB45U.tmp\HiPKILocalSignServer_1.3.4_102700.tmp" /SL5="$50210,6548094,484864,C:\Users\admin\AppData\Local\Temp\Rar$EXa4072.4666\HiPKILocalSignServer_1.3.4_102700.exe" | C:\Users\admin\AppData\Local\Temp\is-HB45U.tmp\HiPKILocalSignServer_1.3.4_102700.tmp | HiPKILocalSignServer_1.3.4_102700.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2312 | "C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\unins000.exe" | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\unins000.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2388 | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer/HiPKIDecrypt.exe "{\"pin\":1234,\"cipher\":\"123\"}" | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\HiPKIDecrypt.exe | — | chtnode.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2576 | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\chtnode.exe hipkiLocalServer.js | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\chtnode.exe | — | CheckServer.exe | |||||||||||
User: admin Company: Node.js Integrity Level: MEDIUM Description: Node.js: Server-side JavaScript Exit code: 0 Version: 4.2.1 Modules
| |||||||||||||||
| 2608 | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer/HiPKISign.exe "{\"pin\":1234,\"tbs\":\"MTIz\"}" | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\HiPKISign.exe | — | chtnode.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2664 | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer/ListInfo.exe {} | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\ListInfo.exe | — | chtnode.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2956 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3196 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 514
Read events
1 273
Write events
232
Delete events
9
Modification events
| (PID) Process: | (4072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4072) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\HiPKILocalSignServer_Client.zip | |||
| (PID) Process: | (4072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4072) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
19
Suspicious files
1
Text files
178
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2236 | HiPKILocalSignServer_1.3.4_102700.tmp | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\is-6CVIT.tmp | — | |
MD5:— | SHA256:— | |||
| 2236 | HiPKILocalSignServer_1.3.4_102700.tmp | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\node_modules\winston\is-HMAIM.tmp | — | |
MD5:— | SHA256:— | |||
| 2236 | HiPKILocalSignServer_1.3.4_102700.tmp | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\node_modules\winston\is-MN0AU.tmp | — | |
MD5:— | SHA256:— | |||
| 2236 | HiPKILocalSignServer_1.3.4_102700.tmp | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\node_modules\winston\is-QLF2D.tmp | — | |
MD5:— | SHA256:— | |||
| 2236 | HiPKILocalSignServer_1.3.4_102700.tmp | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\node_modules\winston\is-8RAET.tmp | — | |
MD5:— | SHA256:— | |||
| 2236 | HiPKILocalSignServer_1.3.4_102700.tmp | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\node_modules\winston\is-GRK1N.tmp | — | |
MD5:— | SHA256:— | |||
| 2236 | HiPKILocalSignServer_1.3.4_102700.tmp | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\node_modules\winston\is-N8F50.tmp | — | |
MD5:— | SHA256:— | |||
| 2236 | HiPKILocalSignServer_1.3.4_102700.tmp | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\node_modules\winston\is-JEMFO.tmp | — | |
MD5:— | SHA256:— | |||
| 2236 | HiPKILocalSignServer_1.3.4_102700.tmp | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\node_modules\winston\docs\is-BE28O.tmp | — | |
MD5:— | SHA256:— | |||
| 2236 | HiPKILocalSignServer_1.3.4_102700.tmp | C:\Users\admin\AppData\Local\Programs\HiPKILocalSignServer\node_modules\winston\examples\is-ON8LS.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3196 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3196 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |