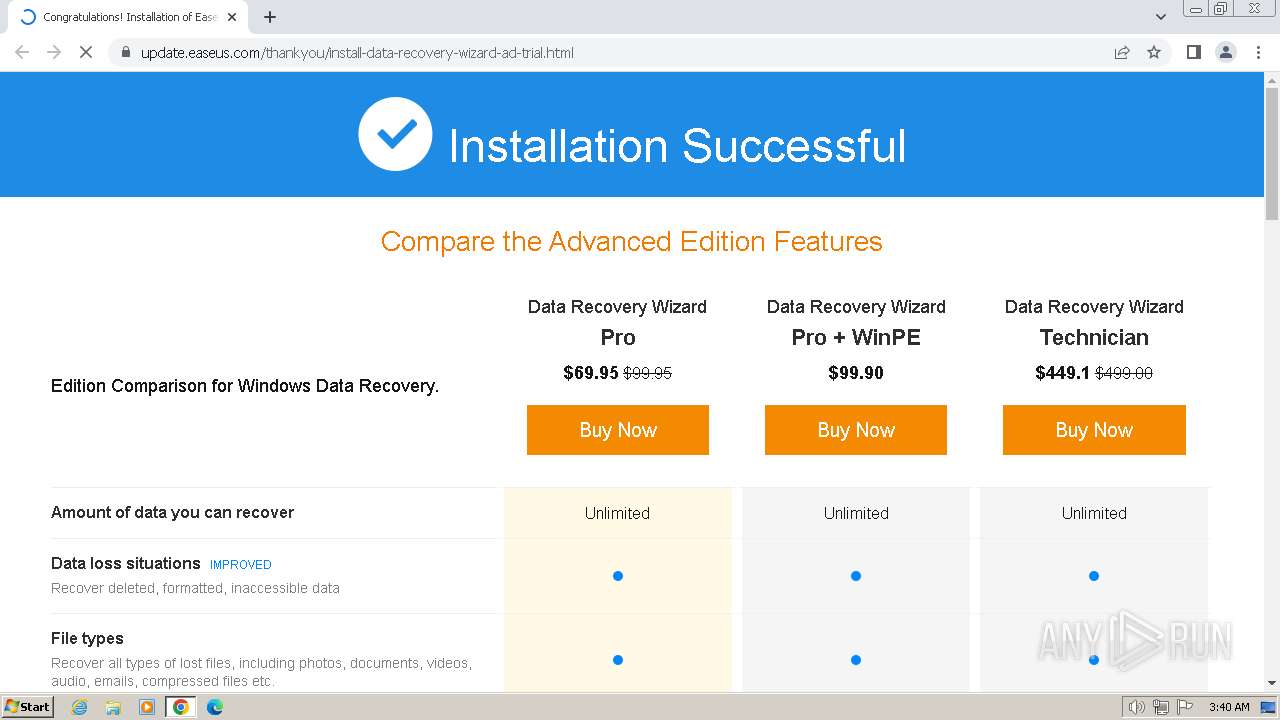
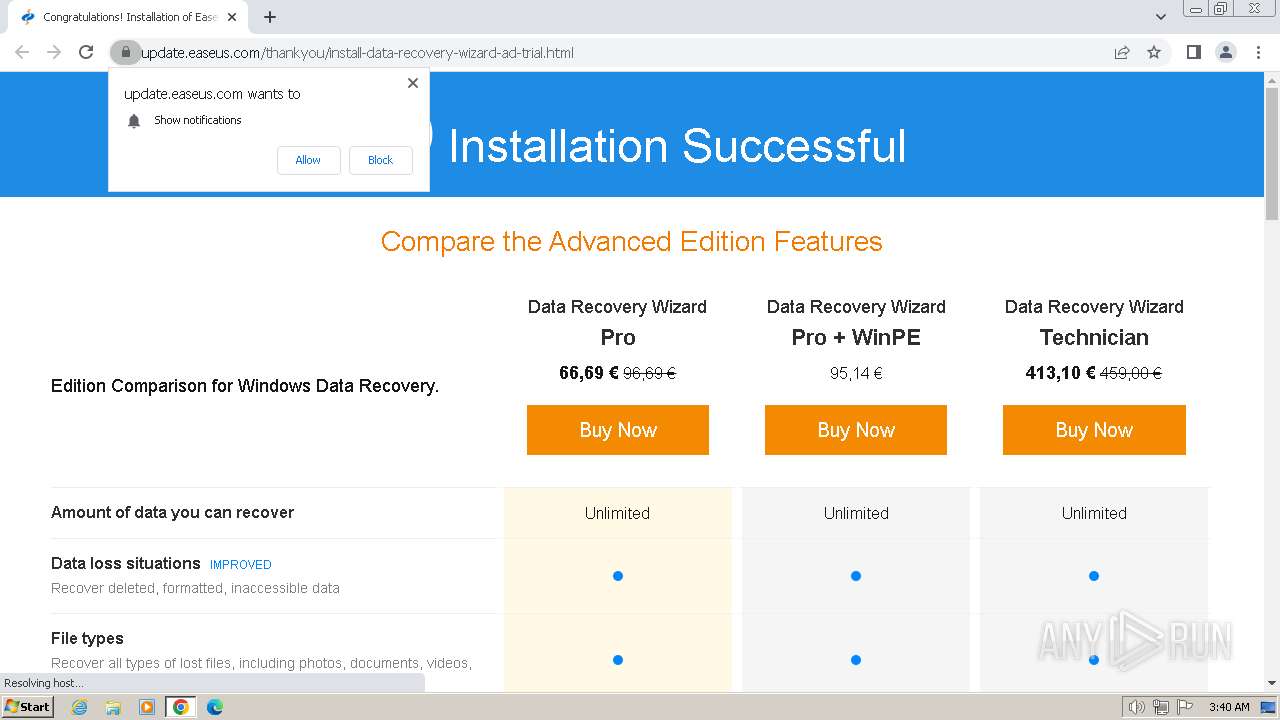
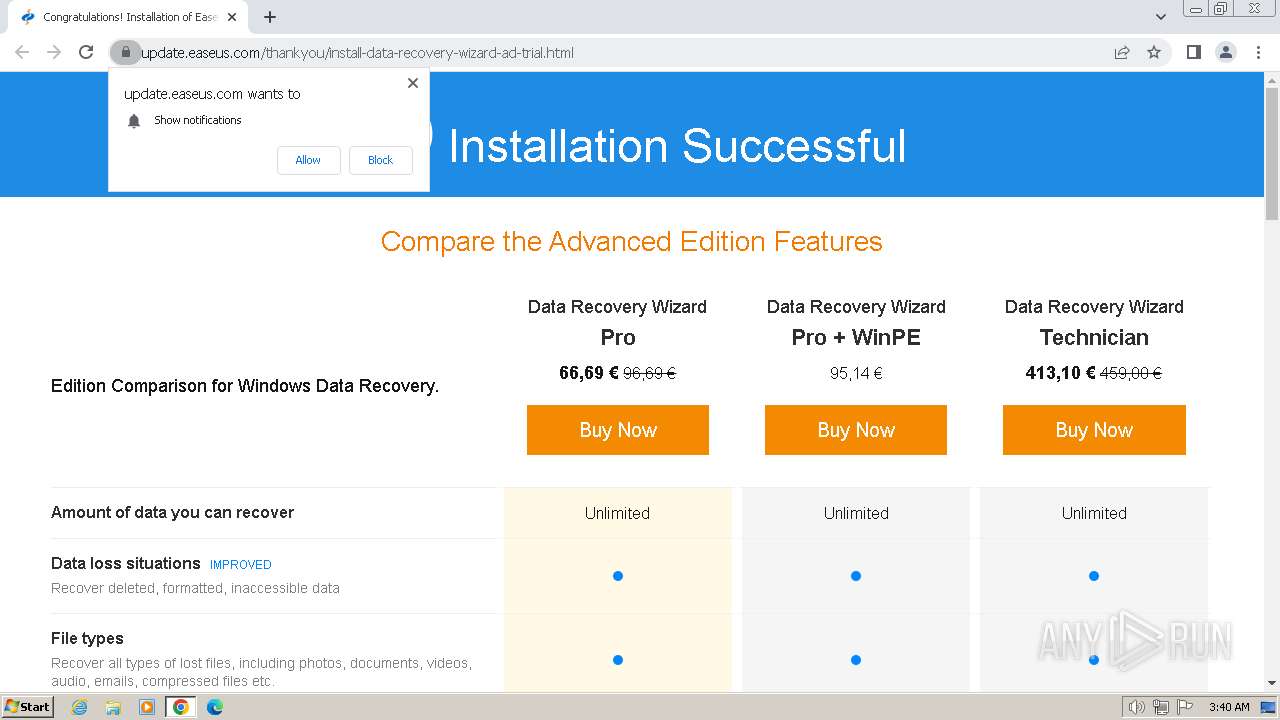
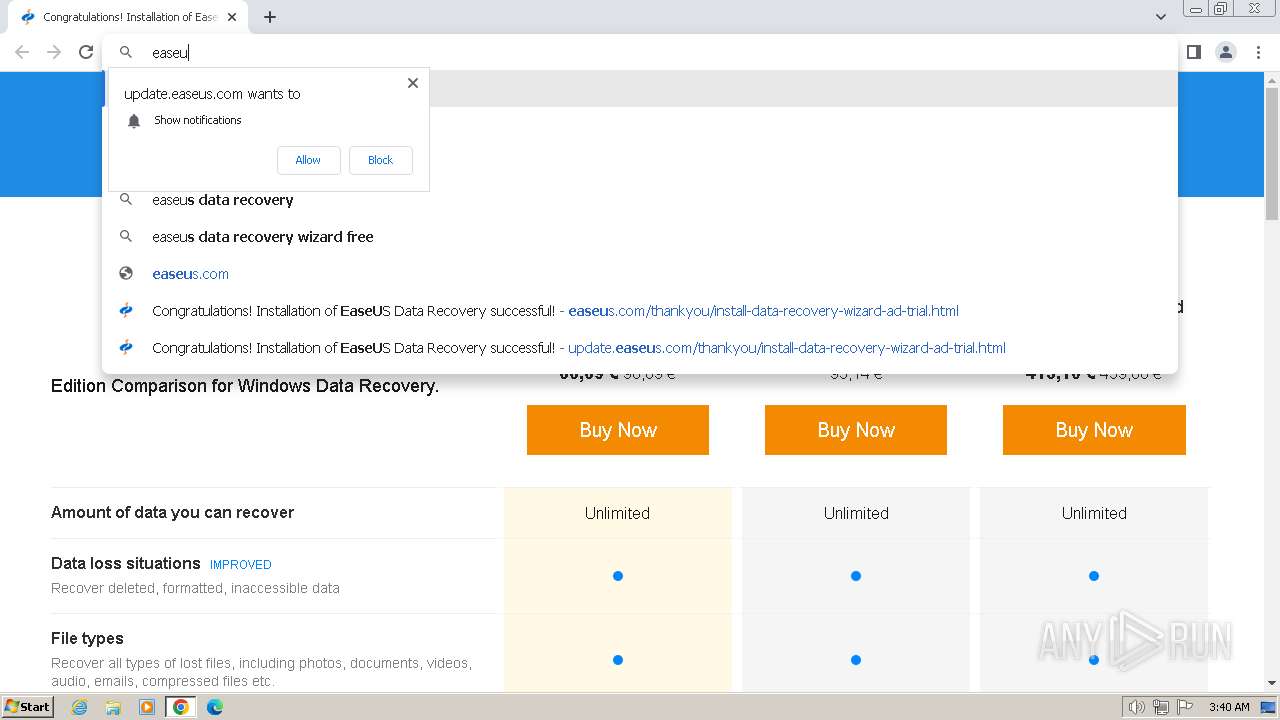
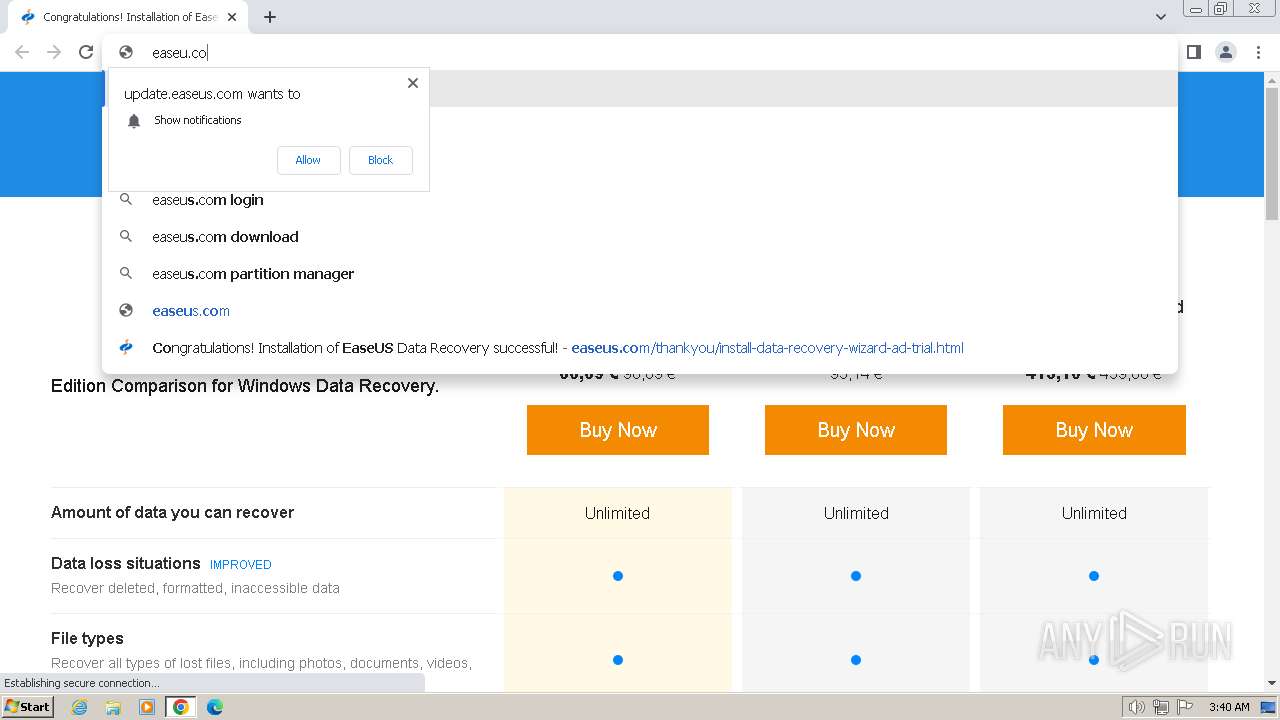
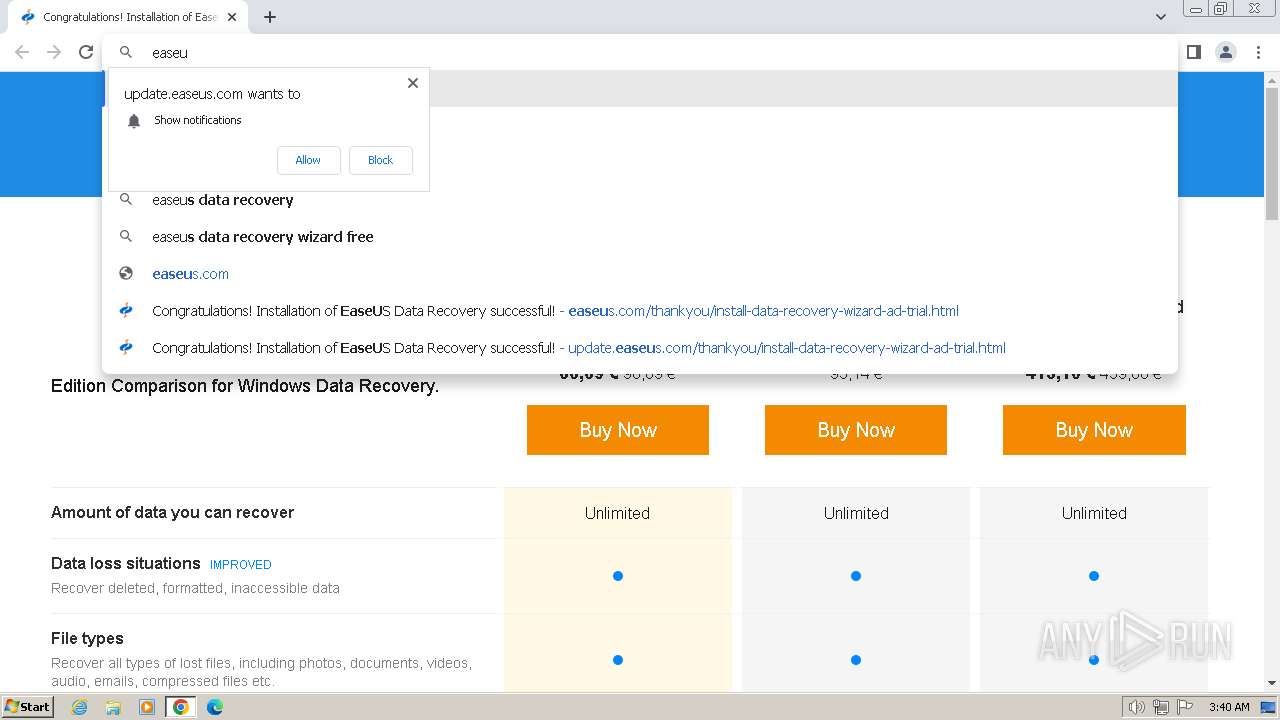
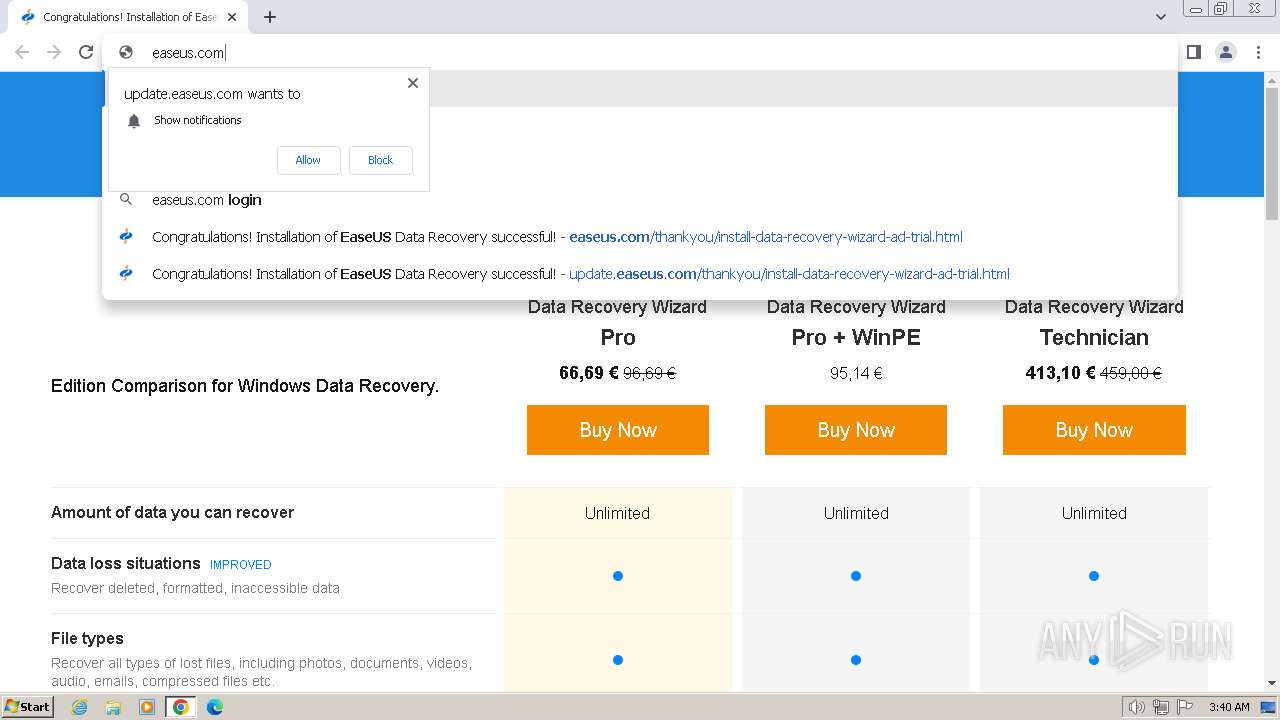
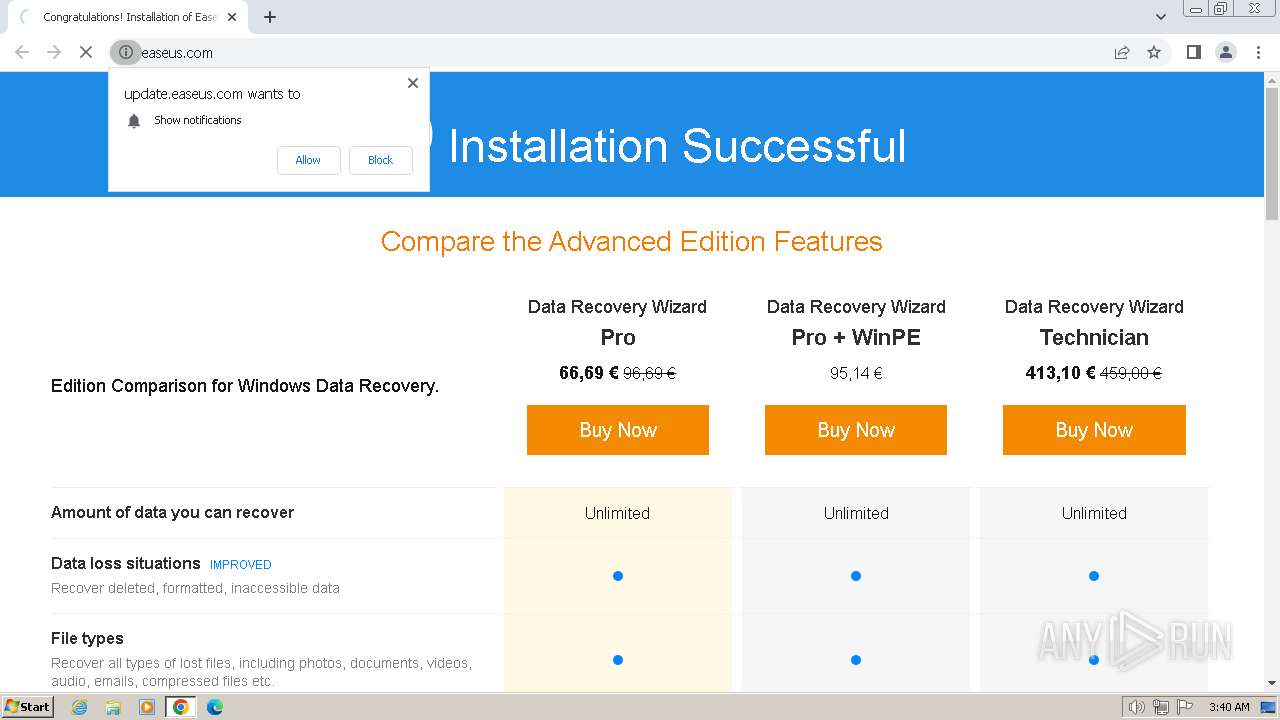
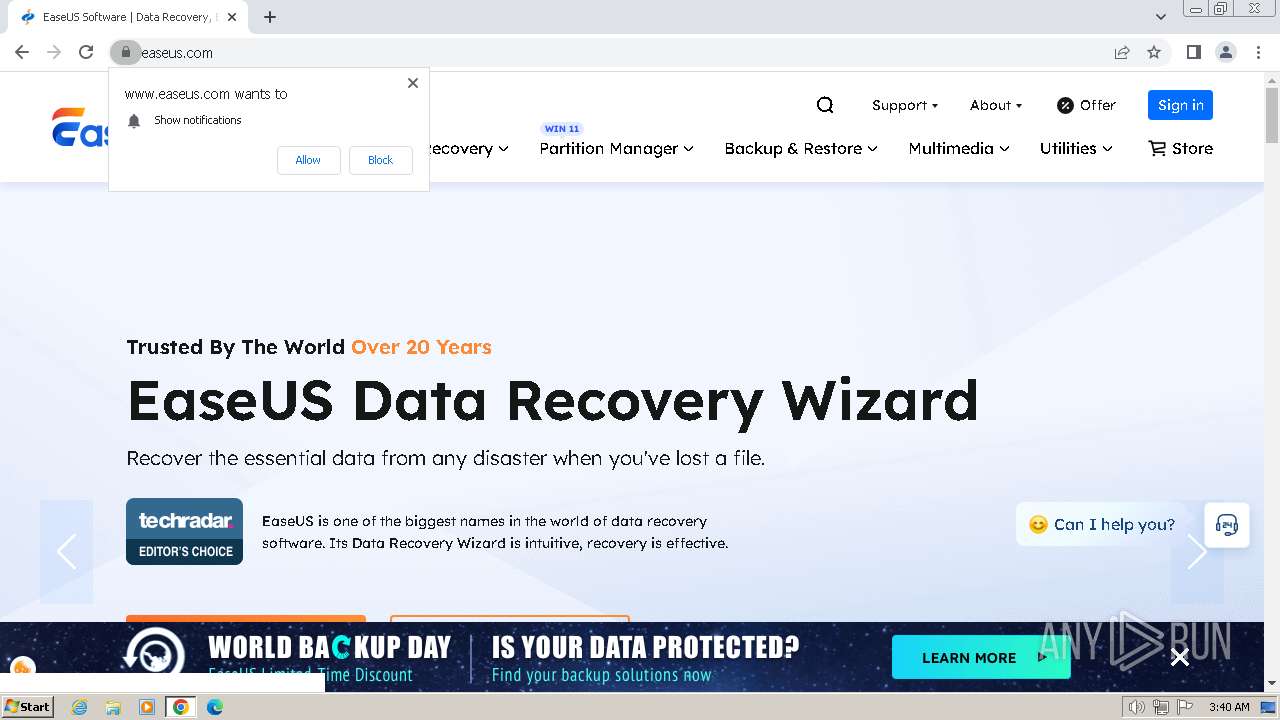
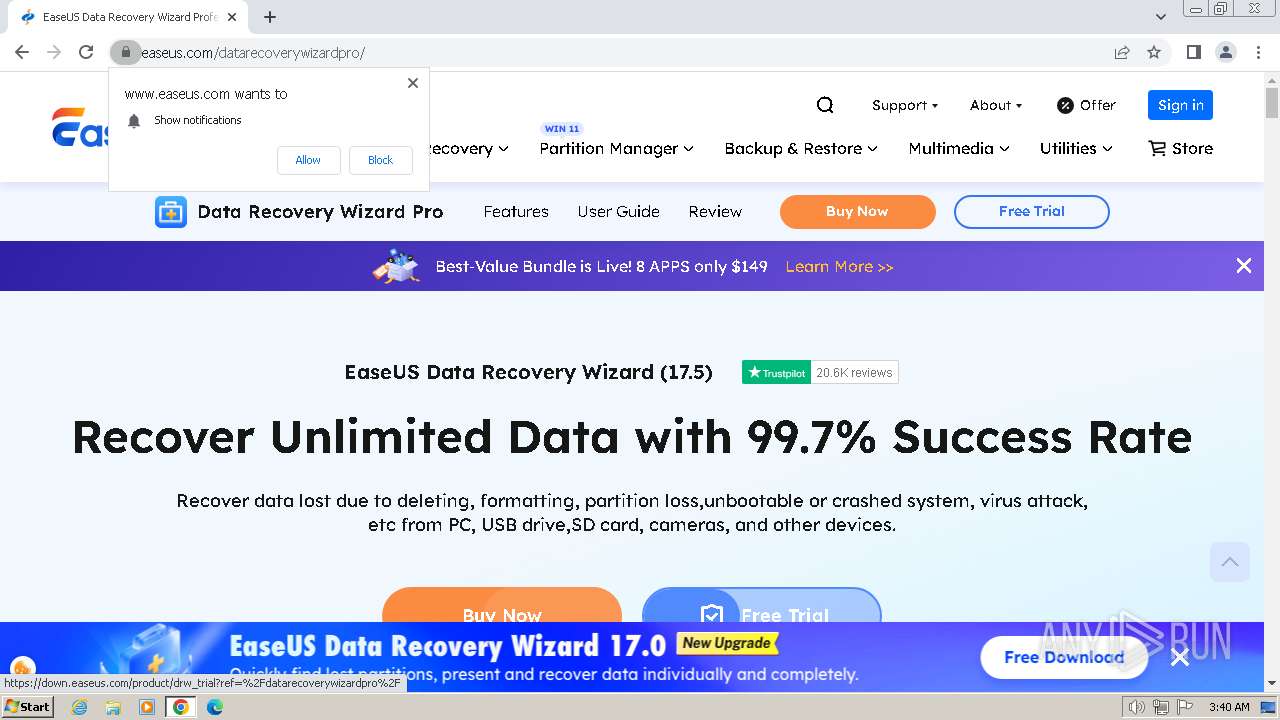
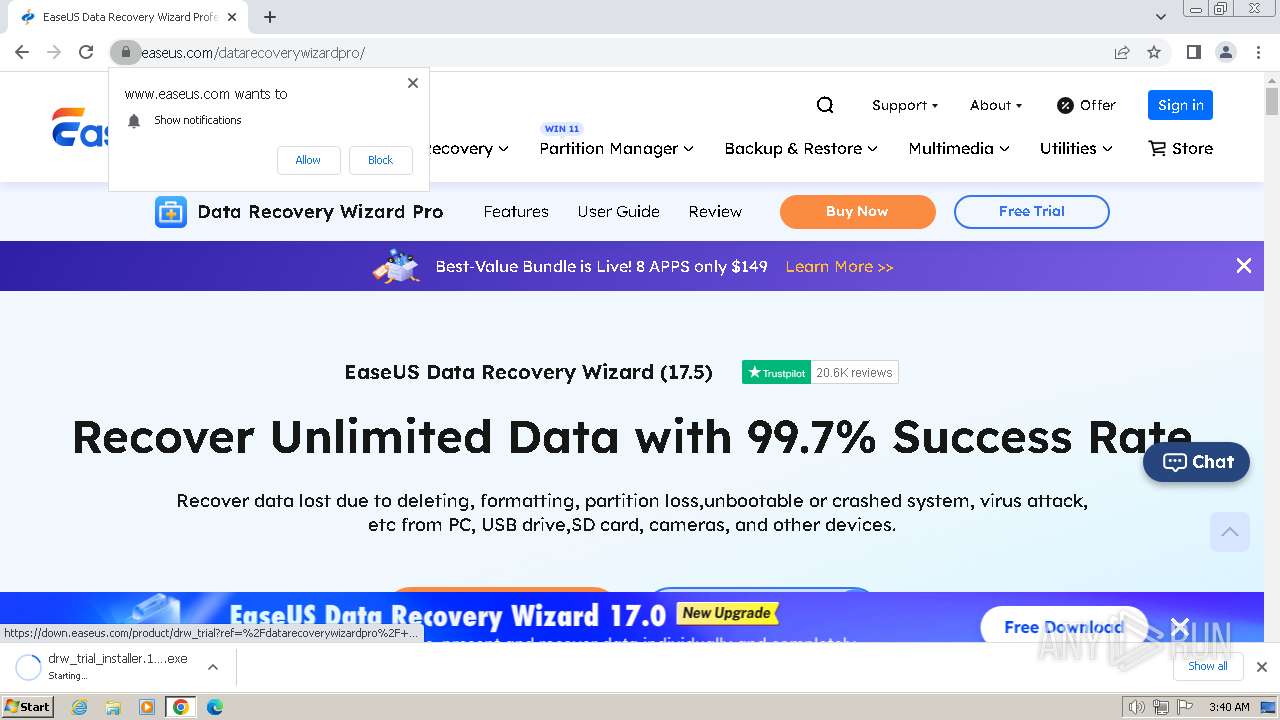
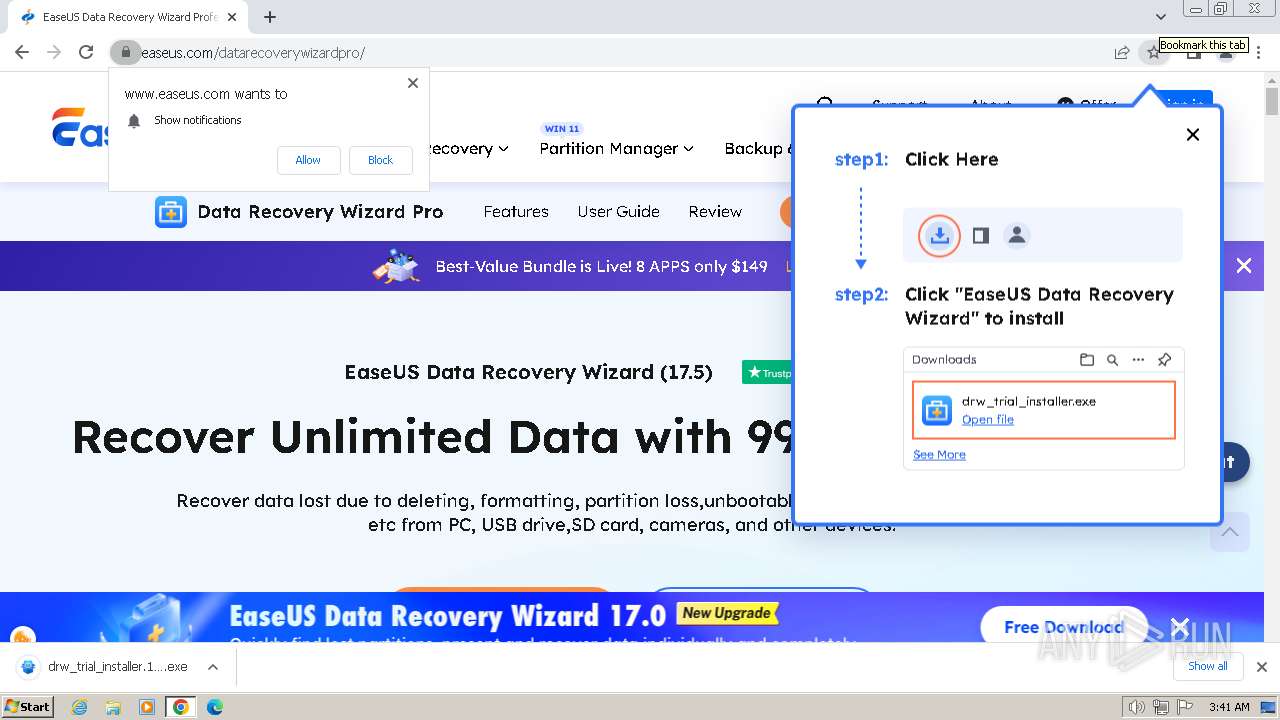
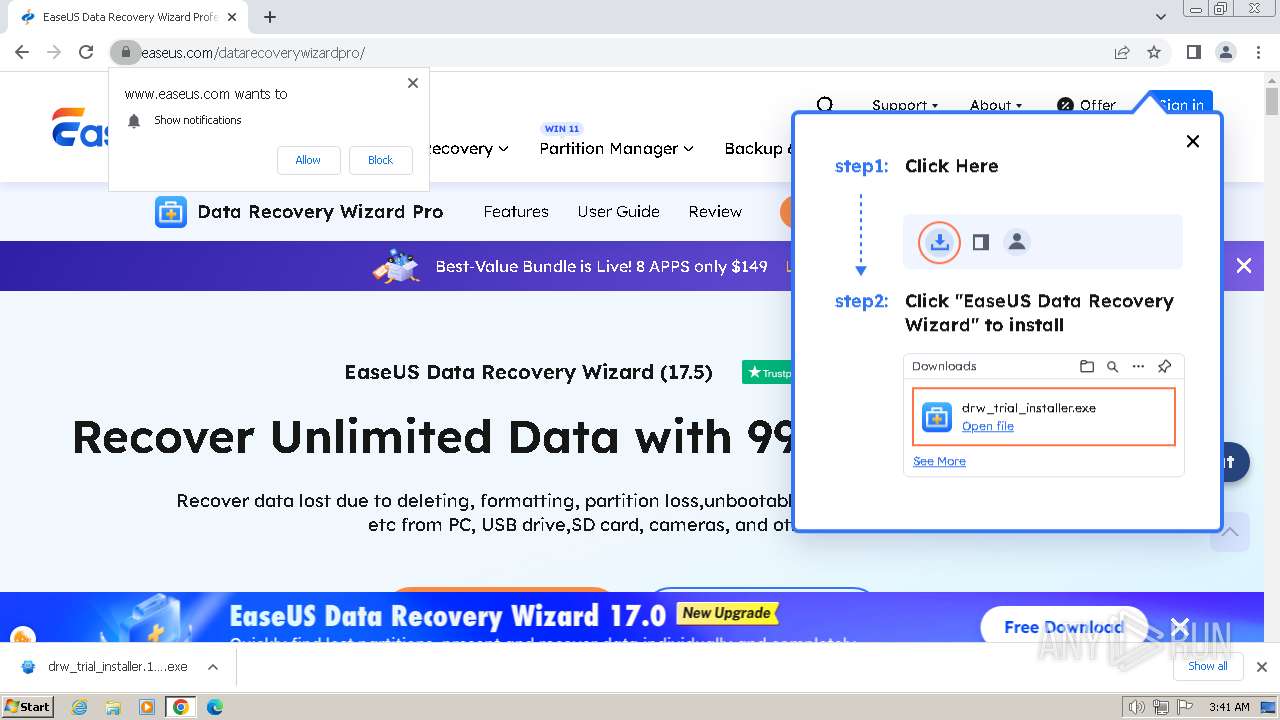
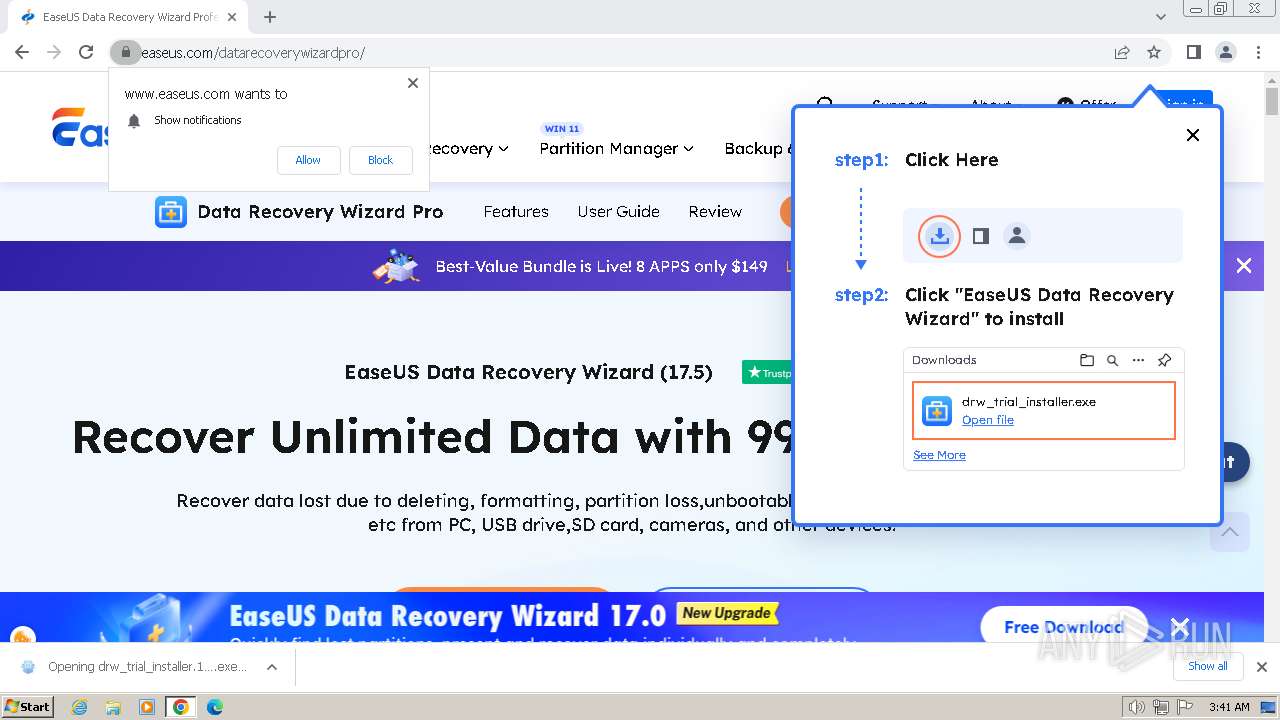
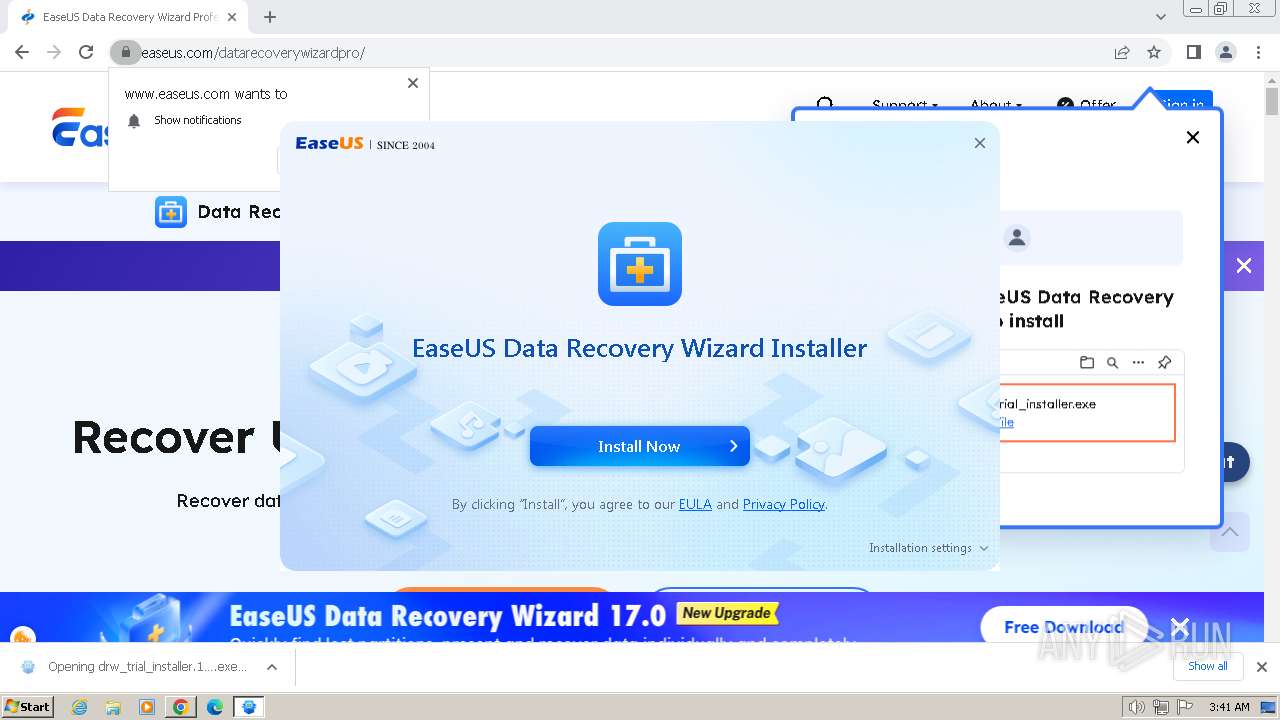
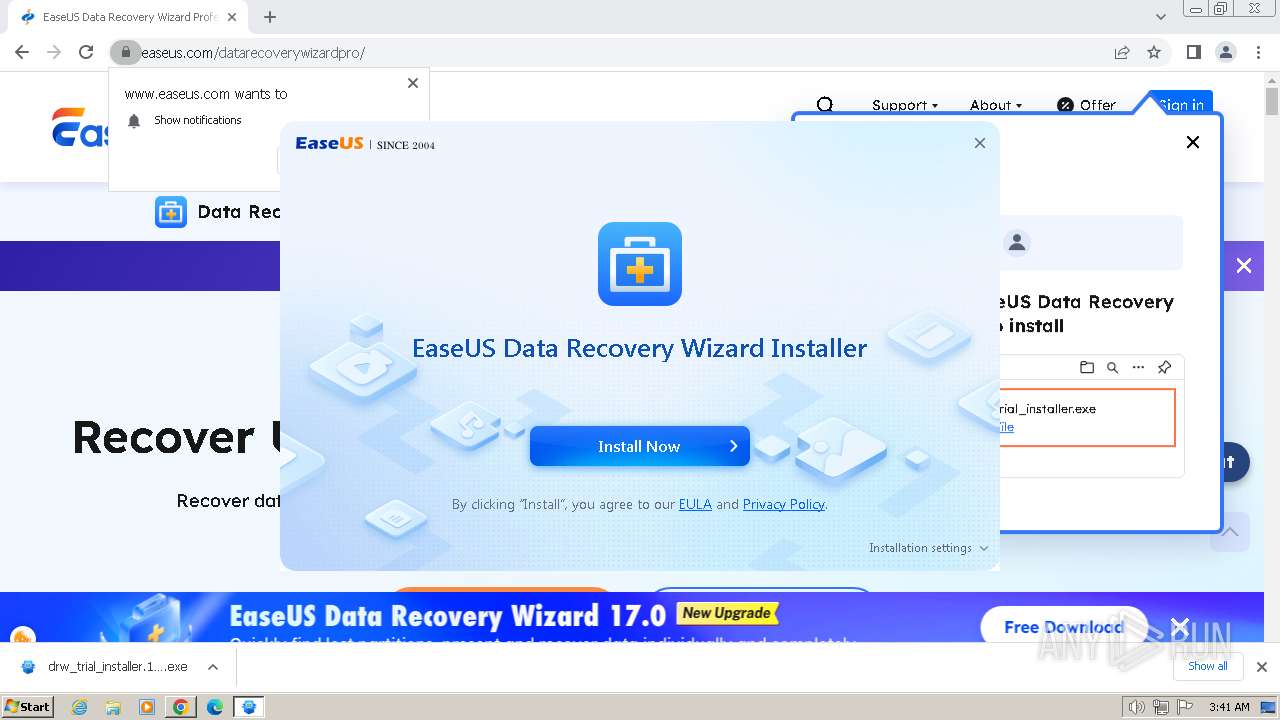
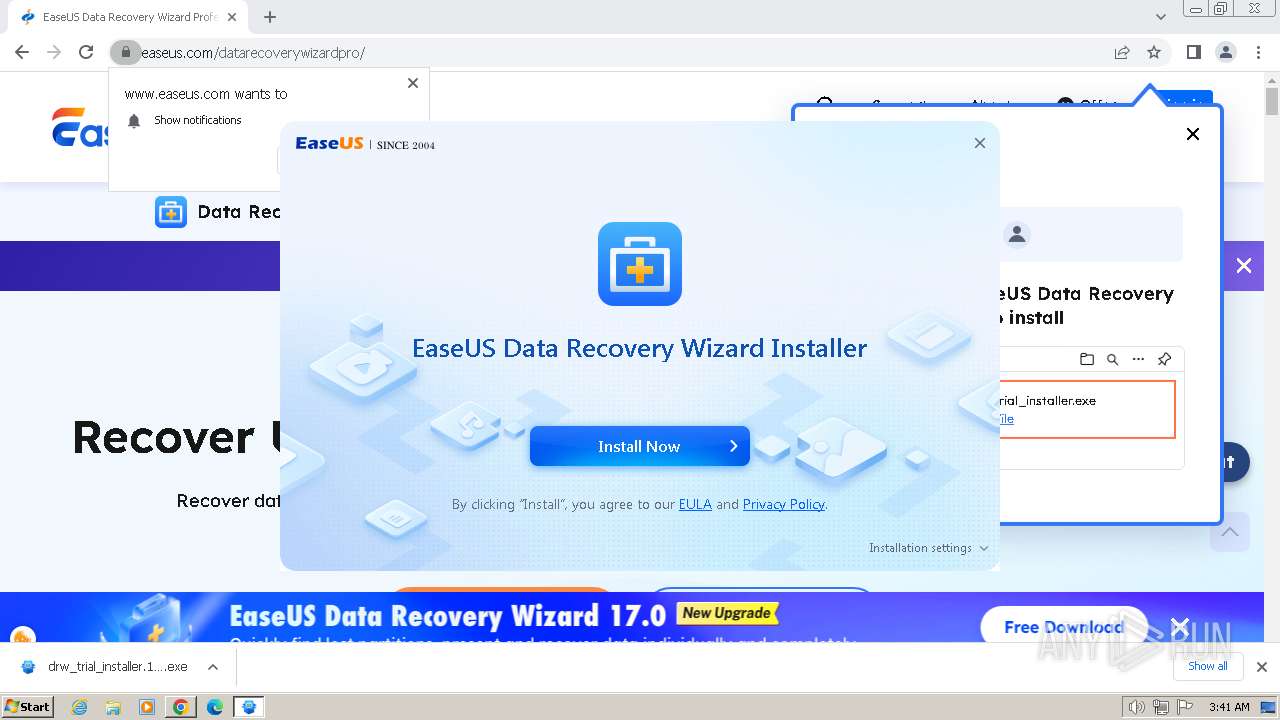
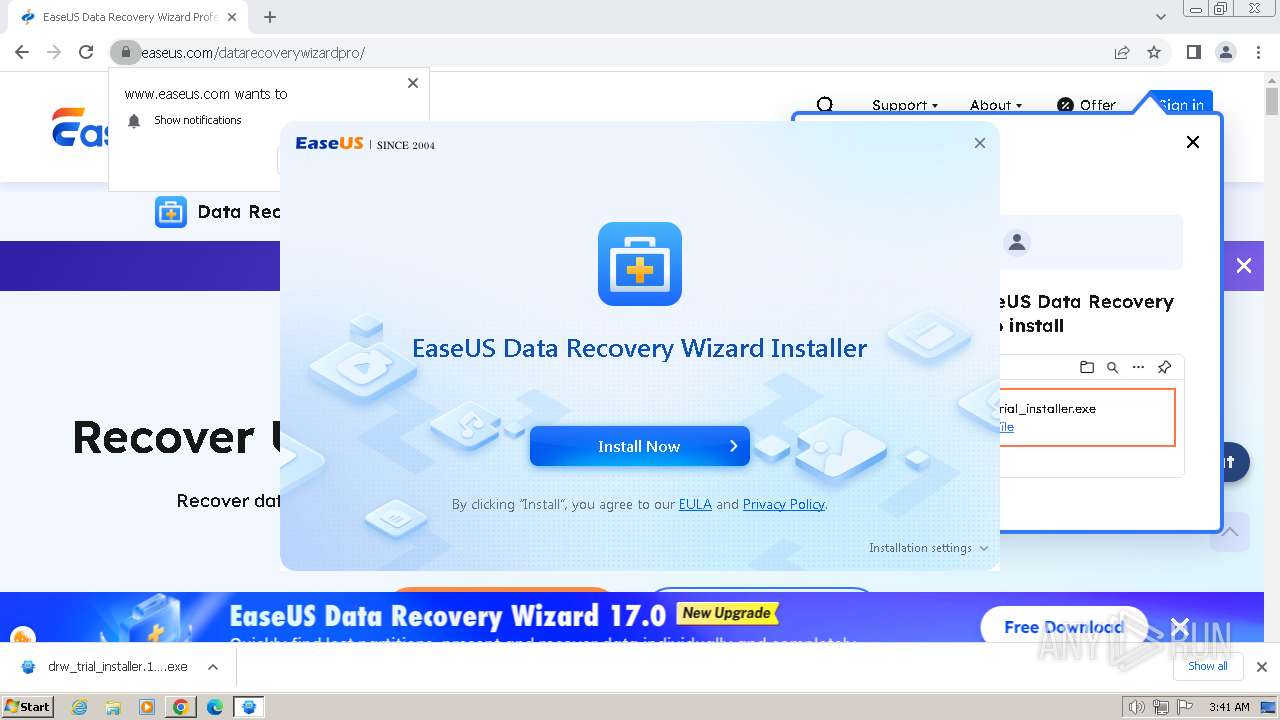
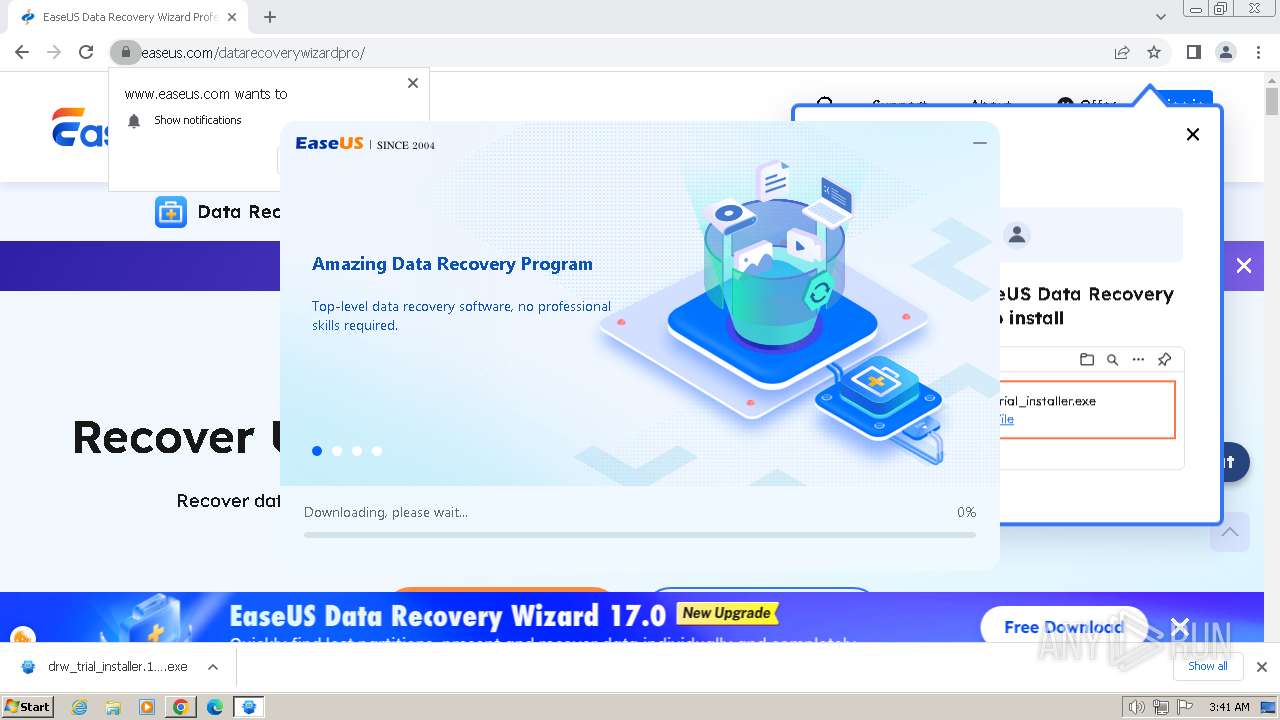
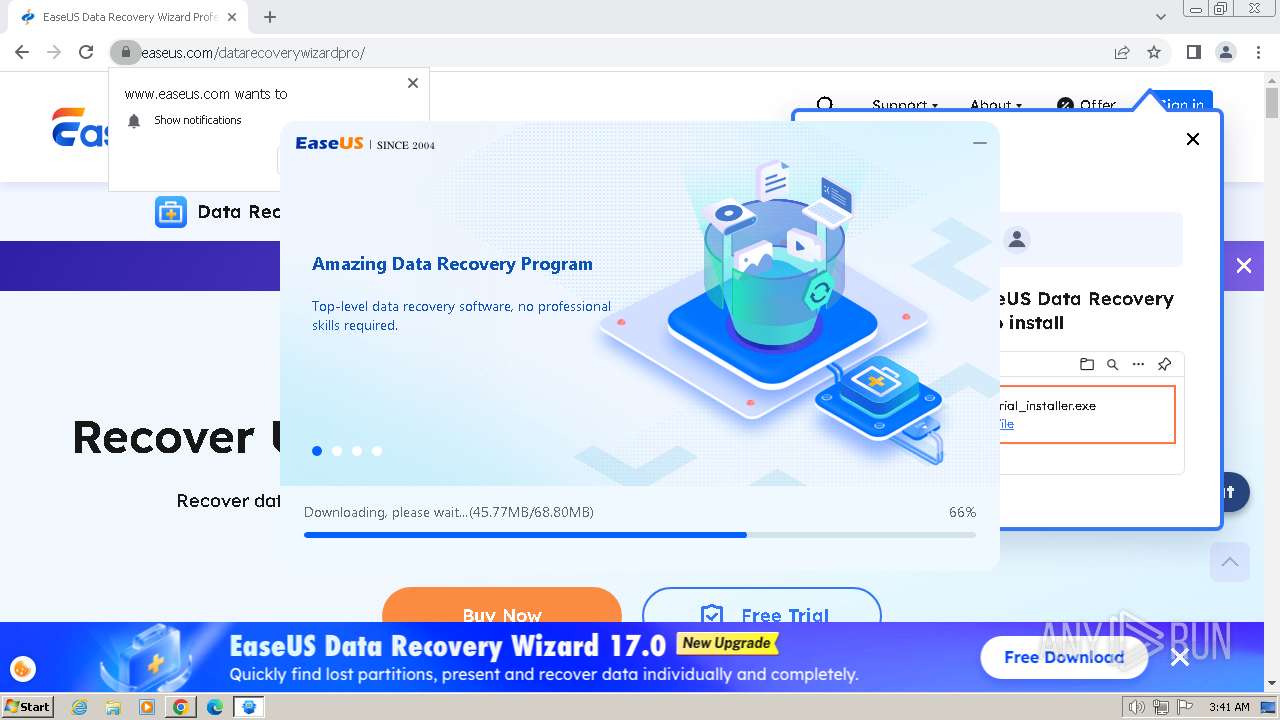
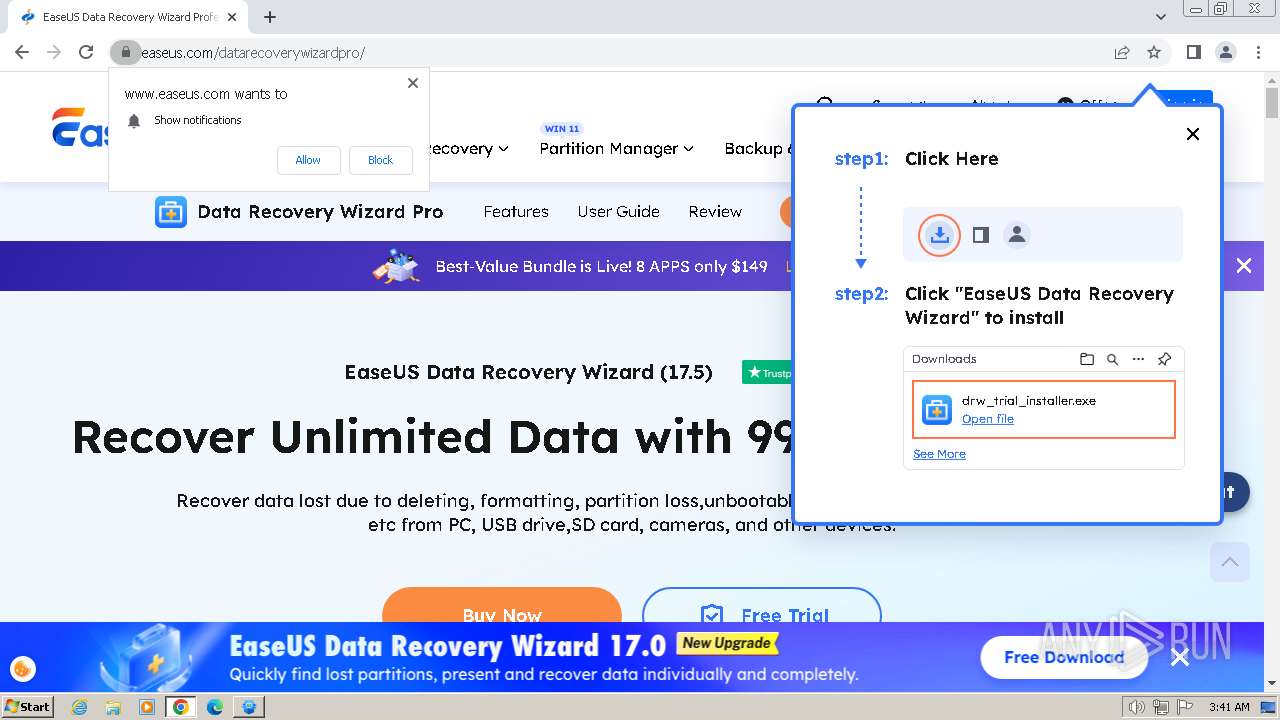
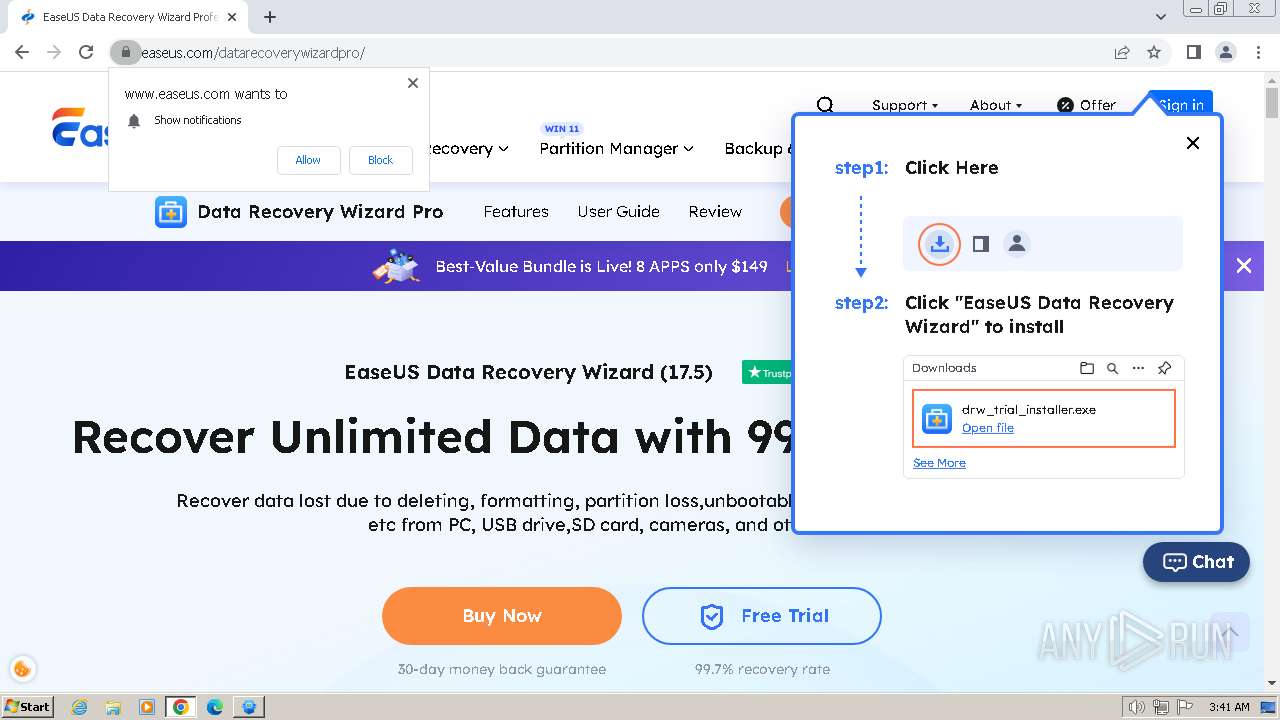
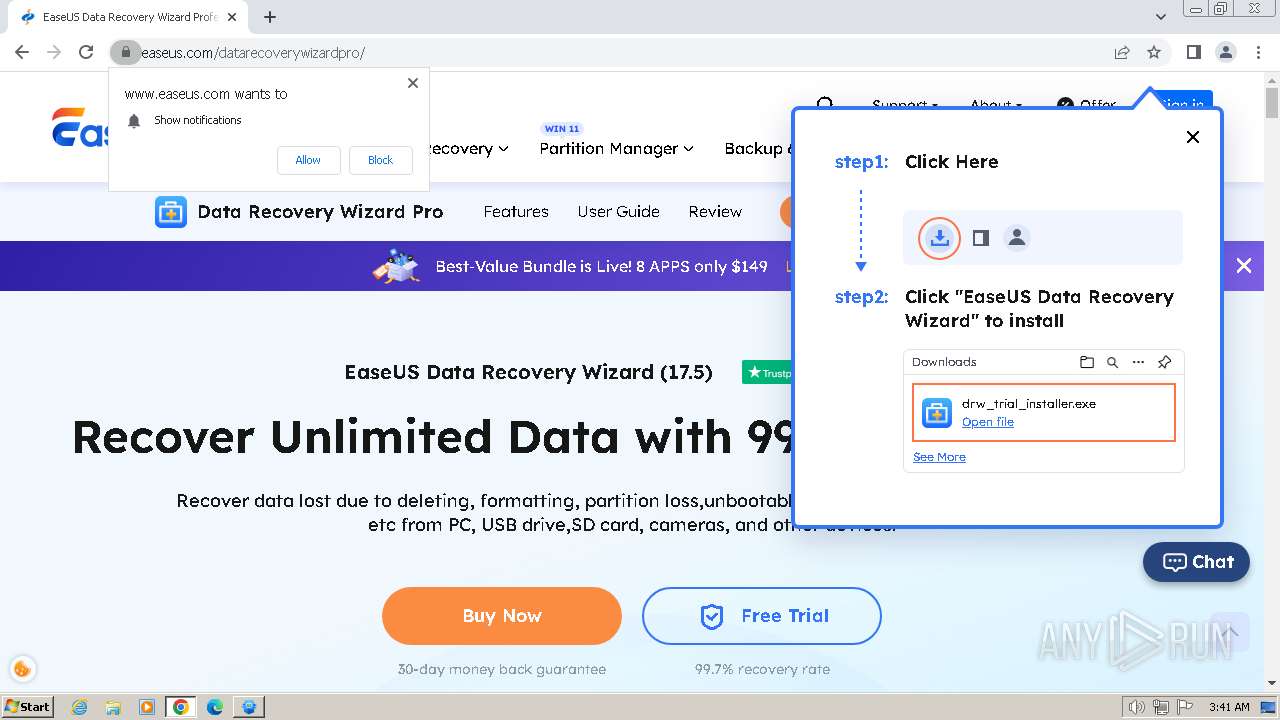
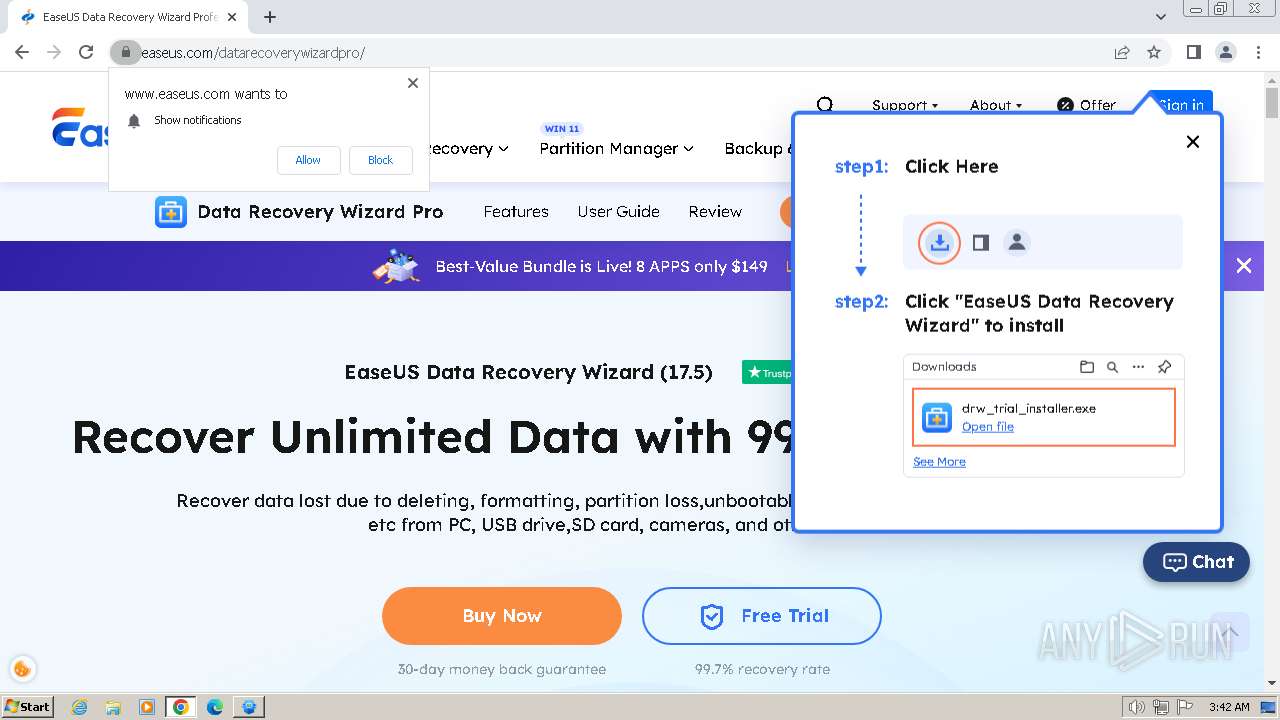
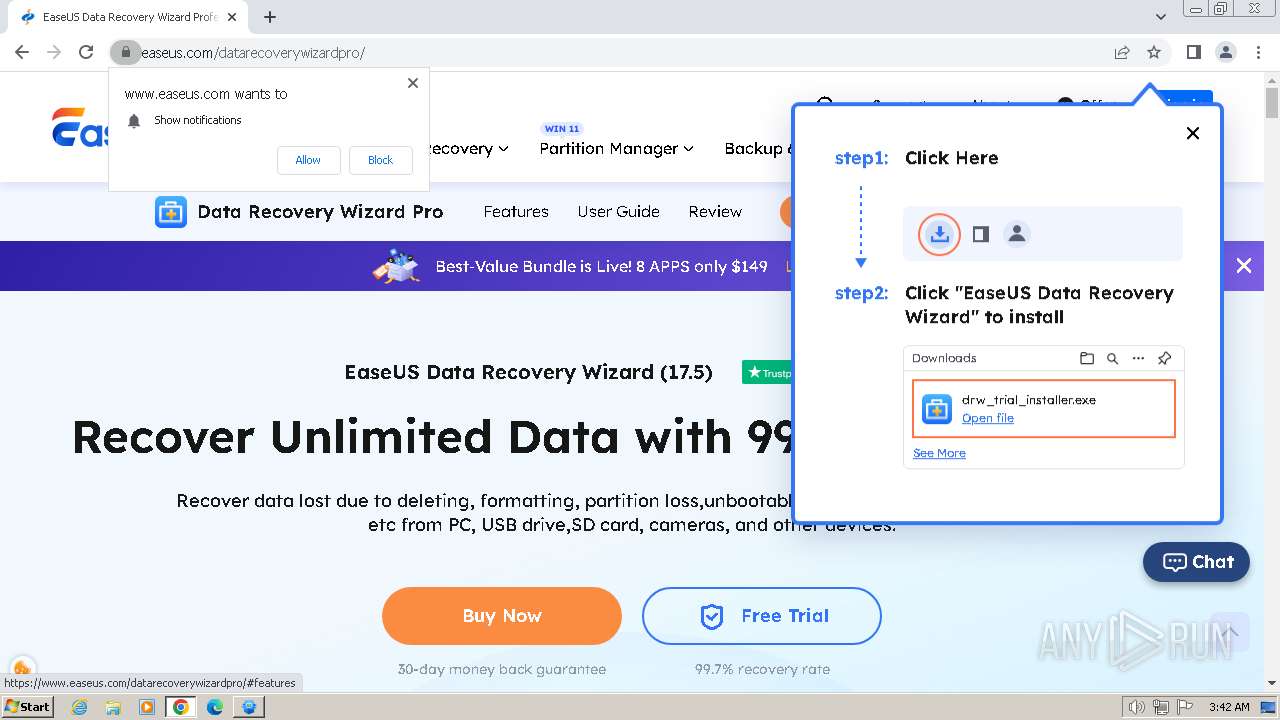
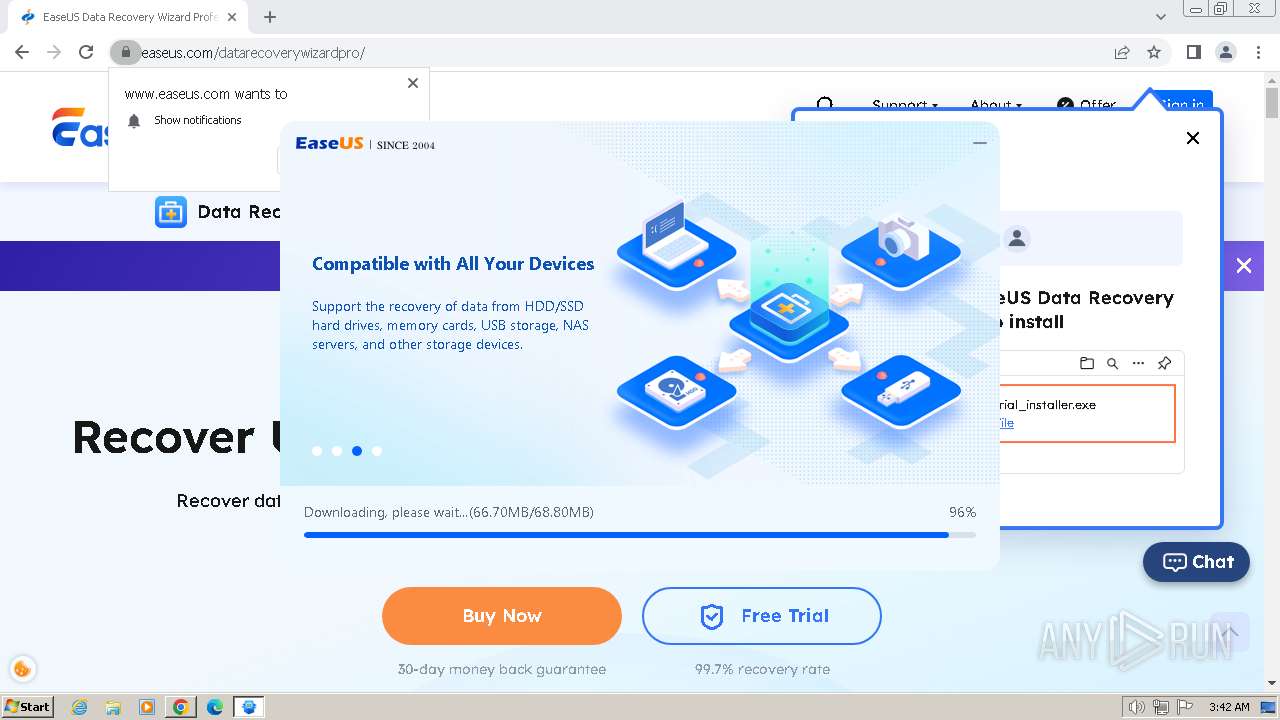
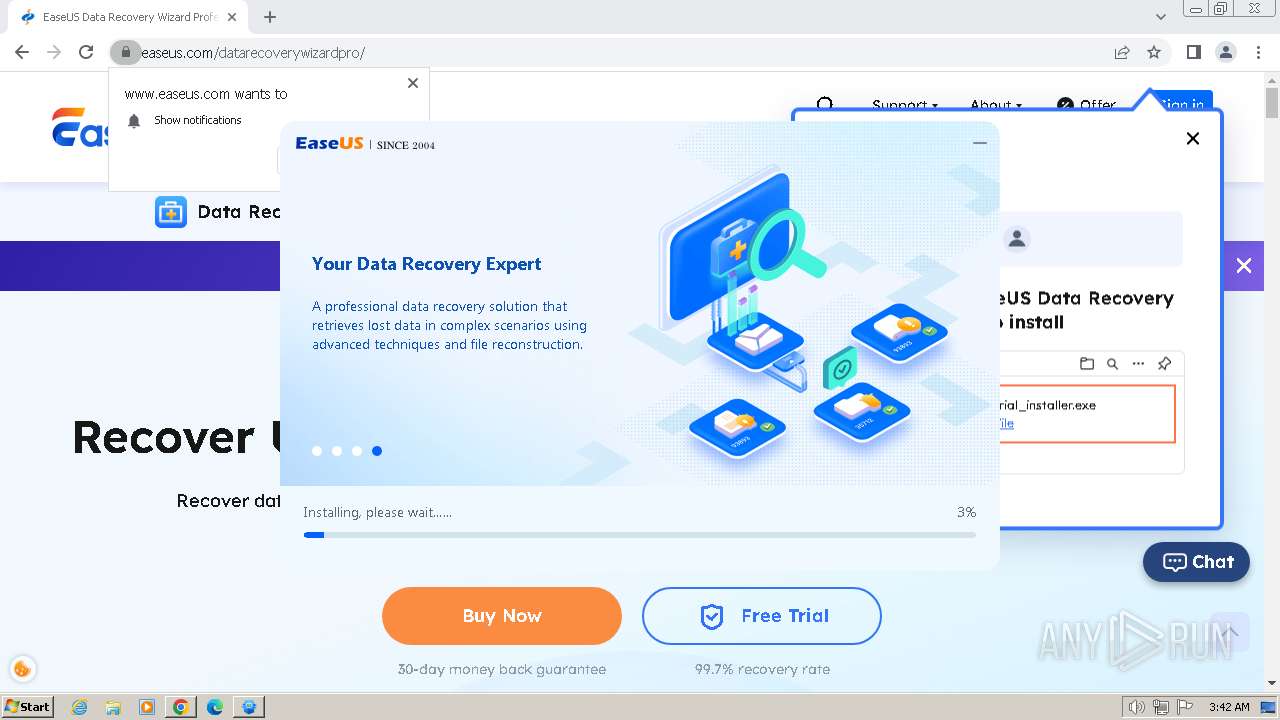
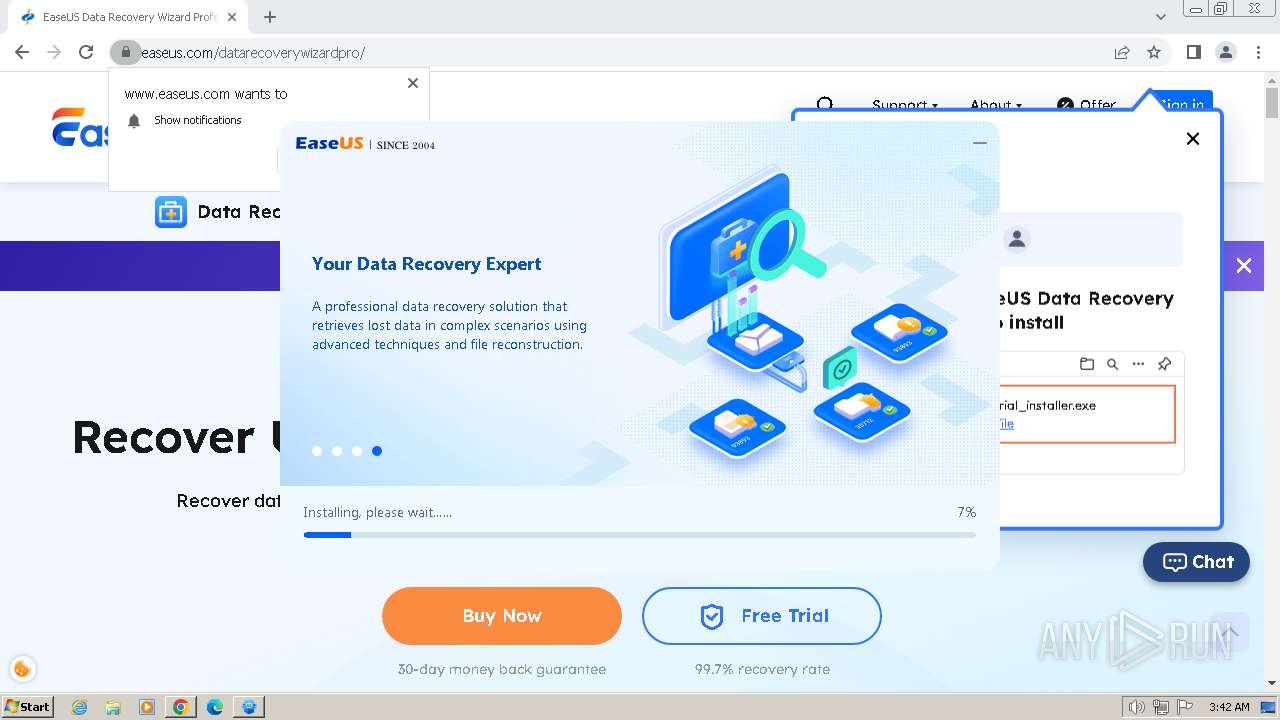
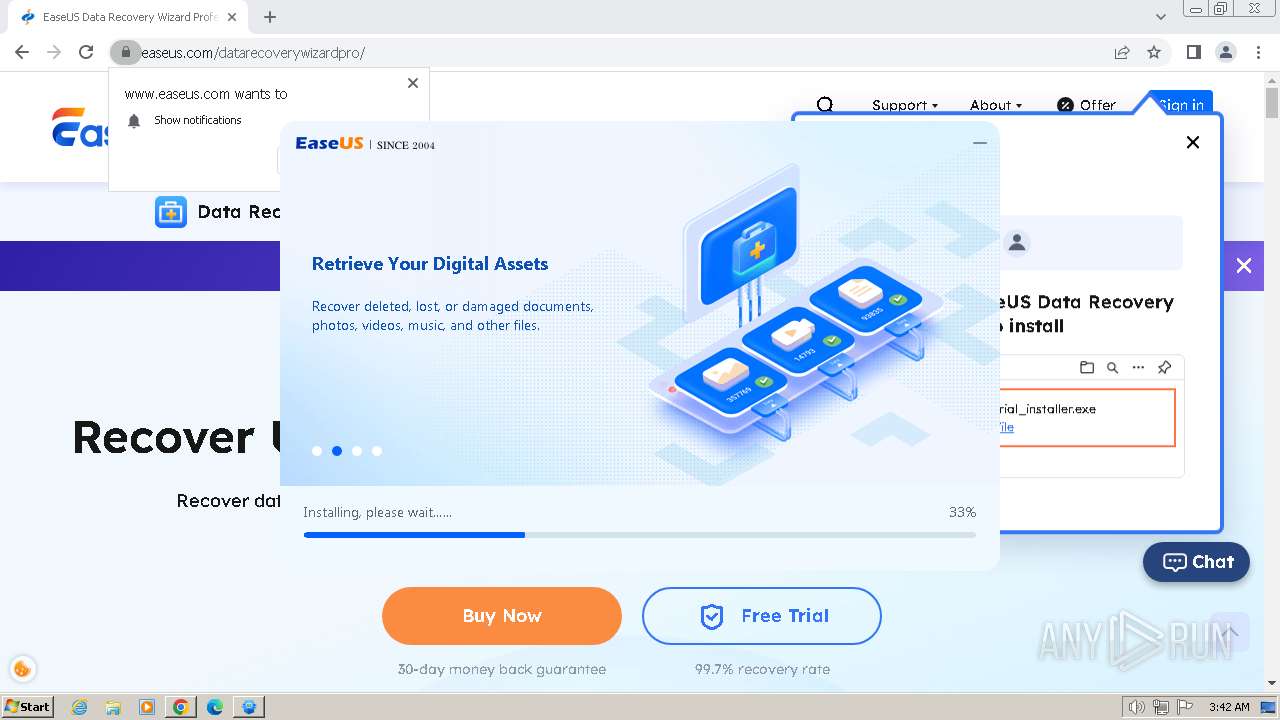
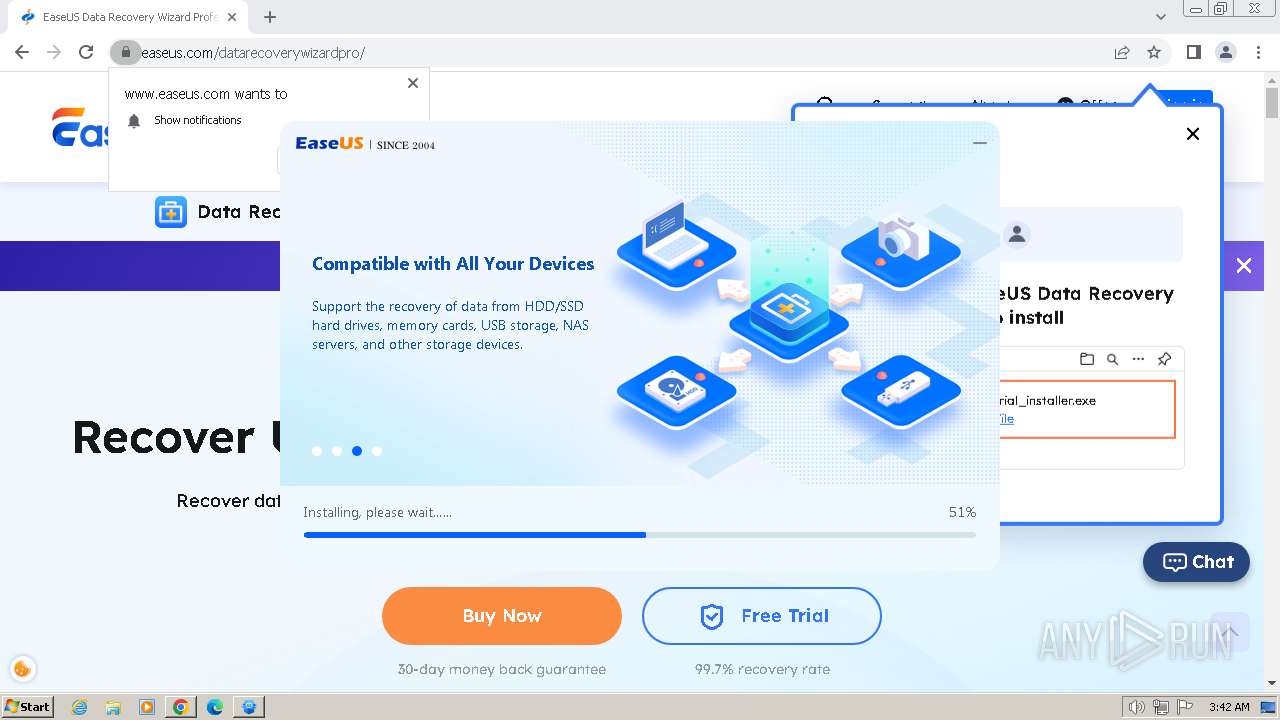
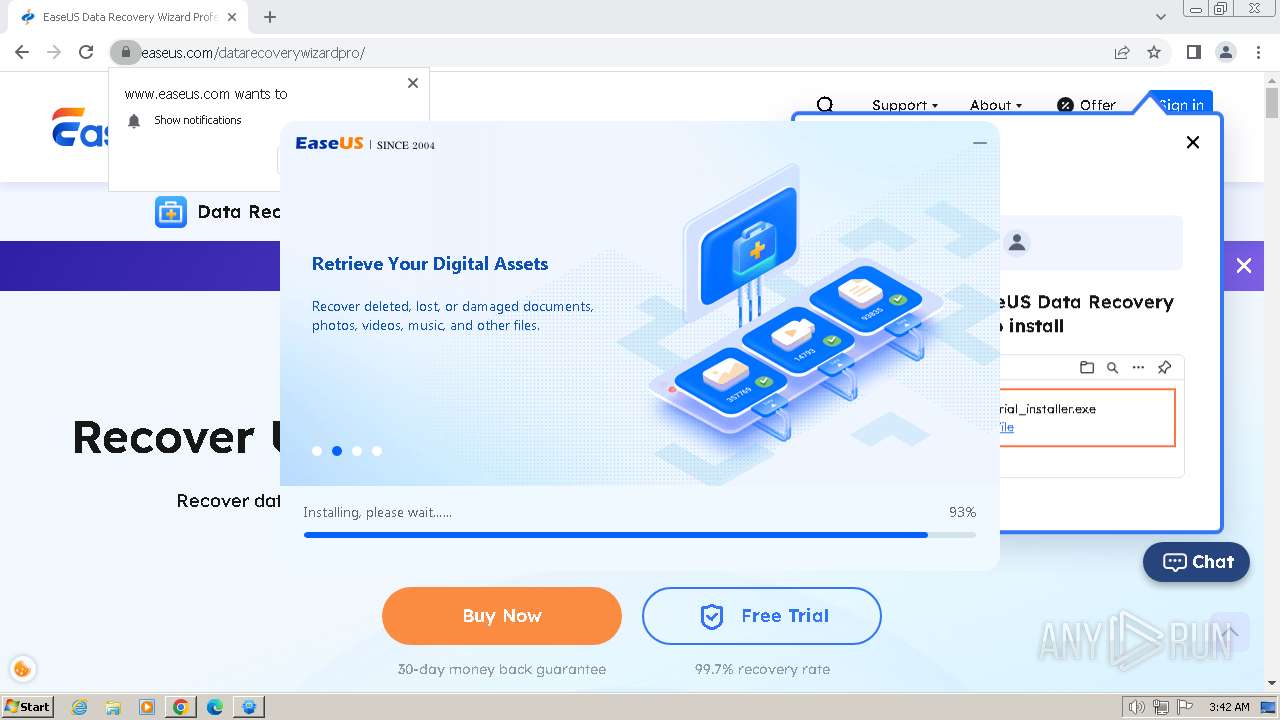
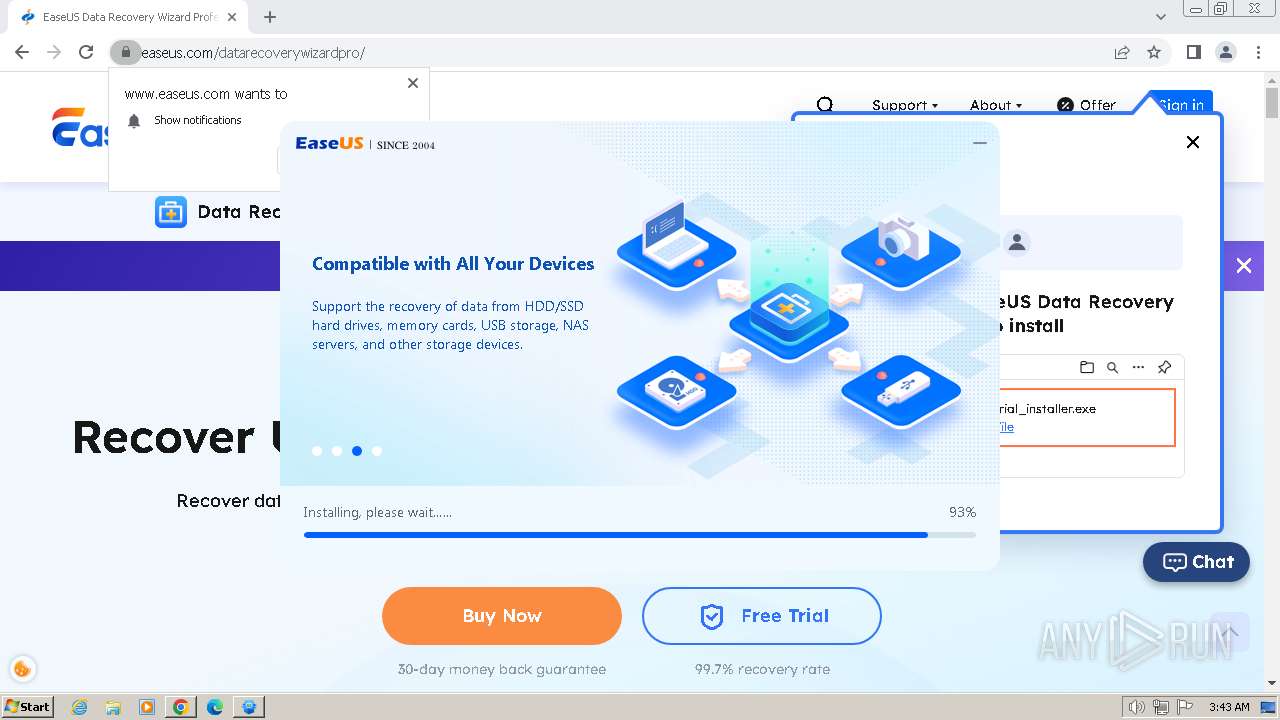
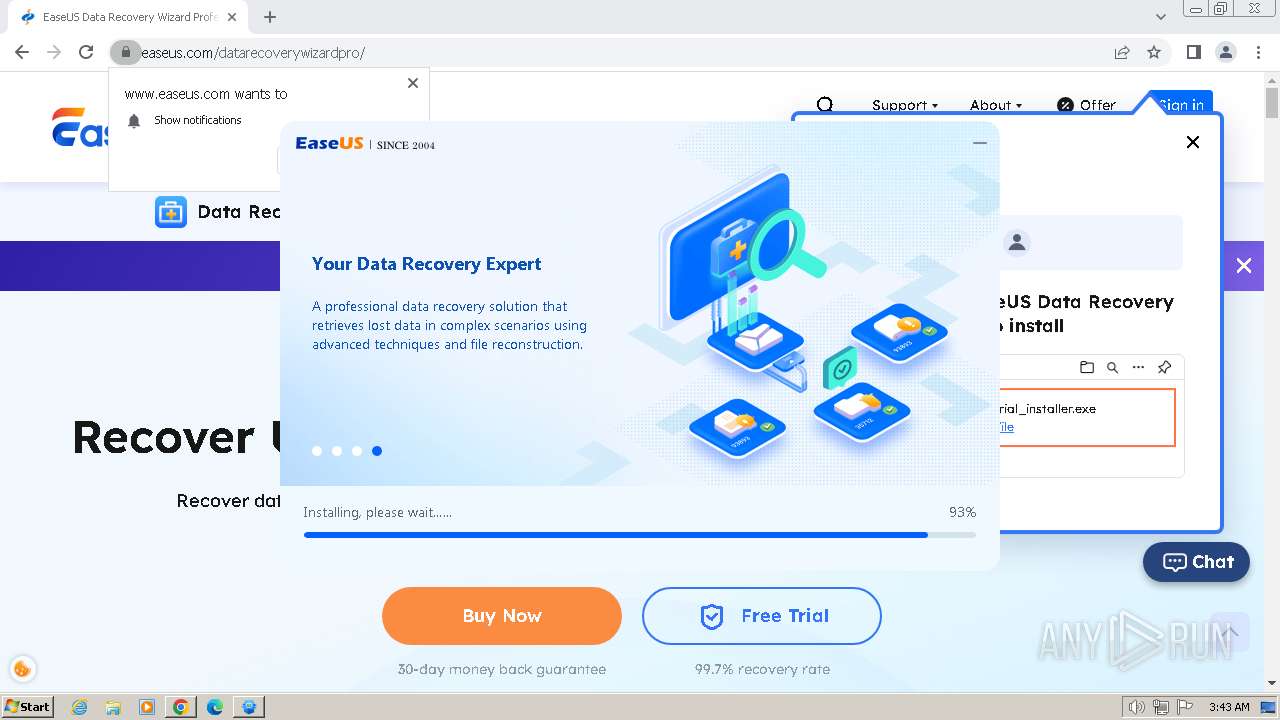
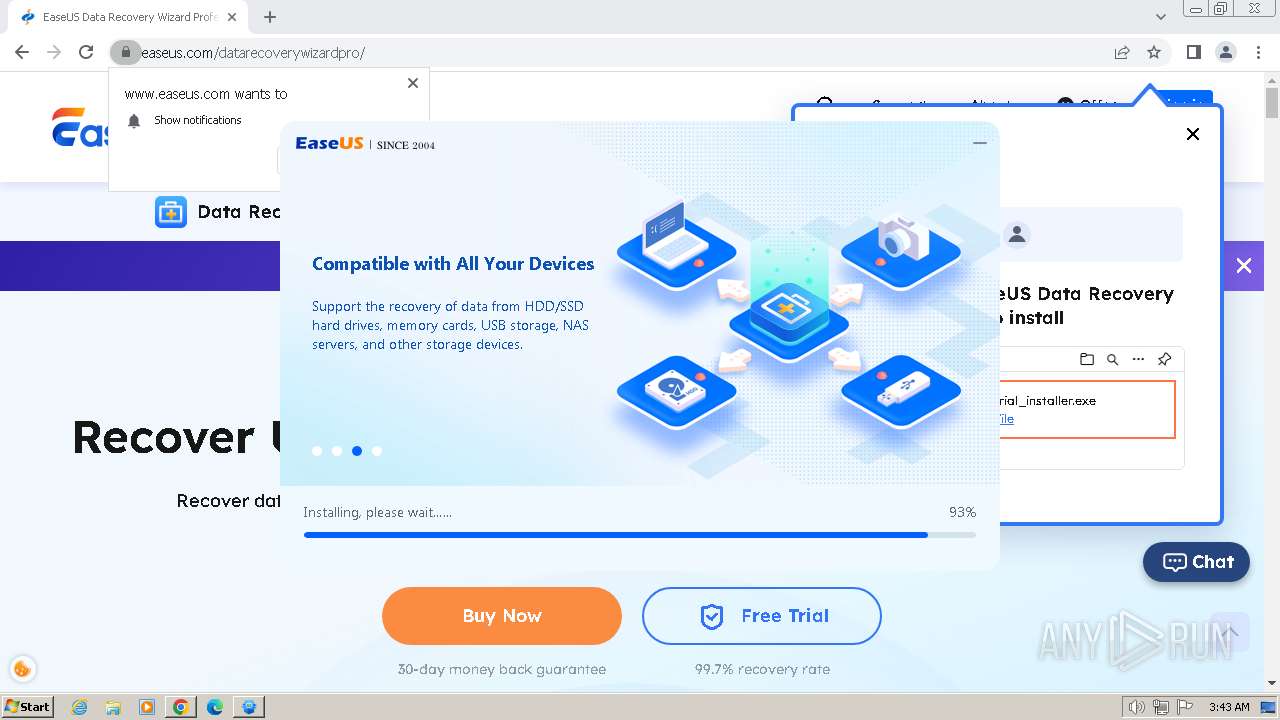
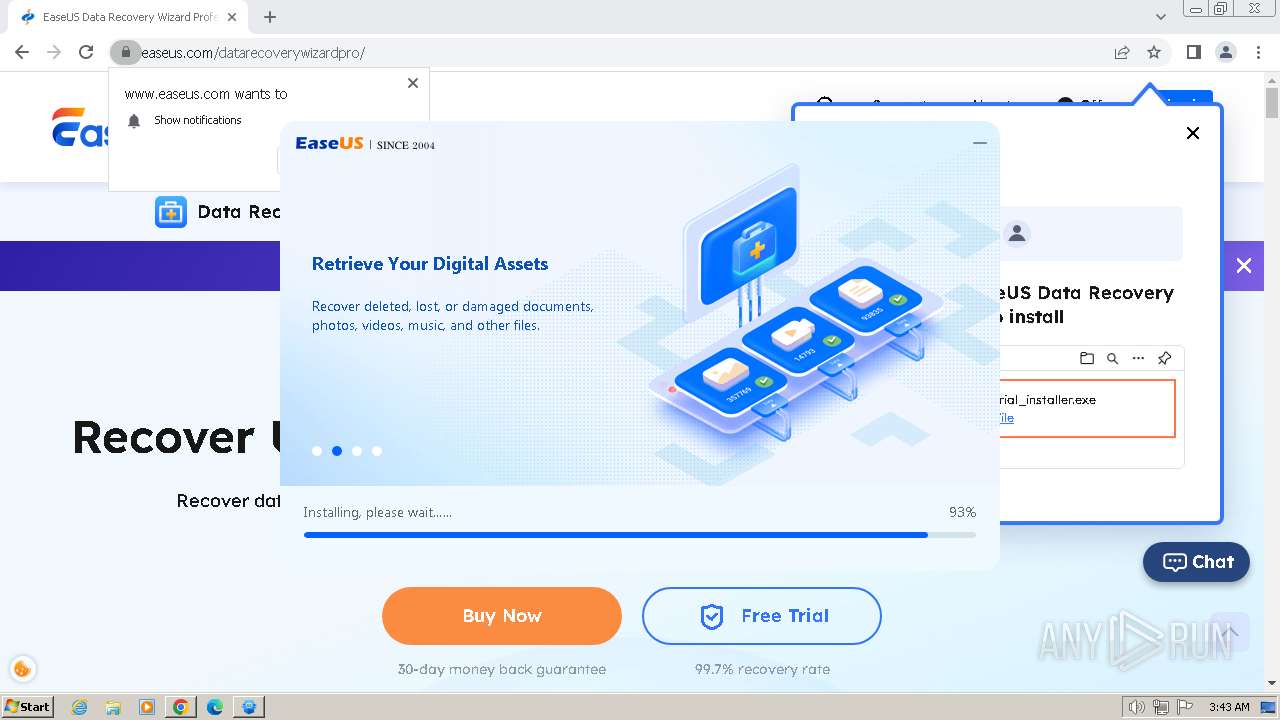
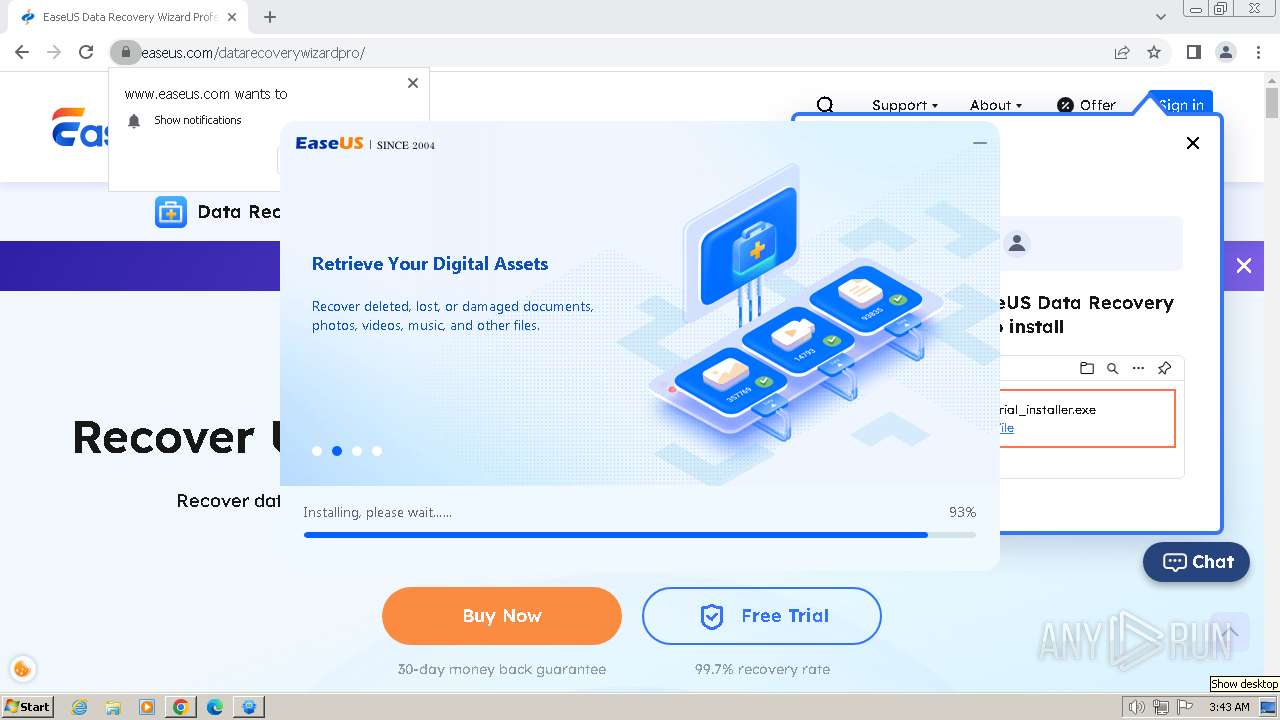
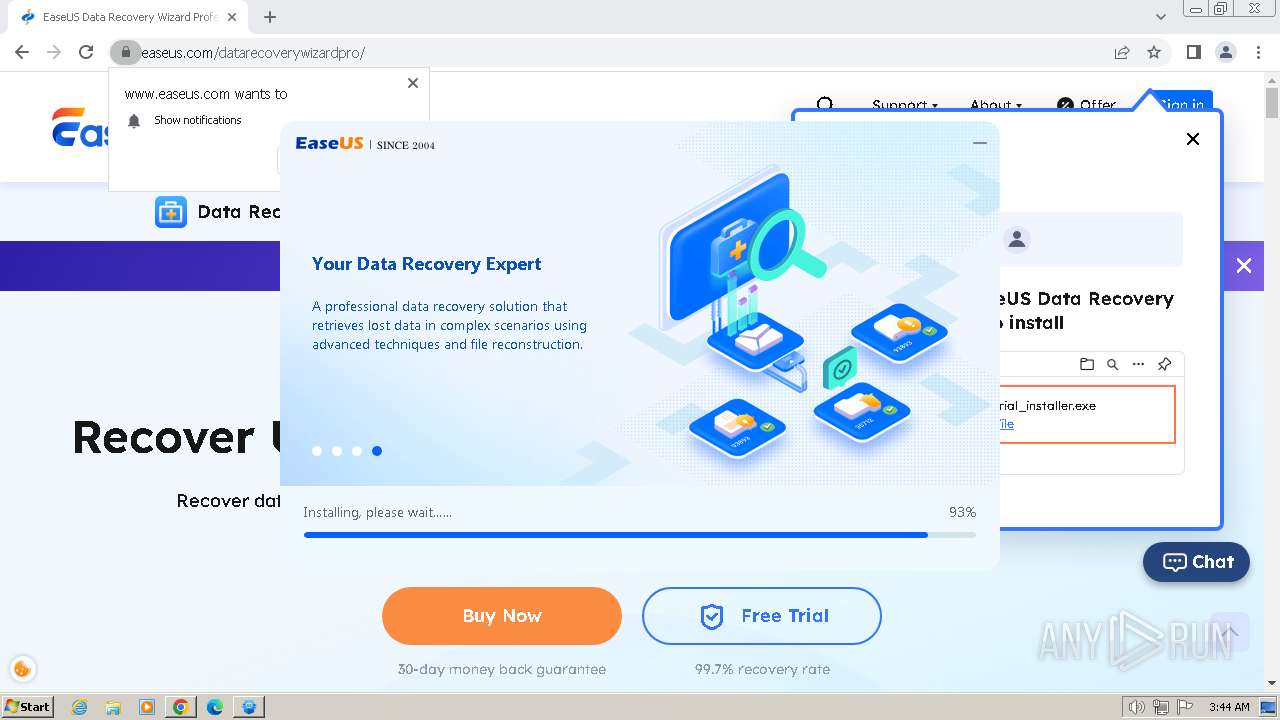
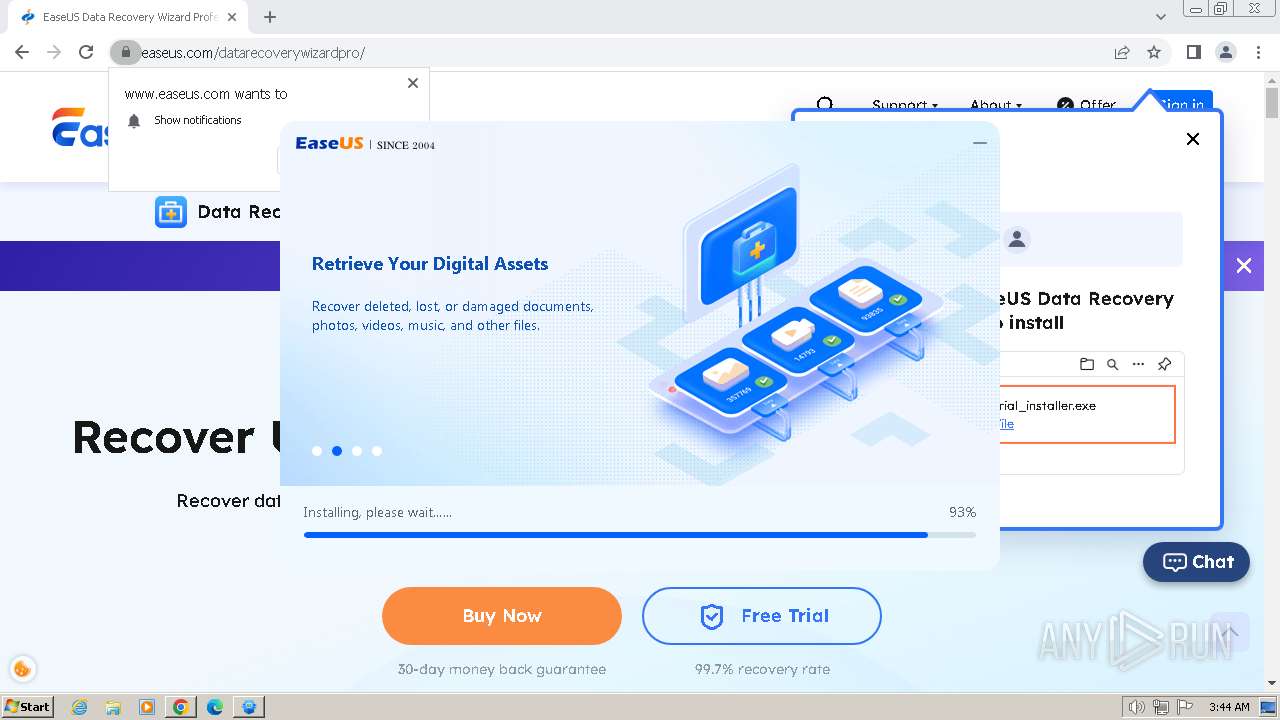
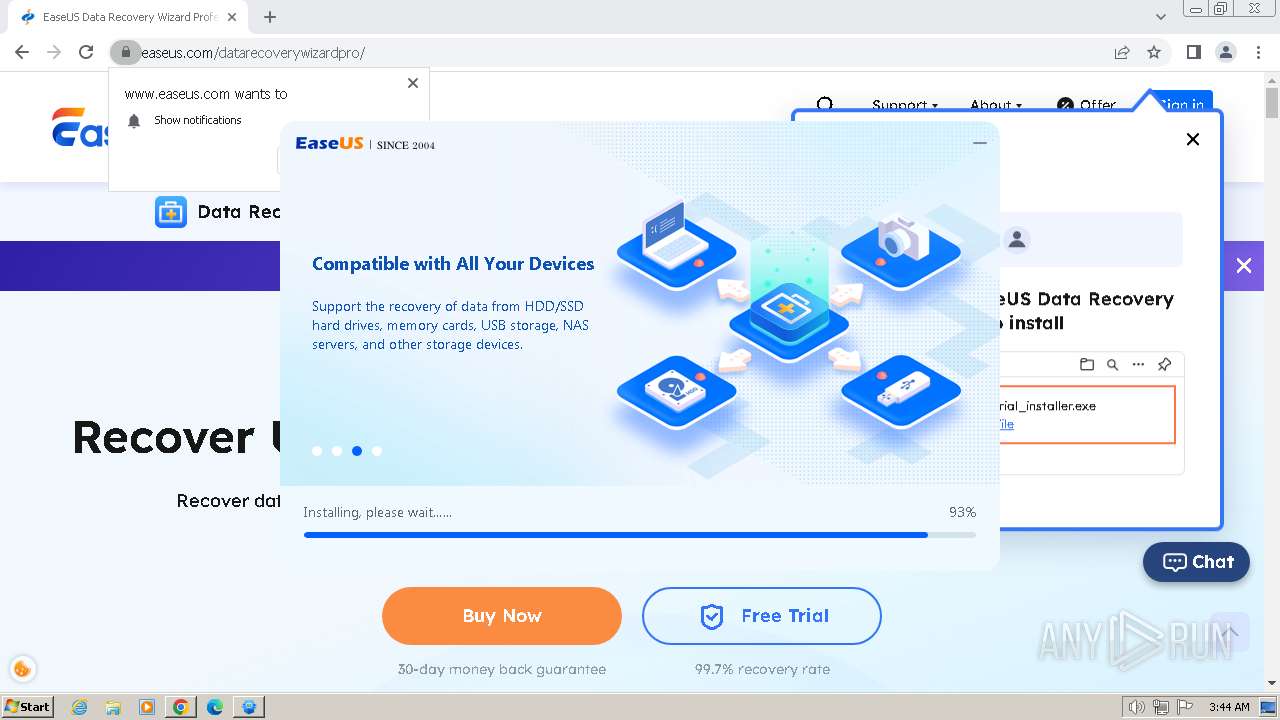
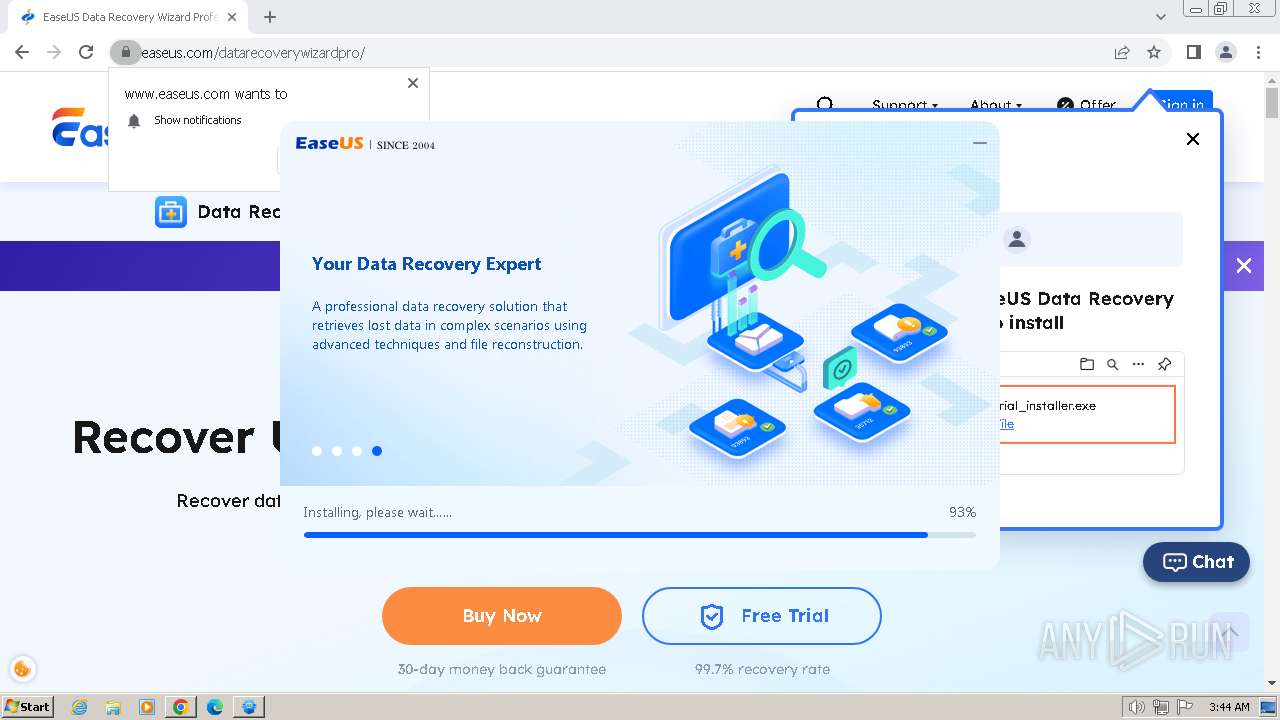
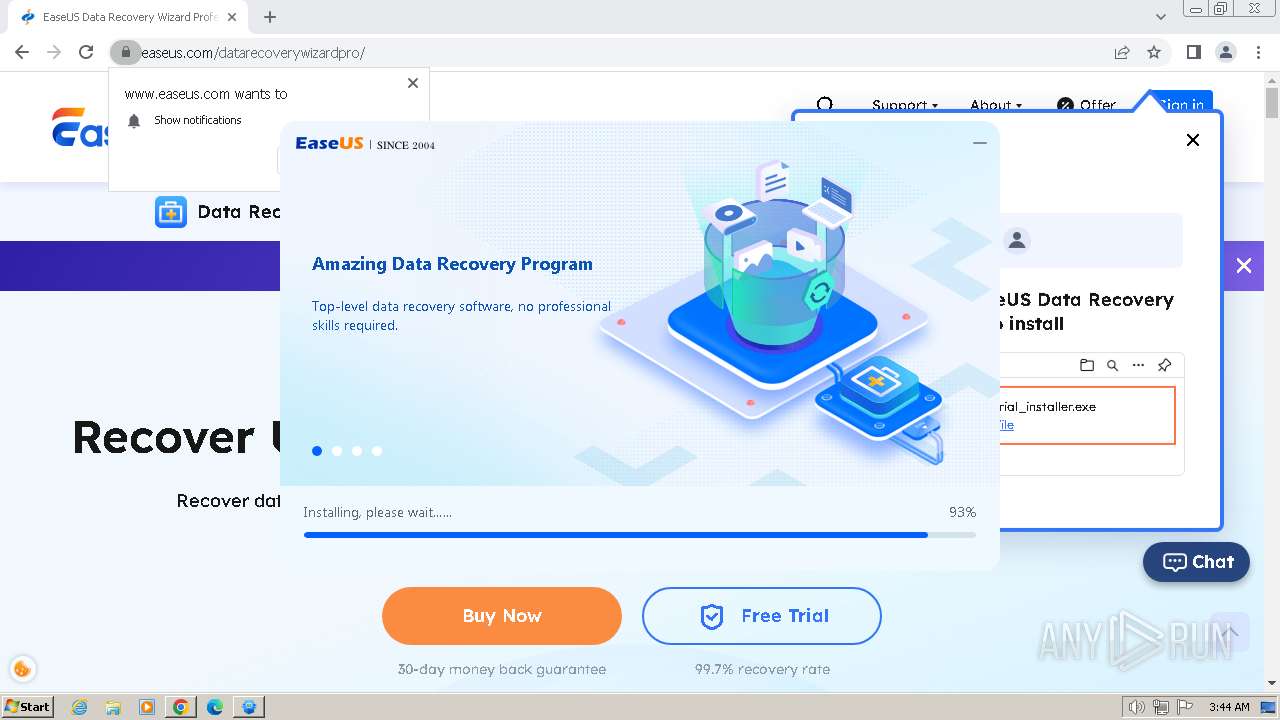
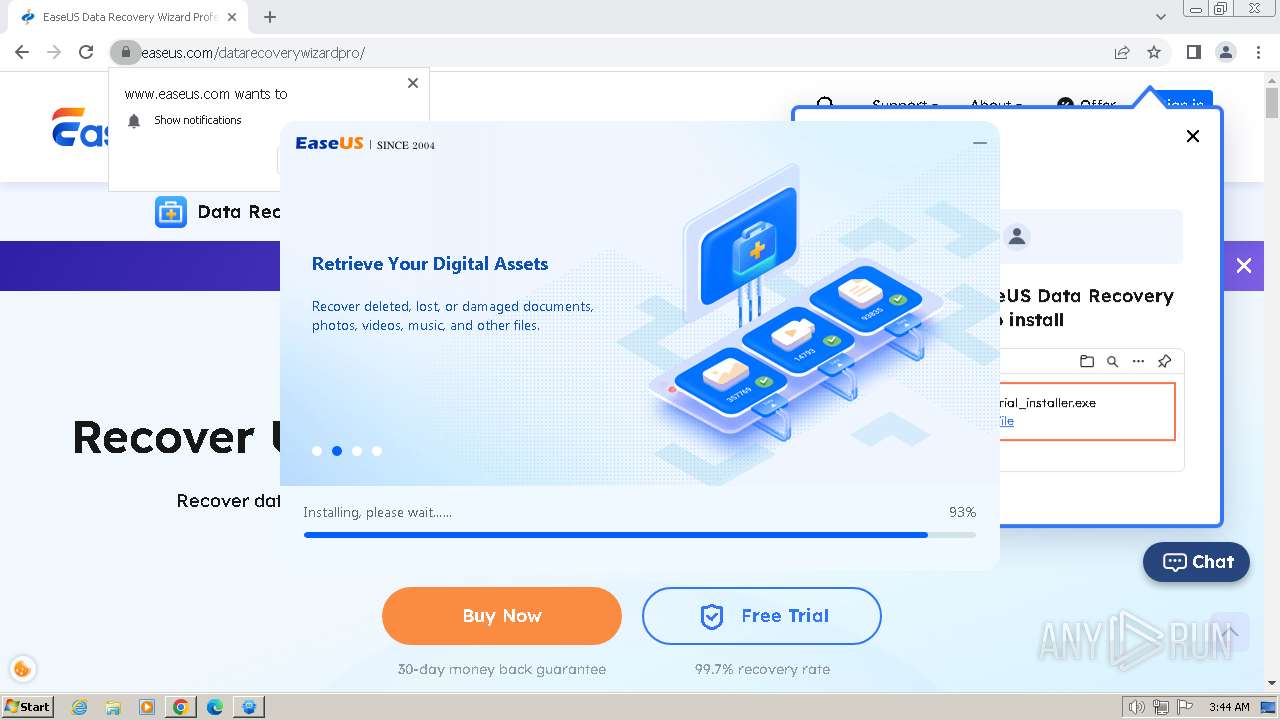
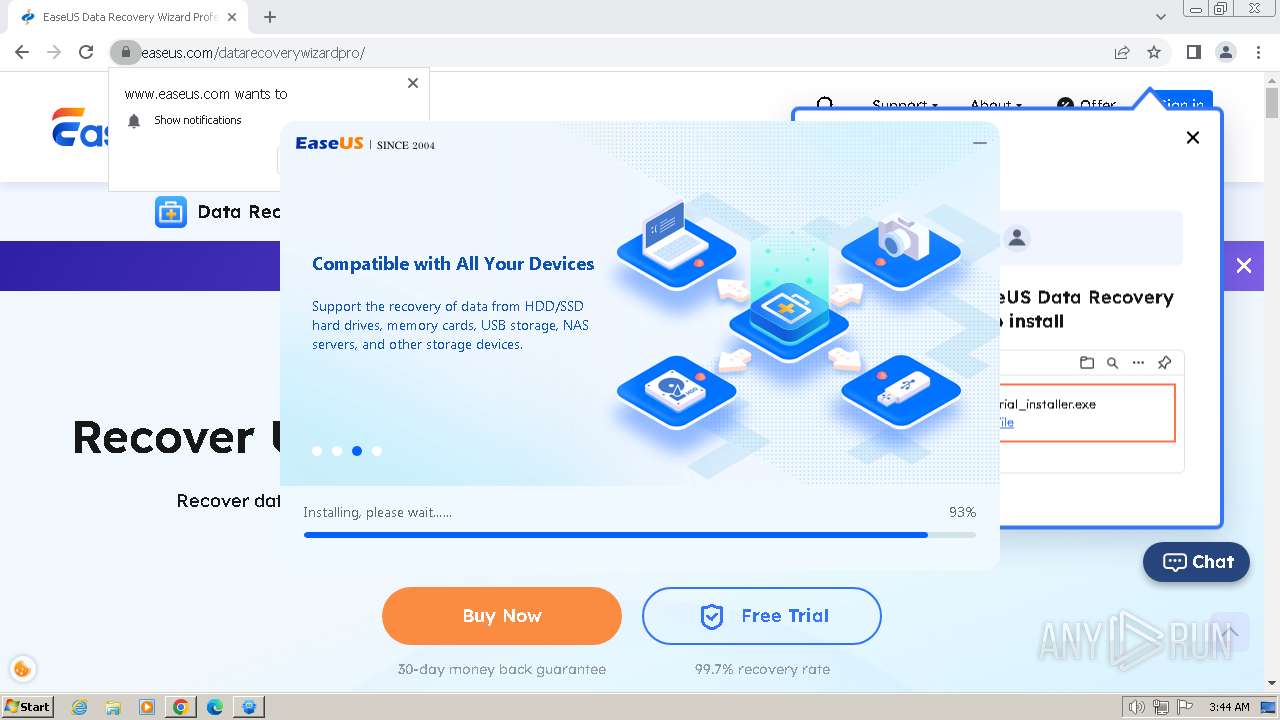
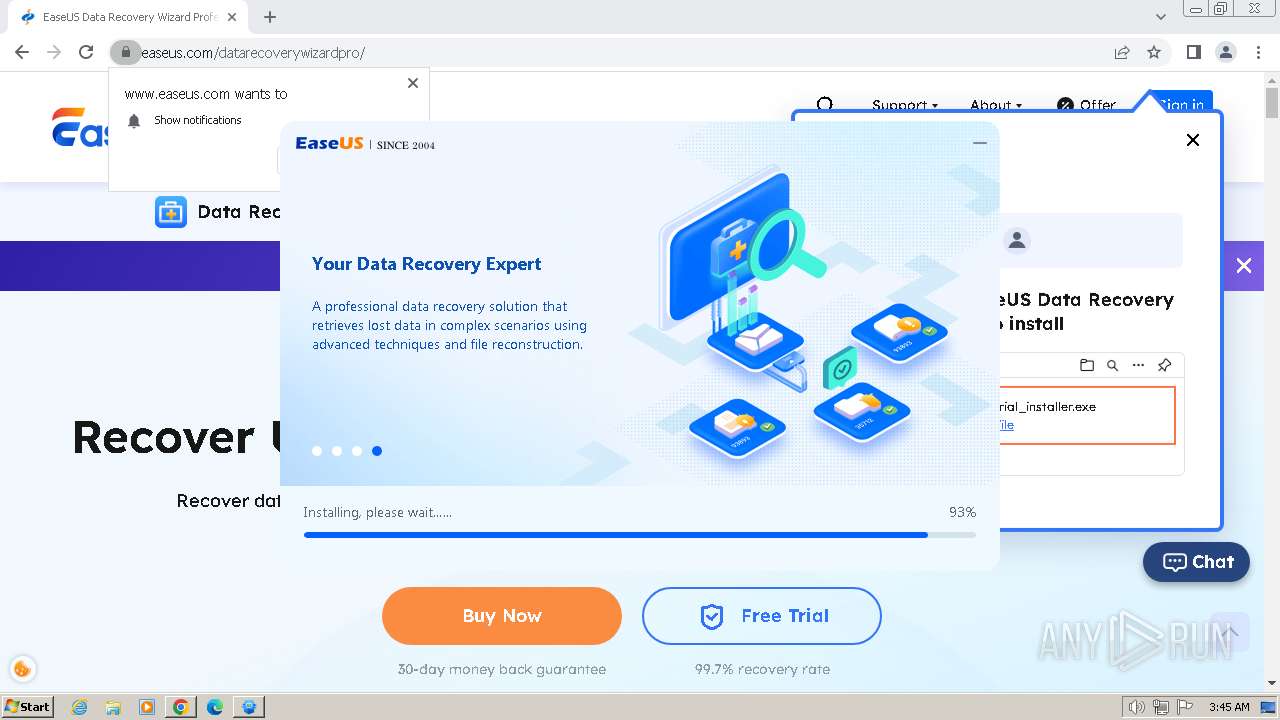
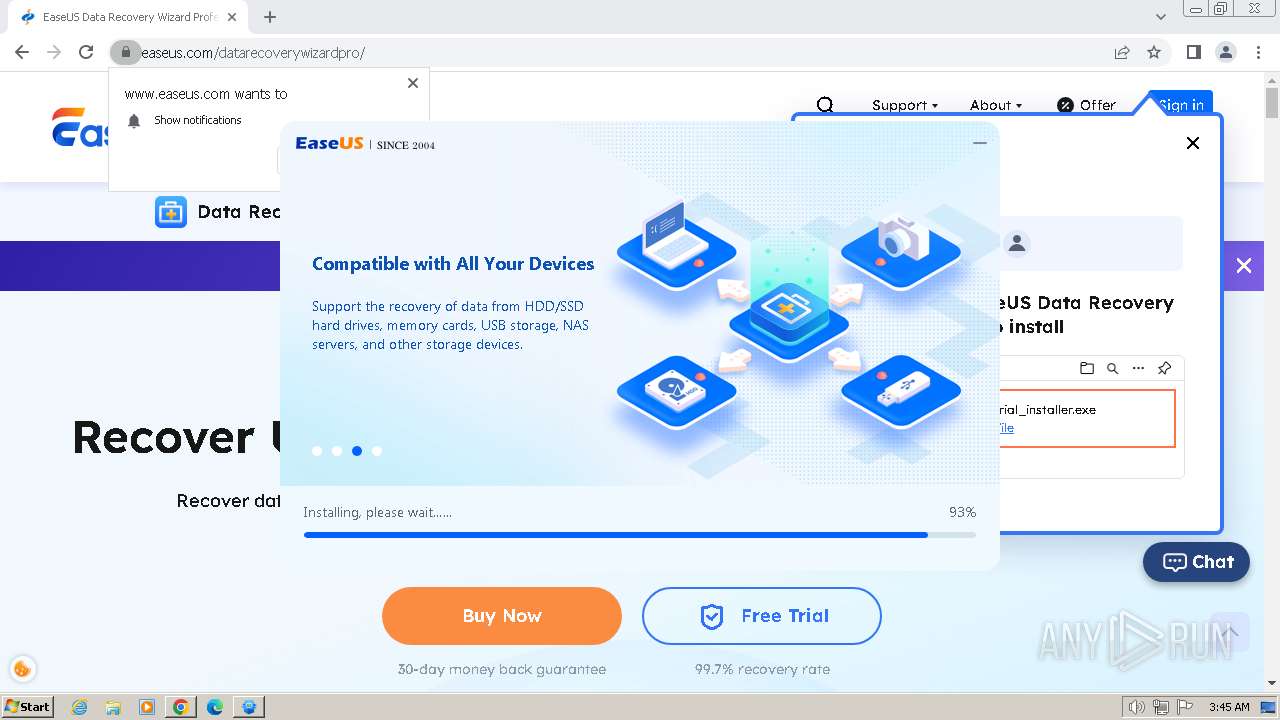
| URL: | www.easeus.com/thankyou/install-data-recovery-wizard-ad-trial.html |
| Full analysis: | https://app.any.run/tasks/c056a3c9-5b81-4632-b2fe-5bf6a3a4a457 |
| Verdict: | Malicious activity |
| Analysis date: | April 19, 2024, 02:40:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CA9F9701662FF6A0414CE076DA1C9336 |
| SHA1: | A8F3FEFC82C55BD878AC8B49A1EE405F352EB32D |
| SHA256: | 3A775434672BAD9098C66CD933FE20D1C474D97513F11D0348F17B85D5DE2BDB |
| SSDEEP: | 3:E9WAnNiOuDJGBGTvE++n:bhVGBcvkn |
MALICIOUS
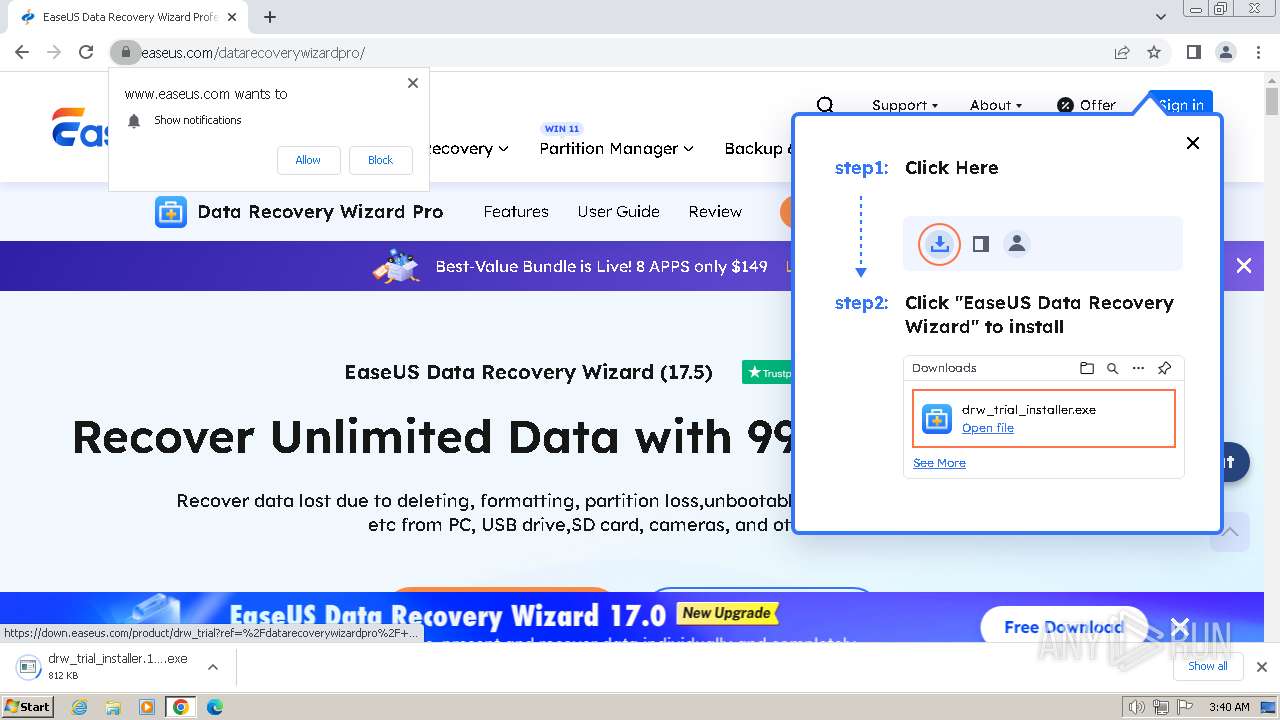
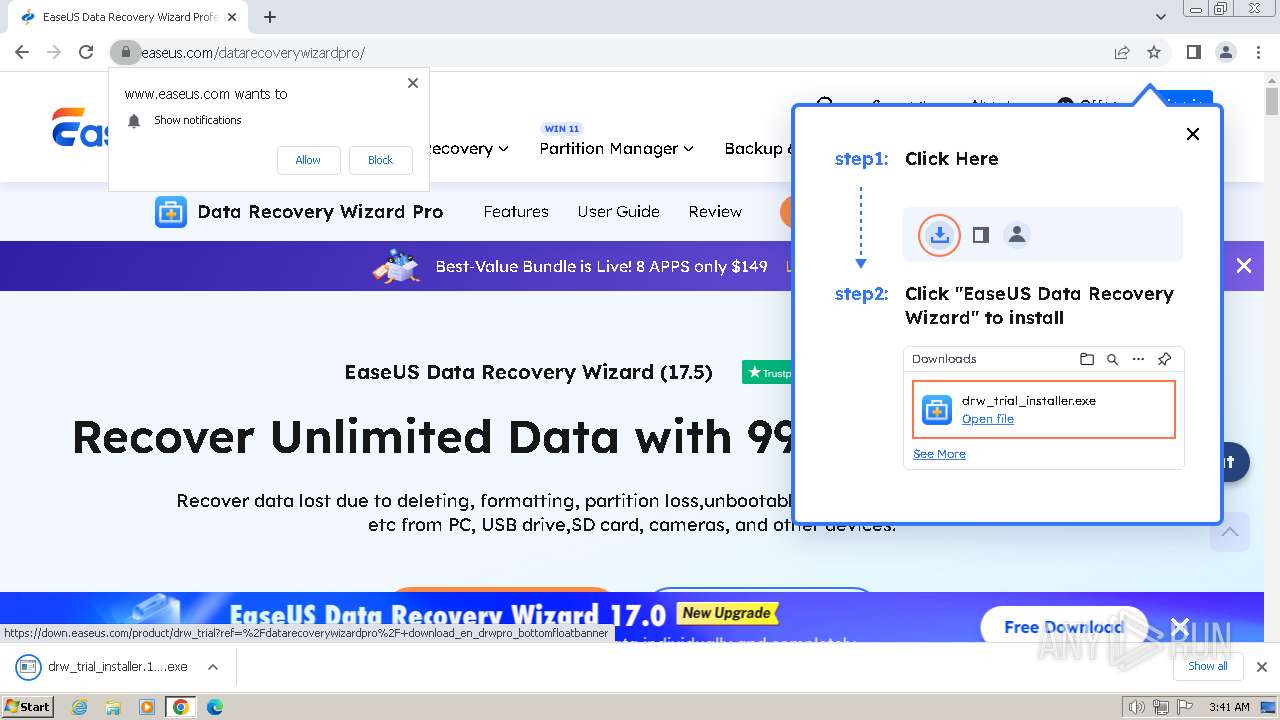
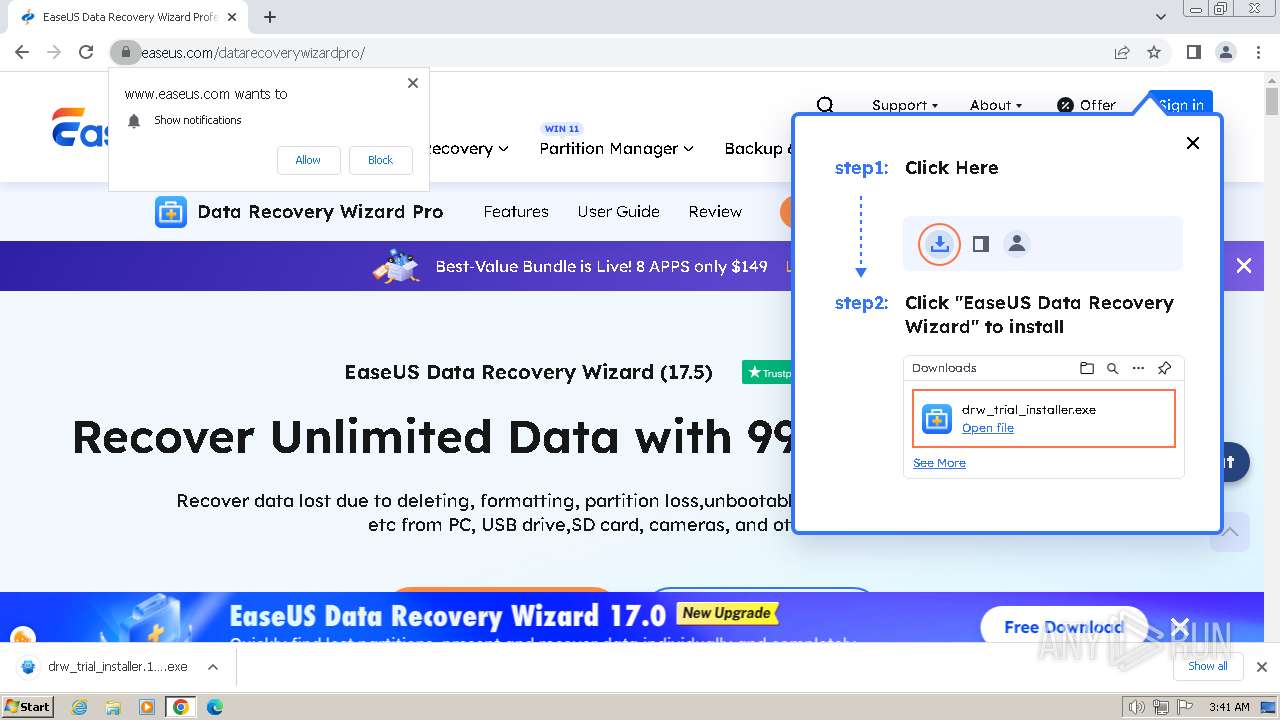
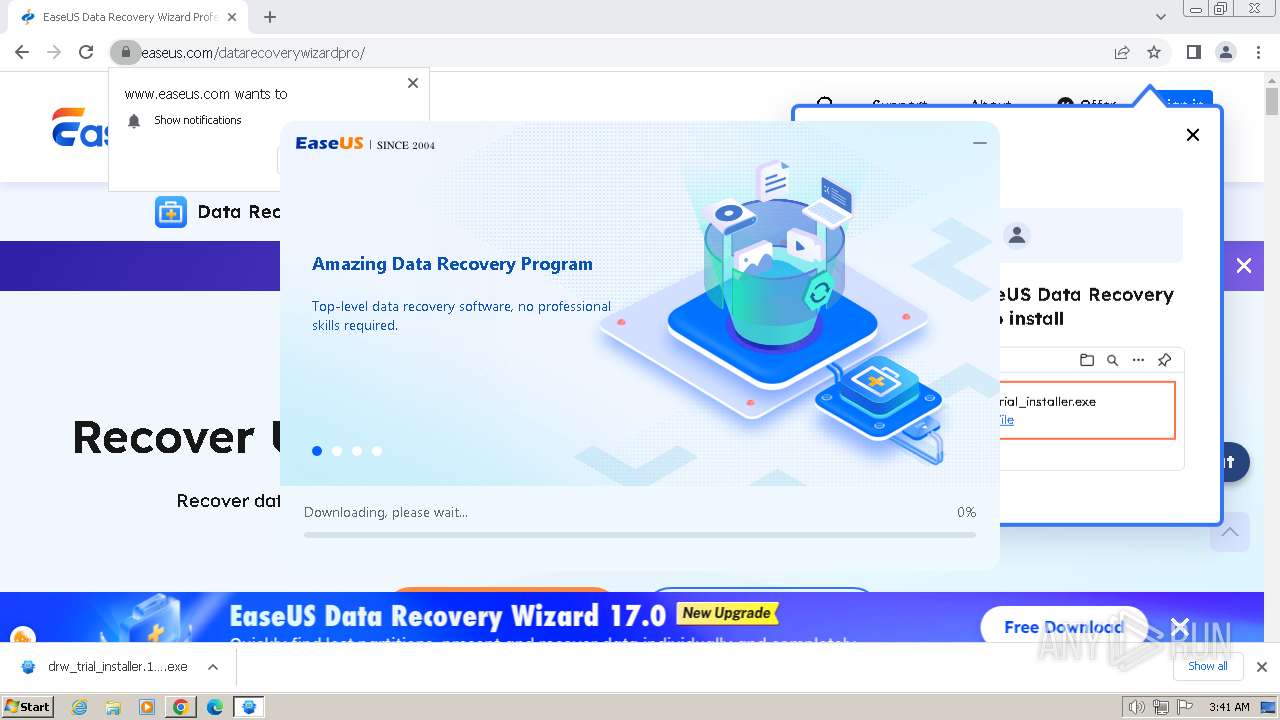
Drops the executable file immediately after the start
- drw_trial_installer.17134944573079b226.exe (PID: 116)
- drw17.5.0.0_trial.tmp (PID: 3796)
- drw17.5.0.0_trial.exe (PID: 2576)
SUSPICIOUS
Reads the Internet Settings
- AliyunWrapExe.Exe (PID: 3060)
- EDownloader.exe (PID: 2316)
- AliyunWrapExe.Exe (PID: 2472)
Reads Microsoft Outlook installation path
- EDownloader.exe (PID: 2316)
Reads security settings of Internet Explorer
- AliyunWrapExe.Exe (PID: 3060)
- EDownloader.exe (PID: 2316)
- AliyunWrapExe.Exe (PID: 2472)
Executable content was dropped or overwritten
- drw_trial_installer.17134944573079b226.exe (PID: 116)
- drw17.5.0.0_trial.tmp (PID: 3796)
- drw17.5.0.0_trial.exe (PID: 2576)
Reads Internet Explorer settings
- EDownloader.exe (PID: 2316)
Reads the Windows owner or organization settings
- drw17.5.0.0_trial.tmp (PID: 3796)
Process drops legitimate windows executable
- drw17.5.0.0_trial.tmp (PID: 3796)
The process drops C-runtime libraries
- drw17.5.0.0_trial.tmp (PID: 3796)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 3416)
Drops the executable file immediately after the start
- chrome.exe (PID: 3416)
Checks supported languages
- EDownloader.exe (PID: 2316)
- AliyunWrapExe.Exe (PID: 3060)
- InfoForSetup.exe (PID: 2900)
- InfoForSetup.exe (PID: 2112)
- InfoForSetup.exe (PID: 2844)
- InfoForSetup.exe (PID: 3068)
- InfoForSetup.exe (PID: 3732)
- InfoForSetup.exe (PID: 2828)
- drw_trial_installer.17134944573079b226.exe (PID: 116)
- InfoForSetup.exe (PID: 2488)
- InfoForSetup.exe (PID: 2164)
- drw17.5.0.0_trial.tmp (PID: 3796)
- AliyunWrapExe.Exe (PID: 2472)
- InfoForSetup.exe (PID: 1816)
- InfoForSetup.exe (PID: 712)
- drw17.5.0.0_trial.exe (PID: 2576)
- InfoForSetup.exe (PID: 3980)
- InfoForSetup.exe (PID: 3912)
Reads the computer name
- drw_trial_installer.17134944573079b226.exe (PID: 116)
- EDownloader.exe (PID: 2316)
- AliyunWrapExe.Exe (PID: 3060)
- drw17.5.0.0_trial.tmp (PID: 3796)
- AliyunWrapExe.Exe (PID: 2472)
Create files in a temporary directory
- EDownloader.exe (PID: 2316)
- InfoForSetup.exe (PID: 2112)
- AliyunWrapExe.Exe (PID: 3060)
- drw_trial_installer.17134944573079b226.exe (PID: 116)
- drw17.5.0.0_trial.tmp (PID: 3796)
- AliyunWrapExe.Exe (PID: 2472)
- drw17.5.0.0_trial.exe (PID: 2576)
Checks proxy server information
- AliyunWrapExe.Exe (PID: 3060)
- EDownloader.exe (PID: 2316)
- AliyunWrapExe.Exe (PID: 2472)
Reads the machine GUID from the registry
- AliyunWrapExe.Exe (PID: 3060)
- EDownloader.exe (PID: 2316)
- AliyunWrapExe.Exe (PID: 2472)
Creates files or folders in the user directory
- AliyunWrapExe.Exe (PID: 3060)
- AliyunWrapExe.Exe (PID: 2472)
The process uses the downloaded file
- chrome.exe (PID: 3944)
- chrome.exe (PID: 3416)
Application launched itself
- chrome.exe (PID: 3416)
Creates files in the program directory
- drw17.5.0.0_trial.tmp (PID: 3796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
97
Monitored processes
56
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Users\admin\Downloads\drw_trial_installer.17134944573079b226.exe" | C:\Users\admin\Downloads\drw_trial_installer.17134944573079b226.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=1380 --field-trial-handle=1112,i,2347481090443931800,6431040082923766038,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 712 | "C:\Users\admin\AppData\Local\Temp\is-5I3KG.tmp\InfoForSetup.exe" /SendInfo "Window" "Licenseagreement" "Activity" "Click_Accept" | C:\Users\admin\AppData\Local\Temp\is-5I3KG.tmp\InfoForSetup.exe | — | drw17.5.0.0_trial.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=3152 --field-trial-handle=1112,i,2347481090443931800,6431040082923766038,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=5076 --field-trial-handle=1112,i,2347481090443931800,6431040082923766038,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=5012 --field-trial-handle=1112,i,2347481090443931800,6431040082923766038,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6ba18b38,0x6ba18b48,0x6ba18b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2028 --field-trial-handle=1112,i,2347481090443931800,6431040082923766038,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3064 --field-trial-handle=1112,i,2347481090443931800,6431040082923766038,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=4620 --field-trial-handle=1112,i,2347481090443931800,6431040082923766038,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
24 165
Read events
23 941
Write events
203
Delete events
21
Modification events
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3416) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
168
Suspicious files
77
Text files
3 746
Unknown types
55
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1bd619.TMP | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RF1bd722.TMP | — | |
MD5:4E2B7997F4C3647F8D1ADA88339BBBA5 | SHA256:C33226C460208AA10537A23CB5128FD887DCBAA335C7DC8BFFBE08A607CCFDF5 | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:23E954DCE0FB0ECF46A96FF4ACBE66F4 | SHA256:68F3B7AA8367C46273C296103B799A112DE3B70DE873C16F7166496CA31C3DDD | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | — | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | — | |
MD5:FA25AF7098FC1571F24F200A9D105D58 | SHA256:4F40C87070B7A151FB241CCF36E7027AA703C15CA0ACB0A1759DA07B2C318574 | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1bdb78.TMP | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:825B582C78EC88D54C215EFDF1EAD639 | SHA256:367995D01A8F13E5C30C79499F86B034775BFD009D83DC97635DE438D47DFA37 | |||
| 3416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old | — | |
MD5:6344721DA60A3CF7027C43288C8991C6 | SHA256:DA3AD5C3641E42979DFB9D4178EDE8533F887C3ACF9C49BE9737D83CEDA55473 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
169
DNS requests
332
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3060 | AliyunWrapExe.Exe | GET | 200 | 163.171.156.15:80 | http://track.easeus.com/product/index.php?c=main&a=getstatus&pid=2 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | unknown | — | — | unknown |
3060 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.15:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | unknown | — | — | unknown |
2316 | EDownloader.exe | POST | 200 | 18.172.112.32:80 | http://download.easeus.com/api2/index.php/Apicp/Drwdl202004/index/ | unknown | — | — | unknown |
3060 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.15:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | unknown | — | — | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | unknown | — | — | unknown |
3060 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.15:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | unknown | — | — | unknown |
3060 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.15:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3472 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | unknown |
3416 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
3472 | chrome.exe | 104.18.7.90:443 | www.easeus.com | CLOUDFLARENET | — | unknown |
3472 | chrome.exe | 18.245.46.18:443 | update.easeus.com | — | US | unknown |
3472 | chrome.exe | 142.250.184.200:443 | www.googletagmanager.com | GOOGLE | US | unknown |
3472 | chrome.exe | 151.101.129.140:443 | www.redditstatic.com | FASTLY | US | unknown |
3472 | chrome.exe | 162.159.153.247:443 | a.quora.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.easeus.com |
| whitelisted |
accounts.google.com |
| shared |
update.easeus.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
a.quora.com |
| whitelisted |
www.redditstatic.com |
| whitelisted |
alb.reddit.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
w3-reporting-nel.reddit.com |
| unknown |
Threats
Process | Message |
|---|---|
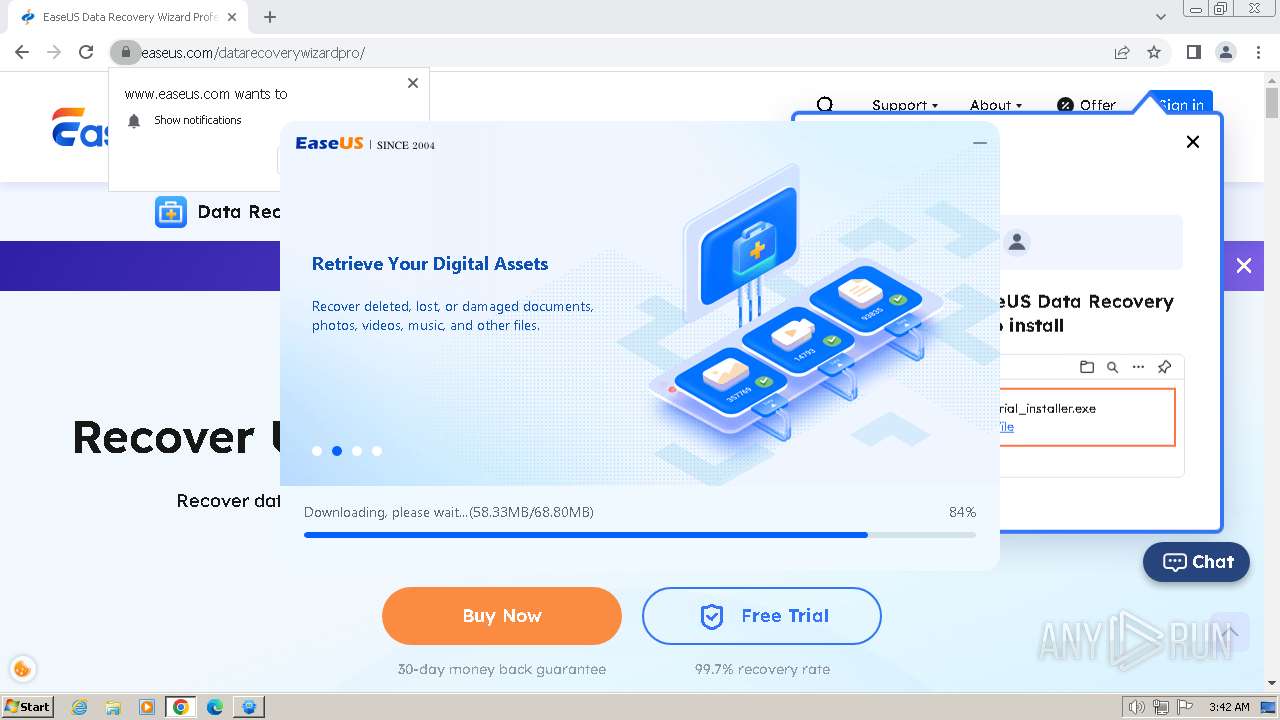
EDownloader.exe | [3660]-03:41:10:666 ParseCmdLine param=EXEDIR=C:\Users\admin\Downloads ||| EXENAME=drw_trial_installer.17134944573079b226.exe ||| DOWNLOAD_VERSION=trial ||| PRODUCT_VERSION=2.0.0 ||| INSTALL_TYPE=0
|
EDownloader.exe | [3660]-03:41:10:690 Install recomand return=259
|
EDownloader.exe | [3660]-03:41:11:074 Install recomand return=259
|
EDownloader.exe | [3660]-03:41:24:364 Install recomand return=259
|
EDownloader.exe | [3660]-03:41:24:367 Install recomand return=259
|
EDownloader.exe | [1656]-03:41:24:380 PostData Start download url=http://download.easeus.com/api2/index.php/Apicp/Drwdl202004/index/?exeNumber=17134944573079b226&lang=English&pcVersion=home&pid=2&tid=1&version=trial
|
EDownloader.exe | [1656]-03:41:27:714 PostData end
|
EDownloader.exe | [1656]-03:41:27:714 Json parse Data Start
|
EDownloader.exe | [1656]-03:41:27:714 Json parse Data end
|
EDownloader.exe | [3660]-03:41:27:714 CHttpHelper::GetDownloadInfo 45 download info code:0
|