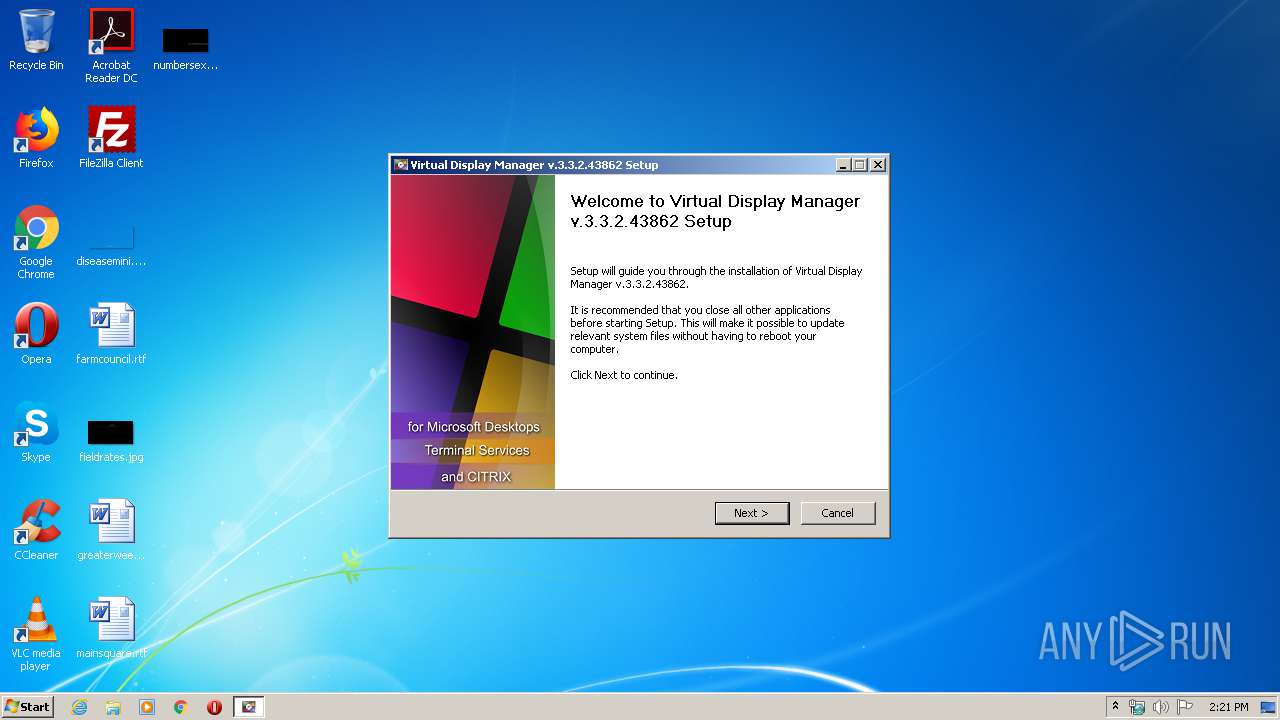
| File name: | SetupVDM.exe |
| Full analysis: | https://app.any.run/tasks/fa5e7d0a-0dd4-41dc-ad26-c4c507f84410 |
| Verdict: | Malicious activity |
| Analysis date: | March 27, 2020, 14:21:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | F87EC81538EB9AE409D9D61853187DDB |
| SHA1: | CA85A7A50CAF4BA2469CD76934FF0CC4B0114383 |
| SHA256: | 3A7684EDEE1283E0ED6D254B1CD7A4DCEE435C3173C611AAA6D60420DEA48E2E |
| SSDEEP: | 98304:pG8YCmCztLfCbYye8JWHCw/1iCwfkHr7DQaC5ishXjtf91brdDr/nxv:pUCmWtLf+k8kN/1Sfg3QaCE6jtllrd9 |
MALICIOUS
Loads dropped or rewritten executable
- SetupVDM.exe (PID: 2956)
- windanr.exe (PID: 1256)
- explorer.exe (PID: 372)
- VDLLIC.exe (PID: 2856)
- DllHost.exe (PID: 2744)
- VDM.exe (PID: 816)
- WinRAR.exe (PID: 3632)
Runs injected code in another process
- VdmSvc32.exe (PID: 1944)
Application was dropped or rewritten from another process
- VdmSvc32.exe (PID: 1944)
- VdmSetup.exe (PID: 540)
- VDLLIC.exe (PID: 2856)
- VDM.exe (PID: 816)
- VDM.exe (PID: 3384)
Application was injected by another process
- explorer.exe (PID: 372)
- windanr.exe (PID: 1256)
SUSPICIOUS
Starts CMD.EXE for commands execution
- SetupVDM.exe (PID: 2956)
Creates files in the program directory
- SetupVDM.exe (PID: 2956)
Creates or modifies windows services
- VdmSvc32.exe (PID: 1944)
Executed as Windows Service
- VdmSvc32.exe (PID: 1944)
Executable content was dropped or overwritten
- SetupVDM.exe (PID: 2956)
Creates files in the user directory
- SetupVDM.exe (PID: 2956)
Creates a software uninstall entry
- SetupVDM.exe (PID: 2956)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:08:01 02:33:55+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x330d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
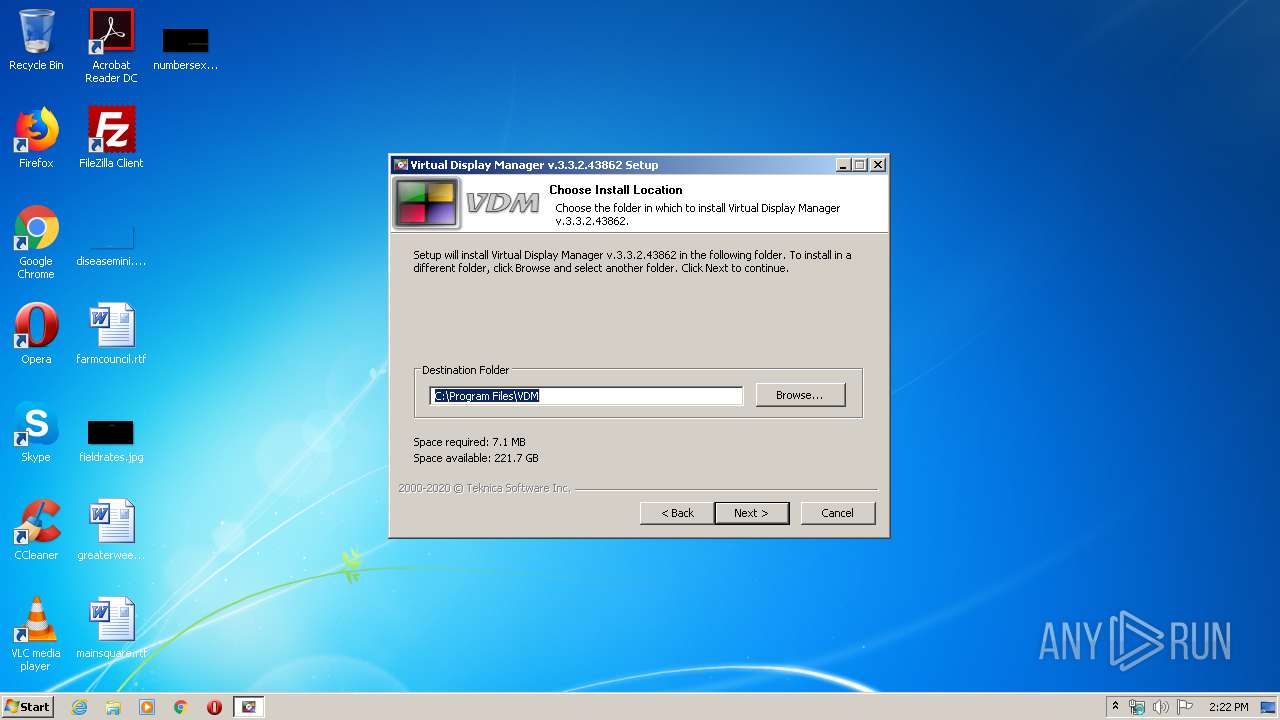
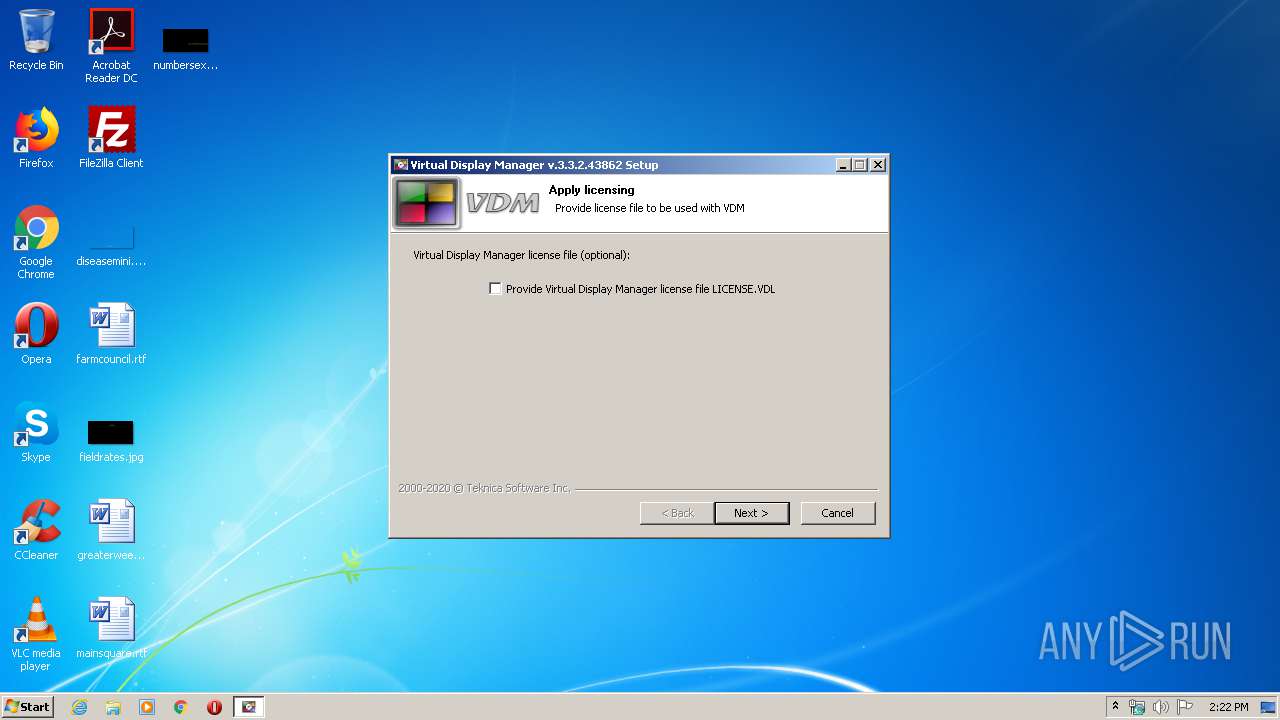
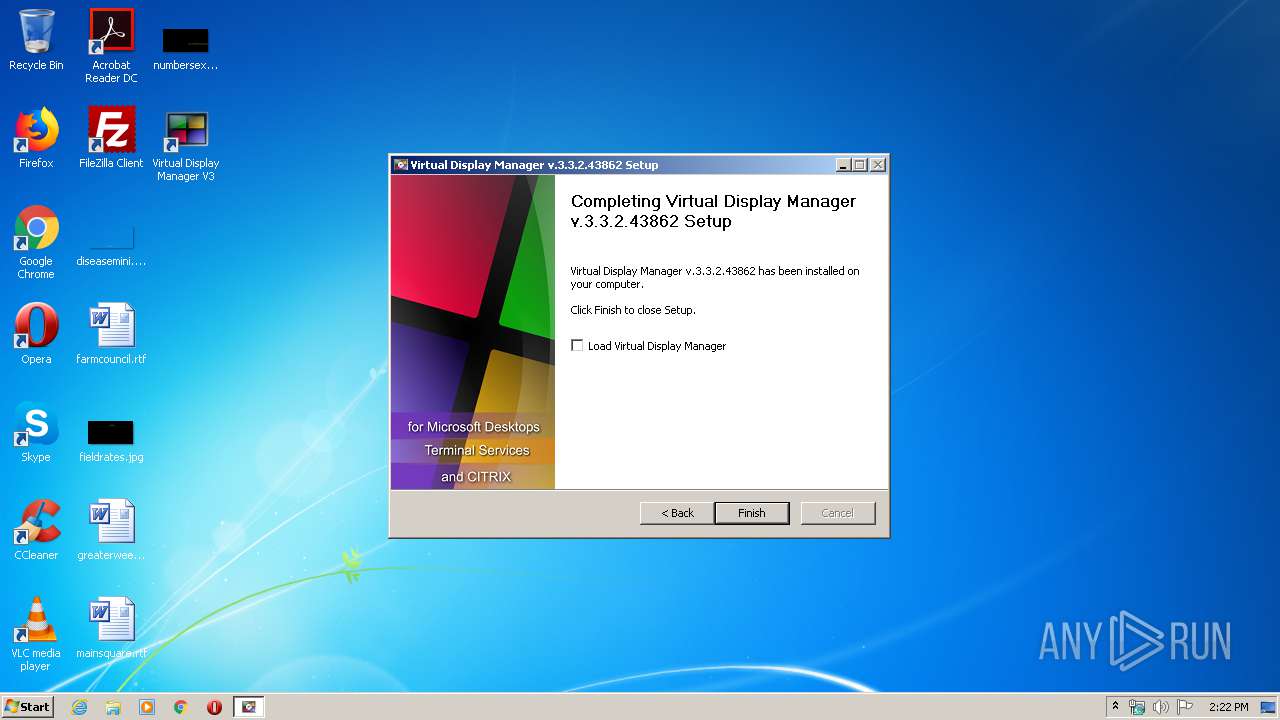
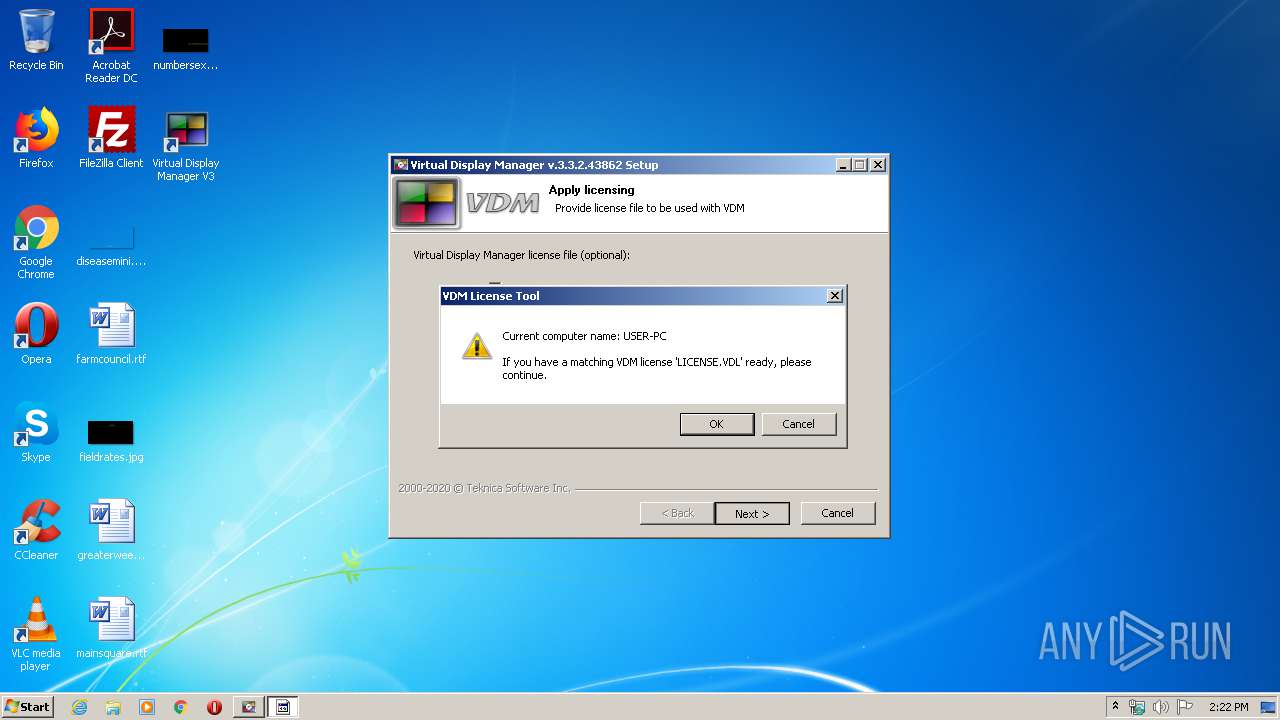
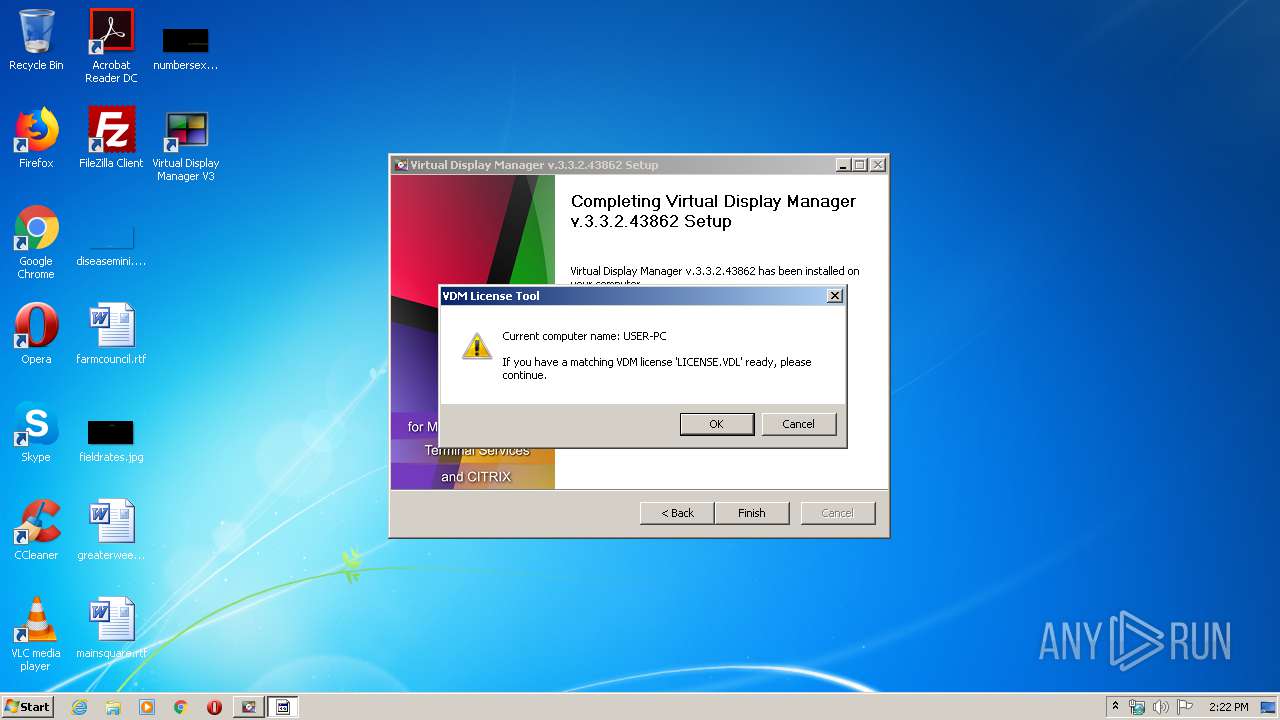
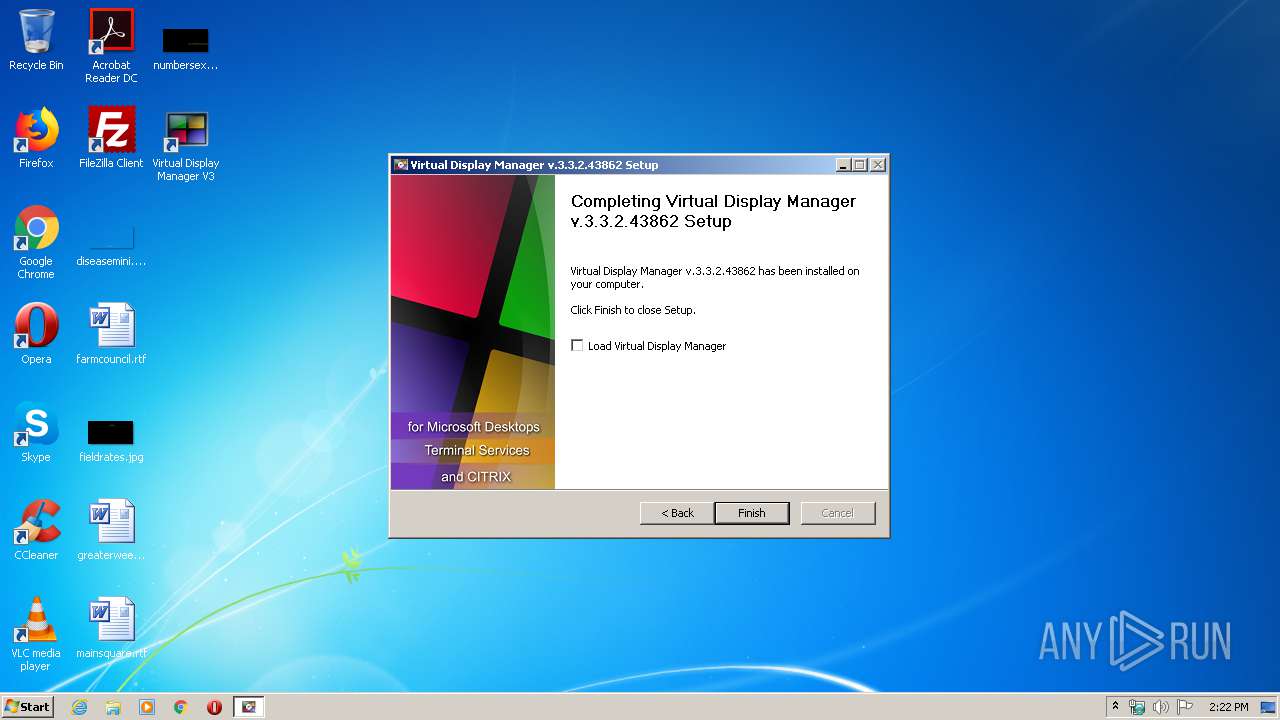
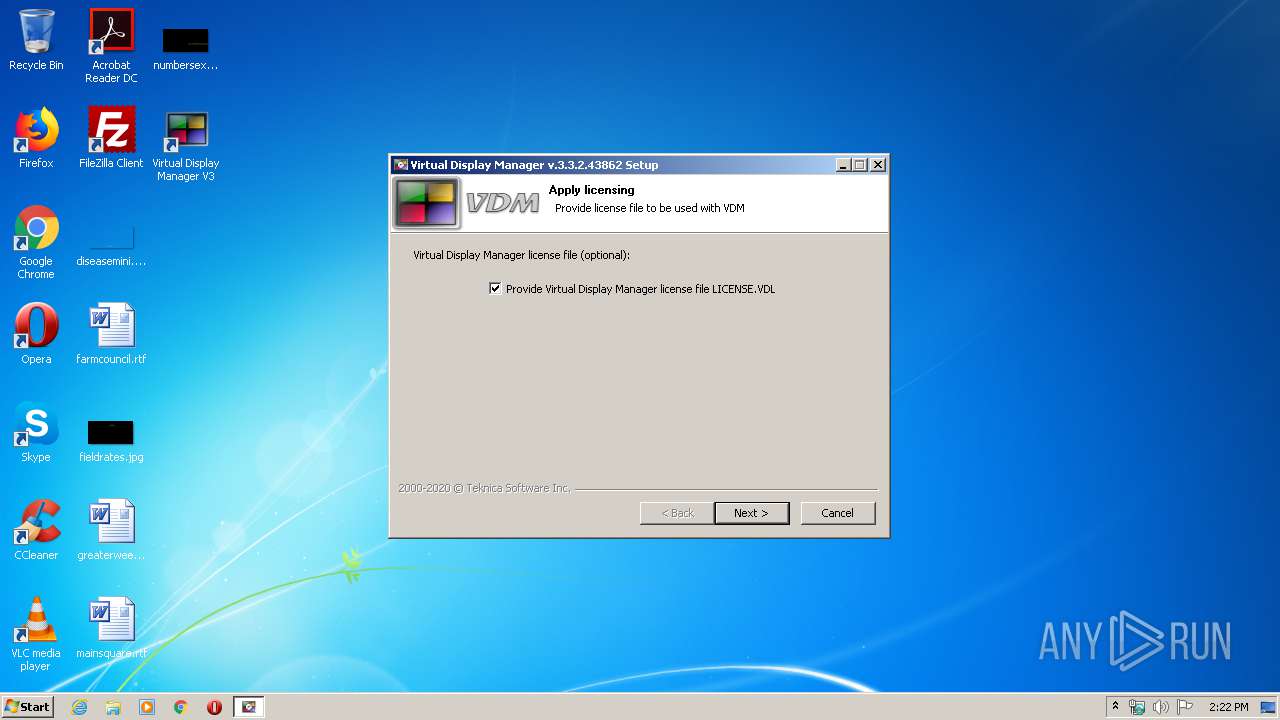
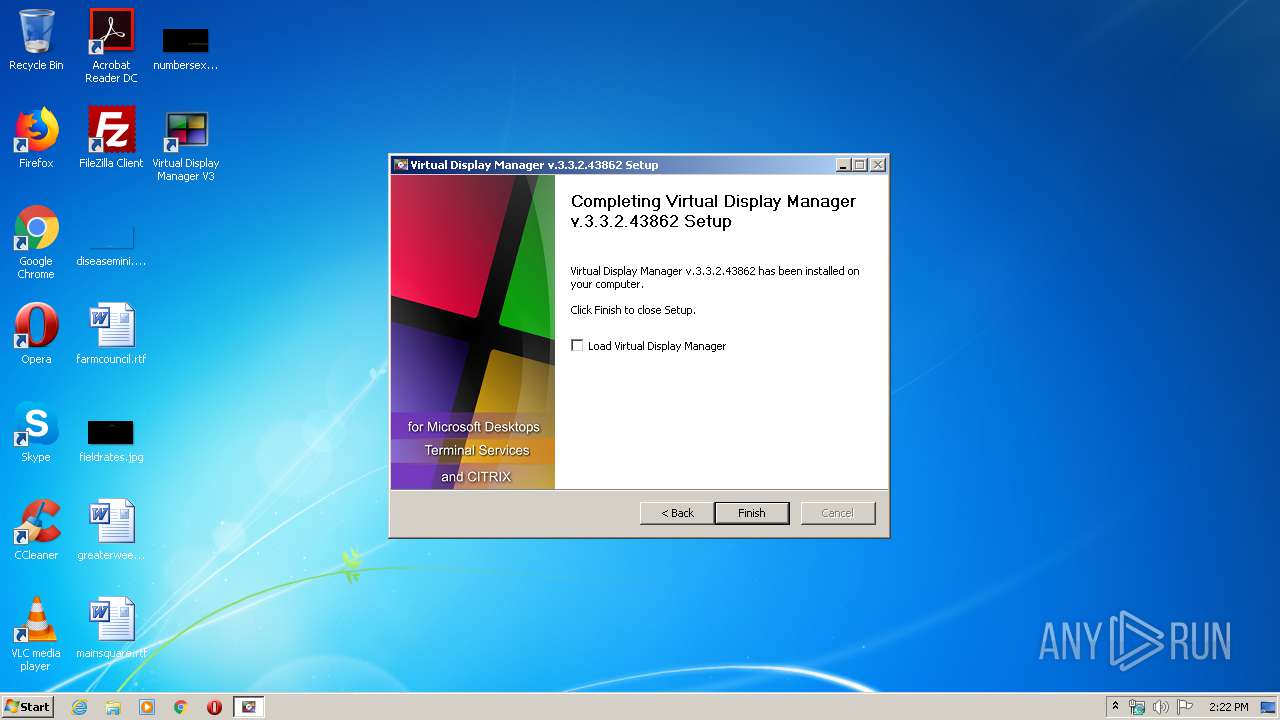
| FileVersionNumber: | 3.3.2.43862 |
| ProductVersionNumber: | 3.3.2.43862 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | Virtual Display Manager V3 |
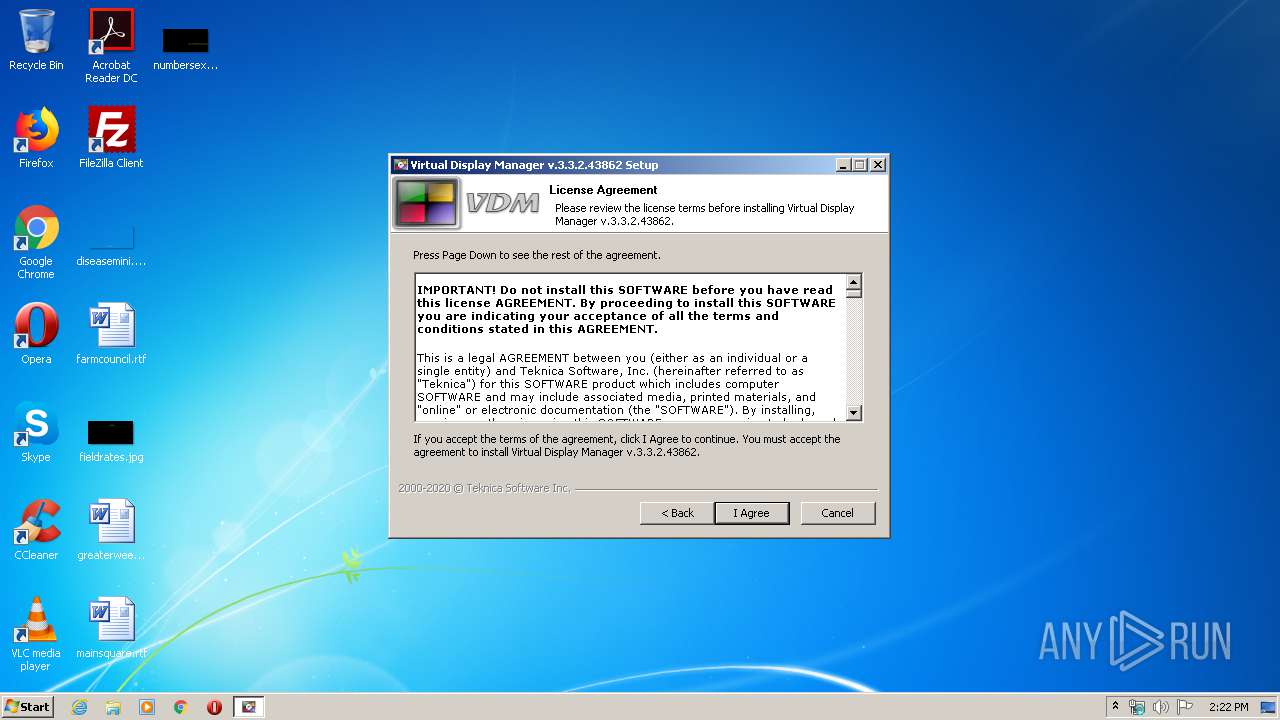
| CompanyName: | Teknica Software Inc. |
| FileDescription: | Virtual Display Manager V3 |
| FileVersion: | 3.3.2.43862 |
| LegalCopyright: | 2000-2020 © Teknica Software Inc. |
| ProductName: | VDM |
| ProductVersion: | 3.3.2.43862 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Aug-2017 00:33:55 |
| Detected languages: |
|
| Comments: | Virtual Display Manager V3 |
| CompanyName: | Teknica Software Inc. |
| FileDescription: | Virtual Display Manager V3 |
| FileVersion: | 3.3.2.43862 |
| LegalCopyright: | 2000-2020 © Teknica Software Inc. |
| ProductName: | VDM |
| ProductVersion: | 3.3.2.43862 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Aug-2017 00:33:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000603C | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.39362 |
.rdata | 0x00008000 | 0x00001248 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04426 |
.data | 0x0000A000 | 0x0001A838 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.22313 |
.ndata | 0x00025000 | 0x0000A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002F000 | 0x0001F1B8 | 0x0001F200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.42702 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2901 | 1072 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.95549 | 20538 | UNKNOWN | English - United States | RT_ICON |
3 | 4.4031 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 4.49353 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 4.71174 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.81142 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 3.52359 | 1384 | UNKNOWN | English - United States | RT_ICON |
8 | 3.39937 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.84458 | 118 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
51
Monitored processes
13
Malicious processes
5
Suspicious processes
1
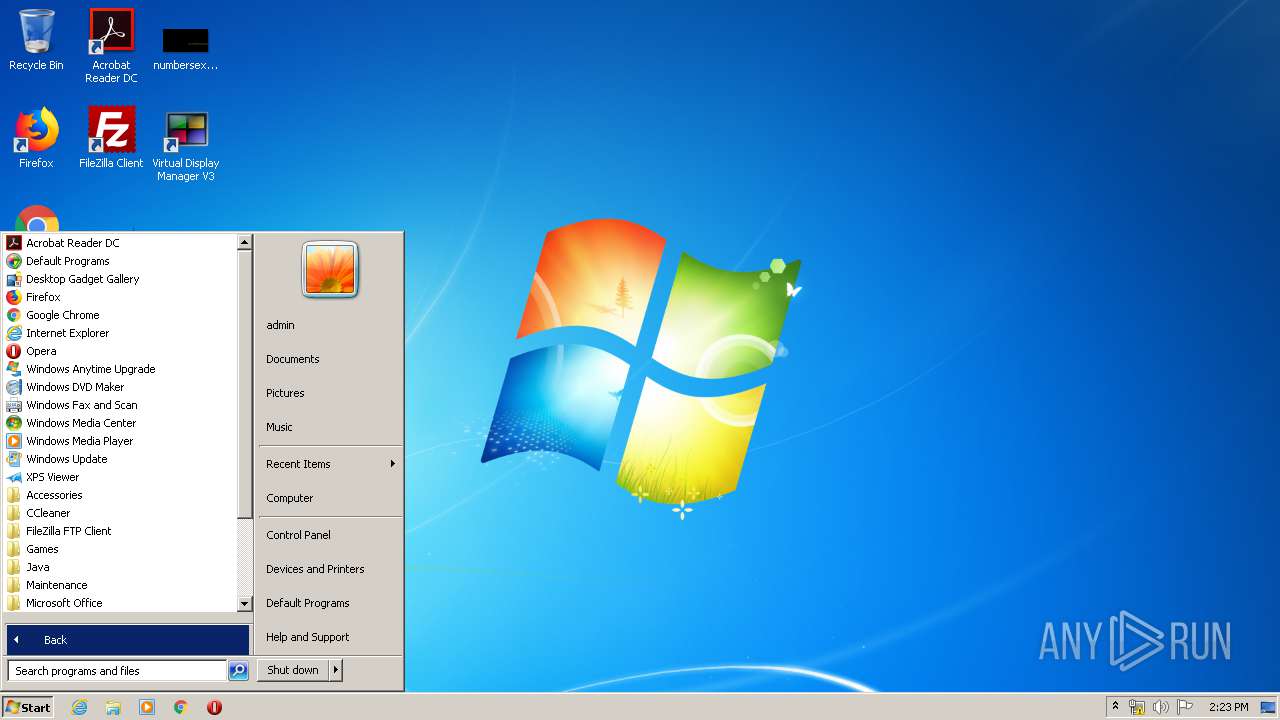
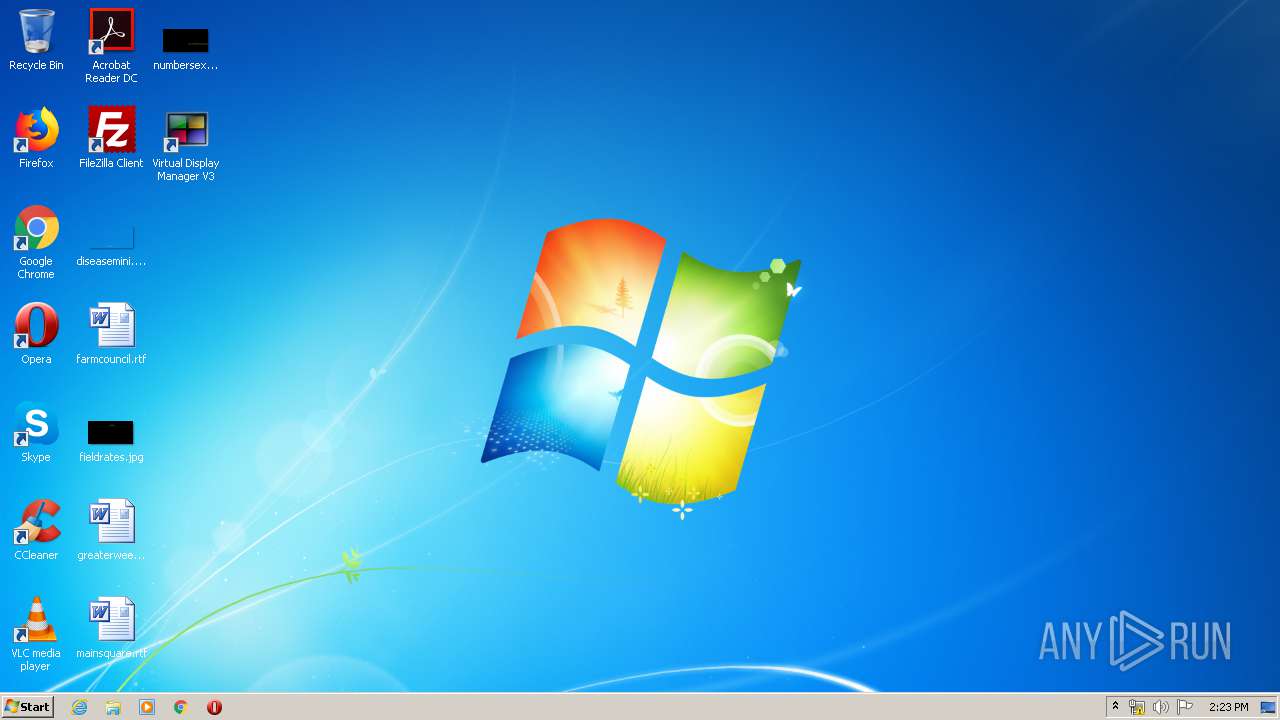
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 540 | "C:\Program Files\VDM\System32\VdmSetup.exe" -s | C:\Program Files\VDM\System32\VdmSetup.exe | — | cmd.exe | |||||||||||
User: admin Company: Teknica Software, Inc. Integrity Level: HIGH Description: VDM 32-bit Setup Exit code: 0 Version: 3.3.2.43862 Modules
| |||||||||||||||
| 816 | "C:\Program Files\VDM\VDM.exe" | C:\Program Files\VDM\VDM.exe | explorer.exe | ||||||||||||
User: admin Company: Teknica Software, Inc. Integrity Level: HIGH Description: Virtual Display Manager Exit code: 0 Version: 3.3.2.43862 Modules
| |||||||||||||||
| 1256 | "windanr.exe" | C:\Windows\system32\windanr.exe | qemu-ga.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\VDM\System32\VdmSvc32.exe" | C:\Program Files\VDM\System32\VdmSvc32.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Teknica Software, Inc. Integrity Level: SYSTEM Description: VDM 32-bit Service Exit code: 0 Version: 3.3.2.43862 Modules
| |||||||||||||||
| 2744 | C:\Windows\system32\DllHost.exe /Processid:{AB8902B4-09CA-4BB6-B78D-A8F59079A8D5} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2856 | "C:\Program Files\VDM\System32\VDLLIC" | C:\Program Files\VDM\System32\VDLLIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Teknica Software, Inc. Integrity Level: HIGH Description: VDLLIC Exit code: 1 Version: 3.3.2.43862 Modules
| |||||||||||||||
| 2916 | C:\Windows\system32\cmd.exe /C "C:\Program Files\VDM\System32\VdmSetup.exe" -s | C:\Windows\system32\cmd.exe | — | SetupVDM.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2956 | "C:\Users\admin\AppData\Local\Temp\SetupVDM.exe" | C:\Users\admin\AppData\Local\Temp\SetupVDM.exe | explorer.exe | ||||||||||||
User: admin Company: Teknica Software Inc. Integrity Level: HIGH Description: Virtual Display Manager V3 Exit code: 0 Version: 3.3.2.43862 Modules
| |||||||||||||||
| 3148 | C:\Windows\system32\cmd.exe /C "C:\Program Files\VDM\System32\VDLLIC" | C:\Windows\system32\cmd.exe | — | SetupVDM.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 4294967295 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 622
Read events
2 460
Write events
156
Delete events
6
Modification events
| (PID) Process: | (1256) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | APPSTARTING |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (1256) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | ARROW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (1256) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | CROSS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (1256) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HAND |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (1256) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HELP |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (1256) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | IBEAM |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (1256) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | NO |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (1256) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZEALL |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (1256) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENESW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (1256) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
Executable files
28
Suspicious files
0
Text files
99
Unknown types
4
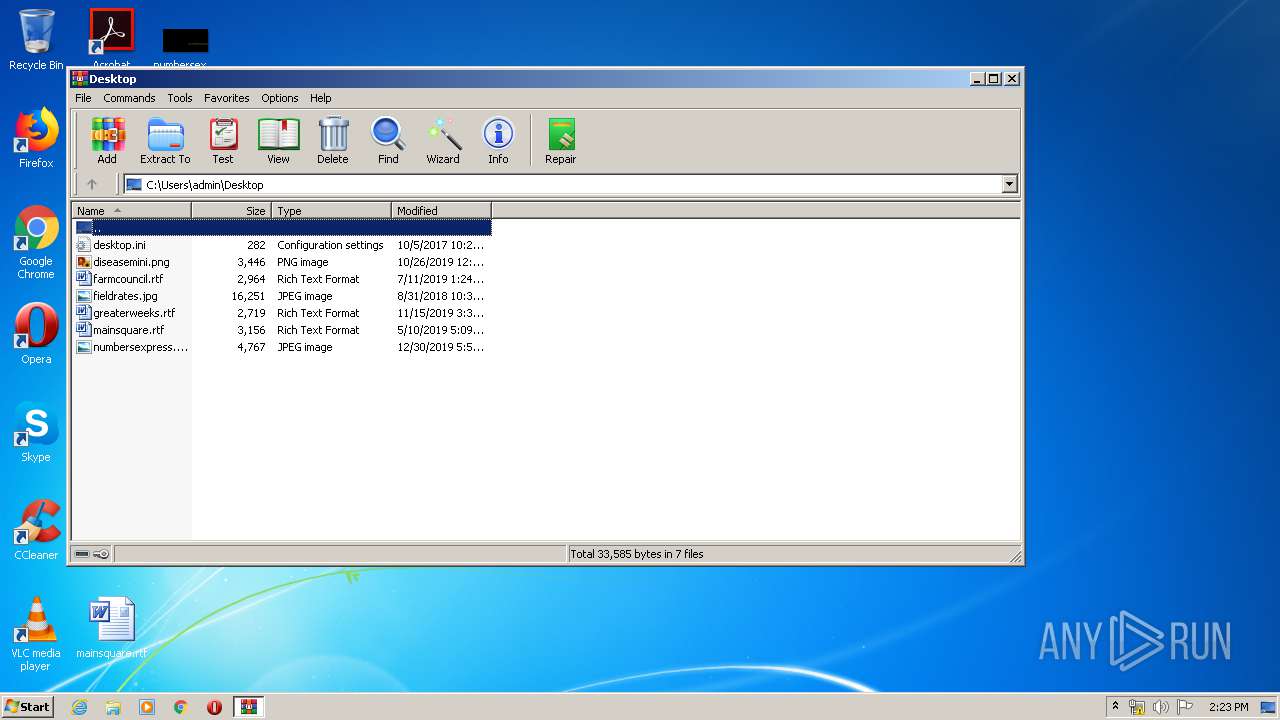
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2956 | SetupVDM.exe | C:\Users\admin\AppData\Local\Temp\nss748E.tmp\ioD.ini | text | |
MD5:— | SHA256:— | |||
| 2956 | SetupVDM.exe | C:\Program Files\VDM\VDM.exe | executable | |
MD5:— | SHA256:— | |||
| 2956 | SetupVDM.exe | C:\Program Files\VDM\System32\VDLLIB.dll | executable | |
MD5:— | SHA256:— | |||
| 2956 | SetupVDM.exe | C:\Program Files\VDM\System32\VdmSvc64.exe | executable | |
MD5:— | SHA256:— | |||
| 2956 | SetupVDM.exe | C:\Program Files\VDM\VDMHelp.chm | chm | |
MD5:— | SHA256:— | |||
| 2956 | SetupVDM.exe | C:\Program Files\VDM\System32\VdmDrv64.sys | executable | |
MD5:— | SHA256:— | |||
| 2956 | SetupVDM.exe | C:\Program Files\VDM\System32\VdmLogon.exe | executable | |
MD5:— | SHA256:— | |||
| 2956 | SetupVDM.exe | C:\Users\admin\AppData\Local\Temp\nss748E.tmp\ioC.ini | text | |
MD5:— | SHA256:— | |||
| 2956 | SetupVDM.exe | C:\Users\admin\AppData\Local\Temp\nss748E.tmp\modern-header.bmp | image | |
MD5:A53F0A8BAEDDEFF5CEC0DA388F4041F9 | SHA256:D6BF2C0281F9C27D7F98580444BCB27609CAC60E8C8ED522671492D98A22097E | |||
| 2956 | SetupVDM.exe | C:\Program Files\VDM\System32\VdmDrv32.sys | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3196 | consent.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.0 Kb | whitelisted |
3196 | consent.exe | GET | 304 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.0 Kb | whitelisted |
3196 | consent.exe | GET | 304 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3196 | consent.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |