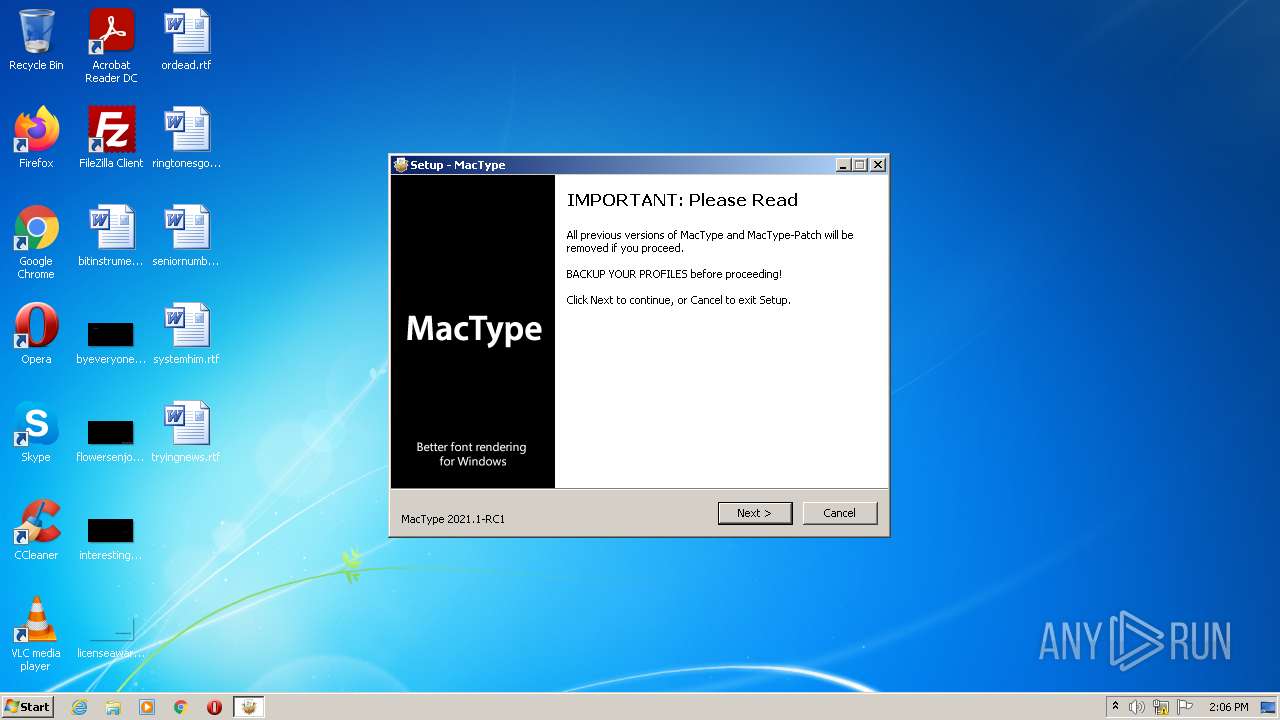
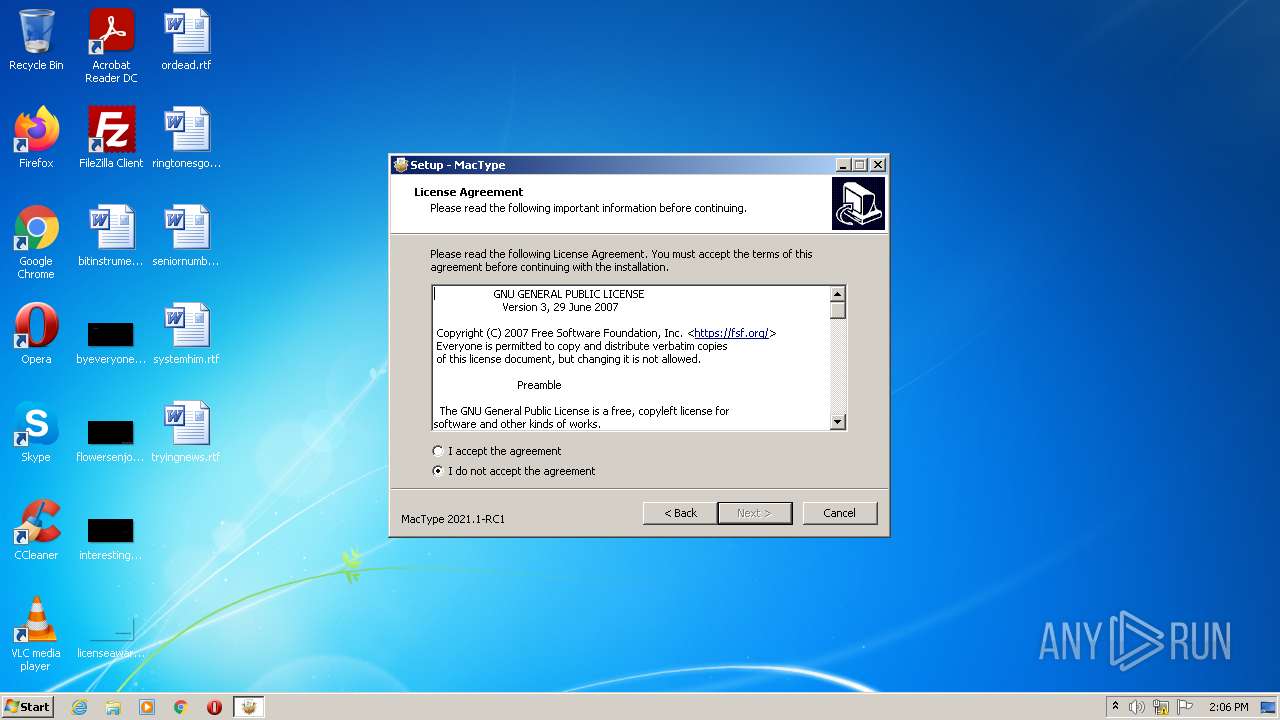
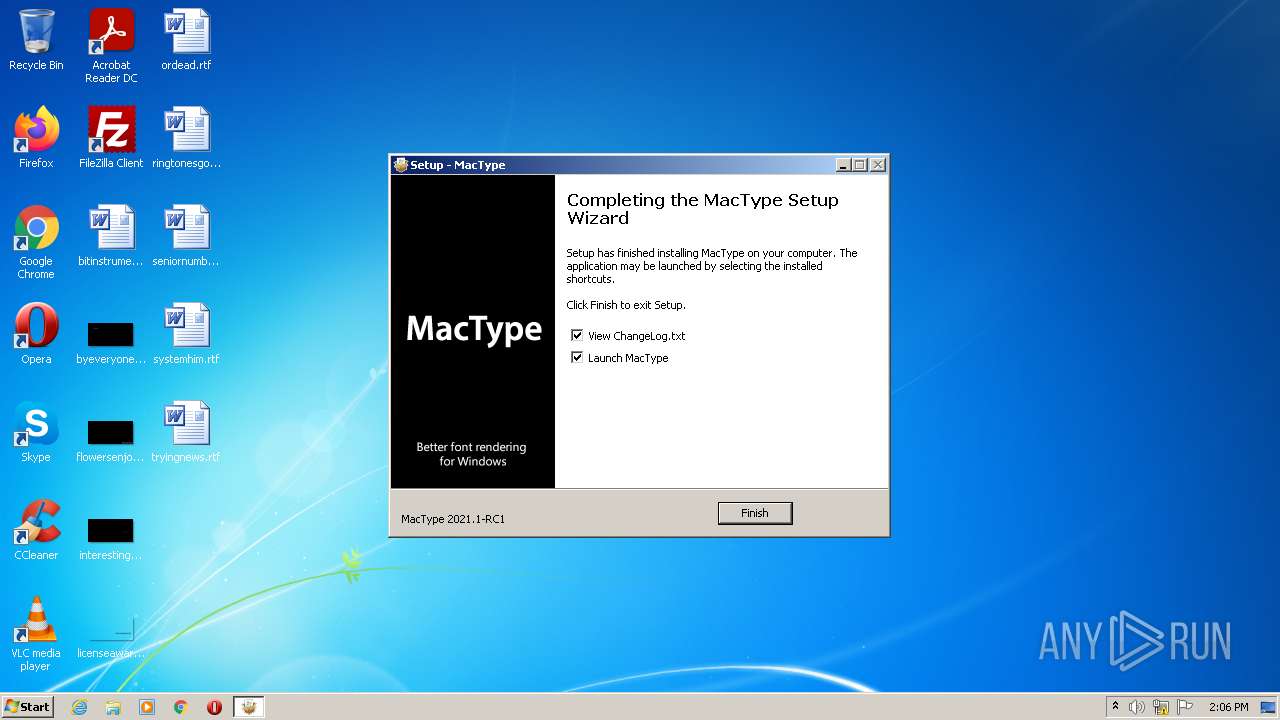
| File name: | MacTypeInstaller_2021.1-rc1.exe |
| Full analysis: | https://app.any.run/tasks/4d36d941-067a-449c-bcb1-4bb6d38f18df |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2022, 14:06:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 54233647A87AD00763E473D724EAC040 |
| SHA1: | 89E01F55D76F4BD1E17E52F21D79D83BFDD4F727 |
| SHA256: | 3A73D19D4940B6308D07F1EB19A9B6DB007423F3D2EBBA1216F2DF224A8B01F5 |
| SSDEEP: | 98304:Y2o9JJzHY9b3/BWvslA1Kk8oImjk2L3kYdi1r5rDgfmjG:uHAb3ZWv6AJHImjk2rNdG5rg+G |
MALICIOUS
Drops executable file immediately after starts
- MacTypeInstaller_2021.1-rc1.exe (PID: 3076)
- MacTypeInstaller_2021.1-rc1.exe (PID: 4084)
Application was dropped or rewritten from another process
- MacWiz.exe (PID: 1128)
- MacWiz.exe (PID: 3112)
- MacTray.exe (PID: 2604)
- MacTray.exe (PID: 1968)
Loads the Task Scheduler DLL interface
- MacTray.exe (PID: 2604)
Loads dropped or rewritten executable
- MacTray.exe (PID: 2604)
- MacTray.exe (PID: 1968)
- Explorer.EXE (PID: 1080)
- unsecapp.exe (PID: 2856)
- ctfmon.exe (PID: 1392)
- NOTEPAD.EXE (PID: 676)
- svchost.exe (PID: 600)
Changes AppInit_DLLs value (autorun option)
- MacTray.exe (PID: 2604)
Application was injected by another process
- svchost.exe (PID: 600)
- ctfmon.exe (PID: 1392)
- Explorer.EXE (PID: 1080)
Runs injected code in another process
- MacTray.exe (PID: 1968)
SUSPICIOUS
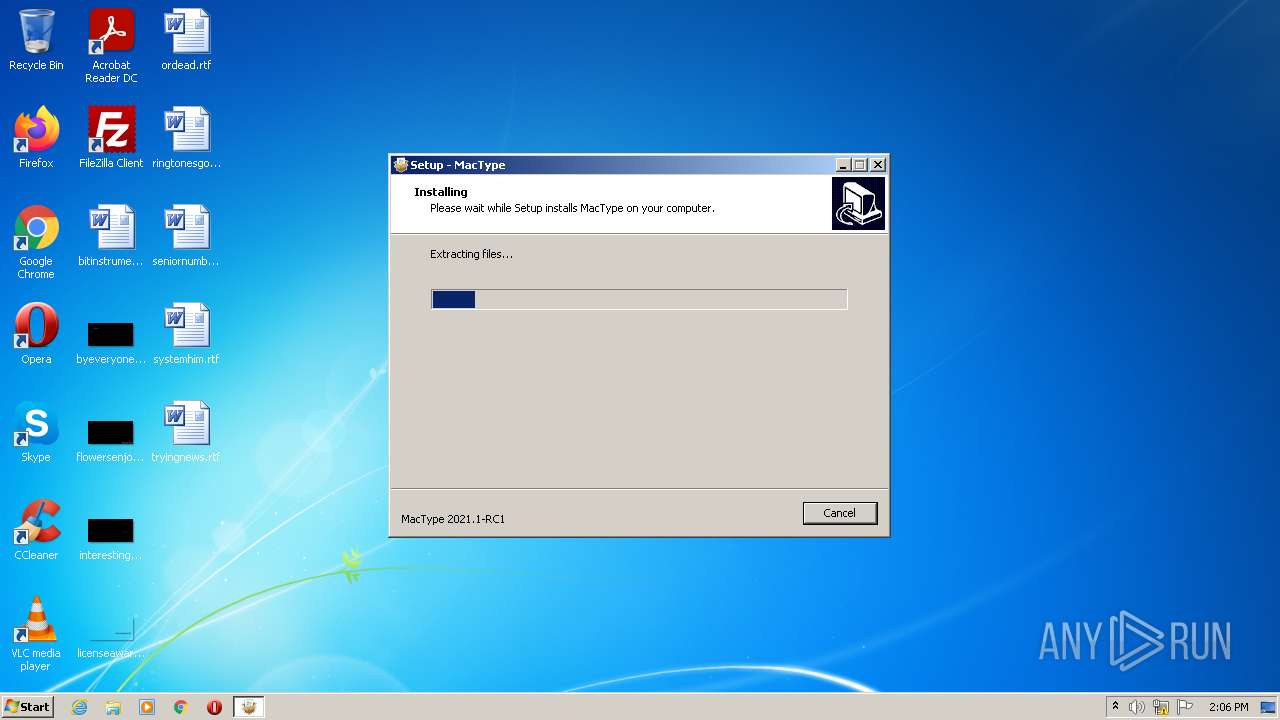
Executable content was dropped or overwritten
- MacTypeInstaller_2021.1-rc1.exe (PID: 3076)
- MacTypeInstaller_2021.1-rc1.exe (PID: 4084)
- MacTypeInstaller_2021.1-rc1.tmp (PID: 2016)
Checks supported languages
- MacTypeInstaller_2021.1-rc1.tmp (PID: 3384)
- MacTypeInstaller_2021.1-rc1.exe (PID: 3076)
- MacTypeInstaller_2021.1-rc1.exe (PID: 4084)
- MacTypeInstaller_2021.1-rc1.tmp (PID: 2016)
- MacWiz.exe (PID: 3112)
- MacTray.exe (PID: 2604)
- MacTray.exe (PID: 1968)
- unsecapp.exe (PID: 2856)
Reads the computer name
- MacTypeInstaller_2021.1-rc1.tmp (PID: 3384)
- MacTypeInstaller_2021.1-rc1.tmp (PID: 2016)
- MacWiz.exe (PID: 3112)
- MacTray.exe (PID: 1968)
- unsecapp.exe (PID: 2856)
- MacTray.exe (PID: 2604)
Starts SC.EXE for service management
- MacTypeInstaller_2021.1-rc1.tmp (PID: 2016)
Reads the Windows organization settings
- MacTypeInstaller_2021.1-rc1.tmp (PID: 2016)
Reads Windows owner or organization settings
- MacTypeInstaller_2021.1-rc1.tmp (PID: 2016)
Executed as Windows Service
- msiexec.exe (PID: 1912)
- MacTray.exe (PID: 1968)
Drops a file that was compiled in debug mode
- MacTypeInstaller_2021.1-rc1.tmp (PID: 2016)
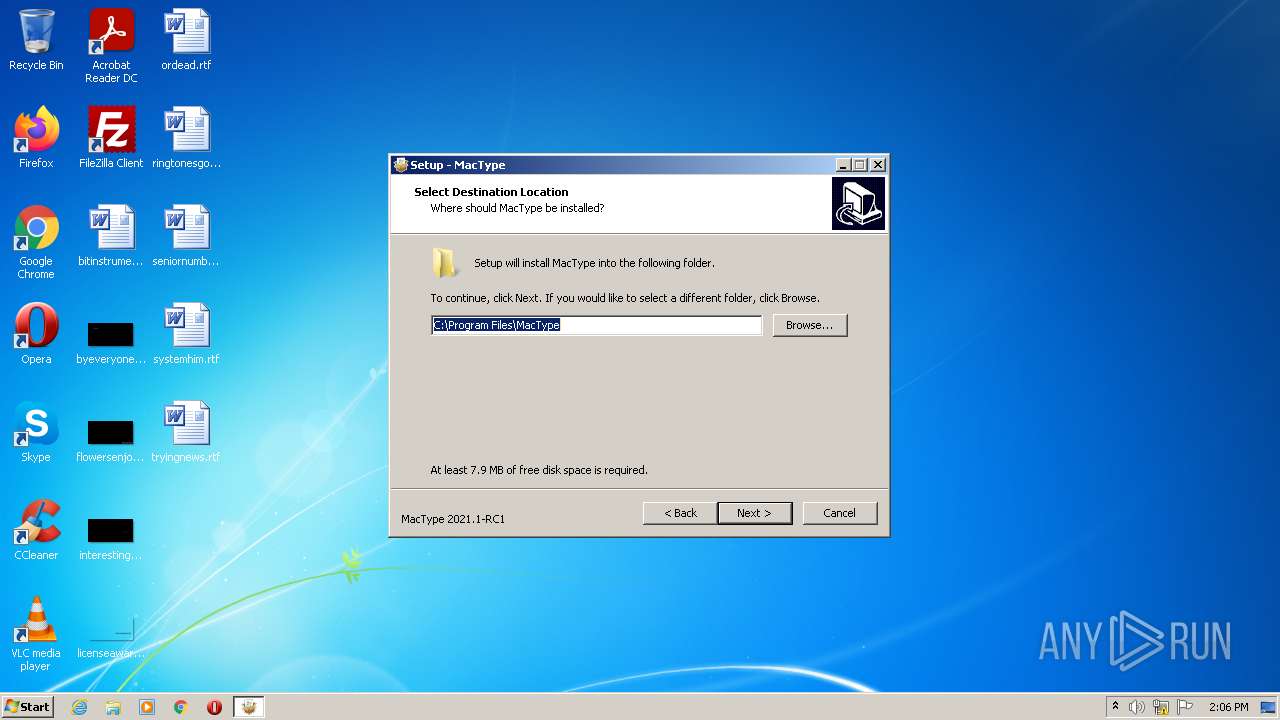
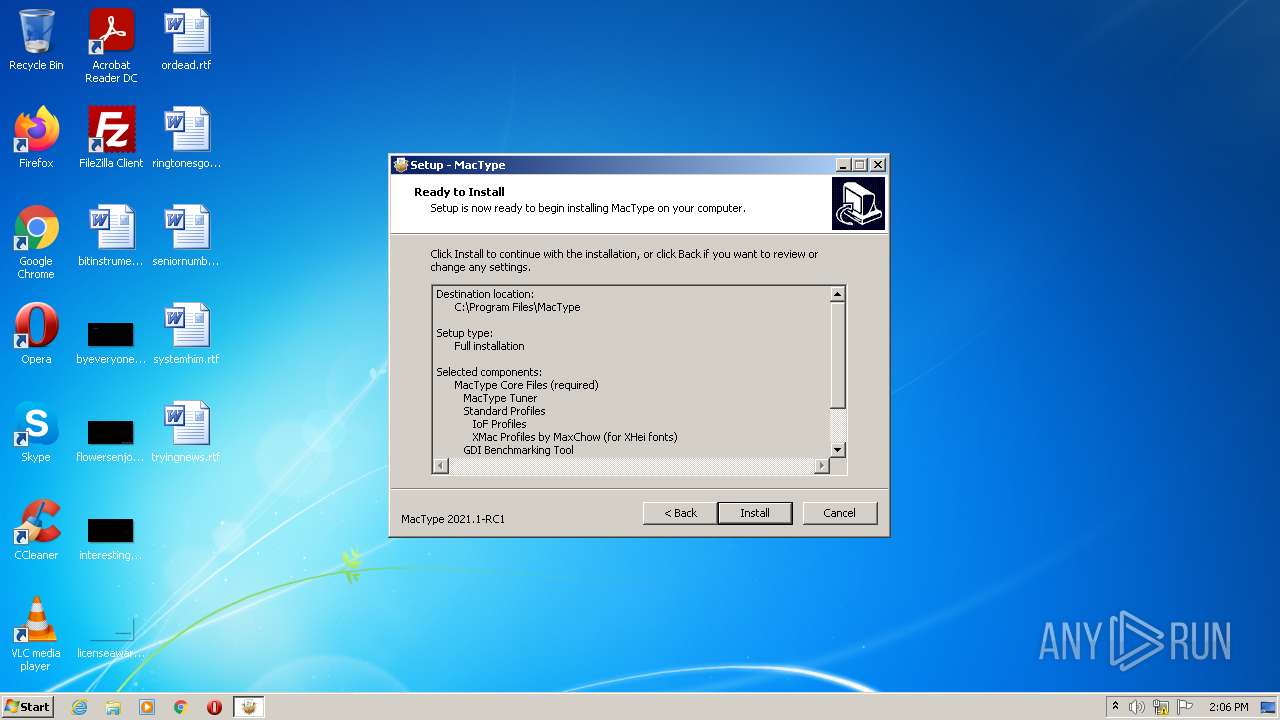
Creates a directory in Program Files
- MacTypeInstaller_2021.1-rc1.tmp (PID: 2016)
Uses TASKKILL.EXE to kill process
- MacTypeInstaller_2021.1-rc1.tmp (PID: 2016)
Removes files from Windows directory
- MacTray.exe (PID: 1968)
Creates or modifies windows services
- MacTray.exe (PID: 2604)
Executed via COM
- unsecapp.exe (PID: 2856)
INFO
Application was dropped or rewritten from another process
- MacTypeInstaller_2021.1-rc1.tmp (PID: 3384)
- MacTypeInstaller_2021.1-rc1.tmp (PID: 2016)
Reads the computer name
- msiexec.exe (PID: 4080)
- sc.exe (PID: 2316)
- sc.exe (PID: 2516)
- msiexec.exe (PID: 2628)
- msiexec.exe (PID: 1912)
- taskkill.exe (PID: 3092)
- taskkill.exe (PID: 3548)
- taskkill.exe (PID: 2472)
- taskkill.exe (PID: 3428)
- taskkill.exe (PID: 1104)
- taskkill.exe (PID: 2560)
- taskkill.exe (PID: 3292)
- msiexec.exe (PID: 2536)
- msiexec.exe (PID: 3572)
- sc.exe (PID: 3932)
- sc.exe (PID: 2520)
- msiexec.exe (PID: 3588)
- sc.exe (PID: 1044)
- sc.exe (PID: 1128)
- msiexec.exe (PID: 3096)
Checks supported languages
- sc.exe (PID: 2316)
- sc.exe (PID: 2516)
- msiexec.exe (PID: 2628)
- msiexec.exe (PID: 1912)
- msiexec.exe (PID: 4080)
- taskkill.exe (PID: 3092)
- taskkill.exe (PID: 3548)
- taskkill.exe (PID: 3428)
- taskkill.exe (PID: 2472)
- taskkill.exe (PID: 2560)
- taskkill.exe (PID: 3292)
- taskkill.exe (PID: 1104)
- msiexec.exe (PID: 2536)
- msiexec.exe (PID: 3572)
- NOTEPAD.EXE (PID: 676)
- sc.exe (PID: 3932)
- sc.exe (PID: 2520)
- msiexec.exe (PID: 3588)
- msiexec.exe (PID: 3096)
- sc.exe (PID: 1044)
- sc.exe (PID: 1128)
Creates a software uninstall entry
- MacTypeInstaller_2021.1-rc1.tmp (PID: 2016)
Creates files in the program directory
- MacTypeInstaller_2021.1-rc1.tmp (PID: 2016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| ProductVersion: | 2021.1-RC1 |
|---|---|
| ProductName: | MacType |
| LegalCopyright: | |
| FileVersion: | |
| FileDescription: | MacType Setup |
| CompanyName: | FlyingSnow, Samantha Glocker |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 0.0.0.0 |
| FileVersionNumber: | 0.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | 6 |
| OSVersion: | 5 |
| EntryPoint: | 0x1181c |
| UninitializedDataSize: | - |
| InitializedDataSize: | 149504 |
| CodeSize: | 66560 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2018:06:14 15:27:46+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jun-2018 13:27:46 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | FlyingSnow, Samantha Glocker |
| FileDescription: | MacType Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | MacType |
| ProductVersion: | 2021.1-RC1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 14-Jun-2018 13:27:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F25C | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37588 |
.itext | 0x00011000 | 0x00000FA4 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.77877 |
.data | 0x00012000 | 0x00000C8C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.30283 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x00022770 | 0x00022800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.60787 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.81594 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.66155 | 488 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.32483 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.56672 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.86992 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.57445 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 4.11988 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 7.98821 | 53342 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 5.32812 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
82
Monitored processes
33
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 600 | C:\Windows\system32\svchost.exe -k DcomLaunch | C:\Windows\system32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
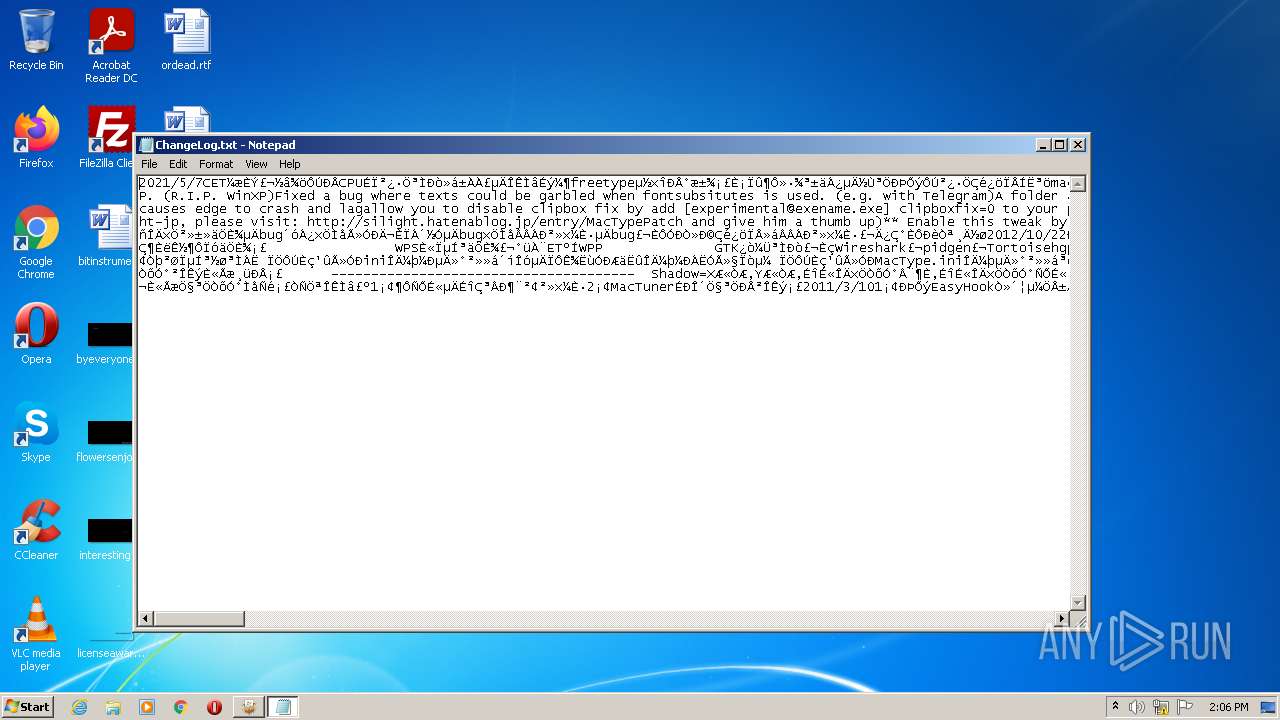
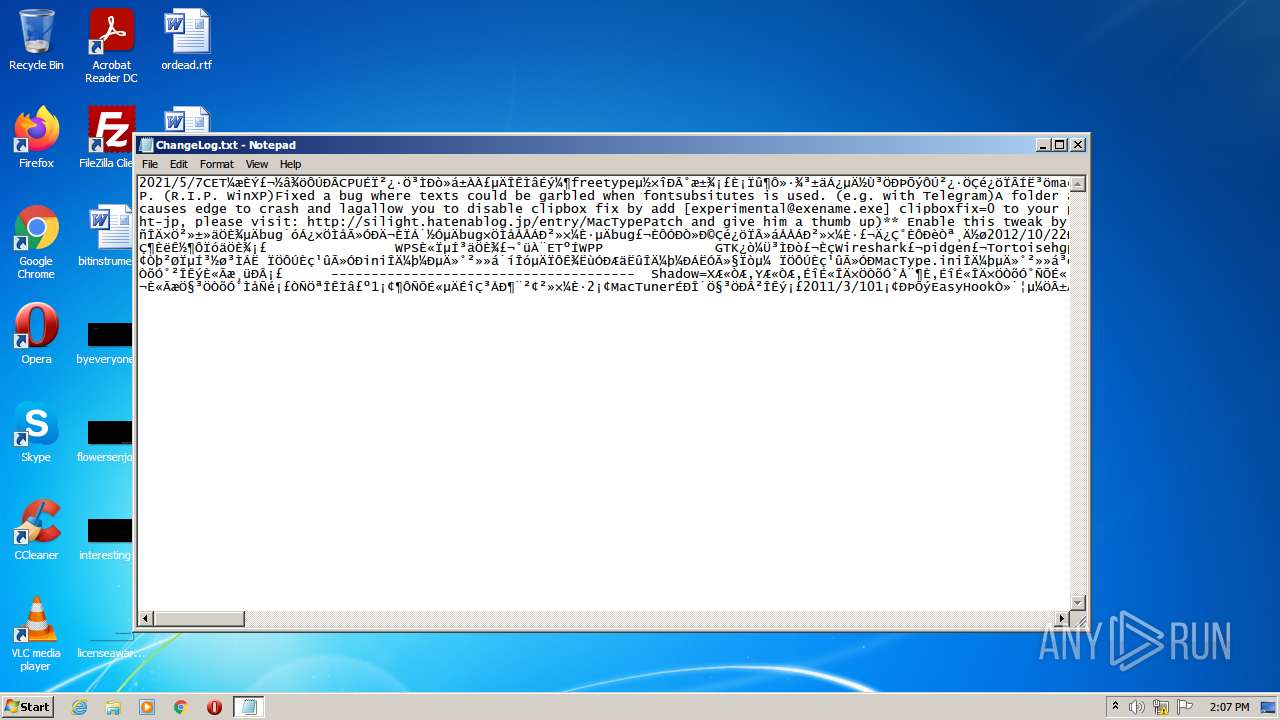
| 676 | "C:\Windows\system32\NOTEPAD.EXE" C:\Program Files\MacType\ChangeLog.txt | C:\Windows\system32\NOTEPAD.EXE | — | MacTypeInstaller_2021.1-rc1.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1044 | "sc" stop mactype | C:\Windows\system32\sc.exe | — | MacTypeInstaller_2021.1-rc1.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1080 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1104 | "taskkill.exe" /f /im "MacLoader.exe" | C:\Windows\system32\taskkill.exe | — | MacTypeInstaller_2021.1-rc1.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
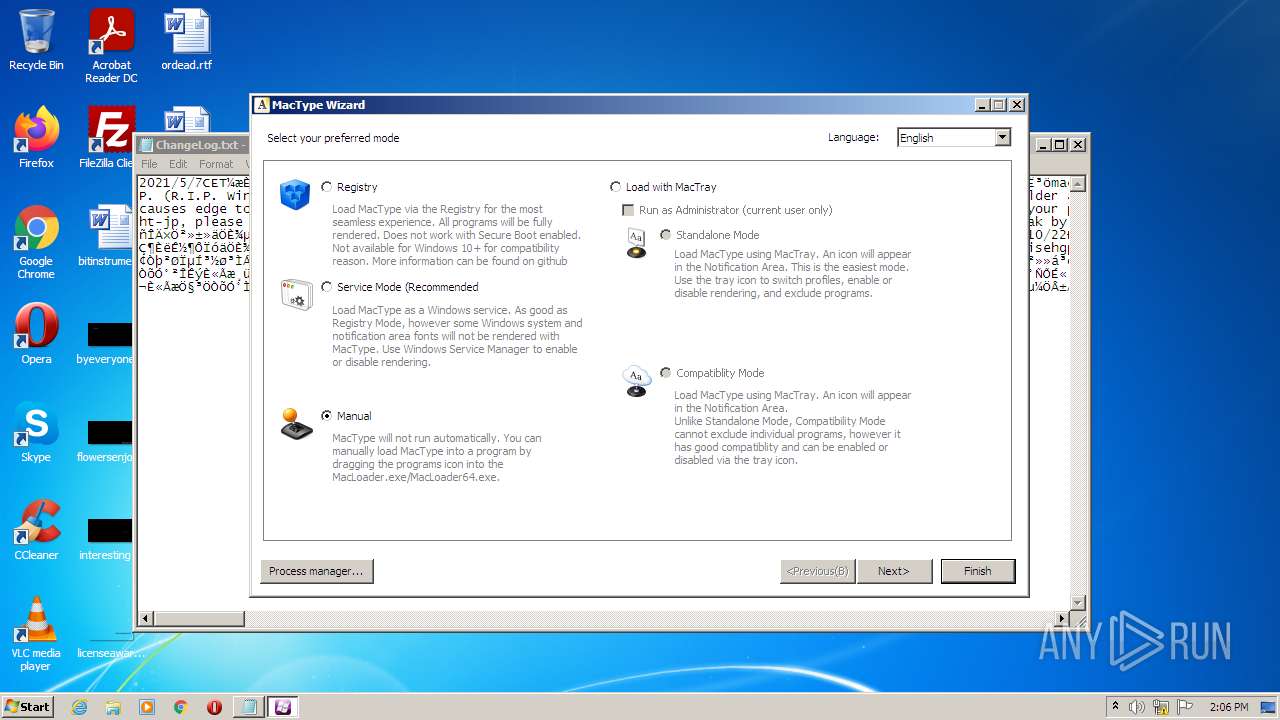
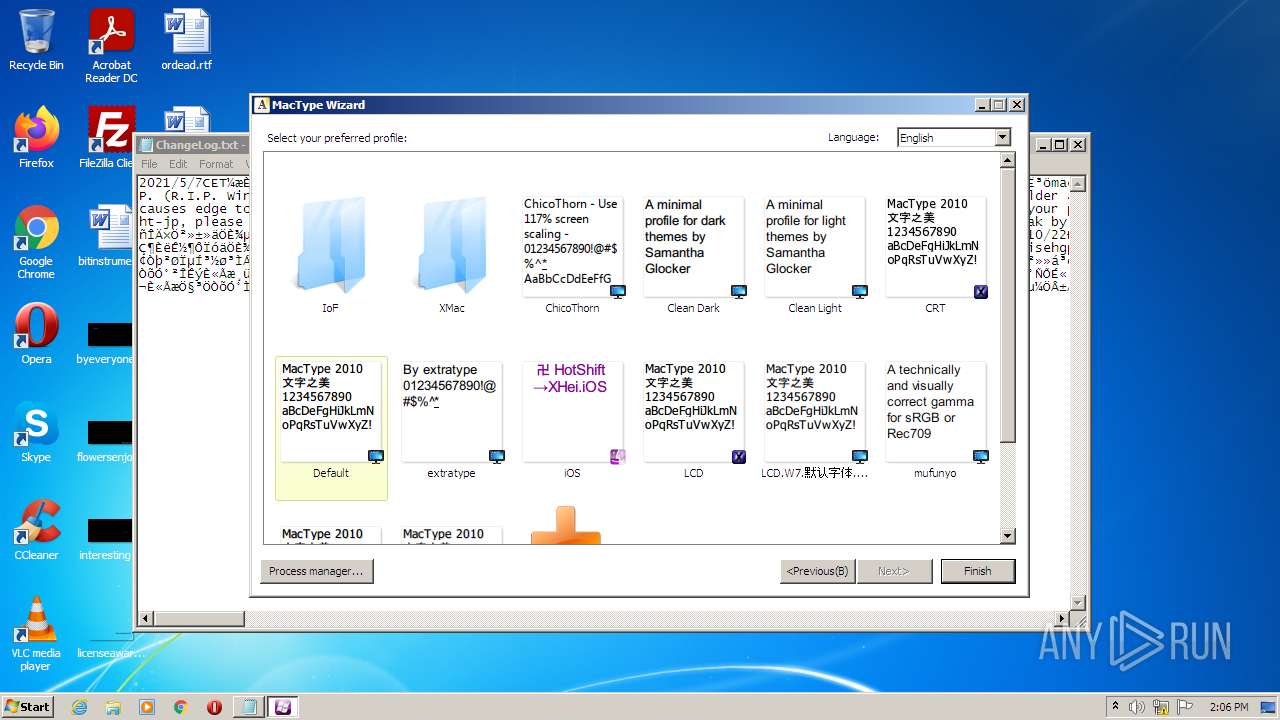
| 1128 | "C:\Program Files\MacType\MacWiz.exe" | C:\Program Files\MacType\MacWiz.exe | — | MacTypeInstaller_2021.1-rc1.tmp | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1128 | "sc" delete mactype | C:\Windows\system32\sc.exe | — | MacTypeInstaller_2021.1-rc1.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1392 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1912 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1968 | "C:\Program Files\MacType\MacTray.exe" -service | C:\Program Files\MacType\MacTray.exe | — | services.exe | |||||||||||
User: SYSTEM Company: FlyingSnow Integrity Level: SYSTEM Description: MacType Exit code: 0 Version: 1.0.2021.1 Modules
| |||||||||||||||
Total events
5 207
Read events
5 116
Write events
83
Delete events
8
Modification events
| (PID) Process: | (2016) MacTypeInstaller_2021.1-rc1.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: E0070000A0CDE952883FD801 | |||
| (PID) Process: | (2016) MacTypeInstaller_2021.1-rc1.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: D5E05CD98041424076E6401F16AB5BD87D786945C0CB1C0B3ADB0C5404D68390 | |||
| (PID) Process: | (2016) MacTypeInstaller_2021.1-rc1.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2016) MacTypeInstaller_2021.1-rc1.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\MacType\GdiBench.exe | |||
| (PID) Process: | (2016) MacTypeInstaller_2021.1-rc1.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 662EE8521B6B3E524CFC7F74D4396169ECBDF4414600F59CB26383677980D97C | |||
| (PID) Process: | (2016) MacTypeInstaller_2021.1-rc1.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{724A2991-CC38-4DD4-B9B4-E30BECA5ED90}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.6.1 (u) | |||
| (PID) Process: | (2016) MacTypeInstaller_2021.1-rc1.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{724A2991-CC38-4DD4-B9B4-E30BECA5ED90}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\MacType | |||
| (PID) Process: | (2016) MacTypeInstaller_2021.1-rc1.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{724A2991-CC38-4DD4-B9B4-E30BECA5ED90}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\MacType\ | |||
| (PID) Process: | (2016) MacTypeInstaller_2021.1-rc1.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{724A2991-CC38-4DD4-B9B4-E30BECA5ED90}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: MacType | |||
| (PID) Process: | (2016) MacTypeInstaller_2021.1-rc1.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{724A2991-CC38-4DD4-B9B4-E30BECA5ED90}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
Executable files
32
Suspicious files
0
Text files
167
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2016 | MacTypeInstaller_2021.1-rc1.tmp | C:\Program Files\MacType\GdiBench.exe | executable | |
MD5:A826E9276BC7F96843337D0394690BC8 | SHA256:7ACA54E301DBA9AC0862A82A89EED827EB6C54DFE415892D92F68C07A9EE2F7B | |||
| 4084 | MacTypeInstaller_2021.1-rc1.exe | C:\Users\admin\AppData\Local\Temp\is-CBEPS.tmp\MacTypeInstaller_2021.1-rc1.tmp | executable | |
MD5:65B379EC022CBC22DA0DEF3819E6F821 | SHA256:8D8F72D08E18043DC2932352588AFB4B1229A10534F975CFF53A322451AA1061 | |||
| 2016 | MacTypeInstaller_2021.1-rc1.tmp | C:\Program Files\MacType\is-SQG1G.tmp | executable | |
MD5:02975795B73944E98584B41BE8805262 | SHA256:93A3844D1423974594A076C136510E567FD8088D1C7D3BC6E36139B8DF0E2AAA | |||
| 2016 | MacTypeInstaller_2021.1-rc1.tmp | C:\Program Files\MacType\is-6VGFM.tmp | text | |
MD5:89A2CDC2C94639CC60AA9986BC758710 | SHA256:A0A38BA7779999A477F86E387EAEE26982B6667A4A601231EB0E17A9D7189E66 | |||
| 2016 | MacTypeInstaller_2021.1-rc1.tmp | C:\Program Files\MacType\is-Q9BNL.tmp | executable | |
MD5:A826E9276BC7F96843337D0394690BC8 | SHA256:7ACA54E301DBA9AC0862A82A89EED827EB6C54DFE415892D92F68C07A9EE2F7B | |||
| 2016 | MacTypeInstaller_2021.1-rc1.tmp | C:\Program Files\MacType\MacTuner.exe | executable | |
MD5:D0522A146494C7FFF0CBD009777E7F5E | SHA256:3D163BF8DD63D2BE49D5F760399170584A0C577A59A89BFB5077FD143944374F | |||
| 2016 | MacTypeInstaller_2021.1-rc1.tmp | C:\Program Files\MacType\gb.txt | text | |
MD5:381F3462A060B51FDEA26787B6FB9E57 | SHA256:4F922F4FA594B843928C949C66883A5F005E40957D047EDD1ED1069AA9EAF312 | |||
| 2016 | MacTypeInstaller_2021.1-rc1.tmp | C:\Program Files\MacType\is-UGFUE.tmp | executable | |
MD5:10CF2935A1EA25CF583E7B35CC693F04 | SHA256:FE14F4EA746ADBA78586D96132366BA1FFB1BEEF41E30BFDD992D6C62CB01CAB | |||
| 2016 | MacTypeInstaller_2021.1-rc1.tmp | C:\Program Files\MacType\is-NM4TI.tmp | text | |
MD5:7F91F37664B10EBC956F50DE134EED2E | SHA256:633AB51574452A31D24D7A7517F895C98FE6CC8CDD0450C8BC1DACF5950FEA6F | |||
| 2016 | MacTypeInstaller_2021.1-rc1.tmp | C:\Program Files\MacType\MacTray.exe | executable | |
MD5:D3BDF8DDC47013AAE75BB7FDF515F75D | SHA256:69FE01F0FBDFD312C9C63E46610CD98AD5778EA3B437A22A71C552E7FBBB7233 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report