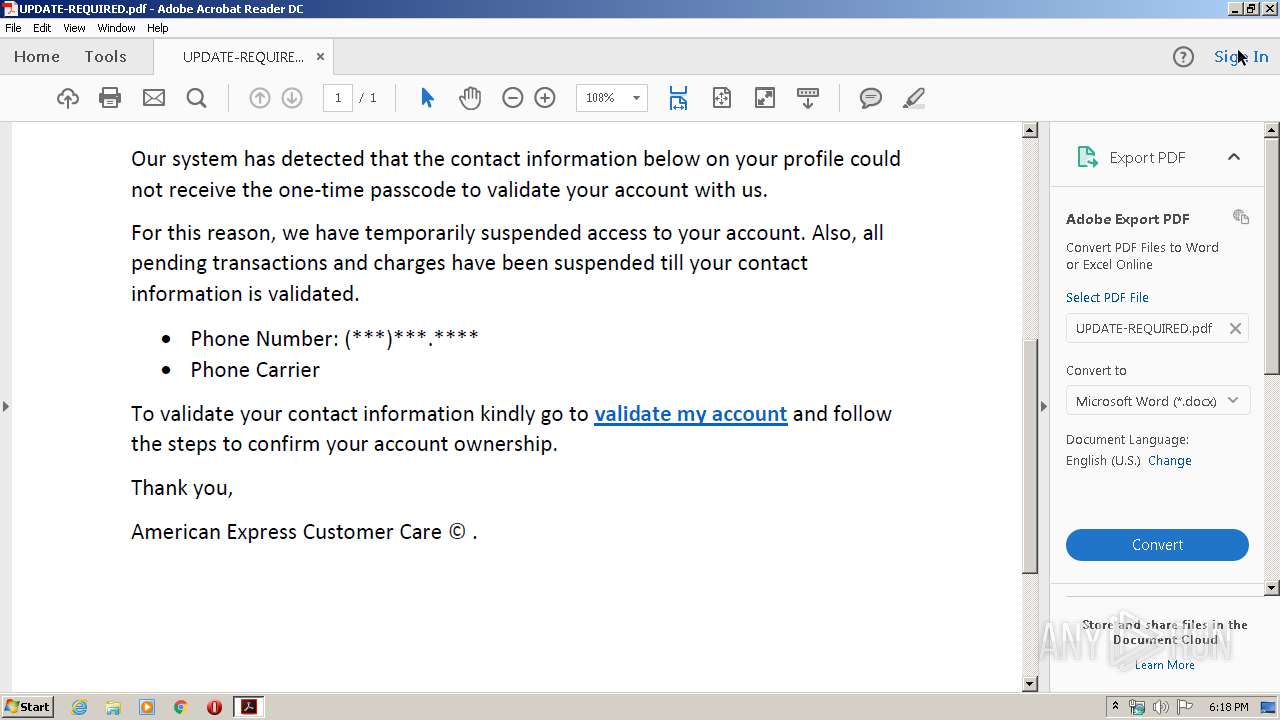
| File name: | UPDATE-REQUIRED.pdf |
| Full analysis: | https://app.any.run/tasks/c1a28b94-25d5-4344-af53-c5432a291478 |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 17:17:41 |
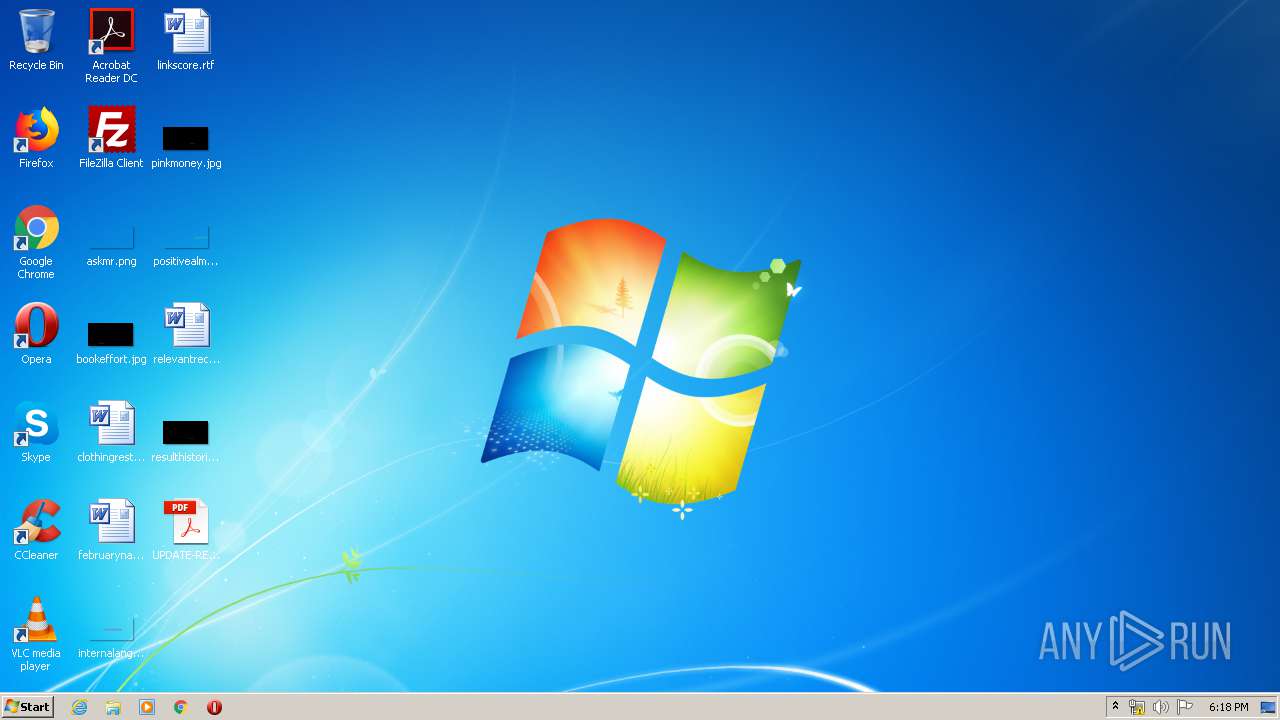
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/pdf |
| File info: | PDF document, version 1.7 |
| MD5: | 47121F9D02502586D95E093907CBEA19 |
| SHA1: | 8304520B9A34AC2AB694E0B74E4D4C7DFE70E40A |
| SHA256: | 3A615037E80B691103894D5ED4AADC1130732106E586AEF791380405B21DDE7B |
| SSDEEP: | 1536:sMFQj9dTjdZg2wMAOt7lSnhLM8khJV+hMWGmCnqalHfQjP2jr/cEMuXIgep:/QBldCZOtInrkjVPWMn5lr/jX2 |
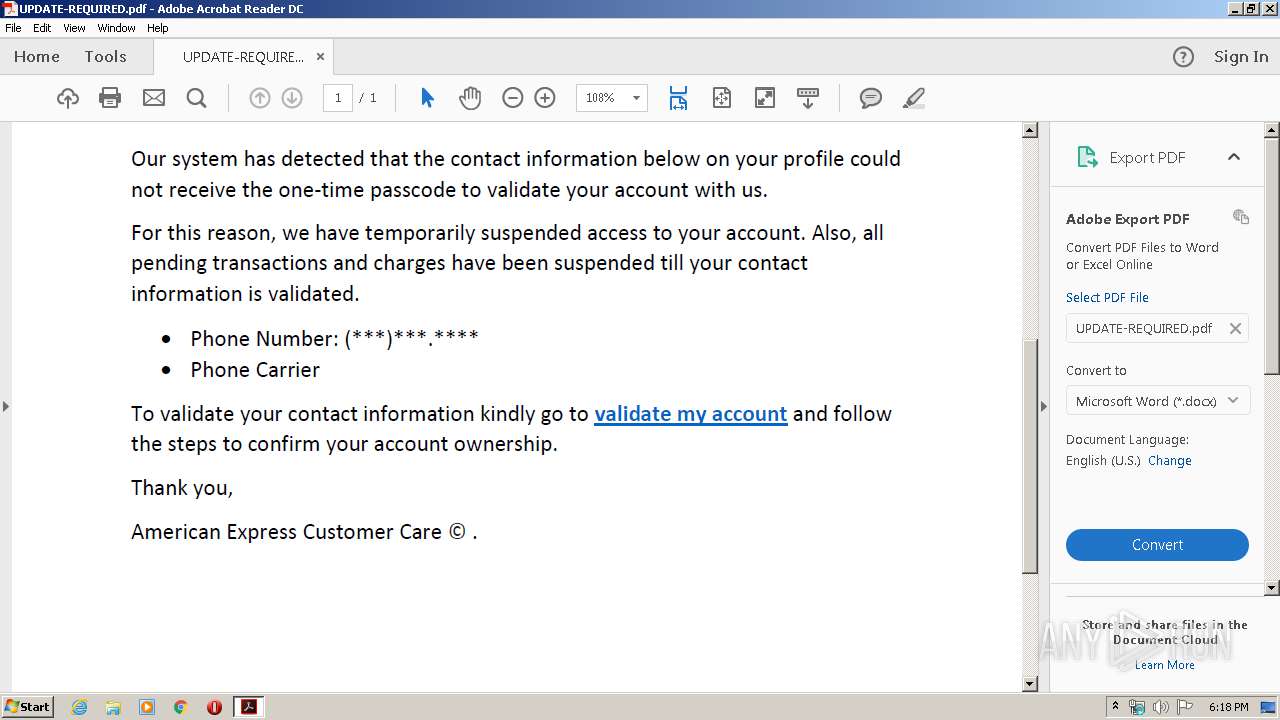
MALICIOUS
No malicious indicators.SUSPICIOUS
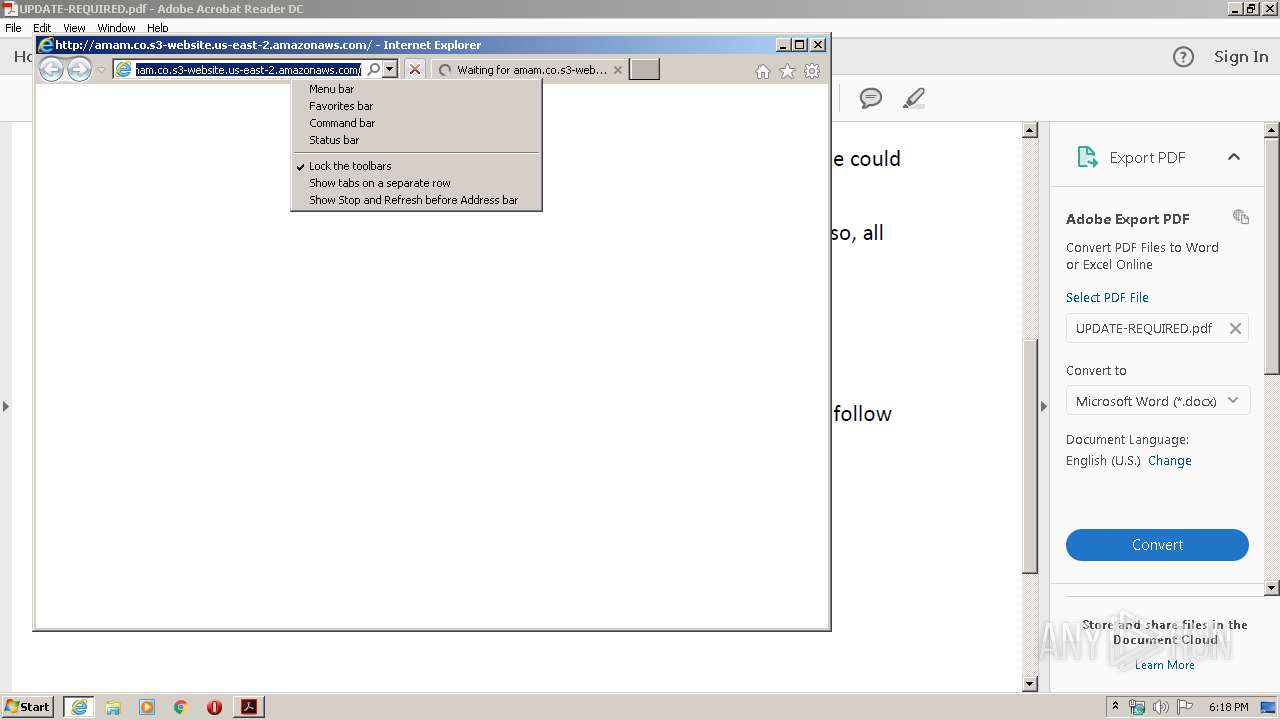
Changes IE settings (feature browser emulation)
- AcroRd32.exe (PID: 3076)
Starts Internet Explorer
- AcroRd32.exe (PID: 3076)
INFO
Application launched itself
- RdrCEF.exe (PID: 3984)
- iexplore.exe (PID: 2528)
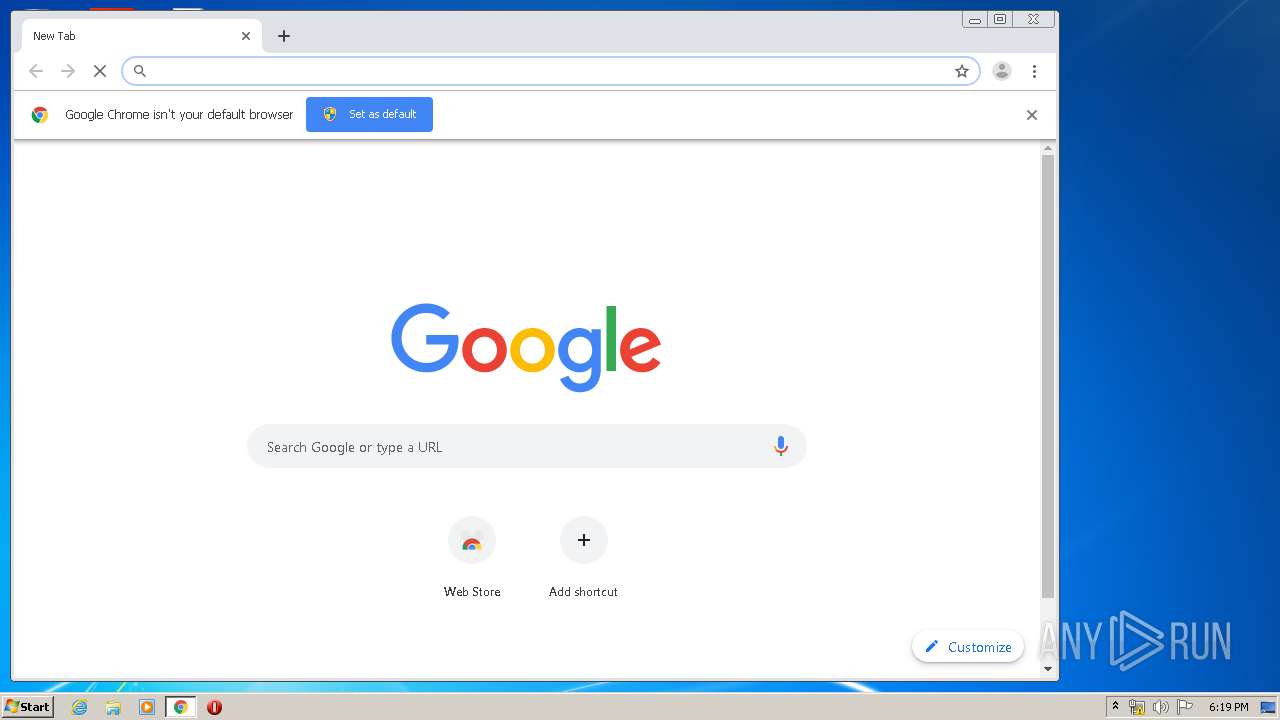
- chrome.exe (PID: 2808)
Reads the hosts file
- RdrCEF.exe (PID: 3984)
- chrome.exe (PID: 3924)
- chrome.exe (PID: 2808)
Reads Internet Cache Settings
- AcroRd32.exe (PID: 3076)
- AcroRd32.exe (PID: 2748)
- iexplore.exe (PID: 2528)
- iexplore.exe (PID: 952)
- iexplore.exe (PID: 2608)
- iexplore.exe (PID: 576)
Reads settings of System Certificates
- AcroRd32.exe (PID: 3076)
- iexplore.exe (PID: 2528)
Changes internet zones settings
- iexplore.exe (PID: 2528)
- iexplore.exe (PID: 2608)
Reads internet explorer settings
- iexplore.exe (PID: 952)
- iexplore.exe (PID: 576)
Creates files in the user directory
- AcroRd32.exe (PID: 3076)
Manual execution by user
- chrome.exe (PID: 2808)
Changes settings of System certificates
- iexplore.exe (PID: 2528)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2528)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| | | Adobe Portable Document Format (100) |
EXIF
| PDFVersion: | 1.7 |
|---|---|
| Linearized: | No |
| PageCount: | 1 |
| Language: | en-US |
| TaggedPDF: | Yes |
| Author: | Rohan Poddar |
| Creator: | Microsoft Word |
| CreateDate: | 2020:03:28 13:03:52-07:00 |
| ModifyDate: | 2020:03:28 13:03:52-07:00 |
XMP
| XMPToolkit: | 3.1-701 |
|---|---|
| Creator: | Rohan Poddar |
| CreatorTool: | Microsoft Word |
| CreateDate: | 2020:03:28 13:03:52-07:00 |
| ModifyDate: | 2020:03:28 13:03:52-07:00 |
| DocumentID: | uuid:47397D74-6FDE-466A-95BF-ABBD4707C468 |
| InstanceID: | uuid:47397D74-6FDE-466A-95BF-ABBD4707C468 |
Total processes
72
Monitored processes
35
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 576 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2608 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,5387242210614205630,5698456233666166549,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11704344923135628898 --mojo-platform-channel-handle=3948 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2528 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,5387242210614205630,5698456233666166549,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14654763074846113640 --mojo-platform-channel-handle=4160 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,5387242210614205630,5698456233666166549,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12702468962747500383 --mojo-platform-channel-handle=1004 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,5387242210614205630,5698456233666166549,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9369521404216274170 --mojo-platform-channel-handle=3764 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="3984.1.619837126\1132251628" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 1844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,5387242210614205630,5698456233666166549,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16385034677827252967 --mojo-platform-channel-handle=2484 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,5387242210614205630,5698456233666166549,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13699565256084980529 --mojo-platform-channel-handle=4492 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,5387242210614205630,5698456233666166549,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2094458217561604775 --mojo-platform-channel-handle=4112 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 365
Read events
781
Write events
1 797
Delete events
787
Modification events
| (PID) Process: | (2748) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (2748) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral |
| Operation: | write | Name: | bExpandRHPInViewer |
Value: 1 | |||
| (PID) Process: | (2748) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\NoTimeOut |
| Operation: | write | Name: | smailto |
Value: 5900 | |||
| (PID) Process: | (3076) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | AcroRd32.exe |
Value: 10001 | |||
| (PID) Process: | (3076) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | aFS |
Value: DOS | |||
| (PID) Process: | (3076) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | tDIText |
Value: /C/Users/admin/Desktop/UPDATE-REQUIRED.pdf | |||
| (PID) Process: | (3076) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | tFileName |
Value: UPDATE-REQUIRED.pdf | |||
| (PID) Process: | (3076) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | tFileSource |
Value: local | |||
| (PID) Process: | (3076) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | sFileAncestors |
Value: 5B5D00 | |||
| (PID) Process: | (3076) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral\cRecentFiles\c1 |
| Operation: | write | Name: | sDI |
Value: 2F432F55736572732F61646D696E2F4465736B746F702F5550444154452D52455155495245442E70646600 | |||
Executable files
0
Suspicious files
31
Text files
159
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2748 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 2748 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1bknitk_10t0bff_24c.tmp | — | |
MD5:— | SHA256:— | |||
| 2748 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R14fo7ao_10t0bfg_24c.tmp | — | |
MD5:— | SHA256:— | |||
| 2748 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rfppx84_10t0bfh_24c.tmp | — | |
MD5:— | SHA256:— | |||
| 2748 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rerb9j2_10t0bfi_24c.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\Cab92F1.tmp | — | |
MD5:— | SHA256:— | |||
| 3076 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\Tar92F2.tmp | — | |
MD5:— | SHA256:— | |||
| 2528 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2528 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFBED53286138400D0.TMP | — | |
MD5:— | SHA256:— | |||
| 2528 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF2B0DF4E6F7C7AA9A.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
40
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3076 | AcroRd32.exe | GET | 304 | 23.55.110.79:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | US | — | — | whitelisted |
3076 | AcroRd32.exe | GET | 304 | 23.55.110.79:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/278_15_23_20070.zip | US | — | — | whitelisted |
3924 | chrome.exe | GET | — | 159.148.69.142:80 | http://r3---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=bs&mip=159.148.186.246&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1585588696&mv=m&mvi=2&pl=24&shardbypass=yes | LV | — | — | whitelisted |
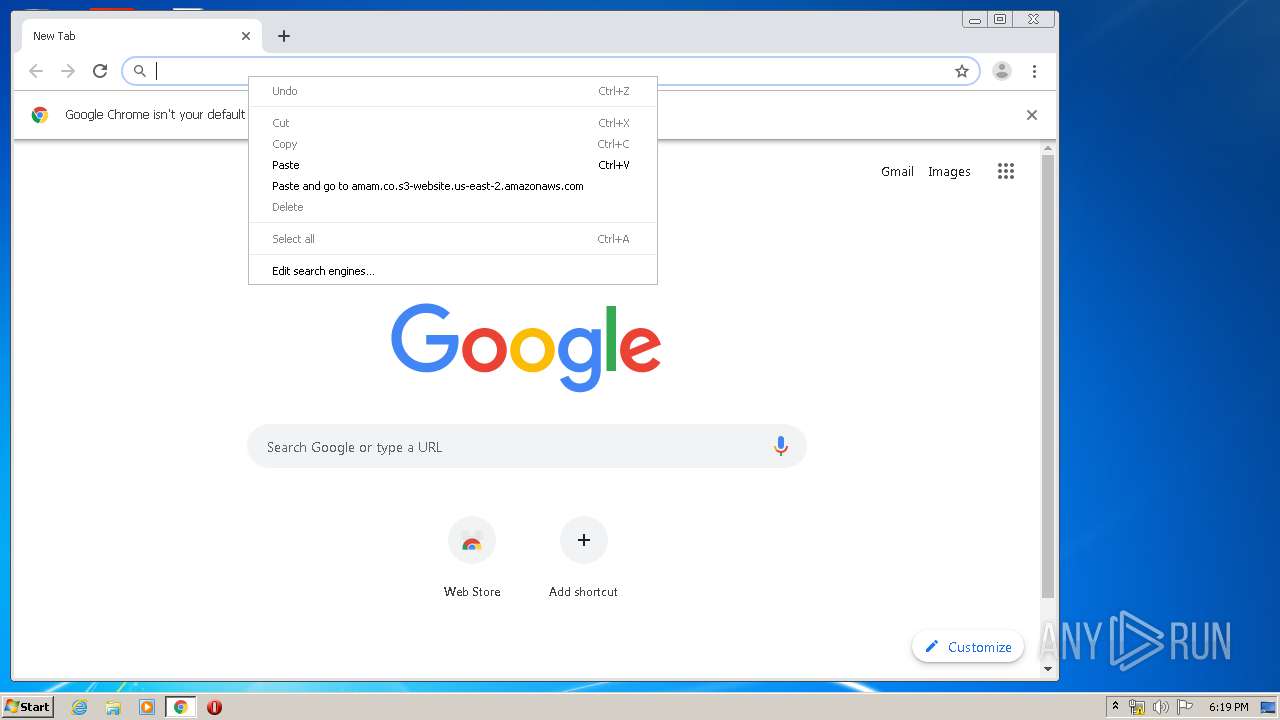
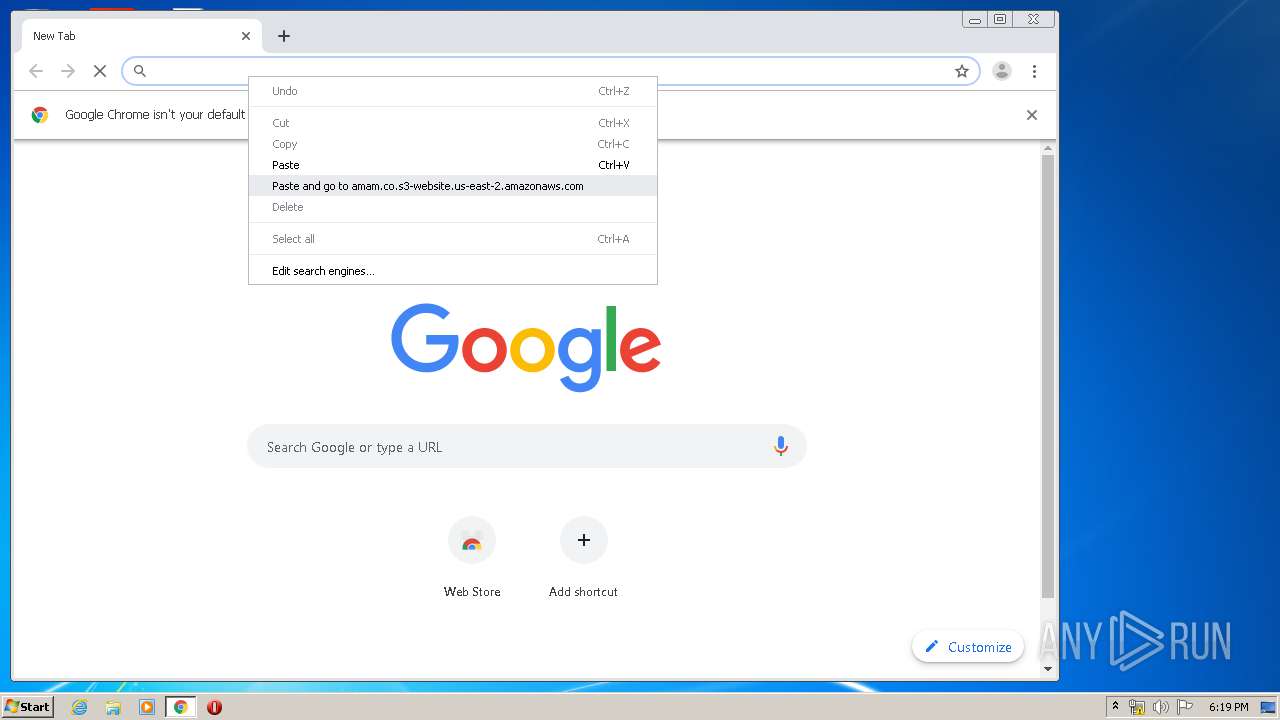
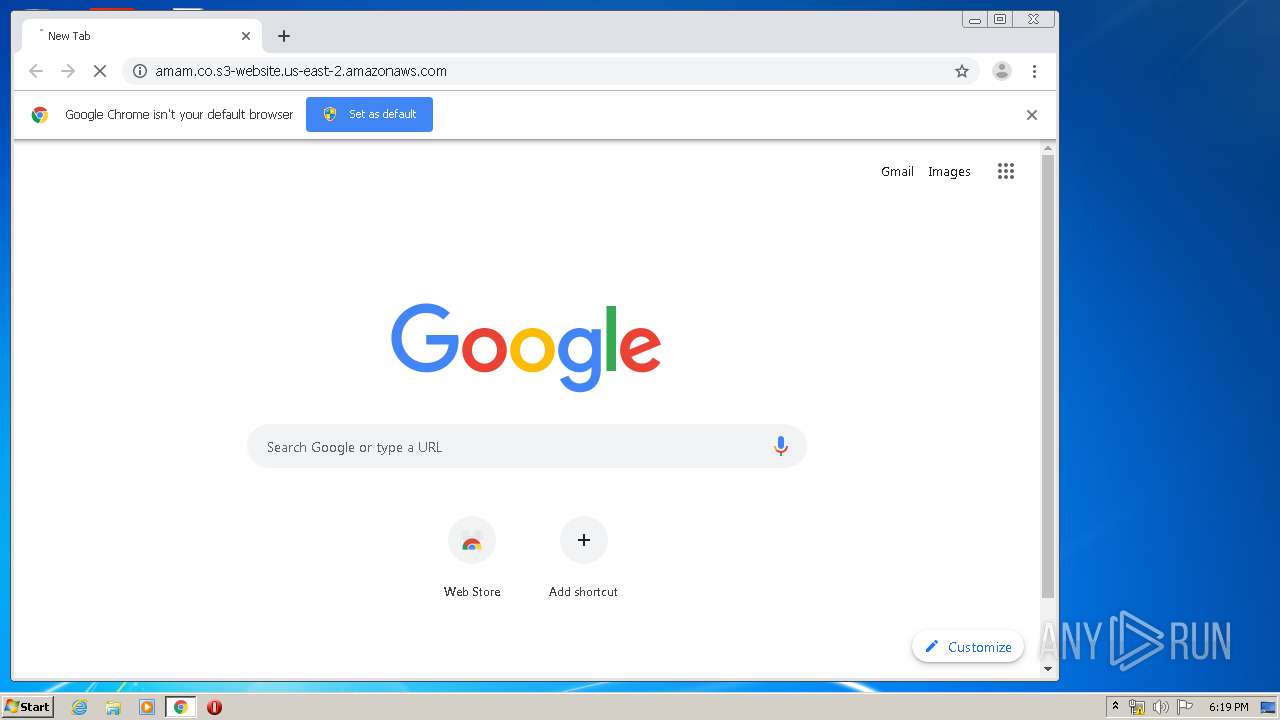
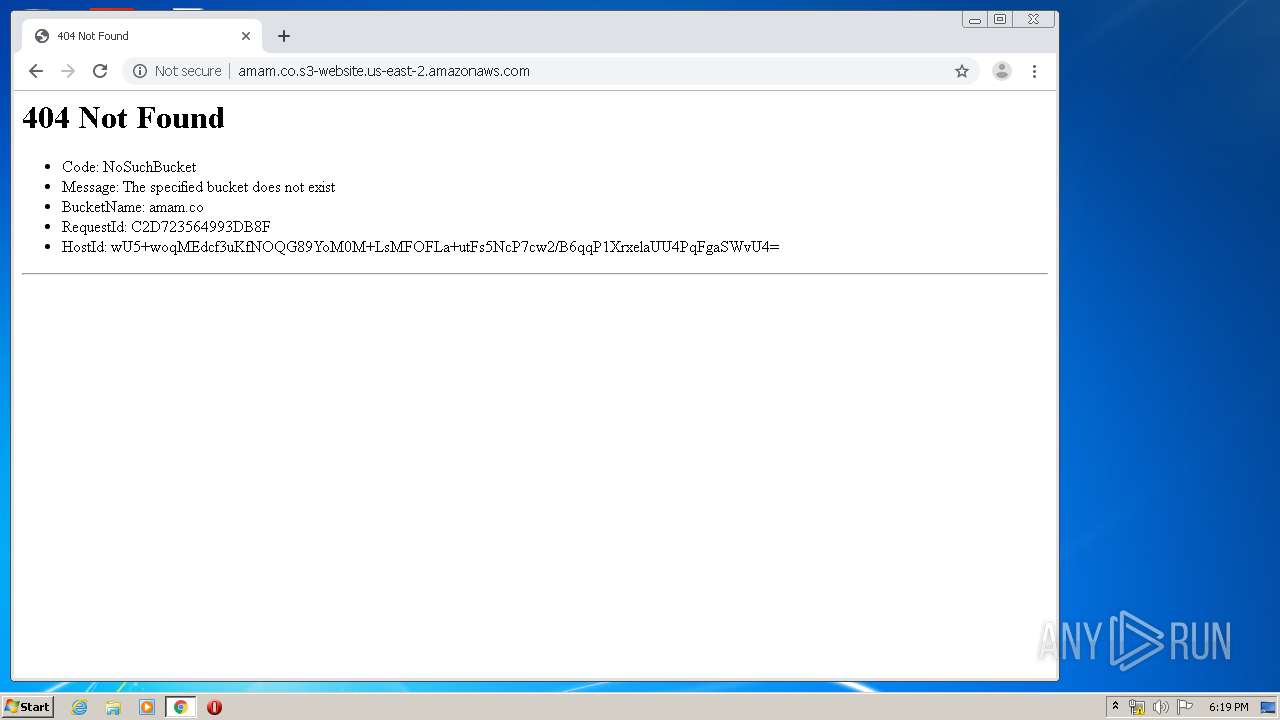
3924 | chrome.exe | GET | 404 | 52.219.88.44:80 | http://amam.co.s3-website.us-east-2.amazonaws.com/ | US | html | 354 b | shared |
3076 | AcroRd32.exe | GET | 304 | 23.55.110.79:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | US | — | — | whitelisted |
3076 | AcroRd32.exe | GET | 304 | 23.55.110.79:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | US | — | — | whitelisted |
3076 | AcroRd32.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3924 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 527 b | whitelisted |
3924 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 532 b | whitelisted |
3076 | AcroRd32.exe | GET | 200 | 23.55.110.79:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | US | compressed | 9.54 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3076 | AcroRd32.exe | 23.55.110.79:80 | acroipm2.adobe.com | NTT America, Inc. | US | suspicious |
3076 | AcroRd32.exe | 23.210.248.251:443 | armmf.adobe.com | Akamai International B.V. | NL | whitelisted |
3076 | AcroRd32.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 23.210.248.251:443 | armmf.adobe.com | Akamai International B.V. | NL | whitelisted |
952 | iexplore.exe | 52.219.80.4:80 | amam.co.s3-website.us-east-2.amazonaws.com | Amazon.com, Inc. | US | shared |
2528 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3924 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
576 | iexplore.exe | 52.219.84.20:80 | amam.co.s3-website.us-east-2.amazonaws.com | Amazon.com, Inc. | US | shared |
2528 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3924 | chrome.exe | 216.58.207.35:443 | www.google.com.ua | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
amam.co.s3-website.us-east-2.amazonaws.com |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |