| File name: | 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader |
| Full analysis: | https://app.any.run/tasks/e5d43b03-ea03-464e-b59f-1bee8ade5425 |
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 01:43:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | C267563B7277F1B8C9878856FC7B133A |
| SHA1: | 3E33ADC32A9AC597C1078C8993E9075FD42BD3B2 |
| SHA256: | 3A2CF2699CE77D4A1305D64A8B722E47F01D04FE3D1C4D29C0FACC563F0C1489 |
| SSDEEP: | 98304:iefUuZuKAuf5jTFPkOefUuZuKAuf5jTFrkHVrGDYwOwjefUuZuKAuf5jTFPkOefq:V |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5640)
- UpdatAuto.exe (PID: 4896)
Starts a Microsoft application from unusual location
- 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5640)
- 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 668)
Executing commands from a ".bat" file
- 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5640)
- UpdatAuto.exe (PID: 4896)
Starts itself from another location
- 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5640)
Starts CMD.EXE for commands execution
- 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5640)
- UpdatAuto.exe (PID: 4896)
Executable content was dropped or overwritten
- 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5640)
- UpdatAuto.exe (PID: 4896)
Creates file in the systems drive root
- UpdatAuto.exe (PID: 4896)
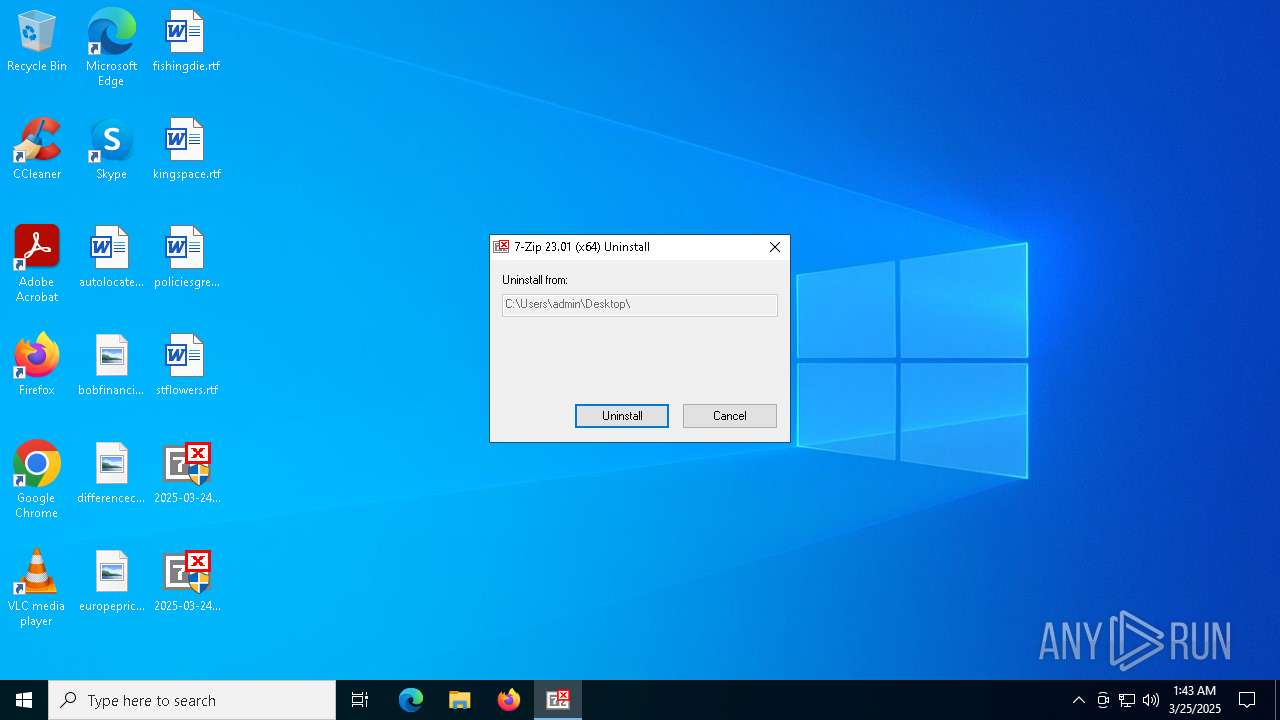
Drops 7-zip archiver for unpacking
- 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5640)
INFO
The sample compiled with chinese language support
- 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5640)
- UpdatAuto.exe (PID: 4896)
Checks supported languages
- 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5640)
- UpdatAuto.exe (PID: 4896)
- 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 2504)
Create files in a temporary directory
- 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5640)
- UpdatAuto.exe (PID: 4896)
The sample compiled with english language support
- 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5640)
Reads the computer name
- 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 2504)
Creates files in the program directory
- UpdatAuto.exe (PID: 4896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (63.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (24.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.1) |
| .exe | | | Win32 Executable (generic) (3.5) |
| .exe | | | Generic Win/DOS Executable (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:03:12 04:30:52+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 102400 |
| InitializedDataSize: | 16384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x27dc |
| OSVersion: | 4 |
| ImageVersion: | 6.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.1.0.0 |
| ProductVersionNumber: | 6.1.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| Comments: | Windows Update Manager for NT |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Windows Update Manager for NT |
| LegalCopyright: | Copyright (C) Microsoft Corp. 1981-1999 |
| ProductName: | Microsoft(R) Windows (R) 2000 Operating System |
| FileVersion: | 6.01 |
| ProductVersion: | 6.01 |
| InternalName: | INCUBUS |
| OriginalFileName: | INCUBUS.exe |
Total processes
130
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Users\admin\Desktop\2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe" | C:\Users\admin\Desktop\2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Manager for NT Exit code: 3221226540 Version: 6.01 Modules
| |||||||||||||||
| 2504 | 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe | C:\Users\admin\Desktop\2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe | — | 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Uninstaller Version: 23.01 Modules
| |||||||||||||||
| 4380 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4400 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4896 | C:\WINDOWS\system32\UpdatAuto.exe | C:\Windows\SysWOW64\UpdatAuto.exe | 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Manager for NT Version: 6.01 Modules
| |||||||||||||||
| 5404 | C:\WINDOWS\system32\cmd.exe /c C:\WINDOWS\system32\Option.bat | C:\Windows\SysWOW64\cmd.exe | — | 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5640 | "C:\Users\admin\Desktop\2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe" | C:\Users\admin\Desktop\2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Update Manager for NT Version: 6.01 Modules
| |||||||||||||||
| 6744 | C:\WINDOWS\system32\cmd.exe /c C:\WINDOWS\system32\Option.bat | C:\Windows\SysWOW64\cmd.exe | — | UpdatAuto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7144 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
216
Read events
216
Write events
0
Delete events
0
Modification events
Executable files
12
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4896 | UpdatAuto.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\CRLogTransport.exe | — | |
MD5:— | SHA256:— | |||
| 4896 | UpdatAuto.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\CRWindowsClientService.exe | — | |
MD5:— | SHA256:— | |||
| 4896 | UpdatAuto.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Eula.exe | — | |
MD5:— | SHA256:— | |||
| 4896 | UpdatAuto.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\LogTransport2.exe | — | |
MD5:— | SHA256:— | |||
| 5640 | 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe | C:\Windows\SysWOW64\Option.bat | text | |
MD5:1D04ABF39E9DF55EED1D04430CC21EB8 | SHA256:0BC485263CF8A962E64DB0B88F156F2A9AF1B81ECFDB1CF9111D497E85DF70F3 | |||
| 4896 | UpdatAuto.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\AcroBroker.exe | executable | |
MD5:A5D22FB559F779EA6B1A67313D9BF64A | SHA256:D9F1B6E47E76FBA85BC032A48313DBC29CDC9C3C74E3F86E7D5BE6B267DF1A93 | |||
| 5640 | 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe | C:\ntldr~8 | executable | |
MD5:1A66531EB30EE7846EB97090007A9A27 | SHA256:3DBB01E3F008F342F50AC18E2718A1EA021F85A5B5D9E75BDBC174002CAC292A | |||
| 4896 | UpdatAuto.exe | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe | executable | |
MD5:2F5EB9FBEB44CF8869A101494DE83953 | SHA256:D2785DB54F906E8956AF3ED0F352EF269A4453D195B698C283B7239B266BA812 | |||
| 5640 | 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe | C:\Windows\SysWOW64\UpdatAuto.exe | executable | |
MD5:1A66531EB30EE7846EB97090007A9A27 | SHA256:3DBB01E3F008F342F50AC18E2718A1EA021F85A5B5D9E75BDBC174002CAC292A | |||
| 5640 | 2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe | C:\Users\admin\Desktop\2025-03-24_c267563b7277f1b8c9878856fc7b133a_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe | executable | |
MD5:76660DBC461F5A98F4955A3E9B706614 | SHA256:DA73B7308AA0BE1A92BA273252B8BA6BE2CE8B0289BD663E6547DAAA433097BE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
18
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
660 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |