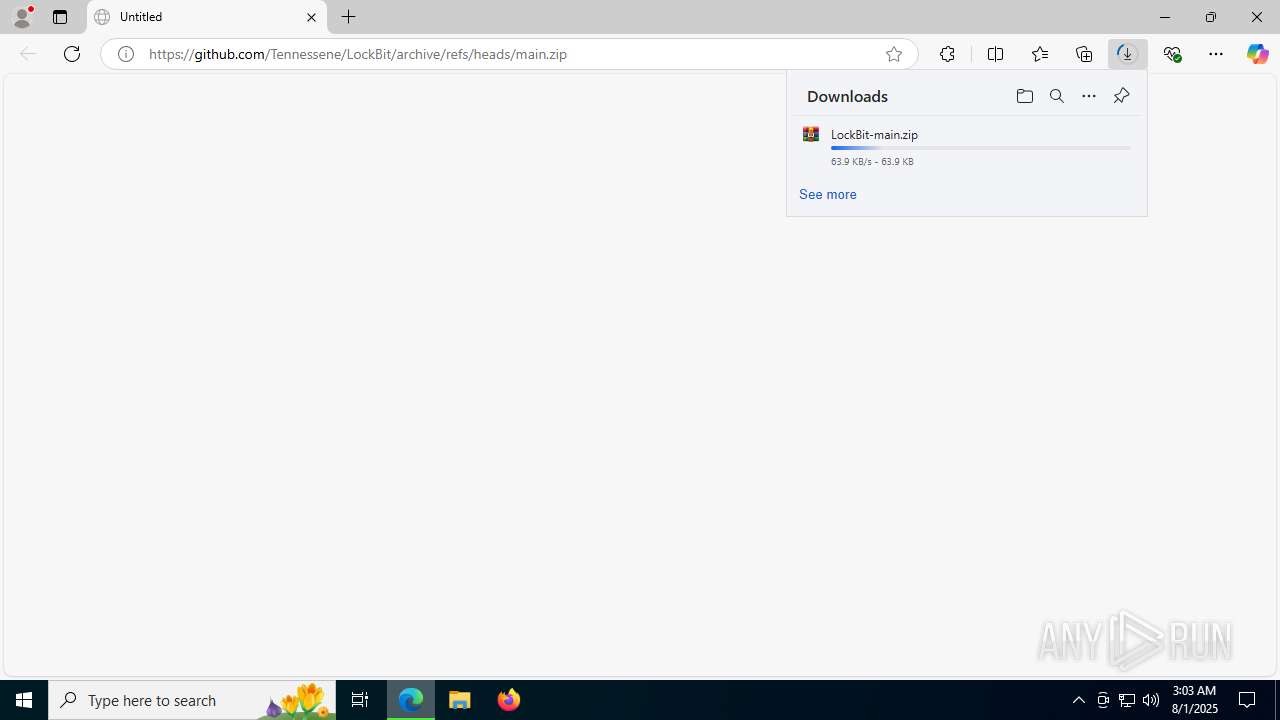
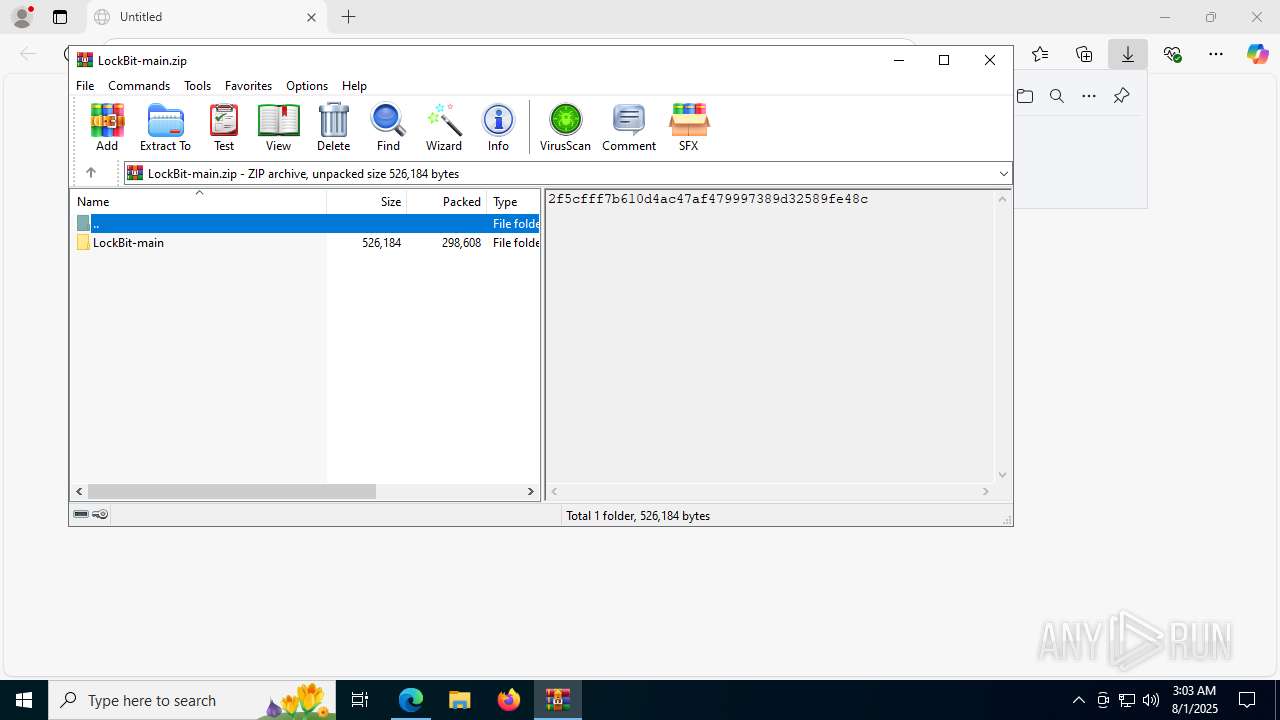
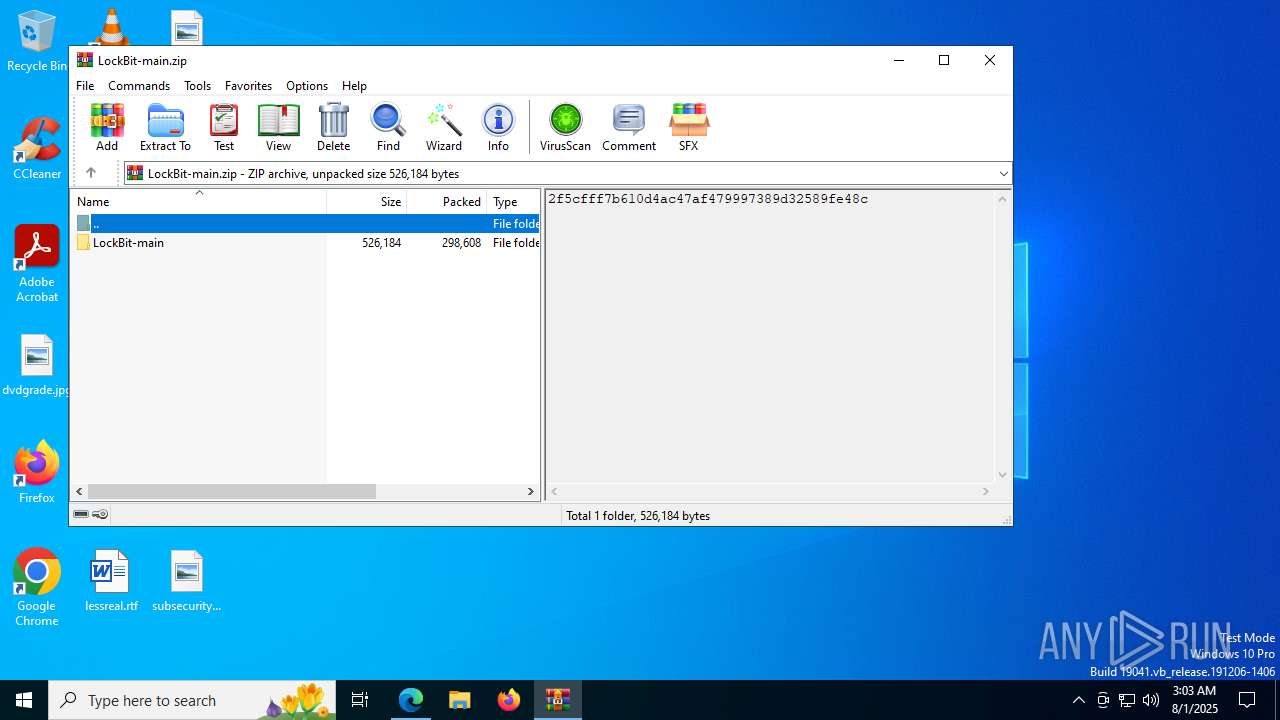
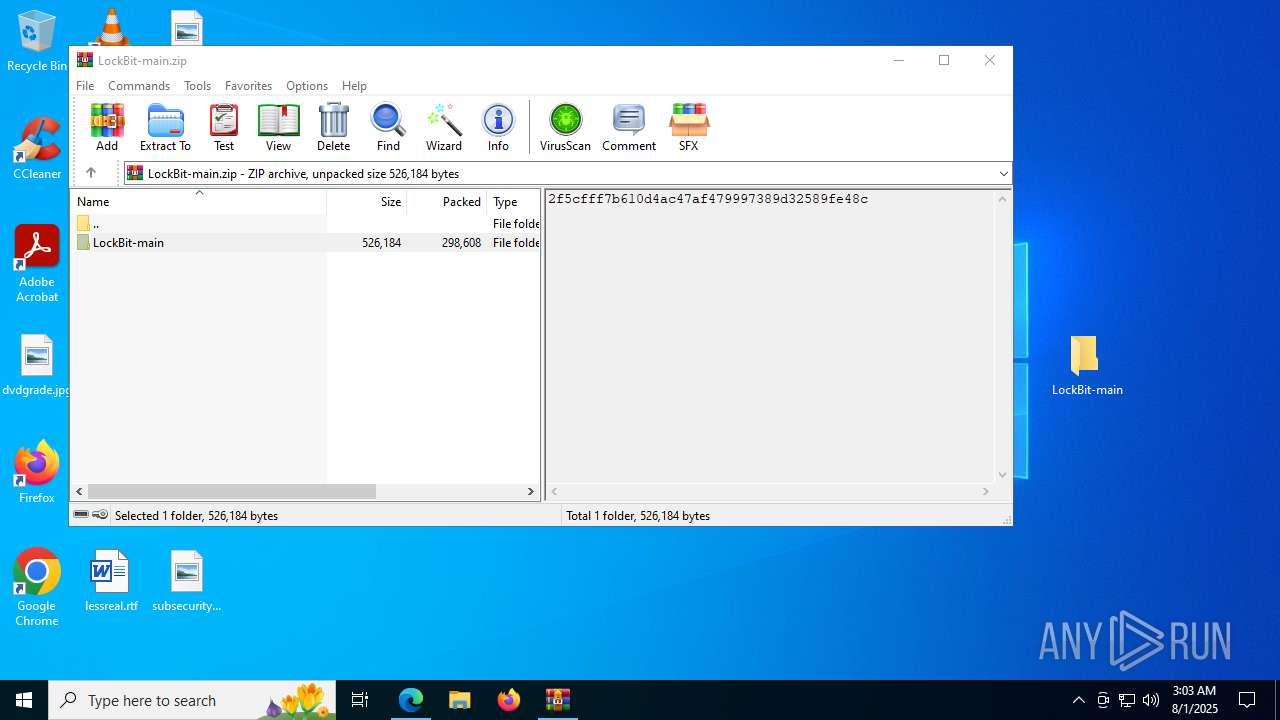
| URL: | https://github.com/Tennessene/LockBit/archive/refs/heads/main.zip |
| Full analysis: | https://app.any.run/tasks/7979b635-0122-41cc-b407-2a3d9ffa8eb5 |
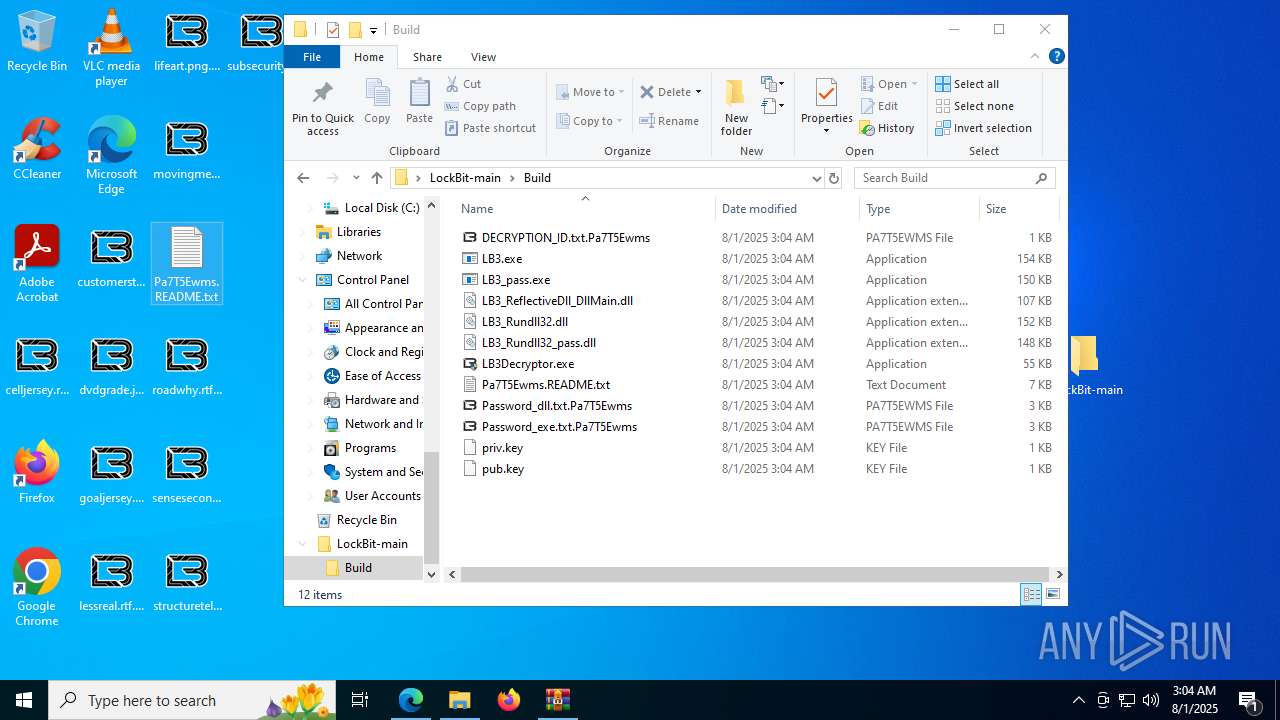
| Verdict: | Malicious activity |
| Threats: | LockBit, a ransomware variant, encrypts data on infected machines, demanding a ransom payment for decryption. Used in targeted attacks, It's a significant risk to organizations. |
| Analysis date: | August 01, 2025, 03:03:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 231CBE9B705645E8C06828BFA6EAB7F5 |
| SHA1: | 42CABD2FBF9B6152364FD8683477C1AED30B41F2 |
| SHA256: | 3A195BBF85B46DA9FE7DE57734105F0FD6DEBE4E5B1464E43F2F78BA7C5F42D7 |
| SSDEEP: | 3:N8tEdsLzTPIfEXz4RSLNLc:2ueLfI2z4ULN4 |
MALICIOUS
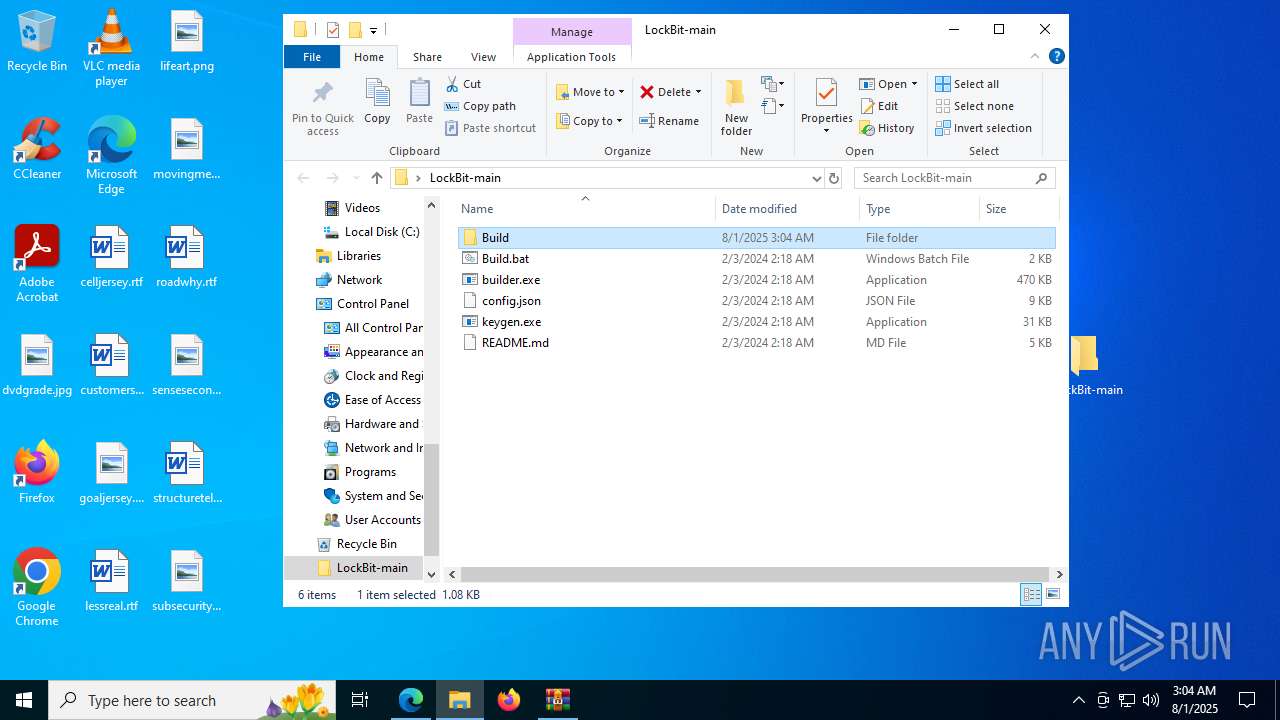
Known privilege escalation attack
- dllhost.exe (PID: 4084)
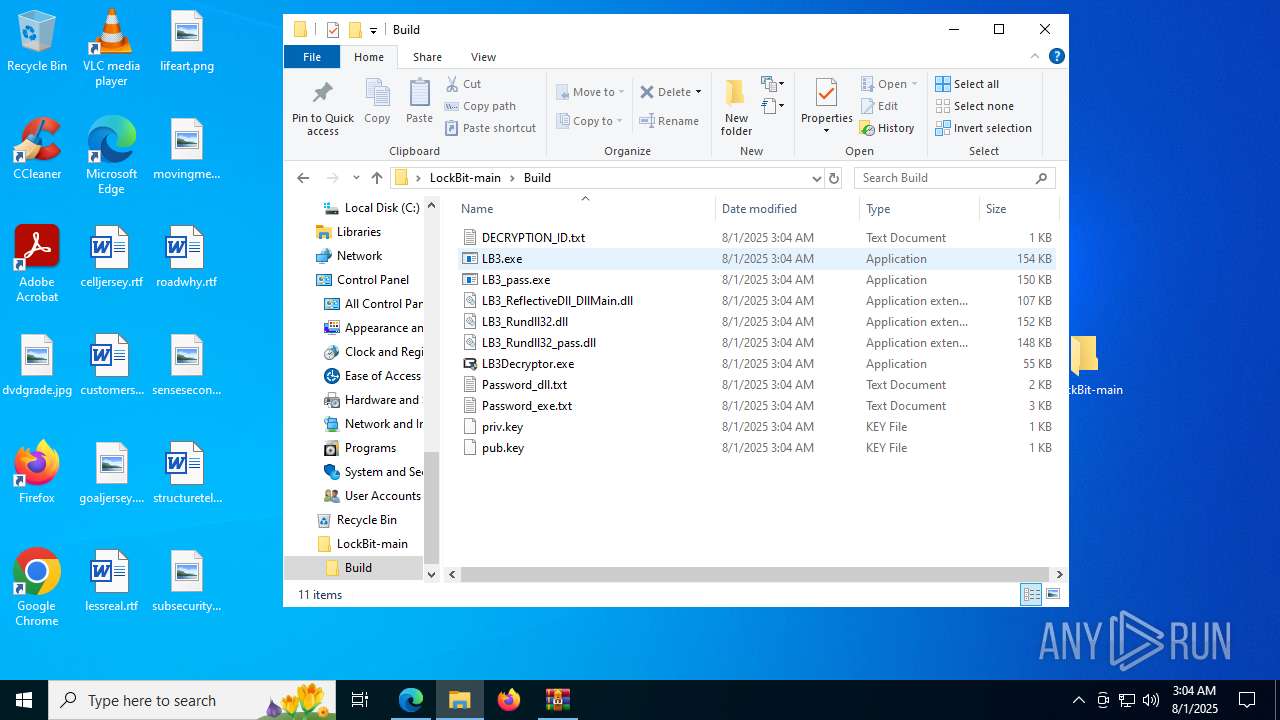
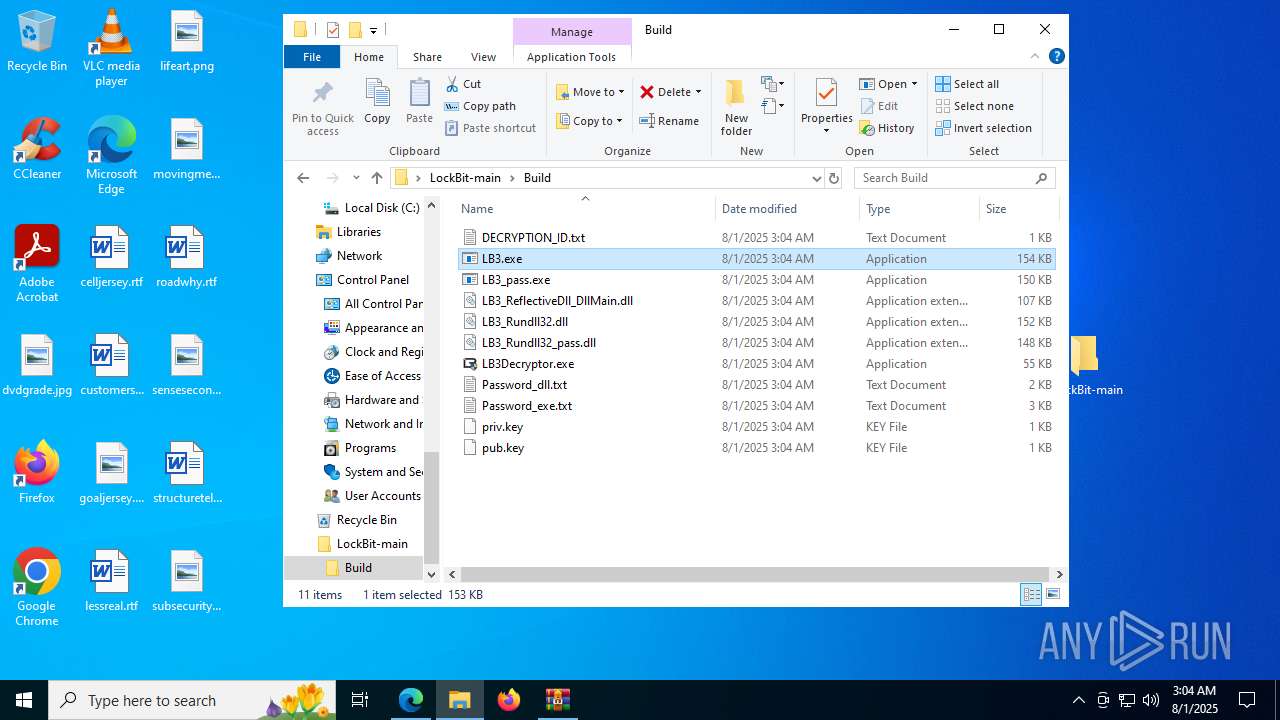
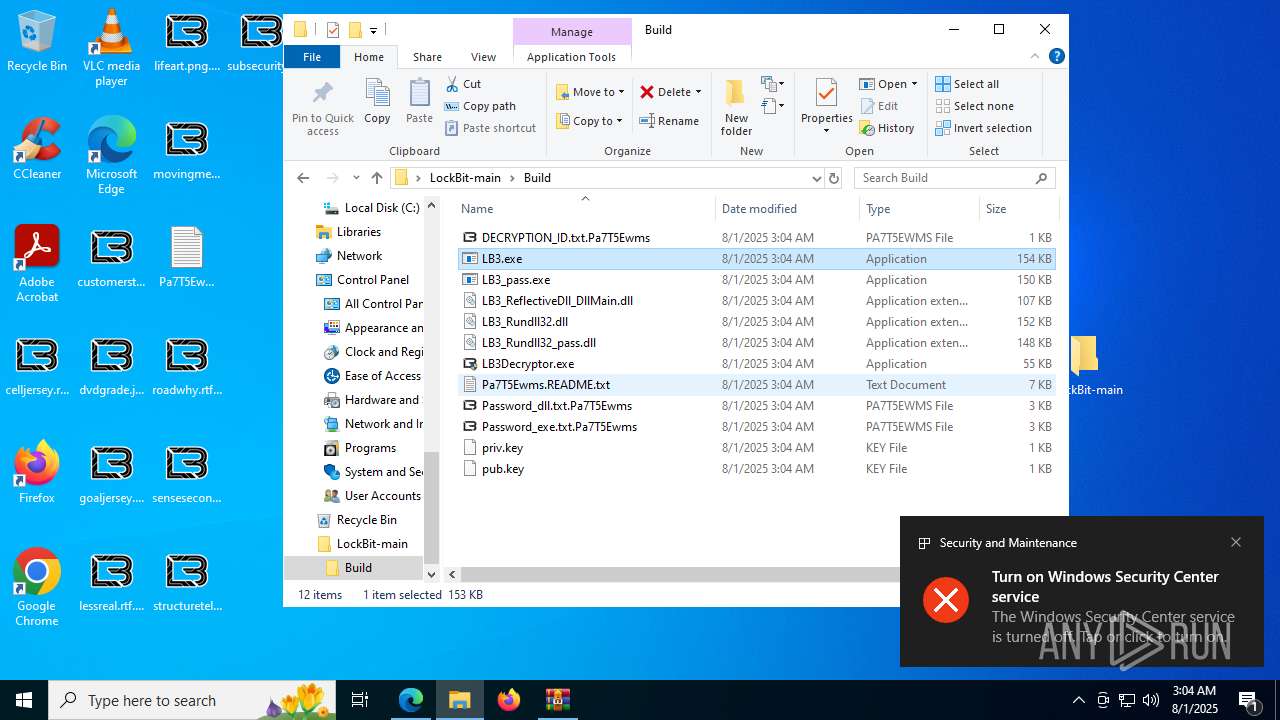
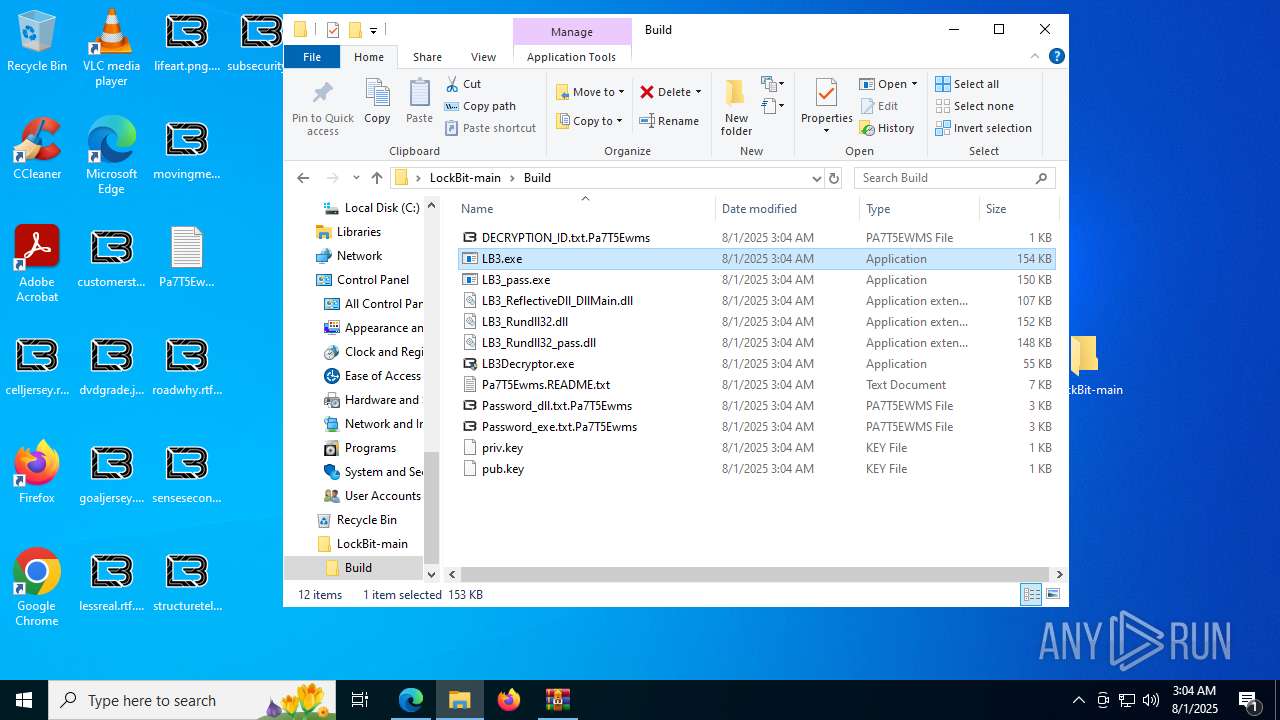
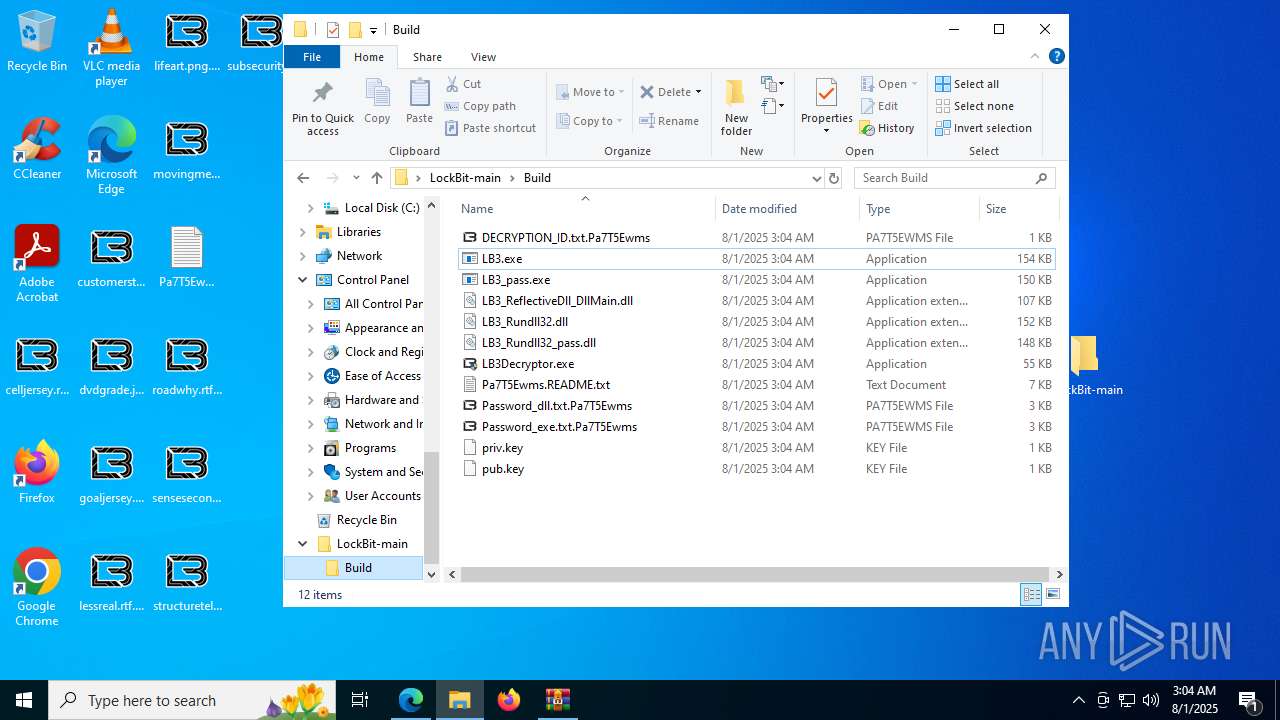
LOCKBIT icon has been detected
- LB3.exe (PID: 1808)
Renames files like ransomware
- LB3.exe (PID: 1808)
BRAINCIPHER has been detected
- LB3.exe (PID: 1808)
RANSOMWARE has been detected
- LB3.exe (PID: 1808)
[YARA] LockBit is detected
- LB3.exe (PID: 1808)
SUSPICIOUS
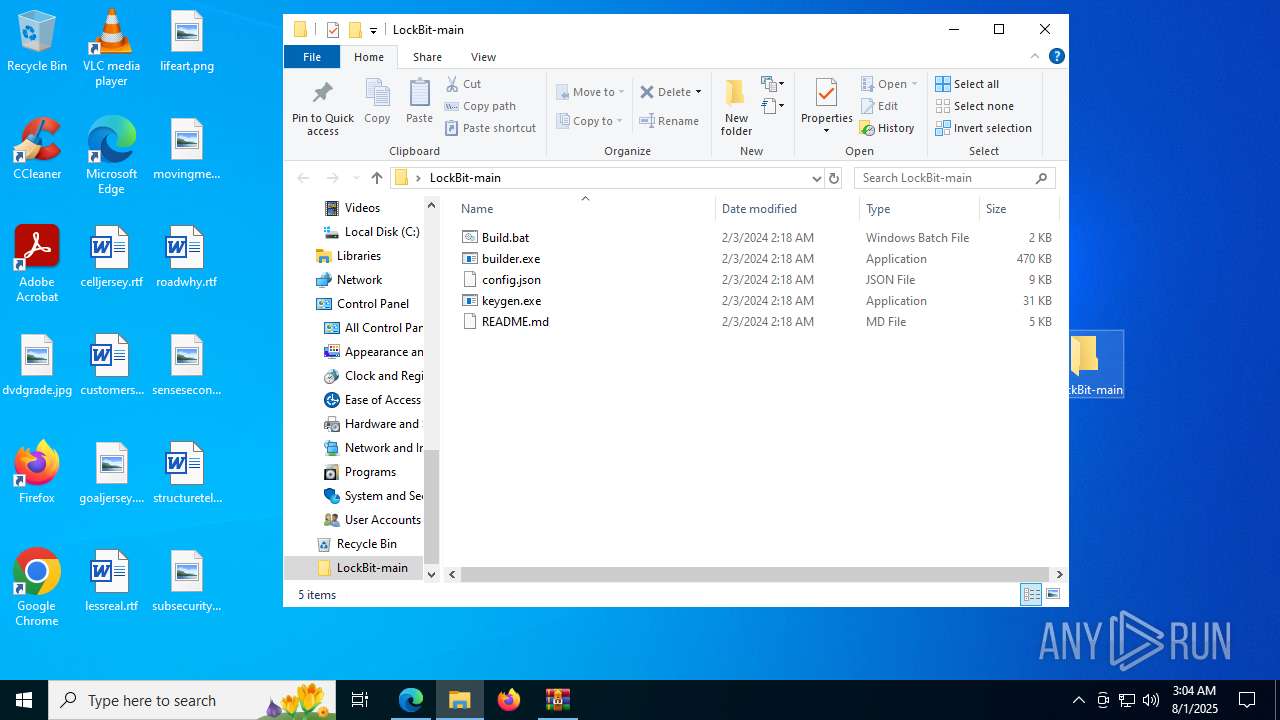
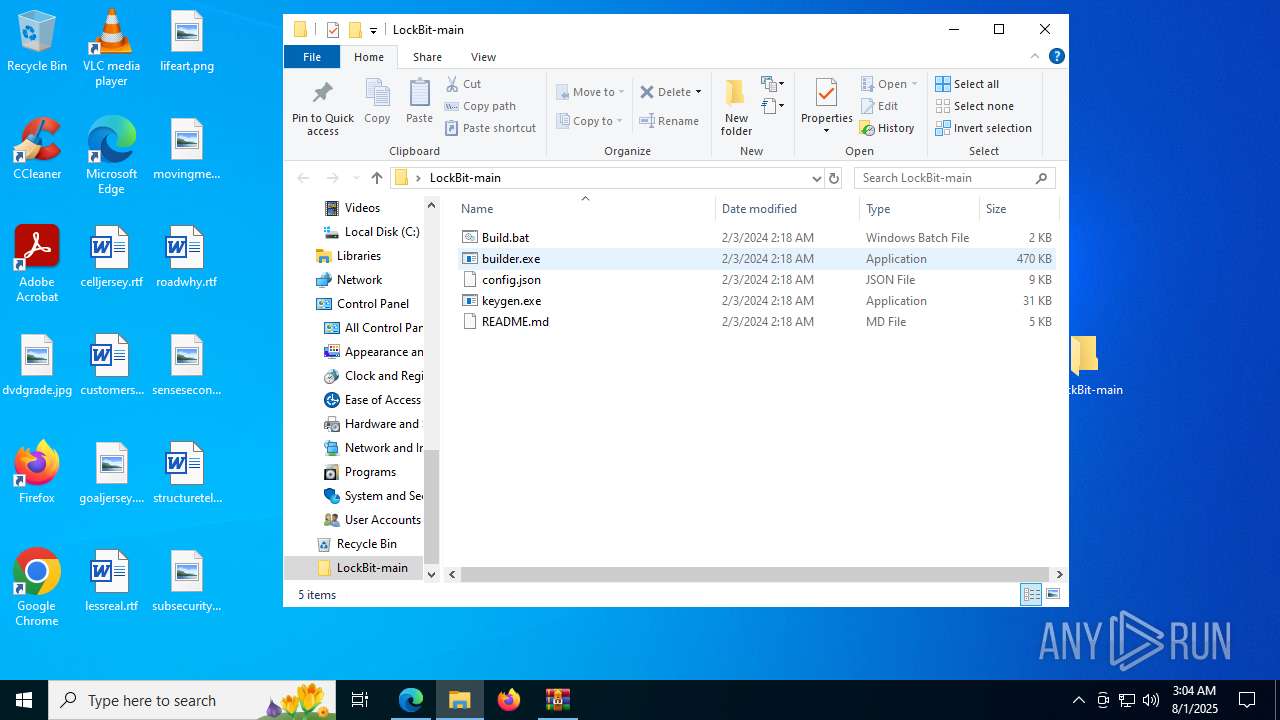
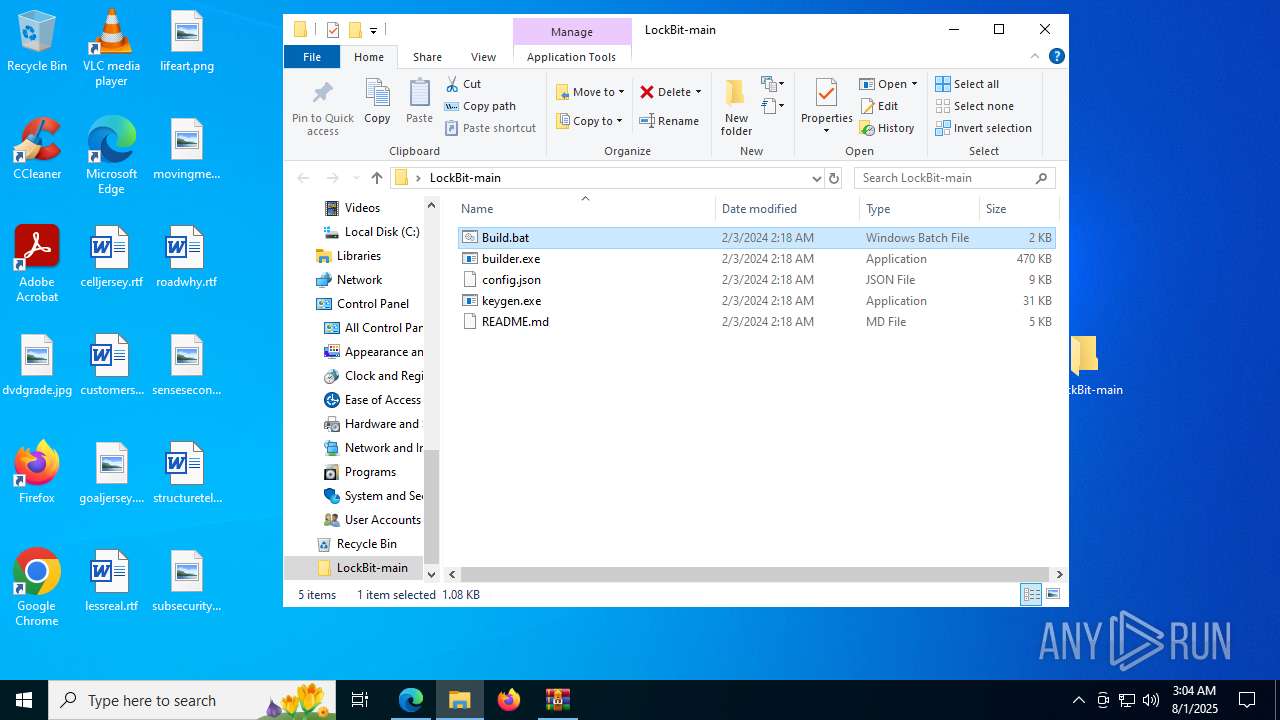
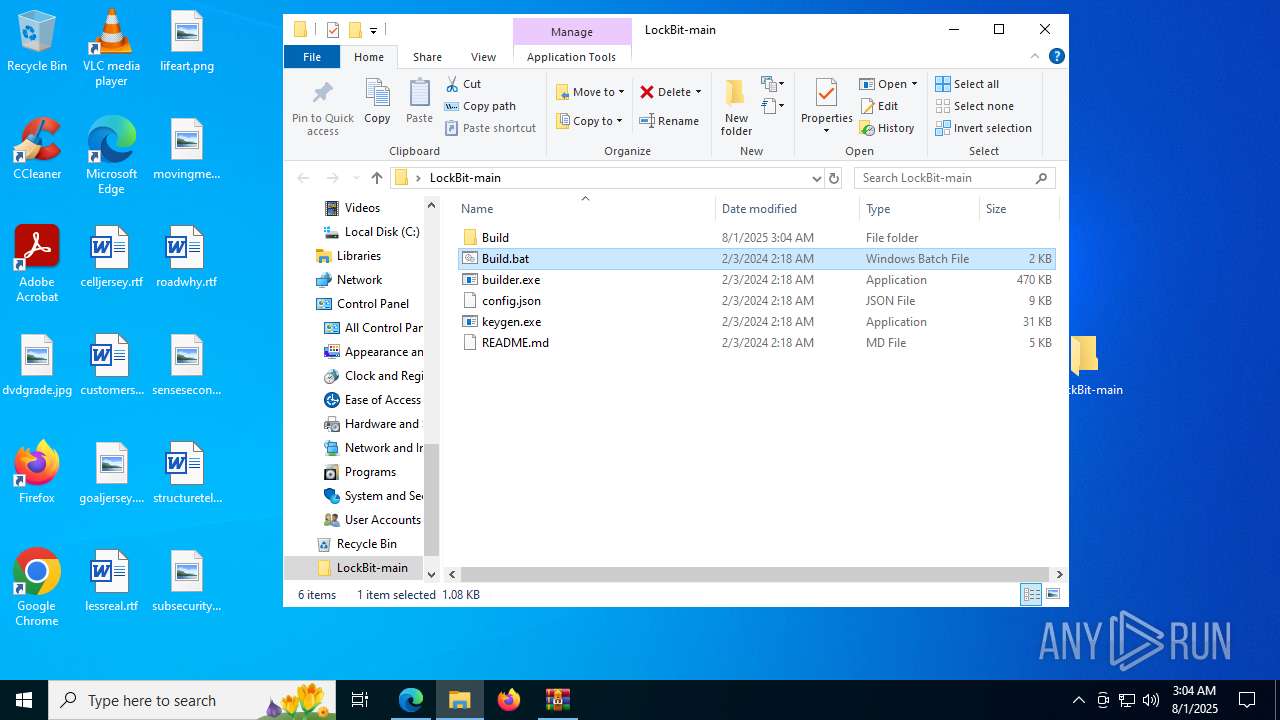
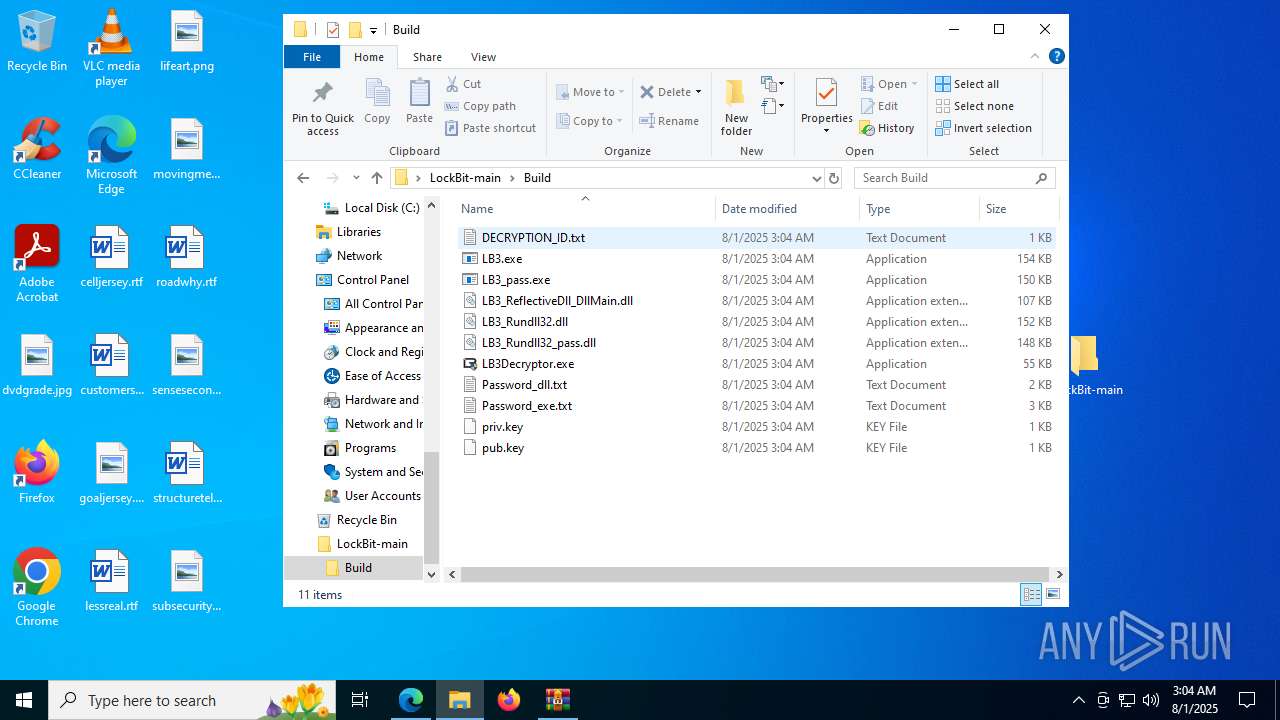
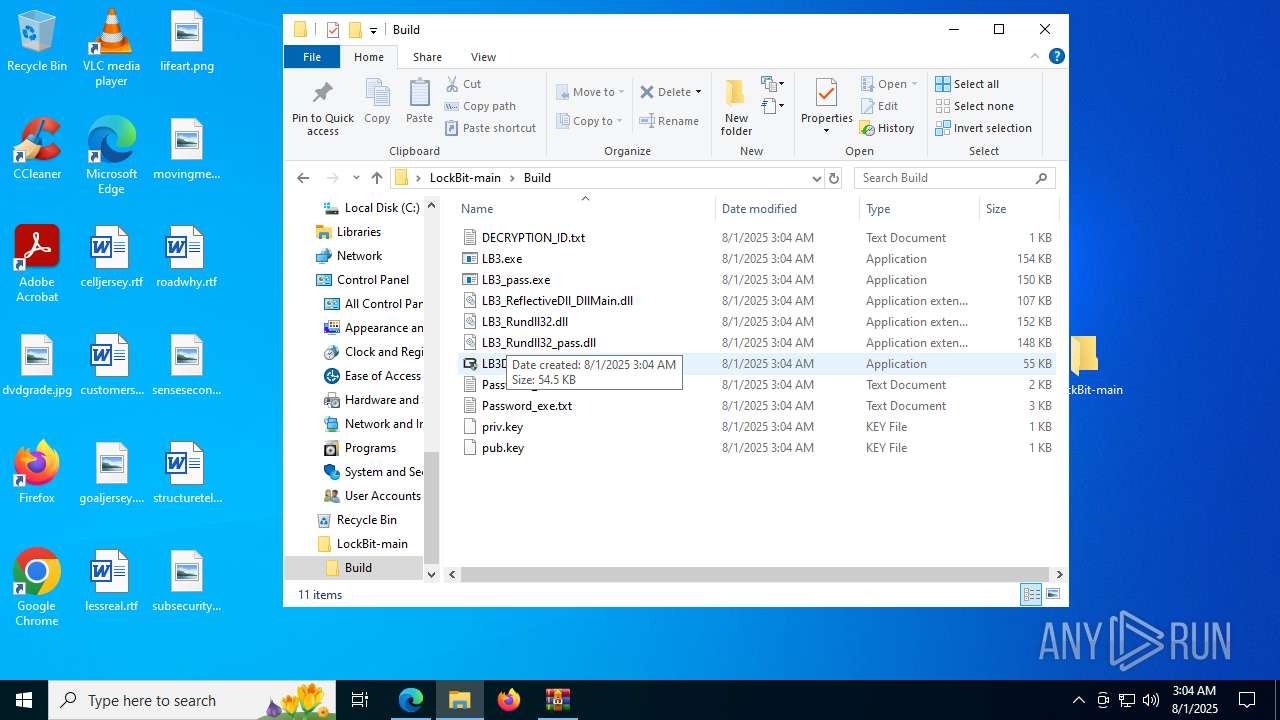
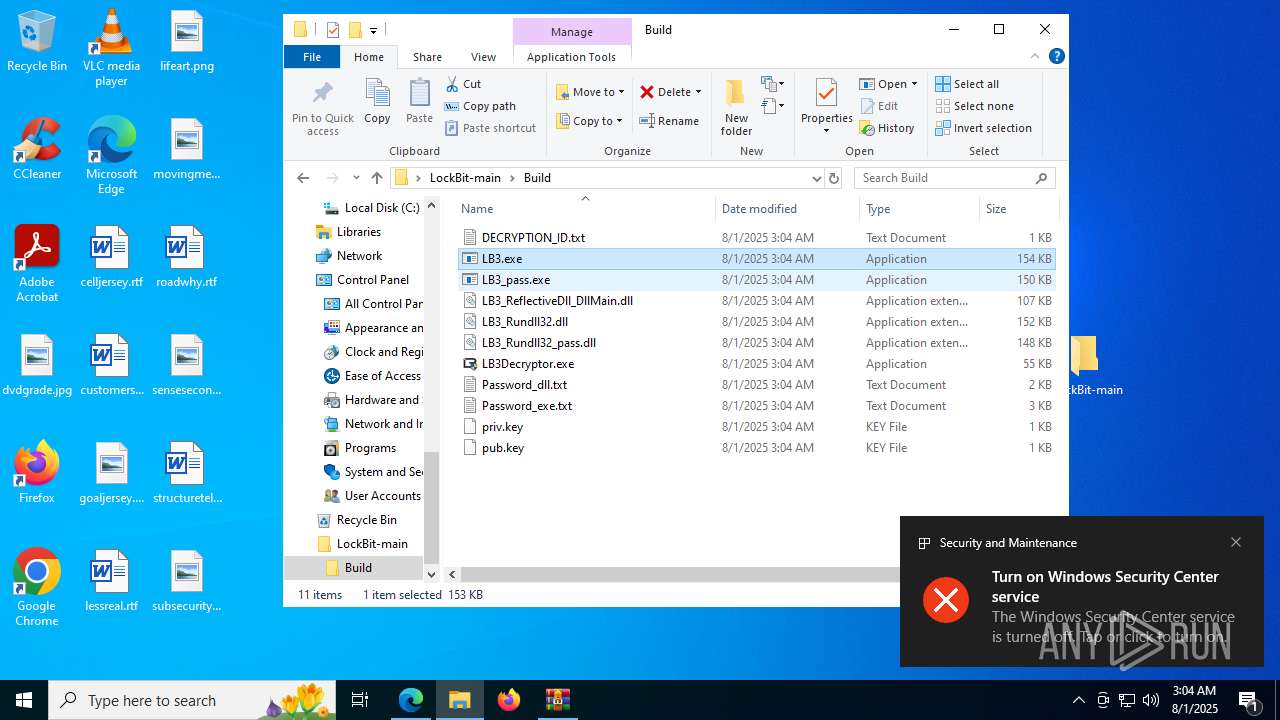
Executable content was dropped or overwritten
- builder.exe (PID: 4760)
- builder.exe (PID: 3688)
- builder.exe (PID: 6176)
- builder.exe (PID: 5904)
- builder.exe (PID: 5968)
- builder.exe (PID: 7660)
The process creates files with name similar to system file names
- builder.exe (PID: 6176)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 6228)
There is functionality for taking screenshot (YARA)
- LB3.exe (PID: 1808)
Write to the desktop.ini file (may be used to cloak folders)
- LB3.exe (PID: 1808)
INFO
Checks supported languages
- identity_helper.exe (PID: 7704)
- builder.exe (PID: 4760)
- builder.exe (PID: 5968)
- builder.exe (PID: 6176)
- builder.exe (PID: 7660)
- LB3.exe (PID: 1808)
- ShellExperienceHost.exe (PID: 6228)
- builder.exe (PID: 3688)
- builder.exe (PID: 3160)
- builder.exe (PID: 5904)
- keygen.exe (PID: 7808)
- LB3.exe (PID: 7620)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8064)
Reads Environment values
- identity_helper.exe (PID: 7704)
Application launched itself
- msedge.exe (PID: 2664)
Reads Microsoft Office registry keys
- msedge.exe (PID: 2664)
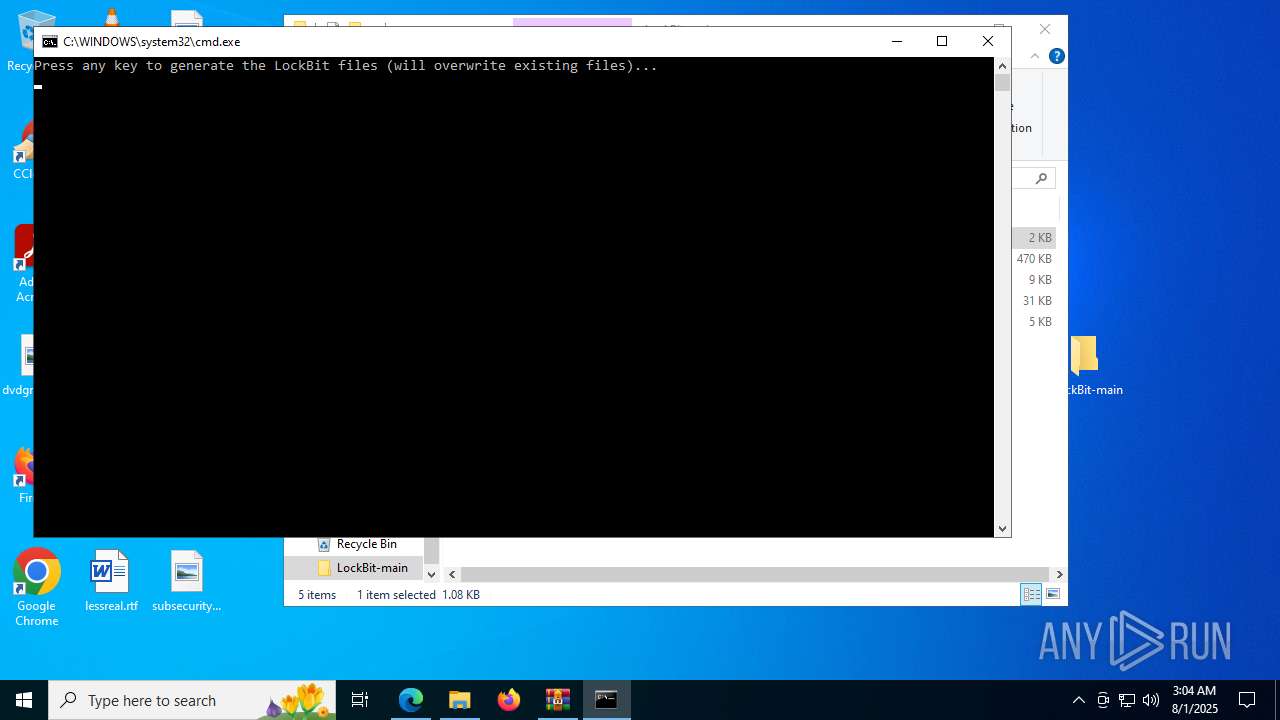
Manual execution by a user
- builder.exe (PID: 3160)
- cmd.exe (PID: 8028)
- LB3.exe (PID: 7620)
- notepad.exe (PID: 7796)
Reads the computer name
- identity_helper.exe (PID: 7704)
- LB3.exe (PID: 7620)
- LB3.exe (PID: 1808)
- ShellExperienceHost.exe (PID: 6228)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 4084)
Reads the machine GUID from the registry
- LB3.exe (PID: 7620)
Creates files in the program directory
- LB3.exe (PID: 1808)
Creates files or folders in the user directory
- LB3.exe (PID: 1808)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
179
Monitored processes
38
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3648,i,5836131309433672185,8338910916491087568,262144 --variations-seed-version --mojo-platform-channel-handle=3668 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3672,i,5836131309433672185,8338910916491087568,262144 --variations-seed-version --mojo-platform-channel-handle=3964 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1740 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1808 | "C:\Users\admin\Desktop\LockBit-main\Build\LB3.exe" | C:\Users\admin\Desktop\LockBit-main\Build\LB3.exe | dllhost.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 2664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://github.com/Tennessene/LockBit/archive/refs/heads/main.zip" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3160 | "C:\Users\admin\Desktop\LockBit-main\builder.exe" | C:\Users\admin\Desktop\LockBit-main\builder.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3460 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2480,i,5836131309433672185,8338910916491087568,262144 --variations-seed-version --mojo-platform-channel-handle=3032 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3688 | builder -type enc -exe -pubkey Build\pub.key -config config.json -ofile Build\LB3.exe | C:\Users\admin\Desktop\LockBit-main\builder.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4084 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4760 | builder -type dec -privkey Build\priv.key -config config.json -ofile Build\LB3Decryptor.exe | C:\Users\admin\Desktop\LockBit-main\builder.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
7 833
Read events
7 808
Write events
25
Delete events
0
Modification events
| (PID) Process: | (2664) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2664) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2664) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2664) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2664) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2664) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2664) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 30FCEF49DB992F00 | |||
| (PID) Process: | (2664) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\525070 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8906097A-C0D7-455C-89E9-A2899F4945E8} | |||
| (PID) Process: | (2664) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\525070 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8F394BF2-8D78-4497-B31D-32147F832D11} | |||
| (PID) Process: | (2664) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 474F324ADB992F00 | |||
Executable files
8
Suspicious files
487
Text files
476
Unknown types
134
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2664 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18d1a3.TMP | — | |
MD5:— | SHA256:— | |||
| 2664 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2664 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18d1a3.TMP | — | |
MD5:— | SHA256:— | |||
| 2664 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2664 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18d685.TMP | — | |
MD5:— | SHA256:— | |||
| 2664 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2664 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18d6a4.TMP | — | |
MD5:— | SHA256:— | |||
| 2664 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2664 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF18d6a4.TMP | — | |
MD5:— | SHA256:— | |||
| 2664 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
51
DNS requests
41
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5372 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:-GEXQHMshe0dPnCgvCZvzvd--BRwXiszT4H0Tv63WIs&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6292 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6292 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6756 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6732 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5372 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5372 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5372 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5372 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
5372 | msedge.exe | 92.123.104.53:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
codeload.github.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |