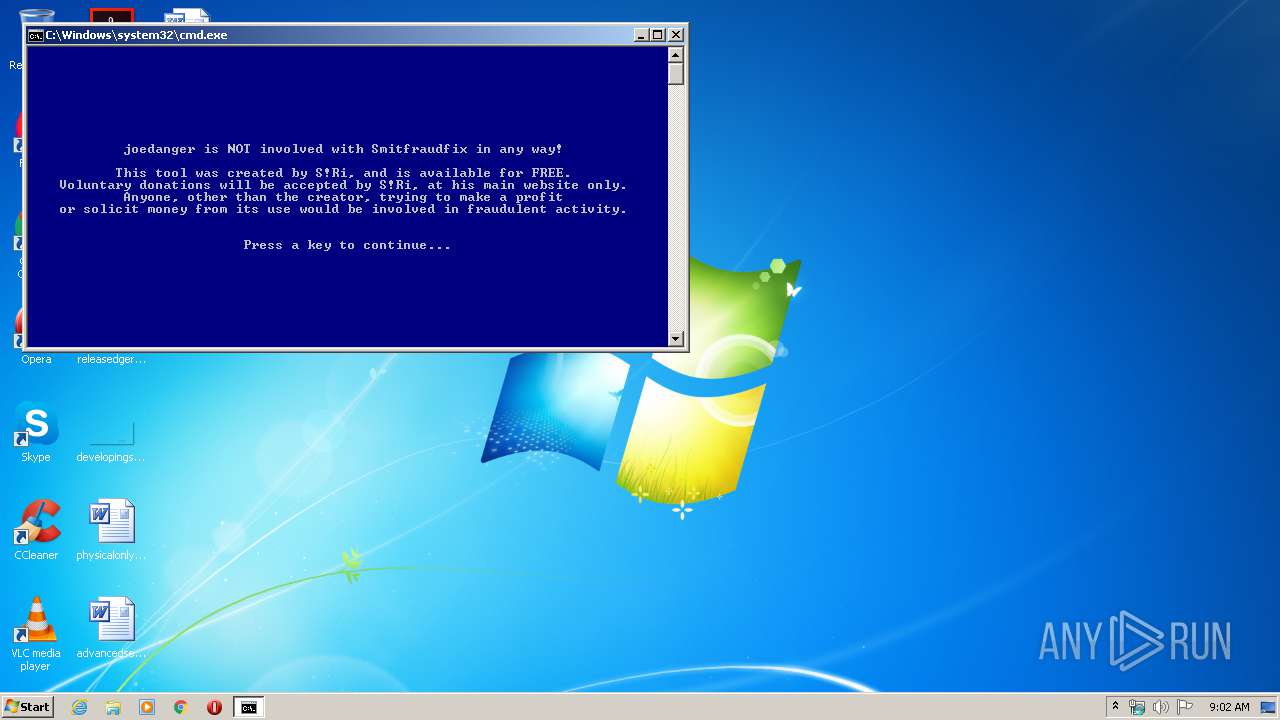
| File name: | SmitfraudFix.exe |
| Full analysis: | https://app.any.run/tasks/9207b2d5-fb1c-4e34-9154-d93c79138d1f |
| Verdict: | Malicious activity |
| Analysis date: | January 29, 2020, 09:01:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8025BE61EB76E2DE01A4068BC3143D06 |
| SHA1: | D07F0F83B6B36984DE97FDB422430C77586E3A6B |
| SHA256: | 3A0D4B187980F8B40F39F059BBAE1613B0B8CE2F57E587D55444AB61EADC535A |
| SSDEEP: | 24576:rUWqistxDo5DNJXnKDYZvZ+/jHvtaX5IeCK3utSxAA8xDvf53LYHR7U/q/5tmxcP:rUUp6DBjHMu2ejxDJ3LKR7Uy/mLba |
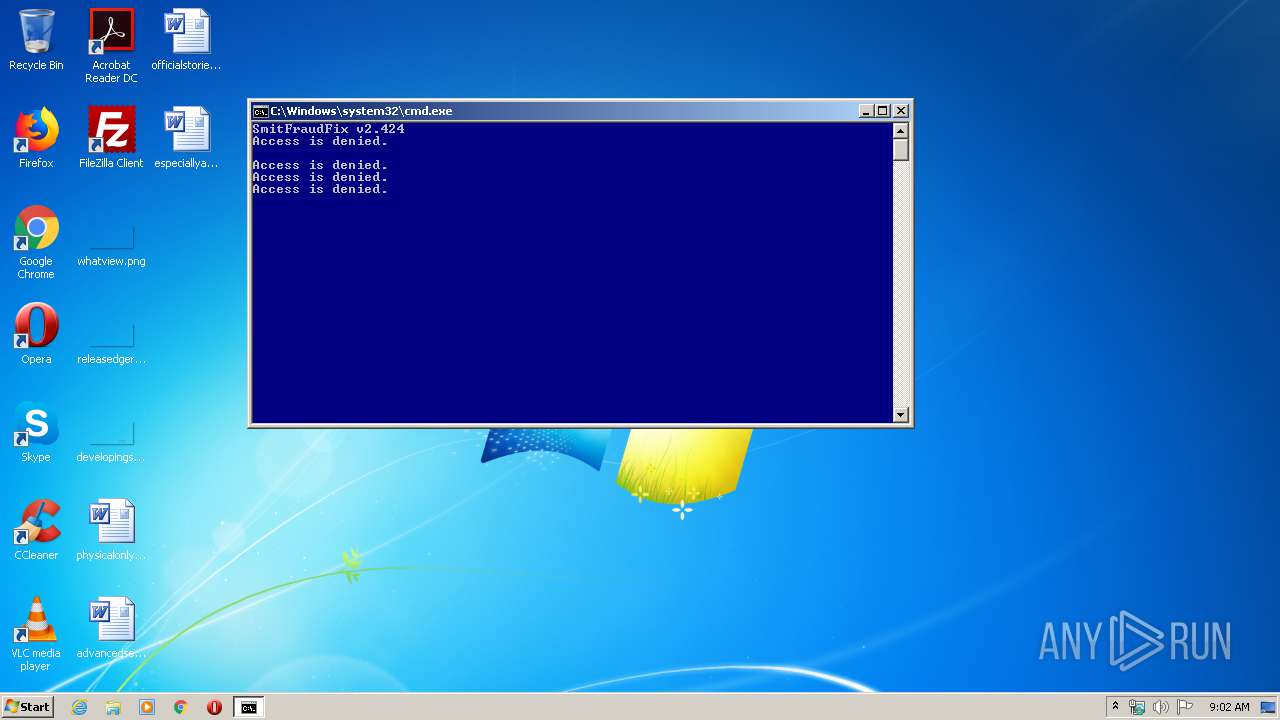
MALICIOUS
Application was dropped or rewritten from another process
- Policies.exe (PID: 3604)
SUSPICIOUS
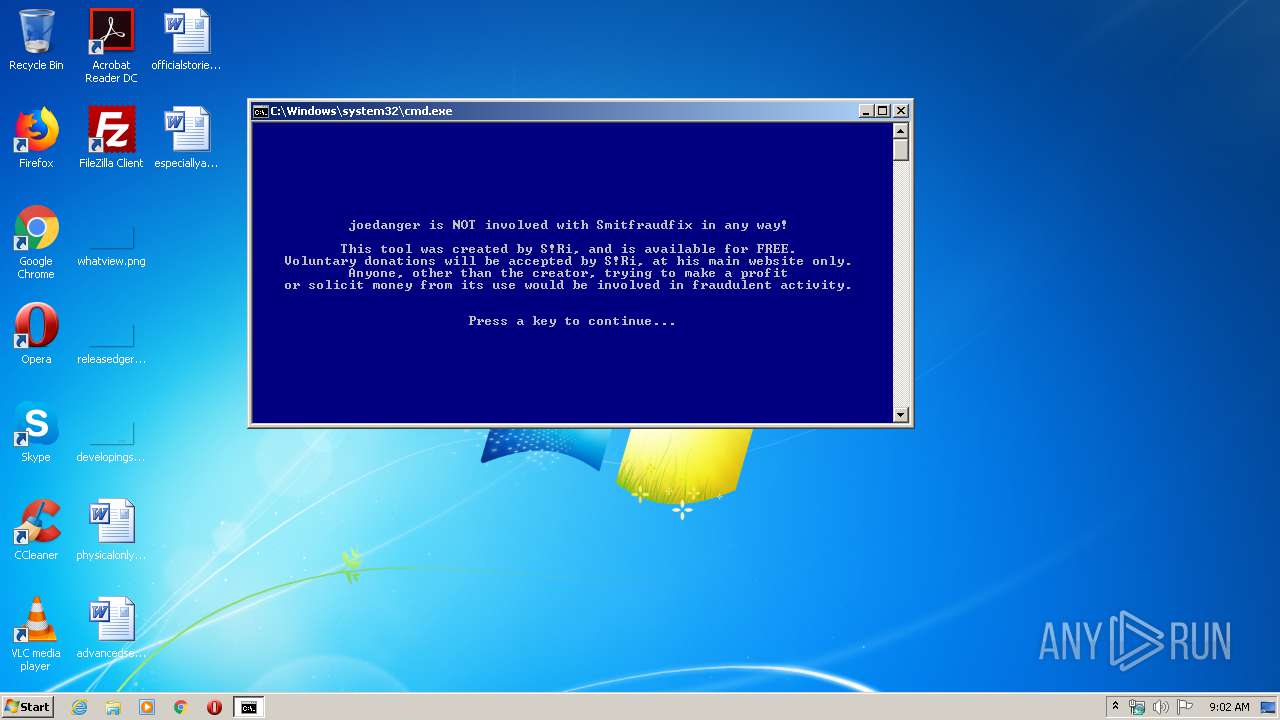
Starts CMD.EXE for commands execution
- Policies.exe (PID: 3604)
- cmd.exe (PID: 3036)
Executes scripts
- cmd.exe (PID: 3036)
Executable content was dropped or overwritten
- SmitfraudFix.exe (PID: 3600)
Application launched itself
- cmd.exe (PID: 3036)
INFO
Dropped object may contain Bitcoin addresses
- SmitfraudFix.exe (PID: 3600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:08:16 13:05:35+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 67584 |
| InitializedDataSize: | 45568 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa7d8 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Aug-2009 11:05:35 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 16-Aug-2009 11:05:35 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001067C | 0x00010800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56176 |
.rdata | 0x00012000 | 0x000017D5 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.51289 |
.data | 0x00014000 | 0x0000BFF4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.54344 |
.CRT | 0x00020000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.213101 |
.rsrc | 0x00021000 | 0x000094D8 | 0x00009600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.62292 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.20816 | 1464 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.737 | 1736 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 5.18679 | 2216 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 4.75001 | 3752 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 4.02485 | 1128 | Latin 1 / Western European | Process Default Language | RT_ICON |
6 | 3.92362 | 2440 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 3.24143 | 556 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.28574 | 946 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.04375 | 530 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.15563 | 638 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
66
Monitored processes
32
Malicious processes
3
Suspicious processes
0
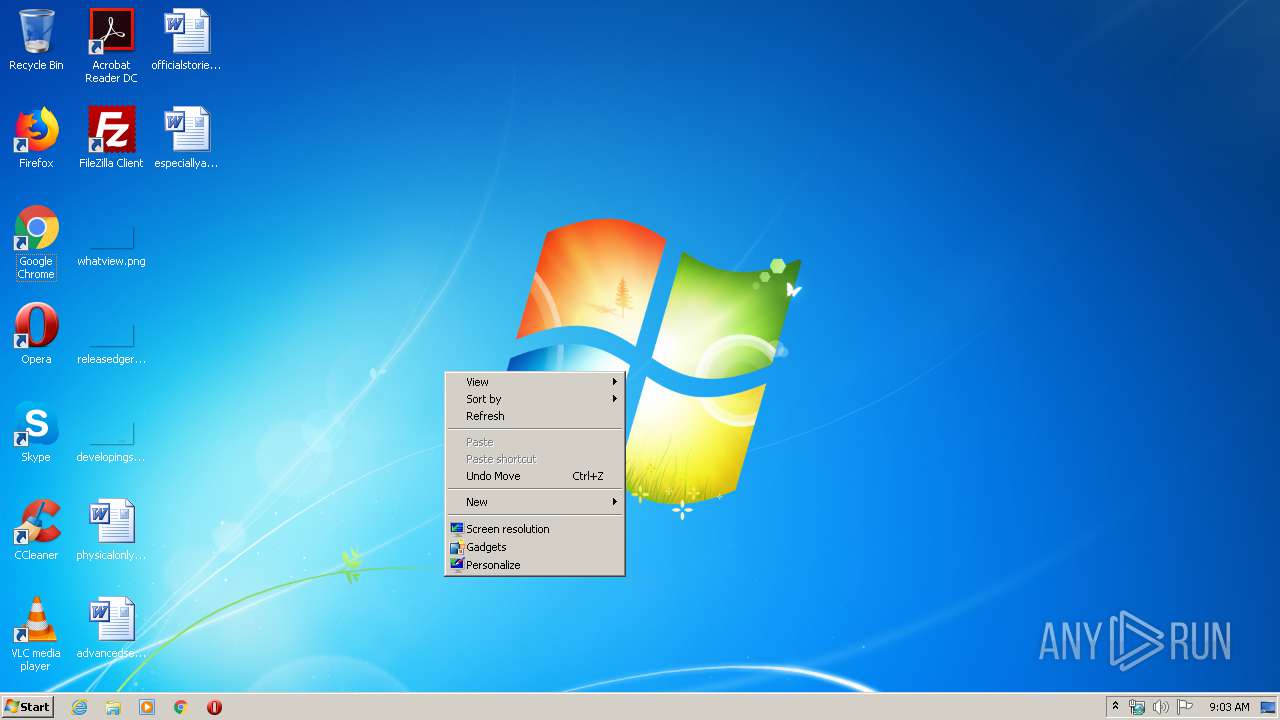
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | find /i "RAW" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 440 | find "Windows 98" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 564 | C:\Windows\system32\cmd.exe /S /D /c" type tmp.txt " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 628 | C:\Windows\system32\cmd.exe /S /D /c" VER" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 820 | find "Version 6.0" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1712 | find /i "NTFS" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1812 | C:\Windows\system32\cmd.exe /c cd | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2076 | find "Windows Millennium" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2228 | C:\Windows\system32\cmd.exe /S /D /c" VER" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2496 | C:\Windows\system32\cmd.exe /S /D /c" VER" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
857
Read events
845
Write events
10
Delete events
2
Modification events
| (PID) Process: | (3600) SmitfraudFix.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3600) SmitfraudFix.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3604) Policies.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced |
| Operation: | delete value | Name: | StartMenuAdminTools |
Value: 0 | |||
| (PID) Process: | (3604) Policies.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced |
| Operation: | delete value | Name: | Start_ShowRecentDocs |
Value: 1 | |||
| (PID) Process: | (3604) Policies.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced |
| Operation: | write | Name: | Start_ShowNetPlaces |
Value: 65 | |||
| (PID) Process: | (3604) Policies.exe | Key: | HKEY_CURRENT_USER\Control Panel\International |
| Operation: | write | Name: | sTimeFormat |
Value: HH:mm:ss | |||
| (PID) Process: | (3604) Policies.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3604) Policies.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
26
Suspicious files
0
Text files
134
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3600 | SmitfraudFix.exe | C:\Users\admin\AppData\Local\Temp\SmitfraudFix\dumphive.exe | executable | |
MD5:21868B2D22C726D94D98F15825D4134B | SHA256:4A0202E069E3C1029ECB1F72639A7E35CCCA28E1A81A7CA08D5F9206B4DC9363 | |||
| 3600 | SmitfraudFix.exe | C:\Users\admin\AppData\Local\Temp\SmitfraudFix\Reboot.exe | executable | |
MD5:7CBCD47BED0F5C9EBA0815BEAA99A120 | SHA256:E851C215CD594BDD17FA123153E290E1EEEC1F7CF79D1751171978B01E5D6943 | |||
| 3600 | SmitfraudFix.exe | C:\Users\admin\AppData\Local\Temp\SmitfraudFix\Agent.OMZ.Fix.exe | executable | |
MD5:C02562A732F0223082D4CCFC7D4F23DF | SHA256:4D40D3826750344C4C6080D20F20AD47F694C972923A024EDAAE998EF23A6AE0 | |||
| 3600 | SmitfraudFix.exe | C:\Users\admin\AppData\Local\Temp\SmitfraudFix\GenericRenosFix.exe | executable | |
MD5:A1FF6254A883D76CDD18CFB982ADCC33 | SHA256:F7517111BEC4B7653026C8C83587FCE14B9B38F59974830CADB7B39343E055B8 | |||
| 3600 | SmitfraudFix.exe | C:\Users\admin\AppData\Local\Temp\SmitfraudFix\beep_2K_original.sys | executable | |
MD5:DF012C2853281CE2BF536E8DE871C8C1 | SHA256:CB9E7EAE3E4A14C49EB9FD2AAF44DAA990BE994CCC1562A8320B69E71E8EBF10 | |||
| 3600 | SmitfraudFix.exe | C:\Users\admin\AppData\Local\Temp\SmitfraudFix\IEDFix.exe | executable | |
MD5:799A9EA3FFB220780AE3D3C11B08D067 | SHA256:F13D26103CBD99B54C059E773B683526902A18A9EE9FE3152342C9B546C8BB8E | |||
| 3600 | SmitfraudFix.exe | C:\Users\admin\AppData\Local\Temp\SmitfraudFix\IEDFix.C.exe | executable | |
MD5:9769AB38CB77C9914C25B8141A2A3FBE | SHA256:7237B3E0C9A5560D505E0AA8AE558F35B70BC34BE08DFB17FF97480B3951622C | |||
| 3600 | SmitfraudFix.exe | C:\Users\admin\AppData\Local\Temp\SmitfraudFix\beep_XP_original.sys | executable | |
MD5:DA1F27D85E0D1525F6621372E7B685E9 | SHA256:5A81A46A3BDD19DAFC6C87D277267A5D44F3A1B5302F2CC1111D84B7BAD5610D | |||
| 3600 | SmitfraudFix.exe | C:\Users\admin\AppData\Local\Temp\SmitfraudFix\Policies.exe | executable | |
MD5:2576EFBFECD8E90F7BCCE395259F77AD | SHA256:DB4E7D651D7331C9C37F53AB4F01F6D8E1DD6BDD53687A632732060CC49CCEDC | |||
| 3600 | SmitfraudFix.exe | C:\Users\admin\AppData\Local\Temp\SmitfraudFix\HostsChk.exe | executable | |
MD5:8C5514F1DDC6BA704311354910BA2518 | SHA256:DC3FD70FF4E138D9380161A1B8BC5AB11F0423D8FDF831927EE6DBA979DC362F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report