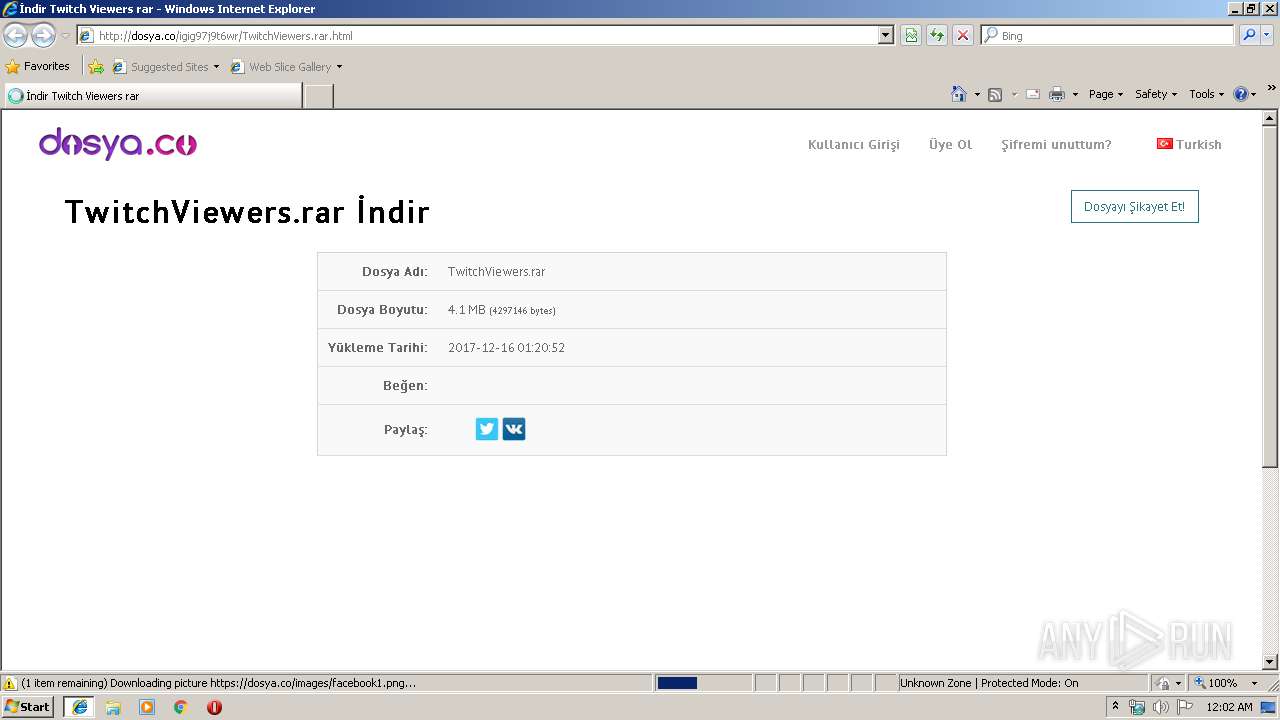
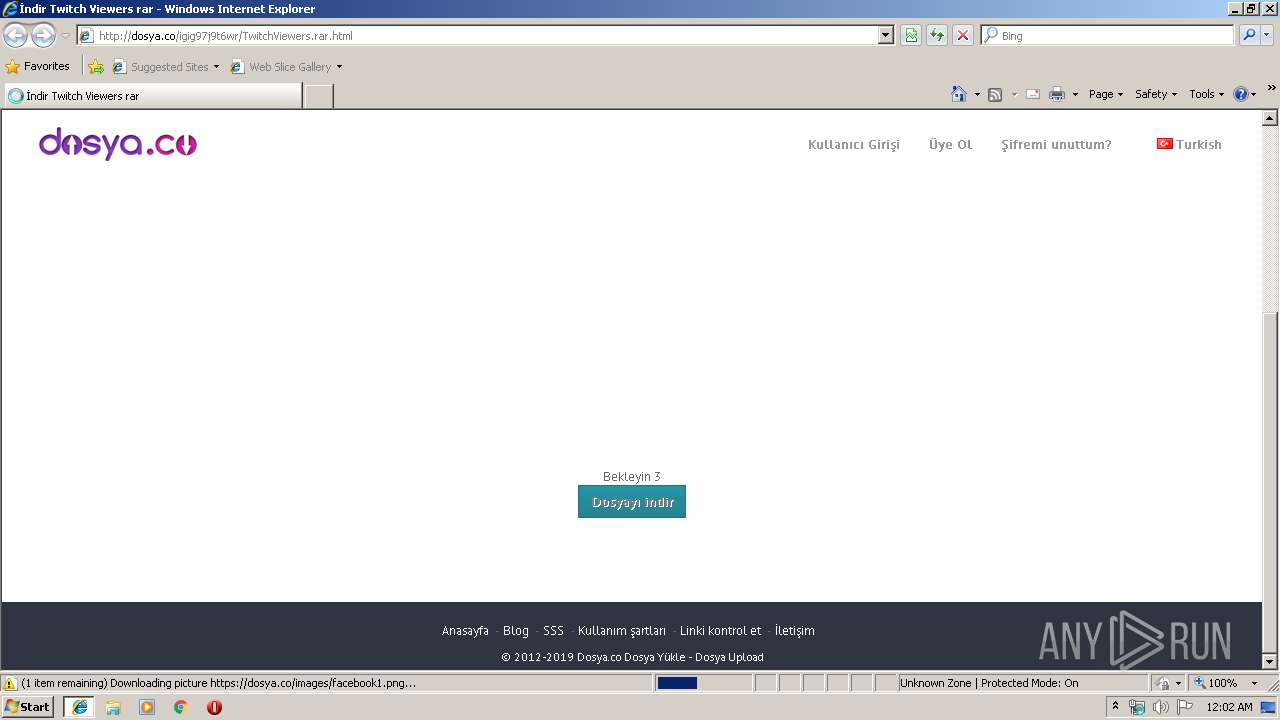
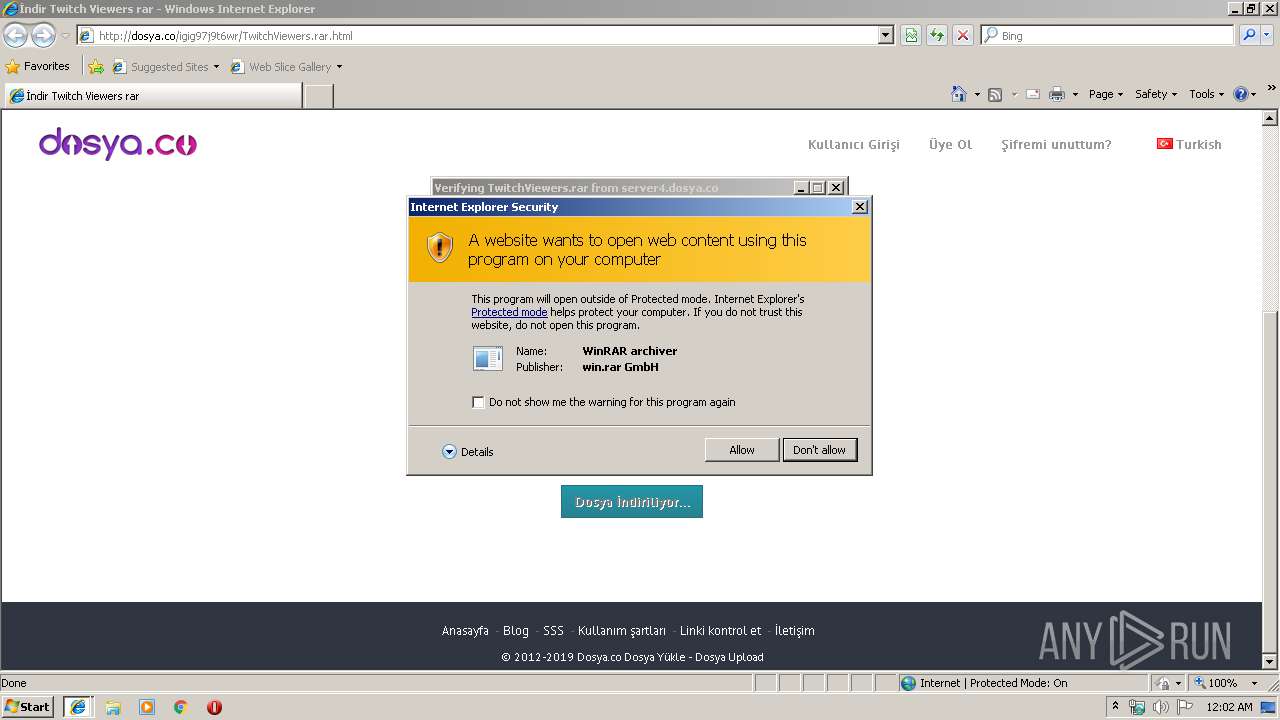
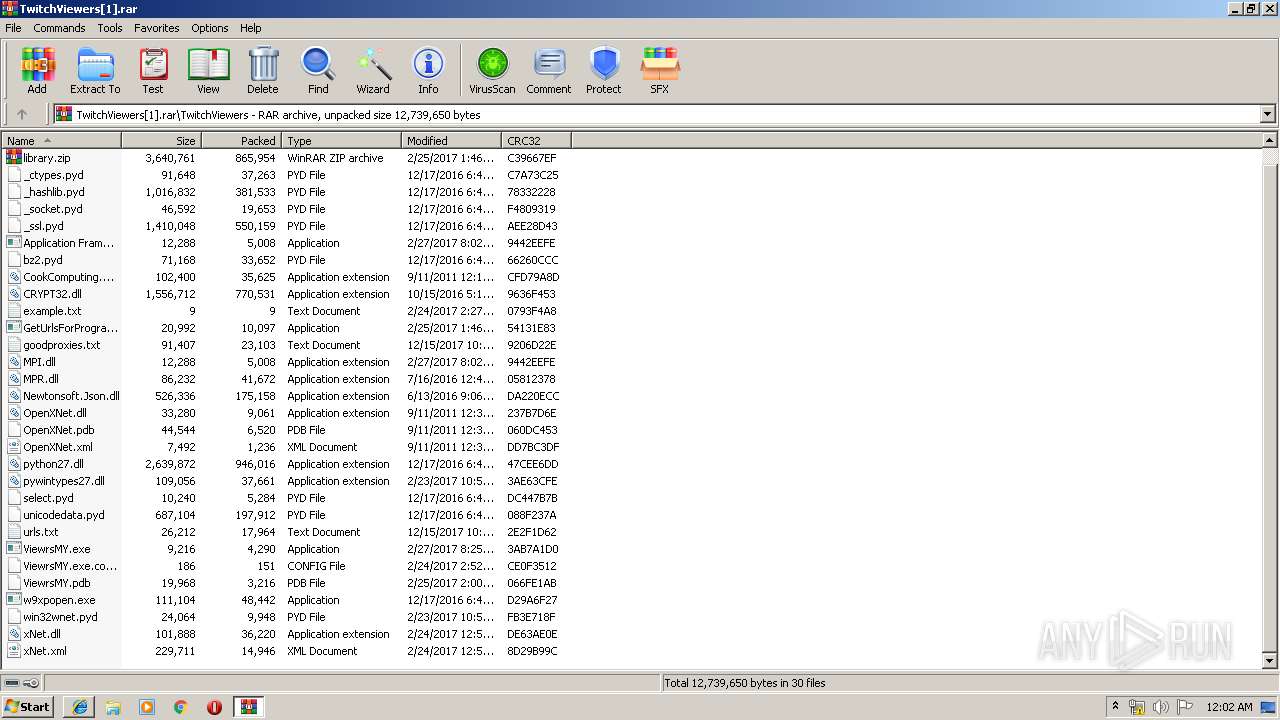
| URL: | http://dosya.co/igig97j9t6wr/TwitchViewers.rar.html |
| Full analysis: | https://app.any.run/tasks/d202981a-49a7-4ae6-8429-fa54320d6e10 |
| Verdict: | Malicious activity |
| Analysis date: | December 27, 2019, 00:01:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B9F005E84753E5C1E561CE3A5F618BA2 |
| SHA1: | 3654849B9D4DD0E1134FA327CC4B7E2DD78317E3 |
| SHA256: | 3A04564B52391117EC2018CECB293D6974970C30A5B918E27EEB2E26673D185F |
| SSDEEP: | 3:N1KaKgLdKjYe6/RaFSxzn:Cadei1xzn |
MALICIOUS
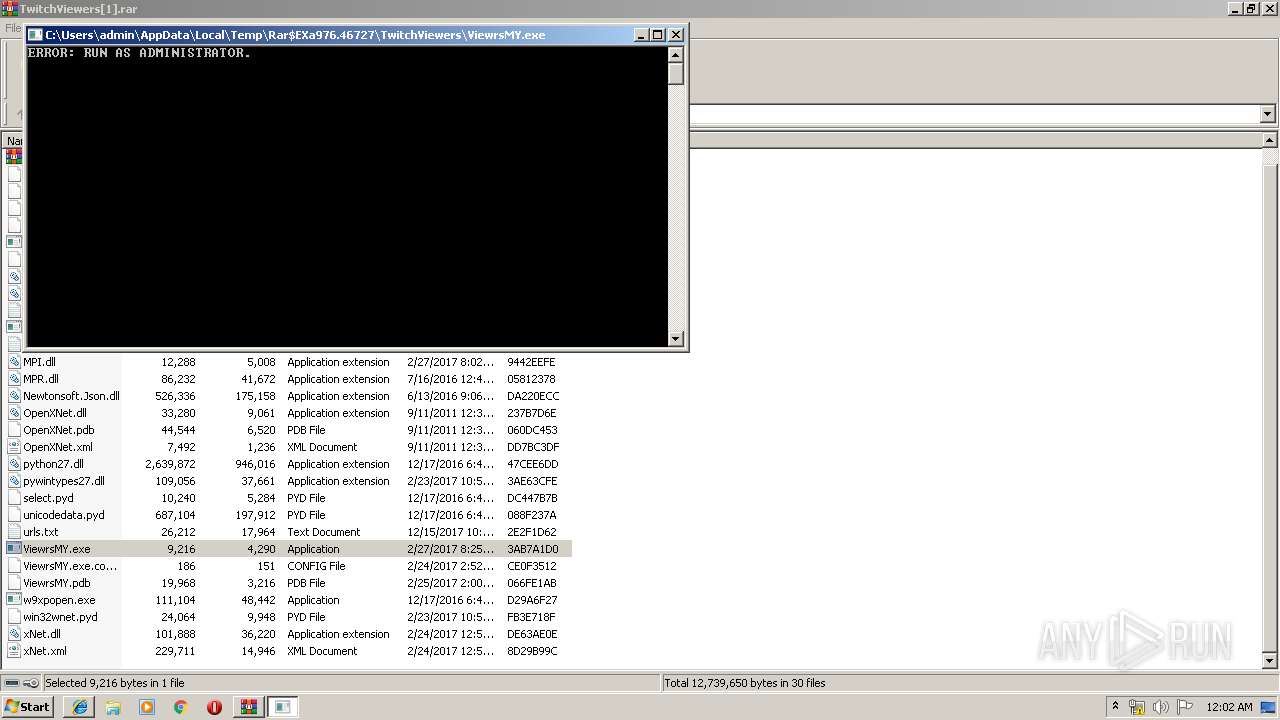
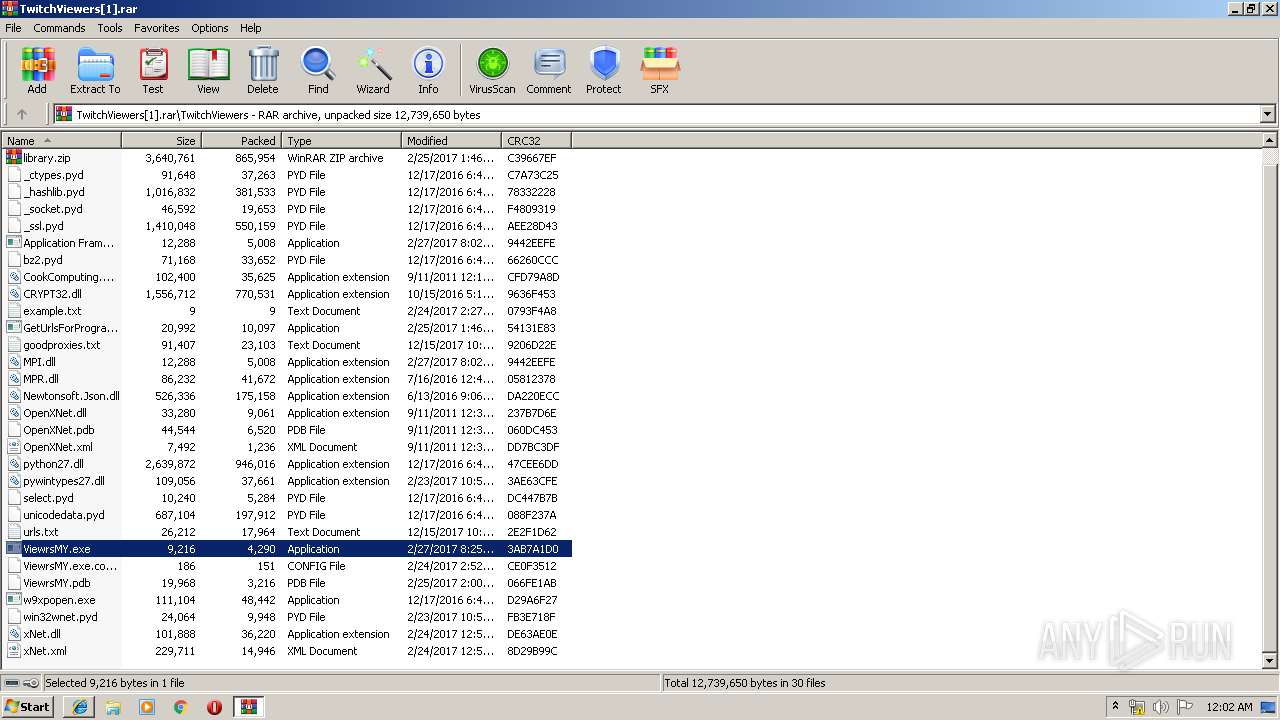
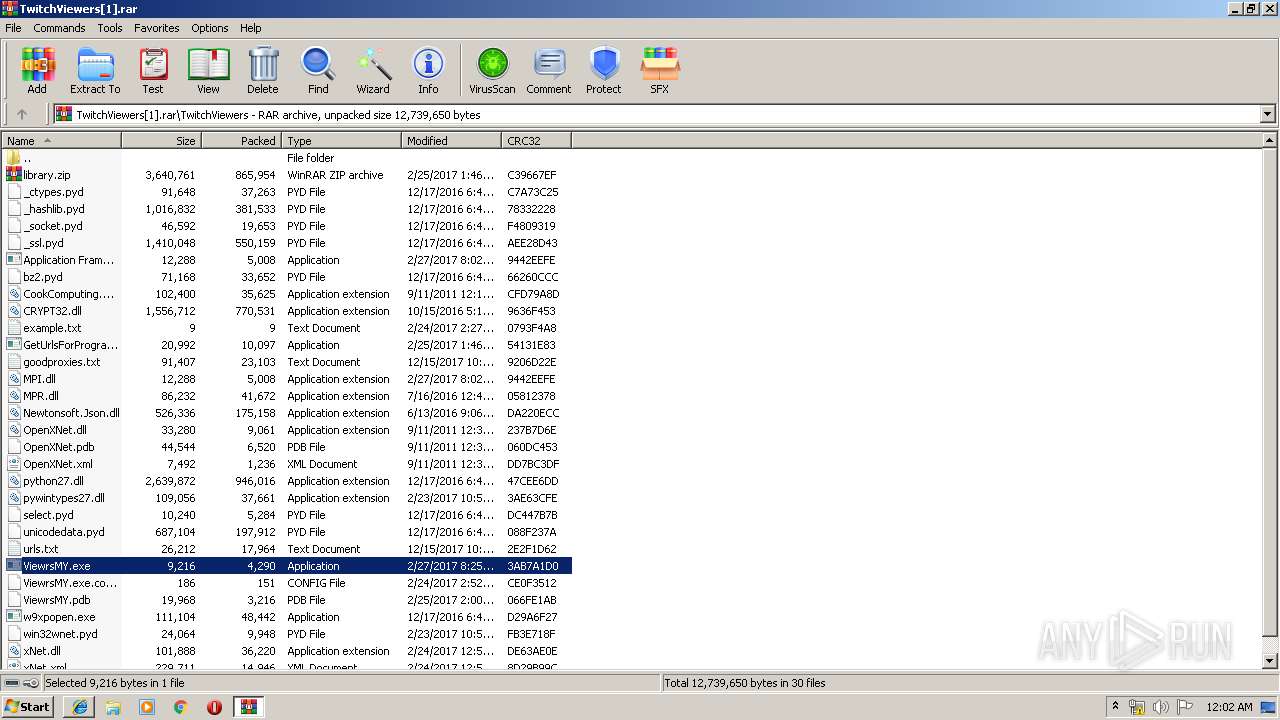
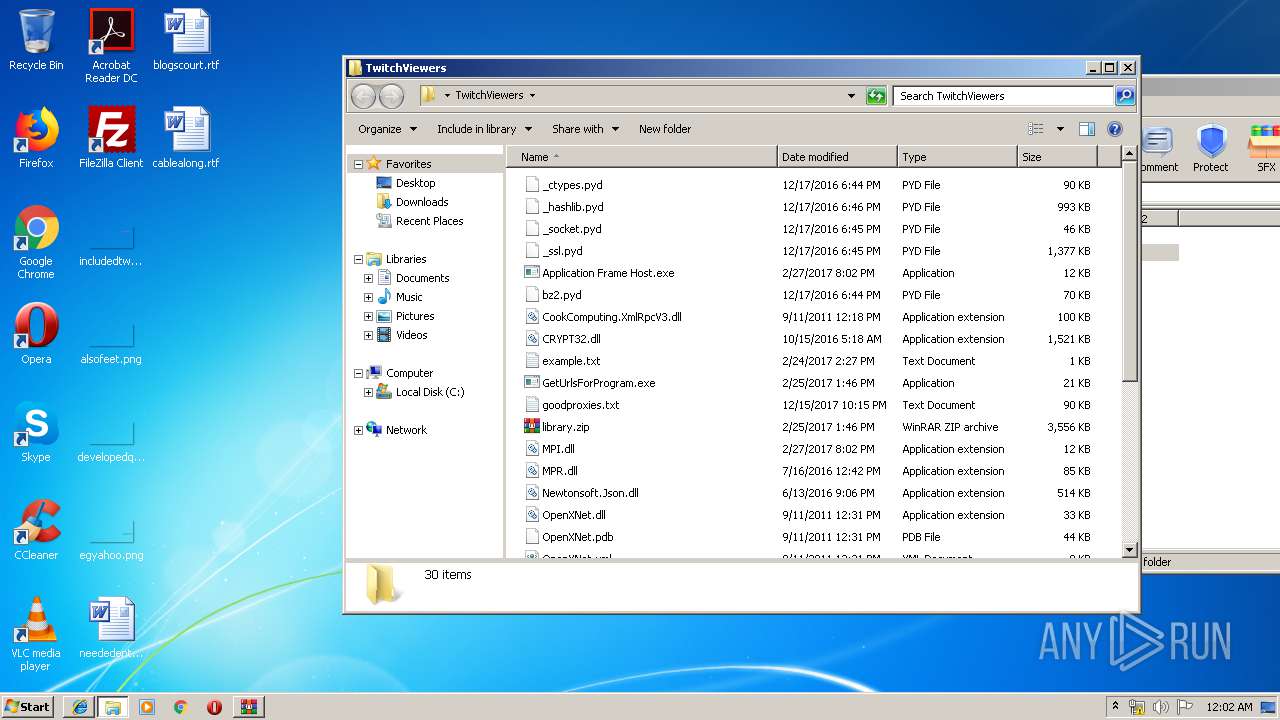
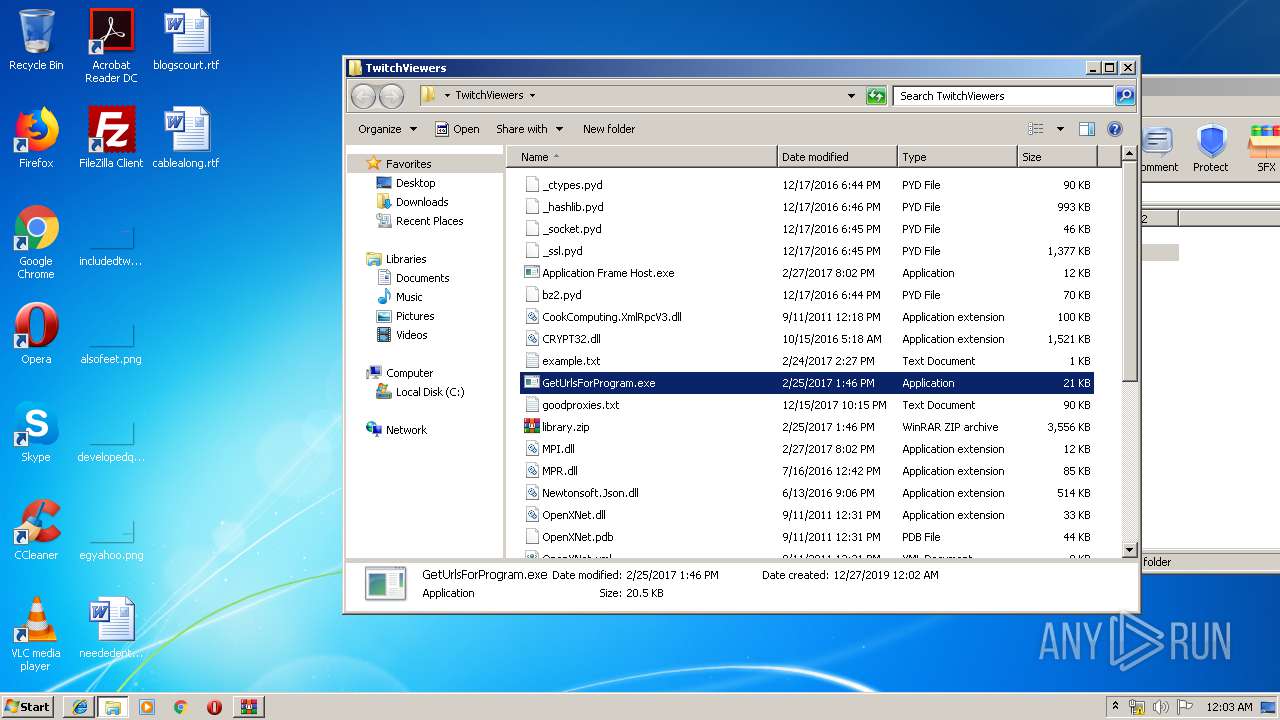
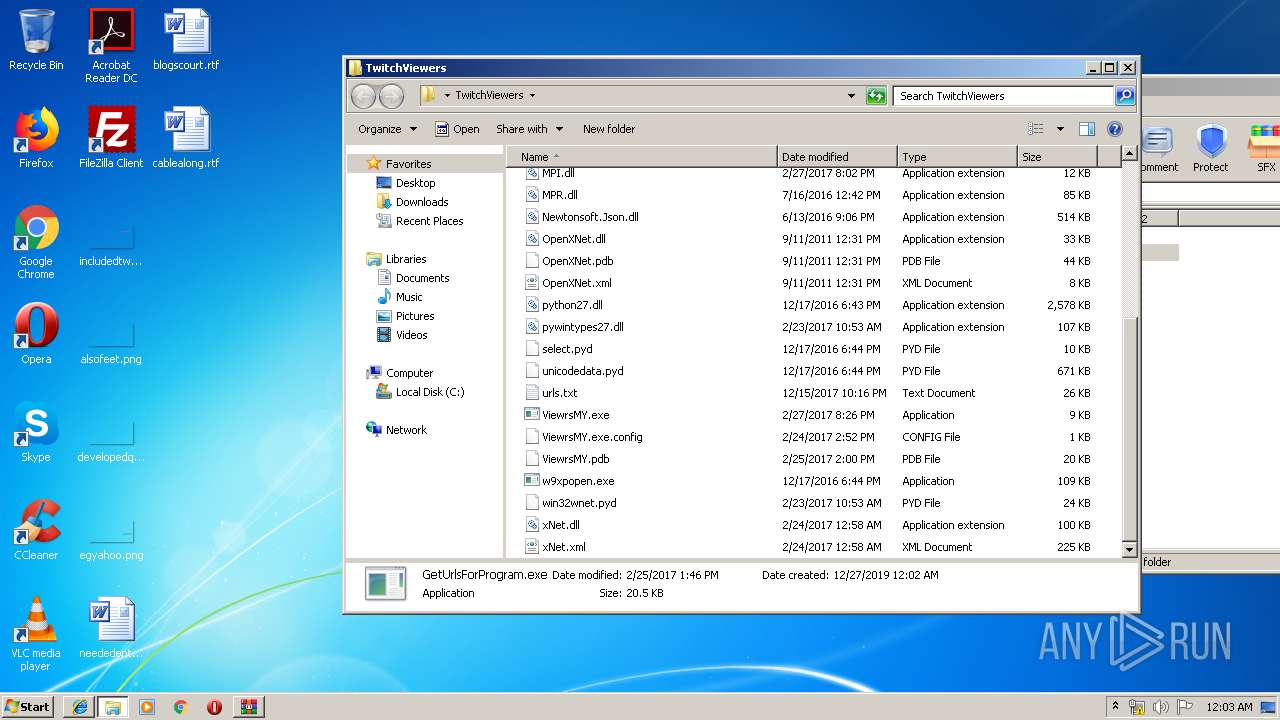
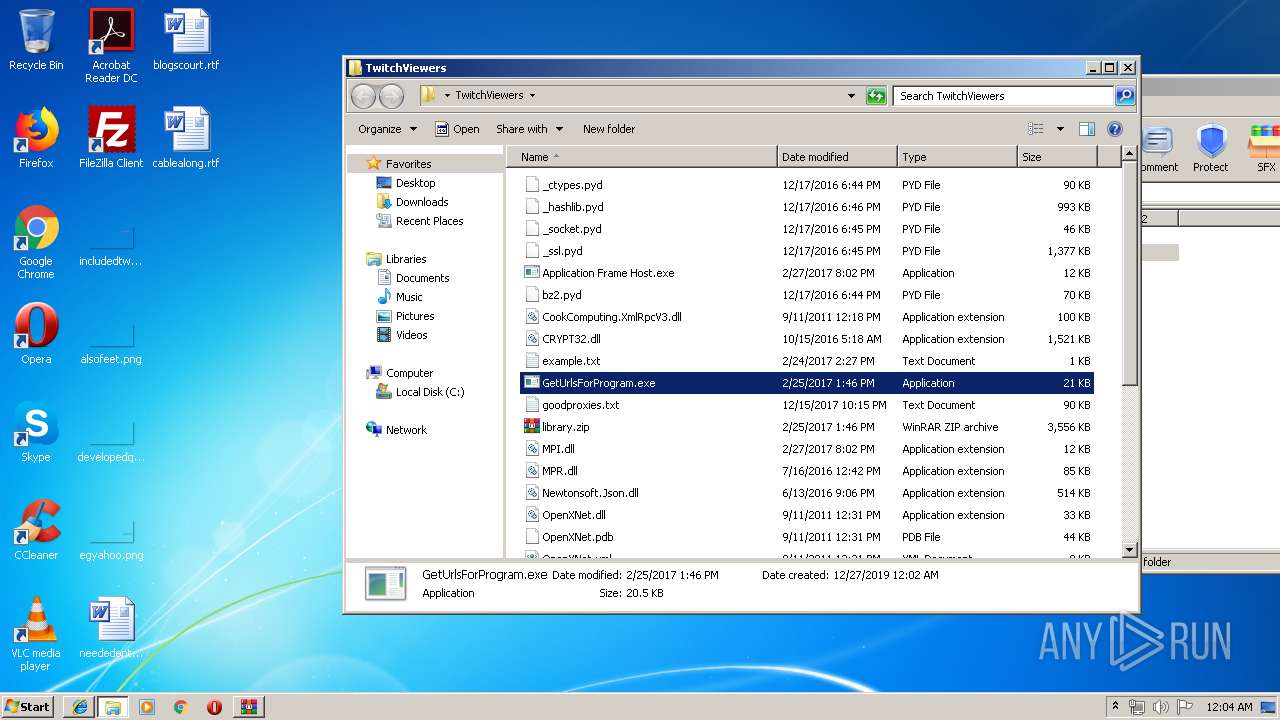
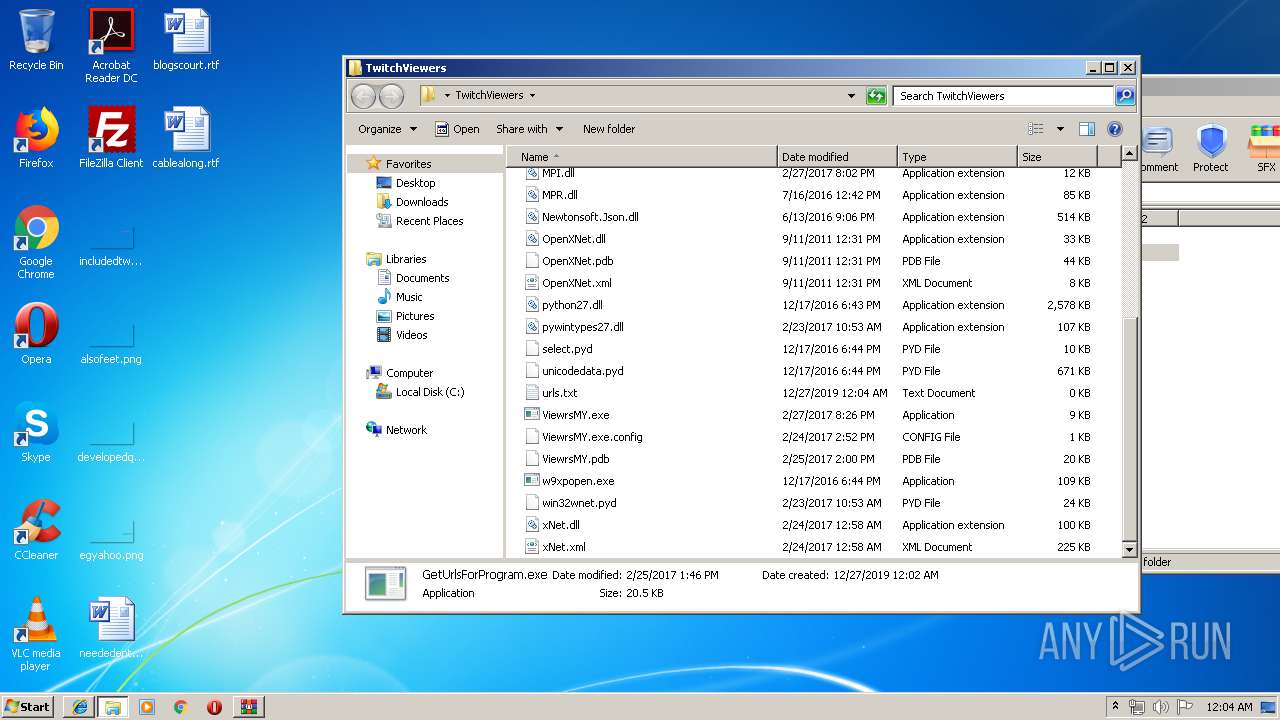
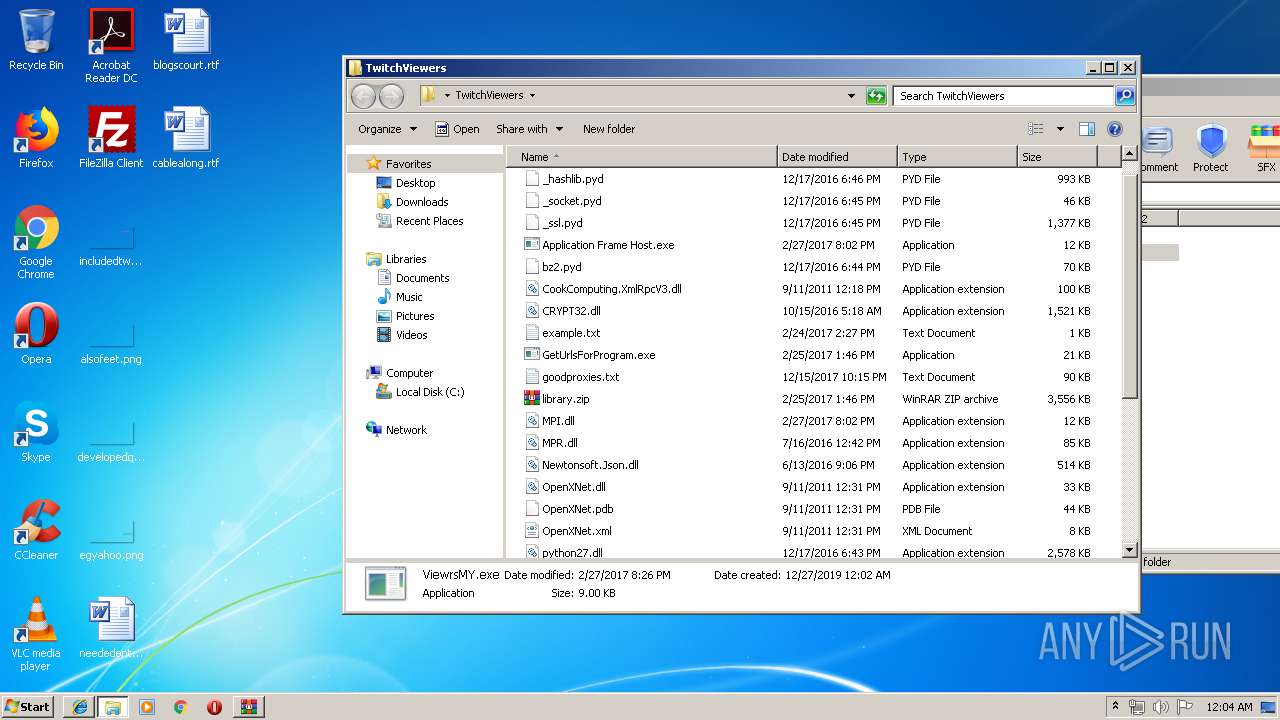
Application was dropped or rewritten from another process
- ViewrsMY.exe (PID: 2532)
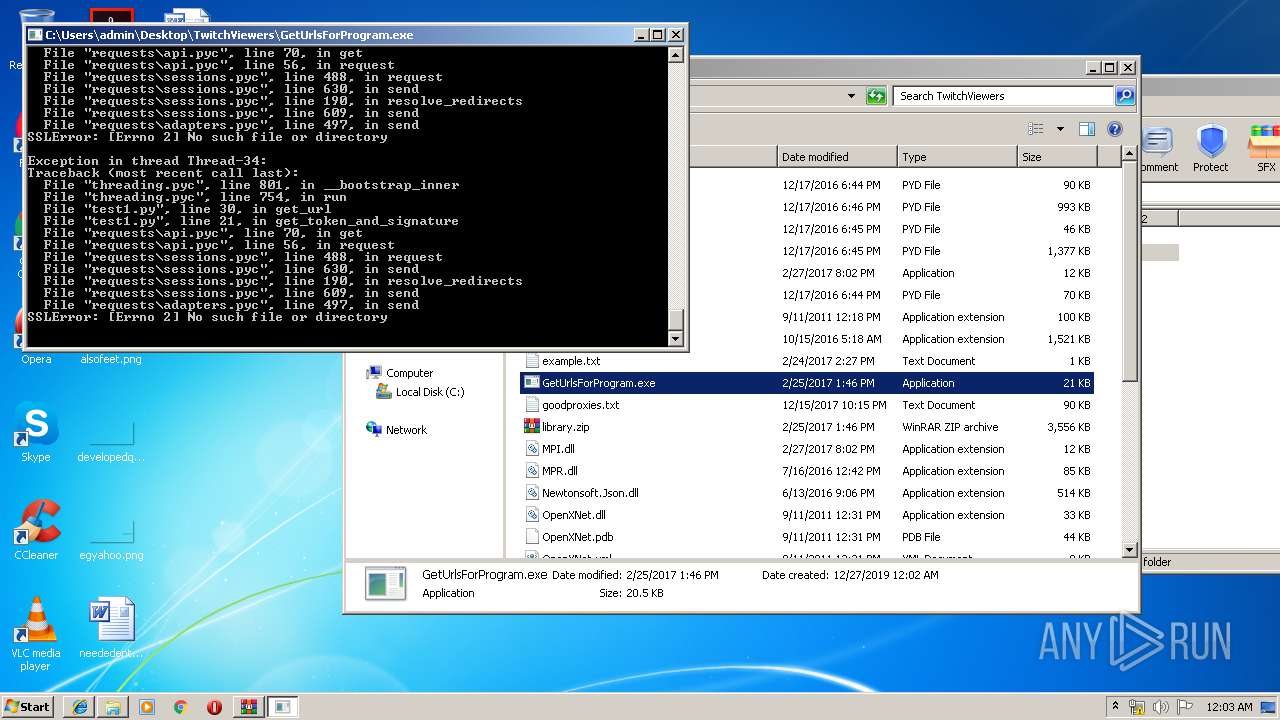
- GetUrlsForProgram.exe (PID: 1936)
- ViewrsMY.exe (PID: 2952)
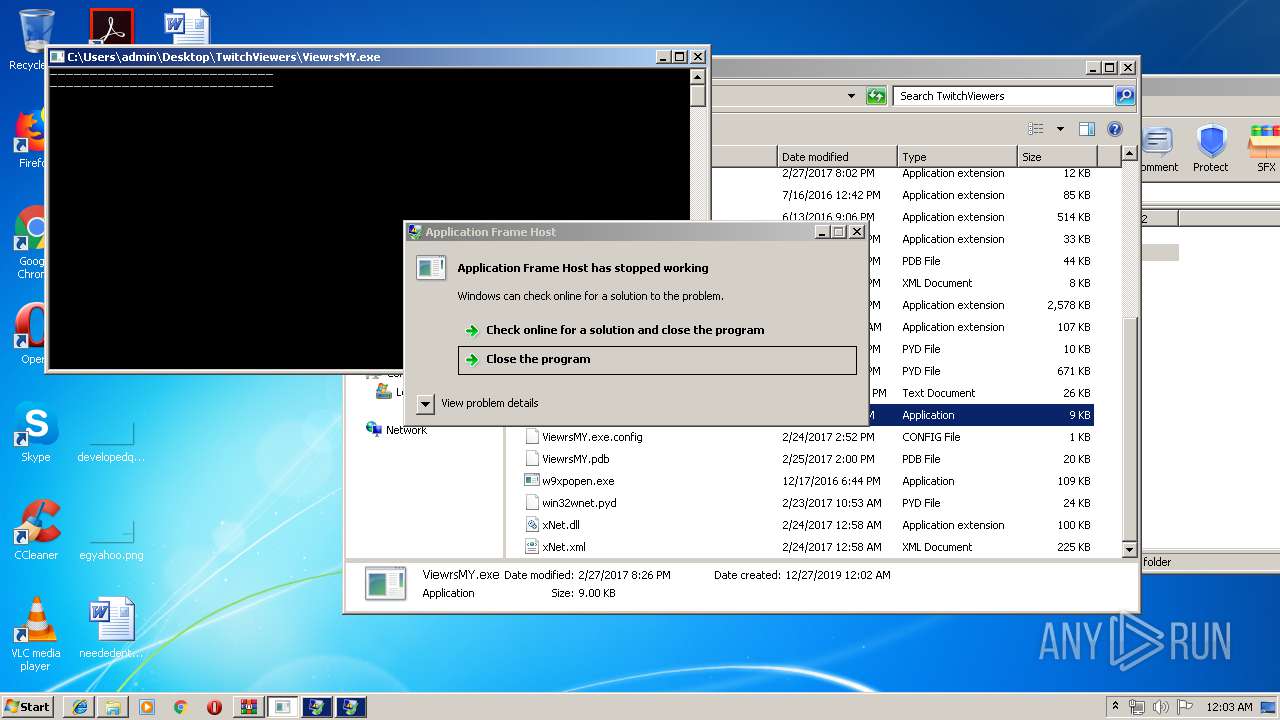
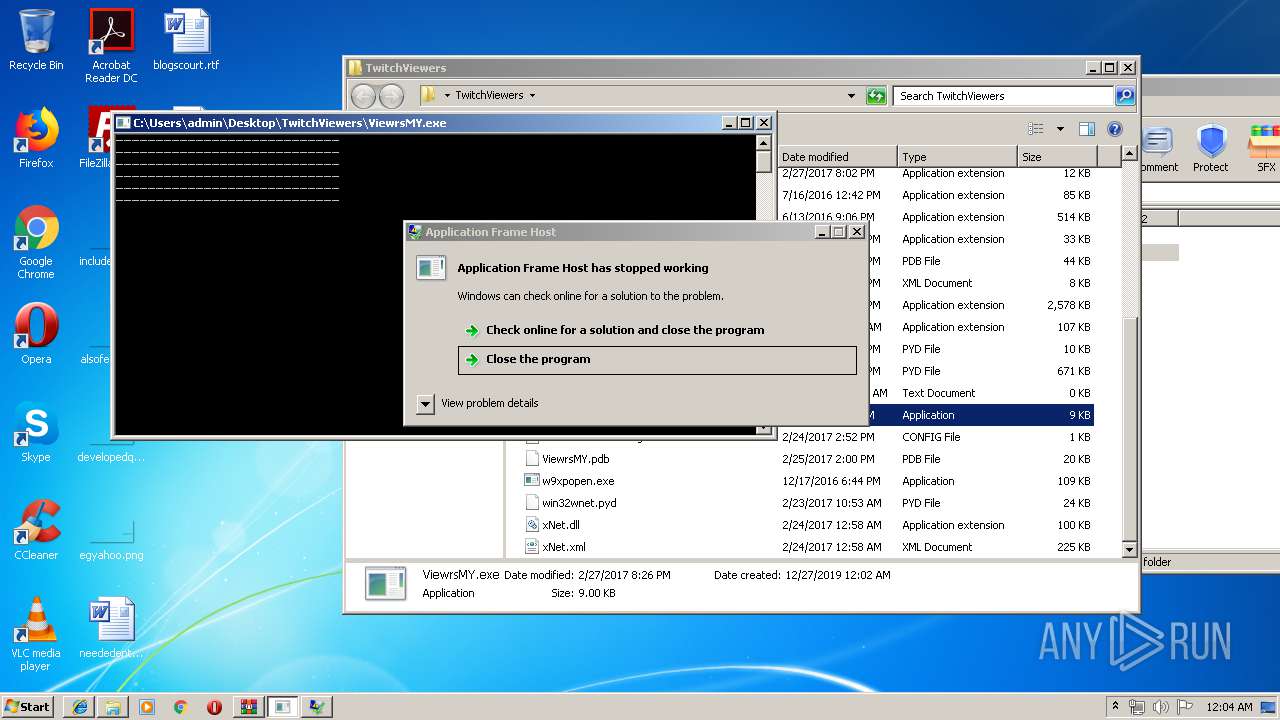
- Application Frame Host.exe (PID: 3708)
- Application Frame Host.exe (PID: 3280)
- Application Frame Host.exe (PID: 3724)
- ViewrsMY.exe (PID: 1524)
- GetUrlsForProgram.exe (PID: 2344)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 184)
- GetUrlsForProgram.exe (PID: 1936)
- GetUrlsForProgram.exe (PID: 2344)
- explorer.exe (PID: 352)
Changes the autorun value in the registry
- ViewrsMY.exe (PID: 2952)
- ViewrsMY.exe (PID: 1524)
SUSPICIOUS
Starts Internet Explorer
- explorer.exe (PID: 352)
Reads Internet Cache Settings
- explorer.exe (PID: 352)
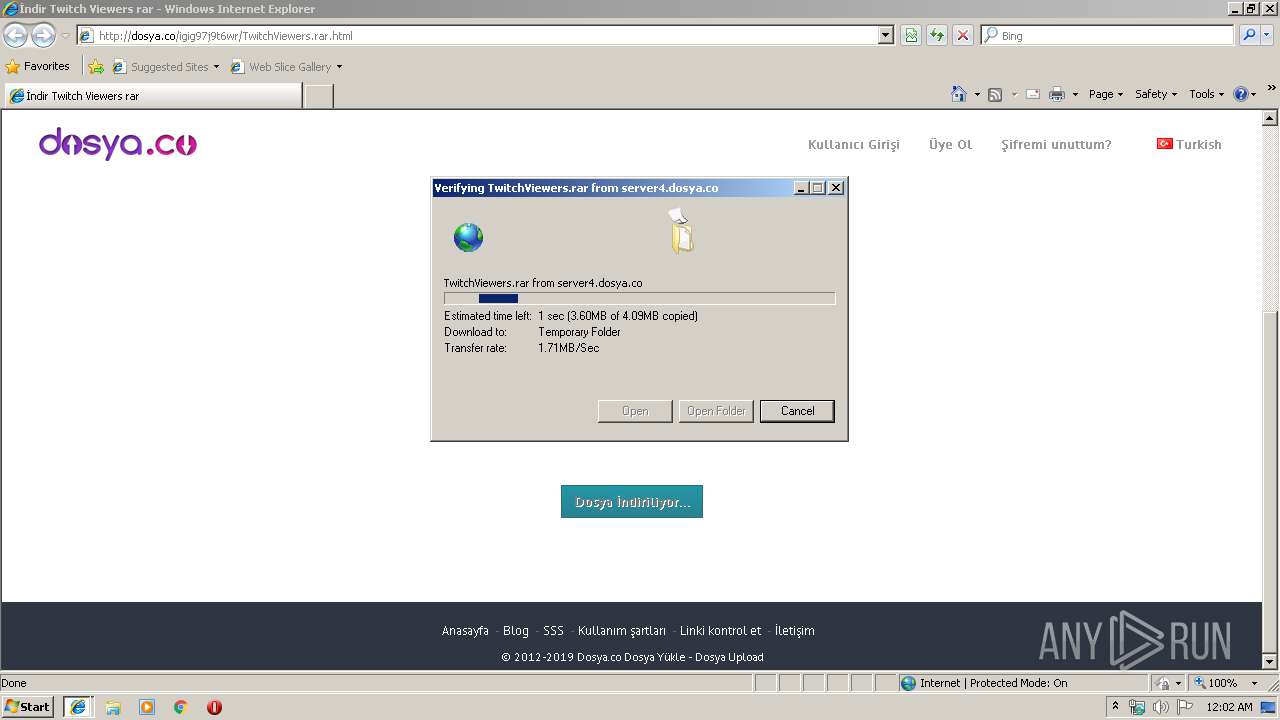
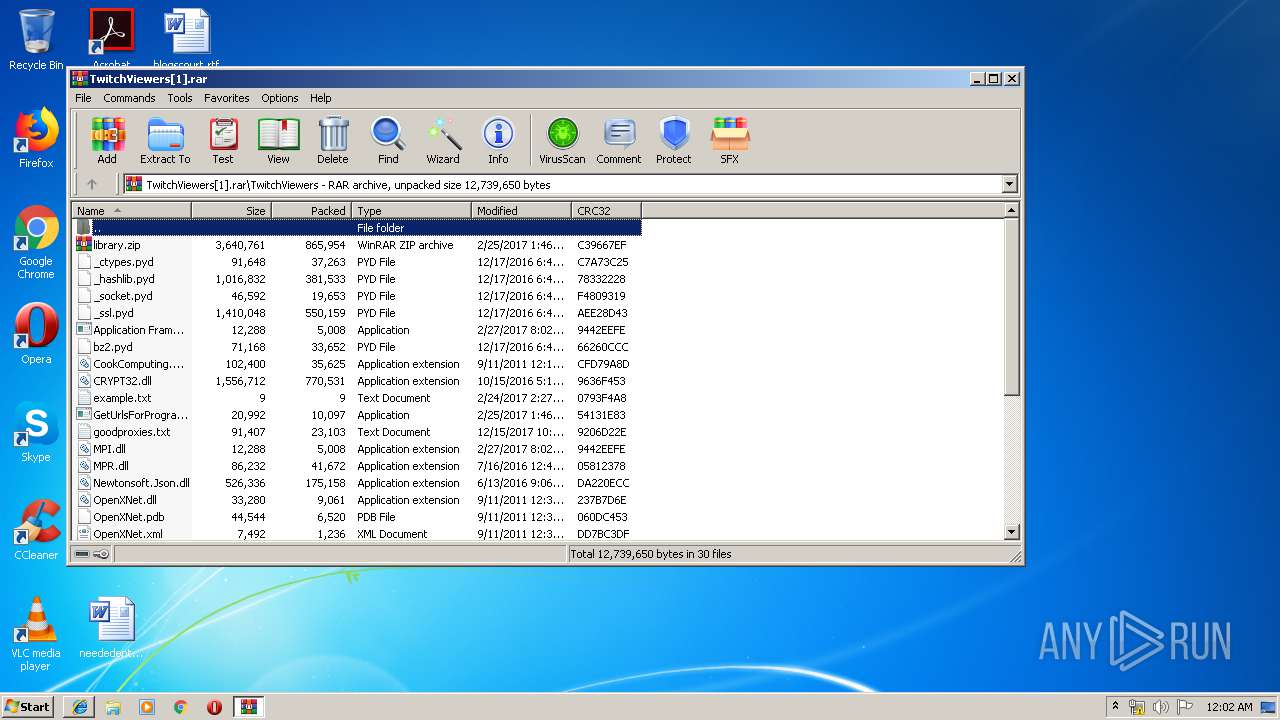
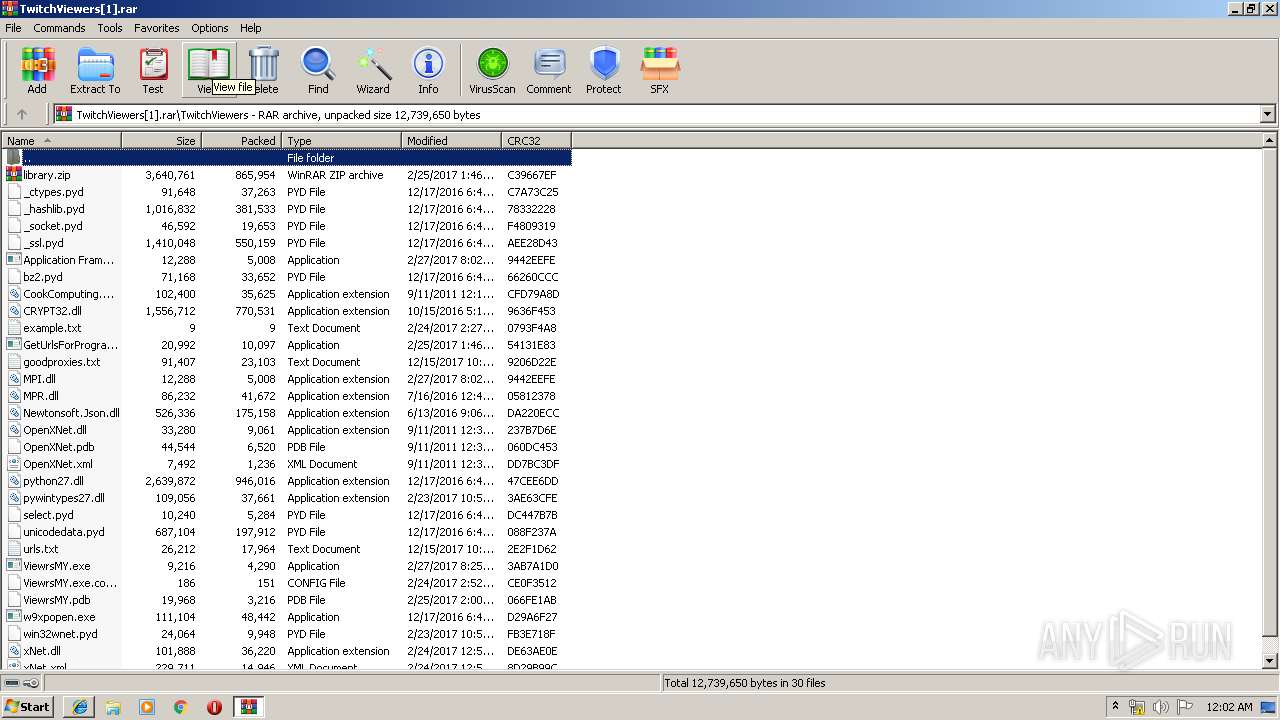
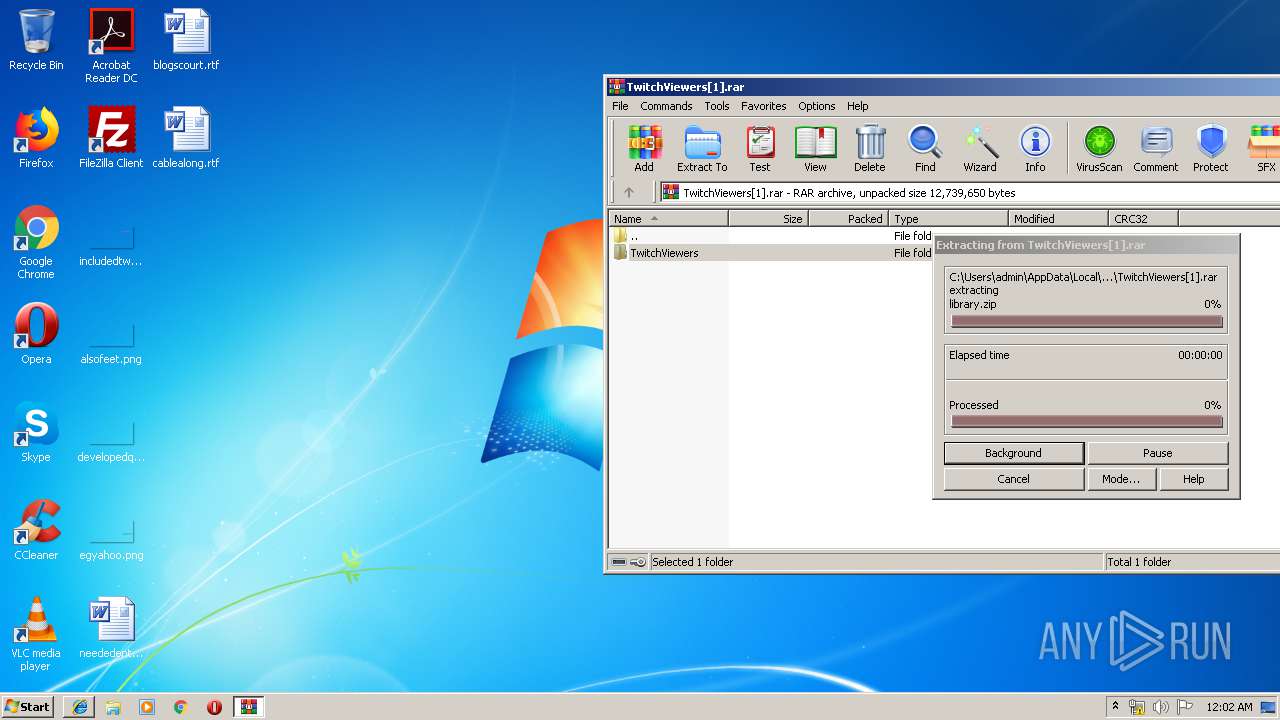
Executable content was dropped or overwritten
- WinRAR.exe (PID: 976)
- ViewrsMY.exe (PID: 2952)
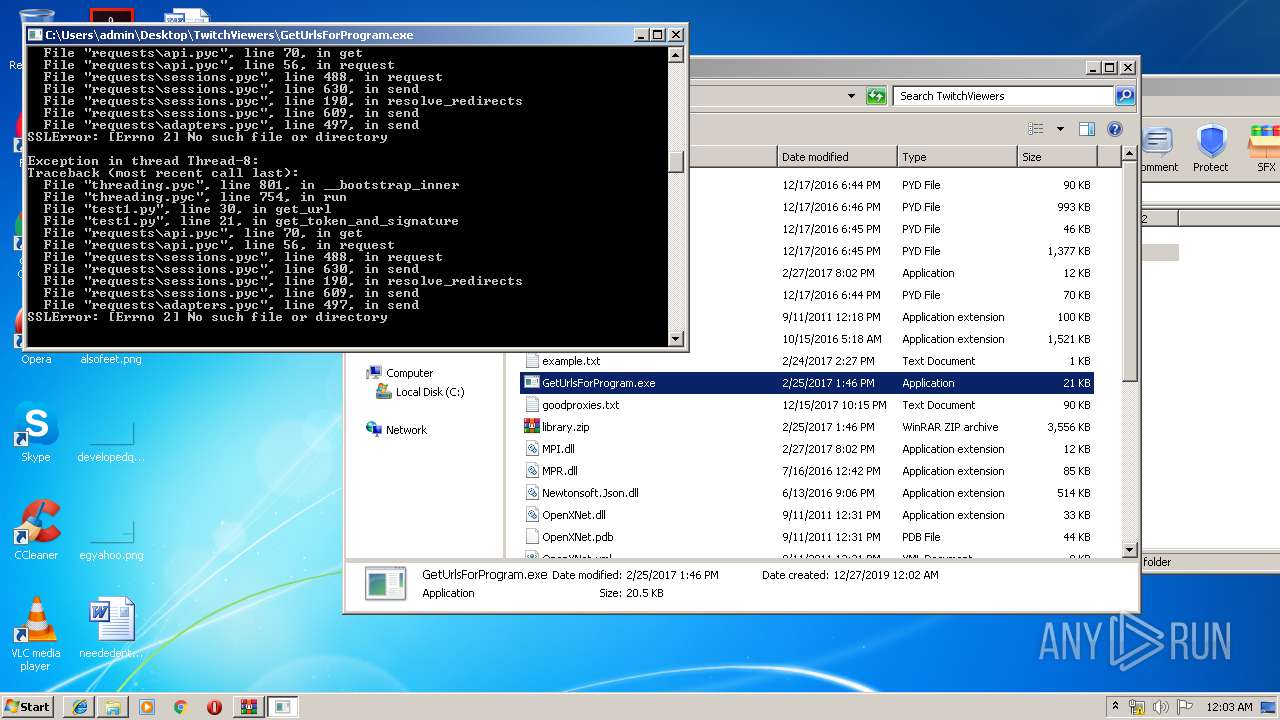
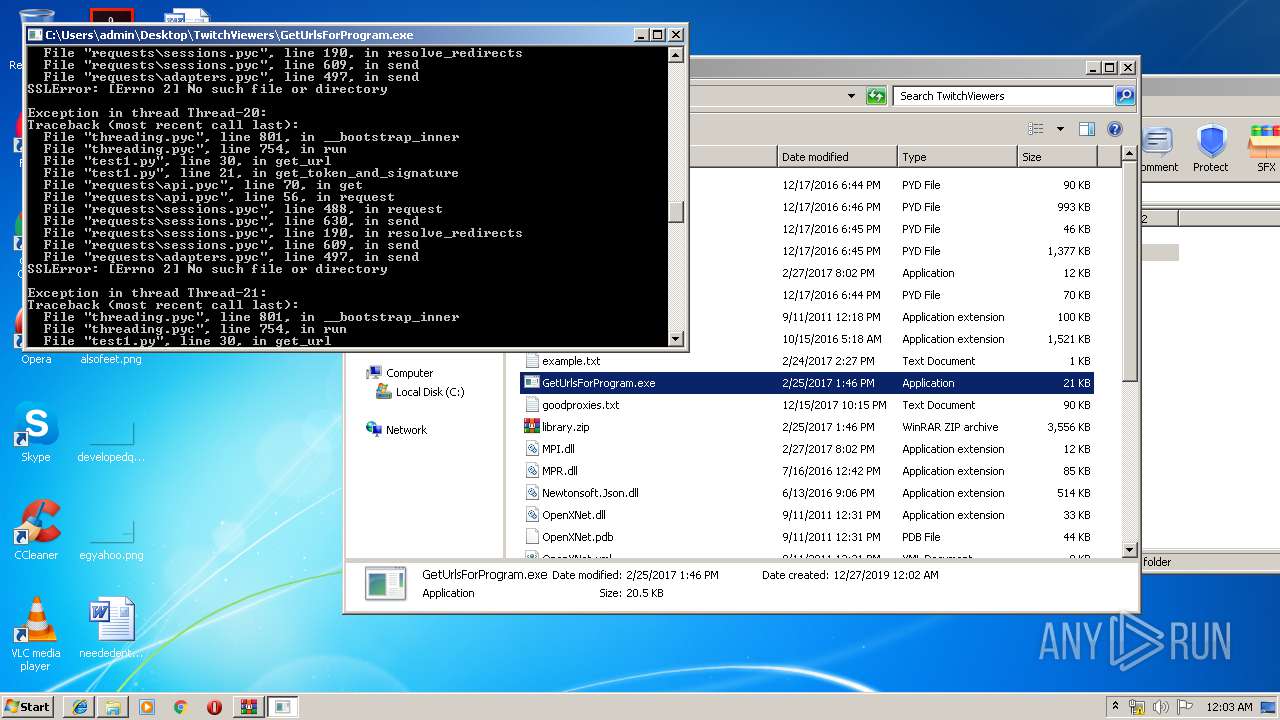
Loads Python modules
- SearchProtocolHost.exe (PID: 184)
- GetUrlsForProgram.exe (PID: 1936)
- GetUrlsForProgram.exe (PID: 2344)
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1016)
Creates files in the program directory
- ViewrsMY.exe (PID: 2952)
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 352)
Connects to unusual port
- ViewrsMY.exe (PID: 2952)
INFO
Creates files in the user directory
- iexplore.exe (PID: 1912)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1016)
- iexplore.exe (PID: 2152)
Application launched itself
- iexplore.exe (PID: 1912)
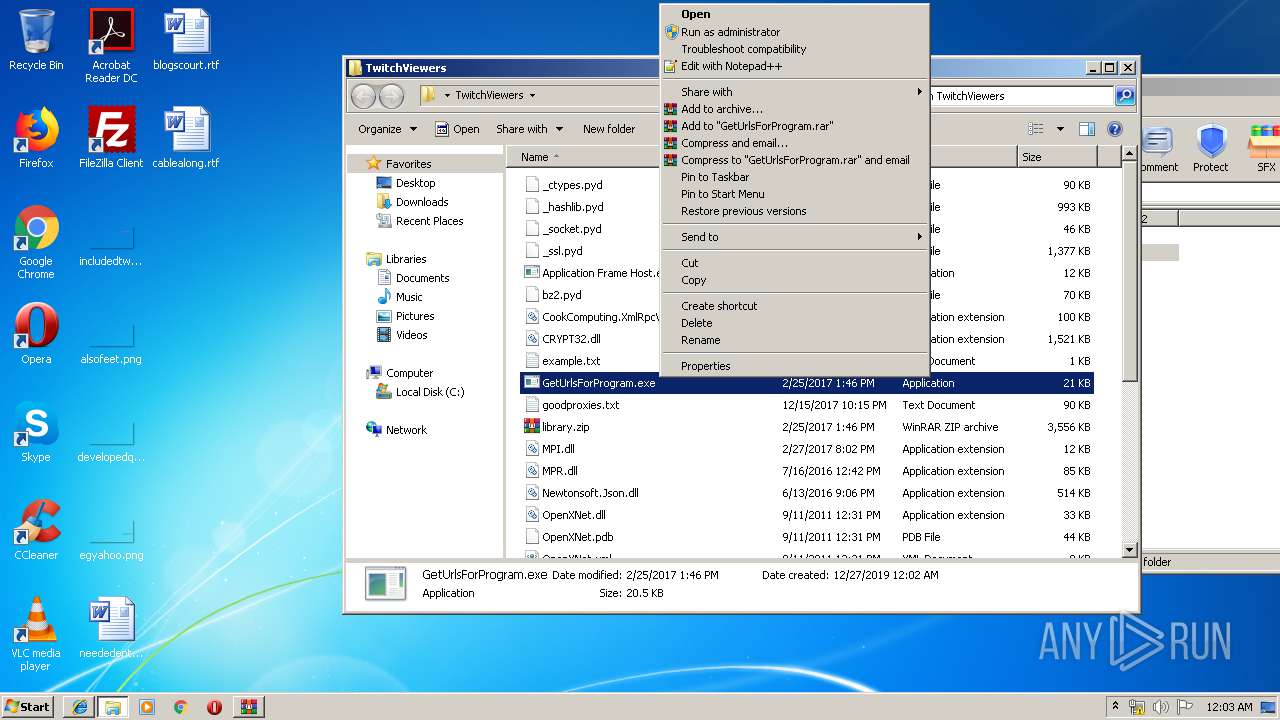
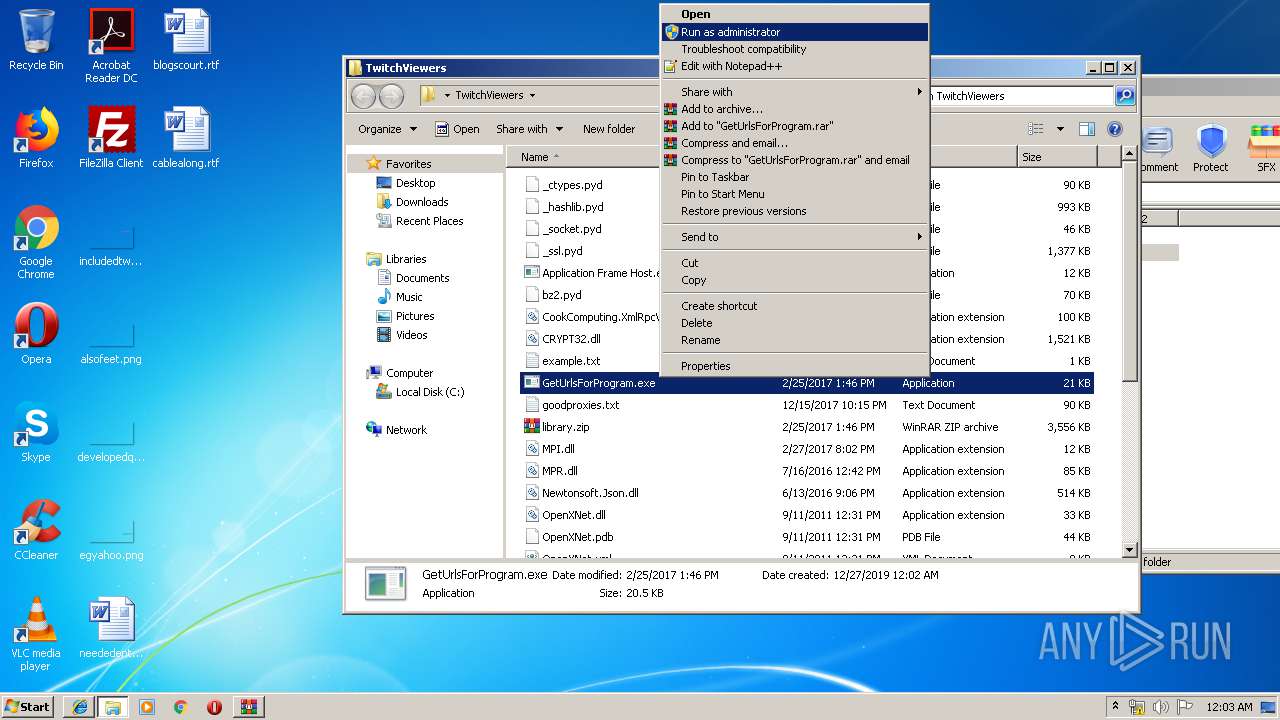
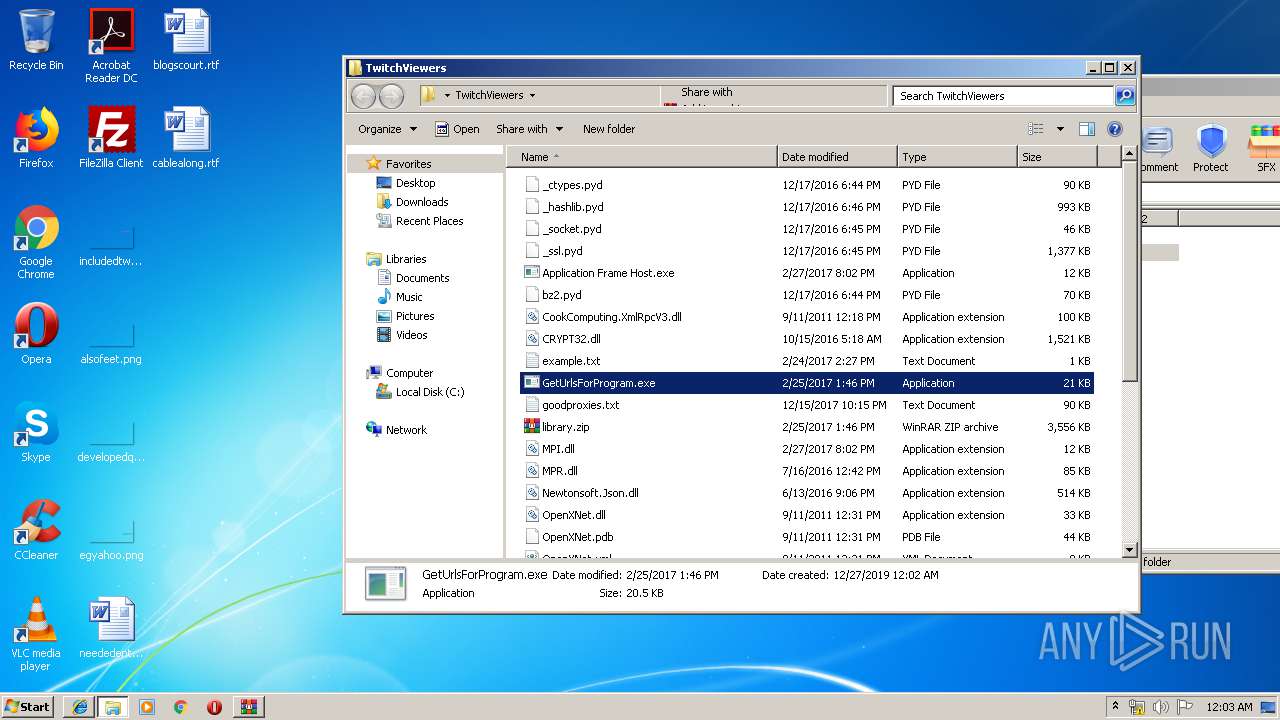
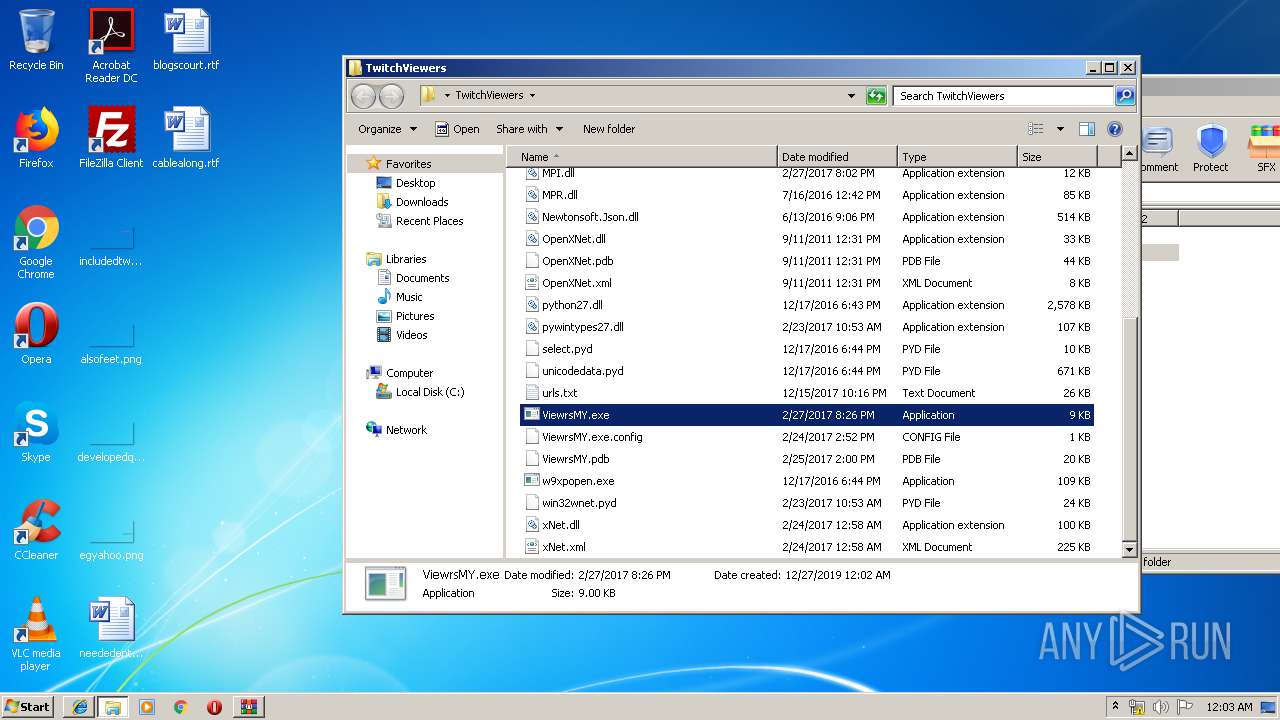
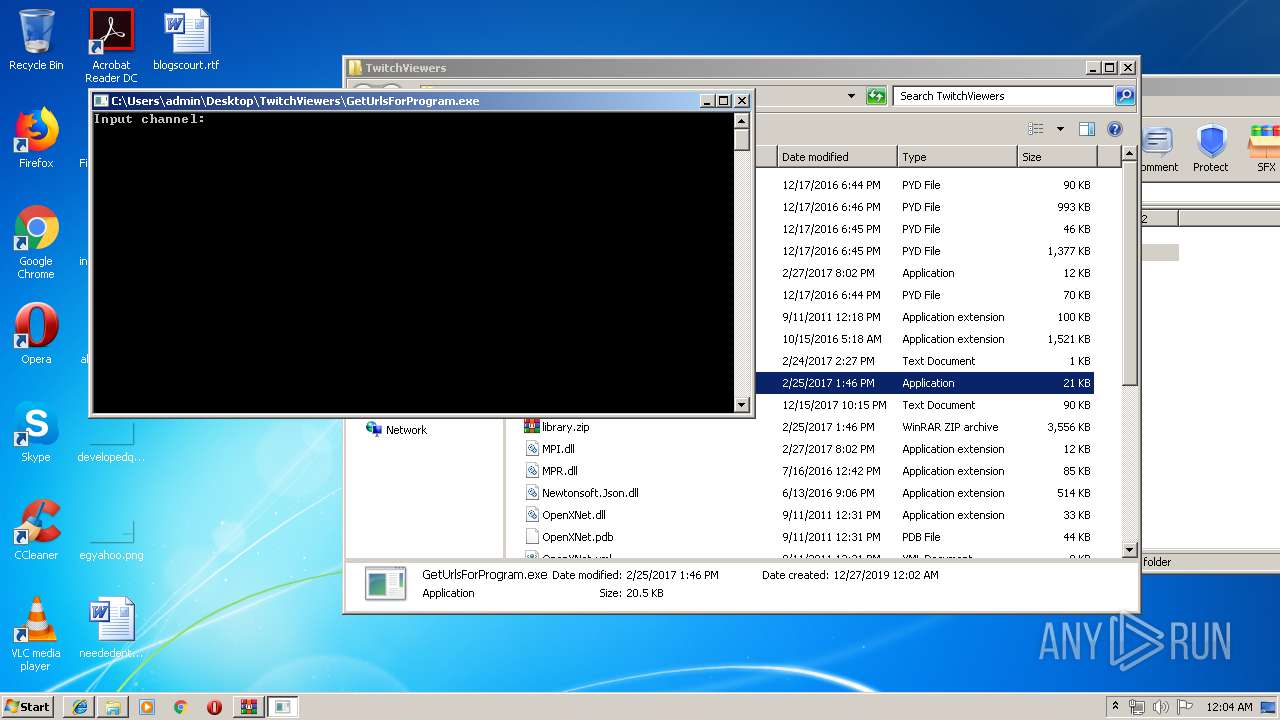
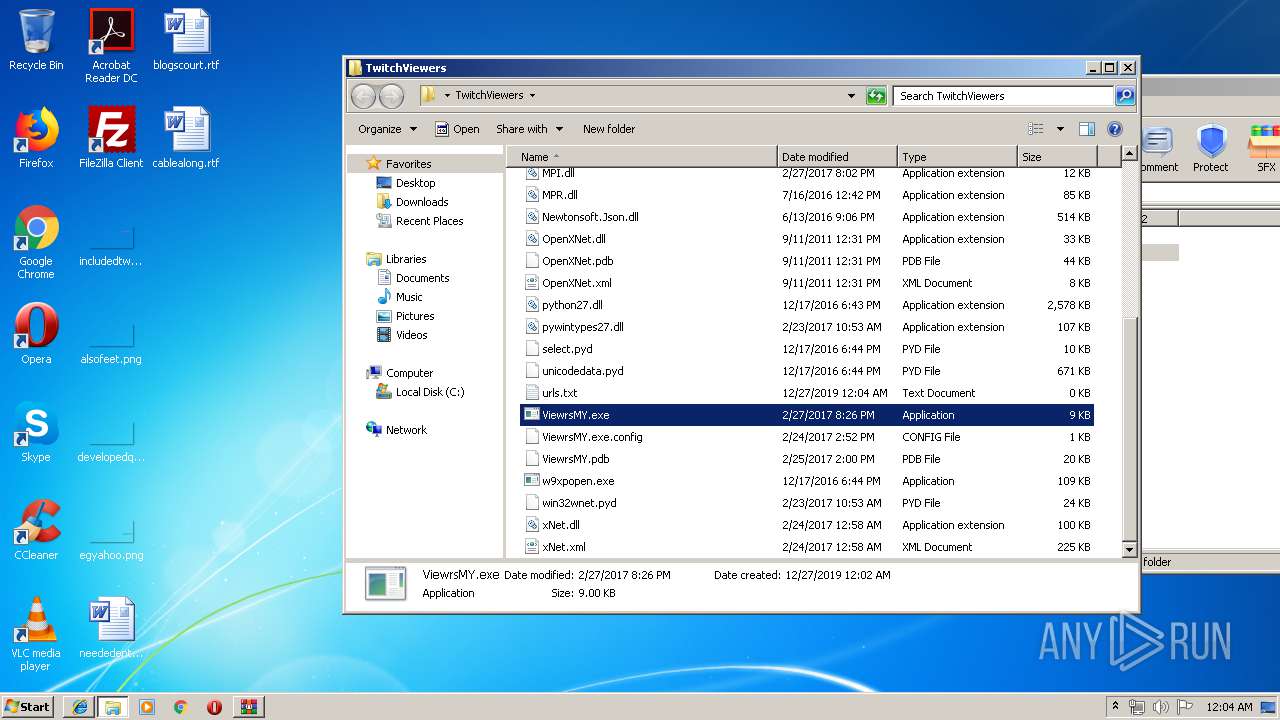
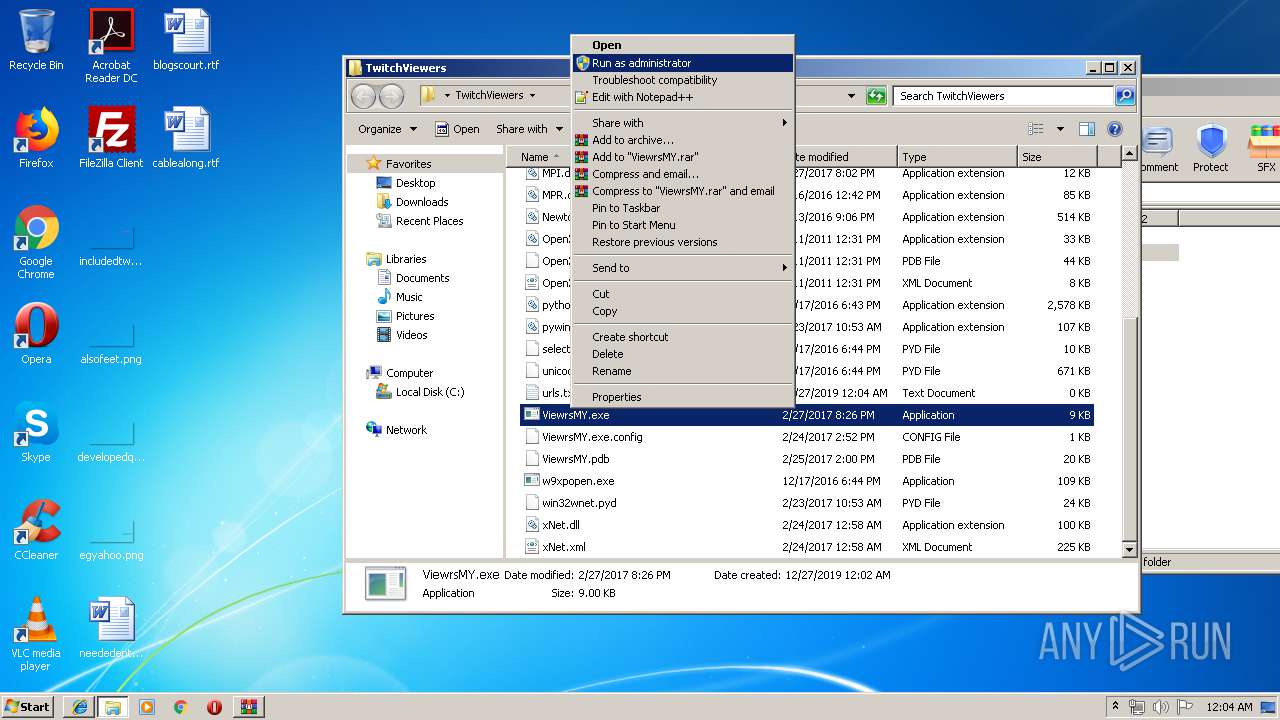
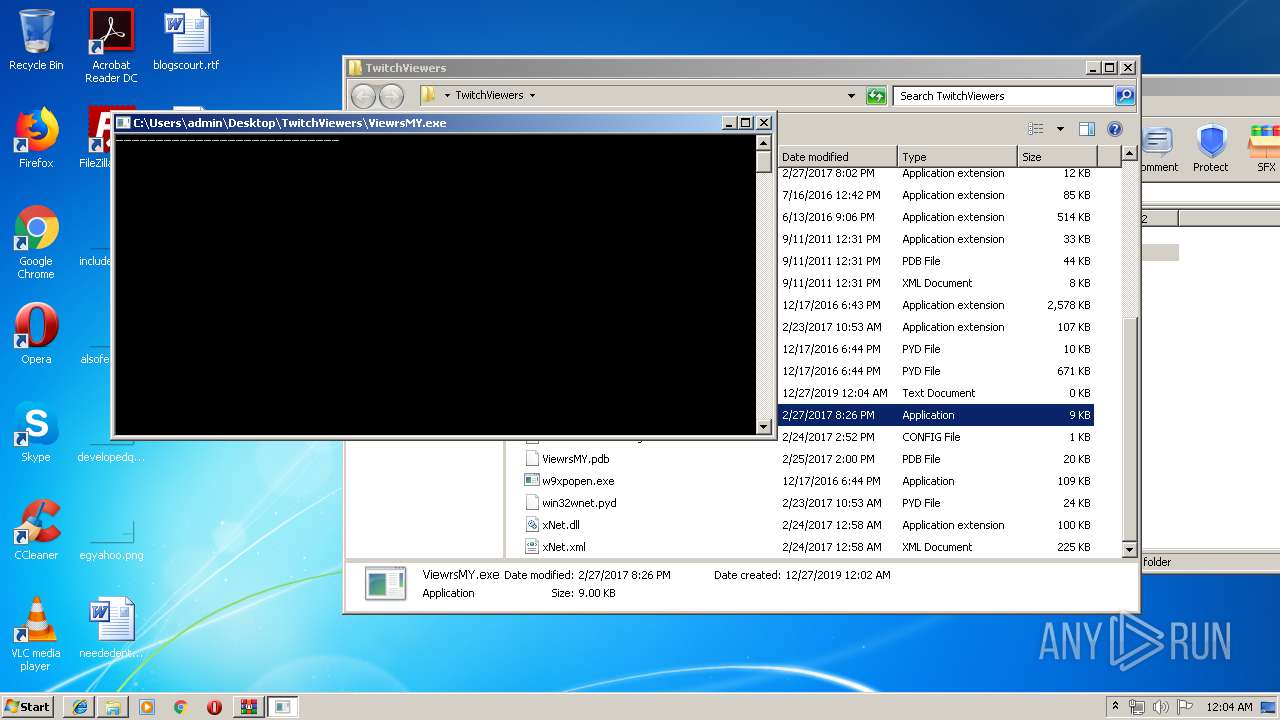
Manual execution by user
- GetUrlsForProgram.exe (PID: 1936)
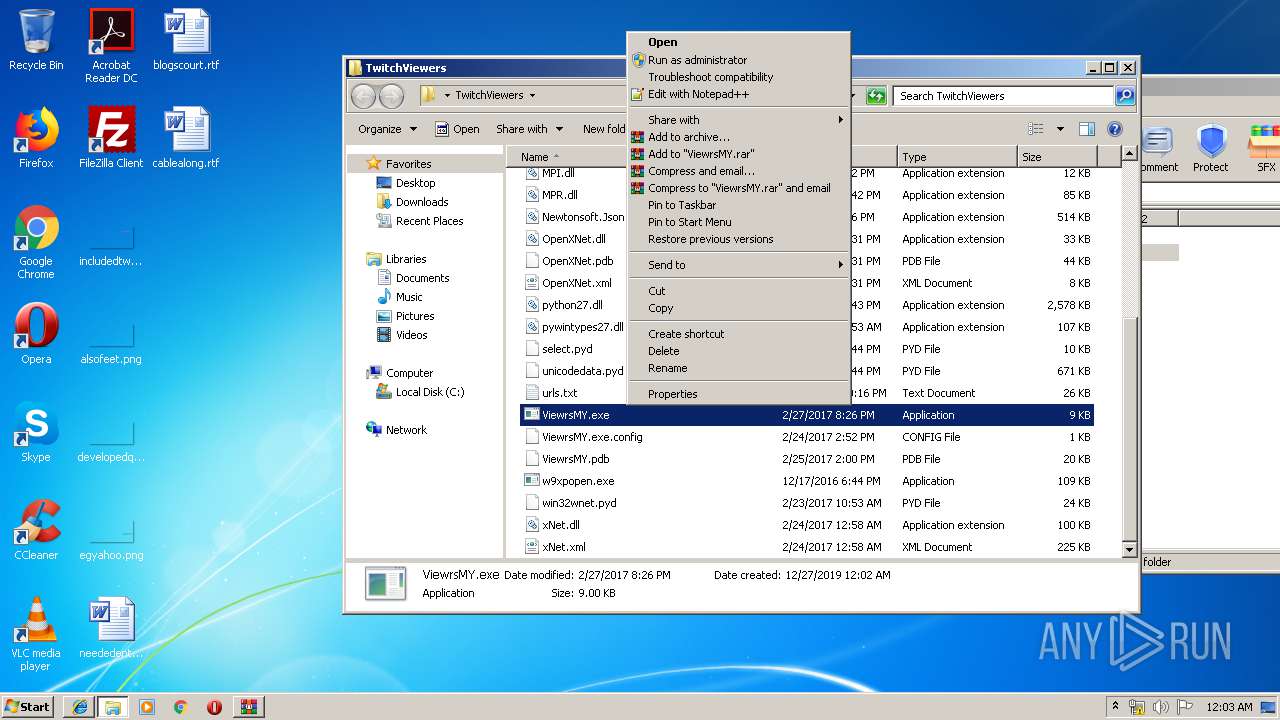
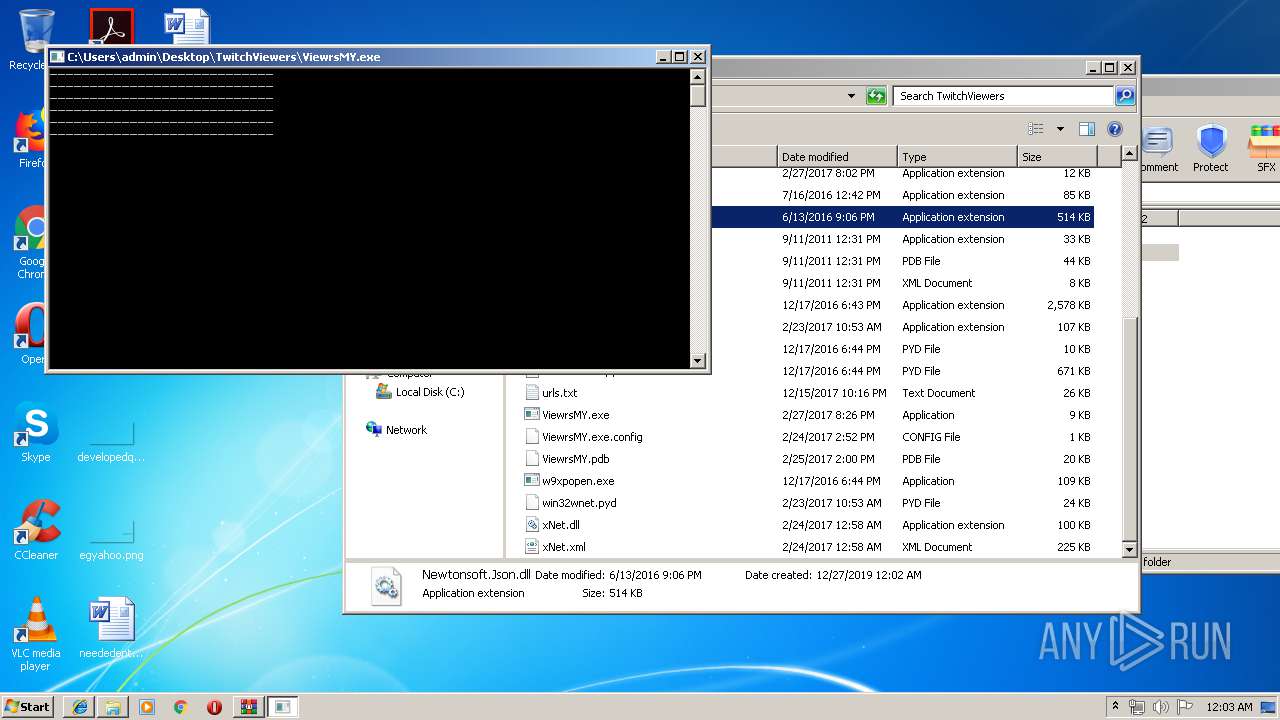
- ViewrsMY.exe (PID: 2952)
- rundll32.exe (PID: 1992)
Reads settings of System Certificates
- iexplore.exe (PID: 1912)
Changes internet zones settings
- iexplore.exe (PID: 1912)
Reads internet explorer settings
- iexplore.exe (PID: 2152)
Reads Internet Cache Settings
- iexplore.exe (PID: 2152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
71
Monitored processes
15
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
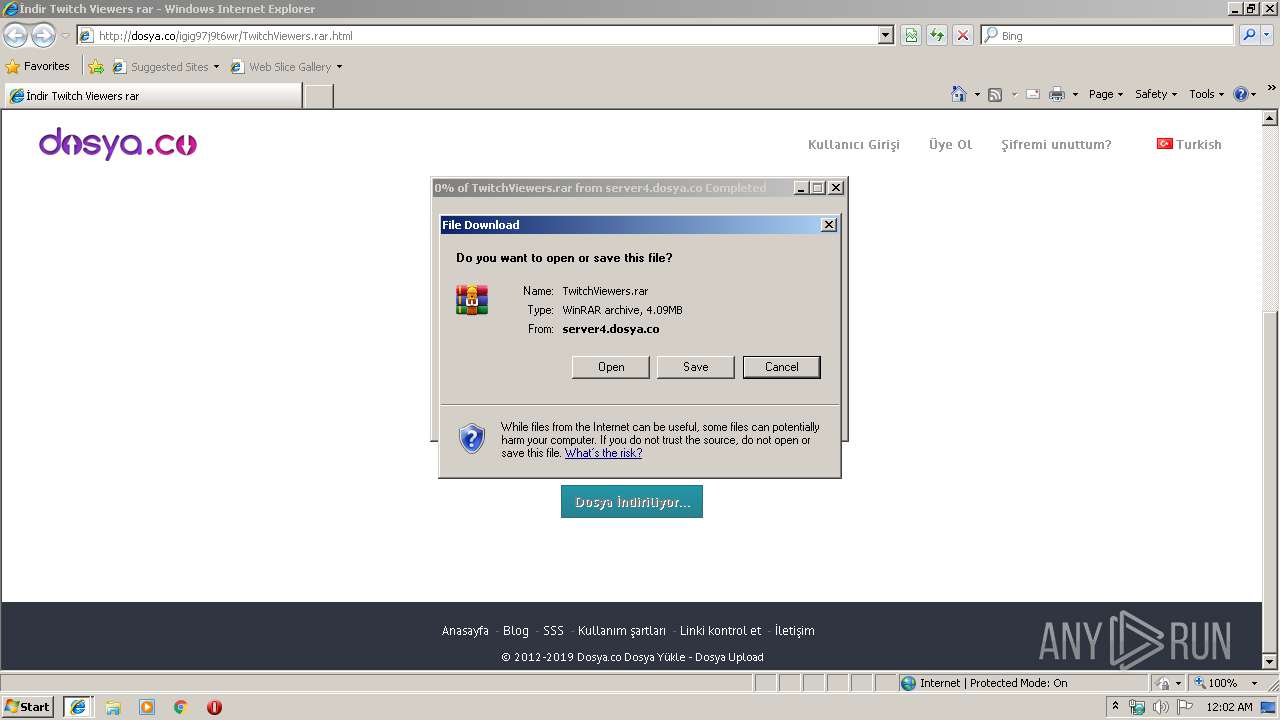
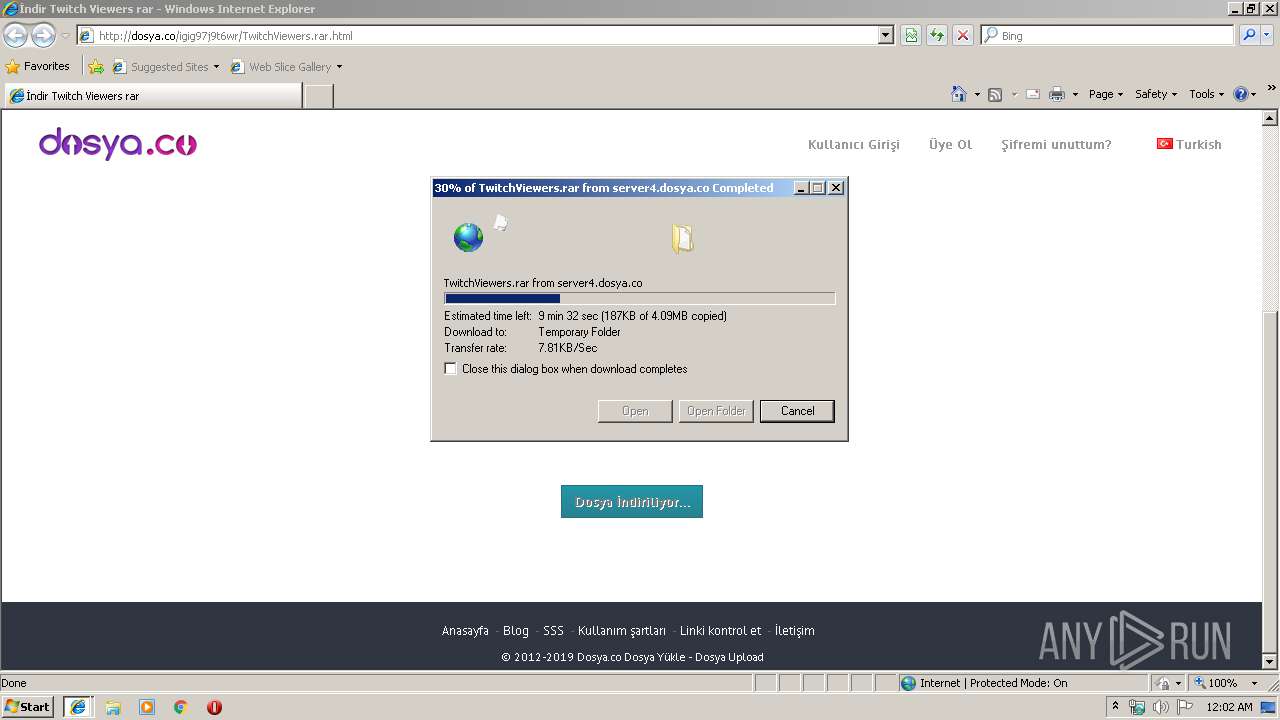
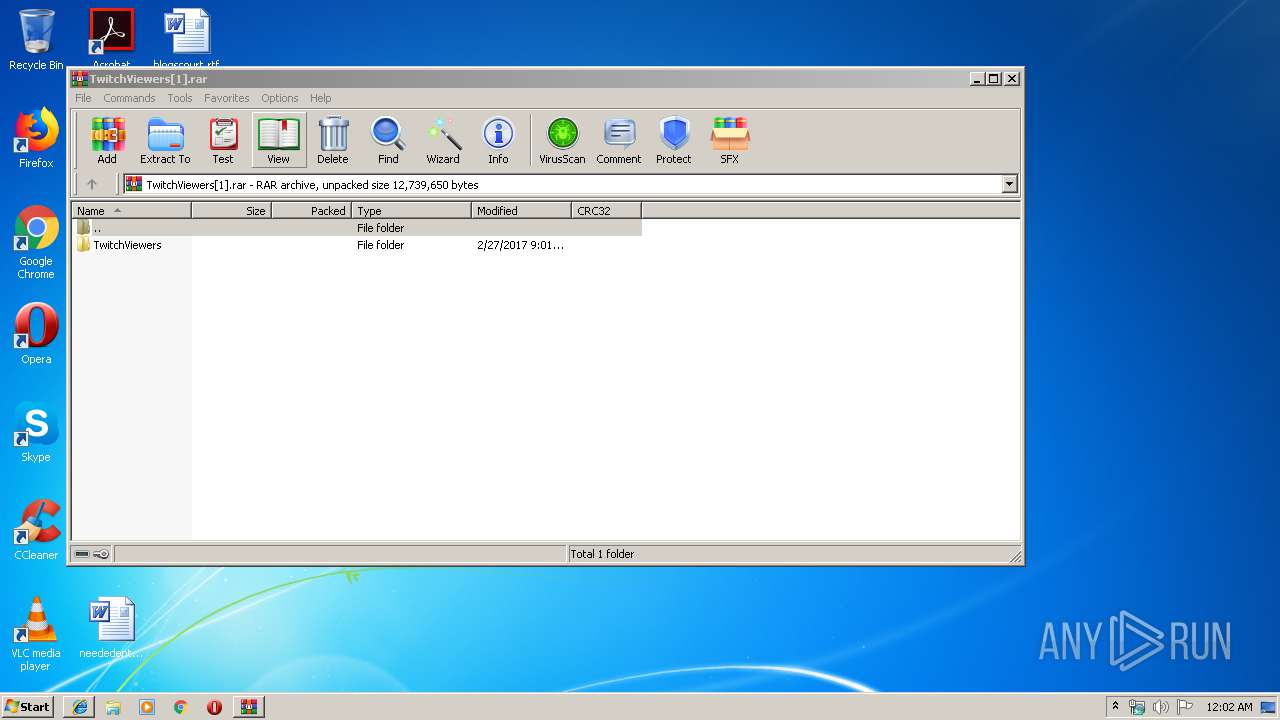
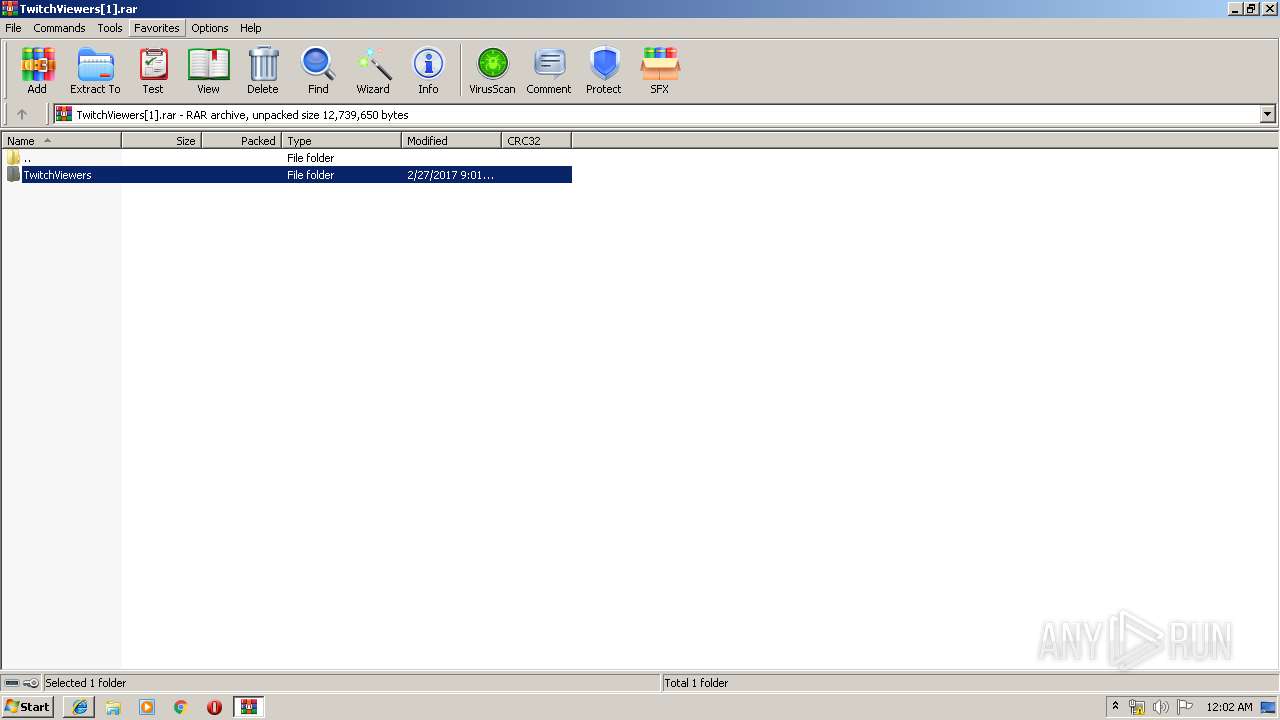
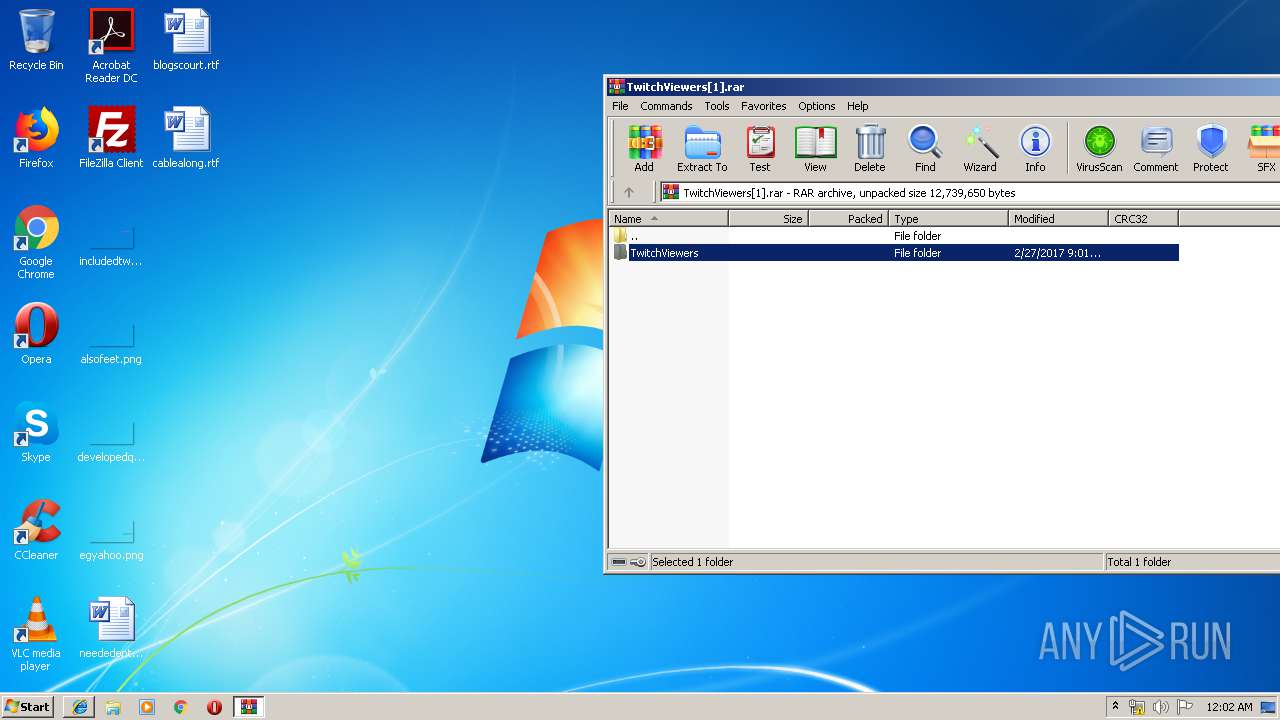
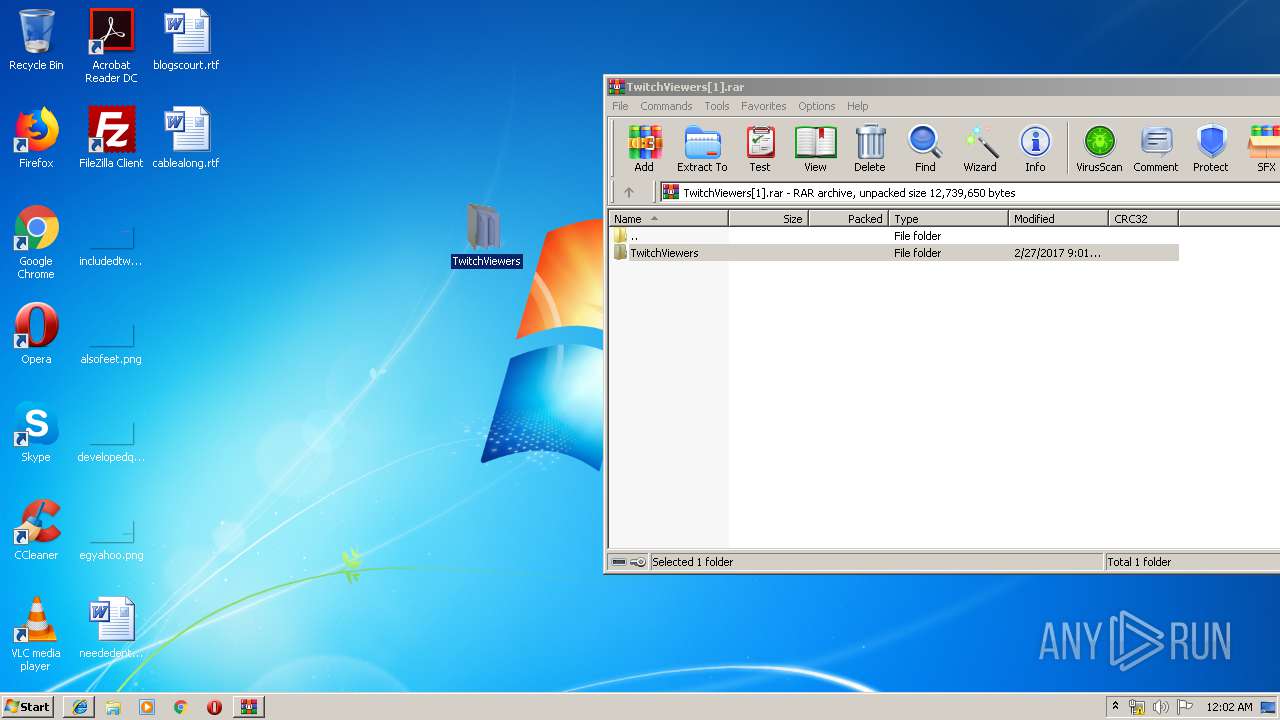
| 976 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\O41FY35B\TwitchViewers[1].rar" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1016 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
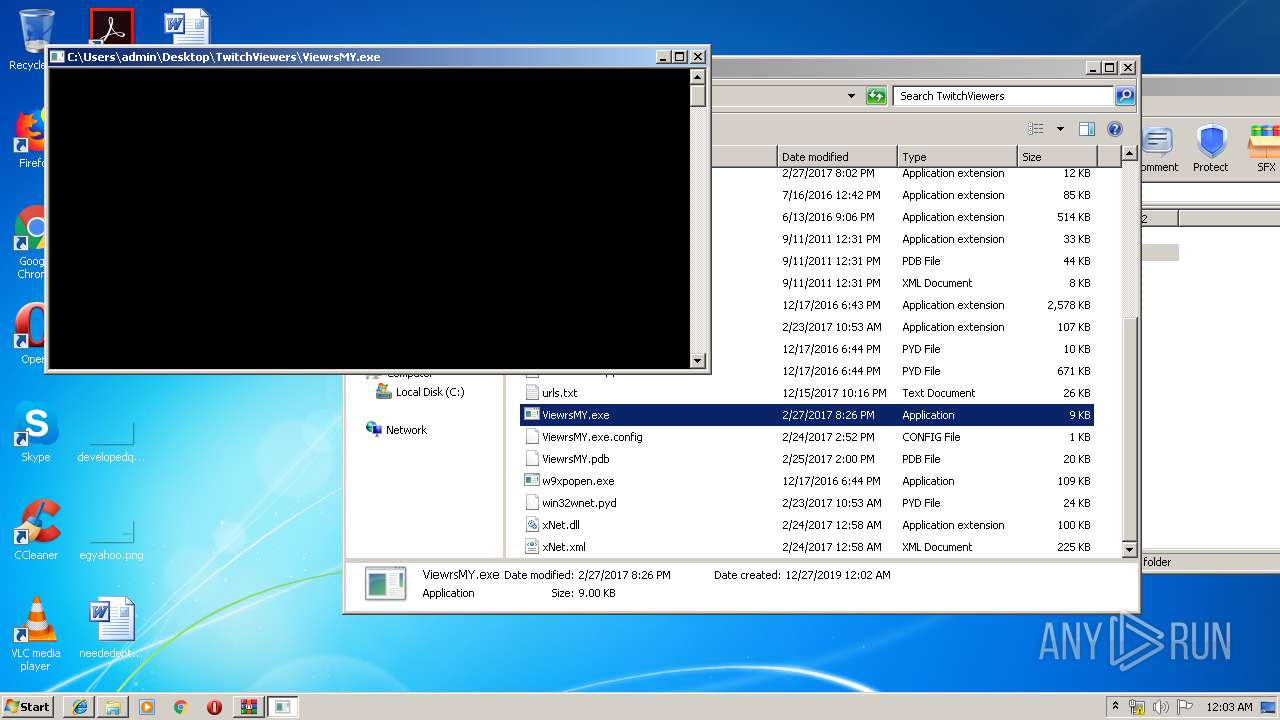
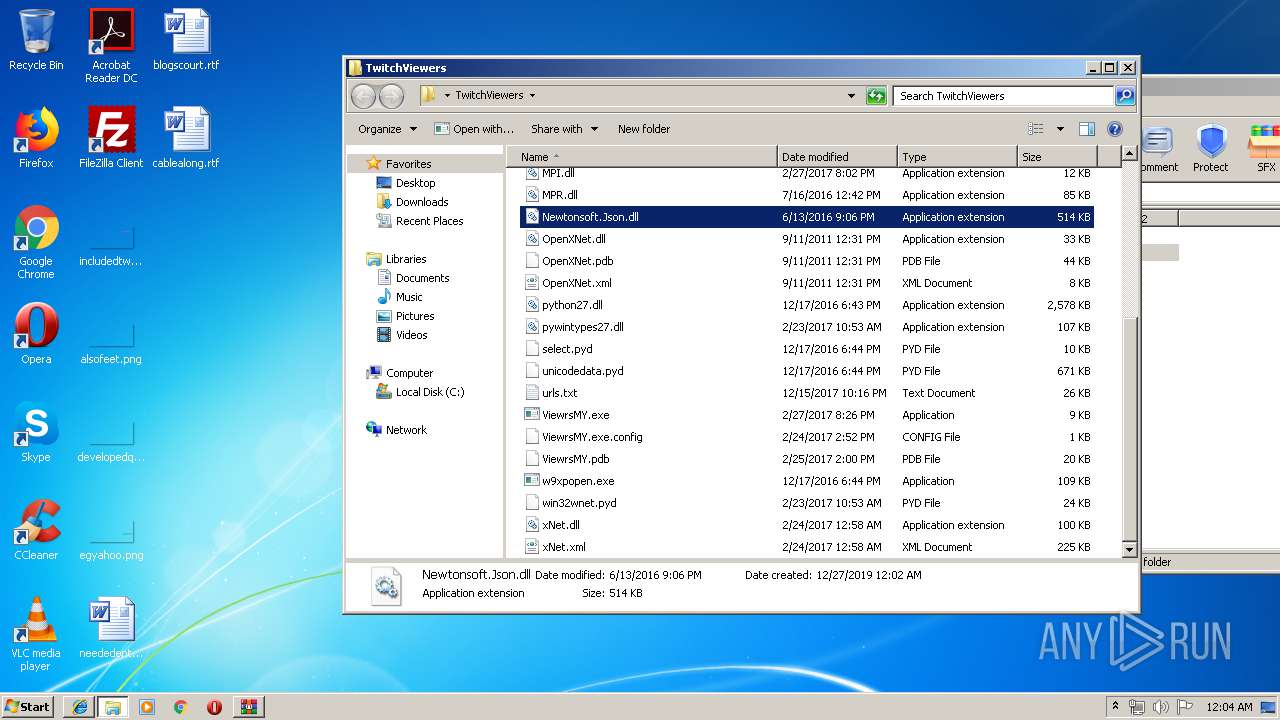
| 1524 | "C:\Users\admin\Desktop\TwitchViewers\ViewrsMY.exe" | C:\Users\admin\Desktop\TwitchViewers\ViewrsMY.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: ViewrsMY Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1912 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://dosya.co/igig97j9t6wr/TwitchViewers.rar.html" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
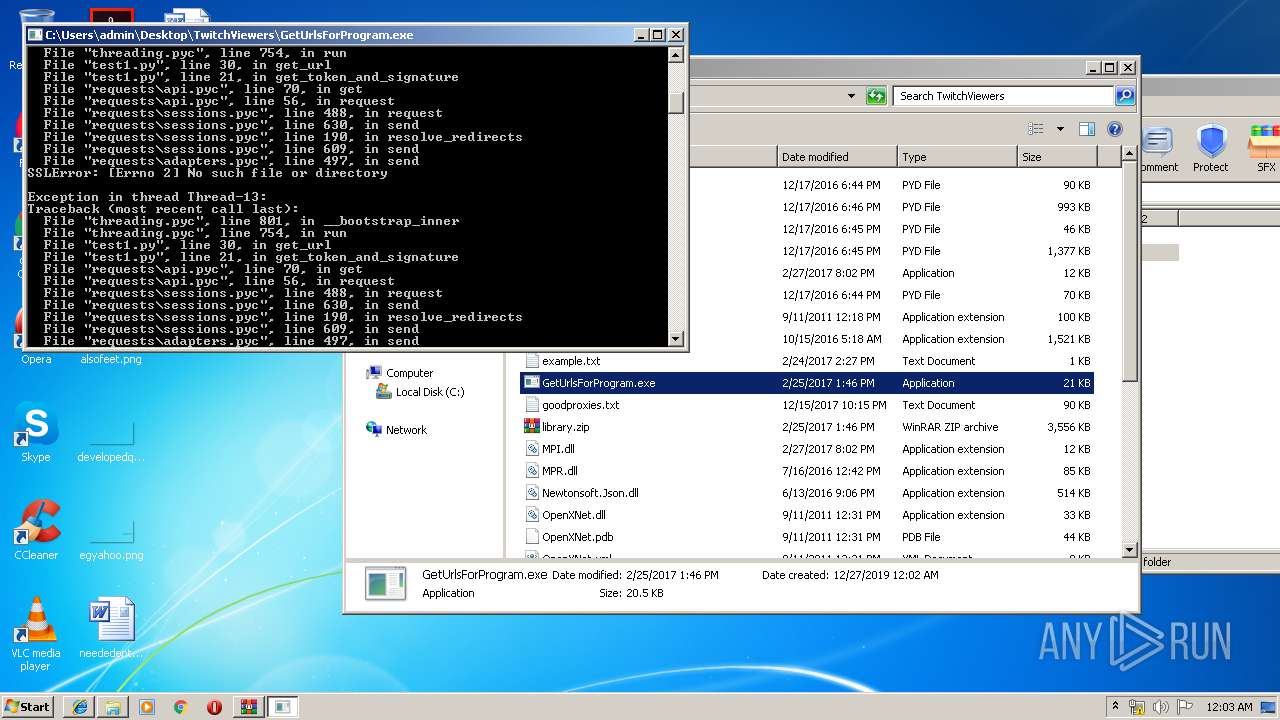
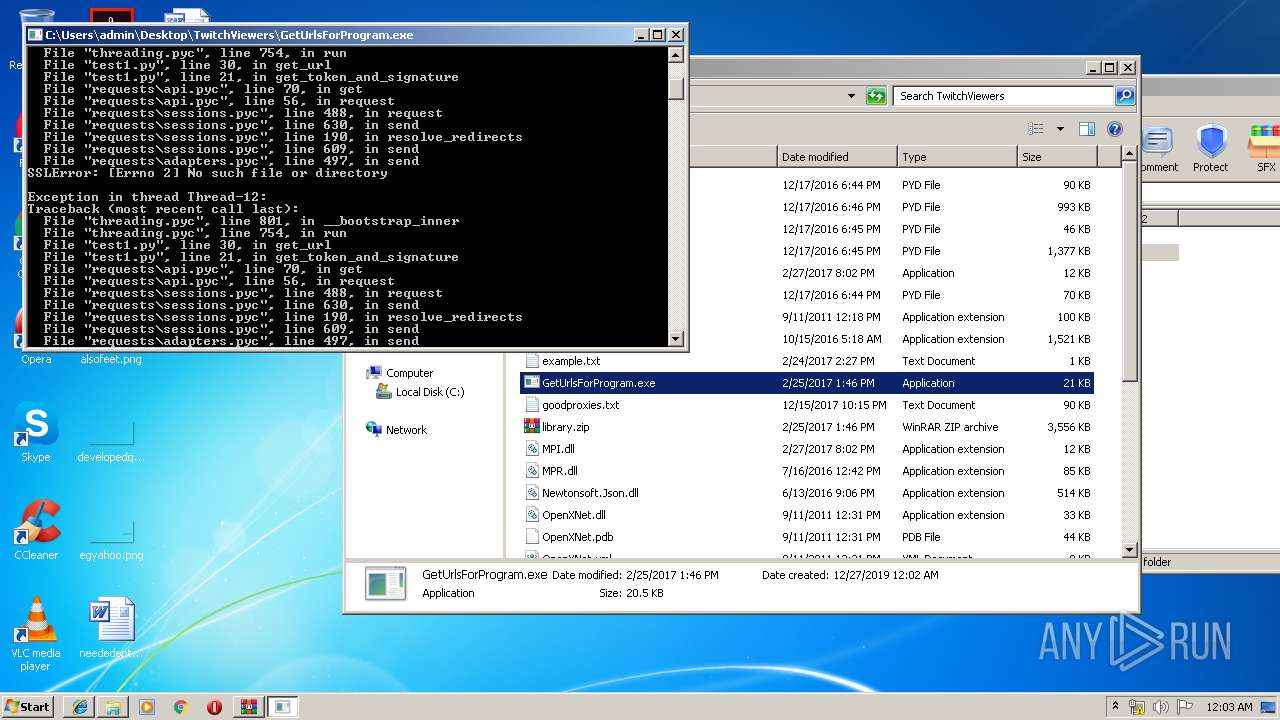
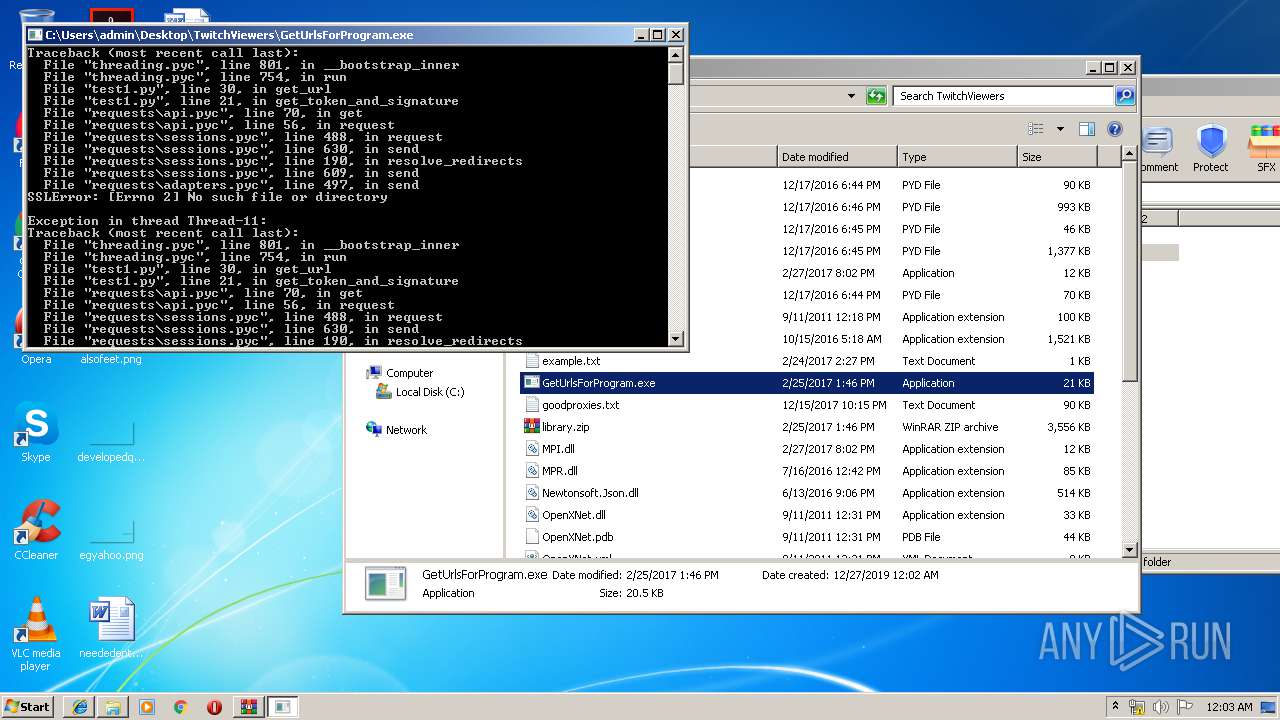
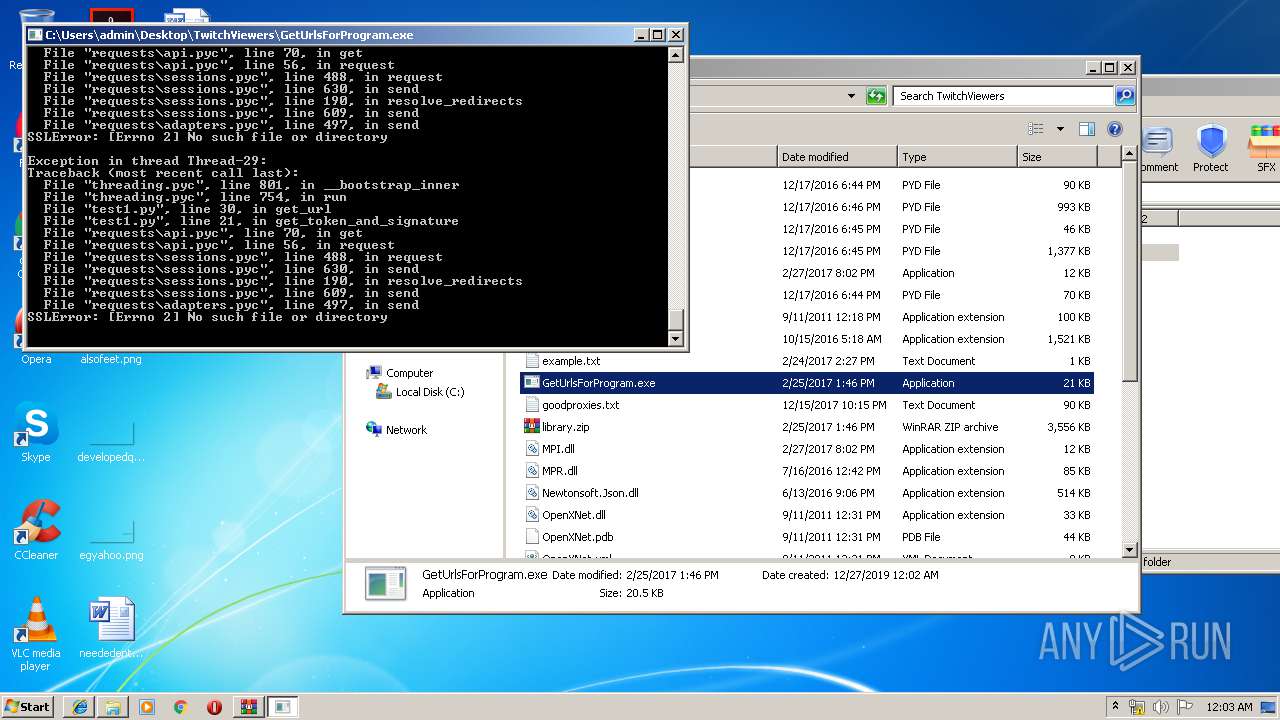
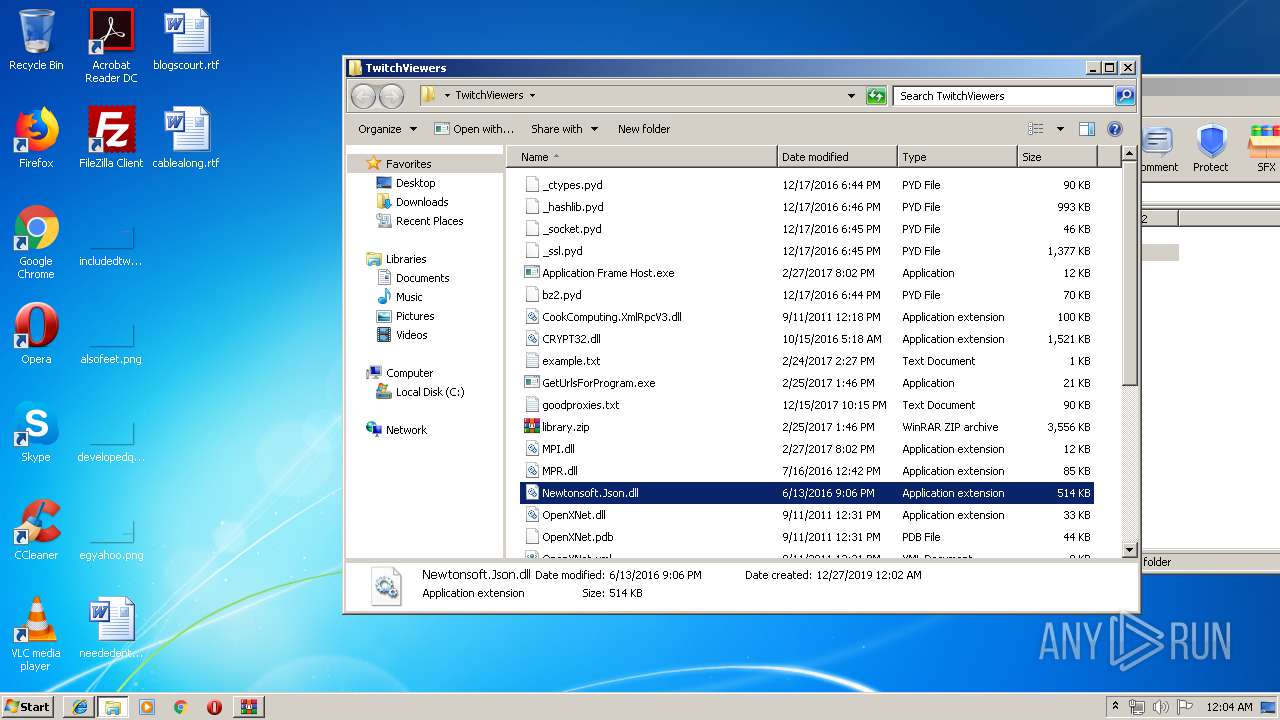
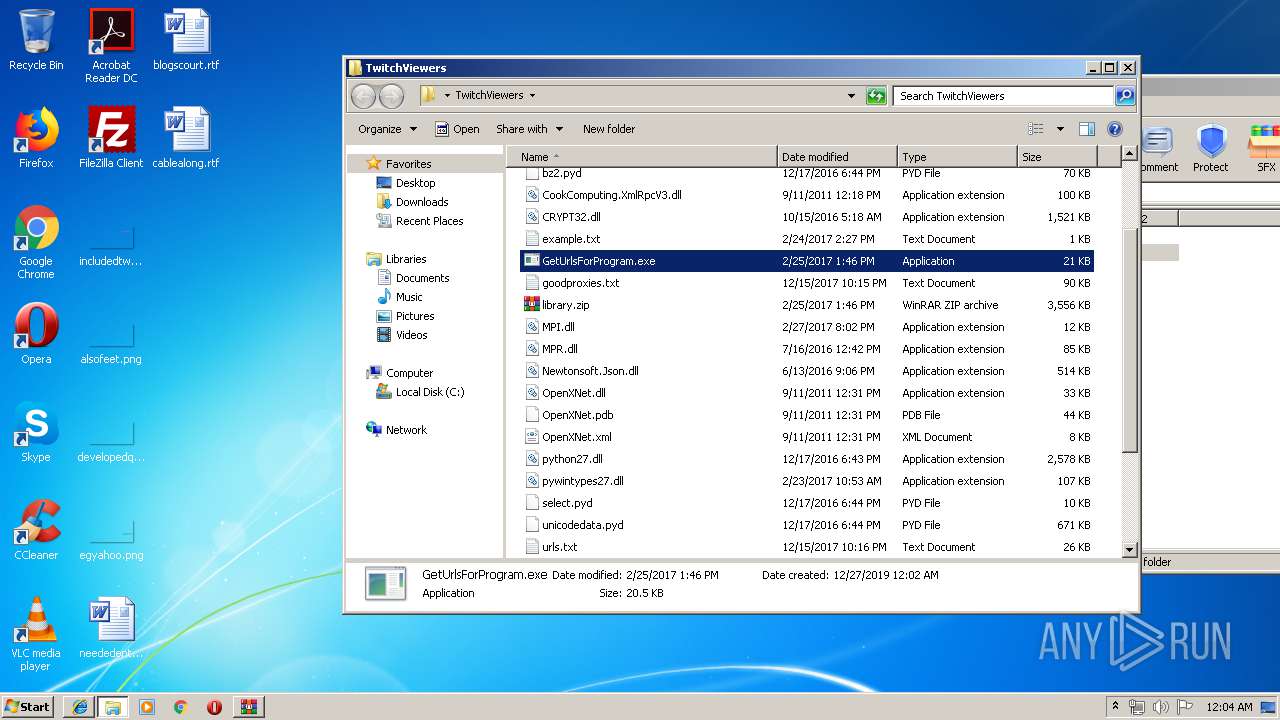
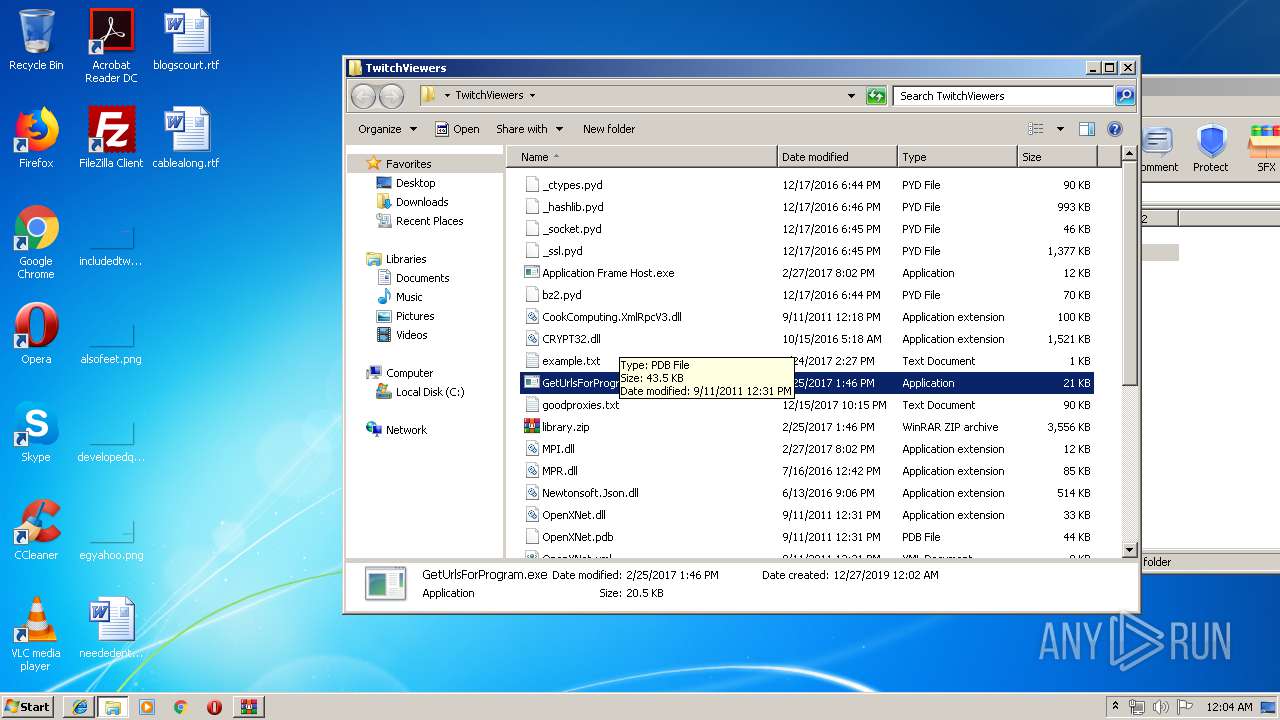
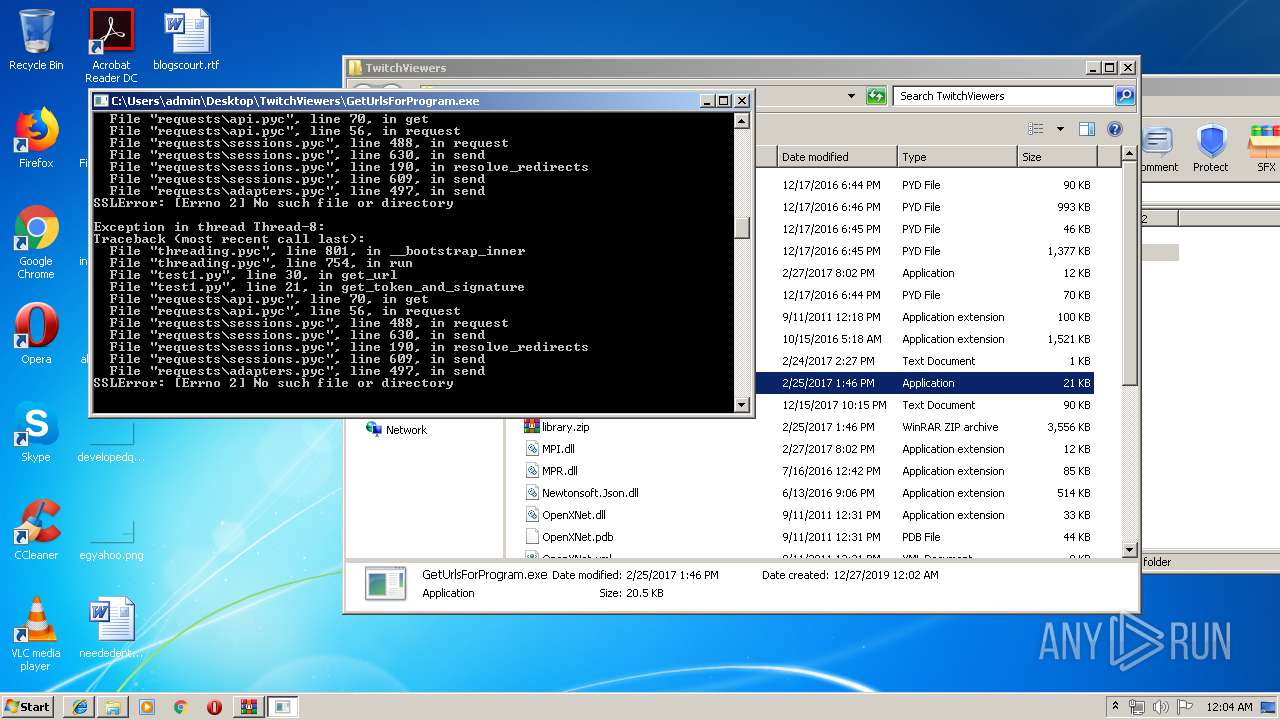
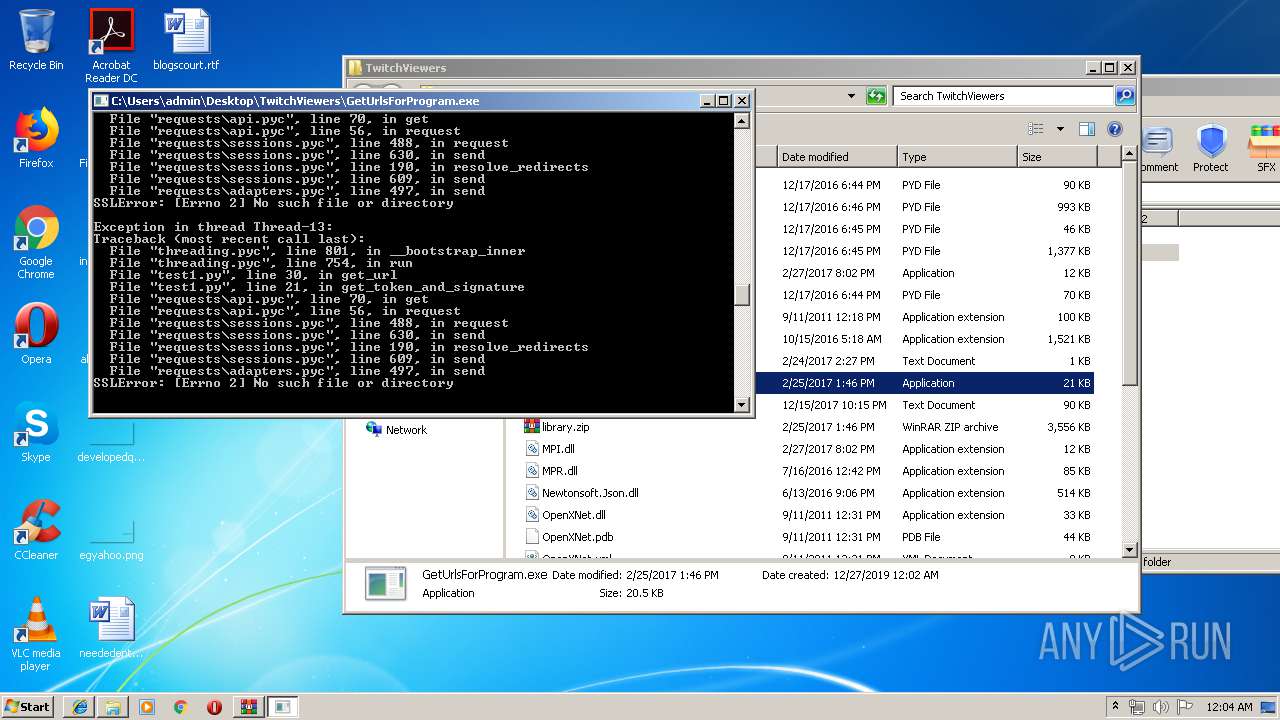
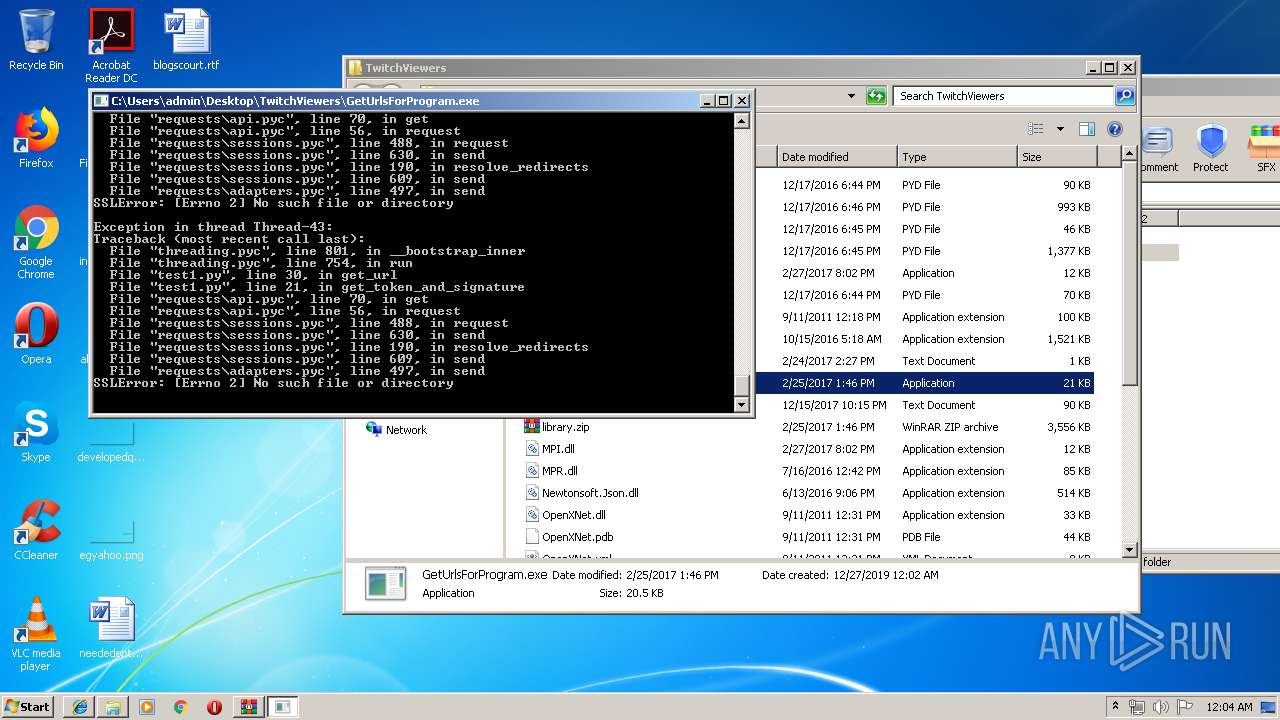
| 1936 | "C:\Users\admin\Desktop\TwitchViewers\GetUrlsForProgram.exe" | C:\Users\admin\Desktop\TwitchViewers\GetUrlsForProgram.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225786 Modules
| |||||||||||||||
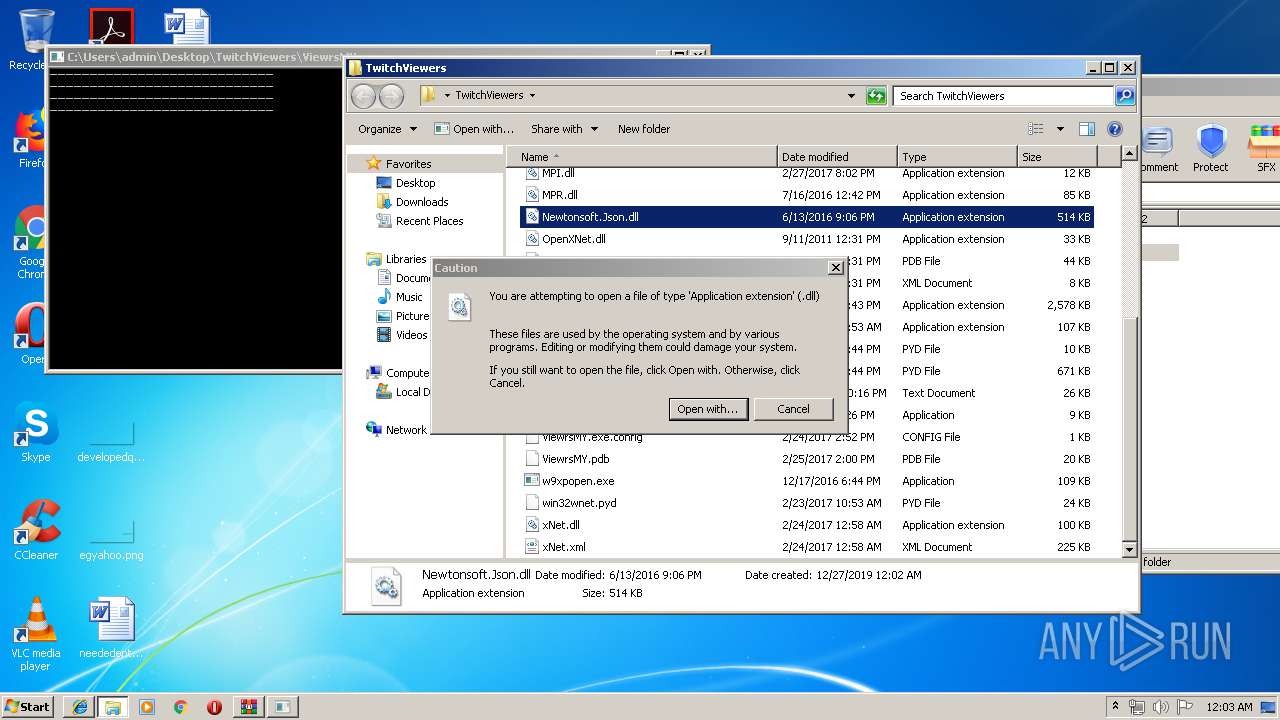
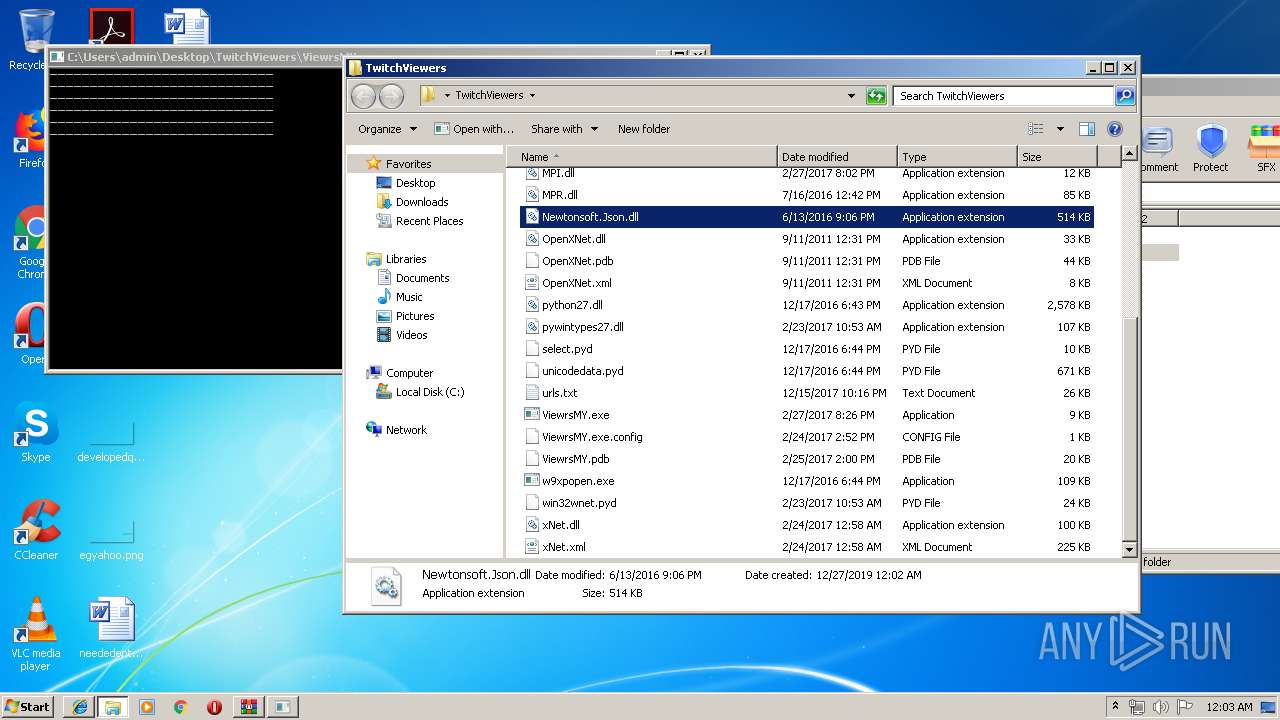
| 1992 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\TwitchViewers\Newtonsoft.Json.dll | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1912 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2344 | "C:\Users\admin\Desktop\TwitchViewers\GetUrlsForProgram.exe" | C:\Users\admin\Desktop\TwitchViewers\GetUrlsForProgram.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
3 887
Read events
3 595
Write events
290
Delete events
2
Modification events
| (PID) Process: | (1912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (1912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {12D90909-283C-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (1912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (1912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (1912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070C0005001B000000010030004600 | |||
Executable files
28
Suspicious files
1
Text files
38
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1912 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1912 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\O8DFT9QZ\TwitchViewers.rar[1].html | html | |
MD5:— | SHA256:— | |||
| 2152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\O8DFT9QZ\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 2152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\O41FY35B\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 2152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\IW8U2JQR\css[1].txt | text | |
MD5:— | SHA256:— | |||
| 2152 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@dosya[1].txt | — | |
MD5:— | SHA256:— | |||
| 2152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\IW8U2JQR\sdk[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
138
TCP/UDP connections
253
DNS requests
18
Threats
184
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1936 | GetUrlsForProgram.exe | GET | 301 | 151.101.114.214:80 | http://api.twitch.tv/api/channels/rhemecoh/access_token?client_id=vs6wipliuaoscybfkrst97x14xa7i8 | US | — | — | whitelisted |
1936 | GetUrlsForProgram.exe | GET | 301 | 151.101.114.214:80 | http://api.twitch.tv/api/channels/rhemecoh/access_token?client_id=vs6wipliuaoscybfkrst97x14xa7i8 | US | — | — | whitelisted |
1936 | GetUrlsForProgram.exe | GET | 301 | 151.101.114.214:80 | http://api.twitch.tv/api/channels/rhemecoh/access_token?client_id=vs6wipliuaoscybfkrst97x14xa7i8 | US | — | — | whitelisted |
1936 | GetUrlsForProgram.exe | GET | 301 | 151.101.114.214:80 | http://api.twitch.tv/api/channels/rhemecoh/access_token?client_id=vs6wipliuaoscybfkrst97x14xa7i8 | US | — | — | whitelisted |
2152 | iexplore.exe | GET | 200 | 195.201.111.49:80 | http://dosya.co/igig97j9t6wr/TwitchViewers.rar.html | RU | html | 4.04 Kb | whitelisted |
2152 | iexplore.exe | GET | 200 | 31.13.92.14:80 | http://connect.facebook.net/tr_TR/sdk.js | IE | text | 1.74 Kb | whitelisted |
2152 | iexplore.exe | GET | 200 | 209.197.3.15:80 | http://maxcdn.bootstrapcdn.com/font-awesome/4.3.0/css/font-awesome.min.css | US | text | 5.31 Kb | whitelisted |
2152 | iexplore.exe | GET | 200 | 195.201.111.49:80 | http://dosya.co/tablo.css | RU | text | 5.33 Kb | whitelisted |
2152 | iexplore.exe | GET | 200 | 195.201.111.49:80 | http://dosya.co/xupload.js? | RU | text | 4.36 Kb | whitelisted |
2152 | iexplore.exe | GET | 200 | 195.201.111.49:80 | http://dosya.co/main.css | RU | text | 7.30 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2152 | iexplore.exe | 195.201.111.49:80 | dosya.co | Awanti Ltd. | RU | suspicious |
2152 | iexplore.exe | 172.217.16.206:443 | apis.google.com | Google Inc. | US | whitelisted |
2152 | iexplore.exe | 172.217.21.194:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2152 | iexplore.exe | 172.217.22.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1912 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2152 | iexplore.exe | 172.217.16.174:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2152 | iexplore.exe | 31.13.92.14:80 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
2152 | iexplore.exe | 31.13.92.14:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
2152 | iexplore.exe | 172.217.16.196:443 | www.google.com | Google Inc. | US | whitelisted |
1912 | iexplore.exe | 195.201.111.49:80 | dosya.co | Awanti Ltd. | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dosya.co |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
apis.google.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1936 | GetUrlsForProgram.exe | Misc activity | SUSPICIOUS [PTsecurity] Python Request HTTP Header |
1936 | GetUrlsForProgram.exe | Misc activity | SUSPICIOUS [PTsecurity] Python Request HTTP Header |
1936 | GetUrlsForProgram.exe | Misc activity | SUSPICIOUS [PTsecurity] Python Request HTTP Header |
1936 | GetUrlsForProgram.exe | Misc activity | SUSPICIOUS [PTsecurity] Python Request HTTP Header |
1936 | GetUrlsForProgram.exe | Misc activity | SUSPICIOUS [PTsecurity] Python Request HTTP Header |
1936 | GetUrlsForProgram.exe | Misc activity | SUSPICIOUS [PTsecurity] Python Request HTTP Header |
1936 | GetUrlsForProgram.exe | Misc activity | SUSPICIOUS [PTsecurity] Python Request HTTP Header |
1936 | GetUrlsForProgram.exe | Misc activity | SUSPICIOUS [PTsecurity] Python Request HTTP Header |
1936 | GetUrlsForProgram.exe | Misc activity | SUSPICIOUS [PTsecurity] Python Request HTTP Header |
1936 | GetUrlsForProgram.exe | Misc activity | SUSPICIOUS [PTsecurity] Python Request HTTP Header |
92 ETPRO signatures available at the full report