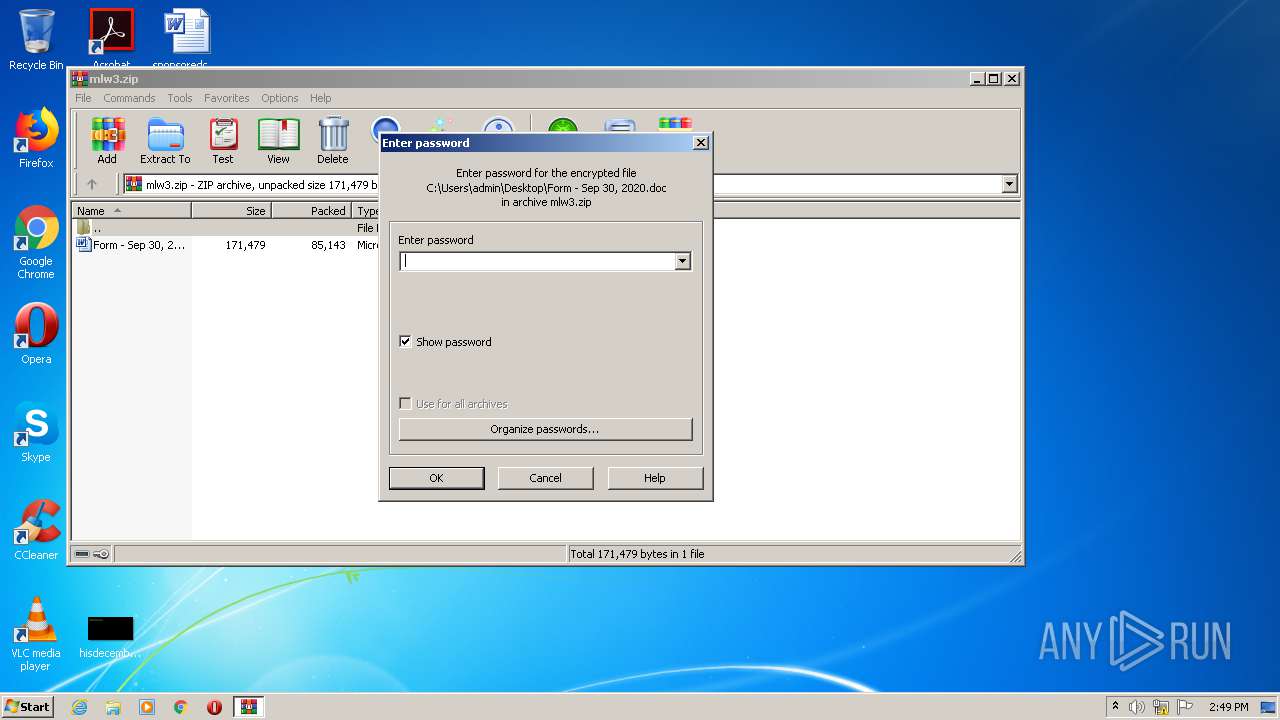
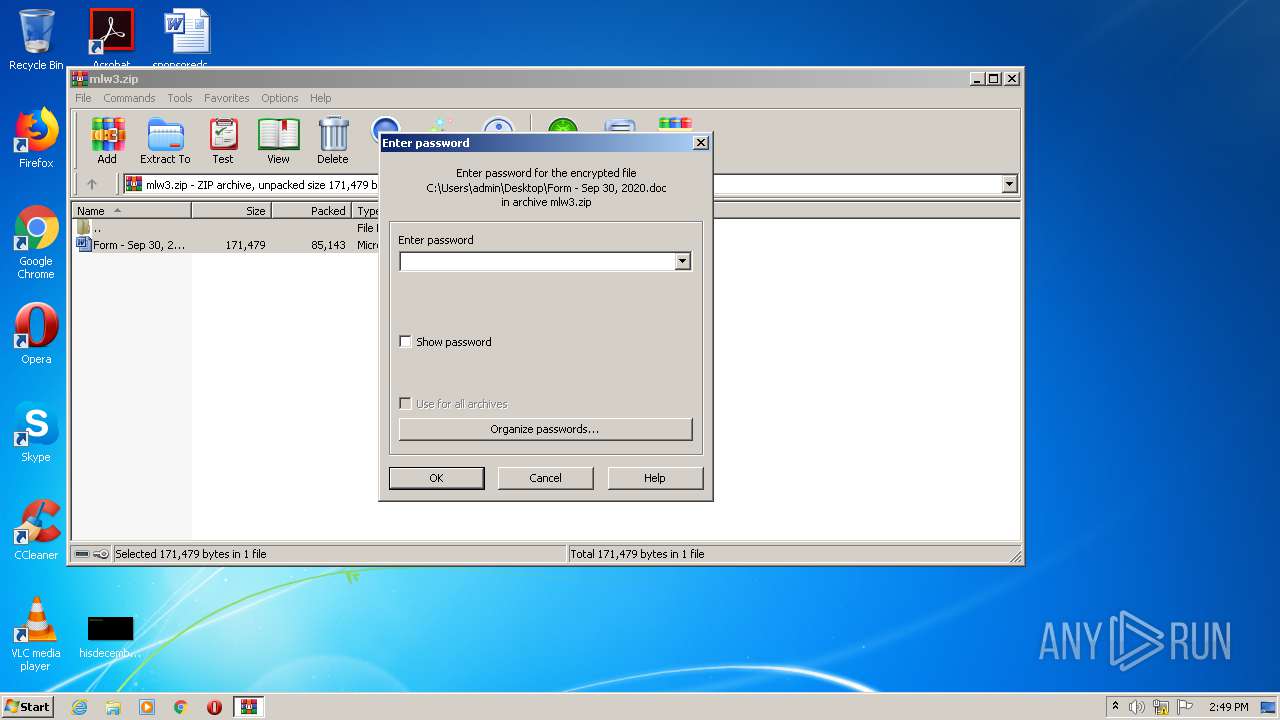
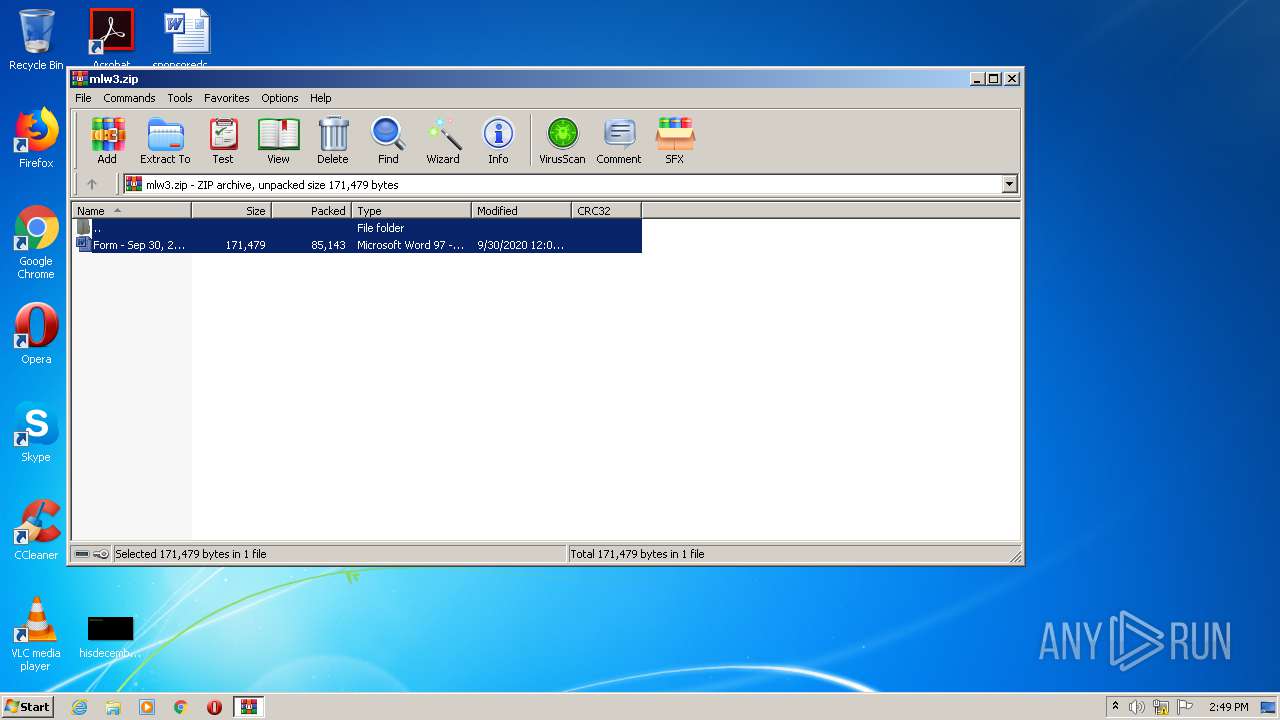
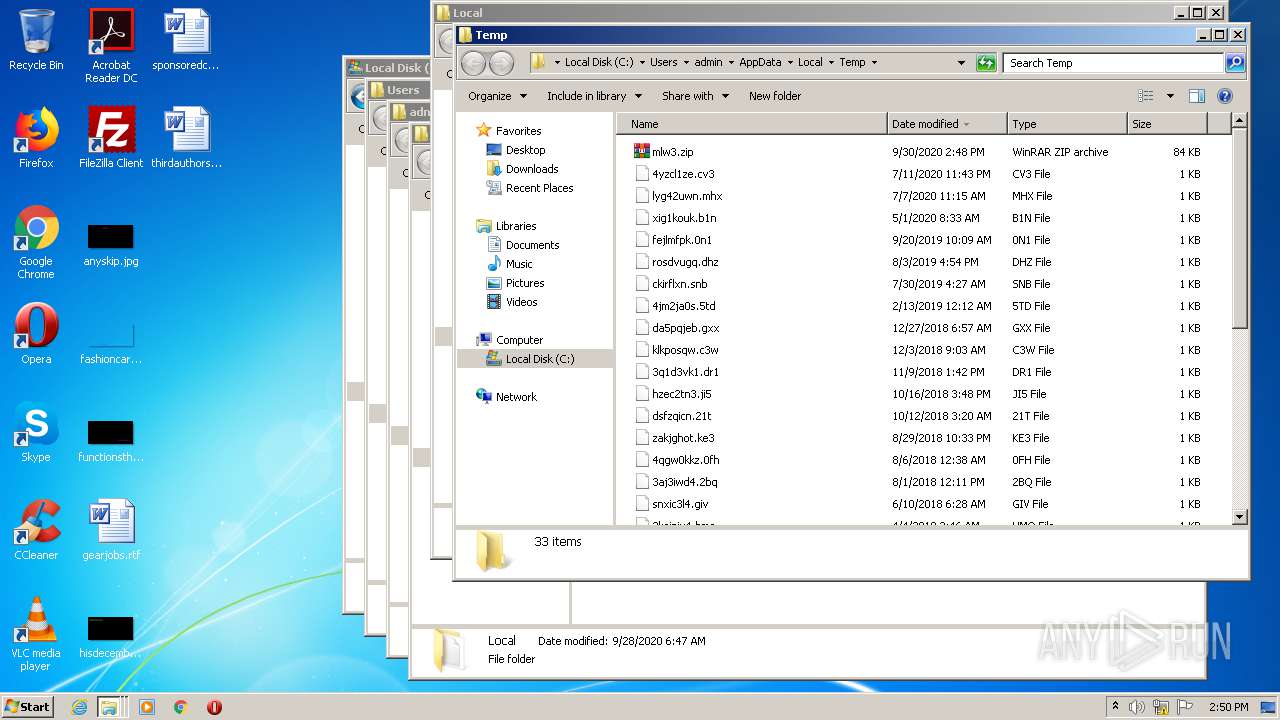
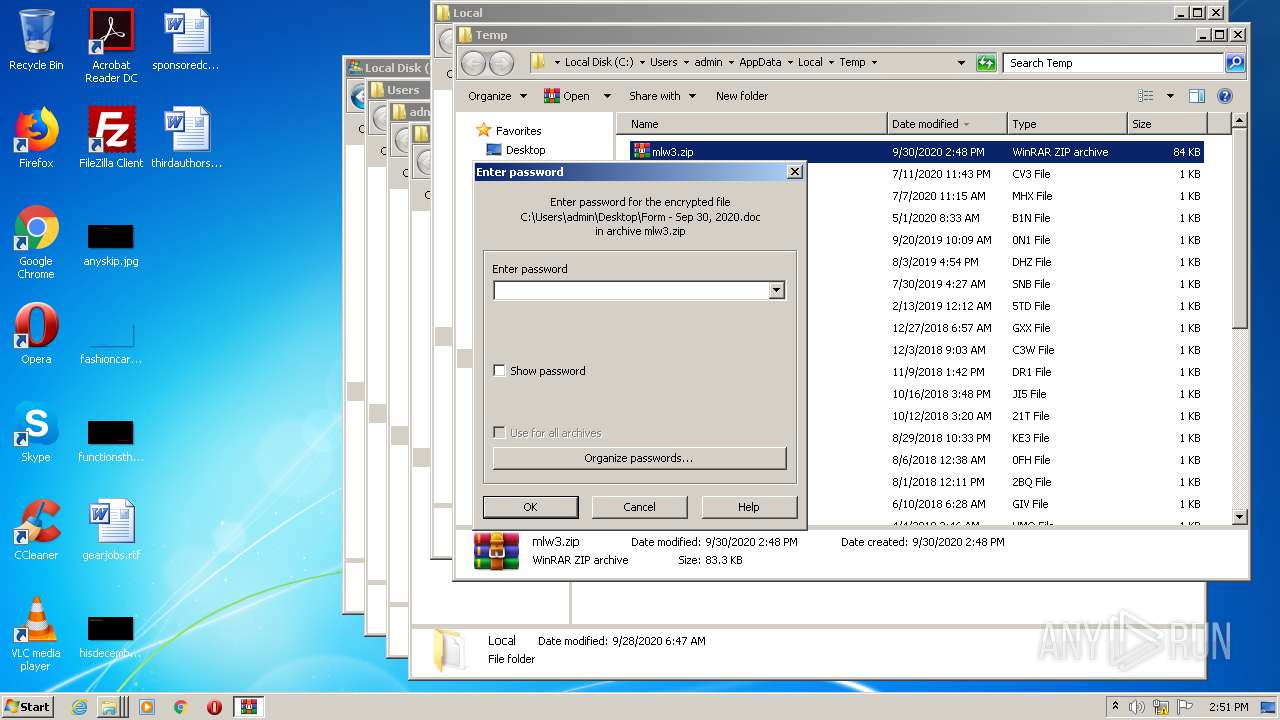
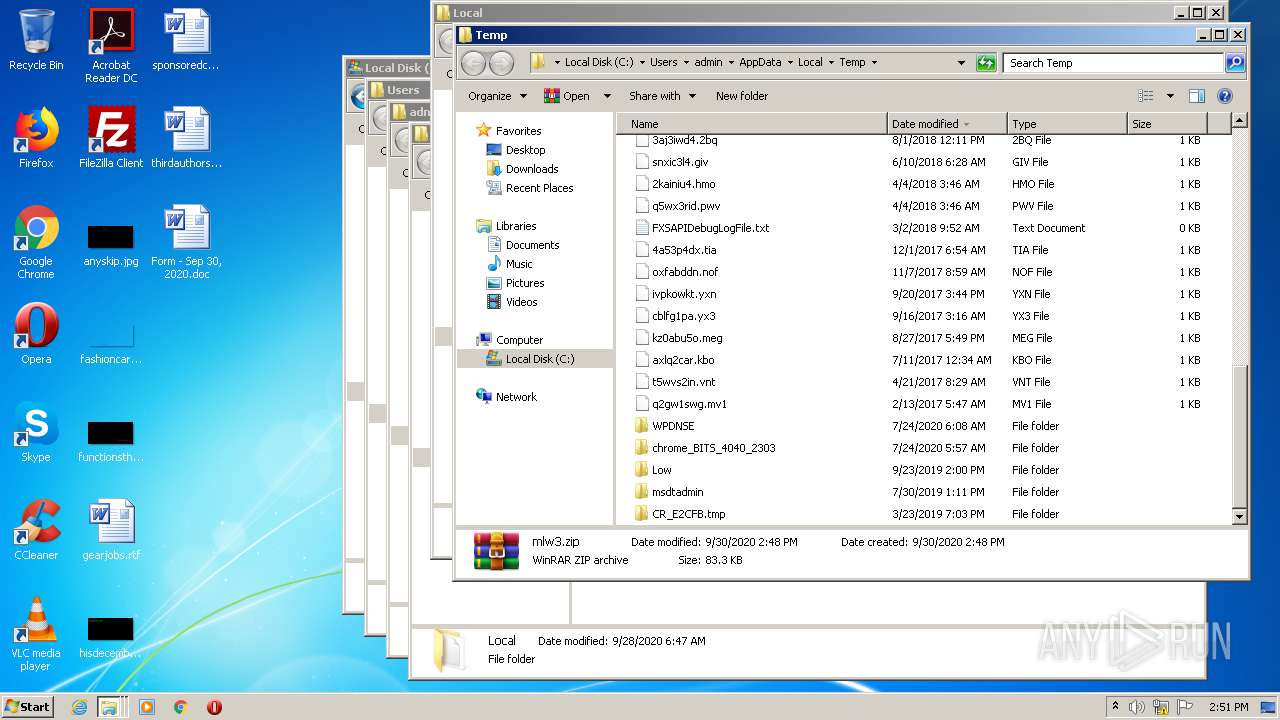
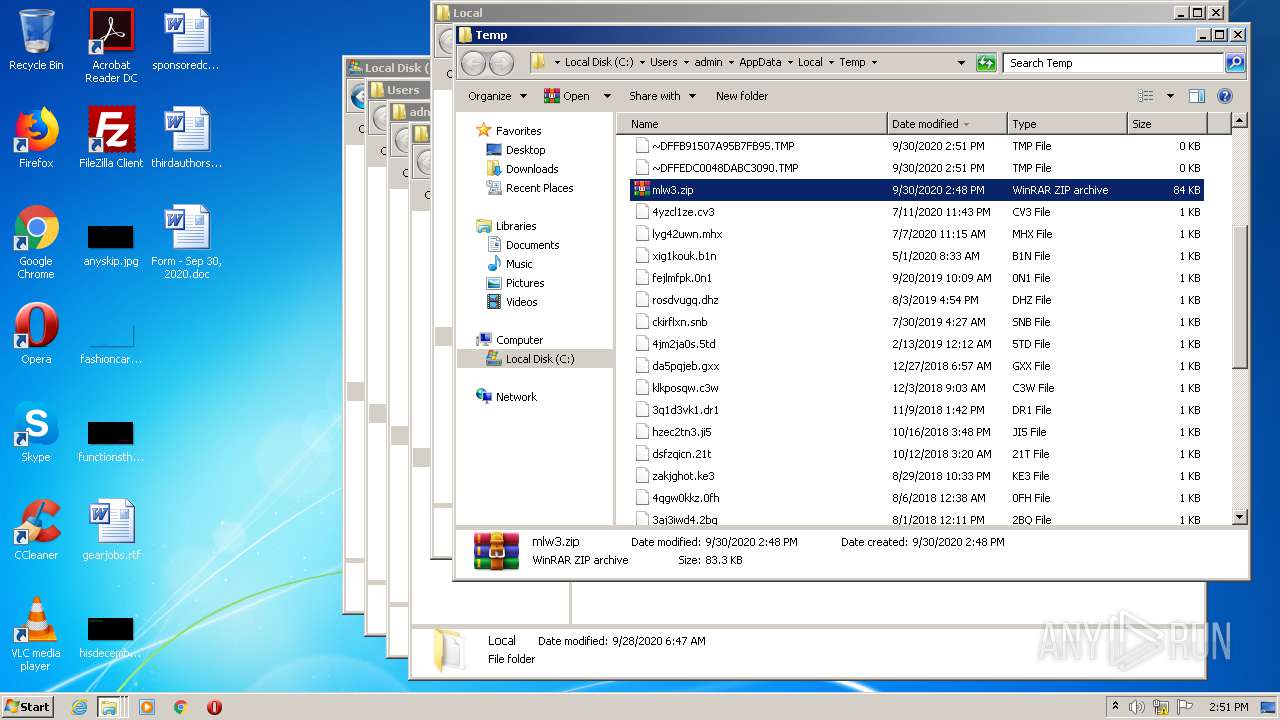
| File name: | mlw3.zip |
| Full analysis: | https://app.any.run/tasks/fd973108-d9fe-424f-8a5d-76d76d73aafa |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 13:47:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
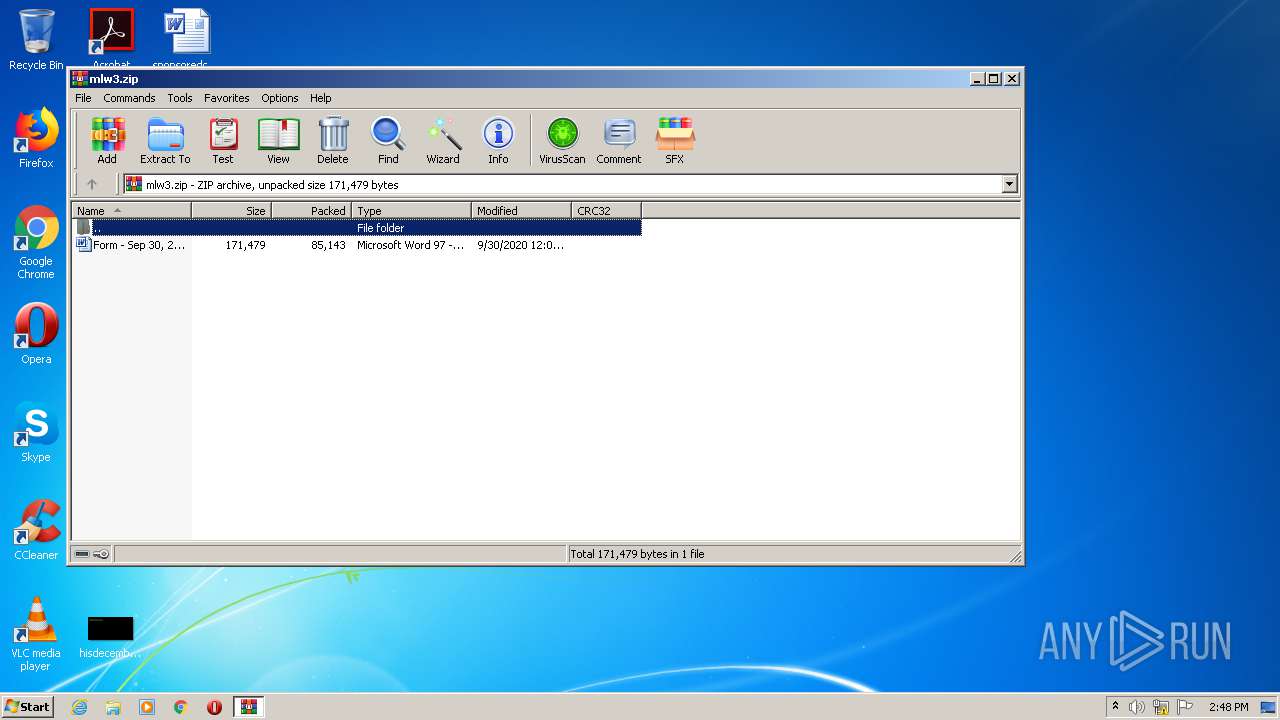
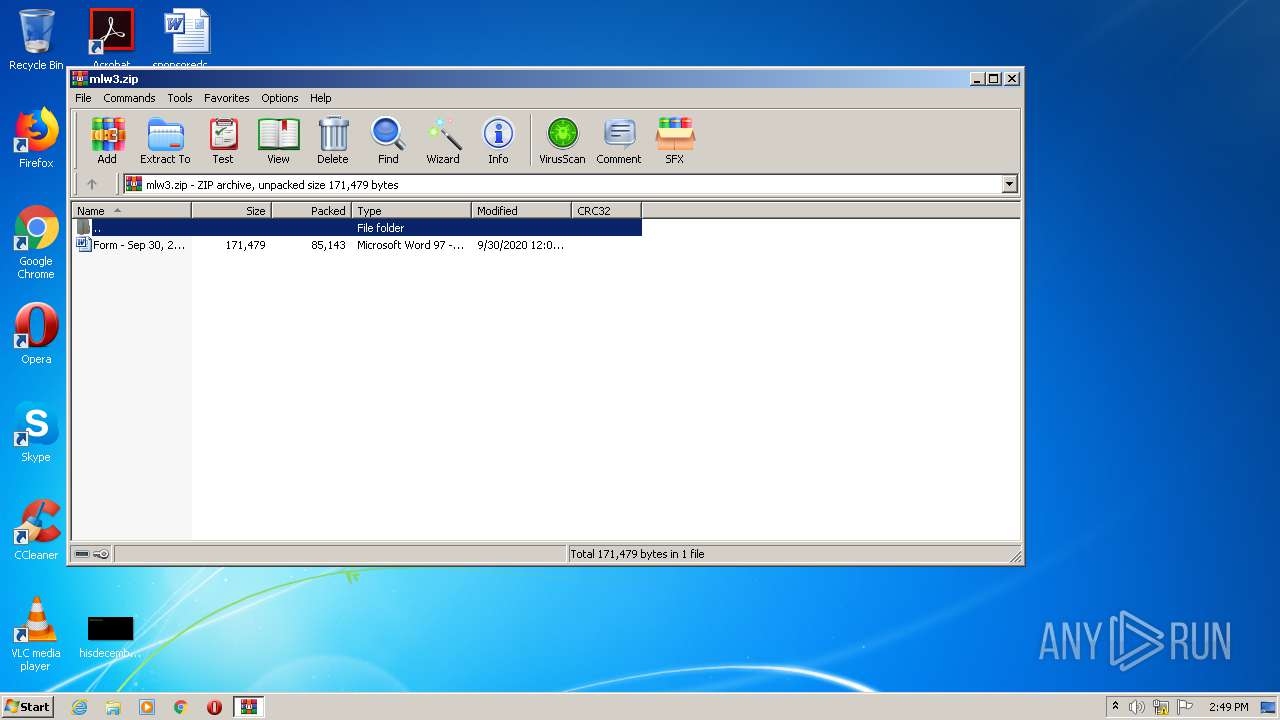
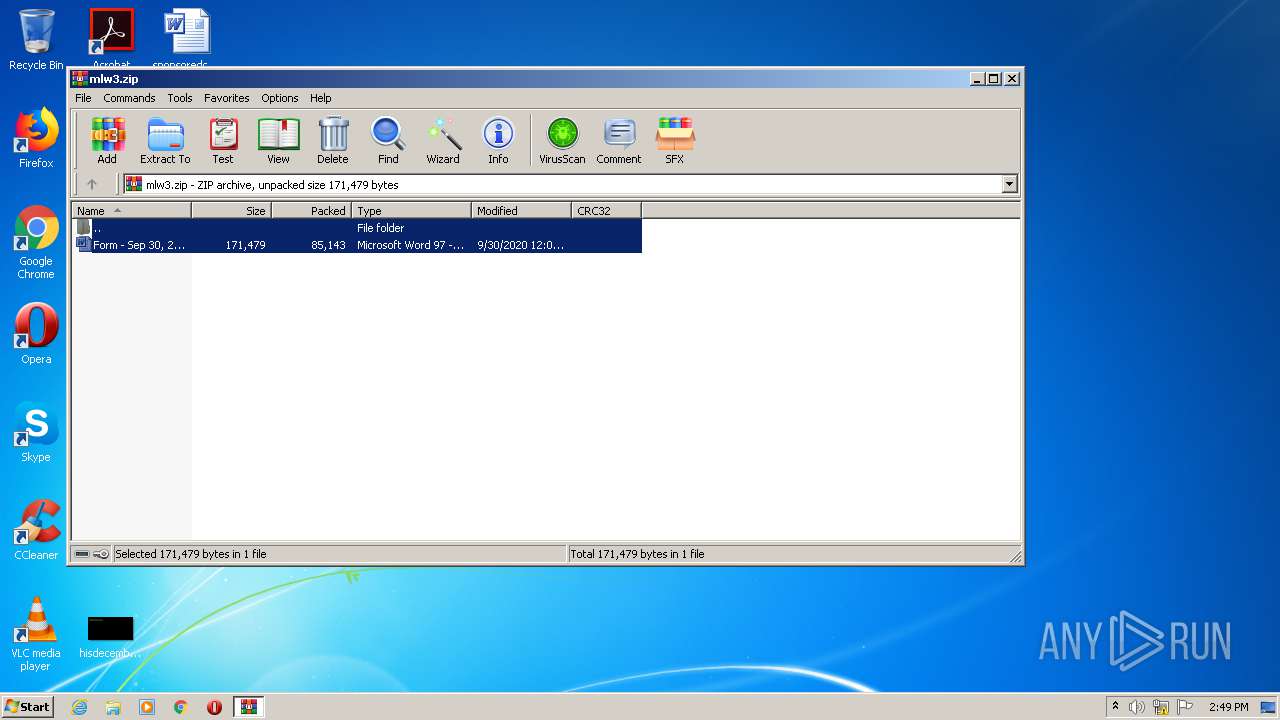
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | 7008175B14A1EA58D62852DE734F0659 |
| SHA1: | 717E83CA4638B6C1D19511A84324219A5B435774 |
| SHA256: | 3A04557270A65FD2AECD6BD7FC2460162ABEA50072CA82BD38E73297D60D5DB6 |
| SSDEEP: | 1536:rkeyJi/xz8vveKIuF9BxuLetfq37JUnKyUUJeRFU7TE8iWEPtsxnDur:rke8iJzRKpttfc7JSKfxFOviW9Dur |
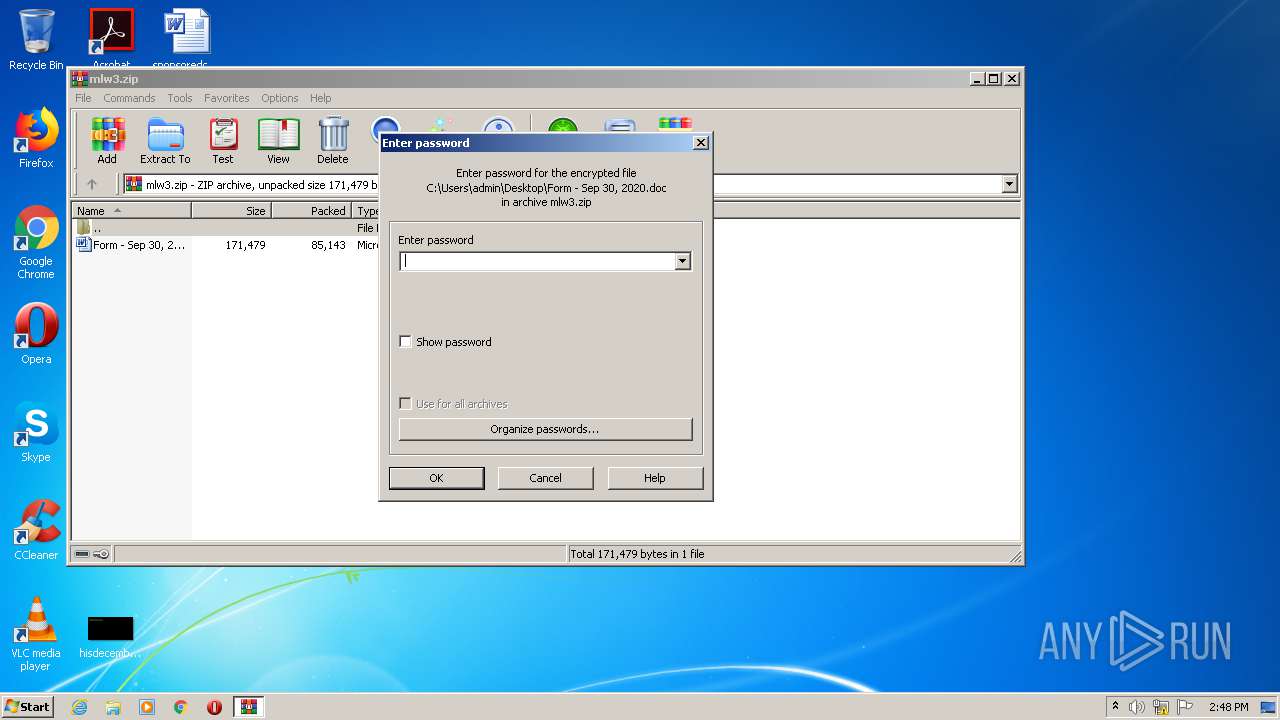
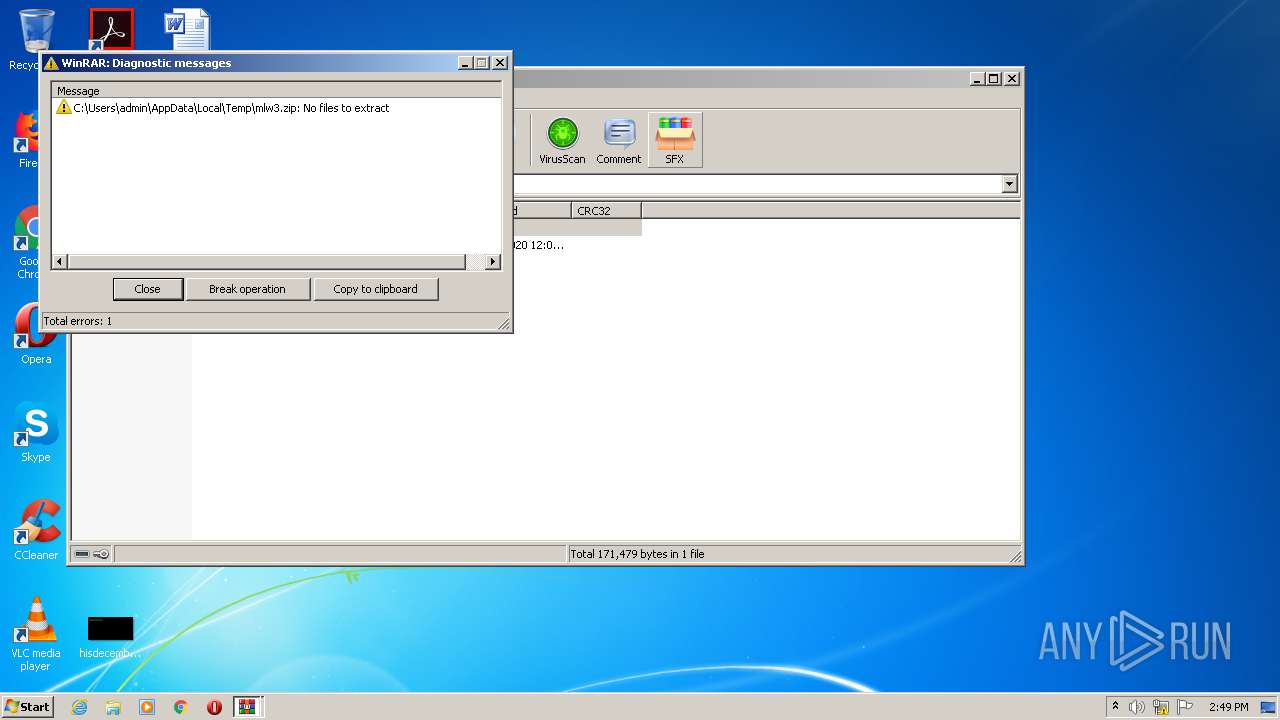
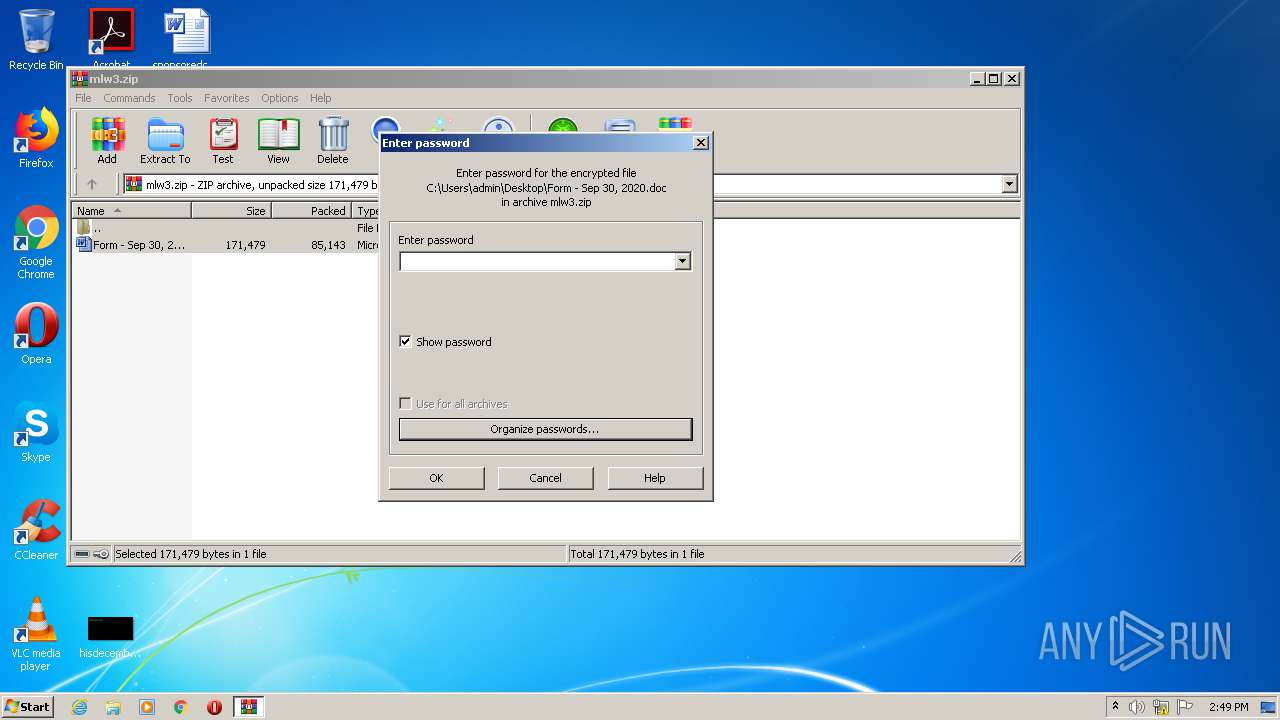
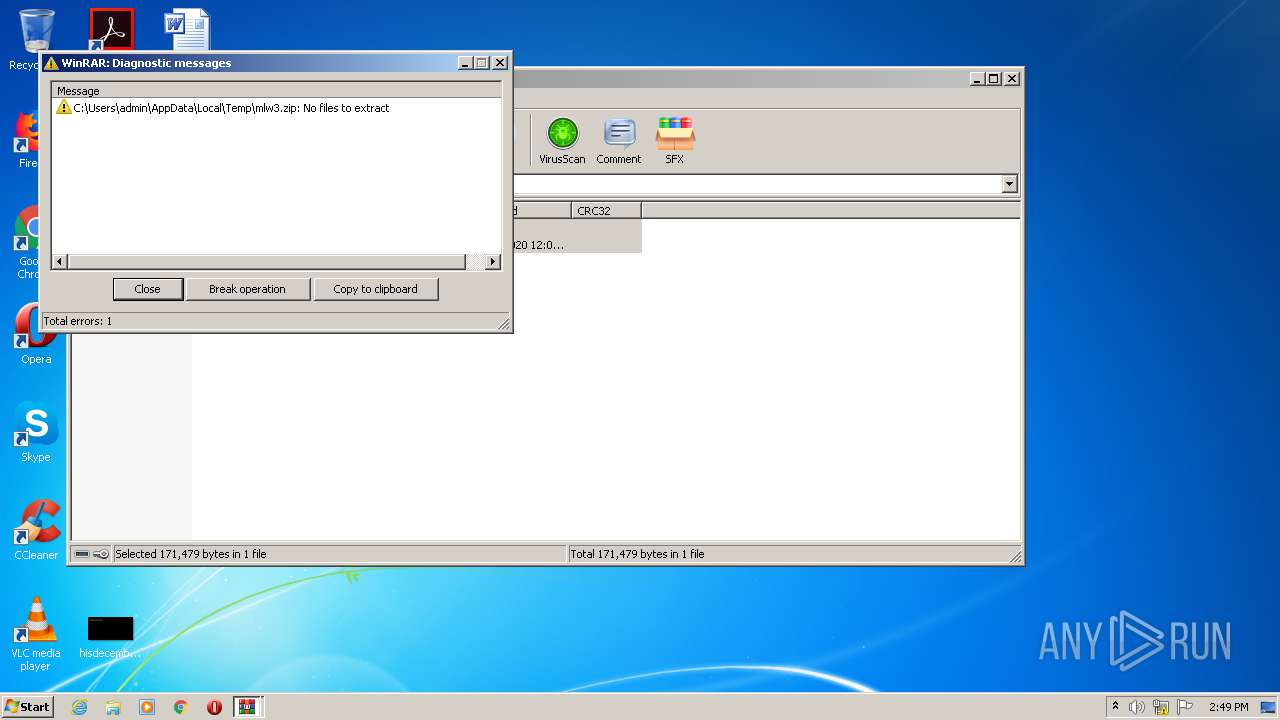
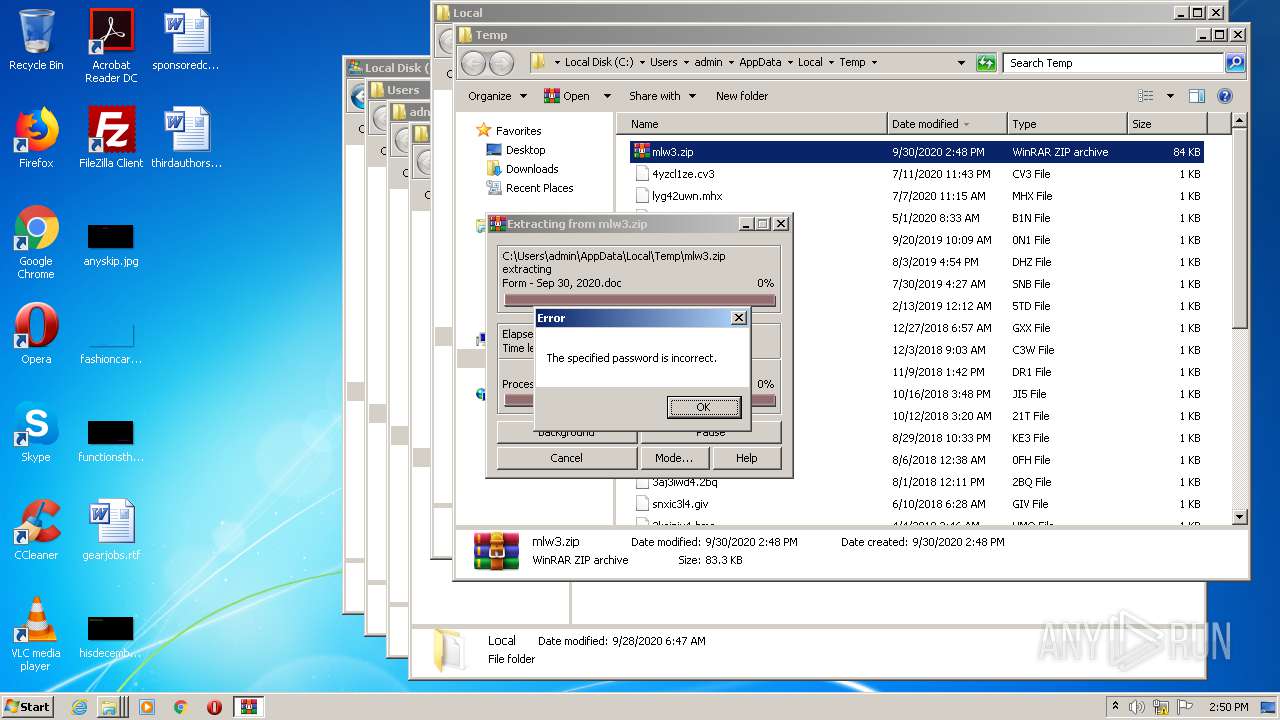
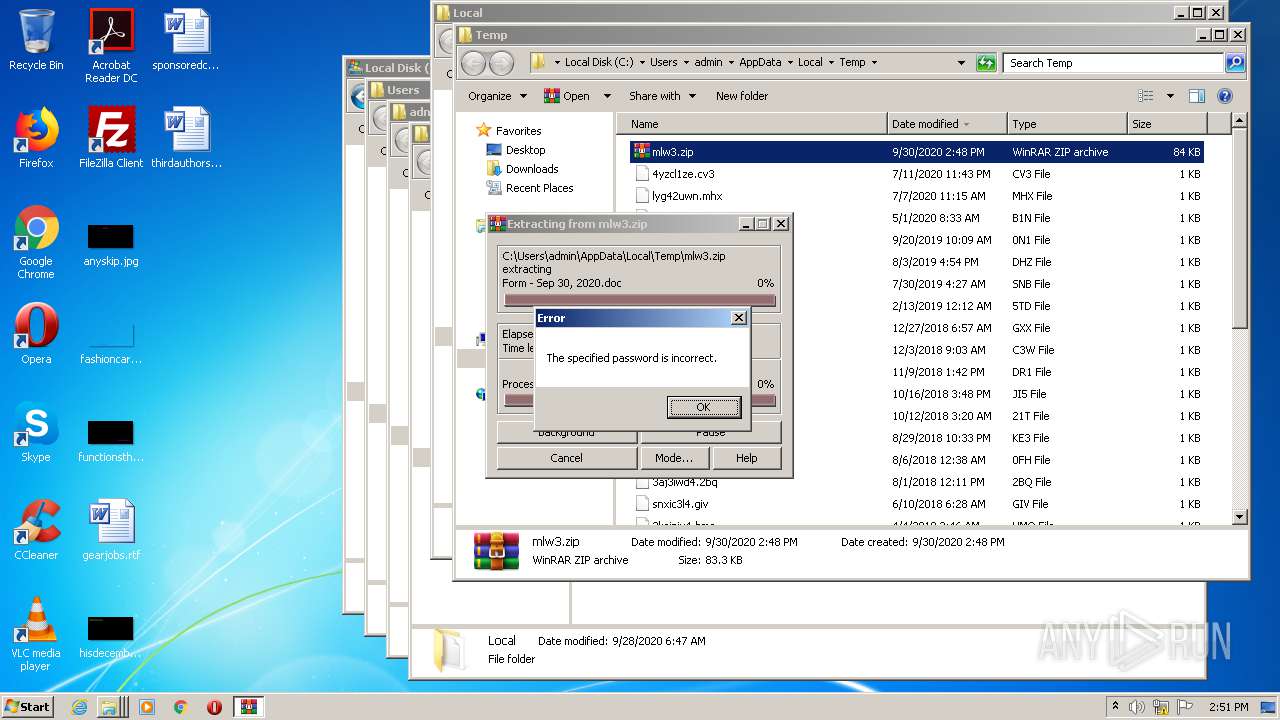
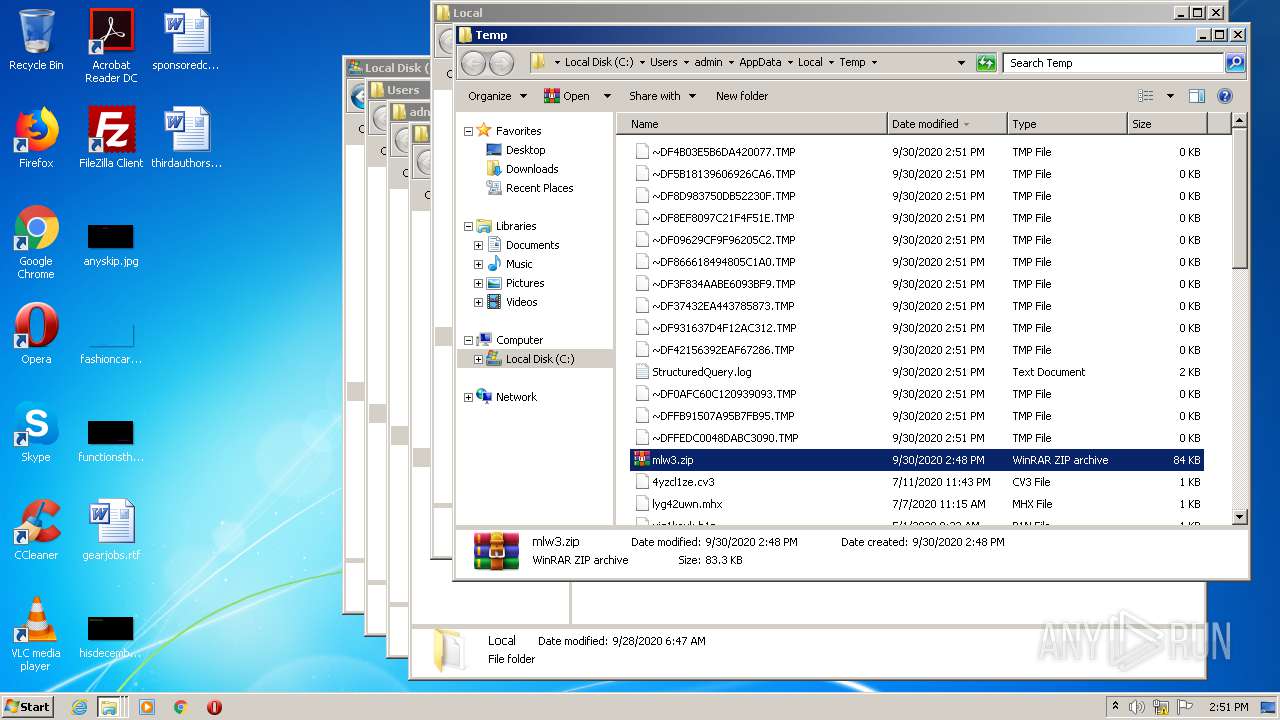
MALICIOUS
Drops known malicious document
- WinRAR.exe (PID: 2740)
SUSPICIOUS
No suspicious indicators.INFO
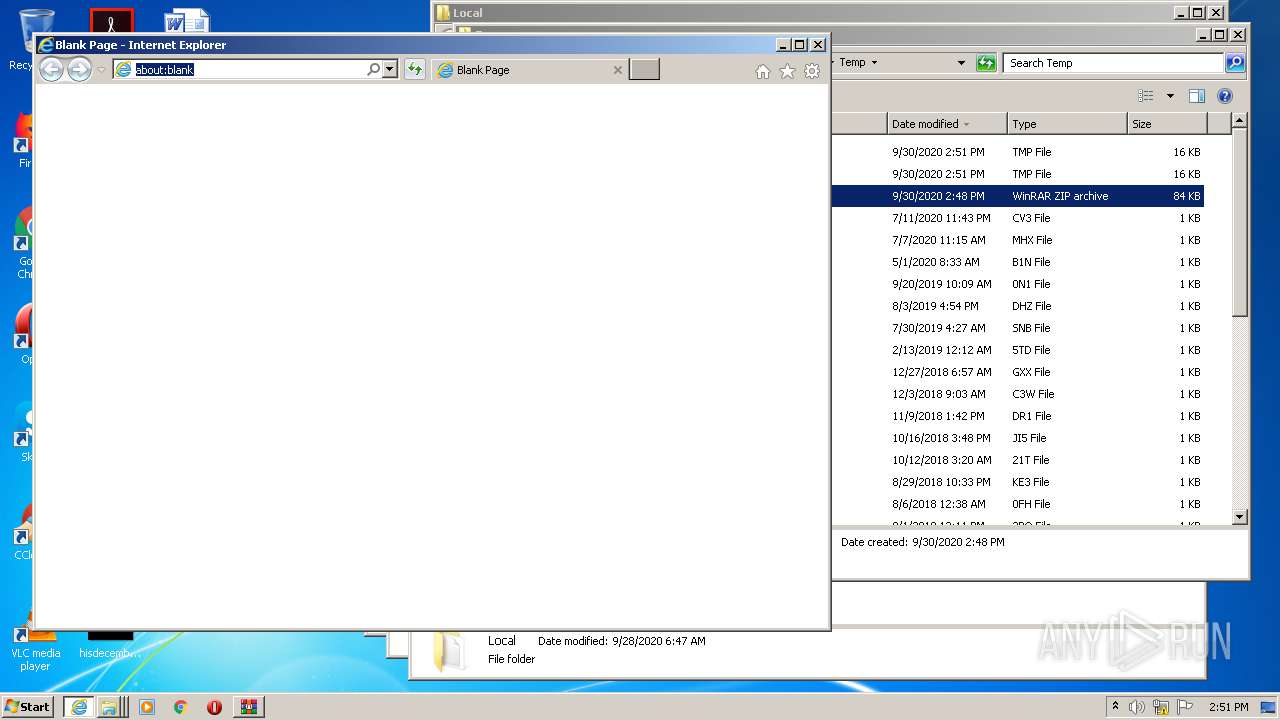
Reads Internet Cache Settings
- iexplore.exe (PID: 3440)
- iexplore.exe (PID: 2436)
- iexplore.exe (PID: 532)
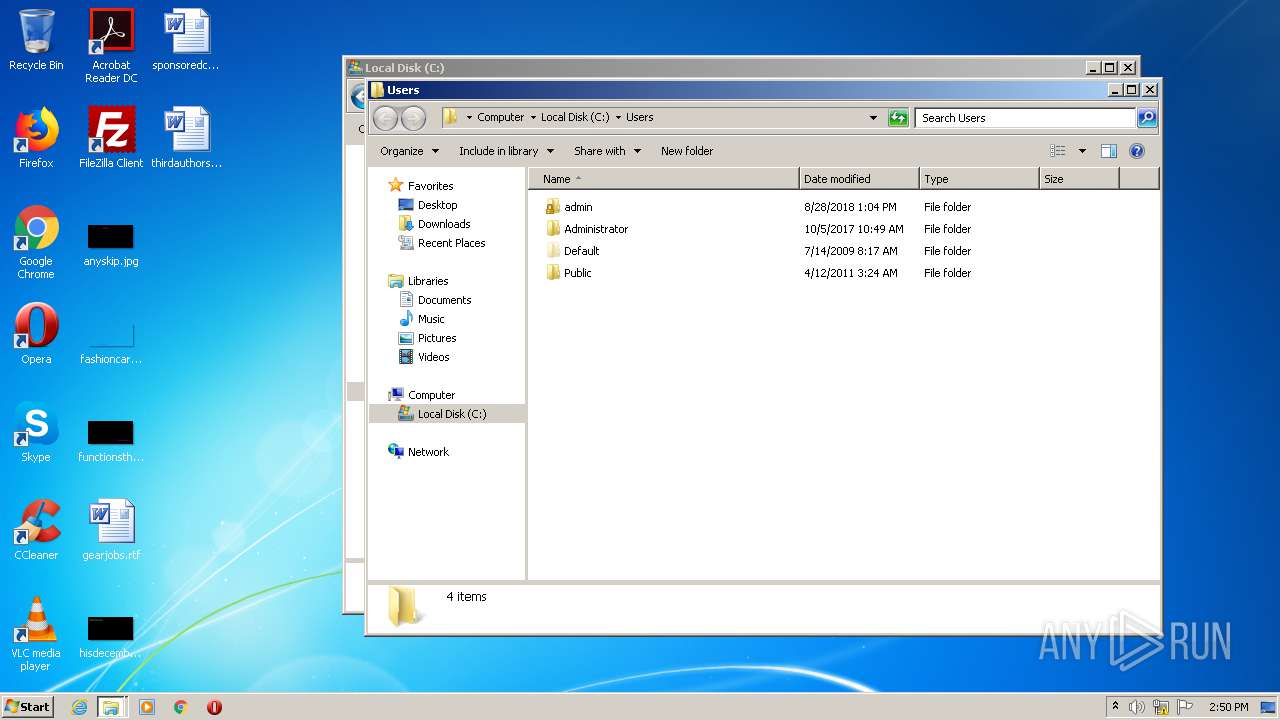
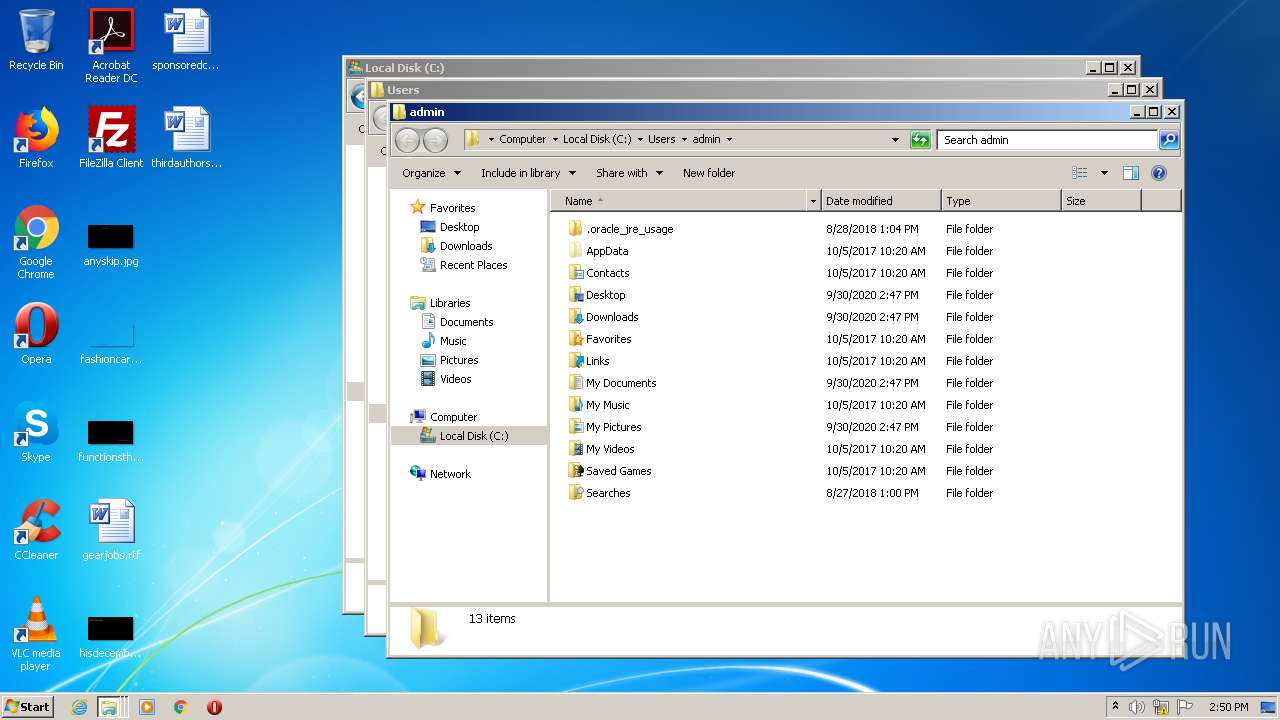
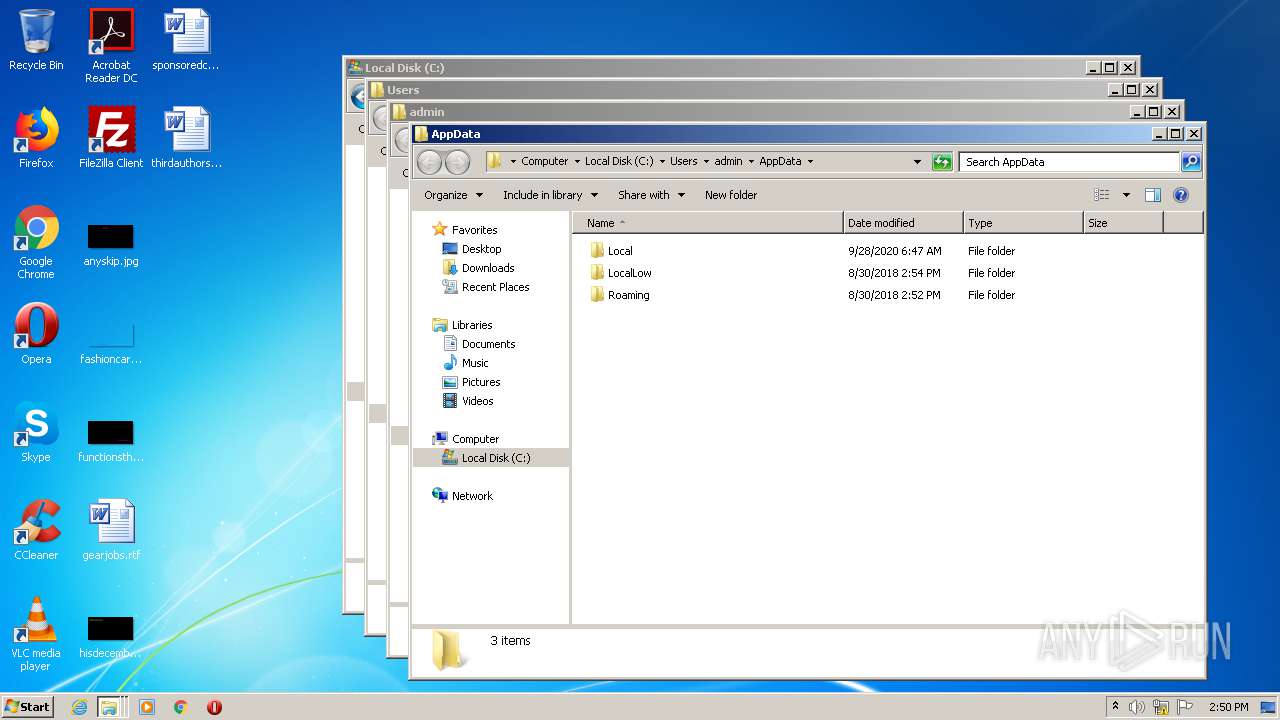
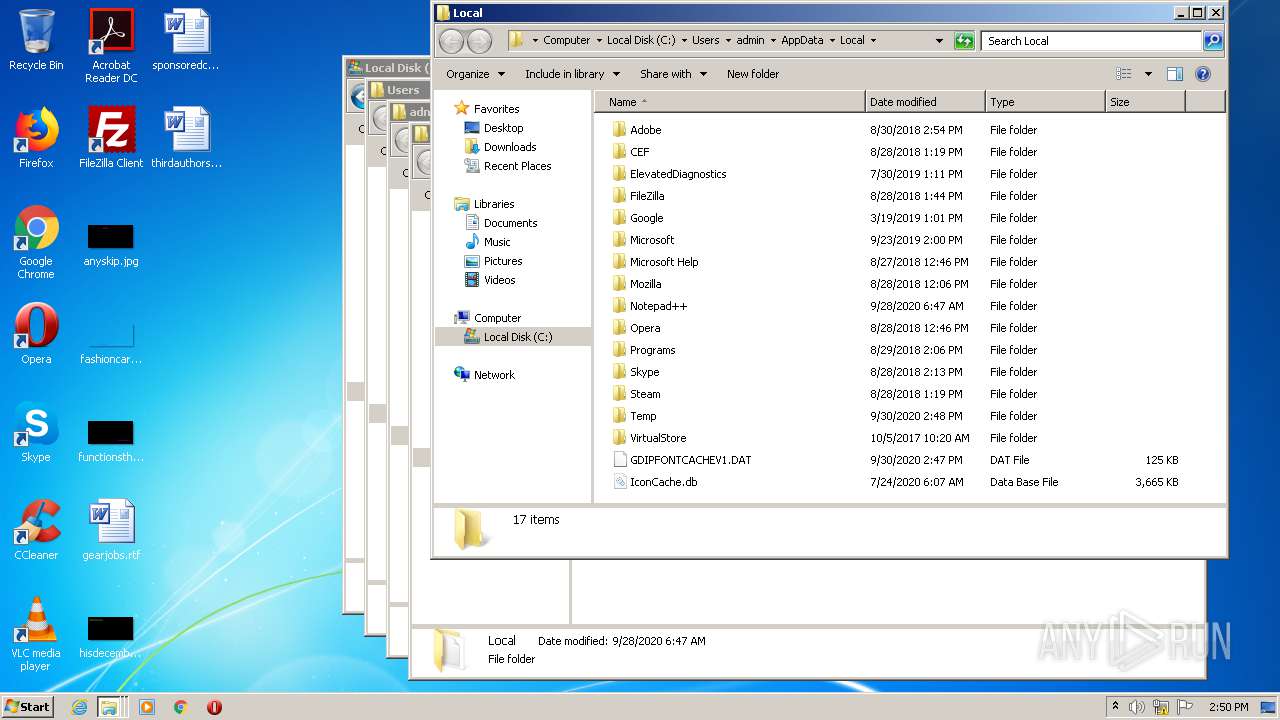
Creates files in the user directory
- iexplore.exe (PID: 3440)
- iexplore.exe (PID: 2436)
Reads internet explorer settings
- iexplore.exe (PID: 2436)
- iexplore.exe (PID: 532)
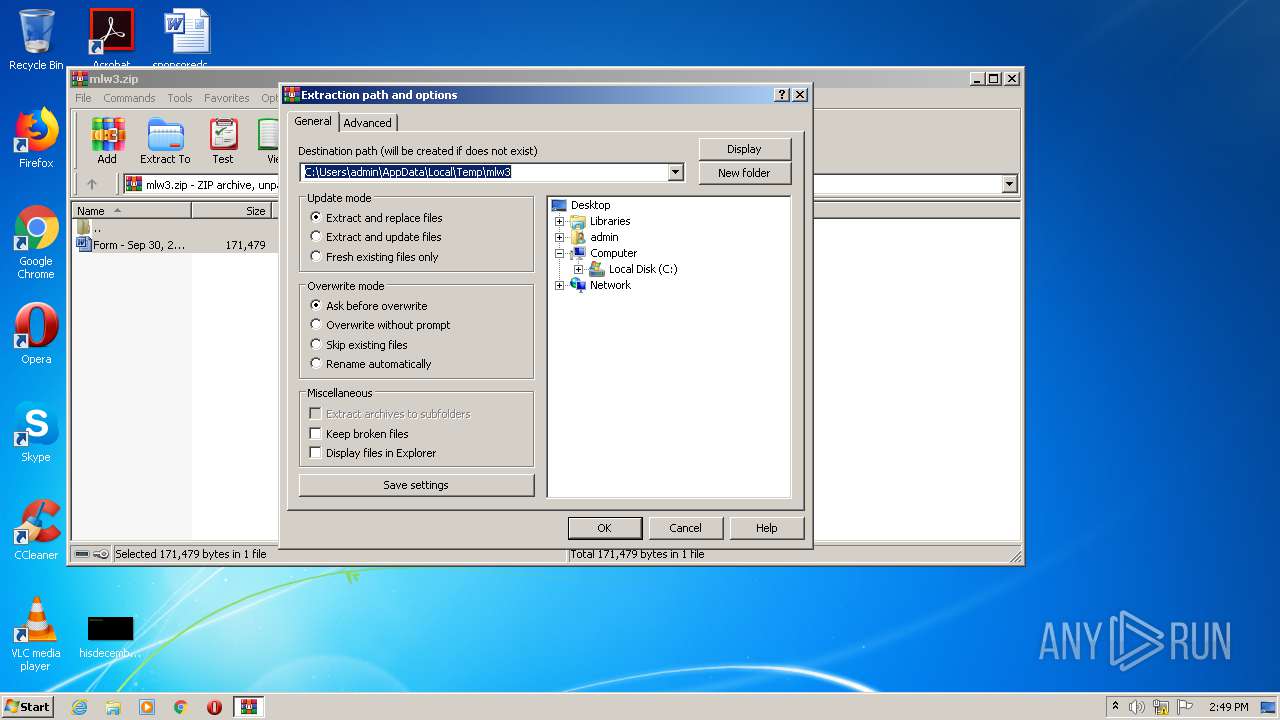
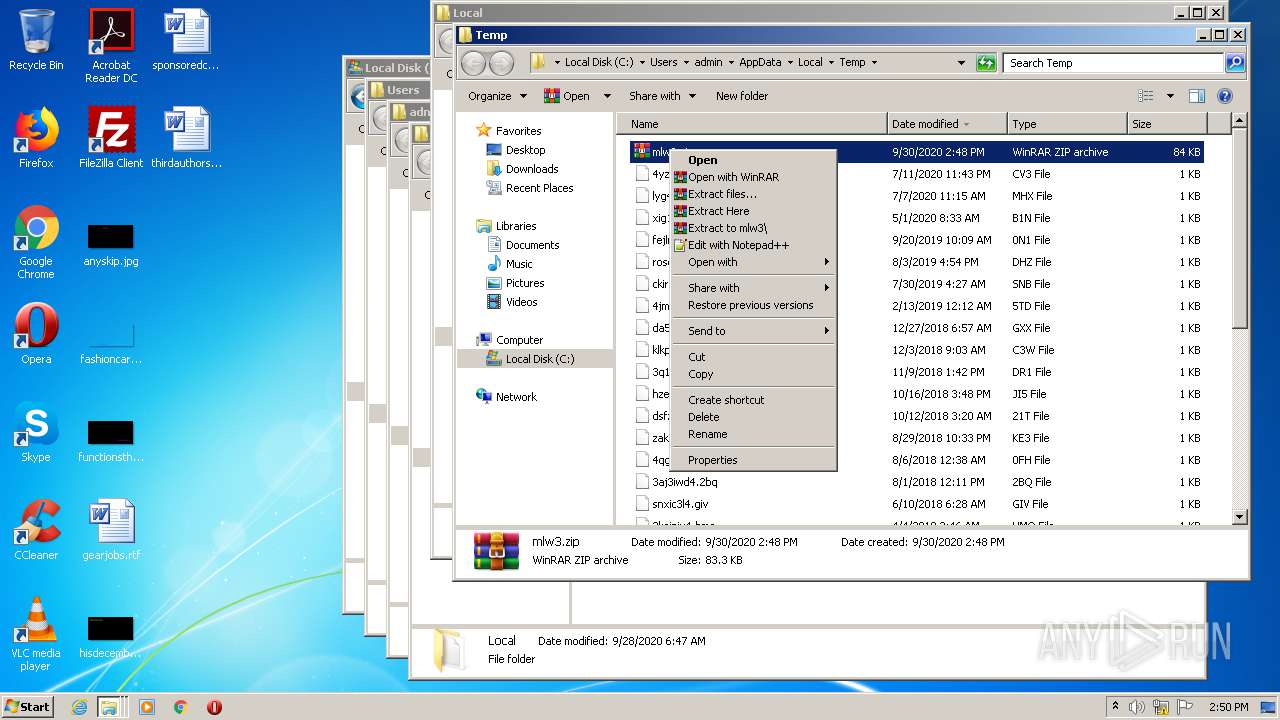
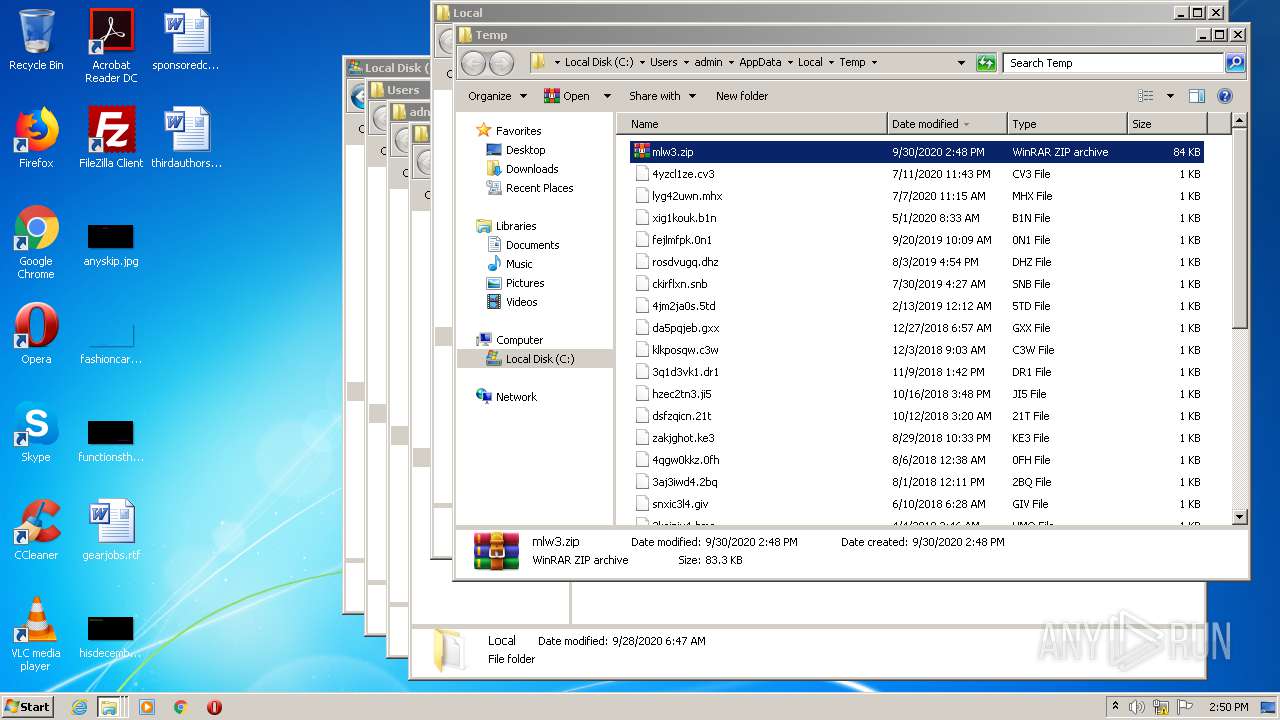
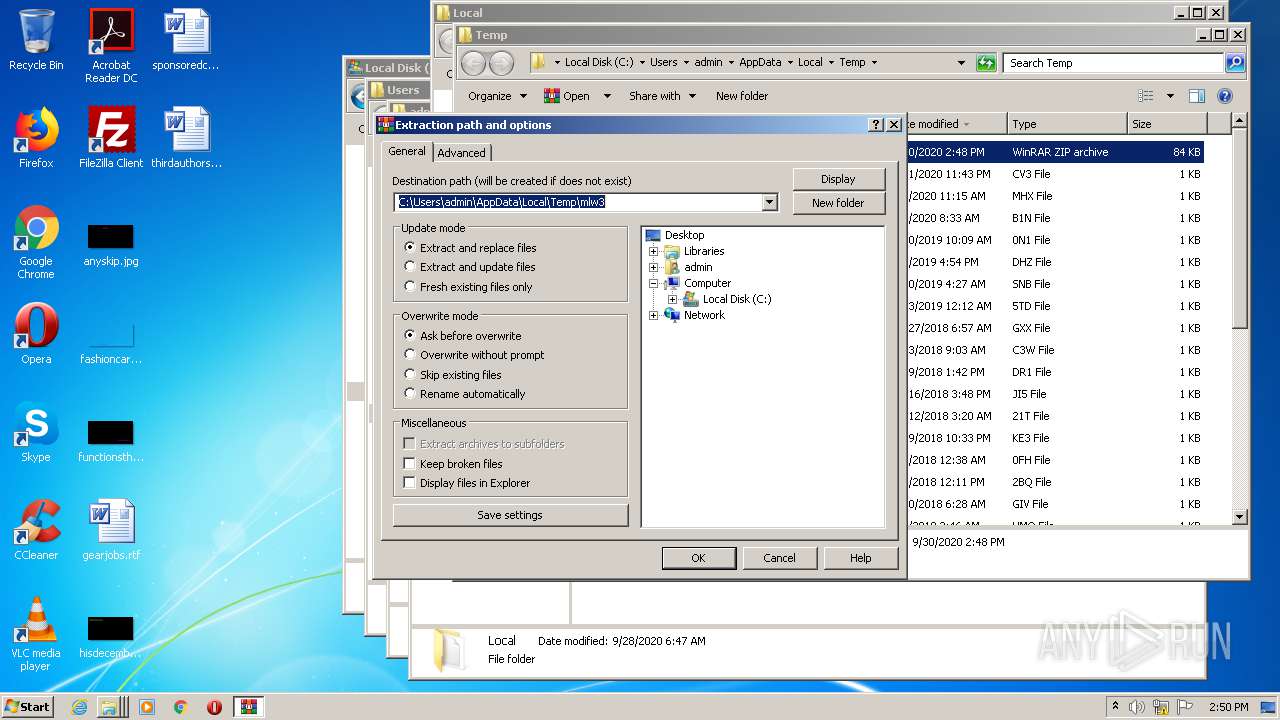
Manual execution by user
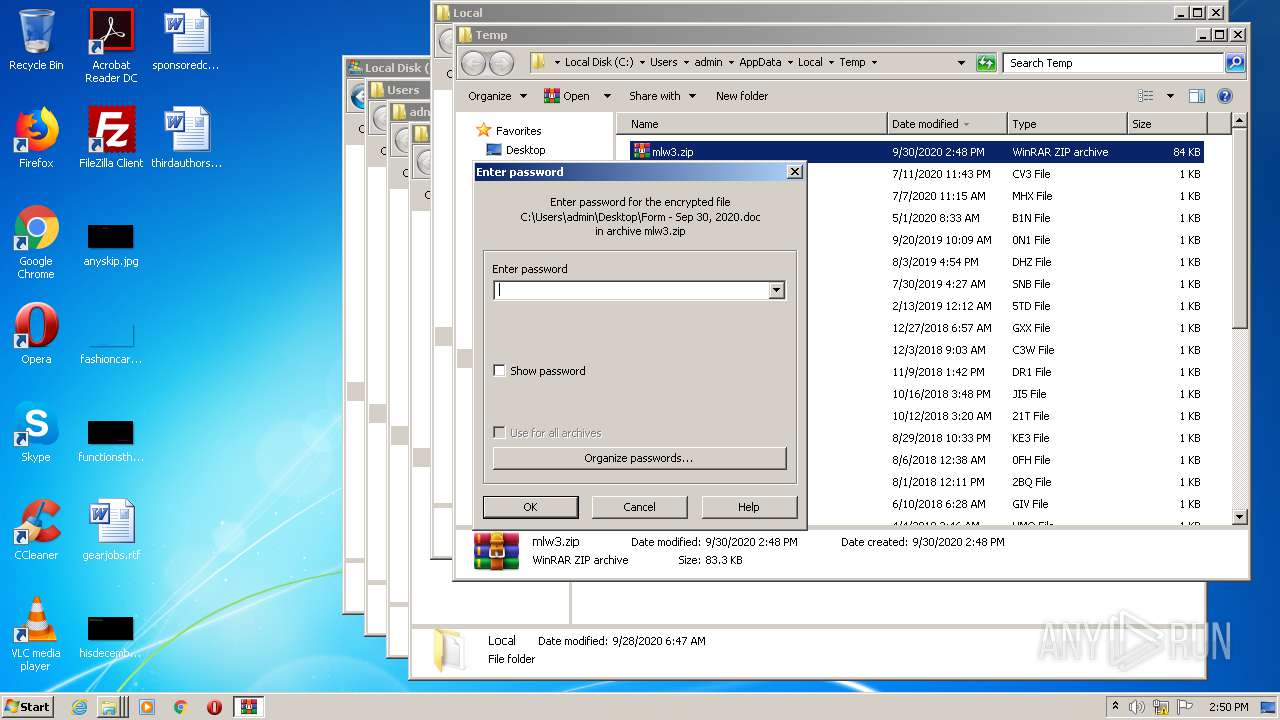
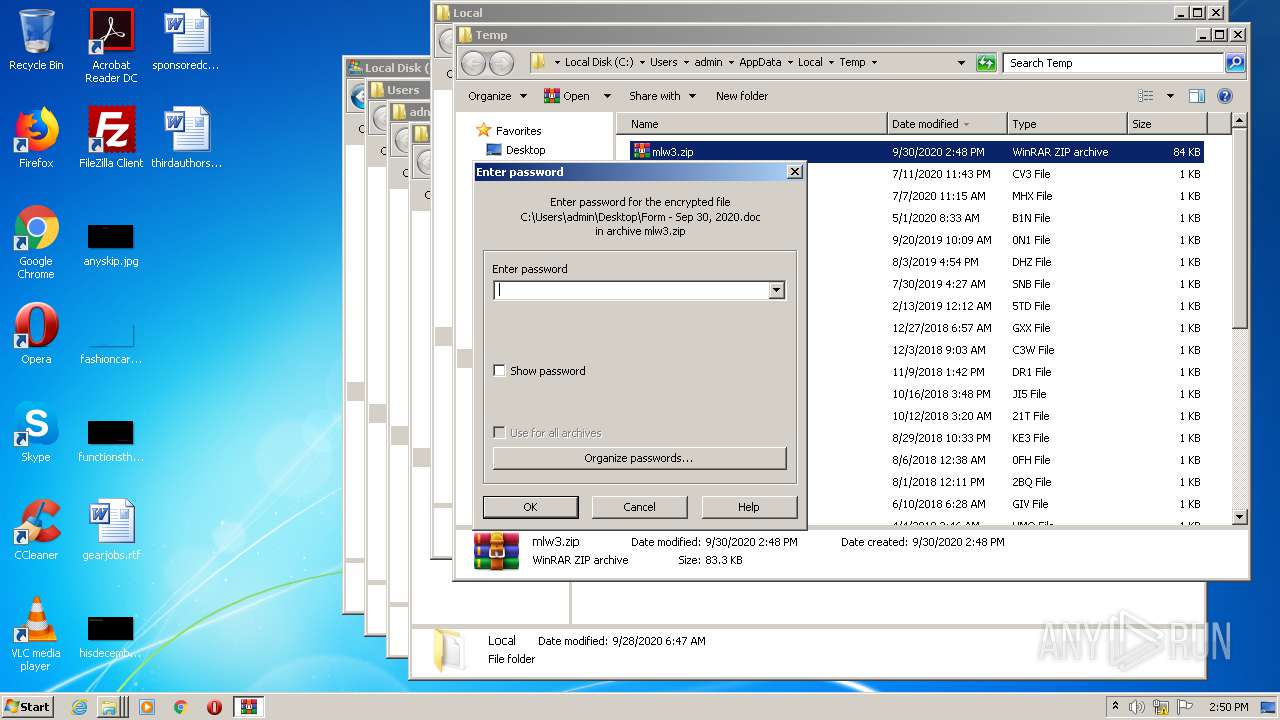
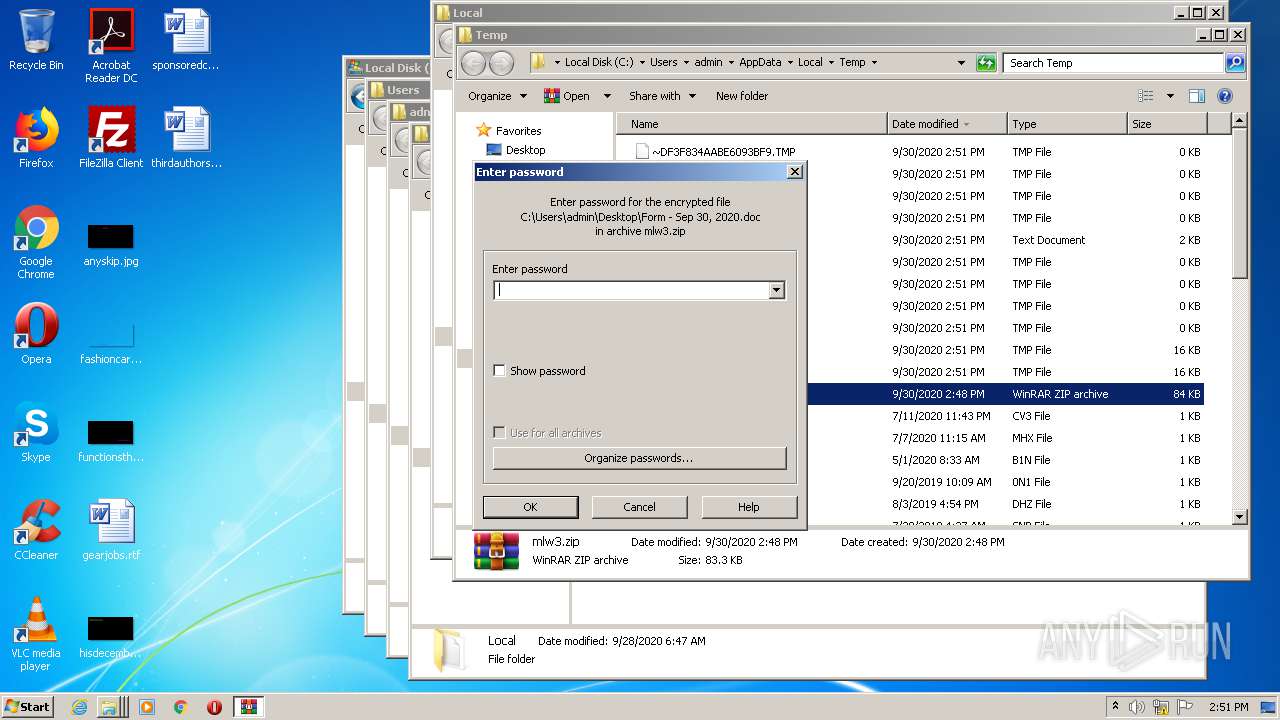
- WinRAR.exe (PID: 2740)
- explorer.exe (PID: 908)
- iexplore.exe (PID: 3440)
Changes internet zones settings
- iexplore.exe (PID: 3440)
Application launched itself
- iexplore.exe (PID: 3440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2020:09:30 00:02:02 |
| ZipCRC: | 0x6131d60b |
| ZipCompressedSize: | 85143 |
| ZipUncompressedSize: | 171479 |
| ZipFileName: | Form - Sep 30, 2020.doc |
Total processes
46
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3440 CREDAT:4134157 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 908 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3440 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
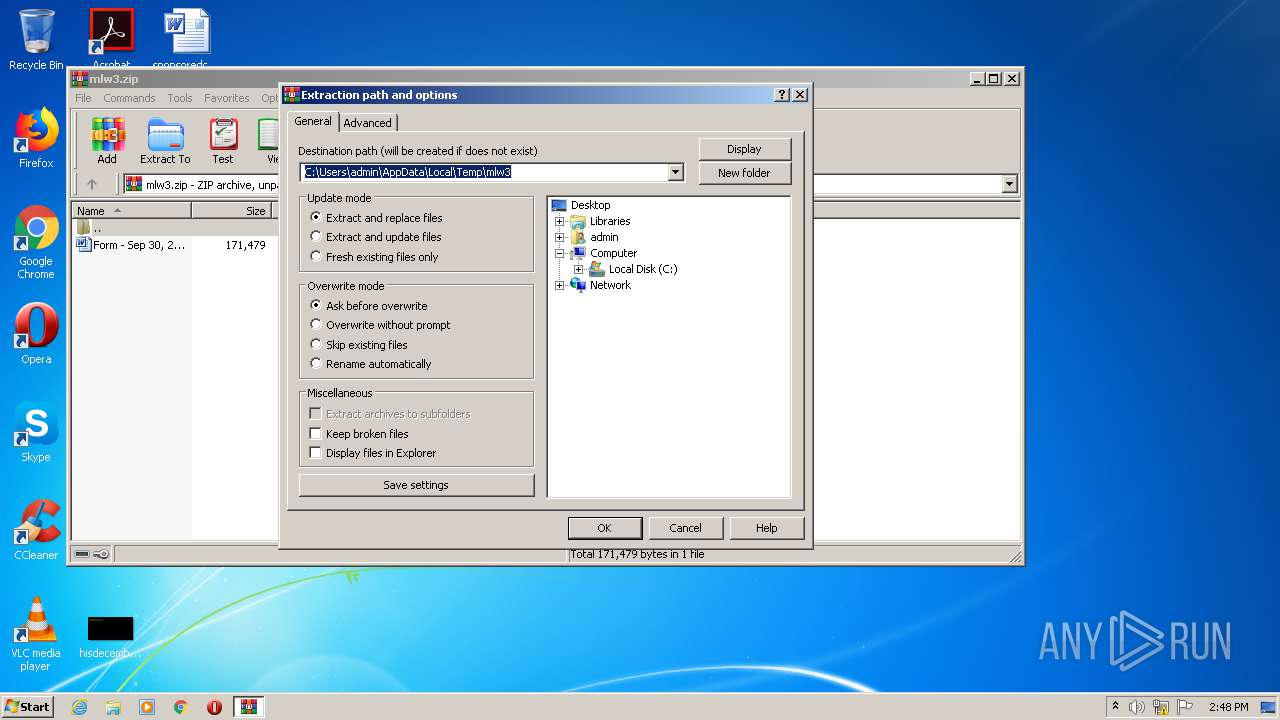
| 2740 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\AppData\Local\Temp\mlw3.zip" "?\" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3140 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\mlw3.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3440 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 380
Read events
1 232
Write events
147
Delete events
1
Modification events
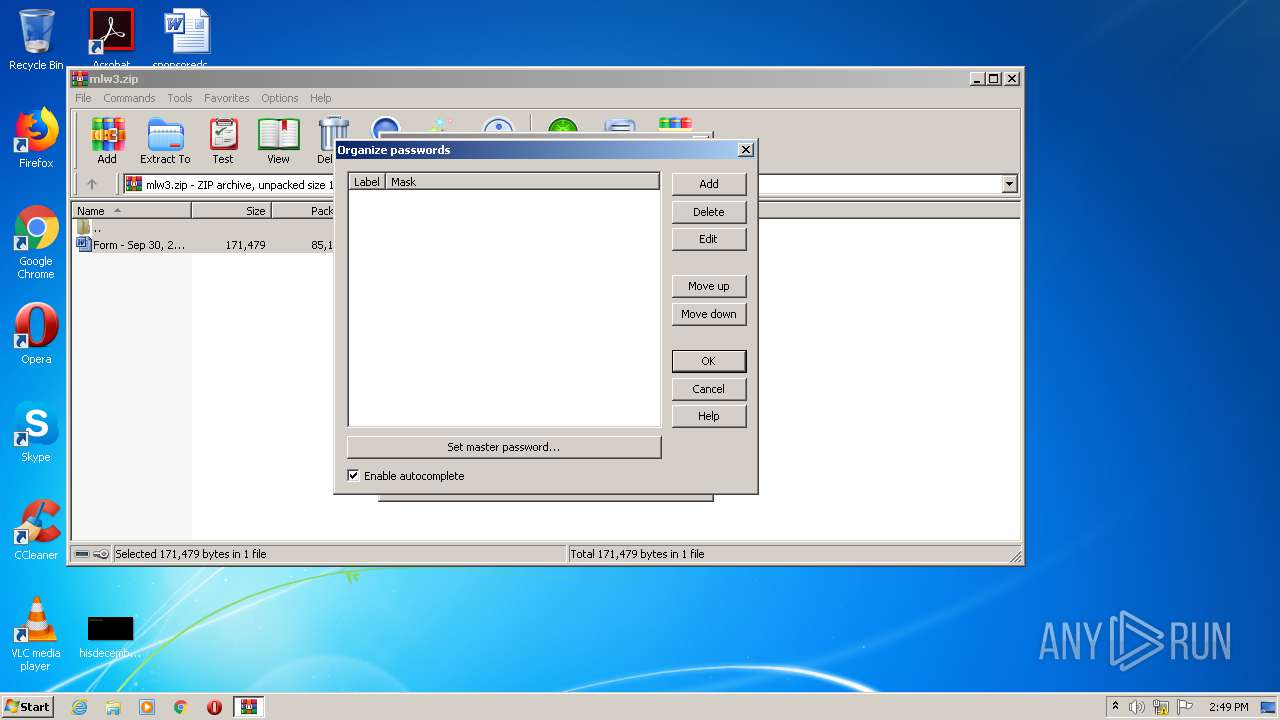
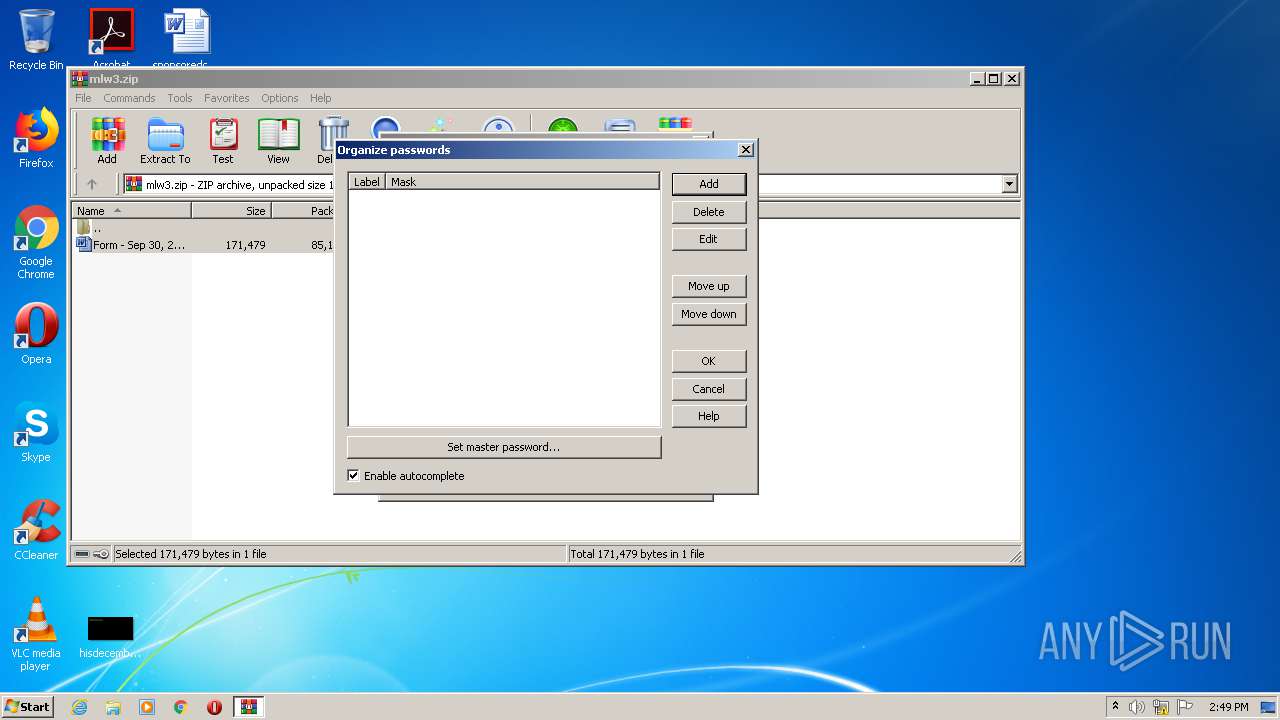
| (PID) Process: | (3140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3140) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\mlw3.zip | |||
| (PID) Process: | (3140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
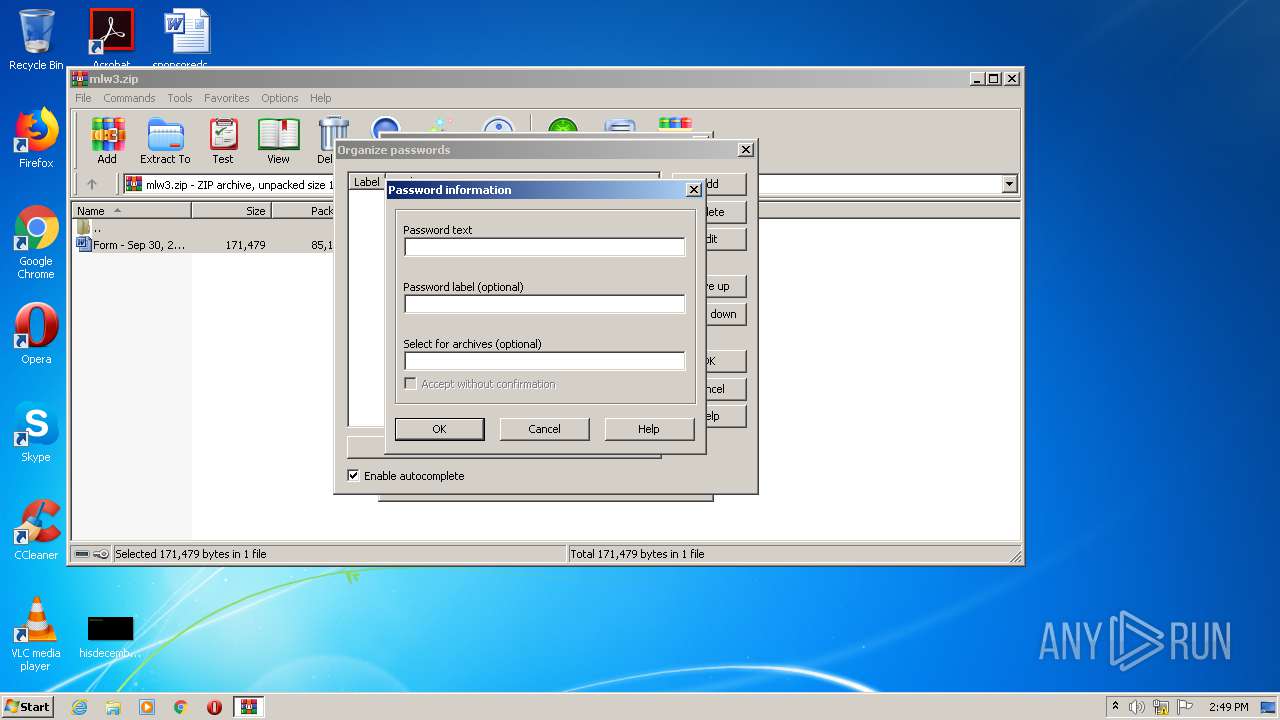
| (PID) Process: | (3140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
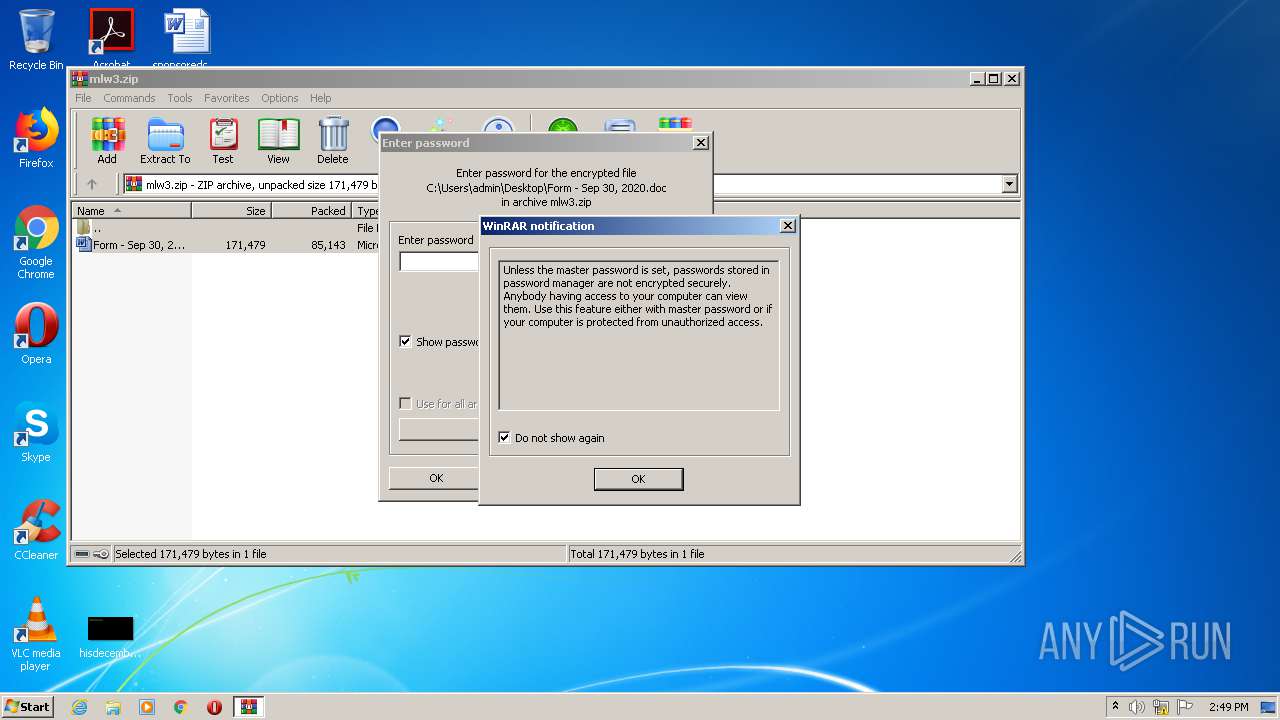
| (PID) Process: | (3140) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Notifications |
| Operation: | write | Name: | NotifyPswMan |
Value: 1 | |||
Executable files
0
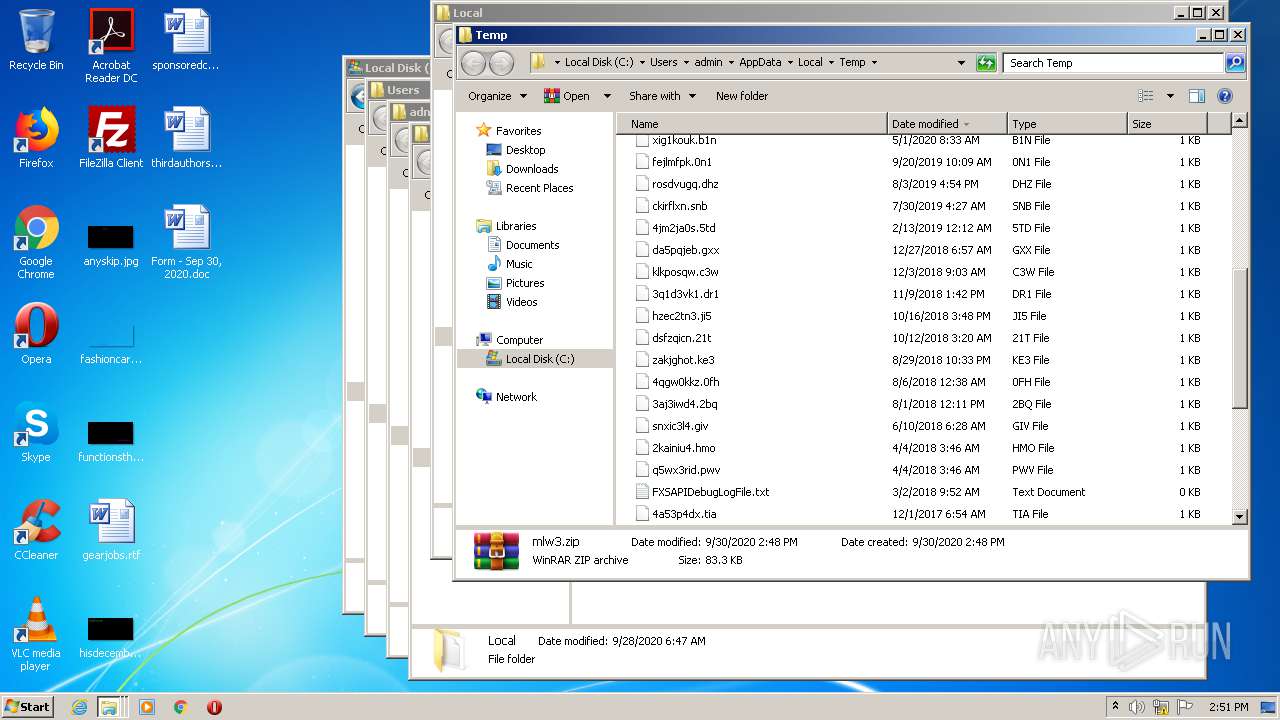
Suspicious files
14
Text files
10
Unknown types
0
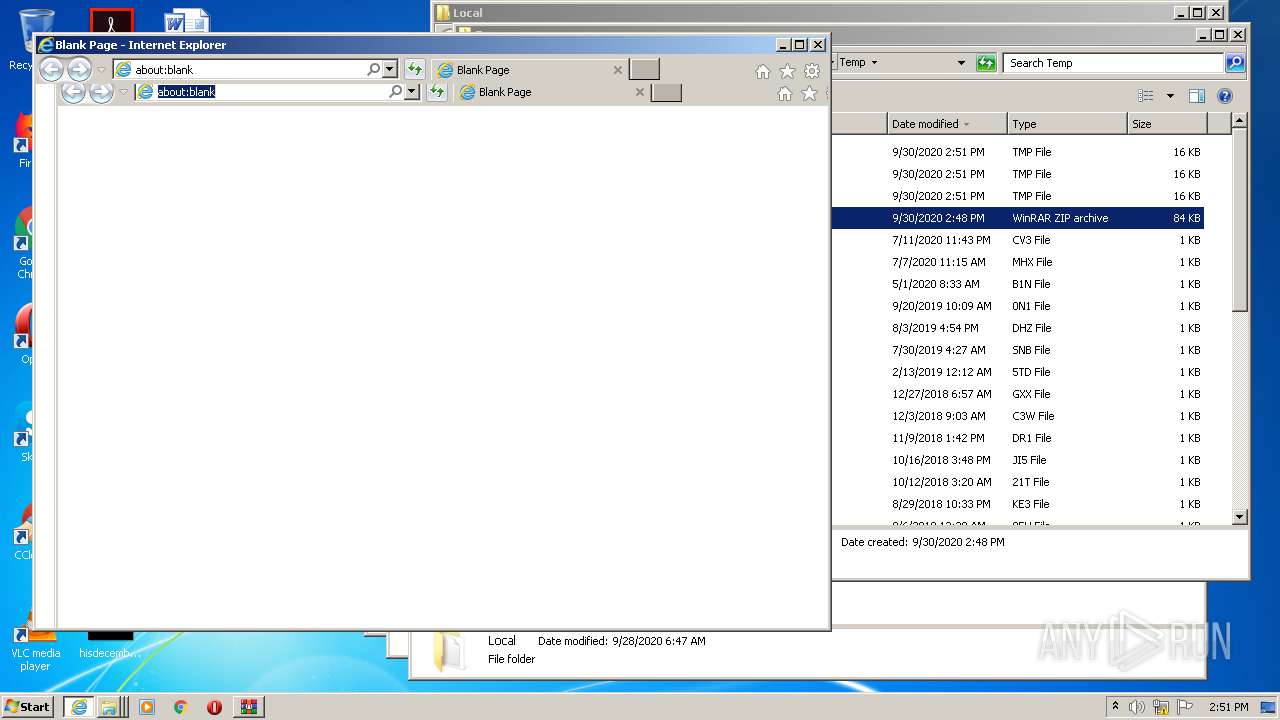
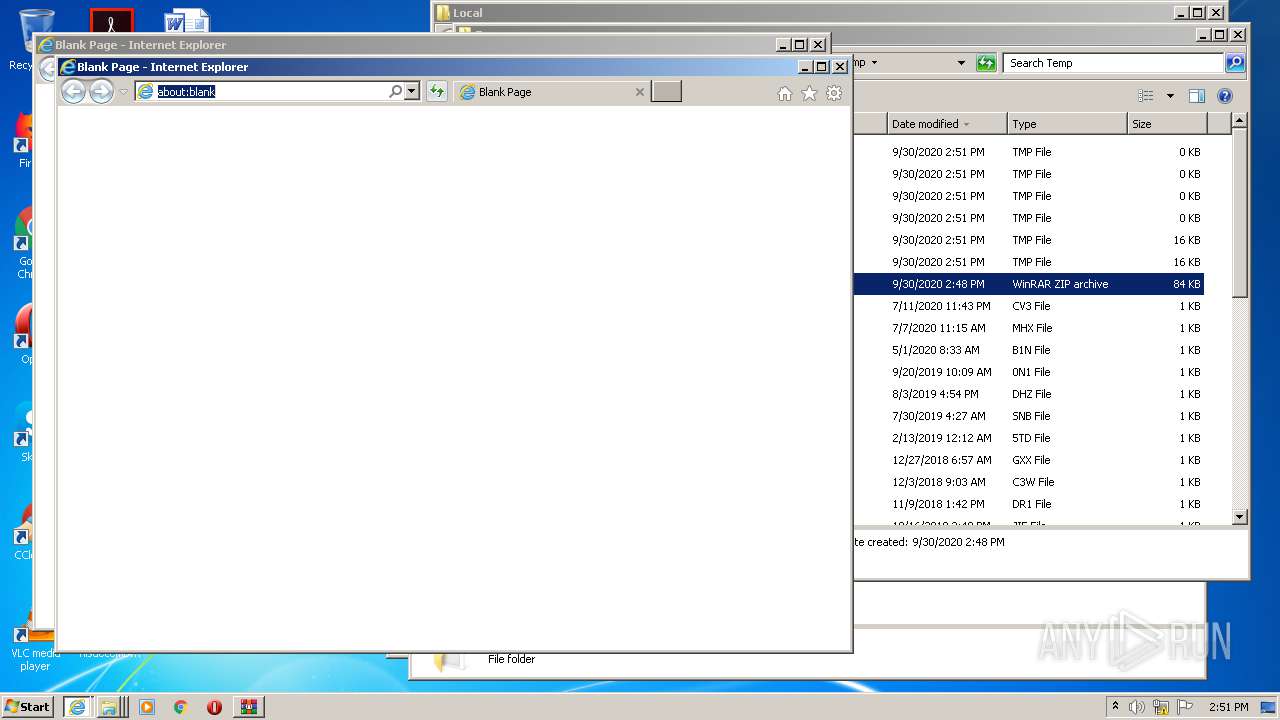
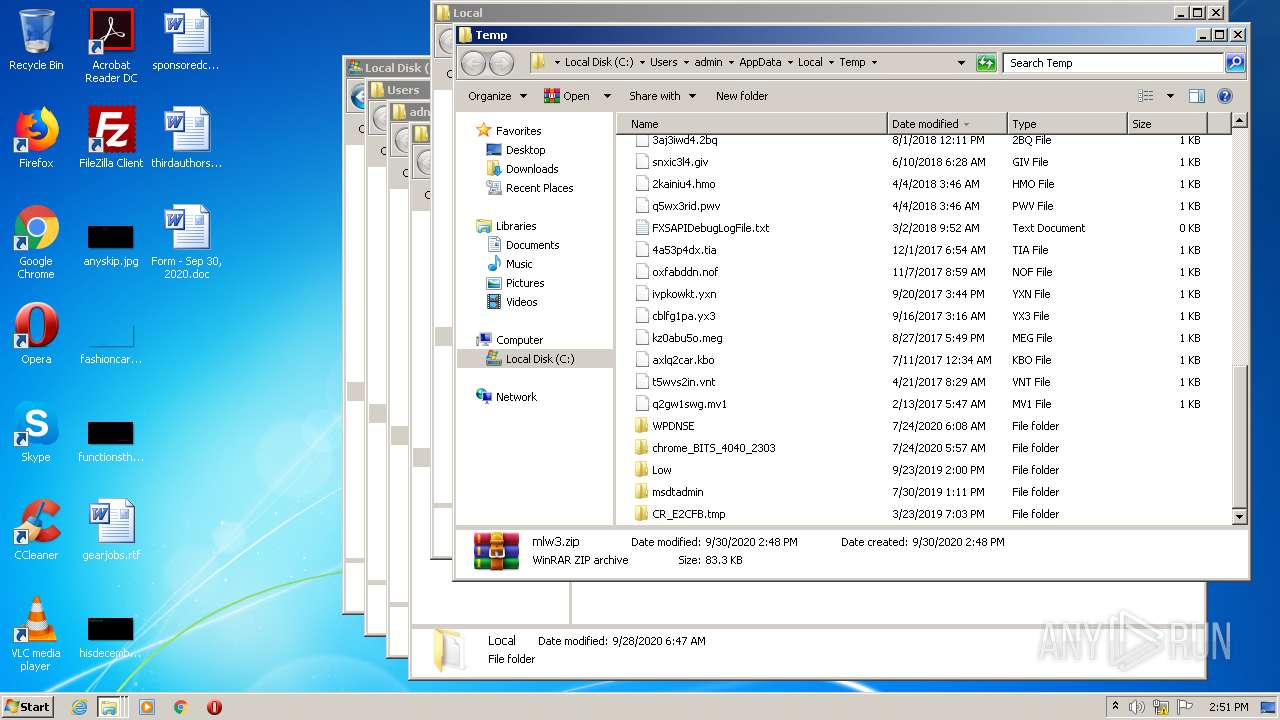
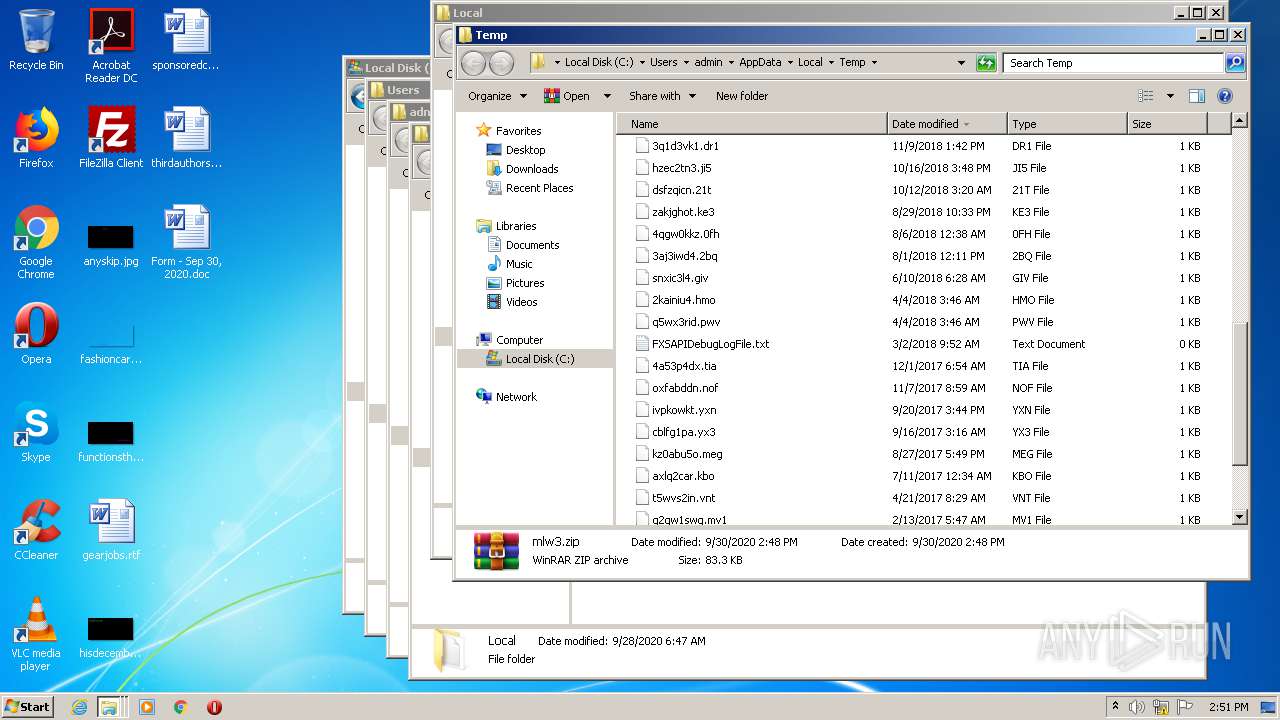
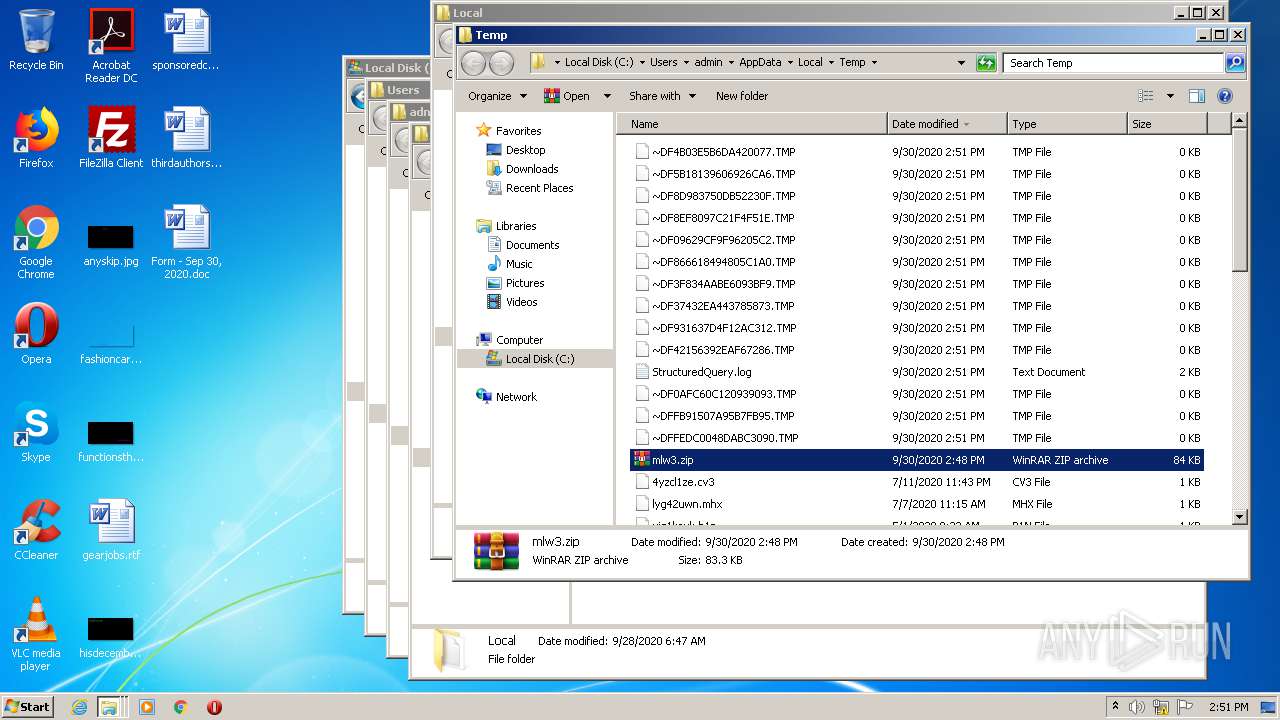
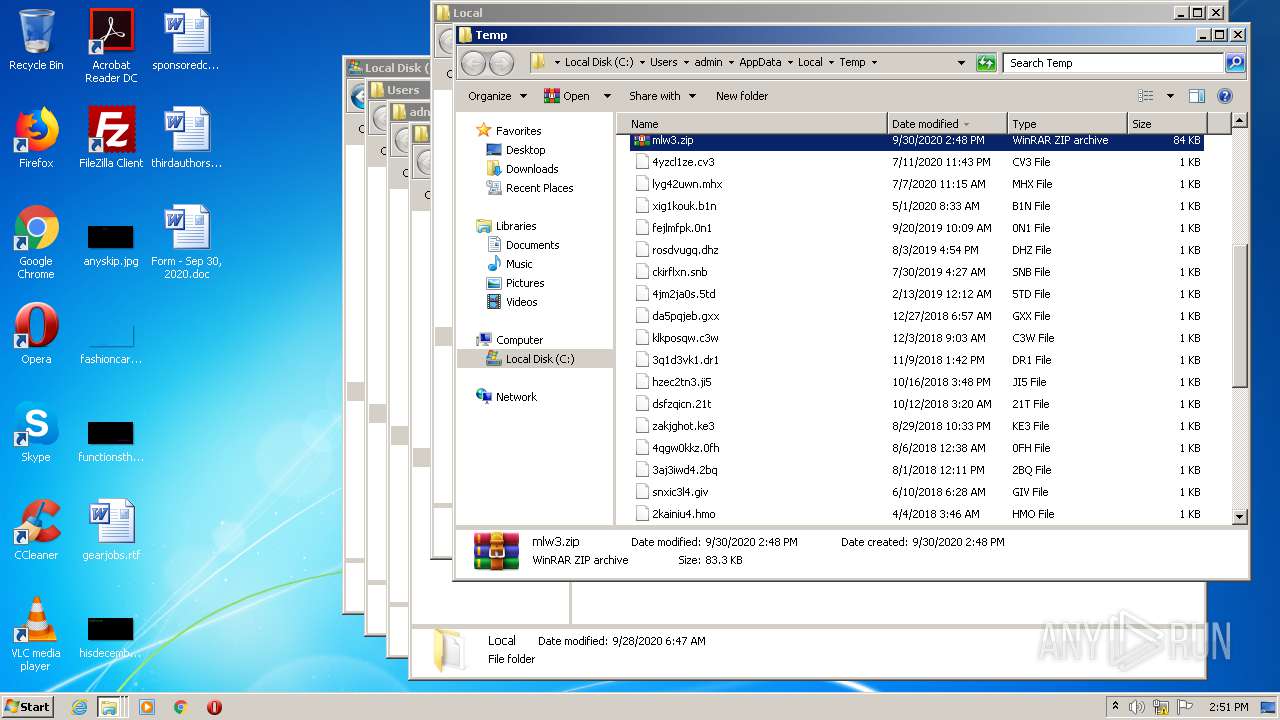
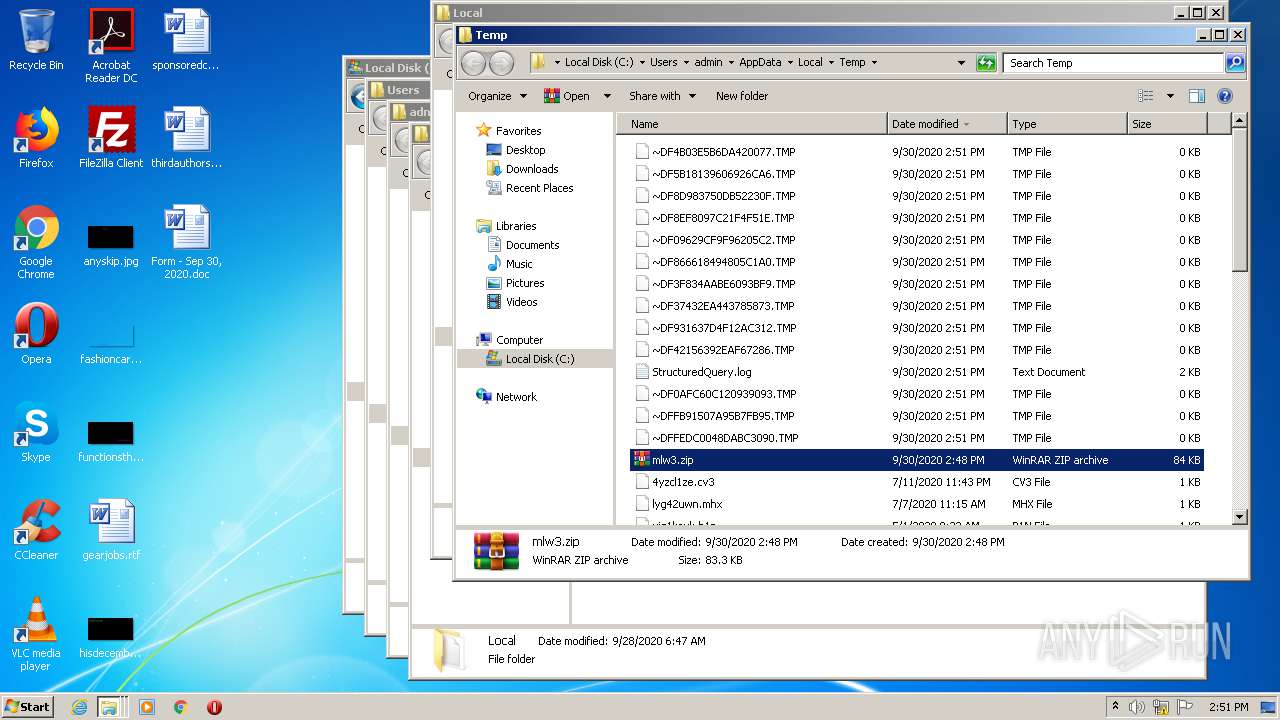
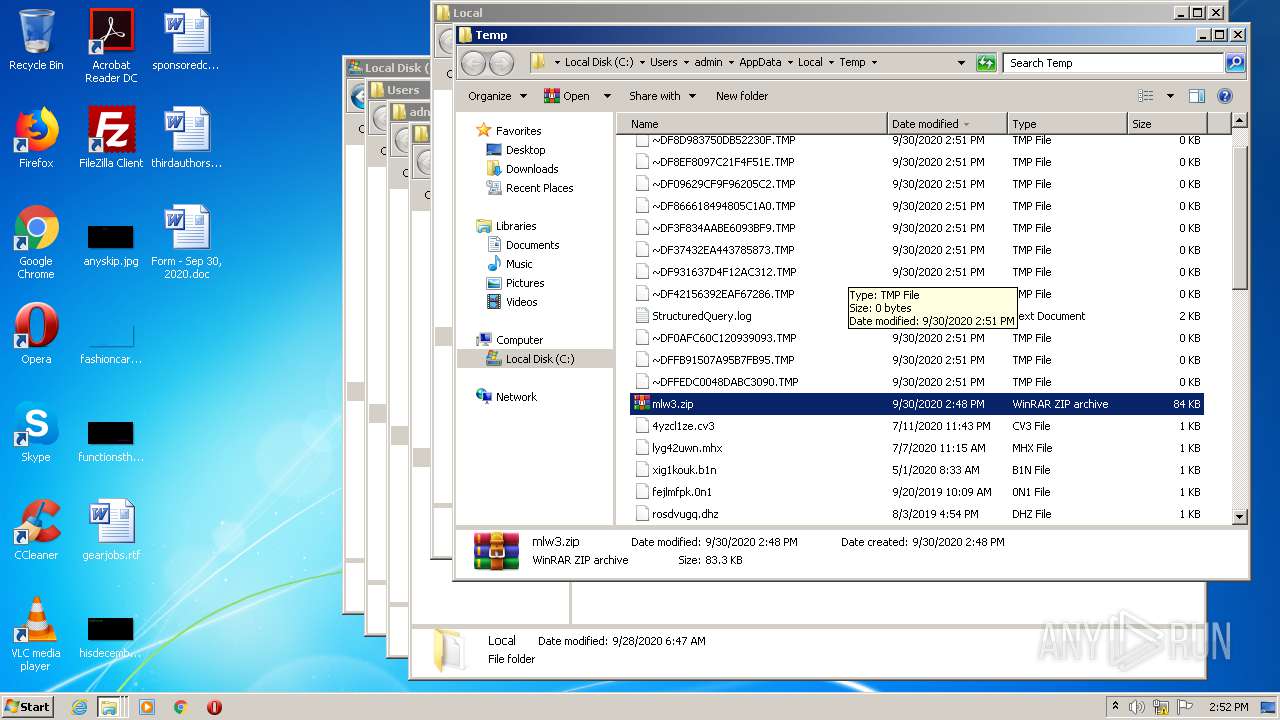
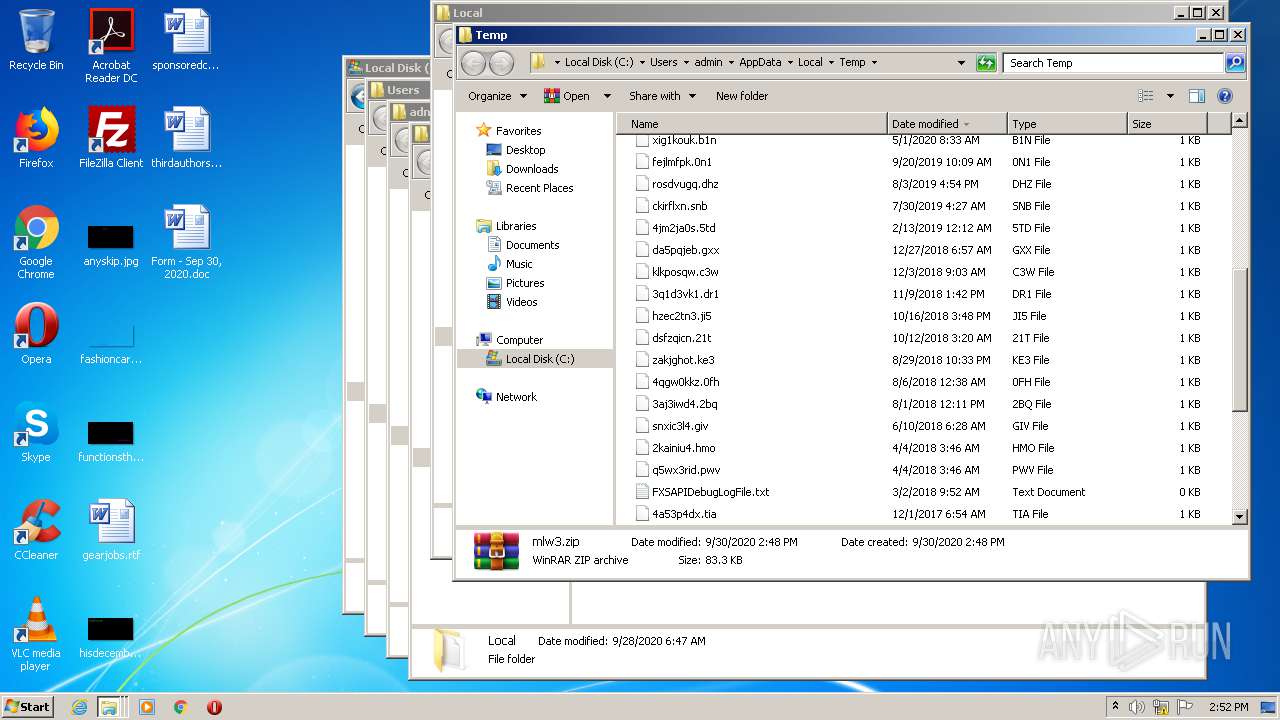
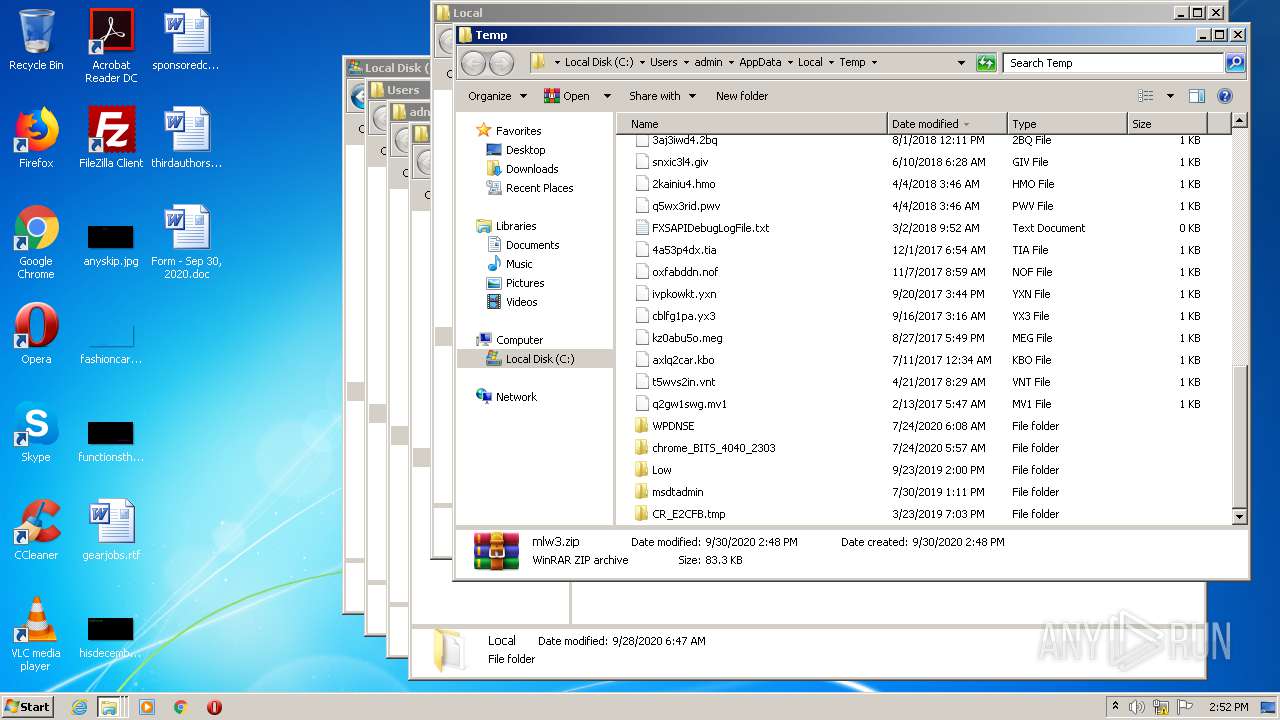
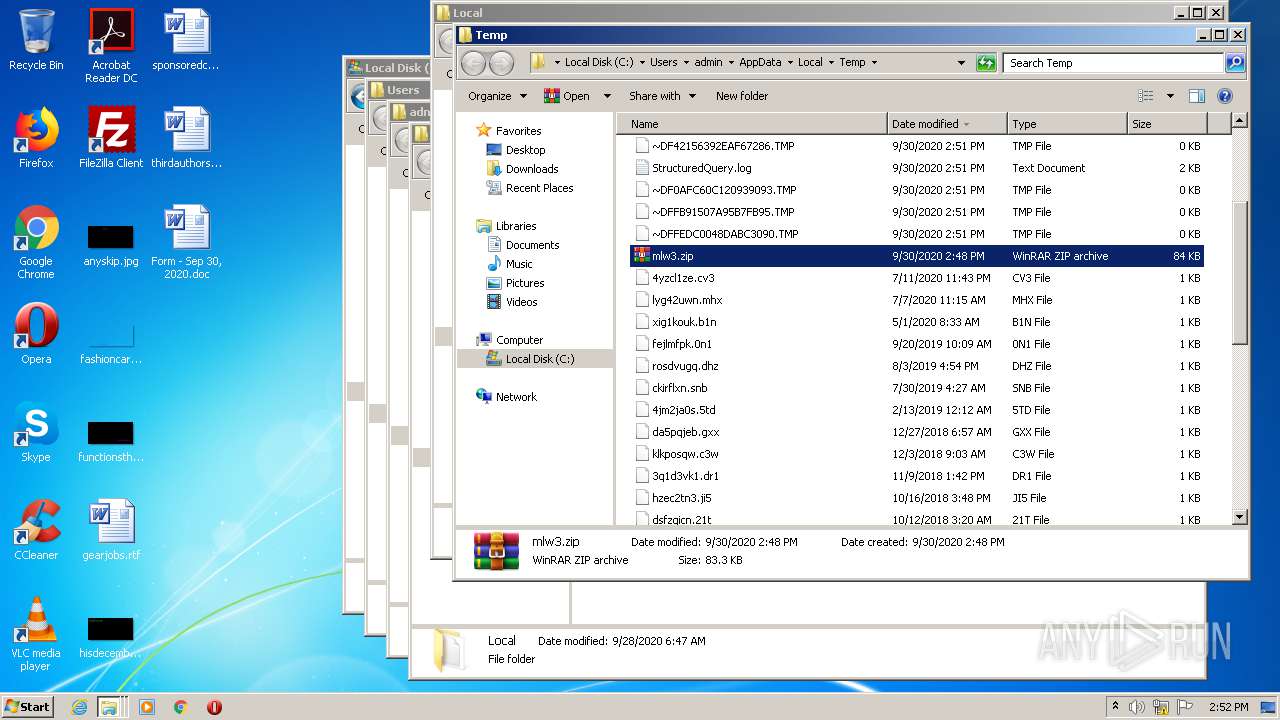
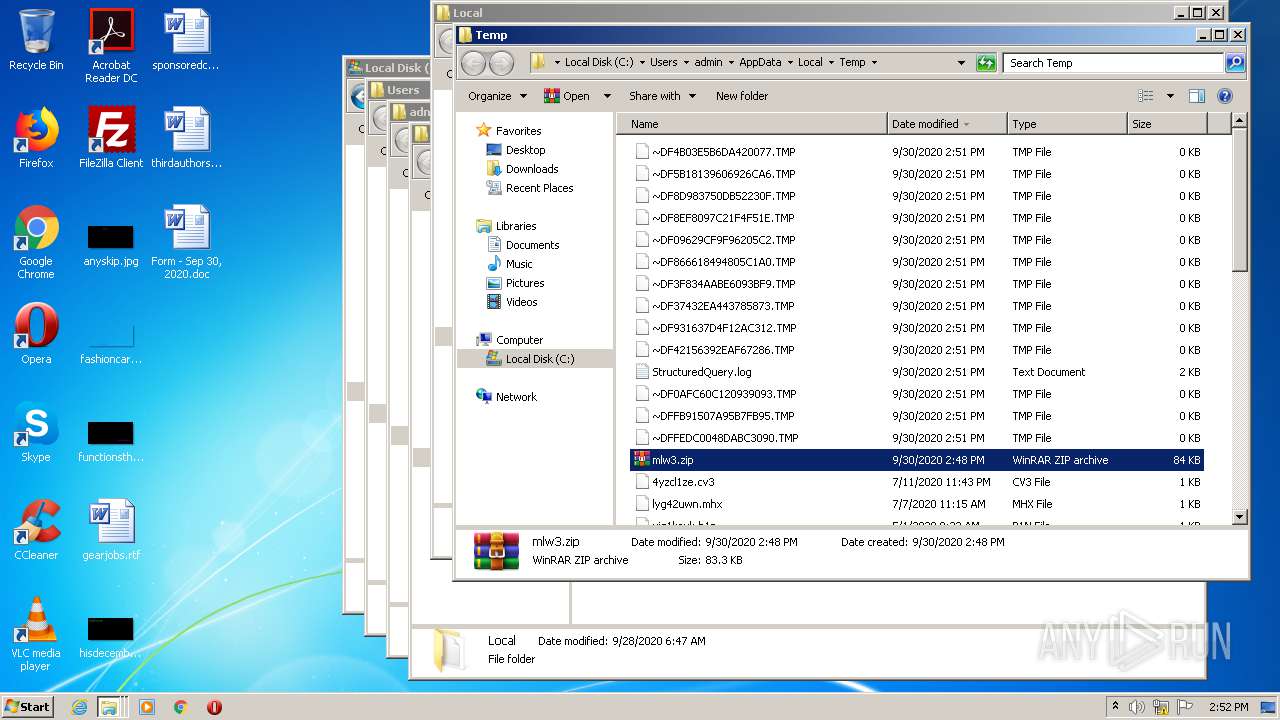
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3440 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF0AFC60C120939093.TMP | — | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFFB91507A95B7FB95.TMP | — | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFFEDC0048DABC3090.TMP | — | |
MD5:— | SHA256:— | |||
| 2436 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\P11GH0PO.txt | — | |
MD5:— | SHA256:— | |||
| 2436 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\JXD8I3C4.txt | — | |
MD5:— | SHA256:— | |||
| 2436 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\qsml[1].htm | — | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF37432EA443785873.TMP | — | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF42156392EAF67286.TMP | — | |
MD5:— | SHA256:— | |||
| 3440 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF3F834AABE6093BF9.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
5
DNS requests
10
Threats
0
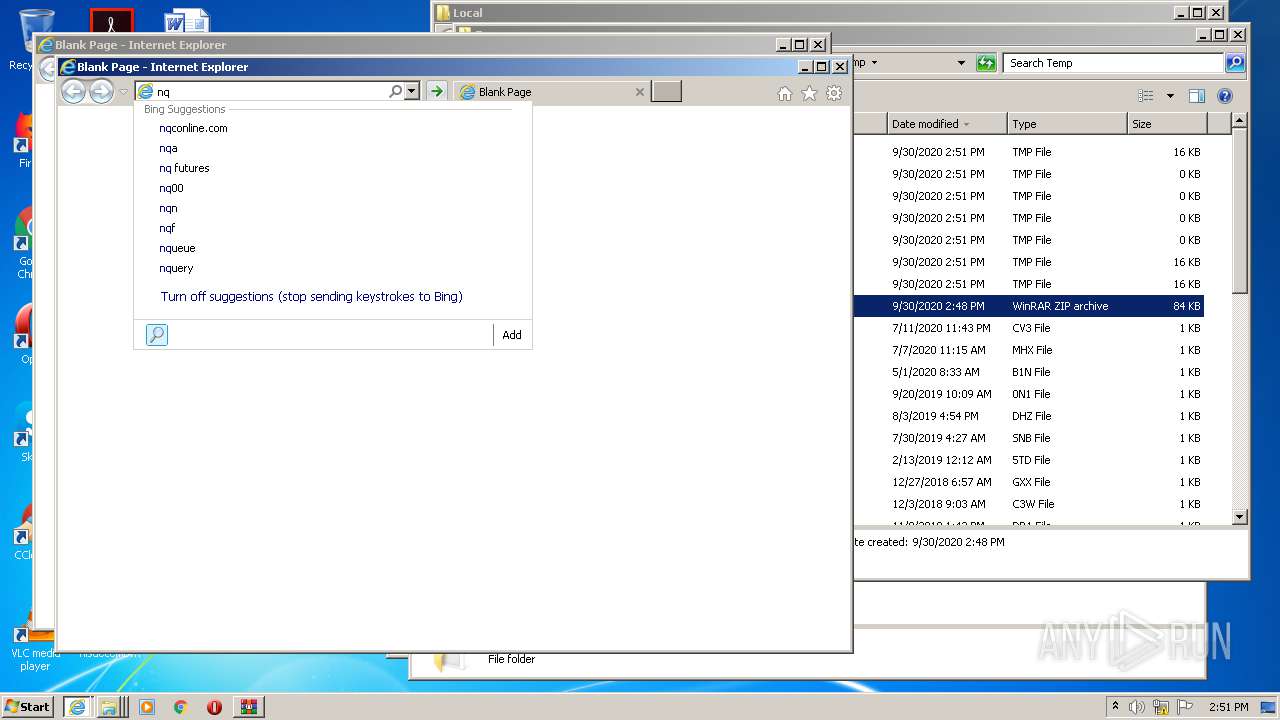
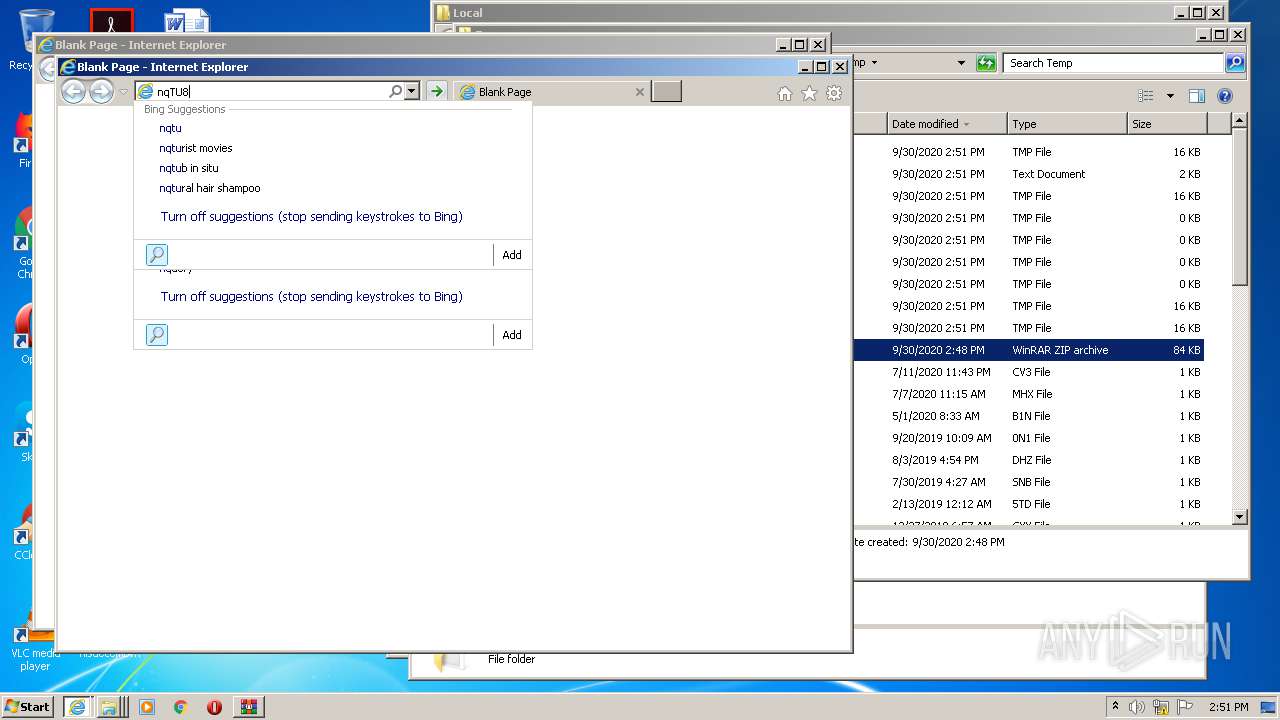
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
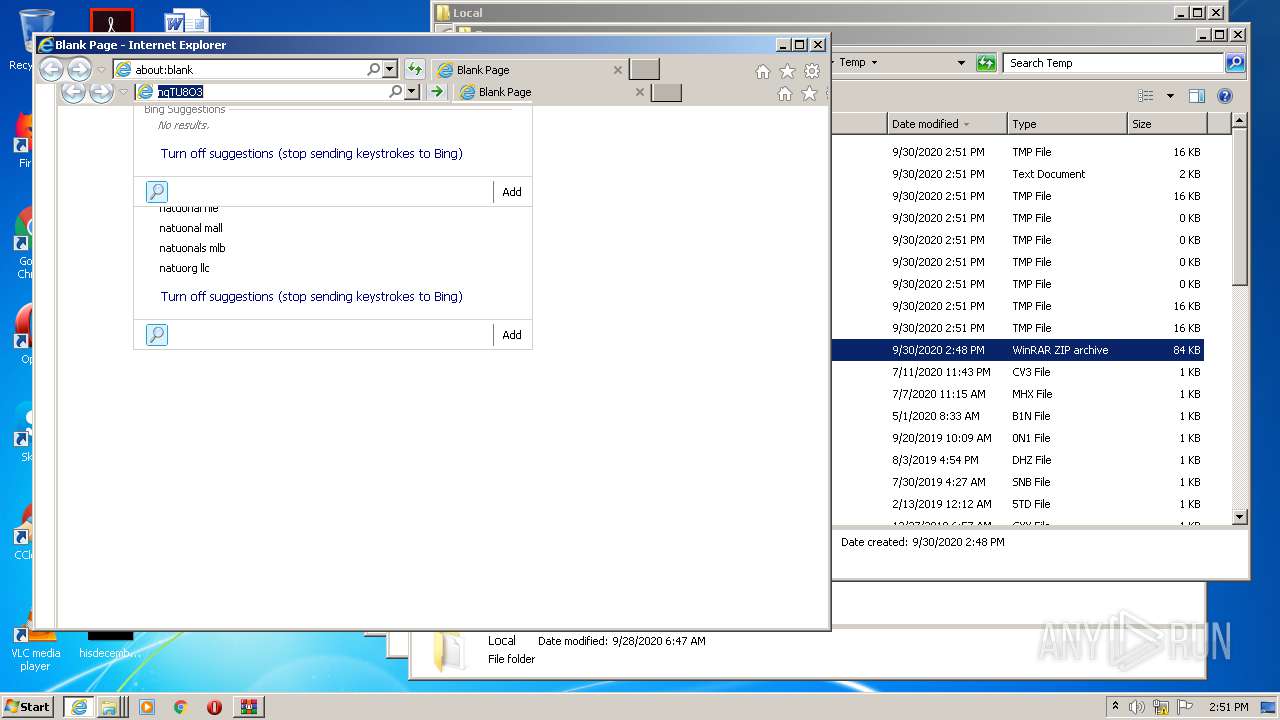
2436 | iexplore.exe | GET | — | 13.107.13.80:80 | http://api.bing.com/qsml.aspx?query=nqT&maxwidth=398&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
2436 | iexplore.exe | GET | 200 | 13.107.13.80:80 | http://api.bing.com/qsml.aspx?query=nq&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 222 b | whitelisted |
2436 | iexplore.exe | GET | 200 | 13.107.13.80:80 | http://api.bing.com/qsml.aspx?query=nqTU8&maxwidth=398&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 240 b | whitelisted |
2436 | iexplore.exe | GET | 200 | 13.107.13.80:80 | http://api.bing.com/qsml.aspx?query=nqTU&maxwidth=398&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 223 b | whitelisted |
2436 | iexplore.exe | GET | 200 | 13.107.13.80:80 | http://api.bing.com/qsml.aspx?query=nqTU8O&maxwidth=398&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 241 b | whitelisted |
3440 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2436 | iexplore.exe | GET | 200 | 13.107.13.80:80 | http://api.bing.com/qsml.aspx?query=nqTU8O3&maxwidth=398&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 172 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3440 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2436 | iexplore.exe | 13.107.13.80:80 | api.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |